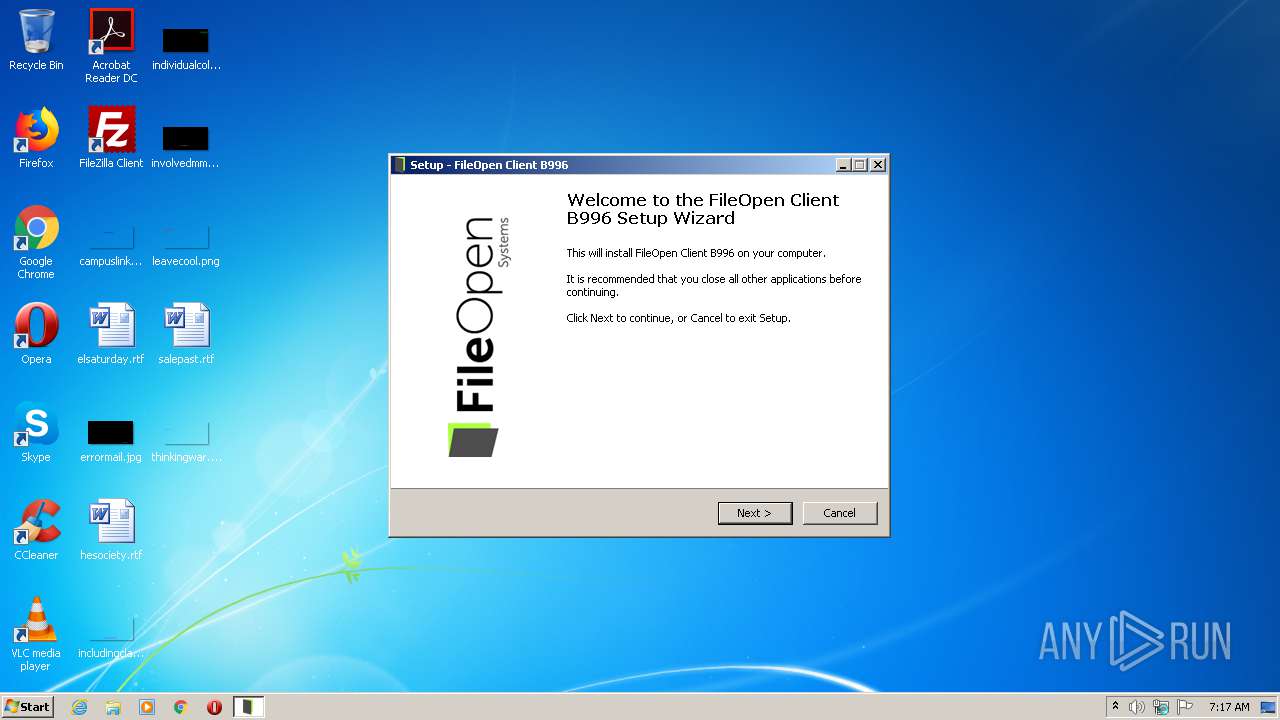
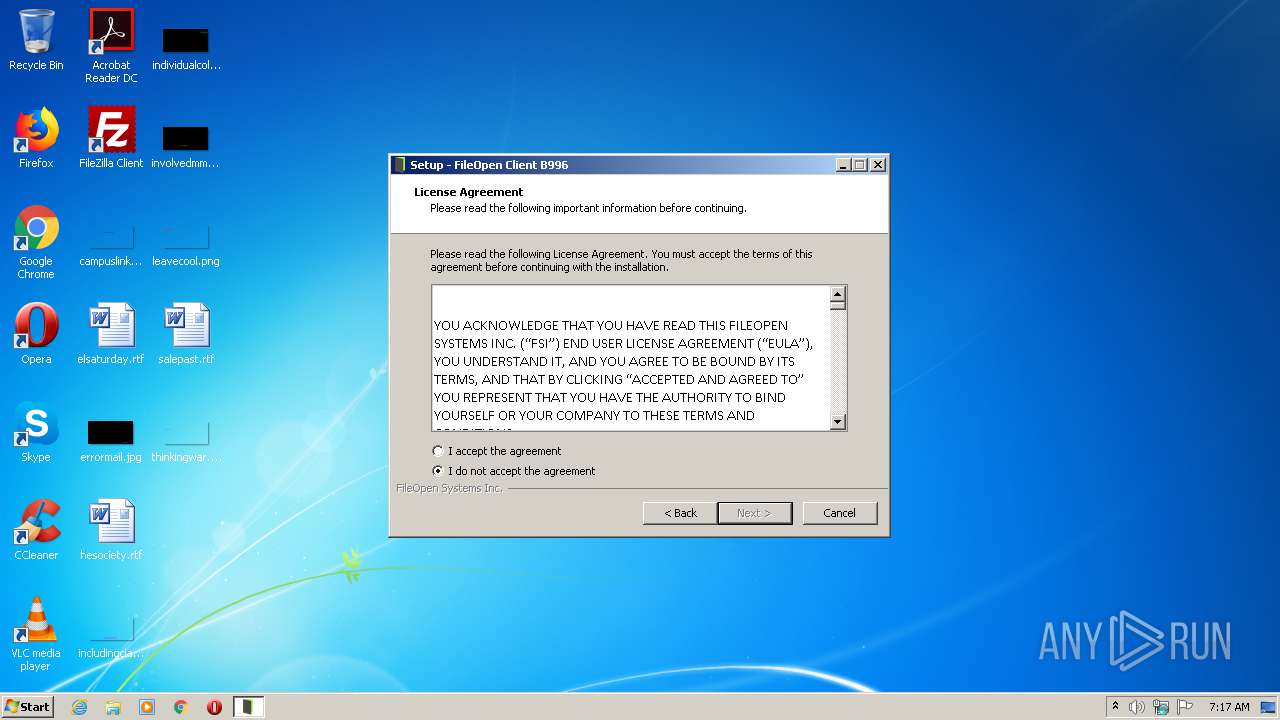
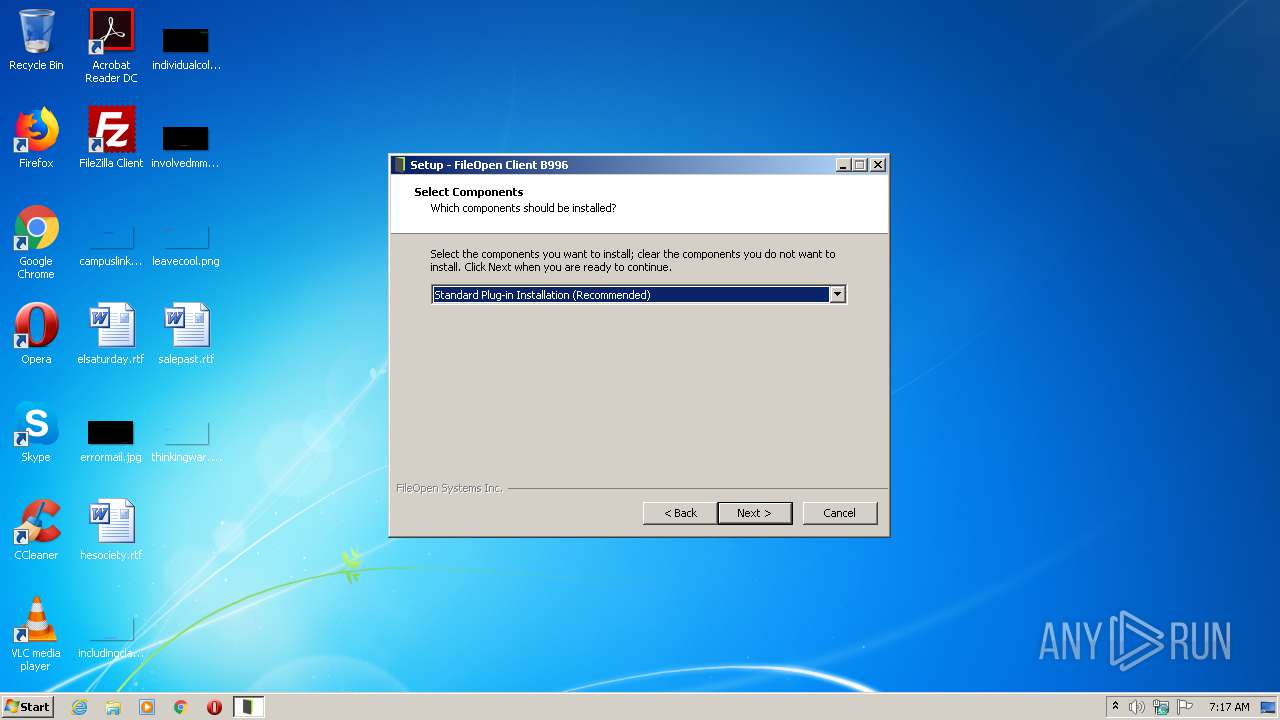
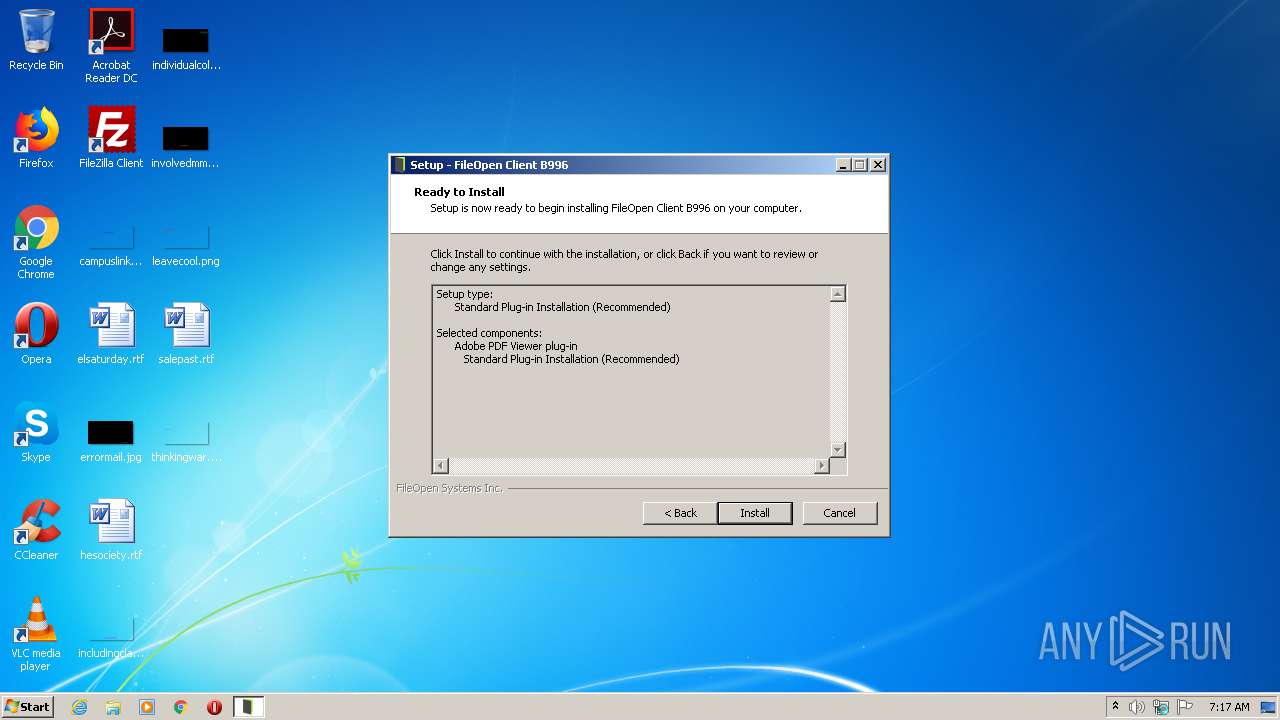
| File name: | FileOpenInstaller.exe |
| Full analysis: | https://app.any.run/tasks/4134b8c1-20be-4499-8110-e47d814f69f1 |
| Verdict: | Malicious activity |
| Analysis date: | April 20, 2021, 06:17:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AB92733EECC19BA622BEA402E36217D7 |
| SHA1: | 0B989591194ACEC8782070B4D92DB2963BFB17A0 |
| SHA256: | 1363A87825C3C707E04E181932702EB2258A9B87ADFDED21909EA58B722047E5 |
| SSDEEP: | 196608:WM8ET8NqoStGwxeNz0rv66CSO4vDMAzGP:WMfHoSRSzMyMvDFzu |
MALICIOUS
Application was dropped or rewritten from another process
- FileOpenManager32.exe (PID: 304)
- FileOpenBroker32.exe (PID: 1928)
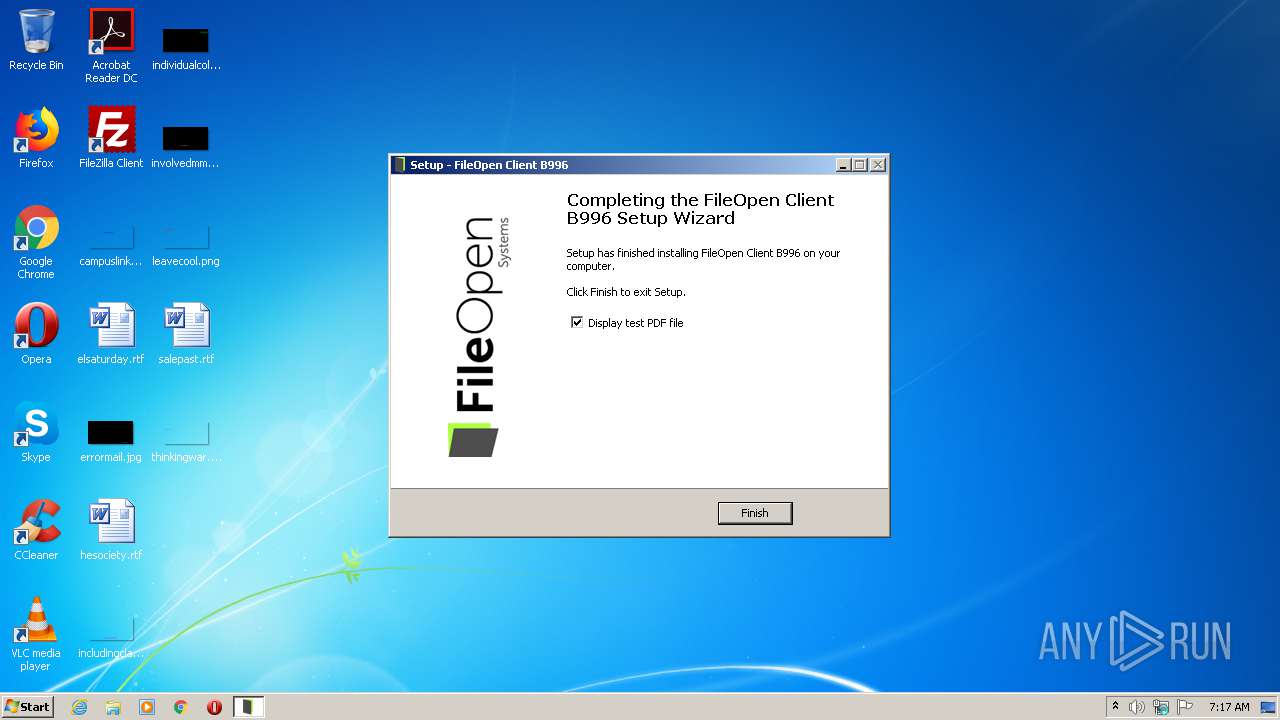
Changes the autorun value in the registry
- FileOpenInstaller.tmp (PID: 4076)
Loads dropped or rewritten executable
- AcroRd32.exe (PID: 2680)
SUSPICIOUS
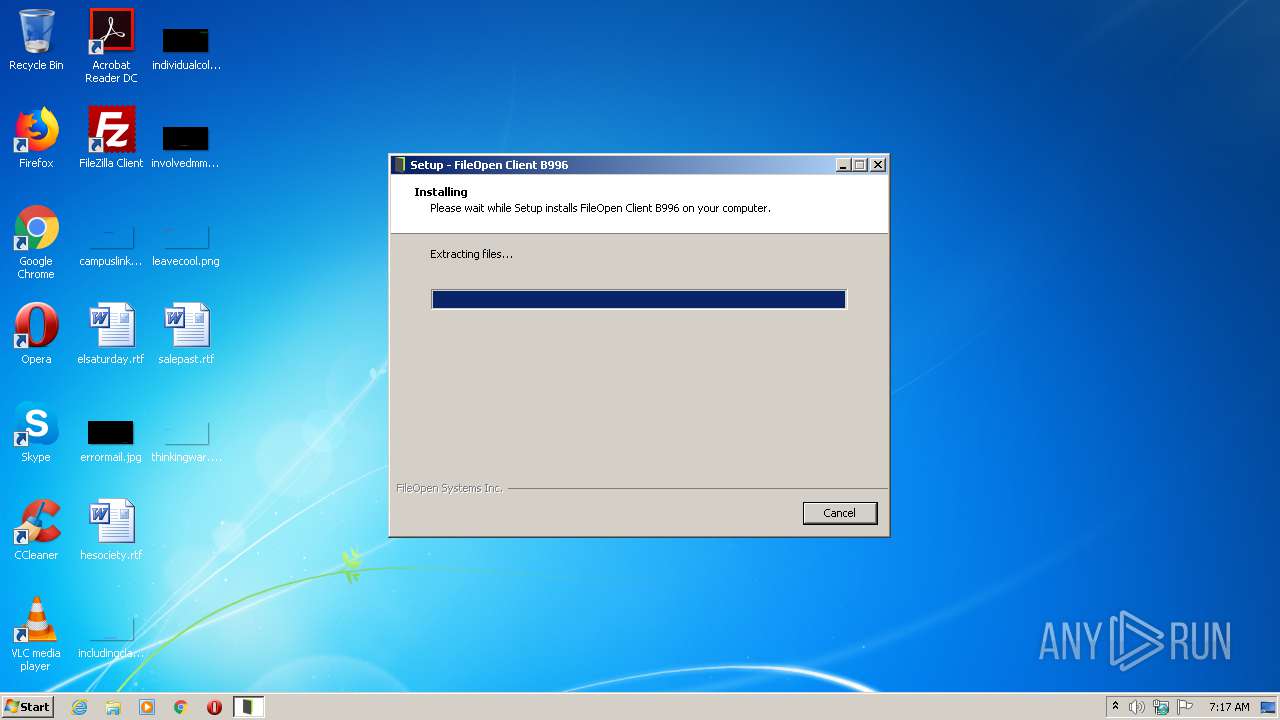
Executable content was dropped or overwritten
- FileOpenInstaller.exe (PID: 3356)
- FileOpenInstaller.exe (PID: 1872)
- FileOpenInstaller.tmp (PID: 4076)
Reads the Windows organization settings
- FileOpenInstaller.tmp (PID: 4076)
Reads Windows owner or organization settings
- FileOpenInstaller.tmp (PID: 4076)
Creates or modifies windows services
- FileOpenManager32.exe (PID: 304)
Drops a file that was compiled in debug mode
- FileOpenInstaller.tmp (PID: 4076)
Creates a directory in Program Files
- FileOpenInstaller.tmp (PID: 4076)
Drops a file with a compile date too recent
- FileOpenInstaller.tmp (PID: 4076)
Starts SC.EXE for service management
- FileOpenInstaller.tmp (PID: 4076)
Executed as Windows Service
- FileOpenManager32.exe (PID: 304)
Creates files in the user directory
- FileOpenBroker32.exe (PID: 1928)
Creates files in the program directory
- AdobeARM.exe (PID: 2724)
INFO
Application was dropped or rewritten from another process
- FileOpenInstaller.tmp (PID: 3548)
- FileOpenInstaller.tmp (PID: 4076)
Loads dropped or rewritten executable
- FileOpenInstaller.tmp (PID: 4076)
Creates files in the program directory
- FileOpenInstaller.tmp (PID: 4076)
Application launched itself
- AcroRd32.exe (PID: 3992)
- RdrCEF.exe (PID: 1852)
Creates a software uninstall entry
- FileOpenInstaller.tmp (PID: 4076)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 3992)
Reads the hosts file
- RdrCEF.exe (PID: 1852)
Reads settings of System Certificates
- AcroRd32.exe (PID: 3992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| ProductVersion: | B996 |
|---|---|
| ProductName: | {cm:FileOpenClient} B996 |
| OriginalFileName: | |
| LegalCopyright: | © 2012-2021 FileOpen Systems Inc. |
| FileVersion: | 1.0.106.996 |
| FileDescription: | {cm:FileOpenClient} B996 |
| CompanyName: | FileOpen Systems Inc. |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.106.996 |
| FileVersionNumber: | 1.0.106.996 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | 6 |
| OSVersion: | 6 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 578560 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2020:03:14 18:59:41+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Mar-2020 17:59:41 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | FileOpen Systems Inc. |
| FileDescription: | {cm:FileOpenClient} B996 |
| FileVersion: | 1.0.106.996 |
| LegalCopyright: | © 2012-2021 FileOpen Systems Inc. |
| OriginalFileName: | - |
| ProductName: | {cm:FileOpenClient} B996 |
| ProductVersion: | B996 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 14-Mar-2020 17:59:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B3604 | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35433 |
.itext | 0x000B5000 | 0x00001684 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.9709 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.04216 |
.bss | 0x000BB000 | 0x00006DA0 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x00088578 | 0x00088600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.15748 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.58114 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.60438 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.71844 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.82994 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.13144 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.3899 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.62234 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 2.39781 | 74792 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 2.59715 | 19496 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054058 |
Total processes
58
Monitored processes
16
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\FileOpen\Services\FileOpenManager32.exe" | C:\Program Files\FileOpen\Services\FileOpenManager32.exe | — | services.exe | |||||||||||
User: SYSTEM Company: FileOpen Systems Inc. Integrity Level: SYSTEM Description: FileOpen Client - Manager Service Exit code: 0 Version: 21.03.31.02 Modules
| |||||||||||||||
| 344 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1872 | "C:\Users\admin\Downloads\FileOpenInstaller.exe" | C:\Users\admin\Downloads\FileOpenInstaller.exe | explorer.exe | ||||||||||||
User: admin Company: FileOpen Systems Inc. Integrity Level: MEDIUM Description: {cm:FileOpenClient} B996 Exit code: 0 Version: 1.0.106.996 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\FileOpen\Services\FileOpenBroker32.exe" | C:\Program Files\FileOpen\Services\FileOpenBroker32.exe | FileOpenInstaller.tmp | ||||||||||||
User: admin Company: FileOpen Systems Inc. Integrity Level: MEDIUM Description: FileOpen Client - Broker Exit code: 0 Version: 21.03.31.02 Modules
| |||||||||||||||
| 2188 | "C:\Windows\system32\sc.exe" description FileOpenManager "FileOpen Client Manager" | C:\Windows\system32\sc.exe | — | FileOpenInstaller.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="1852.0.1116083544\1524624484" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2652 | "C:\Windows\system32\sc.exe" start FileOpenManager | C:\Windows\system32\sc.exe | — | FileOpenInstaller.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer installcomplete.pdf | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="1852.1.1801898378\1974666730" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
Total events
753
Read events
644
Write events
101
Delete events
8
Modification events
| (PID) Process: | (4076) FileOpenInstaller.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: EC0F00004E166DE1AC35D701 | |||
| (PID) Process: | (4076) FileOpenInstaller.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 092A7FFB3ACB83862536DAD538C0A55D4B471C970D92ACCACD13ABE9311F3E19 | |||
| (PID) Process: | (4076) FileOpenInstaller.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (4076) FileOpenInstaller.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\FileOpen\UtilDll.dll | |||
| (PID) Process: | (4076) FileOpenInstaller.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 3581A57C932D6FB7AD5D40899C7E23BDCF15A211C728CCFCF28C4D30A25C5368 | |||
| (PID) Process: | (4076) FileOpenInstaller.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | FileOpenBroker |
Value: "C:\Program Files\FileOpen\Services\FileOpenBroker32.exe" | |||
| (PID) Process: | (4076) FileOpenInstaller.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FileOpenClient_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.0.4 (u) | |||
| (PID) Process: | (4076) FileOpenInstaller.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FileOpenClient_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\FileOpen | |||
| (PID) Process: | (4076) FileOpenInstaller.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FileOpenClient_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\FileOpen\ | |||
| (PID) Process: | (4076) FileOpenInstaller.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FileOpenClient_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: FileOpen | |||
Executable files
10
Suspicious files
9
Text files
31
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4076 | FileOpenInstaller.tmp | C:\Program Files\FileOpen\is-NFSMR.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | FileOpenInstaller.tmp | C:\Program Files\FileOpen\is-R0URB.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | FileOpenInstaller.tmp | C:\Program Files\FileOpen\examples\is-GDIV4.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | FileOpenInstaller.tmp | C:\Program Files\Adobe\Acrobat Reader DC\Reader\plug_ins\is-OMEK8.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | FileOpenInstaller.tmp | C:\Program Files\FileOpen\Services\is-HTK94.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | FileOpenInstaller.tmp | C:\Program Files\FileOpen\Services\is-PR19R.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | FileOpenInstaller.tmp | C:\Program Files\FileOpen\Services\is-VDU6J.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | FileOpenInstaller.tmp | C:\Program Files\FileOpen\Services\is-QD1KN.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | FileOpenInstaller.tmp | C:\ProgramData\FileOpen\Updates\L10n\is-HHPIG.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | FileOpenInstaller.tmp | C:\ProgramData\FileOpen\Updates\L10n\is-8MQRN.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
10
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3992 | AcroRd32.exe | GET | 304 | 2.16.107.24:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
3992 | AcroRd32.exe | GET | 304 | 2.16.107.24:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
1928 | FileOpenBroker32.exe | GET | 200 | 95.101.81.65:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
3992 | AcroRd32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3992 | AcroRd32.exe | GET | 304 | 2.16.107.24:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/279_15_23_20070.zip | unknown | — | — | whitelisted |
3992 | AcroRd32.exe | GET | 304 | 2.16.107.24:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
3992 | AcroRd32.exe | GET | 200 | 2.16.107.24:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | compressed | 9.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1928 | FileOpenBroker32.exe | 64.106.211.90:443 | usr.fileopen.com | DataPipe, Inc. | US | unknown |
1928 | FileOpenBroker32.exe | 95.101.81.65:80 | crl.identrust.com | Akamai International B.V. | — | unknown |
1928 | FileOpenBroker32.exe | 64.106.211.88:443 | plugin.fileopen.com | DataPipe, Inc. | US | unknown |
— | — | 104.76.200.137:443 | ardownload2.adobe.com | Telia Company AB | NL | suspicious |
— | — | 104.79.88.64:443 | armmf.adobe.com | Time Warner Cable Internet LLC | US | suspicious |
3992 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3992 | AcroRd32.exe | 2.16.107.24:80 | acroipm2.adobe.com | Akamai International B.V. | — | malicious |
3992 | AcroRd32.exe | 2.20.40.129:443 | armmf.adobe.com | Akamai International B.V. | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
usr.fileopen.com |
| unknown |
crl.identrust.com |
| whitelisted |
plugin.fileopen.com |
| suspicious |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |