| File name: | Game.exe |
| Full analysis: | https://app.any.run/tasks/8f278224-fef2-4803-9bb0-665b01b911ae |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 17:46:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | A96DCA30D4E8FCADC623F0AE5AECBEE5 |
| SHA1: | 30691B52636D543330C7E86B12E238A9C43B8888 |
| SHA256: | 13264185B8B2EEE6CCF1324B55987E4AF4FDEAFF19CA180AE19027960DAC5731 |
| SSDEEP: | 6144:2/pzWDzYxuxYonBdzkjZipHfKj88Dbtbd:6WDzYxuxYcdzcZip/f8DJZ |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 5548)
- powershell.exe (PID: 6344)
Run PowerShell with an invisible window
- powershell.exe (PID: 6344)
- powershell.exe (PID: 5548)
SUSPICIOUS
Reads security settings of Internet Explorer
- Game.exe (PID: 7464)
- Game_patch-run.exe (PID: 7508)
Executable content was dropped or overwritten
- Game.exe (PID: 7464)
- Game_patch-run.exe (PID: 7508)
Starts itself from another location
- Game.exe (PID: 7464)
The process creates files with name similar to system file names
- Game_patch-run.exe (PID: 7508)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7712)
Malware-specific behavior (creating "System.dll" in Temp)
- Game_patch-run.exe (PID: 7508)
Starts CMD.EXE for commands execution
- Game_patch-run.exe (PID: 7508)
- cmd.exe (PID: 7712)
Executing commands from a ".bat" file
- Game_patch-run.exe (PID: 7508)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7712)
- cmd.exe (PID: 1568)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7712)
Application launched itself
- cmd.exe (PID: 7712)
Manipulates environment variables
- powershell.exe (PID: 5548)
- powershell.exe (PID: 968)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7712)
The process executes Powershell scripts
- cmd.exe (PID: 7712)
There is functionality for taking screenshot (YARA)
- Game_patch-run.exe (PID: 7508)
Executes application which crashes
- Game.exe (PID: 7548)
INFO
Create files in a temporary directory
- Game.exe (PID: 7464)
- Game_patch-run.exe (PID: 7508)
Checks supported languages
- Game.exe (PID: 7464)
- Game_patch-run.exe (PID: 7508)
- identity_helper.exe (PID: 5968)
- Game.exe (PID: 7548)
Reads the computer name
- Game.exe (PID: 7464)
- Game_patch-run.exe (PID: 7508)
- Game.exe (PID: 7548)
Process checks computer location settings
- Game.exe (PID: 7464)
- Game_patch-run.exe (PID: 7508)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 2088)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 2088)
- Game_patch-run.exe (PID: 7508)
Application launched itself
- msedge.exe (PID: 4068)
- msedge.exe (PID: 7152)
Manual execution by a user
- msedge.exe (PID: 7152)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 4740)
- powershell.exe (PID: 968)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7268)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 6344)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 2088)
Reads the machine GUID from the registry
- Game.exe (PID: 7548)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 2088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:07:02 02:09:43+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 139776 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3645 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
195
Monitored processes
59
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4364 --field-trial-handle=2424,i,12563957144283483700,5459678423421546740,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | powershell -Command "(Get-Content -Path 'C:\Users\admin\AppData\Local\cache.ps1').Replace('{UNI}', "$env:LOCALAPPDATA") | Set-Content -Path 'C:\Users\admin\AppData\Local\cache.ps1'" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | C:\WINDOWS\system32\cmd.exe /c powershell -command "gp 'HKCU:\Control Panel\International\Geo\' | select -exp Name" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ffc89c85fd8,0x7ffc89c85fe4,0x7ffc89c85ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6648 --field-trial-handle=2424,i,12563957144283483700,5459678423421546740,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2088 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6660 --field-trial-handle=2424,i,12563957144283483700,5459678423421546740,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5572 --field-trial-handle=2424,i,12563957144283483700,5459678423421546740,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3896 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3832 --field-trial-handle=2424,i,12563957144283483700,5459678423421546740,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
40 404
Read events
40 343
Write events
58
Delete events
3
Modification events
| (PID) Process: | (7720) WerFault.exe | Key: | \REGISTRY\A\{78a2fa9b-8066-f3ad-08e4-cec04f39606e}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (7720) WerFault.exe | Key: | \REGISTRY\A\{78a2fa9b-8066-f3ad-08e4-cec04f39606e}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7356) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7356) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7356) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2088) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2088) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2088) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5800) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5800) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
9
Suspicious files
102
Text files
59
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7720 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_Game.exe_e6159ebf926c70ee51b3becda91393bfb8c3a_ec47739b_763b3ee9-4835-4599-a836-c8c34269c4e2\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7720 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Game.exe.7548.dmp | — | |
MD5:— | SHA256:— | |||
| 2088 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\91510a0a-b28f-4919-80fe-da5509787c86.down_data | — | |
MD5:— | SHA256:— | |||
| 7508 | Game_patch-run.exe | C:\Users\admin\AppData\Local\Temp\Game.exe | executable | |
MD5:C2F26DCF03CE79D120884CB0EC4B8090 | SHA256:8A191BE25D13DDC8EDB54BA5FBD8D19B9F2CC6D7EE6471190C8E641C88189C2B | |||
| 7720 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERD43A.tmp.dmp | binary | |
MD5:269A7A42CB742691CA4624AFFF47E7AB | SHA256:B25C0B5BC5432085BB29860AE4128E36AE2D9BB49545B8AEDA9B5E9BFBE51B82 | |||
| 7720 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERD630.tmp.xml | xml | |
MD5:E466C9C75D9C292AA14EDC280EDE4F1C | SHA256:724F0CD4FB751DB38C49CFE32A7075BD3157E67C7215A76C1D3908D80BA98D4A | |||
| 7720 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERD5E1.tmp.WERInternalMetadata.xml | xml | |
MD5:50817B10599966E33AA5F148DFAF81CE | SHA256:B6B728B449594BBA801C1F68958001BCB6F3C20EDC5EB5EF3C038143E13511B0 | |||
| 7464 | Game.exe | C:\Users\admin\AppData\Local\Temp\Game_patch-run.exe | executable | |
MD5:A96DCA30D4E8FCADC623F0AE5AECBEE5 | SHA256:13264185B8B2EEE6CCF1324B55987E4AF4FDEAFF19CA180AE19027960DAC5731 | |||
| 7508 | Game_patch-run.exe | C:\Users\admin\AppData\Local\Temp\temp_cleanup.ico | text | |
MD5:8D893A385D8BADA26E83E6B4D3EC4A61 | SHA256:B3B47A5E4DDE5F5E9DC0AF07FA92990F6BE632BB6DBBA24915A714493FDD8C52 | |||
| 7720 | WerFault.exe | C:\Windows\appcompat\Programs\Amcache.hve | binary | |
MD5:D054B99F9B6E0DEEE5E0E7BCB7428256 | SHA256:666D704A205AB53F52DBE09E7E7D2B9AE0A8B2D35551395A79F96AF05C2BDC49 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
68
DNS requests
68
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.169:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7784 | SIHClient.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7596 | backgroundTaskHost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7784 | SIHClient.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2088 | BackgroundTransferHost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.169:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 23.63.118.230:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7596 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
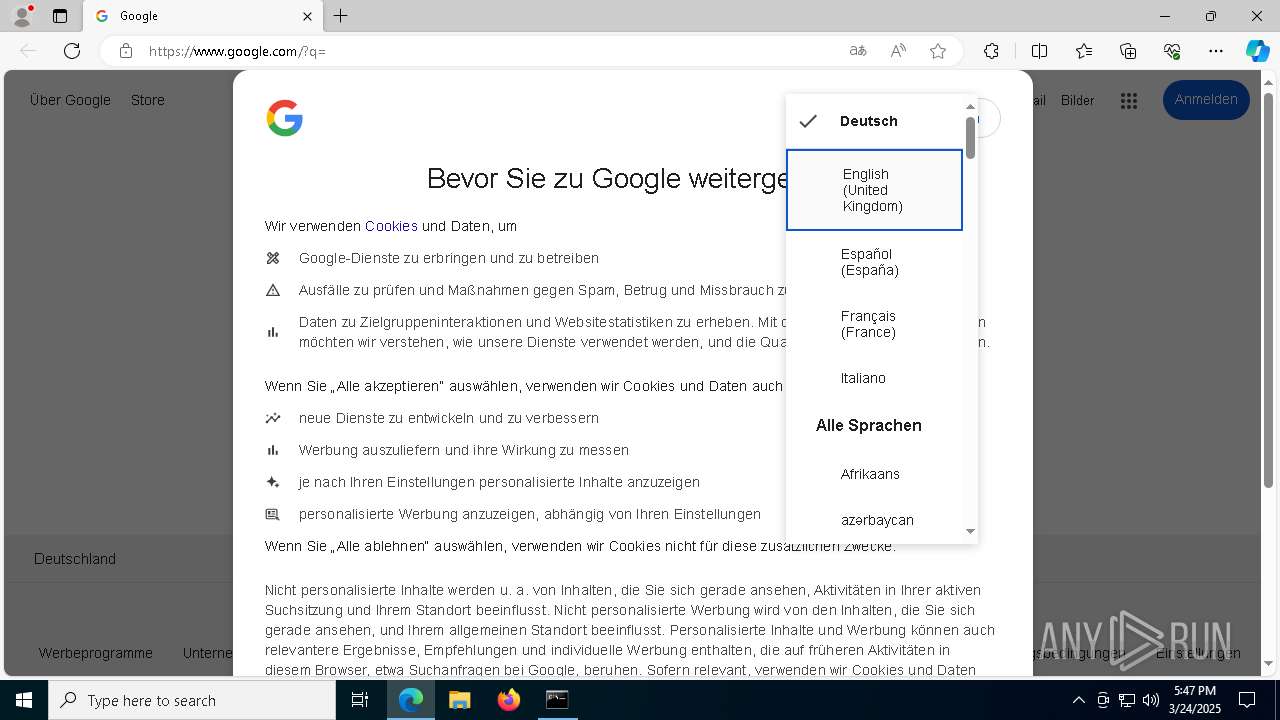
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |