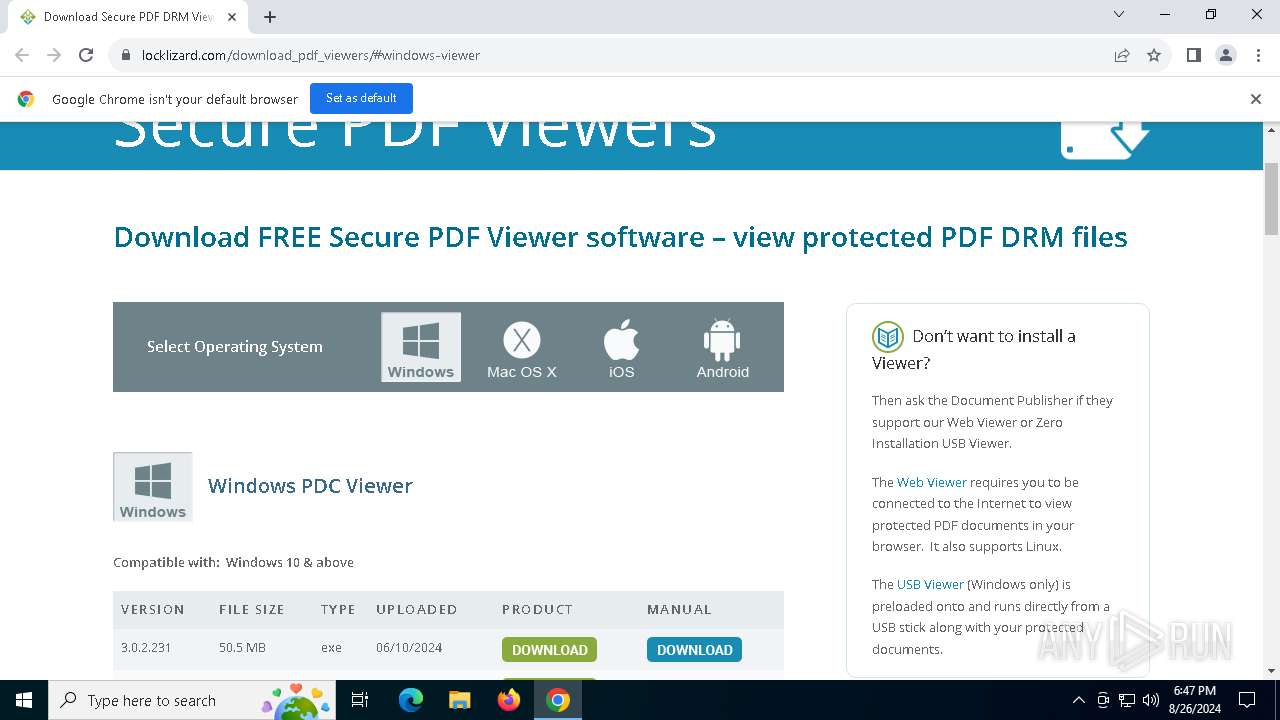
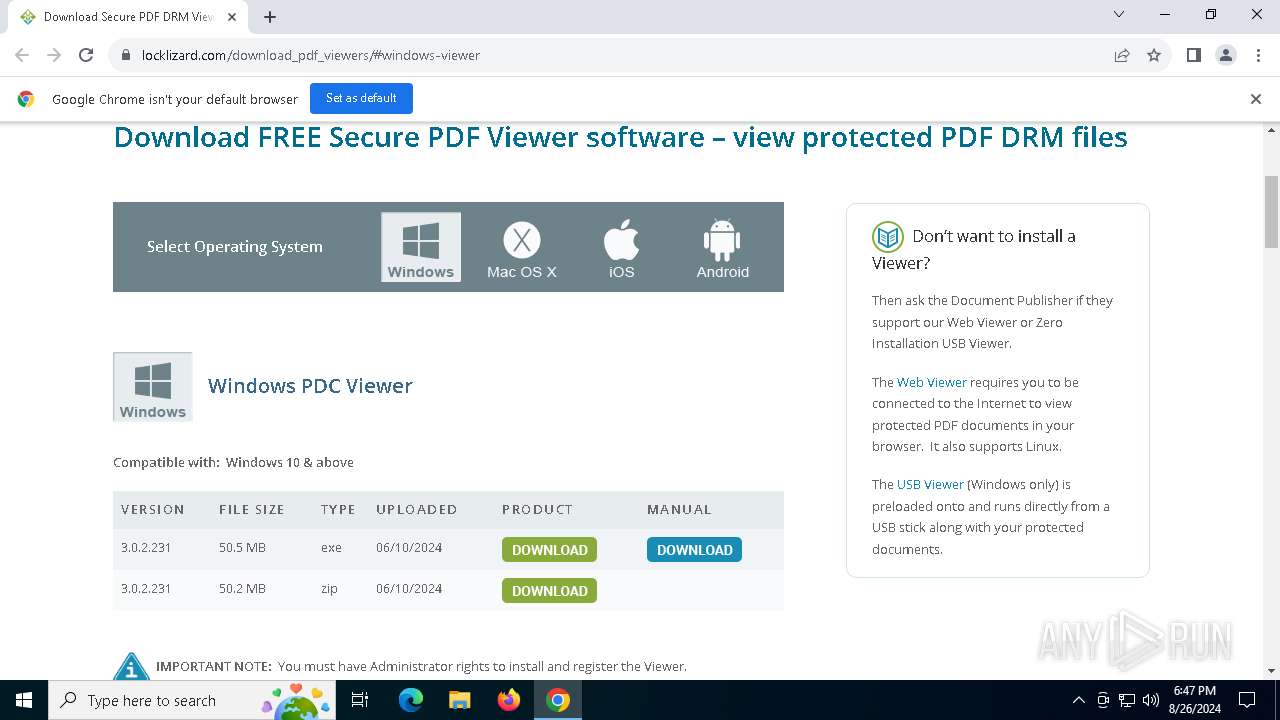
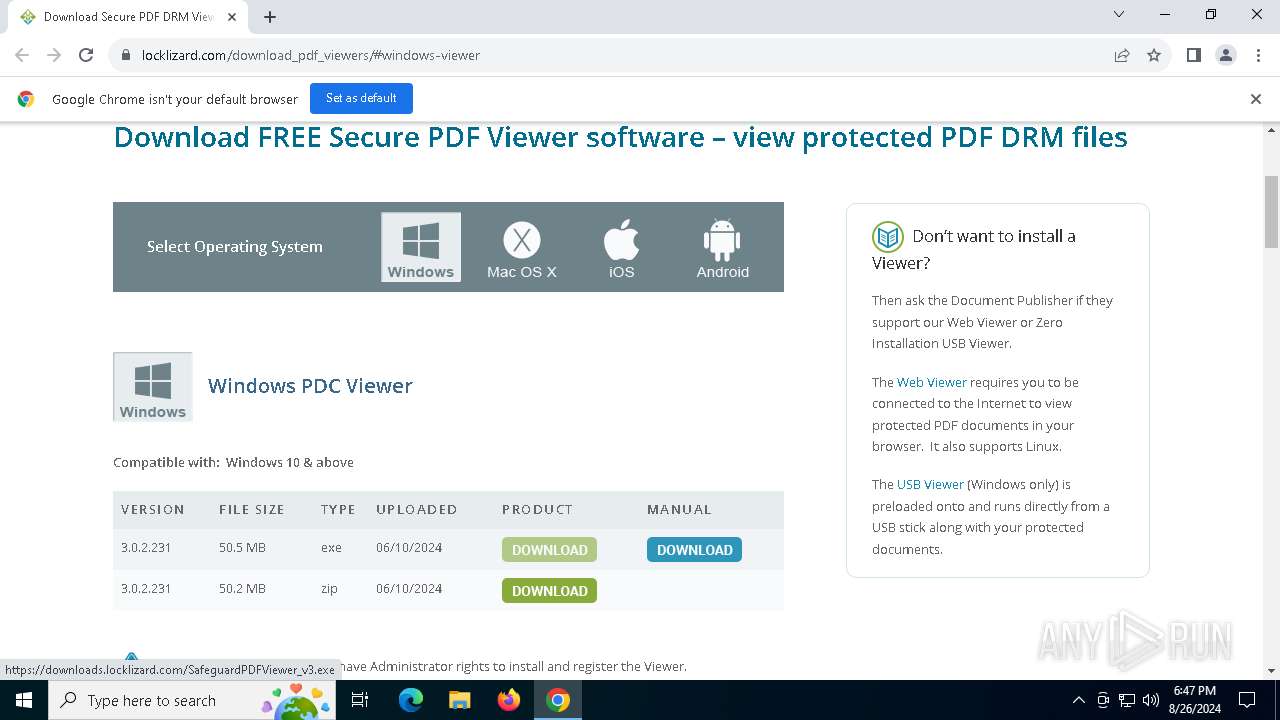
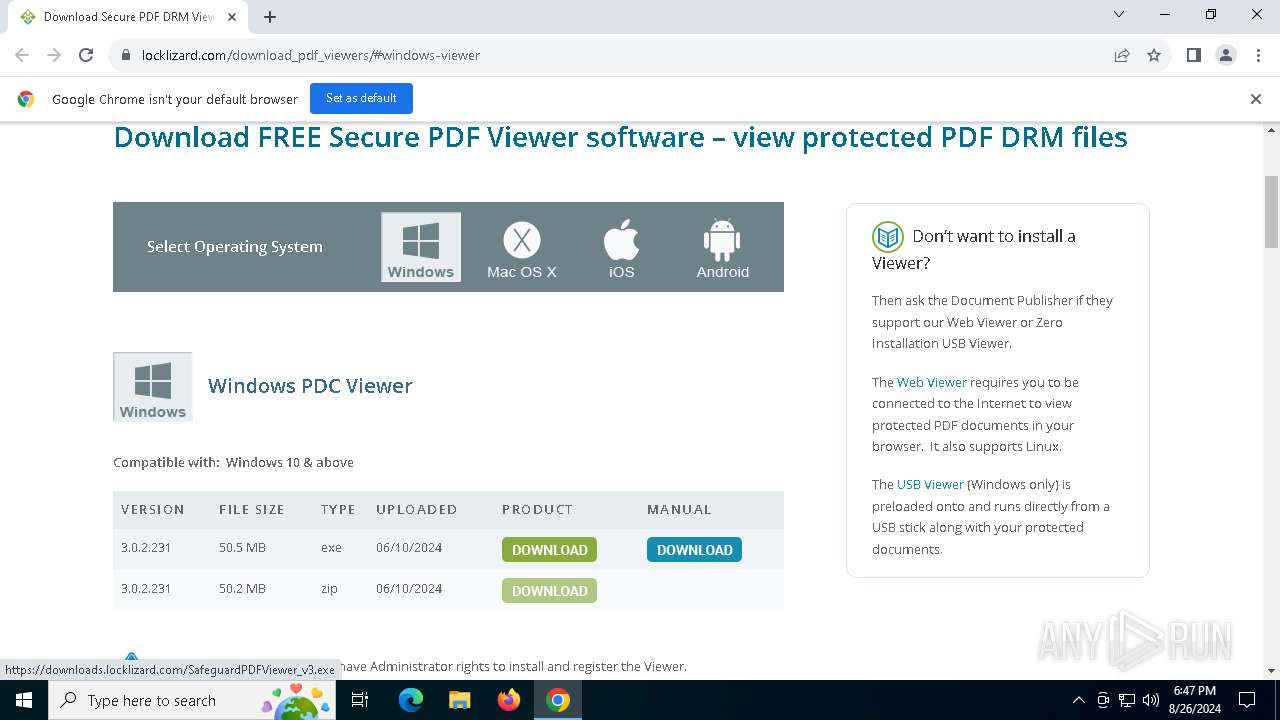
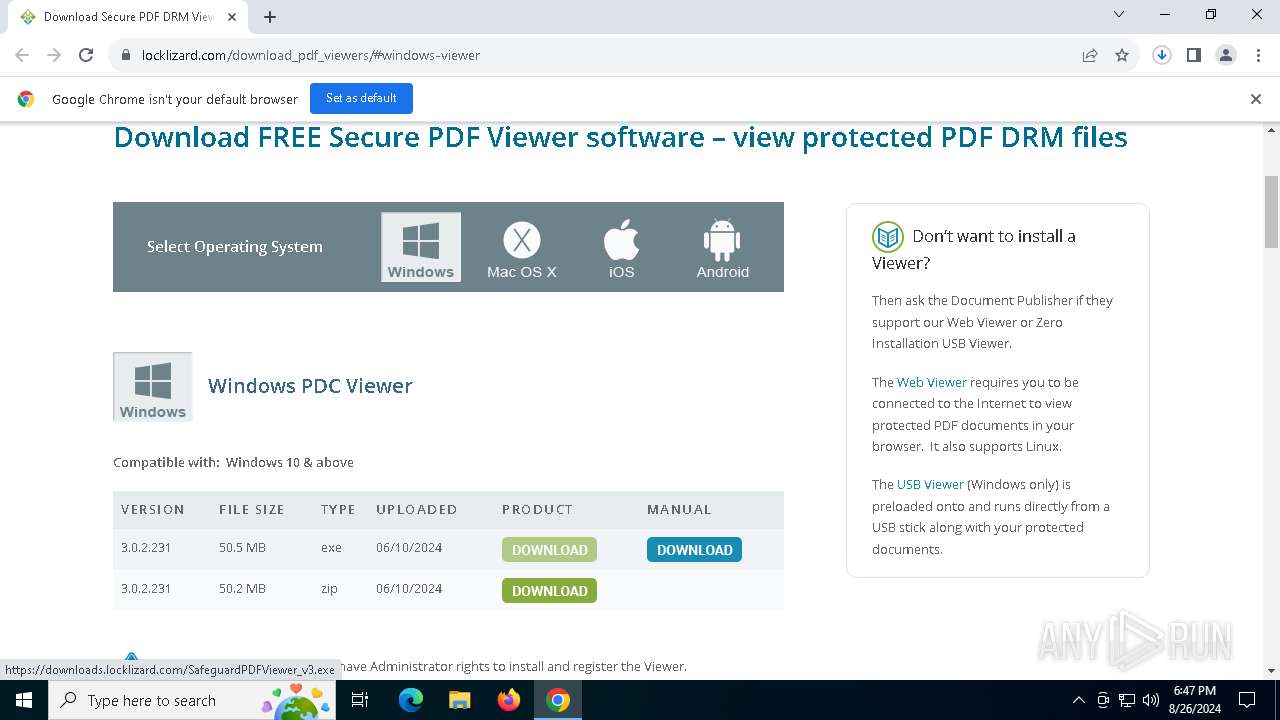
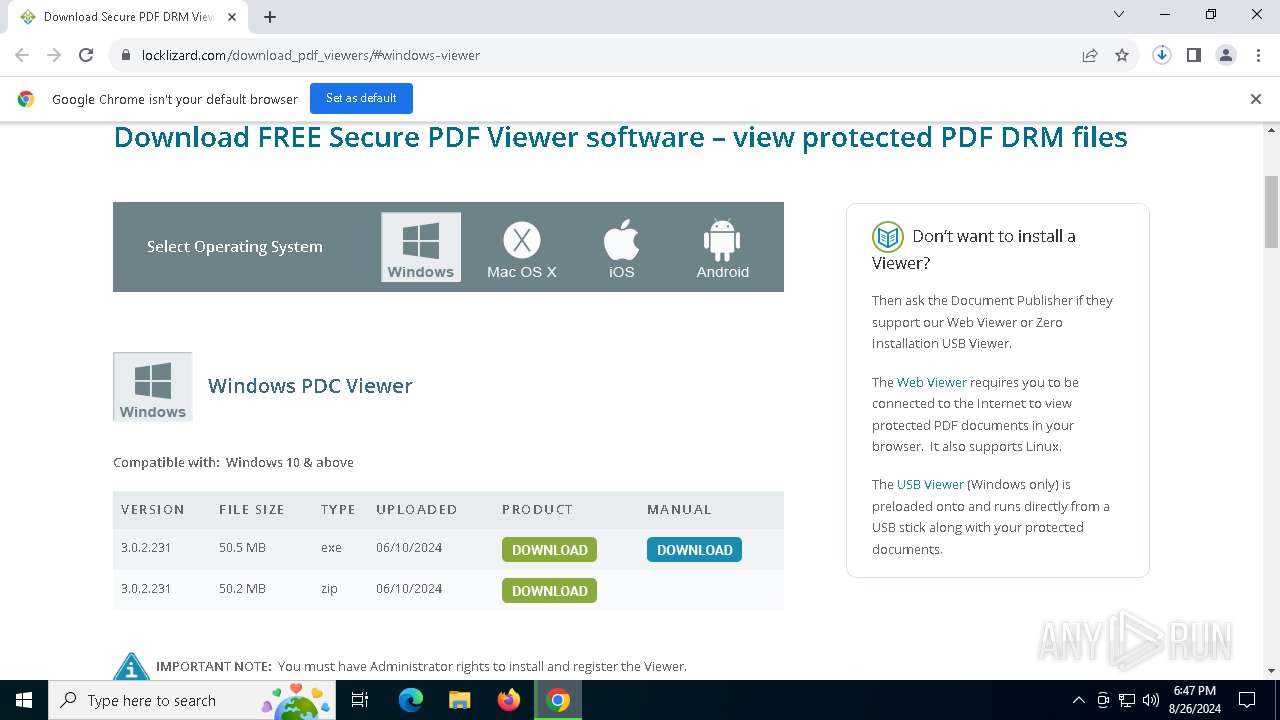
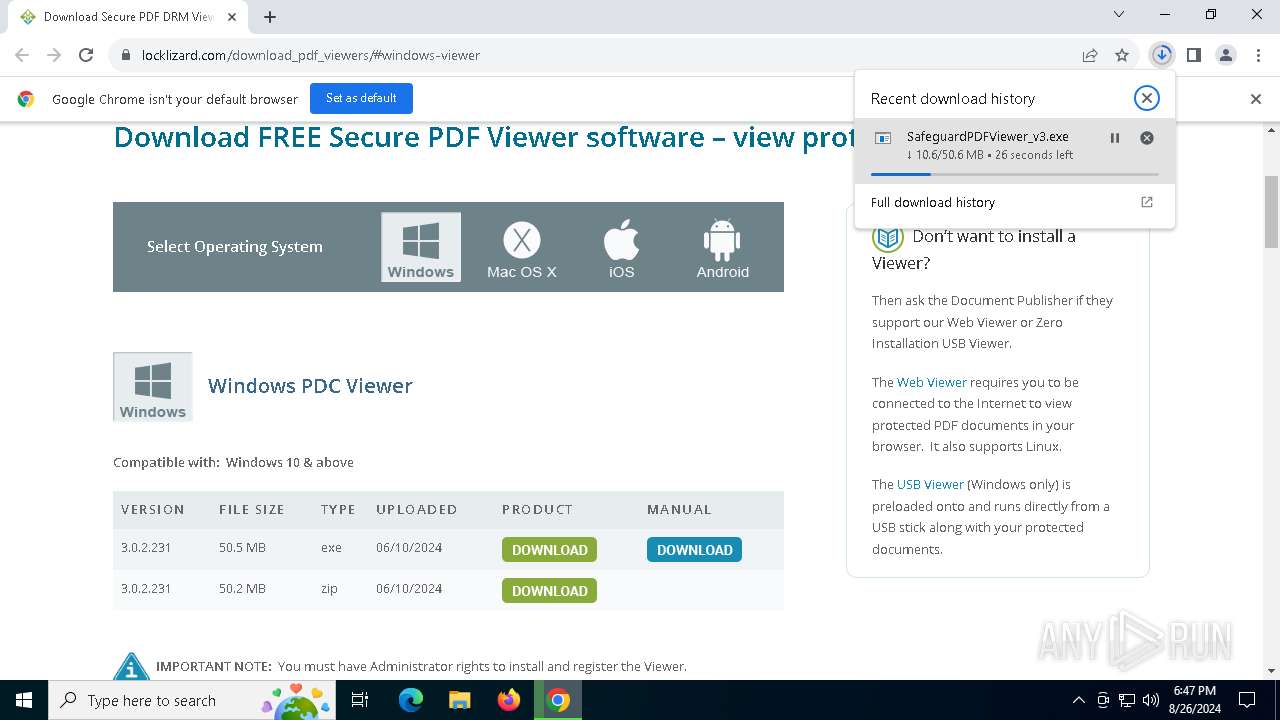
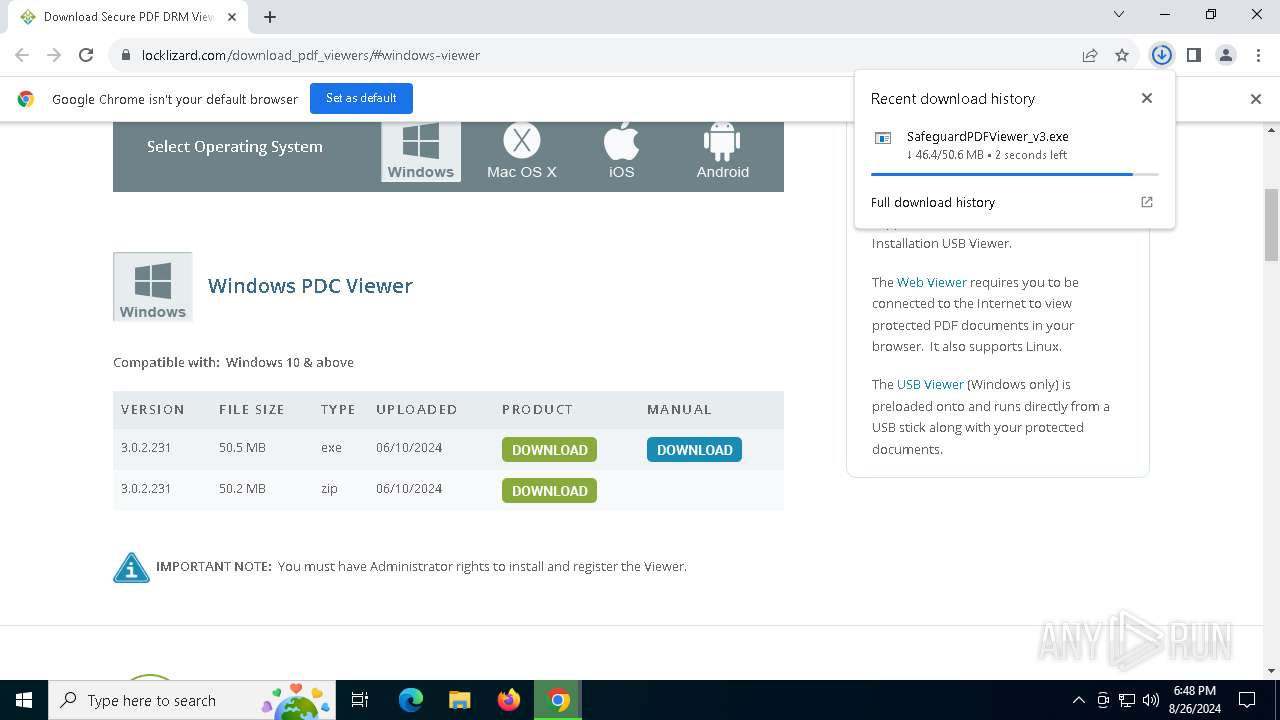
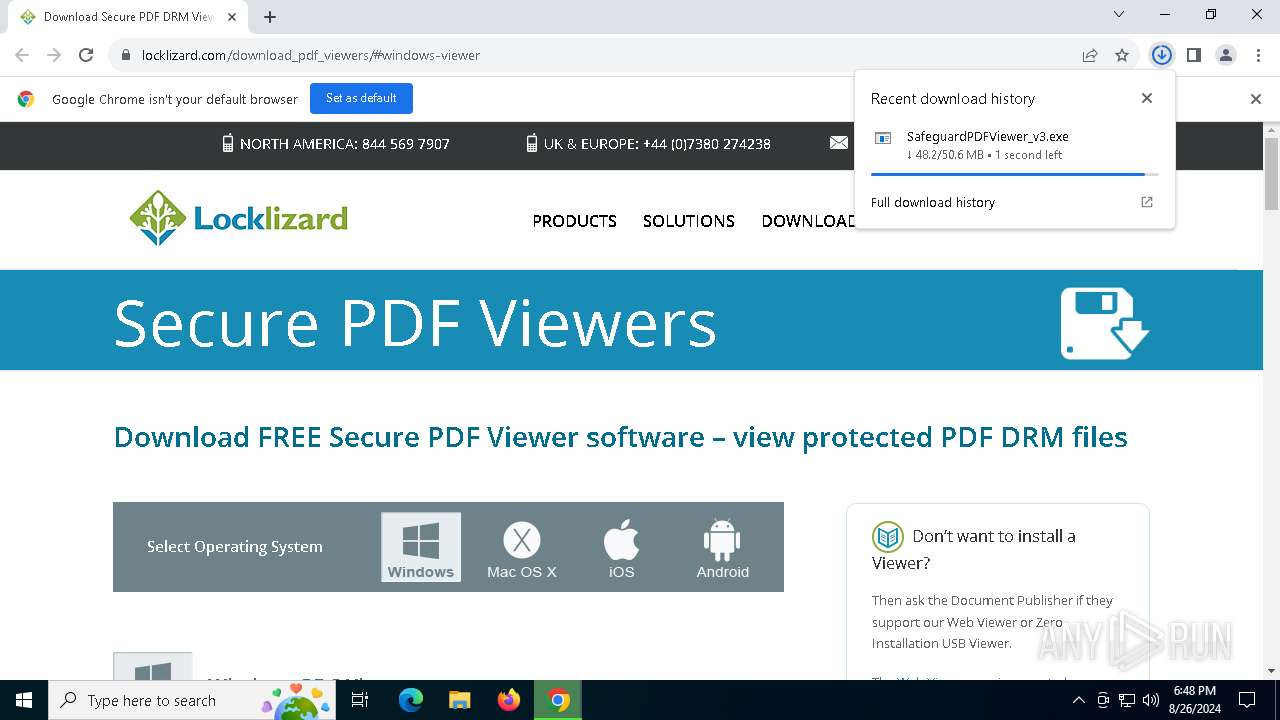
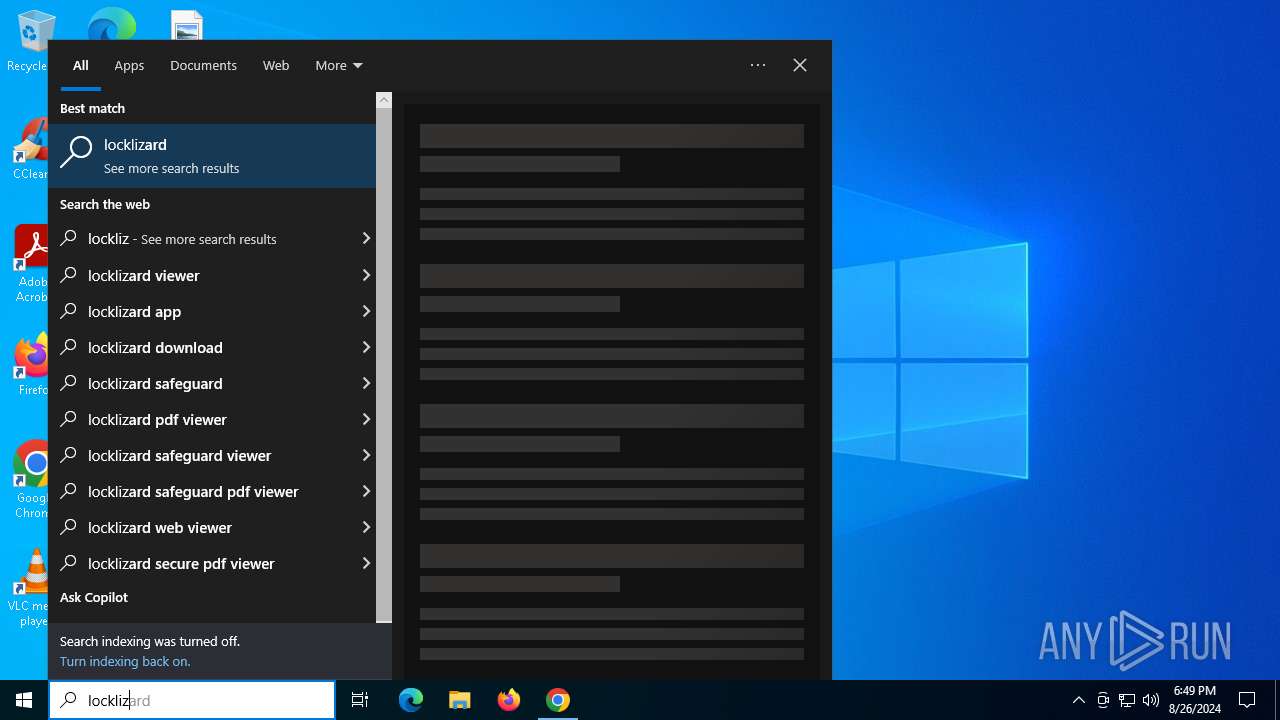
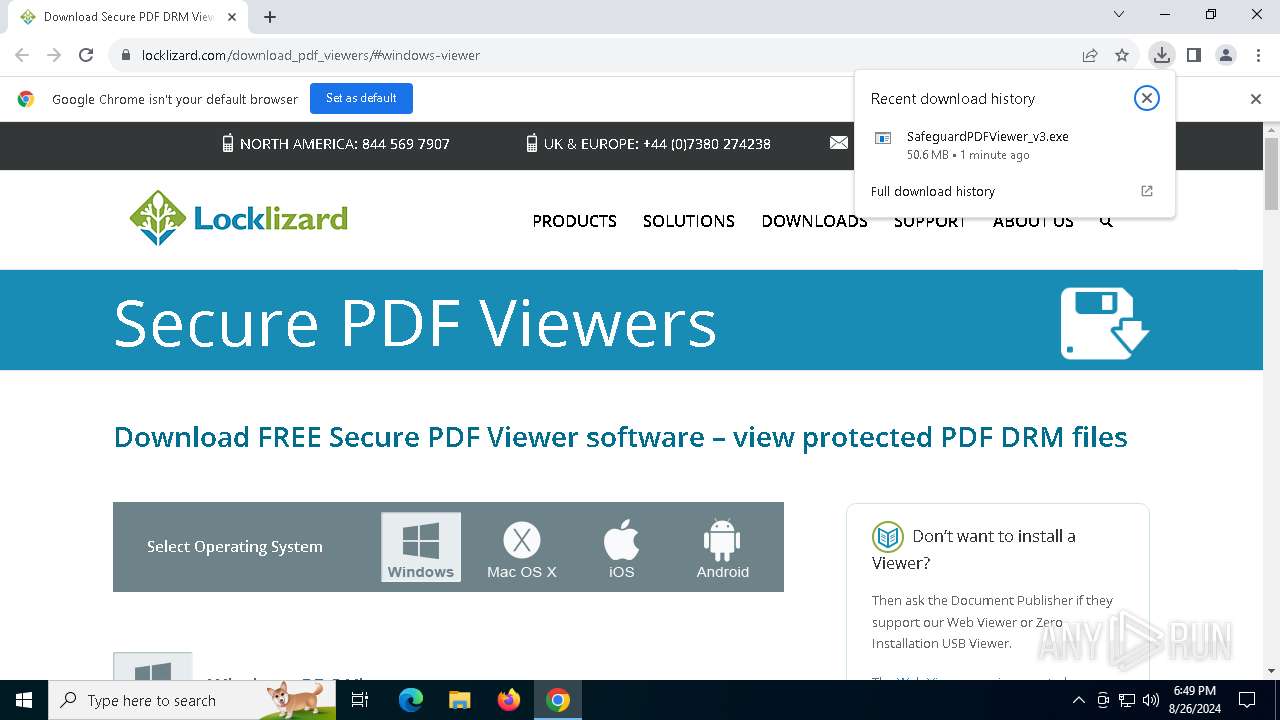
| URL: | https://www.locklizard.com/download_pdf_viewers/#windows-viewer |
| Full analysis: | https://app.any.run/tasks/184467ae-c9e5-44fe-9673-2e4f80055e76 |
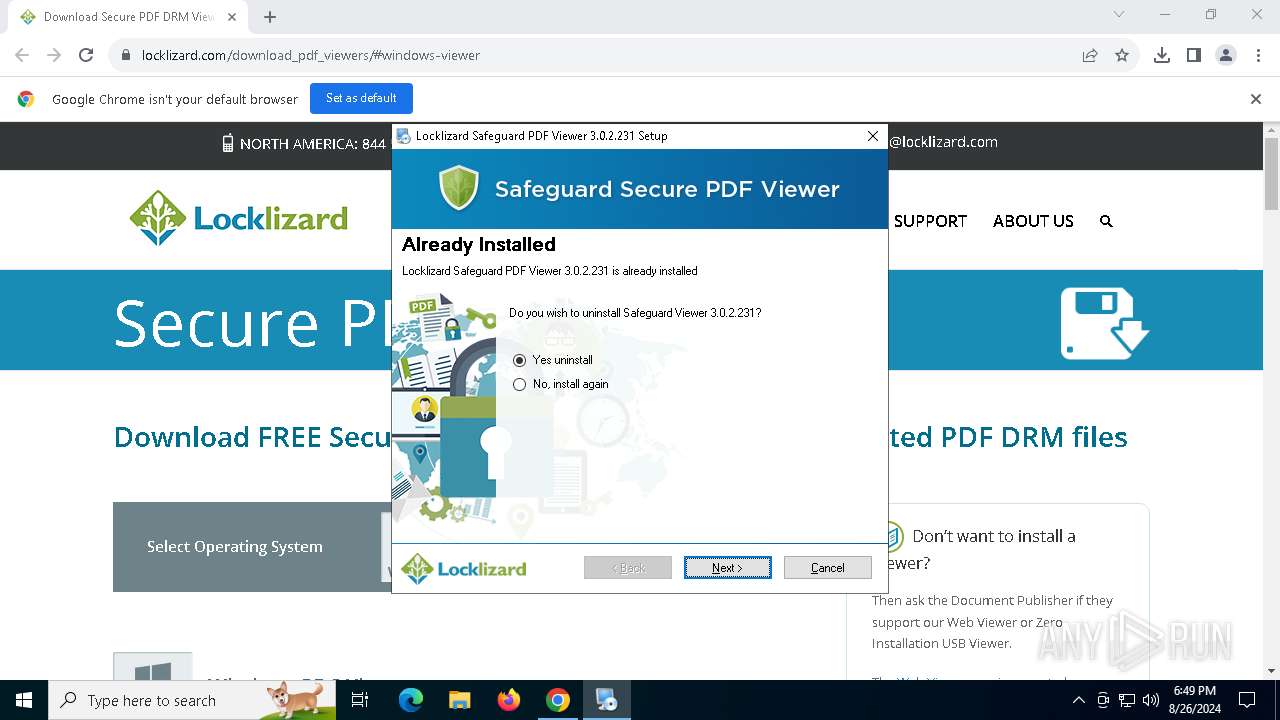
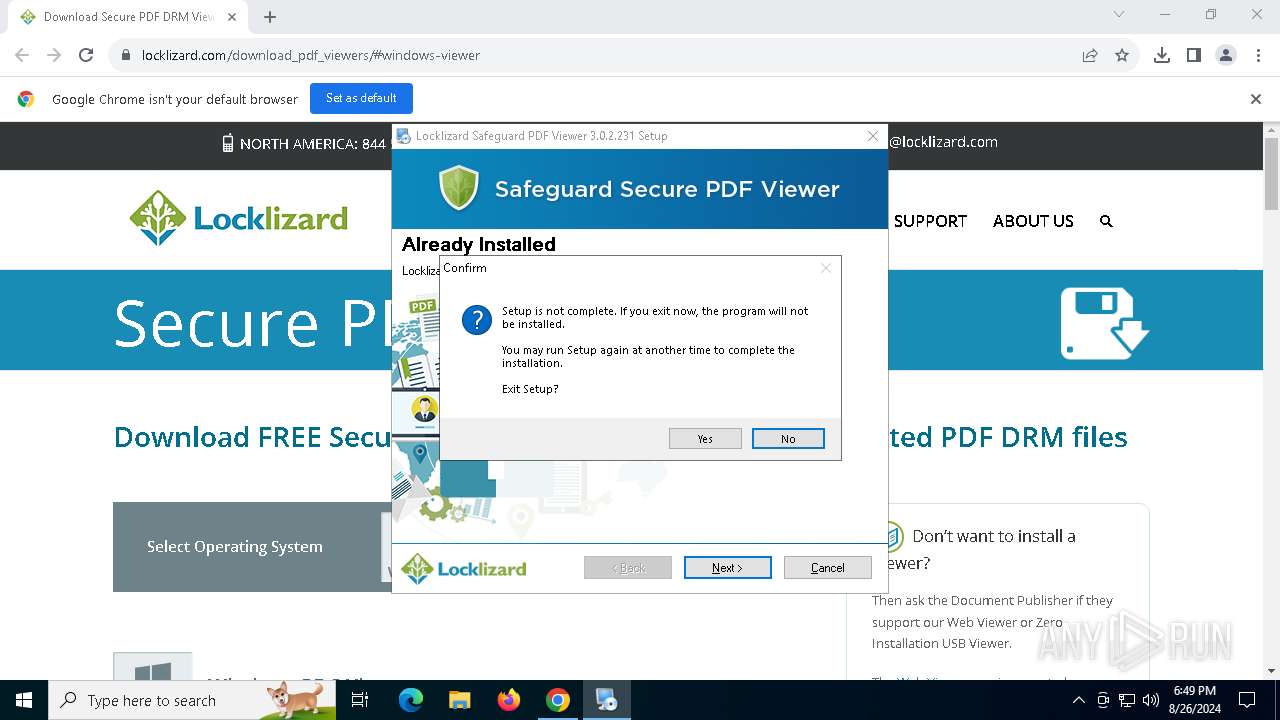
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2024, 18:47:29 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C82FCBA8D3627DF3420387903D7AF3EE |
| SHA1: | 3FCC13E5837F7414841ABD6417F8CB7E465F9D96 |
| SHA256: | 12D75F66A4B5A33669964F4A4163A352E7EFAE427088922809BBD65EFE99B635 |
| SSDEEP: | 3:N8DSLWJMmm7oJdGdCASAXn:2OLW6ZA3y |
MALICIOUS
No malicious indicators.SUSPICIOUS
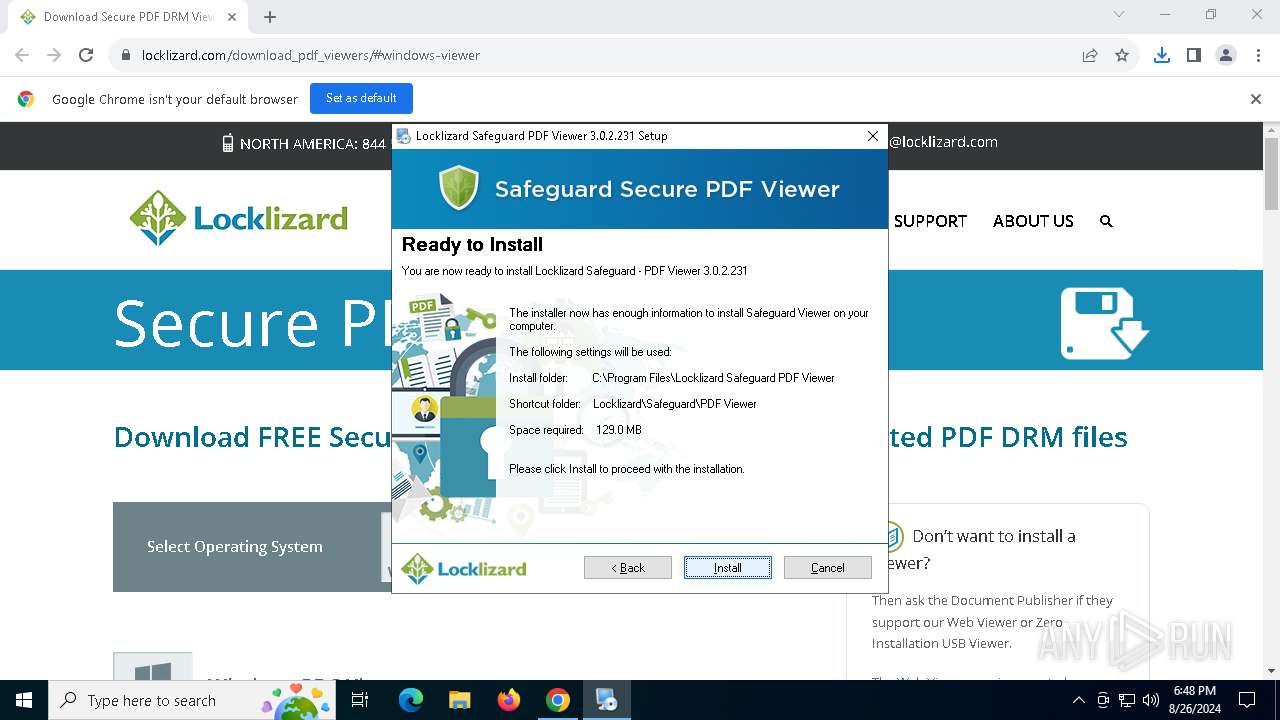
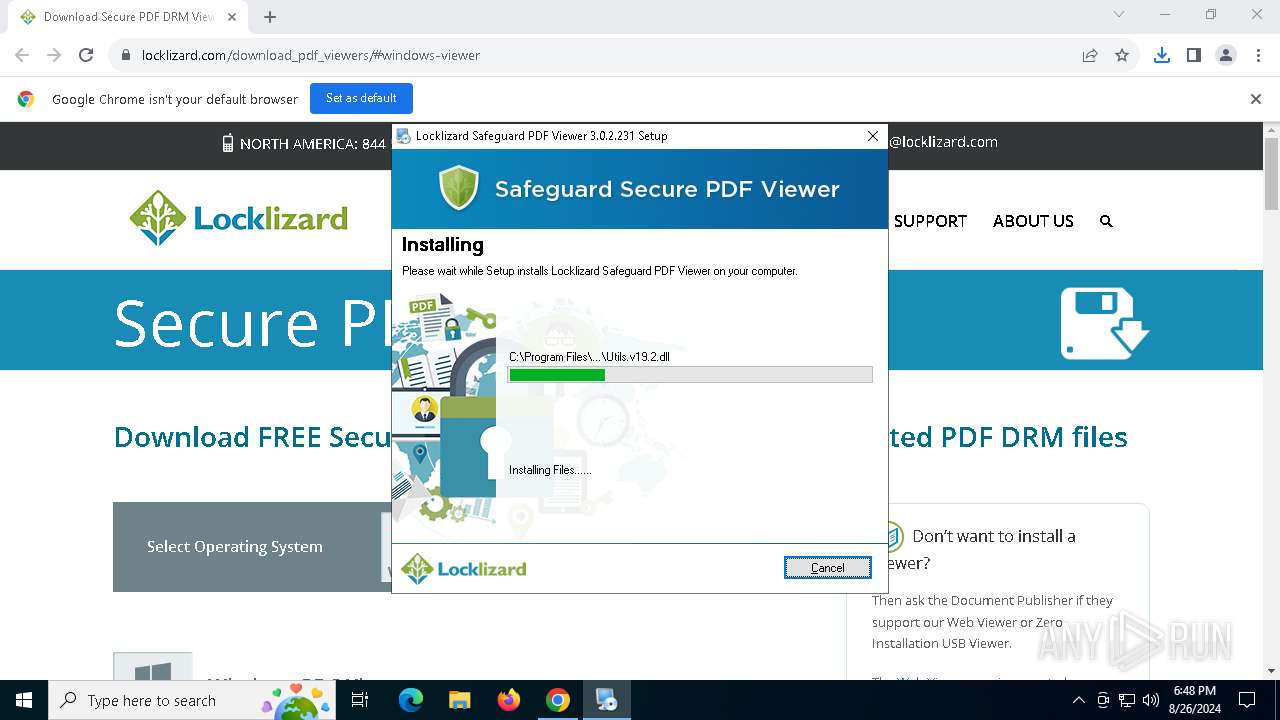
Executable content was dropped or overwritten
- SafeguardPDFViewer_v3.exe (PID: 2892)
- irsetup.exe (PID: 4392)
- SafeguardPDFViewer_v3.exe (PID: 3708)
- irsetup.exe (PID: 6320)
Drops the executable file immediately after the start
- SafeguardPDFViewer_v3.exe (PID: 2892)
- irsetup.exe (PID: 4392)
- SafeguardPDFViewer_v3.exe (PID: 3708)
- irsetup.exe (PID: 6320)
Reads security settings of Internet Explorer
- SafeguardPDFViewer_v3.exe (PID: 2892)
- irsetup.exe (PID: 4392)
- RegAsm.exe (PID: 1332)
- SafeguardPDFViewer_v3.exe (PID: 3708)
Reads the date of Windows installation
- SafeguardPDFViewer_v3.exe (PID: 2892)
- SafeguardPDFViewer_v3.exe (PID: 3708)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 4392)
- irsetup.exe (PID: 6320)
Reads Microsoft Outlook installation path
- irsetup.exe (PID: 4392)
Reads Internet Explorer settings
- irsetup.exe (PID: 4392)
The process creates files with name similar to system file names
- irsetup.exe (PID: 4392)
Reads the BIOS version
- PDCViewer64.exe (PID: 5656)
Creates/Modifies COM task schedule object
- RegAsm.exe (PID: 1332)
- PDCViewer64.exe (PID: 5656)
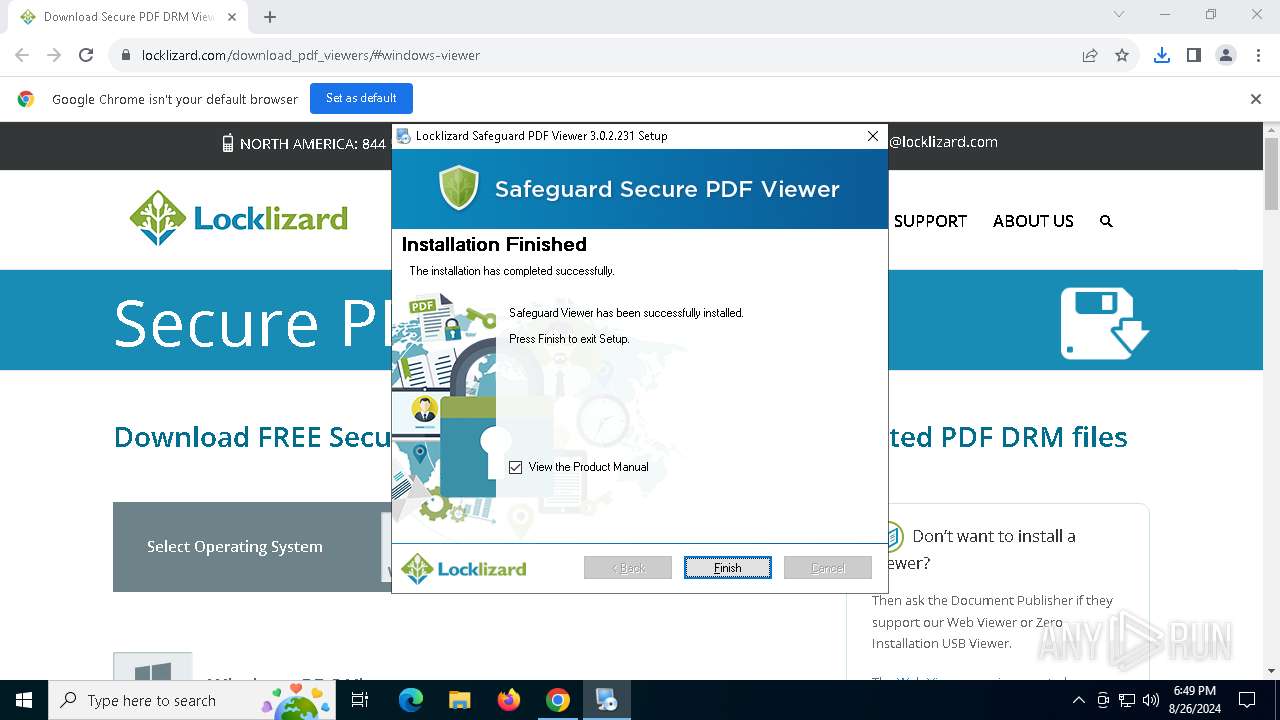
Creates a software uninstall entry
- irsetup.exe (PID: 4392)
Searches for installed software
- irsetup.exe (PID: 6320)
INFO
Application launched itself
- chrome.exe (PID: 4440)
Checks supported languages
- SafeguardPDFViewer_v3.exe (PID: 2892)
- irsetup.exe (PID: 4392)
- srm.exe (PID: 6152)
- RegAsm.exe (PID: 1332)
- PDCViewer64.exe (PID: 5656)
- SafeguardPDFViewer_v3.exe (PID: 3708)
- irsetup.exe (PID: 6320)
Executable content was dropped or overwritten
- chrome.exe (PID: 4440)
- chrome.exe (PID: 2728)
Reads the computer name
- SafeguardPDFViewer_v3.exe (PID: 2892)
- irsetup.exe (PID: 4392)
- srm.exe (PID: 6152)
- RegAsm.exe (PID: 1332)
- PDCViewer64.exe (PID: 5656)
- SafeguardPDFViewer_v3.exe (PID: 3708)
- irsetup.exe (PID: 6320)
Reads Microsoft Office registry keys
- chrome.exe (PID: 4440)
Create files in a temporary directory
- SafeguardPDFViewer_v3.exe (PID: 2892)
- irsetup.exe (PID: 4392)
- irsetup.exe (PID: 6320)
- SafeguardPDFViewer_v3.exe (PID: 3708)
Process checks computer location settings
- SafeguardPDFViewer_v3.exe (PID: 2892)
- SafeguardPDFViewer_v3.exe (PID: 3708)
Checks proxy server information
- irsetup.exe (PID: 4392)
Process checks Internet Explorer phishing filters
- irsetup.exe (PID: 4392)
Reads the machine GUID from the registry
- srm.exe (PID: 6152)
- RegAsm.exe (PID: 1332)
- PDCViewer64.exe (PID: 5656)
Creates files in the program directory
- irsetup.exe (PID: 4392)
- PDCViewer64.exe (PID: 5656)
UPX packer has been detected
- irsetup.exe (PID: 4392)
Process checks whether UAC notifications are on
- PDCViewer64.exe (PID: 5656)
Reads product name
- PDCViewer64.exe (PID: 5656)
Reads Environment values
- PDCViewer64.exe (PID: 5656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
168
Monitored processes
32
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1332 | "C:\WINDOWS\Microsoft.Net\Framework64\v4.0.30319\regasm.exe" /codebase "C:\Program Files\Locklizard Safeguard PDF Viewer\PDCViewerShellExt.dll" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\RegAsm.exe | — | srm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
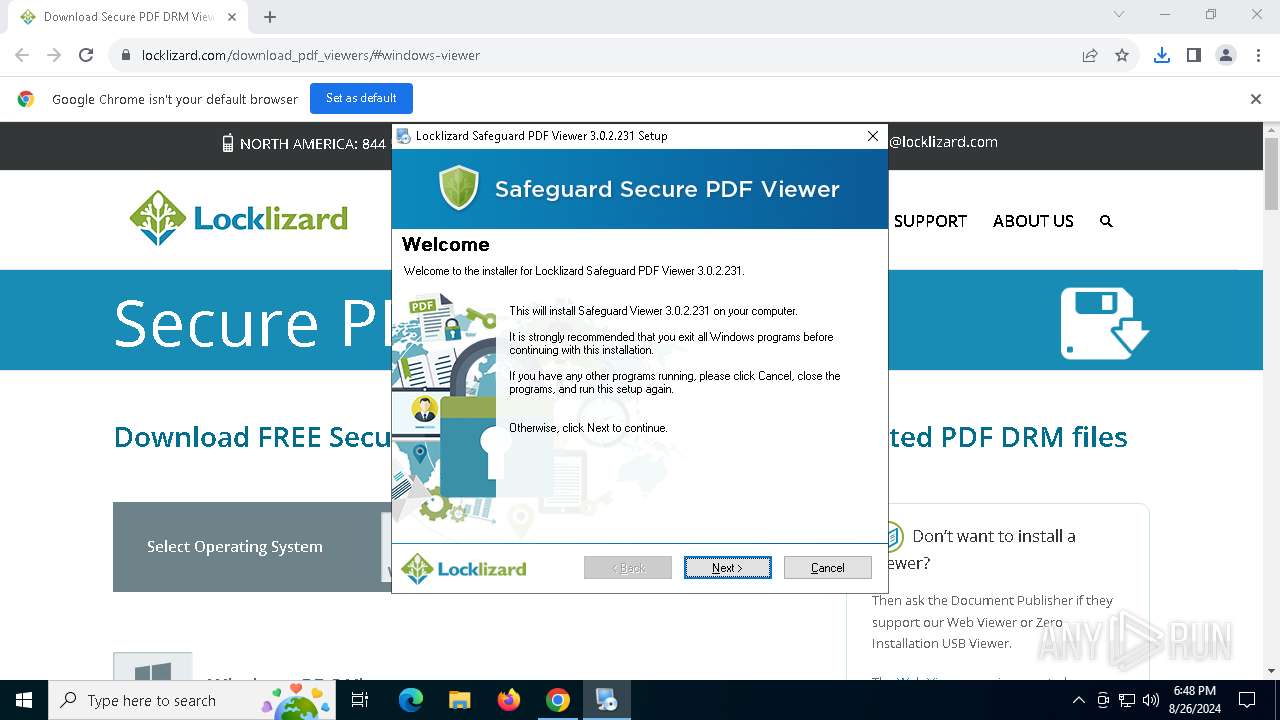
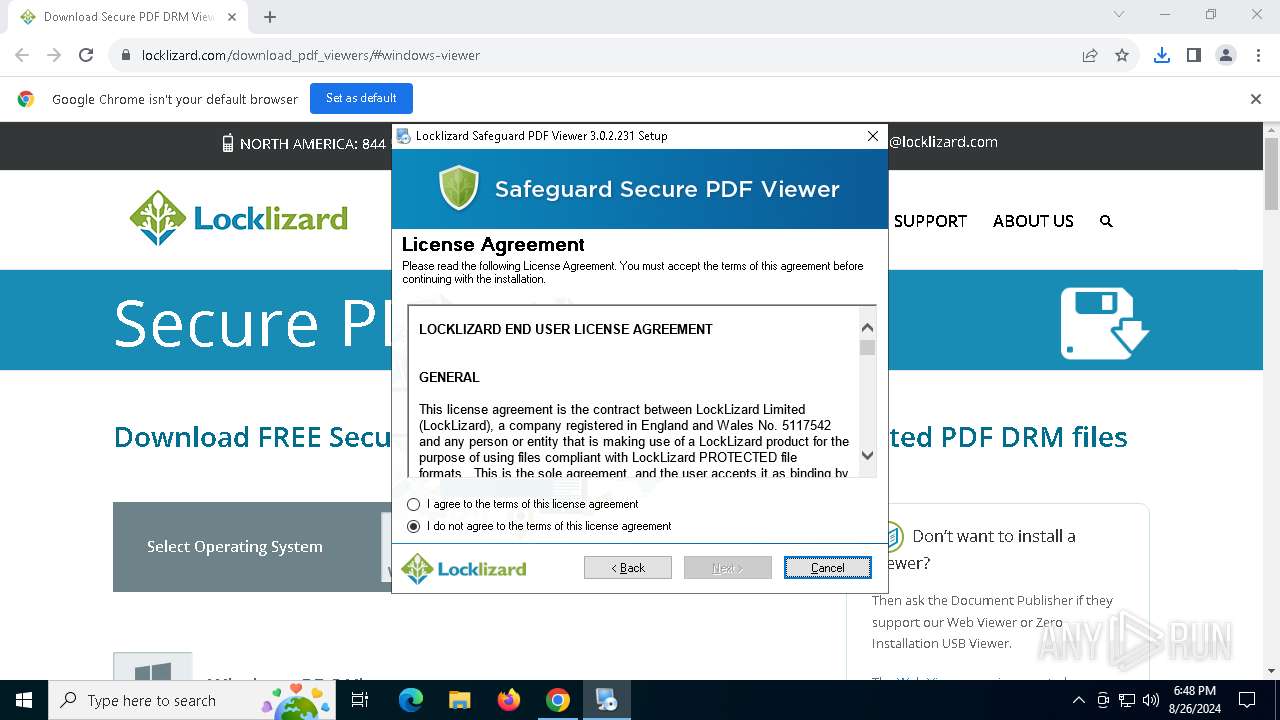
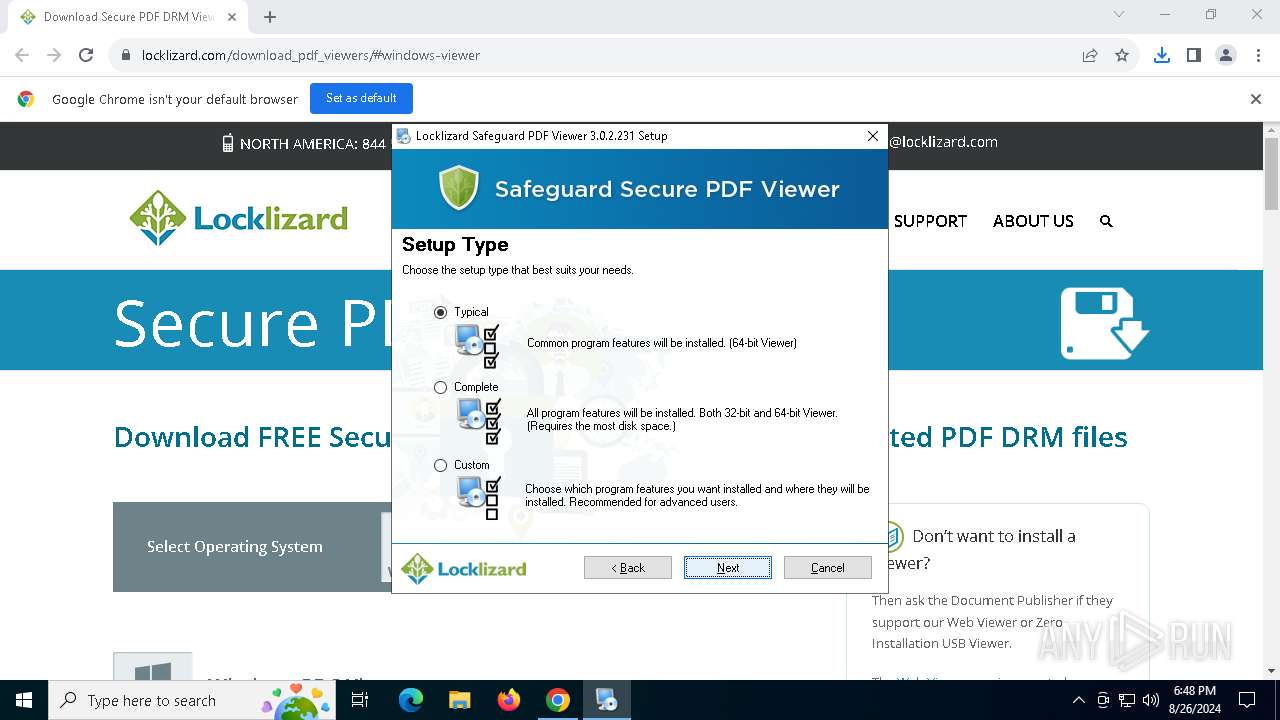
| 1944 | "C:\Users\admin\Downloads\SafeguardPDFViewer_v3.exe" | C:\Users\admin\Downloads\SafeguardPDFViewer_v3.exe | — | chrome.exe | |||||||||||
User: admin Company: Locklizard Integrity Level: MEDIUM Description: Locklizard Safeguard - PDF Viewer Exit code: 3221226540 Version: 3.0.2.231 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2244 --field-trial-handle=1940,i,6687242428764386478,14593711950763479621,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5992 --field-trial-handle=1940,i,6687242428764386478,14593711950763479621,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2724 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | srm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5592 --field-trial-handle=1940,i,6687242428764386478,14593711950763479621,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2892 | "C:\Users\admin\Downloads\SafeguardPDFViewer_v3.exe" | C:\Users\admin\Downloads\SafeguardPDFViewer_v3.exe | chrome.exe | ||||||||||||
User: admin Company: Locklizard Integrity Level: HIGH Description: Locklizard Safeguard - PDF Viewer Exit code: 0 Version: 3.0.2.231 Modules
| |||||||||||||||
| 2944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3220 --field-trial-handle=1940,i,6687242428764386478,14593711950763479621,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5620 --field-trial-handle=1940,i,6687242428764386478,14593711950763479621,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
26 375
Read events
26 226
Write events
141
Delete events
8
Modification events
| (PID) Process: | (4440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (4440) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4440) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
85
Suspicious files
265
Text files
69
Unknown types
208
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12b4c1.TMP | — | |
MD5:— | SHA256:— | |||
| 4440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12b4c1.TMP | — | |
MD5:— | SHA256:— | |||
| 4440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12b483.TMP | text | |
MD5:139F545948FC1F10256A27E3C2CEF062 | SHA256:9399CC6F9C335015E086DB37208B1816A7831221A005B04AC83C4F86CC04230D | |||
| 4440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
59
DNS requests
53
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4392 | irsetup.exe | GET | 200 | 18.217.61.96:80 | http://updates.locklizard.com/Update.inf | unknown | — | — | malicious |
6764 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac45ce45oe3jr3gbjt7oixoisvma_3039/jflookgnkcckhobaglndicnbbgbonegd_3039_all_ac724q5mrfm4b4bxvgsppwnsjyra.crx3 | unknown | — | — | whitelisted |
1932 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6764 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac45ce45oe3jr3gbjt7oixoisvma_3039/jflookgnkcckhobaglndicnbbgbonegd_3039_all_ac724q5mrfm4b4bxvgsppwnsjyra.crx3 | unknown | — | — | whitelisted |
3424 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6764 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac45ce45oe3jr3gbjt7oixoisvma_3039/jflookgnkcckhobaglndicnbbgbonegd_3039_all_ac724q5mrfm4b4bxvgsppwnsjyra.crx3 | unknown | — | — | whitelisted |
3424 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6764 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac45ce45oe3jr3gbjt7oixoisvma_3039/jflookgnkcckhobaglndicnbbgbonegd_3039_all_ac724q5mrfm4b4bxvgsppwnsjyra.crx3 | unknown | — | — | whitelisted |
6764 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac45ce45oe3jr3gbjt7oixoisvma_3039/jflookgnkcckhobaglndicnbbgbonegd_3039_all_ac724q5mrfm4b4bxvgsppwnsjyra.crx3 | unknown | — | — | whitelisted |
6764 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac45ce45oe3jr3gbjt7oixoisvma_3039/jflookgnkcckhobaglndicnbbgbonegd_3039_all_ac724q5mrfm4b4bxvgsppwnsjyra.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6012 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6280 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6472 | chrome.exe | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
4440 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6472 | chrome.exe | 3.14.62.233:443 | www.locklizard.com | AMAZON-02 | US | suspicious |
6472 | chrome.exe | 74.125.21.97:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.locklizard.com |
| unknown |
accounts.google.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
region1.analytics.google.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report