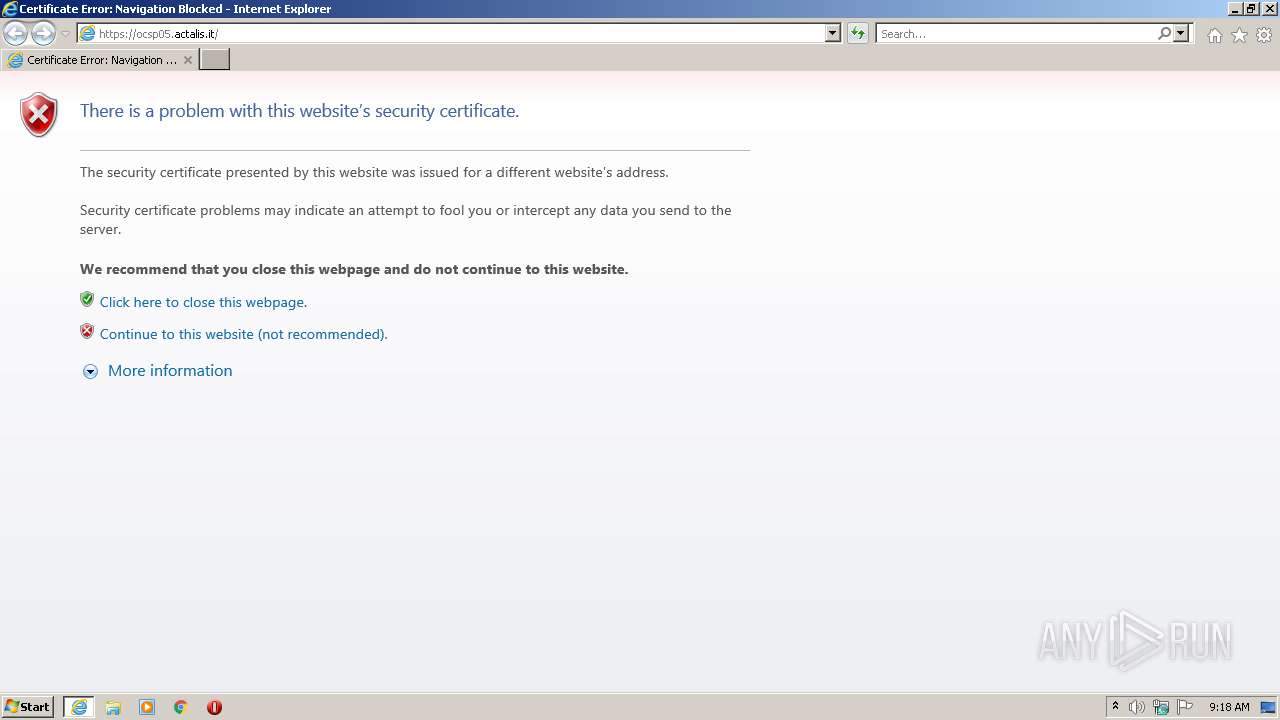
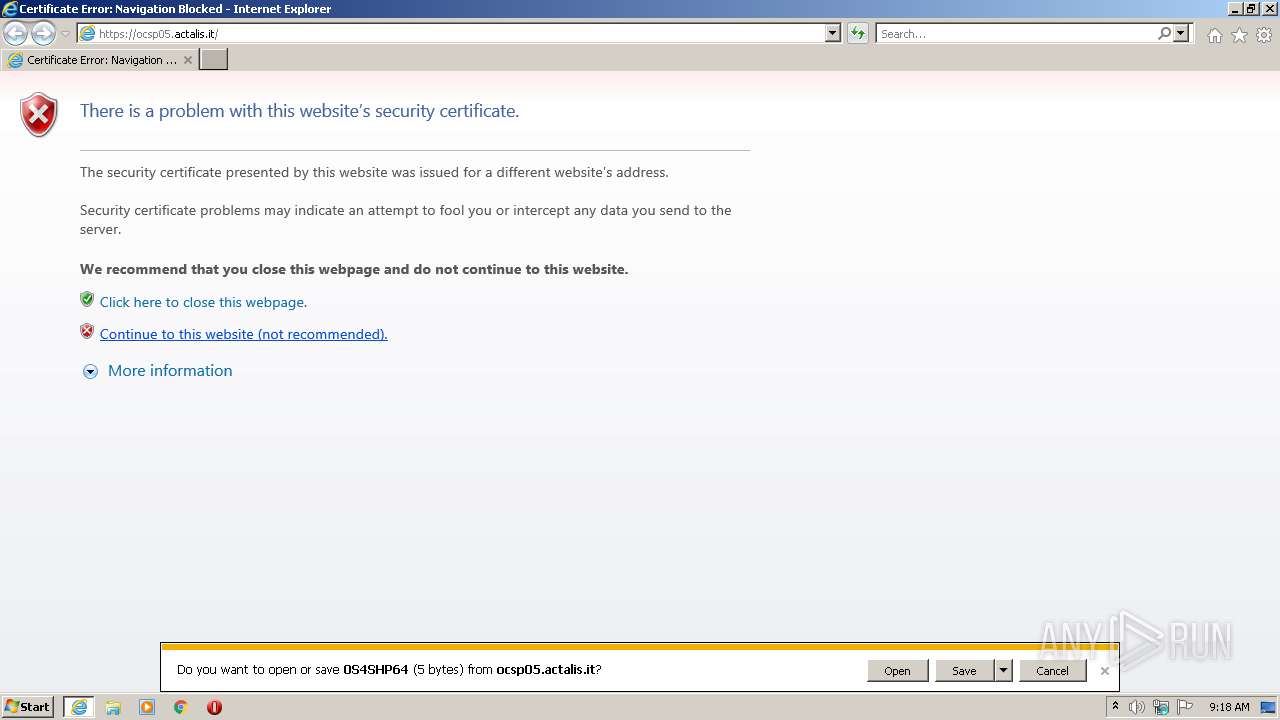
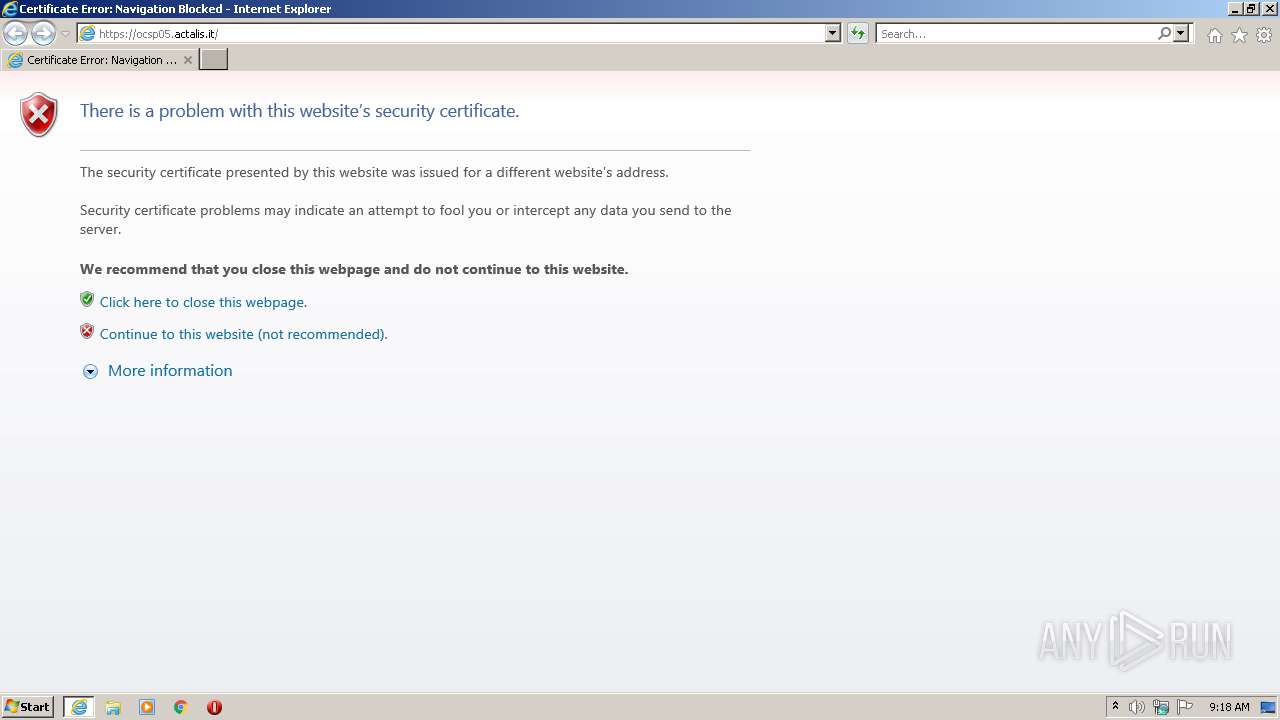
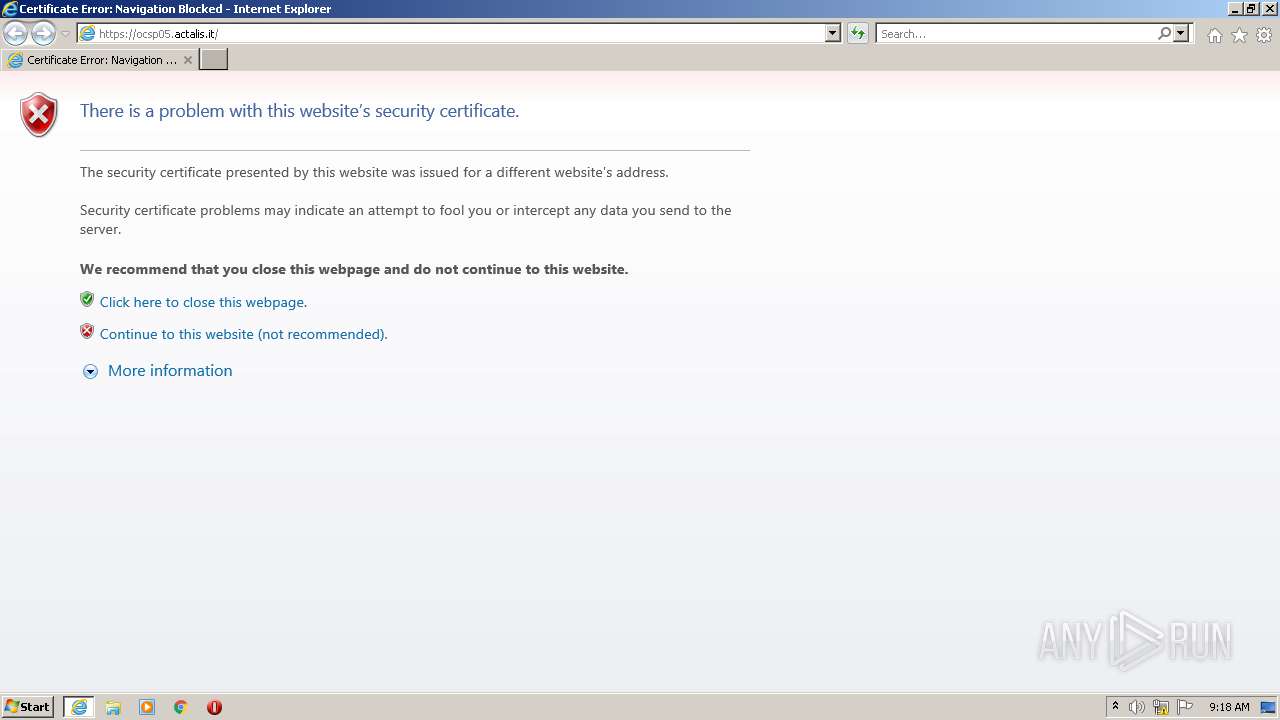
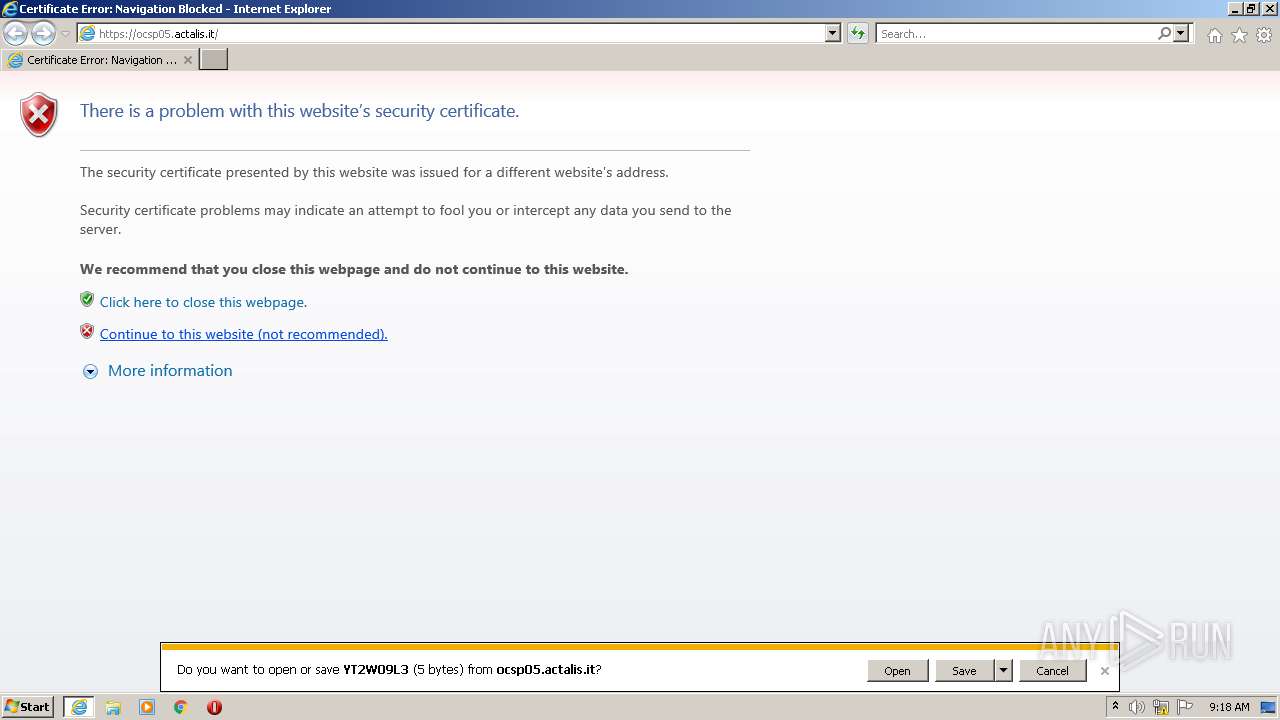
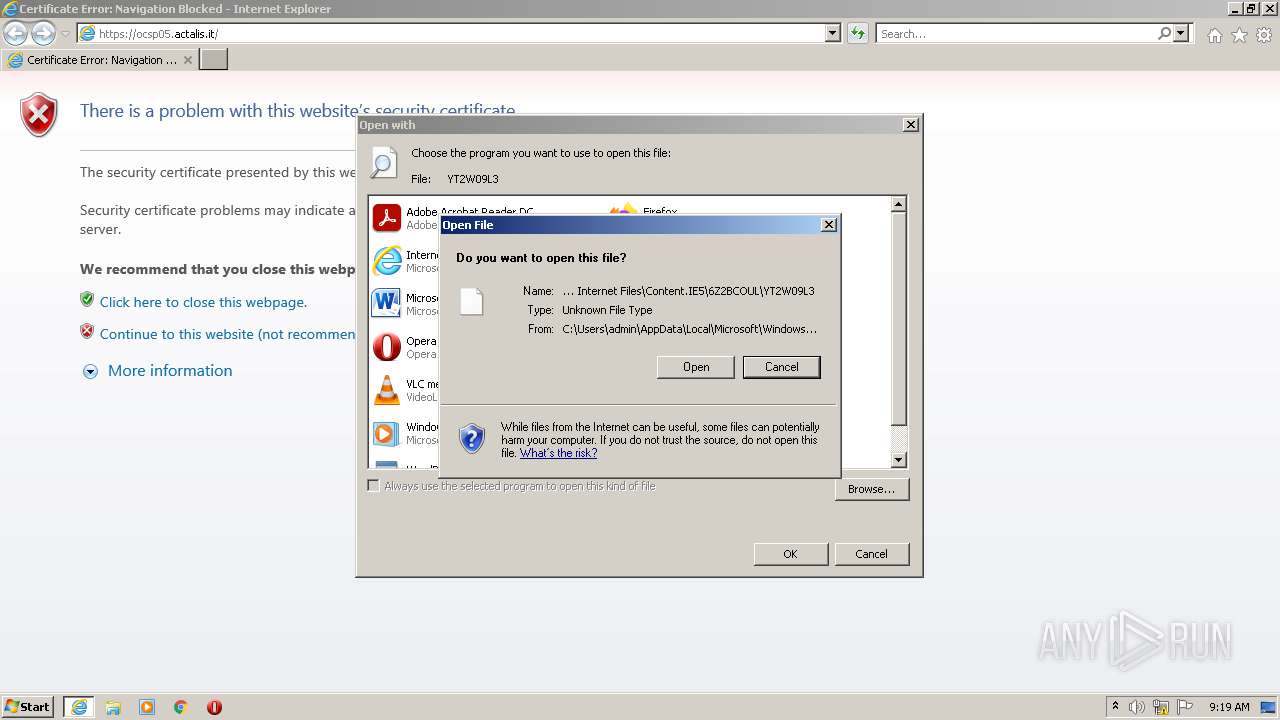
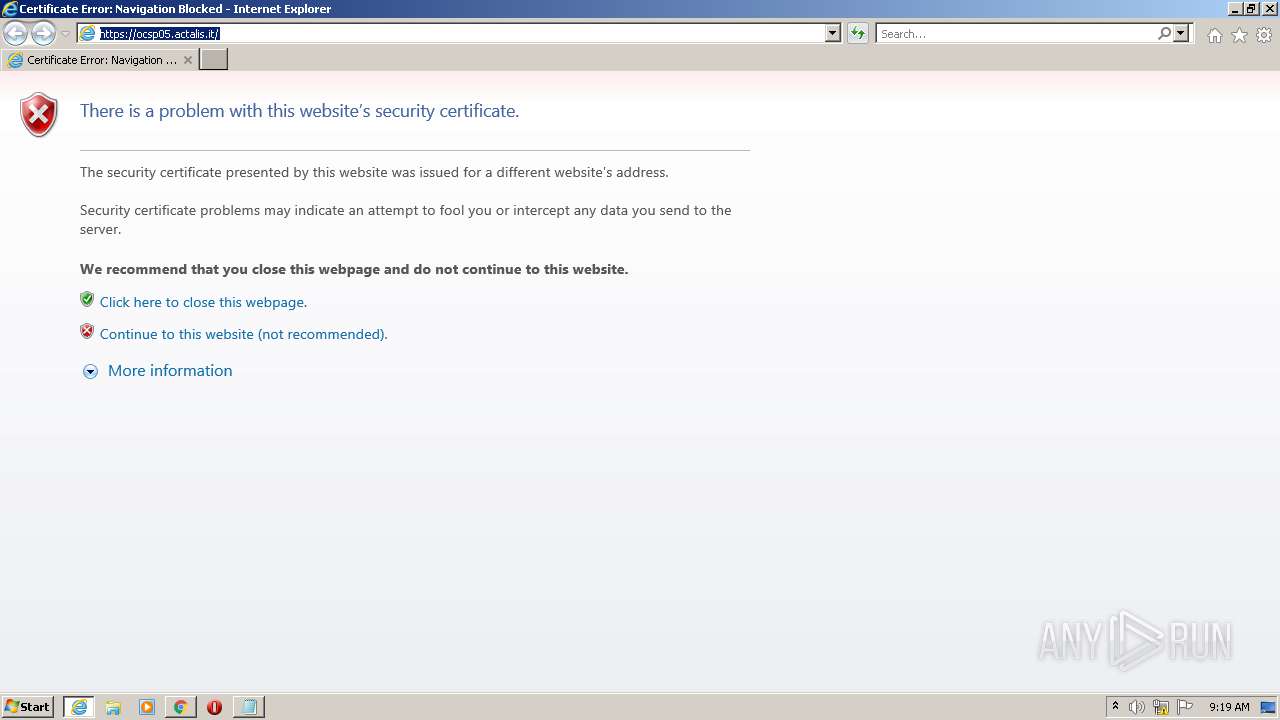
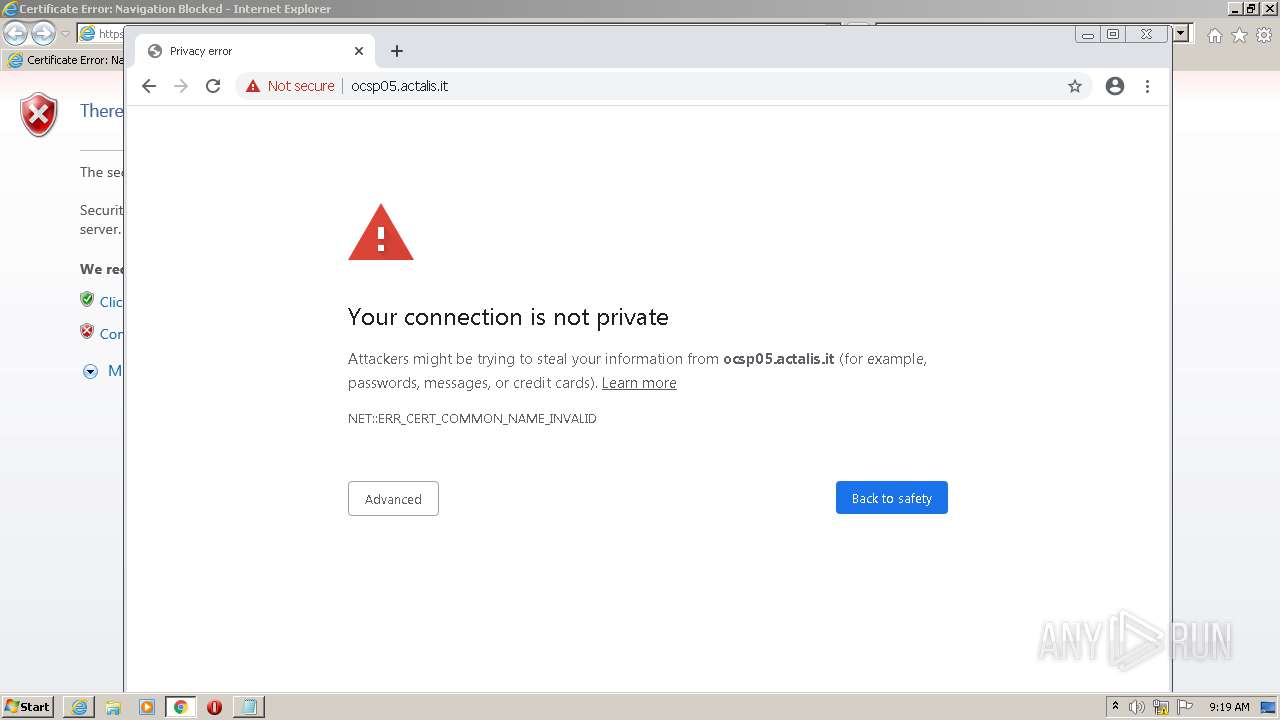
| URL: | https://ocsp05.actalis.it |
| Full analysis: | https://app.any.run/tasks/98daebbc-7e8a-4b88-a049-65fdfa96c067 |
| Verdict: | Malicious activity |
| Analysis date: | June 23, 2021, 08:17:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C918F4A14A266AED8FFD4CD40E95FA67 |
| SHA1: | 54FB93CE43C58D5FA80BD074184A7D5C88AC7D1C |
| SHA256: | 130FA5DC7B6CC2CD82C2B878386A67C4B7B0948B0384DAF3333AAD8942ED6F4B |
| SSDEEP: | 3:N8PSgEGJD:2akV |
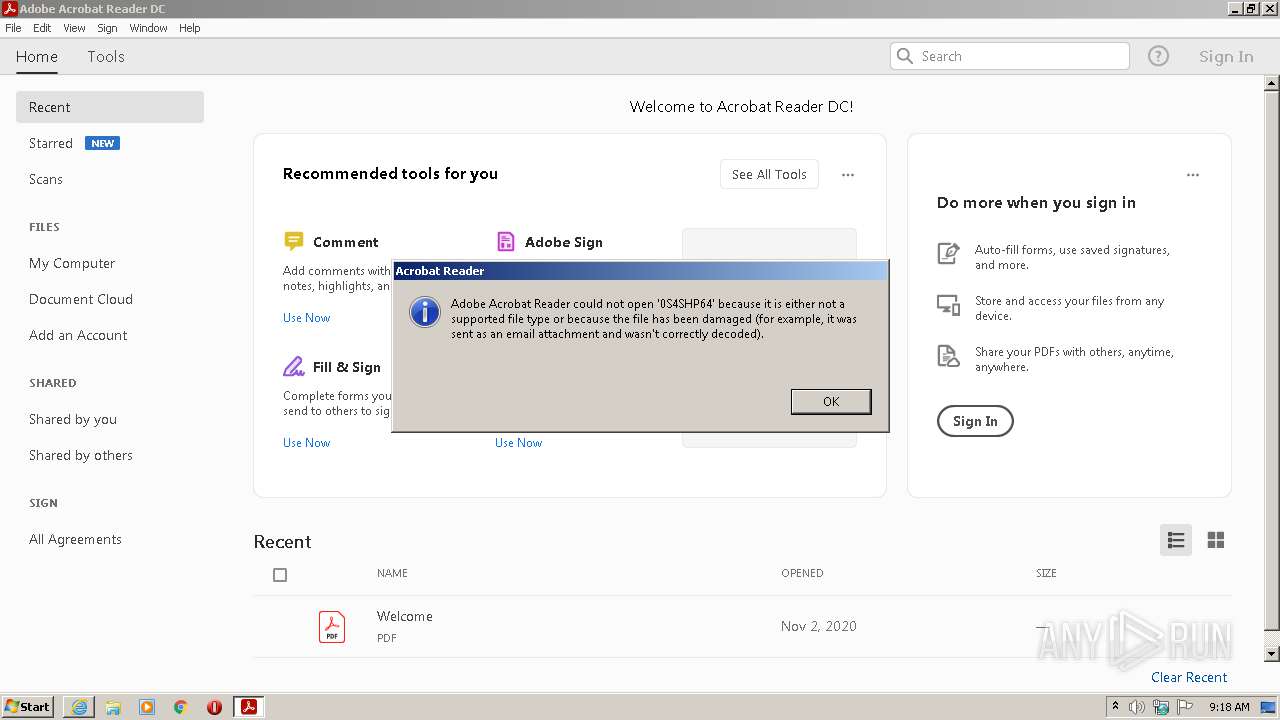
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 688)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2068)
- iexplore.exe (PID: 1032)
Uses RUNDLL32.EXE to load library
- iexplore.exe (PID: 4000)
Reads the date of Windows installation
- rundll32.exe (PID: 2928)
- rundll32.exe (PID: 2928)
- rundll32.exe (PID: 3700)
- rundll32.exe (PID: 3500)
- rundll32.exe (PID: 2764)
Drops a file with a compile date too recent
- RdrCEF.exe (PID: 3764)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2136)
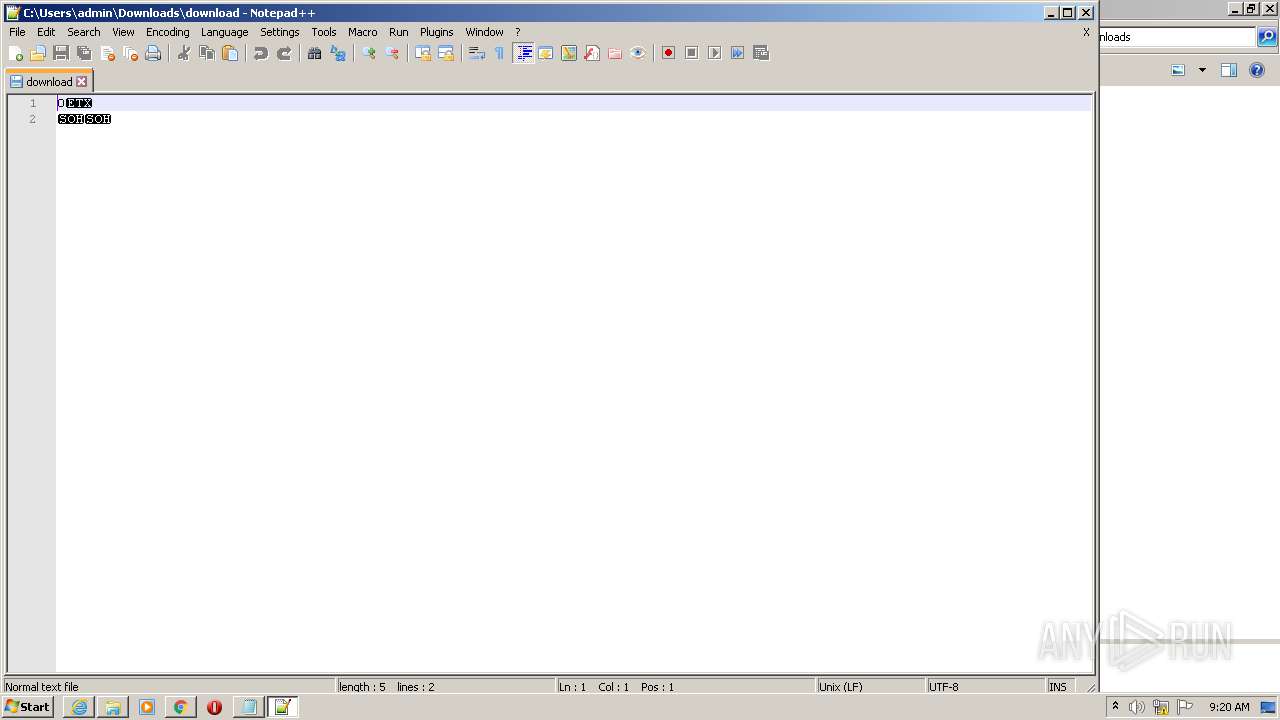
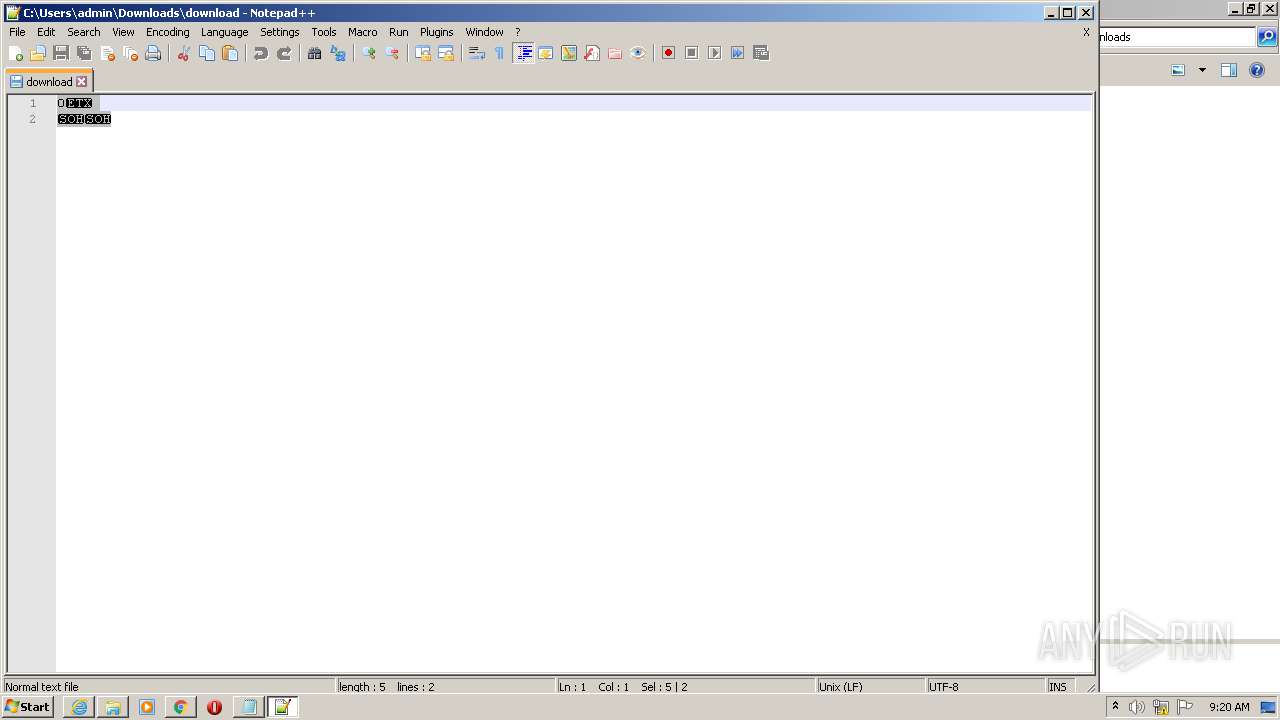
Checks supported languages
- notepad++.exe (PID: 3396)
Executable content was dropped or overwritten
- chrome.exe (PID: 688)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 688)
INFO
Checks supported languages
- iexplore.exe (PID: 4000)
- iexplore.exe (PID: 2068)
- iexplore.exe (PID: 1032)
- rundll32.exe (PID: 2928)
- AcroRd32.exe (PID: 2372)
- AcroRd32.exe (PID: 2500)
- RdrCEF.exe (PID: 744)
- RdrCEF.exe (PID: 3764)
- RdrCEF.exe (PID: 3524)
- RdrCEF.exe (PID: 148)
- RdrCEF.exe (PID: 1948)
- RdrCEF.exe (PID: 2060)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 2588)
- rundll32.exe (PID: 2928)
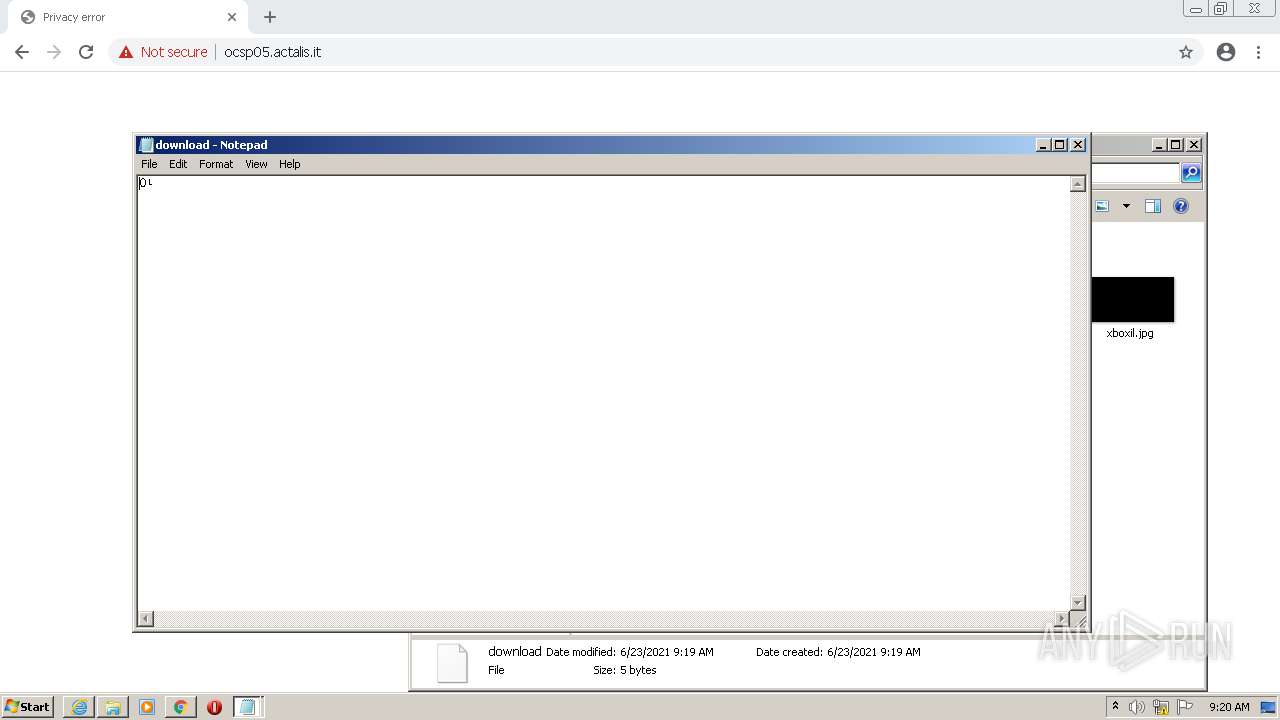
- NOTEPAD.EXE (PID: 1484)
- chrome.exe (PID: 3104)
- RdrCEF.exe (PID: 1124)
- chrome.exe (PID: 2860)
- chrome.exe (PID: 1424)
- chrome.exe (PID: 1684)
- chrome.exe (PID: 400)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 3436)
- chrome.exe (PID: 1680)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 444)
- chrome.exe (PID: 1412)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 1412)
- chrome.exe (PID: 2104)
- chrome.exe (PID: 1460)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 2764)
- rundll32.exe (PID: 3700)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 3916)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 688)
- NOTEPAD.EXE (PID: 3068)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 1440)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 3252)
- rundll32.exe (PID: 3500)
- chrome.exe (PID: 2988)
- firefox.exe (PID: 3348)
- firefox.exe (PID: 2736)
- firefox.exe (PID: 3976)
- firefox.exe (PID: 1076)
- firefox.exe (PID: 2196)
- firefox.exe (PID: 1088)
- firefox.exe (PID: 2824)
- firefox.exe (PID: 3864)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 1428)
- chrome.exe (PID: 288)
- chrome.exe (PID: 3296)
- rundll32.exe (PID: 2764)
- firefox.exe (PID: 3784)
- firefox.exe (PID: 1052)
Reads the computer name
- iexplore.exe (PID: 4000)
- iexplore.exe (PID: 1032)
- iexplore.exe (PID: 2068)
- AcroRd32.exe (PID: 2372)
- AcroRd32.exe (PID: 2500)
- rundll32.exe (PID: 2928)
- RdrCEF.exe (PID: 3764)
- rundll32.exe (PID: 2928)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 2860)
- chrome.exe (PID: 3104)
- chrome.exe (PID: 1680)
- chrome.exe (PID: 444)
- chrome.exe (PID: 2104)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 2764)
- rundll32.exe (PID: 3700)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 3916)
- rundll32.exe (PID: 3500)
- firefox.exe (PID: 1076)
- firefox.exe (PID: 2736)
- firefox.exe (PID: 3976)
- firefox.exe (PID: 2196)
- firefox.exe (PID: 1088)
- firefox.exe (PID: 3864)
- firefox.exe (PID: 2824)
- rundll32.exe (PID: 2764)
- firefox.exe (PID: 3784)
Checks Windows Trust Settings
- iexplore.exe (PID: 4000)
- iexplore.exe (PID: 1032)
- iexplore.exe (PID: 2068)
- rundll32.exe (PID: 2928)
- AcroRd32.exe (PID: 2372)
- rundll32.exe (PID: 2928)
- chrome.exe (PID: 2136)
- rundll32.exe (PID: 3700)
- rundll32.exe (PID: 3500)
- firefox.exe (PID: 1076)
- rundll32.exe (PID: 2764)
Changes internet zones settings
- iexplore.exe (PID: 4000)
Reads settings of System Certificates
- iexplore.exe (PID: 4000)
- iexplore.exe (PID: 2068)
- iexplore.exe (PID: 1032)
- RdrCEF.exe (PID: 3764)
- AcroRd32.exe (PID: 2372)
- chrome.exe (PID: 3104)
Reads internet explorer settings
- iexplore.exe (PID: 2068)
- iexplore.exe (PID: 1032)
Application launched itself
- iexplore.exe (PID: 4000)
- AcroRd32.exe (PID: 2372)
- RdrCEF.exe (PID: 3764)
- chrome.exe (PID: 2136)
- firefox.exe (PID: 1076)
- firefox.exe (PID: 3348)
- firefox.exe (PID: 1052)
Modifies the phishing filter of IE
- iexplore.exe (PID: 4000)
Searches for installed software
- AcroRd32.exe (PID: 2372)
- AcroRd32.exe (PID: 2500)
Reads the hosts file
- RdrCEF.exe (PID: 3764)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 3104)
Reads CPU info
- AcroRd32.exe (PID: 2500)
- firefox.exe (PID: 1076)
- firefox.exe (PID: 3784)
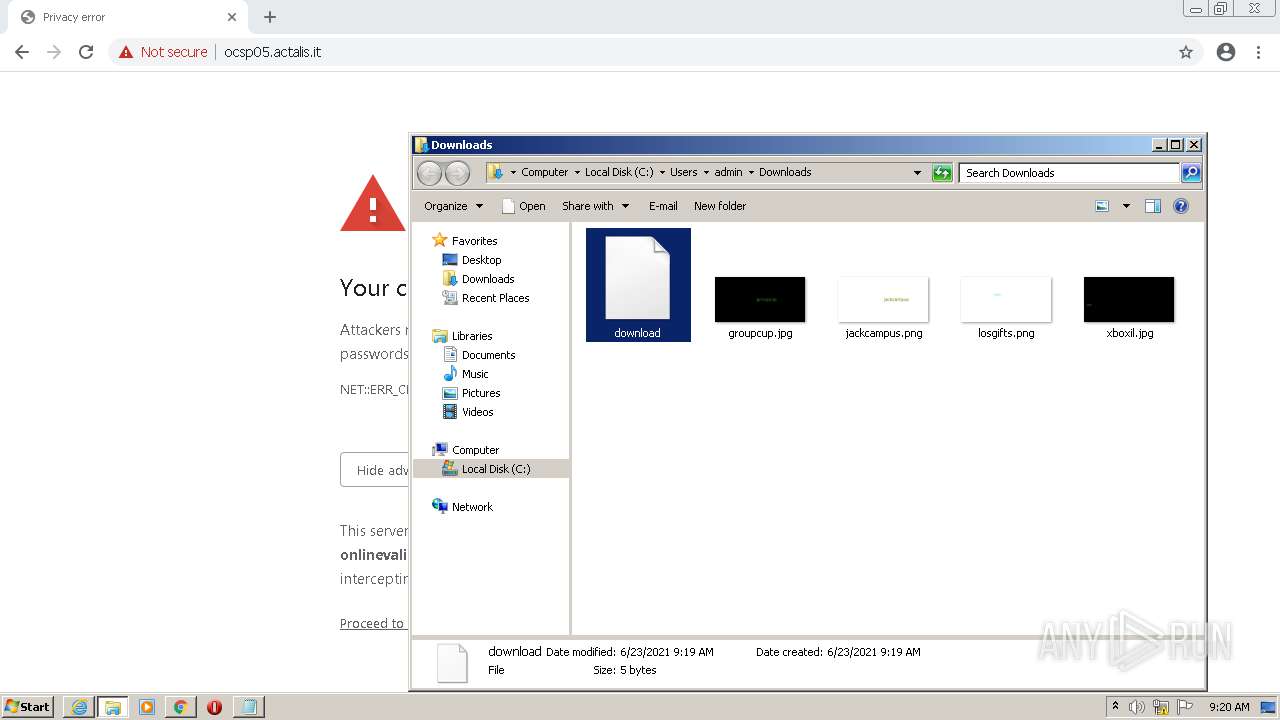
Creates files in the user directory
- iexplore.exe (PID: 4000)
- firefox.exe (PID: 1076)
Changes settings of System certificates
- iexplore.exe (PID: 4000)
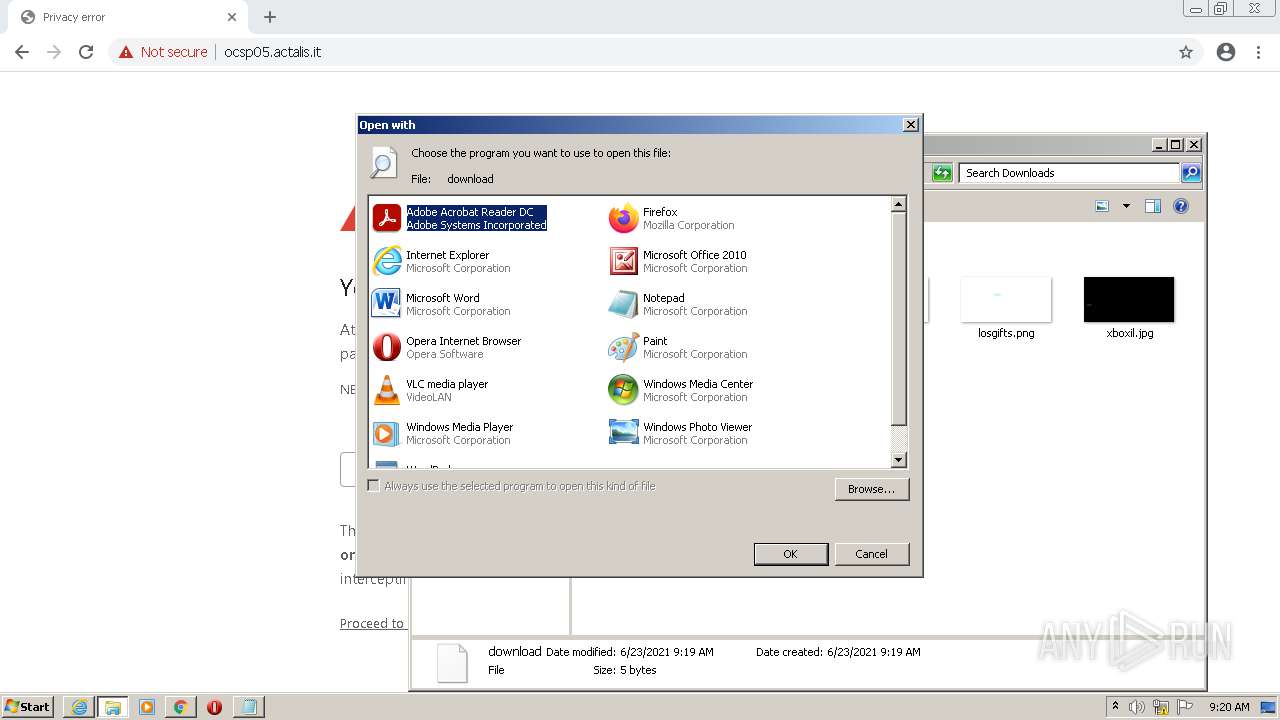
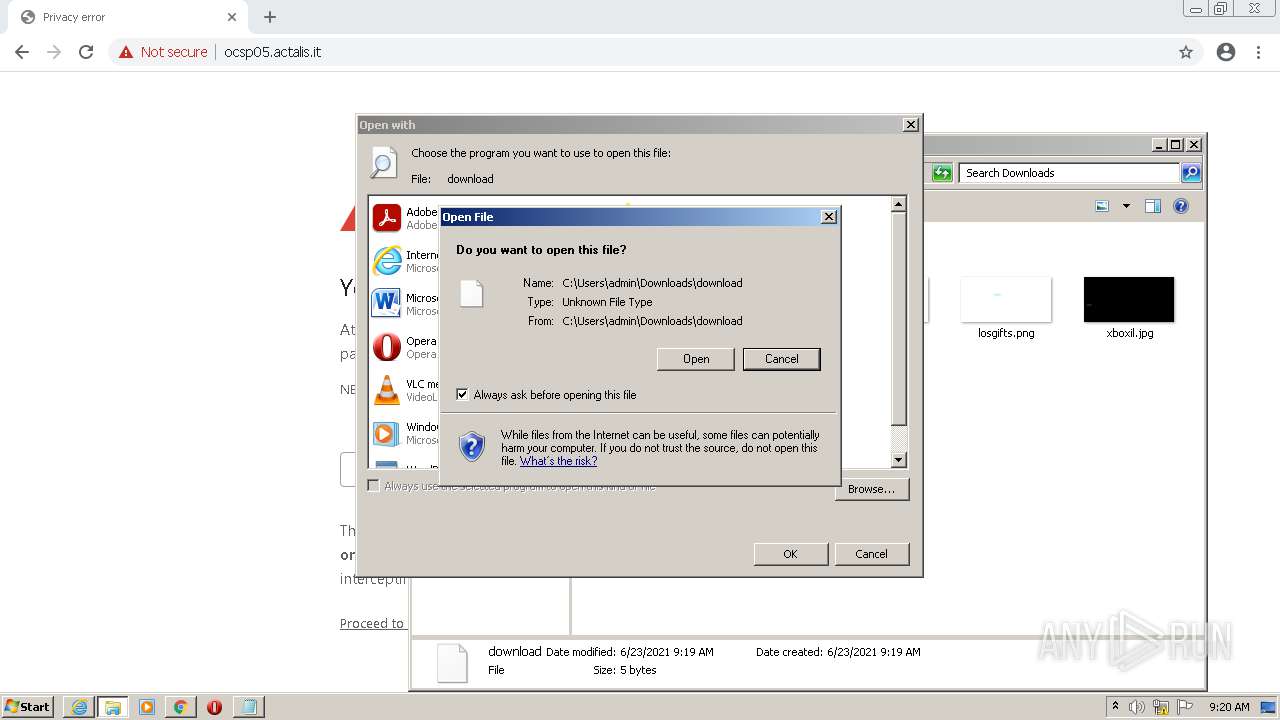
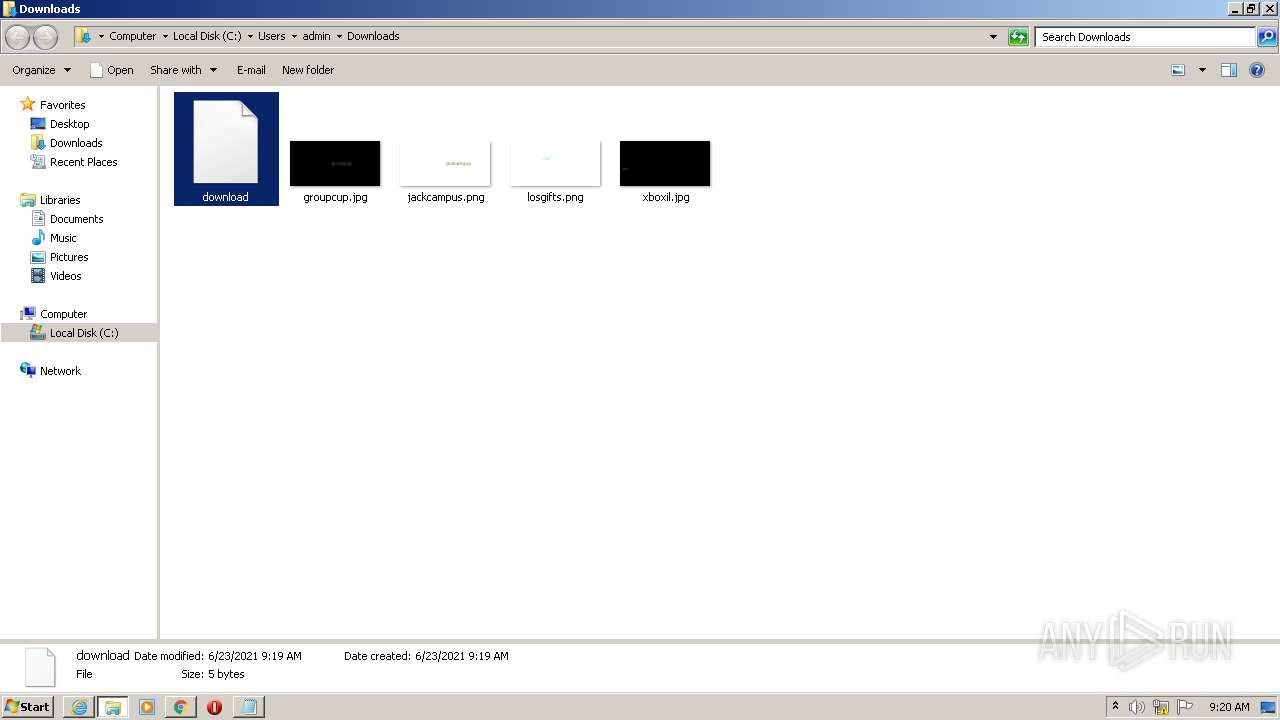
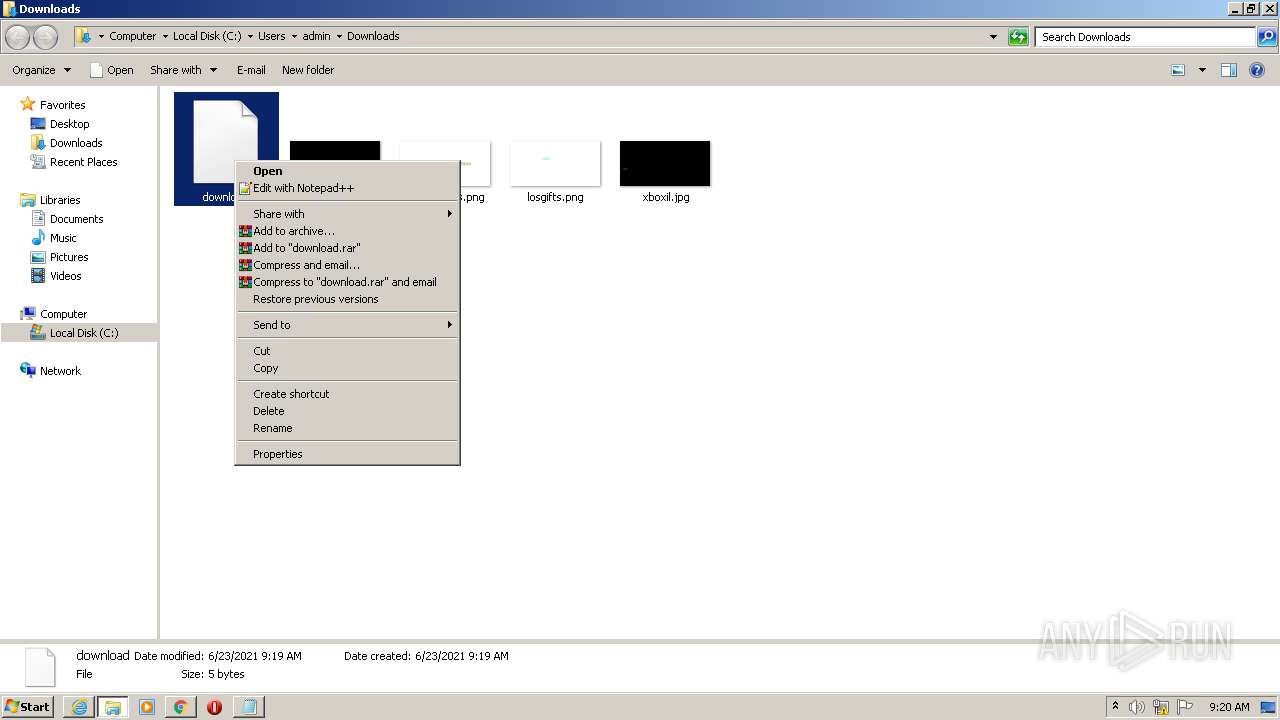
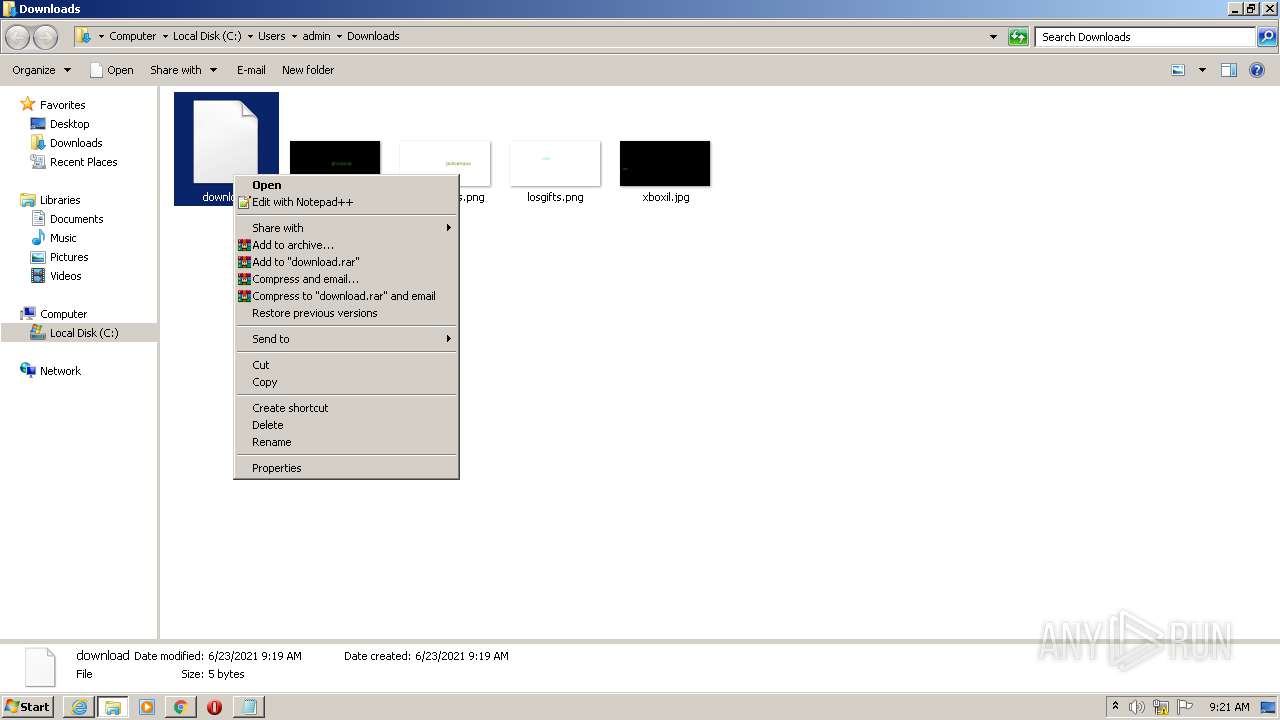
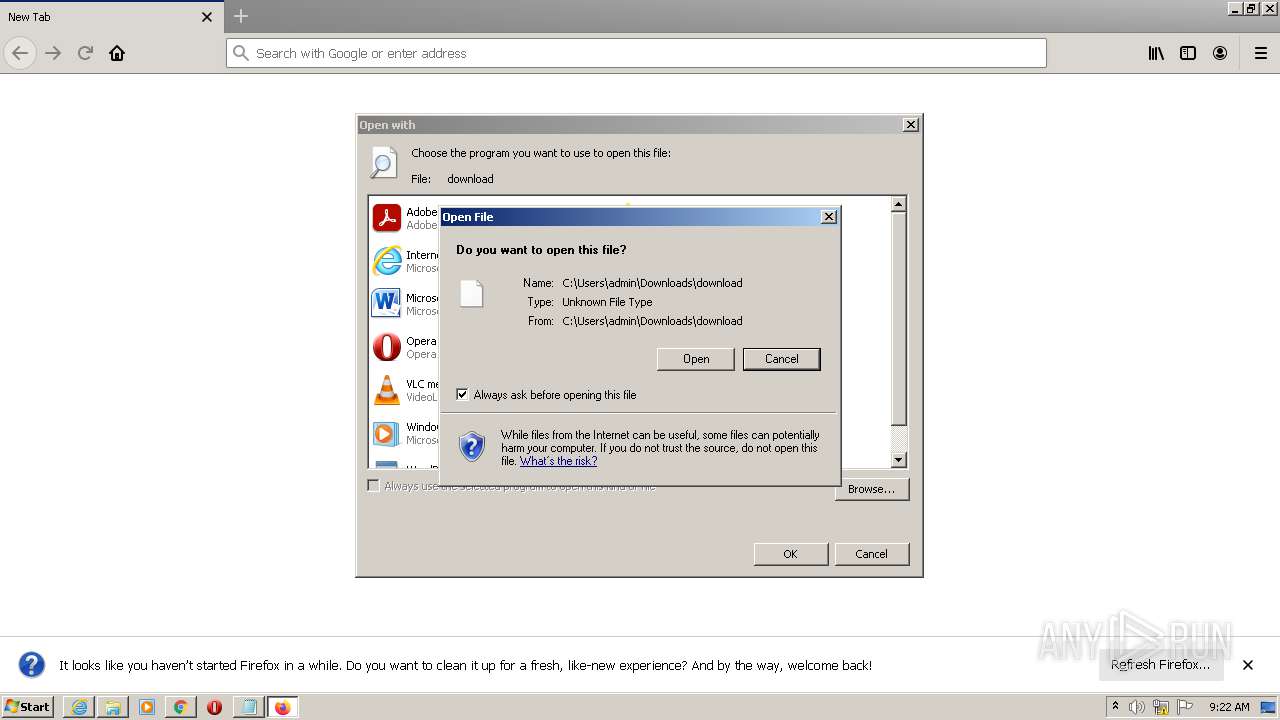
Manual execution by user
- chrome.exe (PID: 2136)
- rundll32.exe (PID: 3700)
- notepad++.exe (PID: 3396)
- rundll32.exe (PID: 3500)
- rundll32.exe (PID: 2764)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4000)
Reads the date of Windows installation
- chrome.exe (PID: 3020)
Creates files in the program directory
- firefox.exe (PID: 1076)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 1076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
108
Monitored processes
68
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1180,756352574885262118,17429915058084552003,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=12826323930663467128 --mojo-platform-channel-handle=1420 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,13545611857928938501,16896529566951859969,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=660 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,13545611857928938501,16896529566951859969,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,13545611857928938501,16896529566951859969,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3392 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,13545611857928938501,16896529566951859969,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=996 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1180,756352574885262118,17429915058084552003,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=14125945283991222279 --mojo-platform-channel-handle=1272 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4000 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
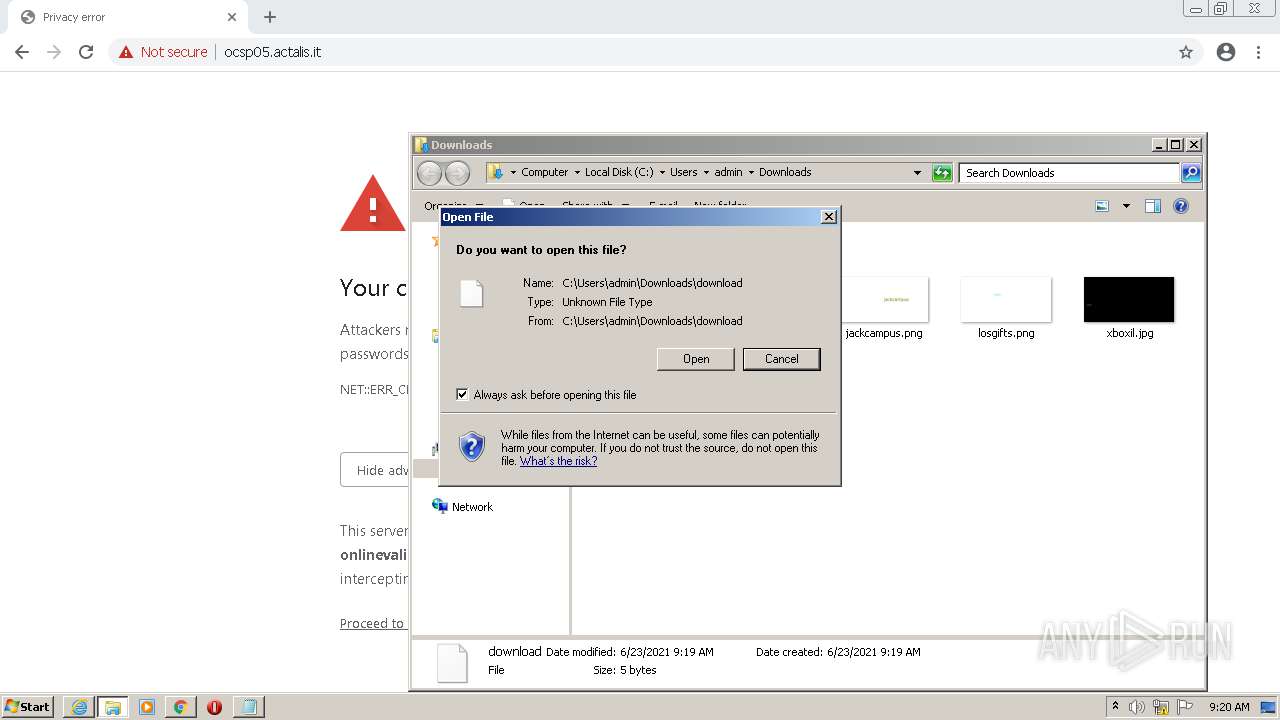
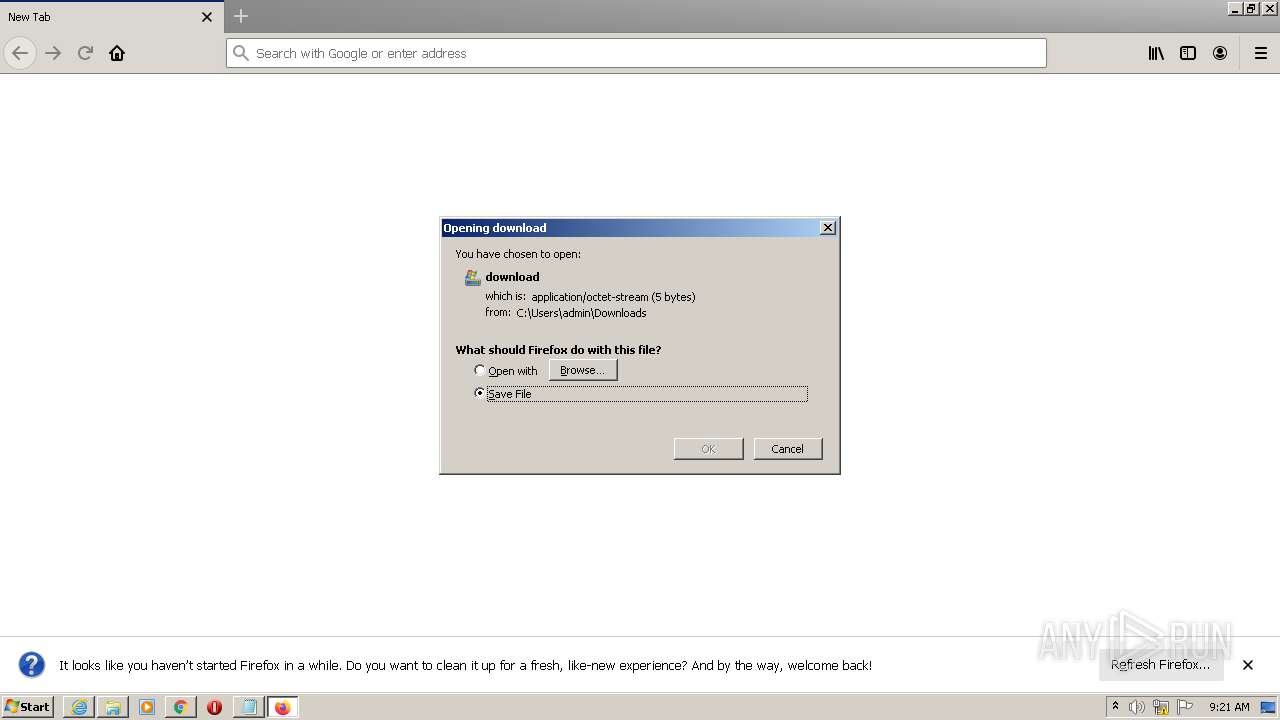
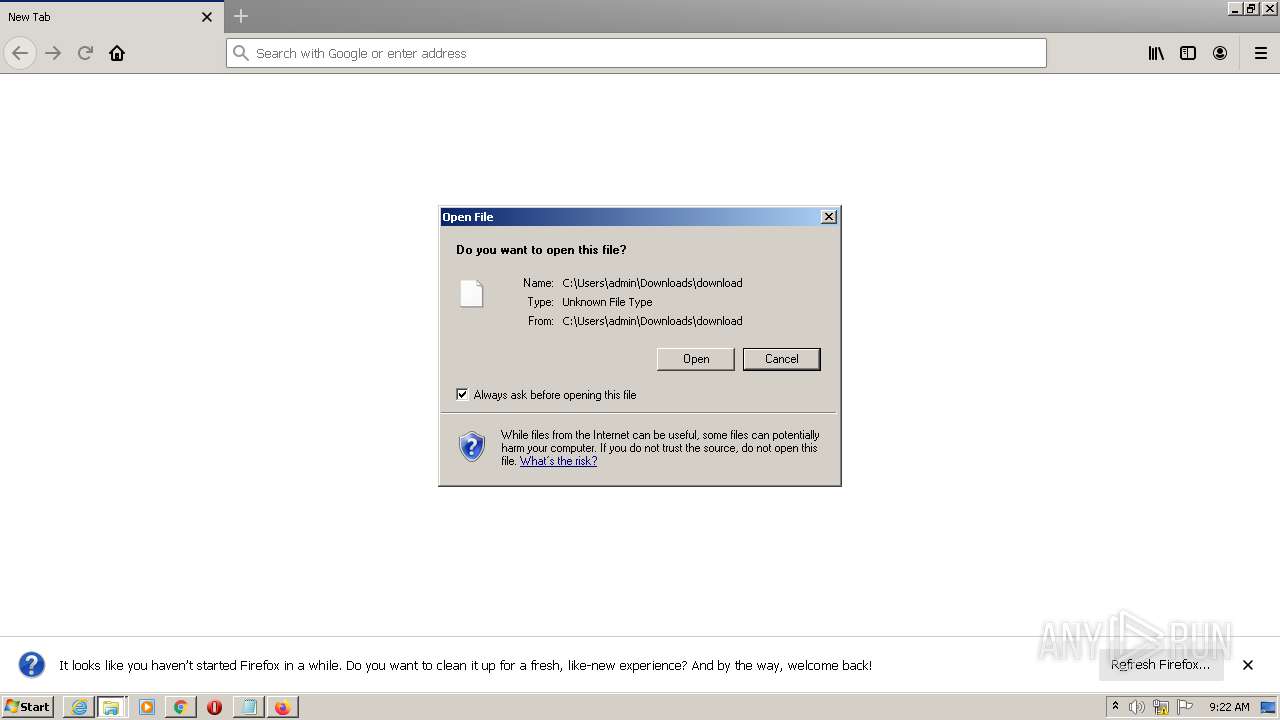
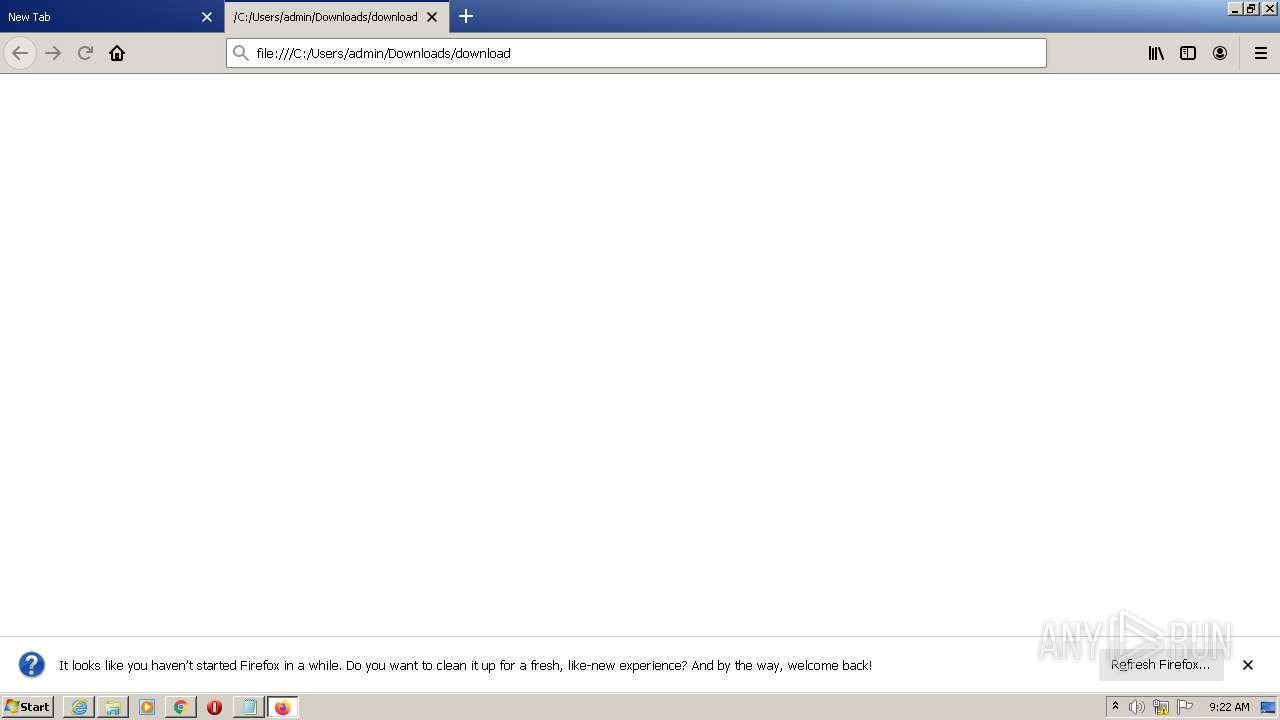
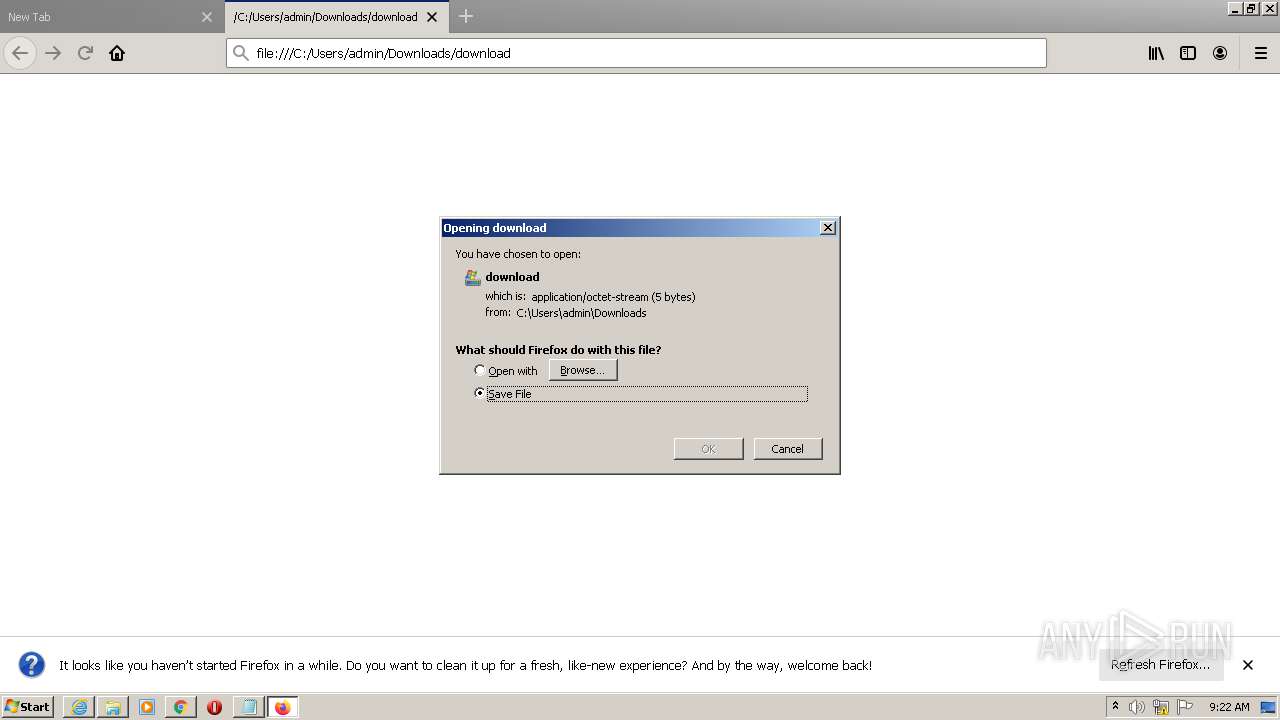
| 1052 | "C:\Program Files\Mozilla Firefox\firefox.exe" -osint -url "C:\Users\admin\Downloads\download" | C:\Program Files\Mozilla Firefox\firefox.exe | — | rundll32.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Mozilla Firefox\firefox.exe" -url C:\Users\admin\Downloads\download | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1076.20.1994284399\1792342386" -childID 3 -isForBrowser -prefsHandle 1744 -prefMapHandle 1748 -prefsLen 7470 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 1076 "\\.\pipe\gecko-crash-server-pipe.1076" 3664 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
54 391
Read events
53 655
Write events
721
Delete events
15
Modification events
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30894088 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30894088 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
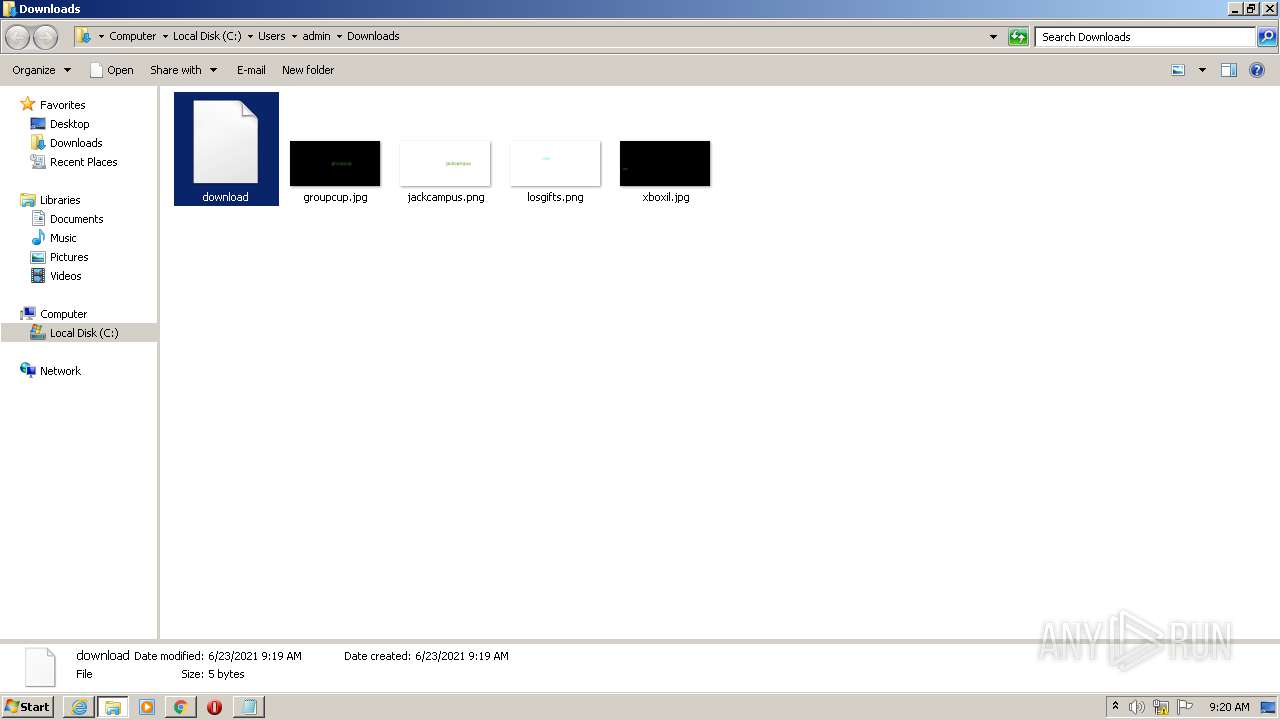
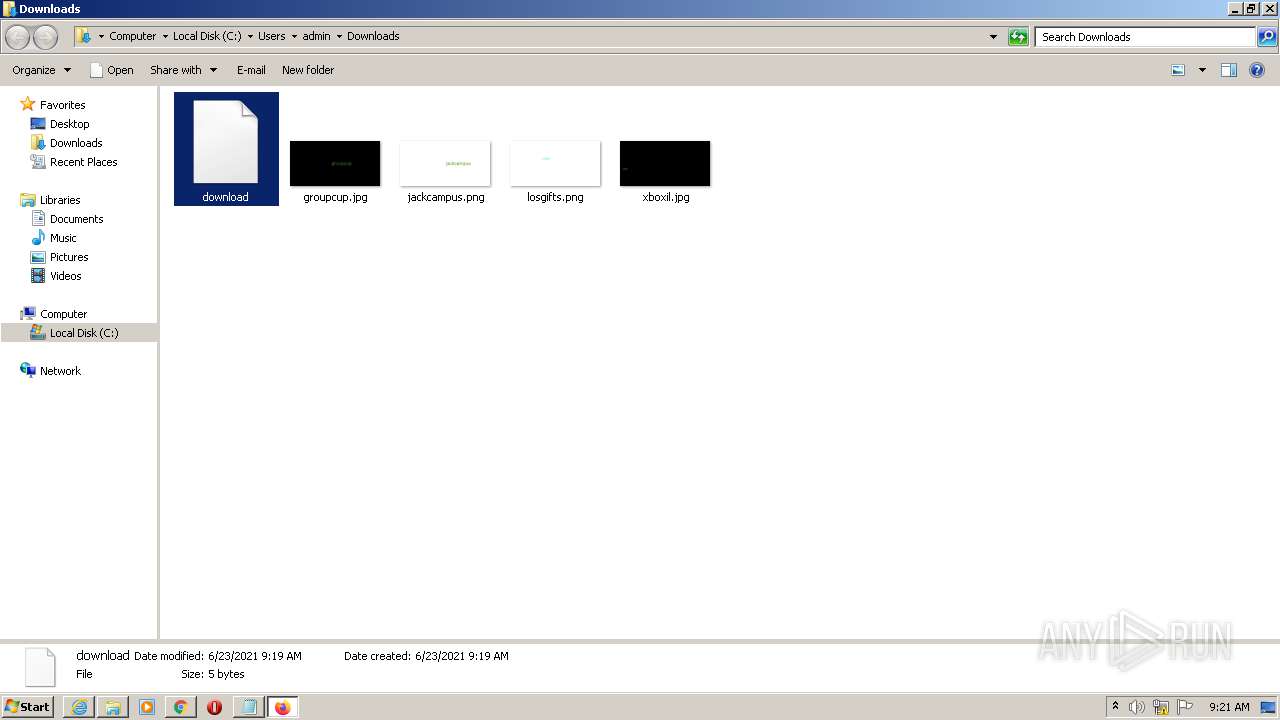
Executable files
1
Suspicious files
270
Text files
320
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
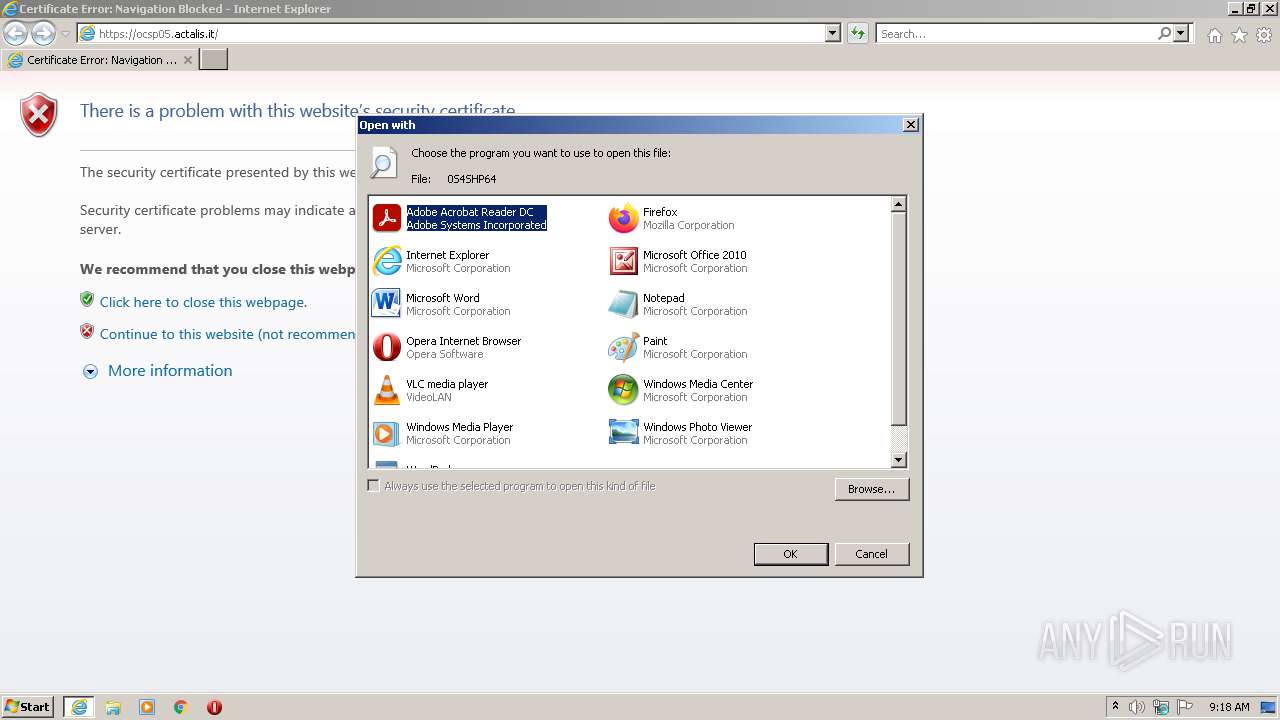
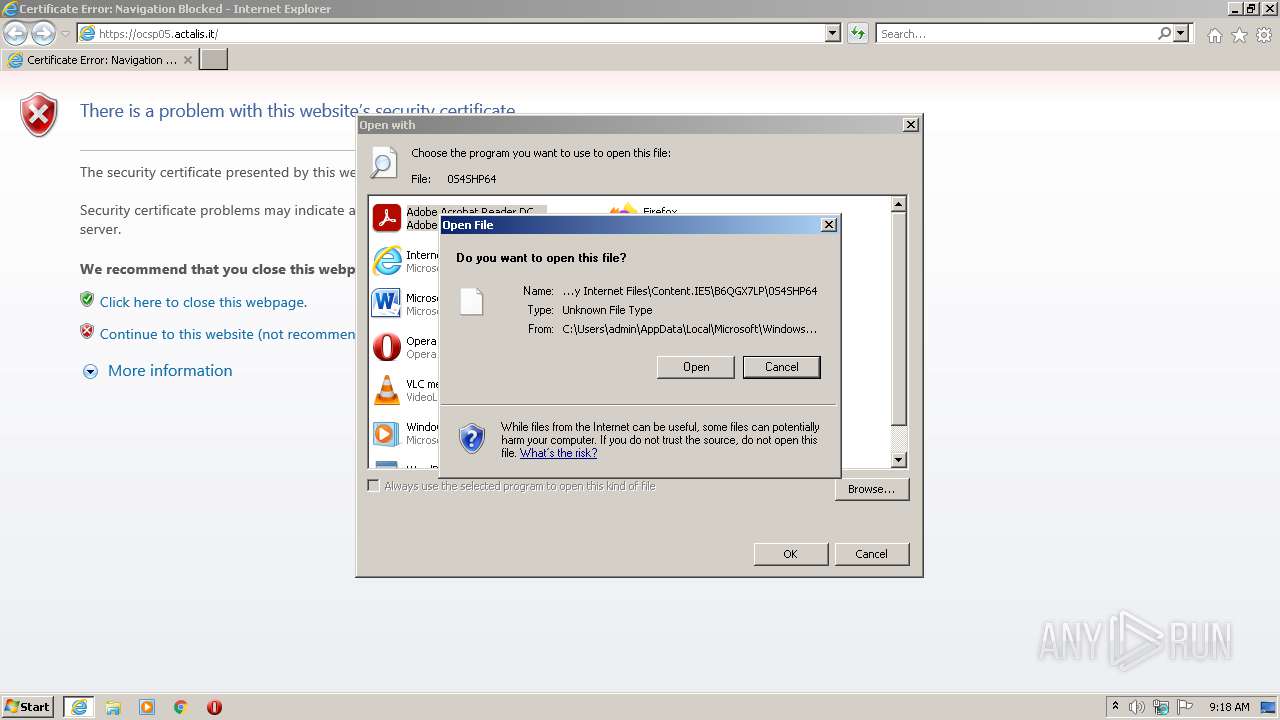
| 1032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B43A6A2AB31D8F6B89DCFD4FD9686D5_51B5A975EEA62653A44730A3B2364546 | der | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB28D4C754335323A.TMP | gmc | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B43A6A2AB31D8F6B89DCFD4FD9686D5_51B5A975EEA62653A44730A3B2364546 | binary | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{94B95965-D3FB-11EB-97B3-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\4312D9E4F5C8D4B73467676D3FF41C7C_CE67929BE7FAF1276E6D4581C96B532B | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
84
DNS requests
92
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3104 | chrome.exe | GET | 204 | 142.250.185.99:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
1776 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | — | — | whitelisted |
1032 | iexplore.exe | GET | 200 | 109.70.240.114:80 | http://ocsp09.actalis.it/VA/AUTHOV-G3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ0v4LB%2FH9ZBPiv3nSFjhLMhCxVJwQUn4qxtfGx3oL0J3y%2BiM3eqUOBo0sCEHIHI0m8t5I5%2FBbNkuqNSlY%3D | IT | der | 1.99 Kb | whitelisted |
1776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 7.10 Kb | whitelisted |
4000 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
4000 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
4000 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1032 | iexplore.exe | GET | 200 | 109.70.240.130:80 | http://ocsp05.actalis.it/VA/AUTH-ROOT/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSw4x5v4bTlizjNRmTdkYSy7q0R9gQUUtiIOsifeGbtifN7OHCUyQICNtACEFw7Pzet%2FCj%2BD8%2FTq%2Fg%2FhVE%3D | IT | der | 2.01 Kb | whitelisted |
4000 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
1776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 88.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
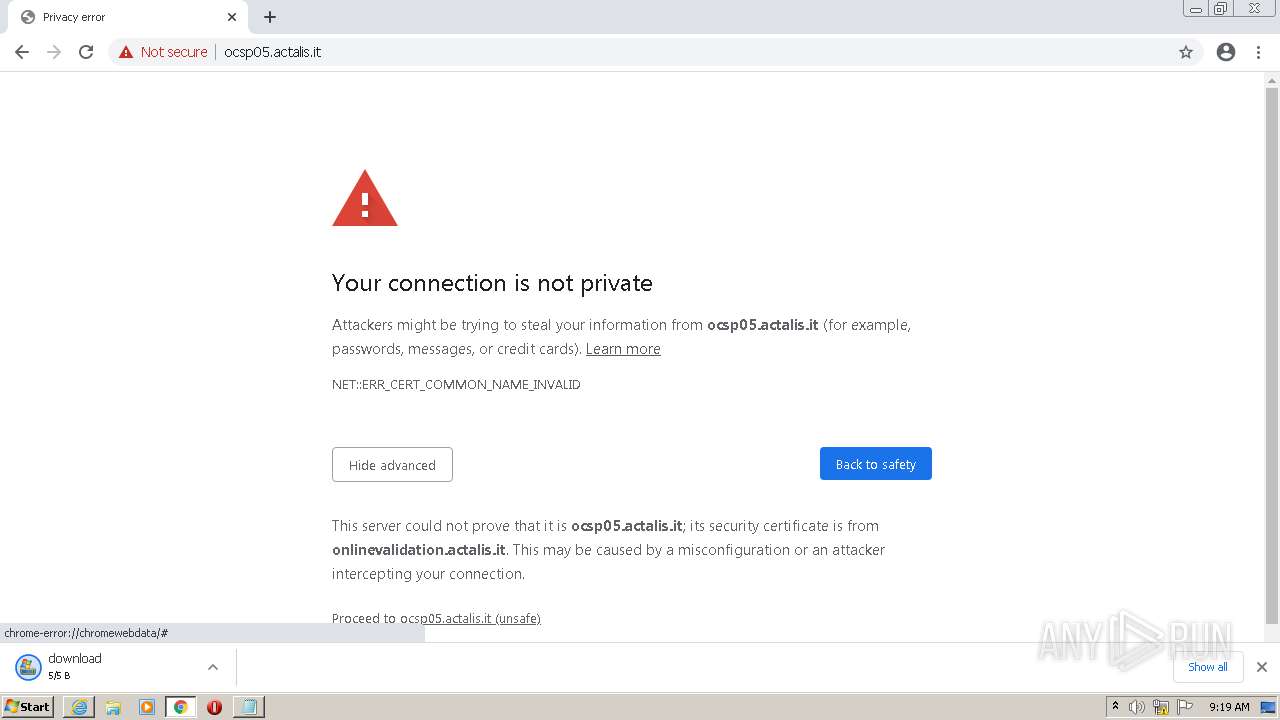
1032 | iexplore.exe | 109.70.240.130:443 | ocsp05.actalis.it | Aruba S.p.A. | IT | suspicious |
4000 | iexplore.exe | 13.107.22.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4000 | iexplore.exe | 23.32.238.153:80 | ctldl.windowsupdate.com | XO Communications | US | unknown |
1032 | iexplore.exe | 109.70.240.114:80 | ocsp09.actalis.it | Aruba S.p.A. | IT | unknown |
2068 | iexplore.exe | 109.70.240.130:443 | ocsp05.actalis.it | Aruba S.p.A. | IT | suspicious |
3764 | RdrCEF.exe | 23.218.208.137:443 | geo2.adobe.com | TATA COMMUNICATIONS (AMERICA) INC | US | suspicious |
3764 | RdrCEF.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
4000 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4000 | iexplore.exe | 131.253.33.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
2372 | AcroRd32.exe | 2.16.107.90:443 | acroipm2.adobe.com | Akamai International B.V. | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp05.actalis.it |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp09.actalis.it |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
geo2.adobe.com |
| whitelisted |
p13n.adobe.io |
| whitelisted |