| File name: | 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e |
| Full analysis: | https://app.any.run/tasks/7bca76ca-d2ef-4725-9d1a-a88fa53dc842 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 07:52:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B3E81FD49AB8C73B101EC02B9AEAFC00 |
| SHA1: | 4FC14EAD6A4996883A46DAB1A3A4E54C3420467E |
| SHA256: | 12A54576C35878B5E947863D449B3D15CFD03A4AD9799DF87B9AA5D8F185EA4E |
| SSDEEP: | 98304:XtIvyybrQFxly63twEQnl/HubgBmkfEaqM5nMJeYA:XtIvgln35kl/O8BmksaqYieYA |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- uiso.tmp (PID: 272)
Application was dropped or rewritten from another process
- uiso.exe (PID: 532)
- isocmd.exe (PID: 2172)
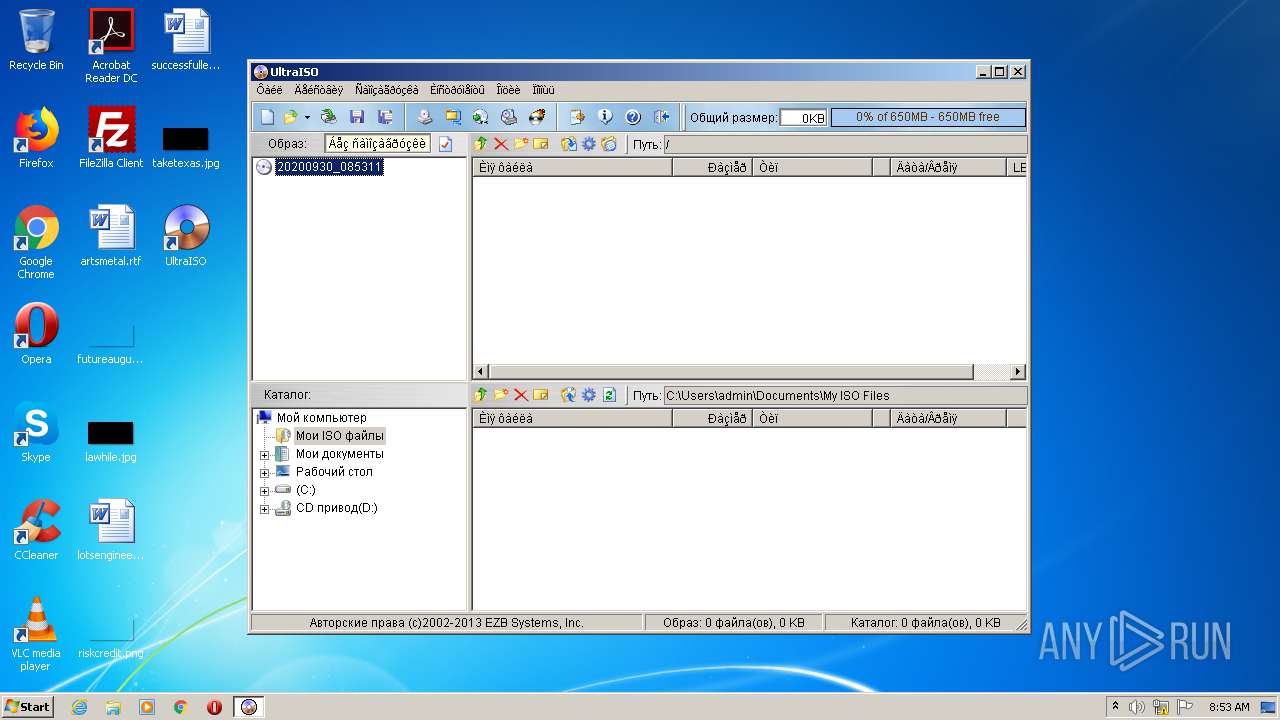
- UltraISO.exe (PID: 3380)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2244)
- UltraISO.exe (PID: 3380)
SUSPICIOUS
Application launched itself
- 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe (PID: 3200)
Executable content was dropped or overwritten
- 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe (PID: 1076)
- uiso.exe (PID: 532)
- uiso.tmp (PID: 272)
Modifies the open verb of a shell class
- uiso.tmp (PID: 272)
Creates COM task schedule object
- regsvr32.exe (PID: 2244)
Creates files in the program directory
- xcopy.exe (PID: 2916)
Uses REG.EXE to modify Windows registry
- 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe (PID: 1076)
INFO
Application was dropped or rewritten from another process
- uiso.tmp (PID: 272)
Creates a software uninstall entry
- uiso.tmp (PID: 272)
Loads dropped or rewritten executable
- uiso.tmp (PID: 272)
Manual execution by user
- UltraISO.exe (PID: 3380)
Creates files in the program directory
- uiso.tmp (PID: 272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:31 01:38:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 89600 |
| InitializedDataSize: | 37376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1638f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.6.0.3000 |
| ProductVersionNumber: | 9.6.0.3000 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | БЕЛOFF |
| FileDescription: | UltraISO Premium Edition |
| FileVersion: | 9.6.0.3000 |
| InternalName: | UltraISO |
| LegalCopyright: | Copyright © 2002-2014 EZB Systems, Inc. All rights reserved |
| OriginalFileName: | UltraISO.exe |
| PrivateBuild: | 21.11.2013 |
| ProductName: | UltraISO |
| ProductVersion: | 9.6.0.3000 |
| Comments: | Handle CD and DVD Images with Ease! |
| LegalTrademarks: | EZB Systems, Inc. |
| SpecialBuild: | 21.11.2013 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Dec-2012 00:38:38 |
| Detected languages: |
|
| CompanyName: | БЕЛOFF |
| FileDescription: | UltraISO Premium Edition |
| FileVersion: | 9.6.0.3000 |
| InternalName: | UltraISO |
| LegalCopyright: | Copyright © 2002-2014 EZB Systems, Inc. All rights reserved |
| OriginalFilename: | UltraISO.exe |
| PrivateBuild: | 21.11.2013 |
| ProductName: | UltraISO |
| ProductVersion: | 9.6.0.3000 |
| Comments: | Handle CD and DVD Images with Ease! |
| LegalTrademarks: | EZB Systems, Inc. |
| SpecialBuild: | 21.11.2013 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 31-Dec-2012 00:38:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00015CFE | 0x00015E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6445 |
.rdata | 0x00017000 | 0x00003982 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.70129 |
.data | 0x0001B000 | 0x00004C8C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.35632 |
.rsrc | 0x00020000 | 0x00004DC8 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.70646 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.23138 | 838 | Latin 1 / Western European | English - United States | RT_MANIFEST |
70 | 5.57446 | 9640 | Latin 1 / Western European | Russian - Russia | RT_ICON |
101 | 3.00652 | 62 | Latin 1 / Western European | Russian - Russia | RT_GROUP_ICON |
9710 | 5.66829 | 4264 | Latin 1 / Western European | Russian - Russia | RT_ICON |
13974 | 5.77822 | 2440 | Latin 1 / Western European | Russian - Russia | RT_ICON |
16414 | 4.00844 | 1128 | Latin 1 / Western European | Russian - Russia | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
52
Monitored processes
10
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Users\admin\AppData\Local\Temp\is-QBRF1.tmp\uiso.tmp" /SL5="$190266,3772826,126976,C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\uiso.exe" /VERYSILENT /NORESTART /SP- | C:\Users\admin\AppData\Local\Temp\is-QBRF1.tmp\uiso.tmp | uiso.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 532 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\uiso.exe" /VERYSILENT /NORESTART /SP- | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\uiso.exe | 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe | ||||||||||||
User: admin Company: EZB Systems, Inc. Integrity Level: HIGH Description: UltraISO Setup Exit code: 0 Version: 9.6.0.3000 Modules
| |||||||||||||||
| 1076 | "C:\Users\admin\AppData\Local\Temp\12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe" -sfxelevation | C:\Users\admin\AppData\Local\Temp\12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe | 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe | ||||||||||||
User: admin Company: БЕЛOFF Integrity Level: HIGH Description: UltraISO Premium Edition Exit code: 0 Version: 9.6.0.3000 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\UltraISO\drivers\isocmd.exe" -i | C:\Program Files\UltraISO\drivers\isocmd.exe | — | uiso.tmp | |||||||||||
User: admin Company: EZB Systems, Inc. Integrity Level: HIGH Description: ISO Command Exit code: 0 Version: 3.12 built by: WinDDK Modules
| |||||||||||||||
| 2244 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\UltraISO\isoshell.dll" | C:\Windows\system32\regsvr32.exe | — | uiso.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2276 | "C:\Windows\System32\reg.exe" Add "HKCU\Software\EasyBoot Systems\UltraISO\5.0" /v "Registration" /t REG_SZ /d "e7f1c59087a69bf6ed8eb89e82a5e7fe" /f | C:\Windows\System32\reg.exe | — | 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2916 | "C:\Windows\System32\xcopy.exe" uikey.ini "C:\Program Files\UltraISO" /e /i /y | C:\Windows\System32\xcopy.exe | — | 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3152 | "C:\Windows\System32\reg.exe" Add "HKCU\Software\EasyBoot Systems\UltraISO\5.0" /v "UserName" /t REG_SZ /d "BELOFF" /f | C:\Windows\System32\reg.exe | — | 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3200 | "C:\Users\admin\AppData\Local\Temp\12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe" | C:\Users\admin\AppData\Local\Temp\12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe | — | explorer.exe | |||||||||||
User: admin Company: БЕЛOFF Integrity Level: MEDIUM Description: UltraISO Premium Edition Exit code: 0 Version: 9.6.0.3000 Modules
| |||||||||||||||
| 3380 | "C:\Program Files\UltraISO\UltraISO.exe" | C:\Program Files\UltraISO\UltraISO.exe | — | explorer.exe | |||||||||||
User: admin Company: EZB Systems, Inc. Integrity Level: MEDIUM Description: UltraISO Premium Exit code: 0 Version: 9.6.0.30000 Modules
| |||||||||||||||
Total events
1 126
Read events
906
Write events
214
Delete events
6
Modification events
| (PID) Process: | (3200) 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3200) 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1076) 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1076) 12a54576c35878b5e947863d449b3d15cfd03a4ad9799df87b9aa5d8f185ea4e.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (272) uiso.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 10010000CAF7D0A4FE96D601 | |||
| (PID) Process: | (272) uiso.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 492D0ACCF0C6C8D4773C91F42D2A0FB40F9396CD50CAB5942113D7D1E6489523 | |||
| (PID) Process: | (272) uiso.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (272) uiso.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\UltraISO\UltraISO.exe | |||
| (PID) Process: | (272) uiso.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: BD6898DA23CC788867A3070A6029B4692A9C740BDF5EACEFA719AA1A9D59B37D | |||
| (PID) Process: | (2244) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Drive\shellex\ContextMenuHandlers\UltraISO |
| Operation: | write | Name: | (default) |
Value: {AD392E40-428C-459F-961E-9B147782D099} | |||
Executable files
54
Suspicious files
0
Text files
7
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 272 | uiso.tmp | C:\Program Files\UltraISO\is-L6A49.tmp | — | |
MD5:— | SHA256:— | |||
| 272 | uiso.tmp | C:\Program Files\UltraISO\is-6D57P.tmp | — | |
MD5:— | SHA256:— | |||
| 272 | uiso.tmp | C:\Program Files\UltraISO\is-S8BBJ.tmp | — | |
MD5:— | SHA256:— | |||
| 272 | uiso.tmp | C:\Program Files\UltraISO\drivers\is-T7APR.tmp | — | |
MD5:— | SHA256:— | |||
| 272 | uiso.tmp | C:\Program Files\UltraISO\drivers\is-KOK9B.tmp | — | |
MD5:— | SHA256:— | |||
| 272 | uiso.tmp | C:\Program Files\UltraISO\drivers\is-0F903.tmp | — | |
MD5:— | SHA256:— | |||
| 272 | uiso.tmp | C:\Program Files\UltraISO\drivers\is-BIJ04.tmp | — | |
MD5:— | SHA256:— | |||
| 272 | uiso.tmp | C:\Program Files\UltraISO\drivers\is-AJP7H.tmp | — | |
MD5:— | SHA256:— | |||
| 272 | uiso.tmp | C:\Program Files\UltraISO\drivers\is-QS5GP.tmp | — | |
MD5:— | SHA256:— | |||
| 272 | uiso.tmp | C:\Program Files\Common Files\EZB Systems\is-AUCKB.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report