| File name: | executable.2772.exe |
| Full analysis: | https://app.any.run/tasks/5ea5cd90-3bea-46f8-9549-00b68227d083 |
| Verdict: | Malicious activity |
| Analysis date: | March 17, 2019, 17:00:46 |
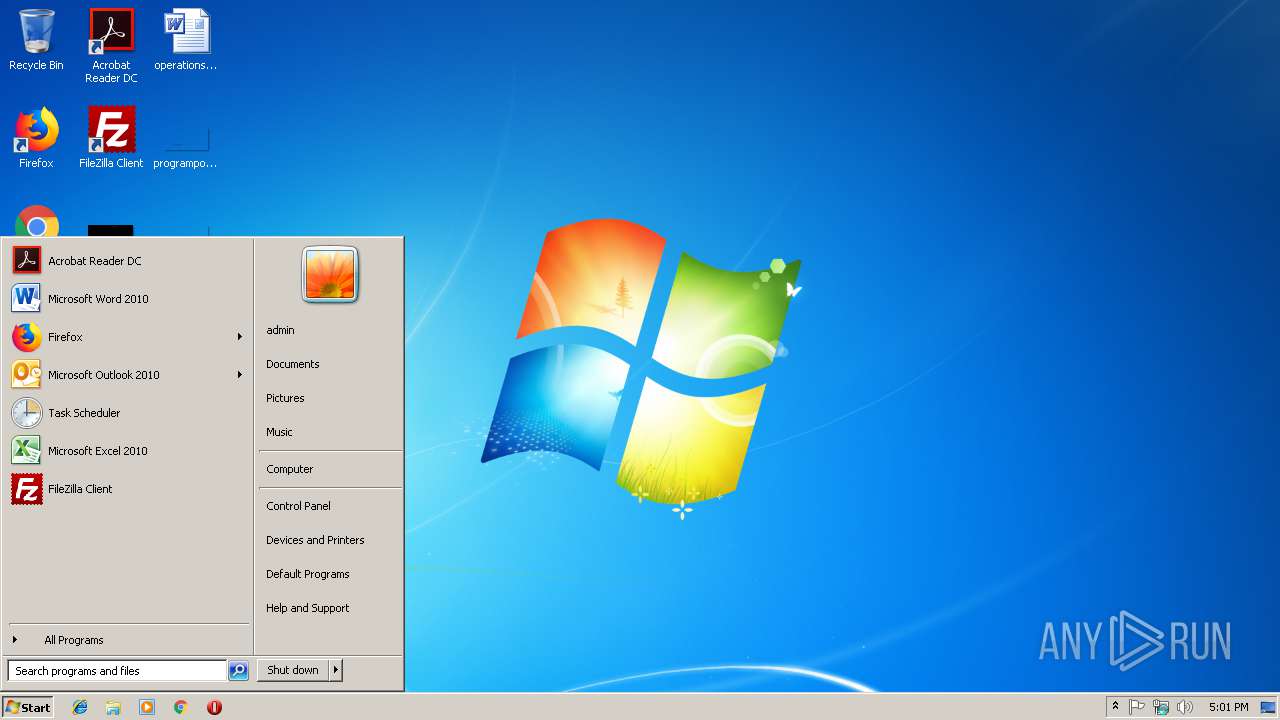
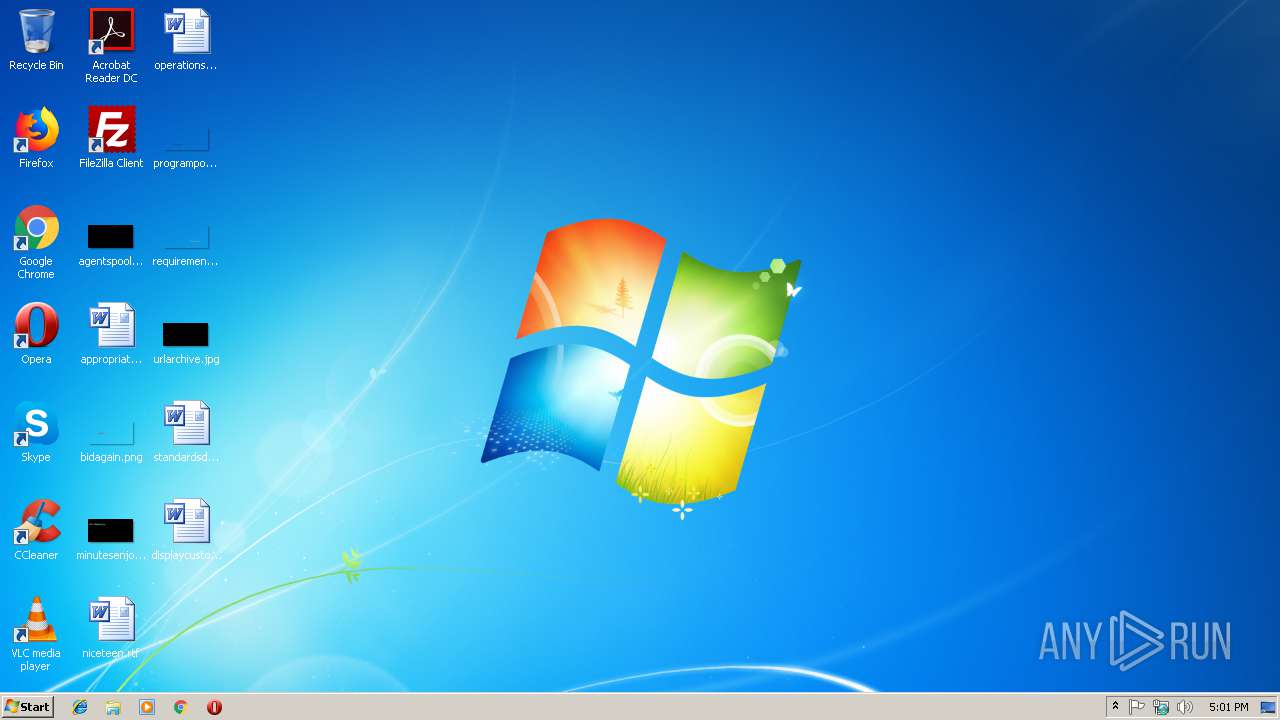
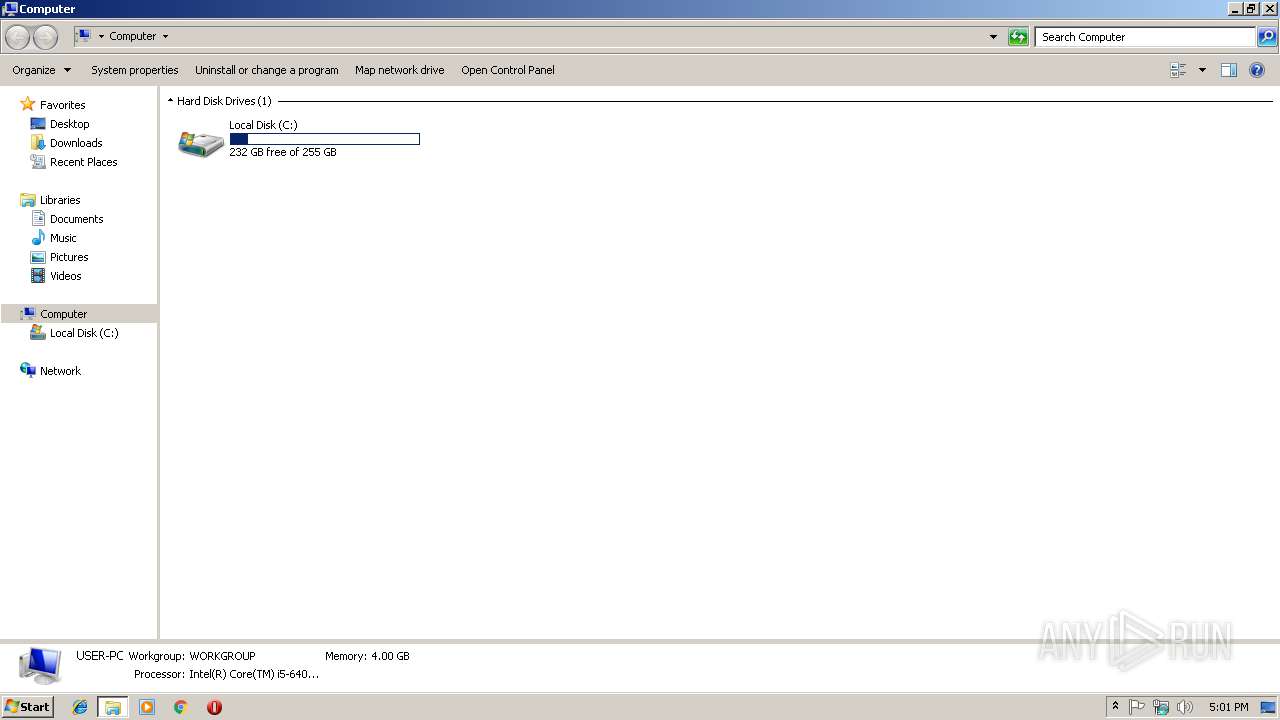
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 05A065421CAA9215958DECA72A5B15F3 |
| SHA1: | E7BE3FD7F0E5F71EC6E55B014CD79C1E93CB2FD8 |
| SHA256: | 13170EC31CF0920AD871B0D0603B6F575F847E523AC977E5177ADAF62D569853 |
| SSDEEP: | 96:S0FKCiwCRG4jynYJfcUdBOEH9LmdhPoJ4IF54:r1SRG4jynKx5yfPoJ4IFi |
MALICIOUS
Loads dropped or rewritten executable
- svchost.exe (PID: 1464)
SUSPICIOUS
Creates files in the program directory
- wmpnetwk.exe (PID: 3328)
Removes files from Windows directory
- wmpnetwk.exe (PID: 3328)
Executable content was dropped or overwritten
- msdt.exe (PID: 2128)
- svchost.exe (PID: 1464)
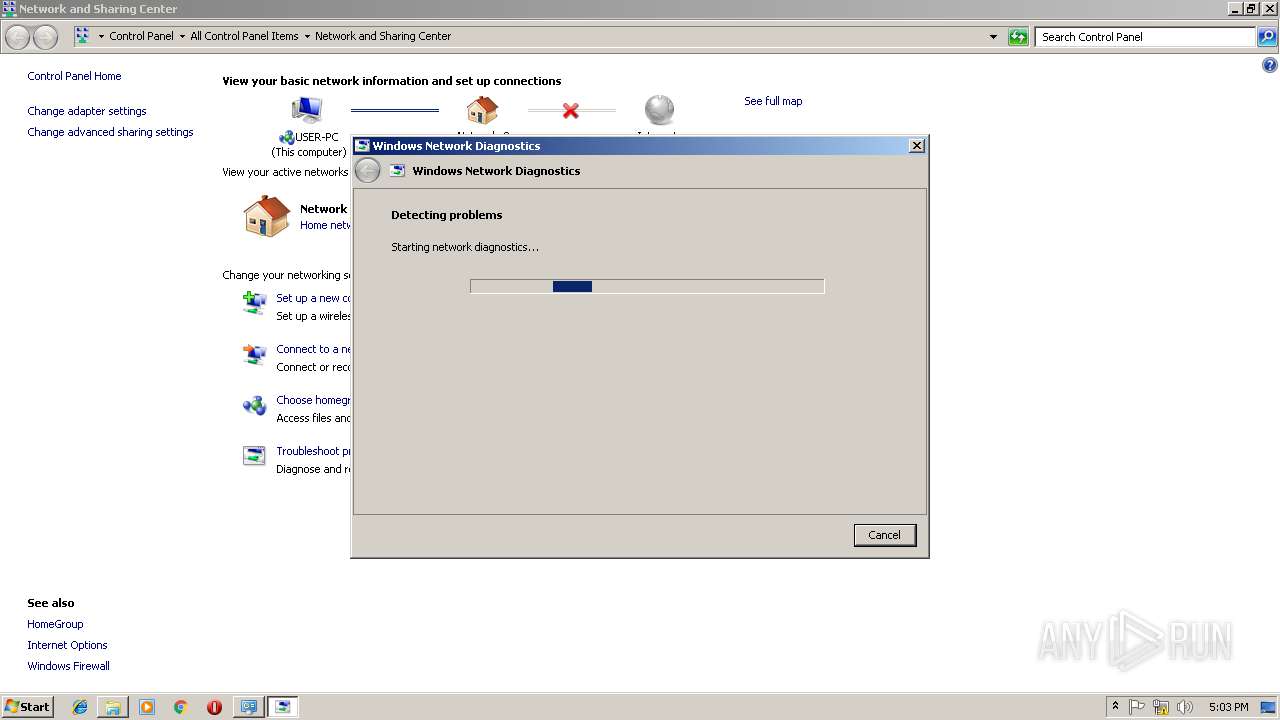
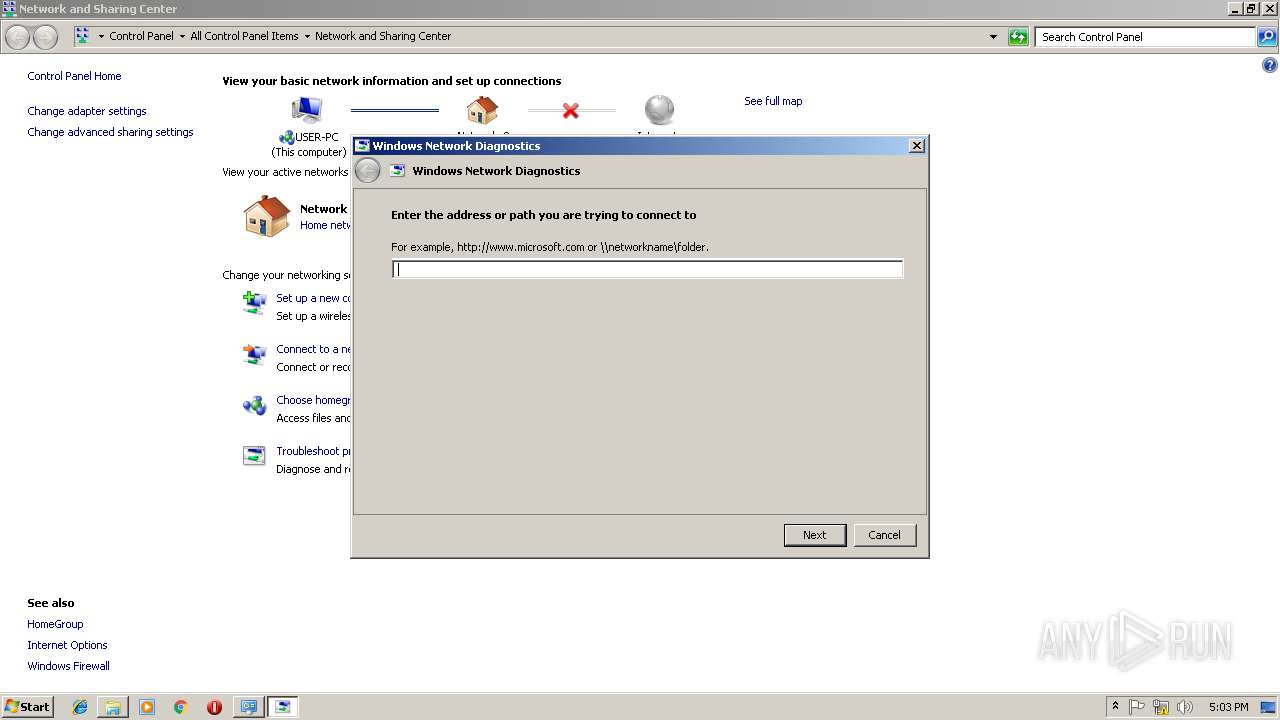
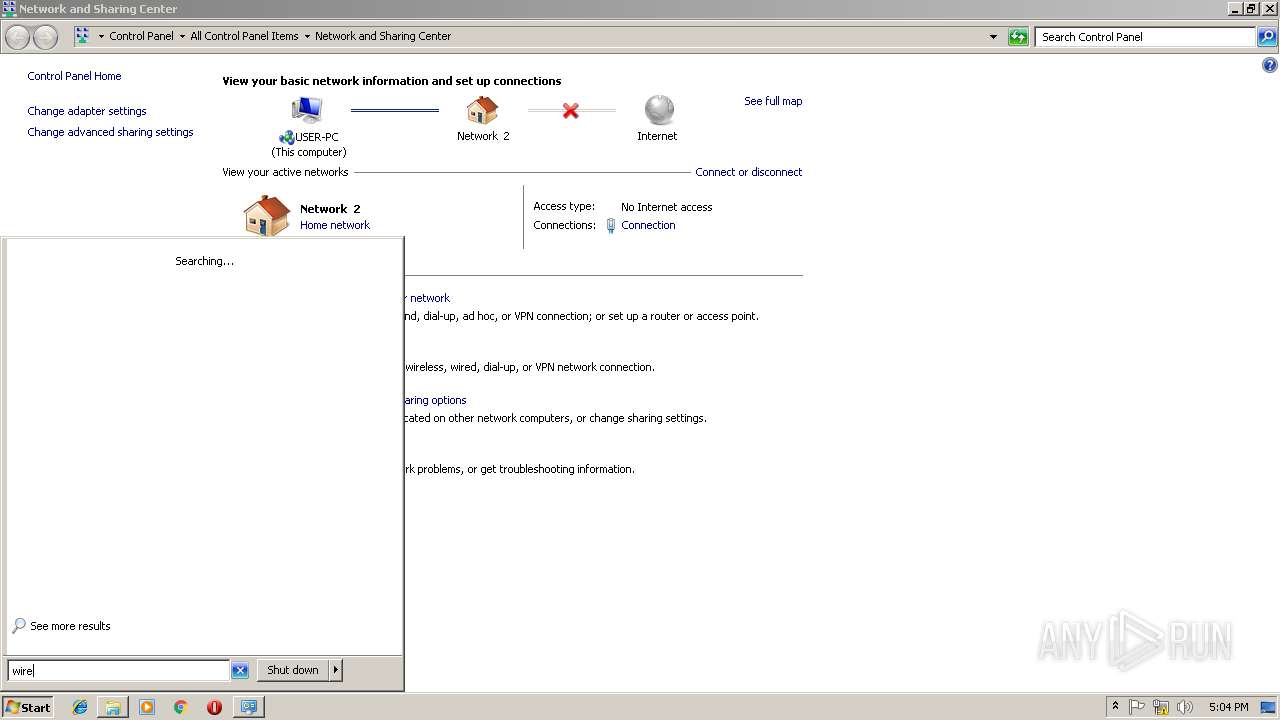
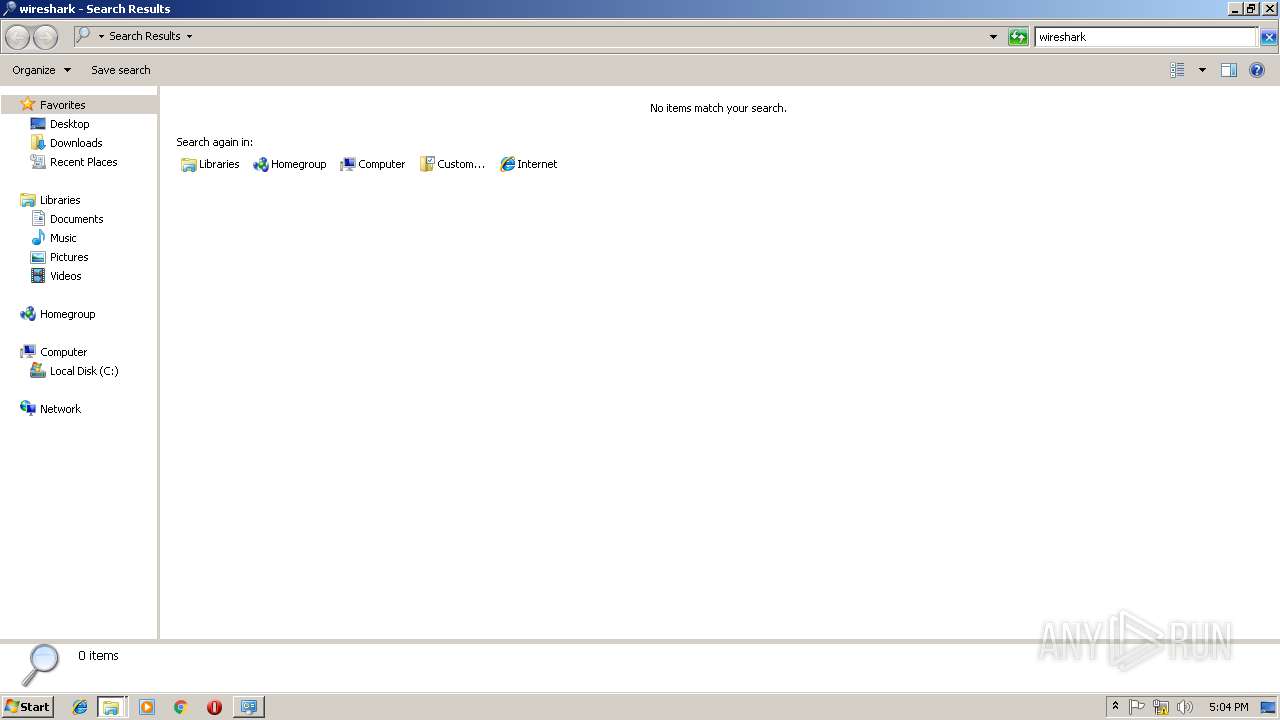
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 2544)
Creates files in the Windows directory
- wmpnetwk.exe (PID: 3328)
- svchost.exe (PID: 1464)
Writes to a desktop.ini file (may be used to cloak folders)
- wmpnetwk.exe (PID: 3328)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:01:12 12:14:48+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 2560 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | 512 |
| EntryPoint: | 0x1110 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Jan-2013 11:14:48 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-Jan-2013 11:14:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000009E4 | 0x00000A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.35009 |
.data | 0x00002000 | 0x00000060 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.691024 |
.rdata | 0x00003000 | 0x00000098 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.42936 |
.bss | 0x00004000 | 0x000000E0 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00005000 | 0x0000038C | 0x00000400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.36302 |
Imports
KERNEL32.dll |
WS2_32.DLL |
msvcrt.dll |
Total processes
57
Monitored processes
17
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 368 | "C:\Windows\System32\msdt.exe" -skip TRUE -path C:\Windows\diagnostics\system\networking -ep NetworkDiagnosticsNetworkMiniMap | C:\Windows\System32\msdt.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1148 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\system32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1464 | C:\Windows\system32\svchost.exe -k LocalServiceAndNoImpersonation | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1504 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1DDC.tmp" "c:\Users\admin\AppData\Local\Temp\CSC1DDB.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2128 | "C:\Windows\System32\msdt.exe" -skip TRUE -path C:\Windows\diagnostics\system\networking -ep NetworkDiagnosticsNetworkMiniMap | C:\Windows\System32\msdt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | "C:\Windows\System32\msdt.exe" -skip TRUE -path C:\Windows\diagnostics\system\networking -ep NetworkDiagnosticsNetworkMiniMap | C:\Windows\System32\msdt.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
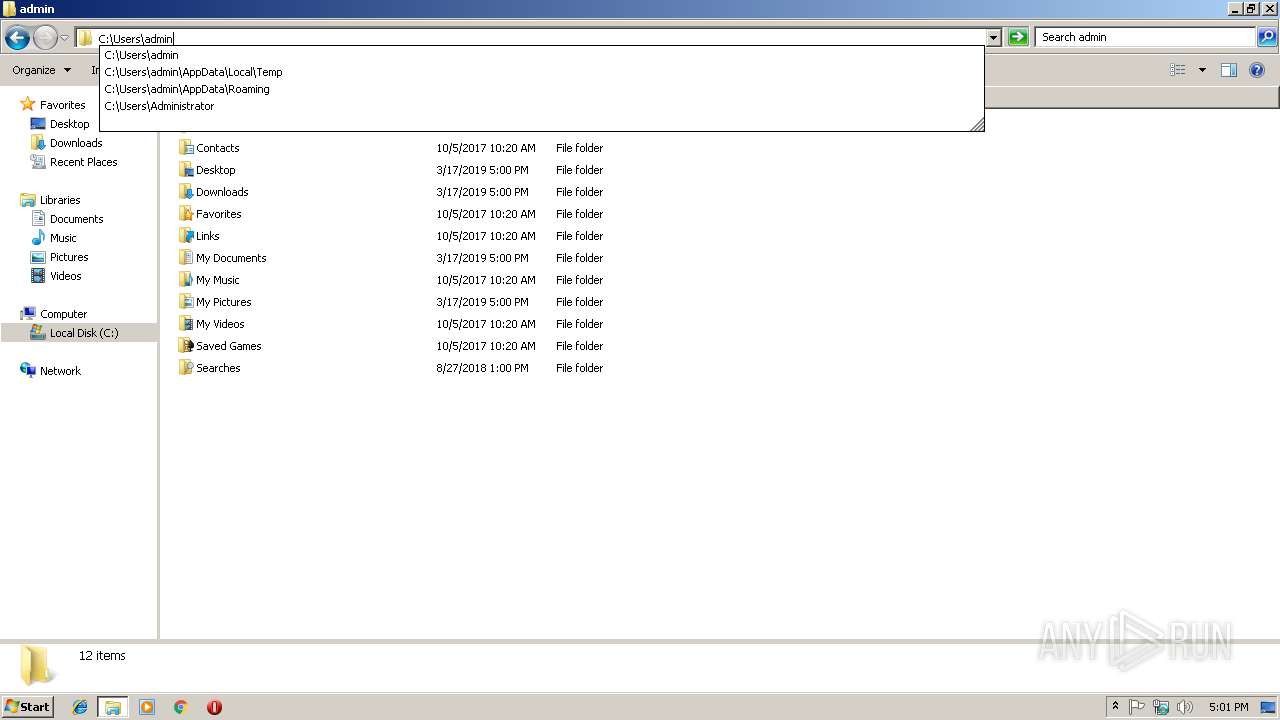
| 2456 | "C:\Users\admin\AppData\Local\Temp\executable.2772.exe" | C:\Users\admin\AppData\Local\Temp\executable.2772.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2544 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2808 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ivic1uez.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
Total events
568
Read events
373
Write events
186
Delete events
9
Modification events
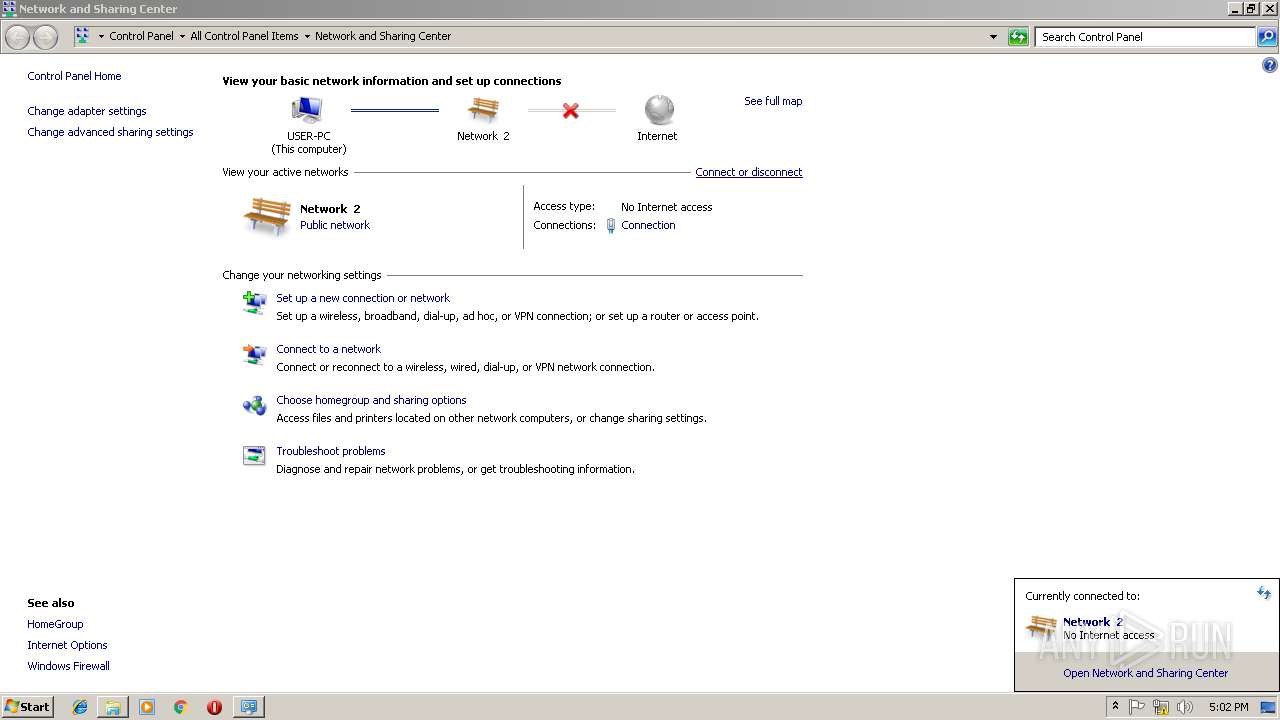
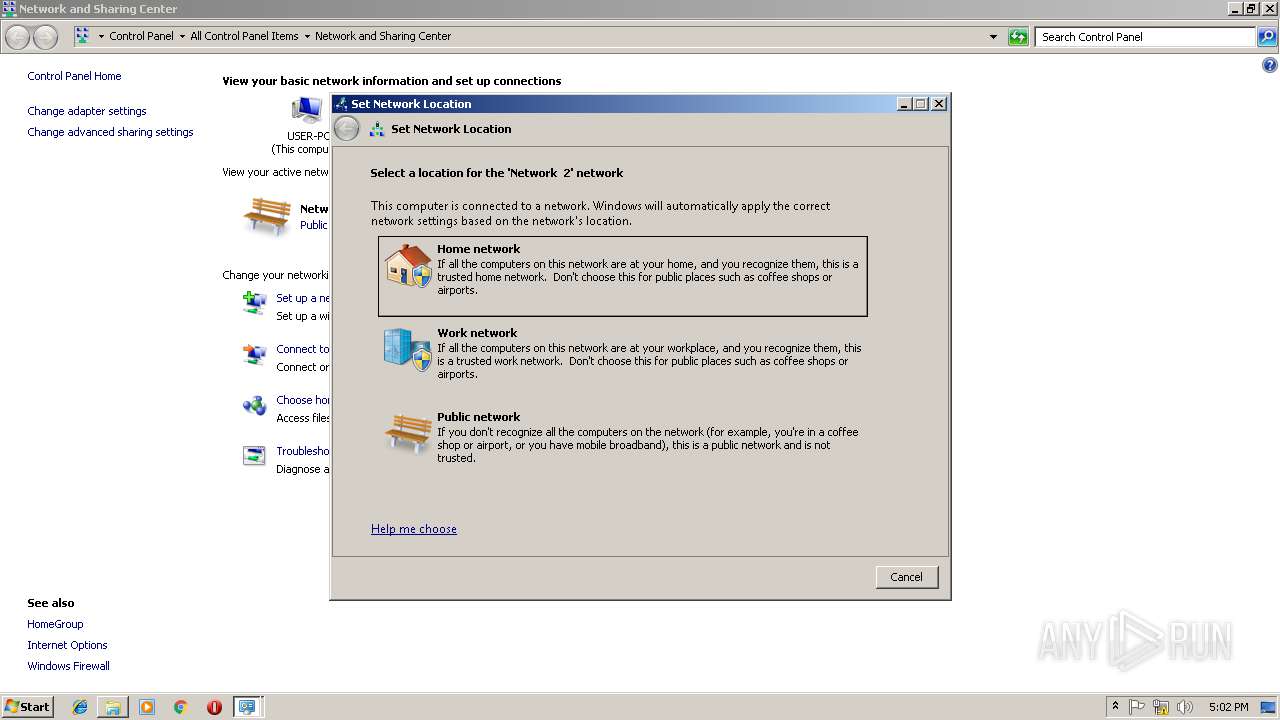
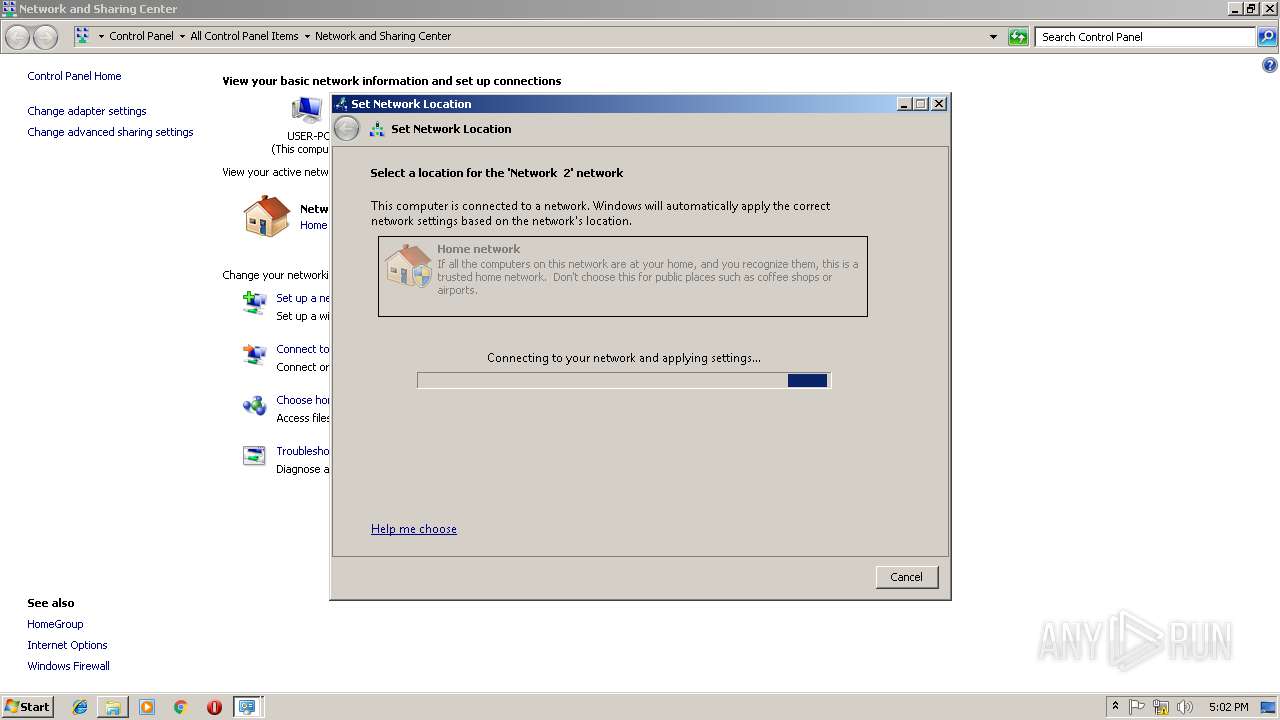
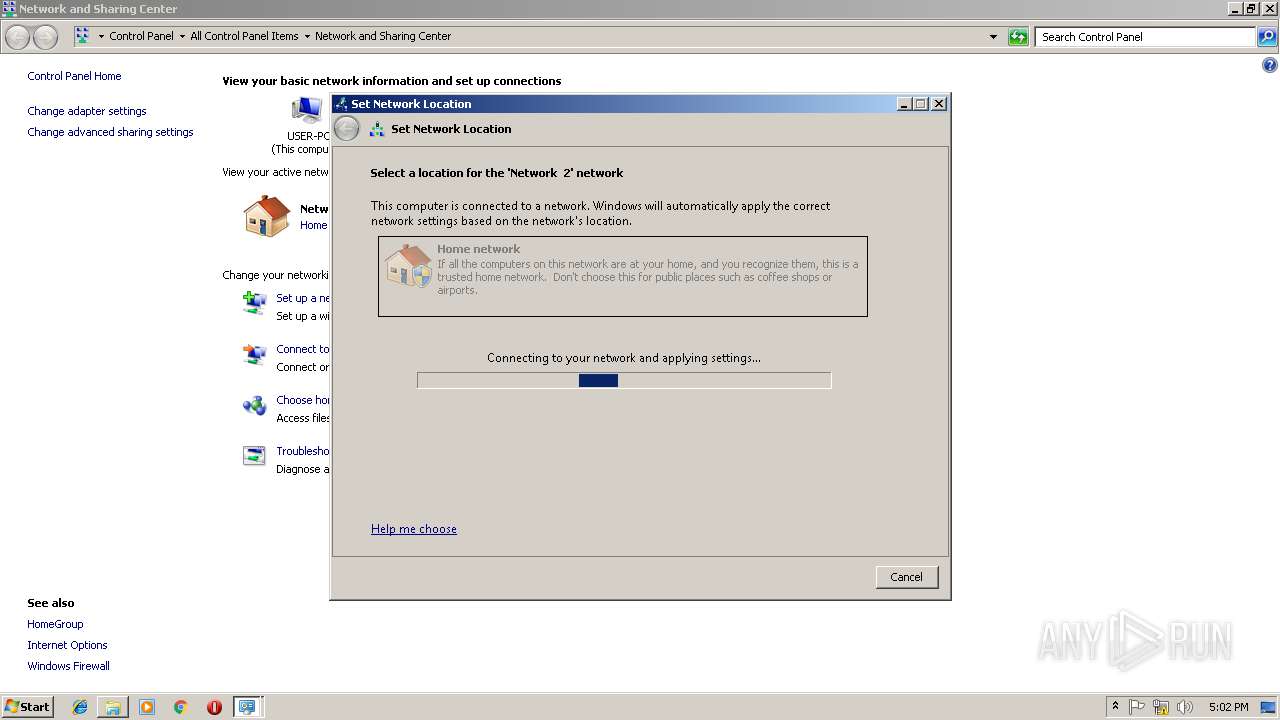
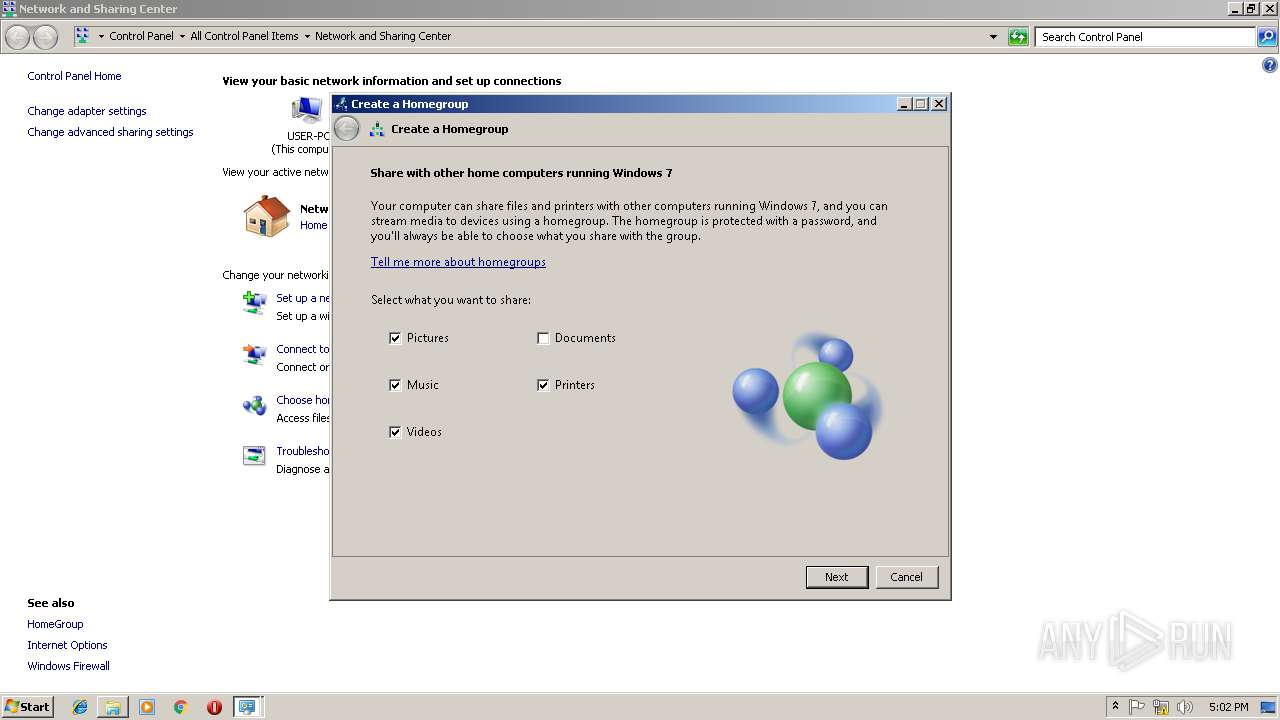
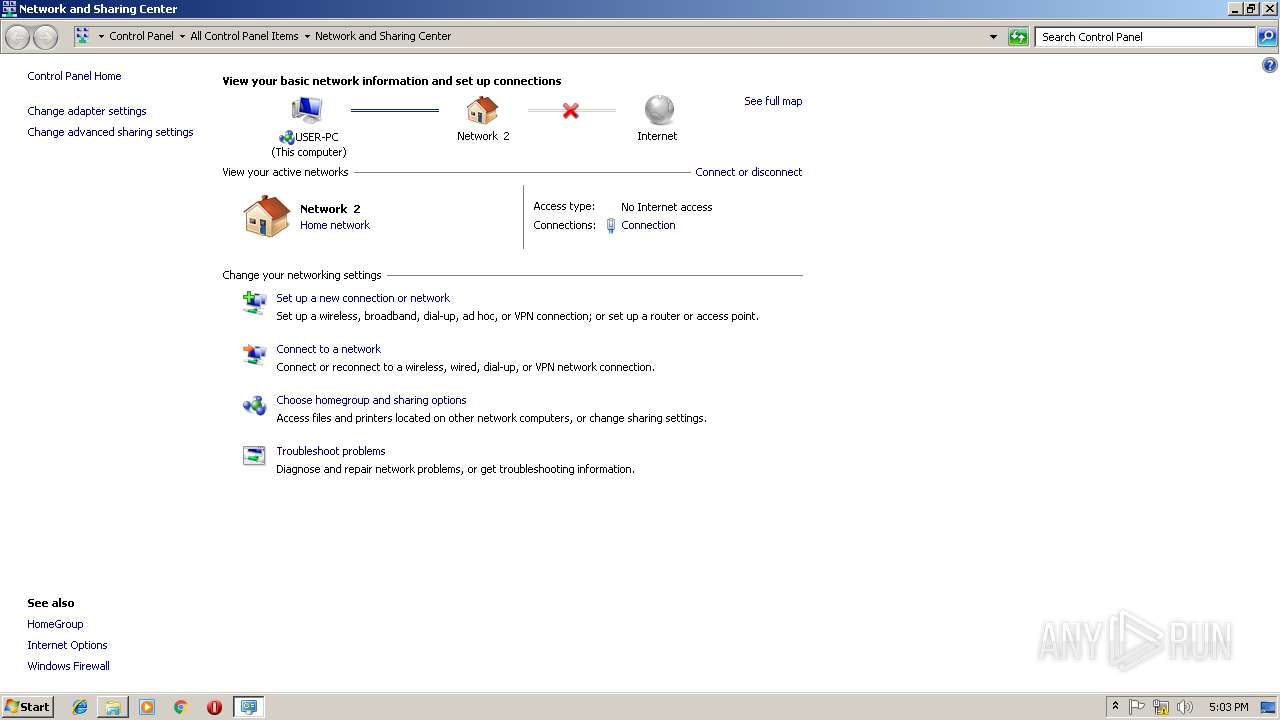
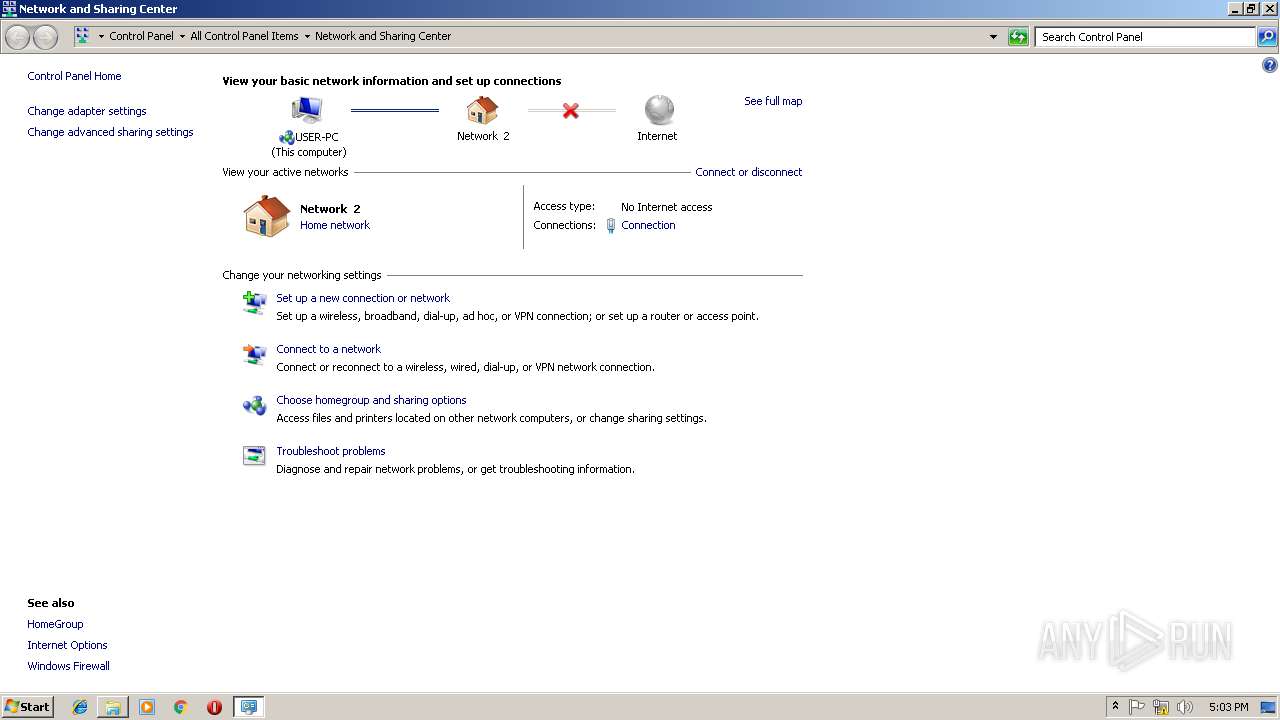
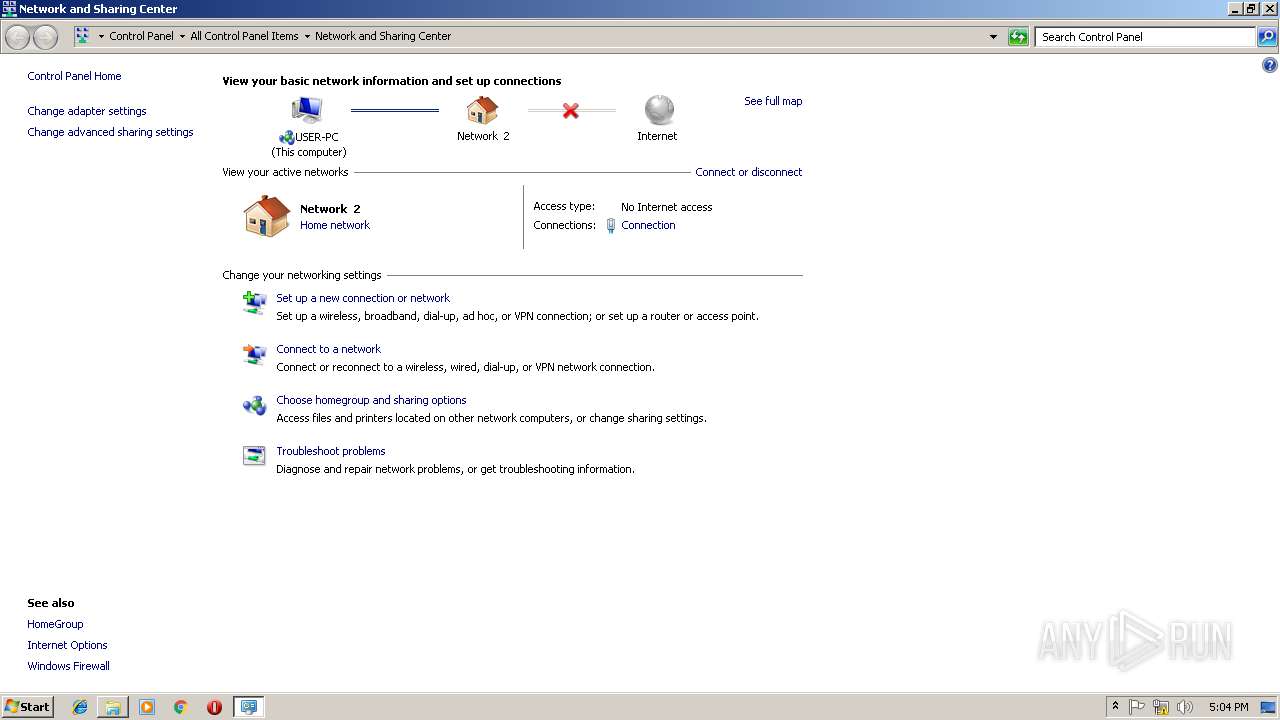
| (PID) Process: | (2948) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\HomeGroup\NetworkLocations\Home |
| Operation: | write | Name: | {DF9EC014-2588-45EF-B2A0-3814C6F29E49} |
Value: Network 2 | |||
| (PID) Process: | (1464) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\FDResPub\ServiceData |
| Operation: | write | Name: | FirstStart |
Value: 3100000000000000 | |||
| (PID) Process: | (3328) wmpnetwk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DRM |
| Operation: | write | Name: | DataPath |
Value: 43003A005C00500072006F006700720061006D0044006100740061005C004D006900630072006F0073006F00660074005C00570069006E0064006F00770073005C00440052004D000000 | |||
| (PID) Process: | (3328) wmpnetwk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{6043F26B-2EDA-413C-A09D-CE16523E678F}\{5DDBBA0A-4D0A-45E9-891D-1DD981E4530C} |
| Operation: | write | Name: | Reason |
Value: 1001 | |||
| (PID) Process: | (3328) wmpnetwk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{6043F26B-2EDA-413C-A09D-CE16523E678F}\{5DDBBA0A-4D0A-45E9-891D-1DD981E4530C} |
| Operation: | write | Name: | ID |
Value: 00-00-00-00-00-00 | |||
| (PID) Process: | (3328) wmpnetwk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{6043F26B-2EDA-413C-A09D-CE16523E678F}\{5DDBBA0A-4D0A-45E9-891D-1DD981E4530C} |
| Operation: | write | Name: | Data |
Value: ignored | |||
| (PID) Process: | (3328) wmpnetwk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{6043F26B-2EDA-413C-A09D-CE16523E678F}\{5DDBBA0A-4D0A-45E9-891D-1DD981E4530C} |
| Operation: | write | Name: | Scope |
Value: ignored | |||
| (PID) Process: | (3328) wmpnetwk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{BD92E4CD-5BB5-4084-9B15-739BB78624CB}\{5DDBBA0A-4D0A-45E9-891D-1DD981E4530C} |
| Operation: | write | Name: | Reason |
Value: 1001 | |||
| (PID) Process: | (3328) wmpnetwk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{6043F26B-2EDA-413C-A09D-CE16523E678F}\{5DDBBA0A-4D0A-45E9-891D-1DD981E4530C} |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3328) wmpnetwk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{BD92E4CD-5BB5-4084-9B15-739BB78624CB}\{5DDBBA0A-4D0A-45E9-891D-1DD981E4530C} |
| Operation: | write | Name: | ID |
Value: 00-00-00-00-00-00 | |||
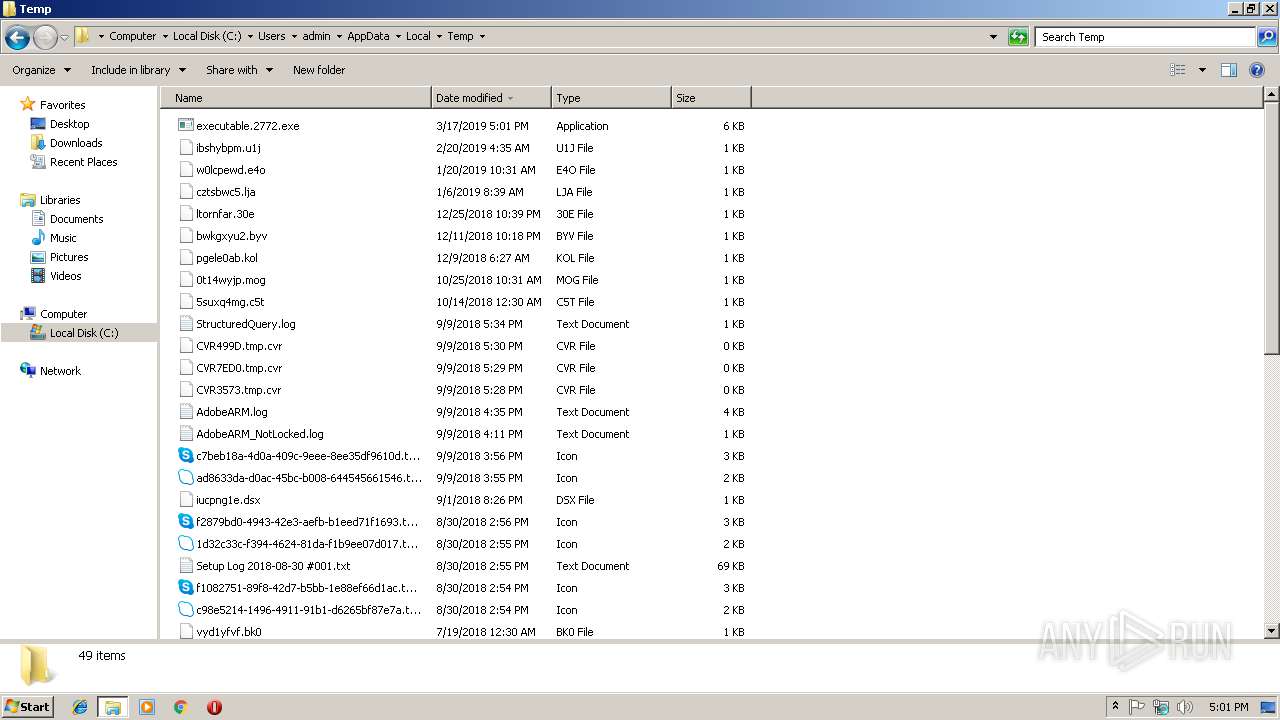
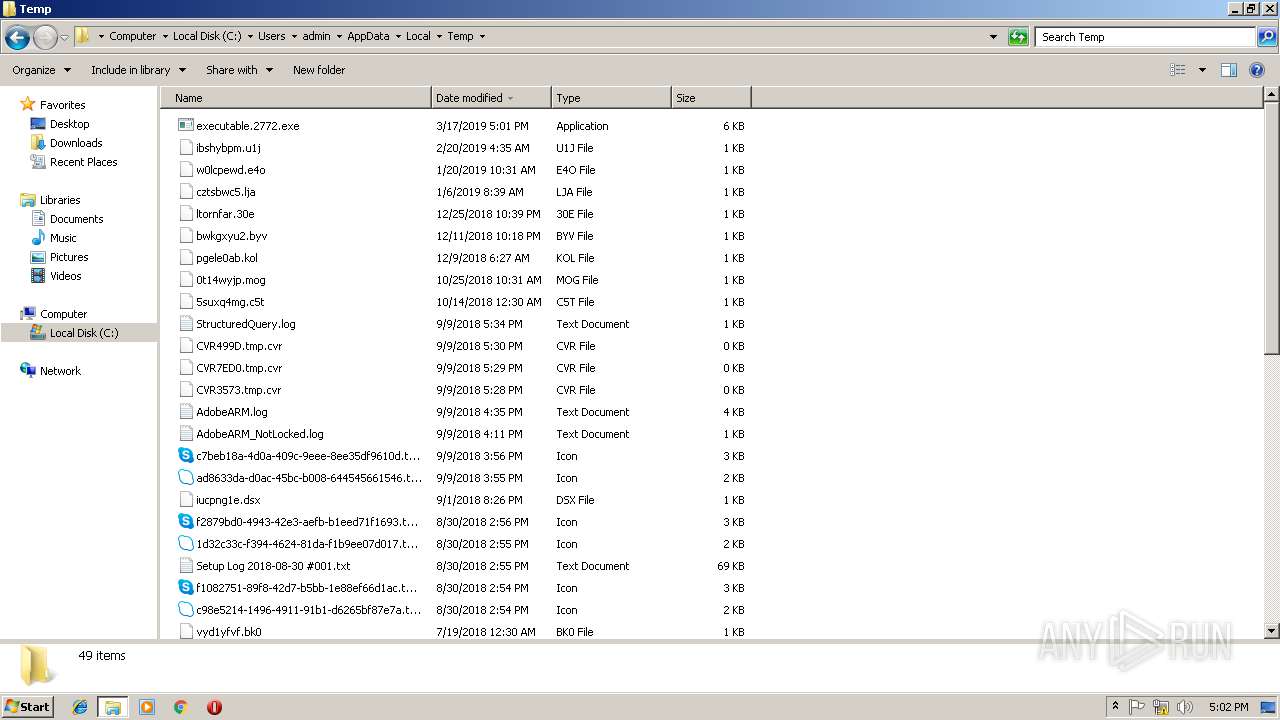
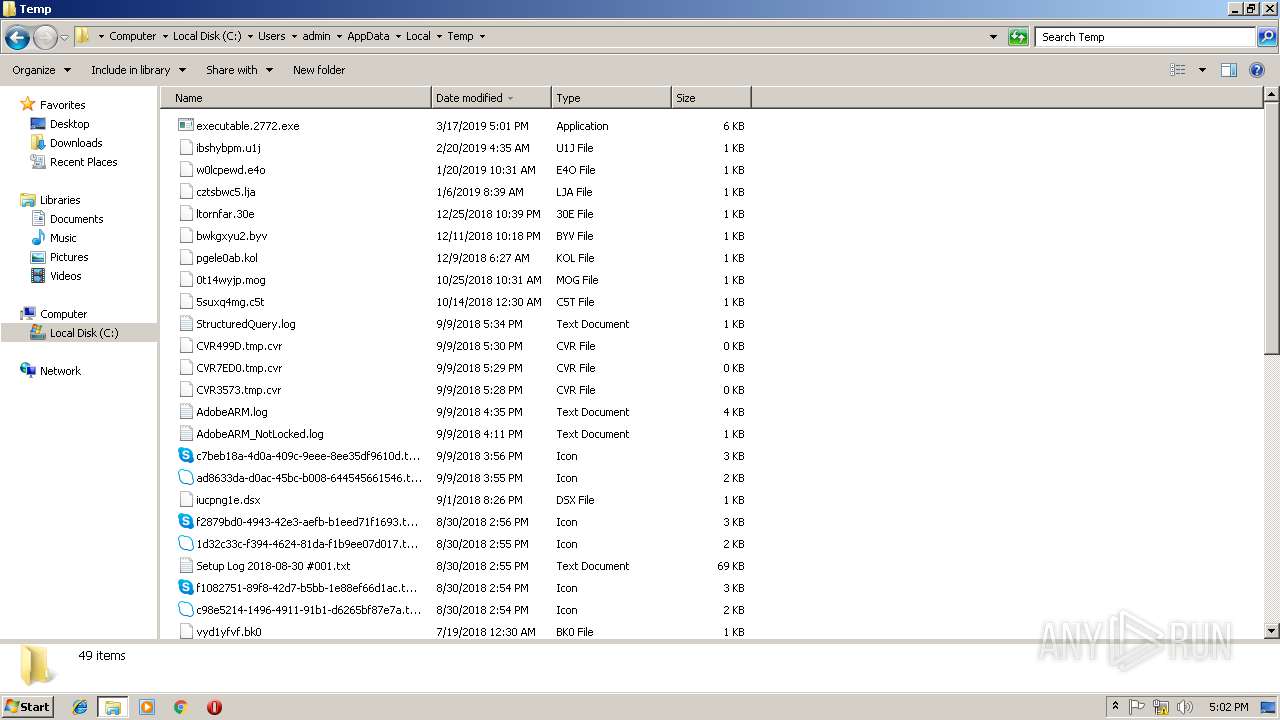
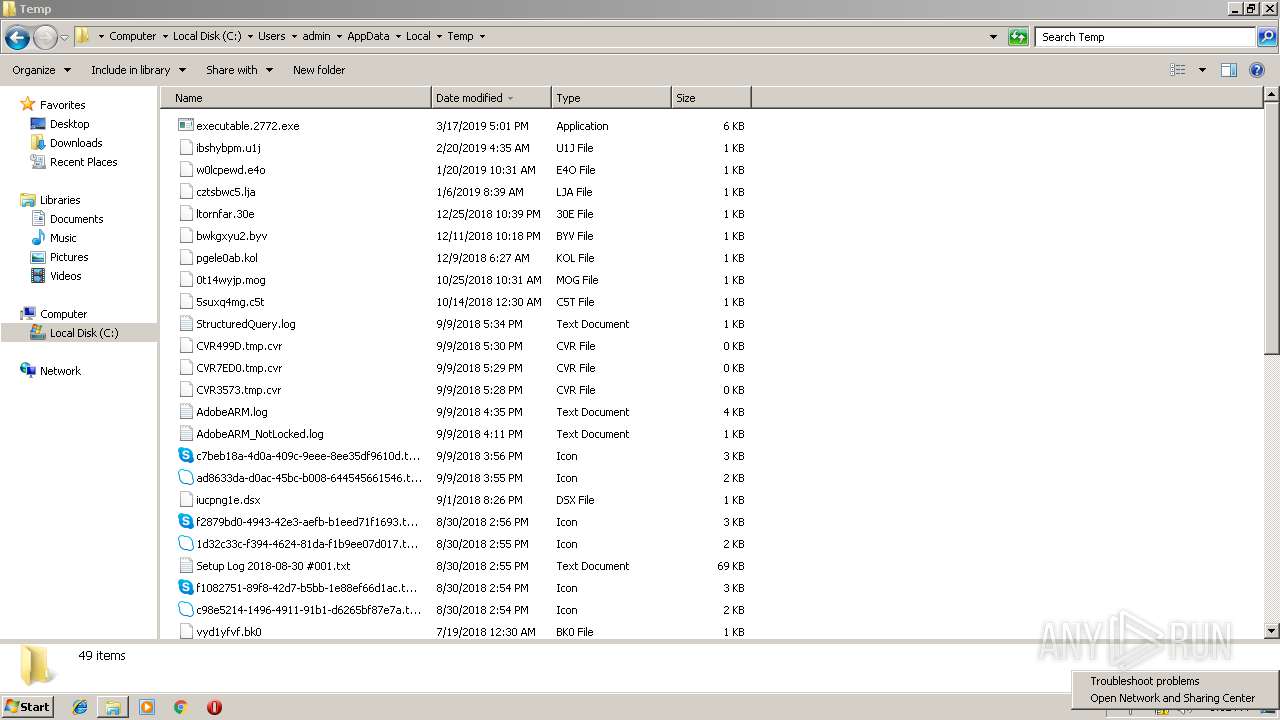
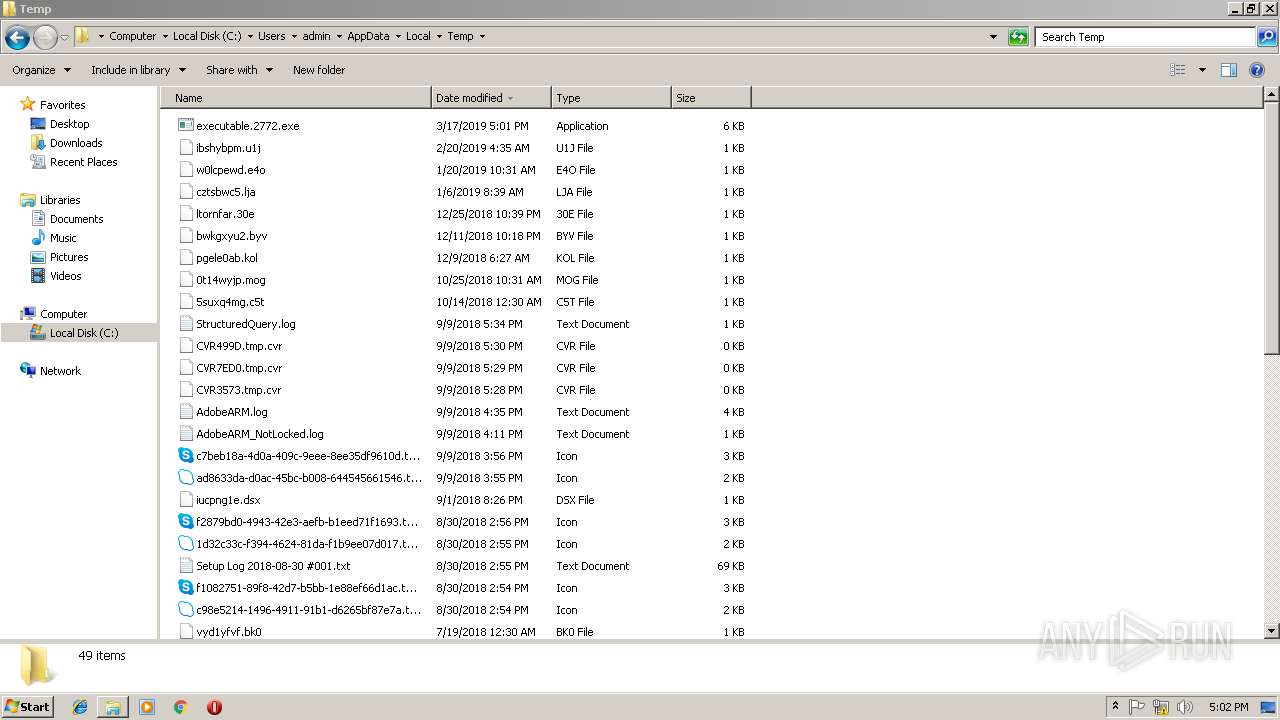
Executable files
3
Suspicious files
7
Text files
42
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3328 | wmpnetwk.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML.bak | — | |
MD5:— | SHA256:— | |||
| 3328 | wmpnetwk.exe | C:\ProgramData\Microsoft\Windows\DRM\v3ks.sec | binary | |
MD5:— | SHA256:— | |||
| 3328 | wmpnetwk.exe | C:\ProgramData\Microsoft\Windows\DRM\v3ks.bla | text | |
MD5:— | SHA256:— | |||
| 3328 | wmpnetwk.exe | C:\ProgramData\Microsoft\Windows\DRM\blackbox.bin | binary | |
MD5:— | SHA256:— | |||
| 3328 | wmpnetwk.exe | C:\ProgramData\Microsoft\Windows\DRM\drmstore.hds | binary | |
MD5:— | SHA256:— | |||
| 3328 | wmpnetwk.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3328 | wmpnetwk.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3328 | wmpnetwk.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.DTD | xml | |
MD5:90BE2701C8112BEBC6BD58A7DE19846E | SHA256:644FBCDC20086E16D57F31C5BAD98BE68D02B1C061938D2F5F91CBE88C871FBF | |||
| 3328 | wmpnetwk.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Microsoft\Windows\Temporary Internet Files\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3328 | wmpnetwk.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML | text | |
MD5:7050D5AE8ACFBE560FA11073FEF8185D | SHA256:CB87767C4A384C24E4A0F88455F59101B1AE7B4FB8DE8A5ADB4136C5F7EE545B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
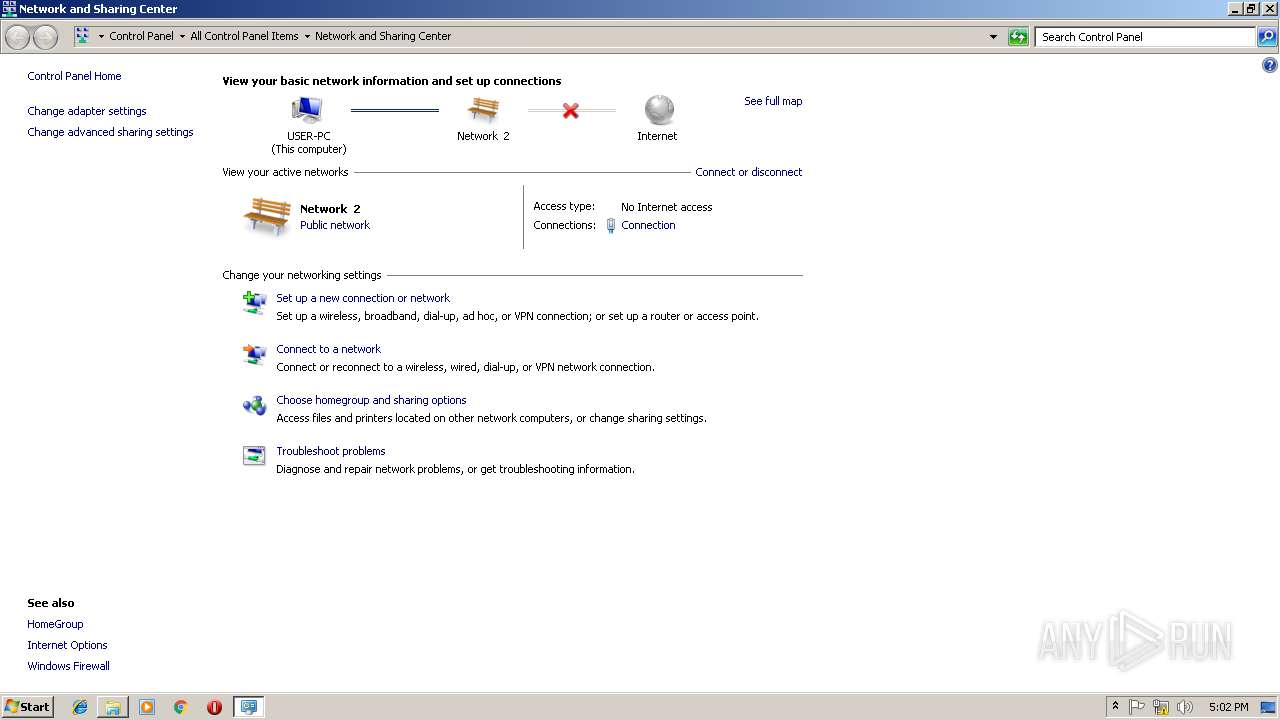
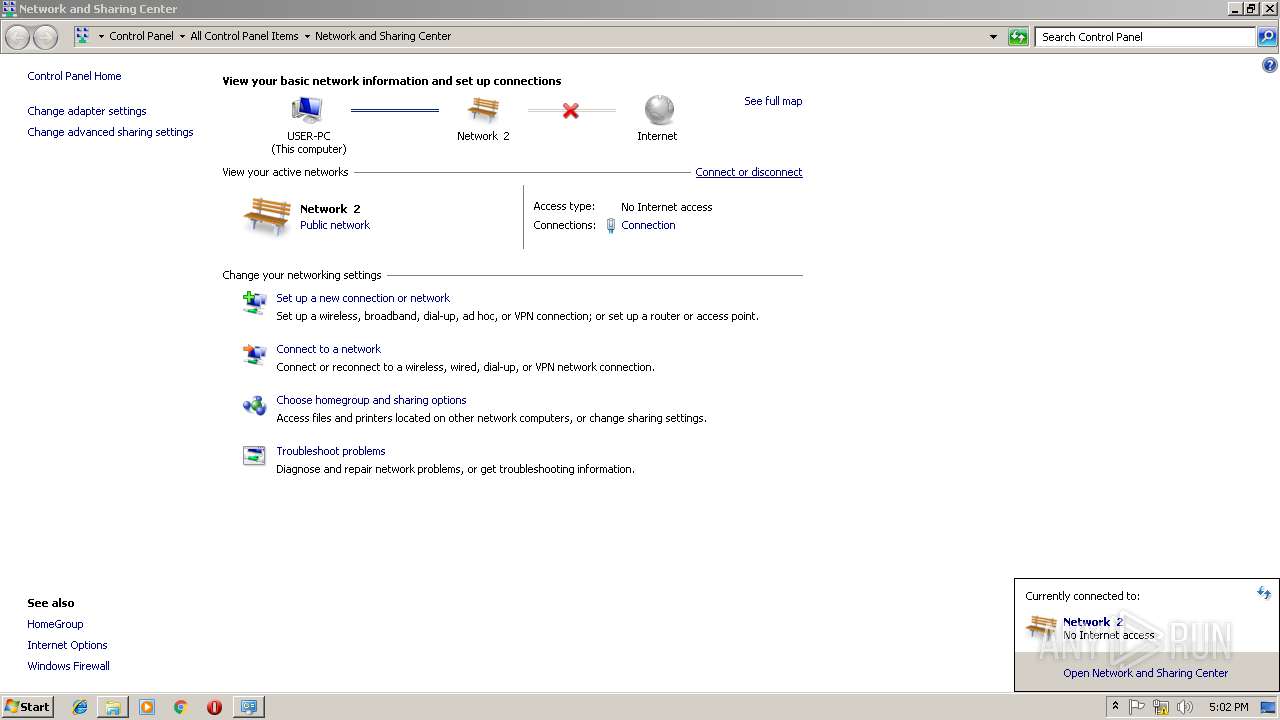
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
976 | svchost.exe | GET | 200 | 2.21.41.70:80 | http://www.microsoft.com/ | FR | html | 1020 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
976 | svchost.exe | 2.21.41.70:80 | www.microsoft.com | GTT Communications Inc. | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|