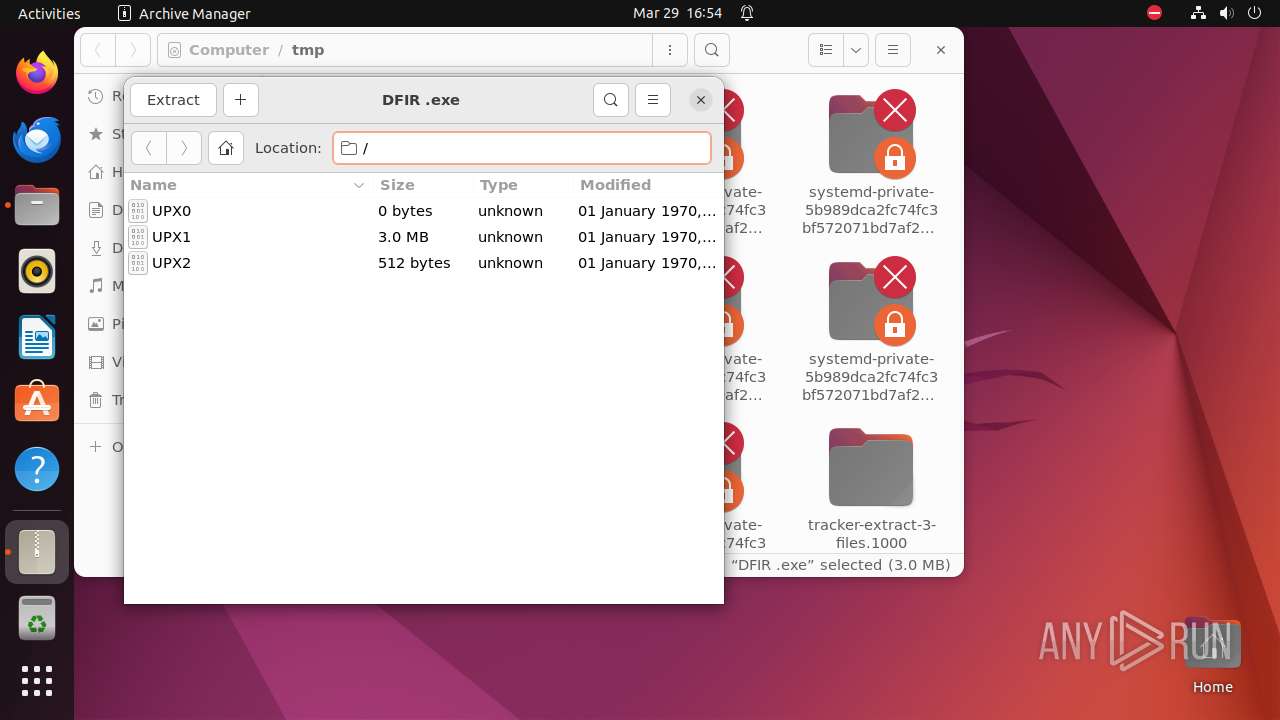
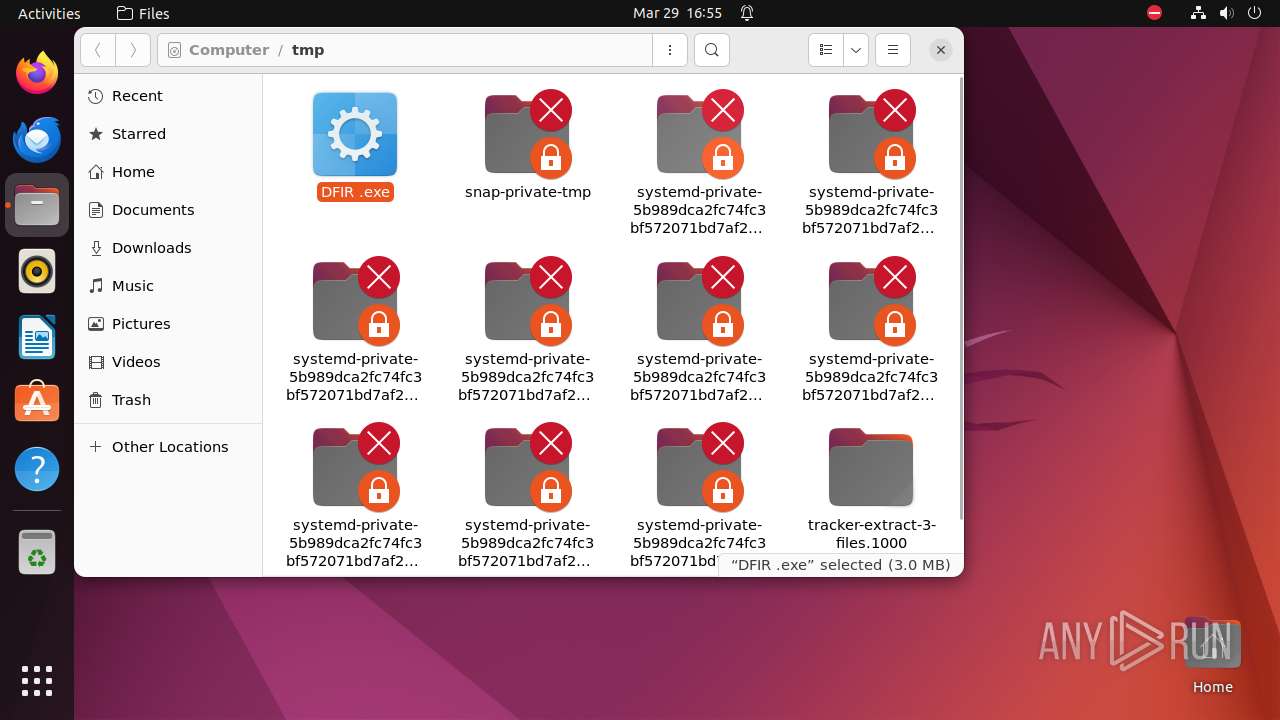
| File name: | DFIR .exe |
| Full analysis: | https://app.any.run/tasks/e9f930b4-ec52-4c2b-954a-12902dcb936f |
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2024, 16:54:31 |
| OS: | Ubuntu 22.04.2 |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows |
| MD5: | E372D1BA2D3A1936E3E8CDD3FEBF2038 |
| SHA1: | 06ED6E0BE895945BC78ADAC9AA0283E50FC93349 |
| SHA256: | 137197636E52F813606D4D979A270447888336D3403D3C94FE39310A903A59F9 |
| SSDEEP: | 49152:f5UX4uCXsw6rBbn0zdkfnDV/4TE6/lIKiebQ+LTq4ujYv9XiwuPNhO8NXB:f5UX4JF6rBYzyfGTJ/lIVebQ+L2ZsVSz |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 9320)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 2973696 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 15036416 |
| EntryPoint: | 0x112cde0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Total processes
234
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
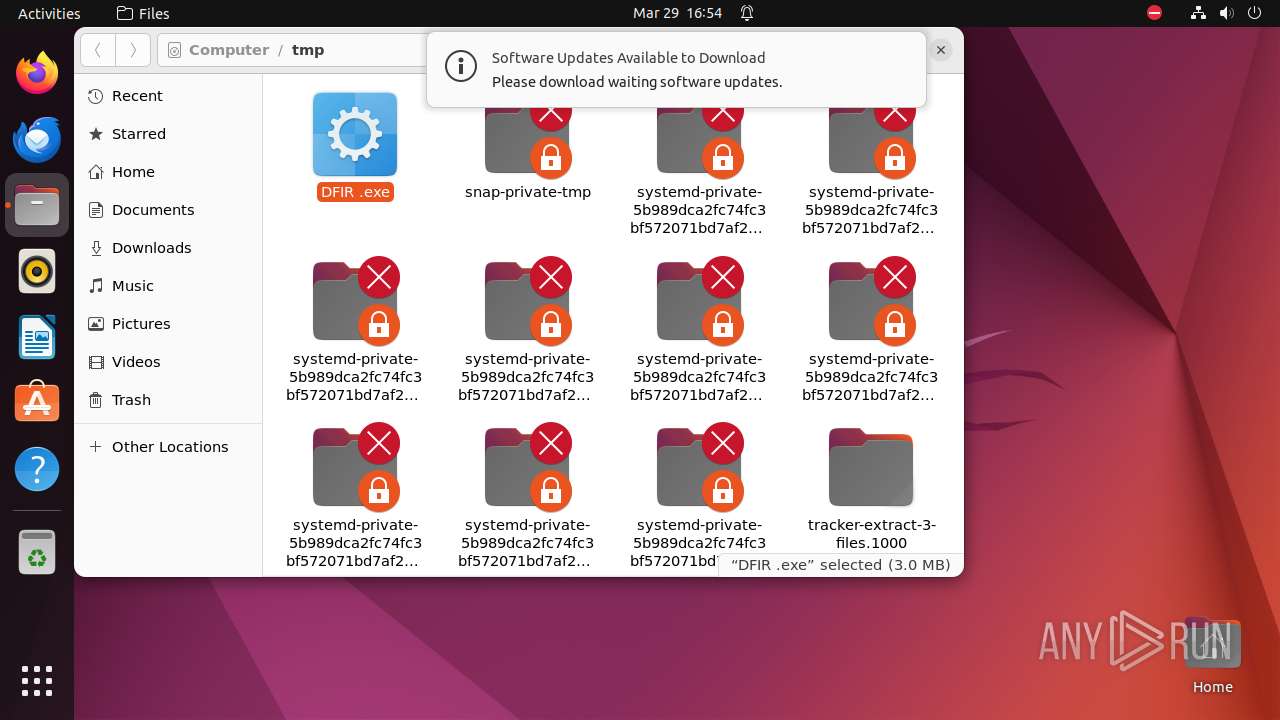
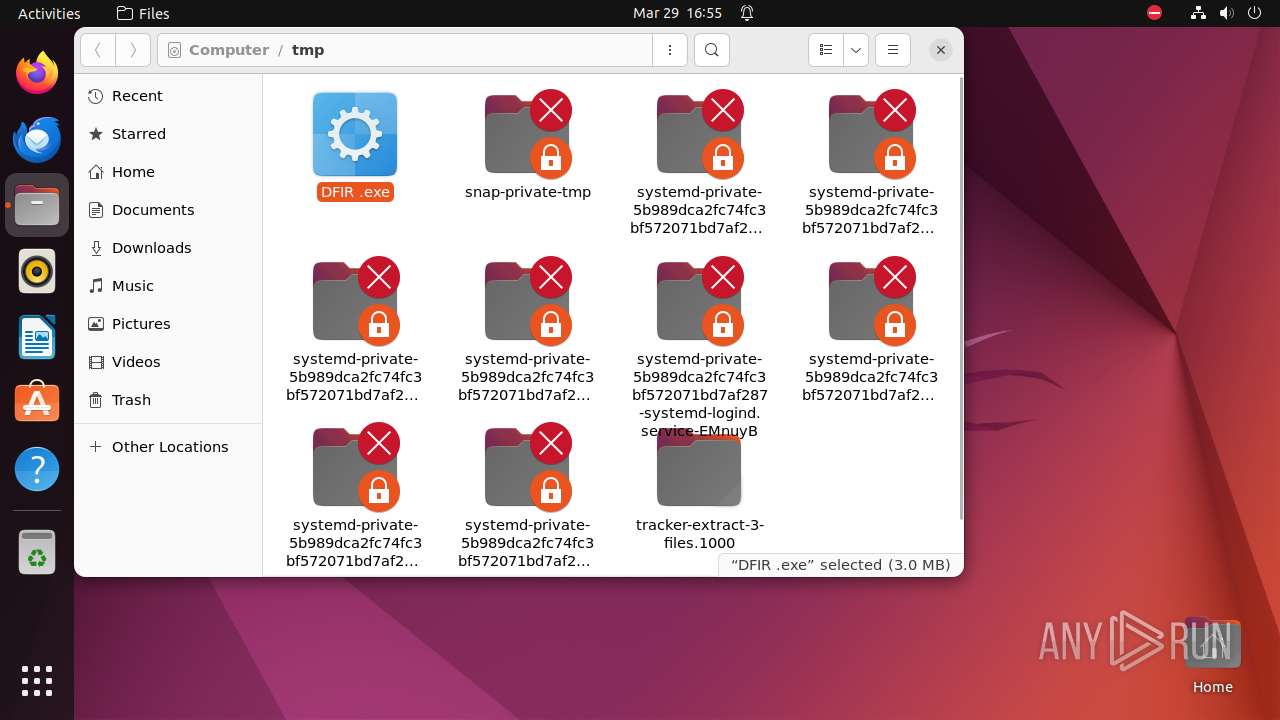
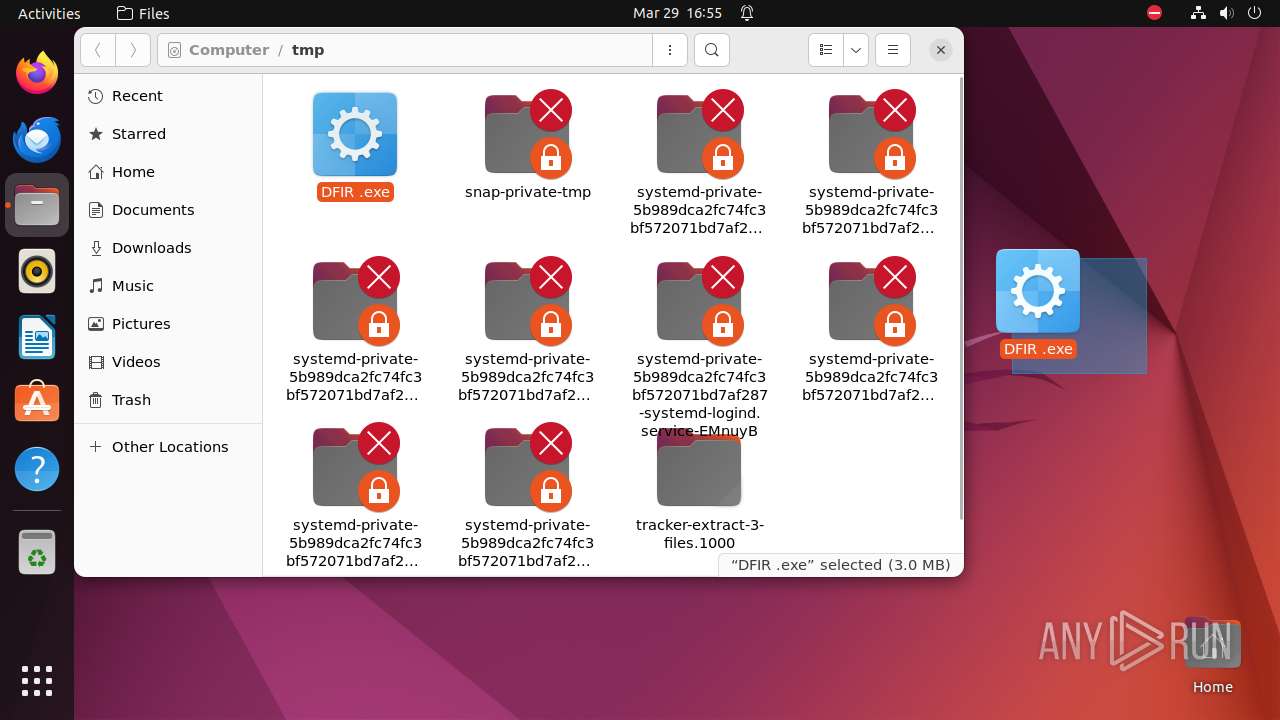
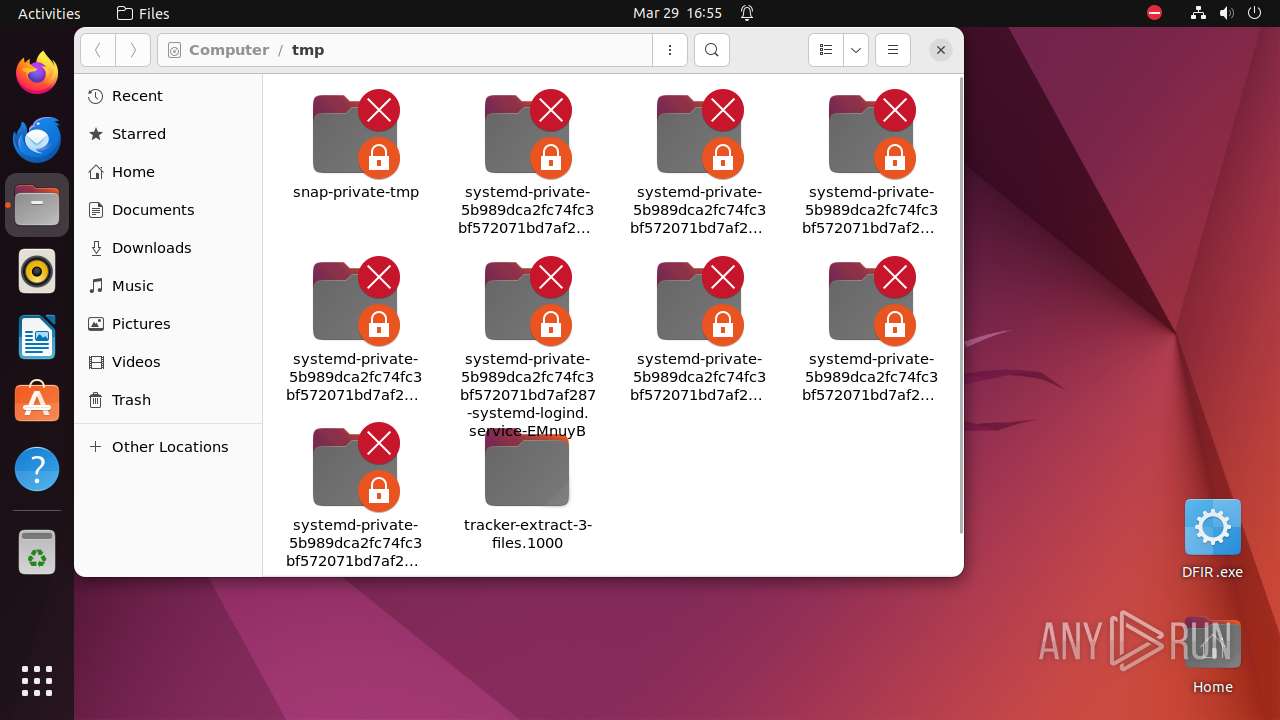
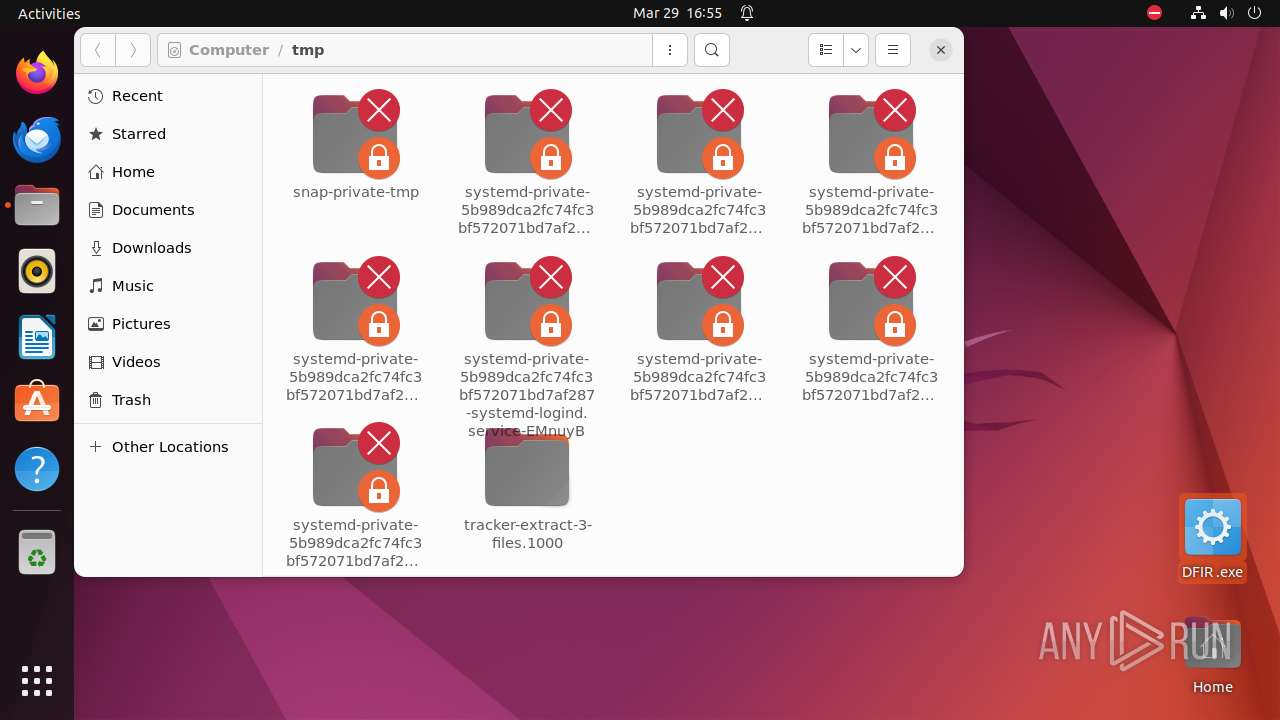
| 9296 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus \"/tmp/DFIR \.exe\" " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 9297 | sudo -iu user nautilus "/tmp/DFIR \.exe" | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN | ||||
| 9298 | nautilus "/tmp/DFIR \.exe" | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 9299 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9320 | /lib/systemd/systemd-hostnamed | /lib/systemd/systemd-hostnamed | — | systemd |
User: root Integrity Level: UNKNOWN Exit code: 9298 | ||||
| 9328 | nautilus "/tmp/DFIR \.exe" | /usr/bin/nautilus | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 496 | ||||
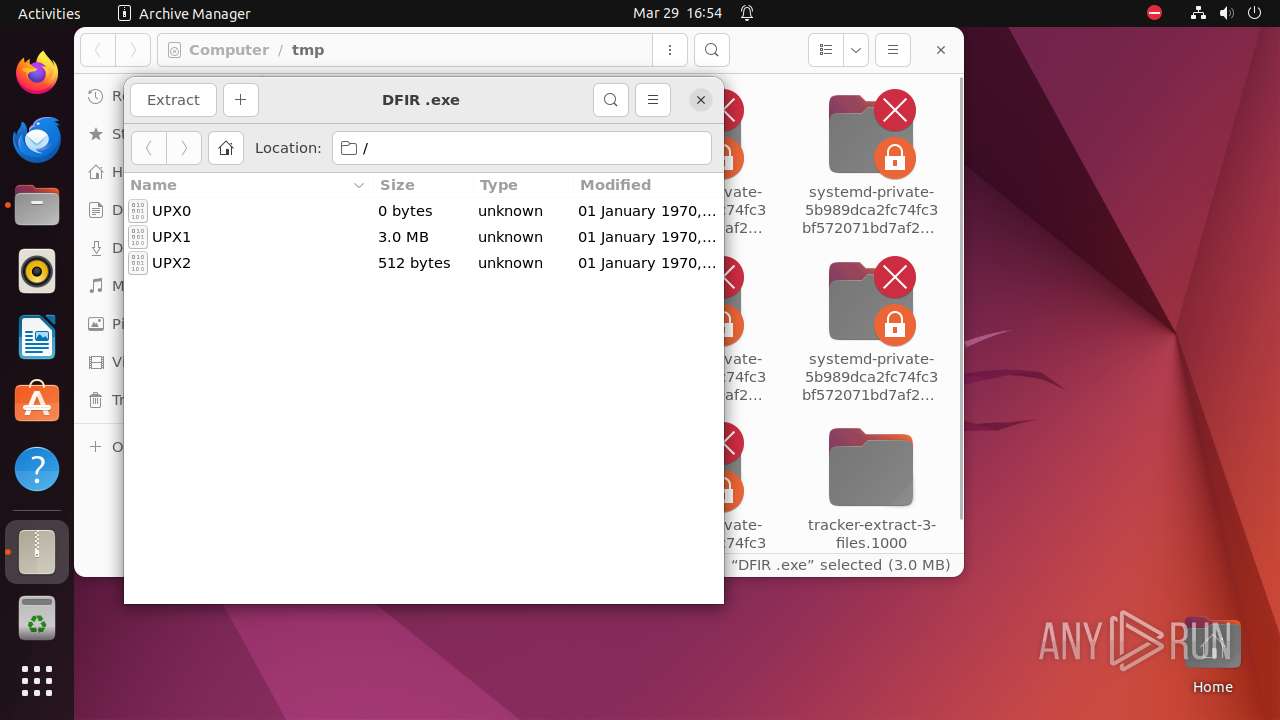
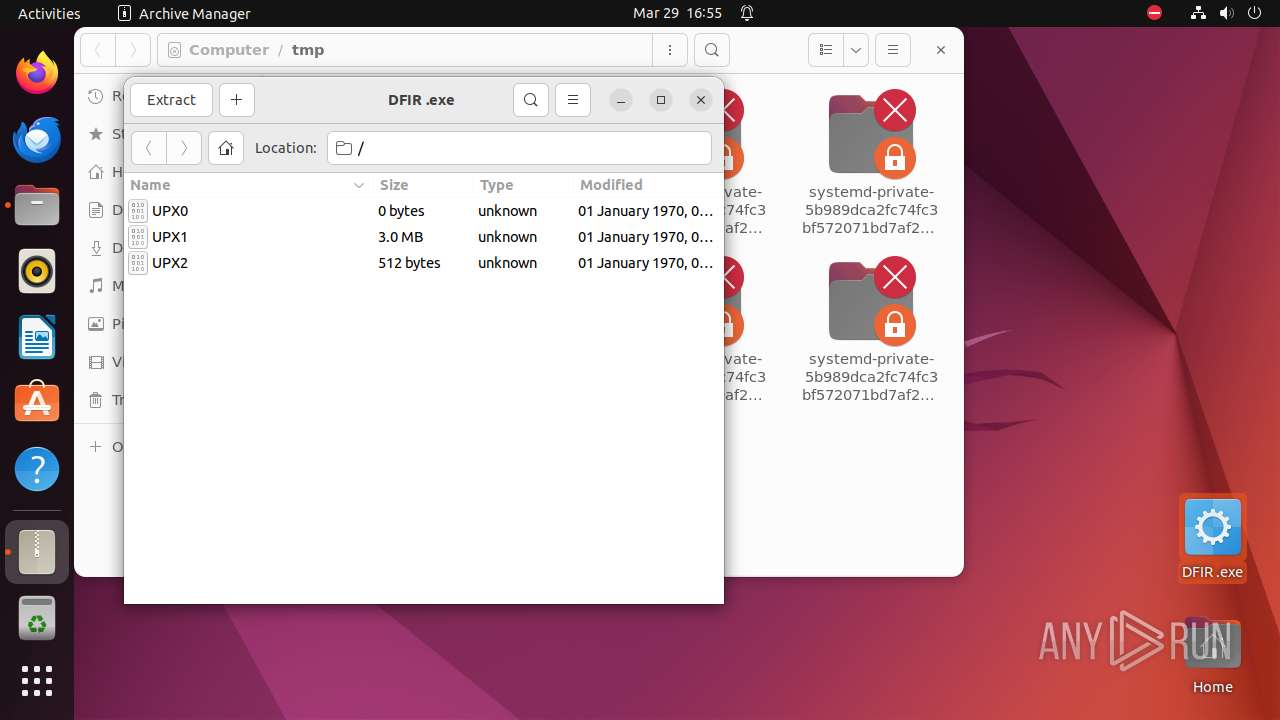
| 9329 | file-roller "/tmp/DFIR \.exe" | /usr/bin/file-roller | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 9298 | ||||
| 9344 | /usr/lib/p7zip/7z l -slt -bd -y -- "/tmp/DFIR \.exe" | /usr/lib/p7zip/7z | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 496 | ||||
| 9358 | /usr/libexec/tracker-extract-3 | /usr/libexec/tracker-extract-3 | — | systemd |
User: user Integrity Level: UNKNOWN Exit code: 9329 | ||||
| 9364 | gjs /usr/share/gnome-shell/extensions/ding@rastersoft.com/ding.js -E -P /usr/share/gnome-shell/extensions/ding@rastersoft.com -M 0 -D 0:0:1280:720:1:27:0:74:0:0 | /usr/bin/gjs-console | — | gjs-console |
User: user Integrity Level: UNKNOWN Exit code: 620 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9298 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-wal | — | |
MD5:— | SHA256:— | |||
| 9298 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-shm | — | |
MD5:— | SHA256:— | |||
| 9298 | nautilus | /home/user/.local/share/nautilus/tags/.meta.isrunning | — | |
MD5:— | SHA256:— | |||
| 9329 | file-roller | /dconf/user | — | |
MD5:— | SHA256:— | |||
| 9298 | nautilus | /home/user/.local/share/recently-used.xbel.787BL2 | — | |
MD5:— | SHA256:— | |||
| 9365 | file-roller | /home/user/.local/share/recently-used.xbel.O6G6K2 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
6
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
30.100.168.192.in-addr.arpa |
| unknown |
connectivity-check.ubuntu.com |
| unknown |
api.snapcraft.io |
| unknown |