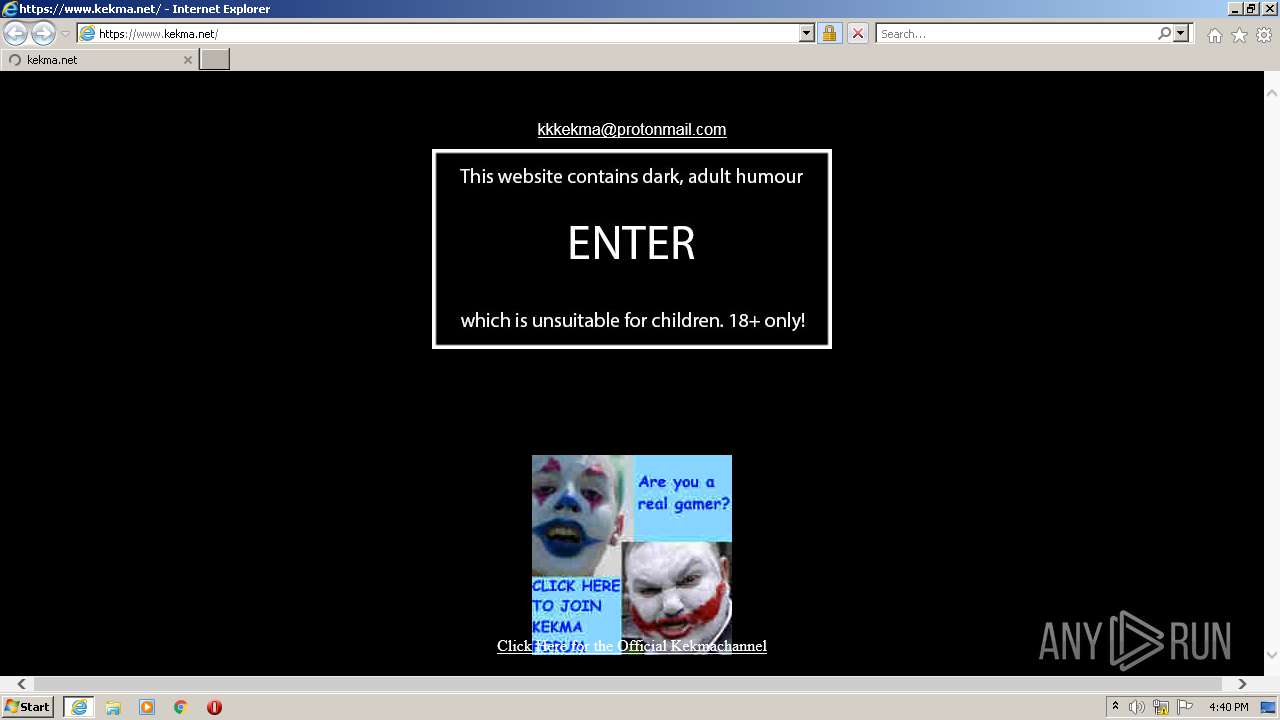
| URL: | https://www.kekma.net/ |
| Full analysis: | https://app.any.run/tasks/5f1db880-7d5b-42be-bc4b-bb740d2b2c83 |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2021, 16:40:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9045F751AAAC833AE01189EB20190F66 |
| SHA1: | 9541DC80F6F122E21CA5DACD6CE6C7A00BDAD0A9 |
| SHA256: | 12D25A39F78E2B2FFE3D73ABFB71BE4758CD2170AABDED1A54407F8A1DB66CD0 |
| SSDEEP: | 3:N8DSL8/As:2OL8Is |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3836)
INFO
Checks supported languages
- iexplore.exe (PID: 2672)
- iexplore.exe (PID: 3836)
Reads the computer name
- iexplore.exe (PID: 2672)
- iexplore.exe (PID: 3836)
Application launched itself
- iexplore.exe (PID: 2672)
Changes internet zones settings
- iexplore.exe (PID: 2672)
Reads settings of System Certificates
- iexplore.exe (PID: 3836)
- iexplore.exe (PID: 2672)
Checks Windows Trust Settings
- iexplore.exe (PID: 3836)
- iexplore.exe (PID: 2672)
Creates files in the user directory
- iexplore.exe (PID: 3836)
Reads internet explorer settings
- iexplore.exe (PID: 3836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2672 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.kekma.net/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3836 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2672 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
10 649
Read events
10 534
Write events
115
Delete events
0
Modification events
| (PID) Process: | (2672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30927954 | |||
| (PID) Process: | (2672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30927954 | |||
| (PID) Process: | (2672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
12
Text files
18
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3836 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\styles[1].css | text | |
MD5:EA75F9604F9462419D2D4441910EEDB5 | SHA256:F297D8F572F13F3A4901D3219C782DC993CE0CDE674000E5A5D3E63CA5BB77B8 | |||
| 3836 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:9FC5583A6A5550740181D0944ED4FD69 | SHA256:8D52791E6E92602A024AF75898D0AE95A52CE78F00DFAB3F9EA5BDD5D836723B | |||
| 3836 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ULCAWSBV.htm | html | |
MD5:51A59BE6E5FE2D9B9AD5DCA64B6676A0 | SHA256:B83C88A3C4AF920C408566FFAD04CBC9E901D06D574D5E11DB3279F14E25E57D | |||
| 3836 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:AA44367B63F2A7A53E8B5DDC076048D9 | SHA256:B910A4C349BF86FA2D8B571B8D0BFBAB8C647C8BDF0CCF431073249B8249561D | |||
| 3836 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:41A95E1AE7F938822FF2559839C9810C | SHA256:CD6703EA0A166A8DD12AED52C906D414ED164A876E0342AF367A915168ADE86F | |||
| 3836 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:B0415C49DB50DD58DD772F2C3586EFF4 | SHA256:8A5C7ED02F015B531C1C3290CE12BB16B70914E996947F58B08056C0A4293879 | |||
| 3836 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:22E0C816CC7580D88EC422C47C2F715B | SHA256:B7E6F016600F3343696CE2D9DF11EB18ABA026D838D3D68B0091414C30C49507 | |||
| 3836 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\email-decode.min[1].js | html | |
MD5:9E8F56E8E1806253BA01A95CFC3D392C | SHA256:2595496FE48DF6FCF9B1BC57C29A744C121EB4DD11566466BC13D2E52E6BBCC8 | |||
| 2672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:1DEE31AD8FB76D2E4055E768AB08F69D | SHA256:F1894F930B59CE77B6C0E5B90E7C8E24B375BADB380DF5A5EF1A1630F365489A | |||
| 2672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:69D672C10EB5D0A23A81559B37916A14 | SHA256:248A04AE2FF7228C5D5561EB2F5A2090F0E66FD623551D4E1431B9E200D0CC32 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
43
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2672 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3836 | iexplore.exe | GET | — | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECDxfmiTtHUPCgAAAAEiS4Q%3D | US | — | — | whitelisted |
3836 | iexplore.exe | GET | 200 | 142.250.181.238:80 | http://crls.pki.goog/gts1c3/zdATt0Ex_Fk.crl | US | der | 5.03 Kb | whitelisted |
3836 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3836 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3836 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCKJpvy9pIOCwoAAAABGVGE | US | der | 472 b | whitelisted |
3836 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://crl.pki.goog/gtsr1/gtsr1.crl | US | der | 760 b | whitelisted |
3836 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3836 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0f4e31f0de1fd7c7 | US | compressed | 4.70 Kb | whitelisted |
3836 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://crl.pki.goog/gsr1/gsr1.crl | US | der | 1.61 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3836 | iexplore.exe | 142.250.181.238:80 | crls.pki.goog | Google Inc. | US | whitelisted |
— | — | 104.18.31.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | unknown |
3836 | iexplore.exe | 172.67.176.245:443 | www.kekma.net | — | US | suspicious |
2672 | iexplore.exe | 104.21.43.81:443 | www.kekma.net | Cloudflare Inc | US | malicious |
3836 | iexplore.exe | 142.250.186.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
— | — | 104.21.43.81:443 | www.kekma.net | Cloudflare Inc | US | malicious |
3836 | iexplore.exe | 104.21.43.81:443 | www.kekma.net | Cloudflare Inc | US | malicious |
3836 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3836 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3836 | iexplore.exe | 142.250.185.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kekma.net |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
code.jquery.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |