| File name: | windowsdesktop-runtime-6.0.20-win-x86.exe |
| Full analysis: | https://app.any.run/tasks/3dae2076-84a1-4e4d-8762-c75dc503ce1f |
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2023, 11:27:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 028652F24AC46F525FF69C58110E4A03 |
| SHA1: | 02E96D56868F4DCB38802A565AA121510D3187A6 |
| SHA256: | 12C881A5280E9159B0C54DD440AAB56CFD4E2903FE9E7710A563C74148D04D91 |
| SSDEEP: | 12288:u5mWukhI2jFMSjysAS9X/GsfTDYrGiDN1Br7GJ1ocx8HuDnml:u5mWpI2jFM5sFzfTpih1pU8Oi |
MALICIOUS
Loads dropped or rewritten executable
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 2416)
SUSPICIOUS
Searches for installed software
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 2416)
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 768)
Executable content was dropped or overwritten
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 1132)
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 2416)
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 768)
Reads the Internet Settings
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 2416)
Starts itself from another location
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 1132)
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 2416)
INFO
Checks supported languages
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 1132)
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 2416)
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 768)
Reads the computer name
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 2416)
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 768)
The process checks LSA protection
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 2416)
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 768)
Create files in a temporary directory
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 1132)
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 2416)
Reads the machine GUID from the registry
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 2416)
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 768)
Creates files in the program directory
- windowsdesktop-runtime-6.0.20-win-x86.exe (PID: 768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| ProductVersion: | 6.0.20.32621 |
|---|---|
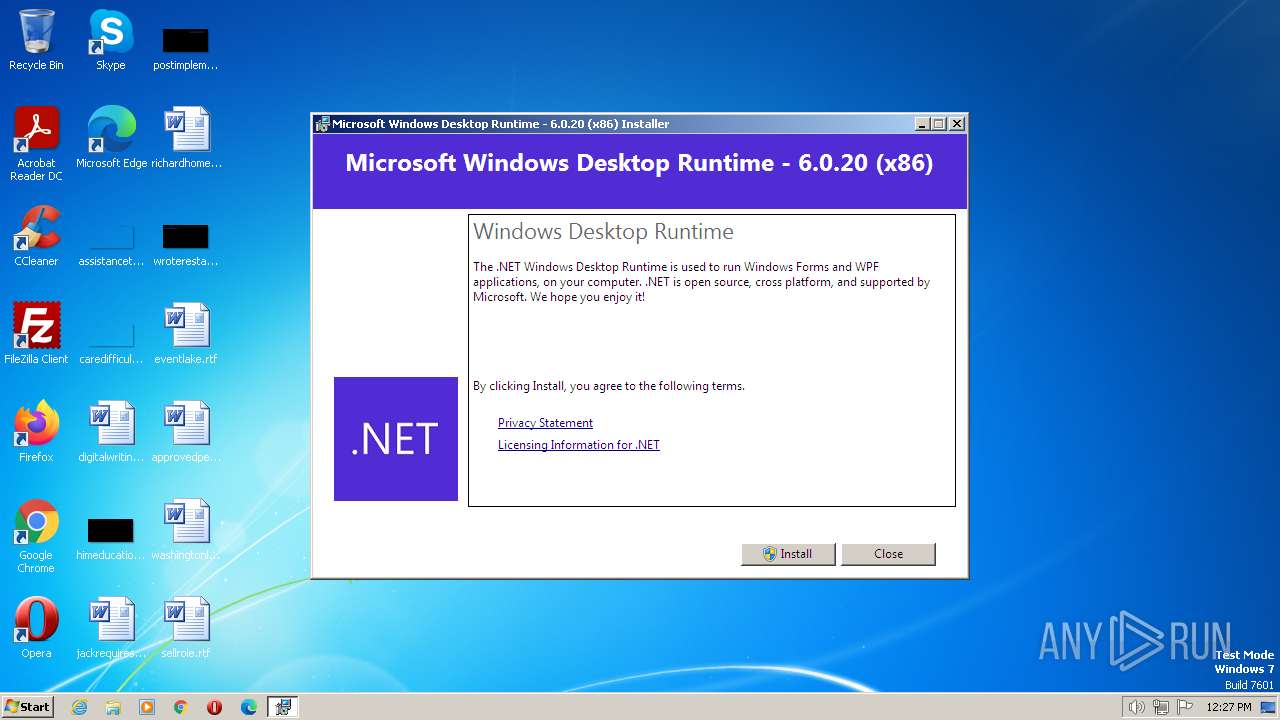
| ProductName: | Microsoft Windows Desktop Runtime - 6.0.20 (x86) |
| OriginalFileName: | windowsdesktop-runtime-6.0.20-win-x86.exe |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| InternalName: | setup |
| FileVersion: | 6.0.20.32621 |
| FileDescription: | Microsoft Windows Desktop Runtime - 6.0.20 (x86) |
| CompanyName: | Microsoft Corporation |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 6.0.20.32621 |
| FileVersionNumber: | 6.0.20.32621 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x2e082 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 162816 |
| CodeSize: | 302080 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| TimeStamp: | 2021:09:22 15:58:18+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Sep-2021 15:58:18 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Windows Desktop Runtime - 6.0.20 (x86) |
| FileVersion: | 6.0.20.32621 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFilename: | windowsdesktop-runtime-6.0.20-win-x86.exe |
| ProductName: | Microsoft Windows Desktop Runtime - 6.0.20 (x86) |
| ProductVersion: | 6.0.20.32621 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 22-Sep-2021 15:58:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00049BC3 | 0x00049C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56876 |
.rdata | 0x0004B000 | 0x0001F274 | 0x0001F400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.07604 |
.data | 0x0006B000 | 0x00001814 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.8557 |
.wixburn8 | 0x0006D000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.584438 |
.rsrc | 0x0006E000 | 0x00003B3C | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.49292 |
.reloc | 0x00072000 | 0x00003DBC | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78712 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
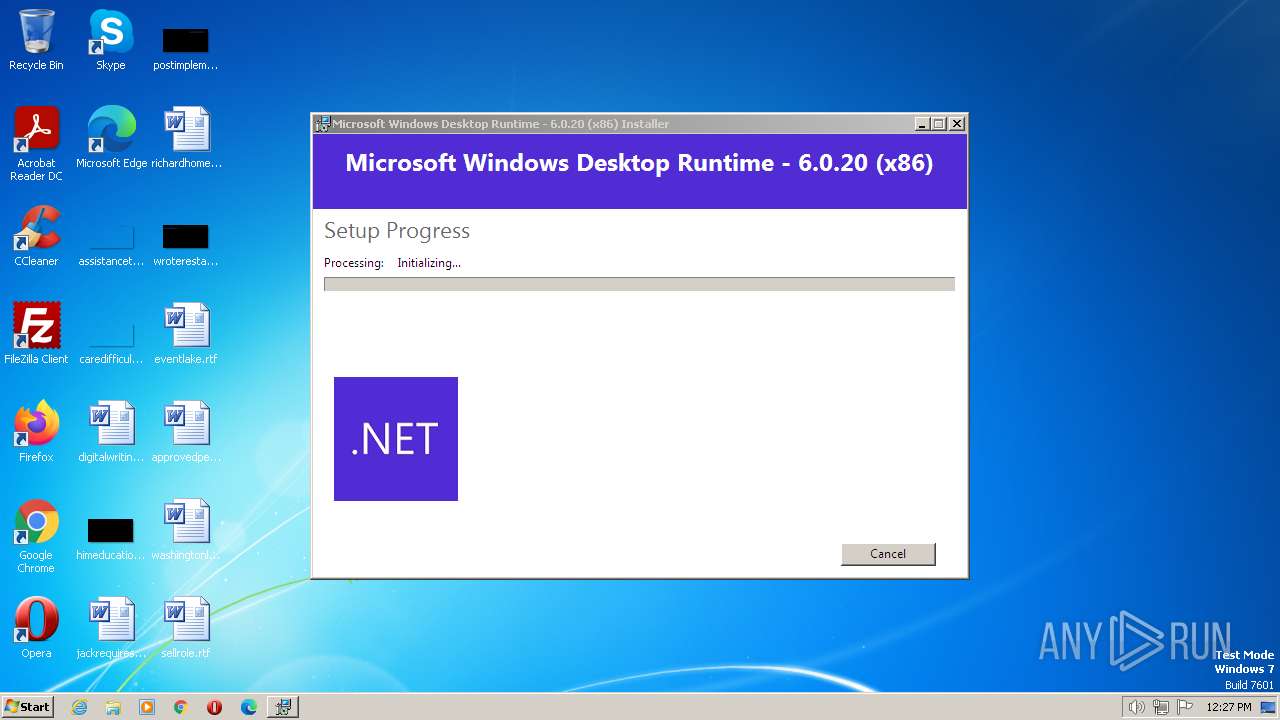
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 768 | "C:\Users\admin\AppData\Local\Temp\{D79C4034-2280-4A4D-9FB6-7DFD52F863A9}\.be\windowsdesktop-runtime-6.0.20-win-x86.exe" -q -burn.elevated BurnPipe.{C2EBDAB6-FB41-4910-822D-DD21631952C8} {37CC07CA-DFA4-426C-B0AC-CB800BDF7662} 2416 | C:\Users\admin\AppData\Local\Temp\{D79C4034-2280-4A4D-9FB6-7DFD52F863A9}\.be\windowsdesktop-runtime-6.0.20-win-x86.exe | windowsdesktop-runtime-6.0.20-win-x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Desktop Runtime - 6.0.20 (x86) Exit code: 1 Version: 6.0.20.32621 Modules
| |||||||||||||||
| 1132 | "C:\Users\admin\AppData\Local\Temp\windowsdesktop-runtime-6.0.20-win-x86.exe" | C:\Users\admin\AppData\Local\Temp\windowsdesktop-runtime-6.0.20-win-x86.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Desktop Runtime - 6.0.20 (x86) Exit code: 1 Version: 6.0.20.32621 Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\AppData\Local\Temp\{884E68C3-E185-4287-A8BC-78BA03FDC010}\.cr\windowsdesktop-runtime-6.0.20-win-x86.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\windowsdesktop-runtime-6.0.20-win-x86.exe" -burn.filehandle.attached=152 -burn.filehandle.self=160 | C:\Users\admin\AppData\Local\Temp\{884E68C3-E185-4287-A8BC-78BA03FDC010}\.cr\windowsdesktop-runtime-6.0.20-win-x86.exe | windowsdesktop-runtime-6.0.20-win-x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Desktop Runtime - 6.0.20 (x86) Exit code: 1 Version: 6.0.20.32621 Modules
| |||||||||||||||
Total events
806
Read events
793
Write events
8
Delete events
5
Modification events
| (PID) Process: | (2416) windowsdesktop-runtime-6.0.20-win-x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2416) windowsdesktop-runtime-6.0.20-win-x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2416) windowsdesktop-runtime-6.0.20-win-x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2416) windowsdesktop-runtime-6.0.20-win-x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (768) windowsdesktop-runtime-6.0.20-win-x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Dependencies\{39139702-799e-4843-8d90-cfe9330b285a}\Dependents\{39139702-799e-4843-8d90-cfe9330b285a} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (768) windowsdesktop-runtime-6.0.20-win-x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Dependencies\{39139702-799e-4843-8d90-cfe9330b285a}\Dependents |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (768) windowsdesktop-runtime-6.0.20-win-x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Dependencies\{39139702-799e-4843-8d90-cfe9330b285a} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (768) windowsdesktop-runtime-6.0.20-win-x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{39139702-799e-4843-8d90-cfe9330b285a} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (768) windowsdesktop-runtime-6.0.20-win-x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | {39139702-799e-4843-8d90-cfe9330b285a} |
Value: "C:\ProgramData\Package Cache\{39139702-799e-4843-8d90-cfe9330b285a}\windowsdesktop-runtime-6.0.20-win-x86.exe" /burn.runonce | |||
Executable files
5
Suspicious files
1
Text files
22
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2416 | windowsdesktop-runtime-6.0.20-win-x86.exe | C:\Users\admin\AppData\Local\Temp\{D79C4034-2280-4A4D-9FB6-7DFD52F863A9}\.ba\thm.xml | xml | |
MD5:302563A713B142EE41B59E3EEAC53A90 | SHA256:83CA096F7BA2C83FC3B3AEB697B8139A788FA35EB8632943E26BB9FFF7C78E63 | |||
| 1132 | windowsdesktop-runtime-6.0.20-win-x86.exe | C:\Users\admin\AppData\Local\Temp\{884E68C3-E185-4287-A8BC-78BA03FDC010}\.cr\windowsdesktop-runtime-6.0.20-win-x86.exe | executable | |
MD5:028652F24AC46F525FF69C58110E4A03 | SHA256:12C881A5280E9159B0C54DD440AAB56CFD4E2903FE9E7710A563C74148D04D91 | |||
| 2416 | windowsdesktop-runtime-6.0.20-win-x86.exe | C:\Users\admin\AppData\Local\Temp\{D79C4034-2280-4A4D-9FB6-7DFD52F863A9}\.ba\1046\thm.wxl | xml | |
MD5:88CB193F0B0C15023D789E0F8FCE3E03 | SHA256:4D6A2D306ABE77E7DBDB2609F6198B4CF99B3F9DC15B9DC72951592AD2F64384 | |||
| 2416 | windowsdesktop-runtime-6.0.20-win-x86.exe | C:\Users\admin\AppData\Local\Temp\{D79C4034-2280-4A4D-9FB6-7DFD52F863A9}\.ba\1055\thm.wxl | xml | |
MD5:2897BAEC061B9A89661744685FE3C217 | SHA256:285E32E649EB71A68F29BCA7321A6CADE50D79F94DD89E50ECE1197DD70E7633 | |||
| 2416 | windowsdesktop-runtime-6.0.20-win-x86.exe | C:\Users\admin\AppData\Local\Temp\{D79C4034-2280-4A4D-9FB6-7DFD52F863A9}\.ba\1041\thm.wxl | xml | |
MD5:E5FD798D4BBDD419A602423A699E2854 | SHA256:00AEC52B4564BC07302881FCFD510F7CCA535AC9E05CFD95A86738171626F6C4 | |||
| 2416 | windowsdesktop-runtime-6.0.20-win-x86.exe | C:\Users\admin\AppData\Local\Temp\{D79C4034-2280-4A4D-9FB6-7DFD52F863A9}\.ba\1045\thm.wxl | xml | |
MD5:8CFBEE02F1C88567CD9AA747FF27182E | SHA256:D92B3838DE7A1685CCBD04FC9C123704FBD198BFD284D8FAECE4A3663494E75A | |||
| 2416 | windowsdesktop-runtime-6.0.20-win-x86.exe | C:\Users\admin\AppData\Local\Temp\{D79C4034-2280-4A4D-9FB6-7DFD52F863A9}\.ba\1036\thm.wxl | xml | |
MD5:9F779700FF90DF7211AE3A3340DDD5FC | SHA256:6AF5C2BC88B1E5CE188A97DD9204061D66369EC2689B3657AFF1DC6188F44F22 | |||
| 2416 | windowsdesktop-runtime-6.0.20-win-x86.exe | C:\Users\admin\AppData\Local\Temp\{D79C4034-2280-4A4D-9FB6-7DFD52F863A9}\.ba\1049\thm.wxl | xml | |
MD5:1D628F2E1DBAA25BDD8CF2D7F2A9CAF2 | SHA256:C7CC8E0BDD4F82DA33984F553B576412DF69C5E1E5B8479542D024CB6B41D050 | |||
| 2416 | windowsdesktop-runtime-6.0.20-win-x86.exe | C:\Users\admin\AppData\Local\Temp\{D79C4034-2280-4A4D-9FB6-7DFD52F863A9}\.ba\1040\thm.wxl | xml | |
MD5:347BE63418F507E7F2A086726E96FCA8 | SHA256:344ACD0D3665BA489EB30EBC0F902C625E1AD33A4E2B5BA7CDD7E463658D5557 | |||
| 2416 | windowsdesktop-runtime-6.0.20-win-x86.exe | C:\Users\admin\AppData\Local\Temp\{D79C4034-2280-4A4D-9FB6-7DFD52F863A9}\.ba\2052\thm.wxl | xml | |
MD5:ED946A363E47DCC77017EC10B1032C54 | SHA256:3BB9CE59BA1C4B76FA6B35F544E2B04C85387053EDD8B25D8C8D4FE637FB0A85 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3388 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1096 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |