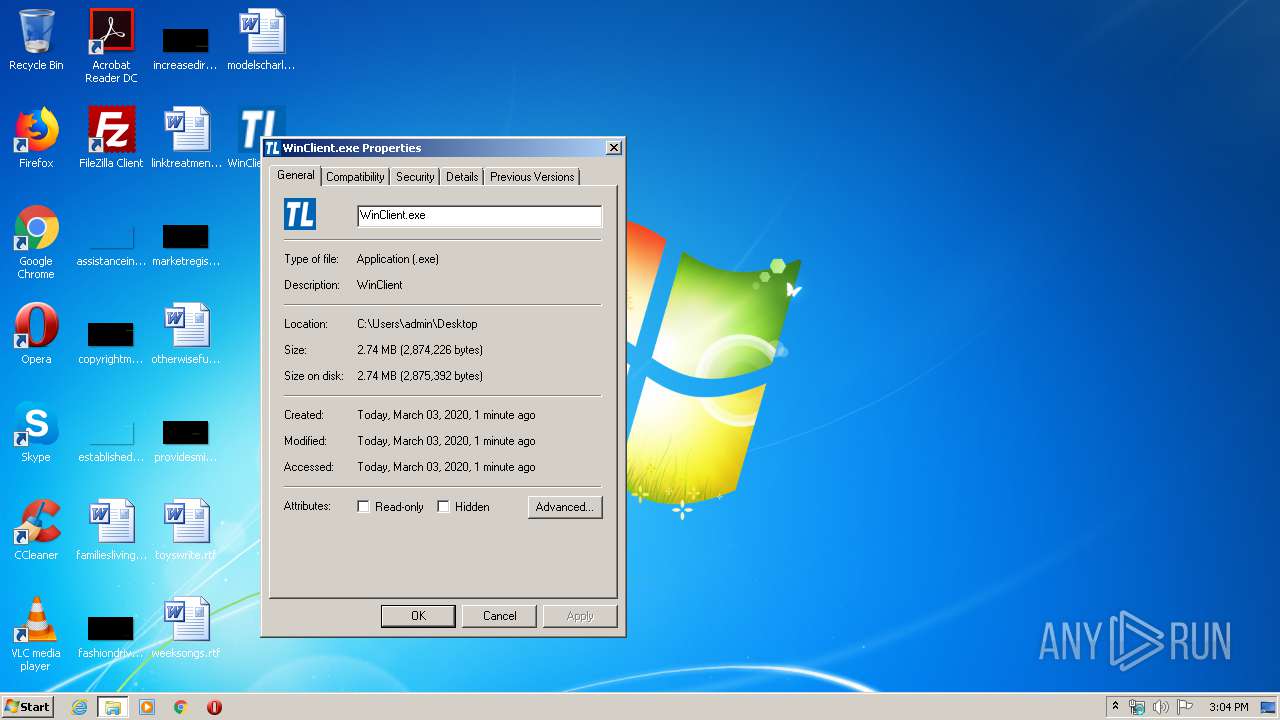
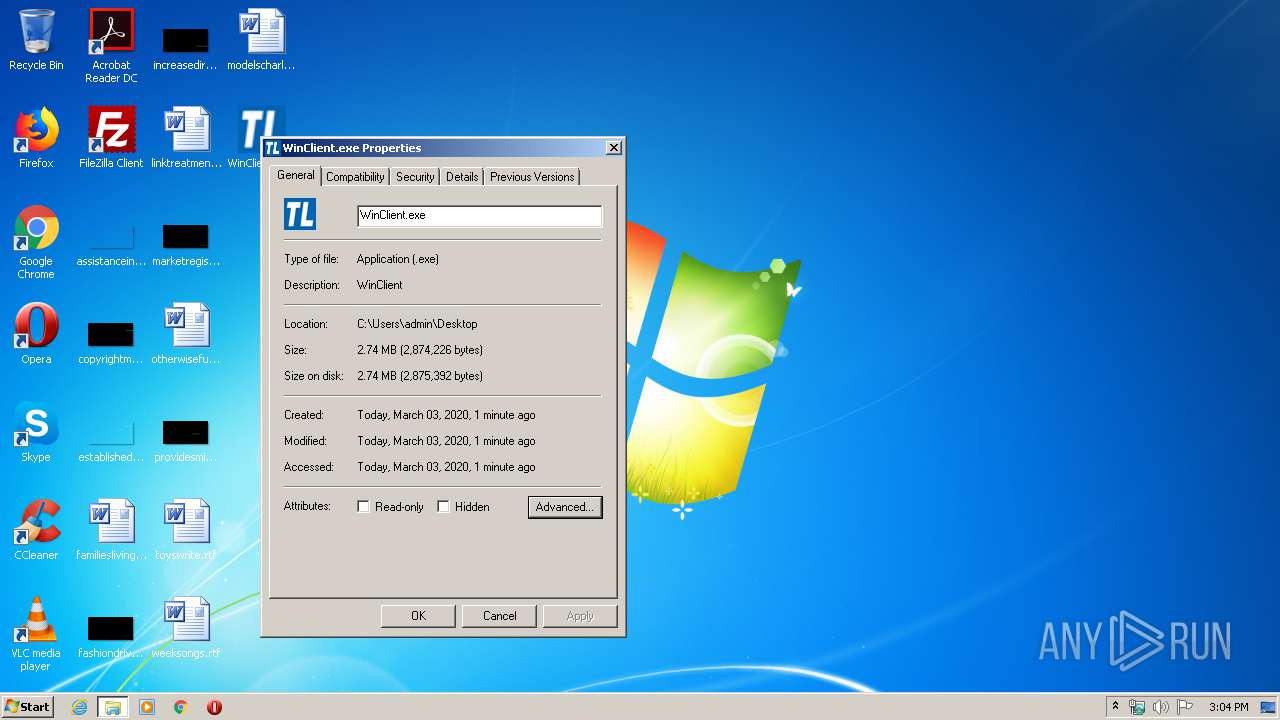
| File name: | WinClient.exe |
| Full analysis: | https://app.any.run/tasks/26856bf3-51d5-413f-9217-222443209398 |
| Verdict: | Malicious activity |
| Analysis date: | March 03, 2020, 15:03:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2424DE078F648A7A75DEB5E33C7A3F2F |
| SHA1: | 3EBE3E90BBB879178C0F6885E187928502DE661F |
| SHA256: | 13015BCEE831EDD60D854B0E52C75428A9FC7074B166C21FF92AABAEE37691DC |
| SSDEEP: | 49152:l+xzHL5cnH9r9L1Mccvj4kxK2HRdf3PZLRp/gyTLHq0ubDrw:gpaFrMcYpHjf3VVnB |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- WinClient.exe (PID: 780)
- WinClient.exe (PID: 2868)
- WinClient.exe (PID: 2132)
Loads dropped or rewritten executable
- WinClient.exe (PID: 2132)
- WinClient.exe (PID: 2868)
- Regsvr32.exe (PID: 2708)
- Regsvr32.exe (PID: 3492)
- WinClient.exe (PID: 780)
- Regsvr32.exe (PID: 3732)
- SearchProtocolHost.exe (PID: 3548)
SUSPICIOUS
Executable content was dropped or overwritten
- WinClient.exe (PID: 780)
- WinClient.exe (PID: 2868)
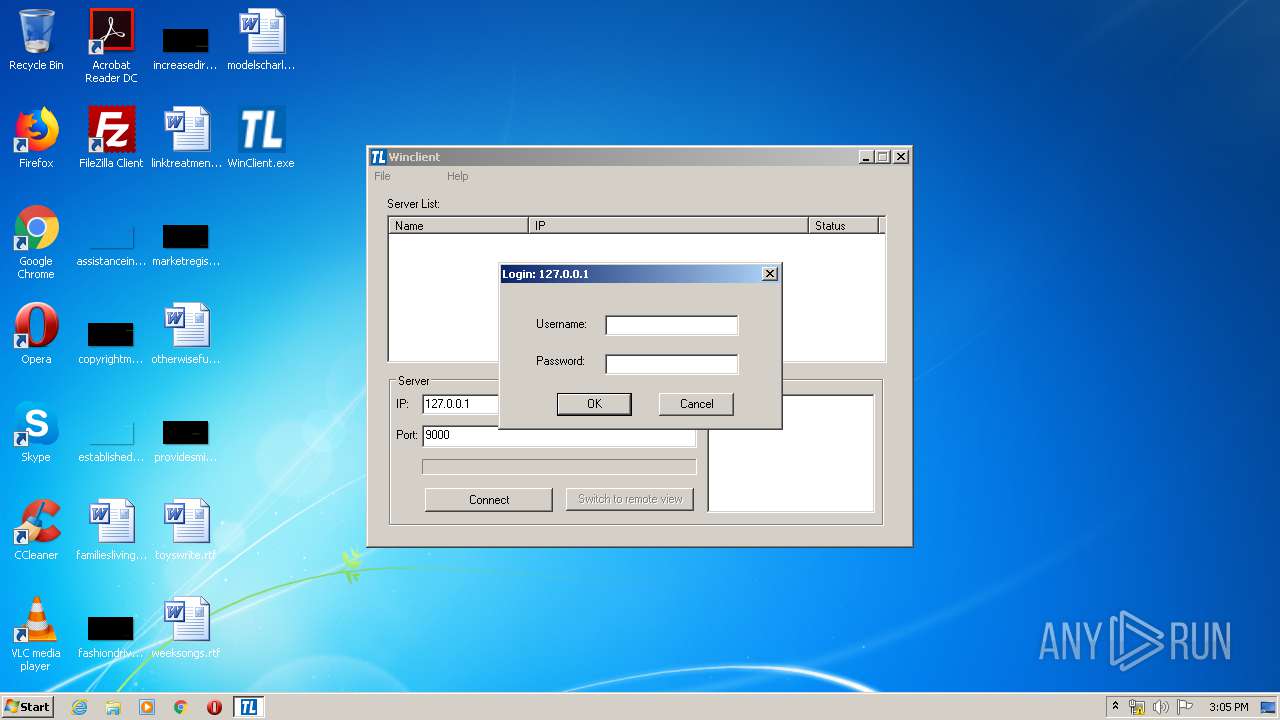
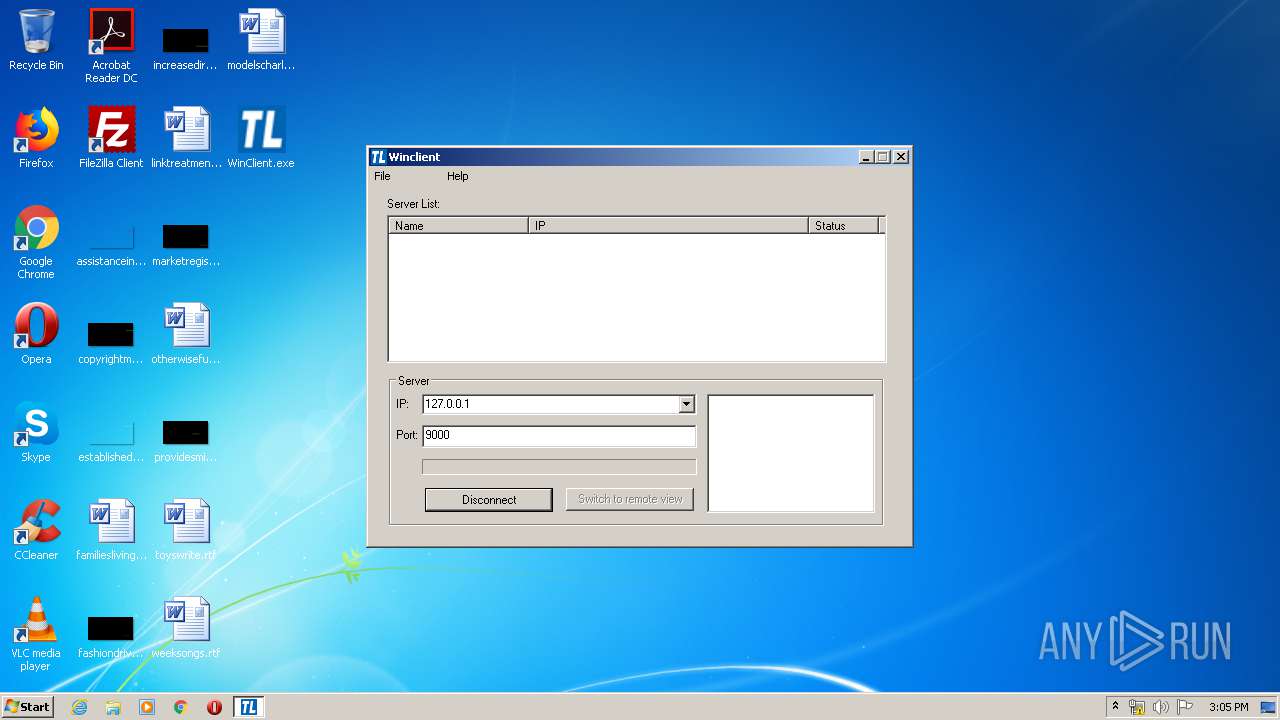
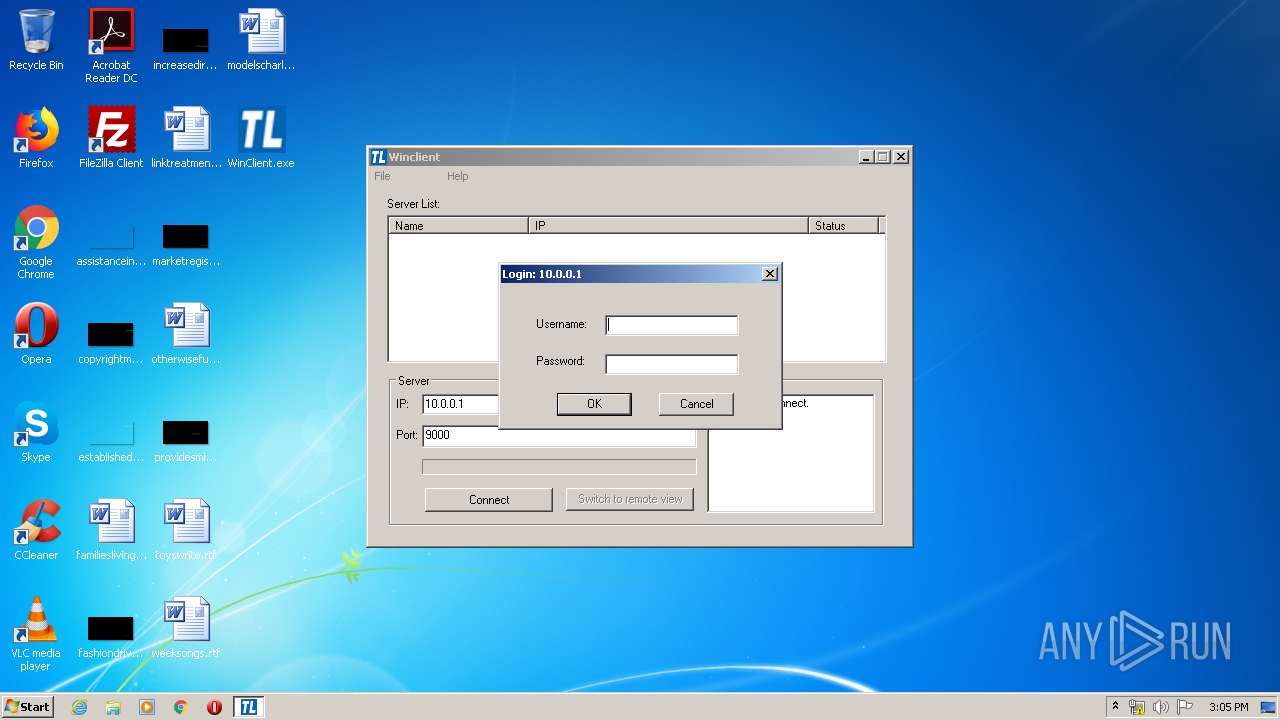
Connects to unusual port
- WinClient.exe (PID: 2868)
INFO
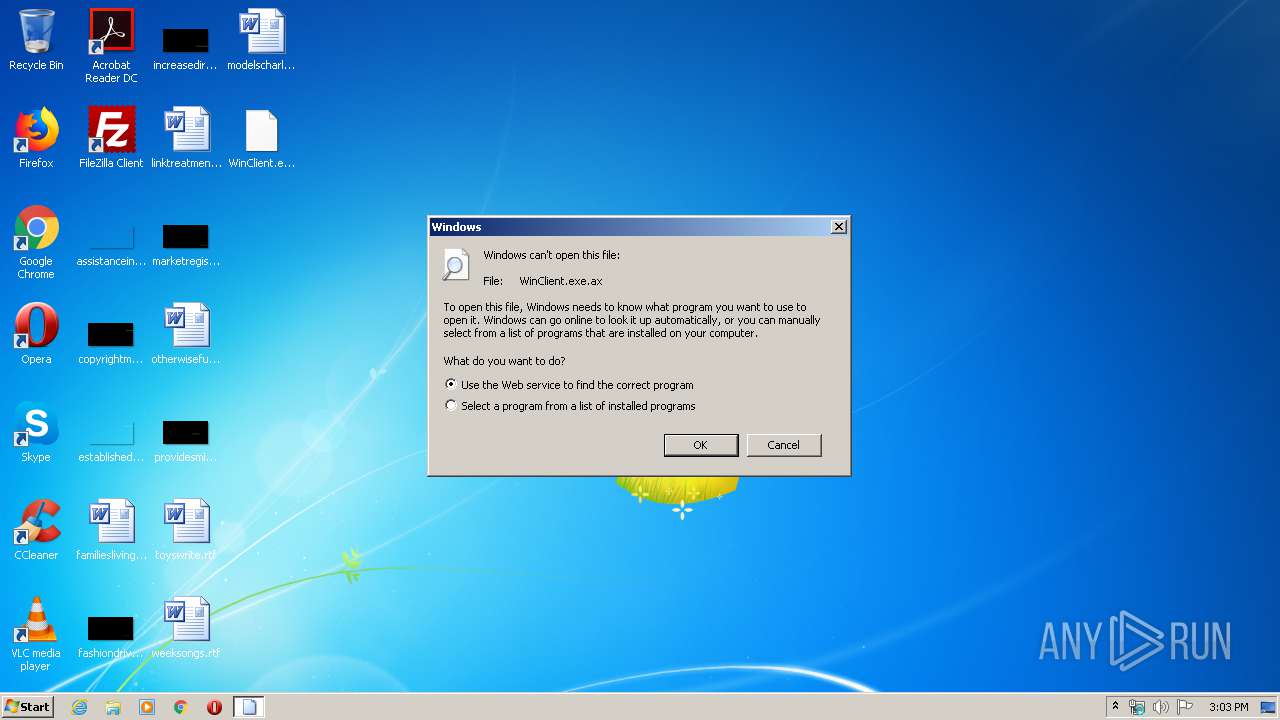
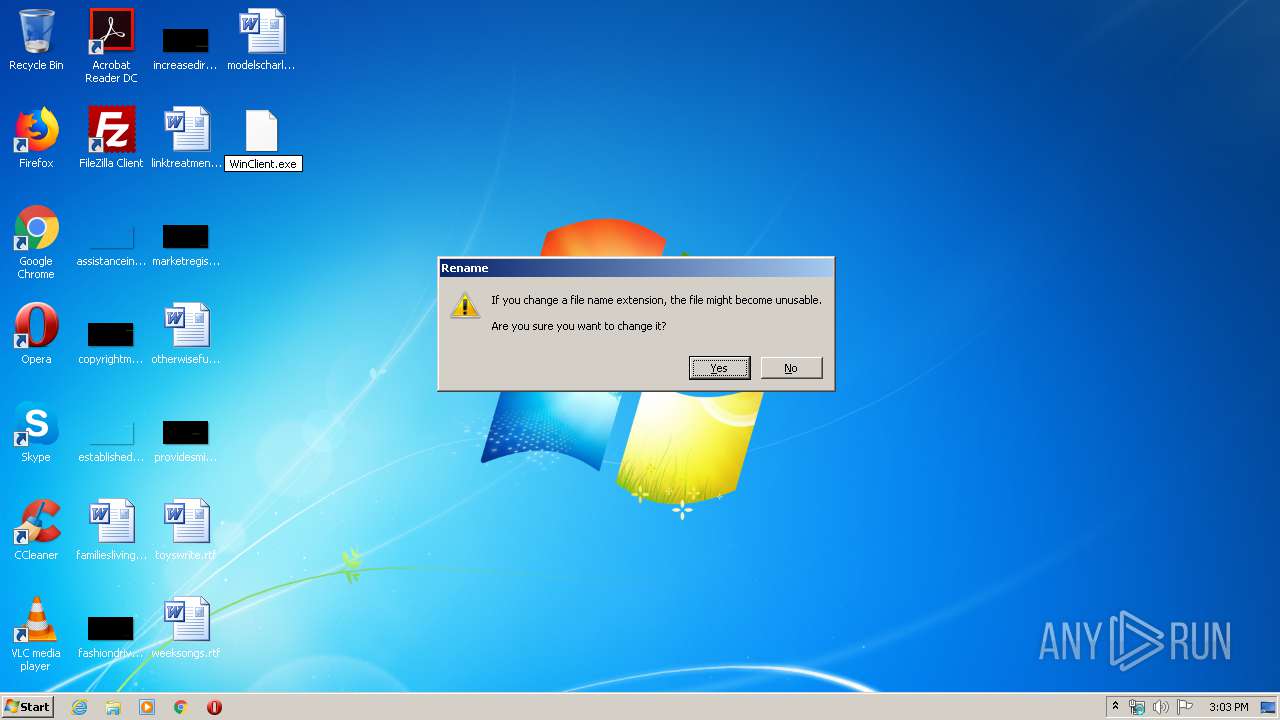
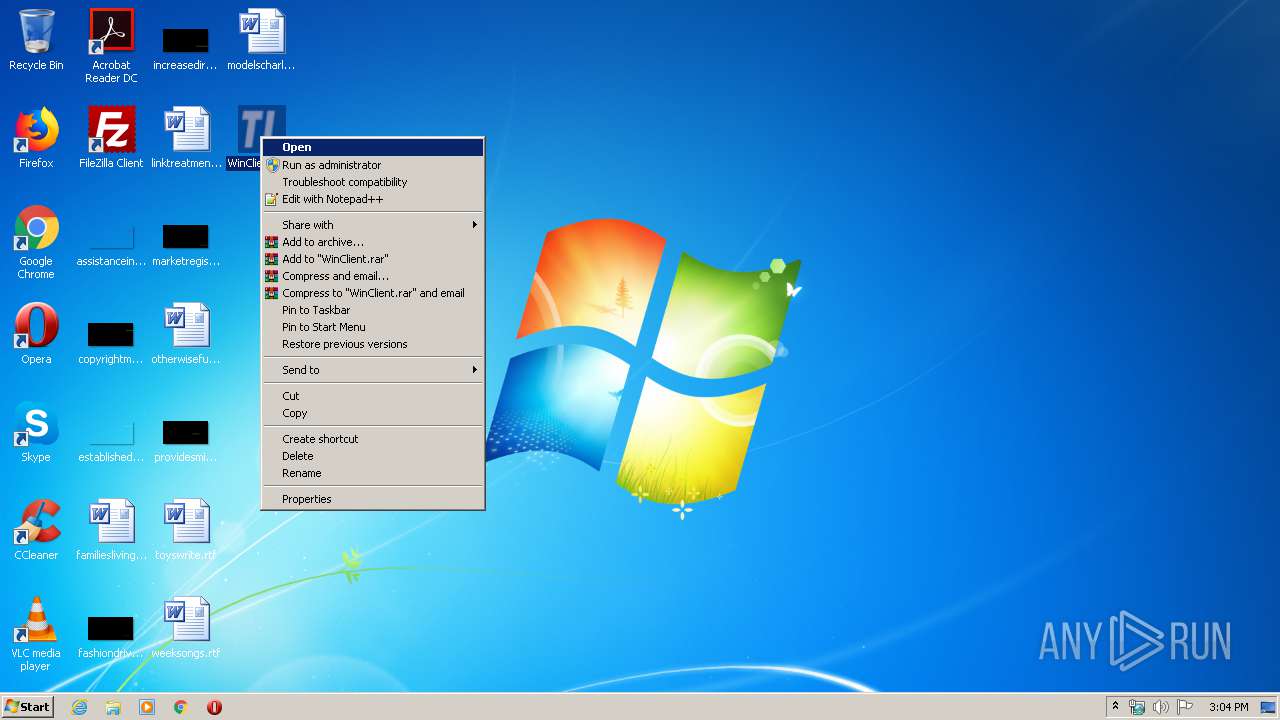
Manual execution by user
- WinClient.exe (PID: 780)
- WinClient.exe (PID: 2868)
- WinClient.exe (PID: 2132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ax | | | DirectShow filter (40.1) |
|---|---|---|
| .exe | | | InstallShield setup (8.5) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (6.2) |
| .exe | | | Win64 Executable (generic) (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:06:29 22:48:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x66af |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WinClient MFC Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | WinClient |
| LegalCopyright: | Copyright (C) 2008 |
| LegalTrademarks: | - |
| OriginalFileName: | WinClient.EXE |
| PrivateBuild: | - |
| ProductName: | WinClient Application |
| ProductVersion: | 1, 0, 0, 1 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jun-2017 20:48:55 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WinClient MFC Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | WinClient |
| LegalCopyright: | Copyright (C) 2008 |
| LegalTrademarks: | - |
| OriginalFilename: | WinClient.EXE |
| PrivateBuild: | - |
| ProductName: | WinClient Application |
| ProductVersion: | 1, 0, 0, 1 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 29-Jun-2017 20:48:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005CB5 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.74005 |
.rdata | 0x00007000 | 0x00001BCE | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39671 |
.data | 0x00009000 | 0x00000668 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.2564 |
.rsrc | 0x0000A000 | 0x00001058 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.5245 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.34256 | 860 | UNKNOWN | English - United States | RT_VERSION |
7 | 1.94432 | 70 | UNKNOWN | English - United States | RT_STRING |
100 | 3.37387 | 274 | UNKNOWN | English - United States | RT_DIALOG |
102 | 3.05807 | 292 | UNKNOWN | English - United States | RT_DIALOG |
145 | 1.81924 | 20 | UNKNOWN | English - Canada | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
MFC42.DLL |
MSVCRT.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
47
Monitored processes
8
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Users\admin\Desktop\WinClient.exe" | C:\Users\admin\Desktop\WinClient.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: WinClient MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\Desktop\WinClient.exe" | C:\Users\admin\Desktop\WinClient.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WinClient MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2380 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\WinClient.exe.ax | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2708 | Regsvr32 /s WinClient36.ocx | C:\Windows\system32\Regsvr32.exe | — | WinClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2868 | "C:\Users\admin\Desktop\WinClient.exe" | C:\Users\admin\Desktop\WinClient.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: WinClient MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3492 | Regsvr32 /s WinClient36.ocx | C:\Windows\system32\Regsvr32.exe | — | WinClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3548 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3732 | Regsvr32 /s WinClient36.ocx | C:\Windows\system32\Regsvr32.exe | — | WinClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
405
Read events
365
Write events
40
Delete events
0
Modification events
| (PID) Process: | (780) WinClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Tripplite\Viewer4141 |
| Operation: | write | Name: | Filename |
Value: C:\Users\admin\Desktop\WinClient.exe | |||
| (PID) Process: | (2868) WinClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Tripplite\Viewer4141 |
| Operation: | write | Name: | Filename |
Value: C:\Users\admin\Desktop\WinClient.exe | |||
| (PID) Process: | (3492) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{54E39DC2-5EDD-40D2-ACCD-EEAAE3D9A61F}\1.0 |
| Operation: | write | Name: | |
Value: WinClient ActiveX Control module | |||
| (PID) Process: | (3492) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{54E39DC2-5EDD-40D2-ACCD-EEAAE3D9A61F}\1.0\FLAGS |
| Operation: | write | Name: | |
Value: 2 | |||
| (PID) Process: | (3492) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{54E39DC2-5EDD-40D2-ACCD-EEAAE3D9A61F}\1.0\0\win32 |
| Operation: | write | Name: | |
Value: C:\Users\admin\TEMP\WinClient36.ocx | |||
| (PID) Process: | (3492) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{54E39DC2-5EDD-40D2-ACCD-EEAAE3D9A61F}\1.0\HELPDIR |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (3492) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{4FE0D5E8-3FED-4D01-826F-86EE44339493} |
| Operation: | write | Name: | |
Value: _DWinClient | |||
| (PID) Process: | (3492) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{4FE0D5E8-3FED-4D01-826F-86EE44339493}\ProxyStubClsid |
| Operation: | write | Name: | |
Value: {00020420-0000-0000-C000-000000000046} | |||
| (PID) Process: | (3492) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{4FE0D5E8-3FED-4D01-826F-86EE44339493}\ProxyStubClsid32 |
| Operation: | write | Name: | |
Value: {00020420-0000-0000-C000-000000000046} | |||
| (PID) Process: | (3492) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{4FE0D5E8-3FED-4D01-826F-86EE44339493}\TypeLib |
| Operation: | write | Name: | |
Value: {54E39DC2-5EDD-40D2-ACCD-EEAAE3D9A61F} | |||
Executable files
5
Suspicious files
0
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2868 | WinClient.exe | C:\Users\admin\AppData\Local\Temp\virtualkey.sys | executable | |
MD5:55FE14D5FAC006D0F602C77D7F2A6FFF | SHA256:456C70E5EDE99232F3E92D58846003096BD7C59E29359D726304846A04796FB0 | |||
| 2868 | WinClient.exe | C:\USERS\ADMIN\TEMP\DEFAULT.INI | text | |
MD5:— | SHA256:— | |||
| 2868 | WinClient.exe | C:\Users\admin\AppData\Local\Temp\virtualkey_amd64.sys | executable | |
MD5:C3C0D165A3D28951CF04B66B28BED0E8 | SHA256:105D5B2EE896615466B6B993D3CE84810541051378FCCEC66C261A914D8E531D | |||
| 2868 | WinClient.exe | C:\Users\admin\AppData\Local\Temp\testinstall64.exe | executable | |
MD5:C2F27D9E8ED8D6D5D5F2E0BDE1B15534 | SHA256:4D7AB0A6B22F463B0873645A7FB76D7842A7540C1F4519122E64C8CB25DC1616 | |||
| 2868 | WinClient.exe | C:\Users\admin\AppData\Local\Temp\testinstall.exe | executable | |
MD5:1385552E2DA7FA090750E667114301DA | SHA256:DC249FC95D8B4007C8203990CA56F30E0210FEF53FF88F96987CD51D2D799047 | |||
| 780 | WinClient.exe | C:\Users\admin\TEMP\WinClient36.ocx | executable | |
MD5:938D7409ADE0044A86FE95A1A0F78A69 | SHA256:4B908237C83F125ABE78C8DD22EAFA4FC346D01C8DD563995F891E4E9CF5C16D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2868 | WinClient.exe | 10.0.0.1:9000 | — | — | — | unknown |
DNS requests
Threats
Process | Message |
|---|---|
WinClient.exe | **InitAll...........1
|
WinClient.exe | **InitAll...........8
|
WinClient.exe | **InitAll...........
|
WinClient.exe | **InitAll...........3
|
WinClient.exe | **InitAll...........5
|
WinClient.exe | **InitAll...........7
|
WinClient.exe | **InitAll...........4
|
WinClient.exe | **InitAll...........6
|
WinClient.exe | **InitAll...........9
|
WinClient.exe | **InitAll...........10
|