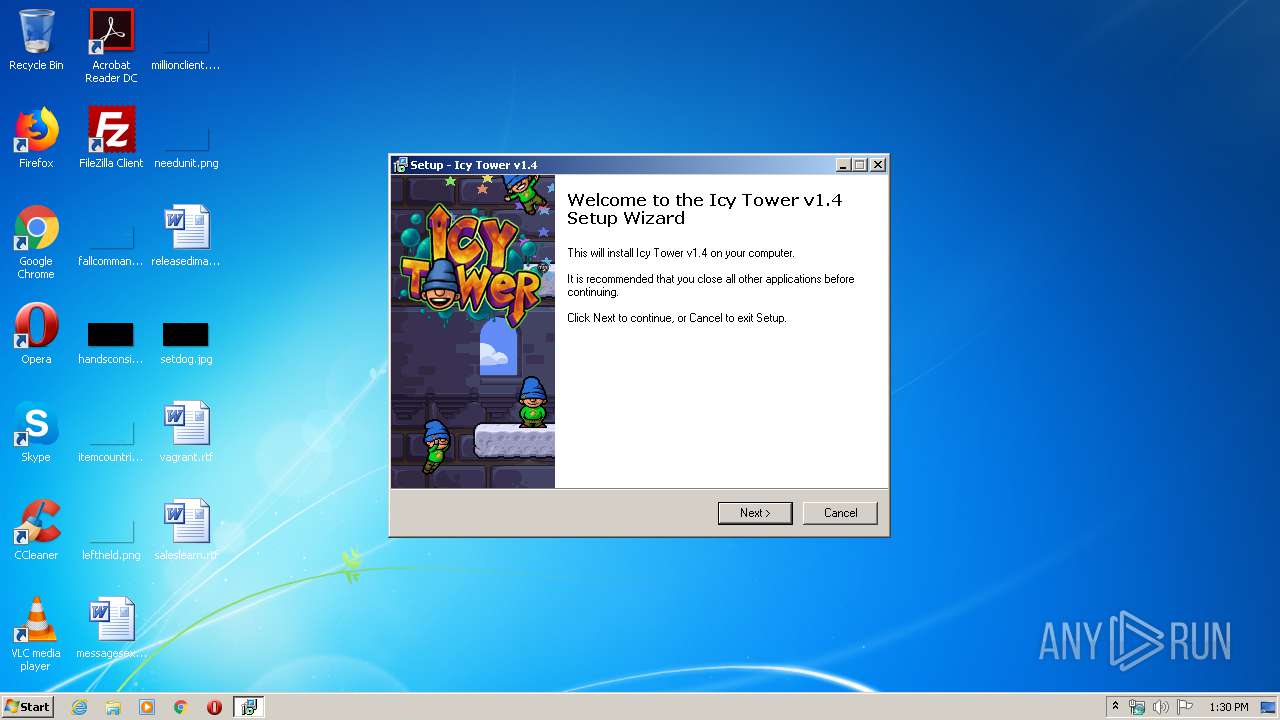
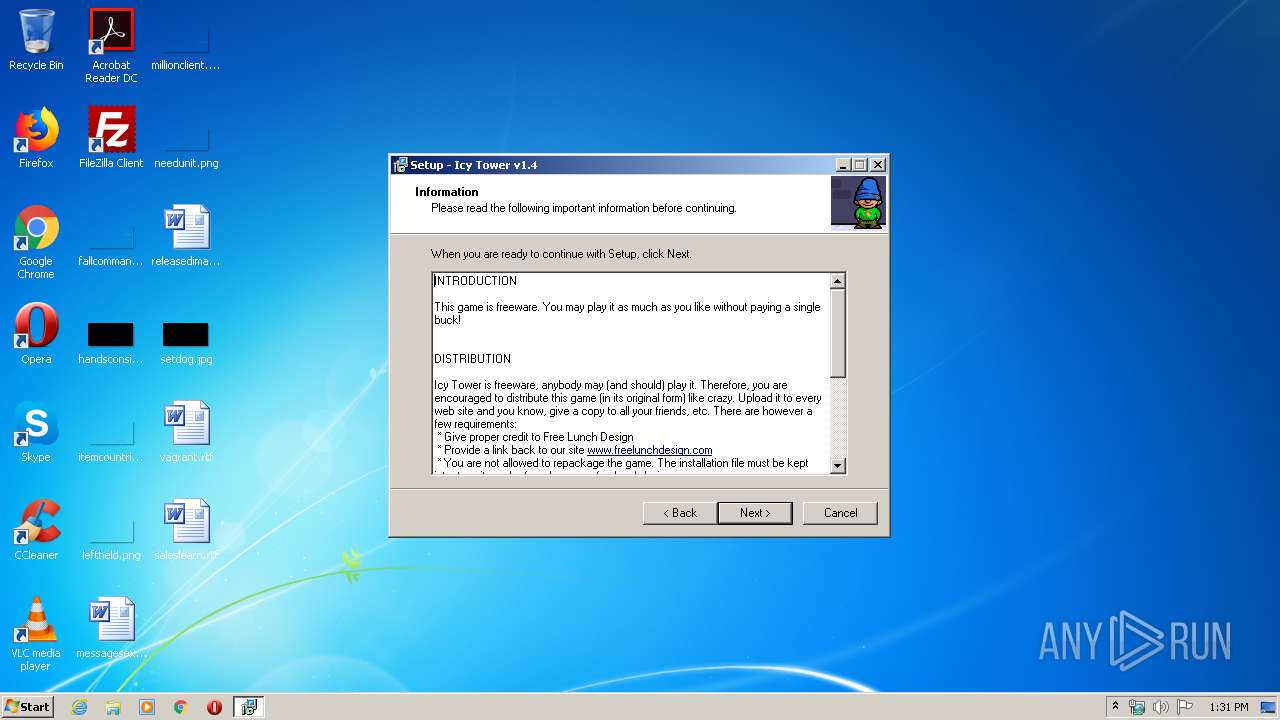
| File name: | icytower14_install.exe |
| Full analysis: | https://app.any.run/tasks/5c7c486e-53a9-4636-bac9-78f2d46de868 |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2020, 12:30:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A3C9078F3D37A7B5D824122502F770B3 |
| SHA1: | 419AAB2CFD09544FA618EC9AB1D70F48FB2F4BE8 |
| SHA256: | 132ED36BF9F6BCC3BD6599B932584BAF30BDCCAB6646F2A65F08118D03D977D7 |
| SSDEEP: | 98304:SPKDiioFlTKqcy8agYkkuZmFo7iXR/mFFJELSfNnSqvnbuJy04EJM/loYlBYQaxY:0KDiFFFcykxgMW/mFFqefNnSUnbuJy0P |
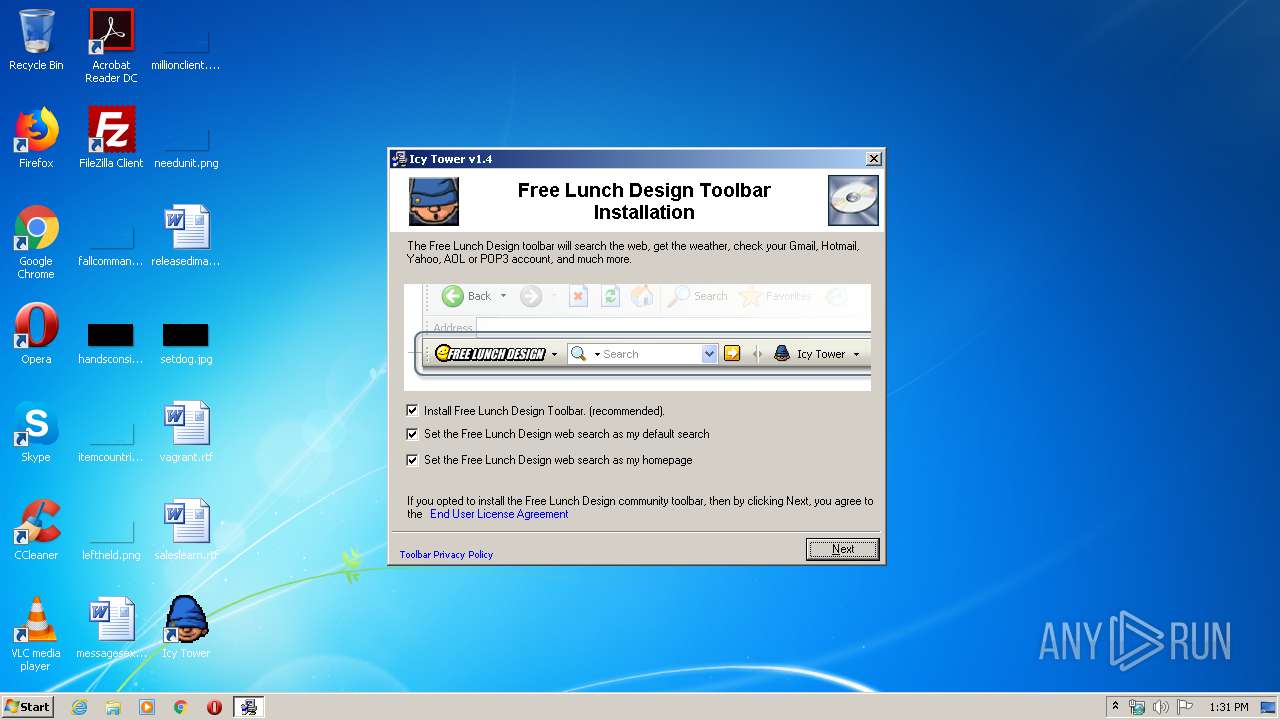
MALICIOUS
Application was dropped or rewritten from another process
- GLBE97E.tmp (PID: 3196)
- icytower14.exe (PID: 3532)
- icytower14.exe (PID: 1760)
Loads dropped or rewritten executable
- icytower14.exe (PID: 3532)
SUSPICIOUS
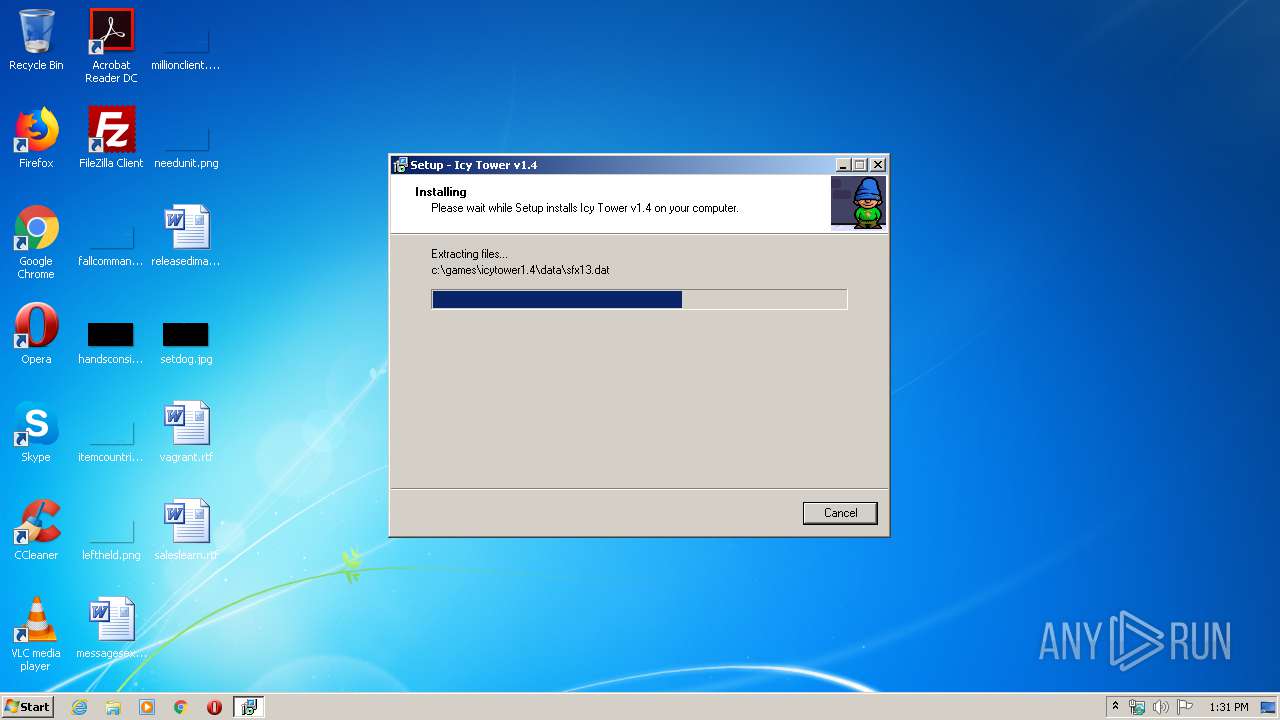
Executable content was dropped or overwritten
- icytower14_install.exe (PID: 1944)
- GLBE97E.tmp (PID: 3196)
- icytower14.exe (PID: 1760)
- is-GCQLA.tmp (PID: 3608)
Creates files in the Windows directory
- GLBE97E.tmp (PID: 3196)
Starts application with an unusual extension
- icytower14_install.exe (PID: 1944)
Removes files from Windows directory
- GLBE97E.tmp (PID: 3196)
Modifies the open verb of a shell class
- is-GCQLA.tmp (PID: 3608)
INFO
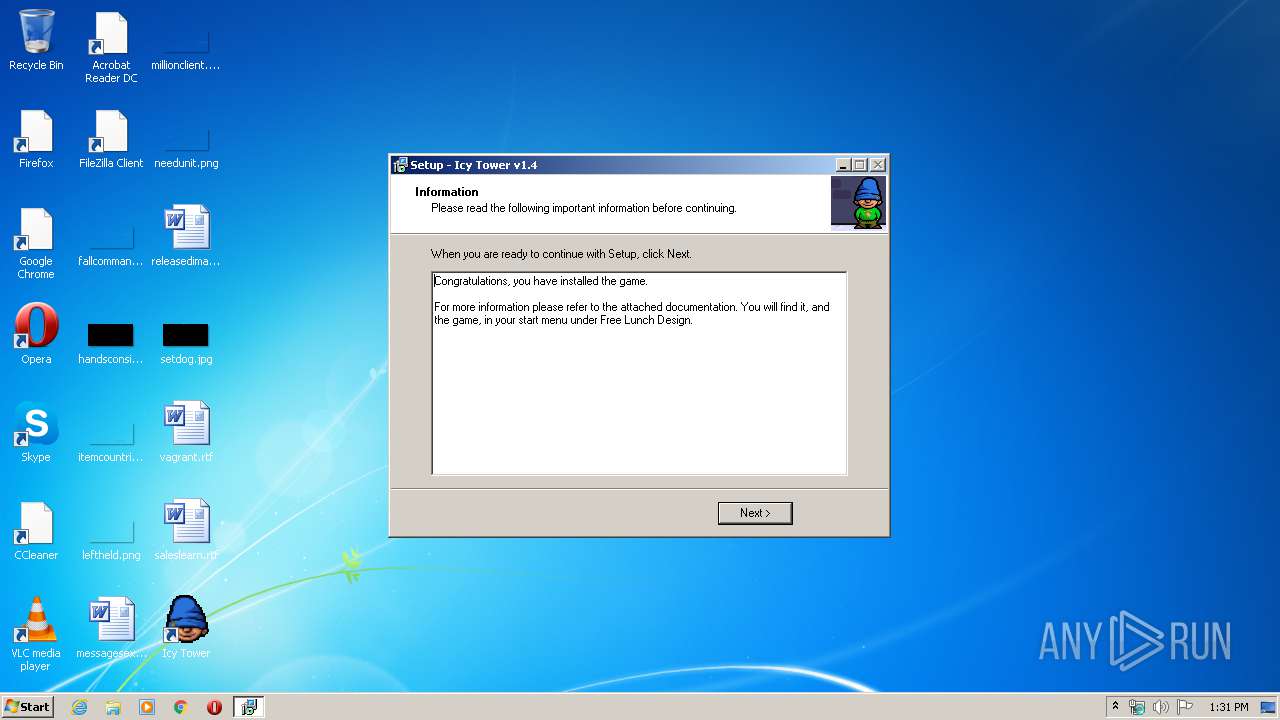
Creates files in the program directory
- is-GCQLA.tmp (PID: 3608)
Loads dropped or rewritten executable
- is-GCQLA.tmp (PID: 3608)
Application was dropped or rewritten from another process
- is-GCQLA.tmp (PID: 3608)
Creates a software uninstall entry
- is-GCQLA.tmp (PID: 3608)
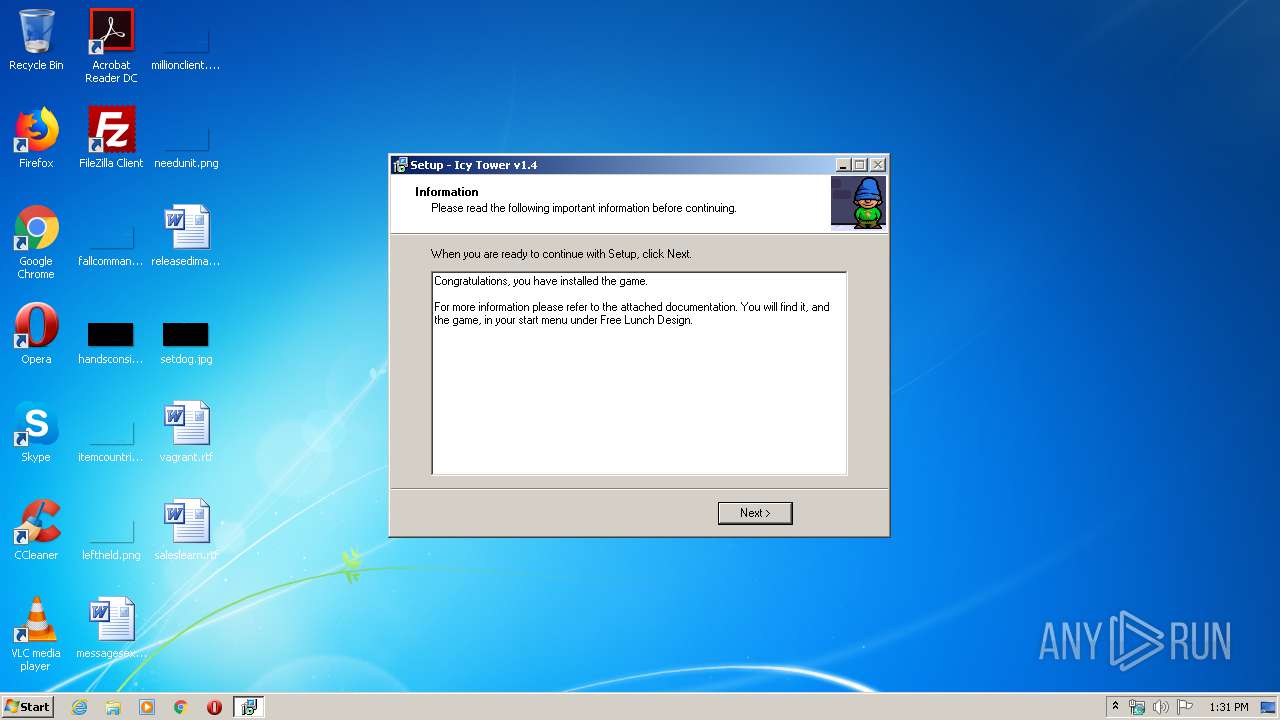
Manual execution by user
- icytower14.exe (PID: 3532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Wise Installer executable (91.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (5.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1999:04:08 22:24:47+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 512 |
| InitializedDataSize: | 5519360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.0.0 |
| ProductVersionNumber: | 1.4.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
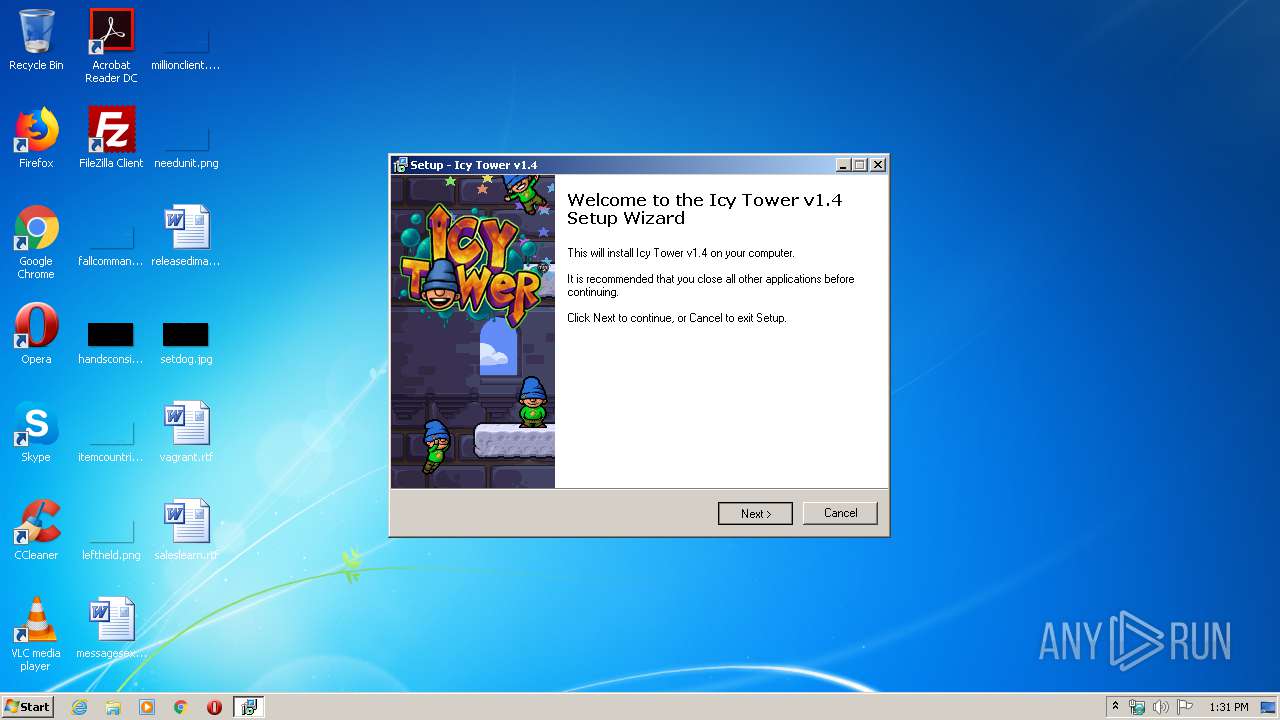
| CompanyName: | Free Lunch Design |
| FileDescription: | Icy Tower v1.4 Setup |
| FileVersion: | 1.4 |
| LegalCopyright: | Free Lunch Design |
Total processes
45
Monitored processes
6
Malicious processes
0
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1760 | "C:\Users\admin\AppData\Local\Temp\icytower14.exe" | C:\Users\admin\AppData\Local\Temp\icytower14.exe | GLBE97E.tmp | ||||||||||||
User: admin Company: Free Lunch Design Integrity Level: HIGH Description: Icy Tower v1.4 Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1944 | "C:\Users\admin\AppData\Local\Temp\icytower14_install.exe" | C:\Users\admin\AppData\Local\Temp\icytower14_install.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3196 | C:\Users\admin\AppData\Local\Temp\GLBE97E.tmp 4736 C:\Users\admin\AppData\Local\Temp\ICYTOW~1.EXE | C:\Users\admin\AppData\Local\Temp\GLBE97E.tmp | icytower14_install.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
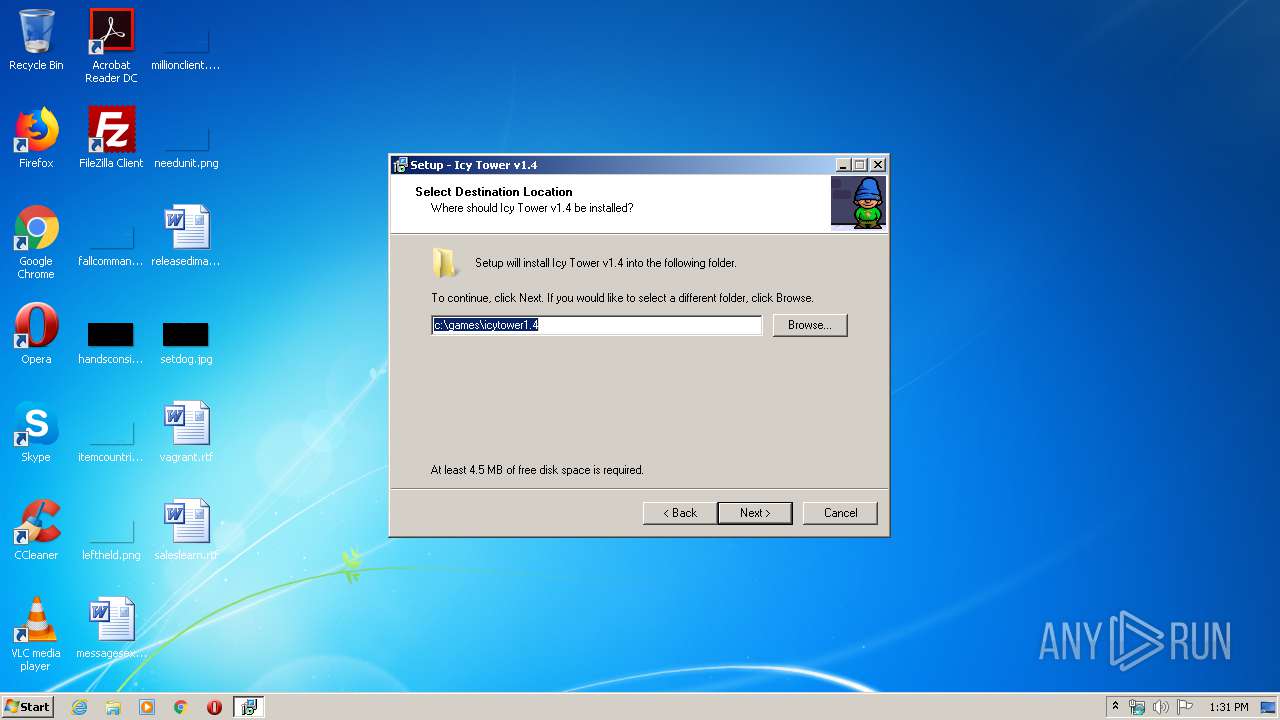
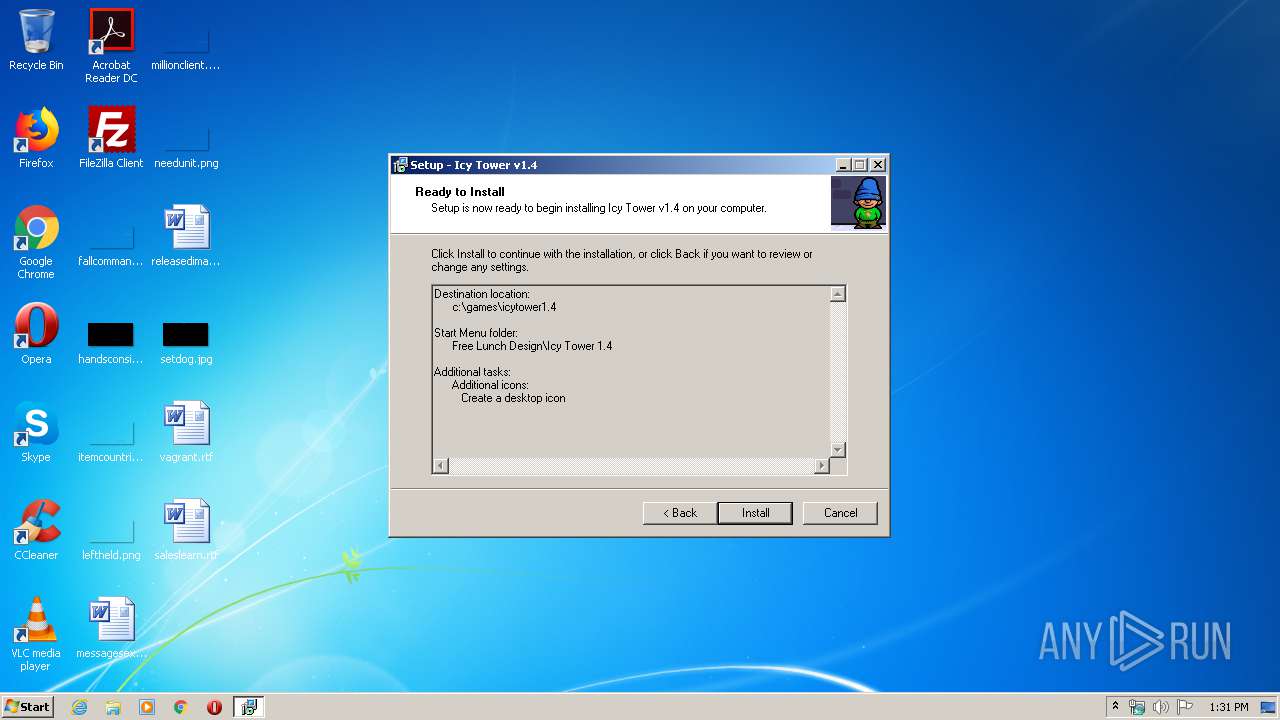
| 3532 | "C:\games\icytower1.4\icytower14.exe" | C:\games\icytower1.4\icytower14.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3588 | "C:\Users\admin\AppData\Local\Temp\icytower14_install.exe" | C:\Users\admin\AppData\Local\Temp\icytower14_install.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3608 | "C:\Users\admin\AppData\Local\Temp\is-OC829.tmp\is-GCQLA.tmp" /SL4 $10023E "C:\Users\admin\AppData\Local\Temp\icytower14.exe" 3024879 52736 | C:\Users\admin\AppData\Local\Temp\is-OC829.tmp\is-GCQLA.tmp | icytower14.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.46.0.0 Modules
| |||||||||||||||
Total events
827
Read events
779
Write events
48
Delete events
0
Modification events
| (PID) Process: | (3196) GLBE97E.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3196) GLBE97E.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3608) is-GCQLA.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.itr |
| Operation: | write | Name: | |
Value: IT14replay | |||
| (PID) Process: | (3608) is-GCQLA.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\IT14replay |
| Operation: | write | Name: | |
Value: Icy Tower 1.4 replay | |||
| (PID) Process: | (3608) is-GCQLA.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\IT14replay\DefaultIcon |
| Operation: | write | Name: | |
Value: c:\games\icytower1.4\icytower14.exe,0 | |||
| (PID) Process: | (3608) is-GCQLA.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\IT14replay\shell\open\command |
| Operation: | write | Name: | |
Value: "c:\games\icytower1.4\icytower14.exe" "%1" | |||
| (PID) Process: | (3608) is-GCQLA.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.itp |
| Operation: | write | Name: | |
Value: IT14Profile | |||
| (PID) Process: | (3608) is-GCQLA.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\IT14Profile |
| Operation: | write | Name: | |
Value: Icy Tower 1.4 profile | |||
| (PID) Process: | (3608) is-GCQLA.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\IT14Profile\DefaultIcon |
| Operation: | write | Name: | |
Value: c:\games\icytower1.4\icytower14.exe,0 | |||
| (PID) Process: | (3608) is-GCQLA.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\IT14Profile\shell\open\command |
| Operation: | write | Name: | |
Value: "c:\games\icytower1.4\icytower14.exe" "%1" | |||
Executable files
12
Suspicious files
3
Text files
65
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3196 | GLBE97E.tmp | C:\Users\admin\AppData\Local\Temp\~GLH0000.TMP | — | |
MD5:— | SHA256:— | |||
| 3608 | is-GCQLA.tmp | C:\games\icytower1.4\is-LA3K5.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | is-GCQLA.tmp | C:\games\icytower1.4\is-PQ8A1.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | is-GCQLA.tmp | C:\games\icytower1.4\is-TN4KJ.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | is-GCQLA.tmp | C:\games\icytower1.4\is-A9IRN.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | is-GCQLA.tmp | C:\games\icytower1.4\is-TA4QH.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | is-GCQLA.tmp | C:\games\icytower1.4\is-R5SSR.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | is-GCQLA.tmp | C:\games\icytower1.4\is-KTKHL.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | is-GCQLA.tmp | C:\games\icytower1.4\is-86F80.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | is-GCQLA.tmp | C:\games\icytower1.4\is-S3IUV.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report