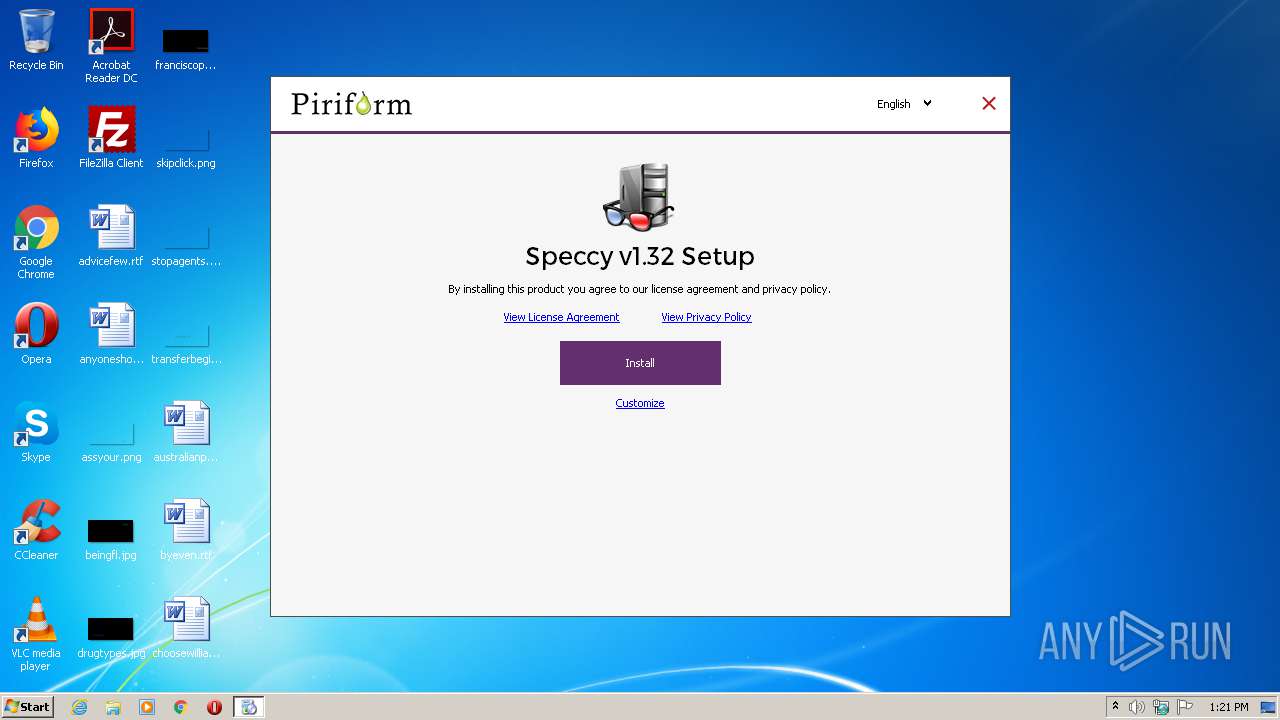
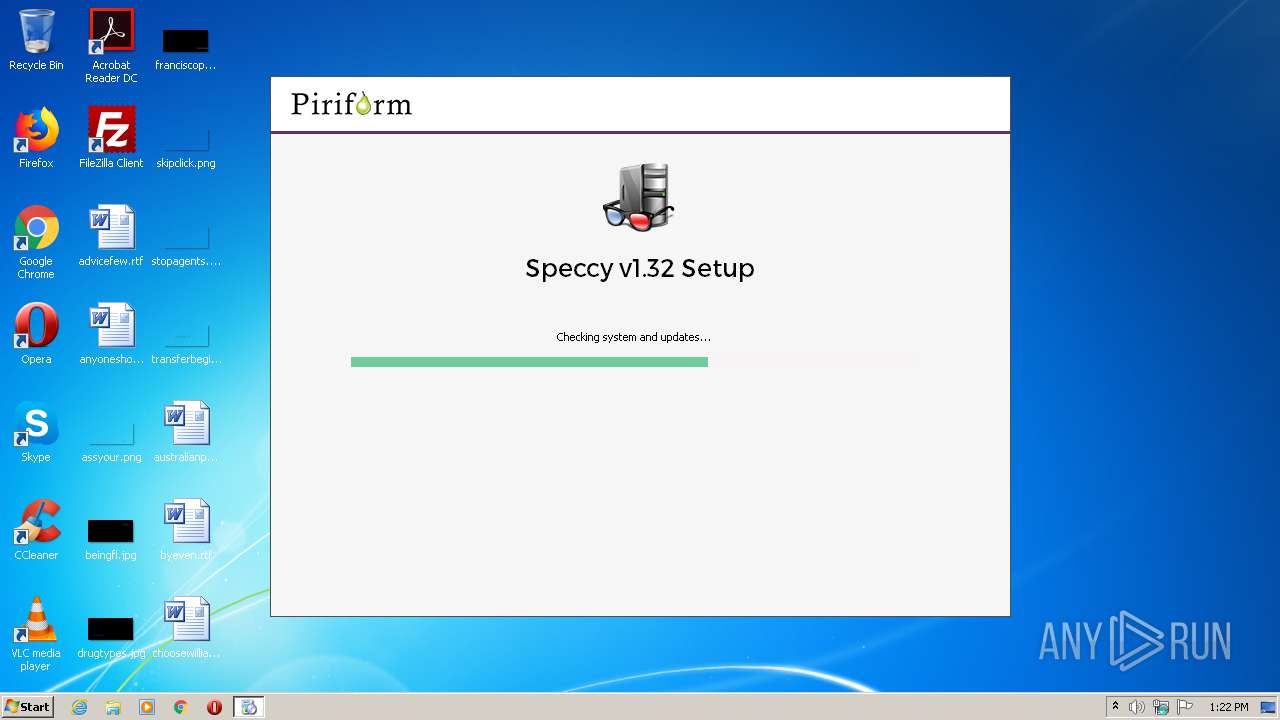
| File name: | spsetup132.exe |
| Full analysis: | https://app.any.run/tasks/2444444f-4e2e-4292-807e-ea5e244c6332 |
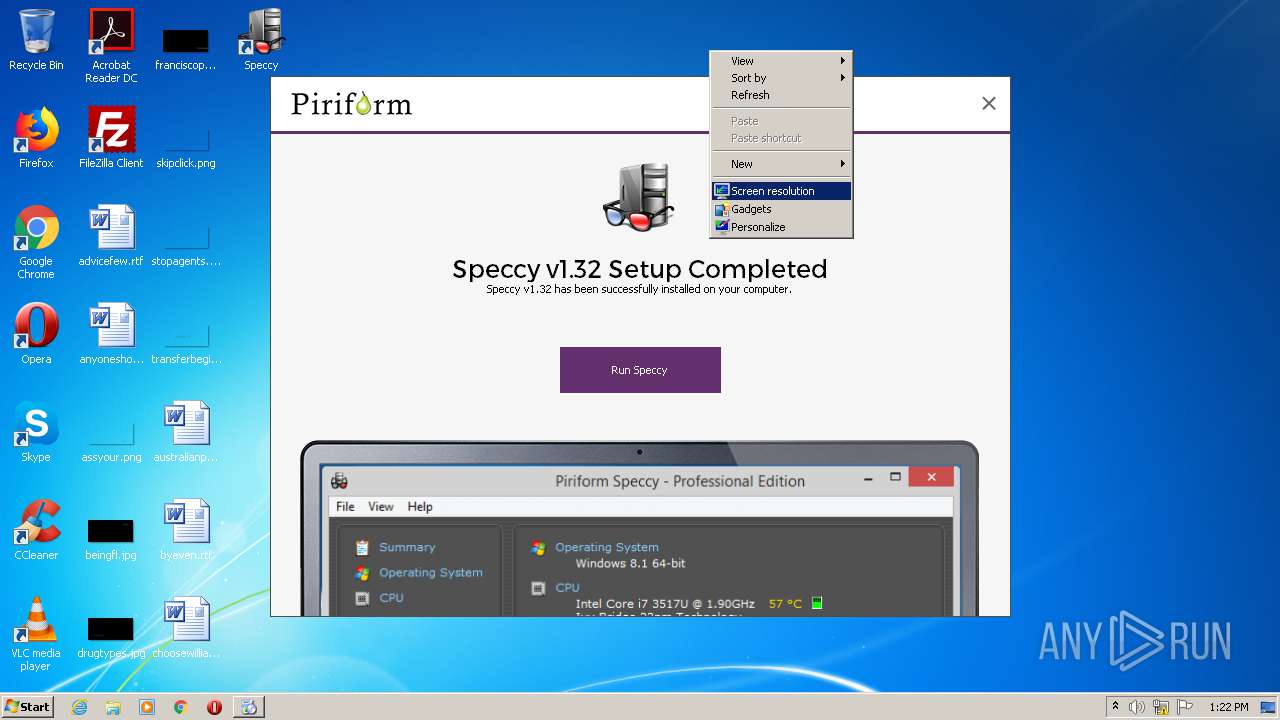
| Verdict: | Malicious activity |
| Analysis date: | September 14, 2020, 12:21:15 |
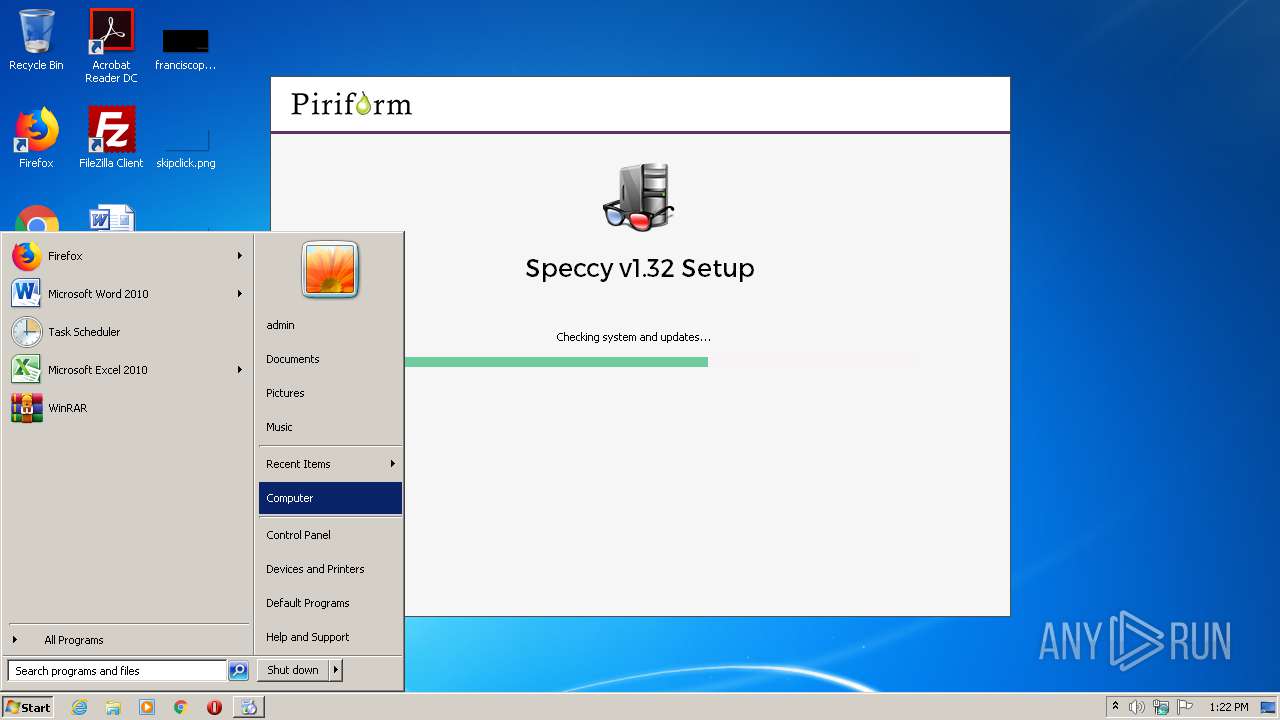
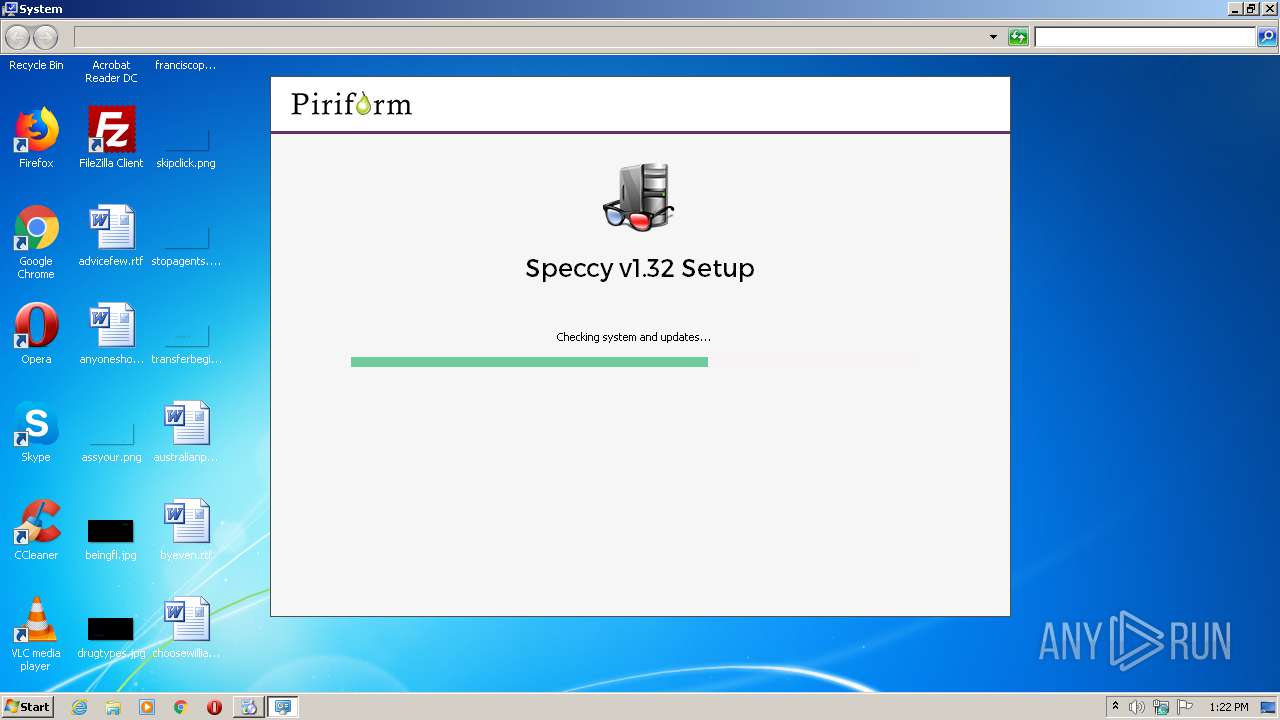
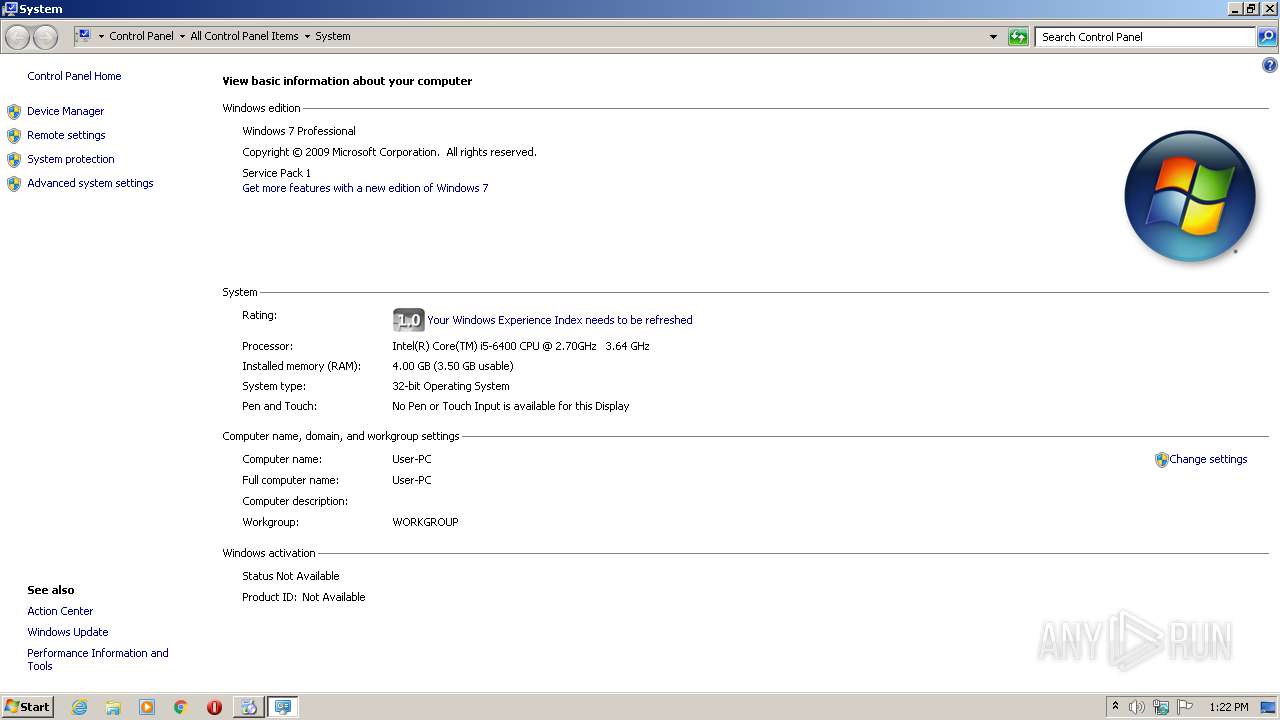
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4C24BB86569C8A0C384BFB4FB95259D6 |
| SHA1: | 74019F340BF280AB55E3ADF2B3E3F66CE50F0E8D |
| SHA256: | 1356CAE1349D3A46692BCAFEB9D275150D21BA024CC995D3D9368D906B41AC0A |
| SSDEEP: | 196608:1XfjcT02U2UQsYRioh4YagF2zSgIdgzGUcbIPDHq//asTMDUfa+V0bd8:1XfjU02UNQ5RinYagF2m/gyUccr8aoMC |
MALICIOUS
Loads the Task Scheduler COM API
- spsetup132.exe (PID: 2232)
Loads dropped or rewritten executable
- spsetup132.exe (PID: 2232)
Actions looks like stealing of personal data
- spsetup132.exe (PID: 2232)
SUSPICIOUS
Executable content was dropped or overwritten
- spsetup132.exe (PID: 2232)
Reads internet explorer settings
- spsetup132.exe (PID: 2232)
Executed as Windows Service
- taskhost.exe (PID: 3392)
Reads Internet Cache Settings
- spsetup132.exe (PID: 2232)
- taskhost.exe (PID: 3392)
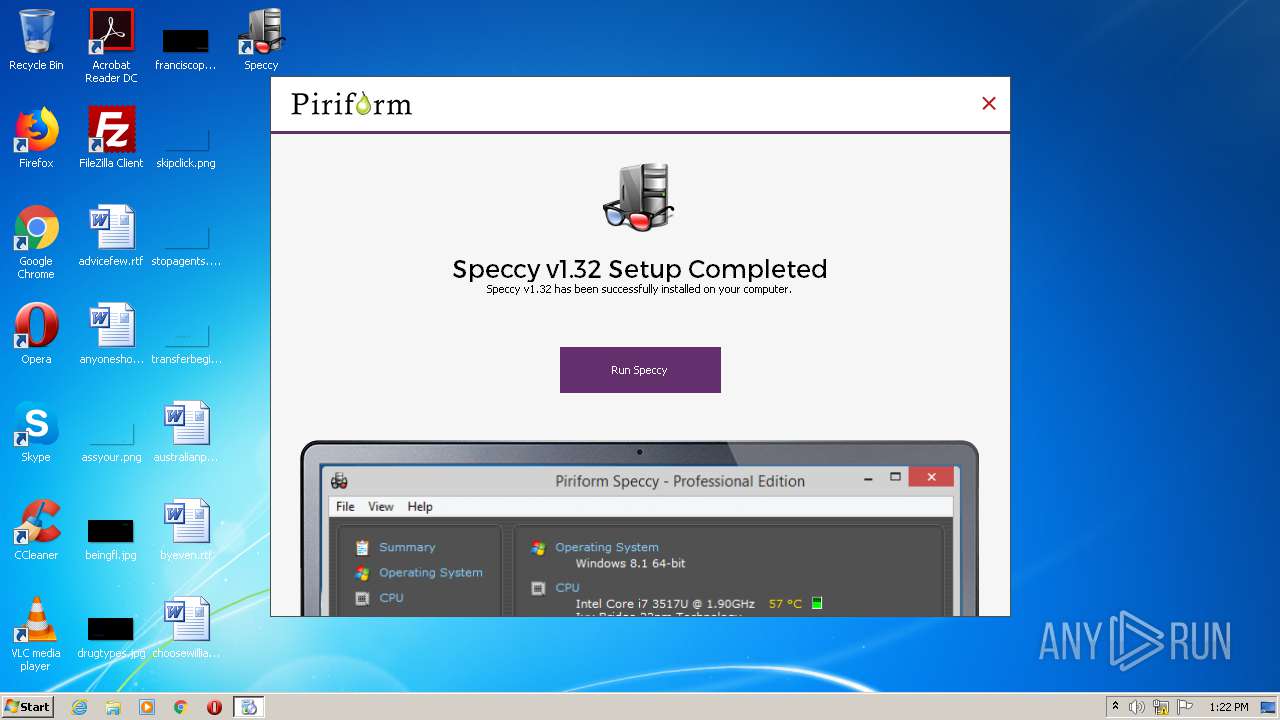
Creates a software uninstall entry
- spsetup132.exe (PID: 2232)
Modifies the open verb of a shell class
- spsetup132.exe (PID: 2232)
Creates files in the user directory
- spsetup132.exe (PID: 2232)
Reads the cookies of Mozilla Firefox
- spsetup132.exe (PID: 2232)
Reads the cookies of Google Chrome
- spsetup132.exe (PID: 2232)
Creates files in the program directory
- spsetup132.exe (PID: 2232)
INFO
Manual execution by user
- control.exe (PID: 2724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:29 22:34:49+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 29696 |
| InitializedDataSize: | 441856 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3a1c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.32.0.774 |
| ProductVersionNumber: | 1.32.0.774 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Piriform Software Ltd |
| FileDescription: | Speccy Installer |
| FileVersion: | 1.32.0.774 |
| LegalCopyright: | Copyright © 2006-2020 Piriform Software Ltd |
| ProductName: | Speccy |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Dec-2015 21:34:49 |
| Detected languages: |
|
| CompanyName: | Piriform Software Ltd |
| FileDescription: | Speccy Installer |
| FileVersion: | 1.32.0.774 |
| LegalCopyright: | Copyright © 2006-2020 Piriform Software Ltd |
| ProductName: | Speccy |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 29-Dec-2015 21:34:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00007250 | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46491 |
.rdata | 0x00009000 | 0x00002B38 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41939 |
.data | 0x0000C000 | 0x00067EDC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.89689 |
.ndata | 0x00074000 | 0x00331000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x003A5000 | 0x00006FB0 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16976 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21562 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.62687 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.7389 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 3.91559 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 5.97397 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.89369 | 744 | UNKNOWN | English - United States | RT_ICON |
103 | 2.72033 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.704 | 688 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.92897 | 344 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
46
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2232 | "C:\Users\admin\AppData\Local\Temp\spsetup132.exe" | C:\Users\admin\AppData\Local\Temp\spsetup132.exe | explorer.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: Speccy Installer Exit code: 0 Version: 1.32.0.774 Modules
| |||||||||||||||
| 2664 | "C:\Users\admin\AppData\Local\Temp\spsetup132.exe" | C:\Users\admin\AppData\Local\Temp\spsetup132.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: Speccy Installer Exit code: 3221226540 Version: 1.32.0.774 Modules
| |||||||||||||||
| 2724 | "C:\Windows\System32\control.exe" SYSTEM | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3392 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
488
Read events
448
Write events
34
Delete events
6
Modification events
| (PID) Process: | (2232) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B808000002DF8397918AD601 | |||
| (PID) Process: | (2232) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: F4786C3FDF4FD7A7A252A1D064F6FD450CBE0B3641B76F46CF66D458B2F87BC9 | |||
| (PID) Process: | (2232) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2232) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | |||
| (PID) Process: | (2232) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 53904A2B31F04E89715371F65116C1EFD23F128839B8128583CC1446ABABE43B | |||
| (PID) Process: | (2232) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: 53904A2B31F04E89715371F65116C1EFD23F128839B8128583CC1446ABABE43B | |||
| (PID) Process: | (2232) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | |||
| (PID) Process: | (2232) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2232) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: F4786C3FDF4FD7A7A252A1D064F6FD450CBE0B3641B76F46CF66D458B2F87BC9 | |||
| (PID) Process: | (2232) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: B808000002DF8397918AD601 | |||
Executable files
77
Suspicious files
5
Text files
9
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2232 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsoF0A.tmp\ui\res\Montserrat-Regular.otf | otf | |
MD5:27E50FFD6A14CBC8221C9DBD3B5208DC | SHA256:40FC1142200A5C1C18F80B6915257083C528C7F7FD2B00A552AEEBC42898D428 | |||
| 2232 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsoF0A.tmp\UserInfo.dll | executable | |
MD5:C1F778A6D65178D34BDE4206161A98E0 | SHA256:9CAF7A78F750713180CF64D18967A2B803B5580E636E59279DCAAF18BA0DAA87 | |||
| 2232 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsoF0A.tmp\ui\res\SP_computer.png | image | |
MD5:873B7C34CED38ADAA2D01752099C09DF | SHA256:ACED6376065F2C71B4B619823F735BBDCAC967A5113CD4E6B978298A58C927C9 | |||
| 2232 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsoF0A.tmp\ui\res\Speccy_Logo_72px.png | image | |
MD5:1787175D95EAB213CF5A8BC25E252676 | SHA256:65FA6BAA9D140251D04069CF538F3262EBBB0E4E62D58D06CC58AD8B22085A83 | |||
| 2232 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsoF0A.tmp\g\gcapi_dll.dll | executable | |
MD5:2973AF8515EFFD0A3BFC7A43B03B3FCC | SHA256:D0E4581210A22135CE5DEB47D9DF4D636A94B3813E0649AAB84822C9F08AF2A0 | |||
| 2232 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsoF0A.tmp\ui\res\PF_logo.png | image | |
MD5:079CCA30760CCA3C01863B6B96E87848 | SHA256:8DD37D3721E25C32C5BF878B6DBA9E61D04B7CE8AEC45BDF703A41BC41802DFA | |||
| 2232 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsoF0A.tmp\ui\res\lang-1034.dll | executable | |
MD5:14FE4B0EF7E19E9AB609B8E55C8F9F80 | SHA256:69A779269E24B4F0BB6015255162C0DDDBBEF4FEC99B3BF3BF6B870CC735CC15 | |||
| 2232 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsoF0A.tmp\ui\res\lang-1043.dll | executable | |
MD5:D1C3DAF7273F4298EDDEDA6014098EF1 | SHA256:AED839848DE0512E30779B2E5F7BA929255D4CA7BA9C16AF5E5FF5DE9BFBC1F6 | |||
| 2232 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsoF0A.tmp\ui\res\lang-1040.dll | executable | |
MD5:A3ED424BA2F740540CB4943DC2E29A4A | SHA256:BAD926CF2D9E670BC52CEEBDFA92ECD08433E950D23EF269CB09C61E0A584BB4 | |||
| 2232 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsoF0A.tmp\ui\res\lang-1041.dll | executable | |
MD5:086D19445388C9046B82BC88D51ADDA8 | SHA256:55CFC9D3430D50BCF0F0E3DBCE8BB833CD65C5CB2AD1DDE6CDB01068863E953F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2232 | spsetup132.exe | GET | 200 | 151.101.0.64:80 | http://service.piriform.com/installcheck.aspx?p=4&v=1.32.774&vx=&l=1033&b=1&o=6.1W3&g=0&i=1&a=0&e=0&n=spsetup132.exe&id=003 | US | text | 4 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 151.101.0.64:80 | service.piriform.com | Fastly | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
service.piriform.com |
| whitelisted |