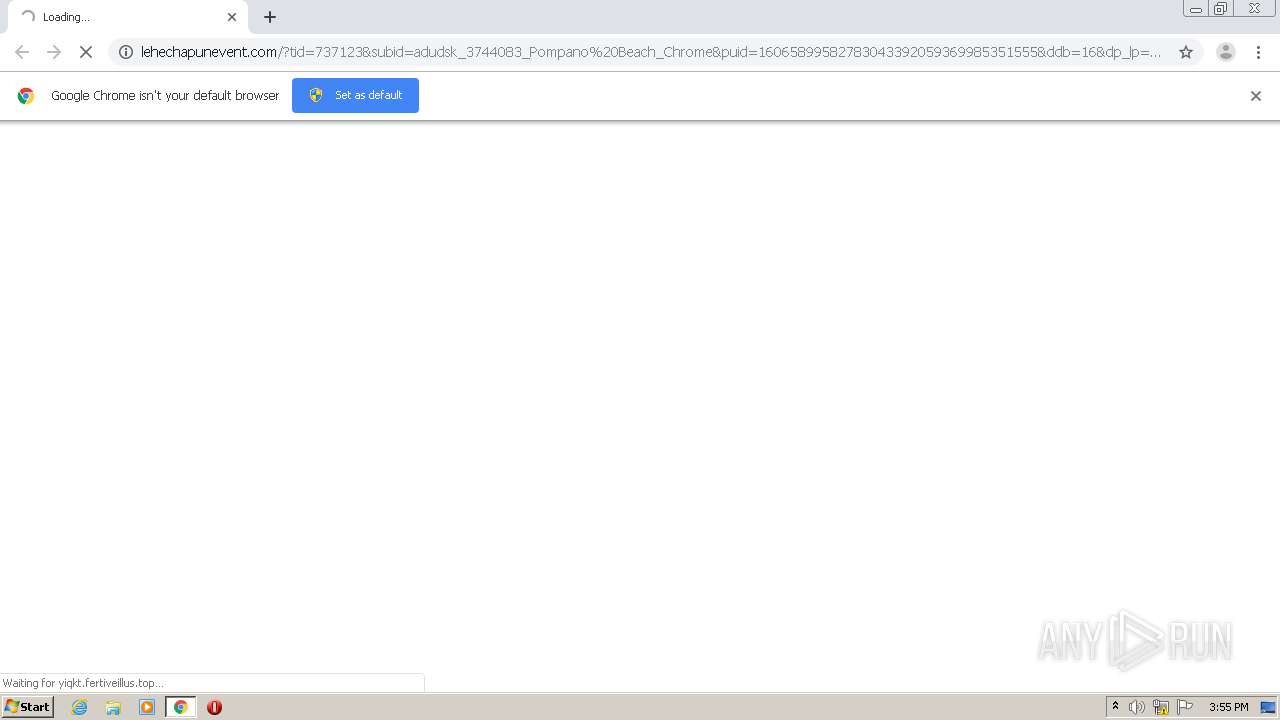
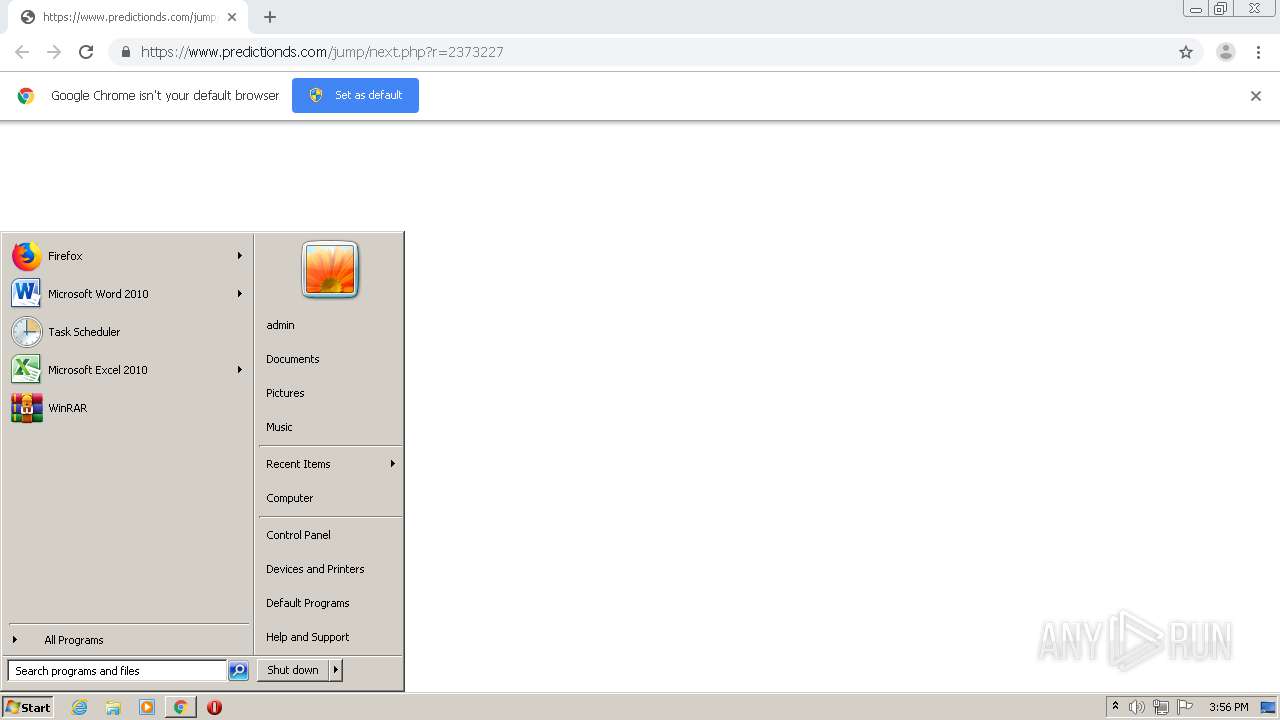
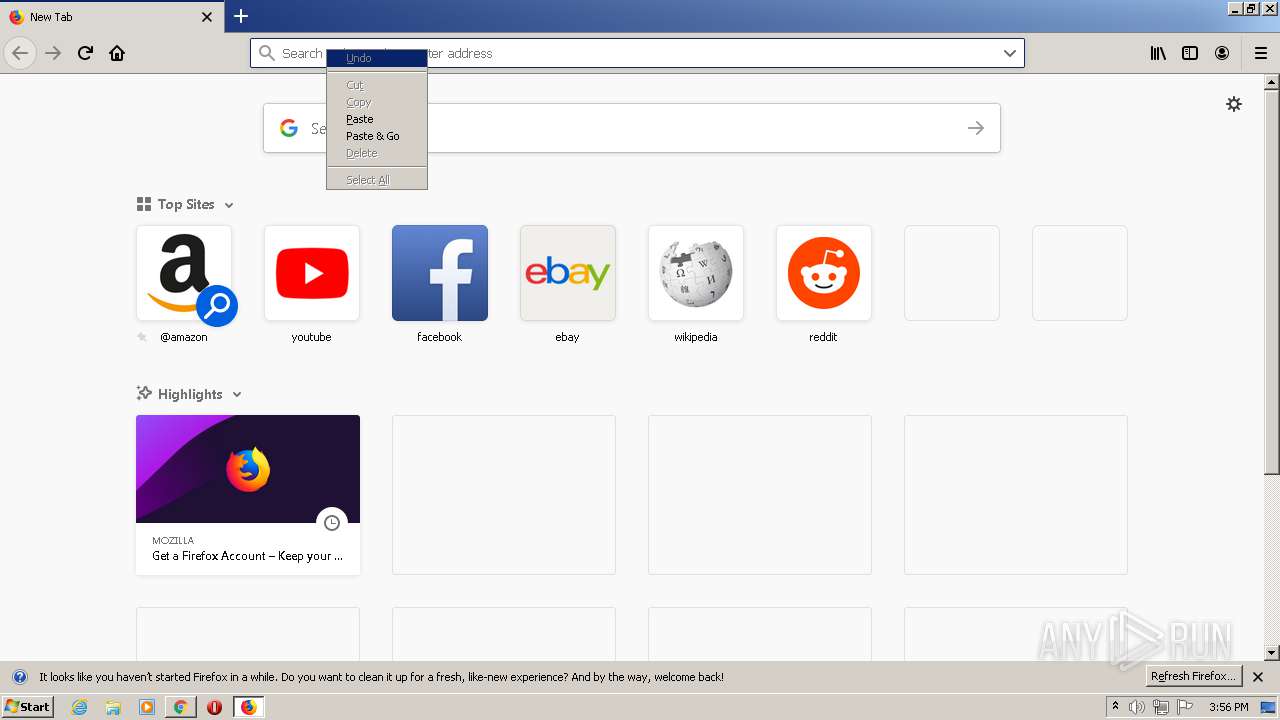
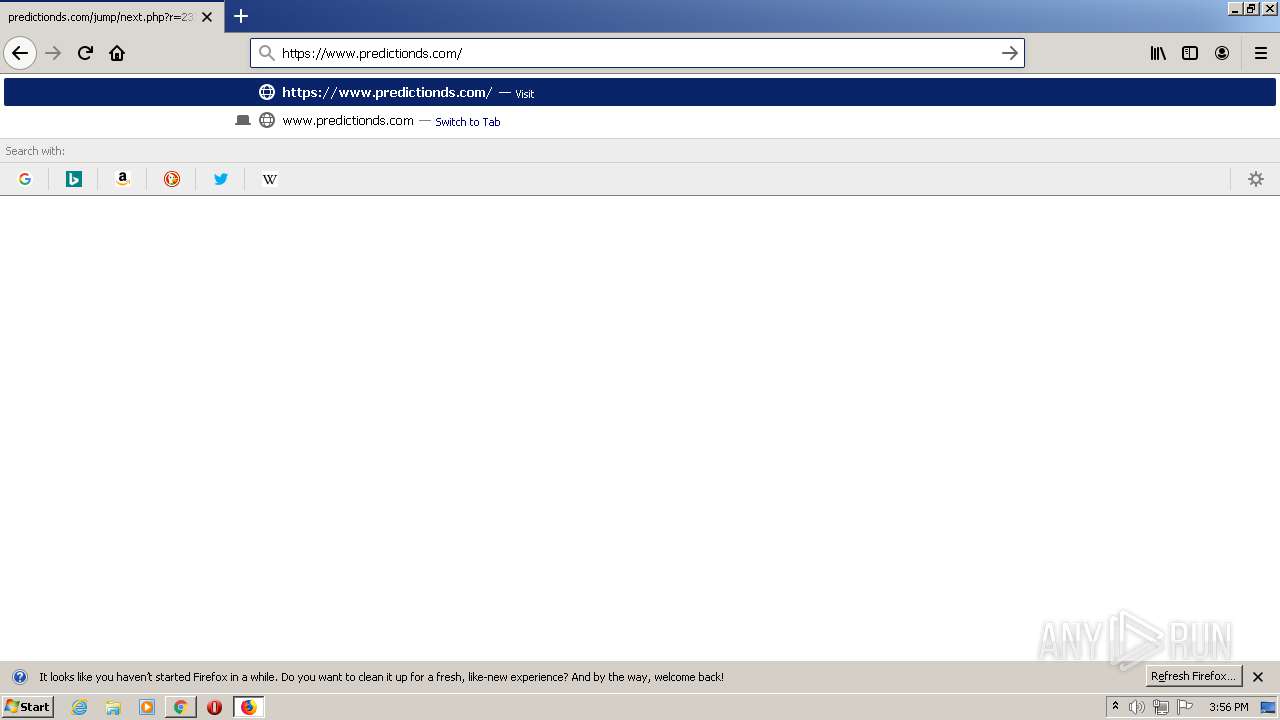
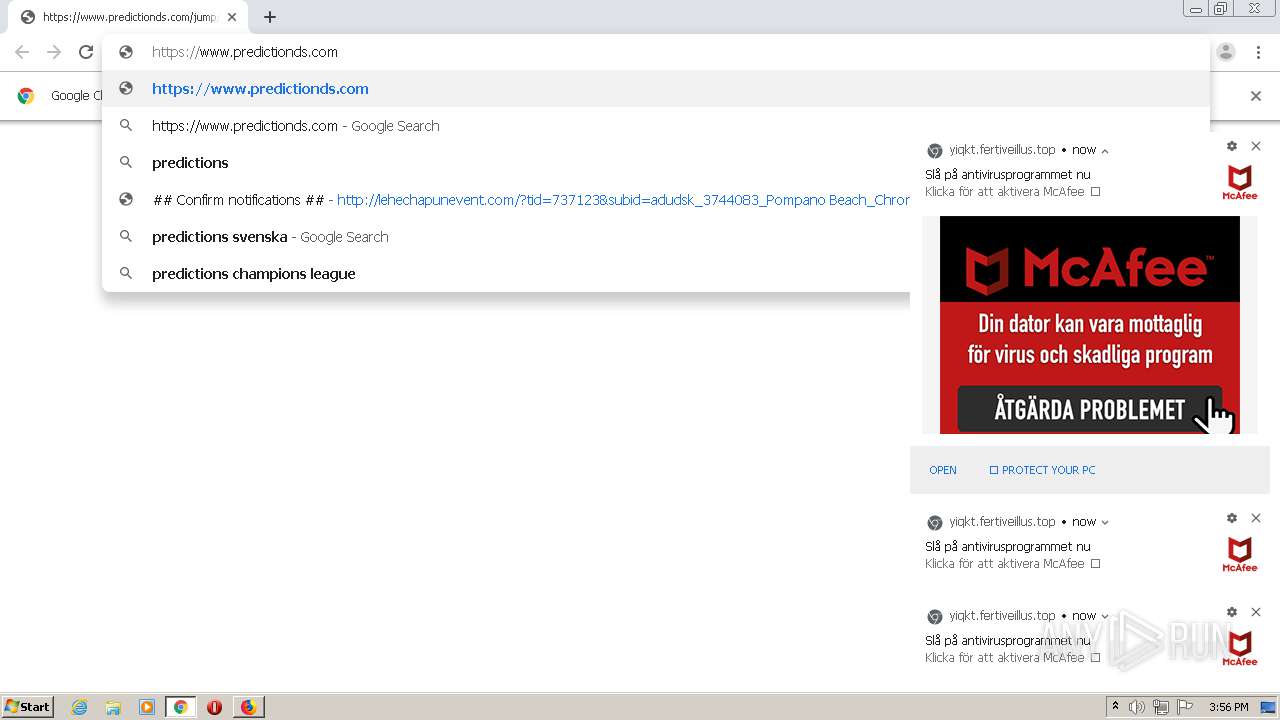
| URL: | http://lehechapunevent.com/?tid=737123&subid=adudsk_3744083_Pompano%20Beach_Chrome&puid=16065899582783043392059369985351555&ddb=16&dp_lp=oct_52&dp_hop=6&dp_ob=redirect&dp_allb=redirect&dp_href=https://www.predictionds.com/jump/next.php?r=2373227&sub1=[WEBSITEID |
| Full analysis: | https://app.any.run/tasks/1f9cdd4d-46a0-4a7a-a1da-ed23ee1e656d |
| Verdict: | Malicious activity |
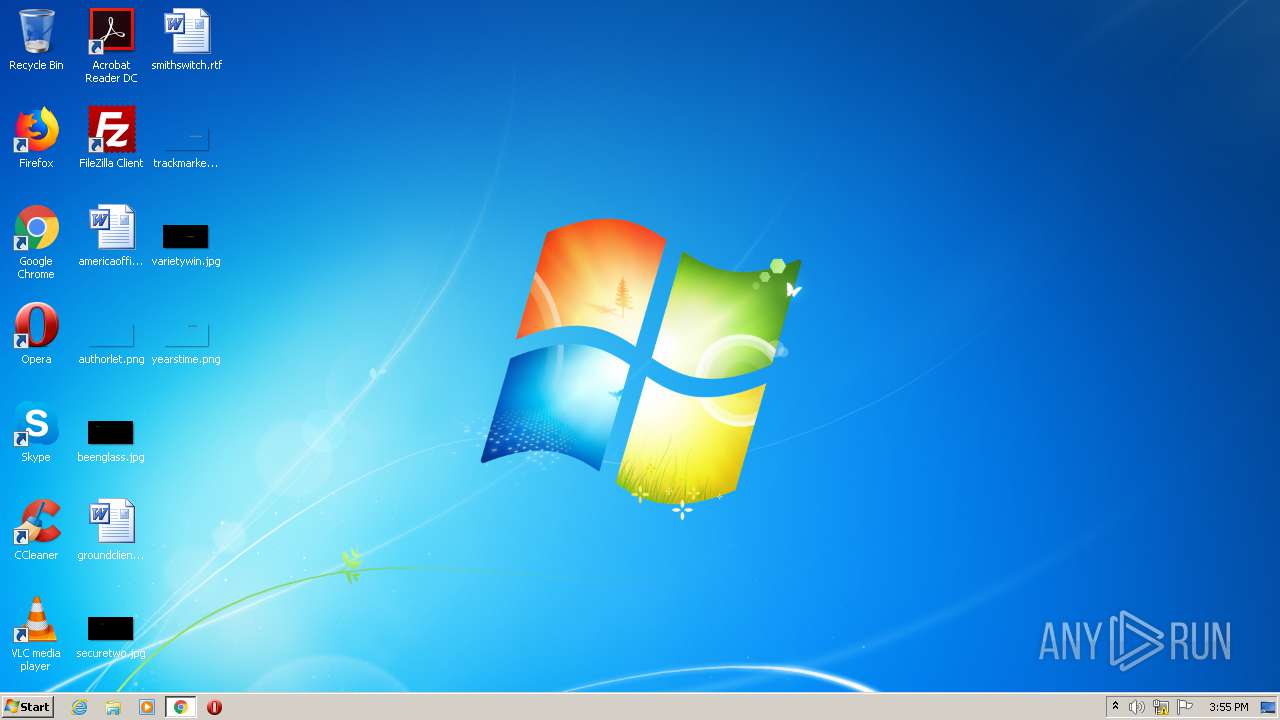
| Analysis date: | November 29, 2020, 15:55:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F747F56370409C1D1334281BE92005BD |
| SHA1: | 1A8EA1236F8BA77EE86FF4EE85BE5DE1EFE174AE |
| SHA256: | 12A91042FE716F817B7D5986549B8D7837F271C762FE5CFC2E65A7447CEAAB0D |
| SSDEEP: | 6:CSkEugKqkgaMRFYwCuj3hm3XrGLvGqctRaA:tRKqEMReUmJqcyA |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2668)
- chrome.exe (PID: 1228)
Application launched itself
- firefox.exe (PID: 1916)
- firefox.exe (PID: 2592)
- chrome.exe (PID: 1228)
Reads CPU info
- firefox.exe (PID: 1916)
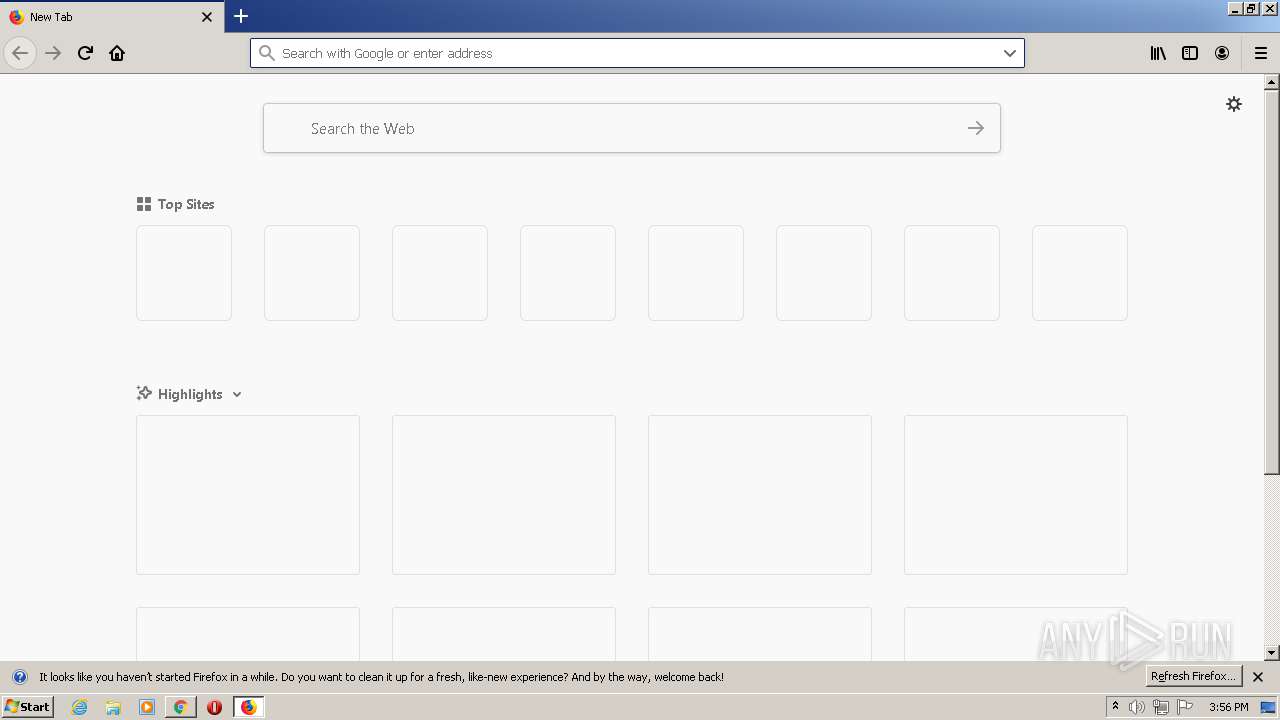
Manual execution by user
- firefox.exe (PID: 2592)
Creates files in the program directory
- firefox.exe (PID: 1916)
Creates files in the user directory
- firefox.exe (PID: 1916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,7739284439634895059,9254845884917453205,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5181748248029726650 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
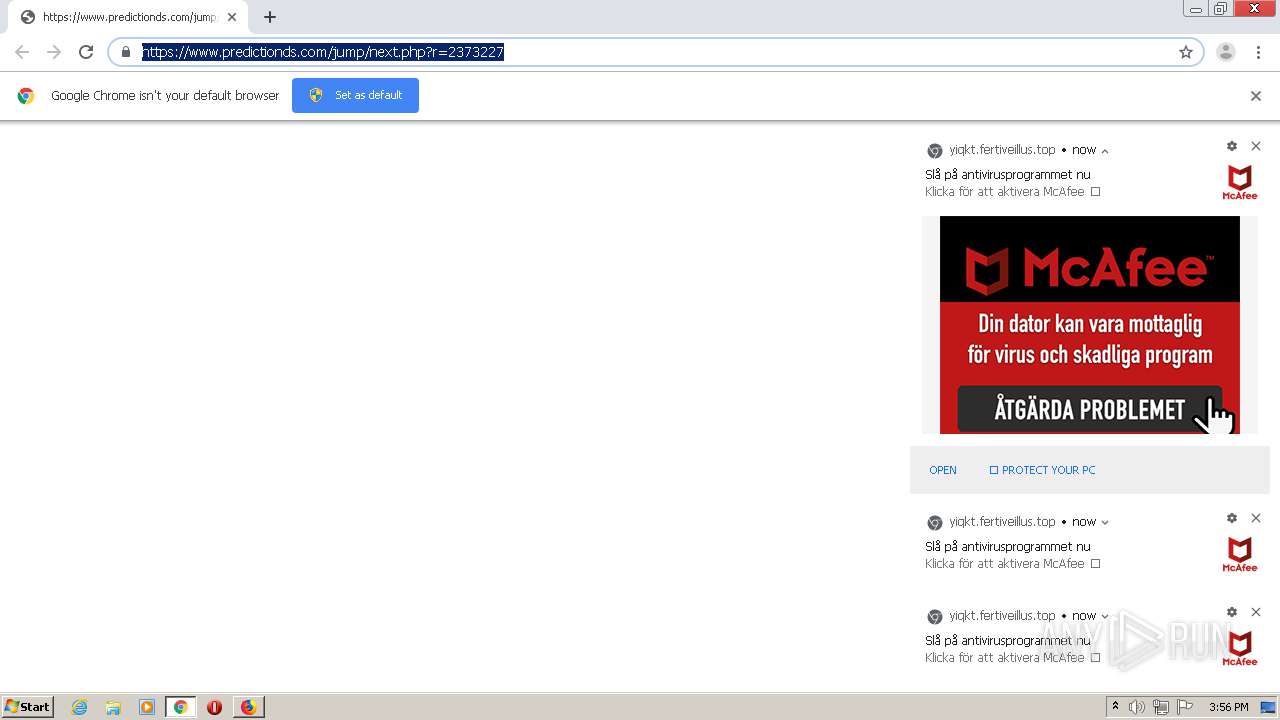
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://lehechapunevent.com/?tid=737123&subid=adudsk_3744083_Pompano%20Beach_Chrome&puid=16065899582783043392059369985351555&ddb=16&dp_lp=oct_52&dp_hop=6&dp_ob=redirect&dp_allb=redirect&dp_href=https://www.predictionds.com/jump/next.php?r=2373227&sub1=[WEBSITEID" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1916.3.487649633\1282036904" -childID 1 -isForBrowser -prefsHandle 1732 -prefMapHandle 1728 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1916 "\\.\pipe\gecko-crash-server-pipe.1916" 1752 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,7739284439634895059,9254845884917453205,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4241560644551453918 --mojo-platform-channel-handle=3632 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,7739284439634895059,9254845884917453205,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7265517237102227628 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3560 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,7739284439634895059,9254845884917453205,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4375039587854766695 --mojo-platform-channel-handle=2408 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,7739284439634895059,9254845884917453205,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7865195455006087438 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2716 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 058
Read events
997
Write events
58
Delete events
3
Modification events
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1228-13251138937192875 |
Value: 259 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1228-13251138937192875 |
Value: 259 | |||
Executable files
0
Suspicious files
71
Text files
109
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC3C479-4CC.pma | — | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\486b7253-a460-4f7e-8180-374e86b2887b.tmp | — | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF18d339.TMP | text | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF18d358.TMP | text | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF18d4ef.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
49
DNS requests
86
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
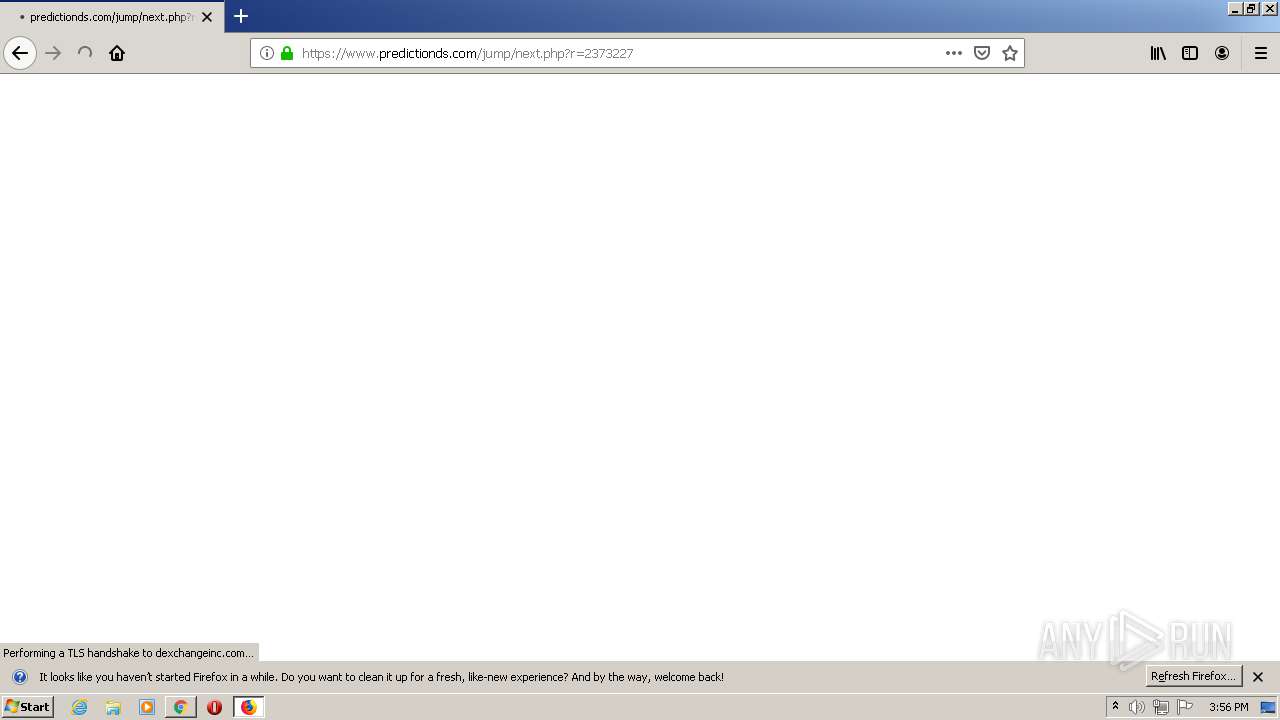
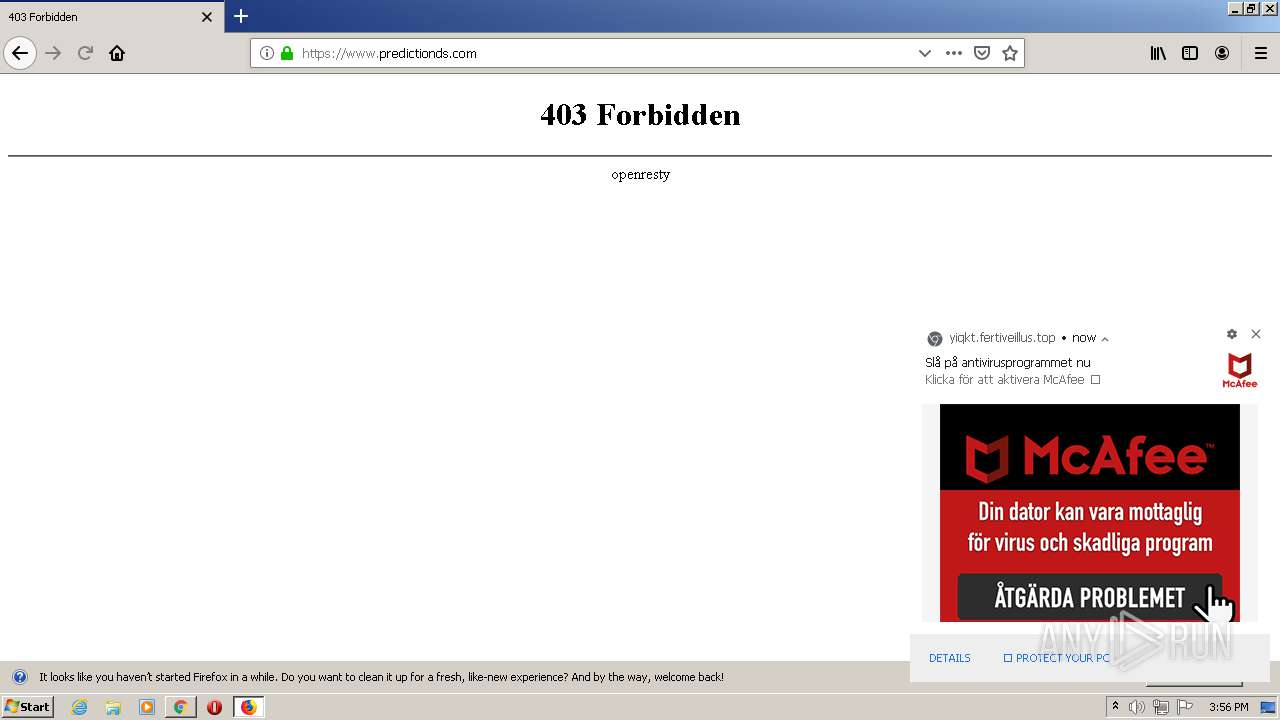
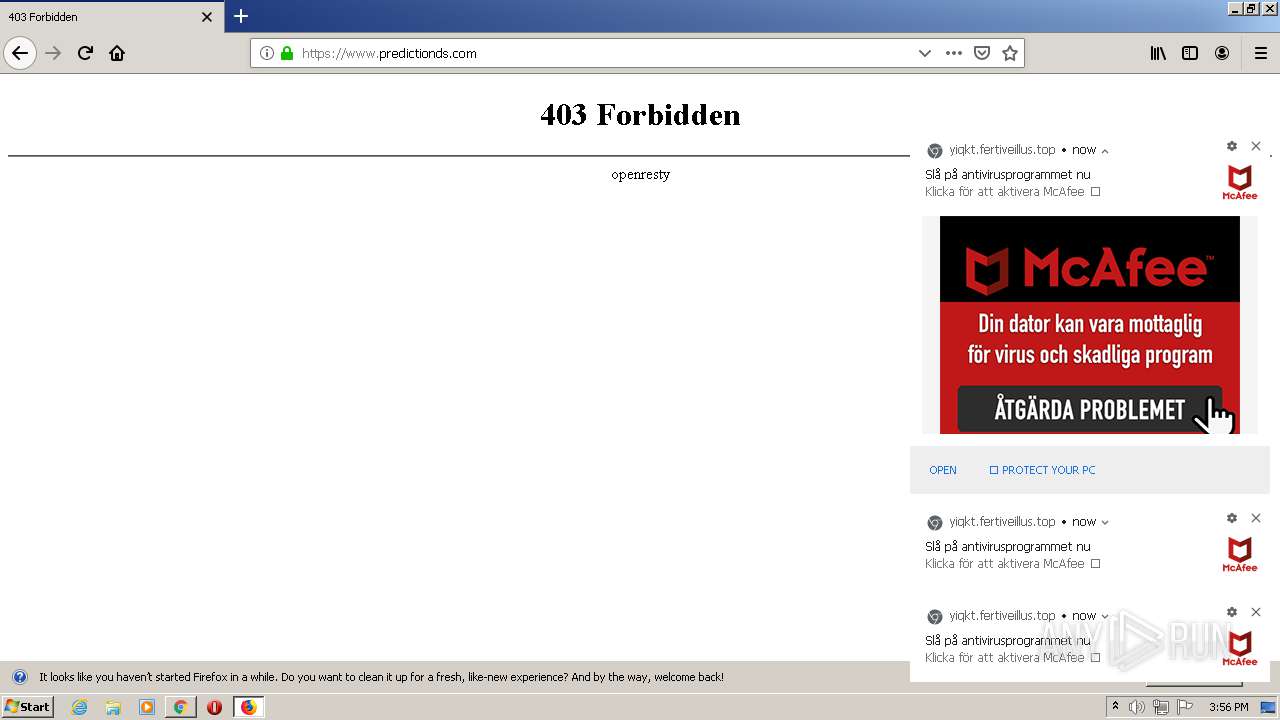
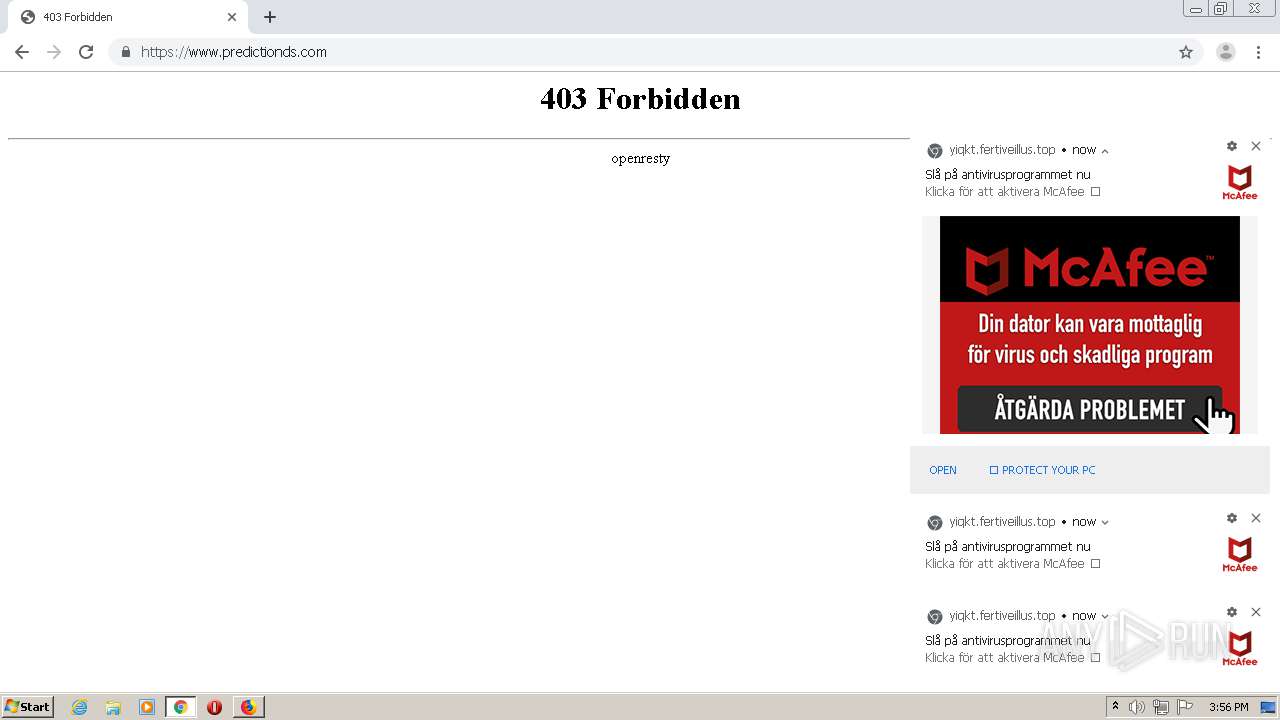
— | — | GET | 302 | 13.225.73.4:80 | http://lehechapunevent.com/?tid=737123&subid=adudsk_3744083_Pompano%20Beach_Chrome&puid=16065899582783043392059369985351555&ddb=16&dp_lp=oct_52&dp_hop=6&dp_ob=redirect&dp_allb=redirect&dp_href=https://www.predictionds.com/jump/next.php?r=2373227&sub1=[WEBSITEID | US | — | — | malicious |
1916 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1916 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
1916 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/ | US | der | 472 b | whitelisted |
1916 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/ | US | der | 472 b | whitelisted |
1916 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1916 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1916 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
1916 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1916 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2668 | chrome.exe | 142.250.64.77:443 | accounts.google.com | Google Inc. | US | unknown |
— | — | 13.225.73.4:80 | lehechapunevent.com | — | US | unknown |
2668 | chrome.exe | 13.225.73.4:80 | lehechapunevent.com | — | US | unknown |
2668 | chrome.exe | 65.9.68.93:443 | astancerta.fun | AT&T Services, Inc. | US | unknown |
2668 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2668 | chrome.exe | 216.58.212.142:443 | android.clients.google.com | Google Inc. | US | whitelisted |
2668 | chrome.exe | 35.190.90.57:443 | www.predictionds.com | Google Inc. | US | whitelisted |
2668 | chrome.exe | 35.201.117.228:443 | dexchangeinc.com | Google Inc. | US | unknown |
2668 | chrome.exe | 65.9.68.122:443 | astancerta.fun | AT&T Services, Inc. | US | malicious |
1916 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lehechapunevent.com |
| malicious |
accounts.google.com |
| shared |
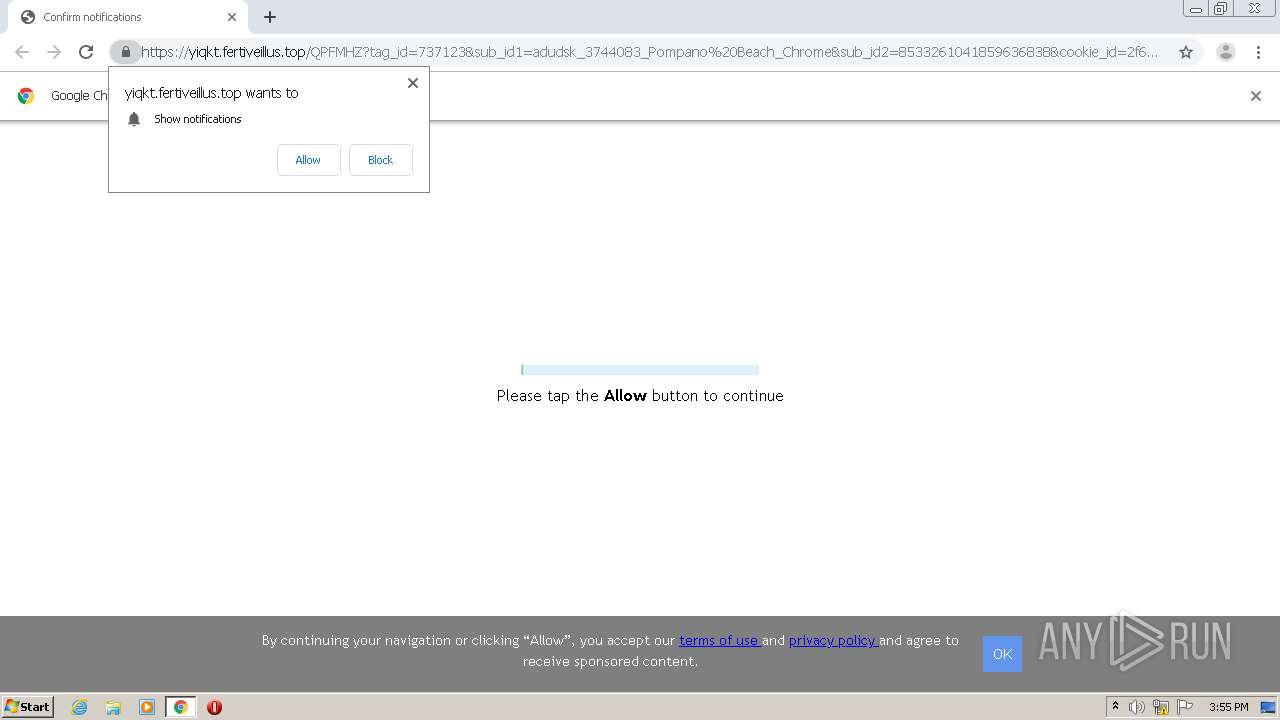
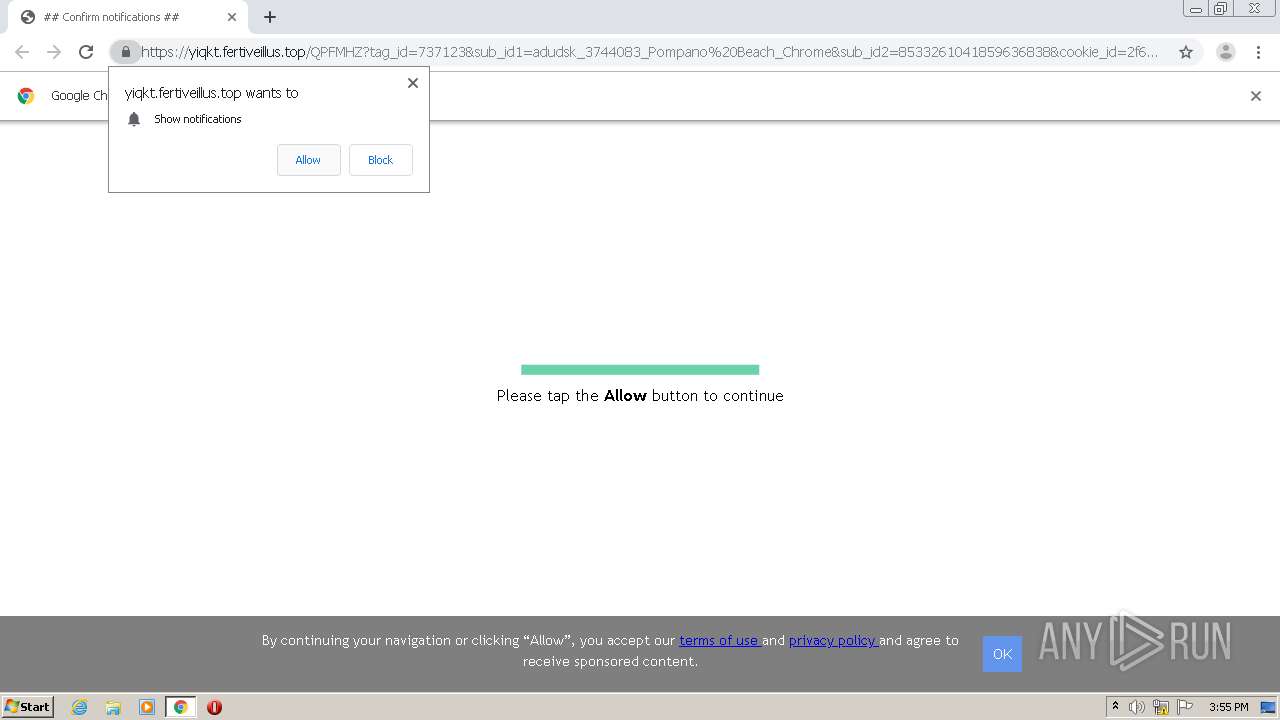
yiqkt.fertiveillus.top |
| shared |
astancerta.fun |
| malicious |
ssl.gstatic.com |
| whitelisted |
android.clients.google.com |
| whitelisted |
mtalk.google.com |
| whitelisted |
www.predictionds.com |
| malicious |
dexchangeinc.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |