| download: | gup5setup.exe |
| Full analysis: | https://app.any.run/tasks/45f178bb-a30c-4b49-905e-2fe26ec4f49e |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 10:57:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 97A848B9EC8DDBAD8BBACDA4F9F42621 |
| SHA1: | 27FD6DD95D294D4F519A3B52CF5C5BD5B100E6AD |
| SHA256: | 1369FE0A6B3207A639F4614EDCC024B4741BE23CF5D1090D597882C6C6693B13 |
| SSDEEP: | 393216:shbf57A5rFTgpTtEM43HIDT0BLOucoCFOyY:MbMFTgpRo3HIDZDoCF7 |
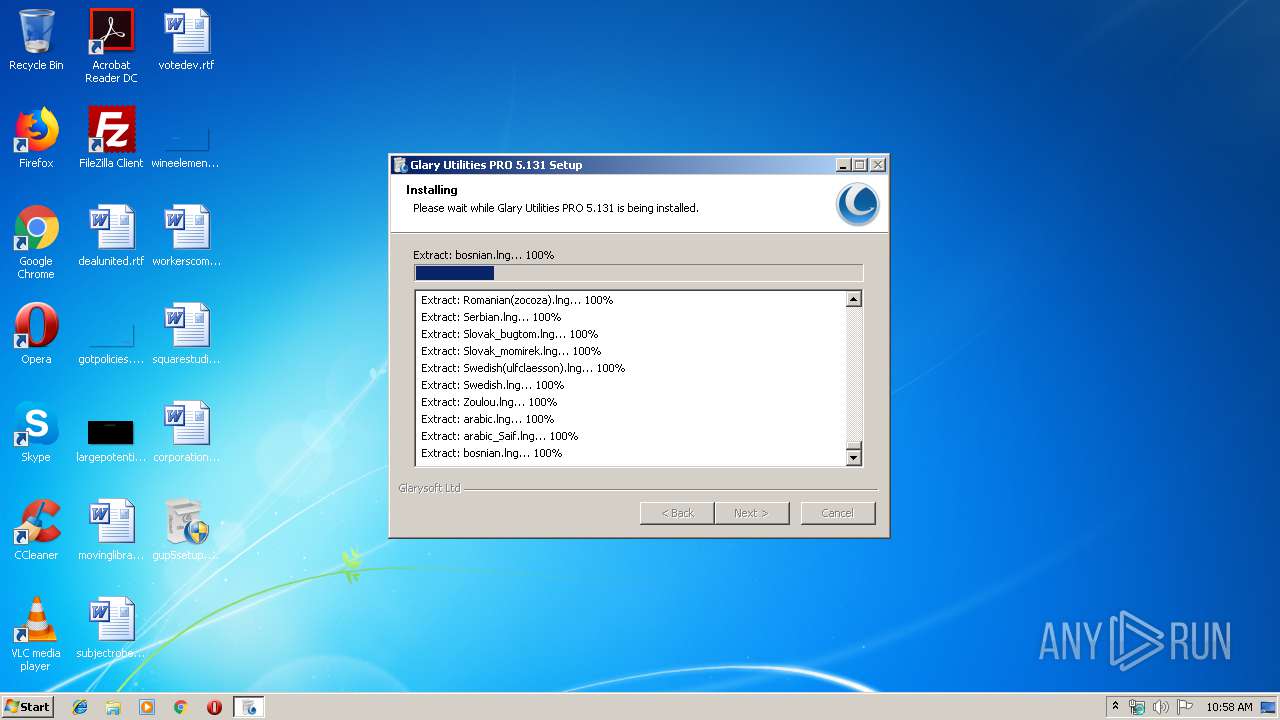
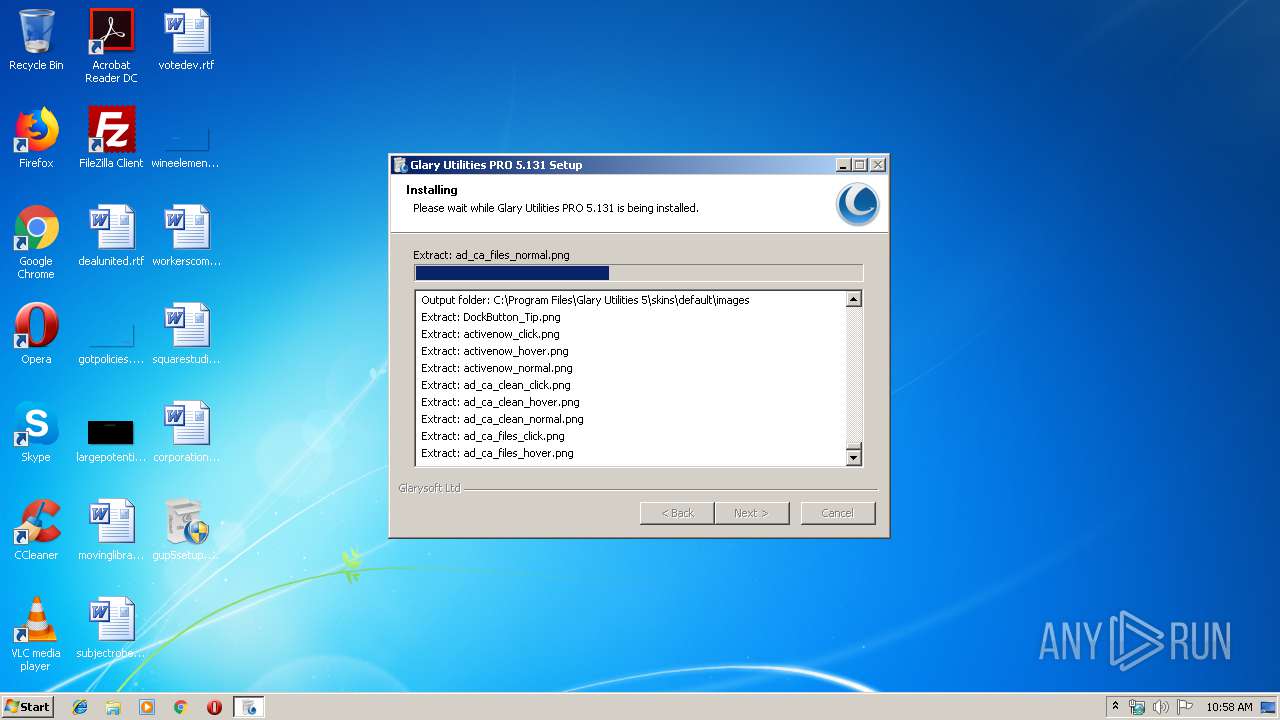
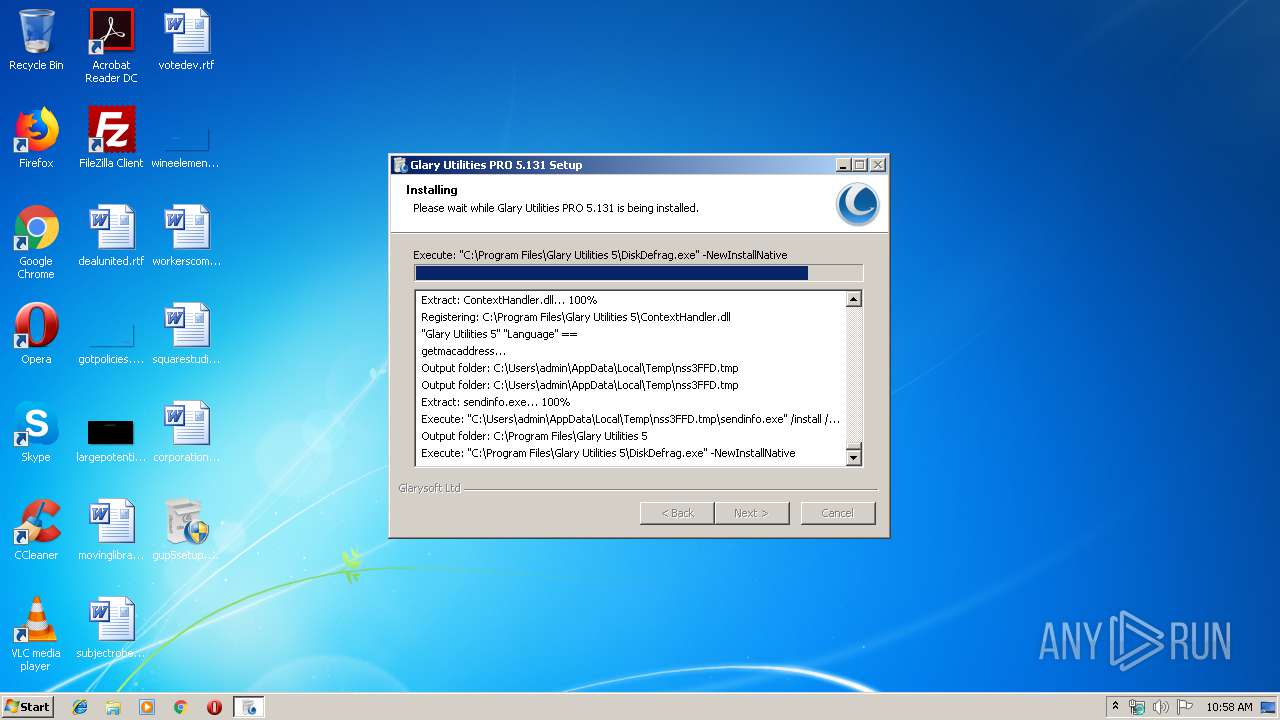
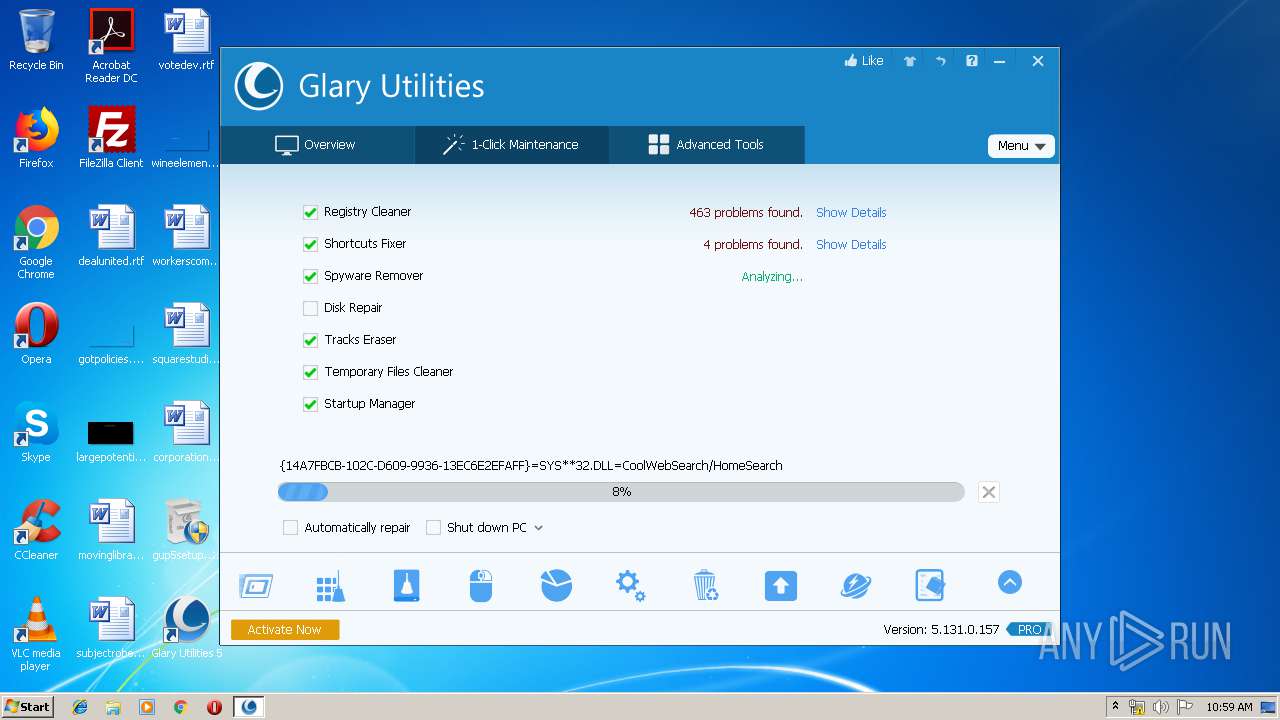
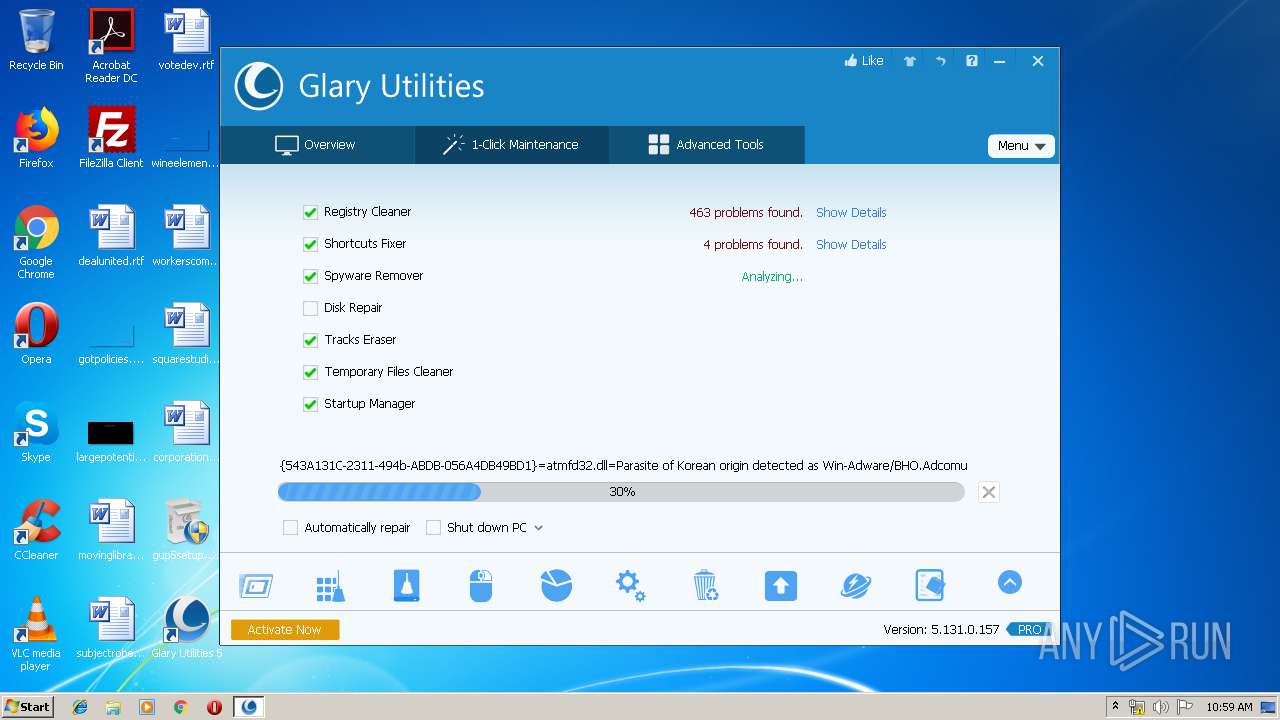
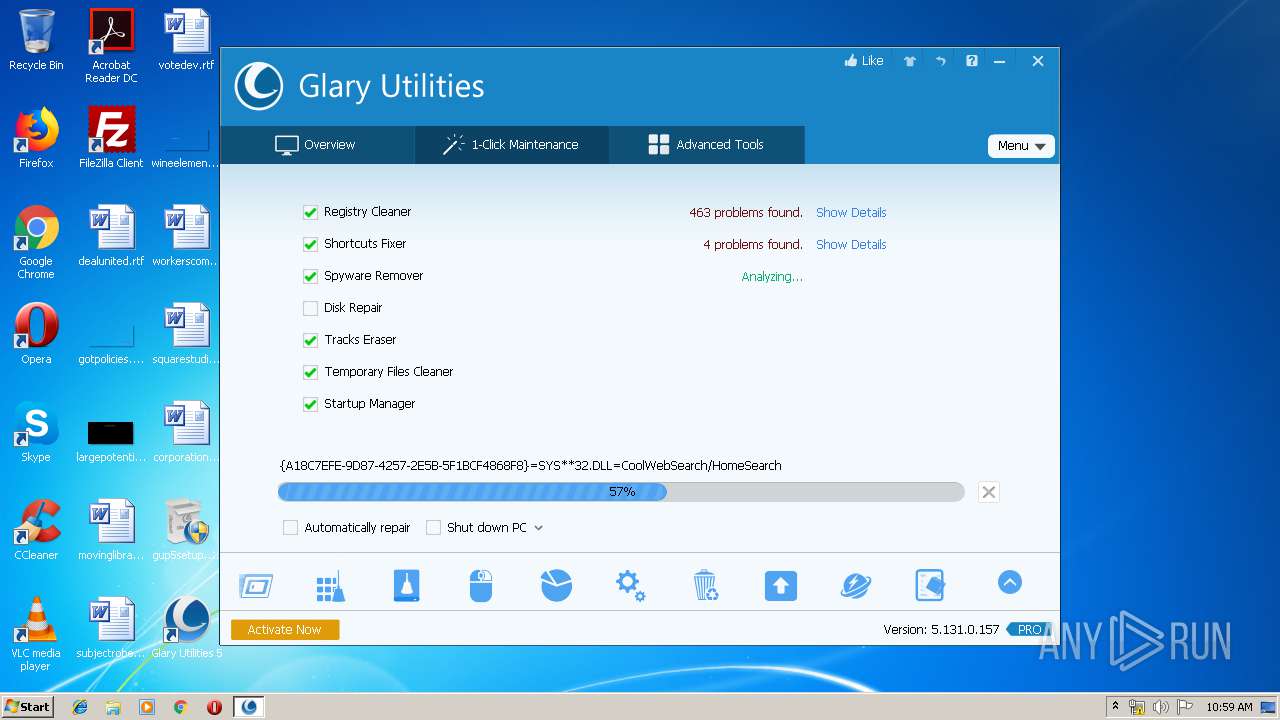
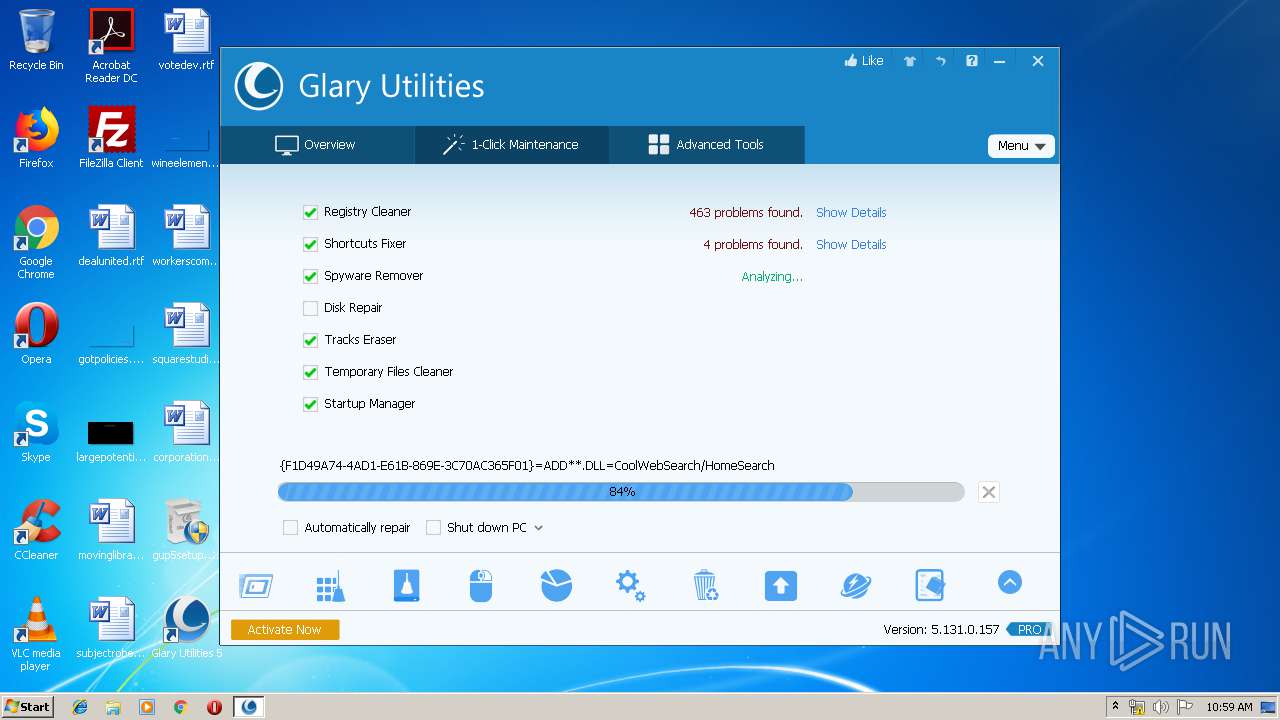
MALICIOUS
Loads dropped or rewritten executable
- gup5setup.exe (PID: 2864)
- gup5setup.exe (PID: 2432)
- DiskDefrag.exe (PID: 2400)
- DiskDefrag.exe (PID: 1936)
- StartupManager.exe (PID: 2720)
- sendinfo.exe (PID: 2496)
- Initialize.exe (PID: 4012)
- Integrator.exe (PID: 1532)
- autoupdate.exe (PID: 2824)
- explorer.exe (PID: 352)
- Integrator.exe (PID: 1560)
- svchost.exe (PID: 864)
- autoupdate.exe (PID: 2208)
- MemfilesService.exe (PID: 2144)
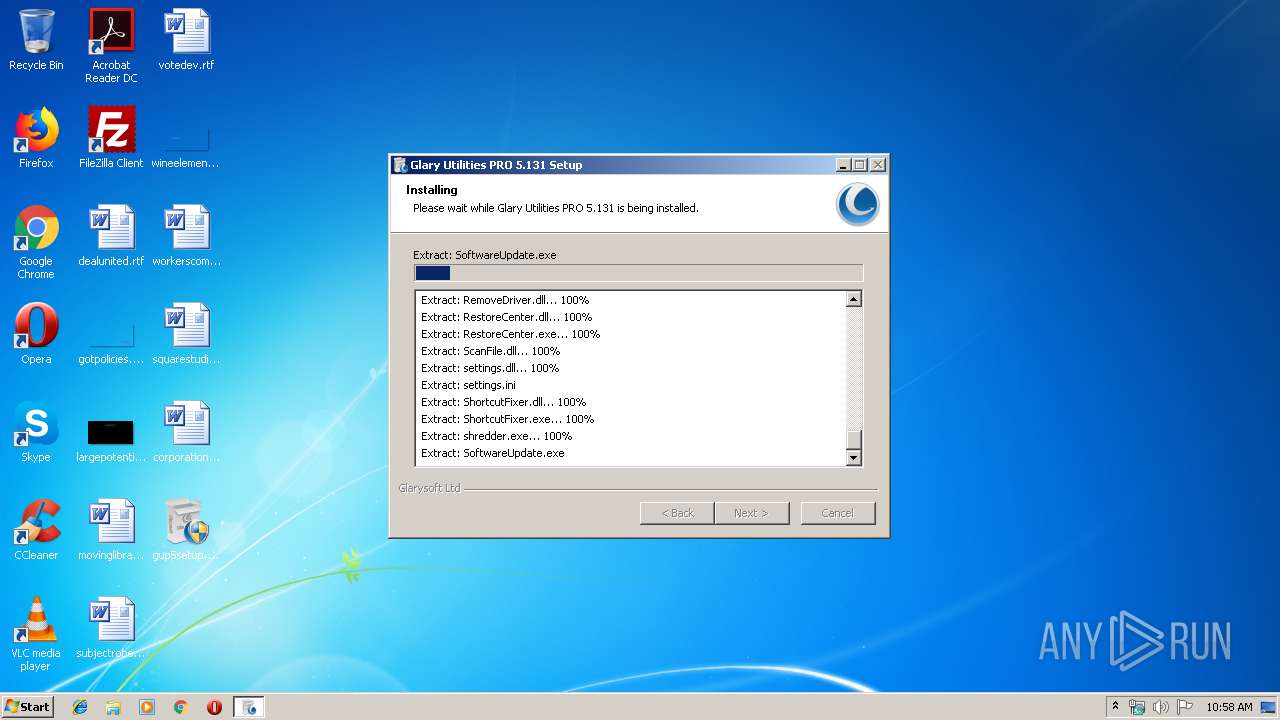
- SoftwareUpdate.exe (PID: 656)
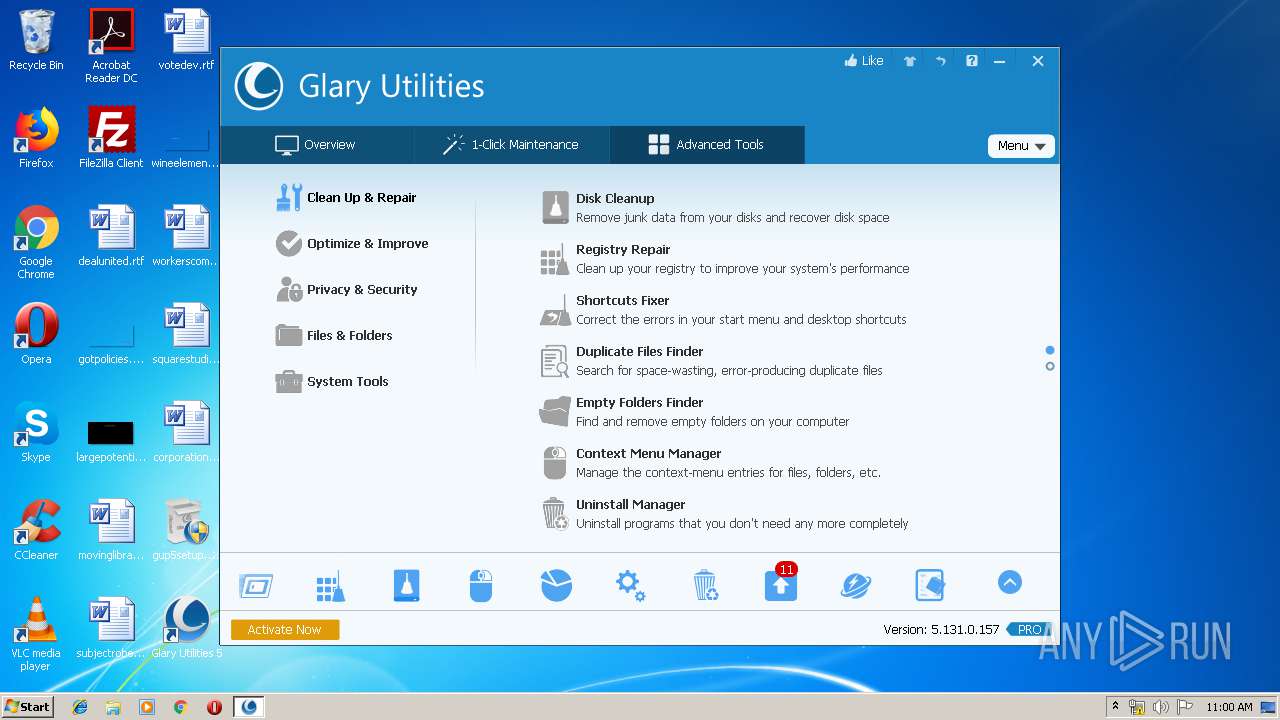
- RegistryCleaner.exe (PID: 3044)
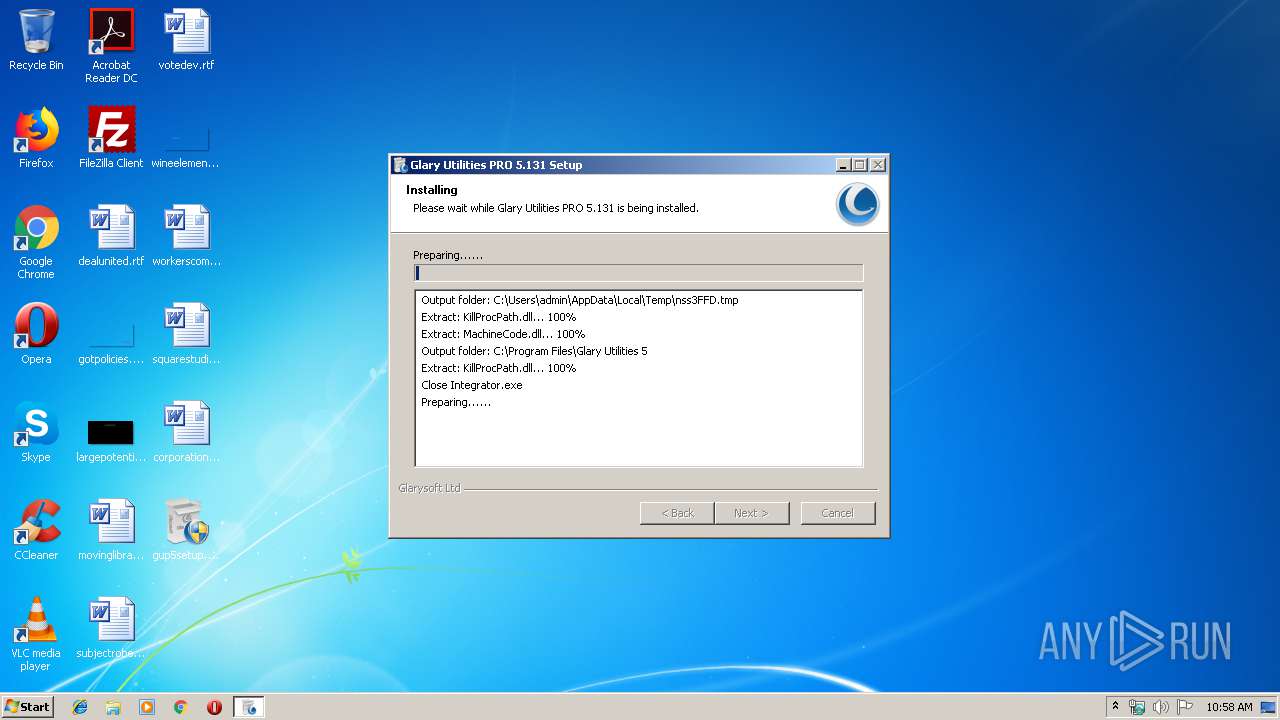
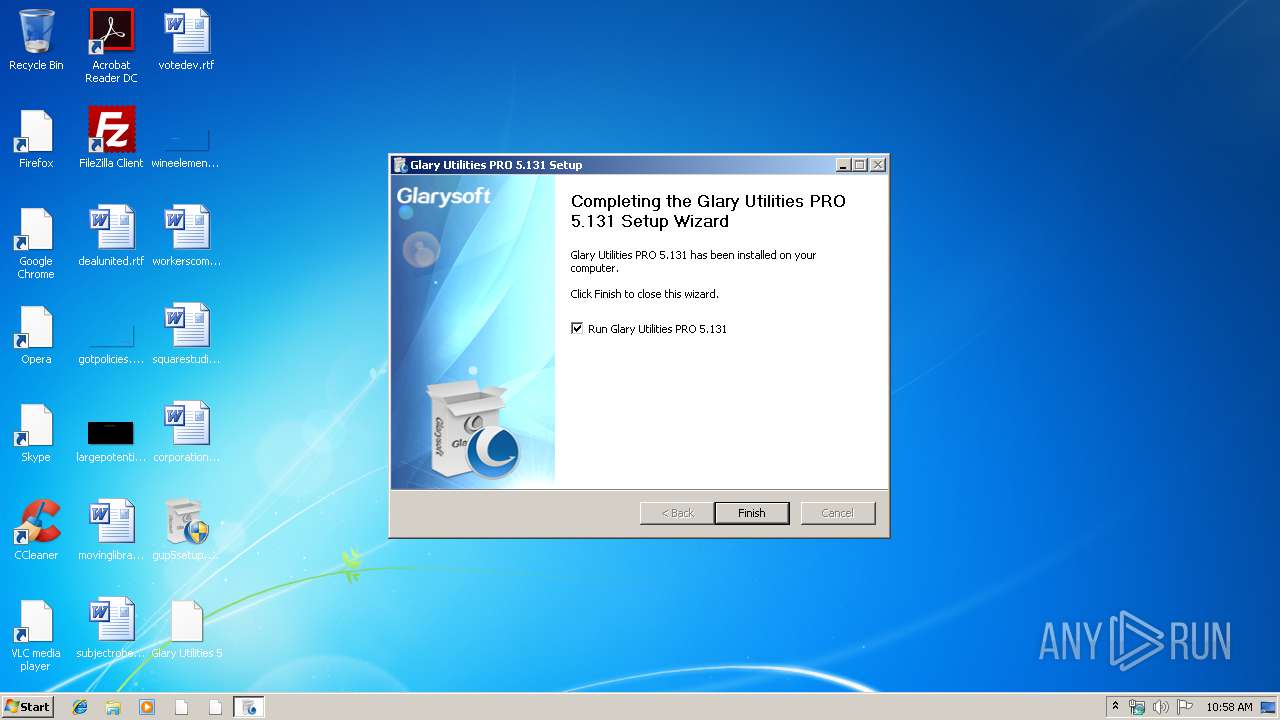
Application was dropped or rewritten from another process
- DiskDefrag.exe (PID: 2400)
- DiskDefrag.exe (PID: 1936)
- StartupManager.exe (PID: 2720)
- Initialize.exe (PID: 4012)
- sendinfo.exe (PID: 2496)
- Integrator.exe (PID: 1532)
- autoupdate.exe (PID: 2824)
- Integrator.exe (PID: 1560)
- autoupdate.exe (PID: 2208)
- MemfilesService.exe (PID: 2144)
- SoftwareUpdate.exe (PID: 656)
- RegistryCleaner.exe (PID: 3044)
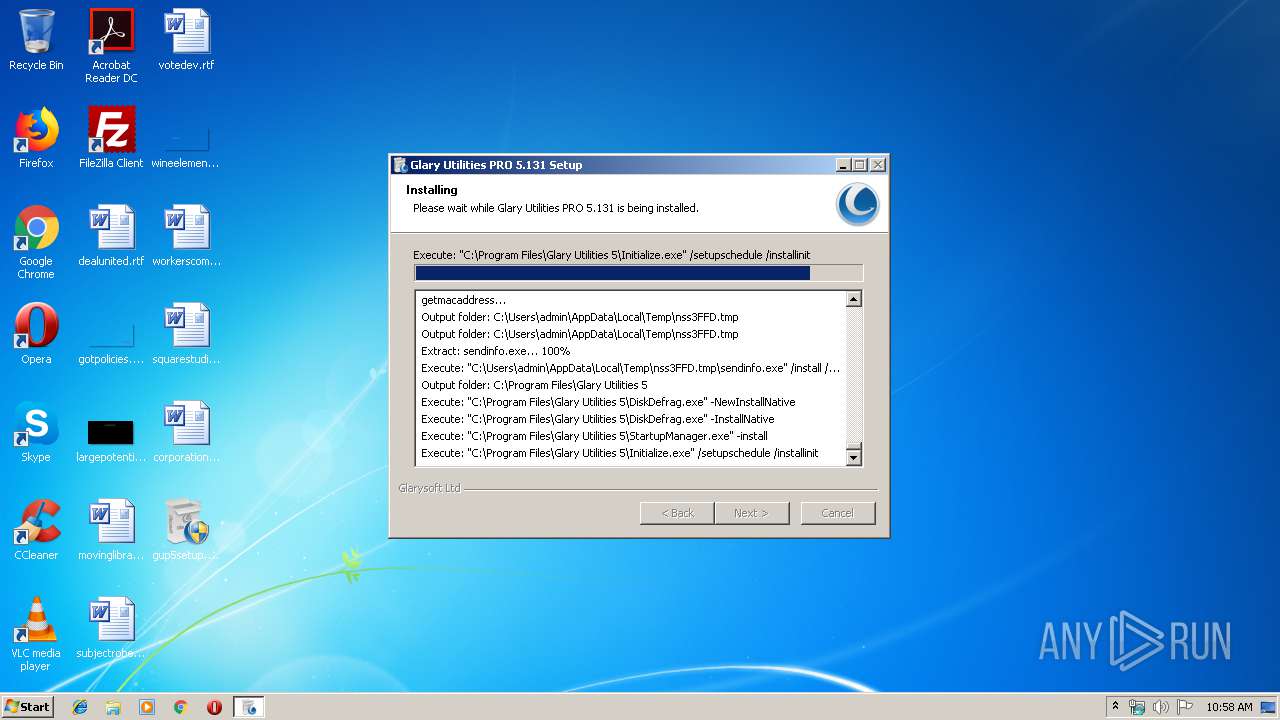
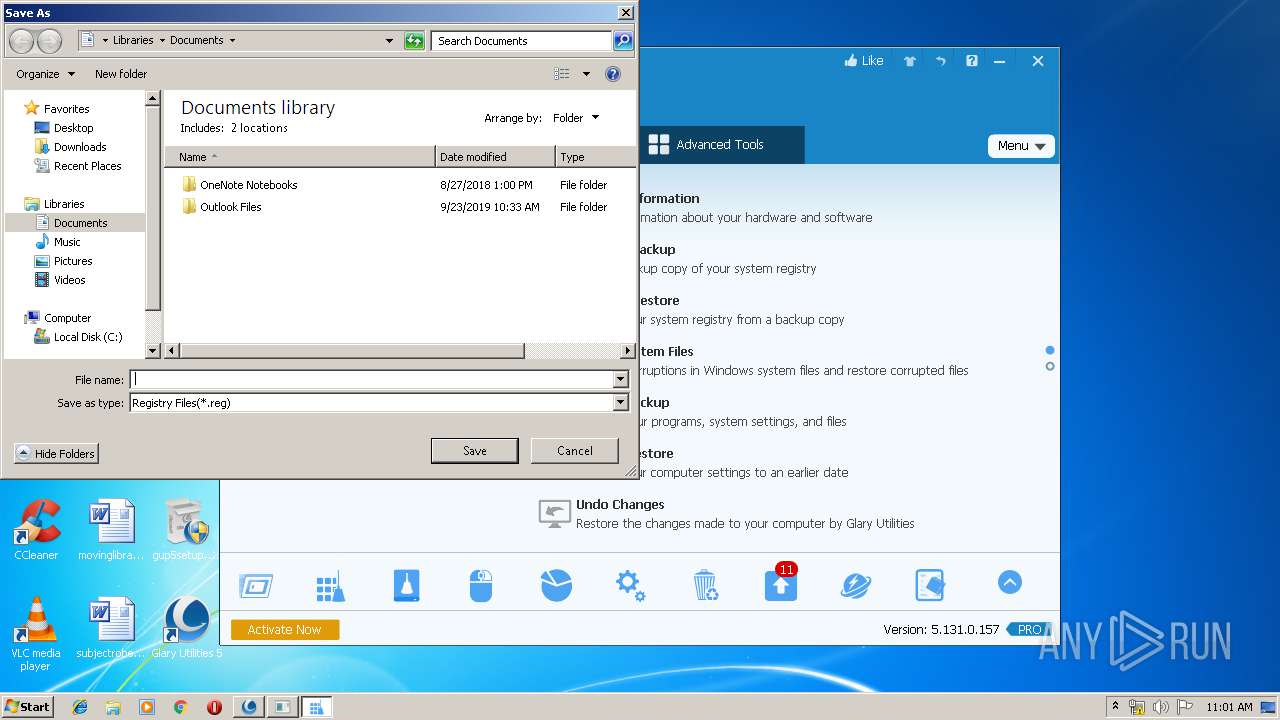
Changes the autorun value in the registry
- StartupManager.exe (PID: 2720)
Actions looks like stealing of personal data
- Initialize.exe (PID: 4012)
- Integrator.exe (PID: 1532)
- Integrator.exe (PID: 1560)
Loads the Task Scheduler COM API
- Initialize.exe (PID: 4012)
- Integrator.exe (PID: 1532)
- Integrator.exe (PID: 1560)
- SoftwareUpdate.exe (PID: 656)
Loads the Task Scheduler DLL interface
- Initialize.exe (PID: 4012)
Changes settings of System certificates
- Integrator.exe (PID: 1532)
SUSPICIOUS
Creates COM task schedule object
- gup5setup.exe (PID: 2432)
Executable content was dropped or overwritten
- sendinfo.exe (PID: 2496)
- DiskDefrag.exe (PID: 2400)
- gup5setup.exe (PID: 2864)
- gup5setup.exe (PID: 2432)
- StartupManager.exe (PID: 2720)
Creates files in the Windows directory
- DiskDefrag.exe (PID: 2400)
- StartupManager.exe (PID: 2720)
- svchost.exe (PID: 864)
Creates files in the driver directory
- DiskDefrag.exe (PID: 2400)
- StartupManager.exe (PID: 2720)
Low-level read access rights to disk partition
- DiskDefrag.exe (PID: 1936)
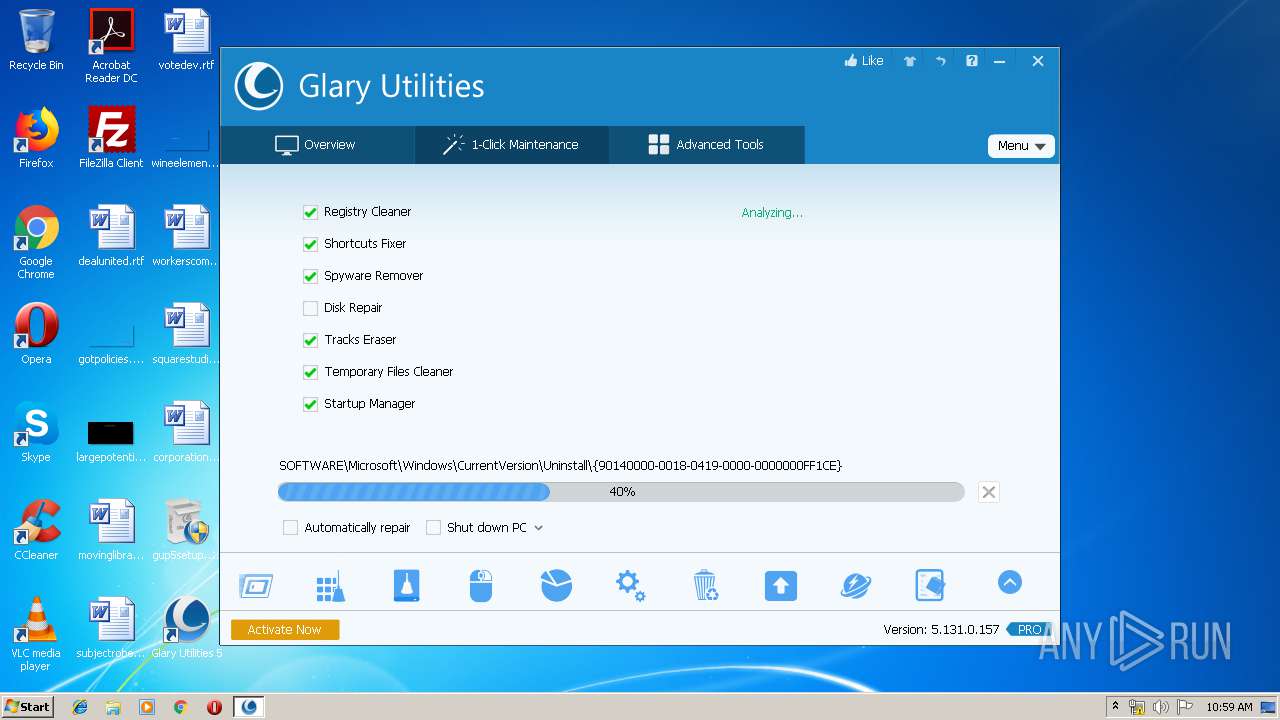
Creates a software uninstall entry
- gup5setup.exe (PID: 2432)
- sendinfo.exe (PID: 2496)
Creates files in the user directory
- DiskDefrag.exe (PID: 2400)
- Initialize.exe (PID: 4012)
- gup5setup.exe (PID: 2432)
- Integrator.exe (PID: 1532)
- Integrator.exe (PID: 1560)
- SoftwareUpdate.exe (PID: 656)
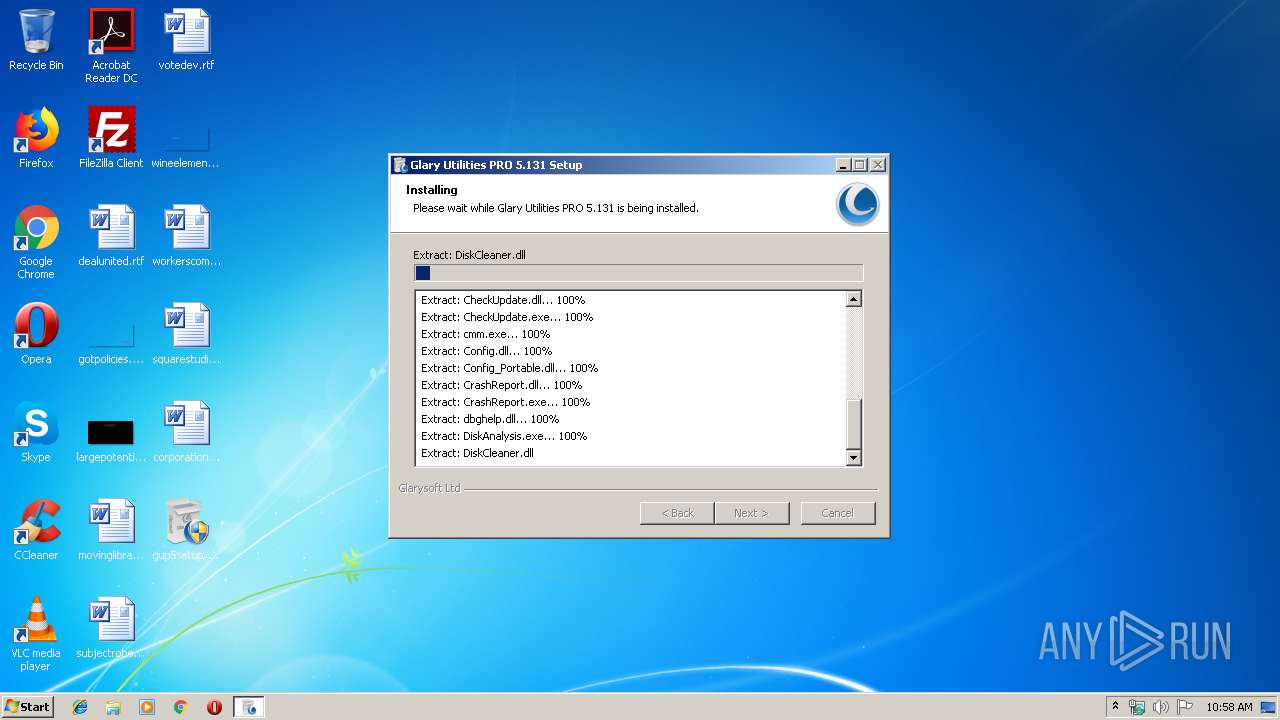
Creates files in the program directory
- gup5setup.exe (PID: 2432)
- StartupManager.exe (PID: 2720)
- Initialize.exe (PID: 4012)
- Integrator.exe (PID: 1532)
- Integrator.exe (PID: 1560)
- RegistryCleaner.exe (PID: 3044)
Creates or modifies windows services
- DiskDefrag.exe (PID: 1936)
Removes files from Windows directory
- DiskDefrag.exe (PID: 1936)
- Integrator.exe (PID: 1560)
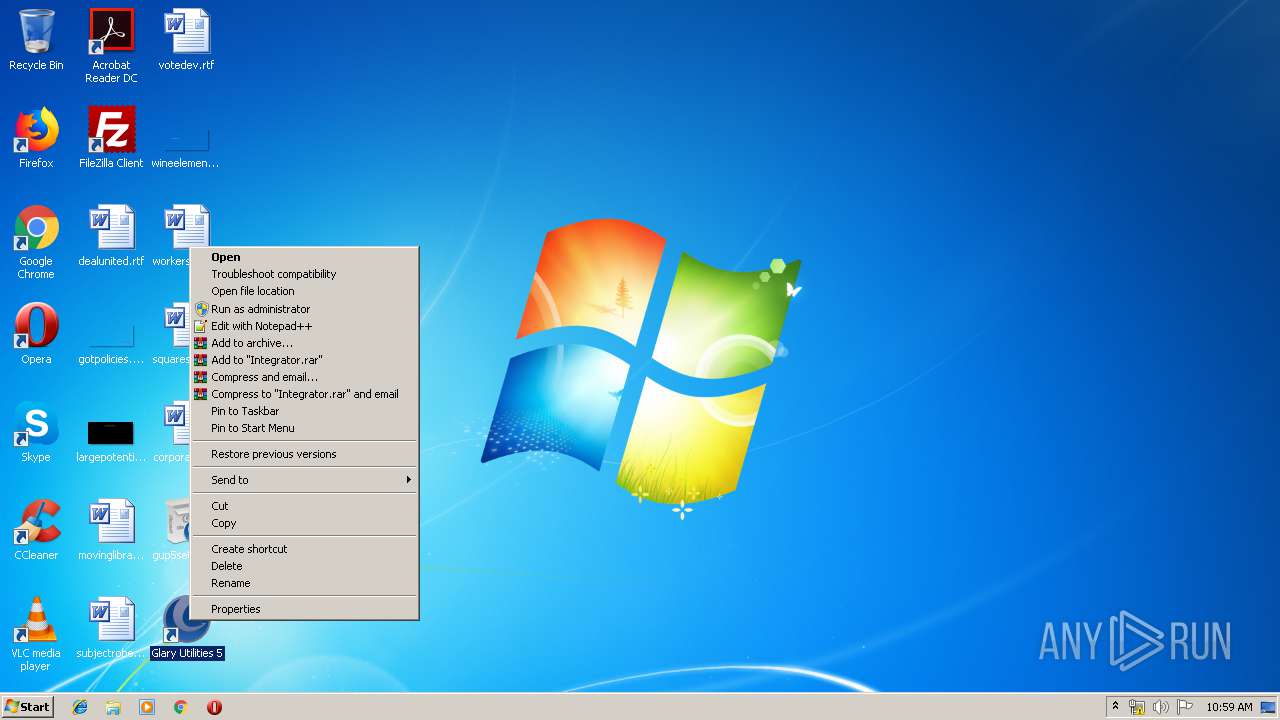
Modifies the open verb of a shell class
- gup5setup.exe (PID: 2432)
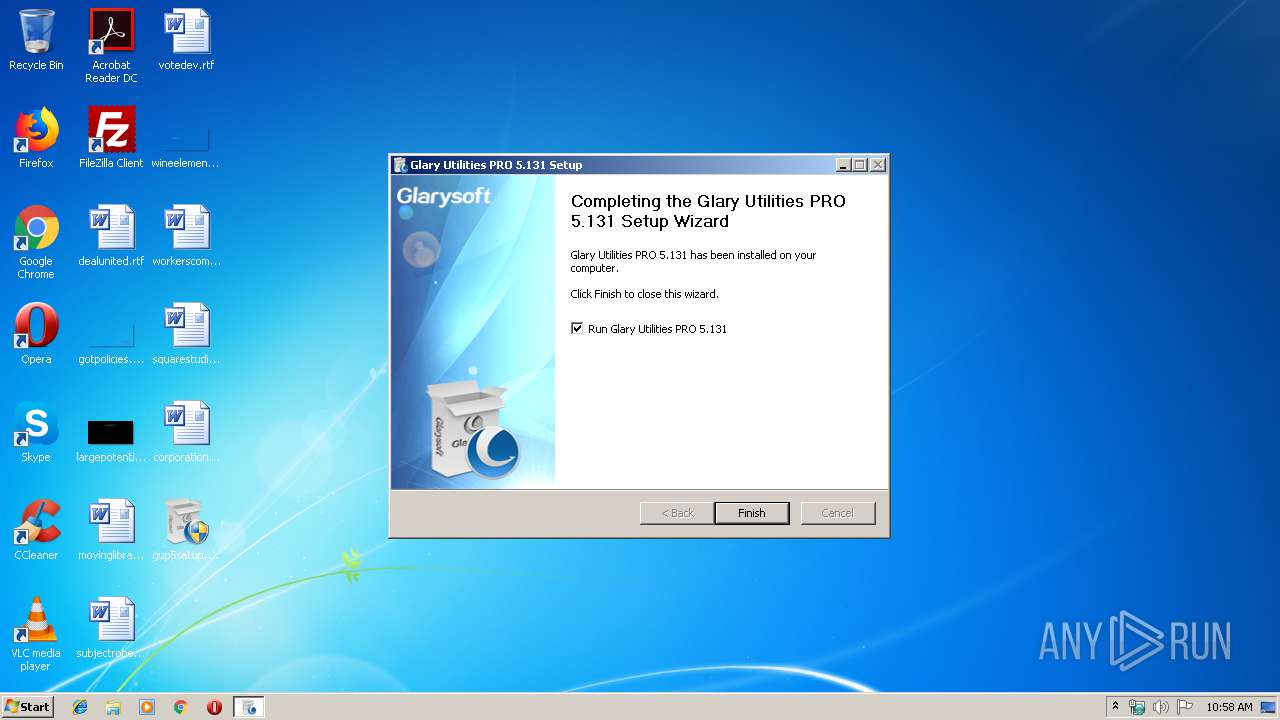
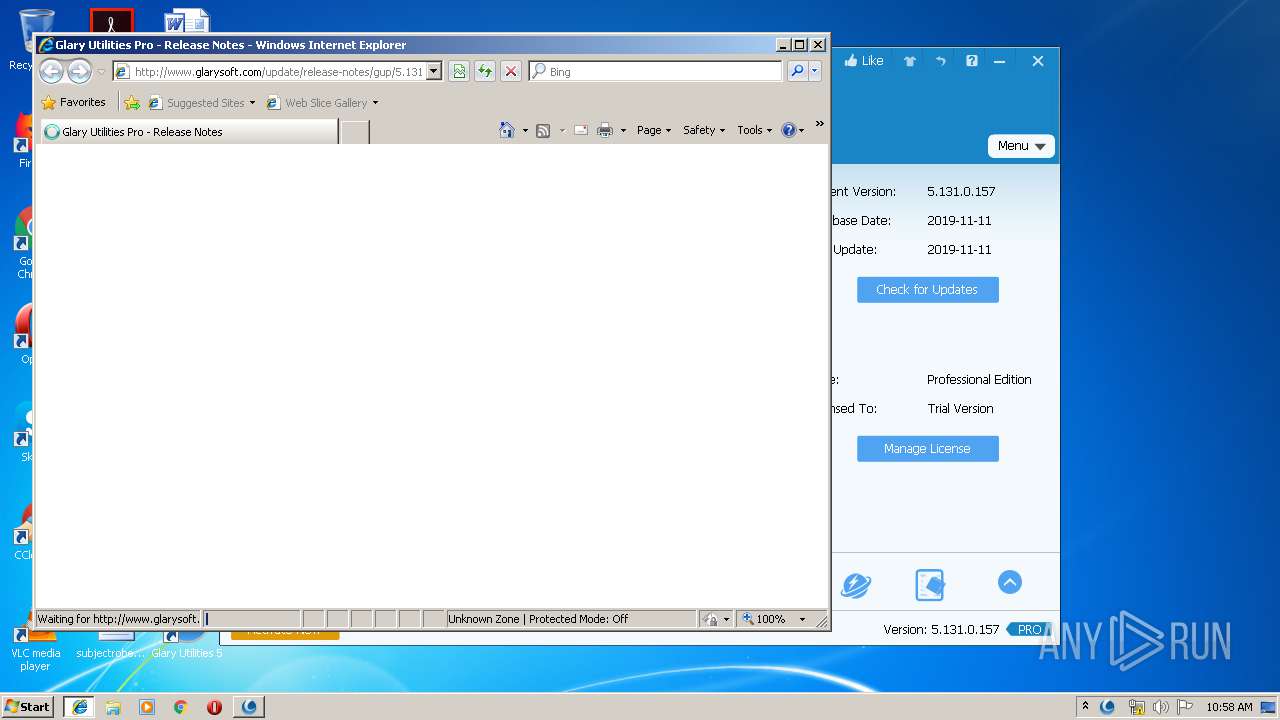
Starts Internet Explorer
- gup5setup.exe (PID: 2432)
Adds / modifies Windows certificates
- Integrator.exe (PID: 1532)
Searches for installed software
- Integrator.exe (PID: 1560)
INFO
Dropped object may contain Bitcoin addresses
- gup5setup.exe (PID: 2432)
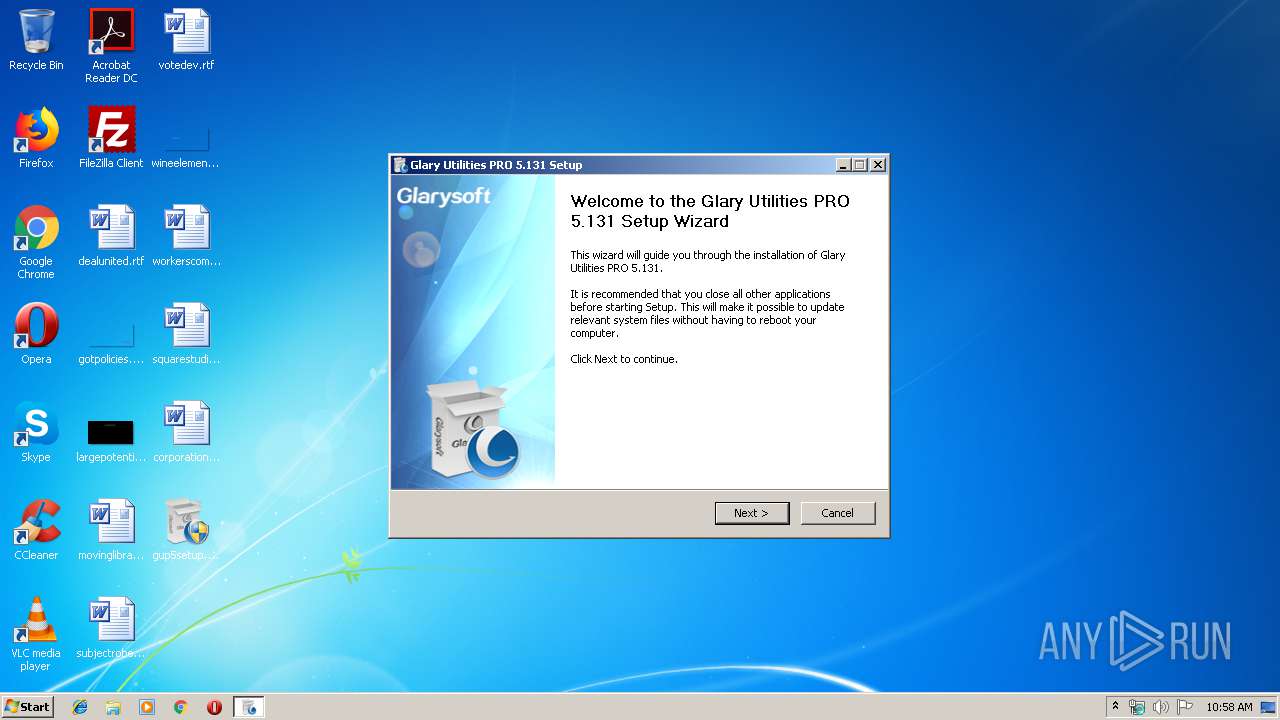
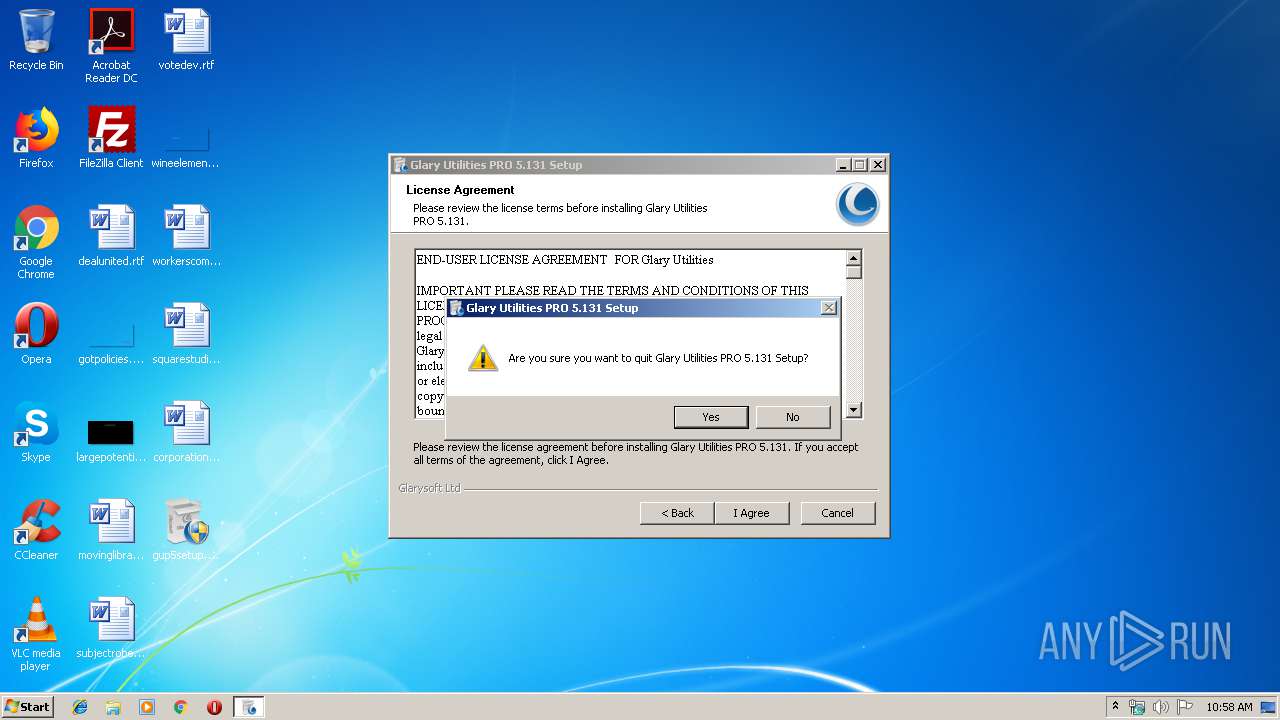
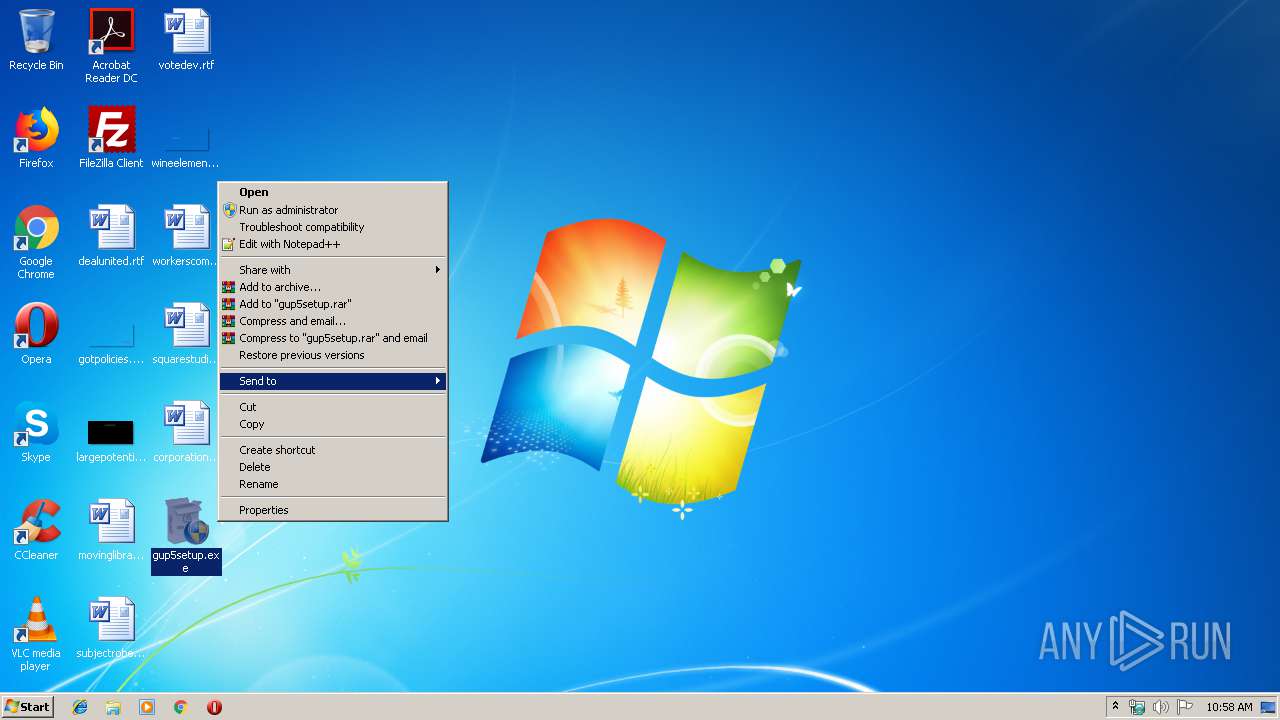
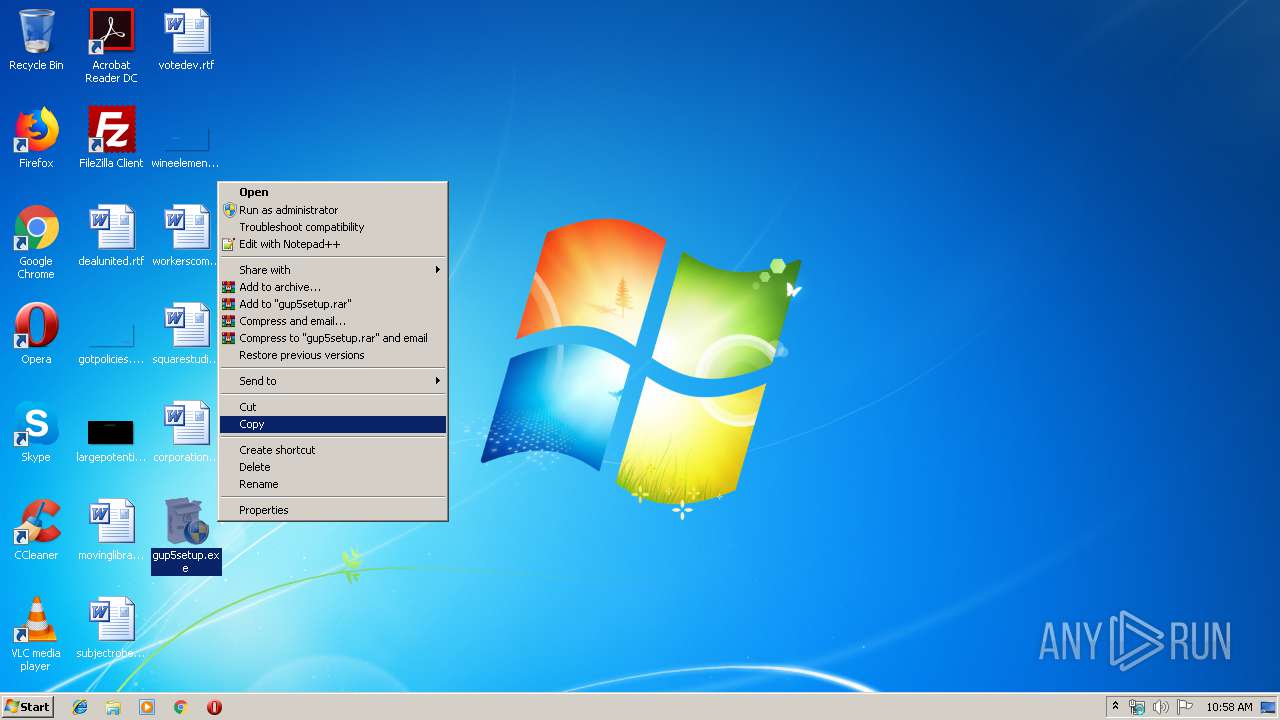
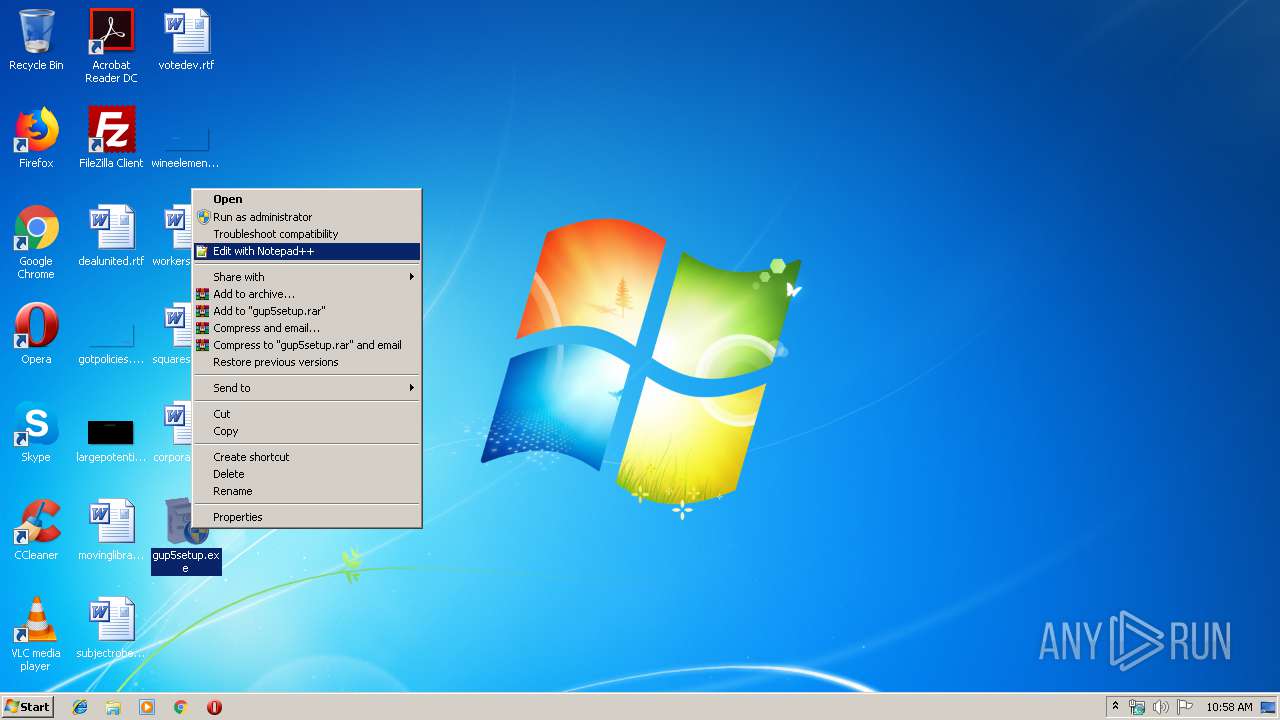
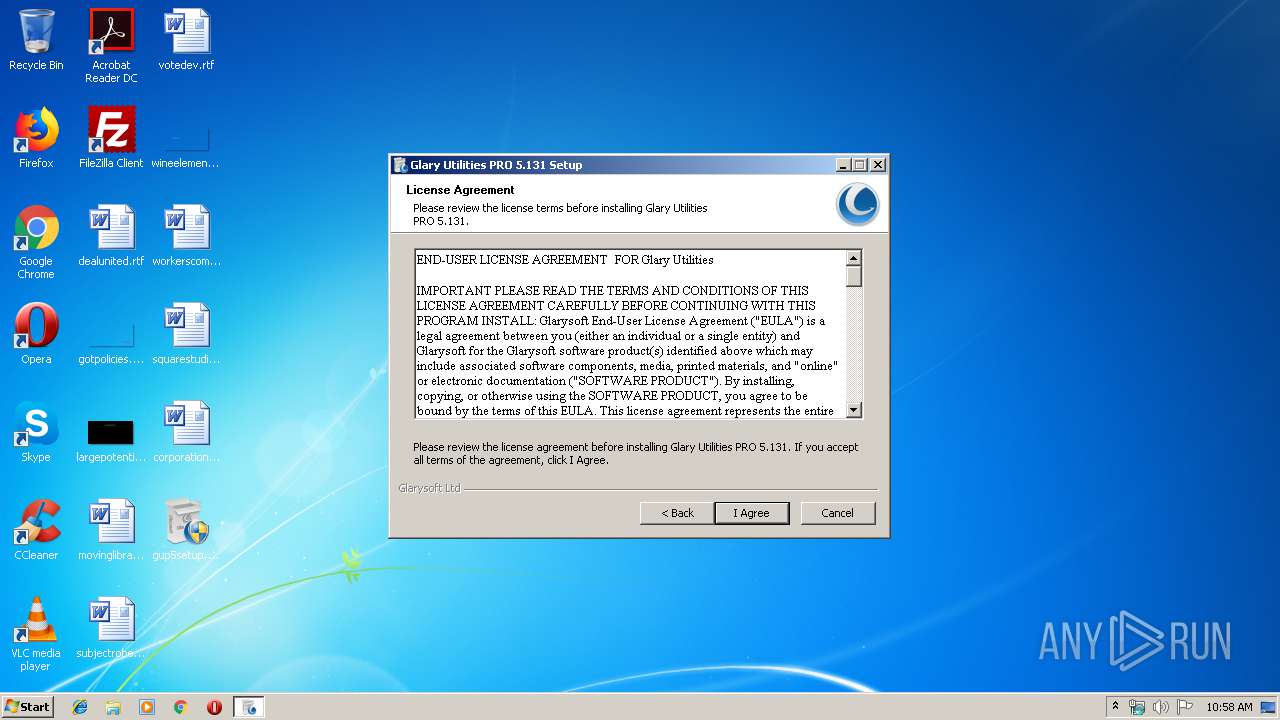
Manual execution by user
- gup5setup.exe (PID: 2432)
Application launched itself
- iexplore.exe (PID: 688)
Changes internet zones settings
- iexplore.exe (PID: 688)
Reads internet explorer settings
- iexplore.exe (PID: 3404)
Reads Internet Cache Settings
- iexplore.exe (PID: 3404)
Creates files in the user directory
- iexplore.exe (PID: 3404)
Reads settings of System Certificates
- iexplore.exe (PID: 3404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 05:20:05+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fb |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
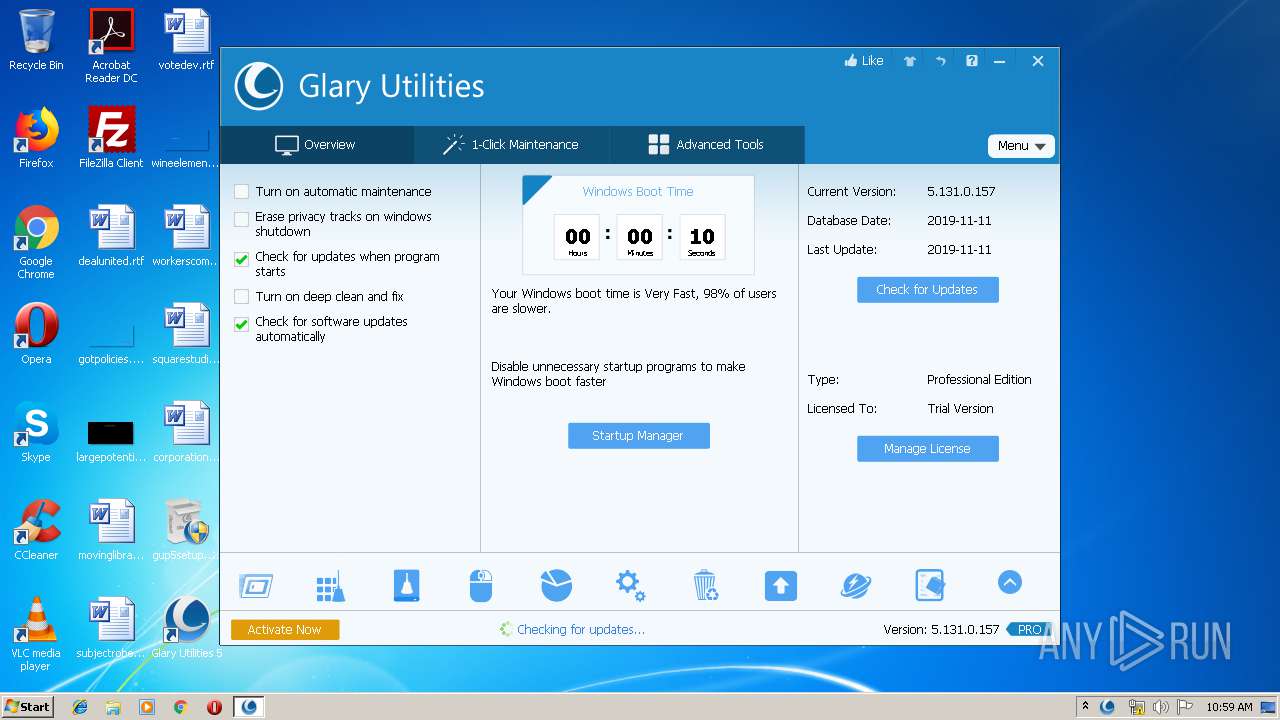
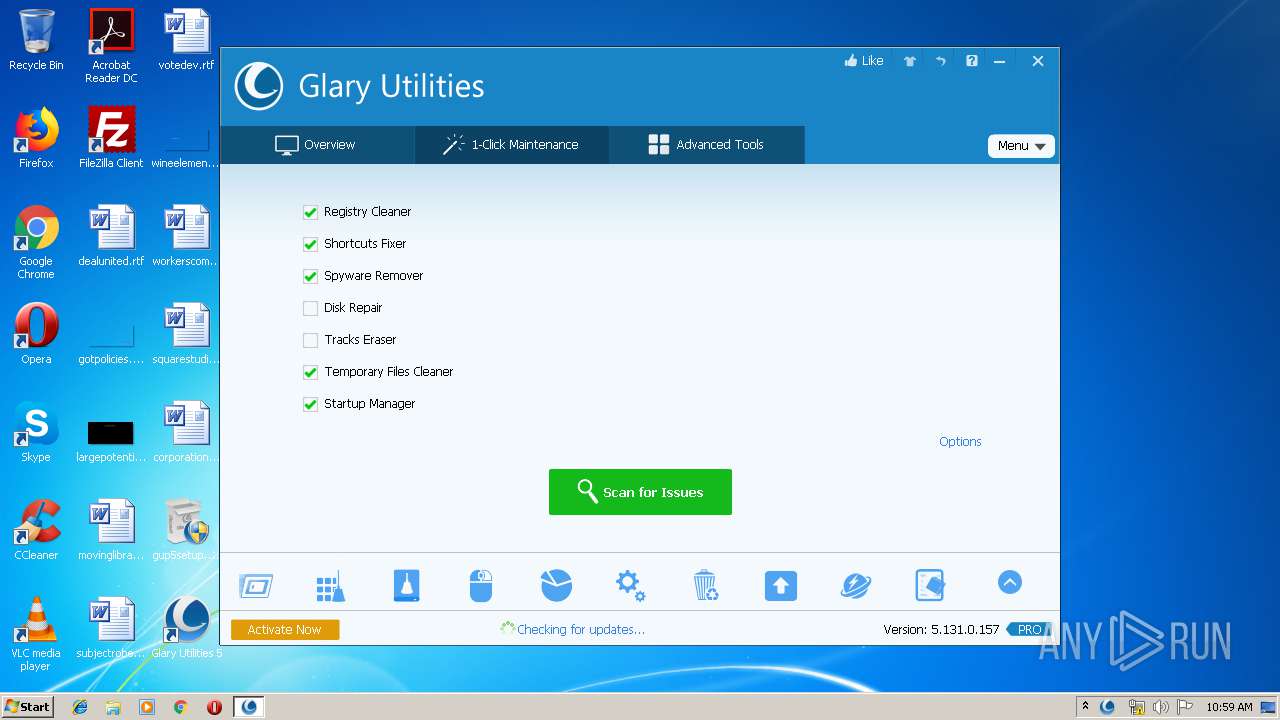
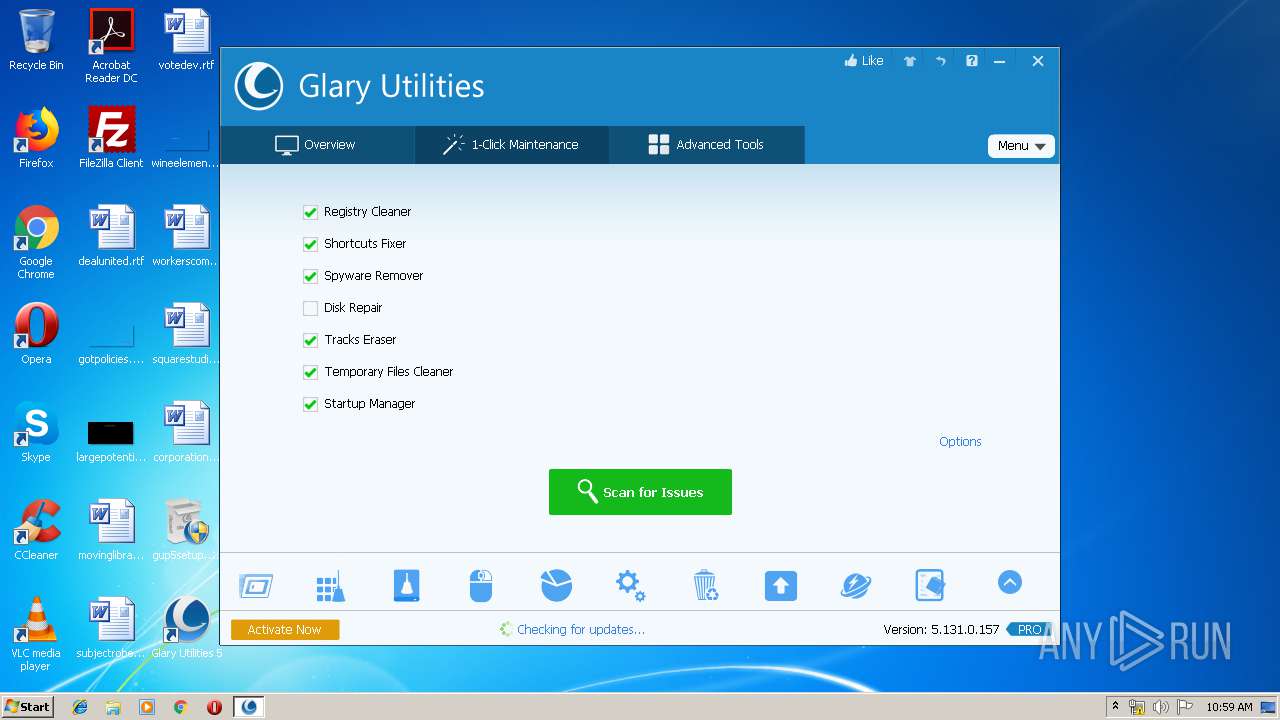
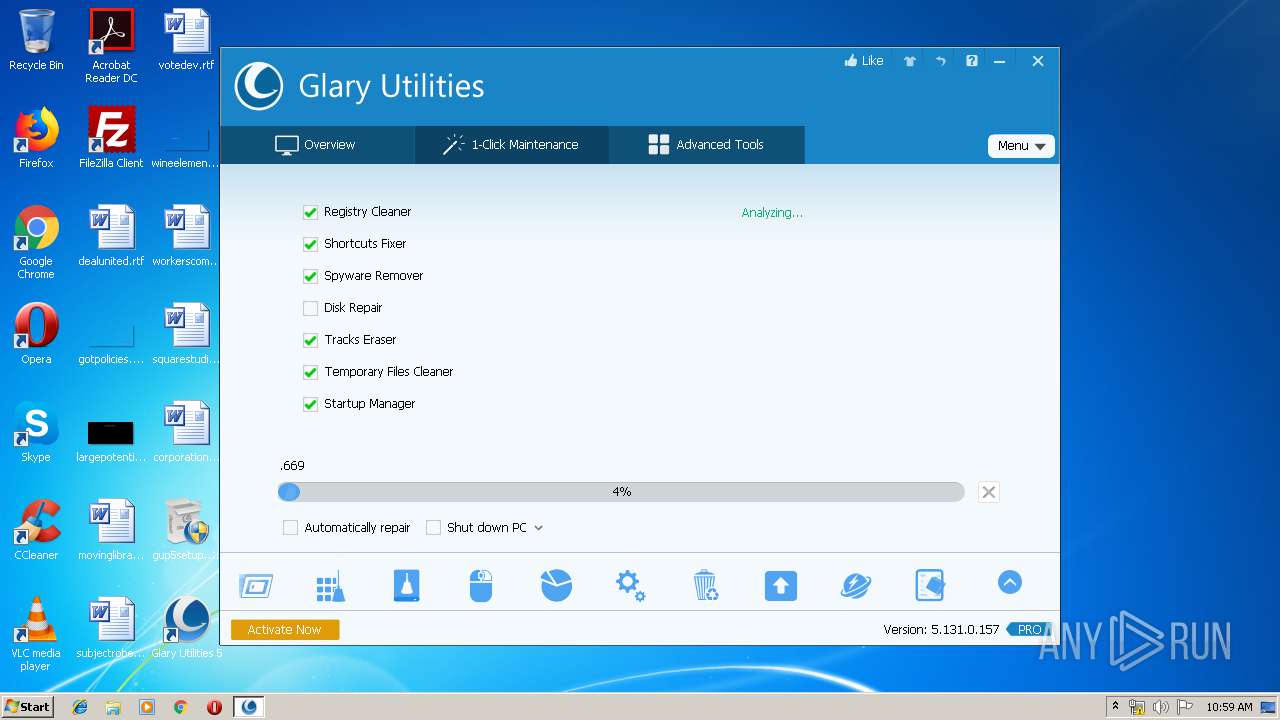
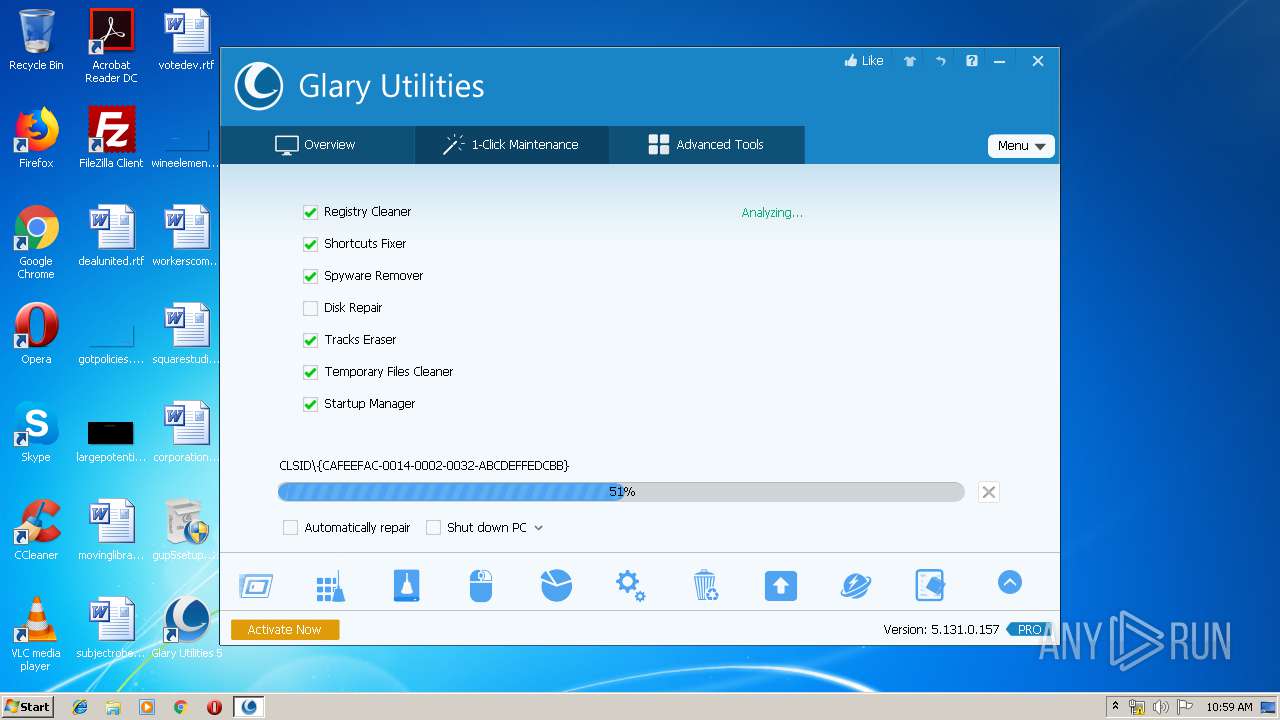
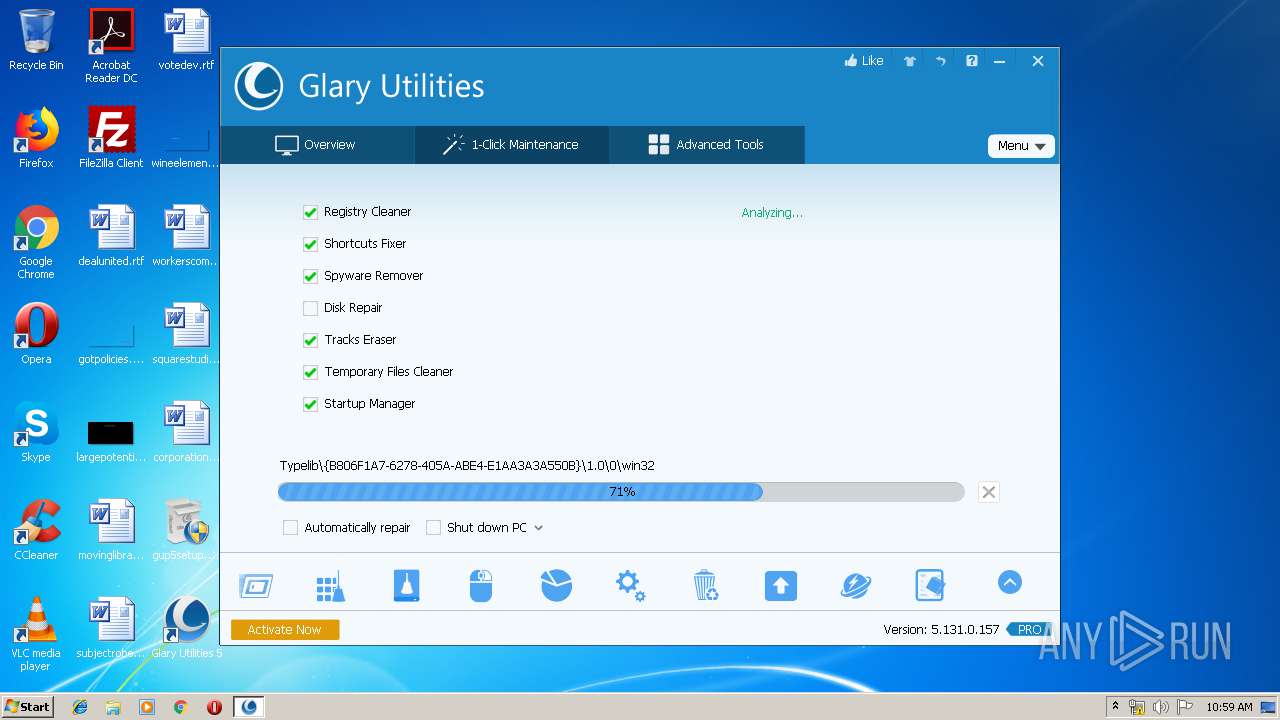
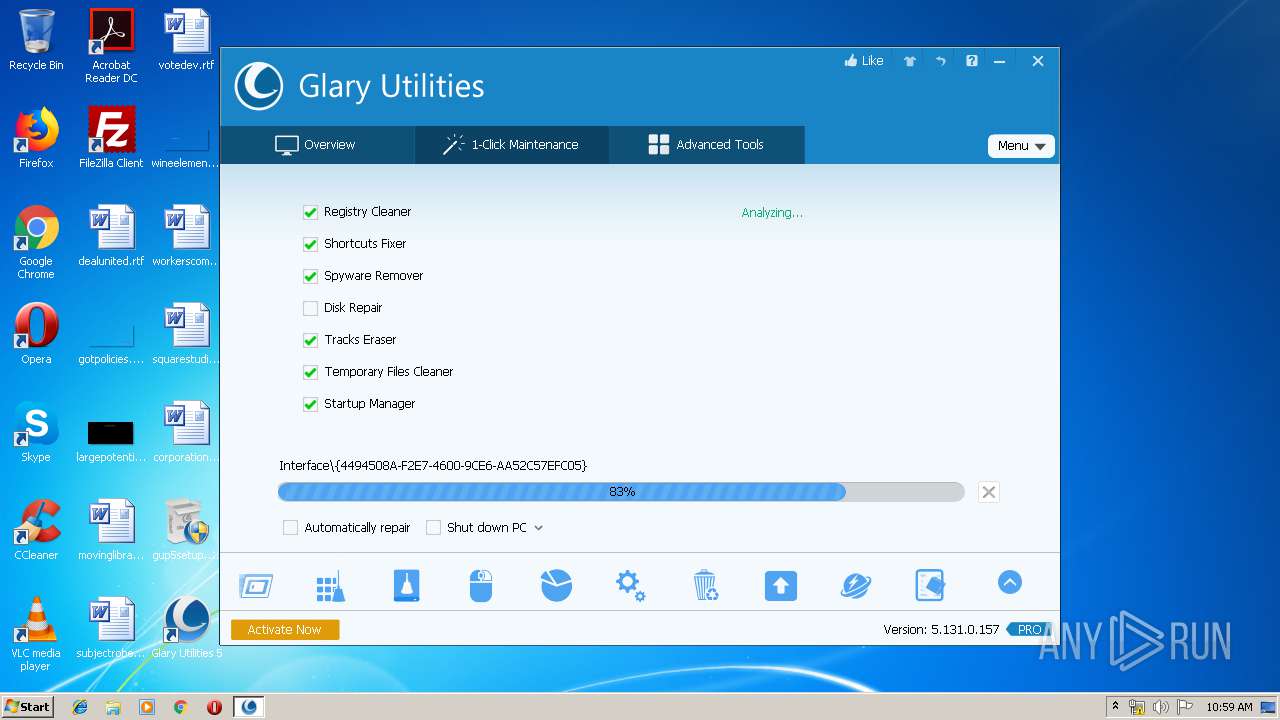
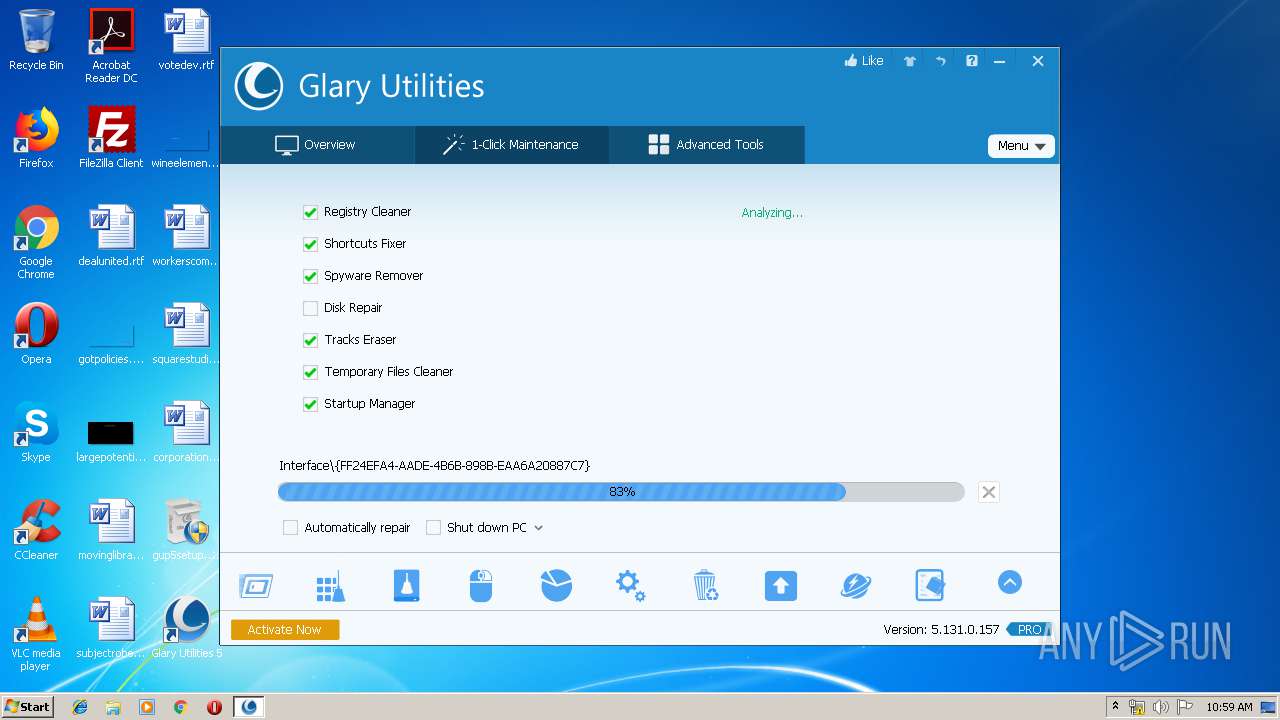
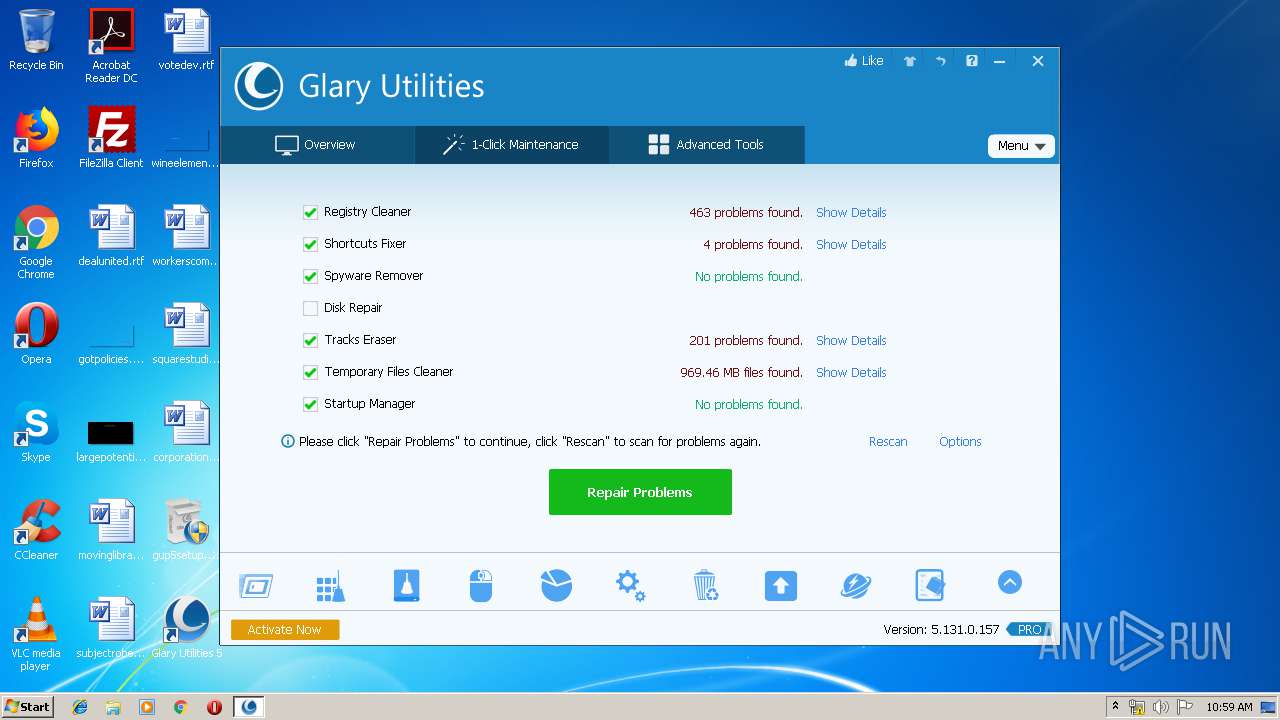
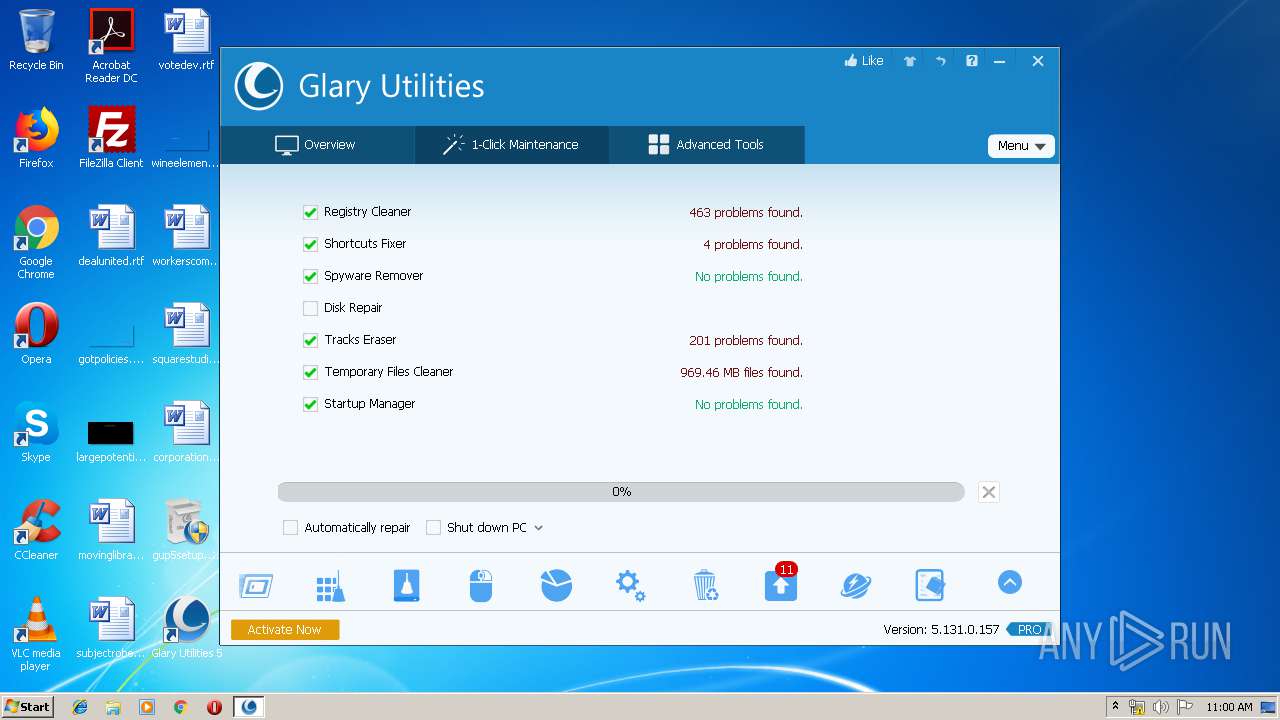
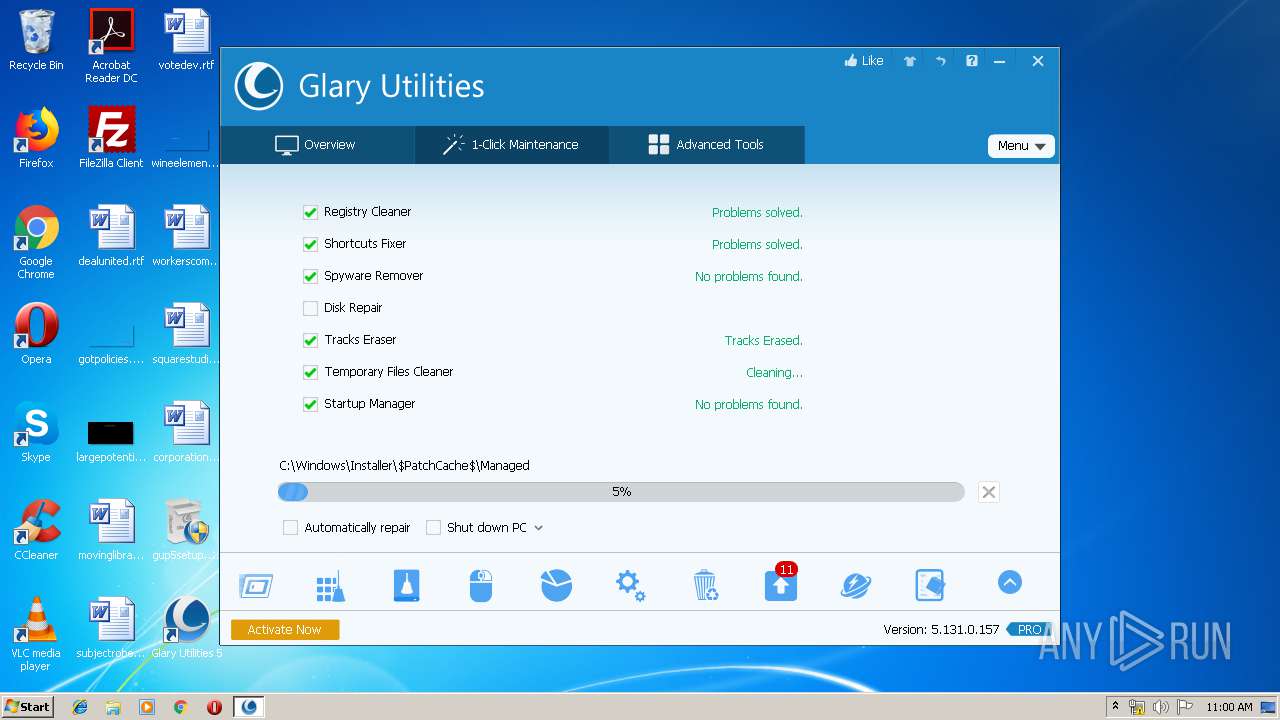
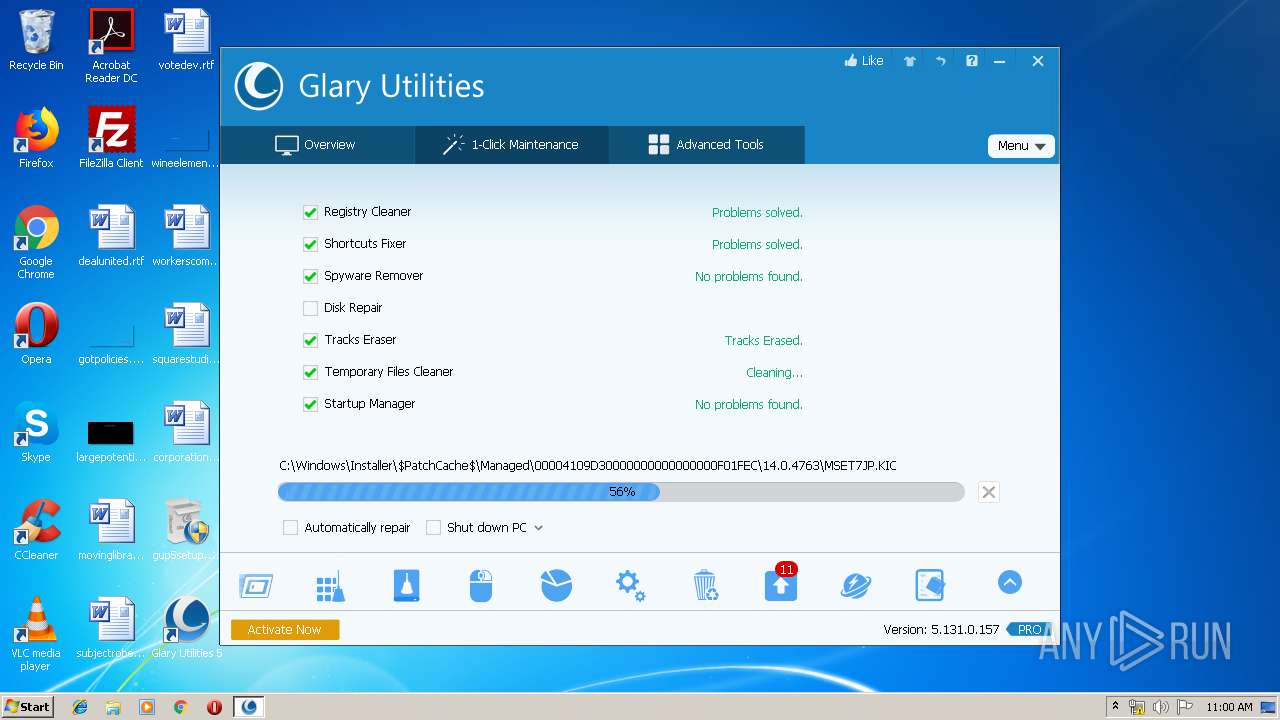
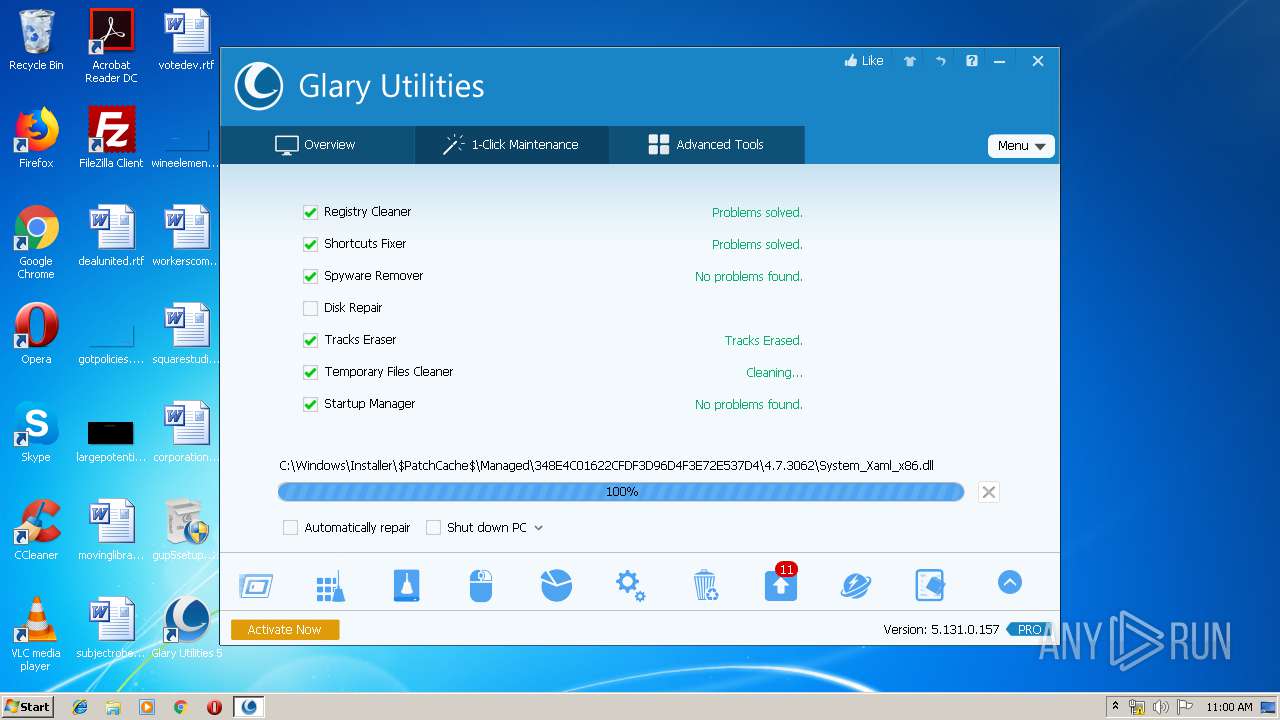
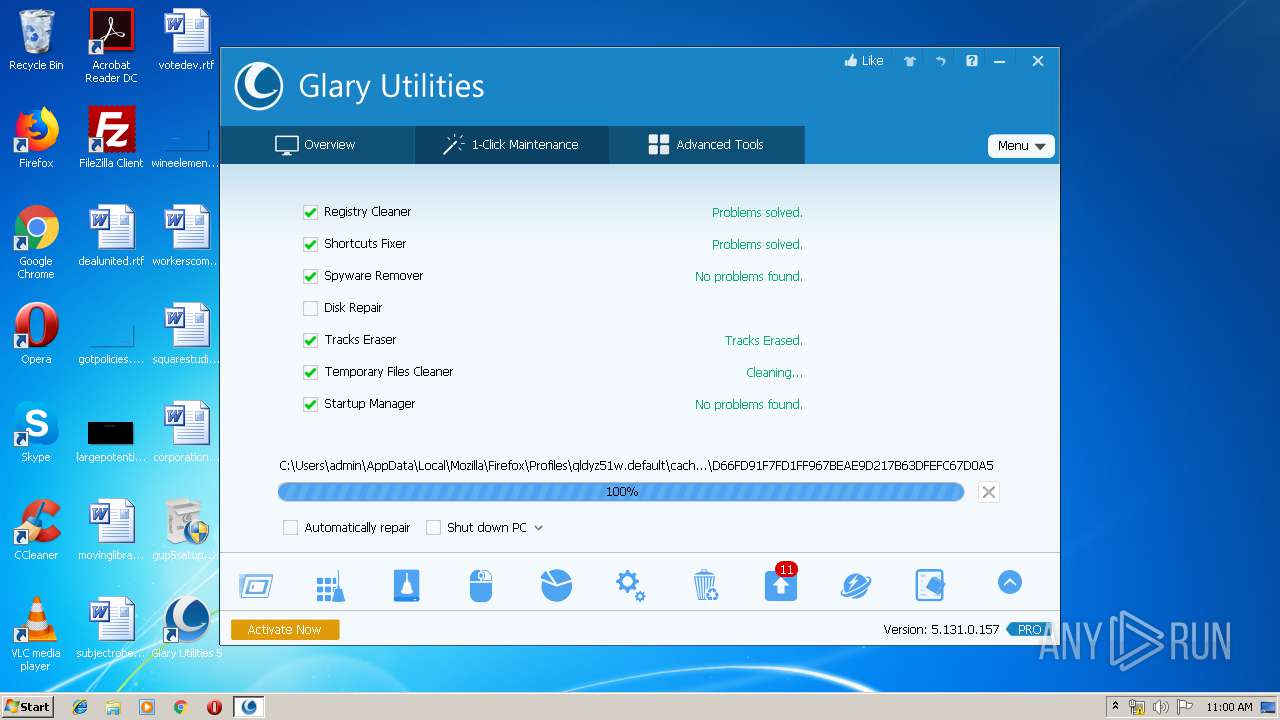
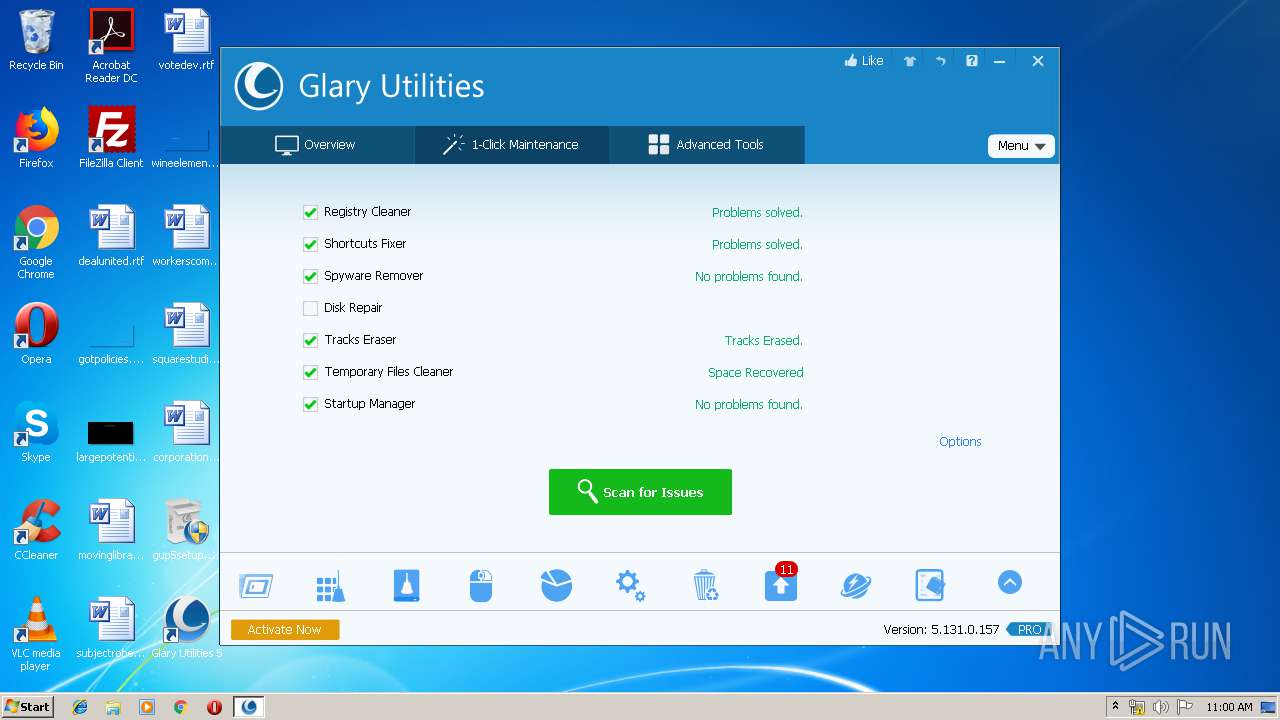
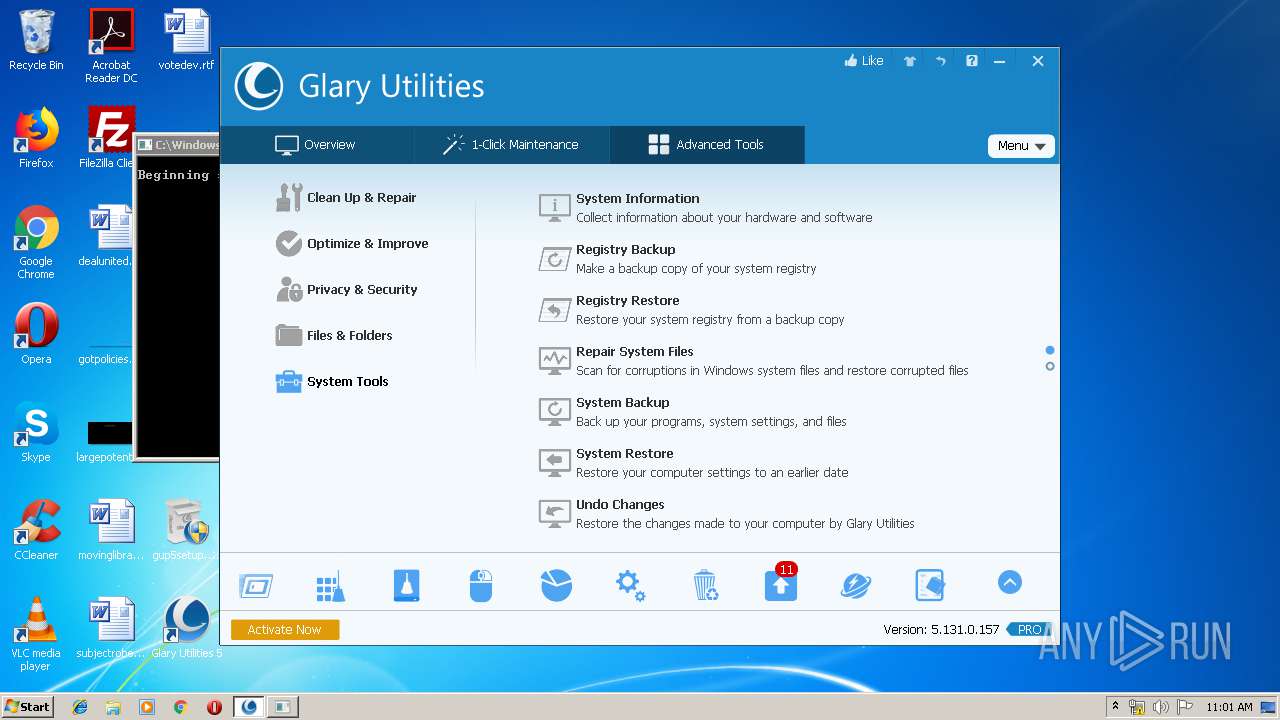
| FileVersionNumber: | 5.131.0.157 |
| ProductVersionNumber: | 5.131.0.157 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unknown (04E9) |
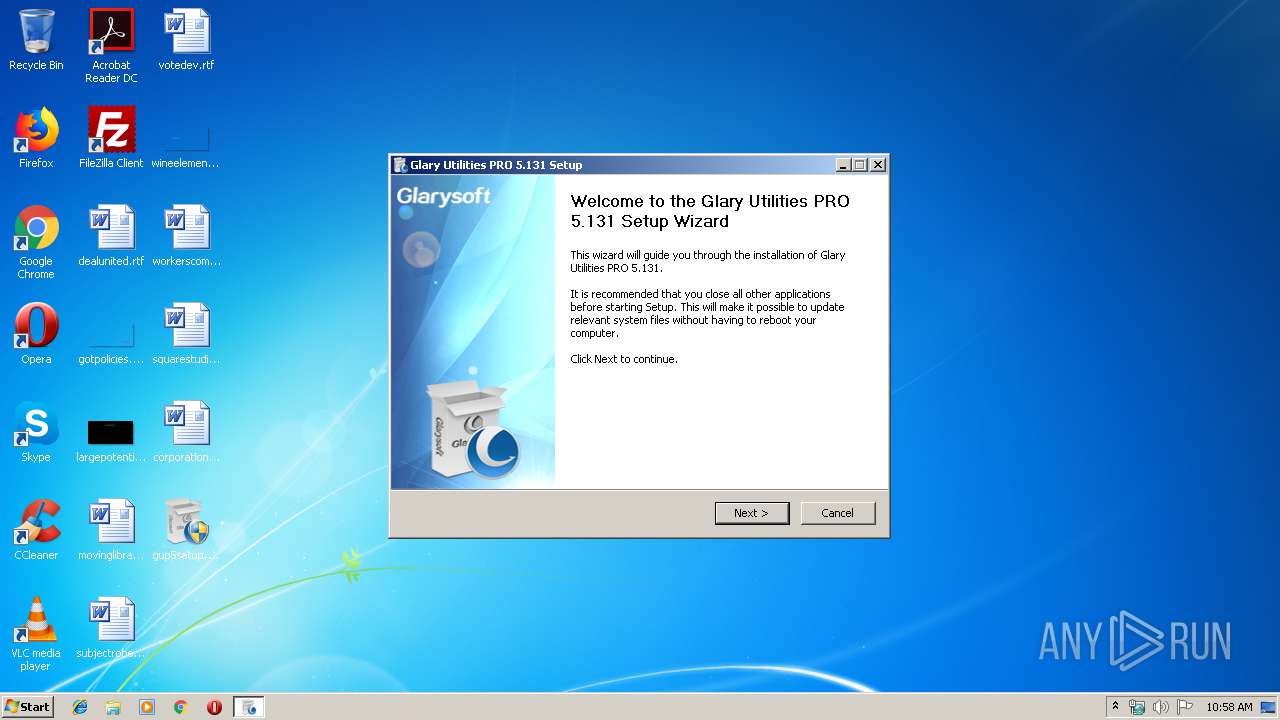
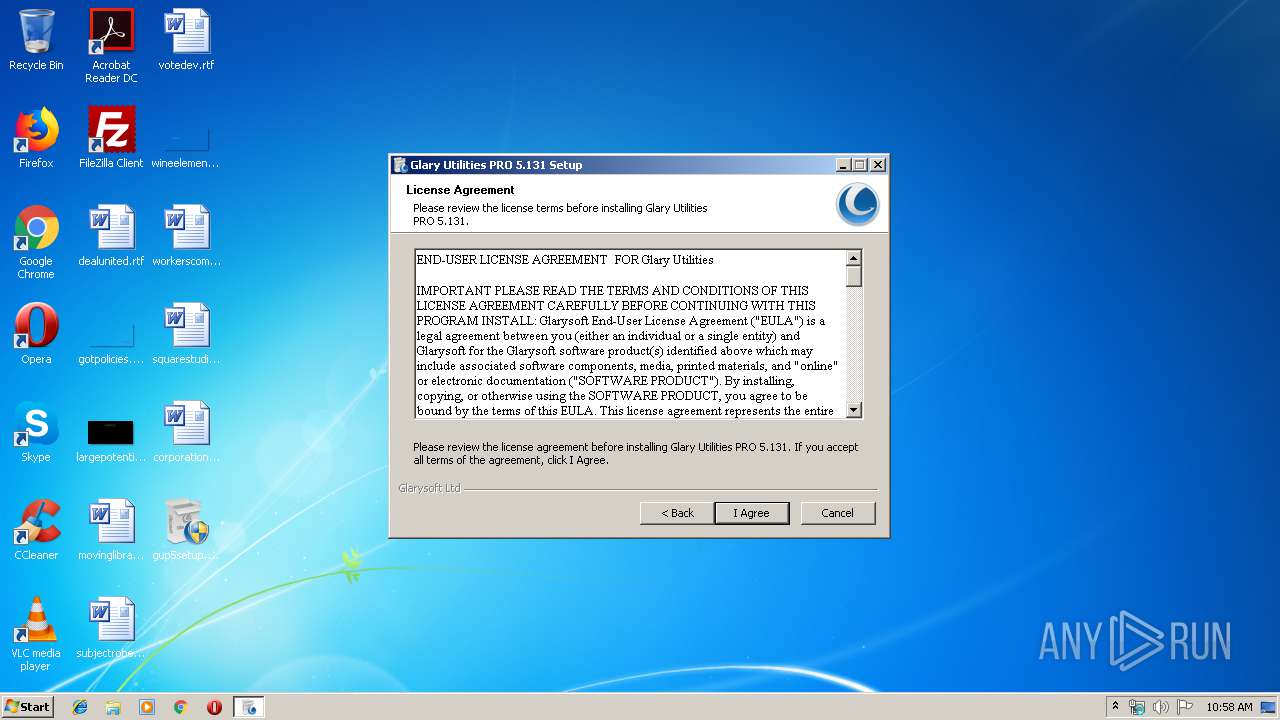
| CompanyName: | Glarysoft Ltd |
| FileDescription: | Glary Utilities Installer |
| LegalCopyright: | Copyright (c) 2003-2018 Glarysoft Ltd |
| ProductName: | Glary Utilities 5 |
| ProductVersion: | 5.131.0.157 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:20:05 |
| Detected languages: |
|
| CompanyName: | Glarysoft Ltd |
| FileDescription: | Glary Utilities Installer |
| LegalCopyright: | Copyright (c) 2003-2018 Glarysoft Ltd |
| ProductName: | Glary Utilities 5 |
| ProductVersion: | 5.131.0.157 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2016 03:20:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005AEB | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42231 |
.rdata | 0x00007000 | 0x00001196 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20292 |
.data | 0x00009000 | 0x0001B038 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04751 |
.ndata | 0x00025000 | 0x00019000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003E000 | 0x00013DB8 | 0x00013E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.22963 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21417 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.55428 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.64012 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.70917 | 2440 | UNKNOWN | English - United States | RT_ICON |
5 | 5.76999 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.70088 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
203 | 2.47654 | 268 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
65
Monitored processes
20
Malicious processes
12
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 656 | "C:\Program Files\Glary Utilities 5\SoftwareUpdate.exe" -autorun show | C:\Program Files\Glary Utilities 5\SoftwareUpdate.exe | Integrator.exe | ||||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities Software Update Exit code: 2 Version: 5.0.0.45 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | gup5setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
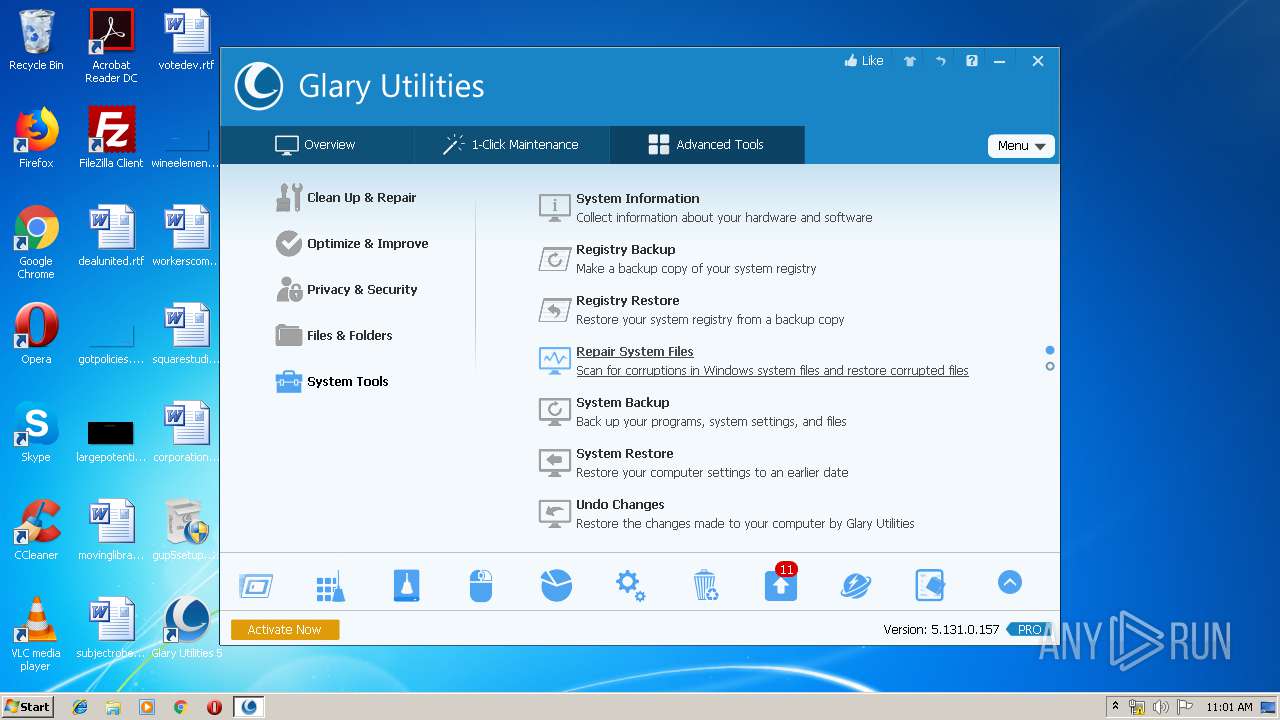
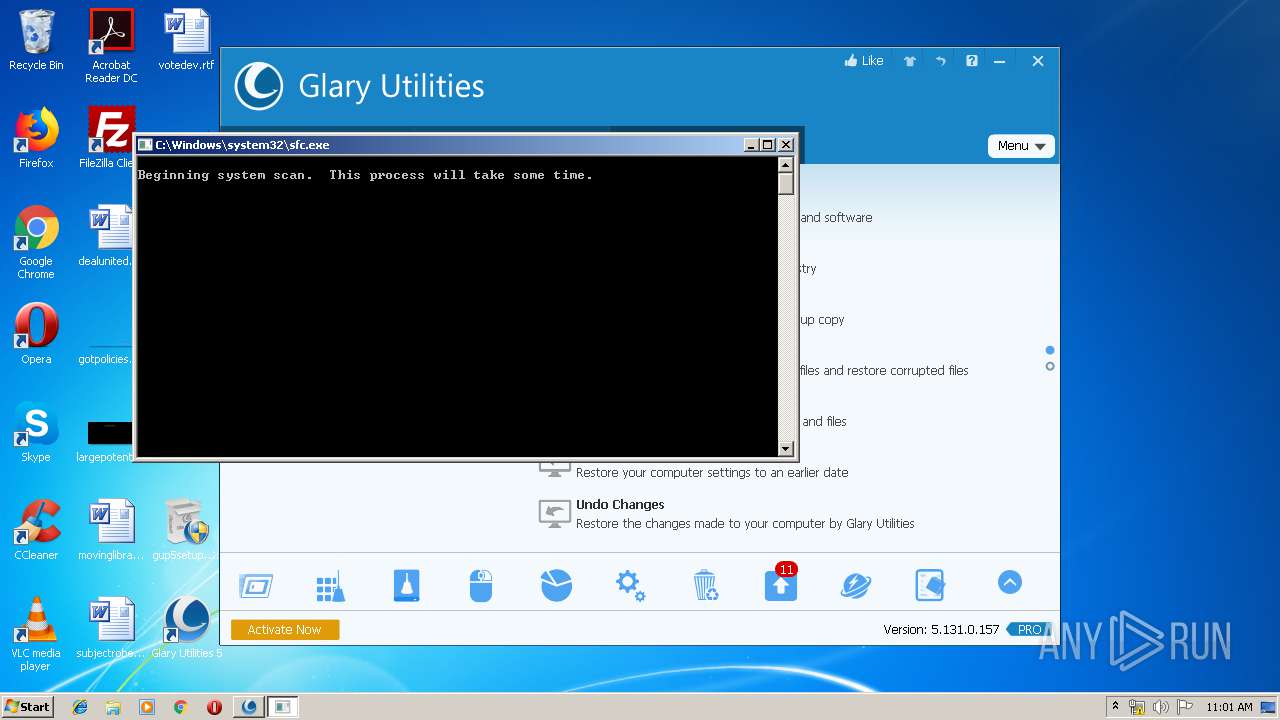
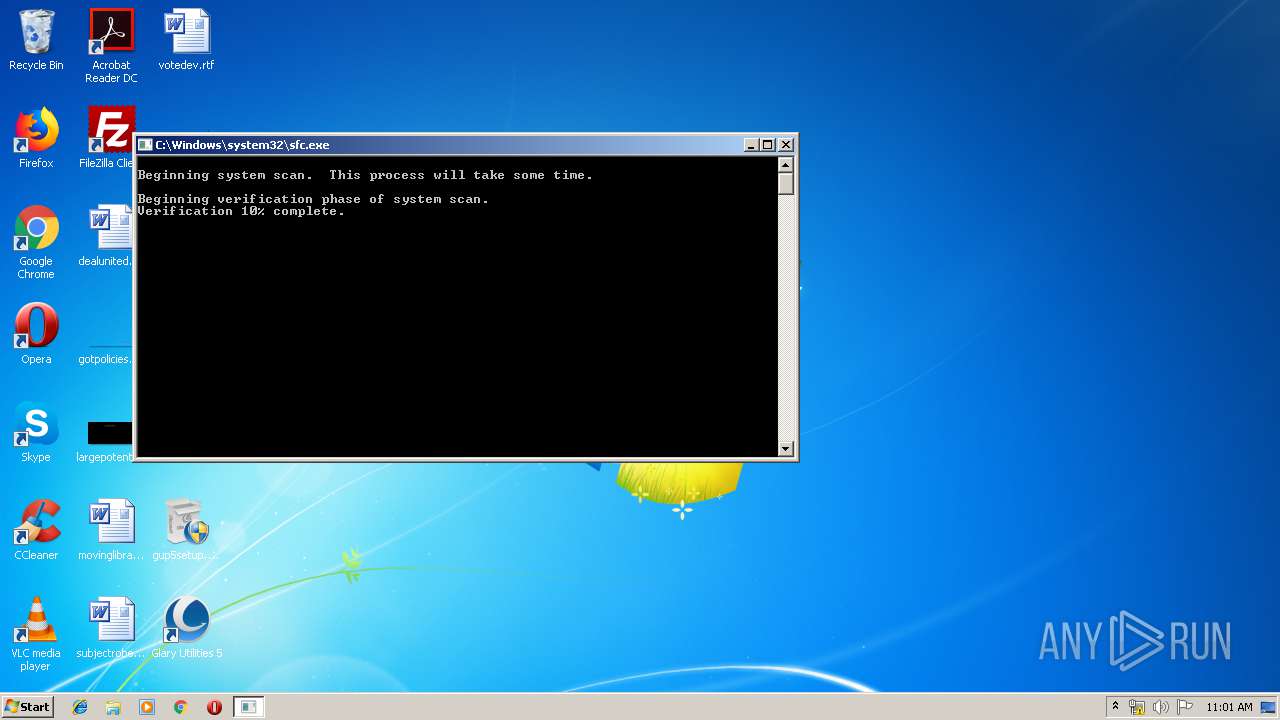
| 896 | "C:\Windows\system32\sfc.exe" /SCANNOW | C:\Windows\system32\sfc.exe | — | Integrator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: System Integrity Check and Repair Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Glary Utilities 5\Integrator.exe" | C:\Program Files\Glary Utilities 5\Integrator.exe | gup5setup.exe | ||||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities 5 Exit code: 32772 Version: 5, 131, 0, 157 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Glary Utilities 5\Integrator.exe" | C:\Program Files\Glary Utilities 5\Integrator.exe | explorer.exe | ||||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities 5 Exit code: 0 Version: 5, 131, 0, 157 Modules
| |||||||||||||||
| 1912 | "C:\Users\admin\Desktop\gup5setup.exe" | C:\Users\admin\Desktop\gup5setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: MEDIUM Description: Glary Utilities Installer Exit code: 3221226540 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Glary Utilities 5\DiskDefrag.exe" -InstallNative | C:\Program Files\Glary Utilities 5\DiskDefrag.exe | — | gup5setup.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities Defragmenter Exit code: 0 Version: 5.0.0.64 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Glary Utilities 5\MemfilesService.exe" | C:\Program Files\Glary Utilities 5\MemfilesService.exe | — | Integrator.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: MemfilesService Exit code: 0 Version: 5.18.1.21 Modules
| |||||||||||||||
Total events
6 967
Read events
4 375
Write events
739
Delete events
1 853
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\thc5frghc.rkr |
Value: 00000000000000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000320000003700000095E01200090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\thc5frghc.rkr |
Value: 0000000000000000000000000F000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003200000037000000A4E01200090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @sendmail.dll,-21 |
Value: Desktop (create shortcut) | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @zipfldr.dll,-10148 |
Value: Compressed (zipped) folder | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @sendmail.dll,-4 |
Value: Mail recipient | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\FXSRESM.dll,-120 |
Value: Fax recipient | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
Executable files
115
Suspicious files
42
Text files
496
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 864 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 2864 | gup5setup.exe | C:\Users\admin\AppData\Local\Temp\nsyCFFD.tmp\System.dll | executable | |
MD5:— | SHA256:— | |||
| 2864 | gup5setup.exe | C:\Users\admin\AppData\Local\Temp\nsyCFFD.tmp\modern-header.bmp | image | |
MD5:— | SHA256:— | |||
| 2864 | gup5setup.exe | C:\Users\admin\AppData\Local\Temp\nsyCFFD.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
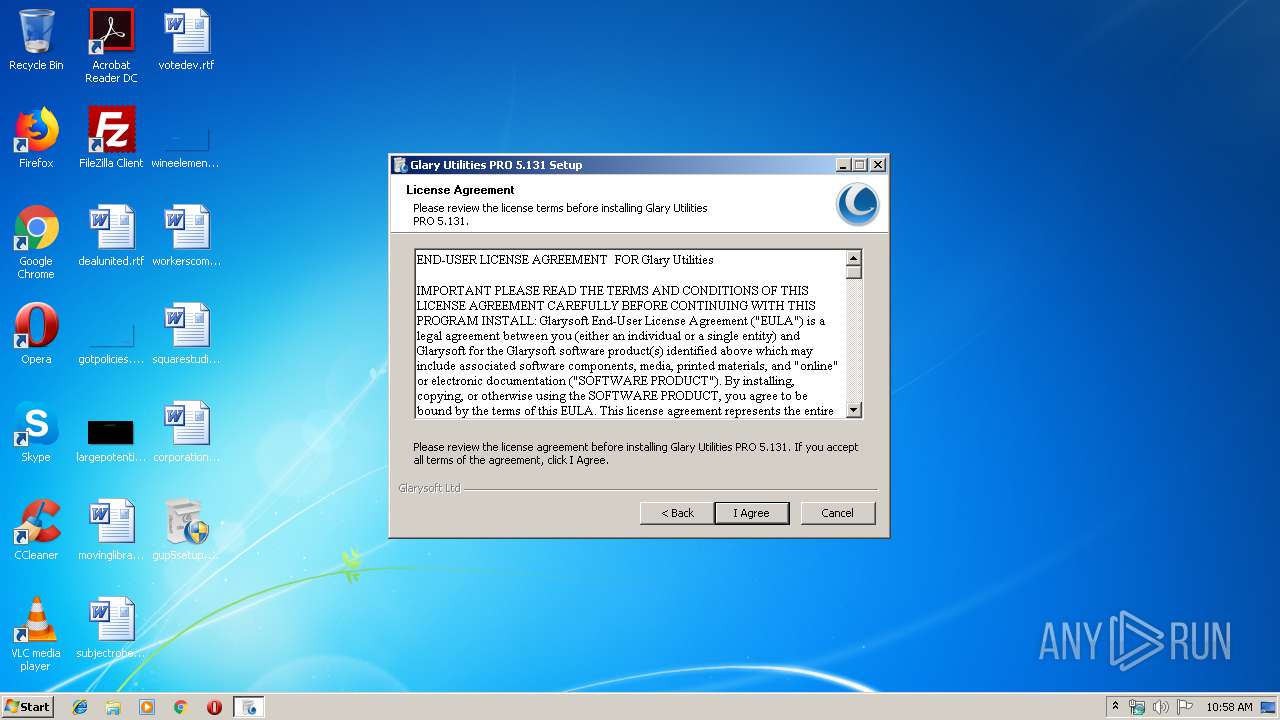
| 2864 | gup5setup.exe | C:\Users\admin\AppData\Local\Temp\nsyCFFD.tmp\EULA.rtf | text | |
MD5:— | SHA256:— | |||
| 2432 | gup5setup.exe | C:\Users\admin\AppData\Local\Temp\nss3FFD.tmp\EULA.rtf | text | |
MD5:— | SHA256:— | |||
| 2432 | gup5setup.exe | C:\Users\admin\AppData\Local\Temp\nss3FFD.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 2432 | gup5setup.exe | C:\Users\admin\AppData\Local\Temp\nss3FFD.tmp\KillProcPath.dll | executable | |
MD5:— | SHA256:— | |||
| 2432 | gup5setup.exe | C:\Users\admin\AppData\Local\Temp\nss3FFD.tmp\MachineCode.dll | executable | |
MD5:— | SHA256:— | |||
| 2432 | gup5setup.exe | C:\Program Files\Glary Utilities 5\AppMetrics.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
39
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2496 | sendinfo.exe | POST | 200 | 54.186.7.180:80 | http://metrics.glarysoft.com/install.php | US | — | — | whitelisted |
3404 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/global.css?191111 | US | html | 255 b | whitelisted |
3404 | iexplore.exe | GET | 200 | 54.243.205.134:80 | http://www.glarysoft.com/update/release-notes/gup/5.131.0.157 | US | html | 24.8 Kb | whitelisted |
3404 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/content.css?18011003 | US | html | 258 b | whitelisted |
3404 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/js/index.js?19113 | US | html | 251 b | whitelisted |
3404 | iexplore.exe | GET | 200 | 172.217.18.10:80 | http://fonts.googleapis.com/css?family=Open+Sans:400,300,600,800,700 | US | text | 167 b | whitelisted |
3404 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/js/jquery.min.js?161014:0914 | US | html | 262 b | whitelisted |
3404 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/layout.css?19111404 | US | html | 257 b | whitelisted |
1532 | Integrator.exe | POST | 200 | 23.23.198.31:80 | http://gu.glarysoft.com/boottime/service.php | US | xml | 675 b | suspicious |
3404 | iexplore.exe | GET | 301 | 54.243.205.134:80 | http://www.glarysoft.com/css/new.css?19111410 | US | html | 254 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3404 | iexplore.exe | 54.243.205.134:443 | www.glarysoft.com | Amazon.com, Inc. | US | unknown |
2496 | sendinfo.exe | 54.186.7.180:80 | metrics.glarysoft.com | Amazon.com, Inc. | US | whitelisted |
3404 | iexplore.exe | 54.243.205.134:80 | www.glarysoft.com | Amazon.com, Inc. | US | unknown |
3404 | iexplore.exe | 143.204.222.220:80 | x.ss2.us | — | US | unknown |
3404 | iexplore.exe | 13.32.211.72:80 | x.ss2.us | Amazon.com, Inc. | US | unknown |
2824 | autoupdate.exe | 54.243.205.134:80 | www.glarysoft.com | Amazon.com, Inc. | US | unknown |
1532 | Integrator.exe | 54.243.205.134:443 | www.glarysoft.com | Amazon.com, Inc. | US | unknown |
1532 | Integrator.exe | 23.23.198.31:80 | gu.glarysoft.com | Amazon.com, Inc. | US | suspicious |
1532 | Integrator.exe | 184.73.187.80:80 | go.glarysoft.com | Amazon.com, Inc. | US | unknown |
1560 | Integrator.exe | 54.243.205.134:443 | www.glarysoft.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
metrics.glarysoft.com |
| whitelisted |
www.glarysoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
css3-mediaqueries-js.googlecode.com |
| whitelisted |
gu.glarysoft.com |
| suspicious |
go.glarysoft.com |
| unknown |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2496 | sendinfo.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |