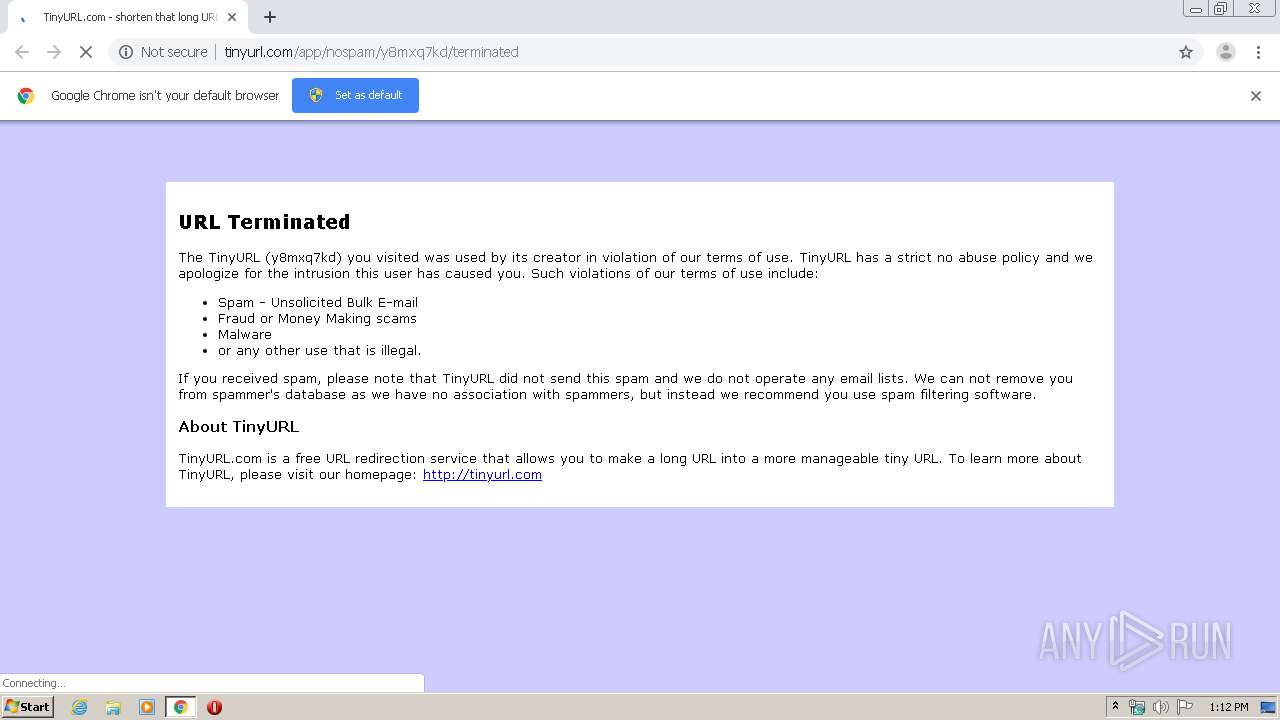
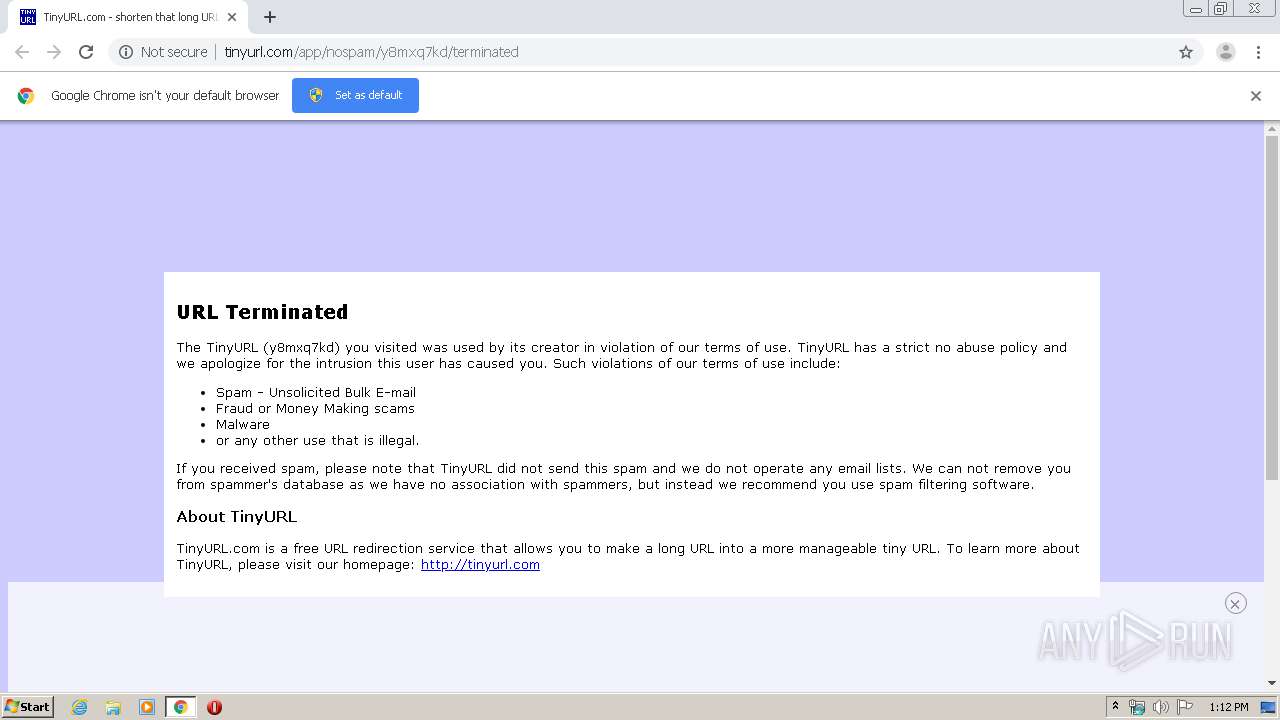
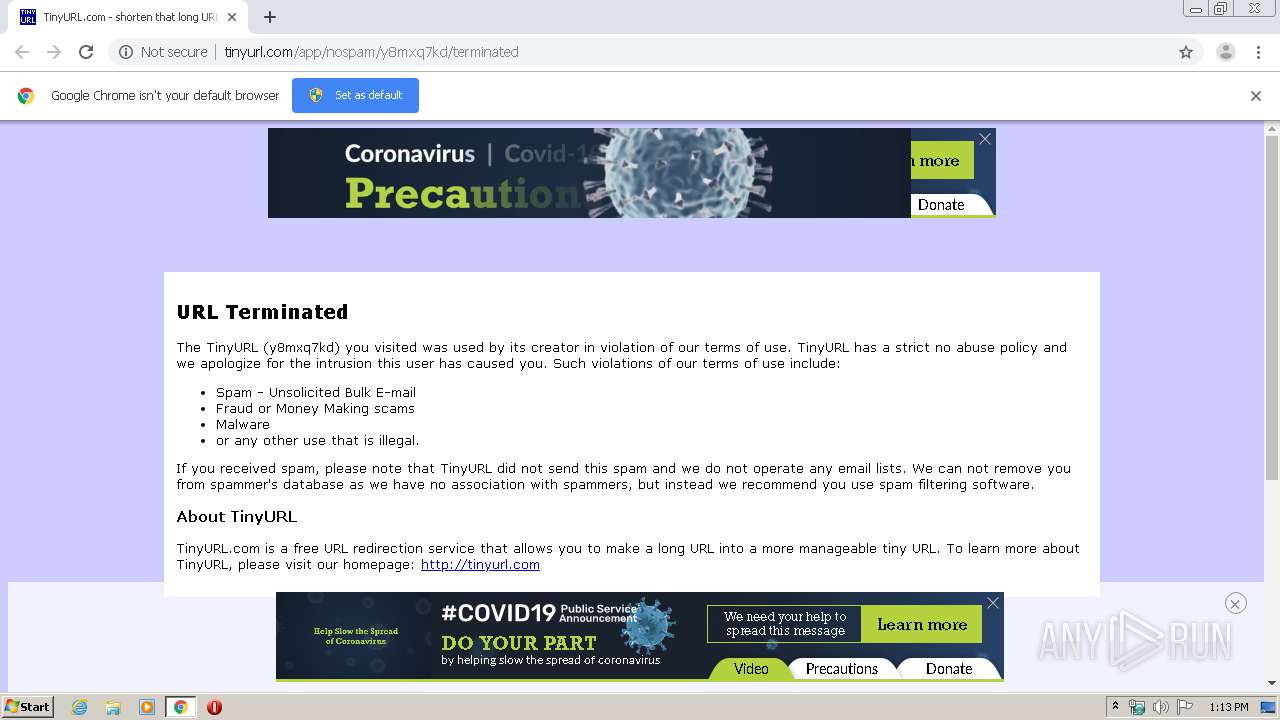
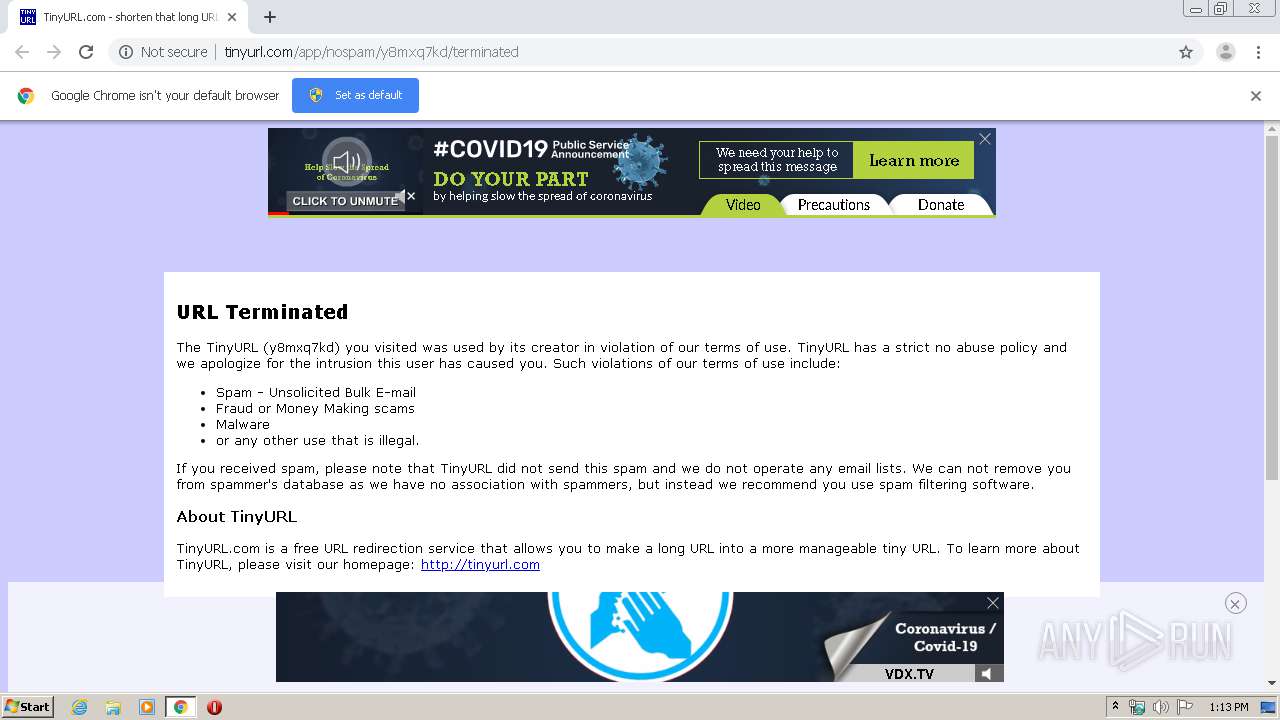
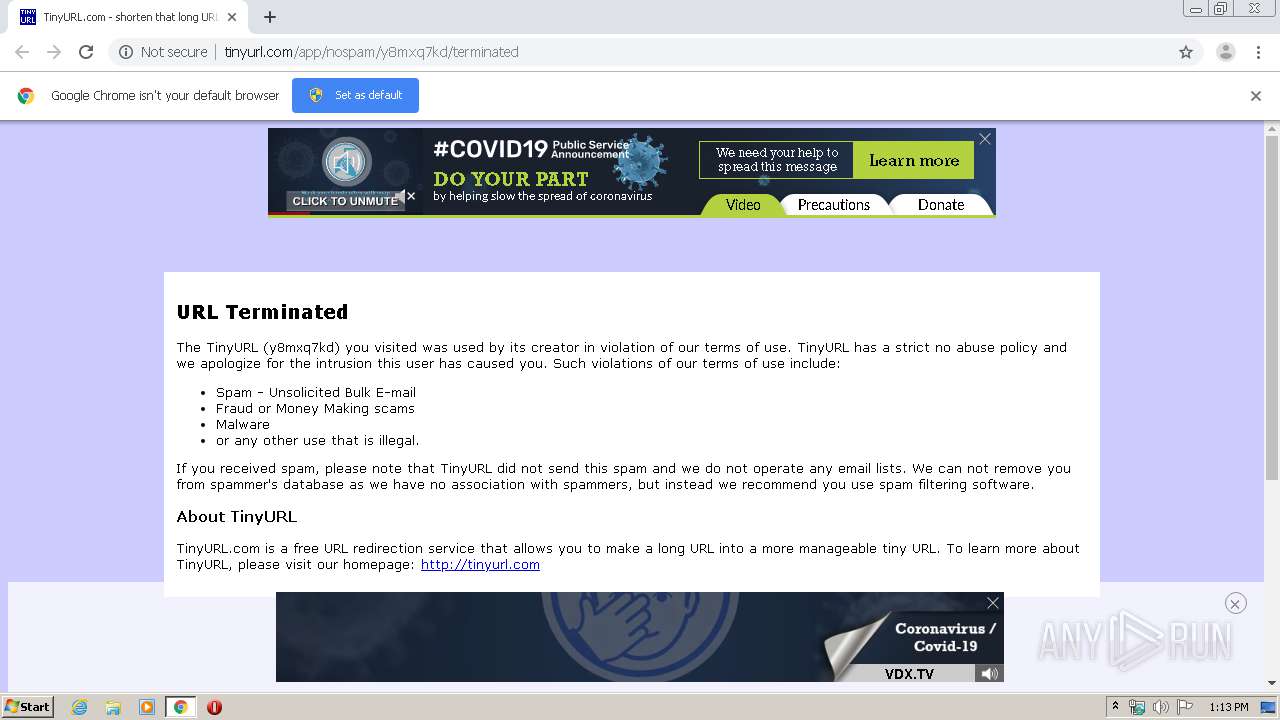
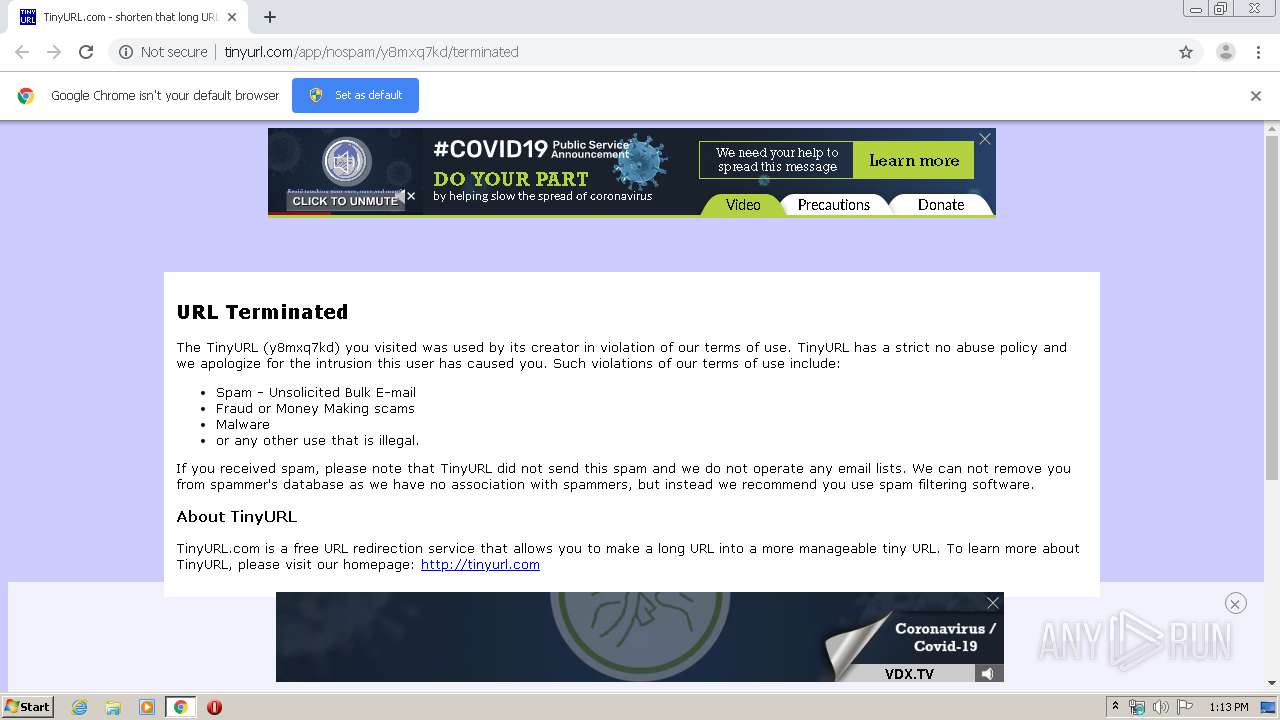
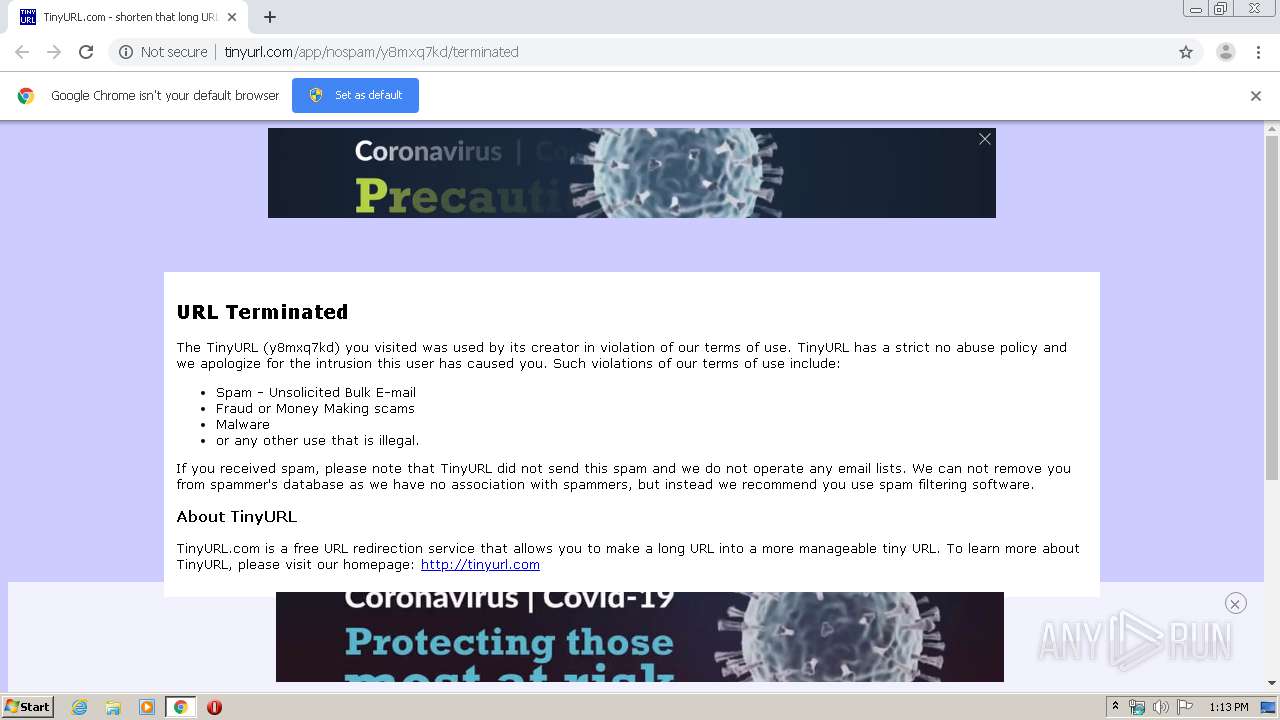
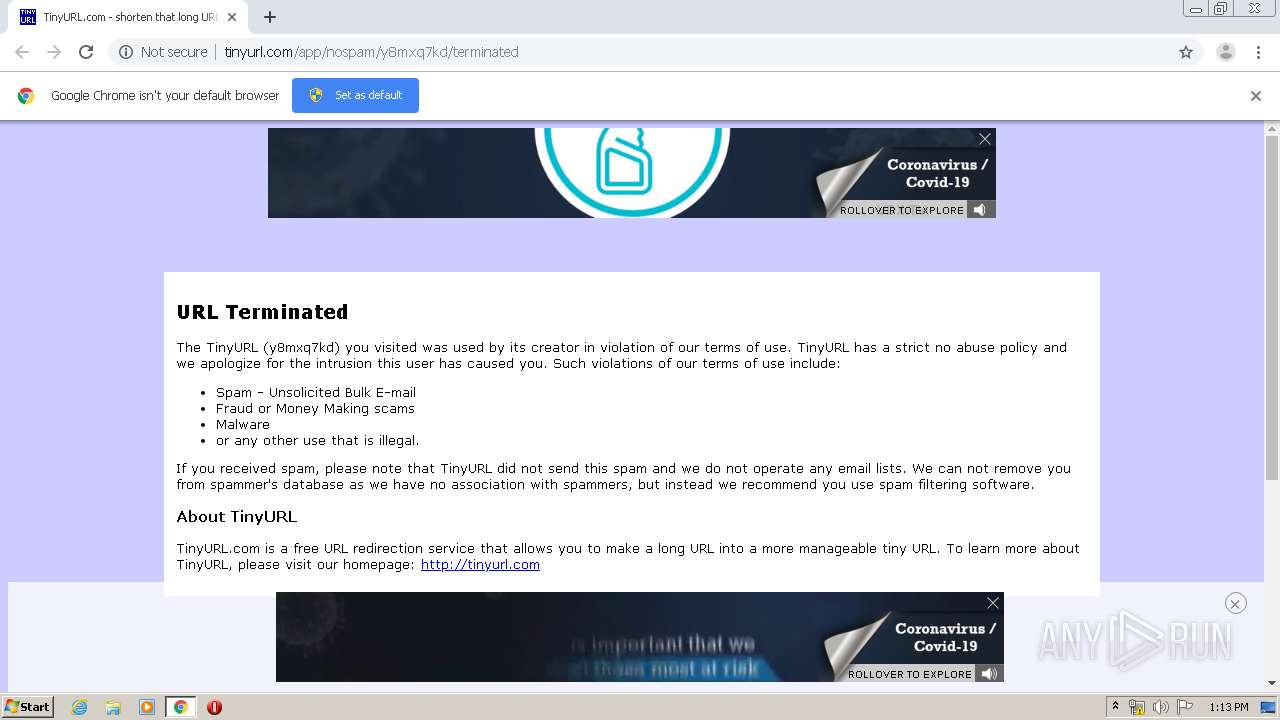
| URL: | http://tinyurl.com/y8mxq7kd |
| Full analysis: | https://app.any.run/tasks/b882ab67-f68b-43f4-8f0f-bed1ed7f5ba1 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 12:12:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2F0D3F18C758C578B4D9E99754285792 |
| SHA1: | FA2507CCD645B666901B0D8BA70F2D8990022FF1 |
| SHA256: | 13640AD02A020BAF213758DB7C542A0CD014210B107BCCEC10B1A639C8E73C0A |
| SSDEEP: | 3:N1KKMzLdIHOOB:CKwdsX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3132)
INFO
Drops Coronavirus (possible) decoy
- chrome.exe (PID: 3152)
Reads the hosts file
- chrome.exe (PID: 3132)
- chrome.exe (PID: 3152)
Application launched itself
- chrome.exe (PID: 3132)
Reads settings of System Certificates
- chrome.exe (PID: 3152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
36
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17733668035594762619,1706972063312616231,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7147251078882201507 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4400 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,17733668035594762619,1706972063312616231,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14727418734104826071 --mojo-platform-channel-handle=4932 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17733668035594762619,1706972063312616231,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=782774661104993280 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,17733668035594762619,1706972063312616231,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13558267288592962957 --mojo-platform-channel-handle=3168 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,17733668035594762619,1706972063312616231,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15308801079224931845 --mojo-platform-channel-handle=4688 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17733668035594762619,1706972063312616231,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5620399806541786767 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,17733668035594762619,1706972063312616231,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1910976704602459457 --mojo-platform-channel-handle=5768 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17733668035594762619,1706972063312616231,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16418772833404064528 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,17733668035594762619,1706972063312616231,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3201315545143509807 --mojo-platform-channel-handle=5276 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,17733668035594762619,1706972063312616231,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3308362085829455758 --mojo-platform-channel-handle=4704 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 146
Read events
1 030
Write events
110
Delete events
6
Modification events
| (PID) Process: | (3132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3132-13235314357467750 |
Value: 259 | |||
| (PID) Process: | (3132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3132) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
138
Text files
248
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED24DB6-C3C.pma | — | |
MD5:— | SHA256:— | |||
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bd3b7791-7451-411d-9ae4-ddef84007b93.tmp | — | |
MD5:— | SHA256:— | |||
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF15d51c.TMP | text | |
MD5:— | SHA256:— | |||
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF15d53b.TMP | text | |
MD5:— | SHA256:— | |||
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15d73f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
265
TCP/UDP connections
177
DNS requests
93
Threats
76
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3152 | chrome.exe | GET | 304 | 8.253.207.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3152 | chrome.exe | GET | 304 | 8.253.207.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3152 | chrome.exe | GET | 301 | 74.125.143.154:80 | http://securepubads.g.doubleclick.net/tag/js/gpt.js | US | html | 249 b | whitelisted |
3152 | chrome.exe | GET | 200 | 104.19.247.53:80 | http://tinyurl.com/app/nospam/y8mxq7kd/terminated | US | html | 2.07 Kb | shared |
3152 | chrome.exe | GET | 301 | 104.19.247.53:80 | http://tinyurl.com/y8mxq7kd | US | html | 442 b | shared |
3152 | chrome.exe | GET | 200 | 8.253.207.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
3152 | chrome.exe | GET | 200 | 104.18.4.23:80 | http://tags.expo9.exponential.com/tags/TinyURLcom/NoBackfill/tags.js | US | html | 2.25 Kb | whitelisted |
3152 | chrome.exe | GET | 304 | 8.253.207.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
3152 | chrome.exe | GET | 200 | 104.18.12.5:80 | http://a.tribalfusion.com/displayAd.js?dver=0.8&th=6796529920 | US | text | 331 b | whitelisted |
3152 | chrome.exe | GET | 200 | 104.18.12.5:80 | http://a.tribalfusion.com/real/tags/TinyURLcom/NoBackfill/tags.js | US | text | 13.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3152 | chrome.exe | 108.177.126.94:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3152 | chrome.exe | 104.19.247.53:80 | tinyurl.com | Cloudflare Inc | US | unknown |
3152 | chrome.exe | 54.239.195.32:80 | tags-cdn.deployads.com | Amazon.com, Inc. | US | unknown |
3152 | chrome.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3152 | chrome.exe | 64.233.184.157:80 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3152 | chrome.exe | 74.125.128.147:443 | www.google.com | Google Inc. | US | whitelisted |
3152 | chrome.exe | 157.240.20.35:443 | www.facebook.com | Facebook, Inc. | US | whitelisted |
3152 | chrome.exe | 54.239.195.10:443 | api.pushnami.com | Amazon.com, Inc. | US | unknown |
3152 | chrome.exe | 74.125.143.154:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
3152 | chrome.exe | 178.162.133.150:80 | apex.go.sonobi.com | LeaseWeb Netherlands B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
tinyurl.com |
| shared |
accounts.google.com |
| shared |
tags-cdn.deployads.com |
| shared |
api.pushnami.com |
| shared |
connect.facebook.net |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.facebook.com |
| whitelisted |
www.google.com |
| malicious |
securepubads.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3152 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3152 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3152 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3152 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3152 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3152 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3152 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3152 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3152 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3152 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |