| URL: | http://speedupplaza.com |
| Full analysis: | https://app.any.run/tasks/925bb977-ae35-4a2b-9fd7-f324963023b5 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 05:30:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6C75A836EBB85545E7AA8E53A2A11345 |
| SHA1: | 94977111546278EDBC8CE9216EB57441A528A5EC |
| SHA256: | 12B9A20BF9D6BF37A193A2F5CA12FBC18F0EA8CB7FE65714DA49374DC5E02E99 |
| SSDEEP: | 3:N1KNVb8E9Tn:CR9T |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1684)
INFO
Creates files in the user directory
- iexplore.exe (PID: 4064)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1684)
- iexplore.exe (PID: 3296)
Changes internet zones settings
- iexplore.exe (PID: 3296)
Application launched itself
- iexplore.exe (PID: 3296)
Reads internet explorer settings
- iexplore.exe (PID: 4064)
Reads Internet Cache Settings
- iexplore.exe (PID: 4064)
- iexplore.exe (PID: 3296)
Reads settings of System Certificates
- iexplore.exe (PID: 3296)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3296)
Changes settings of System certificates
- iexplore.exe (PID: 3296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1684 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3296 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://speedupplaza.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4064 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3296 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
532
Read events
436
Write events
92
Delete events
4
Modification events
| (PID) Process: | (3296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {01AA23BF-A854-11E9-B2FD-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30707000300110005001E0026001901 | |||
Executable files
0
Suspicious files
5
Text files
89
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4064 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@mybetterdl[2].txt | — | |
MD5:— | SHA256:— | |||
| 4064 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@pabgvho[1].txt | — | |
MD5:— | SHA256:— | |||
| 4064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEA7F.tmp | — | |
MD5:— | SHA256:— | |||
| 4064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEA80.tmp | — | |
MD5:— | SHA256:— | |||
| 4064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEA91.tmp | — | |
MD5:— | SHA256:— | |||
| 4064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEA92.tmp | — | |
MD5:— | SHA256:— | |||
| 4064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEB1F.tmp | — | |
MD5:— | SHA256:— | |||
| 4064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEB20.tmp | — | |
MD5:— | SHA256:— | |||
| 4064 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@go.nordvpn[1].txt | — | |
MD5:— | SHA256:— | |||
| 4064 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@nordvpn[1].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
43
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
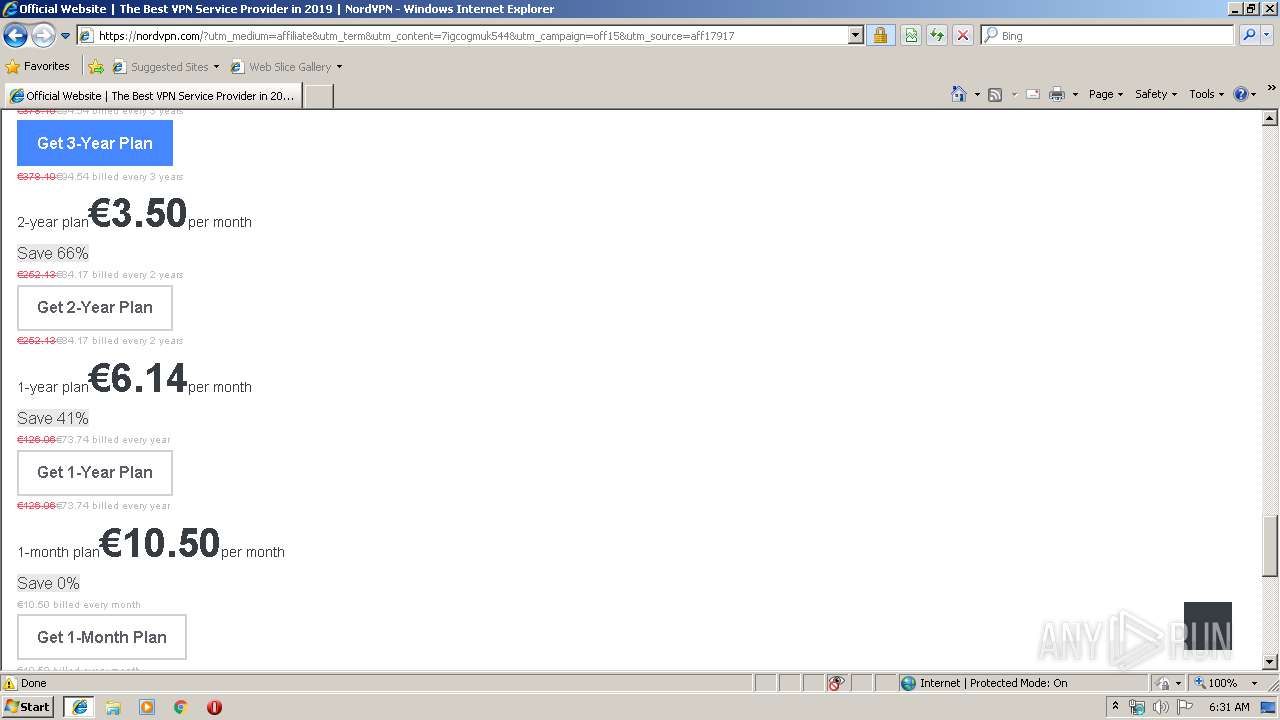
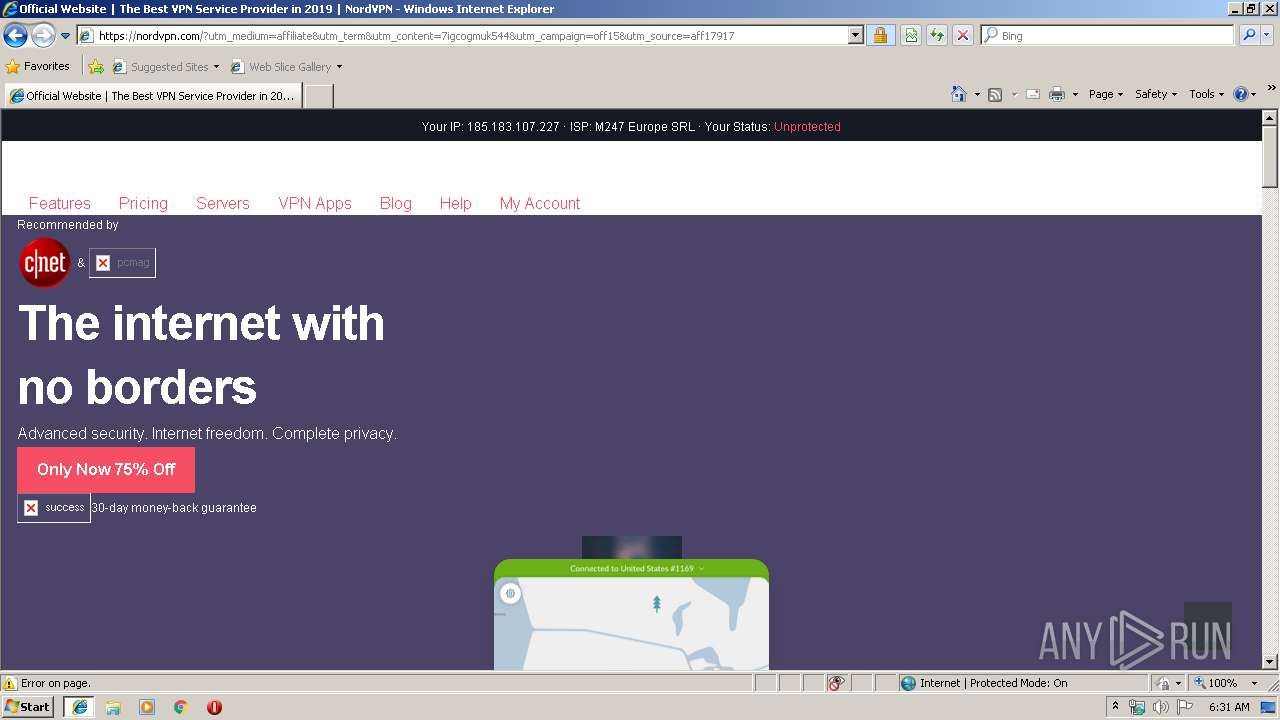
4064 | iexplore.exe | GET | 302 | 72.52.179.175:80 | http://speedupplaza.com/ | US | — | — | malicious |
4064 | iexplore.exe | GET | 302 | 184.173.87.162:80 | http://beta.mybetterdl.com/aS/feedclick?s=tmxvfbadWlkLtgv3D3v8v97qPcR34TlSNwPRuarBsC7icX8KFcsYvbUC6hWIeTga6IkCbg7sKEuYDMm3vSUGcOnR9v5nd2PWGY-JEsN51T4Rp60bMyofPqYZ_8dAZcE4MLekFlfWsTpfBjRhq2gpKDqyEY2UcdgeA4FUttBbb2fbsPhgDX-8X7QyK6ByuYS7tnss-jrr7YUMvkcAT8-DGCkUyJScp6Z3wfVRVjEHTagHEyZdAWcHfidNGTdJt1ZywIVoQ2Q0mscyBEiKHh7QnVLT3f9L9dnNE-fW-R-AAT_gcDgLrMnQezgmPo9VAG3toXALXsadDH1QqBAJc1rINFj17QABwOaNjLFxY_LlkIjwDn_wDWysAo0tPuWED4EfmCqMeGmKlsN3uc9dmvkCp2BCDXFso8NafyJnjoyYxu_LFUKyRqof5vbHOWfcPQoDb5juu8HGt4cbEZKIBBjnonJopkwV_qVCyUgpPvRjaXgwP-Ea8JR_i0CKRFwM03cyrk6NRBLV7daspvvb8qKeWXqrHJXfHEE3x6Rkd8zClIy4CgJqsmKvhg8GhzrfG3o-q0suI1l3wGmiIfjbj_ZR8BnfLO91ciL_vJwtSNxOBPzBk-ejmPcq5Fb3ah6LIYuFLNp47p7201nSblzbEd8MfA-0YPUSGsdqMzNgtecxCV-Kb-8NAyYOPNEwi2oaZptrQ1coXOoyLN8Y7QFMumJtD0zRkCJmOWo_4394Lm2KdSwmV11JiaFm3-rxU8WG9rJPXGFW-k7nFY6QnKT1MiiqT14VyGK37UR2SIH4IDzU7W560a3WL1HYyfQ8qDQZv1l5Q-hS19DstSWwa3MaD_YmDIytr7eyOHDL5r75B9g2HGrONvsMLMD3G_8ZEbKLYhSza46LNuwvMU-DUa8Cb8B3Tw8bCb0KKlqcJ22rwl6FQZDC3LJQkKzRJE09gS8oQmTOVi7e1g0bDIpfINUo3Q4p_-jfihxYUjwjEiv4DF2JndZdL0s41ufwjV6d7dQDrKzvBA6T9LP2AXWWn0MWXPEn24R6QAaXaUQkMcWpPFFbTR3npBiTS3874WI_4vEmrXe57AHU8rK8fguoHo1SK3oURgtFsuKsGfSlFGq24t6kLi-EebKBcc8F5BGtclOiWy2f8UXOooNyxnkSOR4R7y7JSlldXoeP51c-E9X3AYQsCpAEn3pdnGSoQorn9i_PN5gouzPa8jv1G2rAQ85Br1mO7krRJhUw7clDbW1YByshVQc6v7Rcw1vRjR0kmx_hSWcdnpAWuhpxMpt2sFPFaye-wl58GALxbeAPMUtTyFSpO5AXpR1qLlXMteW9V0jD2MysWxp6fmCy6zWBykaoh87Ye8ZjFW49kpaSaPdn2DAPLxuhAh9cYmkvQ0xOwteg4fQdhS-0mWWKAti-bpUc9r8nQBRV6aUDDTpmF8T2a_SJHspGKzWVI-pNt03D-46Wx2GQ4p1Vi0QGFMLNQGzQdKYFbMwUX3BrSWUFNfve48sEM61Yd_hKTtzizLBEEAndBcli8-GzbkMGUT13MeUmLEuDJFHQfX9aFeLizLoCzgMrl54CCnAptrXpWdvPQGgukvNRlVsJwf0yyfPYtDQy9APbznGSvDOhHECgdnCTI_SMUZyrecONlSTMe6cS5fVf4gQfyAoieCQBkjVBas6-TRdKW3dWUsksVCM3KDAKMXsiu-IGrno7uIEofLKIYxkobhDZHe3KZkiZPkuh57Na-g9idwzUYj2Hkdxm2IBu2n015Mg | US | — | — | suspicious |
4064 | iexplore.exe | GET | 302 | 184.173.87.162:80 | http://beta.mybetterdl.com/adServe/domainClick?ai=m2oPVG8fMLZ3dPavZkDsJF0EG_dI0E5saPzqm61k9byegnL1MAGSmmMM574aNh_mKzPlCAYPQ-BWKFAI4-yRmrqtdU3bB3rnzQeUGEmV2rK3l70Jp2tIog17BOWoS8DCL0i9C4mE3uYCv0rOyGlzsEEkAJoHXs3XKDAKMXsiu-KsWvdh7vYlLDi0R_TylciVEzxnGL0Q-78CvLHM1Mhvxc8f7ZEdtba8OscVXFpvZZRanluXw38HrNtmHa-sXA6BXP6n_paJdUeYDMm3vSUGcFU6_k1roiFByRTUvPOEJfEBW3Nb4Gcb8mJWdAgaDFAOJTu6AXYz7K4iX-3NC4bhm1mzx2QGUJIVrBZwfnlpzJktbhIHsrgHaQHU9Rlh80lFnMKLuSA_4rprXZ7fy64Z_MSDPhdk_SCbAOiOAfLKc3X6tVUHBRtKv-3MVfKXZeqn3F5zMqSKTSJIlcCIbSvr_VBKQ8__OyXIgafZ9sDvHt0Fy9LbfW_6duFoOnPfBtp4nikxEDznWgUW0YeVoTdAMXo_8JgIlG3qZZJCxAdeOqU&ui=tmxvfbadWlkLtgv3D3v8v01pepdij83hLWXp3on882KiNKxwAofaTLr7_S6oiuPKsF4ix0y_krs4F7CeG2bROX4N0f4U815-pwNMuXn1mjx0M2wi1jeZRfHMdu12_7f0JyIcYEdvYRw&si=1&oref=ce33fd13b1e60e97c8daf2fad39ec5c6&rb=30cHdPfkeTk&rr=0&isco=t | US | — | — | suspicious |
3296 | iexplore.exe | GET | 200 | 37.46.134.14:80 | http://37.46.134.14/favicon.ico | RU | — | — | suspicious |
4064 | iexplore.exe | GET | 200 | 8.253.207.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.3 Kb | whitelisted |
4064 | iexplore.exe | GET | 200 | 37.46.134.14:80 | http://37.46.134.14/?Nzc4NTA=&fOeKKFMytMi&fIMaWFep=golfer&uoJJUyBXZeS=known&RsFDaHrx=perpetual&BaSHYaOVKF=criticized&cNwMRGNwfpxX=everyone&ff5gfds=xXbQMvWbbRXQDZ3EKv3cT6NMMVHRG0CL2YidmrHYefjac1WkzrrFTF_1ozKATQSG6_ptdfJXDQH&t4tsggf4=hikyFLgw3nY5bUFkU_qn6jkjRyB6VhMHW-kffZg0W_5OdR-du3lzxzbgkdskvwBSH71ENjOweYg&KAEWBbONZJx=strategy&saJCxM=professional&lSXbIsmsGmBdxB=community&YLrJquUSPy=referred&aPQDQyVn=community&YVJzOXEx=known&SdBDVMvSOelaw=community&BvDqvtku=known&ehFkxci=strategy&gfQQvkKoai=wrapped&lHlpCpYSIqRVhsMTA2MTMz | RU | text | 11 b | suspicious |
3296 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
4064 | iexplore.exe | GET | 200 | 52.85.188.132:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
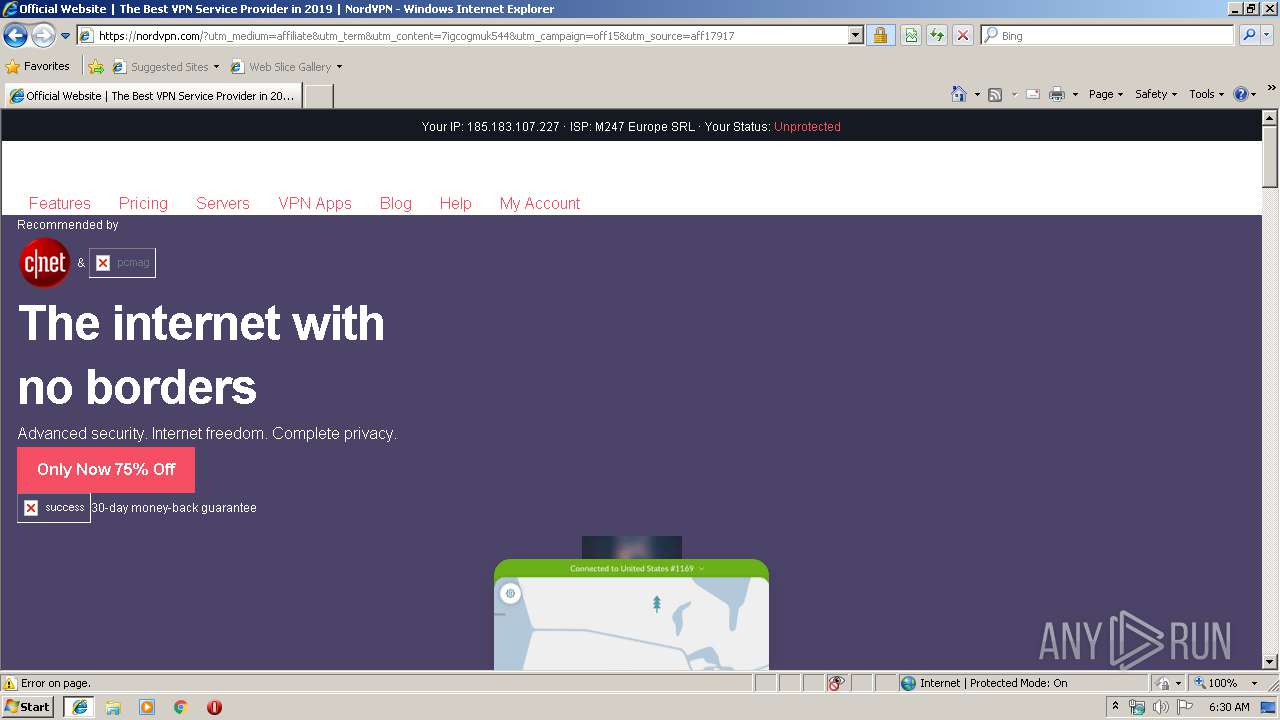
4064 | iexplore.exe | 52.210.254.245:443 | go.nordvpn.net | Amazon.com, Inc. | IE | unknown |
4064 | iexplore.exe | 104.18.229.229:443 | nordvpn.com | Cloudflare Inc | US | shared |
4064 | iexplore.exe | 104.17.168.30:443 | s1.nordcdn.com | Cloudflare Inc | US | shared |
4064 | iexplore.exe | 72.52.179.175:80 | speedupplaza.com | Liquid Web, L.L.C | US | malicious |
3296 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4064 | iexplore.exe | 184.173.87.162:80 | beta.mybetterdl.com | SoftLayer Technologies Inc. | US | suspicious |
4064 | iexplore.exe | 52.58.254.162:443 | pabgvho.com | Amazon.com, Inc. | DE | unknown |
3296 | iexplore.exe | 104.18.229.229:443 | nordvpn.com | Cloudflare Inc | US | shared |
4064 | iexplore.exe | 104.17.50.74:443 | visit.nordvpn.com | Cloudflare Inc | US | shared |
4064 | iexplore.exe | 64.233.167.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
speedupplaza.com |
| malicious |
www.bing.com |
| whitelisted |
beta.mybetterdl.com |
| unknown |
pabgvho.com |
| unknown |
go.nordvpn.net |
| suspicious |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
visit.nordvpn.com |
| unknown |
nordvpn.com |
| unknown |
s1.nordcdn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4064 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |