| File name: | 131eaf37b939f2be9f3e250bc2ae8ba44546801b5ca6268f3a2514e6a9cb8b5c.apk |
| Full analysis: | https://app.any.run/tasks/27e699df-b754-4ddd-9bcb-997f5a98150f |
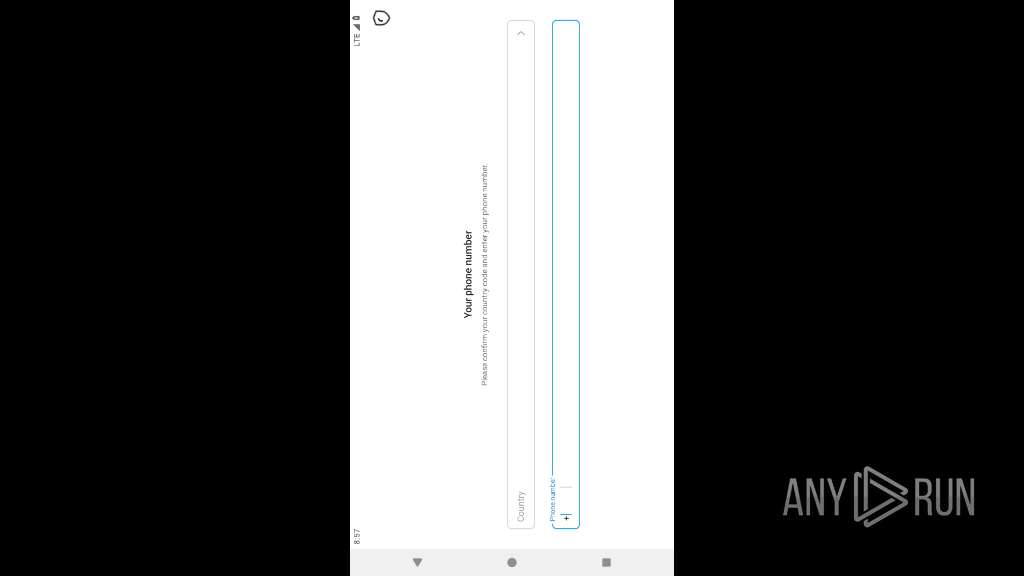
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2025, 20:57:02 |
| OS: | Android 14 |
| Tags: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 25FAEE9BBF214D975415AE4BD2BCD7B9 |
| SHA1: | 06F8CA016B2BF006702501263818B7606851F106 |
| SHA256: | 131EAF37B939F2BE9F3E250BC2AE8BA44546801B5CA6268F3A2514E6A9CB8B5C |
| SSDEEP: | 786432:miYJNvZ81Fcw3BhJZT/dG7EgoRTf65rcIXalr8FI5Q:GZ8TpZT/AoT565rcIkr8 |
MALICIOUS
Executes system commands or scripts
- app_process64 (PID: 2266)
Checks whether the screen is currently on
- app_process64 (PID: 2266)
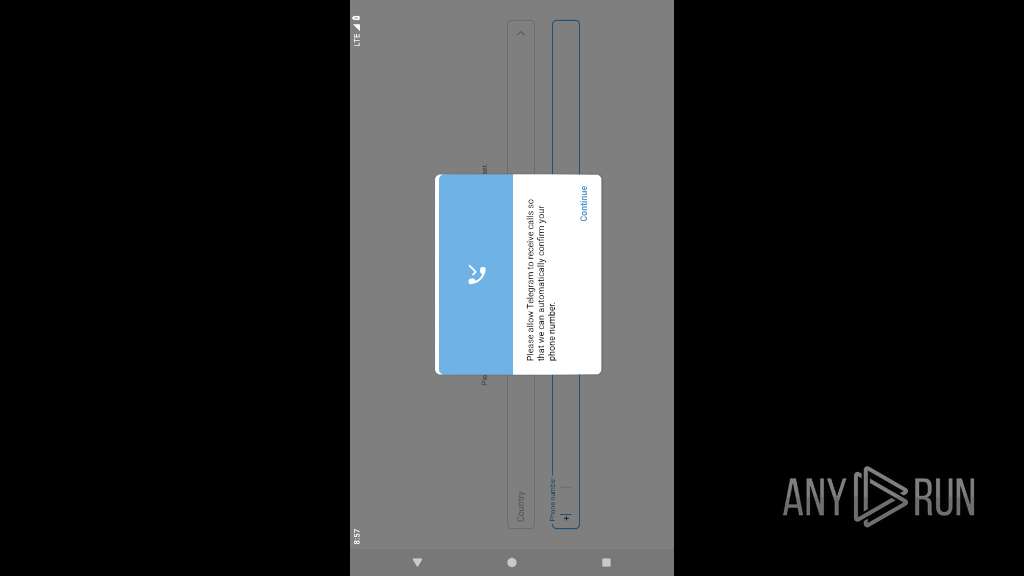
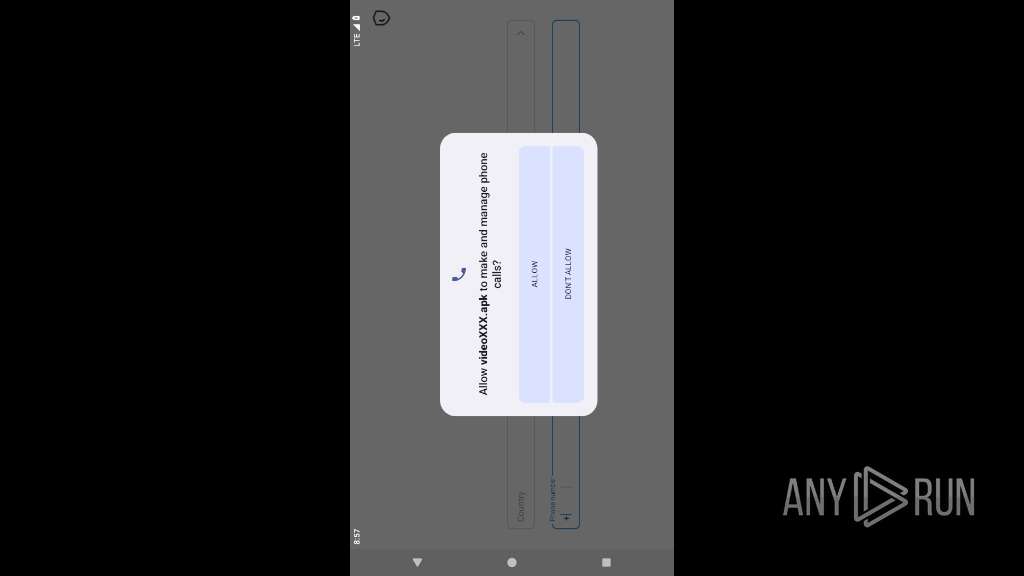
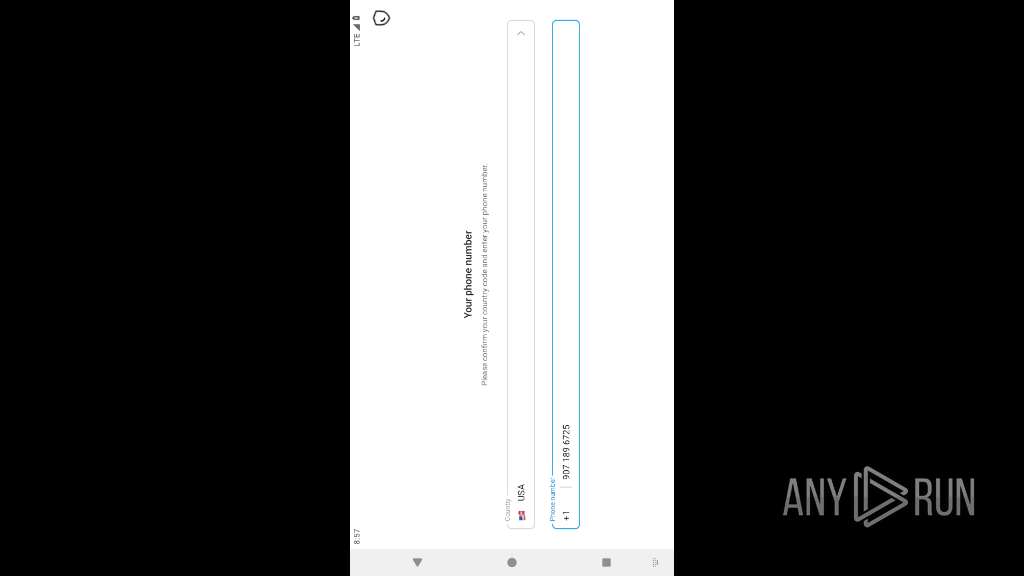
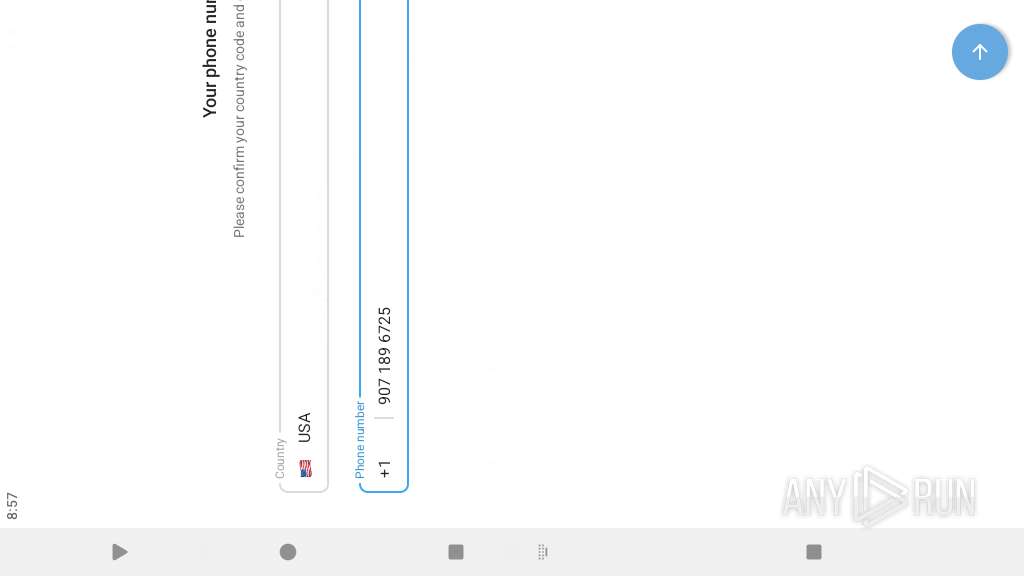
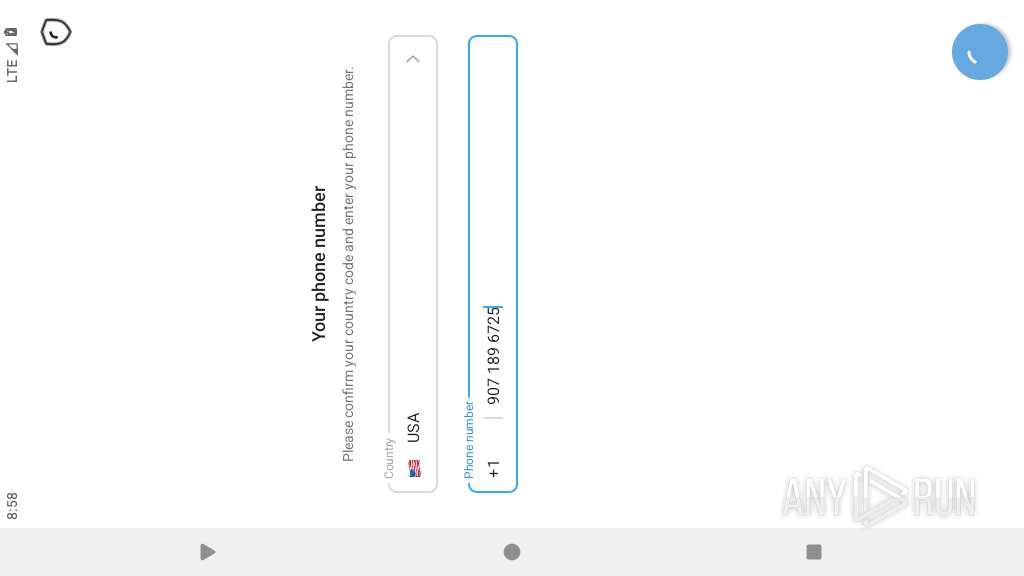
Returns the phone's primary line number (MSISDN)
- app_process64 (PID: 2266)
SUSPICIOUS
Retrieves a list of running application processes
- app_process64 (PID: 2266)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2266)
Scans for popular installed apps
- app_process64 (PID: 2266)
Uses encryption API functions
- app_process64 (PID: 2266)
Detects presence of QEMU emulator
- app_process64 (PID: 2266)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2266)
Establishing a connection
- app_process64 (PID: 2266)
Accesses external device storage files
- app_process64 (PID: 2266)
Detects when screen powers off
- app_process64 (PID: 2266)
Gets data of saved accounts
- app_process64 (PID: 2266)
Retrieves a list of running services
- app_process64 (PID: 2266)
Returns the unique device identifier (IMEI or MEID)
- app_process64 (PID: 2266)
Retrieves installed applications on device
- app_process64 (PID: 2266)
Executes dynamic code using class loader
- app_process64 (PID: 2266)
Creates a WakeLock to manage power state
- app_process64 (PID: 2266)
Reads device MAC address fingerprint
- app_process64 (PID: 2266)
Monitors changes in clipboard content
- app_process64 (PID: 2266)
Reads device bootloader configuration
- app_process64 (PID: 2266)
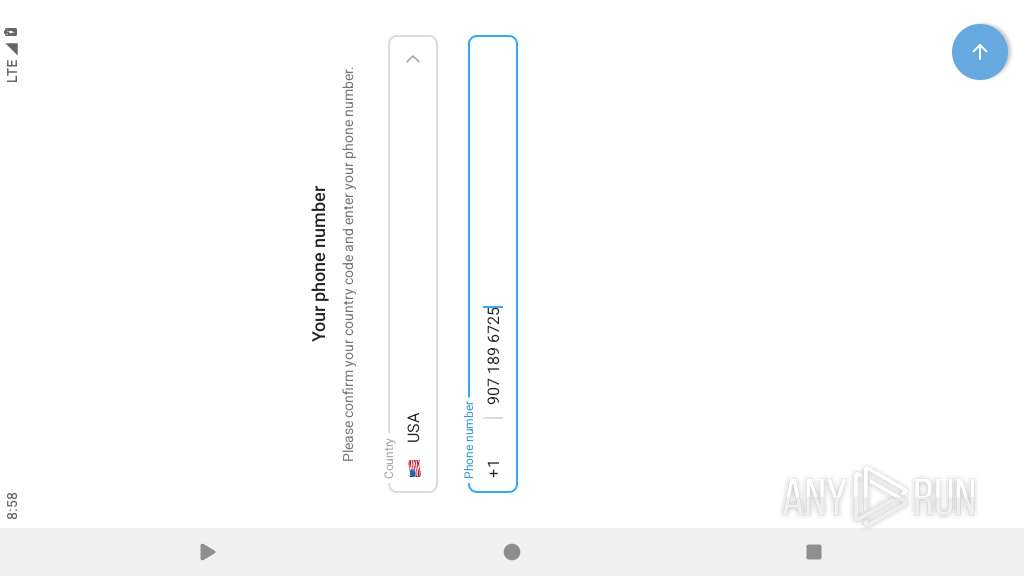
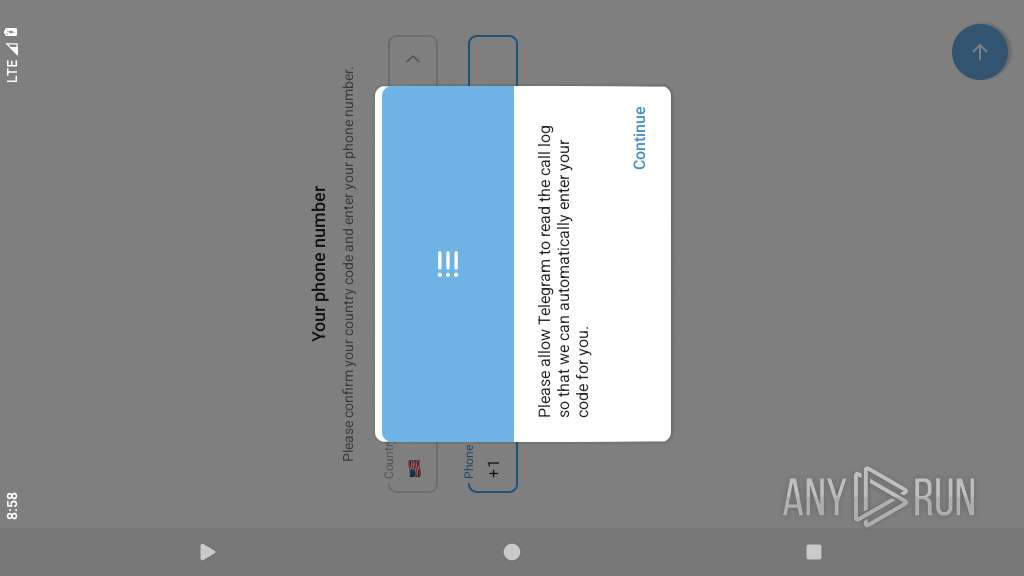
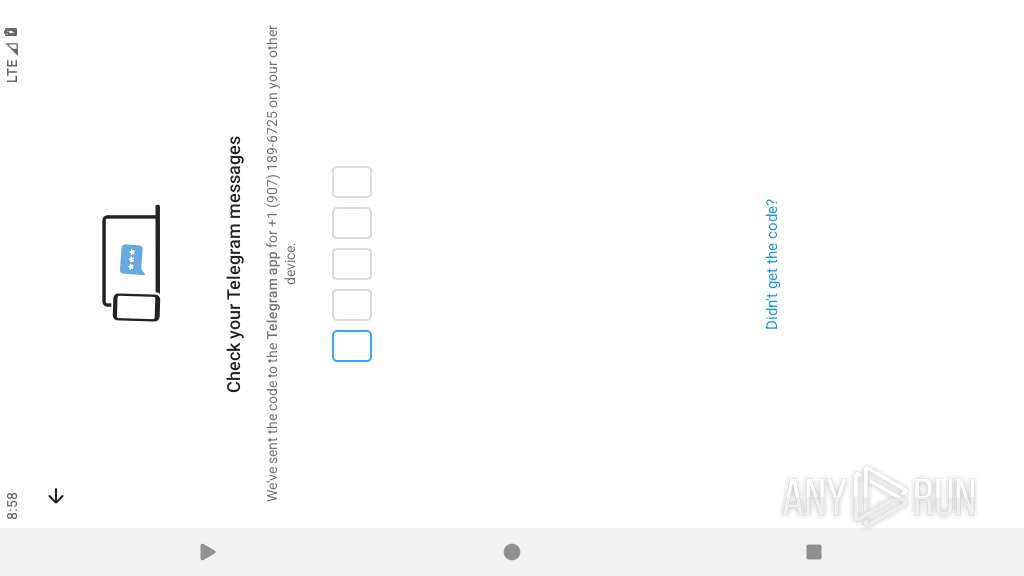
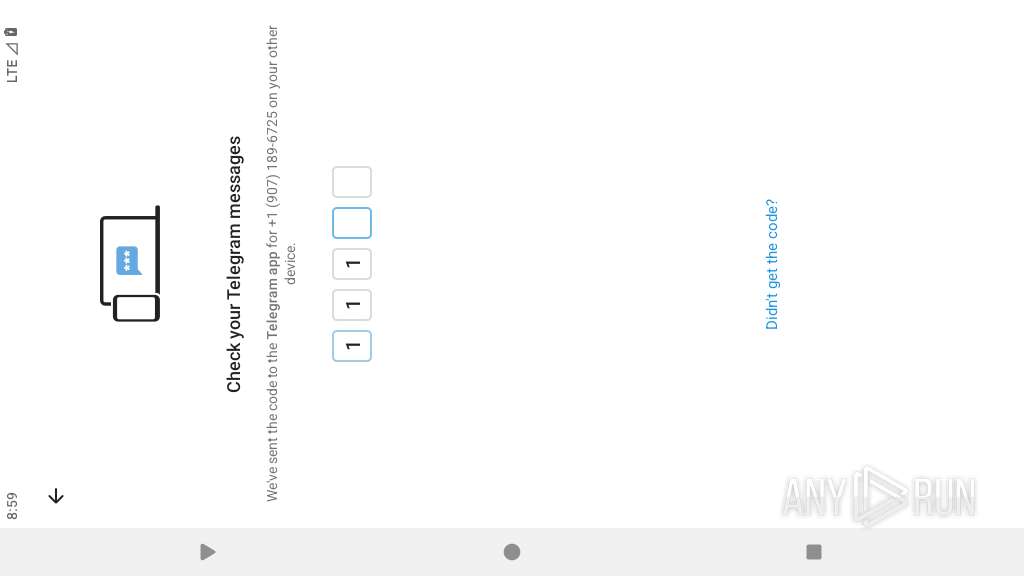
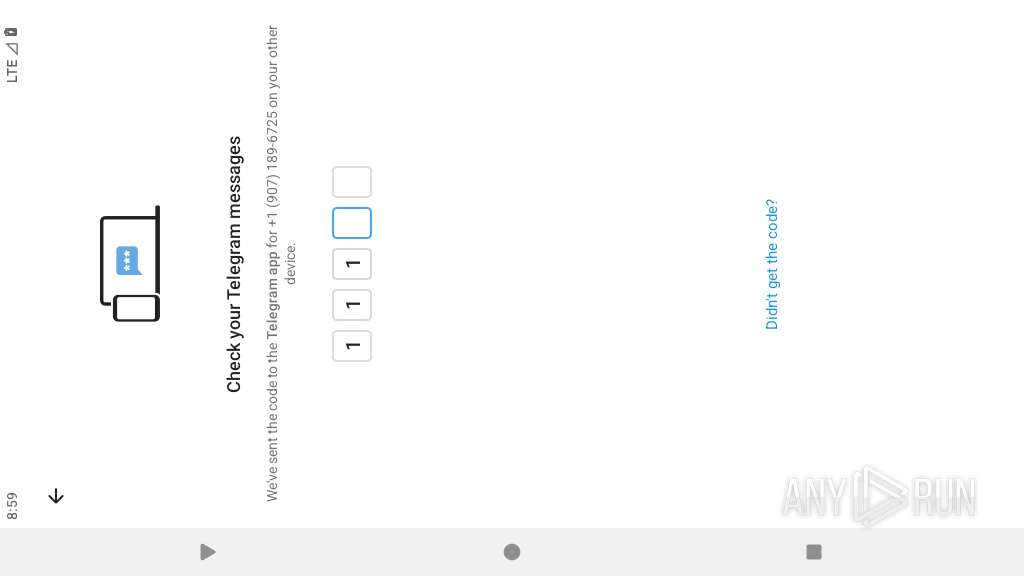
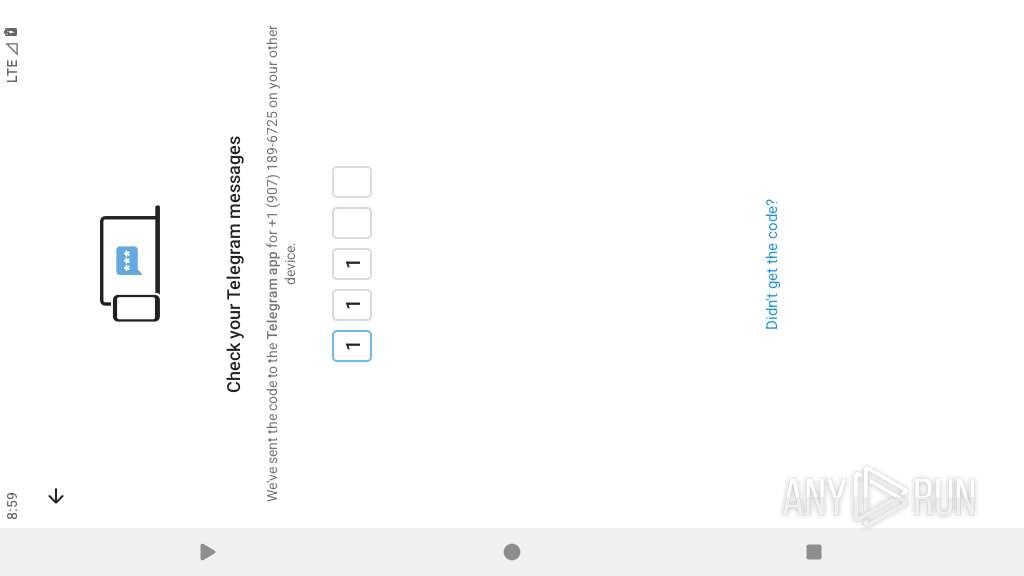
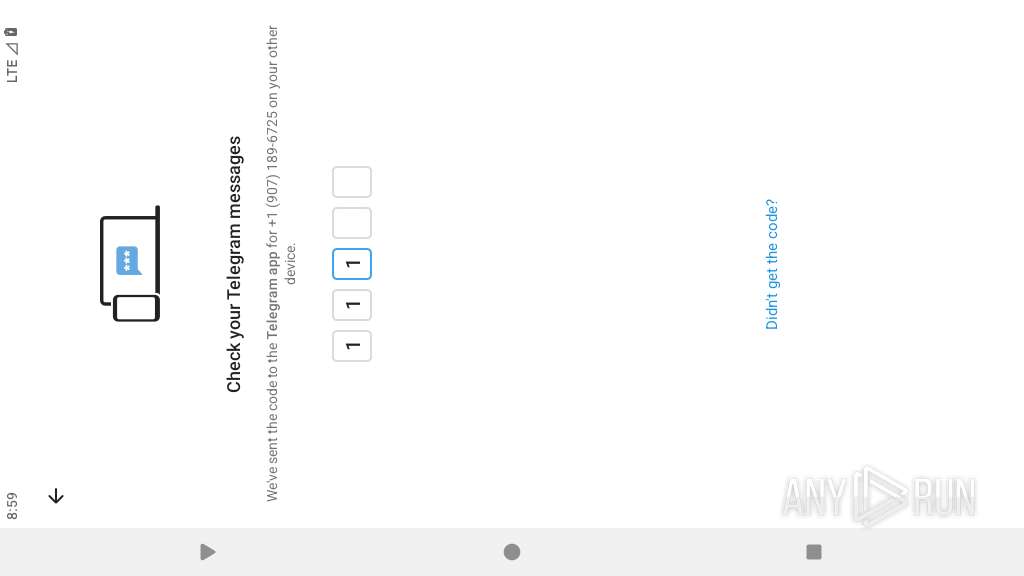
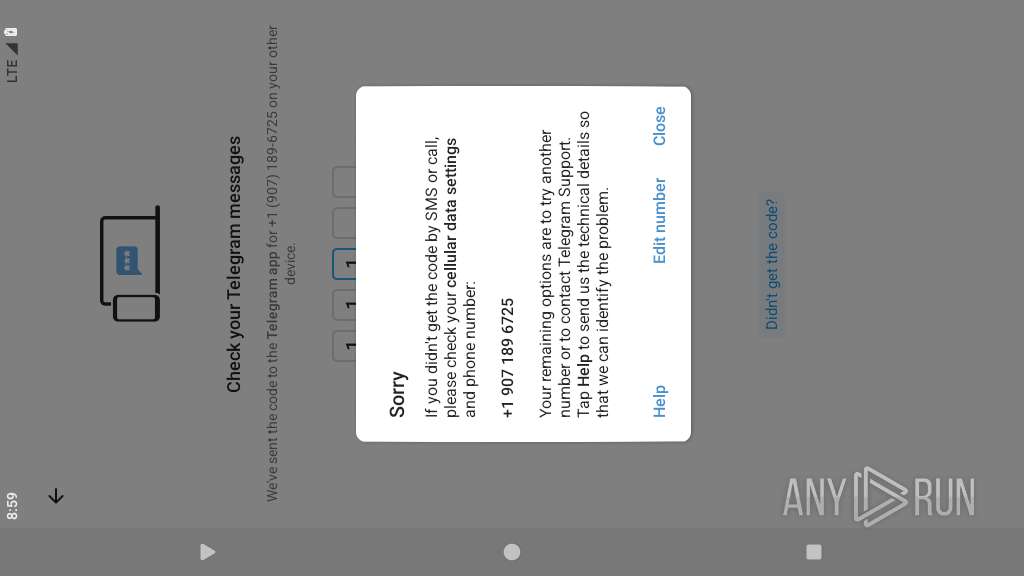
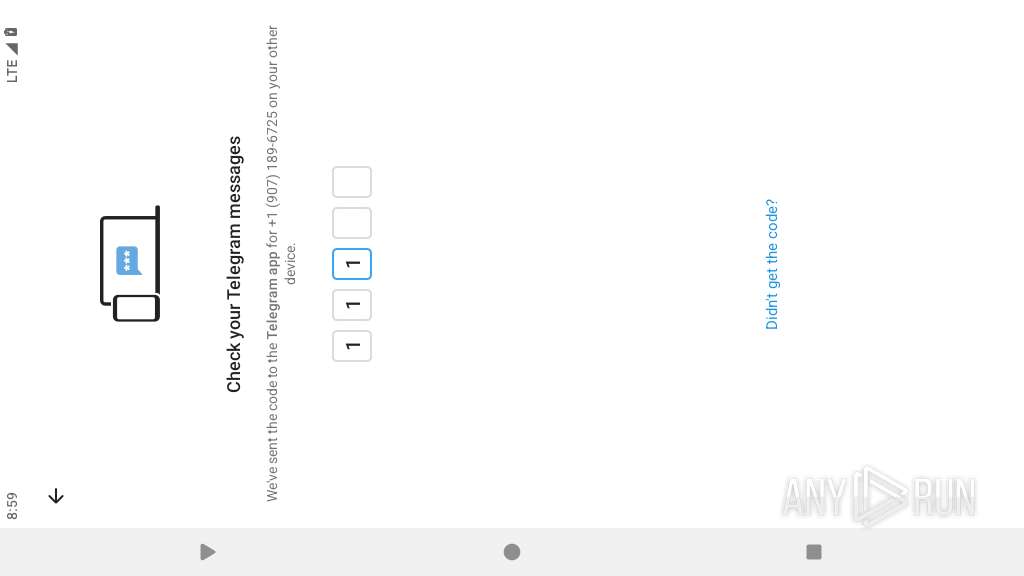
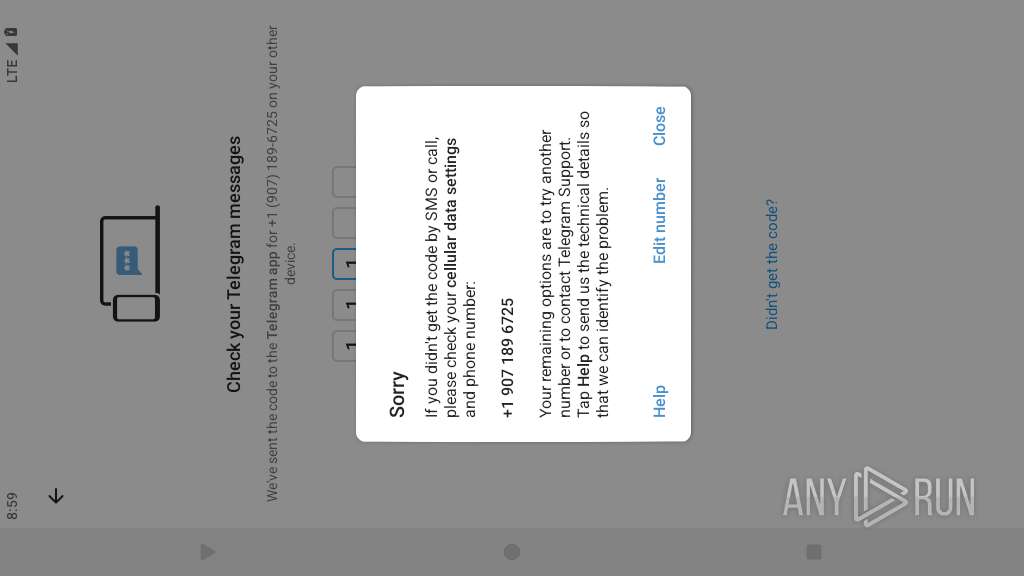
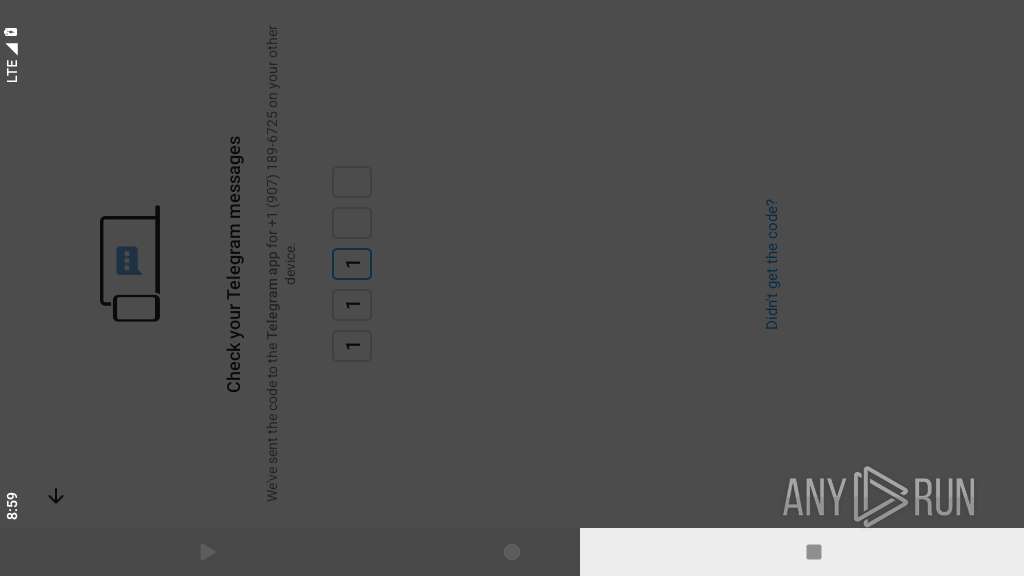
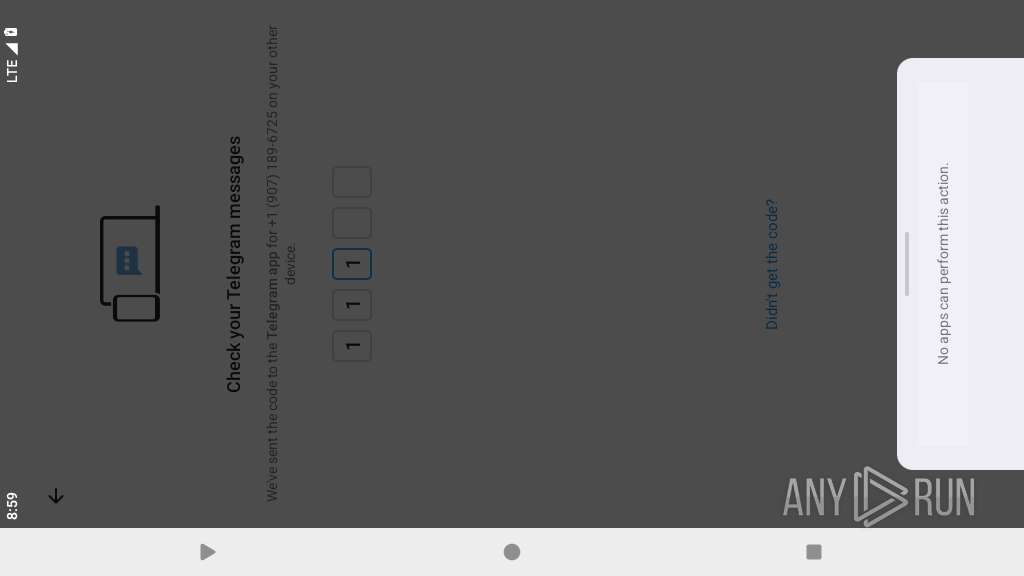
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- app_process64 (PID: 2266)
Connects to unusual port
- app_process64 (PID: 2266)
Accesses system-level resources
- app_process64 (PID: 2266)
Retrieves current clipboard content
- app_process64 (PID: 2266)
INFO
Detects device power status
- app_process64 (PID: 2266)
Retrieves the value of a secure system setting
- app_process64 (PID: 2266)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2266)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2266)
Loads a native library into the application
- app_process64 (PID: 2266)
Creates and writes local files
- app_process64 (PID: 2266)
Dynamically registers broadcast event listeners
- app_process64 (PID: 2266)
Dynamically loads a class in Java
- app_process64 (PID: 2266)
Retrieves CPU core information
- app_process64 (PID: 2266)
Gets file name without full path
- app_process64 (PID: 2266)
Verifies presence of SIM card
- app_process64 (PID: 2266)
Retrieves the value of a system setting
- app_process64 (PID: 2266)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2266)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2266)
Returns elapsed time since boot
- app_process64 (PID: 2266)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (36.7) |
|---|---|---|
| .zip | | | Opera Widget (35.4) |
| .zip | | | ZIP compressed archive (10.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:07 17:54:16 |
| ZipCRC: | 0xd8d2330d |
| ZipCompressedSize: | 394 |
| ZipUncompressedSize: | 646 |
| ZipFileName: | kotlin/internal/internal.kotlin_builtins |
Total processes
173
Monitored processes
48
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2266 | org.sheniandaji.talking | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2366 | org.sheniandaji.talking | /system/bin/app_process64 | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 65280 | ||||
| 2411 | cat /sys/class/net/wlan0/address | /system/bin/toybox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 256 | ||||
| 2415 | getprop ro.yunos.build.version | /system/bin/toolbox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2423 | cat /sys/class/net/wlan0/address | /system/bin/toybox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 256 | ||||
| 2425 | cat /proc/version | /system/bin/toybox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 256 | ||||
| 2453 | cat /sys/class/net/wlan0/address | /system/bin/toybox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 256 | ||||
| 2462 | cat /sys/class/net/wlan0/address | /system/bin/toybox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 256 | ||||
| 2463 | /system/bin/dmesgd | /system/bin/dmesgd | — | init |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2464 | dmesg | /system/bin/toybox | — | dmesgd |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
390
Text files
38
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2266 | app_process64 | /data/data/org.sheniandaji.talking/mx.ini | binary | |
MD5:— | SHA256:— | |||
| 2266 | app_process64 | /data/data/org.sheniandaji.talking/shared_prefs/_sh.xml | binary | |
MD5:— | SHA256:— | |||
| 2266 | app_process64 | /data/data/org.sheniandaji.talking/shared_prefs/_p.xml | binary | |
MD5:— | SHA256:— | |||
| 2266 | app_process64 | /data/data/org.sheniandaji.talking/shared_prefs/sp_Uzoyhme.xml | binary | |
MD5:— | SHA256:— | |||
| 2266 | app_process64 | /data/data/org.sheniandaji.talking/shared_prefs/config_info_def.xml | binary | |
MD5:— | SHA256:— | |||
| 2266 | app_process64 | /data/data/org.sheniandaji.talking/shared_prefs/ssp_datas.xml | binary | |
MD5:— | SHA256:— | |||
| 2266 | app_process64 | /data/data/org.sheniandaji.talking/shared_prefs/A8BCBA59051B454FFA2882F1A.xml | binary | |
MD5:— | SHA256:— | |||
| 2266 | app_process64 | /storage/emulated/0/Android/data/org.sheniandaji.talking/cache/000000000_999999_temp.f | binary | |
MD5:— | SHA256:— | |||
| 2266 | app_process64 | /storage/emulated/0/Android/data/org.sheniandaji.talking/files/Telegram/Telegram Images/000000000_999999.f | binary | |
MD5:— | SHA256:— | |||
| 2266 | app_process64 | /storage/emulated/0/Android/data/org.sheniandaji.talking/files/Telegram/Telegram Video/000000000_999999.f | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
143
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 172.217.16.196:443 | https://www.google.com/generate_204 | unknown | — | — | unknown |
— | — | GET | 204 | 142.250.185.227:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2266 | app_process64 | POST | 200 | 8.222.247.31:10020 | http://xcbm4.0pk05.com:10020/reportLoginStatus | unknown | — | — | unknown |
2266 | app_process64 | POST | 200 | 8.222.247.31:10020 | http://xcbm4.0pk05.com:10020/appInfo | unknown | — | — | unknown |
— | — | POST | 200 | 108.177.96.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:fetchEekChain | unknown | binary | 699 b | whitelisted |
— | — | GET | 200 | 169.150.247.36:443 | https://kivr8.wd6vy.com/xwnpdcs/slwr3orws8w89.zip | unknown | binary | 53.3 Kb | unknown |
— | — | GET | 200 | 169.150.247.36:443 | https://kivr8.wd6vy.com/zhuti/hwds9359ref779.zip | unknown | binary | 48.8 Kb | unknown |
— | — | GET | 200 | 169.150.247.36:443 | https://kivr8.wd6vy.com/hwyw/hguw73r97.zip | unknown | binary | 54.9 Kb | unknown |
— | — | GET | 200 | 169.150.247.36:443 | https://kivr8.wd6vy.com/dy/UIEF877S7W834REF67SR_PZ.zip | unknown | binary | 12.3 Kb | unknown |
— | — | POST | 200 | 34.160.223.119:443 | https://kvinit-prod.api.kochava.com/track/kvinit | unknown | binary | 262 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
443 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 142.250.181.228:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.185.227:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 216.239.35.8:123 | time.android.com | — | — | whitelisted |
— | — | 108.177.96.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
— | — | 216.239.35.0:123 | time.android.com | — | — | whitelisted |
568 | app_process64 | 216.239.35.12:123 | time.android.com | — | — | whitelisted |
2266 | app_process64 | 47.84.82.193:13341 | v8d1a.2l3kg.xyz | — | US | unknown |
2266 | app_process64 | 8.222.247.31:20103 | e9tec.w5auz.xyz | — | SG | unknown |
2266 | app_process64 | 169.150.247.37:443 | kivr8.wd6vy.com | — | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
google.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
v8d1a.2l3kg.xyz |
| unknown |
e9tec.w5auz.xyz |
| unknown |
kivr8.wd6vy.com |
| unknown |
xcbm4.0pk05.com |
| unknown |
xc06a.0pk05.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |
2266 | app_process64 | Misc activity | ET INFO Observed Google DNS over HTTPS Domain (dns .google .com in TLS SNI) |