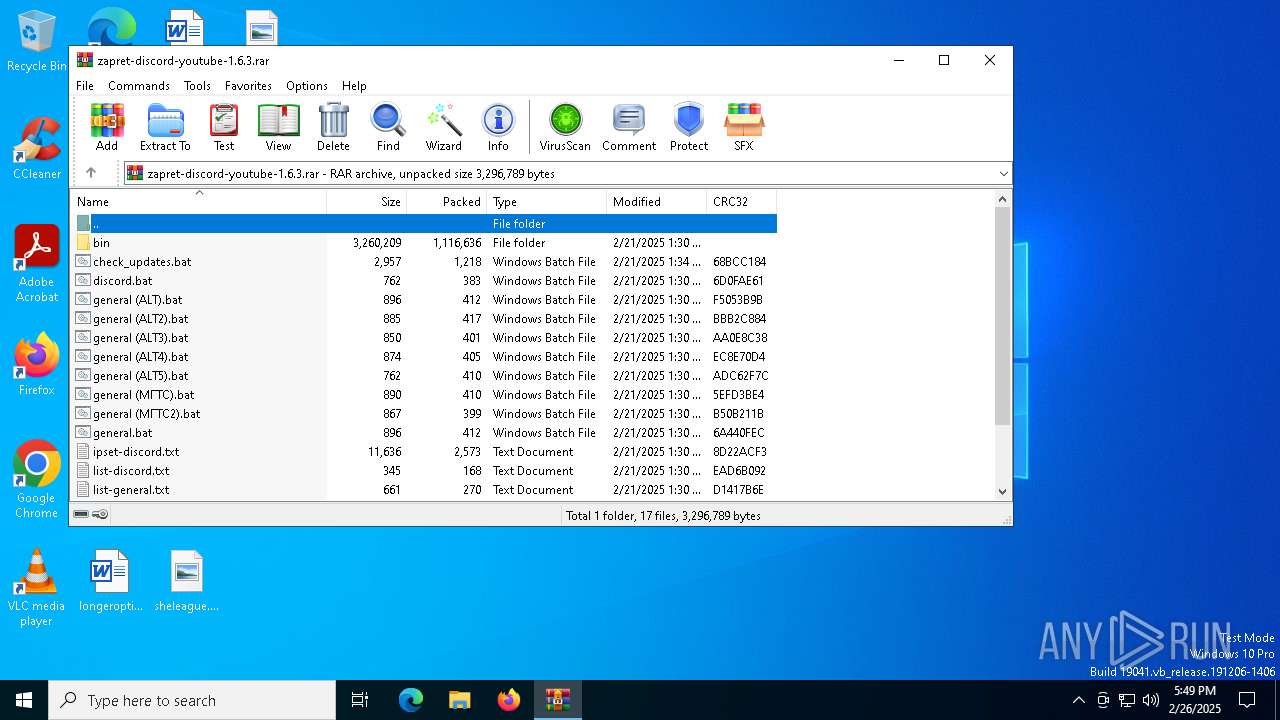
| File name: | zapret-discord-youtube-1.6.3.rar |
| Full analysis: | https://app.any.run/tasks/db0229e0-71c4-4916-a675-af64ca0c0ed6 |
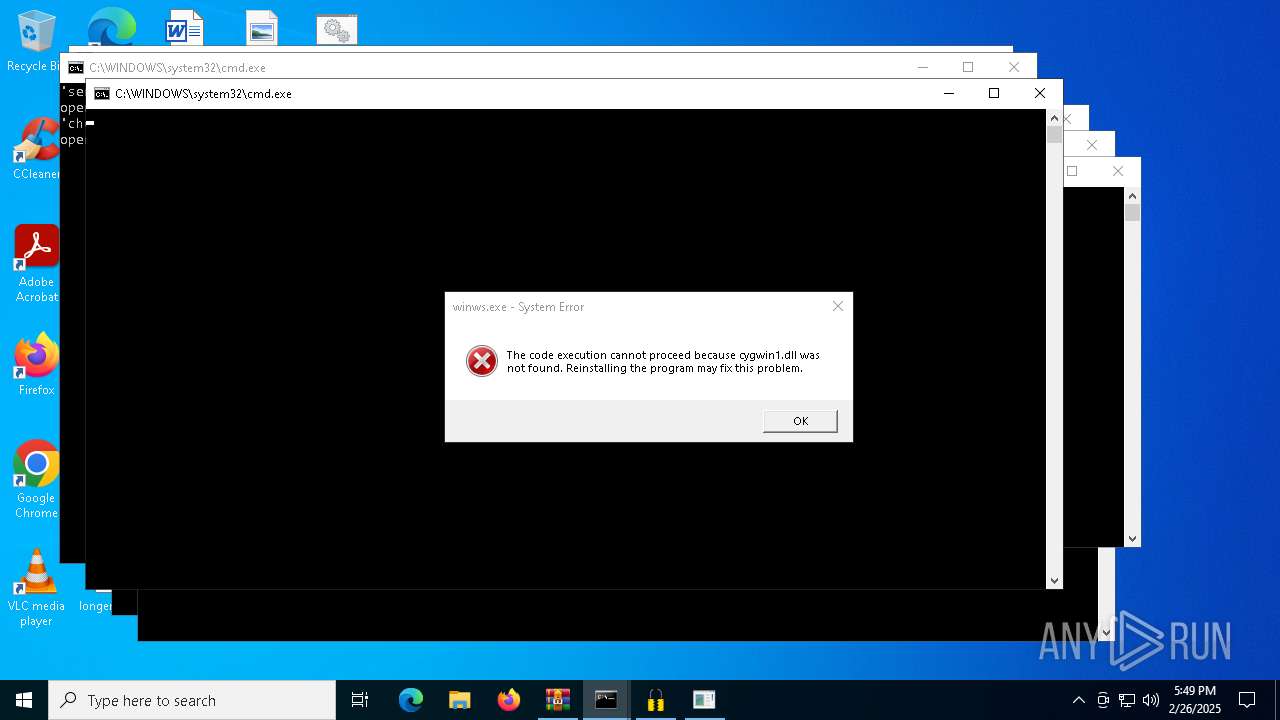
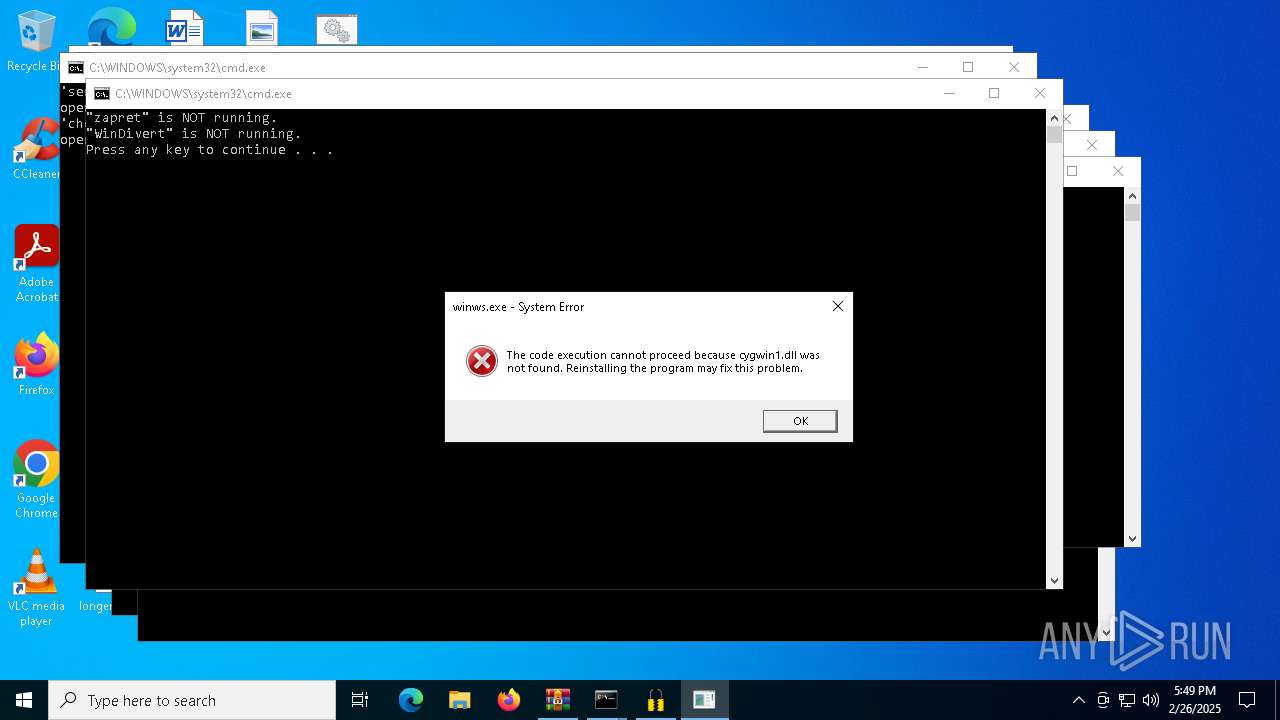
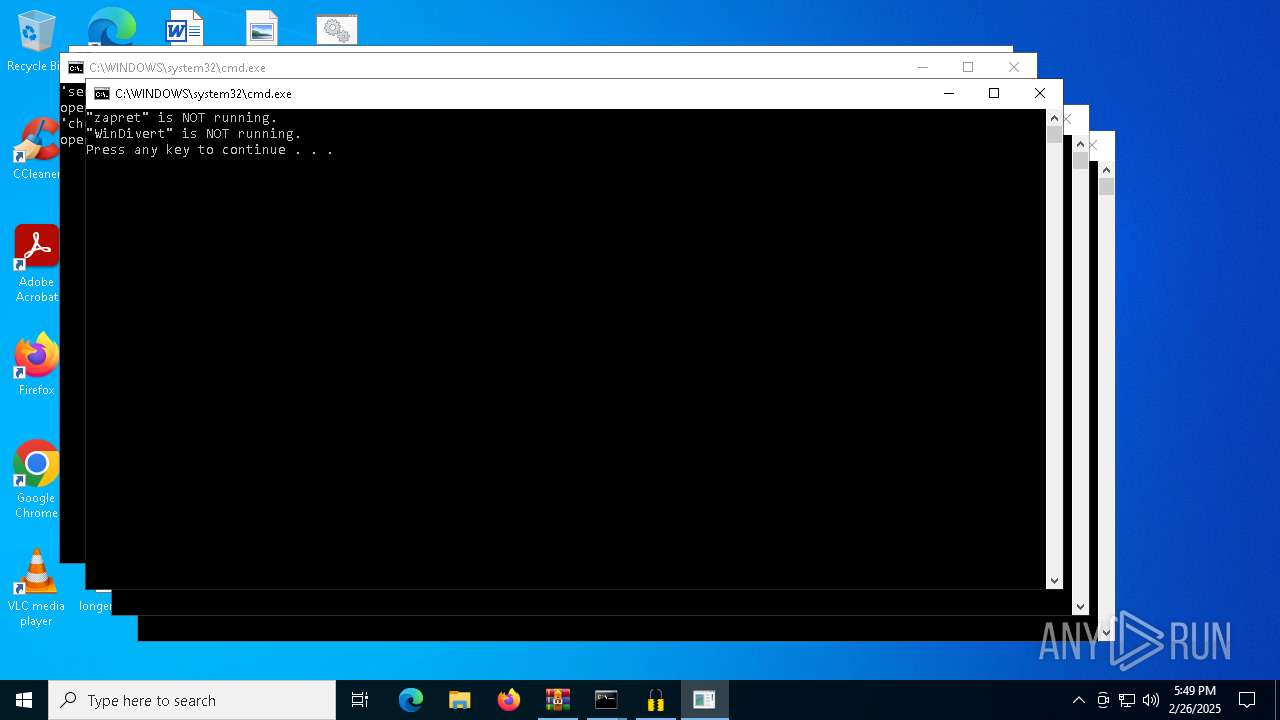
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2025, 17:49:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A4EB00D76AF347865ADA43830B6F1609 |
| SHA1: | 88A86EE3ED6AA0C9A3B1F7FE61516818067FA340 |
| SHA256: | 134CADD52F12AD101DD11412218920585556ADD2D46C3E641360F302A423AD5A |
| SSDEEP: | 49152:5Rckt37ZRWJIIw3nM7ZfsDvHlkoanajWkEhhSdq5XKlvaB0mkr5Bw0IHZj09u70K:56kVZ4IIw34ZfsbSoWajHUGqtKli1krI |
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 8080)
- net.exe (PID: 5892)
- net.exe (PID: 7052)
- net.exe (PID: 1228)
SUSPICIOUS
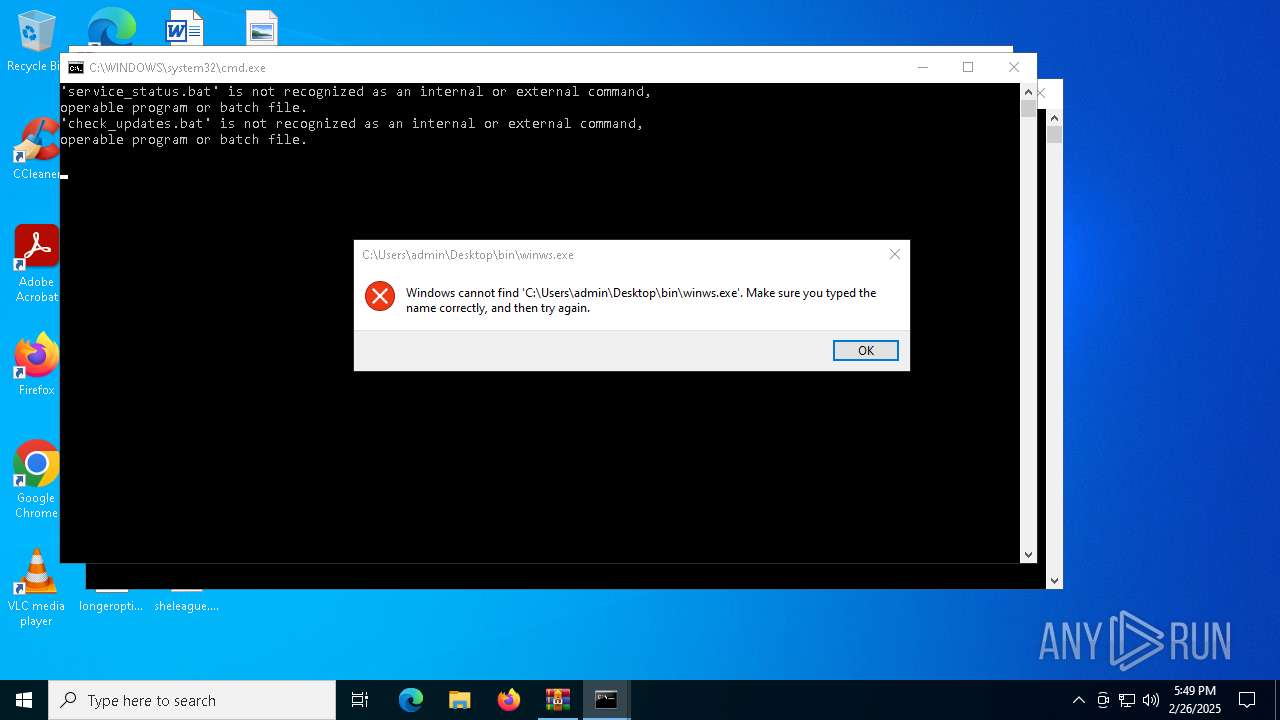
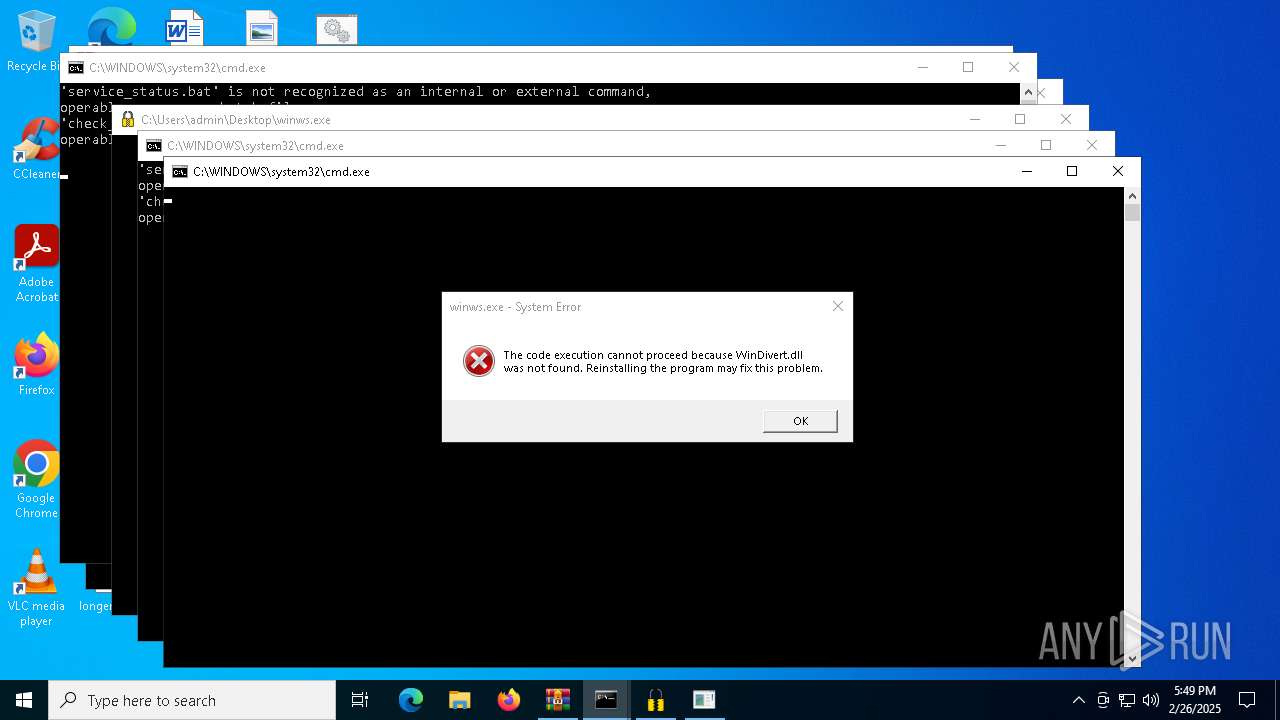
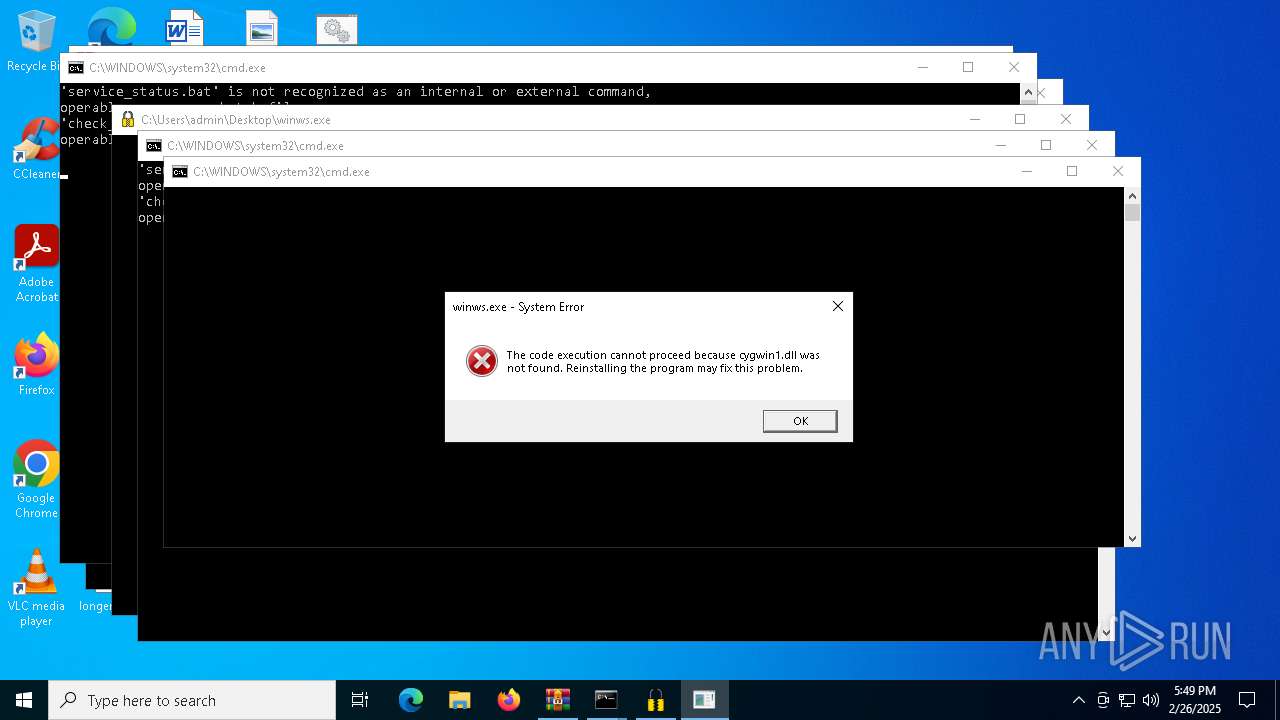
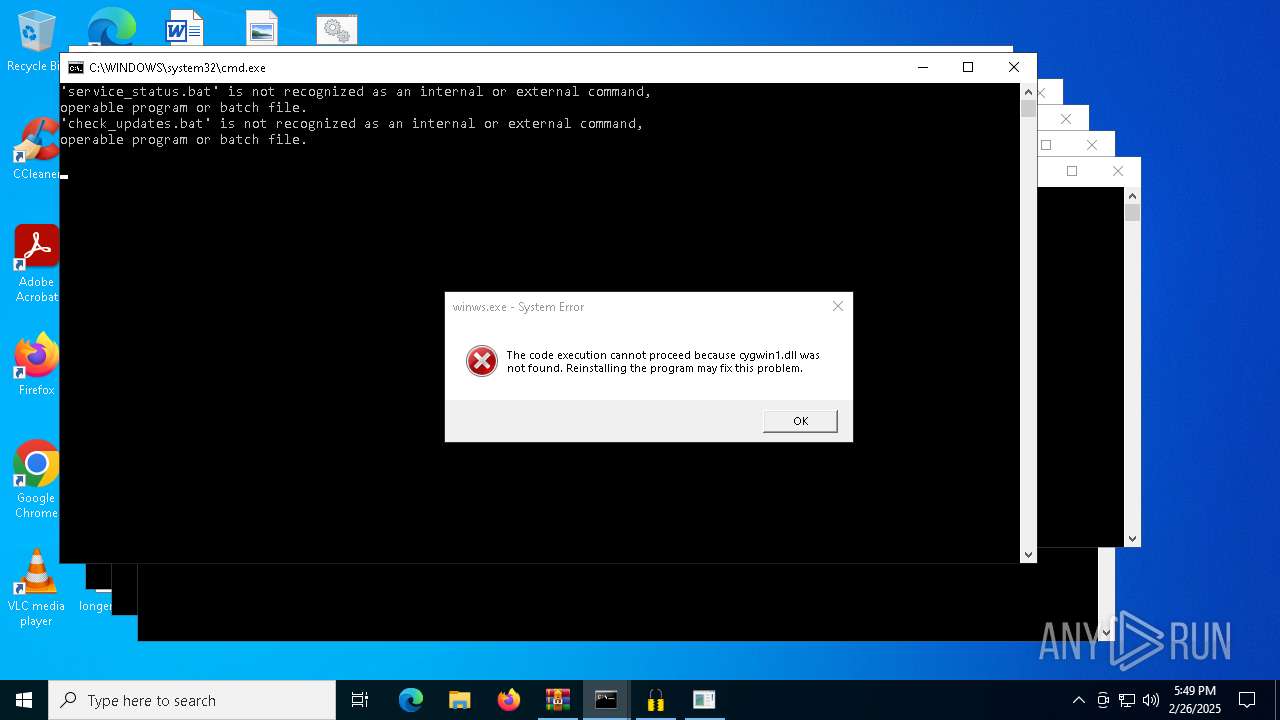
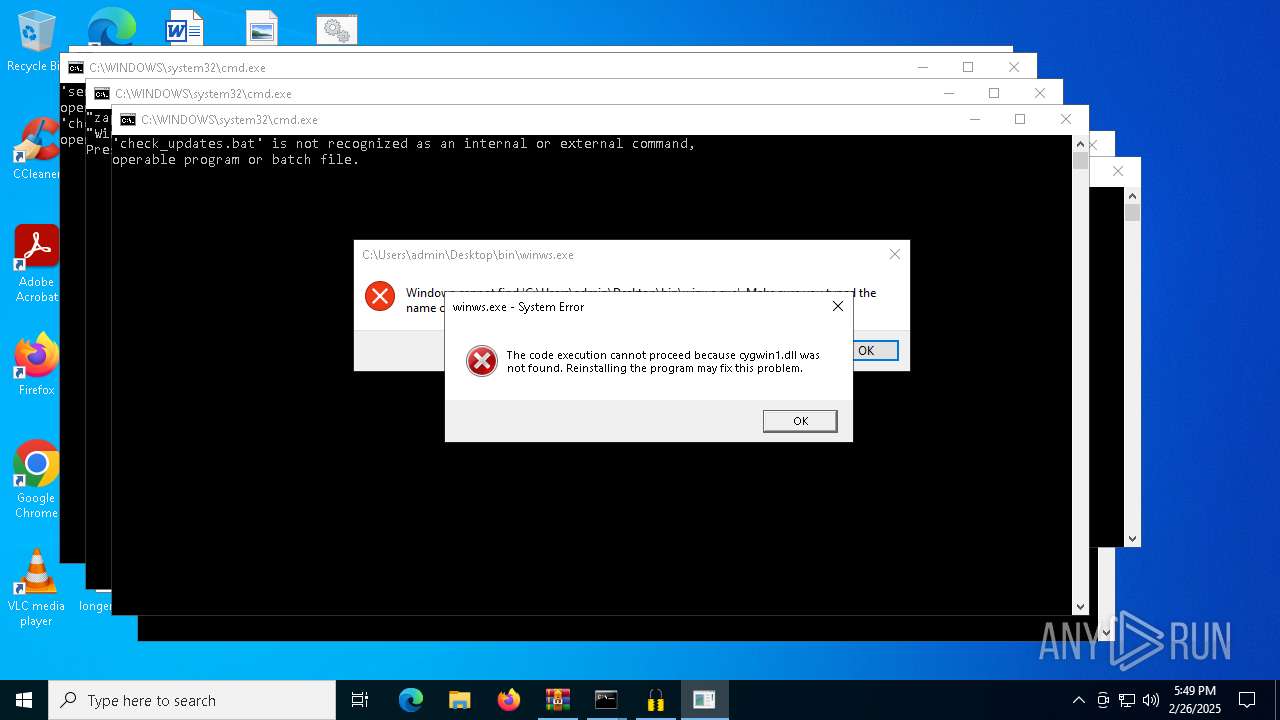
Starts application with an unusual extension
- cmd.exe (PID: 7224)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7792)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 1244)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 8080)
Starts process via Powershell
- powershell.exe (PID: 7908)
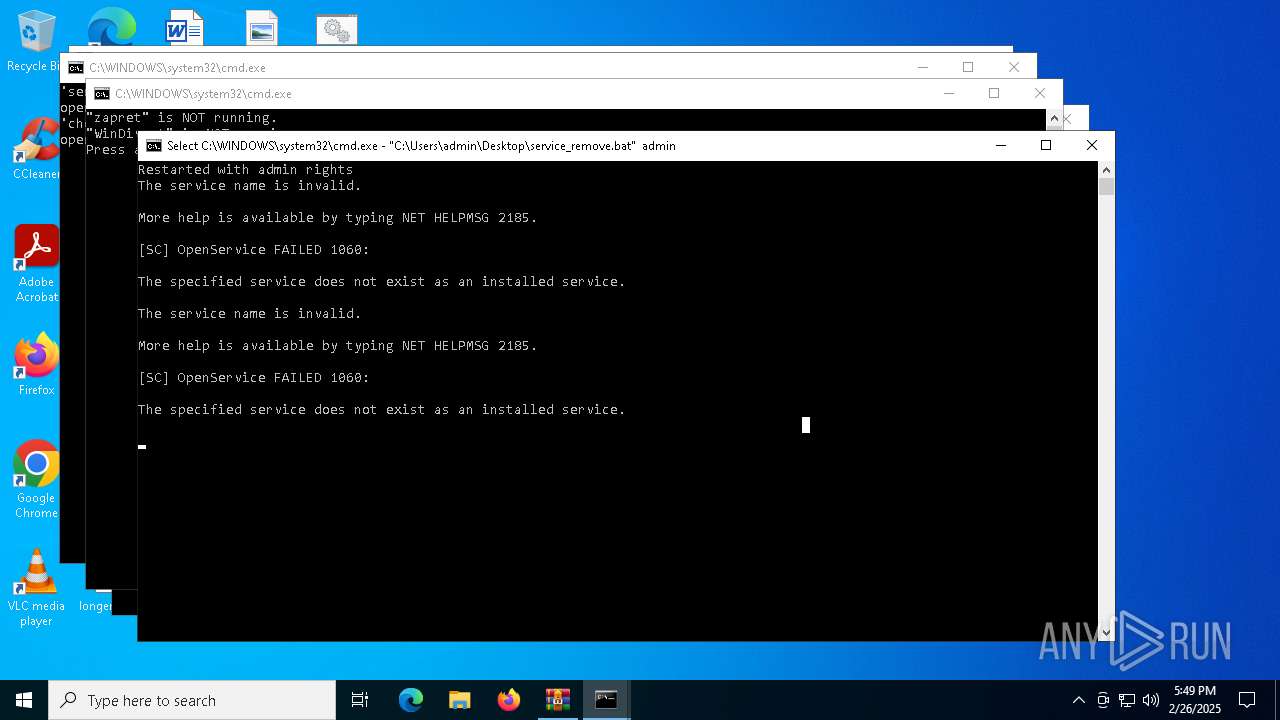
Windows service management via SC.EXE
- sc.exe (PID: 1184)
- sc.exe (PID: 7804)
- sc.exe (PID: 5392)
- sc.exe (PID: 1056)
- sc.exe (PID: 2692)
Application launched itself
- cmd.exe (PID: 1244)
- cmd.exe (PID: 7504)
Starts SC.EXE for service management
- cmd.exe (PID: 6872)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 5800)
- cmd.exe (PID: 8080)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7792)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5800)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 6872)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7504)
- powershell.exe (PID: 7908)
- cmd.exe (PID: 1244)
Executing commands from a ".bat" file
- powershell.exe (PID: 7908)
INFO
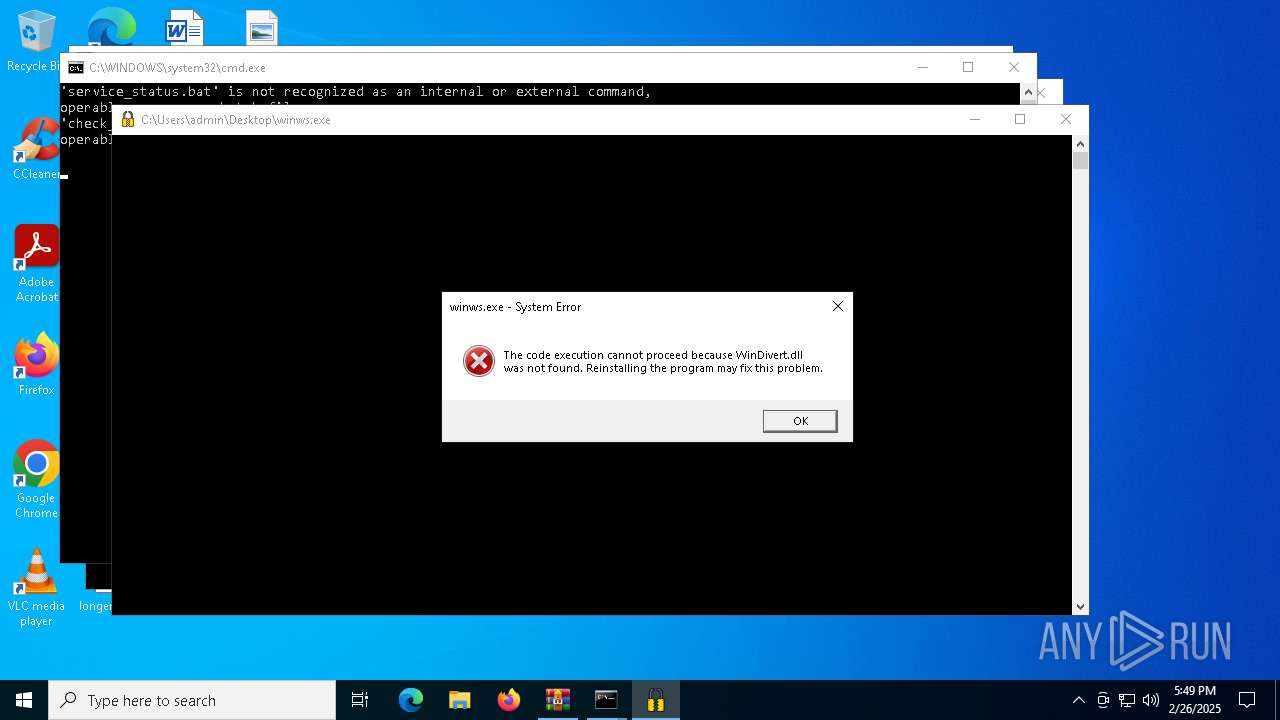
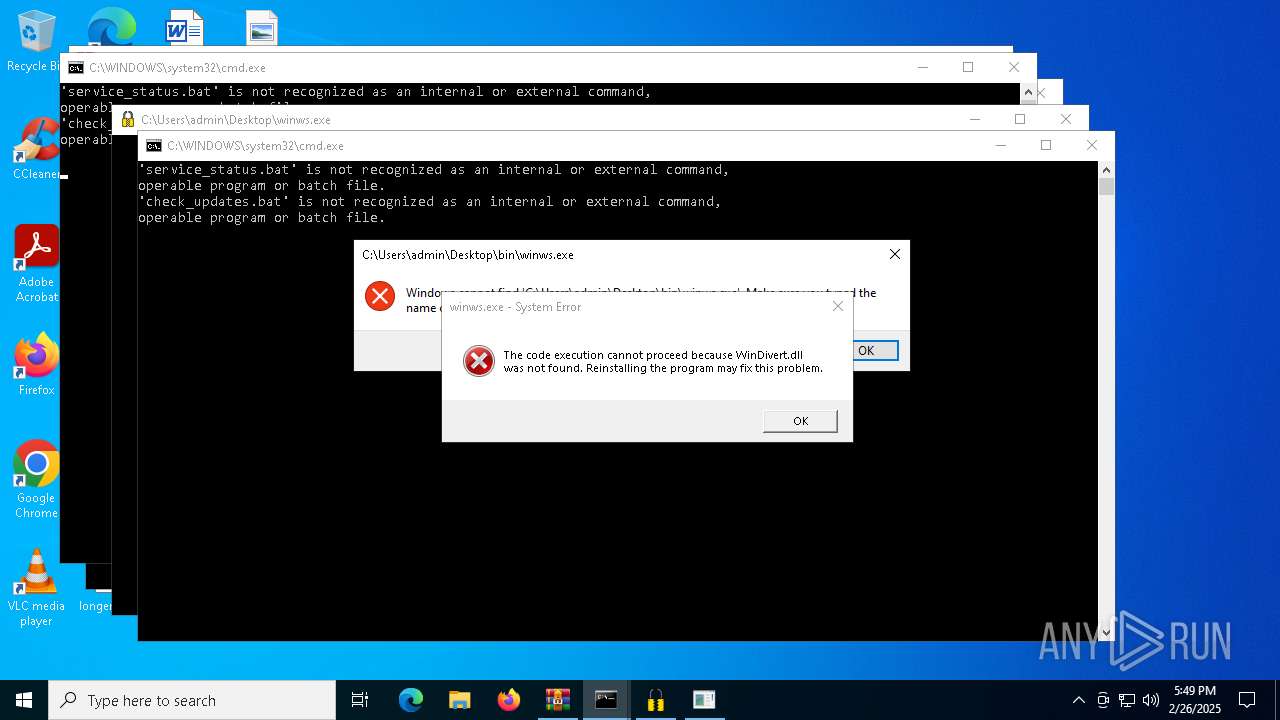
Manual execution by a user
- cmd.exe (PID: 7224)
- cmd.exe (PID: 7288)
- winws.exe (PID: 7524)
- winws.exe (PID: 7476)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7792)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 1244)
- cmd.exe (PID: 7504)
The sample compiled with english language support
- WinRAR.exe (PID: 3900)
Changes the display of characters in the console
- cmd.exe (PID: 7224)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7792)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 1244)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 8080)
Checks supported languages
- chcp.com (PID: 7364)
- chcp.com (PID: 7392)
- chcp.com (PID: 7668)
- chcp.com (PID: 7884)
- chcp.com (PID: 8084)
- chcp.com (PID: 6272)
- chcp.com (PID: 4000)
- chcp.com (PID: 7624)
- chcp.com (PID: 4996)
- chcp.com (PID: 3020)
Reads the software policy settings
- slui.exe (PID: 7776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 383 |
| UncompressedSize: | 762 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | discord.bat |
Total processes
186
Monitored processes
53
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | sc delete zapret | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | sc query "zapret" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | net stop "WinDivert" | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\service_status.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | sc delete "WinDivert" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3020 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3132 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3900 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.6.3.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4000 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 626
Read events
7 618
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3900) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3900) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3900) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3900) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.6.3.rar | |||
| (PID) Process: | (3900) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3900) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3900) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3900) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7908 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:79E333FDAA8296DAECC3AE43FDF3F5F8 | SHA256:32D3EE39DC1802E08C76CA373B19FB99C1EB95C3A5400AC0F84C905AE41B726B | |||
| 7908 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gnrbvjwp.dzo.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7908 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jysnyjt2.02l.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
25
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
456 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
456 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3008 | backgroundTaskHost.exe | 2.21.65.132:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |