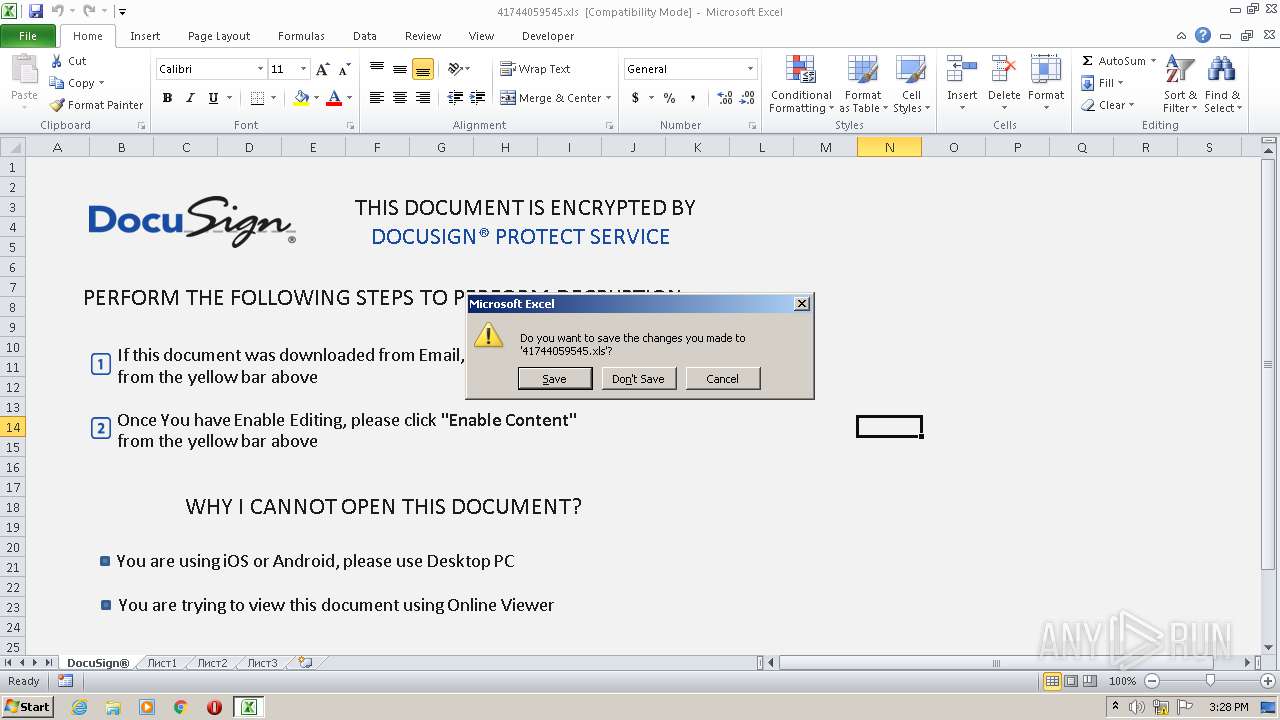
| File name: | 41744059545.xls |
| Full analysis: | https://app.any.run/tasks/e8db4d66-86d4-4acf-8ed9-1cdf0f81be77 |
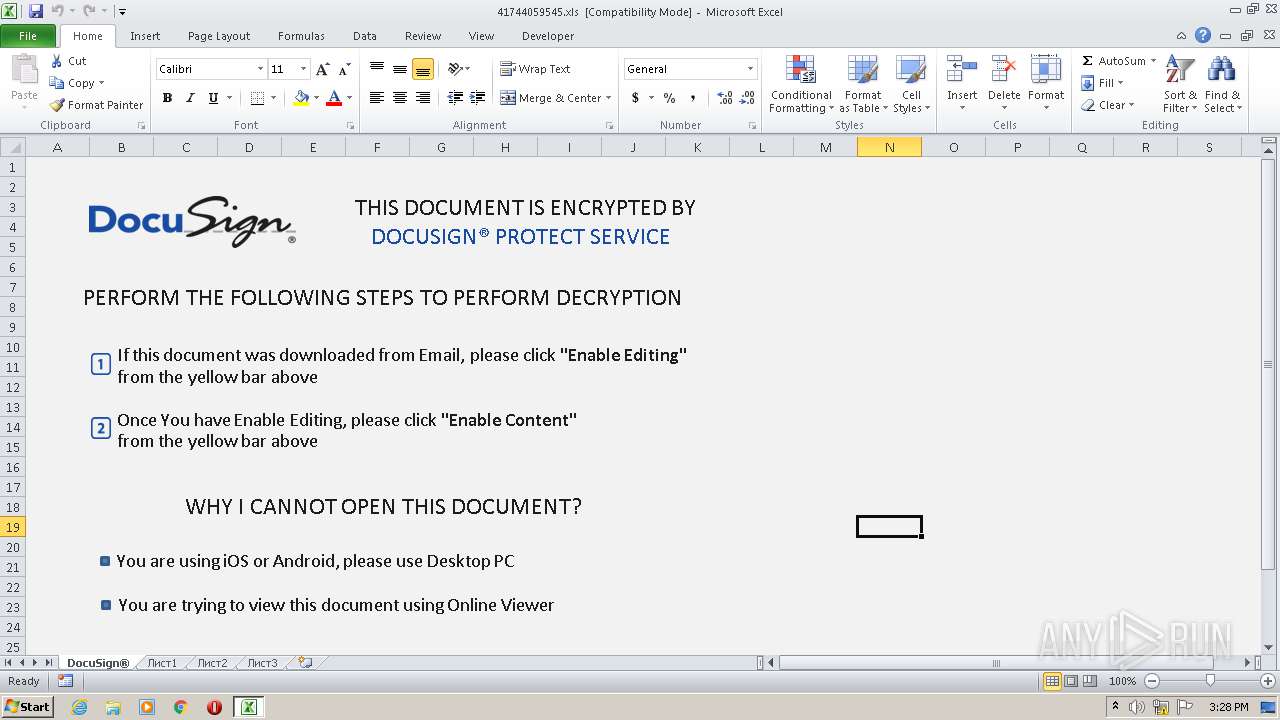
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 14:28:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1251, Name of Creating Application: Microsoft Excel, Create Time/Date: Sat Sep 16 01:00:00 2006, Last Saved Time/Date: Tue Sep 29 12:38:08 2020, Security: 0 |
| MD5: | AB5A3DD9C396AEEA7B5E7998B37B9228 |
| SHA1: | 923E10A21D356A5E1131C77B94B34E0BAD0D0876 |
| SHA256: | 12E22A6A2217770CF1D22DBAA6B157156DFB0219D710E79C98987D1AAA248B79 |
| SSDEEP: | 1536:j/7uDphYHceXVhca+fMHLtyeGxcl8/dguD6yzsFyBCKM11AI:j/7uDphYHceXVhca+fMHLtyeGxcl8/d2 |
MALICIOUS
Drops known malicious document
- EXCEL.EXE (PID: 896)
SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- EXCEL.EXE (PID: 896)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 896)
- WINWORD.EXE (PID: 1912)
- WINWORD.EXE (PID: 2800)
Manual execution by user
- WINWORD.EXE (PID: 1912)
- WINWORD.EXE (PID: 2800)
Creates files in the user directory
- EXCEL.EXE (PID: 896)
- WINWORD.EXE (PID: 1912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Software: | Microsoft Excel |
| CreateDate: | 2006:09:16 00:00:00 |
| ModifyDate: | 2020:09:29 11:38:08 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\returncontrol.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\rapellc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 044
Read events
1 625
Write events
252
Delete events
167
Modification events
| (PID) Process: | (896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 3{% |
Value: 337B250080030000010000000000000000000000 | |||
| (PID) Process: | (896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (896) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
4
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 896 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRAB93.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 896 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF179C3E6120E68012.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | EXCEL.EXE | C:\Users\admin\Desktop\453B1000 | — | |
MD5:— | SHA256:— | |||
| 896 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFC2C612C99B81B704.TMP | — | |
MD5:— | SHA256:— | |||
| 1912 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6E47.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1912 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{208174EA-76A5-4866-9FEF-69E7CE93BC4B}.tmp | — | |
MD5:— | SHA256:— | |||
| 1912 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{1BB8B145-8B06-430C-B5D0-14C8821AB10D}.tmp | — | |
MD5:— | SHA256:— | |||
| 1912 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{59E55E3F-5882-4C1F-AF61-4E1881BF3527}.tmp | — | |
MD5:— | SHA256:— | |||
| 2800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8DC5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 896 | EXCEL.EXE | C:\Users\admin\Desktop\F045B3BB.tmp | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
896 | EXCEL.EXE | GET | — | 200.73.116.32:80 | http://www.avaluocomercial.cl/zfalbrcb/88888.png | CL | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
896 | EXCEL.EXE | 200.73.116.32:80 | www.avaluocomercial.cl | POWER HOST E.I.R.L. | CL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.avaluocomercial.cl |
| unknown |