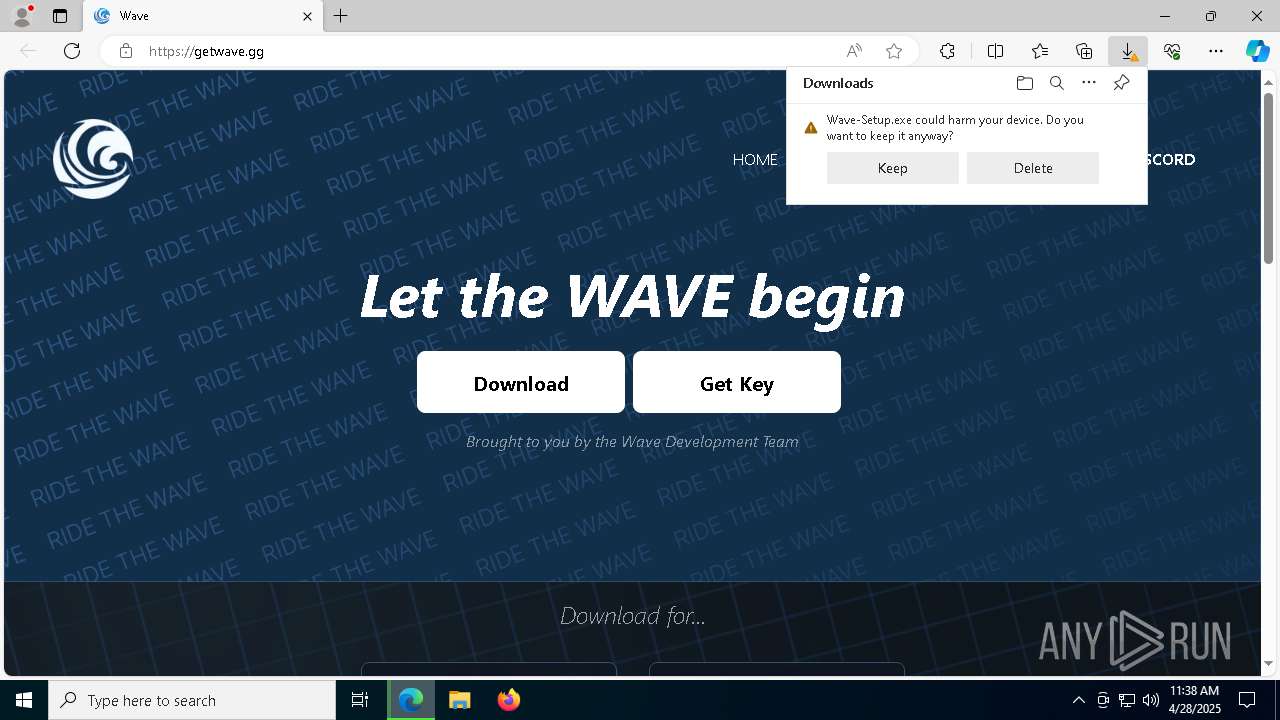
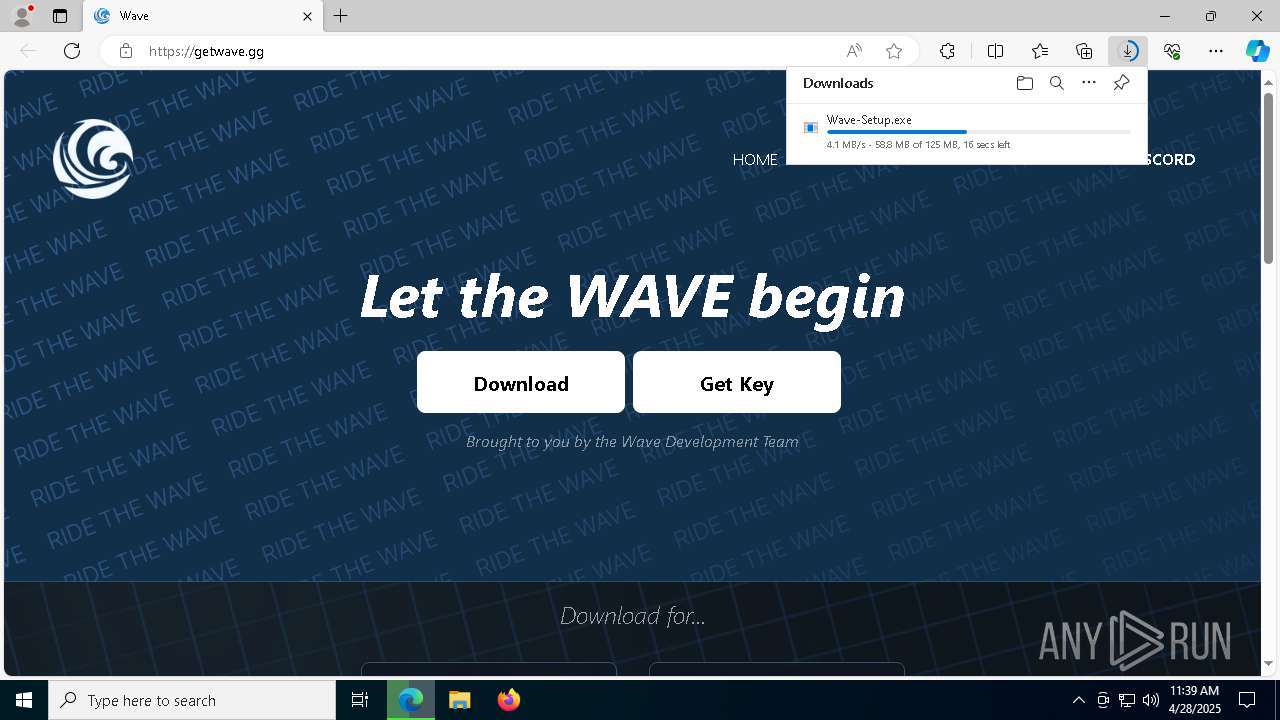
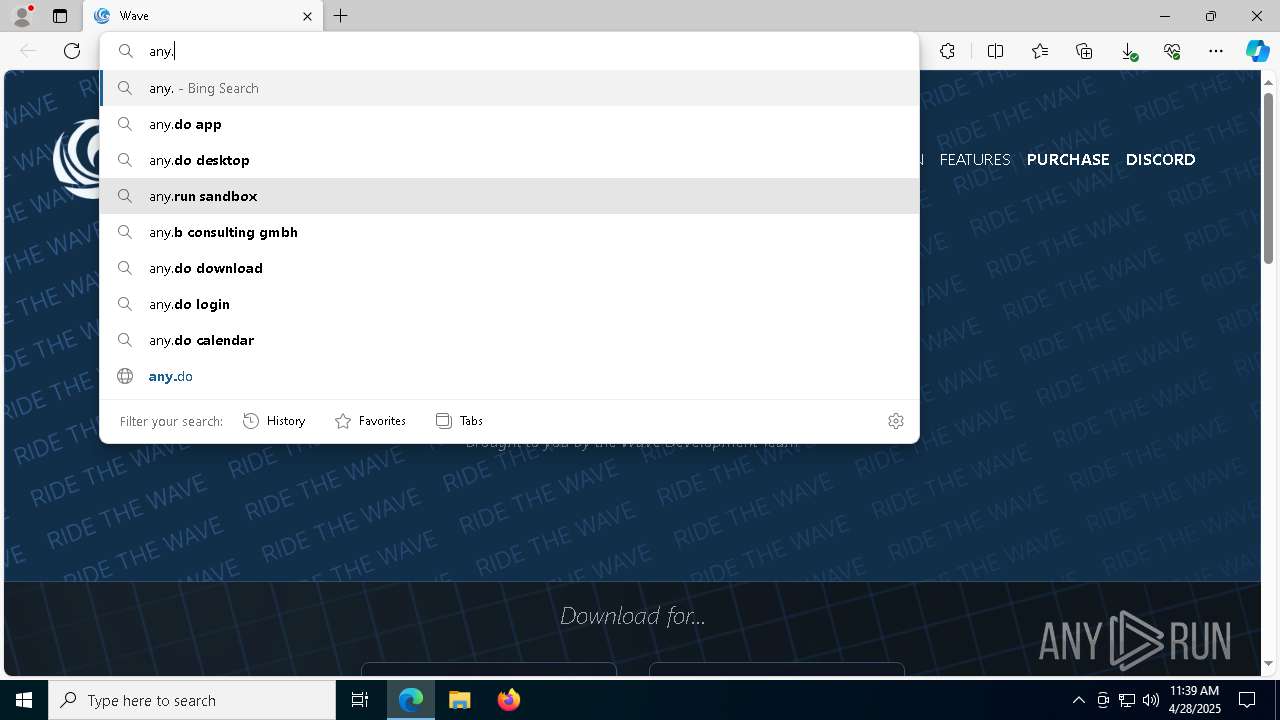
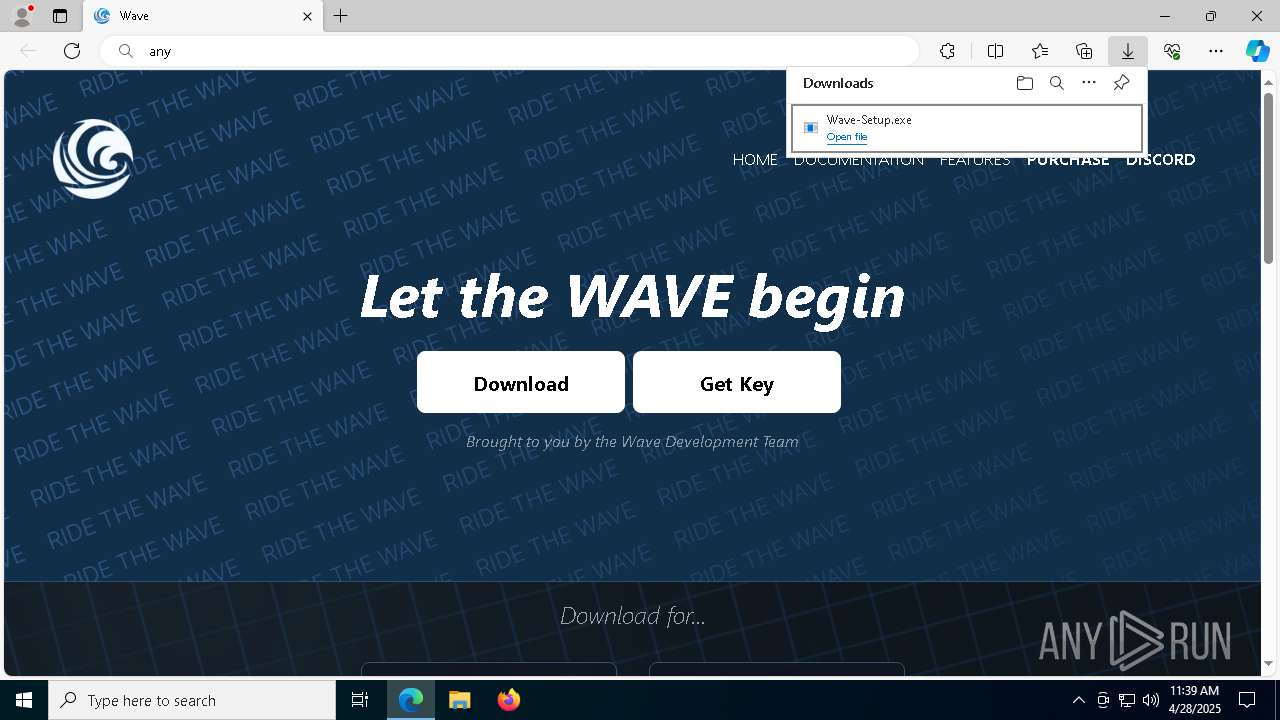
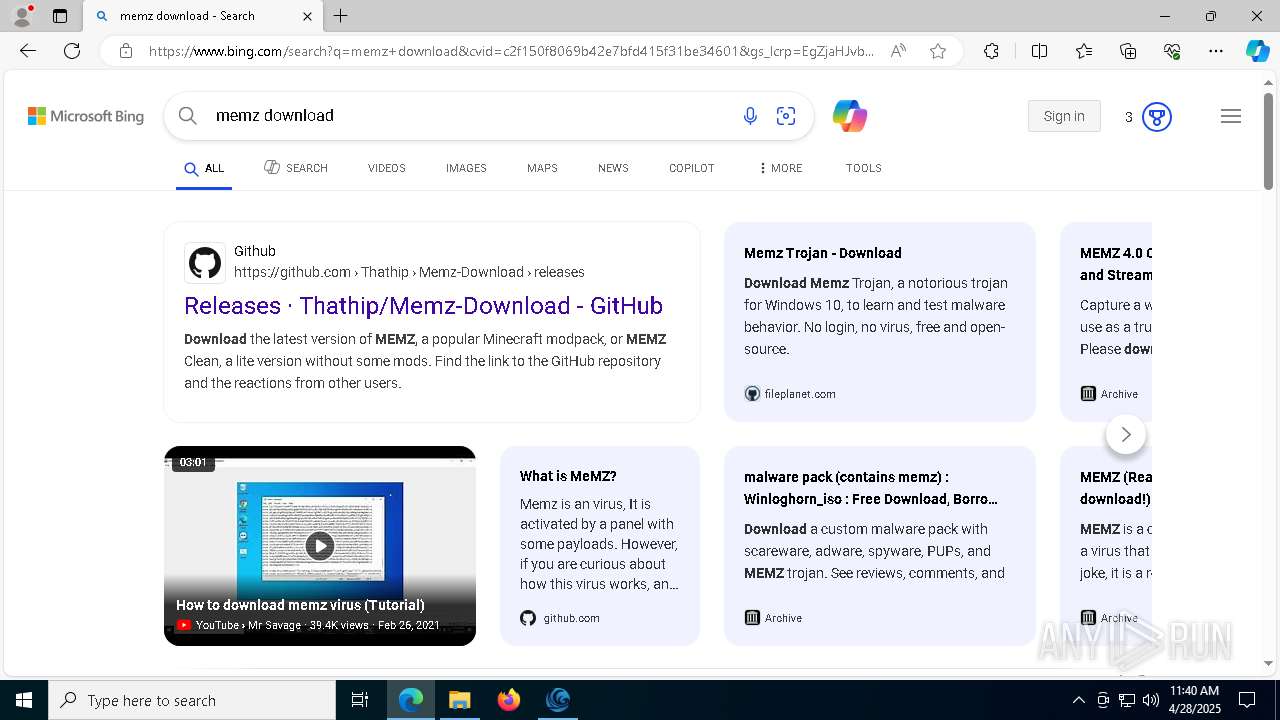
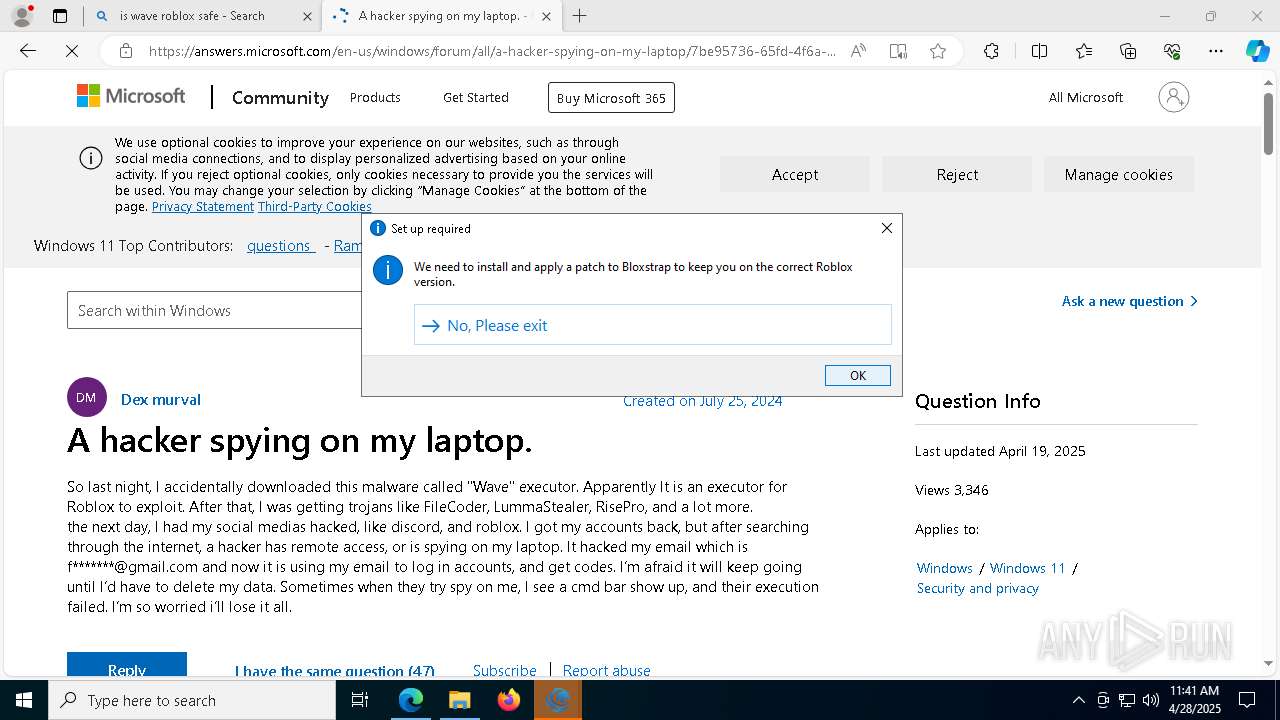
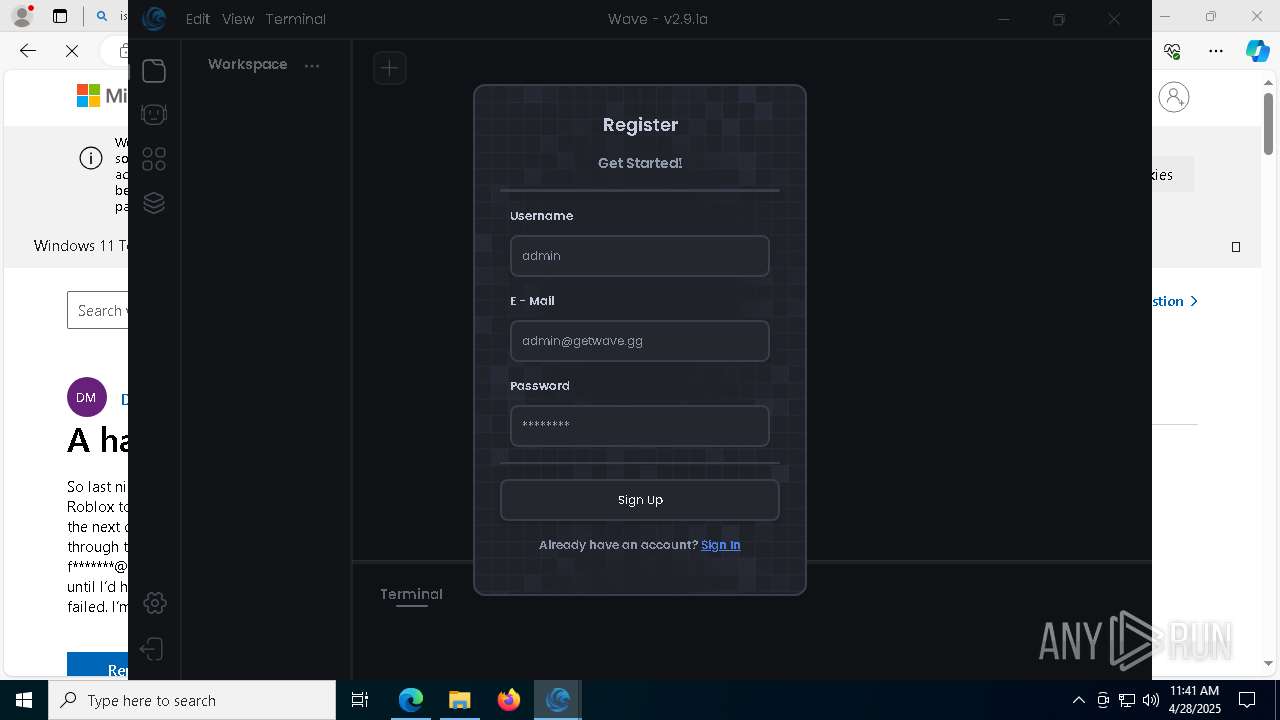
| URL: | Getwave.gg |
| Full analysis: | https://app.any.run/tasks/0990f4f6-1da5-42f9-bc90-a2deb717c798 |
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2025, 11:38:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 4F5F4DC86BF93A2BFC418B2581B686AB |
| SHA1: | 488925D8427633473CB5B87F8BA853C0BD95A195 |
| SHA256: | 13839180D1CC6C97A4F450FF572E74E96166DCEC33D2E60A7C52048422101E16 |
| SSDEEP: | 3:gqC:C |
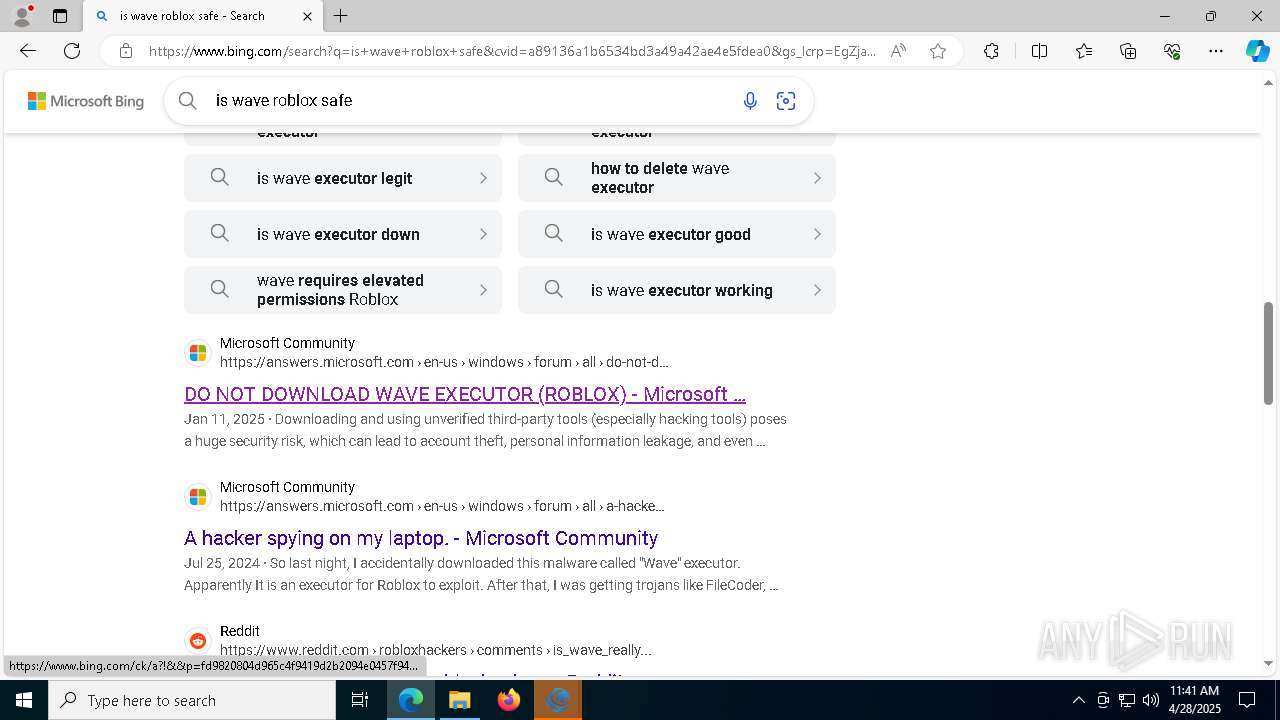
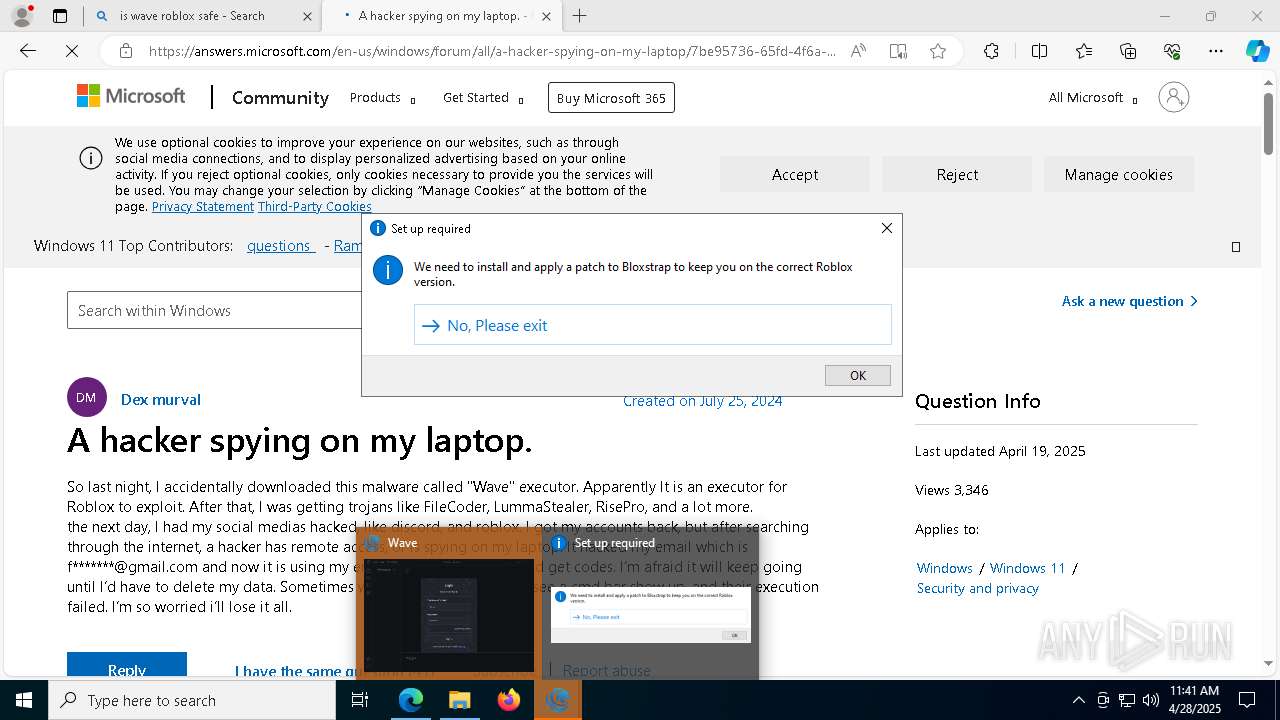
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1088)
SUSPICIOUS
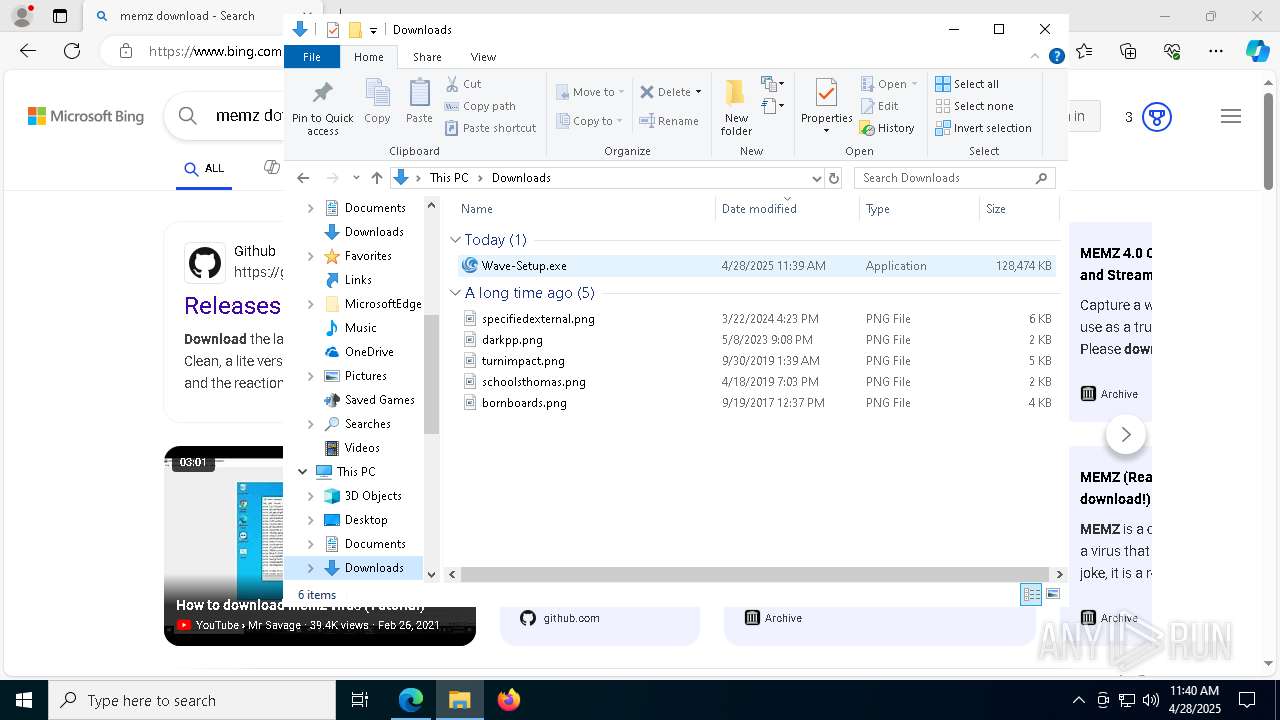
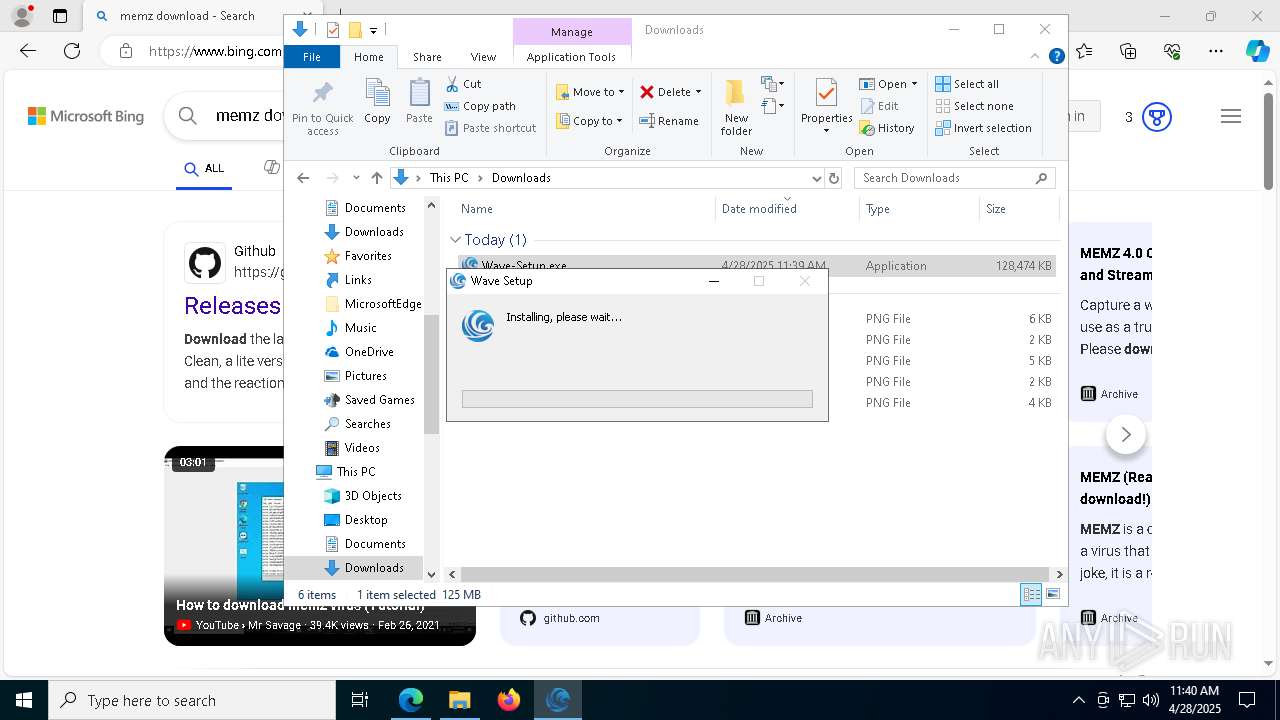
Executable content was dropped or overwritten
- Wave-Setup.exe (PID: 3968)
The process creates files with name similar to system file names
- Wave-Setup.exe (PID: 3968)
Malware-specific behavior (creating "System.dll" in Temp)
- Wave-Setup.exe (PID: 3968)
Get information on the list of running processes
- Wave-Setup.exe (PID: 3968)
- cmd.exe (PID: 5036)
Starts CMD.EXE for commands execution
- Wave-Setup.exe (PID: 3968)
- Wave.exe (PID: 3828)
- powershell.exe (PID: 1088)
- Wave.exe (PID: 5608)
Reads security settings of Internet Explorer
- Wave-Setup.exe (PID: 3968)
Process drops legitimate windows executable
- Wave-Setup.exe (PID: 3968)
Drops 7-zip archiver for unpacking
- Wave-Setup.exe (PID: 3968)
There is functionality for taking screenshot (YARA)
- Wave-Setup.exe (PID: 3968)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5008)
Starts process via Powershell
- powershell.exe (PID: 1088)
Creates a software uninstall entry
- Wave-Setup.exe (PID: 3968)
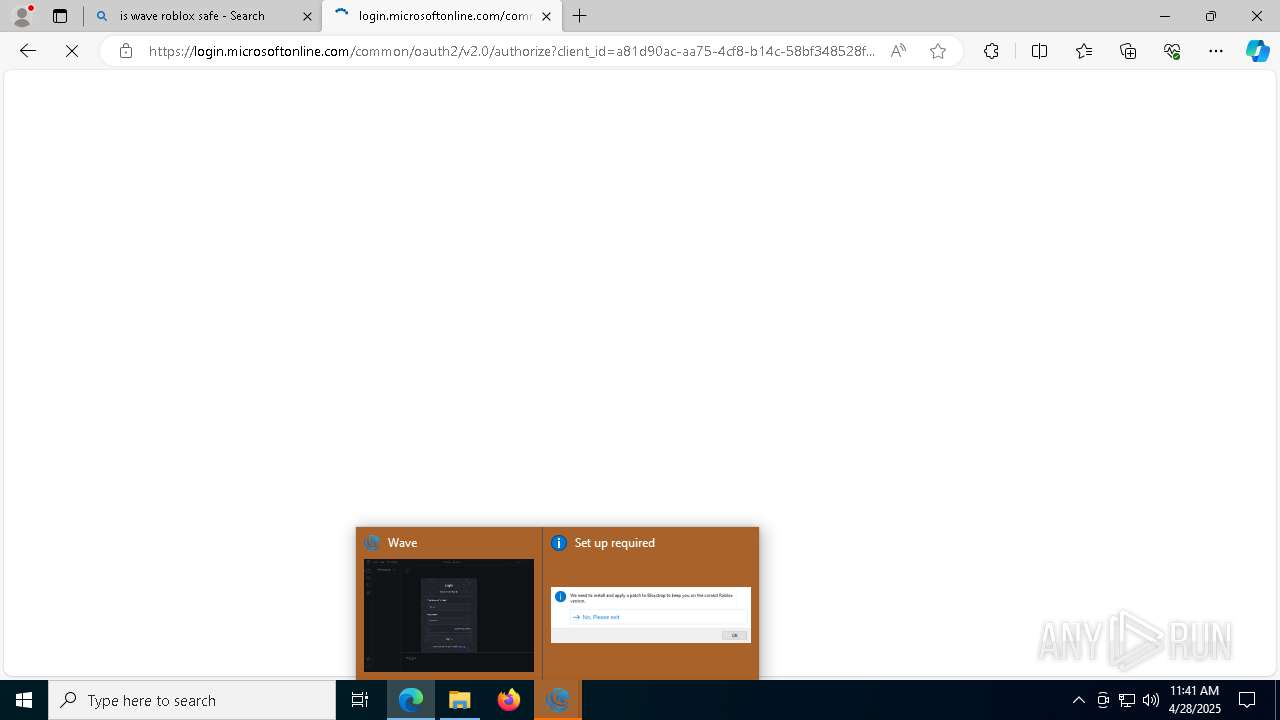
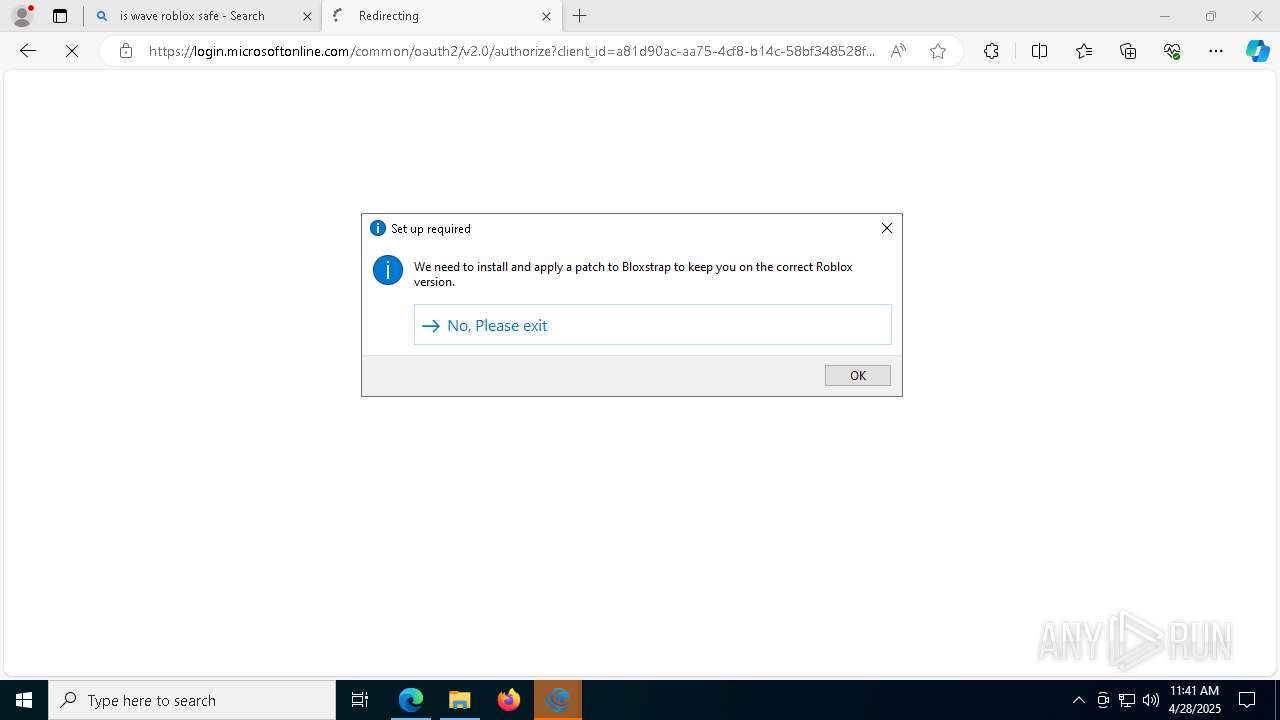
Application launched itself
- Wave.exe (PID: 3828)
- Wave.exe (PID: 5608)
Executing commands from a ".bat" file
- Wave.exe (PID: 3828)
- powershell.exe (PID: 1088)
Starts application with an unusual extension
- cmd.exe (PID: 4724)
The executable file from the user directory is run by the CMD process
- Wave.exe (PID: 5608)
INFO
Application launched itself
- msedge.exe (PID: 6036)
Reads the computer name
- identity_helper.exe (PID: 7960)
- Wave-Setup.exe (PID: 3968)
Checks supported languages
- identity_helper.exe (PID: 7960)
- Wave-Setup.exe (PID: 3968)
Executable content was dropped or overwritten
- msedge.exe (PID: 6036)
Reads Environment values
- identity_helper.exe (PID: 7960)
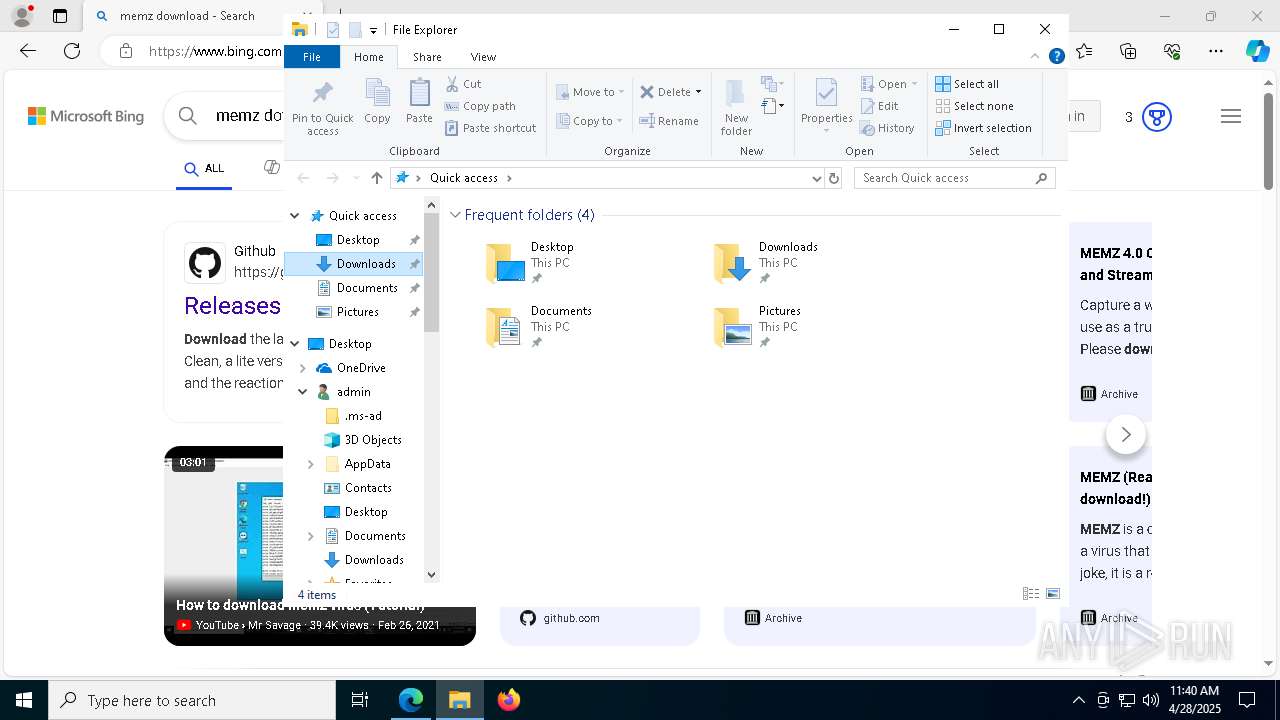
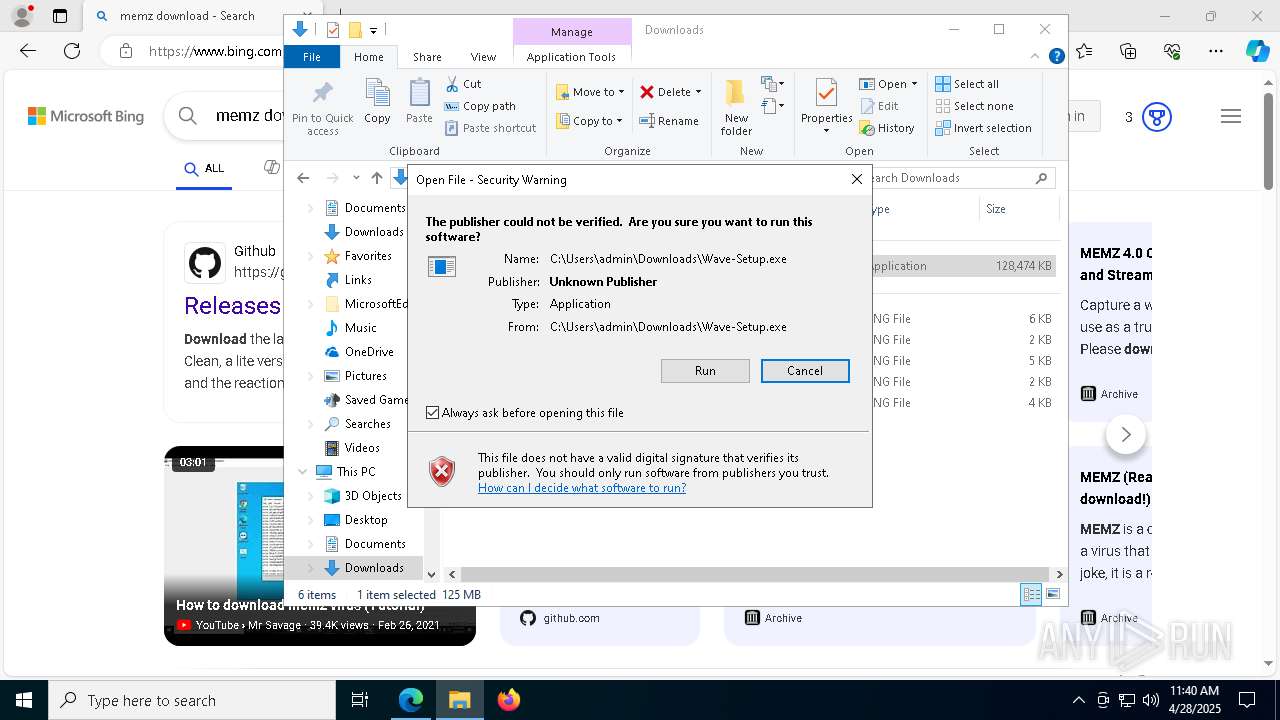
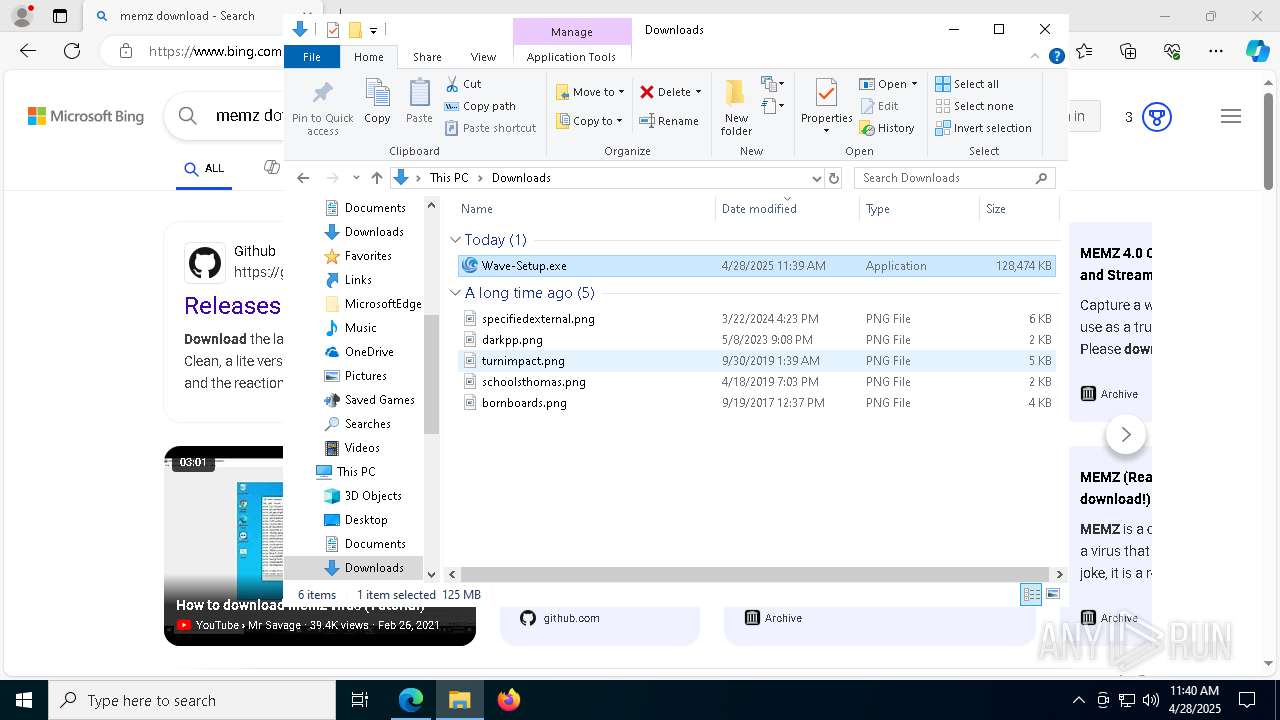
Manual execution by a user
- Wave-Setup.exe (PID: 3968)
- Wave.exe (PID: 3828)
Create files in a temporary directory
- Wave-Setup.exe (PID: 3968)
Reads the software policy settings
- slui.exe (PID: 7700)
The sample compiled with english language support
- Wave-Setup.exe (PID: 3968)
Creates files or folders in the user directory
- Wave-Setup.exe (PID: 3968)
Changes the display of characters in the console
- cmd.exe (PID: 4724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
292
Monitored processes
155
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=95 --mojo-platform-channel-handle=11056 --field-trial-handle=2472,i,7754723713420916453,10642157836613304404,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
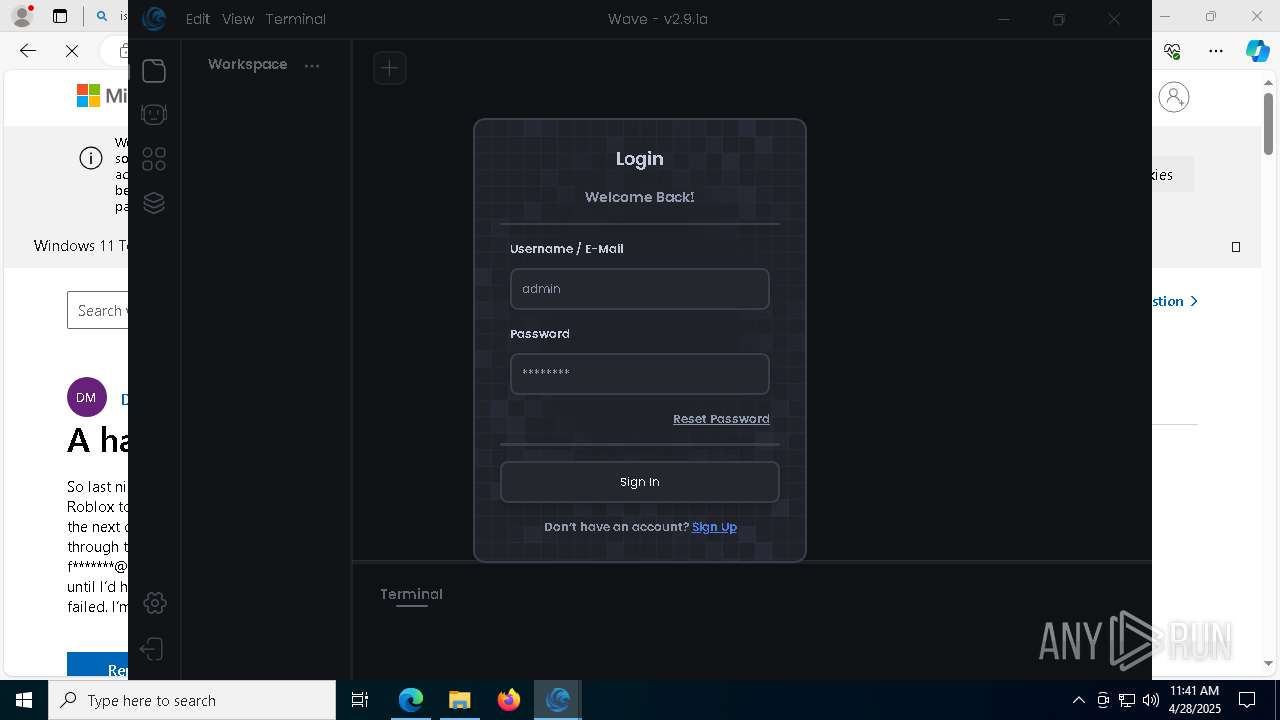
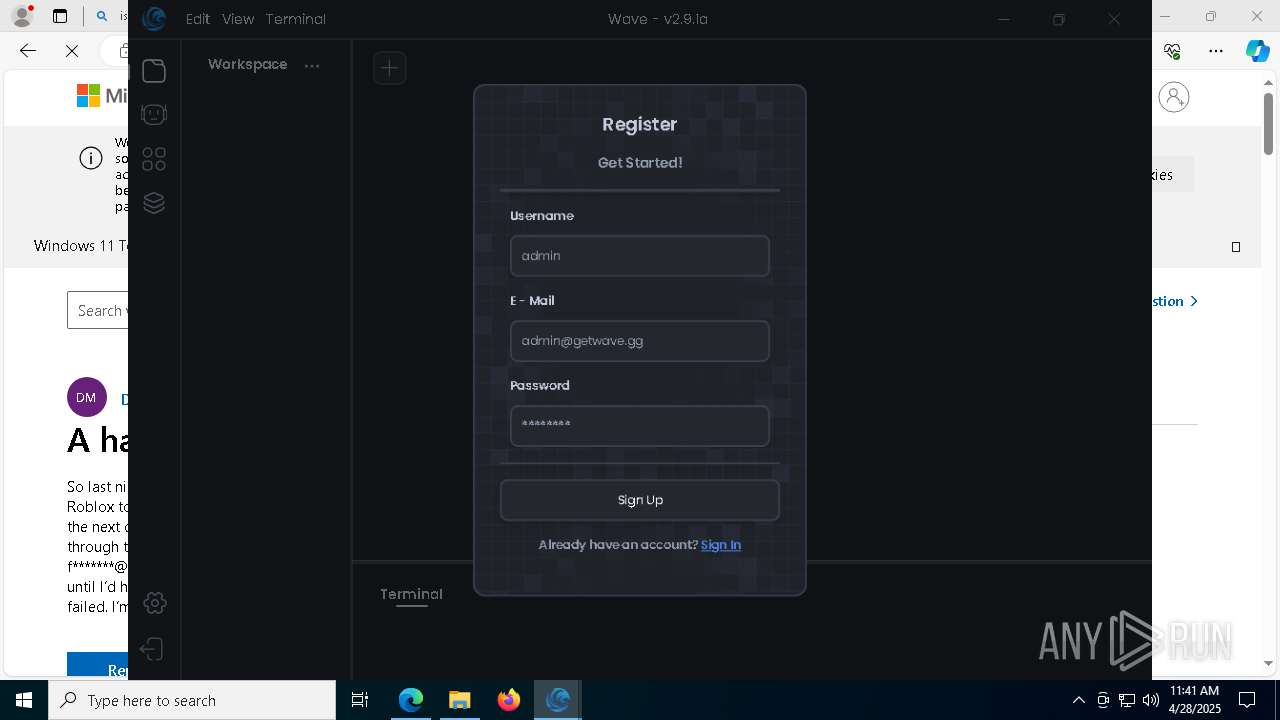
| 1004 | "C:\Users\admin\AppData\Local\Programs\Wave\Wave.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\Wave" --standard-schemes=app --secure-schemes=app --field-trial-handle=1996,i,11334309765721970672,11294379809144815573,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=1992 /prefetch:3 | C:\Users\admin\AppData\Local\Programs\Wave\Wave.exe | Wave.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: HIGH Description: Wave Version: 0.4.6 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc88825fd8,0x7ffc88825fe4,0x7ffc88825ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1088 | powershell.exe Start-Process -FilePath "'C:\Users\admin\AppData\Local\Temp\00d8d8b3780da34e0ba8a18b17e48006\execute.bat'" -WindowStyle hidden -Verb runAs | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6880 --field-trial-handle=2472,i,7754723713420916453,10642157836613304404,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6040 --field-trial-handle=2472,i,7754723713420916453,10642157836613304404,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=40 --mojo-platform-channel-handle=4220 --field-trial-handle=2472,i,7754723713420916453,10642157836613304404,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1748 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=67 --mojo-platform-channel-handle=8324 --field-trial-handle=2472,i,7754723713420916453,10642157836613304404,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2384 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2464 --field-trial-handle=2472,i,7754723713420916453,10642157836613304404,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=72 --mojo-platform-channel-handle=8512 --field-trial-handle=2472,i,7754723713420916453,10642157836613304404,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
16 810
Read events
16 682
Write events
110
Delete events
18
Modification events
| (PID) Process: | (6036) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F9497A696B922F00 | |||
| (PID) Process: | (6036) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CAA082696B922F00 | |||
| (PID) Process: | (6036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {844C835E-56D6-44FF-8402-6B0D45149C86} | |||
| (PID) Process: | (6036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {26BA6C5C-F5E0-4461-816F-43338ADA10E3} | |||
| (PID) Process: | (6036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D363CF1C-815B-45D7-A554-3D0483ADEE53} | |||
| (PID) Process: | (6036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E64482C3-895A-4B66-97C3-C7F53932AF88} | |||
| (PID) Process: | (6036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
71
Suspicious files
1 198
Text files
150
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b98e.TMP | — | |
MD5:— | SHA256:— | |||
| 6036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b98e.TMP | — | |
MD5:— | SHA256:— | |||
| 6036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b99d.TMP | — | |
MD5:— | SHA256:— | |||
| 6036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b99d.TMP | — | |
MD5:— | SHA256:— | |||
| 6036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b99d.TMP | — | |
MD5:— | SHA256:— | |||
| 6036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
720
DNS requests
789
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5984 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5984 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1188 | svchost.exe | HEAD | 200 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746418467&P2=404&P3=2&P4=QWphCIGrQtBfLupFPl6y%2bQFUzk%2f3qHrr4CholTXM94hRS40hFrWAPX5pC2OzJ%2bSQHEbFM87ztqFwoFmss3pgaQ%3d%3d | unknown | — | — | whitelisted |
1188 | svchost.exe | GET | 206 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746418467&P2=404&P3=2&P4=QWphCIGrQtBfLupFPl6y%2bQFUzk%2f3qHrr4CholTXM94hRS40hFrWAPX5pC2OzJ%2bSQHEbFM87ztqFwoFmss3pgaQ%3d%3d | unknown | — | — | whitelisted |
1188 | svchost.exe | GET | 206 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746418467&P2=404&P3=2&P4=QWphCIGrQtBfLupFPl6y%2bQFUzk%2f3qHrr4CholTXM94hRS40hFrWAPX5pC2OzJ%2bSQHEbFM87ztqFwoFmss3pgaQ%3d%3d | unknown | — | — | whitelisted |
1188 | svchost.exe | GET | 206 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746418467&P2=404&P3=2&P4=QWphCIGrQtBfLupFPl6y%2bQFUzk%2f3qHrr4CholTXM94hRS40hFrWAPX5pC2OzJ%2bSQHEbFM87ztqFwoFmss3pgaQ%3d%3d | unknown | — | — | whitelisted |
1188 | svchost.exe | GET | 206 | 217.20.57.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746418467&P2=404&P3=2&P4=QWphCIGrQtBfLupFPl6y%2bQFUzk%2f3qHrr4CholTXM94hRS40hFrWAPX5pC2OzJ%2bSQHEbFM87ztqFwoFmss3pgaQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6620 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6036 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6620 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6620 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
getwave.gg |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
6620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
6620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
6620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
6620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
6620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
6620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] DNS Query to Cloudflare Worker App |
6620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] DNS Query to Cloudflare Worker App |
6620 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Cloudflare workers.dev Domain |
6620 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Cloudflare workers.dev Domain |