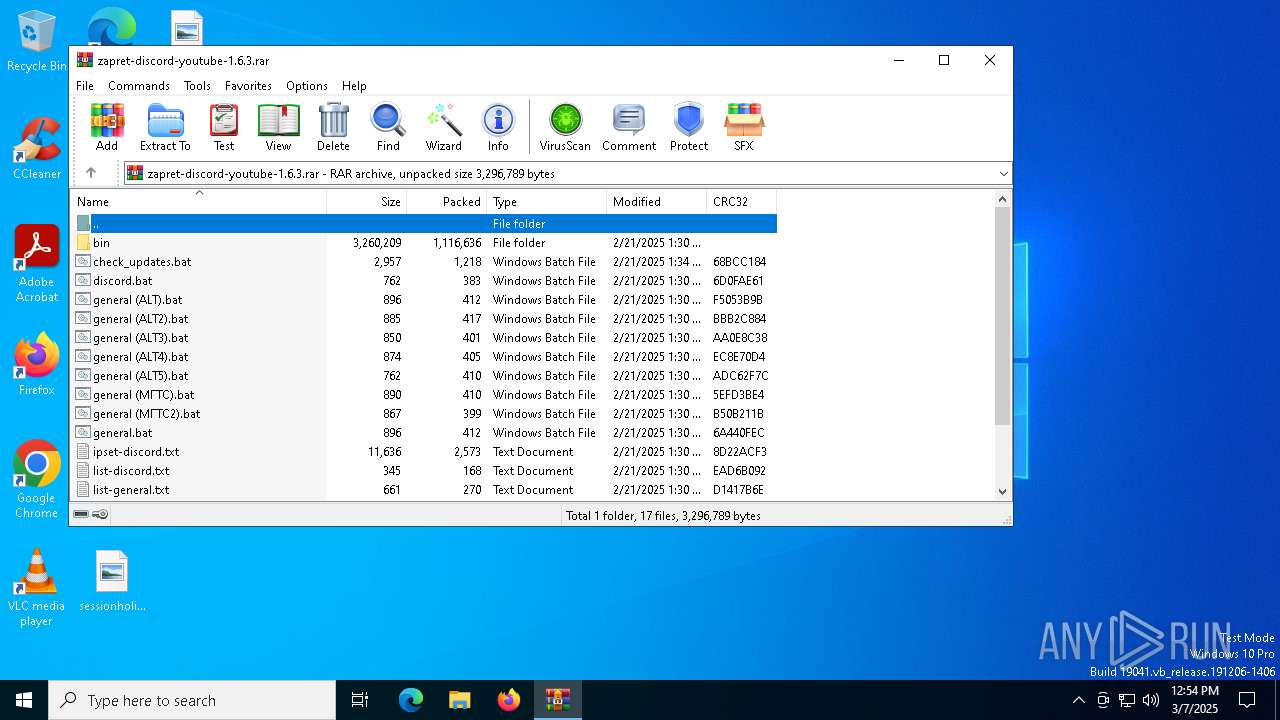
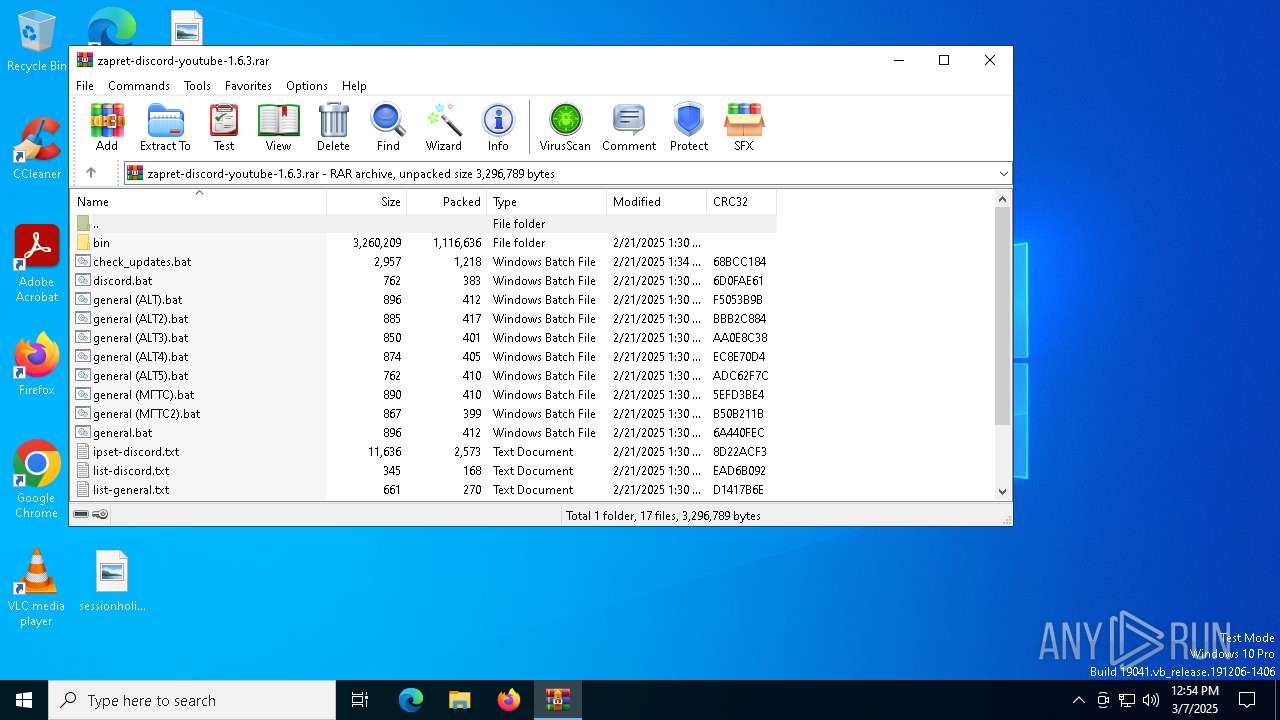
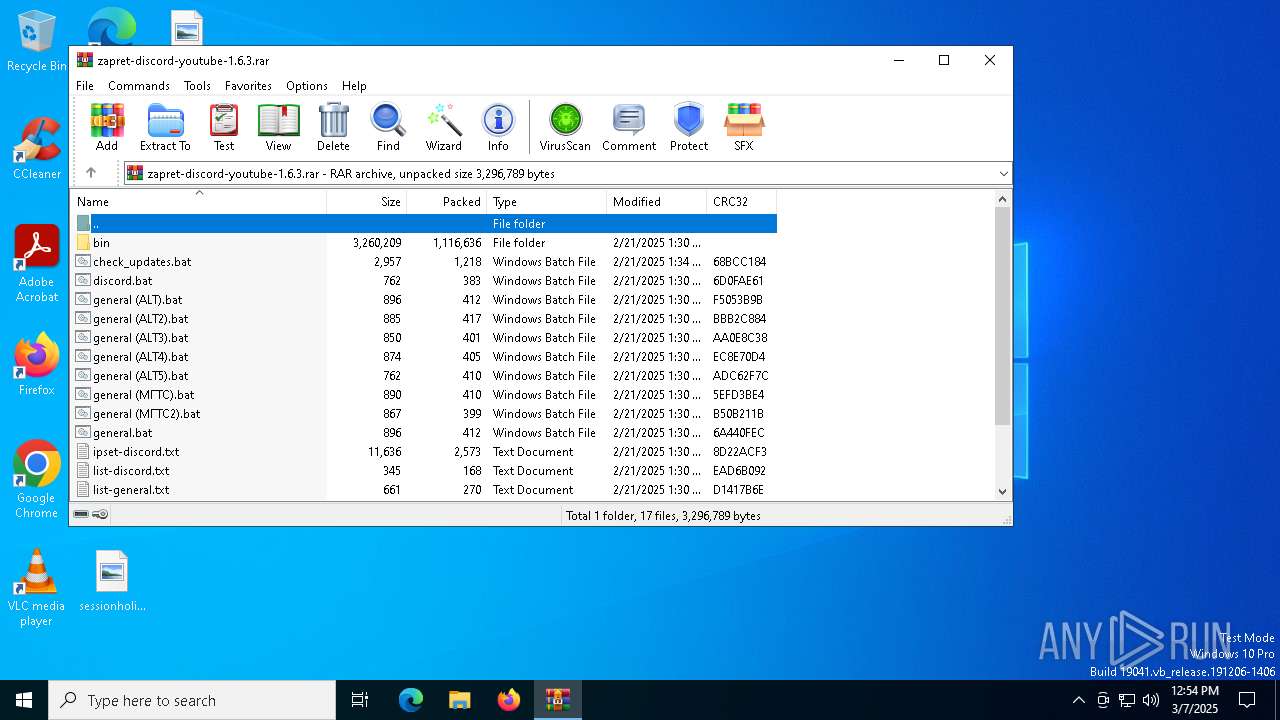
| File name: | zapret-discord-youtube-1.6.3.rar |
| Full analysis: | https://app.any.run/tasks/f364c6e2-c96e-4934-8396-cfdf7ce52570 |
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2025, 12:54:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A4EB00D76AF347865ADA43830B6F1609 |
| SHA1: | 88A86EE3ED6AA0C9A3B1F7FE61516818067FA340 |
| SHA256: | 134CADD52F12AD101DD11412218920585556ADD2D46C3E641360F302A423AD5A |
| SSDEEP: | 49152:5Rckt37ZRWJIIw3nM7ZfsDvHlkoanajWkEhhSdq5XKlvaB0mkr5Bw0IHZj09u70K:56kVZ4IIw34ZfsbSoWajHUGqtKli1krI |
MALICIOUS
GENERIC has been found (auto)
- WinRAR.exe (PID: 4244)
Generic archive extractor
- WinRAR.exe (PID: 4244)
Detects Cygwin installation
- WinRAR.exe (PID: 4244)
Malicious driver has been detected
- WinRAR.exe (PID: 4244)
Starts NET.EXE for service management
- cmd.exe (PID: 5400)
- net.exe (PID: 4488)
- cmd.exe (PID: 2152)
- net.exe (PID: 7012)
- net.exe (PID: 7780)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 4244)
Starts application with an unusual extension
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 7708)
- cmd.exe (PID: 4724)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 7456)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 2152)
Application launched itself
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 7708)
- cmd.exe (PID: 7456)
- cmd.exe (PID: 4724)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 5400)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 7708)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 7456)
- cmd.exe (PID: 4724)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 8156)
- powershell.exe (PID: 2088)
- cmd.exe (PID: 5400)
- powershell.exe (PID: 6244)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7984)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 7684)
- cmd.exe (PID: 7344)
- cmd.exe (PID: 2240)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 1052)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 7184)
Hides command output
- cmd.exe (PID: 8160)
- cmd.exe (PID: 7720)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5256)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 6584)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 5400)
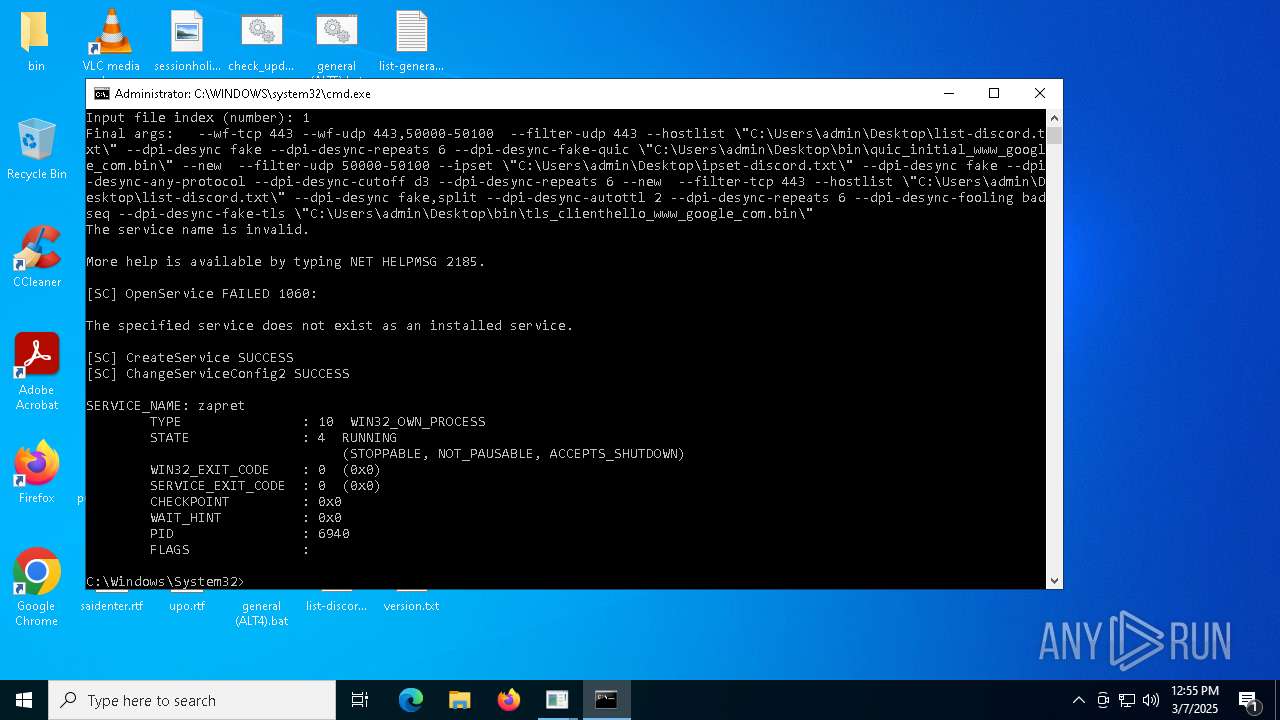
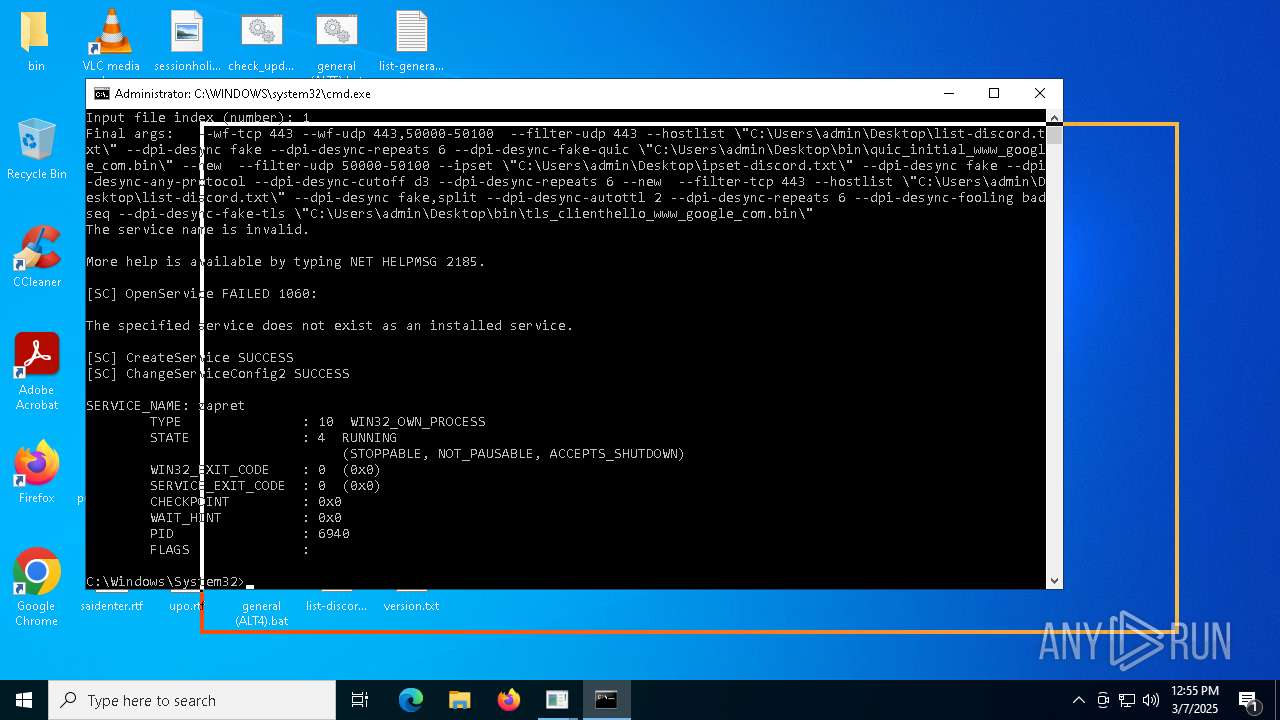
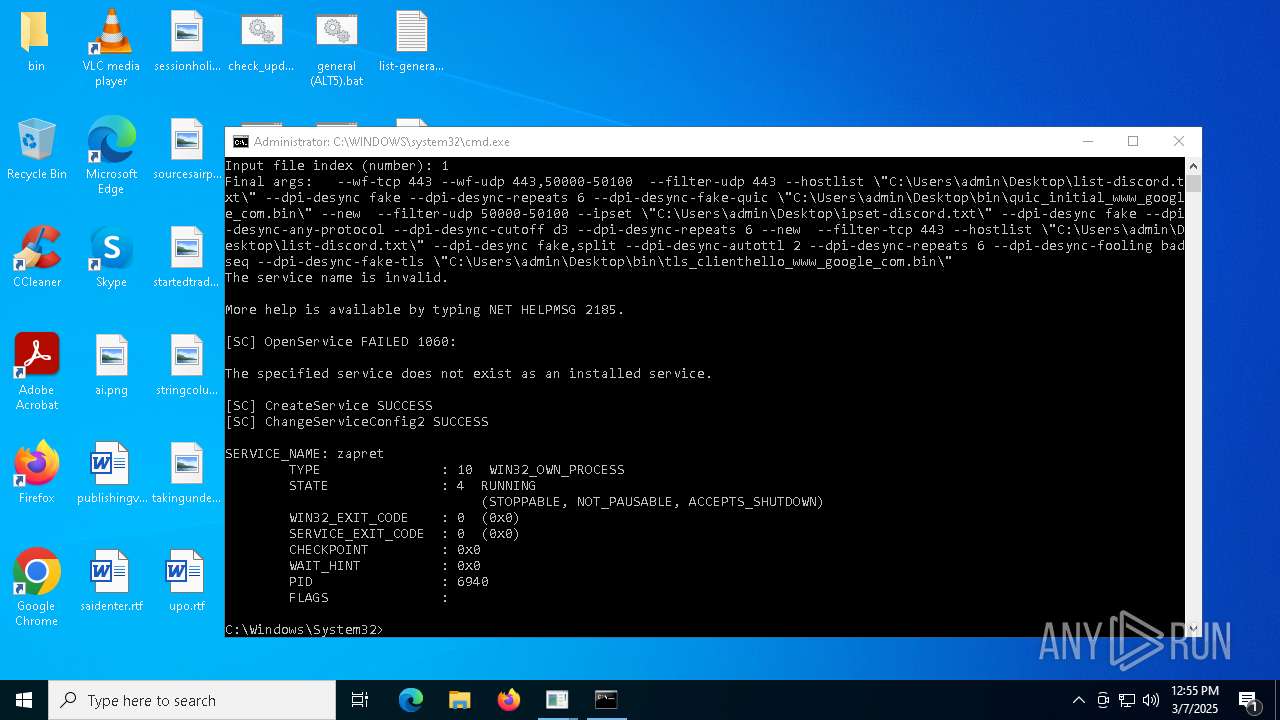
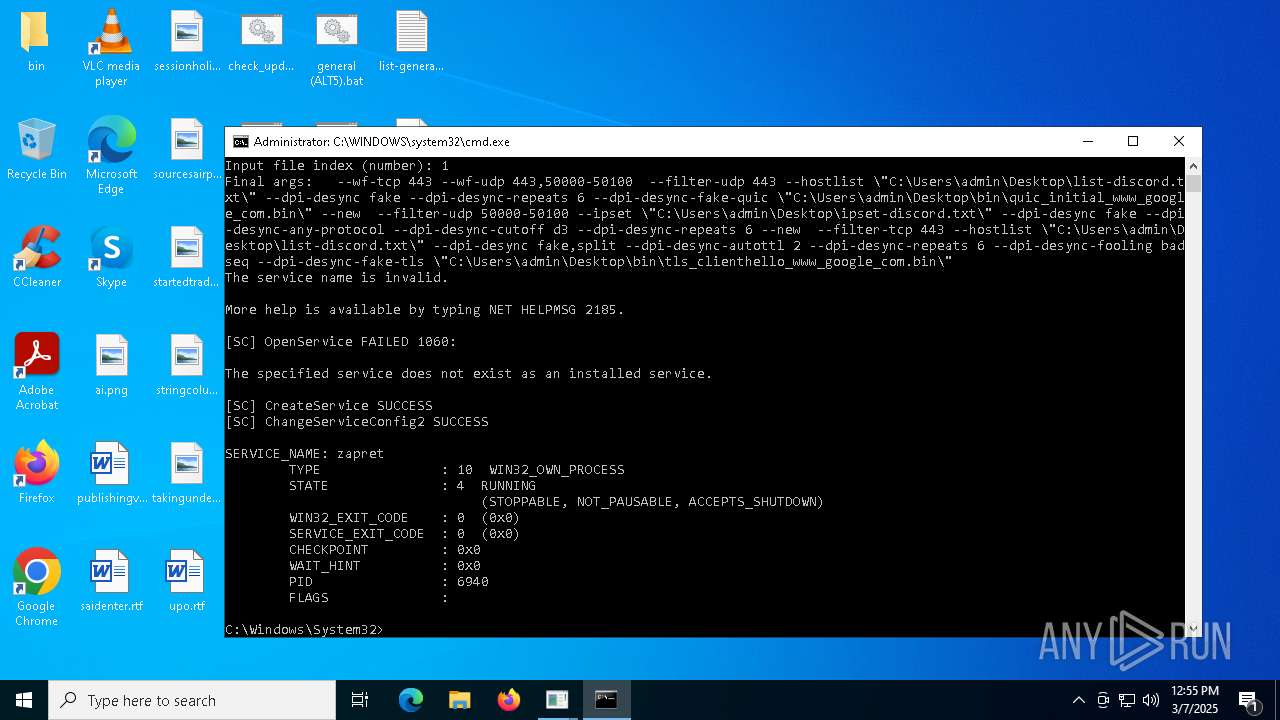
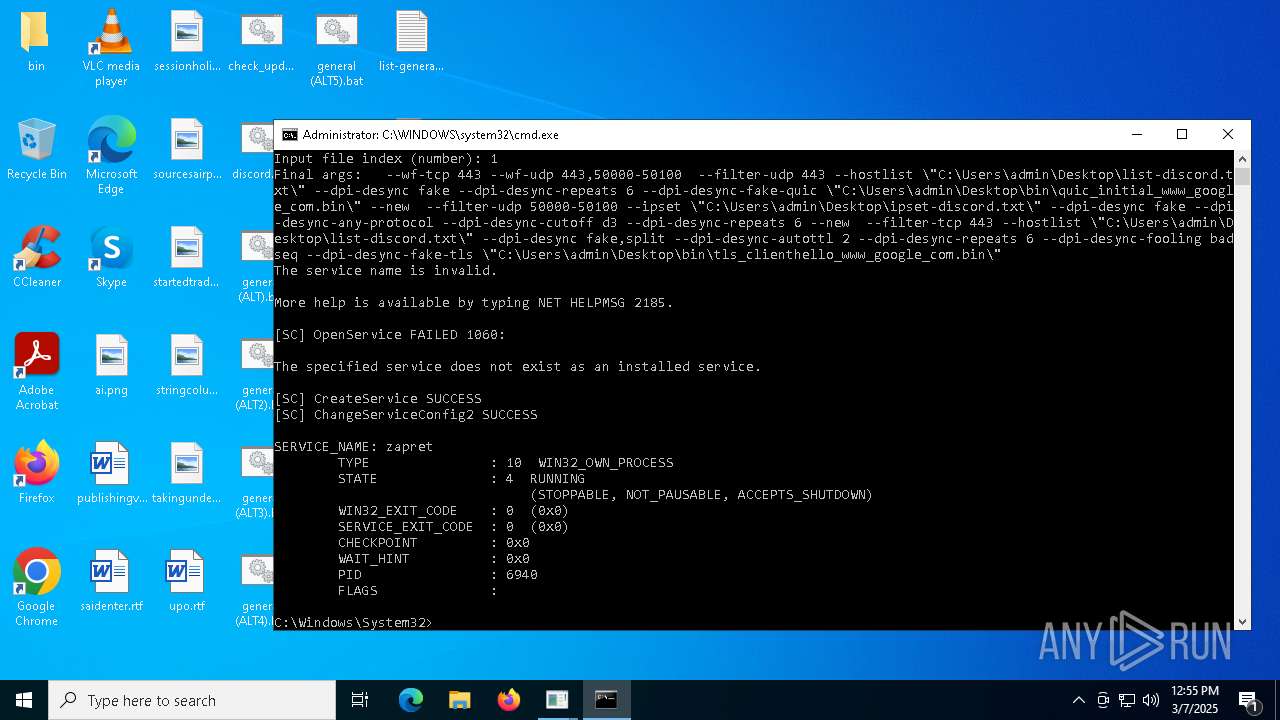
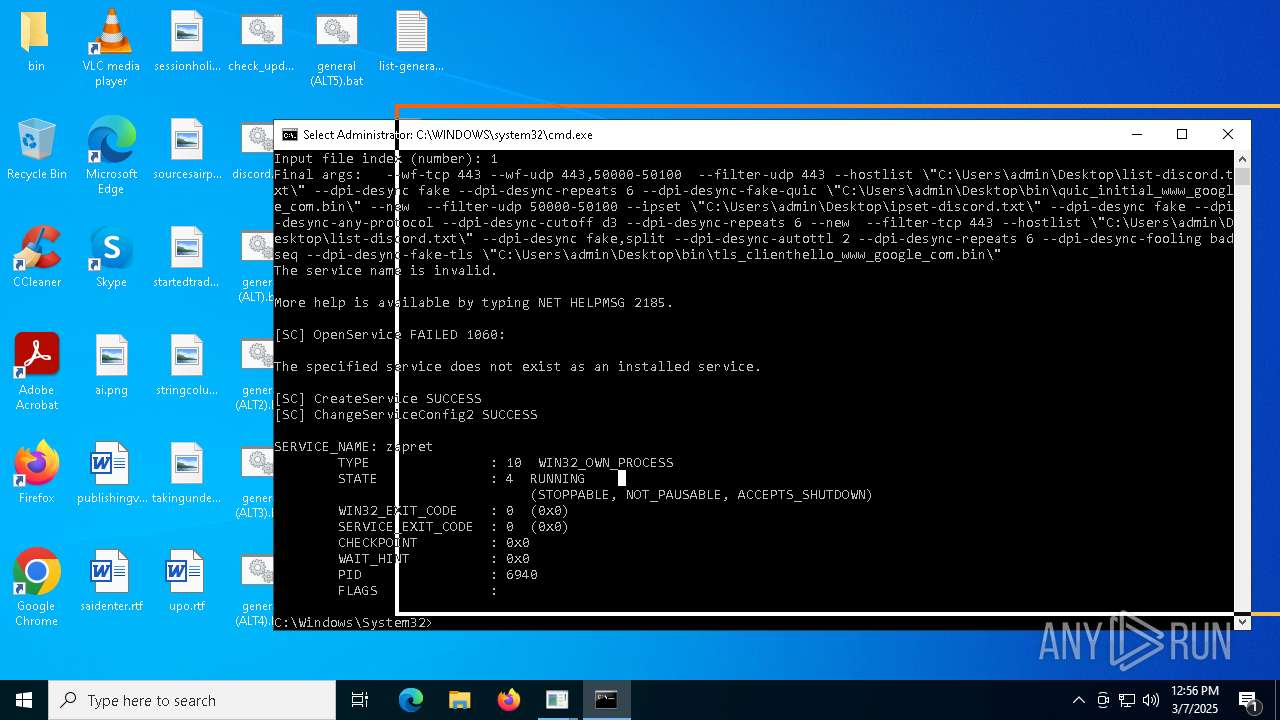
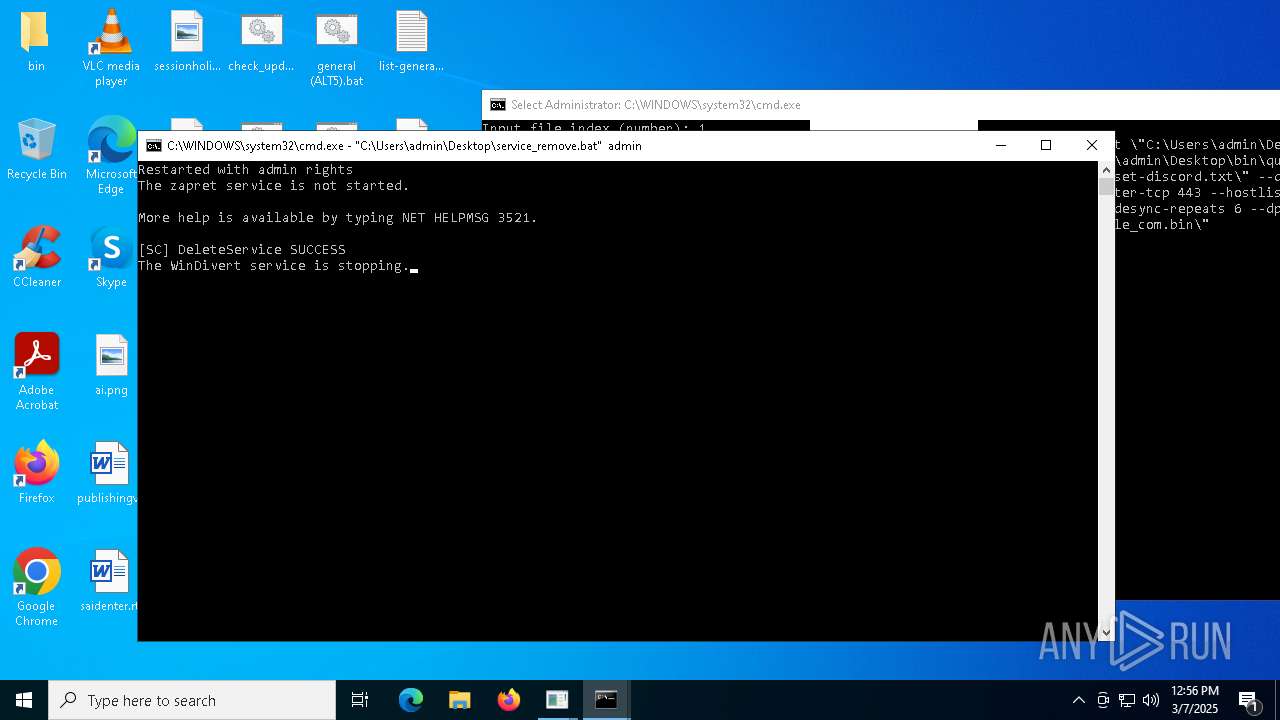
Windows service management via SC.EXE
- sc.exe (PID: 5244)
- sc.exe (PID: 8124)
- sc.exe (PID: 7376)
- sc.exe (PID: 6028)
- sc.exe (PID: 7876)
- sc.exe (PID: 7968)
- sc.exe (PID: 6592)
- sc.exe (PID: 7728)
- sc.exe (PID: 8112)
- sc.exe (PID: 8084)
- sc.exe (PID: 4988)
- sc.exe (PID: 7248)
- sc.exe (PID: 6068)
Starts SC.EXE for service management
- cmd.exe (PID: 5256)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 6584)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 2152)
Starts process via Powershell
- powershell.exe (PID: 2088)
- powershell.exe (PID: 6244)
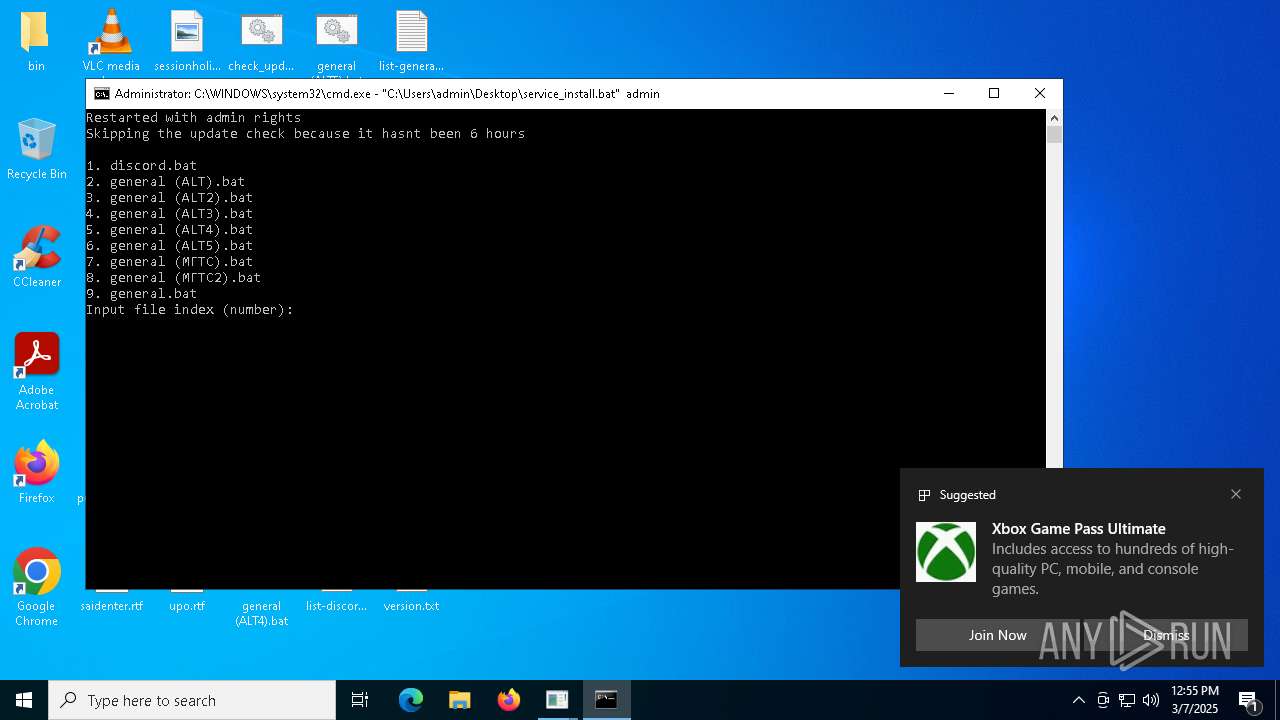
Executing commands from a ".bat" file
- powershell.exe (PID: 2088)
- cmd.exe (PID: 5400)
- powershell.exe (PID: 6244)
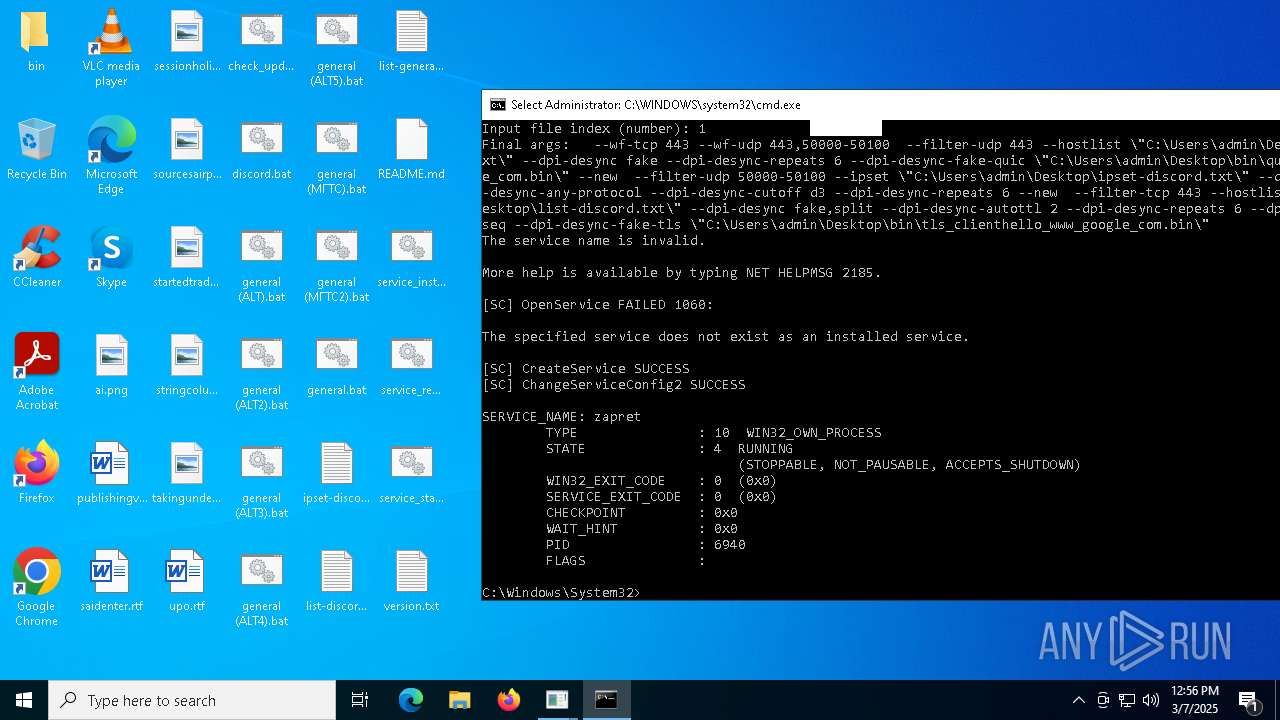
Creates a new Windows service
- sc.exe (PID: 7280)
Executes as Windows Service
- winws.exe (PID: 6940)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5256)
- BackgroundTransferHost.exe (PID: 8032)
- BackgroundTransferHost.exe (PID: 1188)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5256)
- powershell.exe (PID: 8176)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5256)
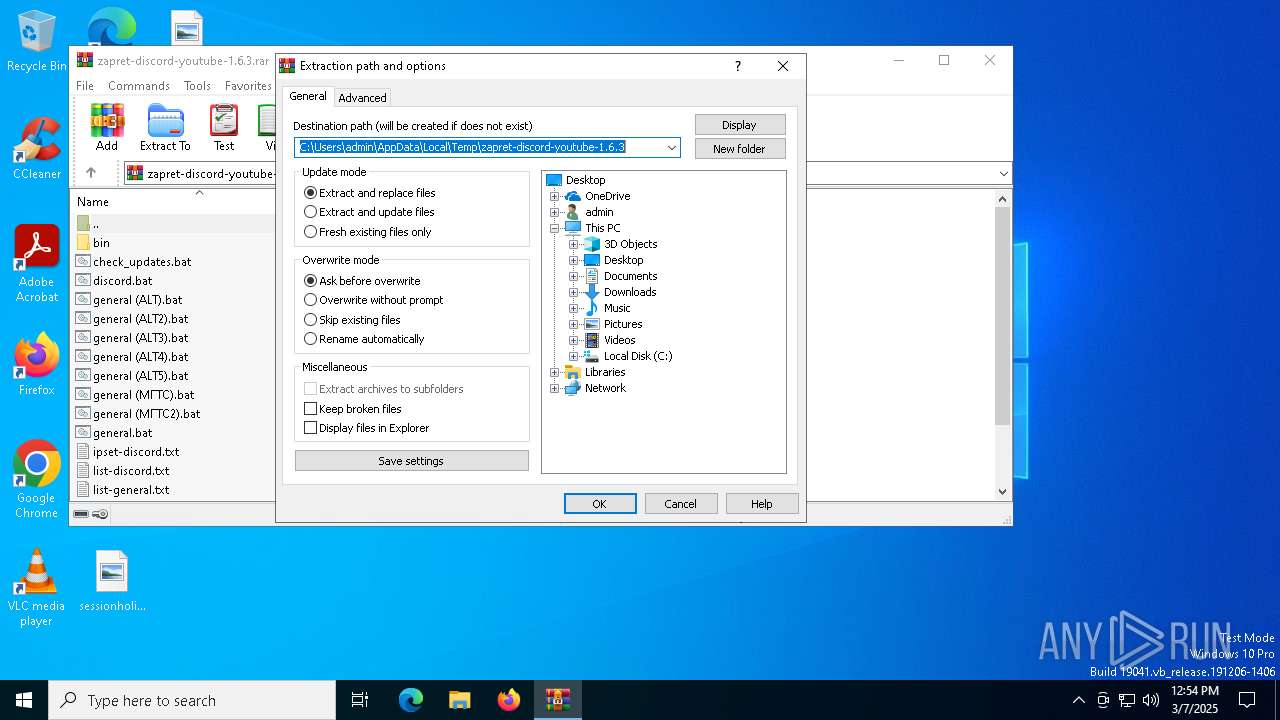
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4244)
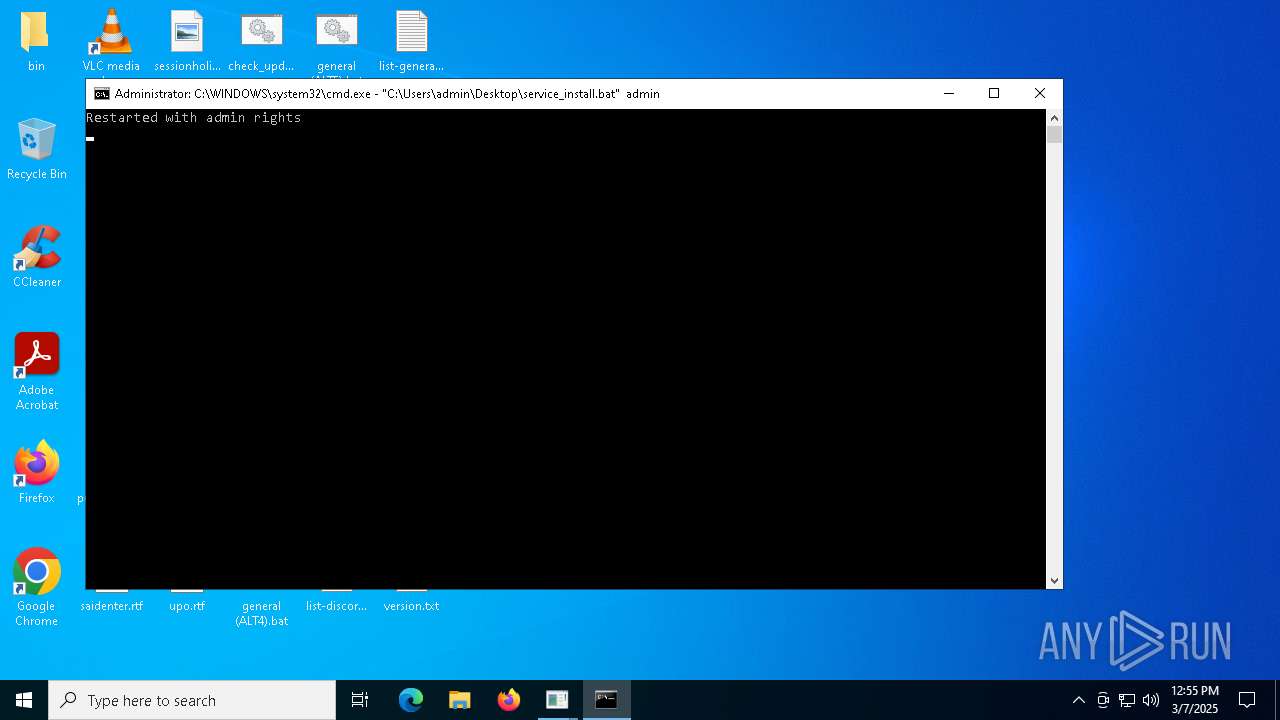
Manual execution by a user
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 7708)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 4724)
- cmd.exe (PID: 7456)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 7184)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5256)
The sample compiled with english language support
- WinRAR.exe (PID: 4244)
Checks supported languages
- chcp.com (PID: 7804)
Changes the display of characters in the console
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 4724)
- cmd.exe (PID: 7708)
- cmd.exe (PID: 7456)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 2152)
Disables trace logs
- powershell.exe (PID: 8176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 383 |
| UncompressedSize: | 762 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | discord.bat |
Total processes
358
Monitored processes
207
Malicious processes
16
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Users\admin\Desktop\bin\winws.exe" --wf-tcp=80,443 --wf-udp=443,50000-50100 --filter-udp=443 --hostlist="list-general.txt" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic="C:\Users\admin\Desktop\bin\quic_initial_www_google_com.bin" --new --filter-udp=50000-50100 --ipset="ipset-discord.txt" --dpi-desync=fake --dpi-desync-any-protocol --dpi-desync-cutoff=d3 --dpi-desync-repeats=6 --new --filter-tcp=80 --hostlist="list-general.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="list-general.txt" --dpi-desync=fake,split --dpi-desync-autottl=5 --dpi-desync-repeats=6 --dpi-desync-fooling=badseq --dpi-desync-fake-tls="C:\Users\admin\Desktop\bin\tls_clienthello_www_google_com.bin" | C:\Users\admin\Desktop\bin\winws.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 664 | "C:\Users\admin\Desktop\bin\winws.exe" --wf-tcp=80,443 --wf-udp=443,50000-50100 --filter-udp=443 --hostlist="list-general.txt" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic="C:\Users\admin\Desktop\bin\quic_initial_www_google_com.bin" --new --filter-udp=50000-50100 --ipset="ipset-discord.txt" --dpi-desync=fake --dpi-desync-any-protocol --dpi-desync-cutoff=d3 --dpi-desync-repeats=6 --new --filter-tcp=80 --hostlist="list-general.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="list-general.txt" --dpi-desync=fake --dpi-desync-autottl=2 --dpi-desync-repeats=6 --dpi-desync-fooling=badseq --dpi-desync-fake-tls="C:\Users\admin\Desktop\bin\tls_clienthello_www_google_com.bin" | C:\Users\admin\Desktop\bin\winws.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 672 | "C:\Users\admin\Desktop\bin\winws.exe" --wf-tcp=80,443 --wf-udp=443,50000-50100 --filter-udp=443 --hostlist="list-general.txt" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic="C:\Users\admin\Desktop\bin\quic_initial_www_google_com.bin" --new --filter-udp=50000-50100 --ipset="ipset-discord.txt" --dpi-desync=fake --dpi-desync-any-protocol --dpi-desync-cutoff=d3 --dpi-desync-repeats=6 --new --filter-tcp=80 --hostlist="list-general.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="list-general.txt" --dpi-desync=fake --dpi-desync-autottl=2 --dpi-desync-repeats=6 --dpi-desync-fooling=badseq --dpi-desync-fake-tls="C:\Users\admin\Desktop\bin\tls_clienthello_www_google_com.bin" | C:\Users\admin\Desktop\bin\winws.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 680 | powershell -command "[datetime]::Now.ToString('yyyy-MM-dd HH:mm:ss')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Users\admin\Desktop\bin\winws.exe" --wf-tcp=80,443 --wf-udp=443,50000-50100 --filter-udp=443 --hostlist="list-general.txt" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic="C:\Users\admin\Desktop\bin\quic_initial_www_google_com.bin" --new --filter-udp=50000-50100 --ipset="ipset-discord.txt" --dpi-desync=fake --dpi-desync-any-protocol --dpi-desync-cutoff=d3 --dpi-desync-repeats=8 --new --filter-tcp=80 --hostlist="list-general.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="list-general.txt" --dpi-desync=fake,split2 --dpi-desync-repeats=6 --dpi-desync-fooling=md5sig --dpi-desync-fake-tls="C:\Users\admin\Desktop\bin\tls_clienthello_www_google_com.bin" | C:\Users\admin\Desktop\bin\winws.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 736 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | winws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | findstr /i "winws.exe" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | winws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | findstr ":" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
67 505
Read events
67 442
Write events
50
Delete events
13
Modification events
| (PID) Process: | (4244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.6.3.rar | |||
| (PID) Process: | (4244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8032) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8032) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
4
Suspicious files
8
Text files
46
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5256 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\68c06e0f-d6a8-4615-8d1c-afec09474199.down_data | — | |
MD5:— | SHA256:— | |||
| 5256 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:7C48C30BA63B689902BB426C7A0DDC09 | SHA256:32716D5FC0139B83464450DC3B8550672E5530480DCA1050D2606F95DFDF67EB | |||
| 4244 | WinRAR.exe | C:\Users\admin\Desktop\discord.bat | text | |
MD5:EBF82AEABAB4E1D541DD6103186B7FA2 | SHA256:356D30EEBA3E1276FA40A49F3253B661519B18405FFF3068E124558AAB10FFD3 | |||
| 5256 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\856a0f60-b1a9-4f53-ad93-f4bd766b2815.up_meta_secure | binary | |
MD5:8C136DC8A347E593B93577F6CF9BCAE8 | SHA256:CE4C8BE89F8DB11C3F967634C89252AA4E7BD19C96A03498E5E5FE79D1AD444D | |||
| 4244 | WinRAR.exe | C:\Users\admin\Desktop\ipset-discord.txt | text | |
MD5:86934C7445AEE042A64D7CB1B6AEEAD1 | SHA256:E793ECE7A0169069FCBAE6E3E8C45E3D2604FA97187A1DBE9A005DEF2800B2AC | |||
| 4244 | WinRAR.exe | C:\Users\admin\Desktop\list-general.txt | text | |
MD5:BF417BCAF5D7040C1B80B1B57EC07772 | SHA256:DB86FFB24AFDC1FBA9F54C85E52528FEF8517CF05E205F233CD629551D4DF4A6 | |||
| 4244 | WinRAR.exe | C:\Users\admin\Desktop\general (МГТС).bat | text | |
MD5:2A5363D20832A82D6BD5EE7DB2ADBDF6 | SHA256:7F25EEA3B79A0A712E52D927158A671A4A5511EC2C93AE75A89AF98E048DE1B8 | |||
| 4244 | WinRAR.exe | C:\Users\admin\Desktop\service_remove.bat | text | |
MD5:F7AD12616404A382B1689C9E3937C9E5 | SHA256:9D8F0B7105D86DE09B9408515F30B2BC2BB935430F4E73196021368906B7F128 | |||
| 4244 | WinRAR.exe | C:\Users\admin\Desktop\list-discord.txt | text | |
MD5:53C6FE42FF860FDFA8CFAFA9ACFA92FC | SHA256:F015C31EB1C5C13D235AA107B9E618F45AB3AFDEF623C5749BF18494937312A4 | |||
| 4244 | WinRAR.exe | C:\Users\admin\Desktop\README.md | html | |
MD5:069E7EEE62F00FC06744E6FFE48AF38A | SHA256:0D5ED33AE1F7990F07F7930C1E12E609B15C3F9918207EA4683C32B06E068DFF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
29
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7324 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5256 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6372 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6372 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2568 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7324 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7324 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |