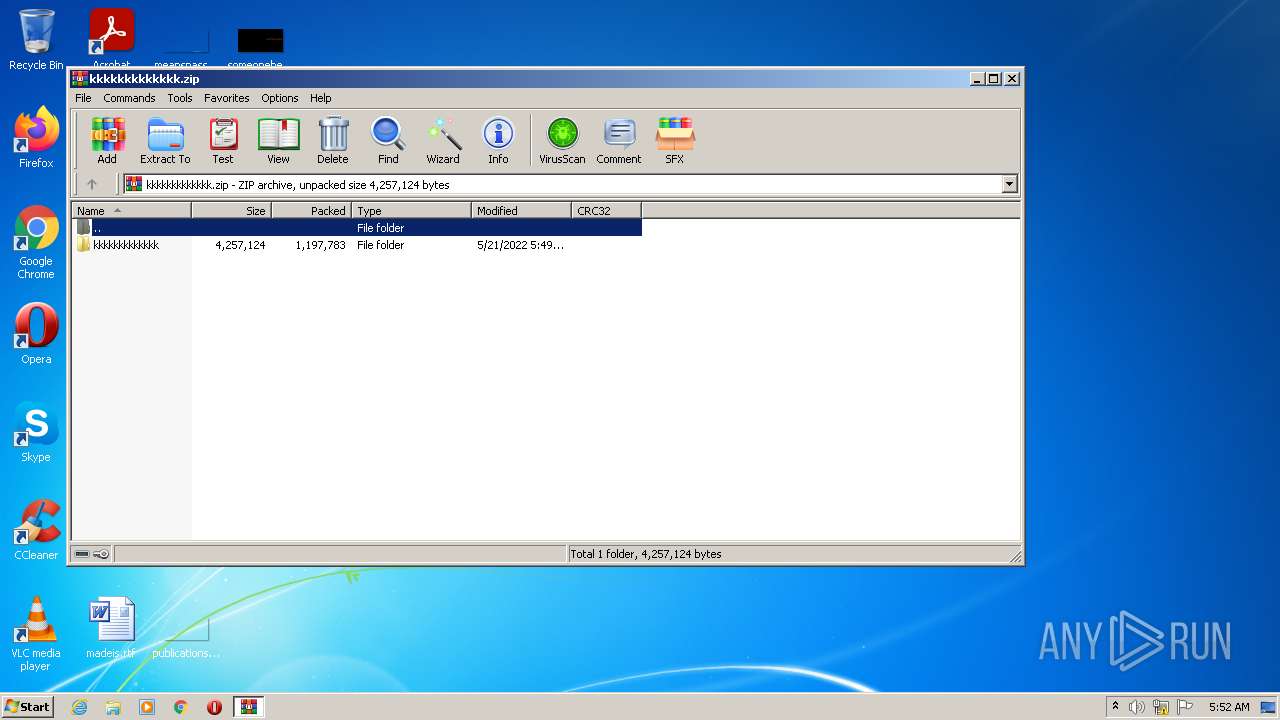
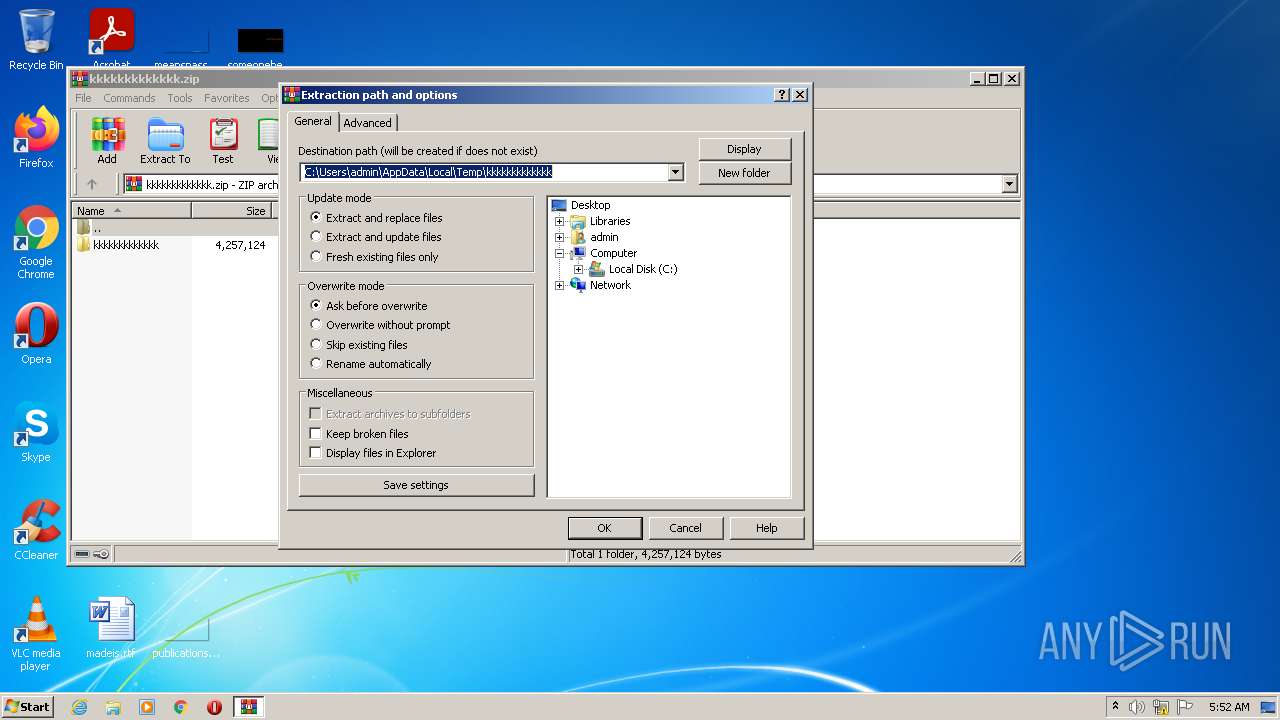
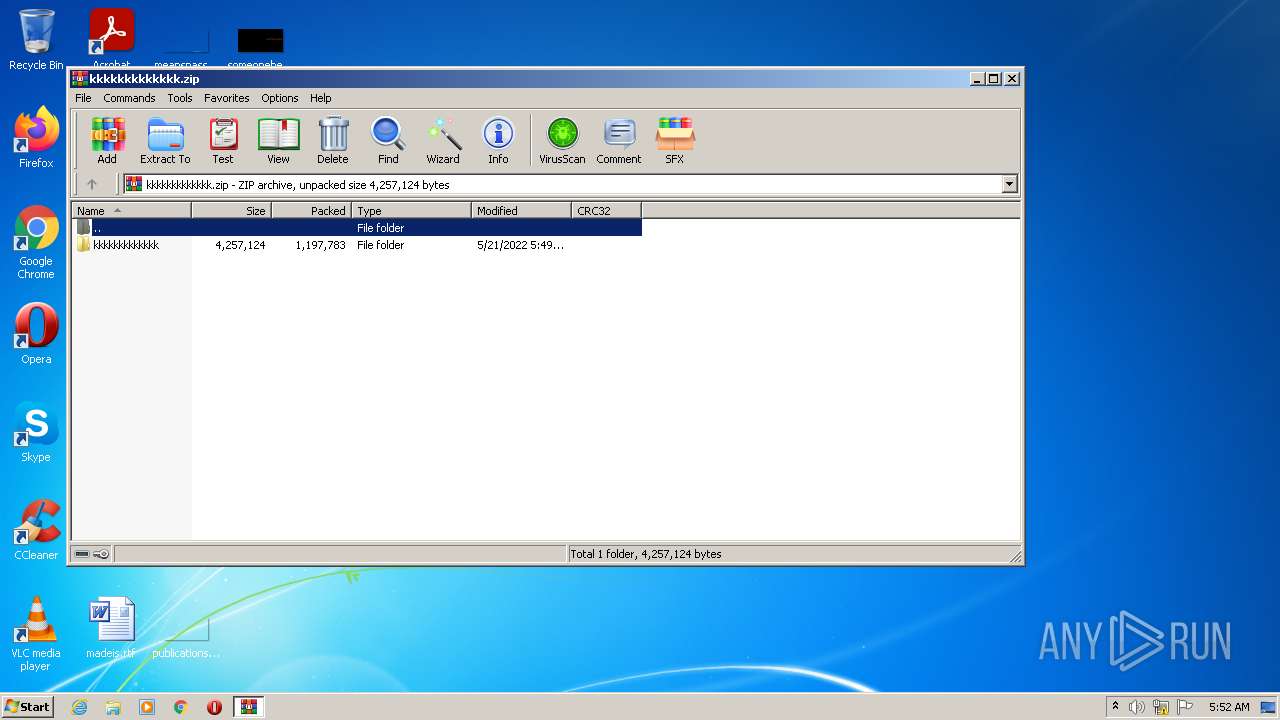
| File name: | kkkkkkkkkkkkk.zip |
| Full analysis: | https://app.any.run/tasks/df80bce5-253a-4127-805e-44b6930419ac |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 04:52:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 54ECCFEC337C3A34CCB747753381C49A |
| SHA1: | 9AA29E1A165EF331E65652F34BA007514E627110 |
| SHA256: | 13286BB8E7617B9BAFF9C754660A9F8CD32878473ECED61AE06709D0AEF42536 |
| SSDEEP: | 24576:jmeJdF28MRd6ZiyNlP1QI9CXSlxtKN5HXj32uOHtE+1AEdr:jmAU8MRyN71QCCCgNlj32uCtEgxr |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 2860)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3564)
- VitorBotdeViews.exe (PID: 1728)
Application was dropped or rewritten from another process
- VitorBotdeViews.exe (PID: 1728)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2860)
- VitorBotdeViews.exe (PID: 1728)
Reads the computer name
- WinRAR.exe (PID: 2860)
- VitorBotdeViews.exe (PID: 1728)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2860)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2860)
Reads Microsoft Outlook installation path
- VitorBotdeViews.exe (PID: 1728)
- iexplore.exe (PID: 7340)
Reads Environment values
- VitorBotdeViews.exe (PID: 1728)
Reads internet explorer settings
- VitorBotdeViews.exe (PID: 1728)
Creates files in the user directory
- VitorBotdeViews.exe (PID: 1728)
Starts Internet Explorer
- VitorBotdeViews.exe (PID: 1728)
INFO
Manual execution by user
- NOTEPAD.EXE (PID: 1416)
- VitorBotdeViews.exe (PID: 1728)
Checks supported languages
- NOTEPAD.EXE (PID: 1416)
- iexplore.exe (PID: 5316)
- iexplore.exe (PID: 7340)
Reads settings of System Certificates
- VitorBotdeViews.exe (PID: 1728)
- iexplore.exe (PID: 7340)
- iexplore.exe (PID: 5316)
Reads the computer name
- iexplore.exe (PID: 5316)
- iexplore.exe (PID: 7340)
Reads internet explorer settings
- iexplore.exe (PID: 7340)
Application launched itself
- iexplore.exe (PID: 5316)
Changes internet zones settings
- iexplore.exe (PID: 5316)
Checks Windows Trust Settings
- iexplore.exe (PID: 7340)
- iexplore.exe (PID: 5316)
Adds / modifies Windows certificates
- iexplore.exe (PID: 5316)
Changes settings of System certificates
- iexplore.exe (PID: 5316)
Reads the date of Windows installation
- iexplore.exe (PID: 5316)
Creates files in the user directory
- iexplore.exe (PID: 7340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
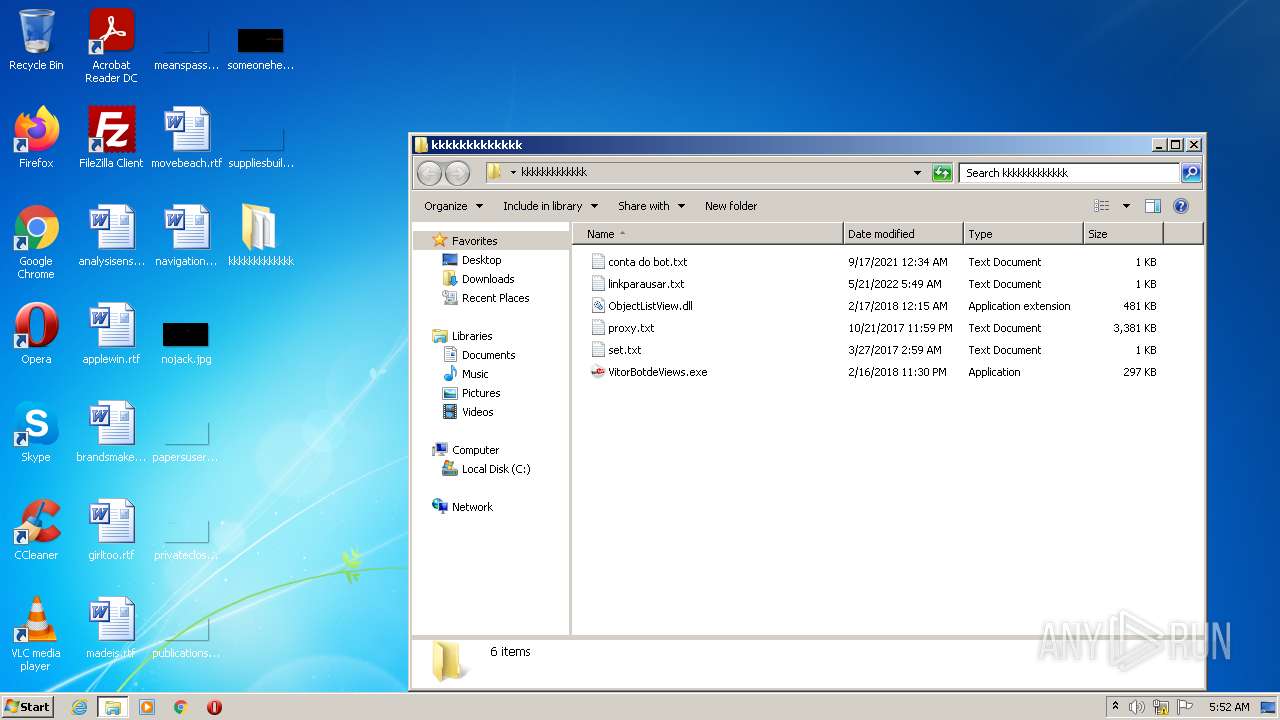
| ZipFileName: | kkkkkkkkkkkkk/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2022:05:21 01:49:22 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 788 |
Total processes
43
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
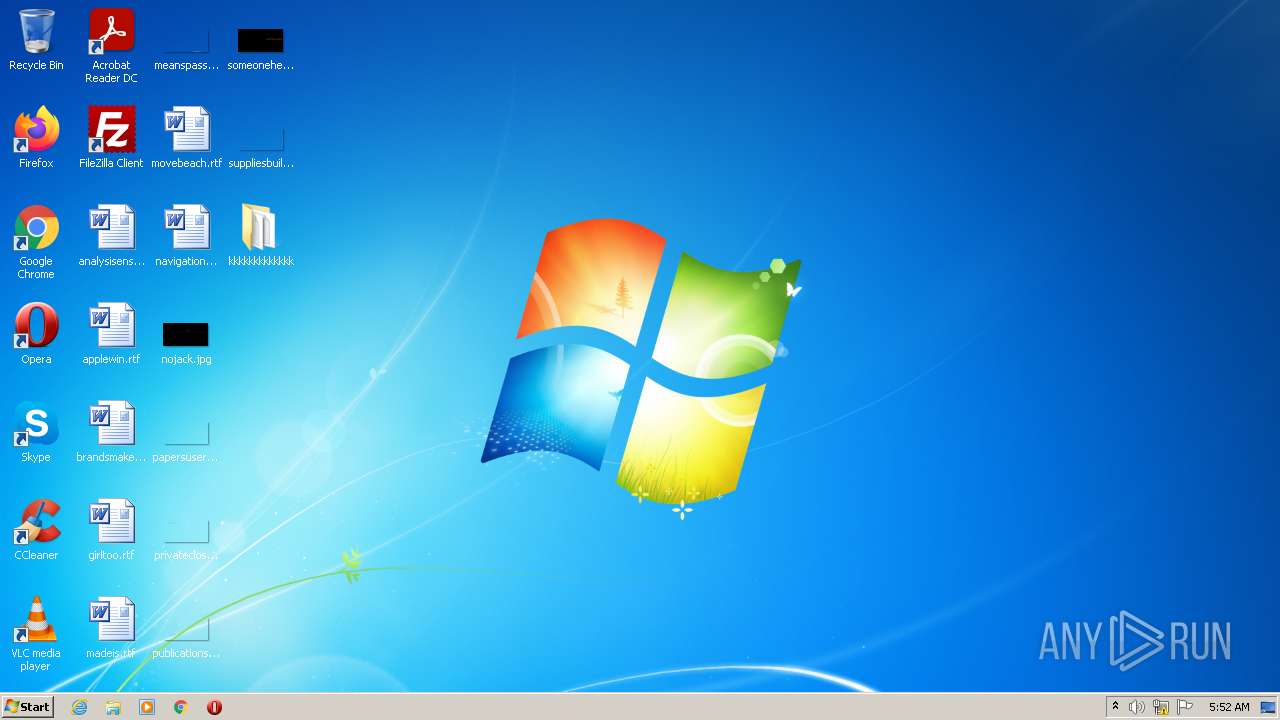
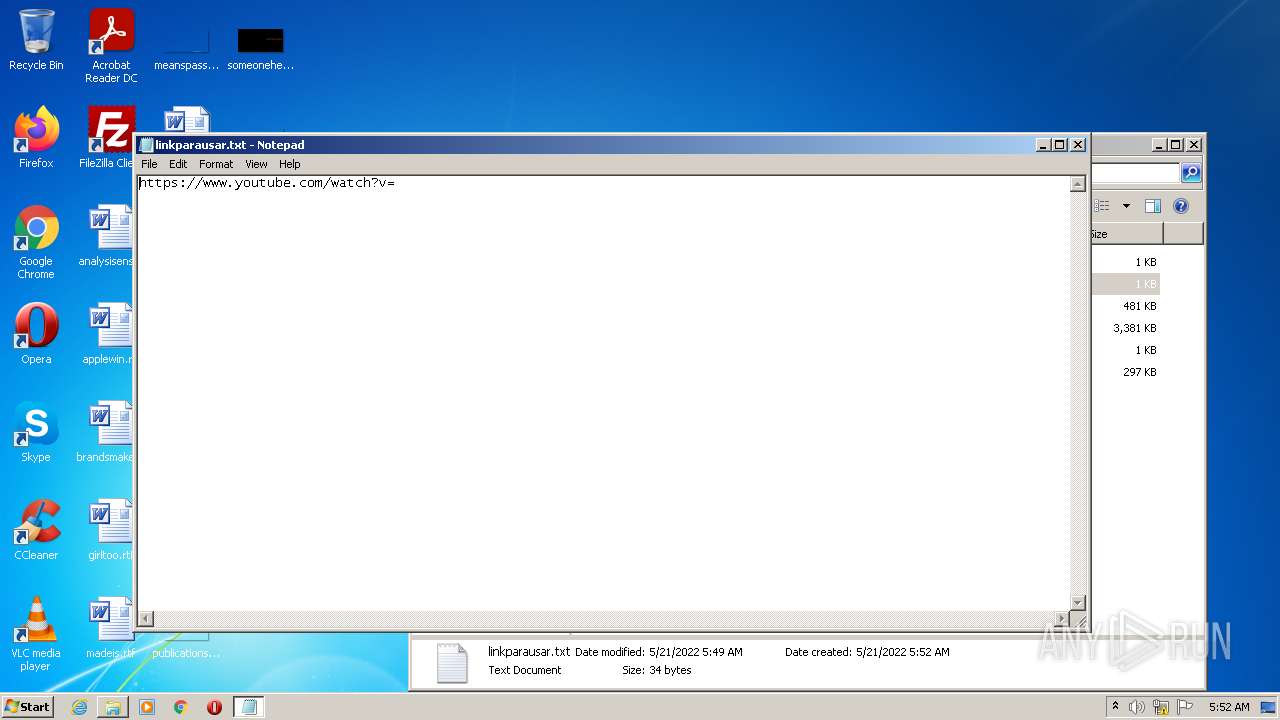
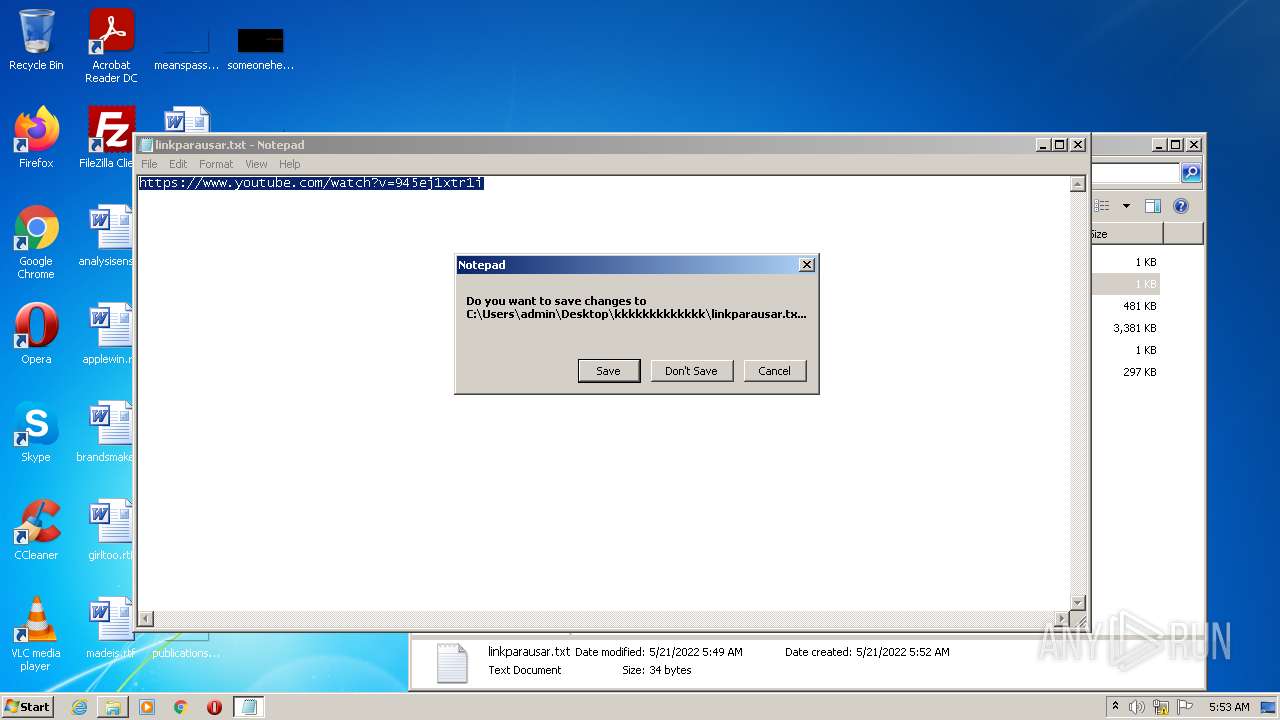
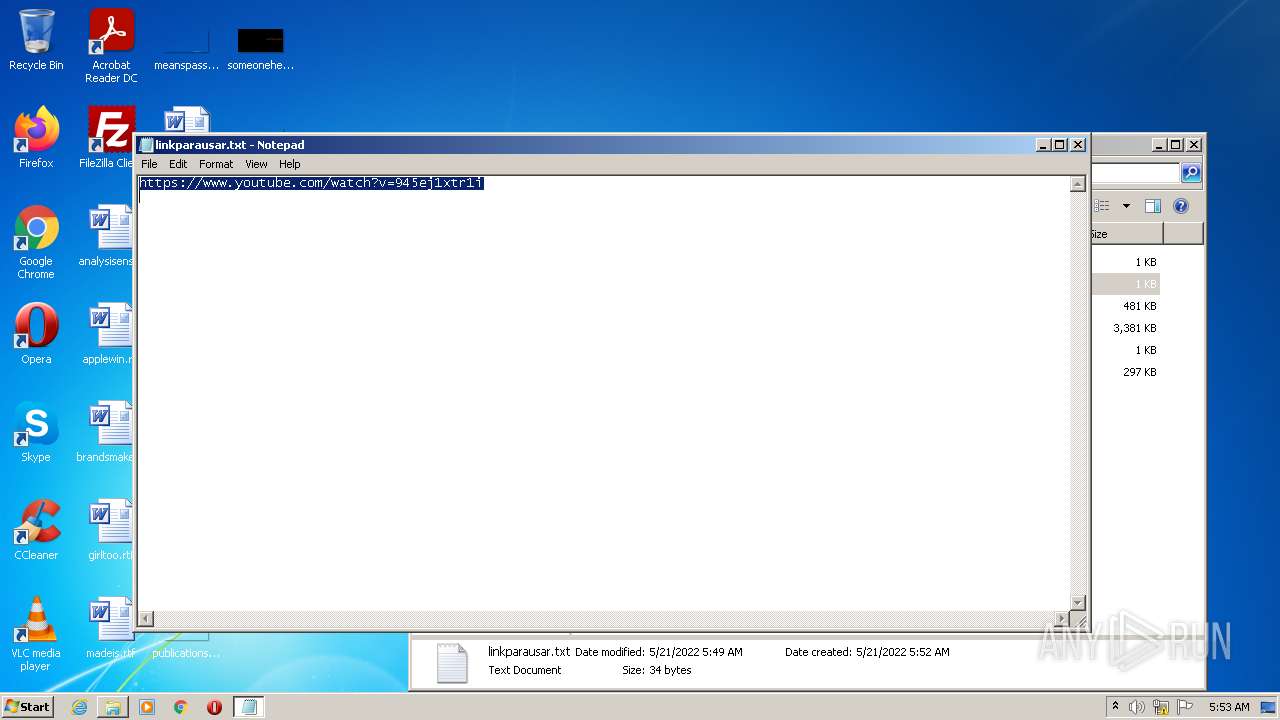
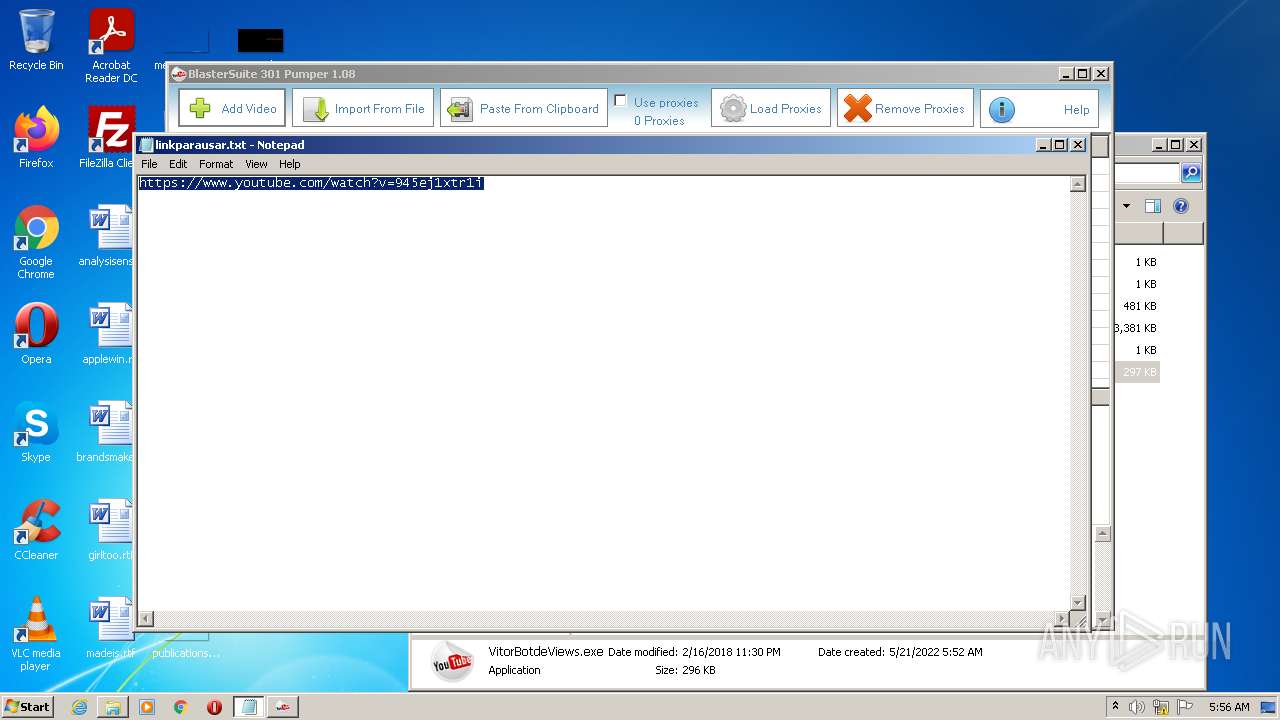
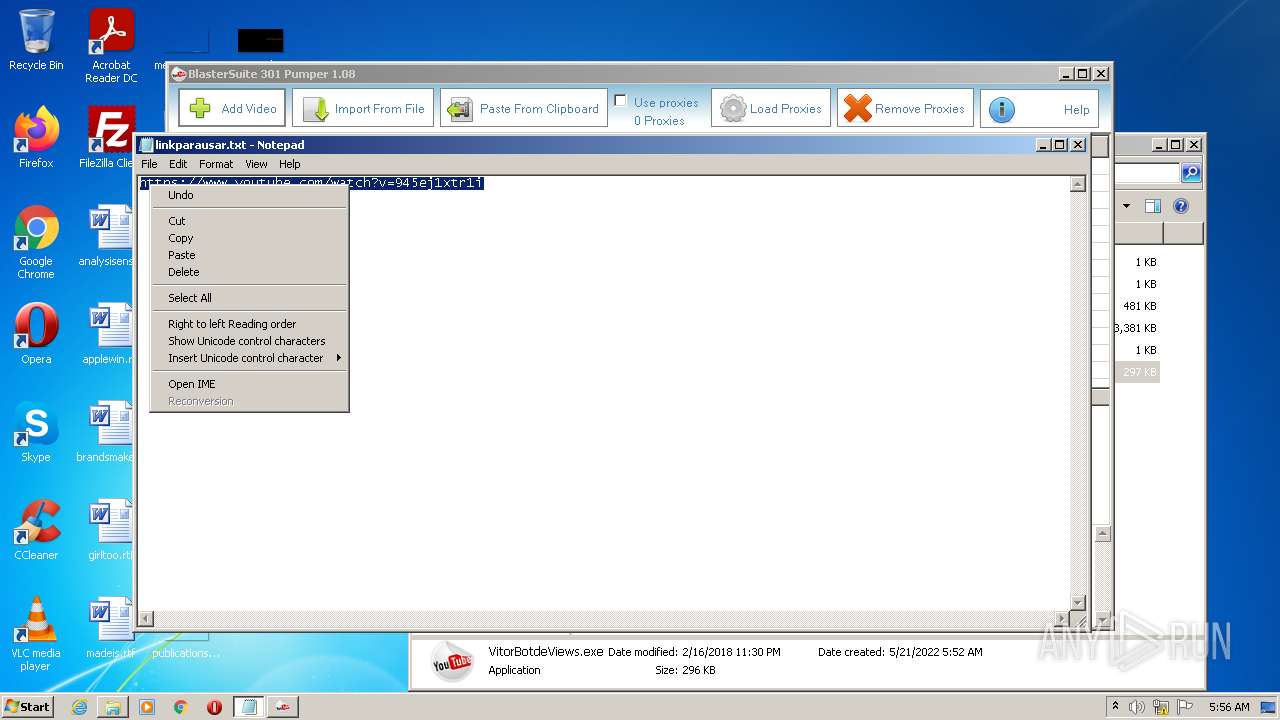
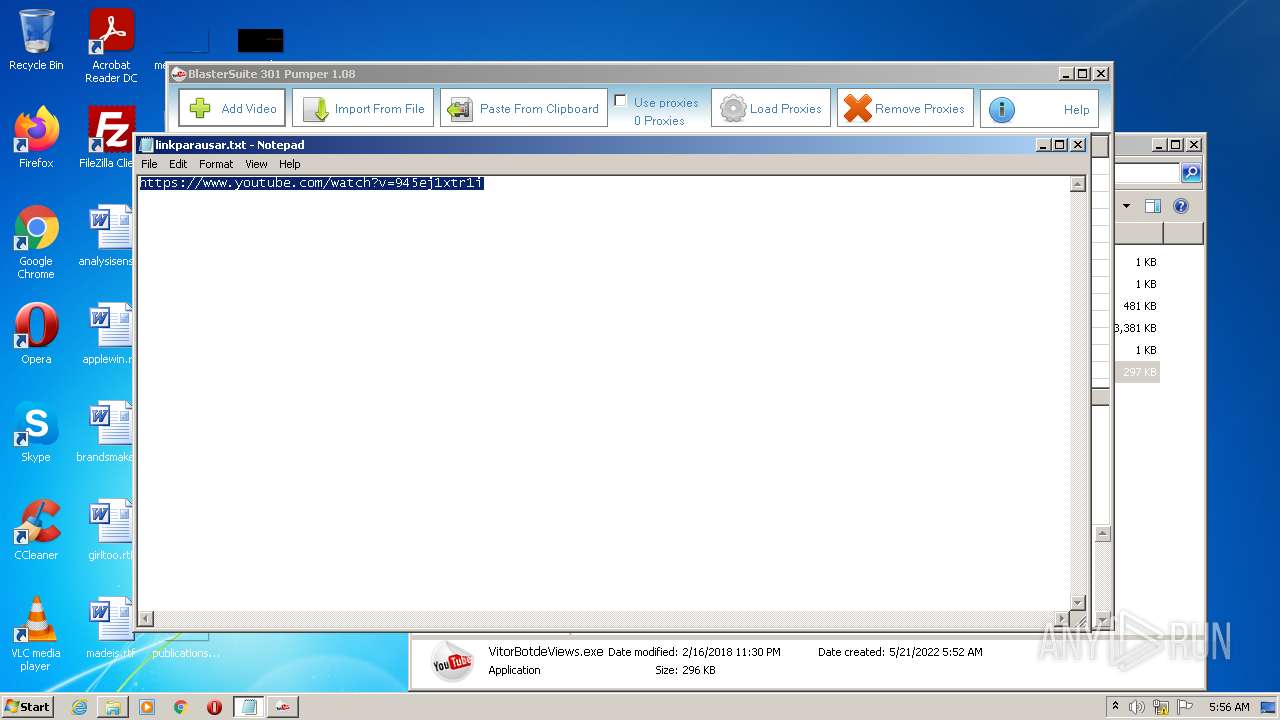
| 1416 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\kkkkkkkkkkkkk\linkparausar.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
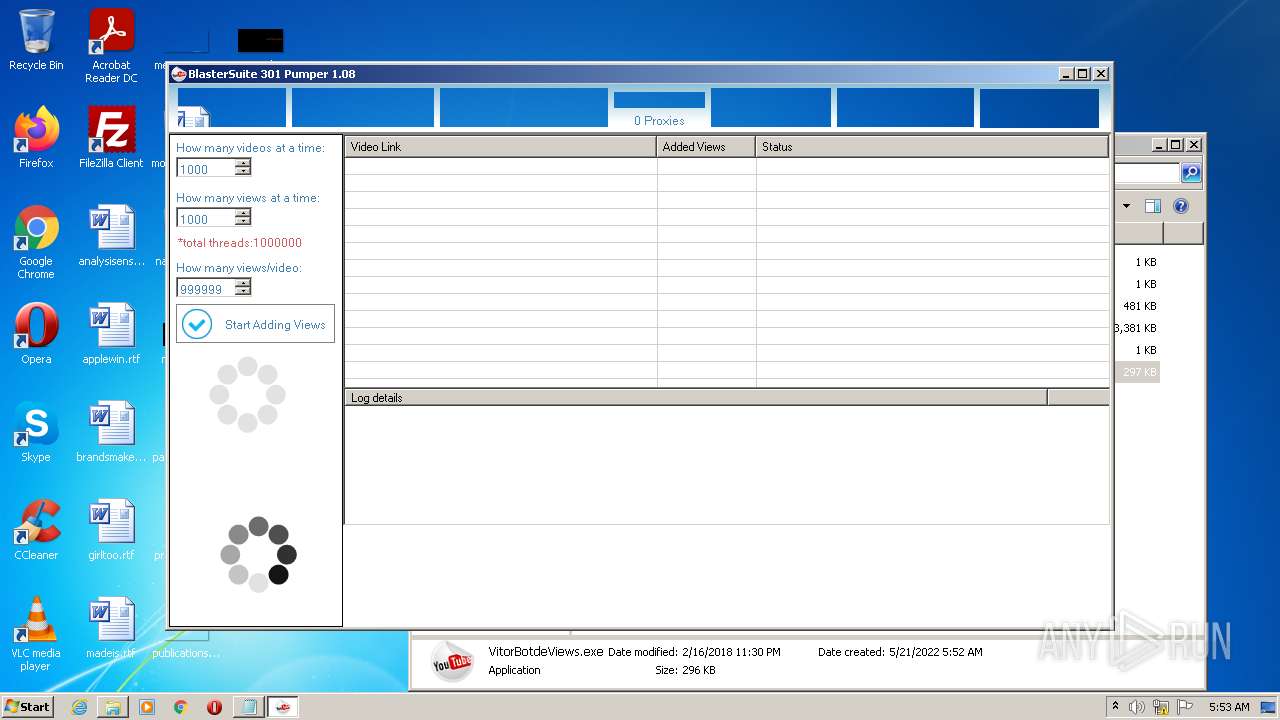
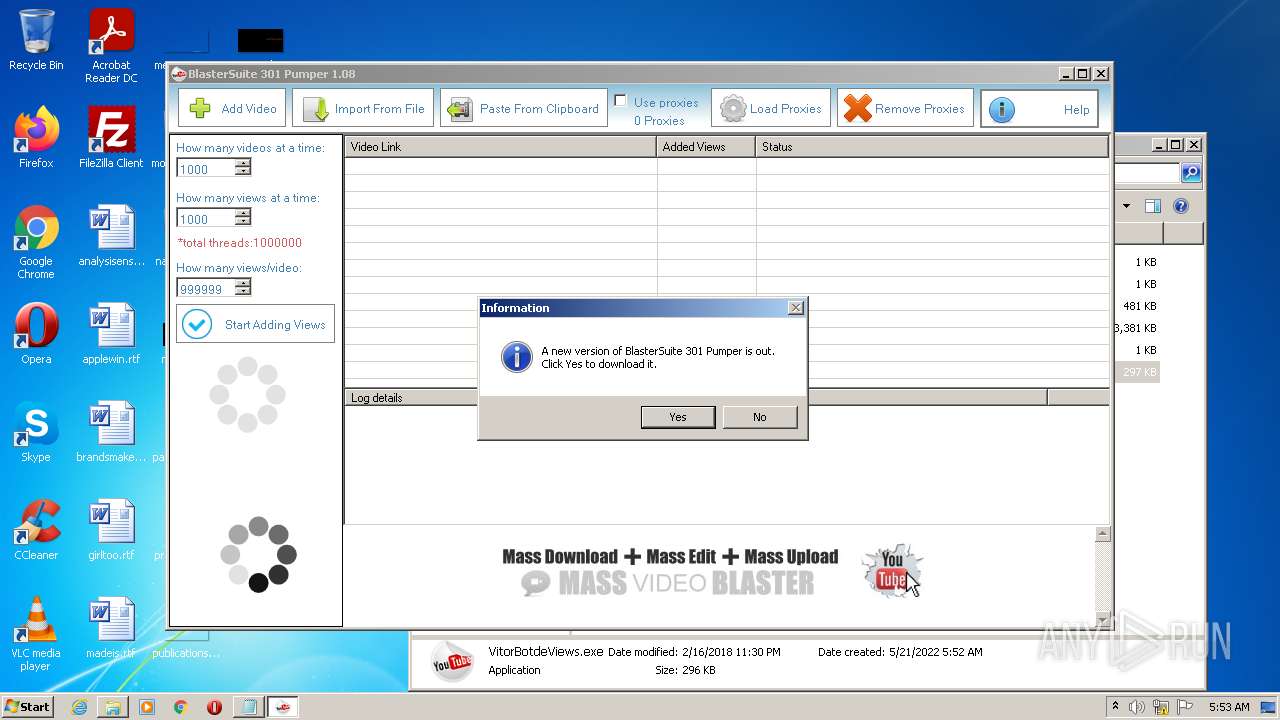
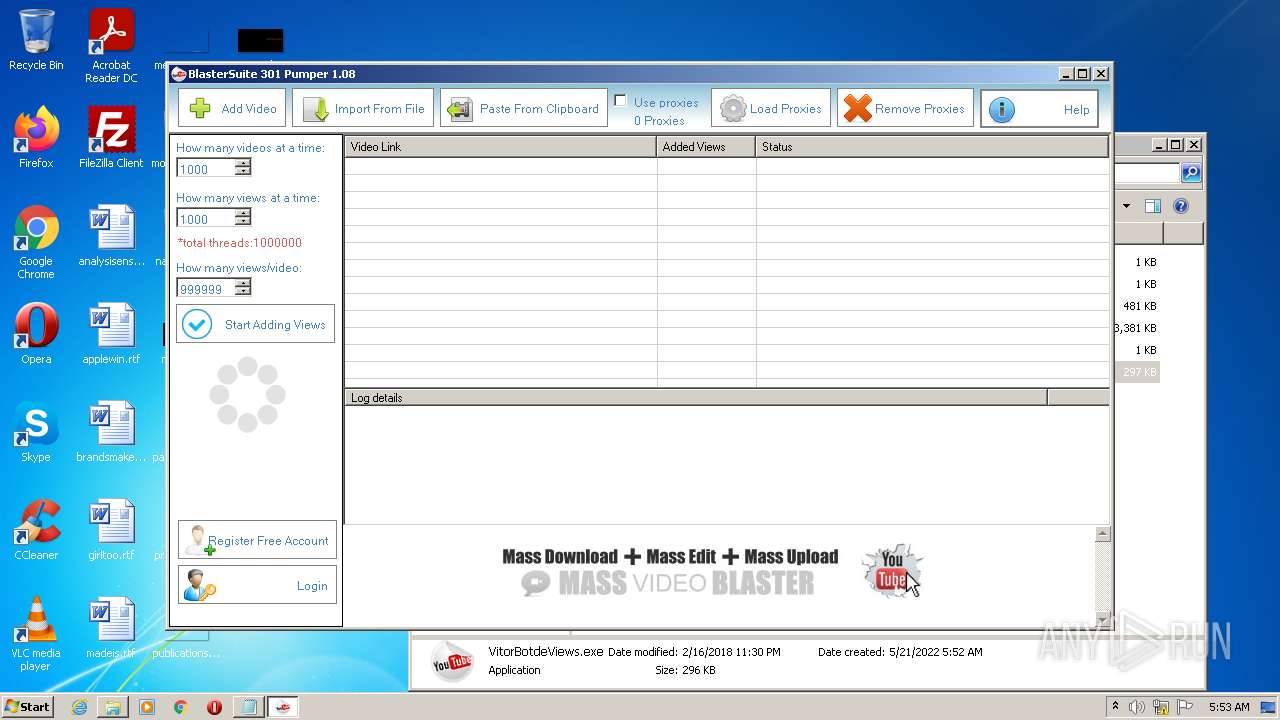
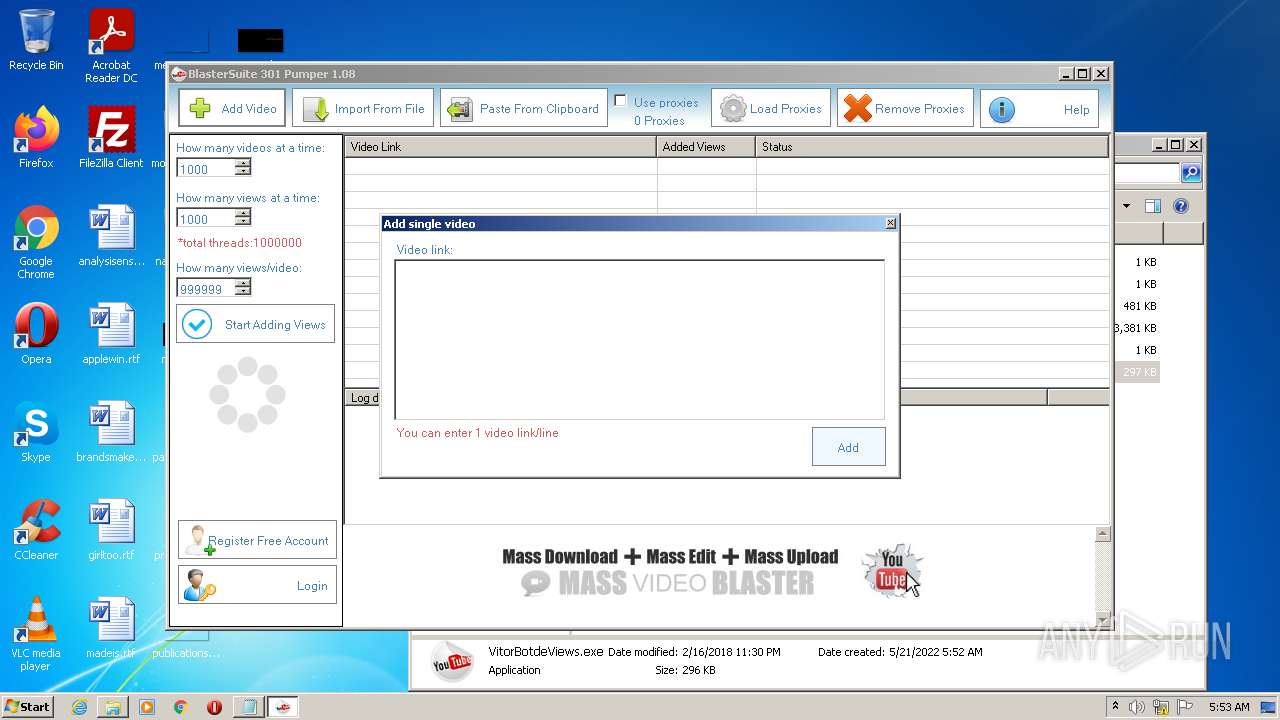
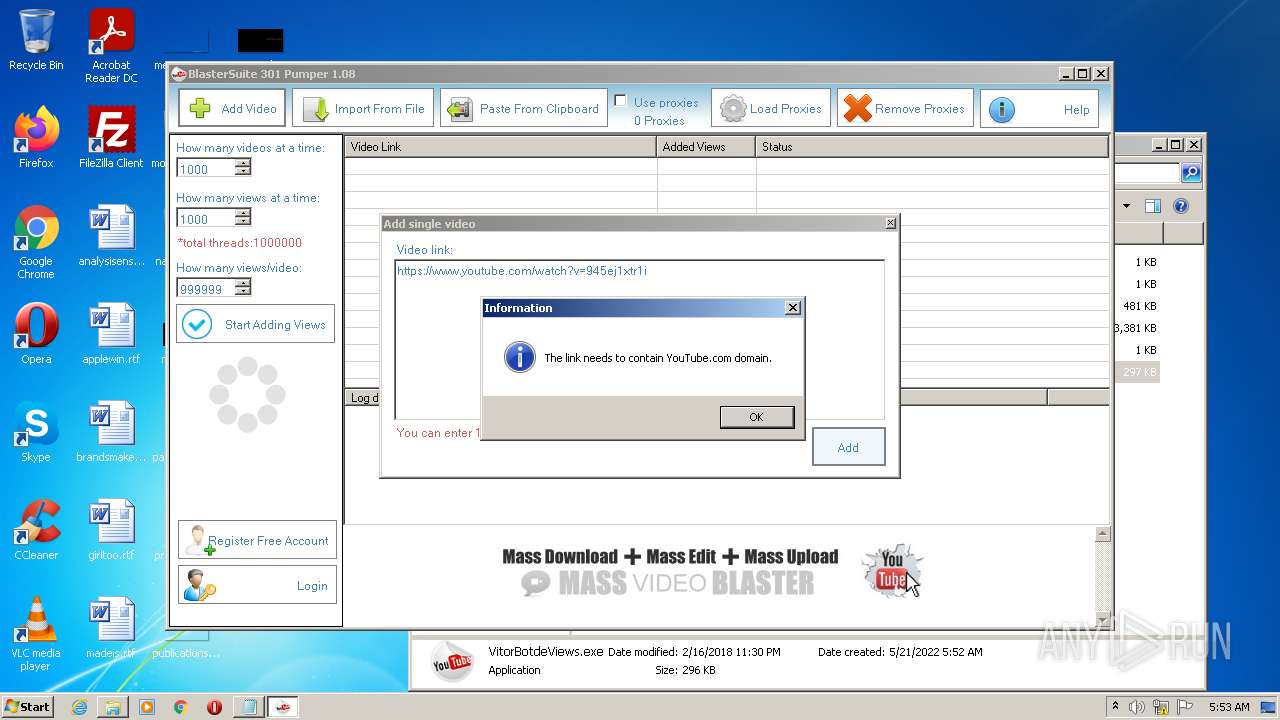
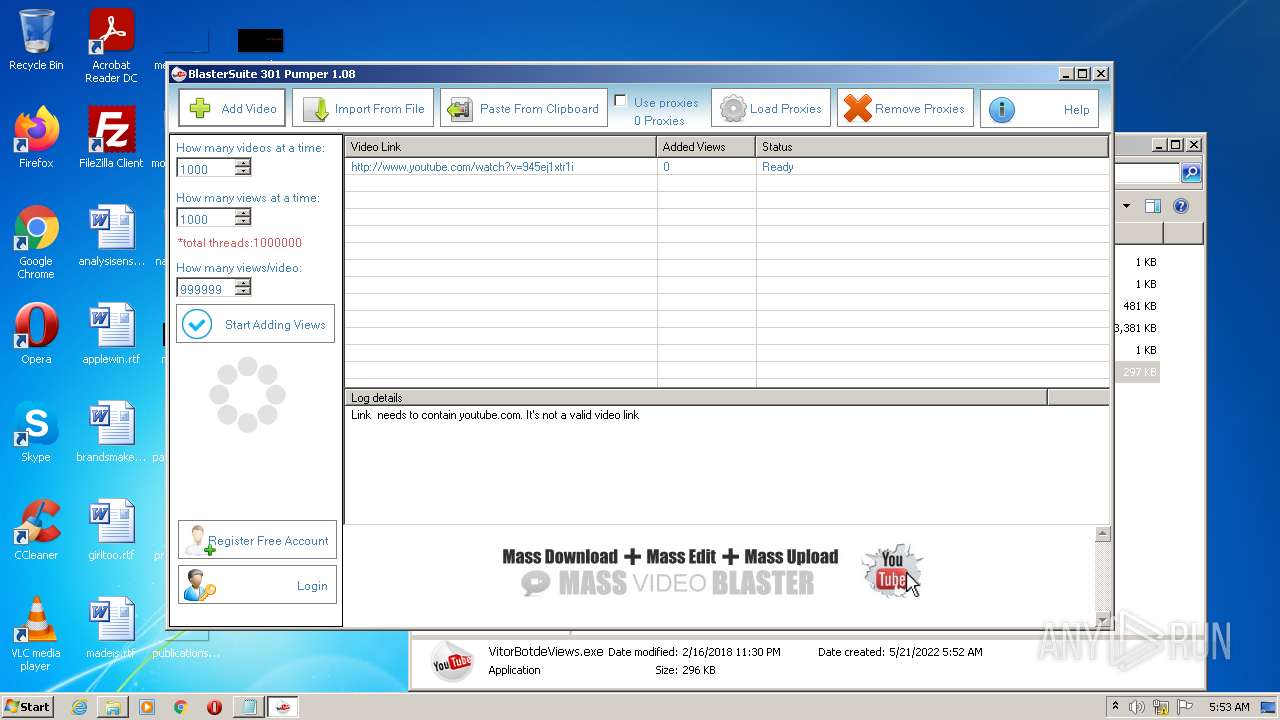
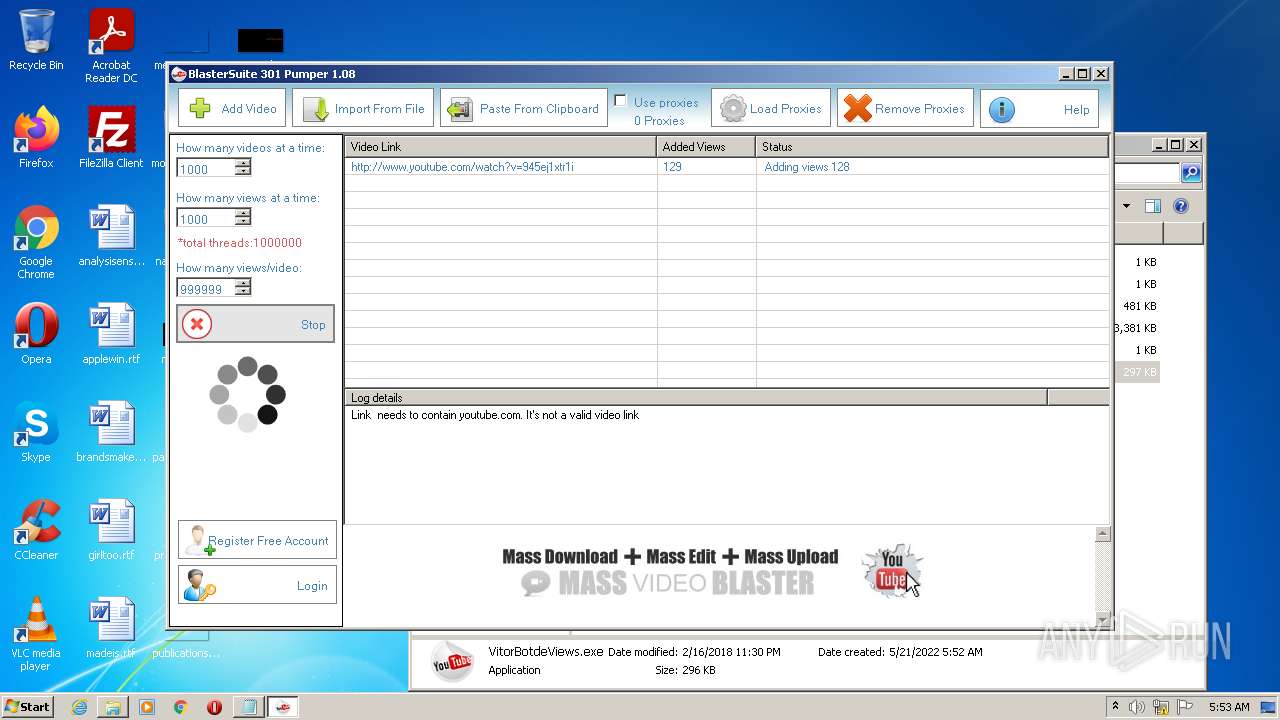
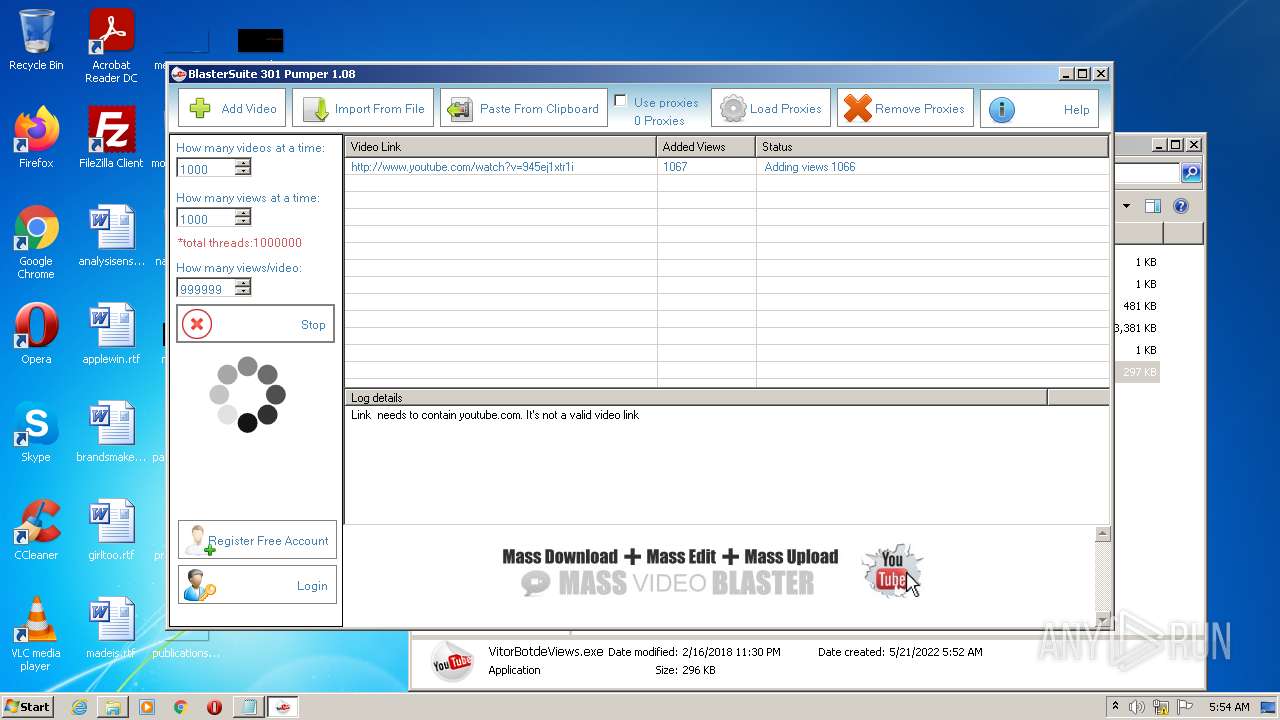
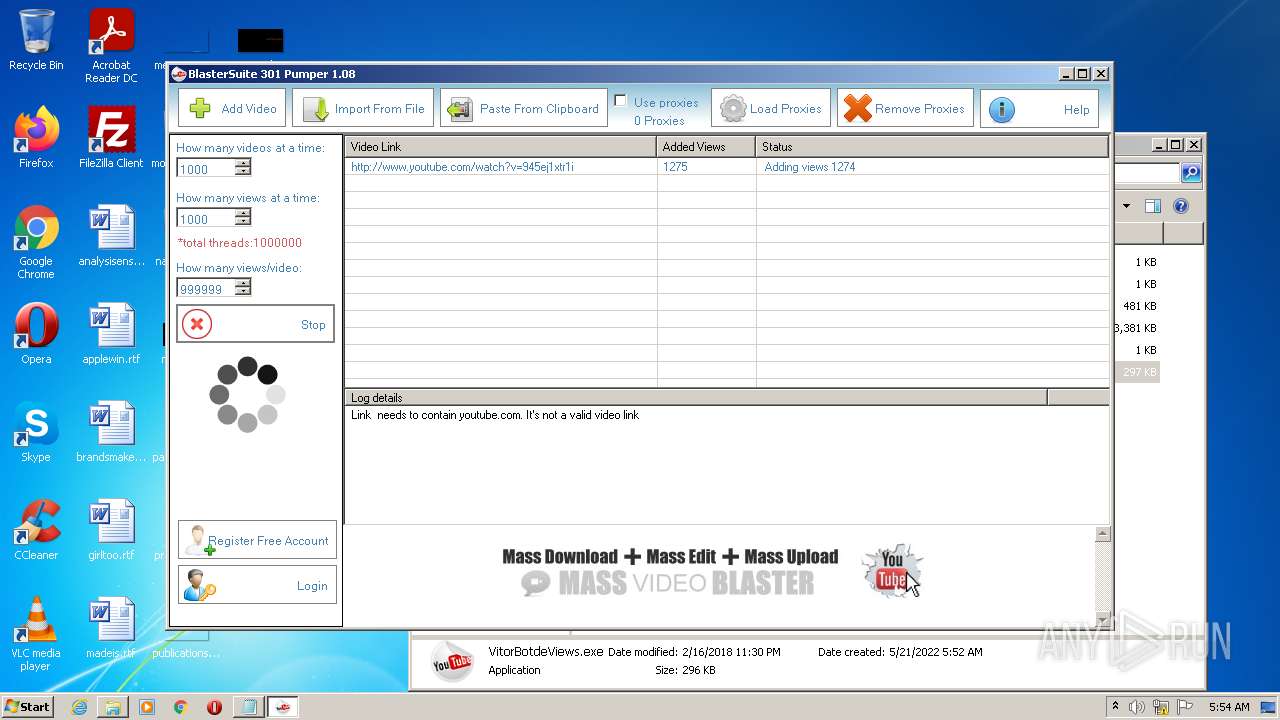
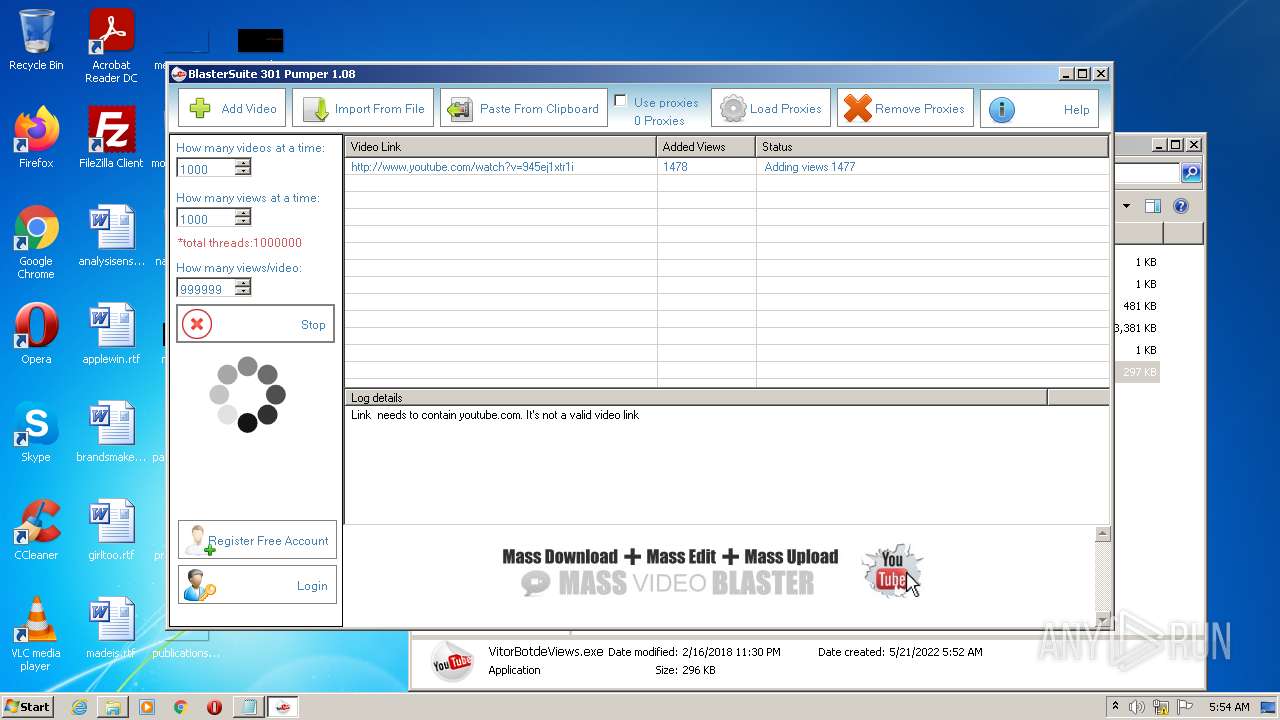
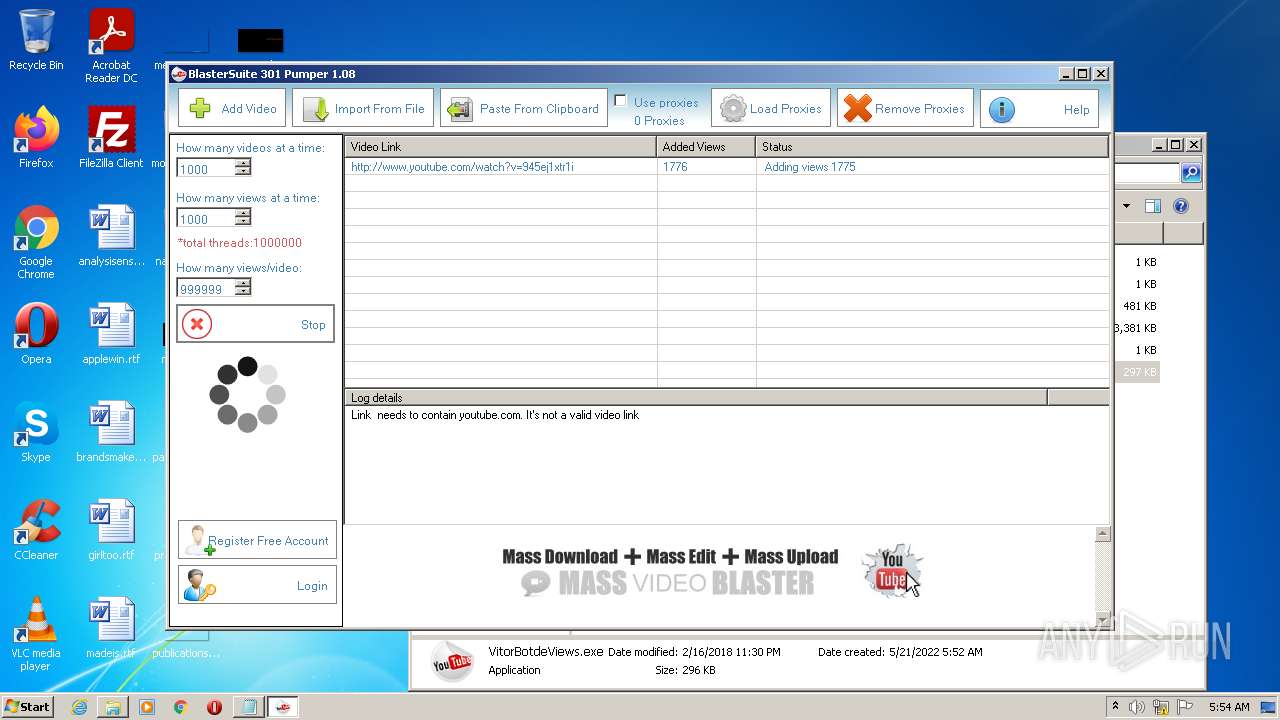
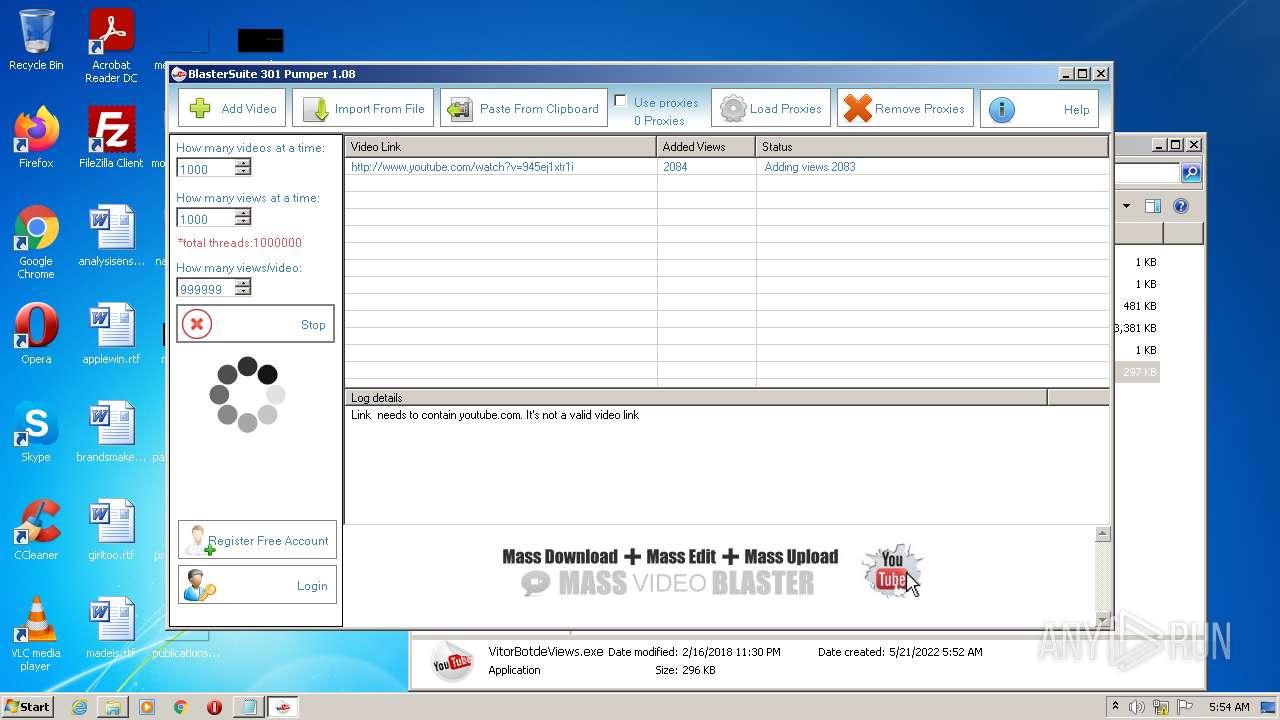
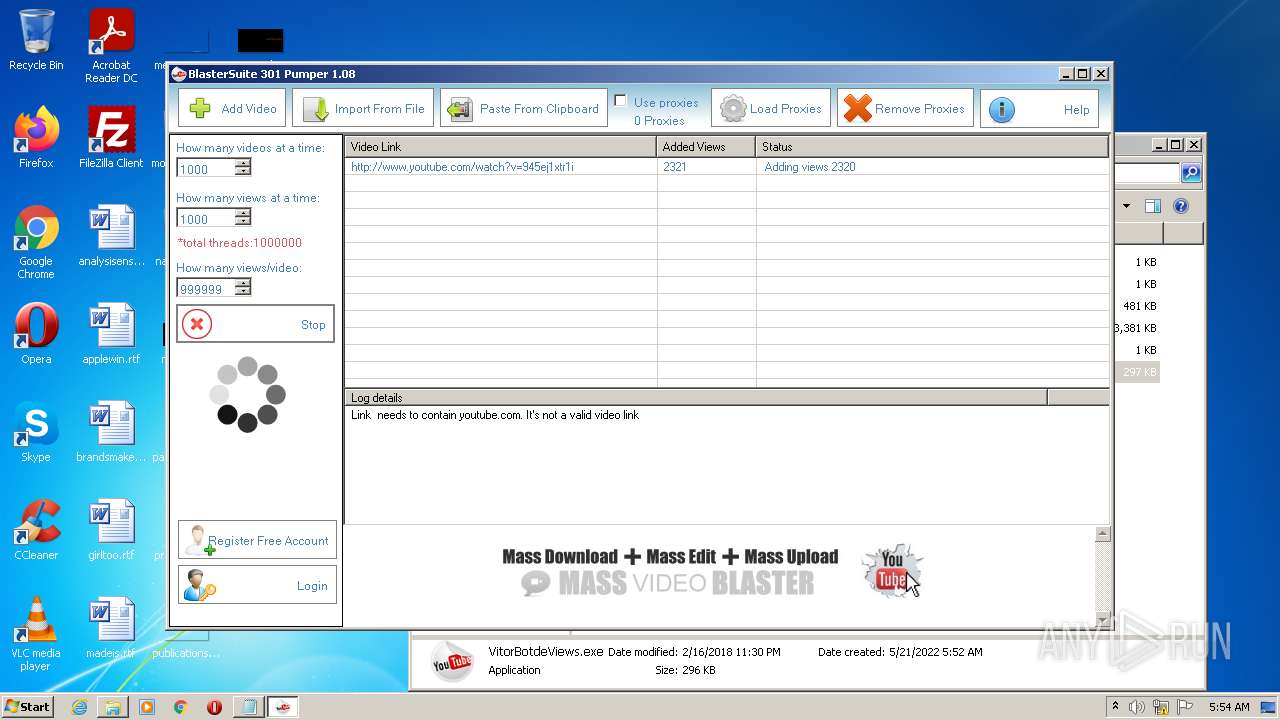
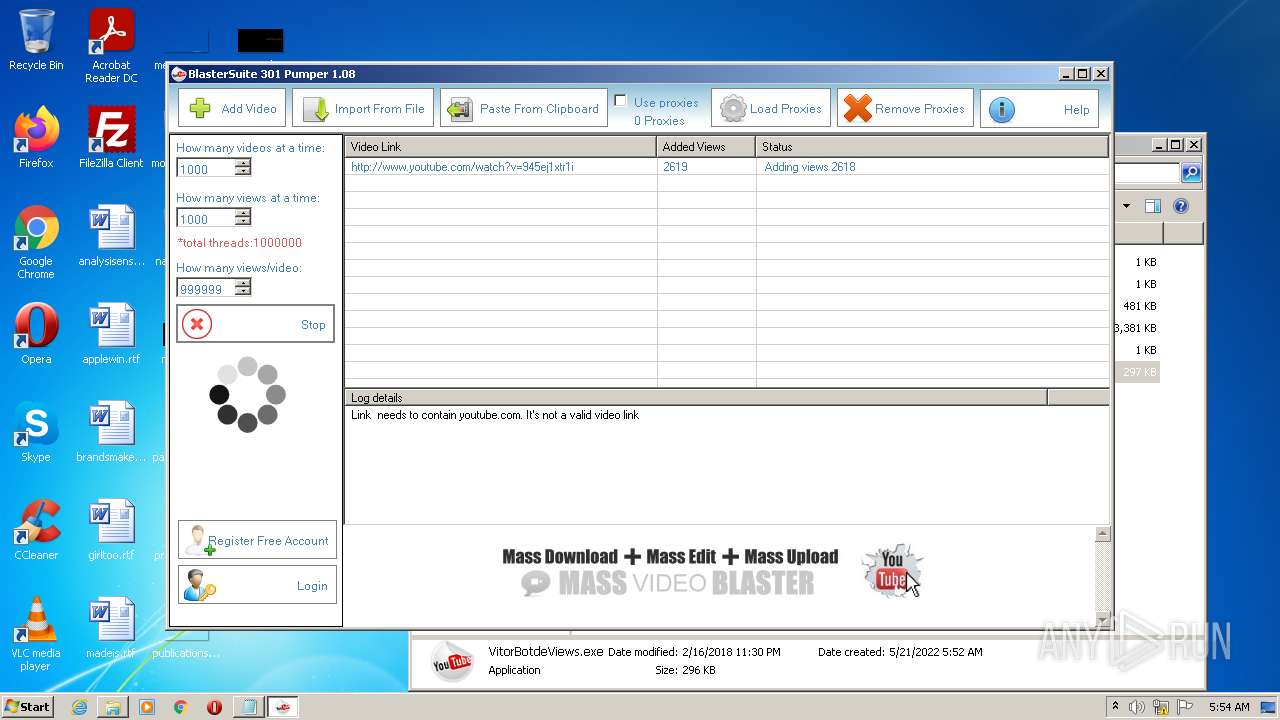
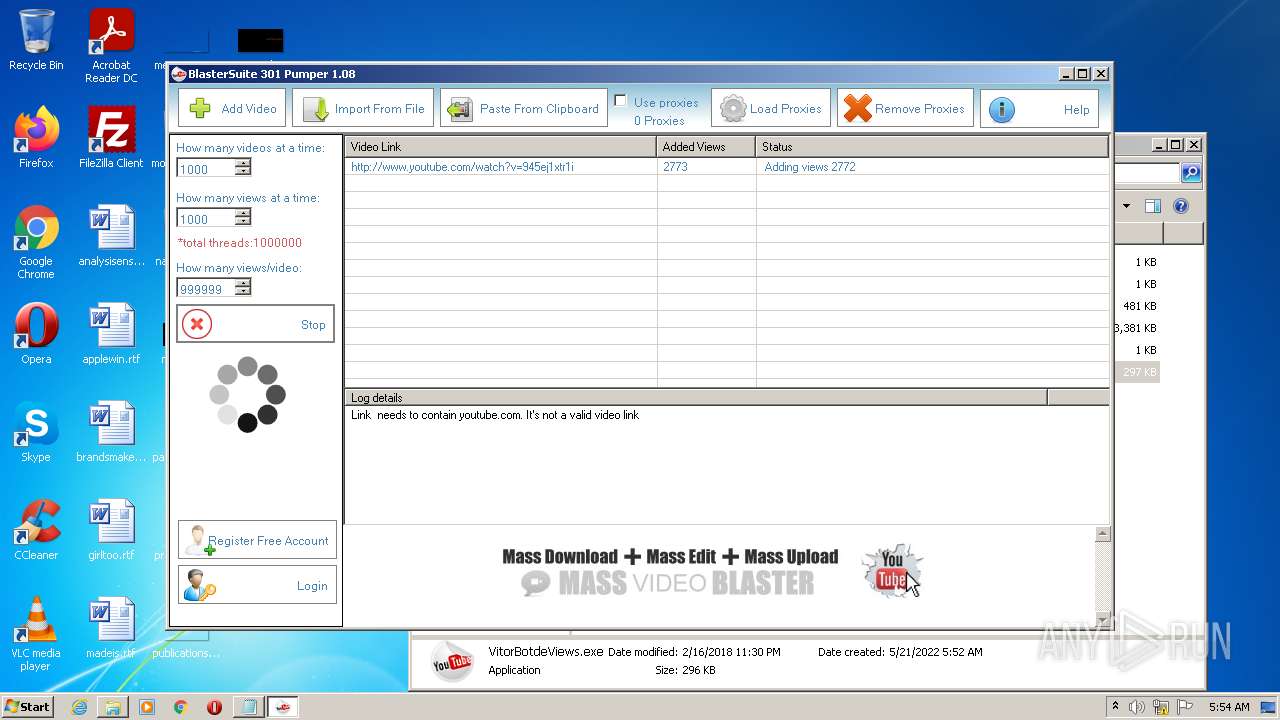
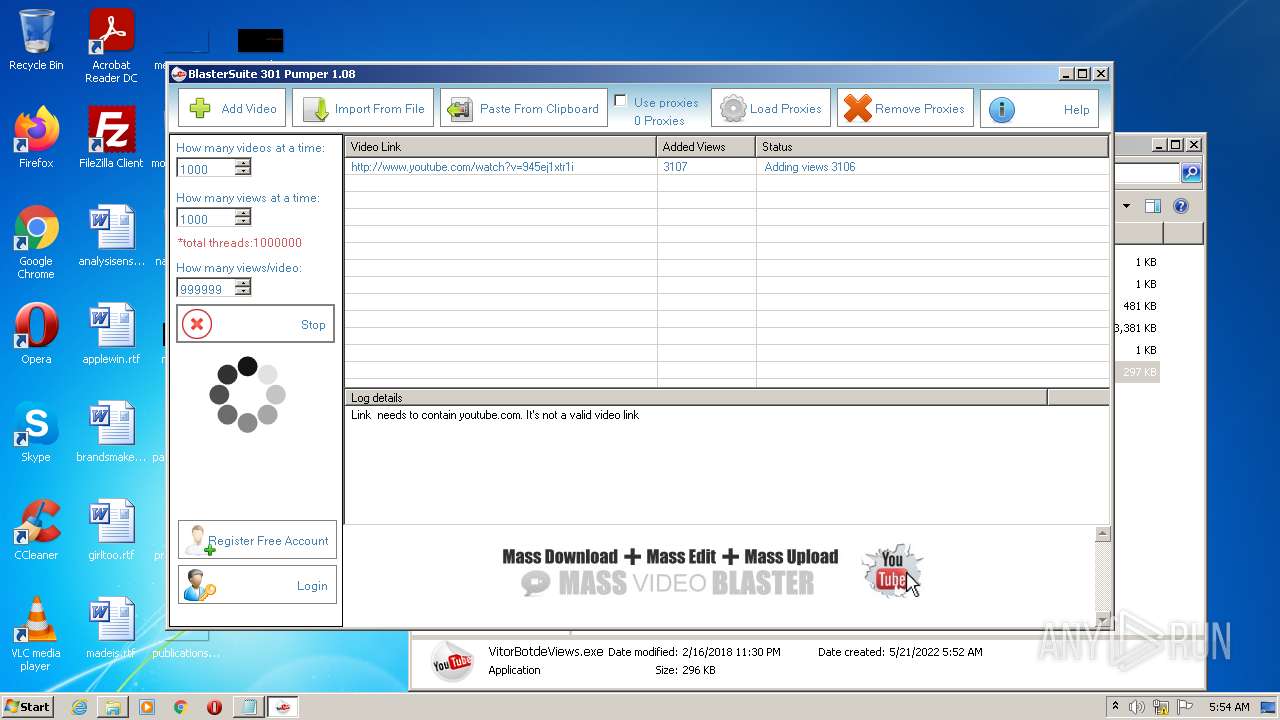
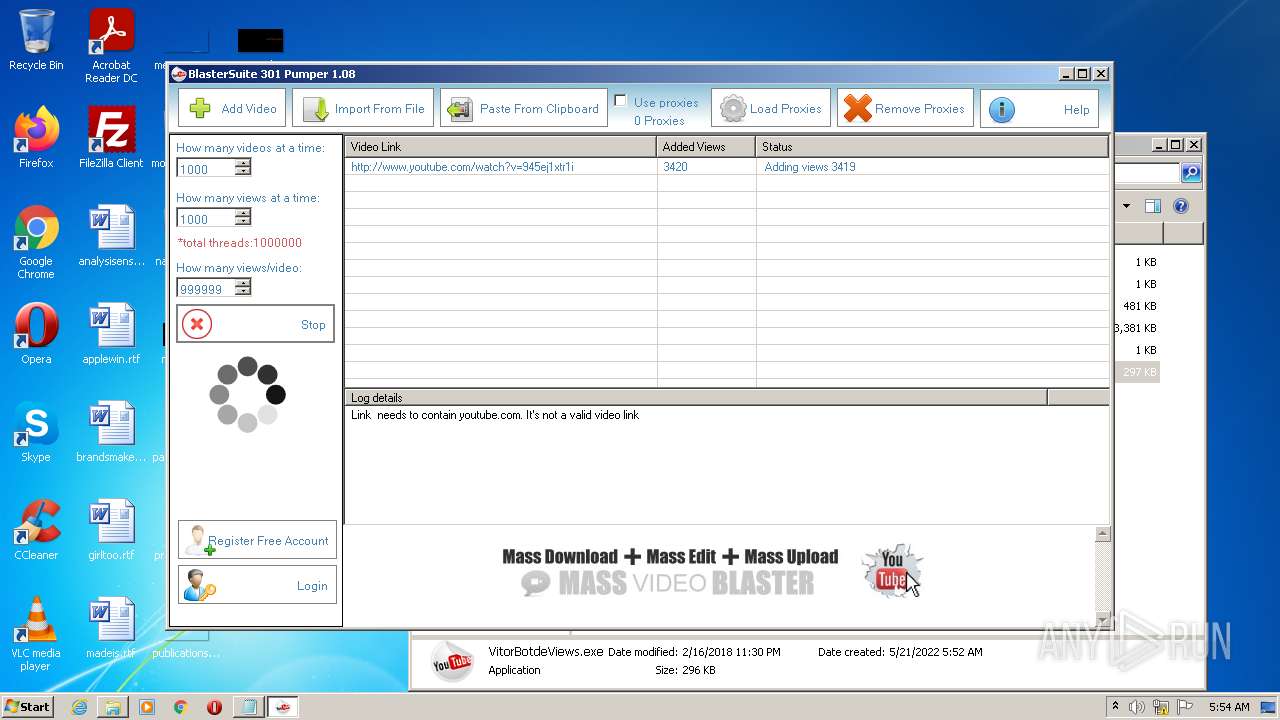
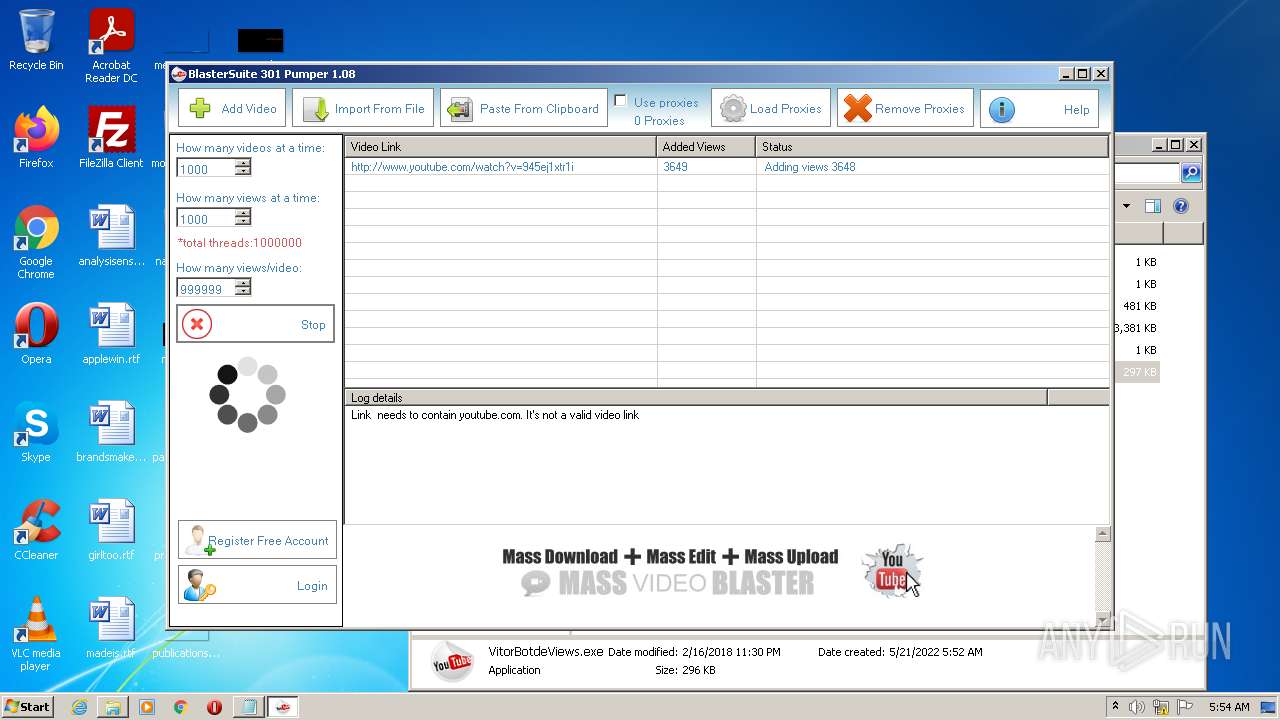
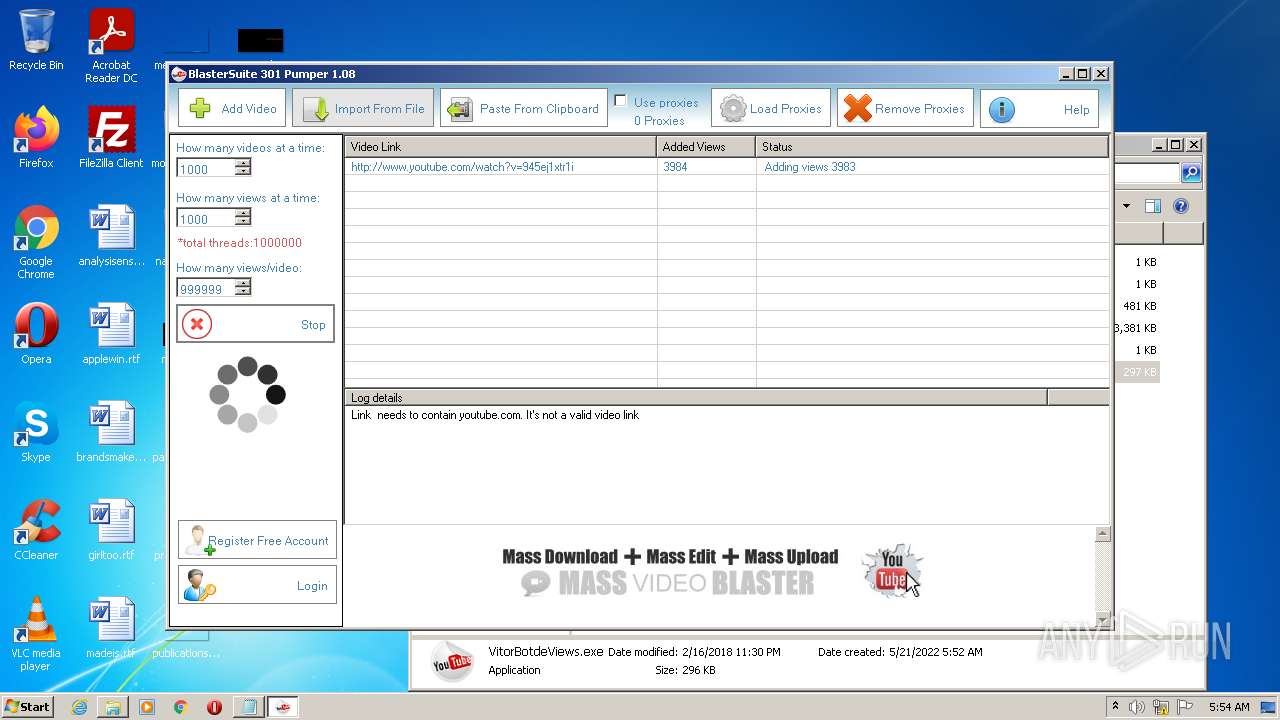
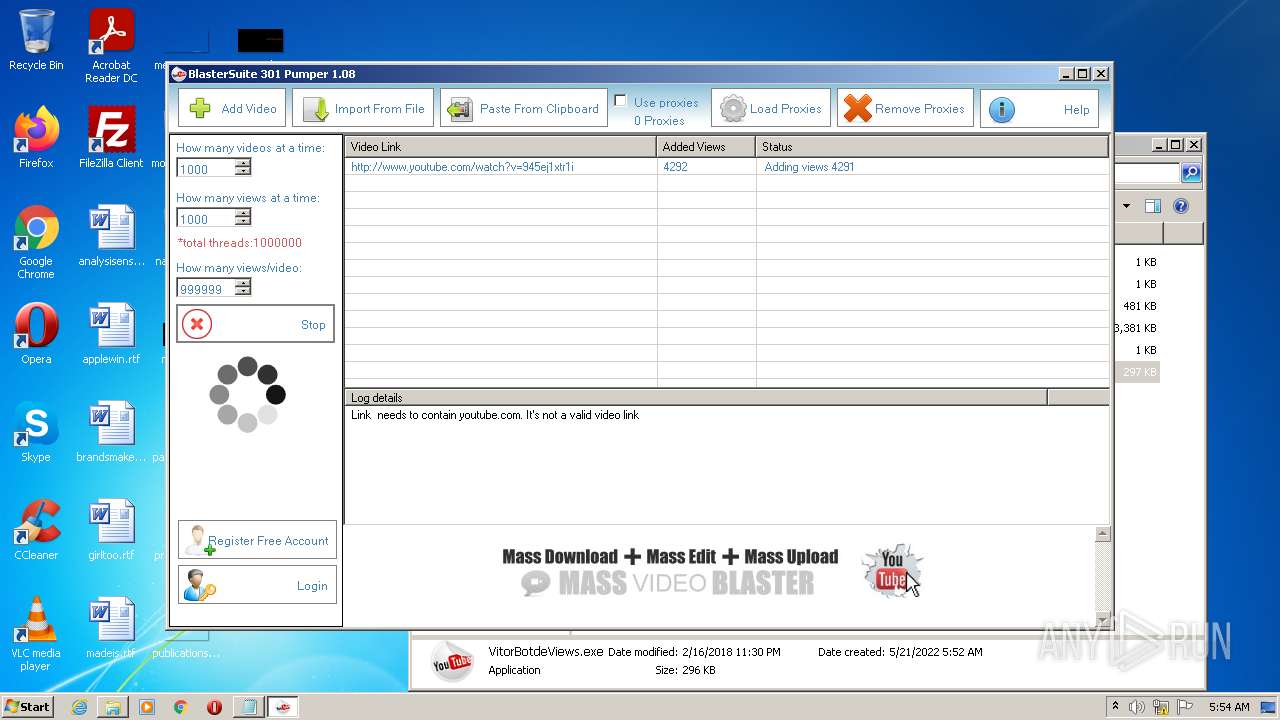
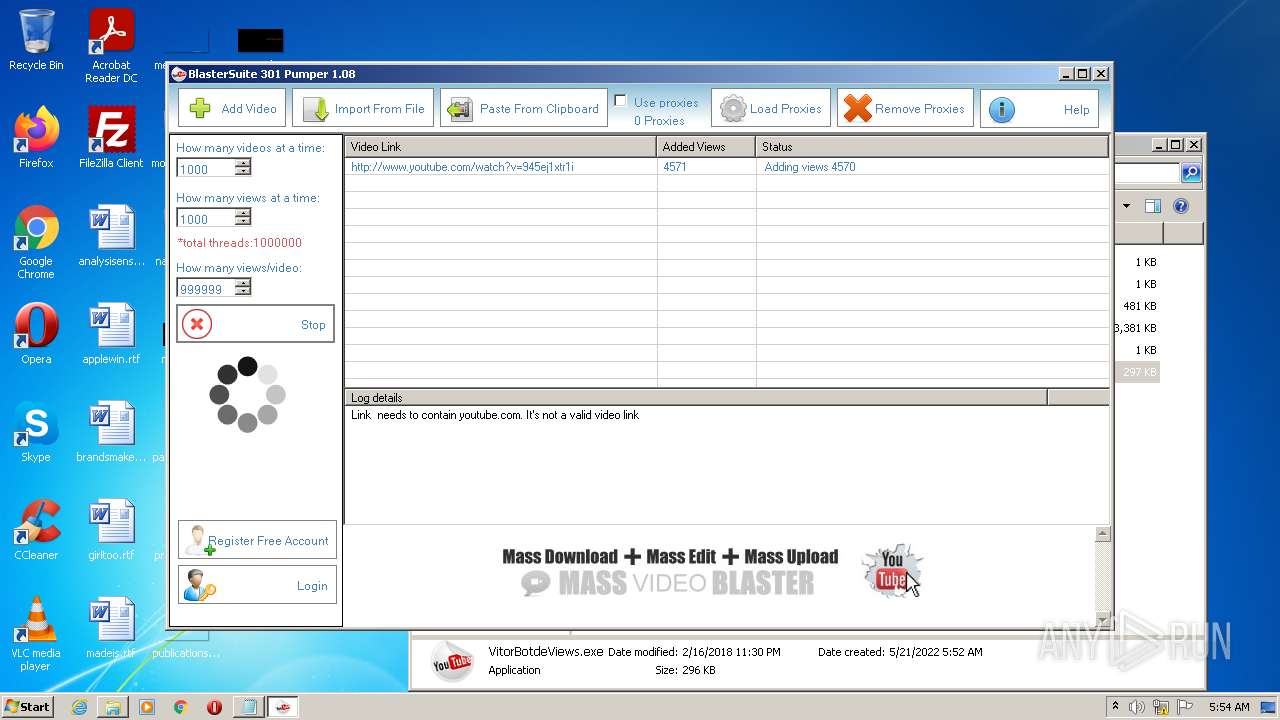
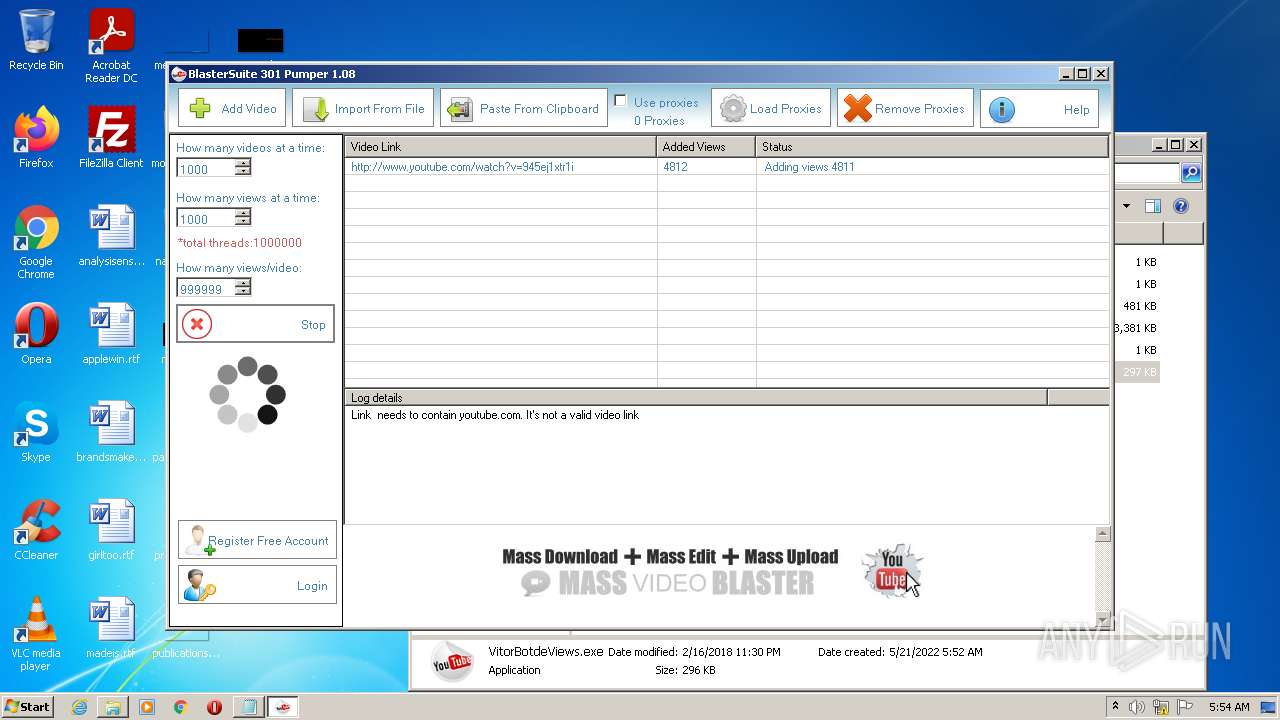
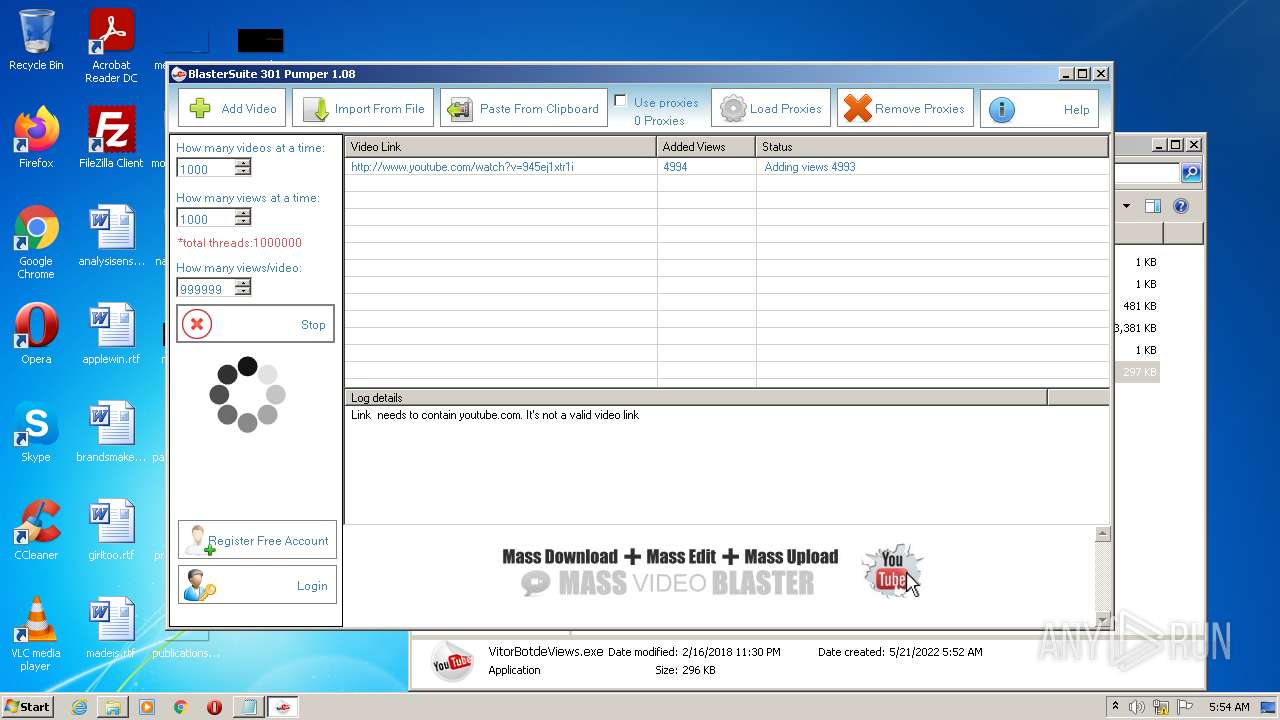
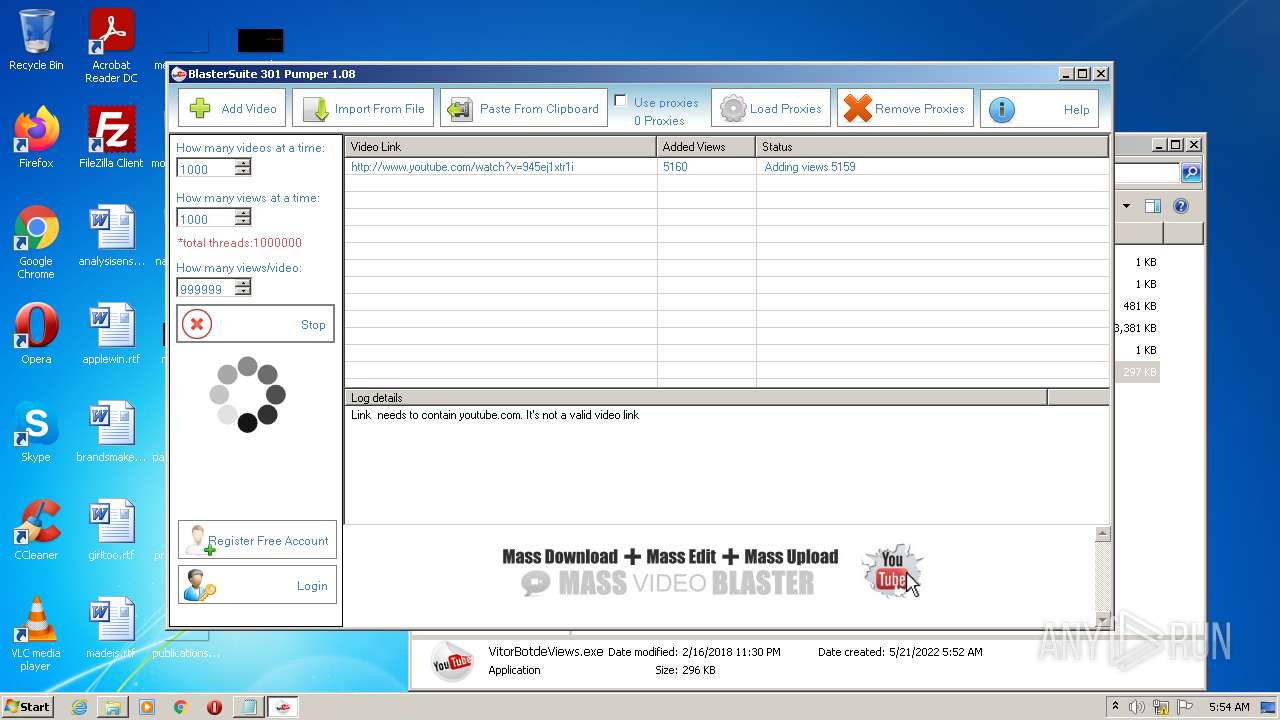
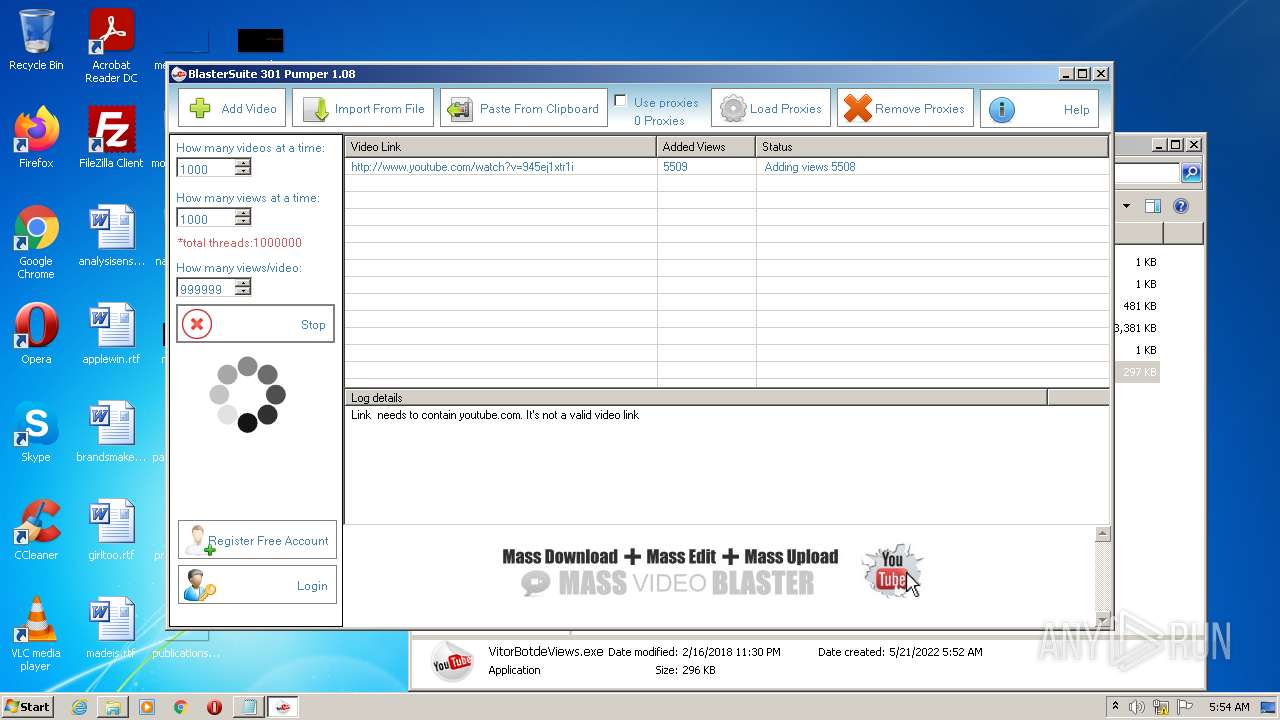
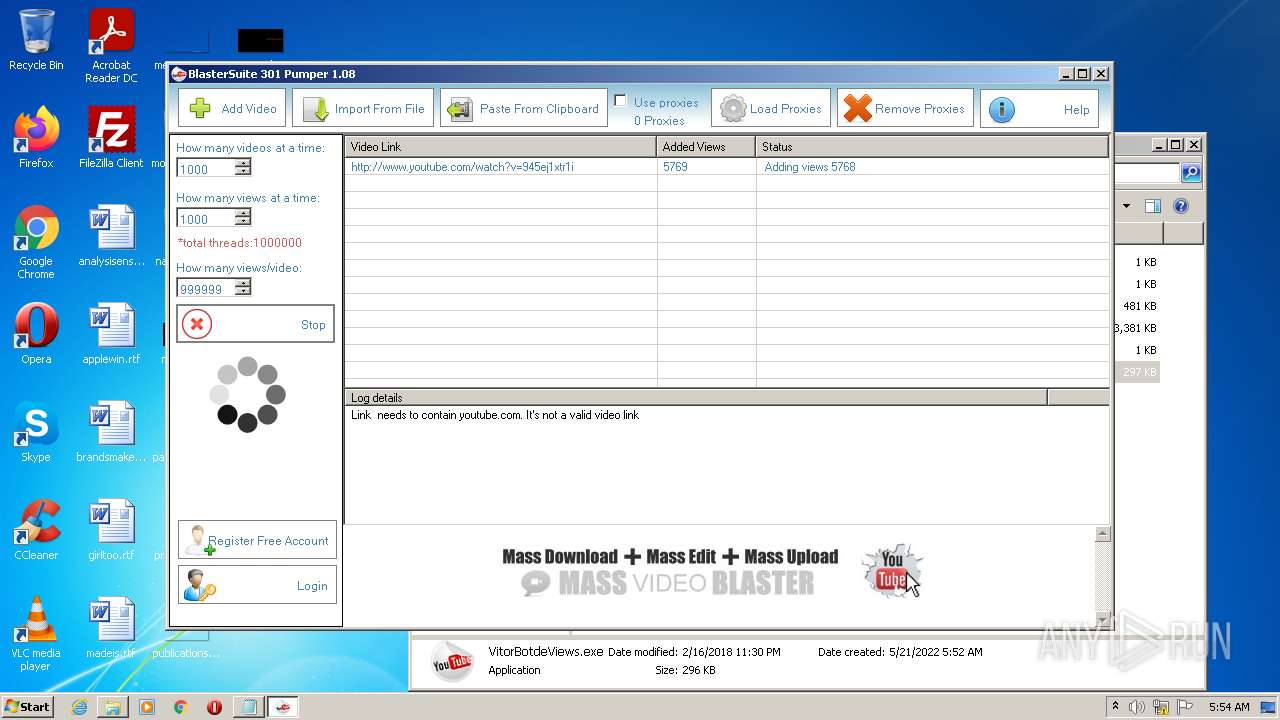
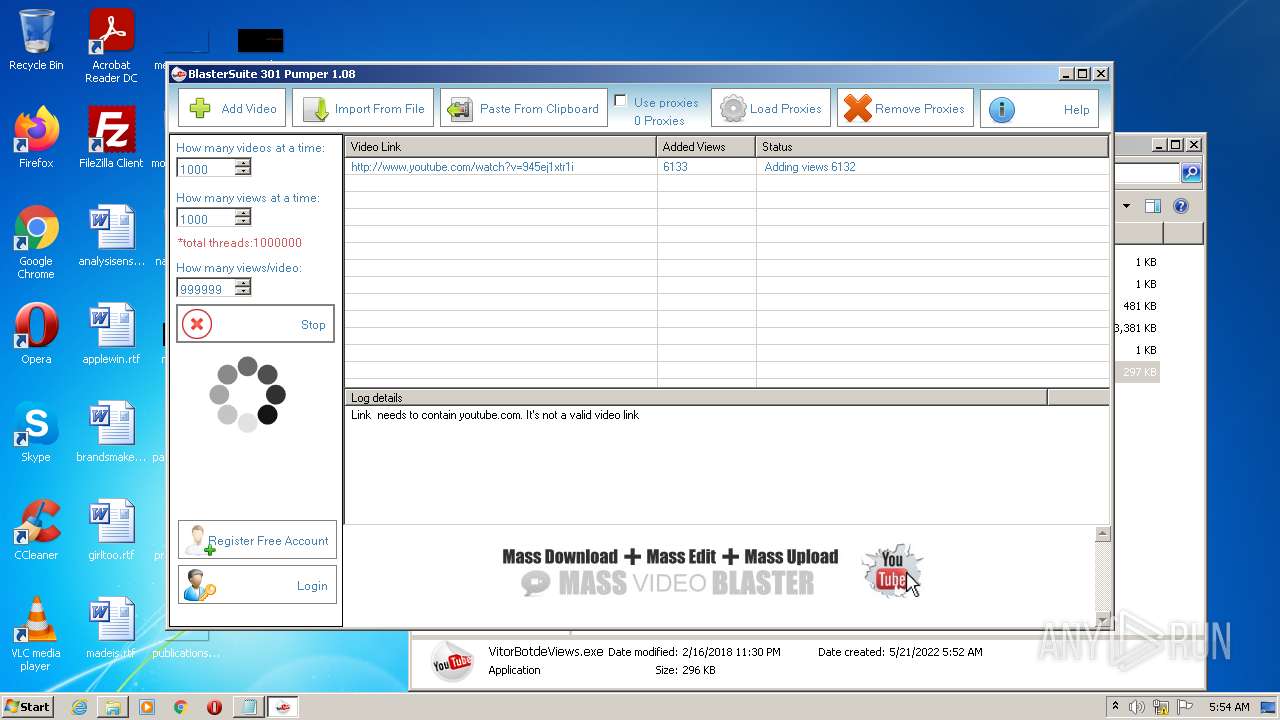
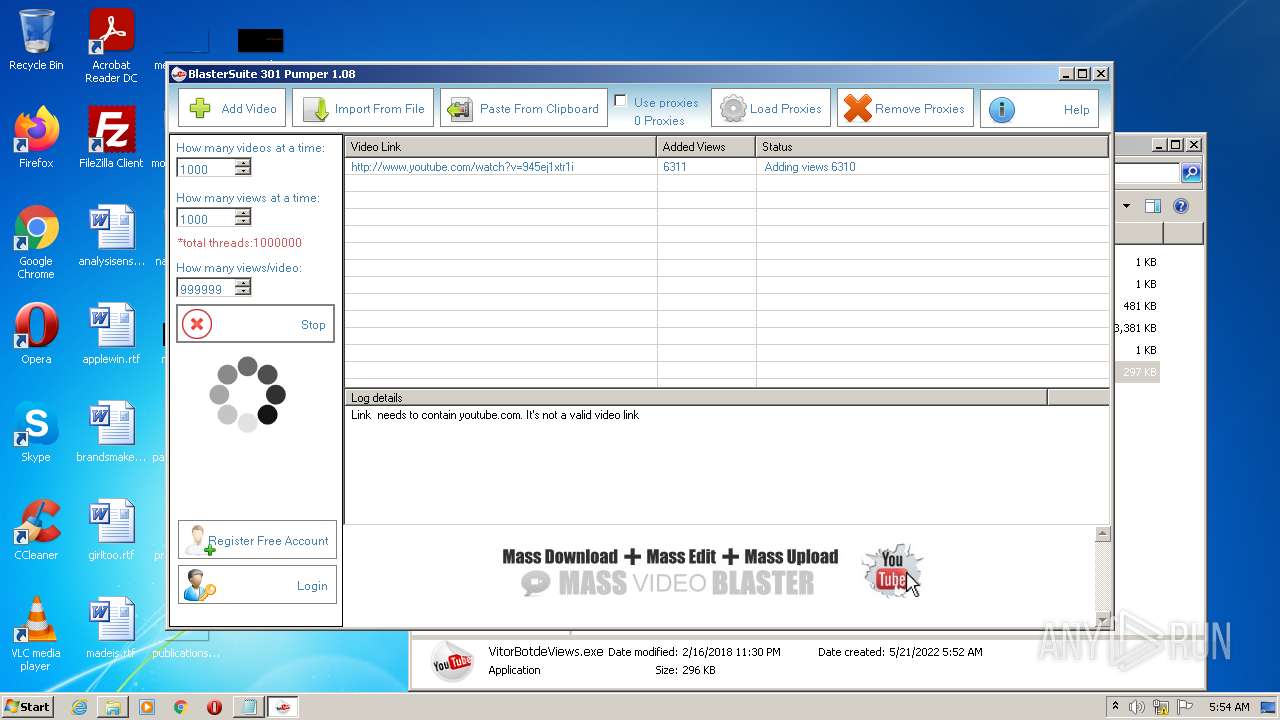
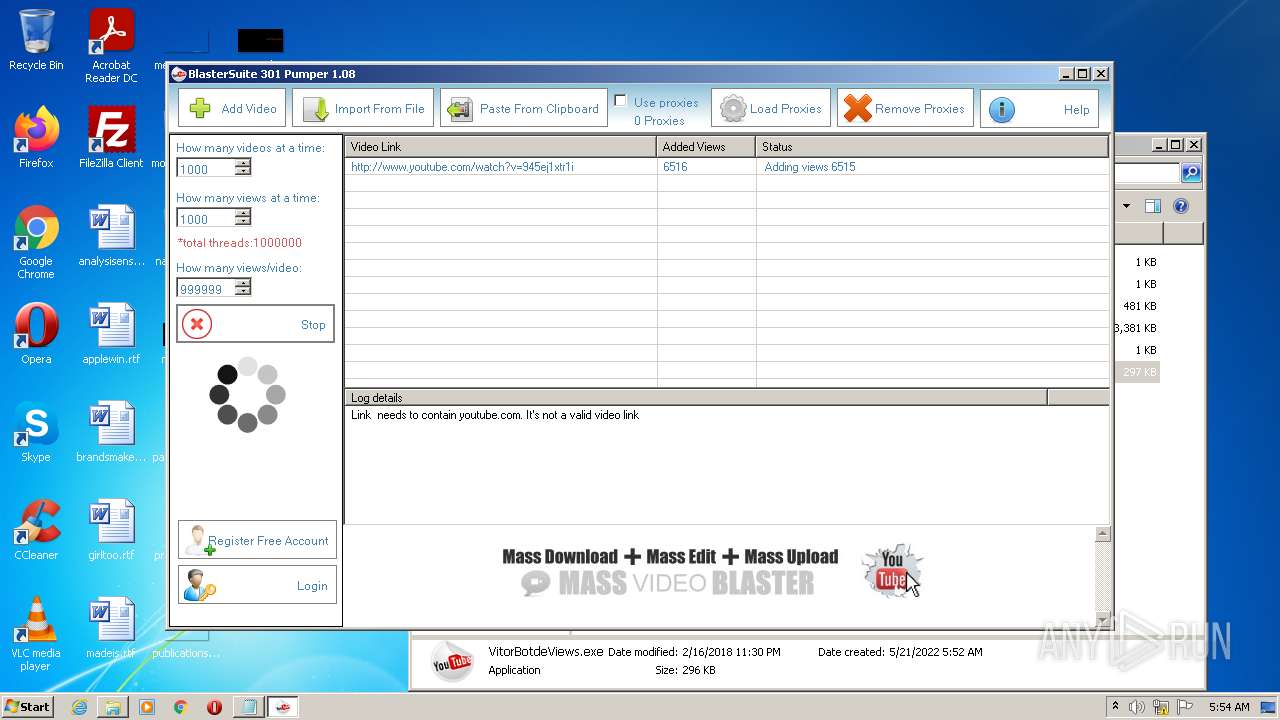
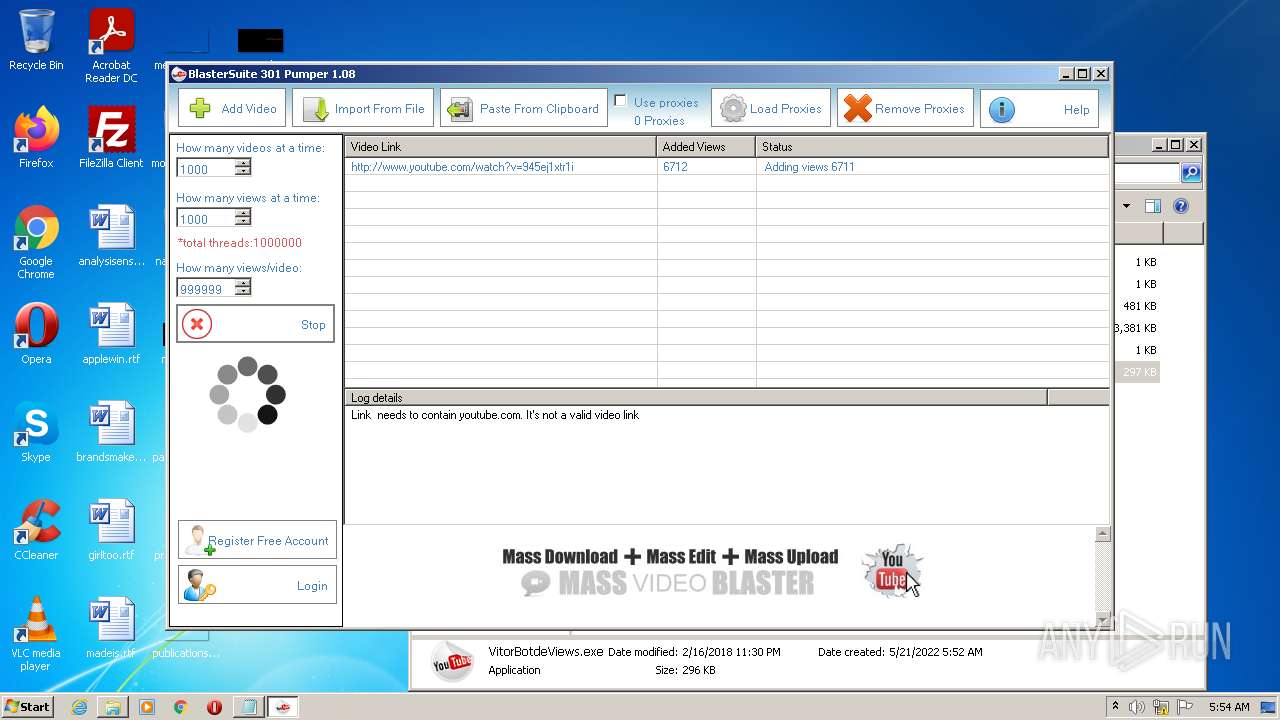
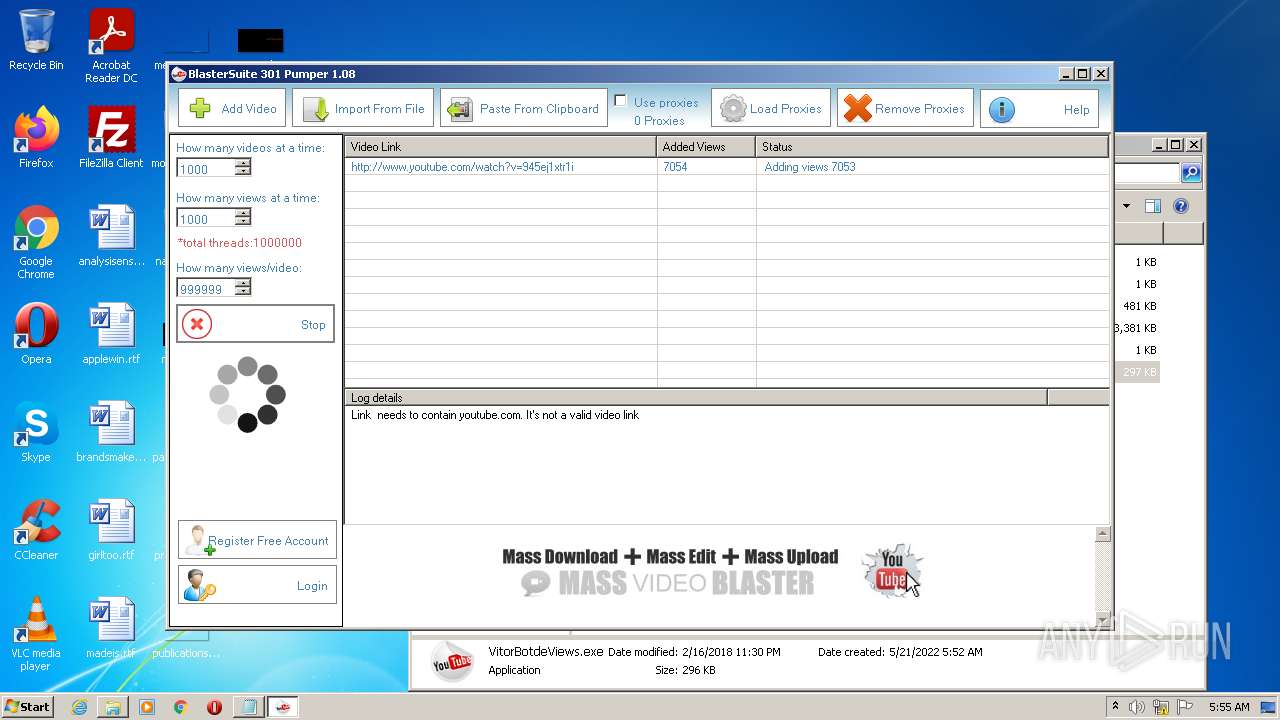
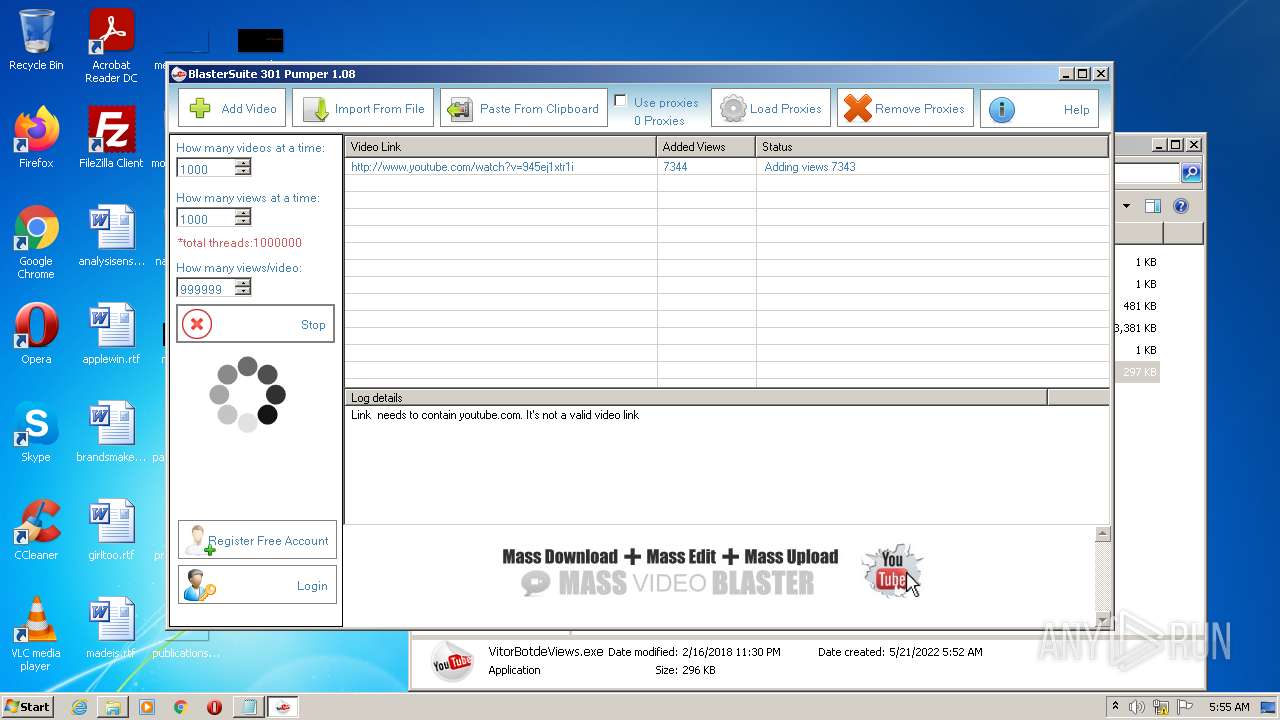
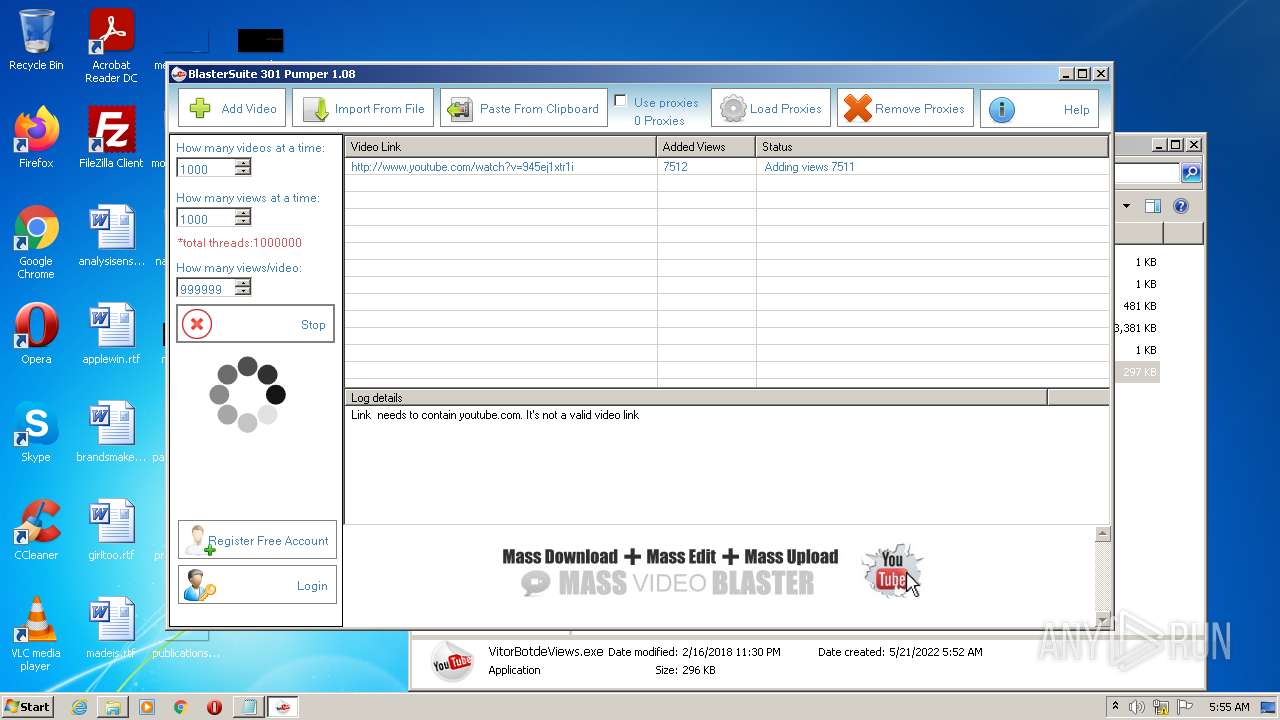
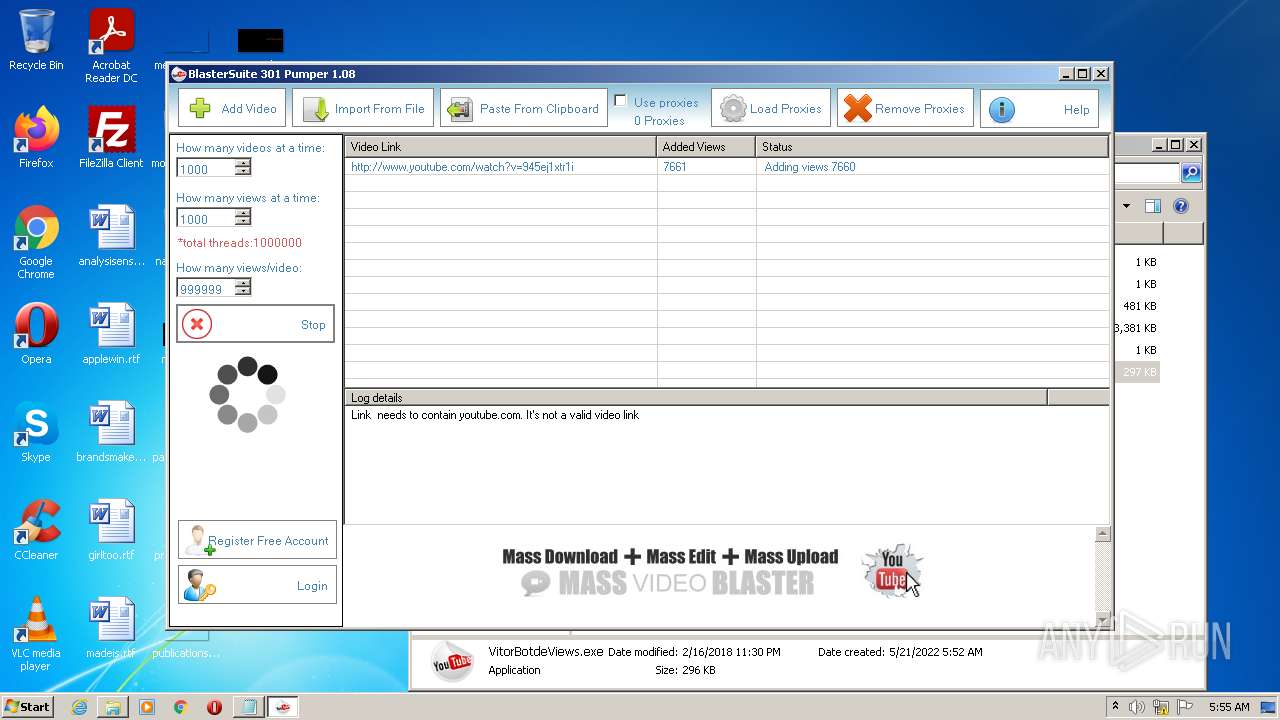
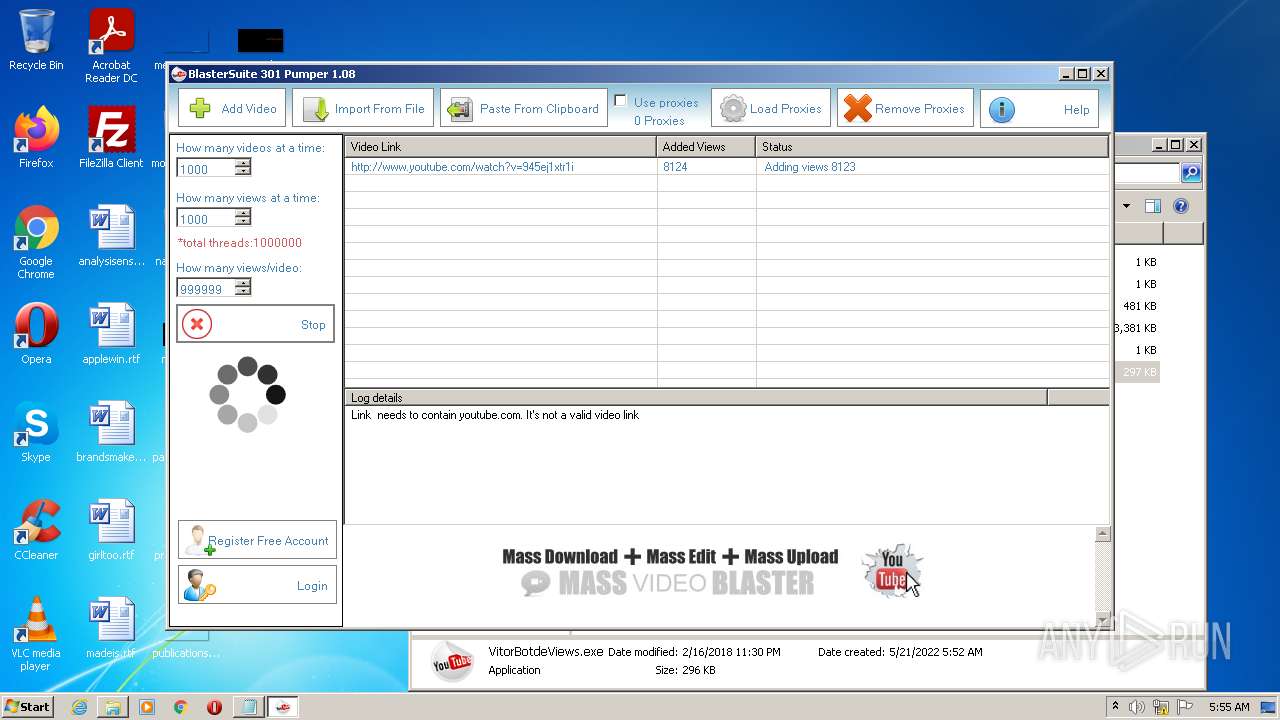
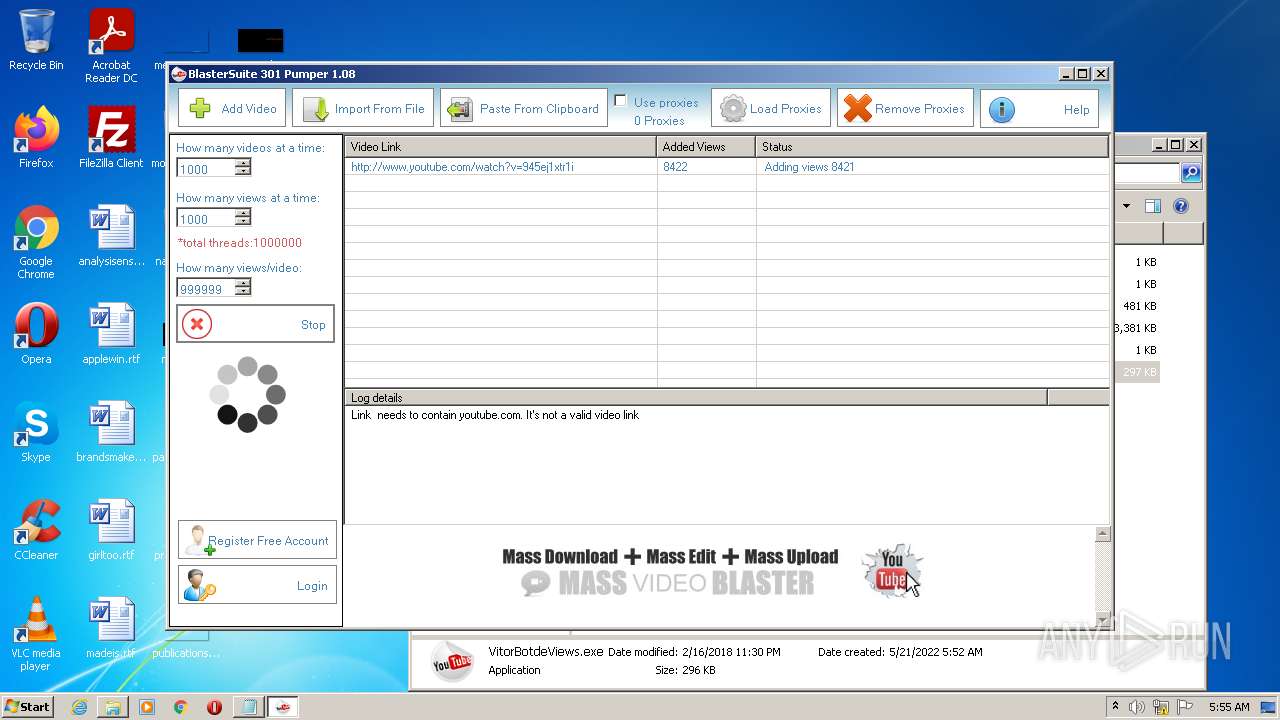
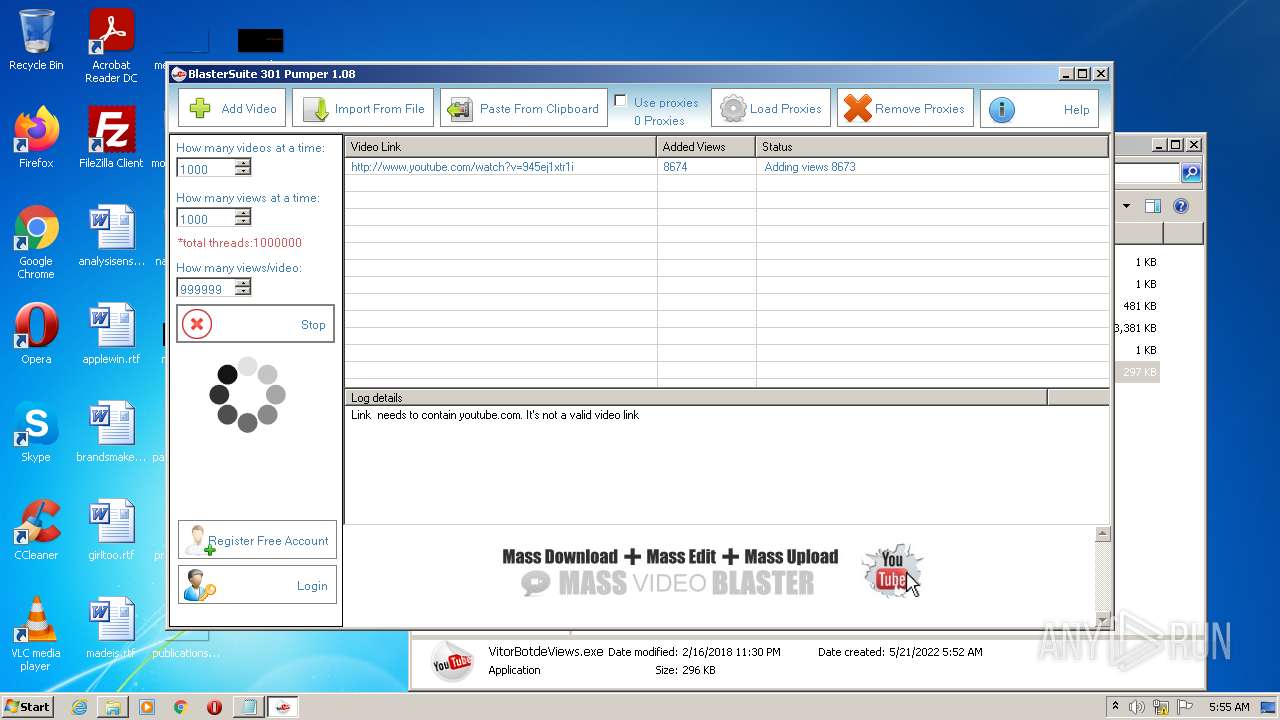
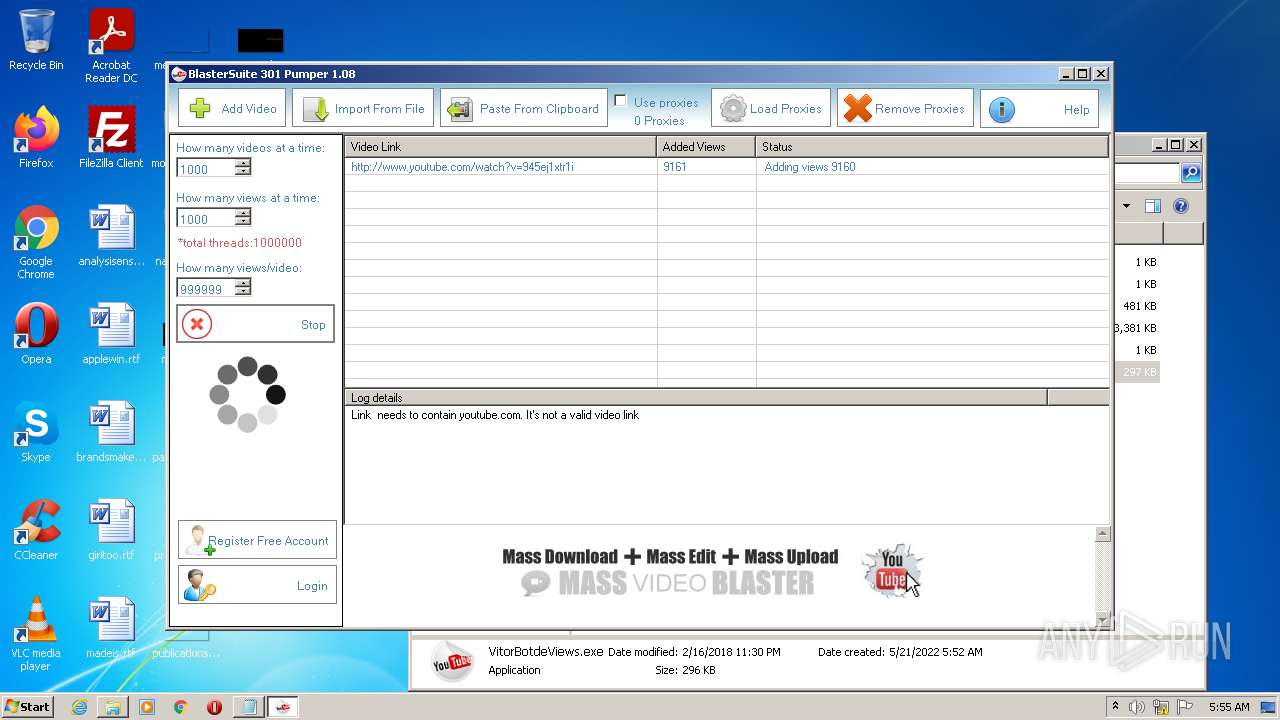
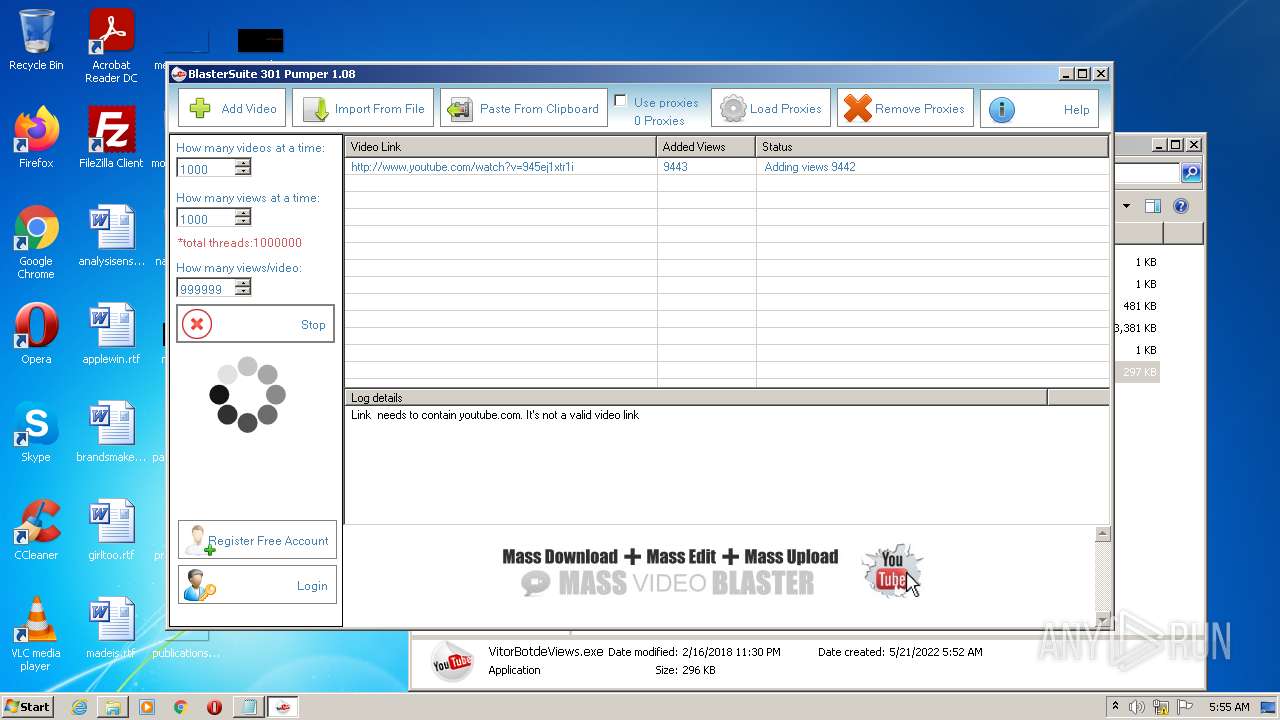
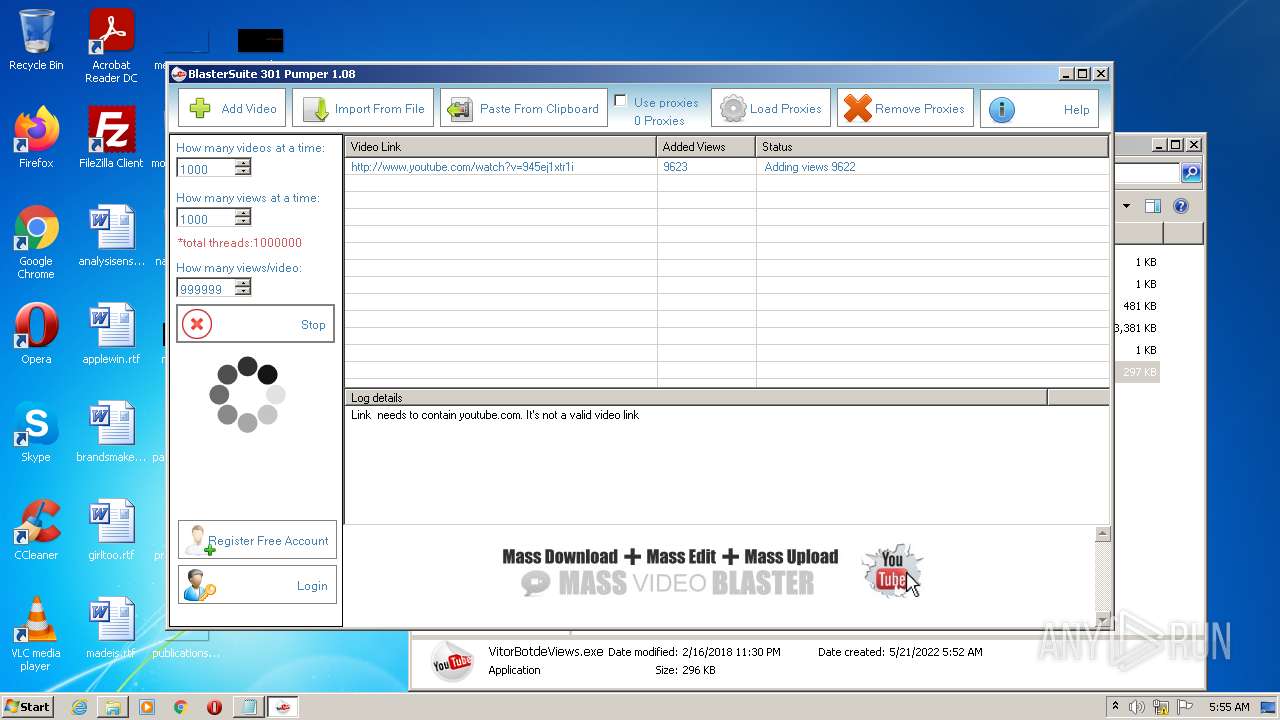
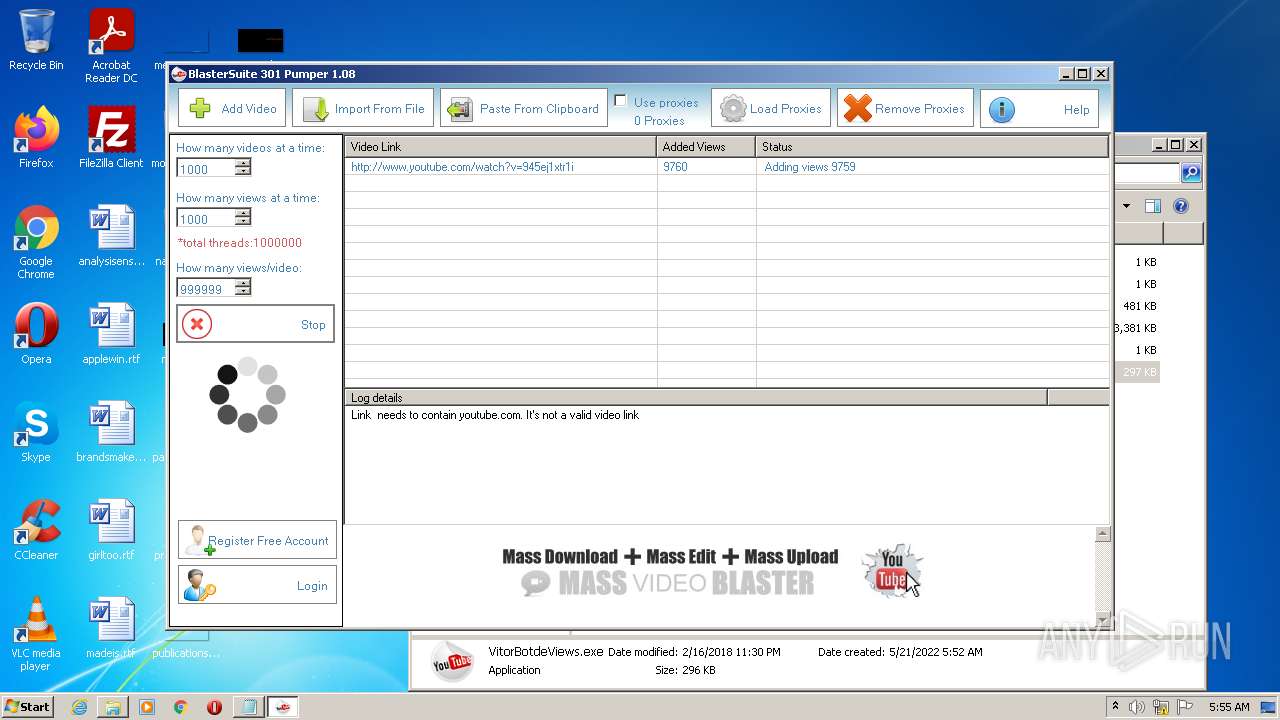
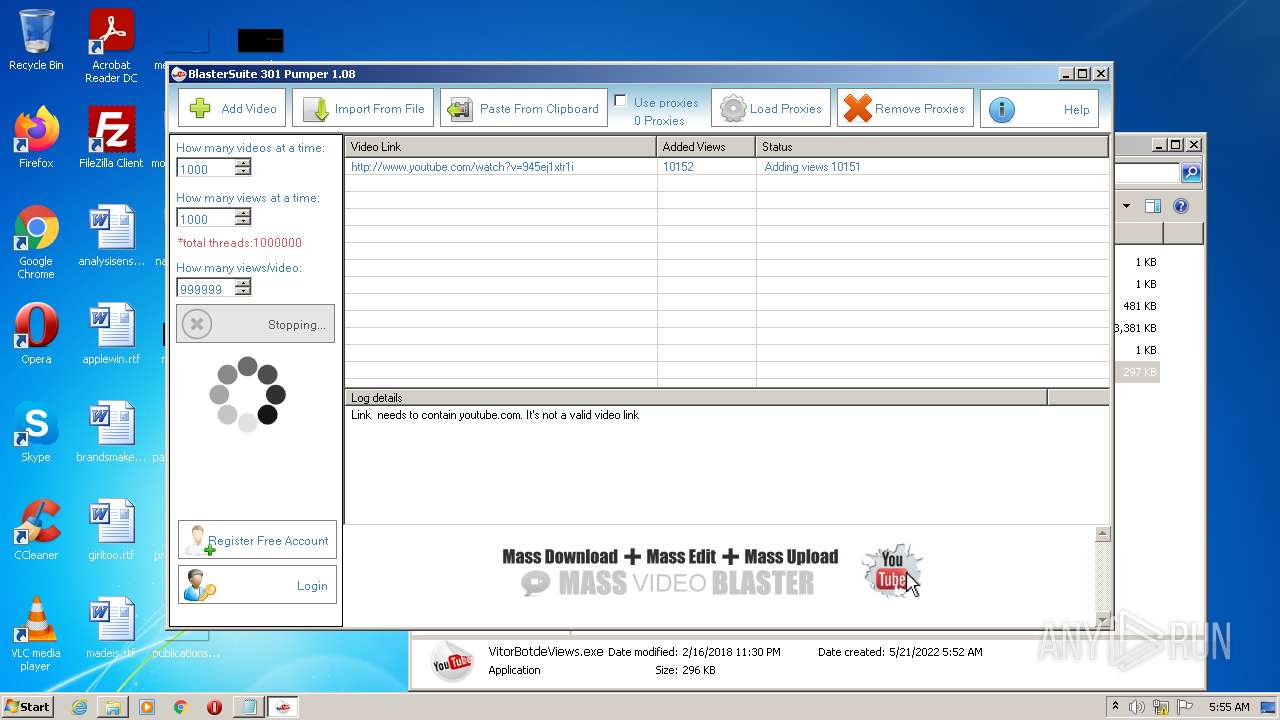
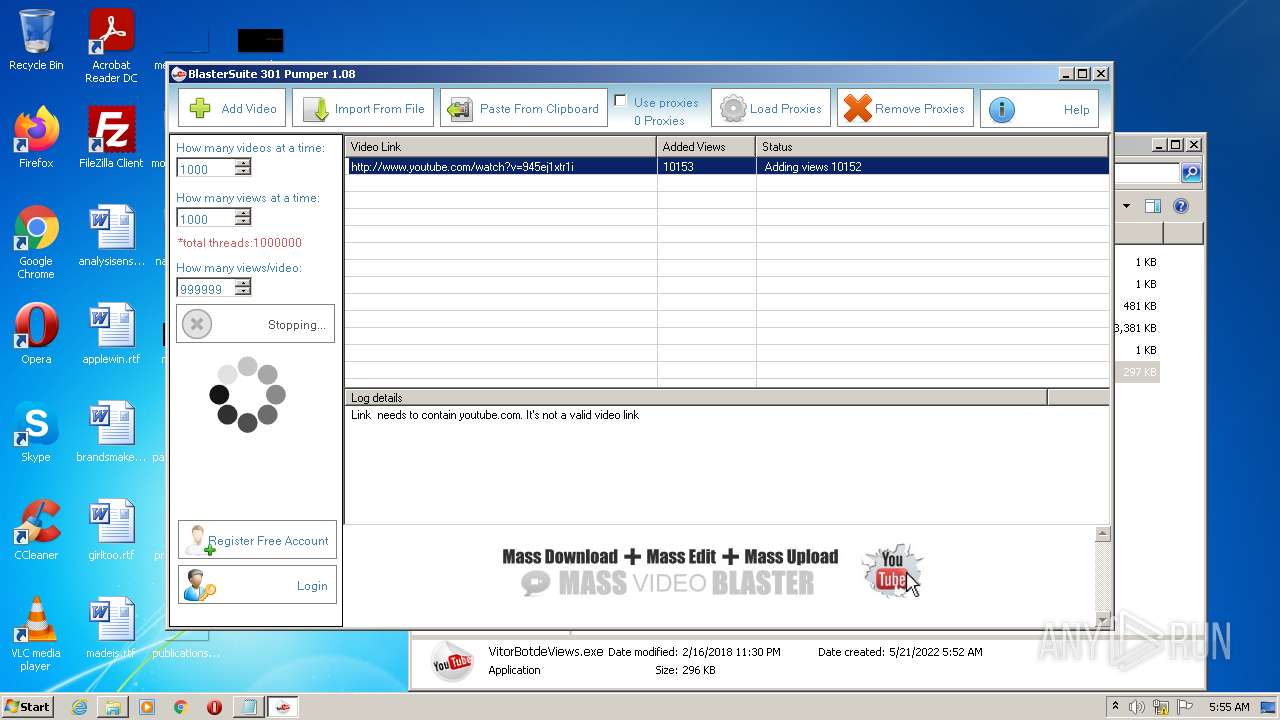
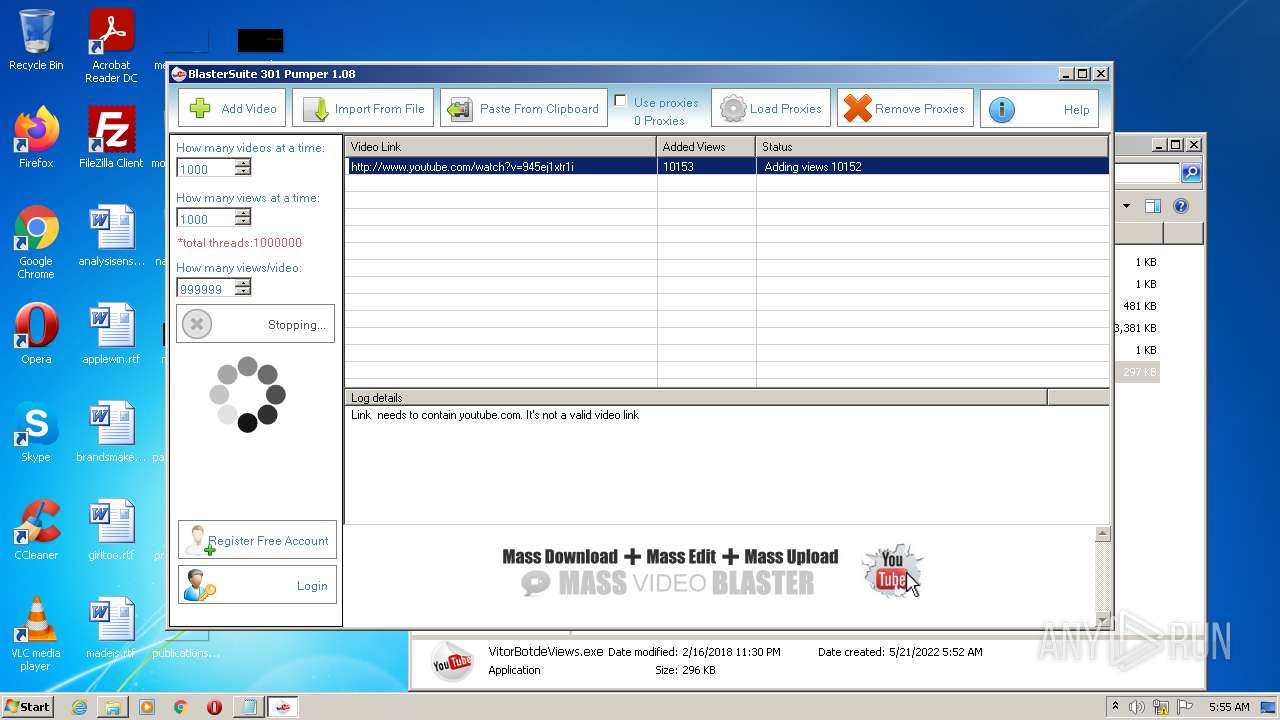
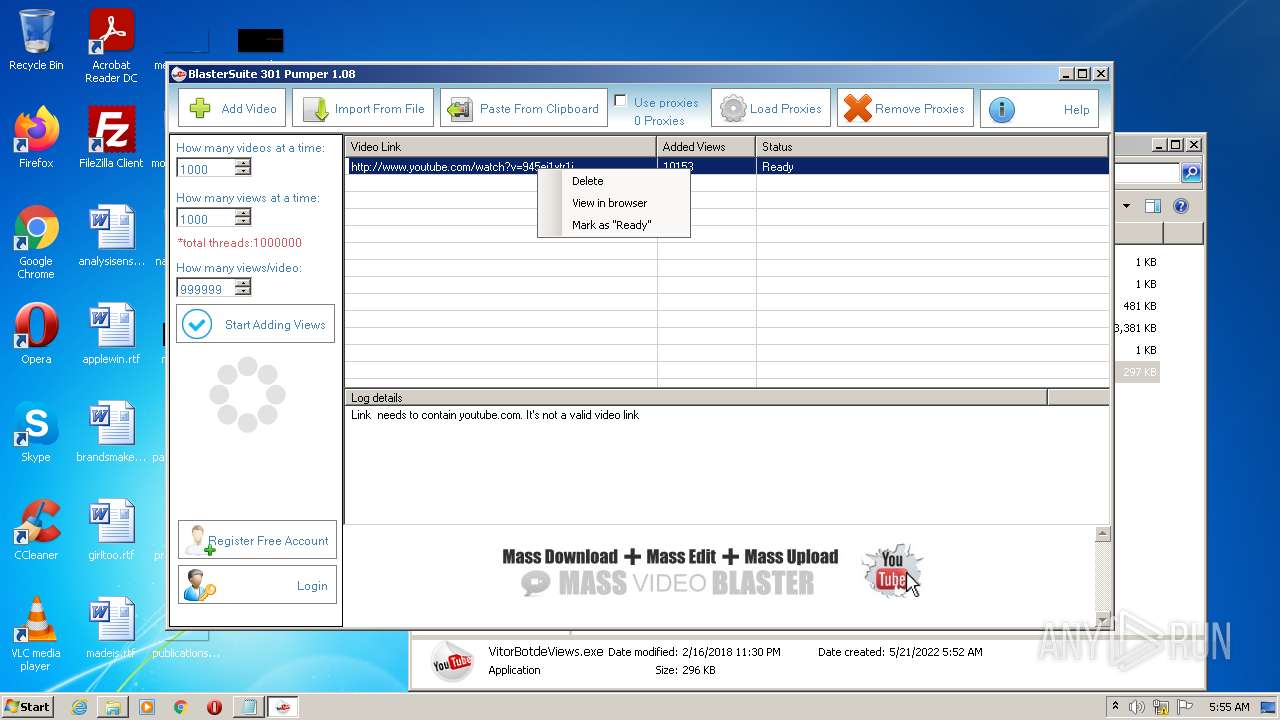
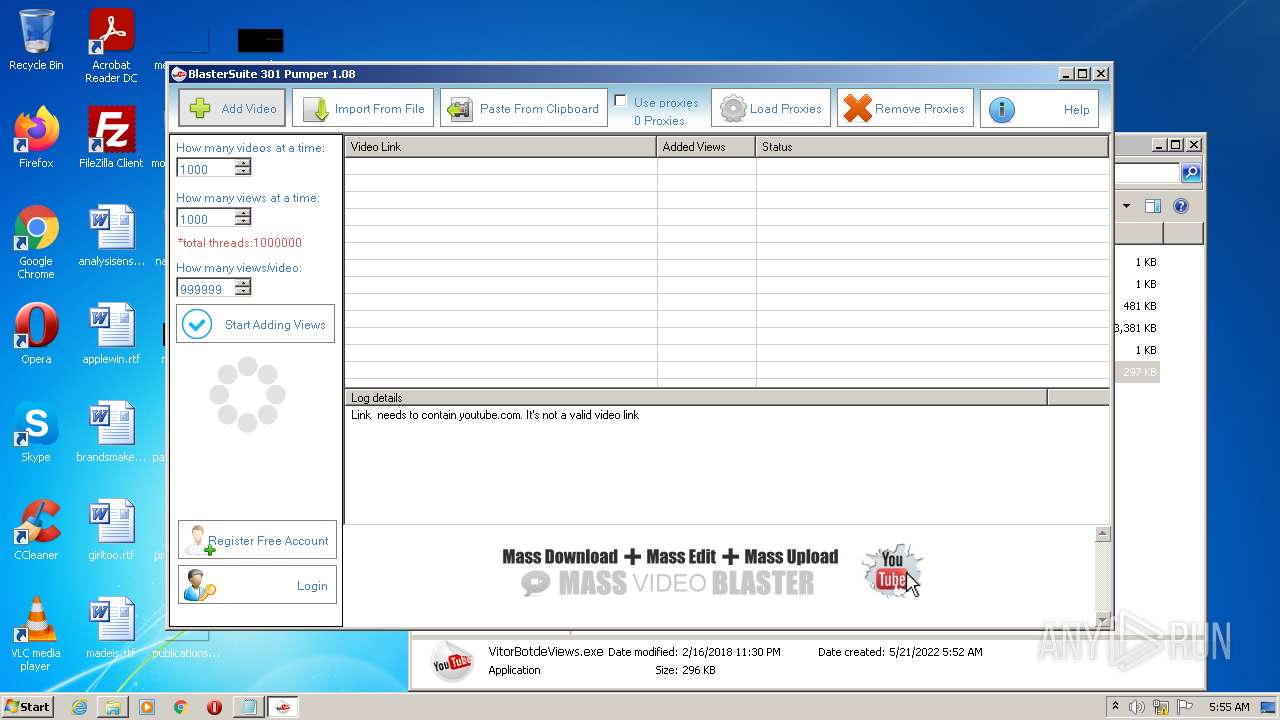
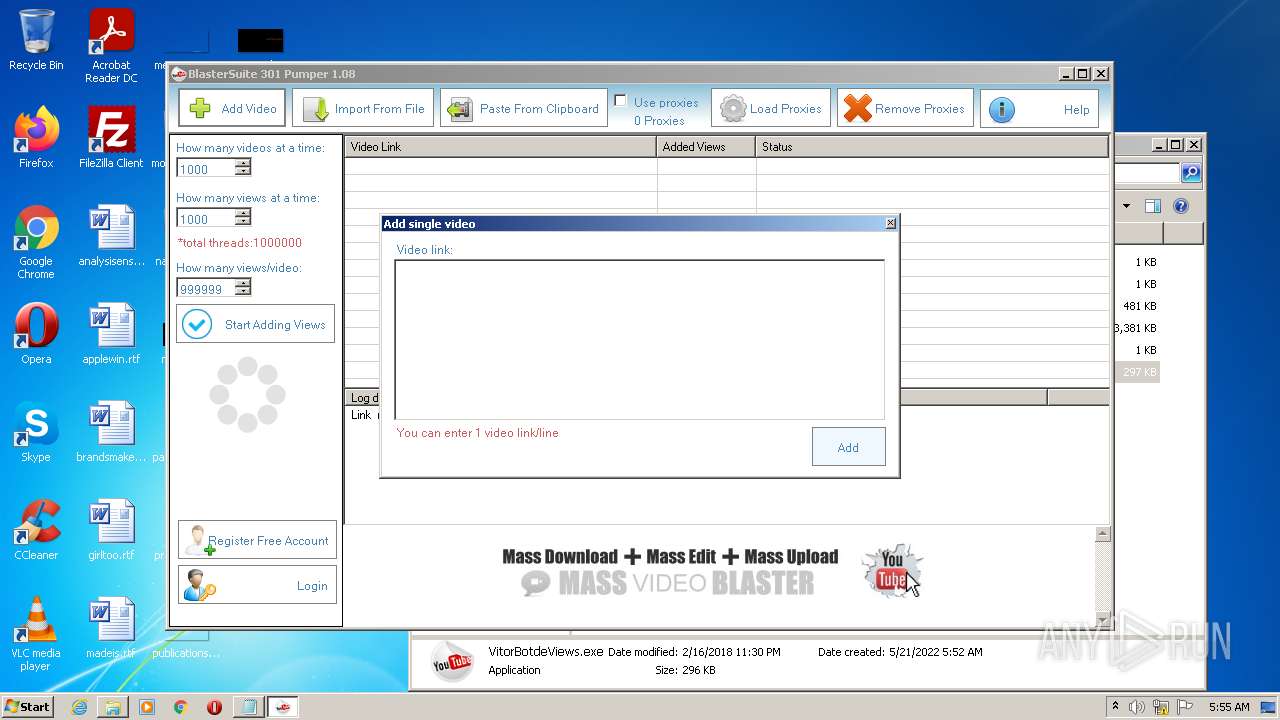
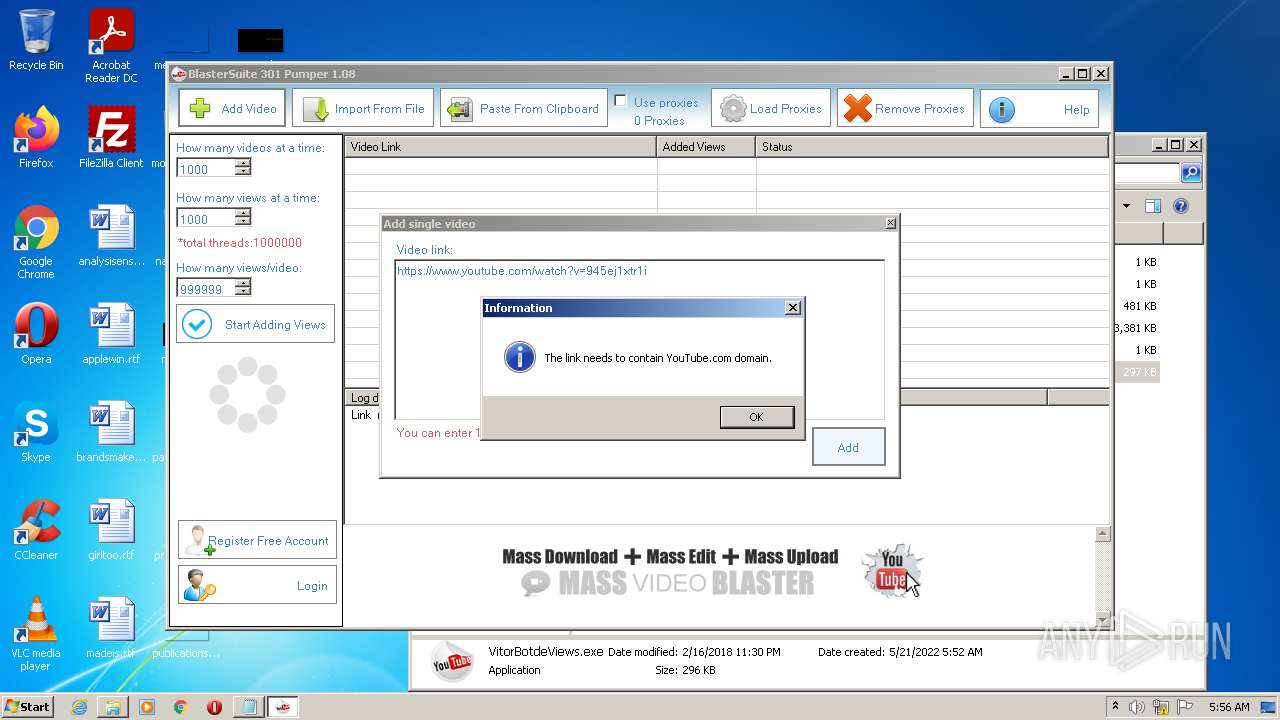
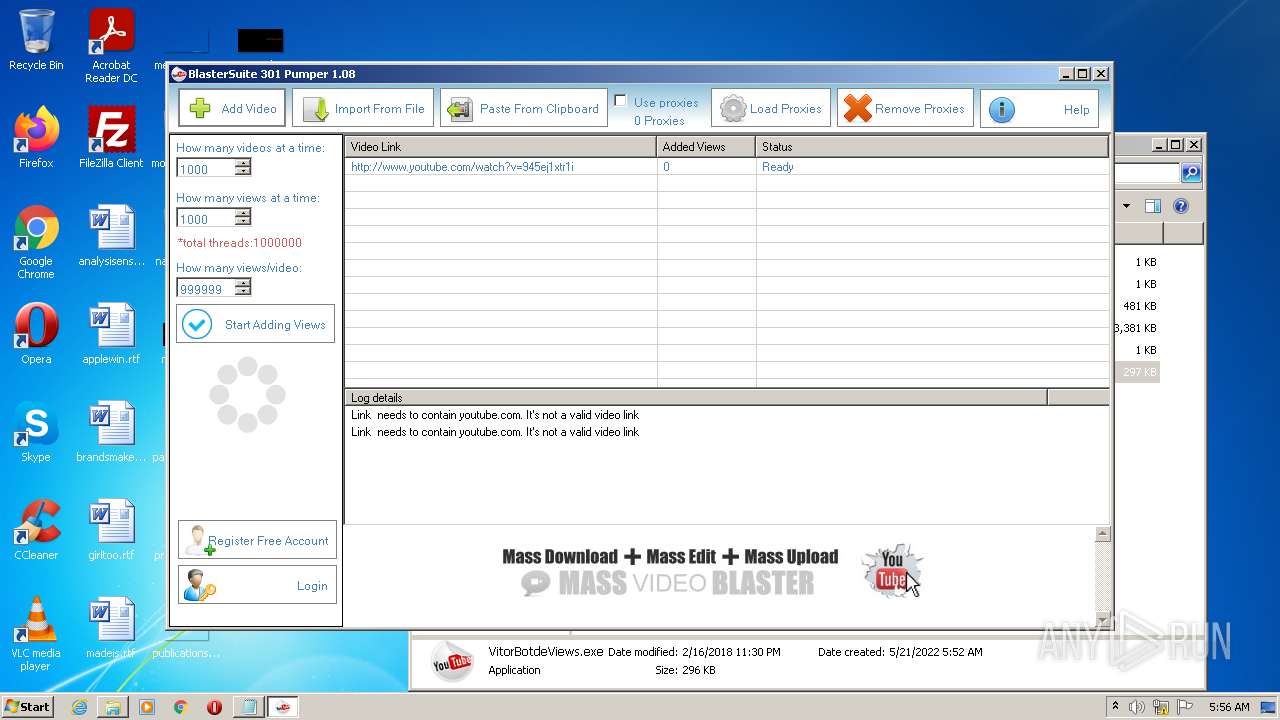
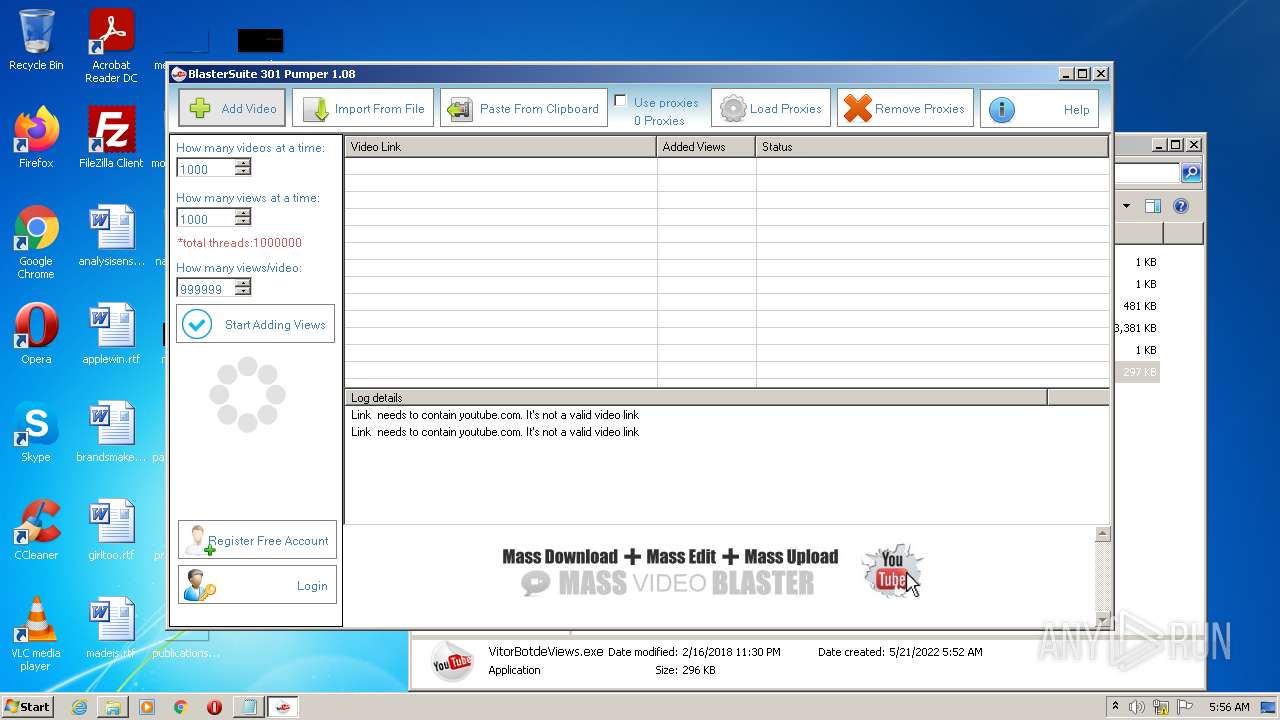
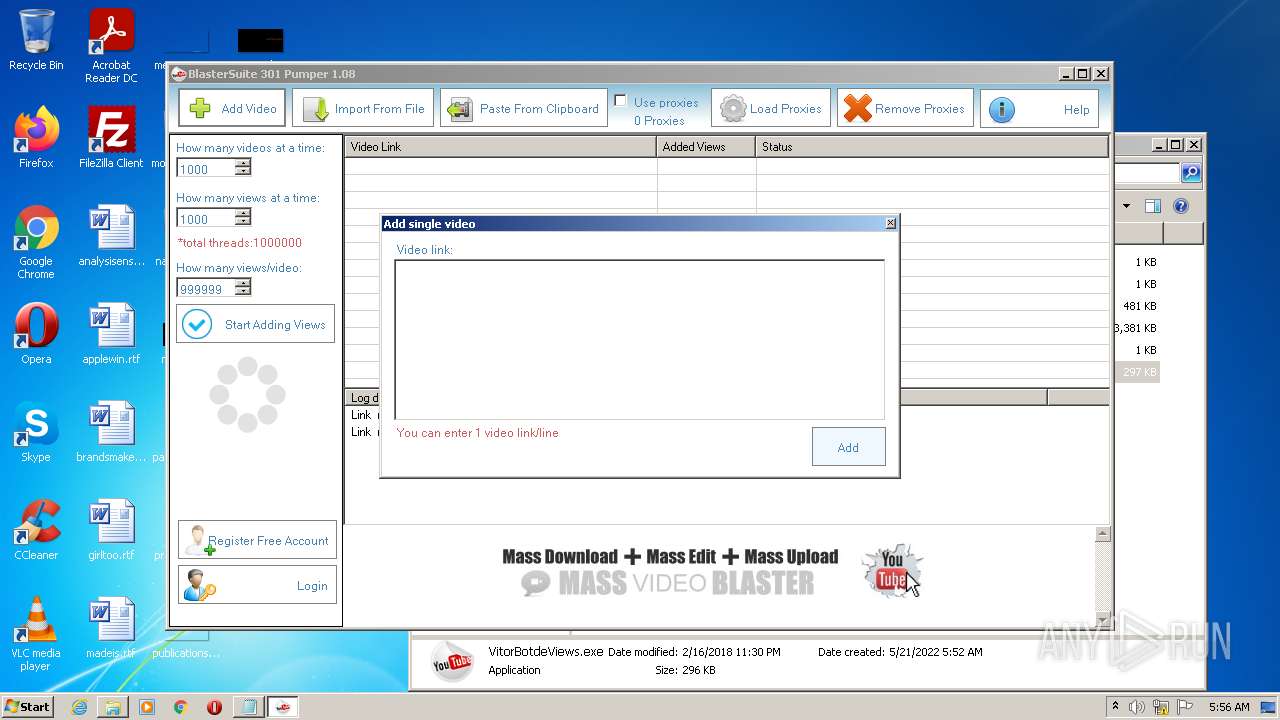
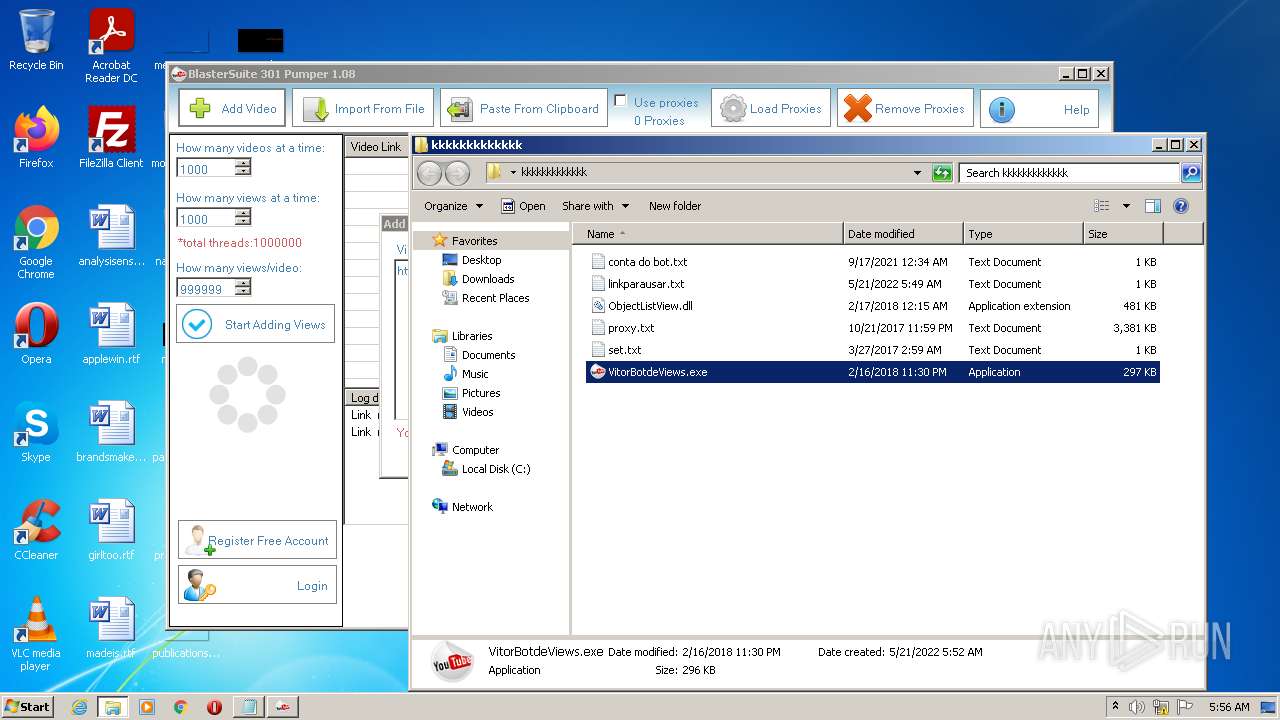
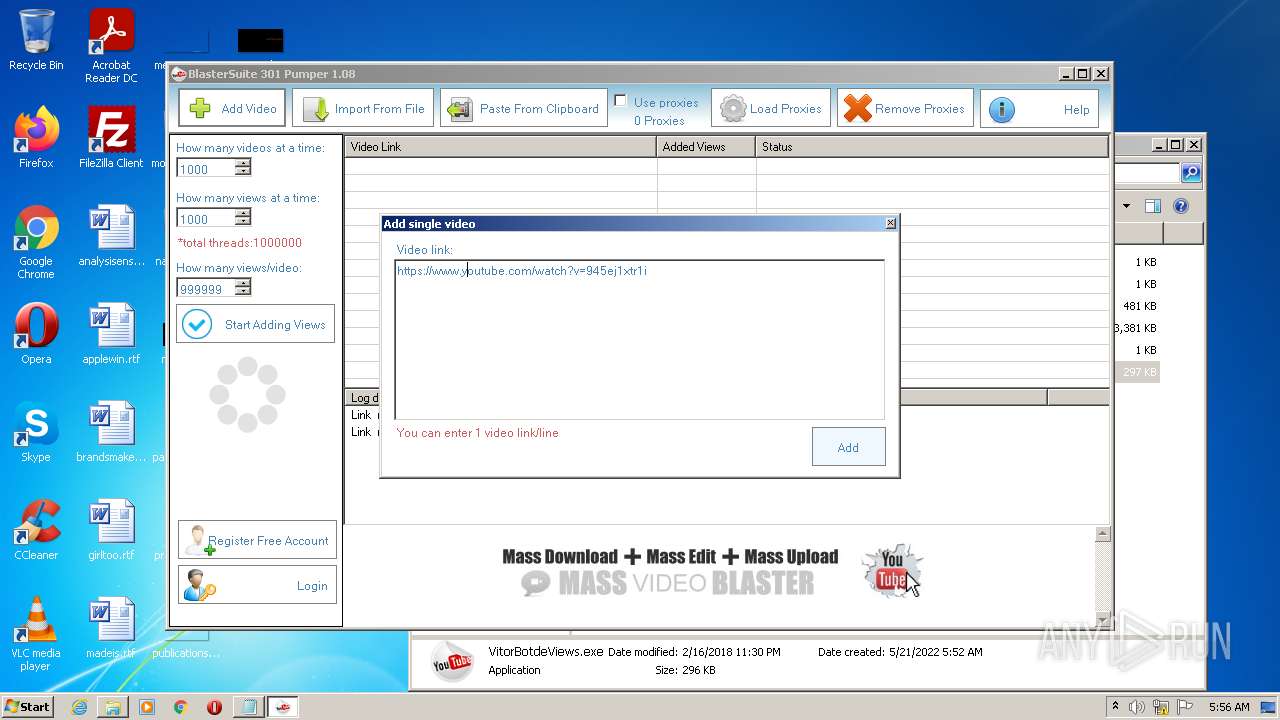
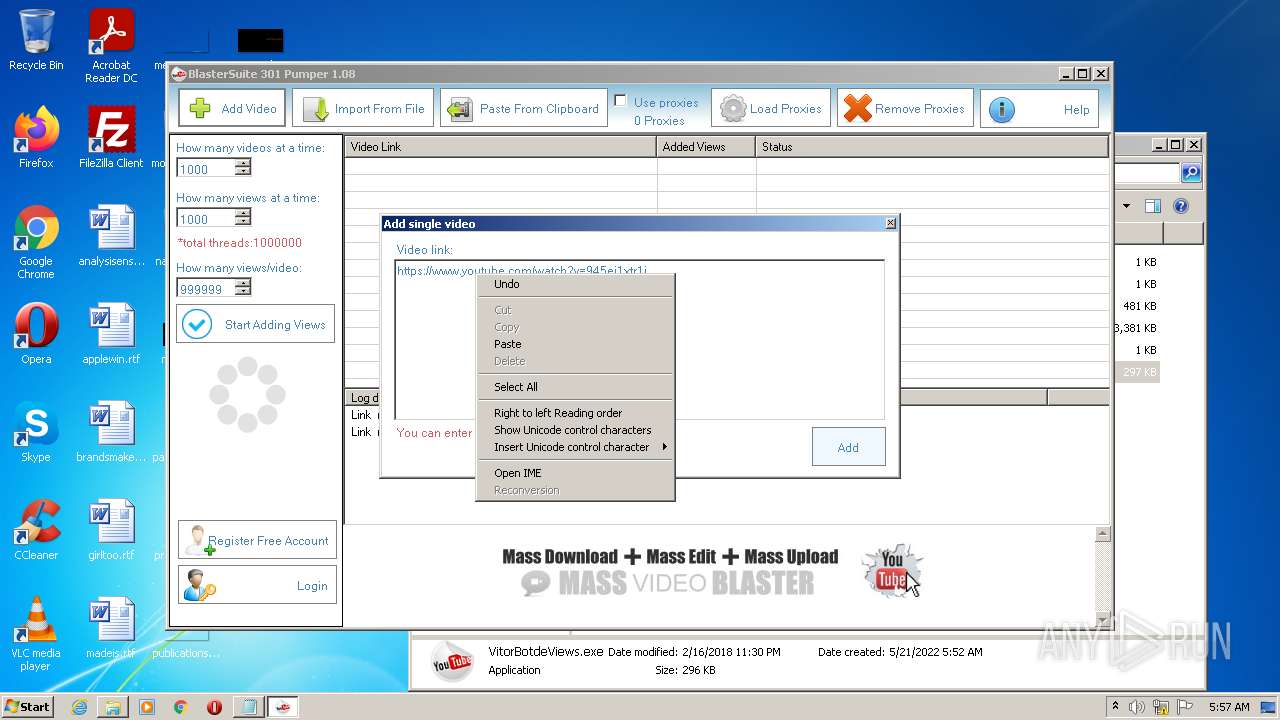
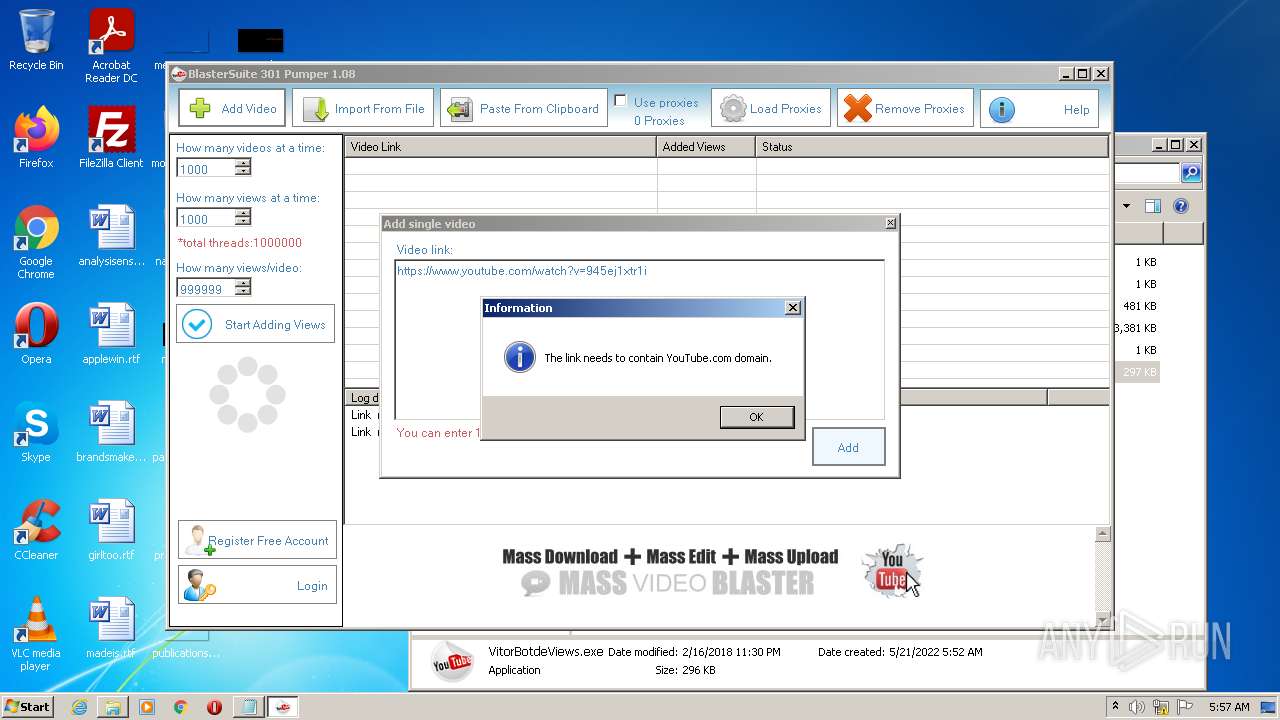
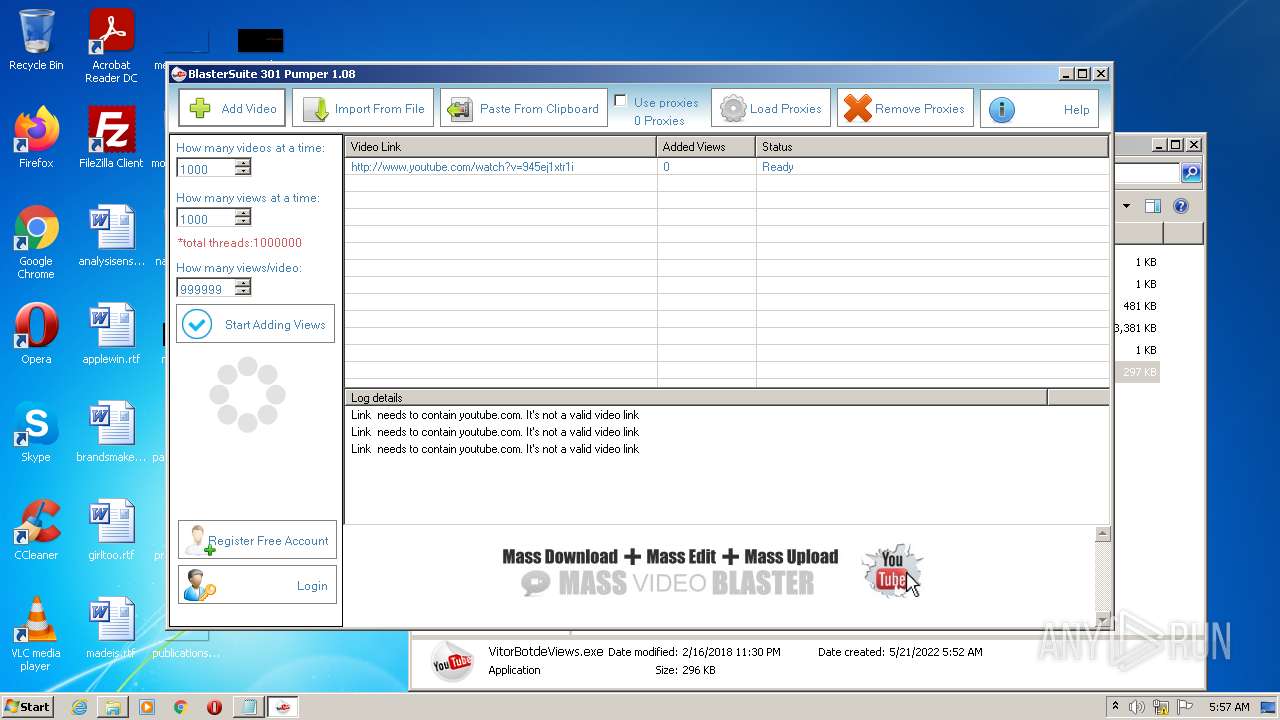
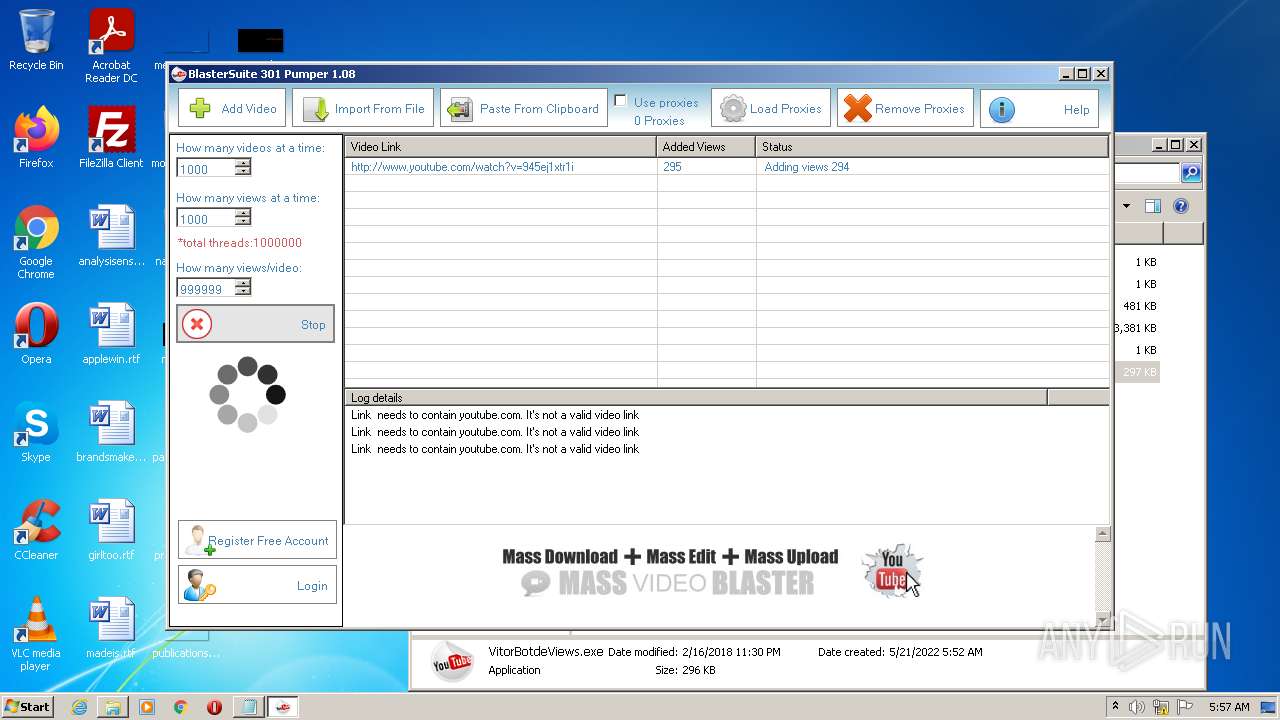
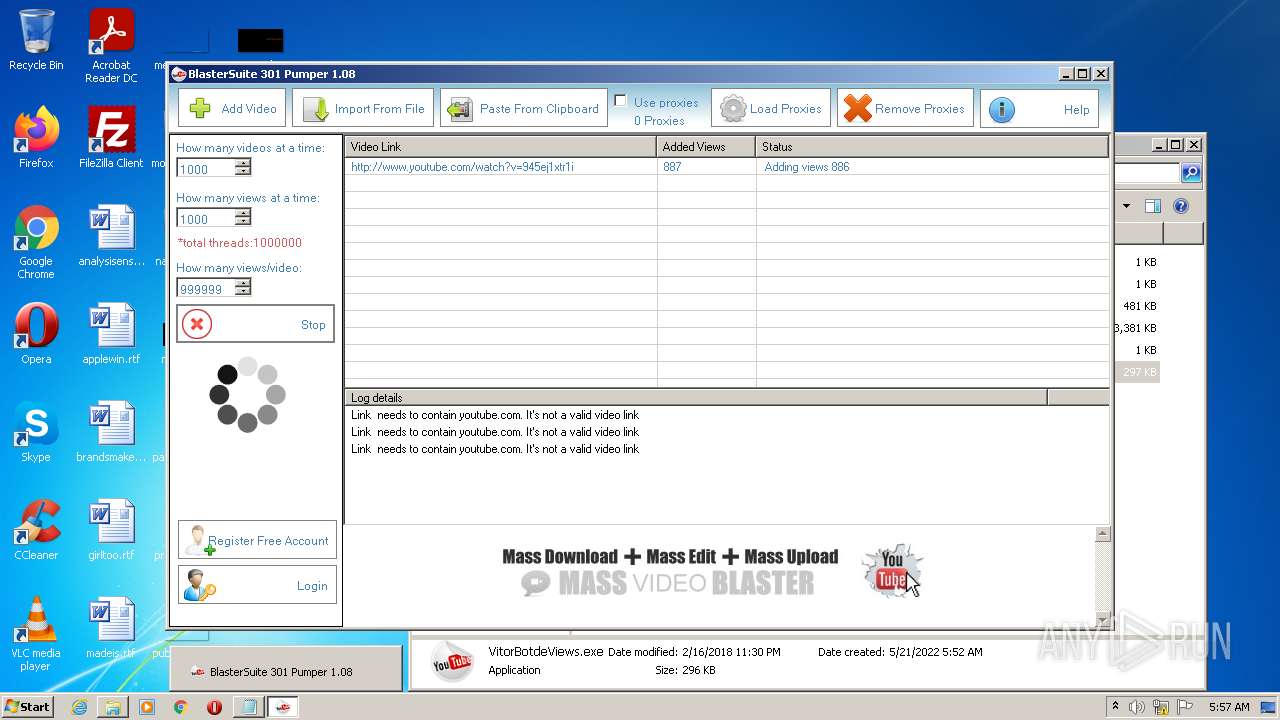
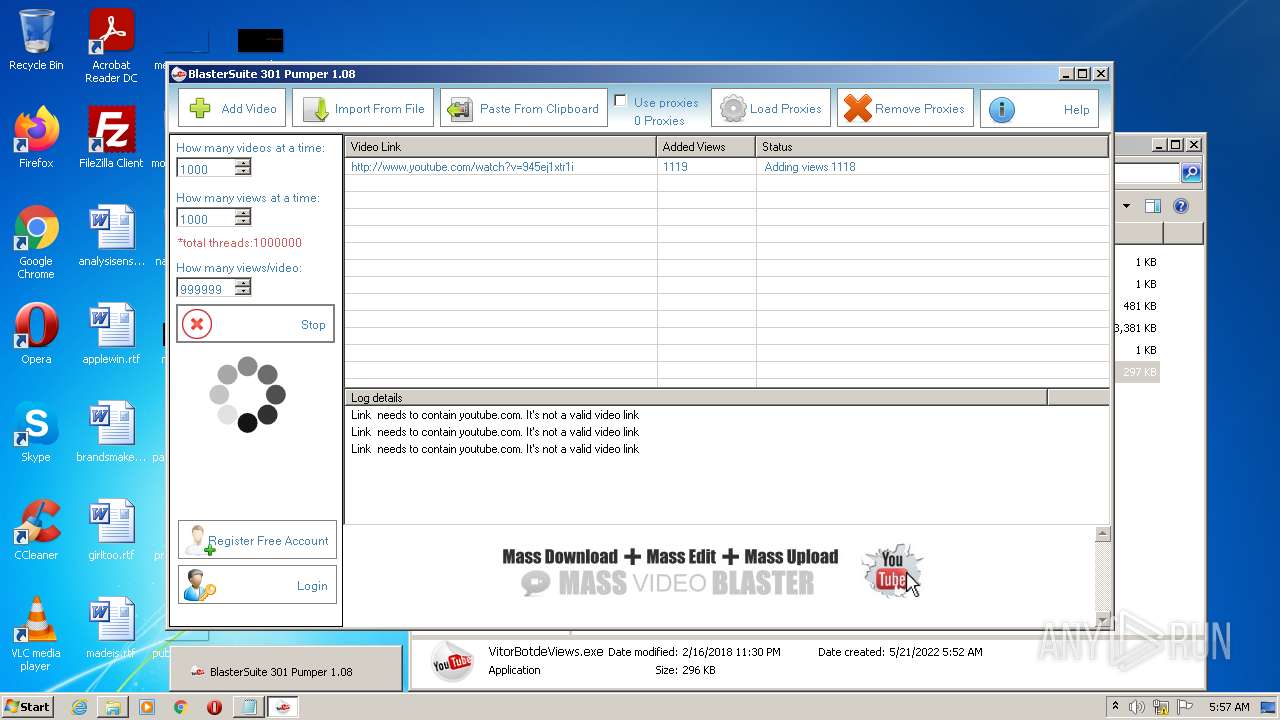
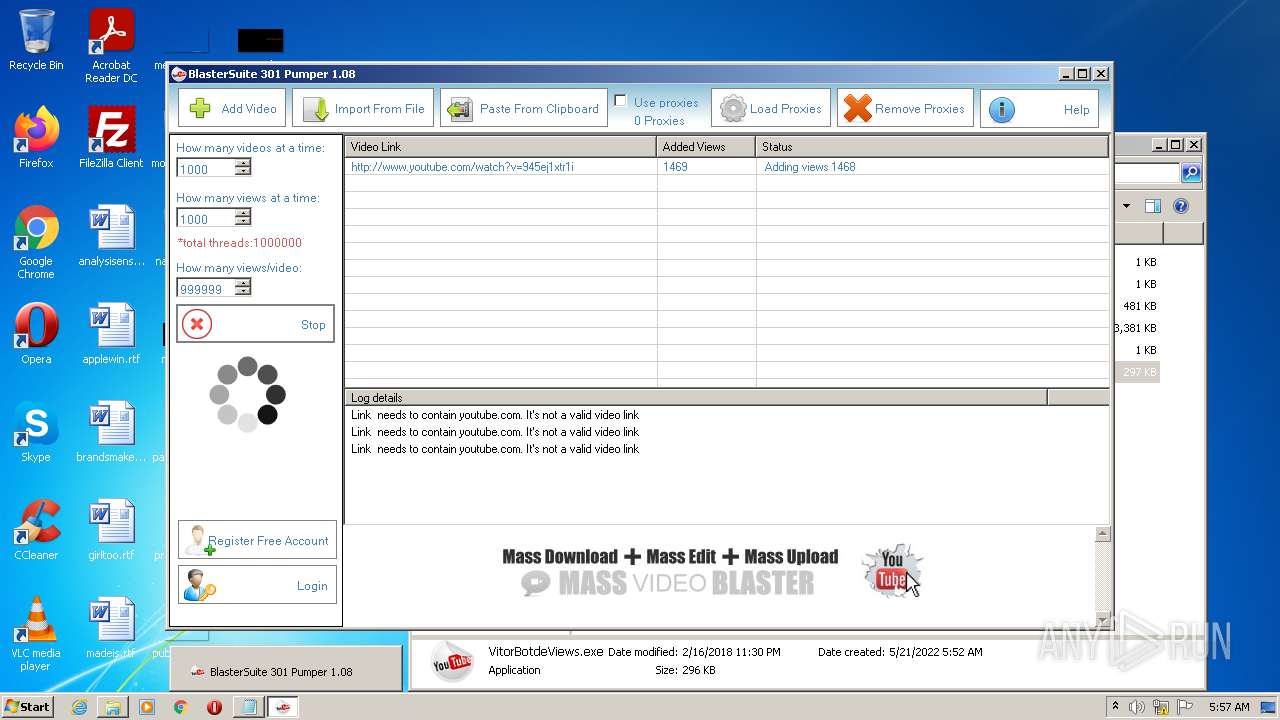
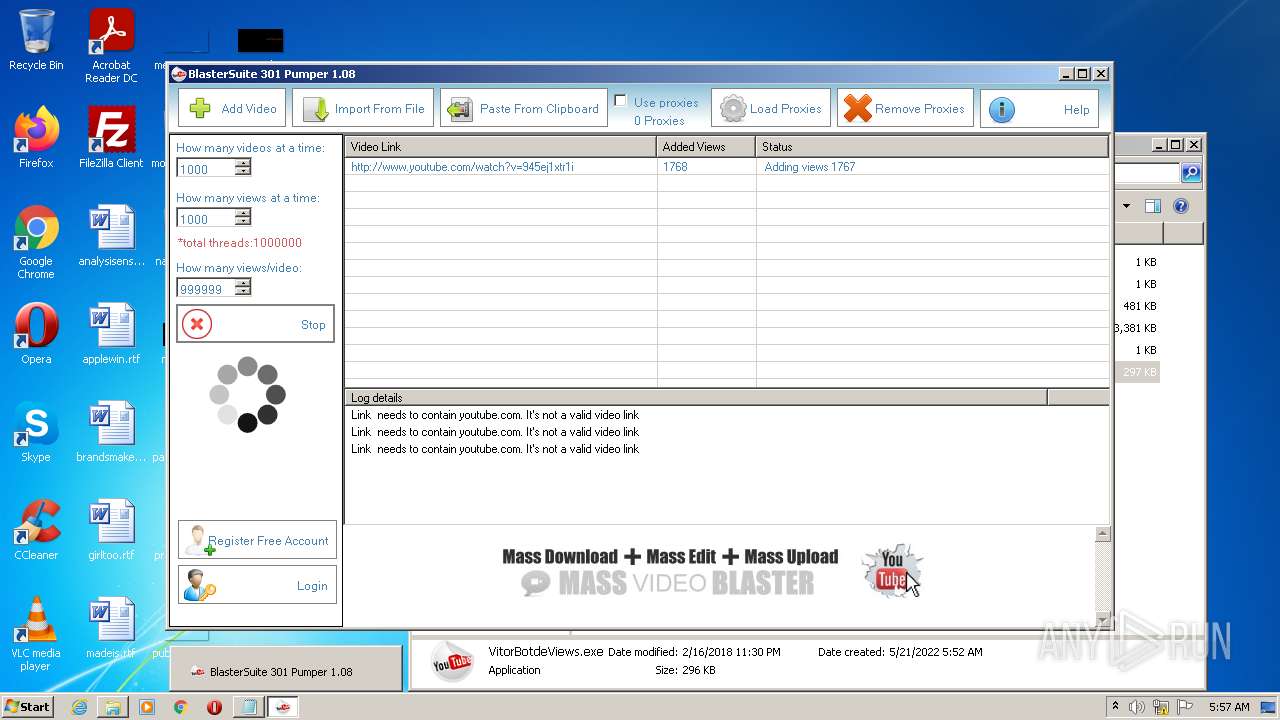
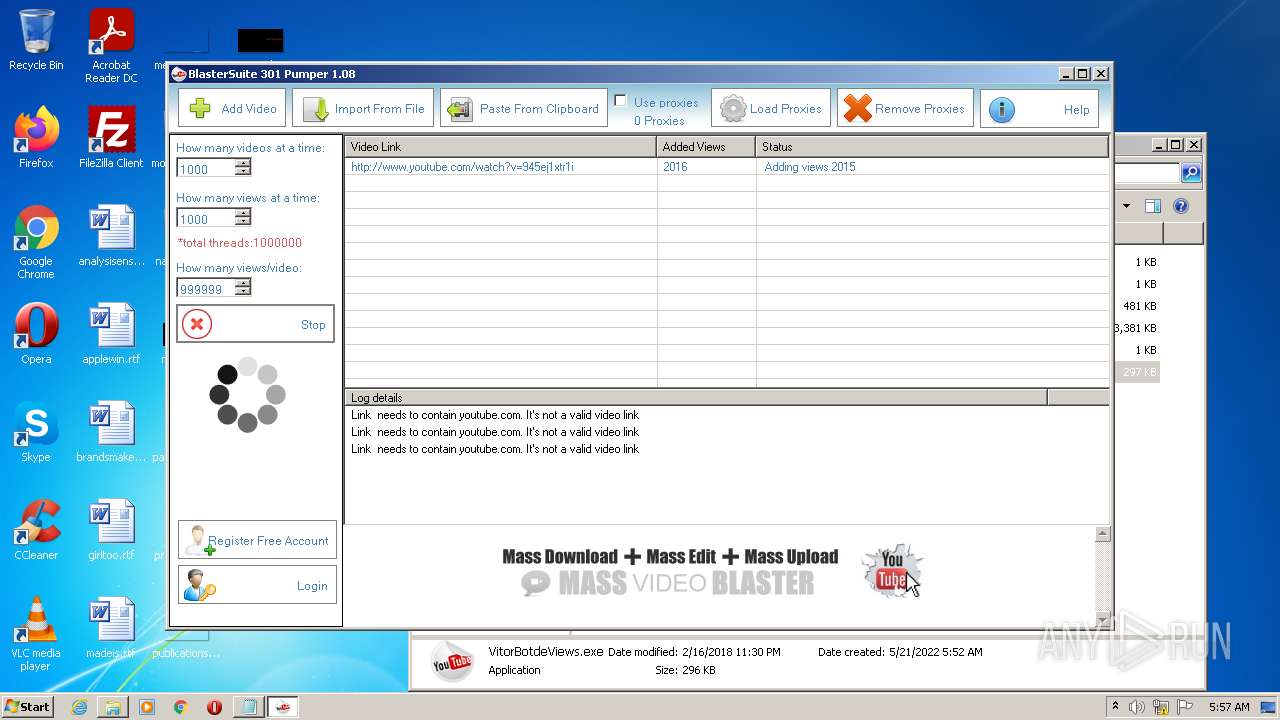
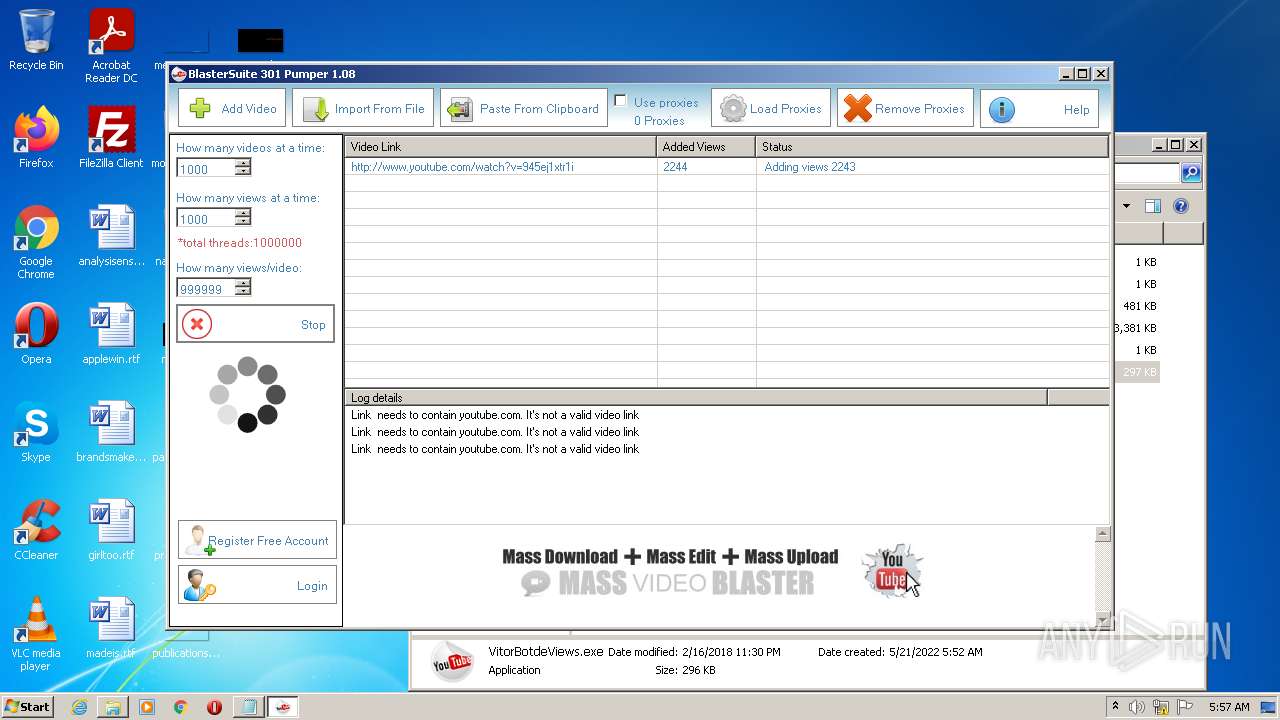
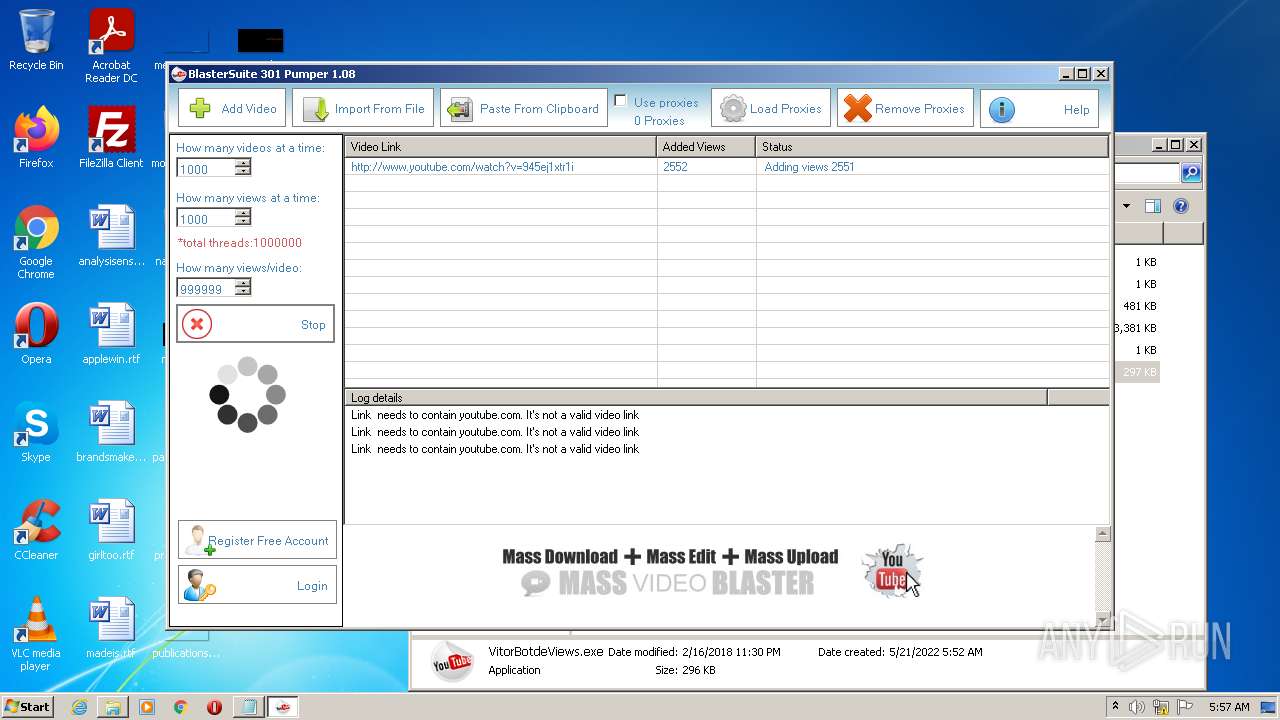
| 1728 | "C:\Users\admin\Desktop\kkkkkkkkkkkkk\VitorBotdeViews.exe" | C:\Users\admin\Desktop\kkkkkkkkkkkkk\VitorBotdeViews.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 301ViewPumper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2860 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\kkkkkkkkkkkkk.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3564 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 5316 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.youtube.com/watch?v=945ej1xtr1i | C:\Program Files\Internet Explorer\iexplore.exe | VitorBotdeViews.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 7340 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:5316 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
21 419
Read events
21 220
Write events
194
Delete events
5
Modification events
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\kkkkkkkkkkkkk.zip | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
15
Text files
25
Unknown types
21
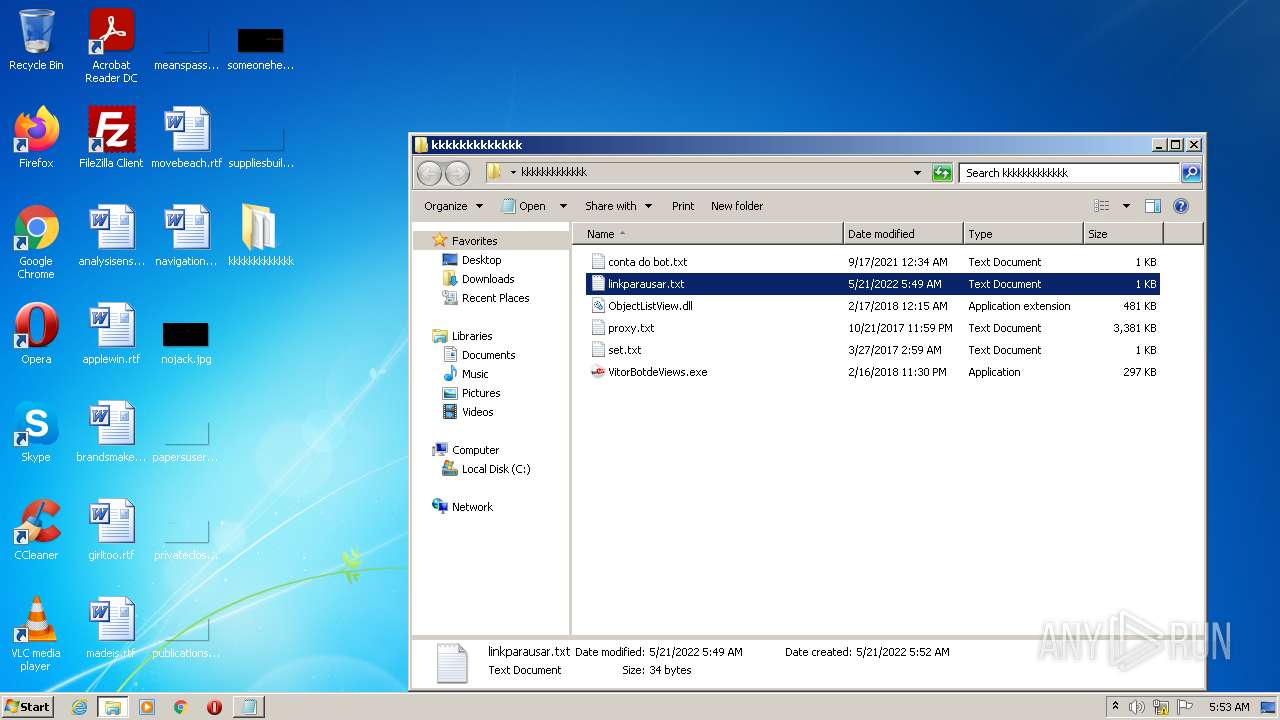
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2860 | WinRAR.exe | C:\Users\admin\Desktop\kkkkkkkkkkkkk\ObjectListView.dll | executable | |
MD5:— | SHA256:— | |||
| 1728 | VitorBotdeViews.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\reclama_dreapta[1].htm | html | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\Desktop\kkkkkkkkkkkkk\conta do bot.txt | text | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\Desktop\kkkkkkkkkkkkk\linkparausar.txt | text | |
MD5:— | SHA256:— | |||
| 1728 | VitorBotdeViews.exe | C:\Users\admin\AppData\Roaming\301Pumper\links.fdt | pi2 | |
MD5:— | SHA256:— | |||
| 1728 | VitorBotdeViews.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\reclama_imagine[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\Desktop\kkkkkkkkkkkkk\proxy.txt | text | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\Desktop\kkkkkkkkkkkkk\VitorBotdeViews.exe | executable | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\Desktop\kkkkkkkkkkkkk\set.txt | text | |
MD5:— | SHA256:— | |||
| 7340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
324
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1728 | VitorBotdeViews.exe | GET | 200 | 158.69.225.63:80 | http://blastersuite.com/301views/reclama_imagine.jpg | CA | image | 9.59 Kb | whitelisted |
1728 | VitorBotdeViews.exe | GET | 200 | 158.69.225.63:80 | http://blastersuite.com/301views/check_reg.php?email=&code= | CA | text | 18 b | whitelisted |
7340 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
7340 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCdUrA%2FwvrytArhIvu6cF3d | US | der | 472 b | whitelisted |
7340 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEG3aTvFLTYzNCmxS2fUJutw%3D | US | der | 471 b | whitelisted |
5316 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
7340 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDExSUZ712qmxLhqE9UUaDV | US | der | 472 b | whitelisted |
1728 | VitorBotdeViews.exe | GET | 200 | 158.69.225.63:80 | http://blastersuite.com/301views/reclama_dreapta.html | CA | html | 187 b | whitelisted |
1728 | VitorBotdeViews.exe | GET | 200 | 158.69.225.63:80 | http://blastersuite.com/301views/version.txt | CA | text | 4 b | whitelisted |
7340 | iexplore.exe | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7314a71fd6d42cb5 | DE | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1728 | VitorBotdeViews.exe | 158.69.225.63:80 | blastersuite.com | OVH SAS | CA | suspicious |
1728 | VitorBotdeViews.exe | 142.250.186.46:443 | www.youtube.com | Google Inc. | US | whitelisted |
1728 | VitorBotdeViews.exe | 209.85.200.113:443 | s.youtube.com | Google Inc. | US | unknown |
— | — | 142.250.186.46:443 | www.youtube.com | Google Inc. | US | whitelisted |
1728 | VitorBotdeViews.exe | 142.250.185.206:443 | www.youtube.com | Google Inc. | US | whitelisted |
— | — | 209.85.200.113:443 | s.youtube.com | Google Inc. | US | unknown |
7340 | iexplore.exe | 178.79.242.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | whitelisted |
7340 | iexplore.exe | 178.79.242.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | malicious |
7340 | iexplore.exe | 142.250.185.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
7340 | iexplore.exe | 142.250.185.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blastersuite.com |
| whitelisted |
www.youtube.com |
| whitelisted |
m.youtube.com |
| whitelisted |
s.youtube.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1728 | VitorBotdeViews.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |