| File name: | AutoMouseKey.exe |
| Full analysis: | https://app.any.run/tasks/6f1f9901-51c1-4629-8455-63569741fb08 |
| Verdict: | Malicious activity |
| Analysis date: | August 02, 2021, 17:18:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EBE03C4ED0A989CCE324542EA93938C7 |
| SHA1: | 673B5EF770FF9D65CA24F14EDBA93DCE9CE34143 |
| SHA256: | 12B824D1114793B92438B8A961A696F082546A3ACA14B07DF49A1487E6258240 |
| SSDEEP: | 98304:u5rXWkuNkfOHGzrZneBBIth+Mh3TdpvL7iEcDRPjItVW7:8rXWNNqwu420Mh3Jpvij6VW7 |
MALICIOUS
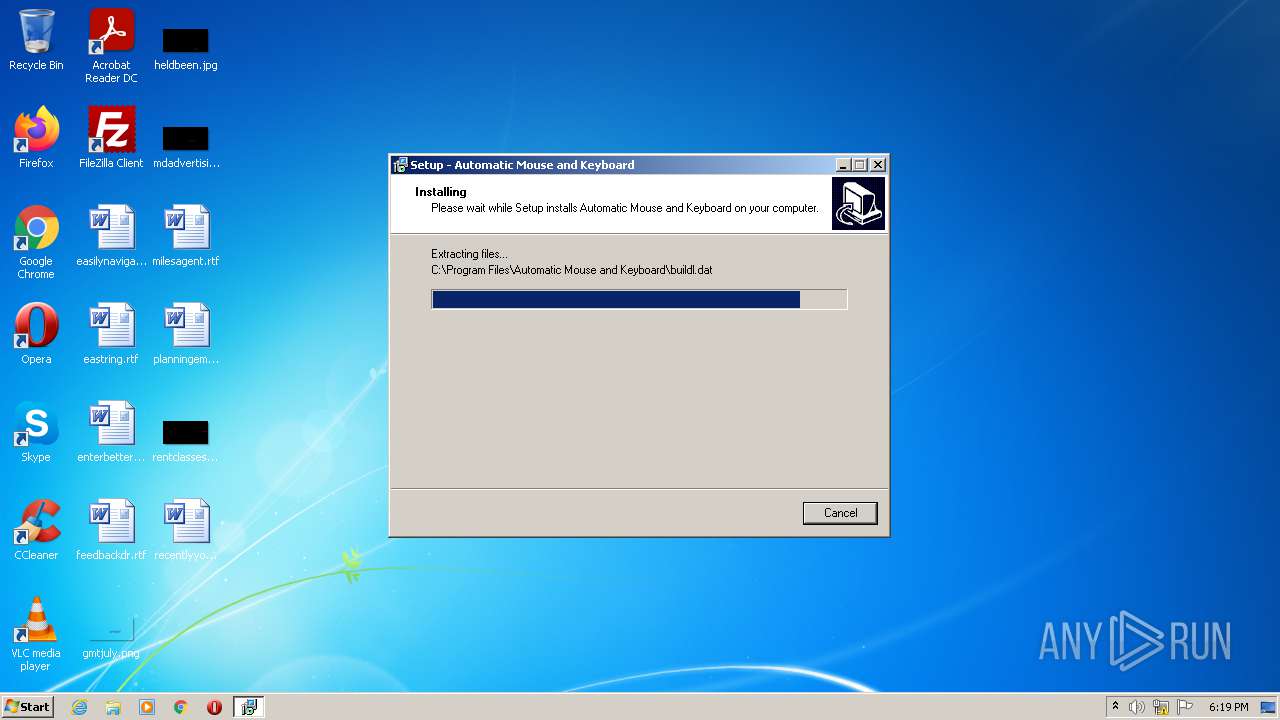
Drops executable file immediately after starts
- AutoMouseKey.exe (PID: 864)
- AutoMouseKey.exe (PID: 1008)
- AutoMouseKey.tmp (PID: 3664)
- AutoMouseKey.exe (PID: 2952)
Application was dropped or rewritten from another process
- AutoMouseKey.exe (PID: 2952)
- AutoMouseKey.exe (PID: 1008)
SUSPICIOUS
Drops a file with too old compile date
- AutoMouseKey.exe (PID: 864)
- AutoMouseKey.exe (PID: 1008)
- AutoMouseKey.tmp (PID: 3664)
Executable content was dropped or overwritten
- AutoMouseKey.exe (PID: 864)
- AutoMouseKey.exe (PID: 1008)
- AutoMouseKey.tmp (PID: 3664)
- AutoMouseKey.exe (PID: 2952)
Checks supported languages
- AutoMouseKey.exe (PID: 864)
- AutoMouseKey.exe (PID: 1008)
- AutoMouseKey.tmp (PID: 2456)
- AutoMouseKey.tmp (PID: 3664)
- AutoMouseKey.exe (PID: 2952)
Reads the computer name
- AutoMouseKey.tmp (PID: 2456)
- AutoMouseKey.tmp (PID: 3664)
- AutoMouseKey.exe (PID: 2952)
Reads Windows owner or organization settings
- AutoMouseKey.tmp (PID: 3664)
Reads the Windows organization settings
- AutoMouseKey.tmp (PID: 3664)
Drops a file that was compiled in debug mode
- AutoMouseKey.tmp (PID: 3664)
- AutoMouseKey.exe (PID: 2952)
Changes default file association
- AutoMouseKey.tmp (PID: 3664)
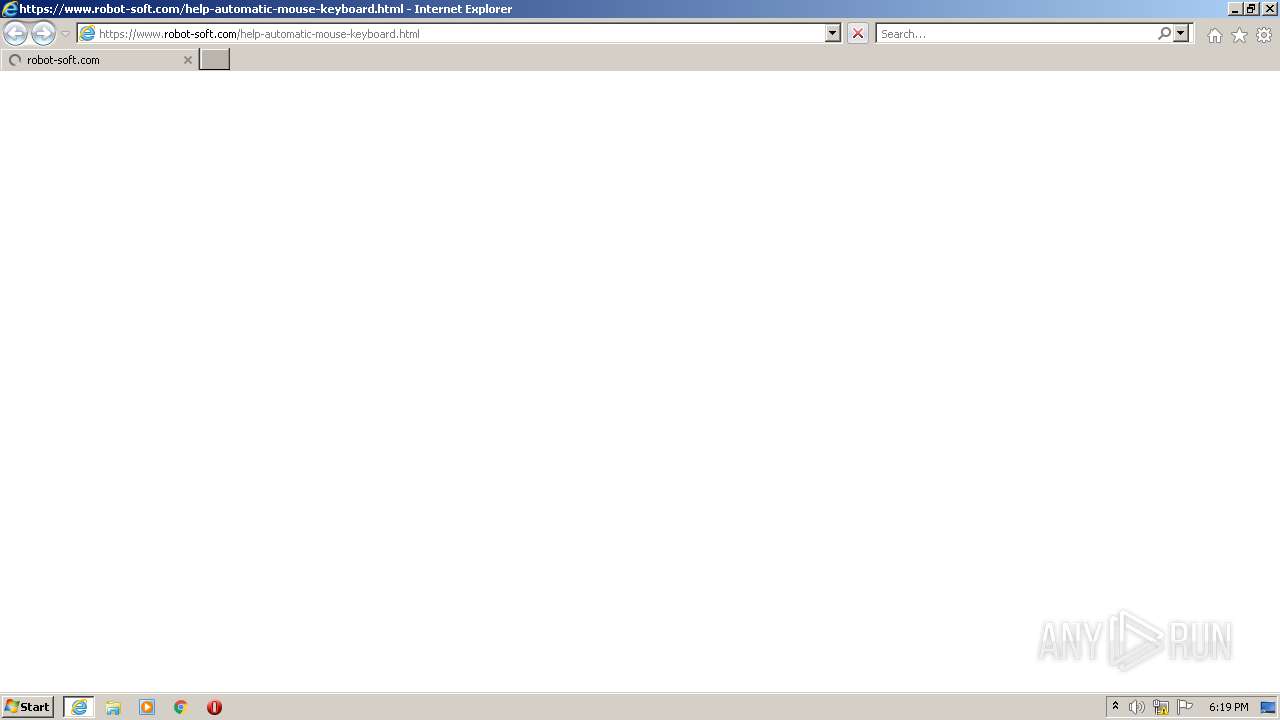
Starts Internet Explorer
- AutoMouseKey.tmp (PID: 2456)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3852)
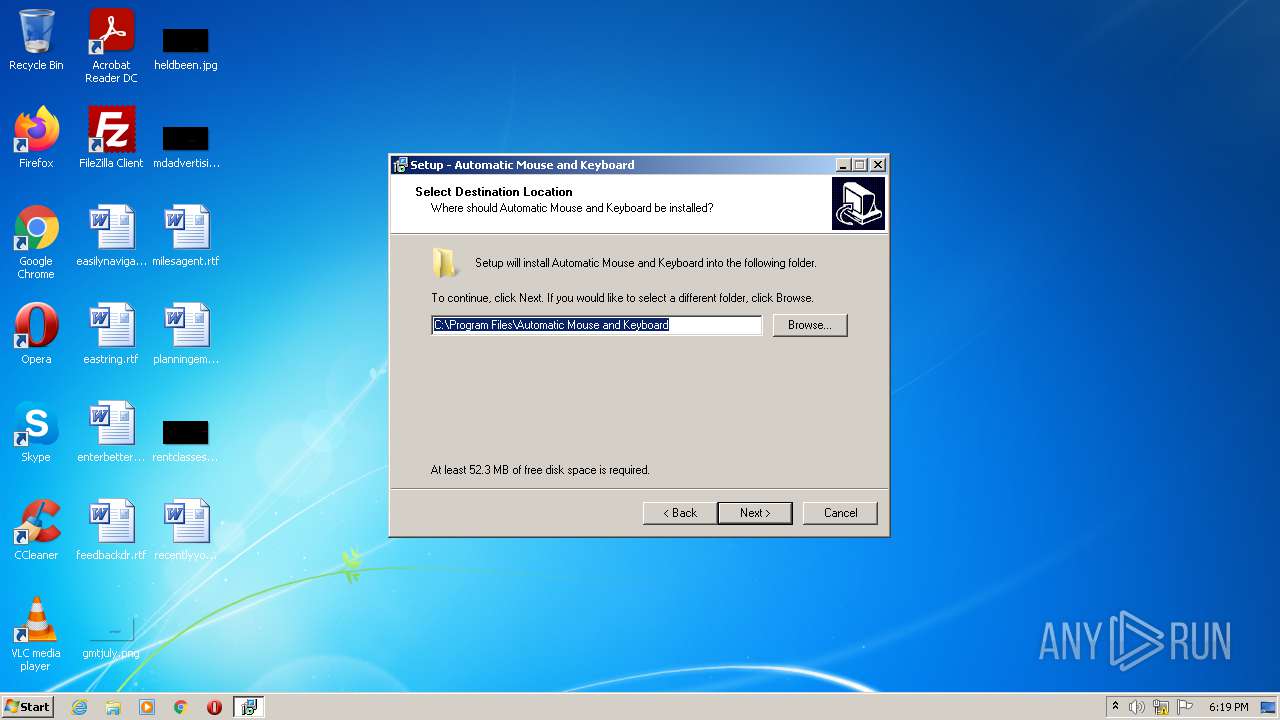
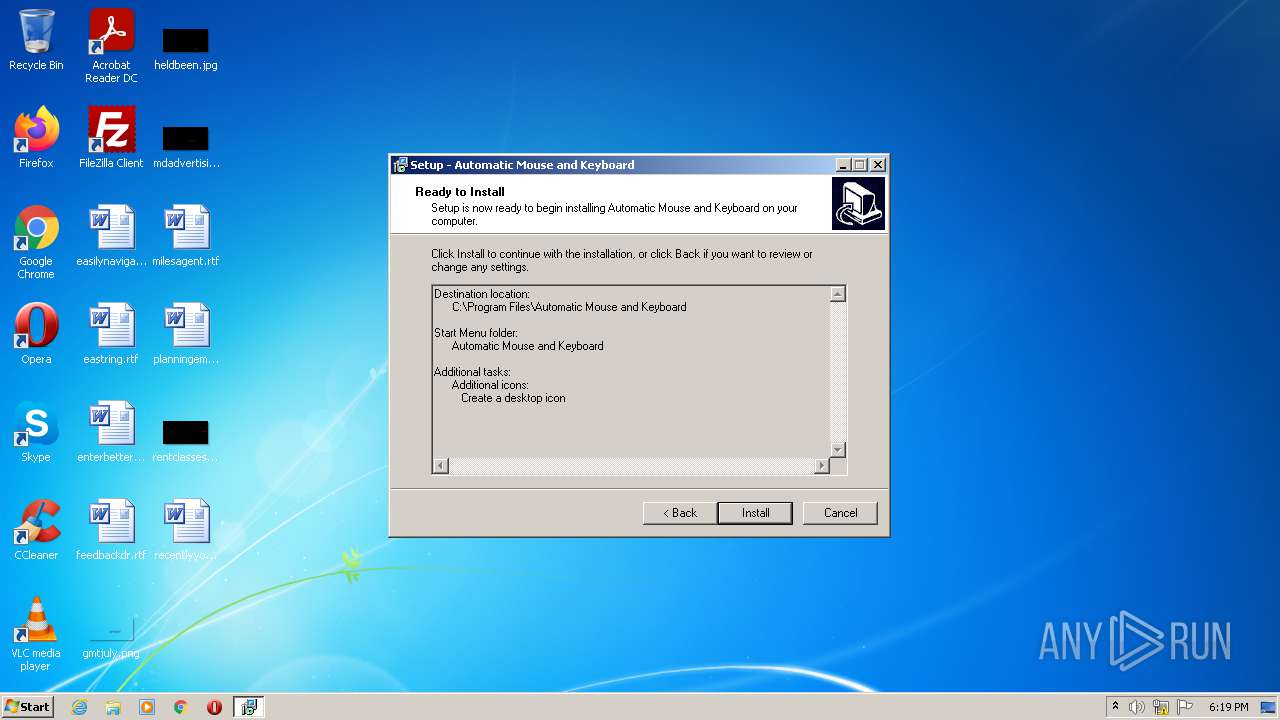
Creates a directory in Program Files
- AutoMouseKey.tmp (PID: 3664)
Creates files in the user directory
- AutoMouseKey.exe (PID: 2952)
INFO
Application was dropped or rewritten from another process
- AutoMouseKey.tmp (PID: 2456)
- AutoMouseKey.tmp (PID: 3664)
Loads dropped or rewritten executable
- AutoMouseKey.tmp (PID: 3664)
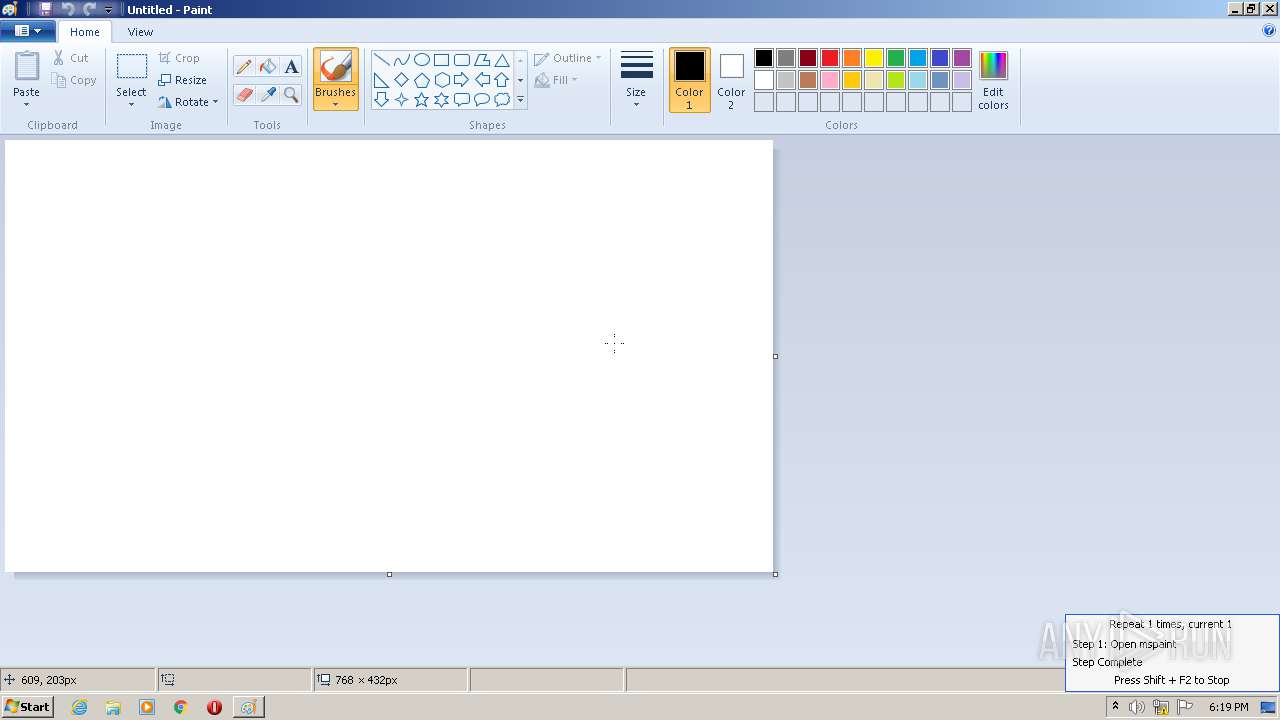
Checks supported languages
- iexplore.exe (PID: 592)
- iexplore.exe (PID: 3852)
- mspaint.exe (PID: 3184)
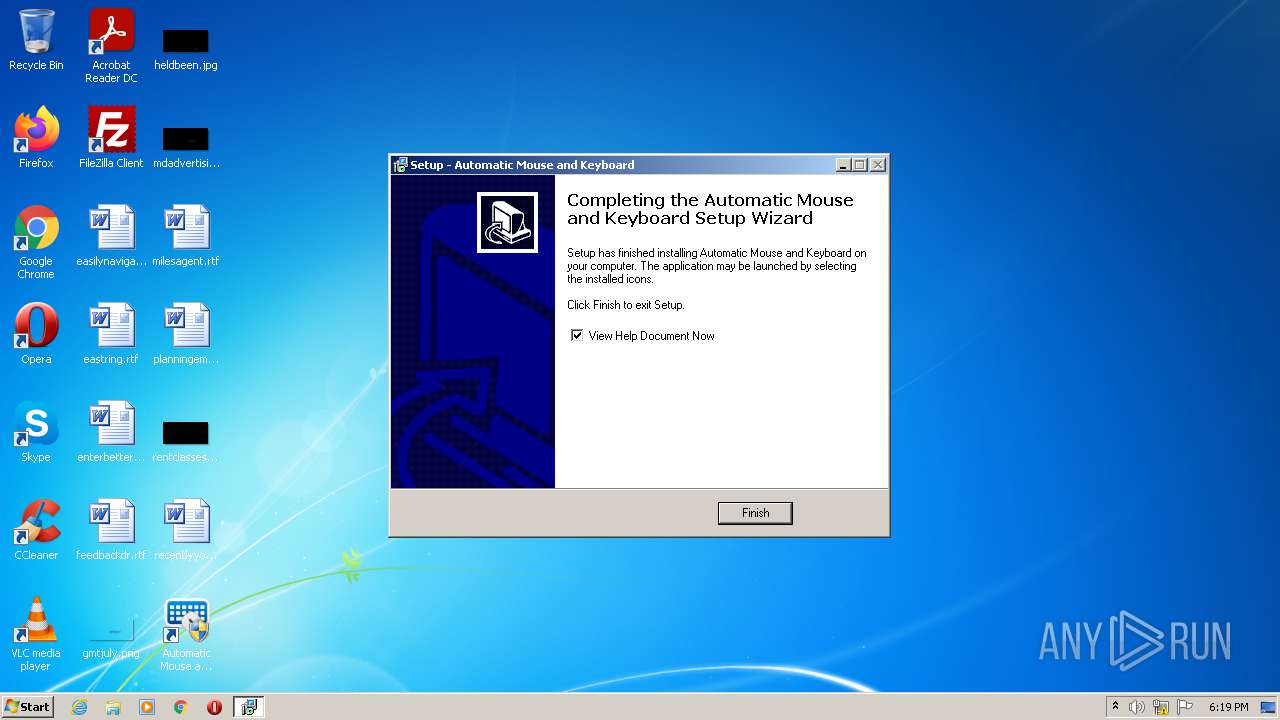
Creates a software uninstall entry
- AutoMouseKey.tmp (PID: 3664)
Reads the computer name
- iexplore.exe (PID: 592)
- iexplore.exe (PID: 3852)
- mspaint.exe (PID: 3184)
Reads settings of System Certificates
- iexplore.exe (PID: 3852)
Changes internet zones settings
- iexplore.exe (PID: 592)
Application launched itself
- iexplore.exe (PID: 592)
Checks Windows Trust Settings
- iexplore.exe (PID: 3852)
Reads internet explorer settings
- iexplore.exe (PID: 3852)
Reads the date of Windows installation
- iexplore.exe (PID: 592)
Creates files in the program directory
- AutoMouseKey.tmp (PID: 3664)
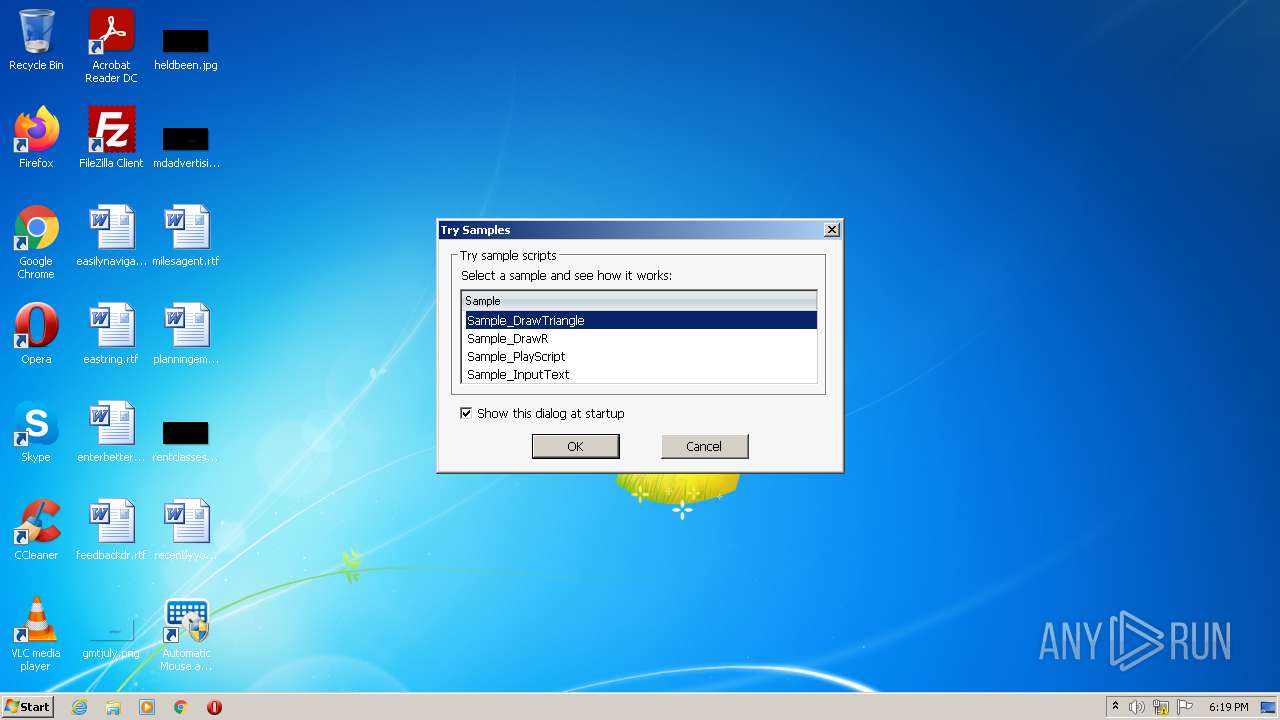
Manual execution by user
- AutoMouseKey.exe (PID: 1008)
- AutoMouseKey.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
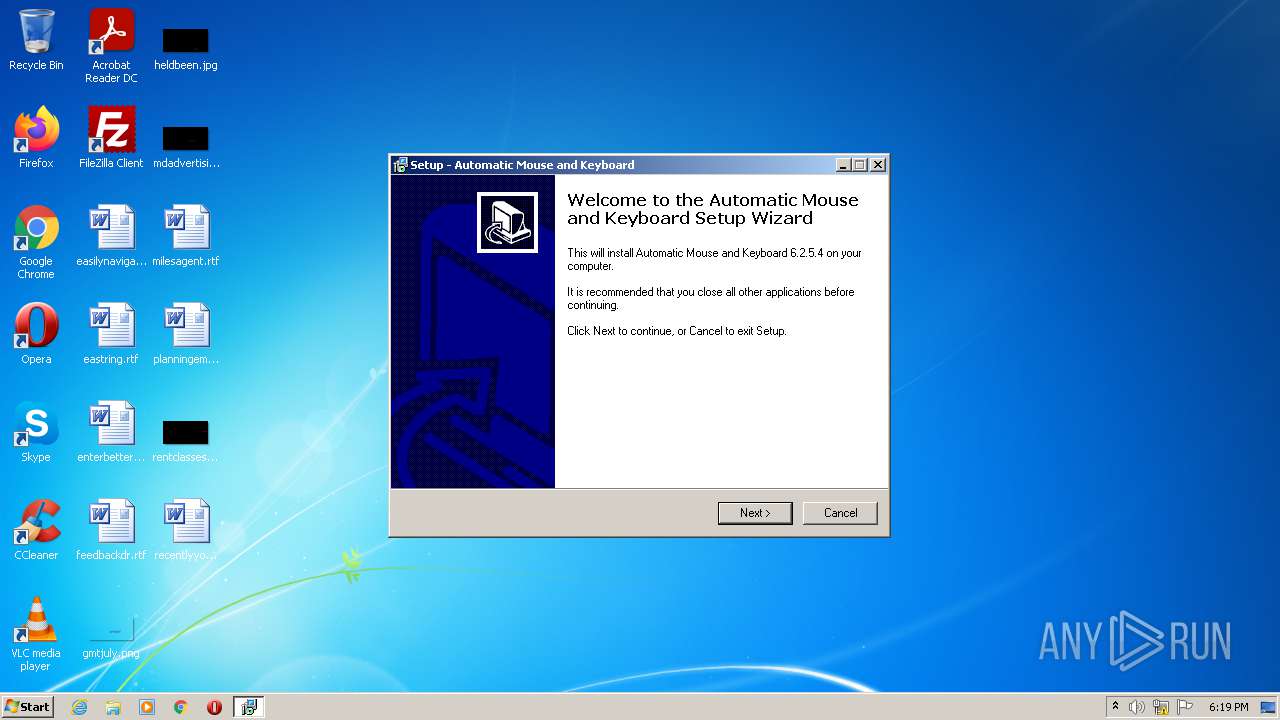
| ProductVersion: | 6.2.5.4 |
|---|---|
| ProductName: | Automatic Mouse and Keyboard |
| LegalCopyright: | |
| FileVersion: | 6.2.5.4 |
| FileDescription: | Automatic Mouse and Keyboard Setup |
| CompanyName: | Robot-Soft.com, Inc. |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 6.2.5.4 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 1 |
| EntryPoint: | 0x9a58 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 17408 |
| CodeSize: | 37376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Robot-Soft.com, Inc. |
| FileDescription: | Automatic Mouse and Keyboard Setup |
| FileVersion: | 6.2.5.4 |
| LegalCopyright: | - |
| ProductName: | Automatic Mouse and Keyboard |
| ProductVersion: | 6.2.5.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009174 | 0x00009200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56625 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73508 |
BSS | 0x0000C000 | 0x00000E48 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002A00 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.50488 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94378 | 1150 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
50
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.robot-soft.com/help-automatic-mouse-keyboard.html | C:\Program Files\Internet Explorer\iexplore.exe | — | AutoMouseKey.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 864 | "C:\Users\admin\AppData\Local\Temp\AutoMouseKey.exe" | C:\Users\admin\AppData\Local\Temp\AutoMouseKey.exe | Explorer.EXE | ||||||||||||
User: admin Company: Robot-Soft.com, Inc. Integrity Level: MEDIUM Description: Automatic Mouse and Keyboard Setup Exit code: 0 Version: 6.2.5.4 Modules
| |||||||||||||||
| 1008 | "C:\Users\admin\AppData\Local\Temp\AutoMouseKey.exe" /SPAWNWND=$8015C /NOTIFYWND=$60162 | C:\Users\admin\AppData\Local\Temp\AutoMouseKey.exe | AutoMouseKey.tmp | ||||||||||||
User: admin Company: Robot-Soft.com, Inc. Integrity Level: HIGH Description: Automatic Mouse and Keyboard Setup Exit code: 0 Version: 6.2.5.4 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Automatic Mouse and Keyboard\AutoMouseKey.exe" | C:\Program Files\Automatic Mouse and Keyboard\AutoMouseKey.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Robot Soft, www.robot-soft.com Integrity Level: MEDIUM Description: Automatic Mouse and Keyboard Exit code: 3221226540 Version: 6.2.5.4 Modules
| |||||||||||||||
| 2456 | "C:\Users\admin\AppData\Local\Temp\is-S6G7D.tmp\AutoMouseKey.tmp" /SL5="$60162,4325841,53248,C:\Users\admin\AppData\Local\Temp\AutoMouseKey.exe" | C:\Users\admin\AppData\Local\Temp\is-S6G7D.tmp\AutoMouseKey.tmp | — | AutoMouseKey.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Automatic Mouse and Keyboard\AutoMouseKey.exe" | C:\Program Files\Automatic Mouse and Keyboard\AutoMouseKey.exe | Explorer.EXE | ||||||||||||
User: admin Company: Robot Soft, www.robot-soft.com Integrity Level: HIGH Description: Automatic Mouse and Keyboard Exit code: 0 Version: 6.2.5.4 Modules
| |||||||||||||||
| 3184 | "C:\Windows\System32\mspaint.exe" | C:\Windows\System32\mspaint.exe | — | AutoMouseKey.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Paint Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3664 | "C:\Users\admin\AppData\Local\Temp\is-LK8TR.tmp\AutoMouseKey.tmp" /SL5="$7015E,4325841,53248,C:\Users\admin\AppData\Local\Temp\AutoMouseKey.exe" /SPAWNWND=$8015C /NOTIFYWND=$60162 | C:\Users\admin\AppData\Local\Temp\is-LK8TR.tmp\AutoMouseKey.tmp | AutoMouseKey.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 3852 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:592 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
10 077
Read events
9 956
Write events
119
Delete events
2
Modification events
| (PID) Process: | (3664) AutoMouseKey.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Robot Soft Action Script File |
| Operation: | write | Name: | (default) |
Value: Robot Soft Action Script File | |||
| (PID) Process: | (3664) AutoMouseKey.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Robot Soft Action Script File\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Automatic Mouse and Keyboard\AutoMouseKey.exe,0 | |||
| (PID) Process: | (3664) AutoMouseKey.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Robot Soft Action Script File\shell\open\command |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Automatic Mouse and Keyboard\AutoMouseKey.exe %1 | |||
| (PID) Process: | (3664) AutoMouseKey.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.amk |
| Operation: | write | Name: | (default) |
Value: Robot Soft Action Script File | |||
| (PID) Process: | (3664) AutoMouseKey.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.amk\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Automatic Mouse and Keyboard\AutoMouseKey.exe,0 | |||
| (PID) Process: | (3664) AutoMouseKey.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{BFD646B6-E892-4B00-B6E2-71545D92BAEA}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.2.3 | |||
| (PID) Process: | (3664) AutoMouseKey.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{BFD646B6-E892-4B00-B6E2-71545D92BAEA}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Automatic Mouse and Keyboard | |||
| (PID) Process: | (3664) AutoMouseKey.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{BFD646B6-E892-4B00-B6E2-71545D92BAEA}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Automatic Mouse and Keyboard\ | |||
| (PID) Process: | (3664) AutoMouseKey.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{BFD646B6-E892-4B00-B6E2-71545D92BAEA}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Automatic Mouse and Keyboard | |||
| (PID) Process: | (3664) AutoMouseKey.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{BFD646B6-E892-4B00-B6E2-71545D92BAEA}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
33
Suspicious files
10
Text files
151
Unknown types
114
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3664 | AutoMouseKey.tmp | C:\Program Files\Automatic Mouse and Keyboard\is-J1VS8.tmp | executable | |
MD5:— | SHA256:— | |||
| 3664 | AutoMouseKey.tmp | C:\Program Files\Automatic Mouse and Keyboard\AutoMouseKey.exe | executable | |
MD5:— | SHA256:— | |||
| 3664 | AutoMouseKey.tmp | C:\Program Files\Automatic Mouse and Keyboard\AutoHotkey.exe | executable | |
MD5:— | SHA256:— | |||
| 3664 | AutoMouseKey.tmp | C:\Program Files\Automatic Mouse and Keyboard\is-TO55S.tmp | executable | |
MD5:— | SHA256:— | |||
| 3664 | AutoMouseKey.tmp | C:\Program Files\Automatic Mouse and Keyboard\is-N0CJ4.tmp | executable | |
MD5:— | SHA256:— | |||
| 3664 | AutoMouseKey.tmp | C:\Program Files\Automatic Mouse and Keyboard\build.dat | executable | |
MD5:— | SHA256:— | |||
| 3664 | AutoMouseKey.tmp | C:\Program Files\Automatic Mouse and Keyboard\is-RM54R.tmp | executable | |
MD5:— | SHA256:— | |||
| 3664 | AutoMouseKey.tmp | C:\Program Files\Automatic Mouse and Keyboard\is-O56U8.tmp | executable | |
MD5:— | SHA256:— | |||
| 3664 | AutoMouseKey.tmp | C:\Program Files\Automatic Mouse and Keyboard\KeyPresser.exe | executable | |
MD5:— | SHA256:— | |||
| 3664 | AutoMouseKey.tmp | C:\Program Files\Automatic Mouse and Keyboard\MouseClicker.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
13
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3852 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEQDwHUvue3yjezwFZqwFlyRY | US | der | 728 b | whitelisted |
3852 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
3852 | iexplore.exe | GET | 200 | 205.185.216.42:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8b7cb2cf8aa4ce57 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3852 | iexplore.exe | 23.235.219.143:443 | www.robot-soft.com | InMotion Hosting, Inc. | US | unknown |
3852 | iexplore.exe | 205.185.216.42:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3852 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.robot-soft.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |