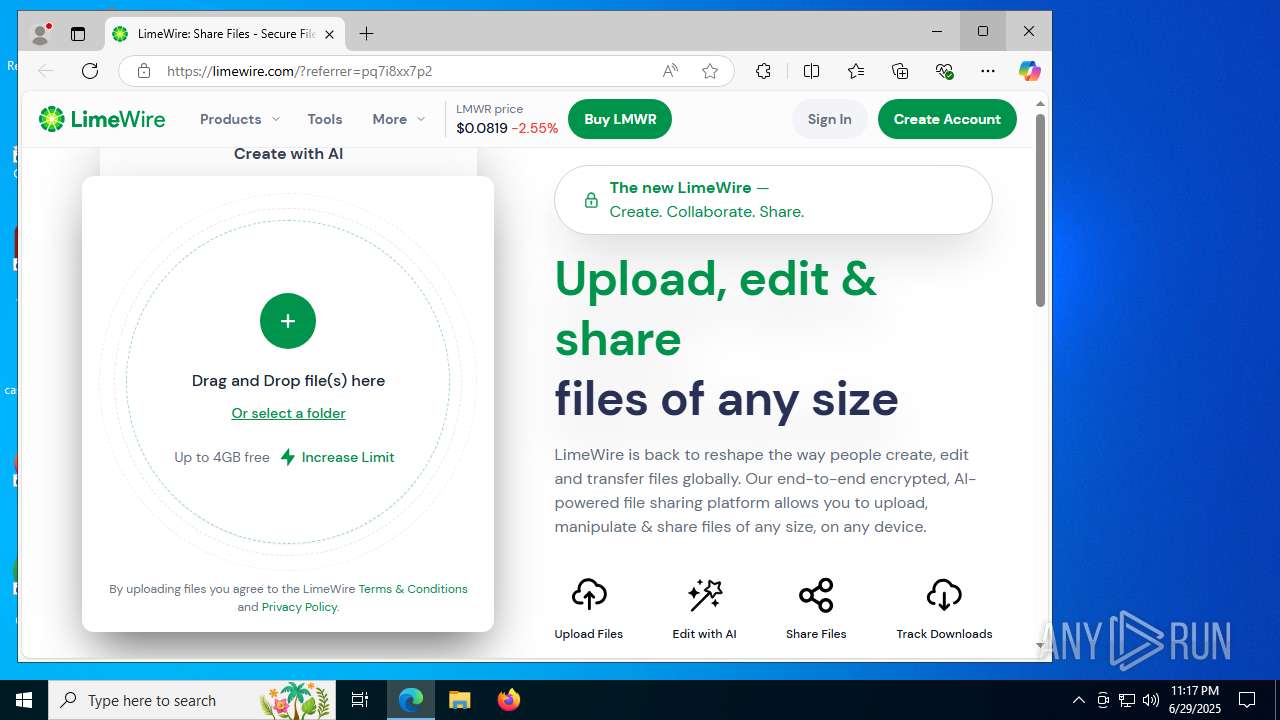
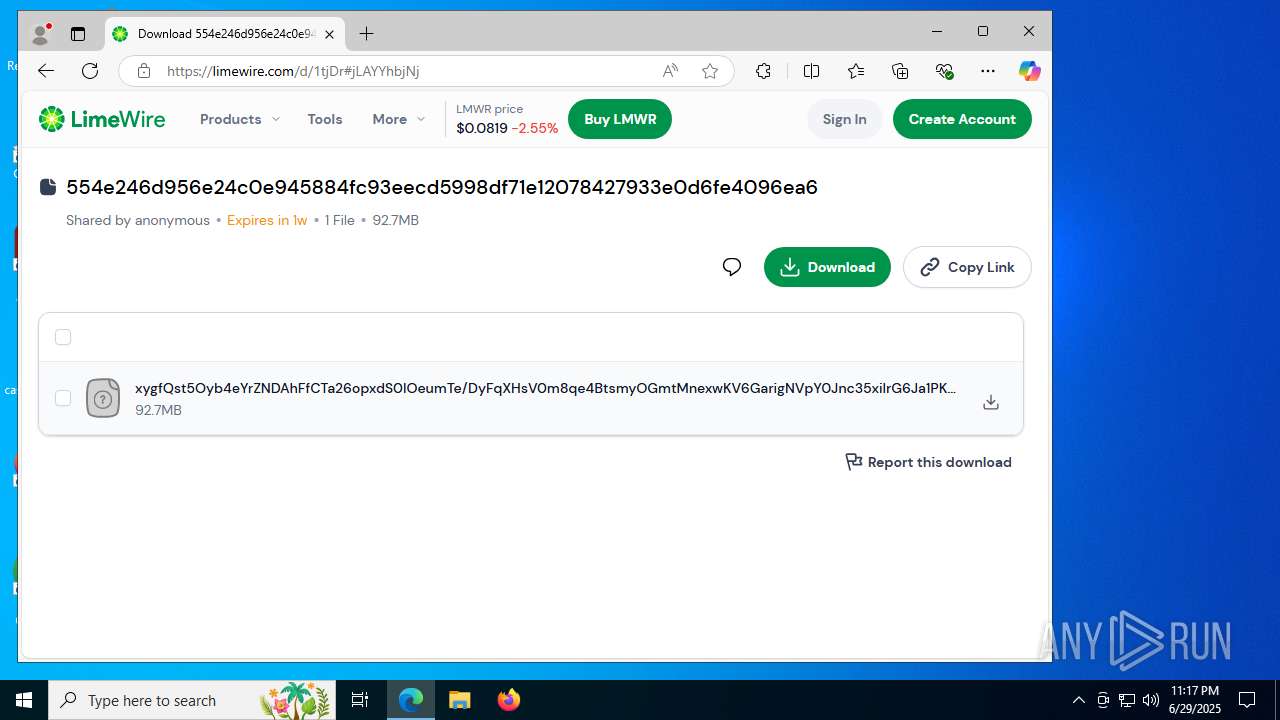
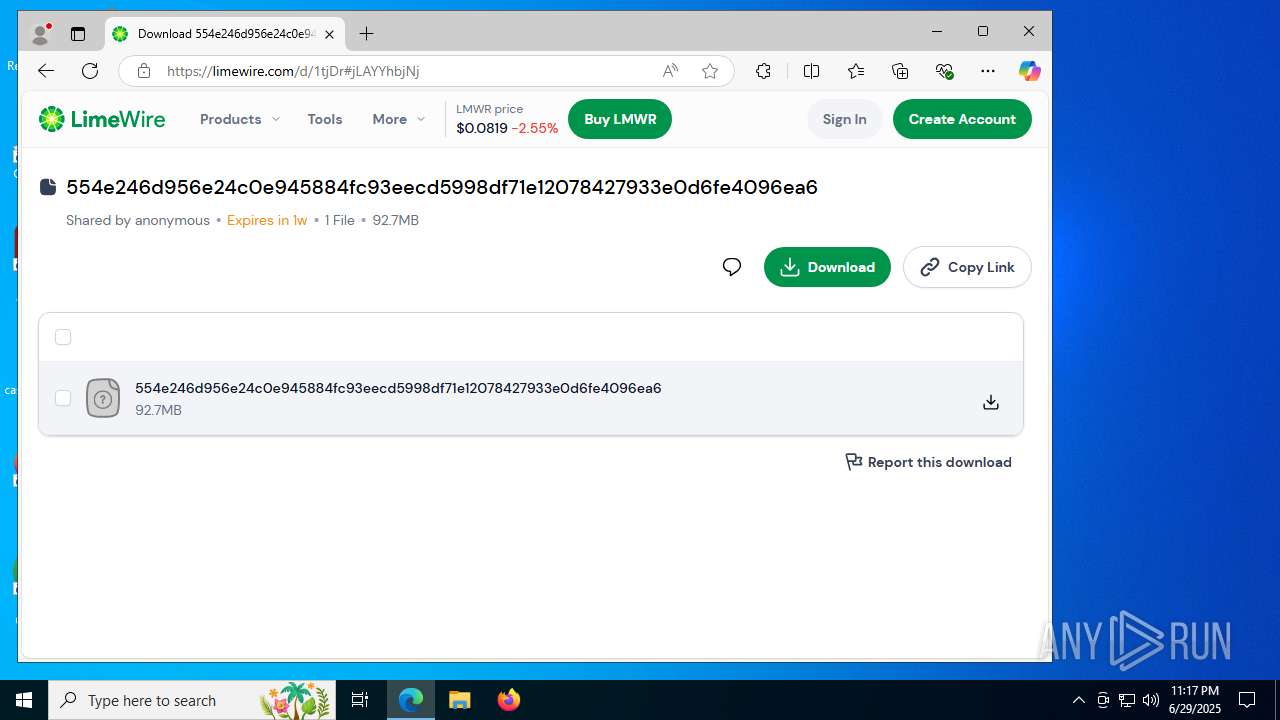
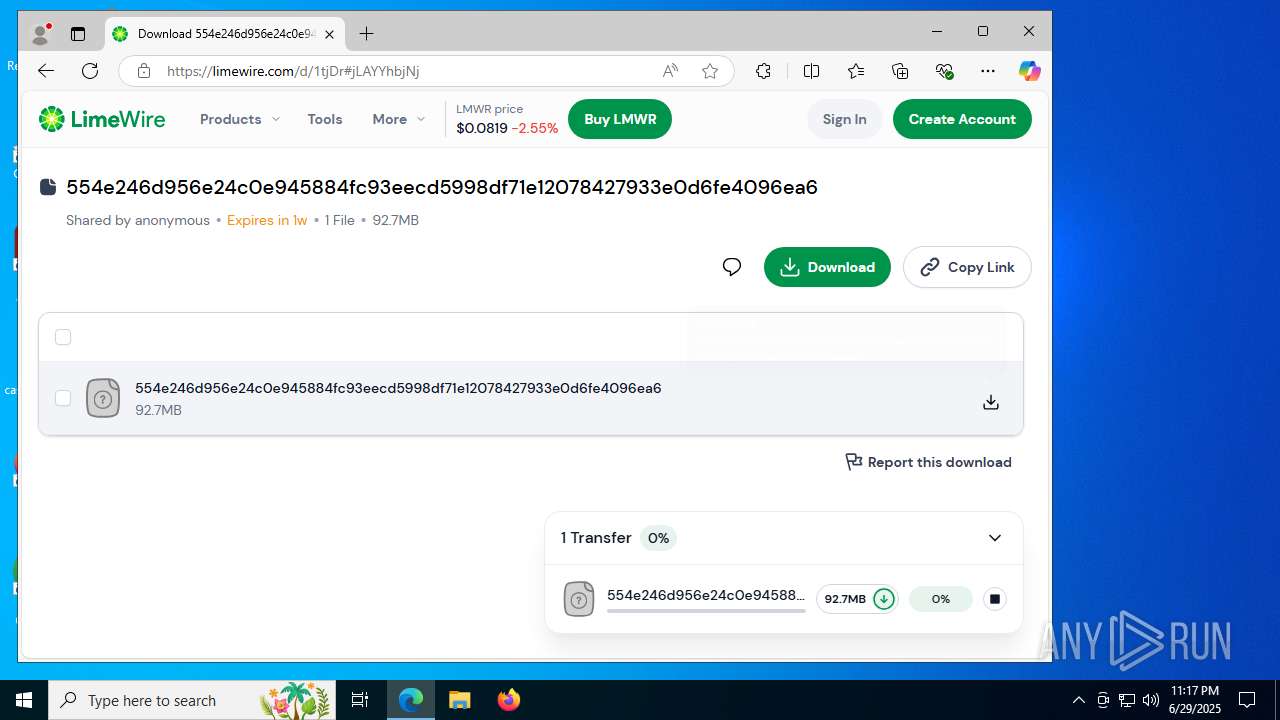
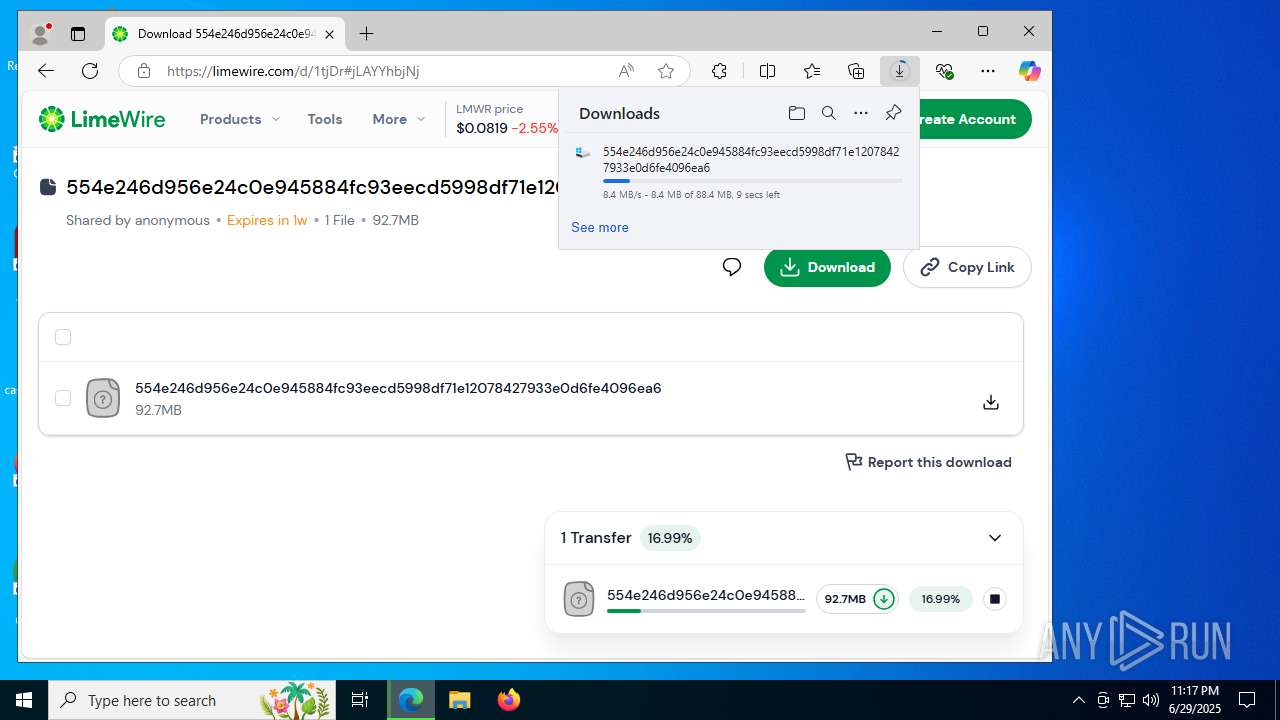
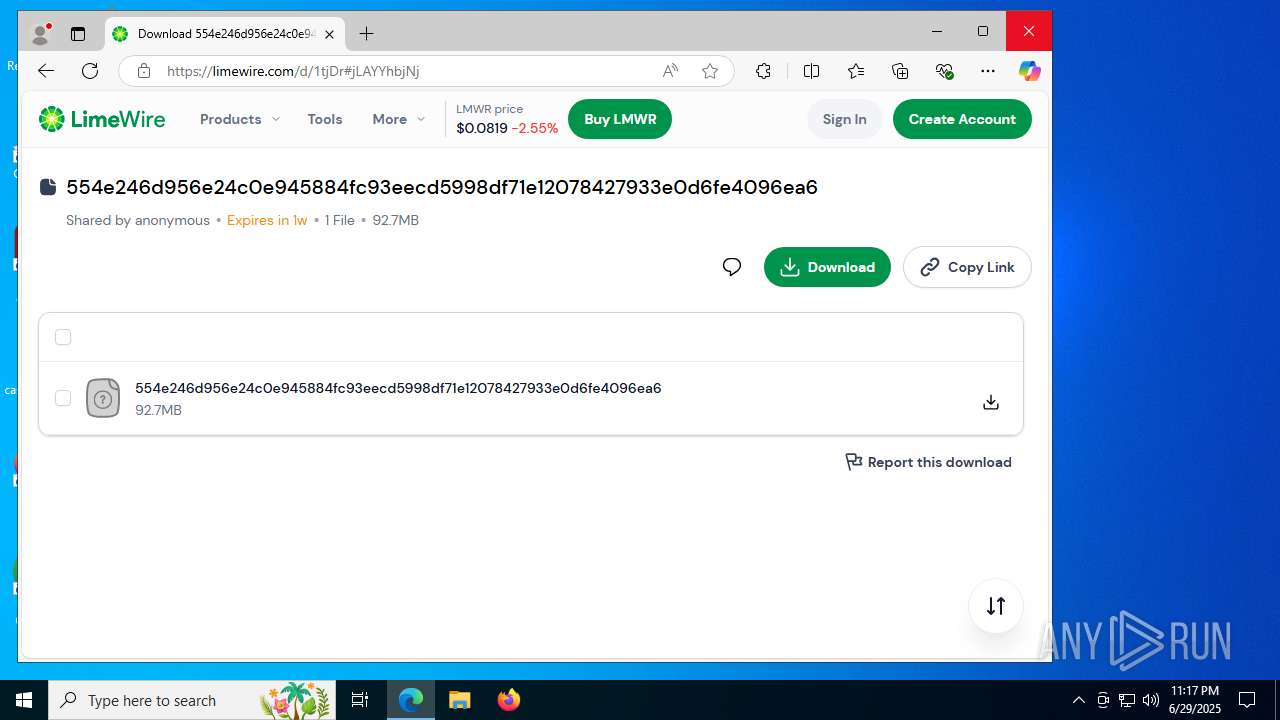
| URL: | https://limewire.com/?referrer=pq7i8xx7p2 |
| Full analysis: | https://app.any.run/tasks/e09d5261-b555-4288-a0b5-7240a760dbb8 |
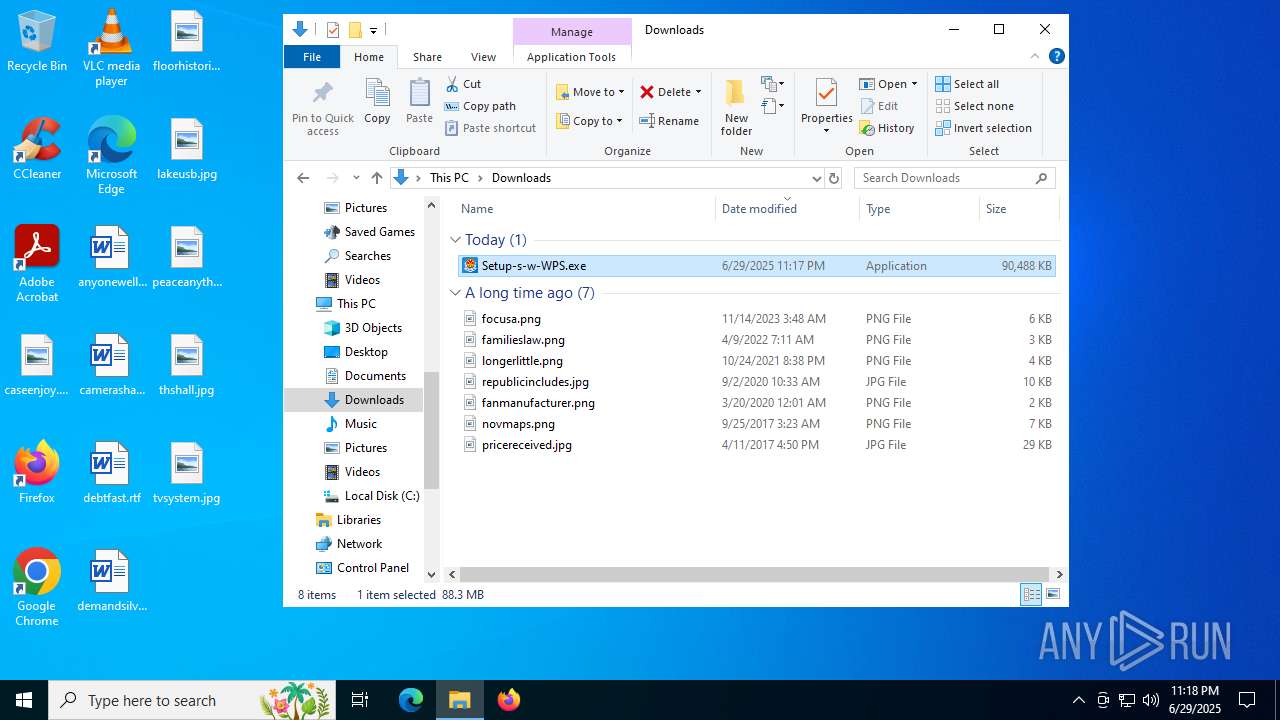
| Verdict: | Malicious activity |
| Analysis date: | June 29, 2025, 23:16:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5653FFC77705BD936262135DD6855EA2 |
| SHA1: | 6470FC89D62E564481474027785C82167E6C5388 |
| SHA256: | 135739014C0A232BBD83681384708953EEB5305BE05B9CC0B1473CFCD80EEAB4 |
| SSDEEP: | 3:N8MIA/eXgynSVX:2MIA/eXtg |
MALICIOUS
Starts NET.EXE for service management
- NSecRTS.exe (PID: 1936)
- net.exe (PID: 4880)
- net.exe (PID: 1132)
- net.exe (PID: 4888)
- net.exe (PID: 4120)
Creates or modifies Windows services
- NSecRTS.exe (PID: 1936)
Registers / Runs the DLL via REGSVR32.EXE
- NSecRTS.exe (PID: 1936)
Changes the autorun value in the registry
- rundll32.exe (PID: 2148)
SUSPICIOUS
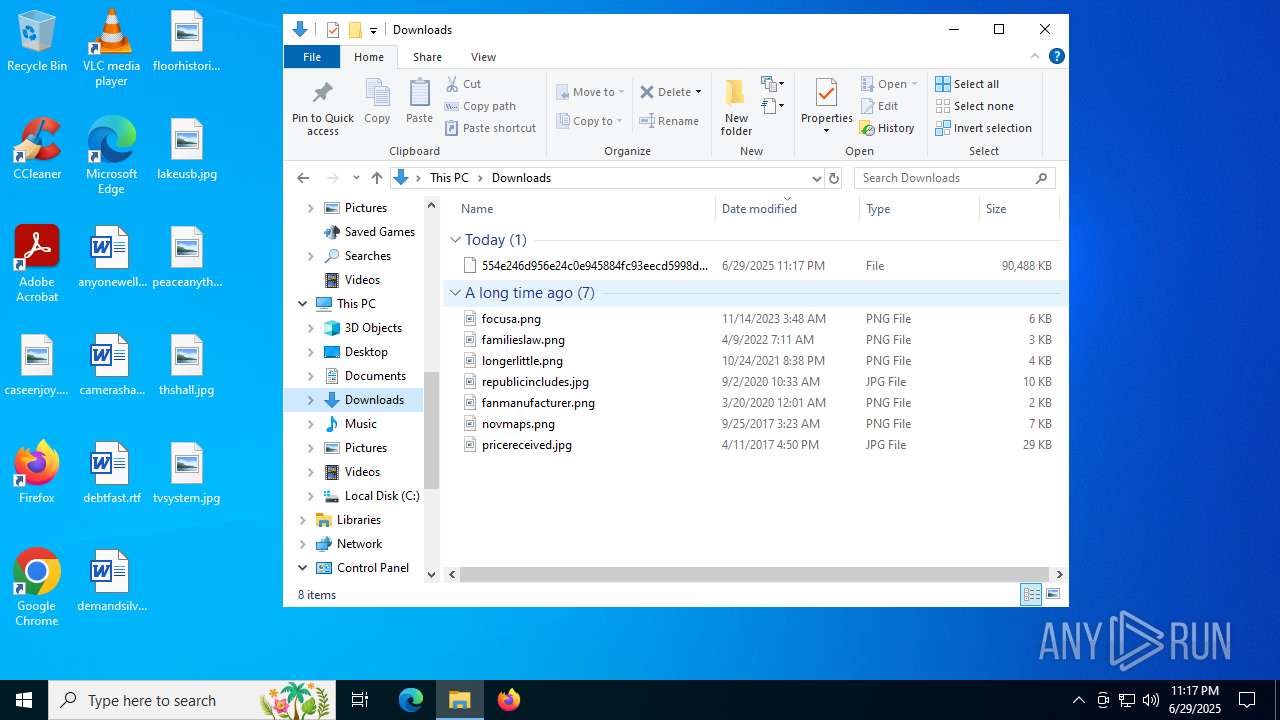
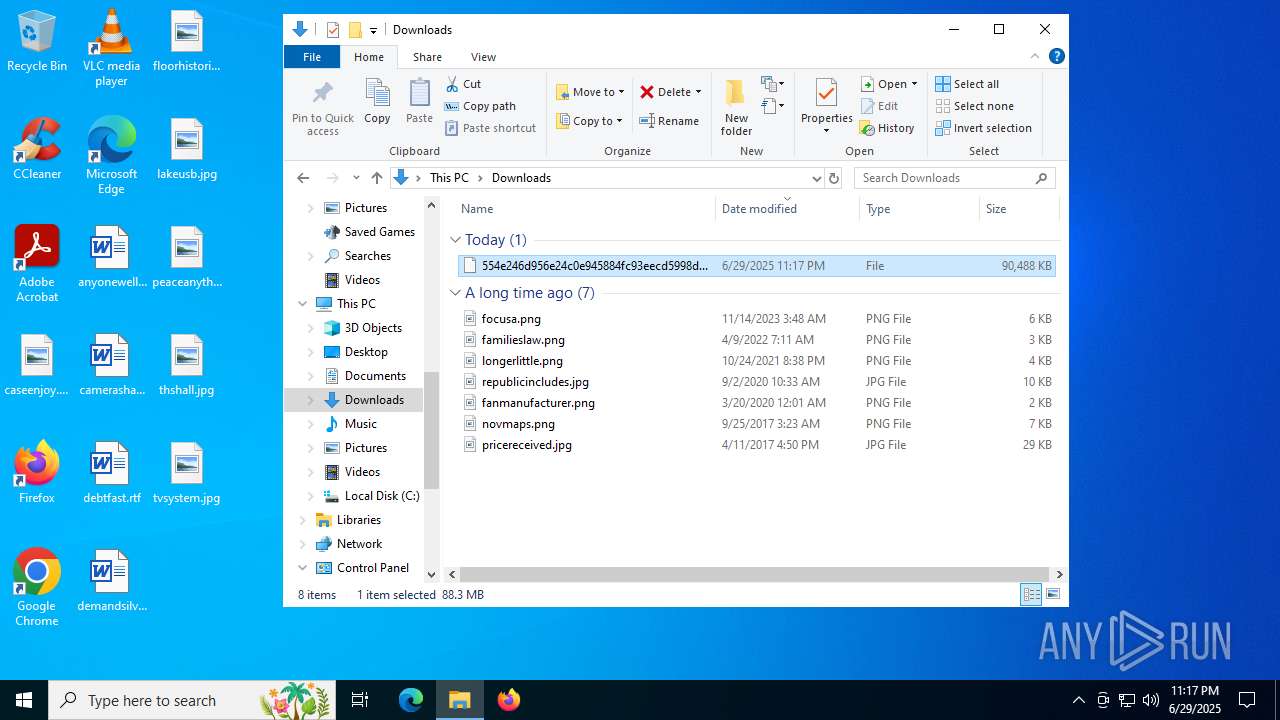
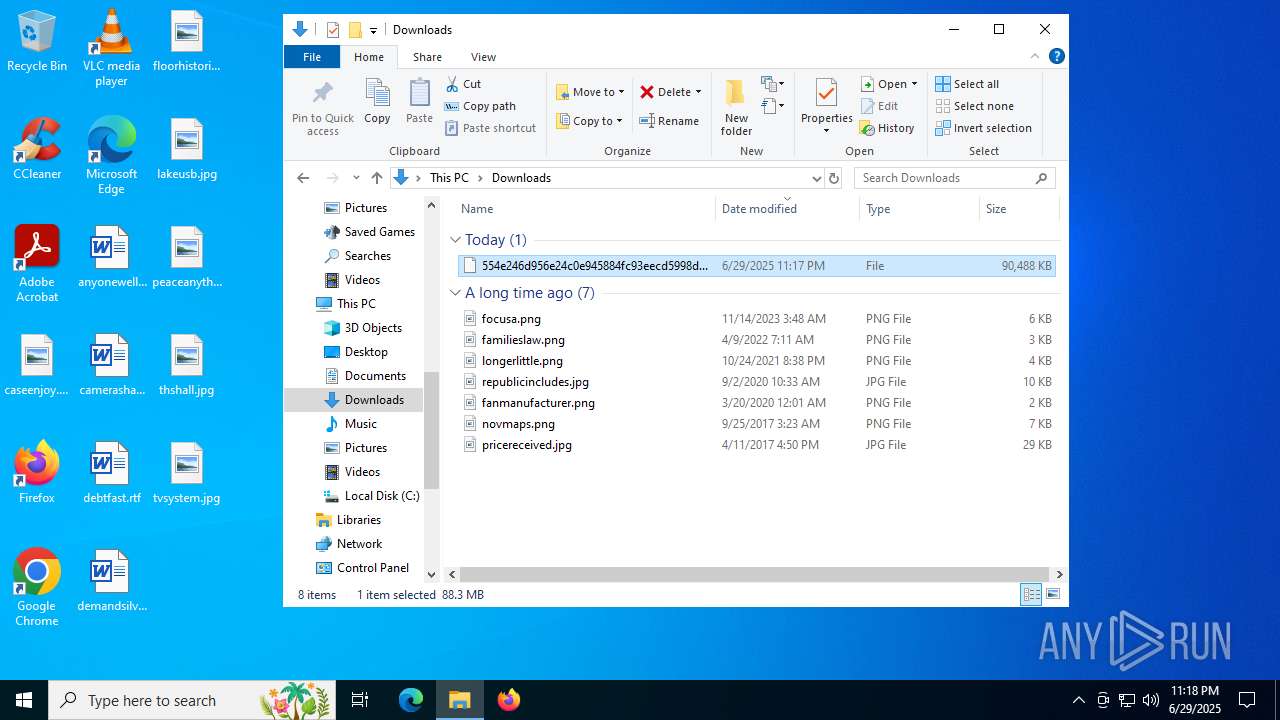
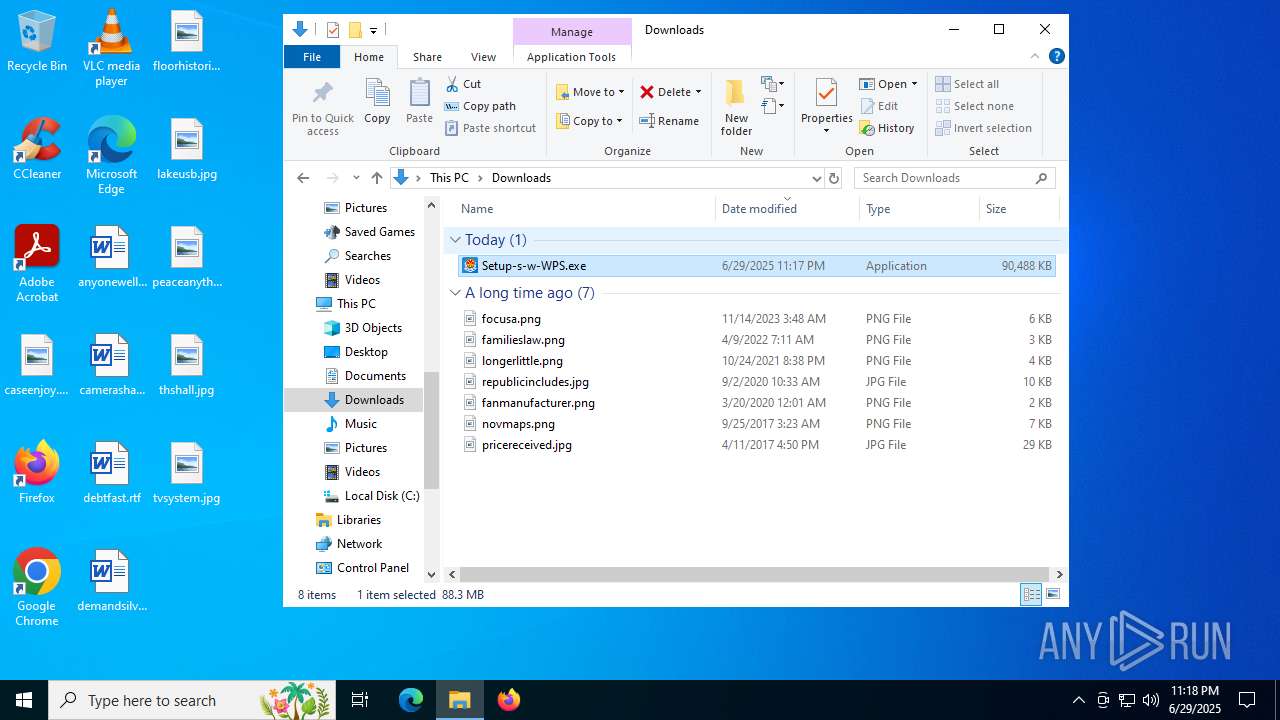
Executable content was dropped or overwritten
- Setup-s-w-WPS.exe (PID: 7836)
- Setup-s-w-WPS.tmp (PID: 8036)
- Setup-s-w-WPS.exe (PID: 864)
- rundll32.exe (PID: 2148)
- drvinst.exe (PID: 5684)
- NSecRTS.exe (PID: 1936)
Drops 7-zip archiver for unpacking
- Setup-s-w-WPS.tmp (PID: 8036)
Reads security settings of Internet Explorer
- Setup-s-w-WPS.tmp (PID: 4112)
Reads the Windows owner or organization settings
- Setup-s-w-WPS.tmp (PID: 8036)
The process drops C-runtime libraries
- Setup-s-w-WPS.tmp (PID: 8036)
Process drops legitimate windows executable
- Setup-s-w-WPS.tmp (PID: 8036)
Drops a system driver (possible attempt to evade defenses)
- Setup-s-w-WPS.tmp (PID: 8036)
- rundll32.exe (PID: 2148)
- drvinst.exe (PID: 5684)
Process drops SQLite DLL files
- Setup-s-w-WPS.tmp (PID: 8036)
Application launched itself
- NSecRTS.exe (PID: 1936)
Creates or modifies Windows services
- NSecDs.exe (PID: 6820)
- drvinst.exe (PID: 7720)
Executes as Windows Service
- NSecDs.exe (PID: 7724)
- NSecRTS.exe (PID: 1936)
The process checks if it is being run in the virtual environment
- NSecRTS.exe (PID: 1440)
- NSecRTS.exe (PID: 1936)
Connects to unusual port
- NSecRTS.exe (PID: 1440)
- NSecRTS.exe (PID: 1936)
- NSecRTS.exe (PID: 6756)
Windows service management via SC.EXE
- sc.exe (PID: 5628)
Uses RUNDLL32.EXE to load library
- NSecRTS.exe (PID: 7668)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 7044)
- regsvr32.exe (PID: 7736)
Creates files in the driver directory
- drvinst.exe (PID: 5684)
Starts POWERSHELL.EXE for commands execution
- NSecRTS.exe (PID: 1440)
Reads the date of Windows installation
- NSecRTS.exe (PID: 1936)
Searches for installed software
- NSecRTS.exe (PID: 1936)
INFO
Checks supported languages
- identity_helper.exe (PID: 7608)
- identity_helper.exe (PID: 7604)
- Setup-s-w-WPS.exe (PID: 7836)
- Setup-s-w-WPS.tmp (PID: 4112)
- Setup-s-w-WPS.tmp (PID: 8036)
- Doubleing.exe (PID: 4080)
- Setup-s-w-WPS.exe (PID: 864)
- NSec.exe (PID: 5920)
- instrap.exe (PID: 7508)
- NSecRTS.exe (PID: 7236)
- setup_Ir5swe5ApecDUxXBUQuvwQ5N==.exe (PID: 1688)
- Fixit.exe (PID: 7204)
- NSecDs.exe (PID: 6820)
- NSecRTS.exe (PID: 1936)
- NSecRTS.exe (PID: 1440)
- NSecDs.exe (PID: 7724)
- Fixit.exe (PID: 8016)
- NSecRTS.exe (PID: 7668)
- drvinst.exe (PID: 5684)
- drvinst.exe (PID: 7720)
- NSecRTS.exe (PID: 6756)
Application launched itself
- msedge.exe (PID: 2708)
- msedge.exe (PID: 5616)
Reads the computer name
- identity_helper.exe (PID: 7608)
- identity_helper.exe (PID: 7604)
- Setup-s-w-WPS.tmp (PID: 8036)
- Doubleing.exe (PID: 4080)
- Setup-s-w-WPS.tmp (PID: 4112)
- Setup-s-w-WPS.exe (PID: 864)
- NSecRTS.exe (PID: 7236)
- NSecRTS.exe (PID: 1936)
- NSecDs.exe (PID: 6820)
- NSecRTS.exe (PID: 1440)
- NSecDs.exe (PID: 7724)
- NSecRTS.exe (PID: 7668)
- drvinst.exe (PID: 5684)
- drvinst.exe (PID: 7720)
- NSecRTS.exe (PID: 6756)
Reads Environment values
- identity_helper.exe (PID: 7608)
- identity_helper.exe (PID: 7604)
Executable content was dropped or overwritten
- msedge.exe (PID: 2708)
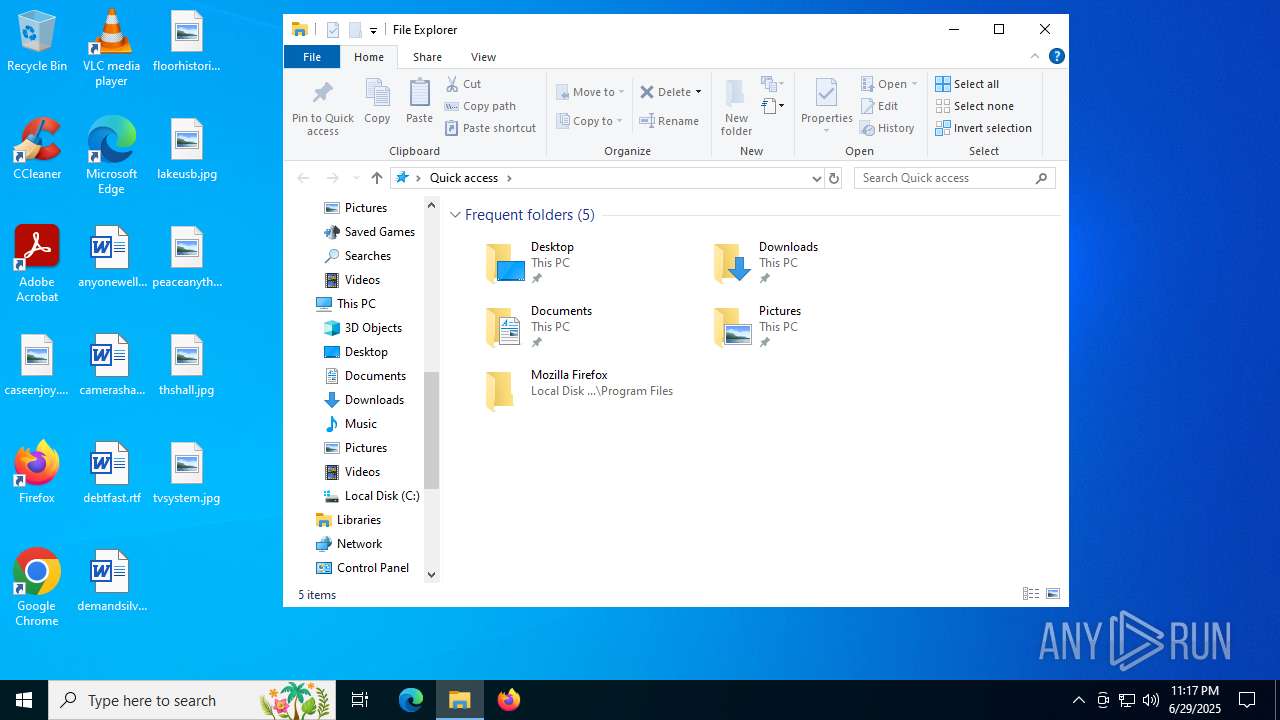
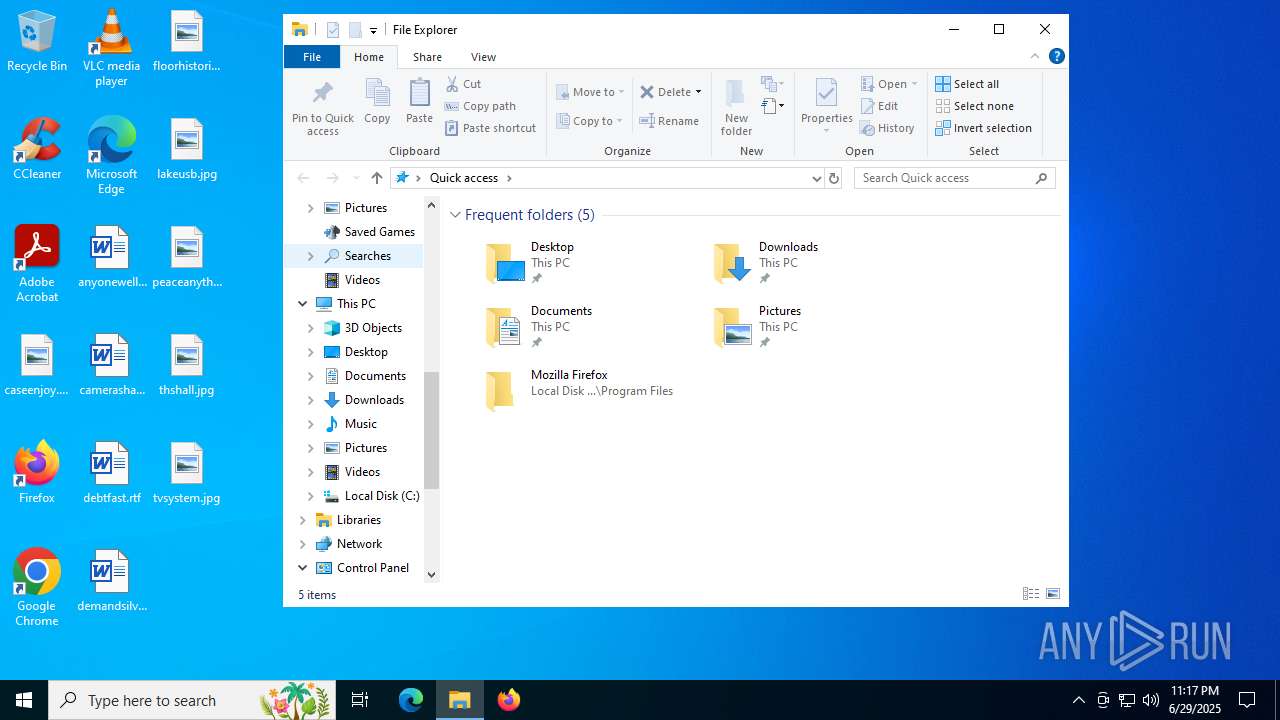
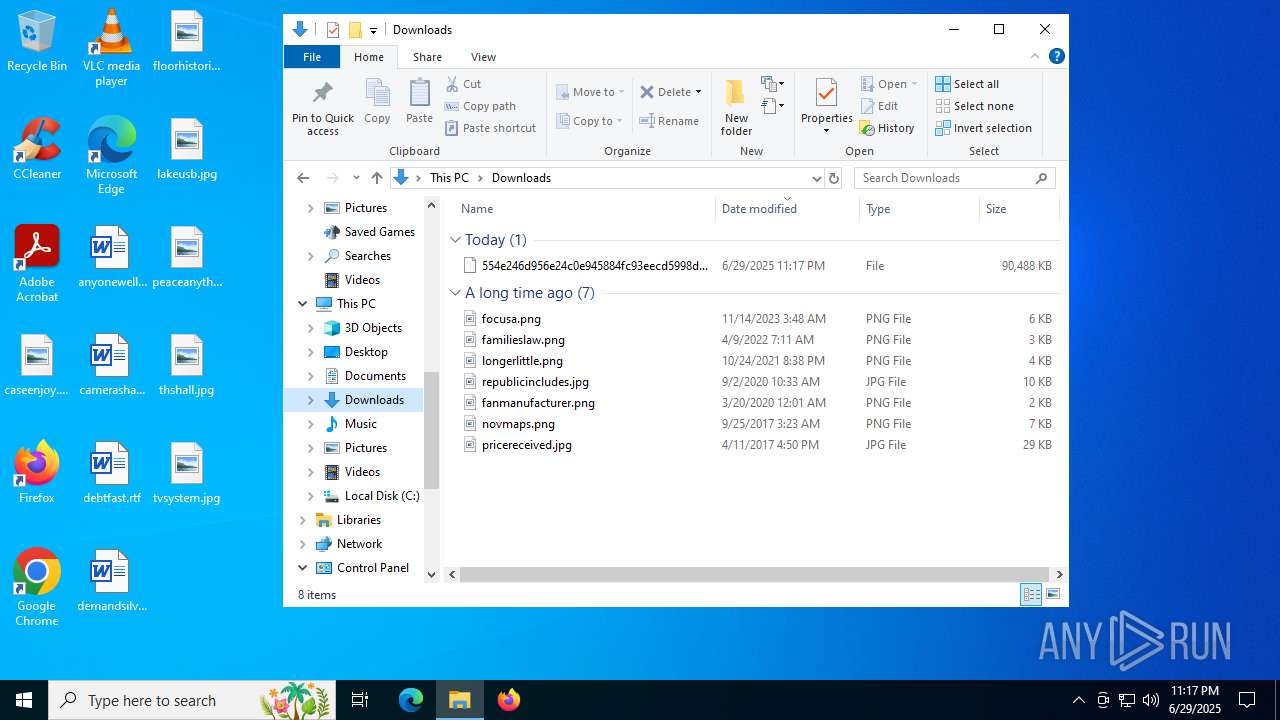
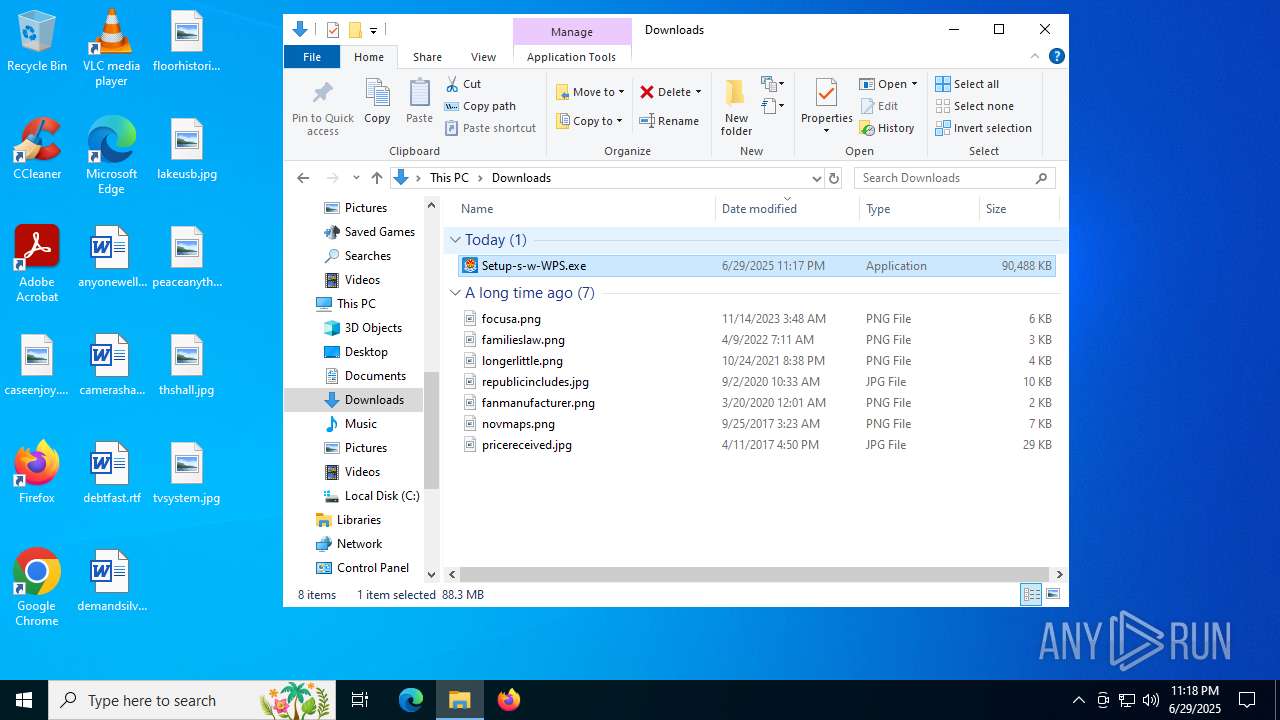
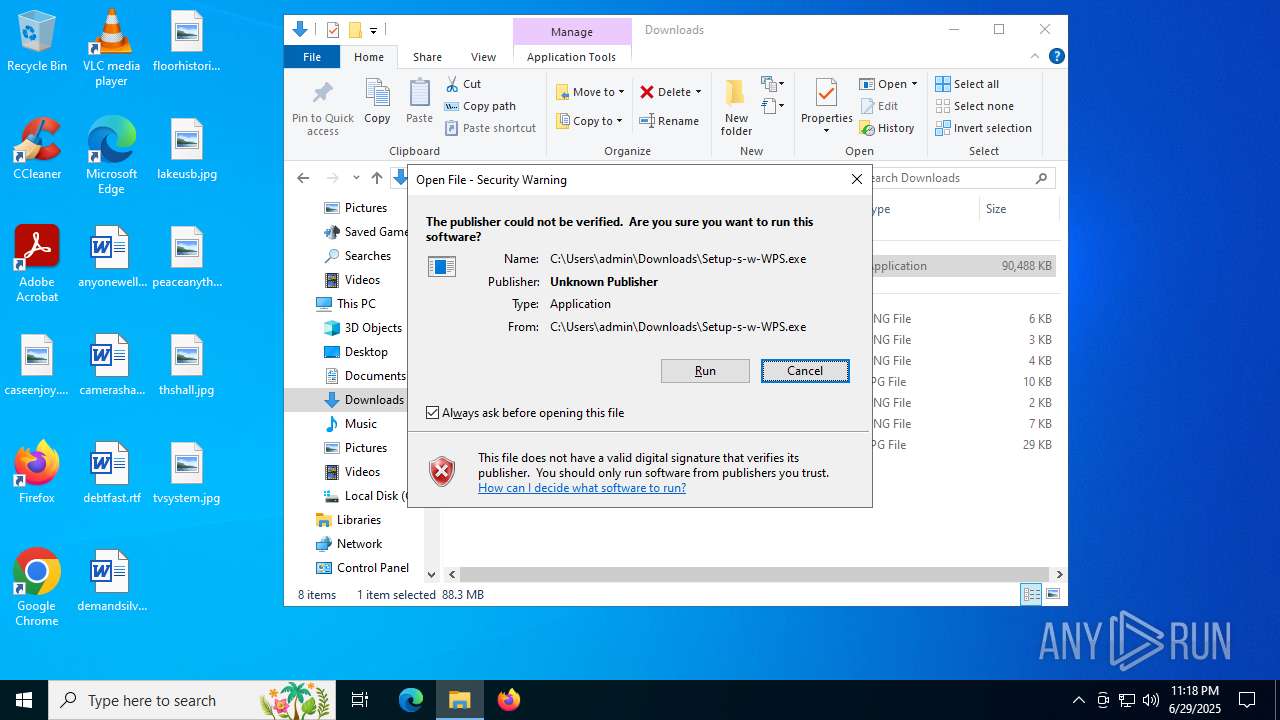
Manual execution by a user
- Setup-s-w-WPS.exe (PID: 7836)
Create files in a temporary directory
- Setup-s-w-WPS.exe (PID: 7836)
- Doubleing.exe (PID: 4080)
- Setup-s-w-WPS.tmp (PID: 8036)
- Setup-s-w-WPS.exe (PID: 864)
The sample compiled with chinese language support
- Setup-s-w-WPS.tmp (PID: 8036)
- NSecRTS.exe (PID: 1936)
Creates files in the program directory
- Setup-s-w-WPS.tmp (PID: 8036)
- NSecRTS.exe (PID: 1440)
- NSecRTS.exe (PID: 7236)
- NSecRTS.exe (PID: 1936)
The sample compiled with english language support
- Setup-s-w-WPS.tmp (PID: 8036)
- rundll32.exe (PID: 2148)
- drvinst.exe (PID: 5684)
Process checks computer location settings
- Setup-s-w-WPS.tmp (PID: 4112)
Compiled with Borland Delphi (YARA)
- Setup-s-w-WPS.exe (PID: 7836)
- Setup-s-w-WPS.tmp (PID: 4112)
- Setup-s-w-WPS.tmp (PID: 8036)
- Setup-s-w-WPS.exe (PID: 864)
Detects InnoSetup installer (YARA)
- Setup-s-w-WPS.tmp (PID: 4112)
- Setup-s-w-WPS.exe (PID: 864)
- Setup-s-w-WPS.tmp (PID: 8036)
- Setup-s-w-WPS.exe (PID: 7836)
Checks proxy server information
- slui.exe (PID: 7656)
Reads the software policy settings
- slui.exe (PID: 7656)
- drvinst.exe (PID: 5684)
Creates a software uninstall entry
- Setup-s-w-WPS.tmp (PID: 8036)
Process checks whether UAC notifications are on
- NSecRTS.exe (PID: 1440)
- NSecRTS.exe (PID: 6756)
Reads Microsoft Office registry keys
- NSecRTS.exe (PID: 1936)
- NSecRTS.exe (PID: 1440)
Reads the machine GUID from the registry
- drvinst.exe (PID: 5684)
Reads security settings of Internet Explorer
- runonce.exe (PID: 4520)
Launching a file from a Registry key
- rundll32.exe (PID: 2148)
Reads CPU info
- NSecRTS.exe (PID: 1936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
248
Monitored processes
90
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x298,0x29c,0x2a0,0x290,0x2a8,0x7ffc4396f208,0x7ffc4396f214,0x7ffc4396f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 768 | C:\WINDOWS\system32\regsvr32.exe /s "C:\Program Files (x86)\Microsoft Research\NSEC\NShellExt64.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | NSecRTS.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3632,i,2233887623028099750,4604519838992255459,262144 --variations-seed-version --mojo-platform-channel-handle=3648 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 864 | "C:\Users\admin\Downloads\Setup-s-w-WPS.exe" /SPAWNWND=$90244 /NOTIFYWND=$A0346 | C:\Users\admin\Downloads\Setup-s-w-WPS.exe | Setup-s-w-WPS.tmp | ||||||||||||
User: admin Company: Treeholdings Integrity Level: HIGH Description: Treeholdings Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1132 | net stop mswtd | C:\Windows\SysWOW64\net.exe | — | NSecRTS.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4700,i,11719291610210722220,10766711848291529759,262144 --variations-seed-version --mojo-platform-channel-handle=5220 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1440 | "C:\Program Files (x86)\Common Files\NSEC\NSecRTS.exe" -elevated | C:\Program Files (x86)\Common Files\NSEC\NSecRTS.exe | NSecRTS.exe | ||||||||||||
User: admin Company: XOR Co.,Ltd Integrity Level: HIGH Description: Endpoint Protection & DLP Real-time Service Version: 3.7.86.17889 Modules
| |||||||||||||||
| 1484 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1636 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
29 380
Read events
28 899
Write events
472
Delete events
9
Modification events
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 732A666354972F00 | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328442 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DDA73AEF-F630-4781-B21F-A72CD0A2E58E} | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328442 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {81F173B3-94C5-4135-B675-D37FF1610683} | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328442 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9608389C-6083-4221-B413-2EF8DDAFE8E2} | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328442 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {ABD01082-3FA9-4232-A2E0-0F9C866C5D43} | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328442 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8BFA30DF-D0CC-4979-A090-5B58BC23412E} | |||
Executable files
1 010
Suspicious files
601
Text files
246
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175a64.TMP | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175a74.TMP | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF175a84.TMP | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175ab2.TMP | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF175ab2.TMP | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175ab2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
193
DNS requests
102
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4156 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:uT3Ute_C9ZzqcnZkVKkm4Ta5zB1vfLUjCsY_gVsjzVg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 104.85.1.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5896 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3584 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3584 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1948 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751724307&P2=404&P3=2&P4=XTi0ZT%2bgVv%2fG8Z1bEQ6G9P6HEI25dnDq0q1j%2bxOnd1coKflujPRtjrIYSCwklZzTrjJwoLqNG8lt61U2Yb8mbg%3d%3d | unknown | — | — | whitelisted |
1948 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751724307&P2=404&P3=2&P4=XTi0ZT%2bgVv%2fG8Z1bEQ6G9P6HEI25dnDq0q1j%2bxOnd1coKflujPRtjrIYSCwklZzTrjJwoLqNG8lt61U2Yb8mbg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4040 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4156 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4156 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4156 | msedge.exe | 104.22.37.240:443 | limewire.com | CLOUDFLARENET | — | unknown |
4156 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4156 | msedge.exe | 2.19.195.104:443 | copilot.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
limewire.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
js.stripe.com |
| whitelisted |
api.limewire.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
4156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
4156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
4156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
4156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
1936 | NSecRTS.exe | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |
Process | Message |
|---|---|
NSecRTS.exe | [23:19:38][PID:7236 TID:2464][Level:Info]NSecRTS!ParentPID:7508, ParentPath:.
|
NSecRTS.exe | [23:19:38][PID:7236 TID:2464][Level:Info]--------------------------Image:C:\Program Files (x86)\Common Files\NSEC\NSecRTS.exe Commandline:-i Version:3.7.86.17889--------------------------
|
NSecRTS.exe | [23:19:38][PID:1936 TID:3908][Level:Info]NSecRTS!ParentPID:744, ParentPath:C:\Windows\System32\services.exe.
|
NSecRTS.exe | [23:19:38][PID:1936 TID:5400][Level:Info]NSecRTS!UpdateService!UpdateThread 5400 will check and update after 681 sec
|
NSecRTS.exe | [23:19:38][PID:1936 TID:3908][Level:Info]--------------------------Image:C:\Program Files (x86)\Common Files\NSEC\NSecRTS.exe Commandline:-r Version:3.7.86.17889--------------------------
|
NSecRTS.exe | [23:19:38][PID:1936 TID:7252][Level:Info]NSecRTS!Service!Start NSEC service...
|
NSecRTS.exe | [23:19:38][PID:1936 TID:6228][Level:Info]NSecRTS!Update!Wait for fixit exit.
|
NSecRTS.exe | [23:19:38][PID:1936 TID:6228][Level:Info]NSecRTS!Update!Fixit has exited.
|
NSecRTS.exe | [23:19:39][PID:1936 TID:8100][Level:Info]NPFSvc!ProcessNotifyServiceThread ID:8100
|
NSecRTS.exe | [23:19:39][PID:1936 TID:6228][Level:Info]ModuleFix!CreateAgentProcessAsUser session:1 pid:1440.
|