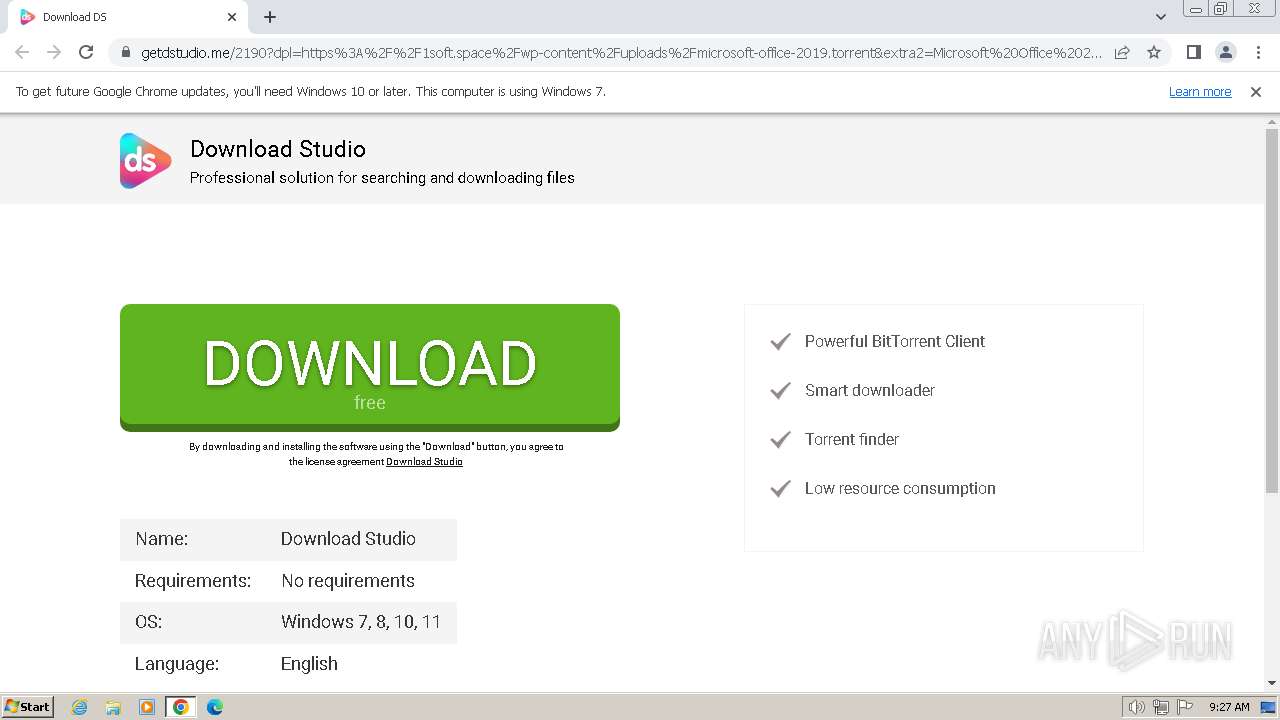
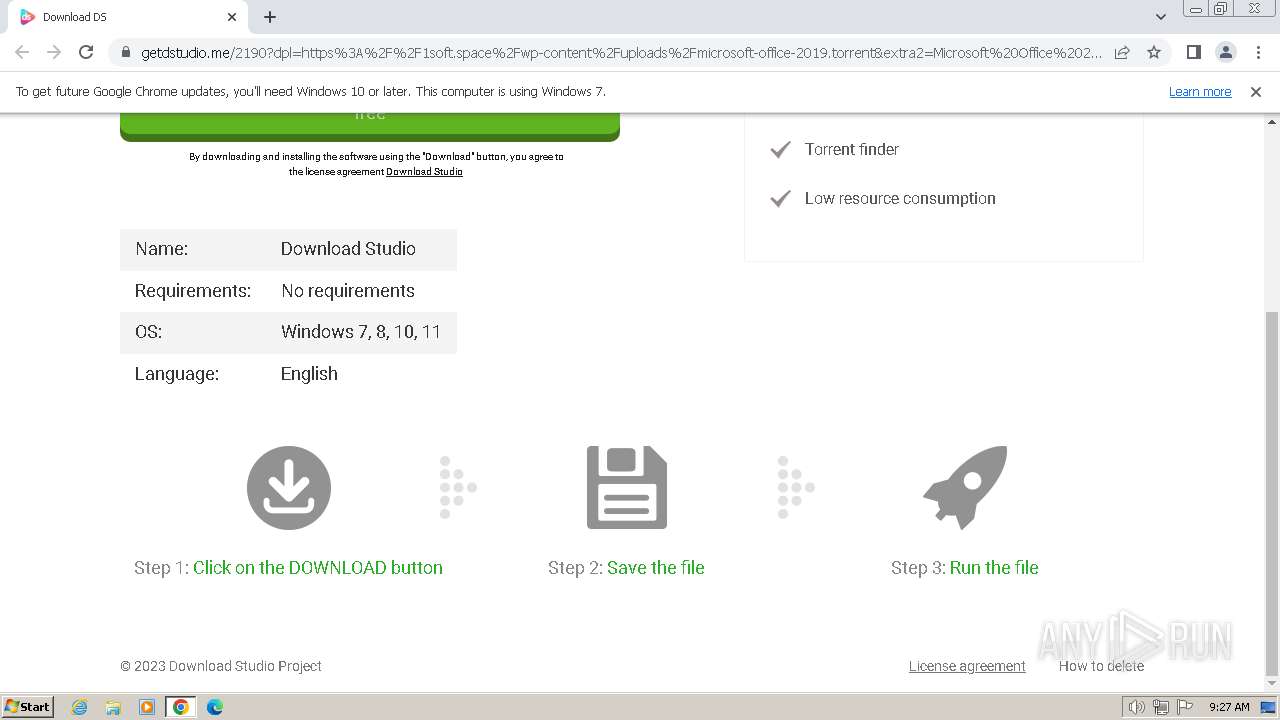
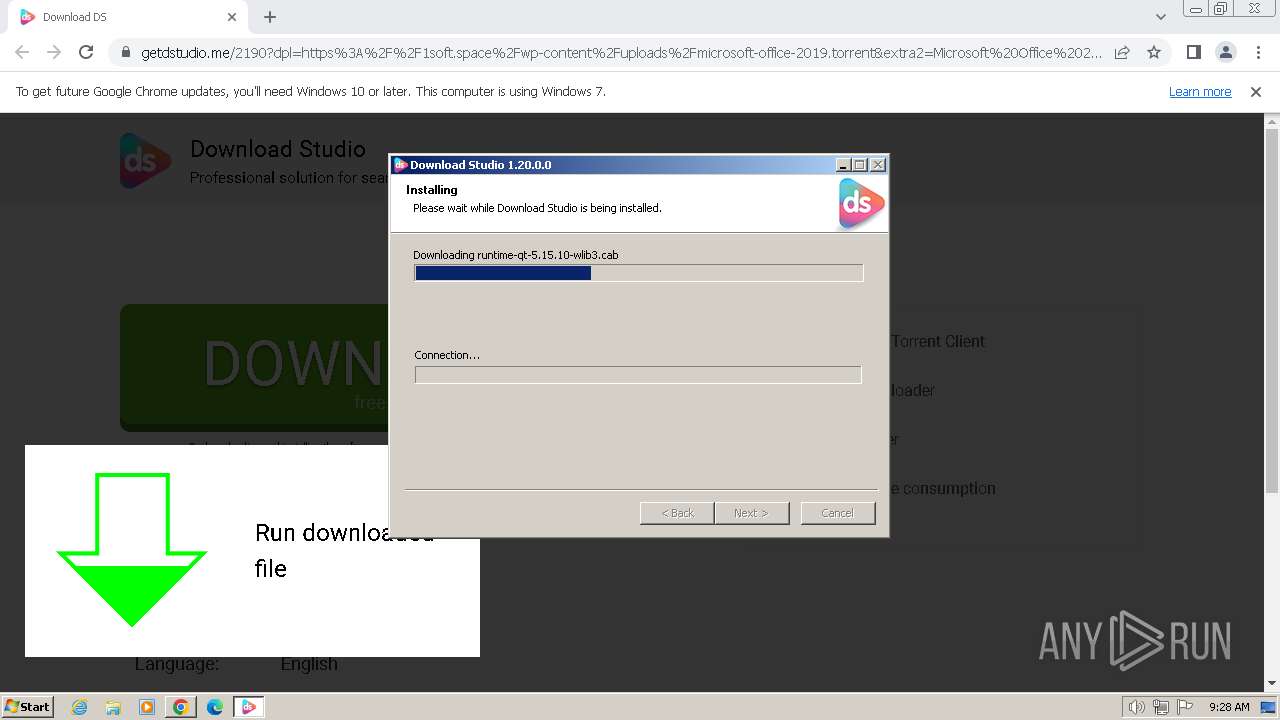
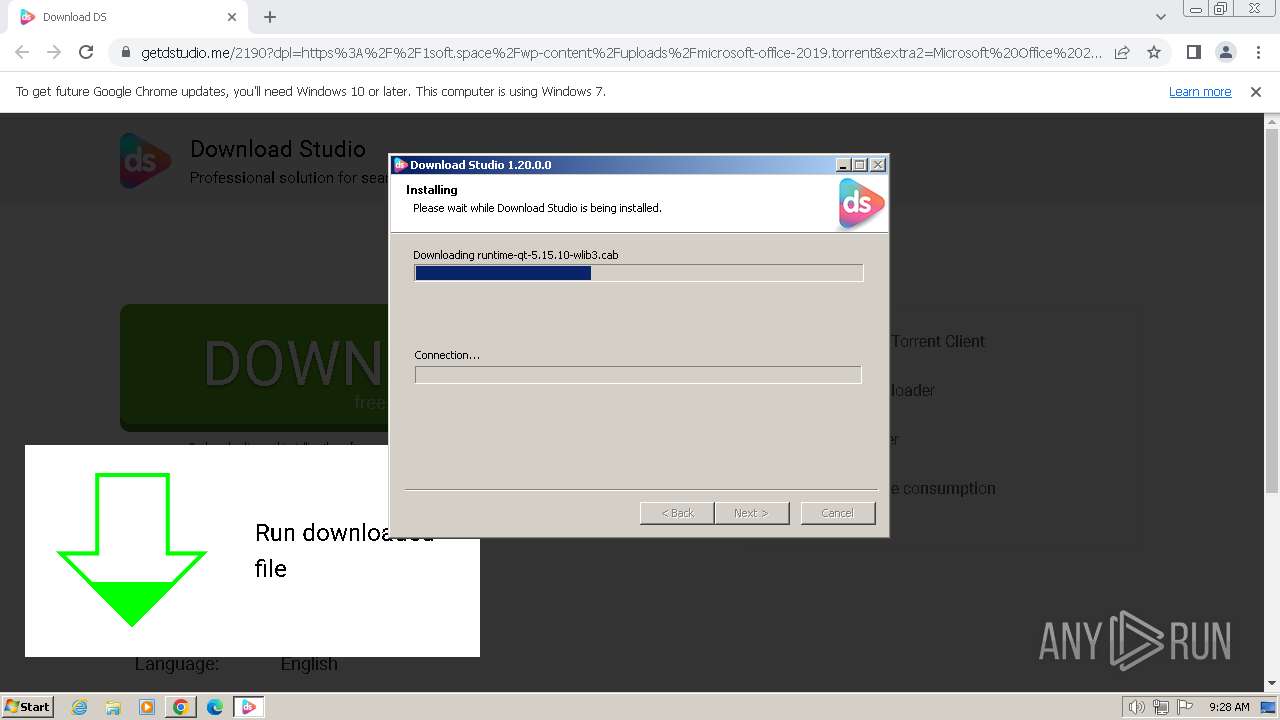
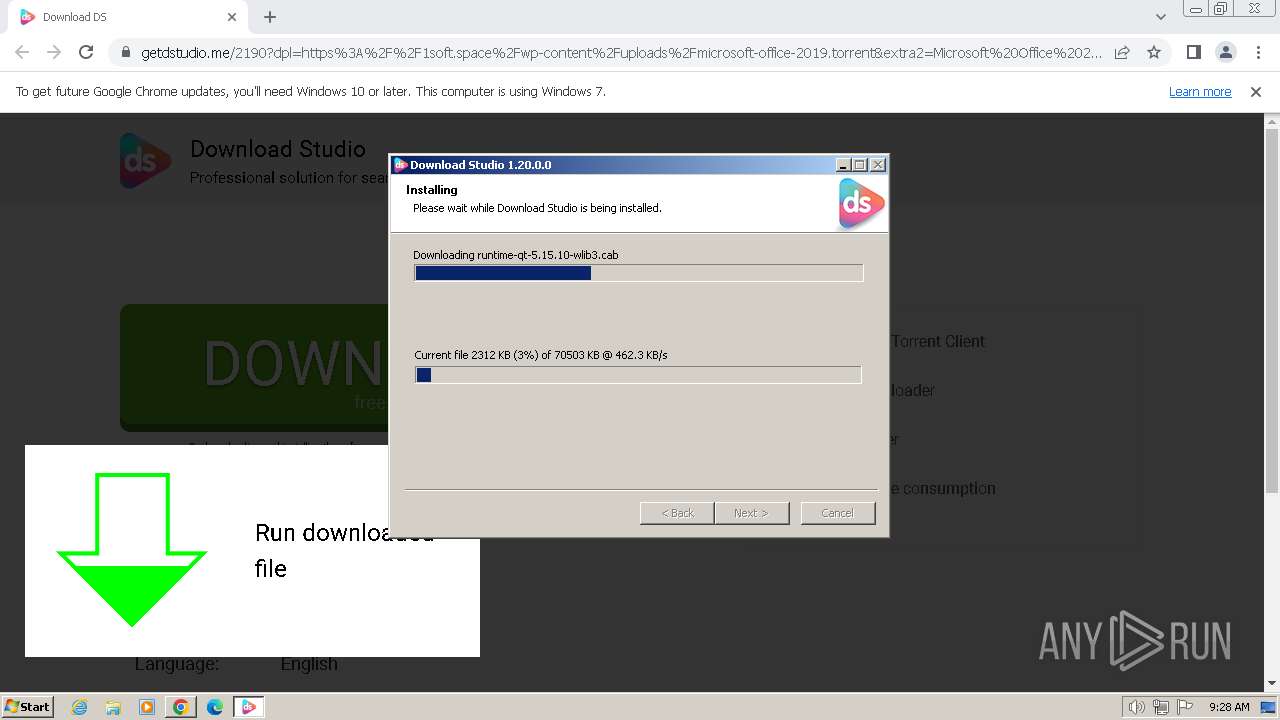
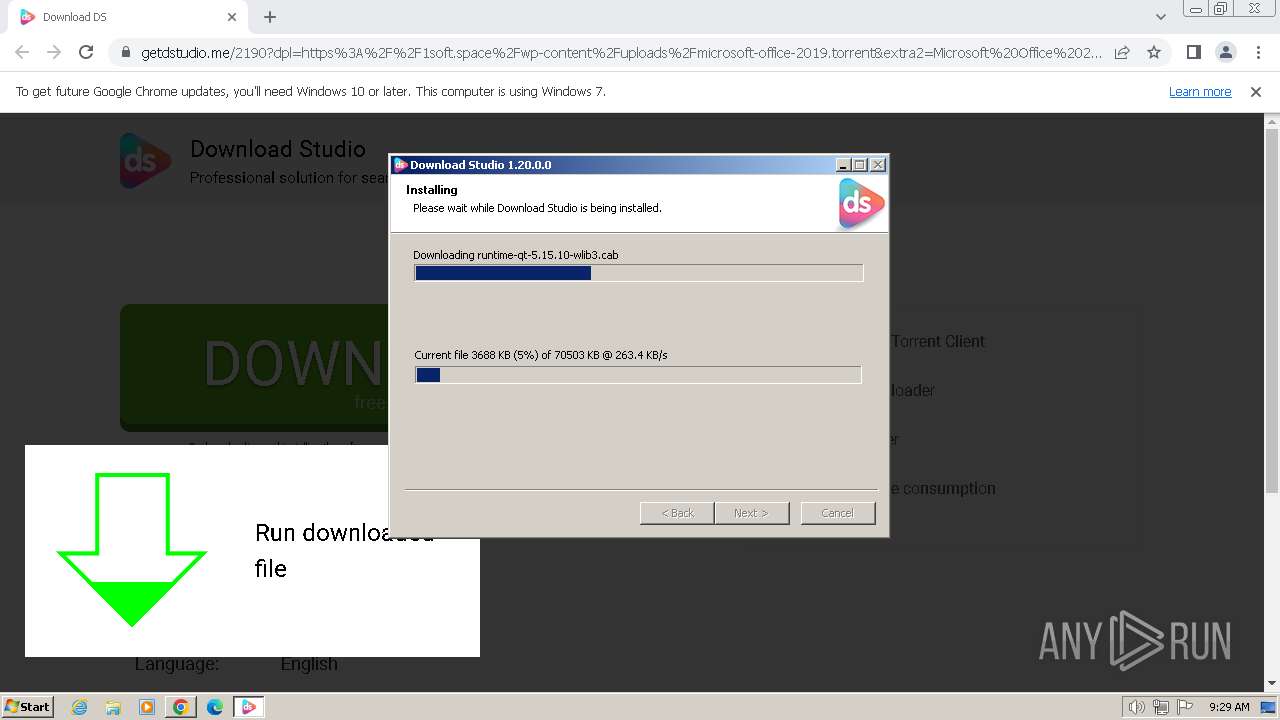
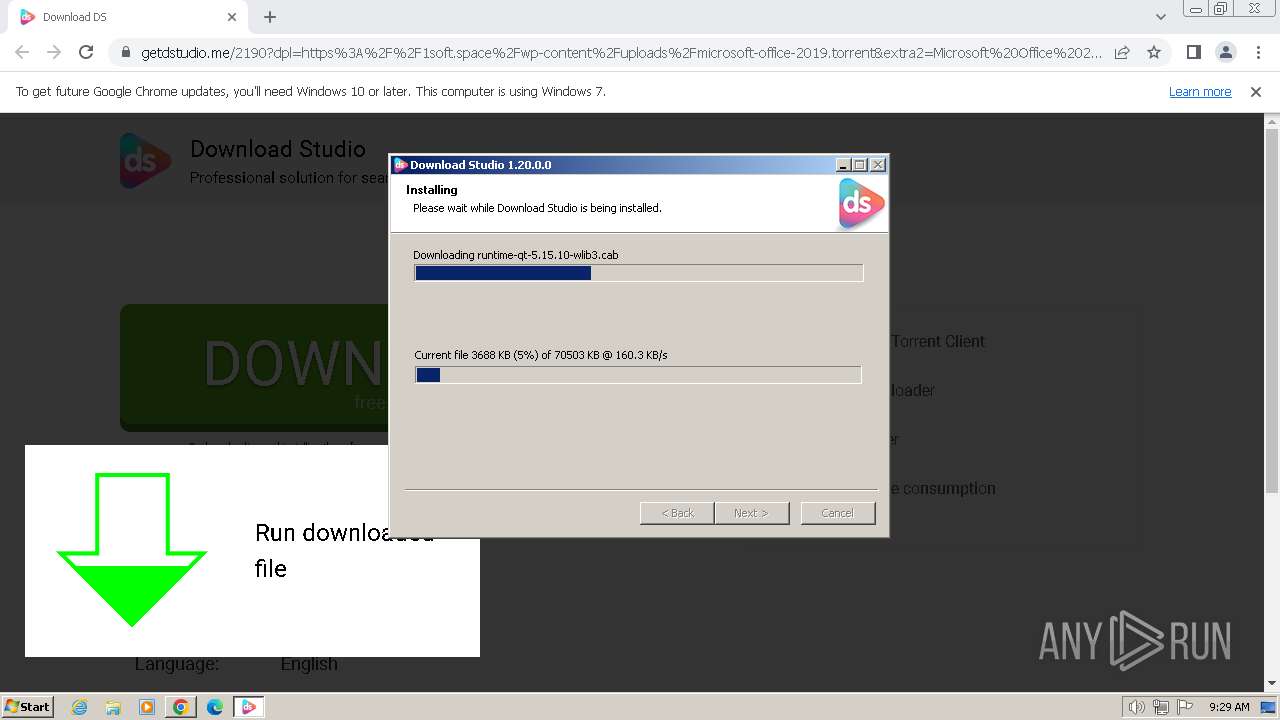
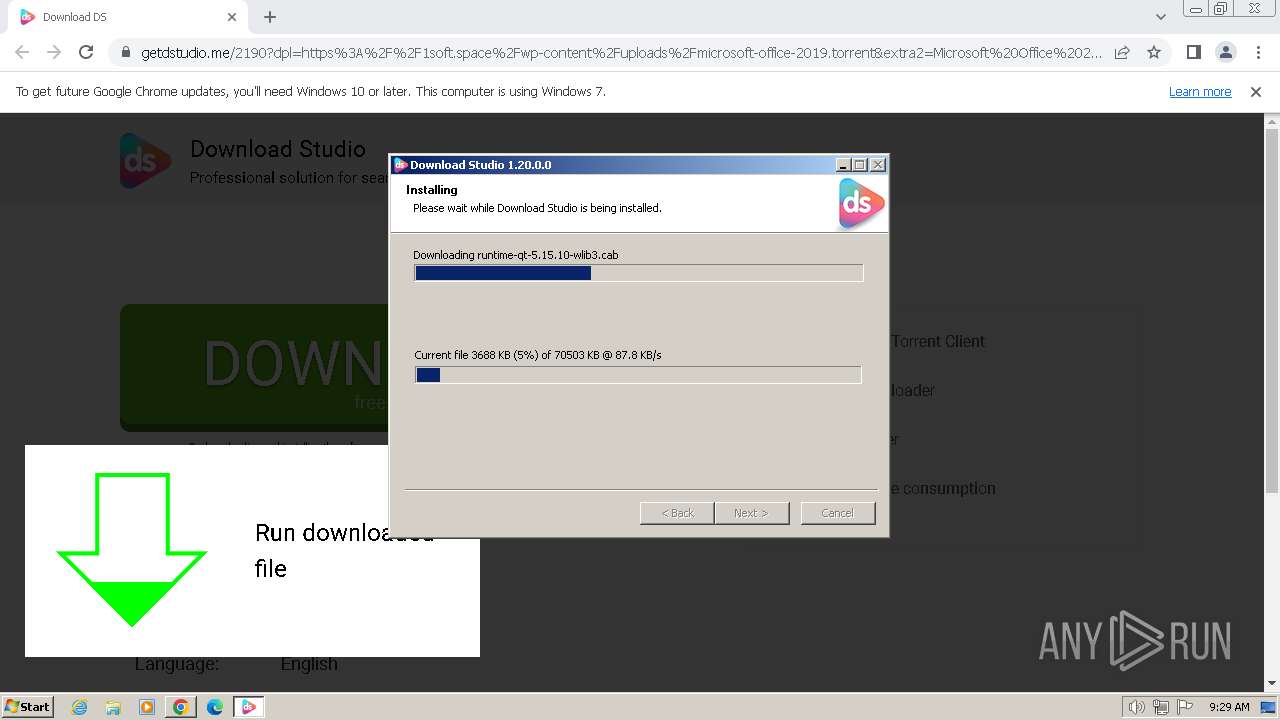
| URL: | https://getdstudio.me/2190?dpl=https%3A%2F%2F1soft.space%2Fwp-content%2Fuploads%2Fmicrosoft-office-2019.torrent&extra2=Microsoft%20Office%202019%20Pro%20Plus%20x32%2F64%20Bit |
| Full analysis: | https://app.any.run/tasks/32788481-da12-48ad-b783-e28dbe68081f |
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2024, 09:27:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 30ECA5F99C97378178CD4F9C26978CC6 |
| SHA1: | 0B76E3C4FDDFF45F6227604C78305854A3B47E62 |
| SHA256: | 12A54051063B8A3B824E7F4E388D09191D16E7C863DCE9107136352D53FC79DC |
| SSDEEP: | 3:N8hWRQBMQoEcwBVKBWCXjy5XidLRAa8VJNX0MAKRuuHlVUclK+DzXFemFOt36vbi:2A7QoyjYzy5XeRApJNFZuuHsclFDzVe3 |
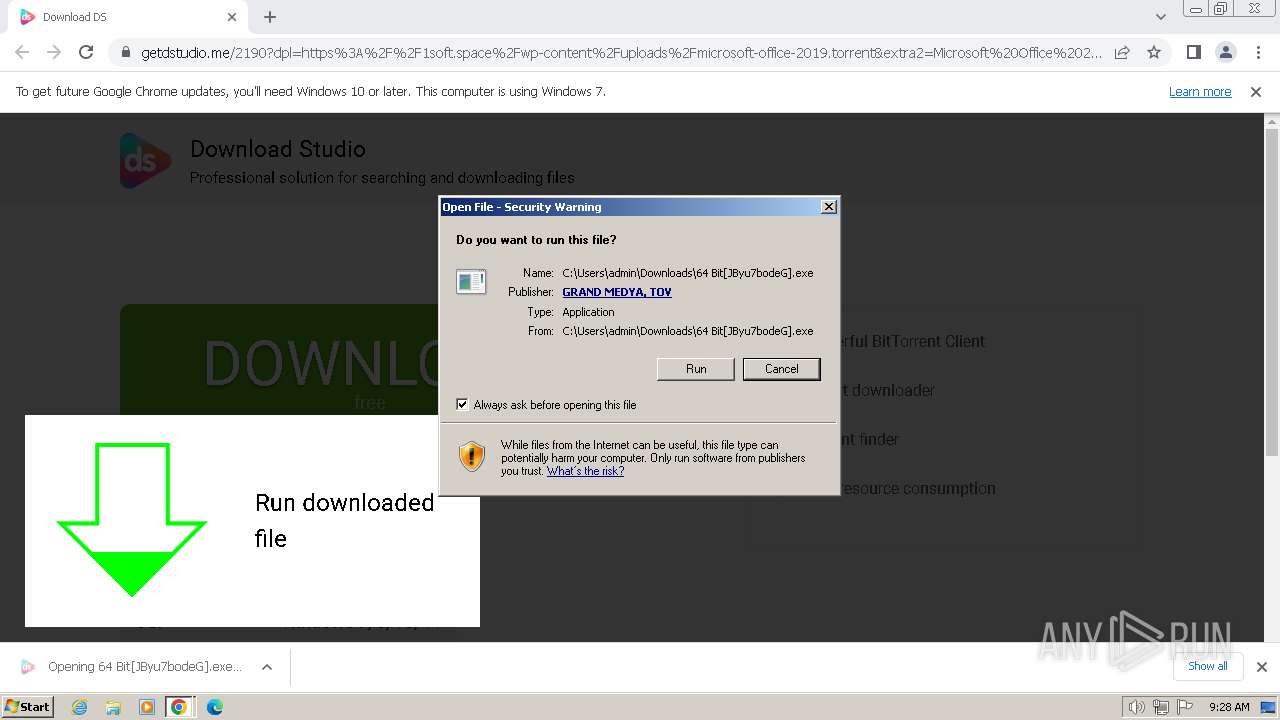
MALICIOUS
Drops the executable file immediately after the start
- 64 Bit[JByu7bodeG].exe (PID: 552)
- 64 Bit[JByu7bodeG].exe (PID: 480)
Actions looks like stealing of personal data
- 64 Bit[JByu7bodeG].exe (PID: 552)
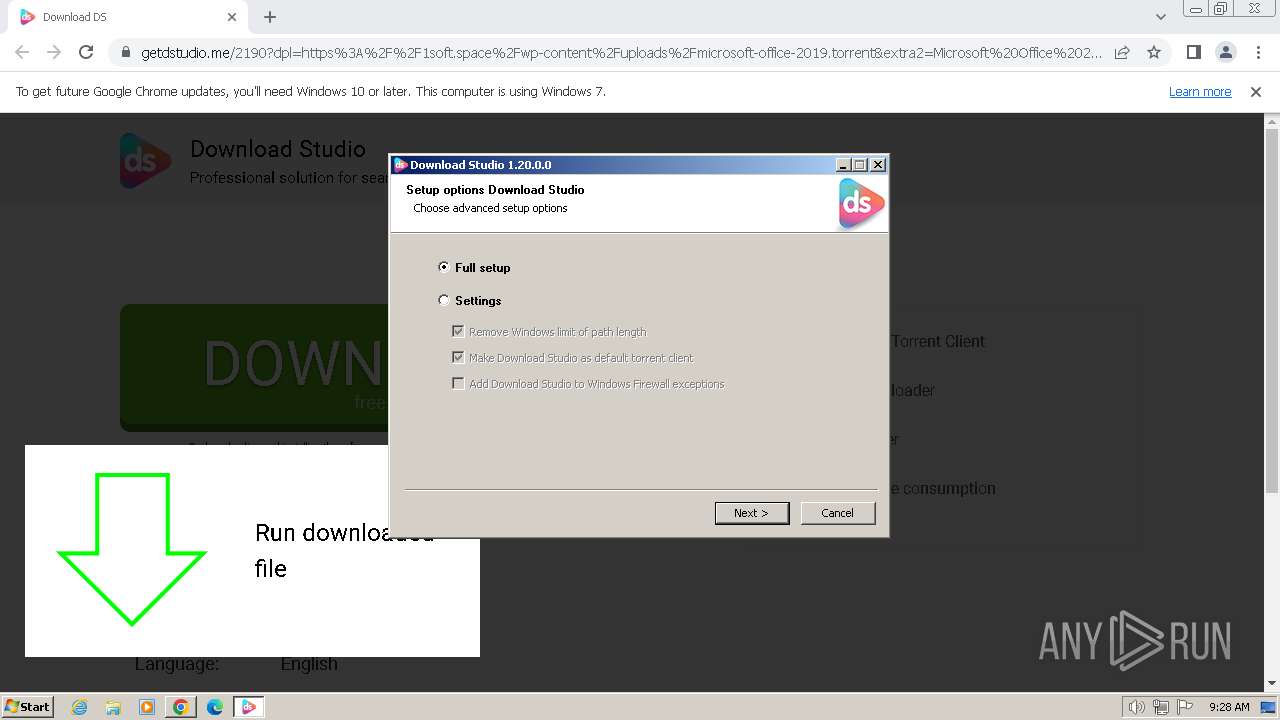
SUSPICIOUS
Application launched itself
- 64 Bit[JByu7bodeG].exe (PID: 480)
The process creates files with name similar to system file names
- 64 Bit[JByu7bodeG].exe (PID: 552)
Malware-specific behavior (creating "System.dll" in Temp)
- 64 Bit[JByu7bodeG].exe (PID: 552)
Executable content was dropped or overwritten
- 64 Bit[JByu7bodeG].exe (PID: 552)
- 64 Bit[JByu7bodeG].exe (PID: 480)
Reads the Internet Settings
- 64 Bit[JByu7bodeG].exe (PID: 552)
Reads security settings of Internet Explorer
- 64 Bit[JByu7bodeG].exe (PID: 552)
Reads settings of System Certificates
- 64 Bit[JByu7bodeG].exe (PID: 552)
Checks Windows Trust Settings
- 64 Bit[JByu7bodeG].exe (PID: 552)
Adds/modifies Windows certificates
- 64 Bit[JByu7bodeG].exe (PID: 552)
Reads the date of Windows installation
- 64 Bit[JByu7bodeG].exe (PID: 552)
Reads Microsoft Outlook installation path
- 64 Bit[JByu7bodeG].exe (PID: 552)
Reads Internet Explorer settings
- 64 Bit[JByu7bodeG].exe (PID: 552)
INFO
Application launched itself
- chrome.exe (PID: 3864)
Checks supported languages
- 64 Bit[JByu7bodeG].exe (PID: 480)
- 64 Bit[JByu7bodeG].exe (PID: 552)
Executable content was dropped or overwritten
- chrome.exe (PID: 3864)
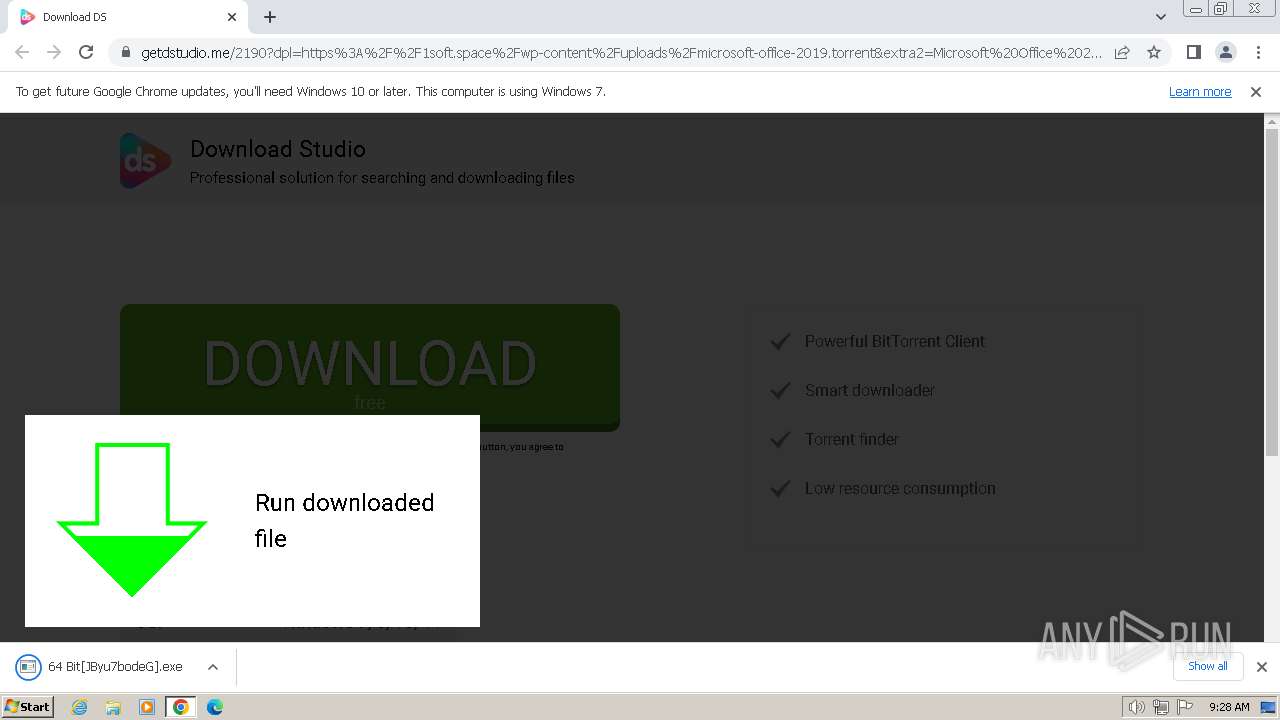
The process uses the downloaded file
- chrome.exe (PID: 3864)
- chrome.exe (PID: 2504)
Drops the executable file immediately after the start
- chrome.exe (PID: 3864)
Create files in a temporary directory
- 64 Bit[JByu7bodeG].exe (PID: 552)
- 64 Bit[JByu7bodeG].exe (PID: 480)
Checks proxy server information
- 64 Bit[JByu7bodeG].exe (PID: 552)
Reads the machine GUID from the registry
- 64 Bit[JByu7bodeG].exe (PID: 552)
Reads the software policy settings
- 64 Bit[JByu7bodeG].exe (PID: 552)
Creates files or folders in the user directory
- 64 Bit[JByu7bodeG].exe (PID: 552)
Reads the computer name
- 64 Bit[JByu7bodeG].exe (PID: 552)
- 64 Bit[JByu7bodeG].exe (PID: 480)
Creates files in the program directory
- 64 Bit[JByu7bodeG].exe (PID: 552)
Process checks whether UAC notifications are on
- 64 Bit[JByu7bodeG].exe (PID: 480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
18
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
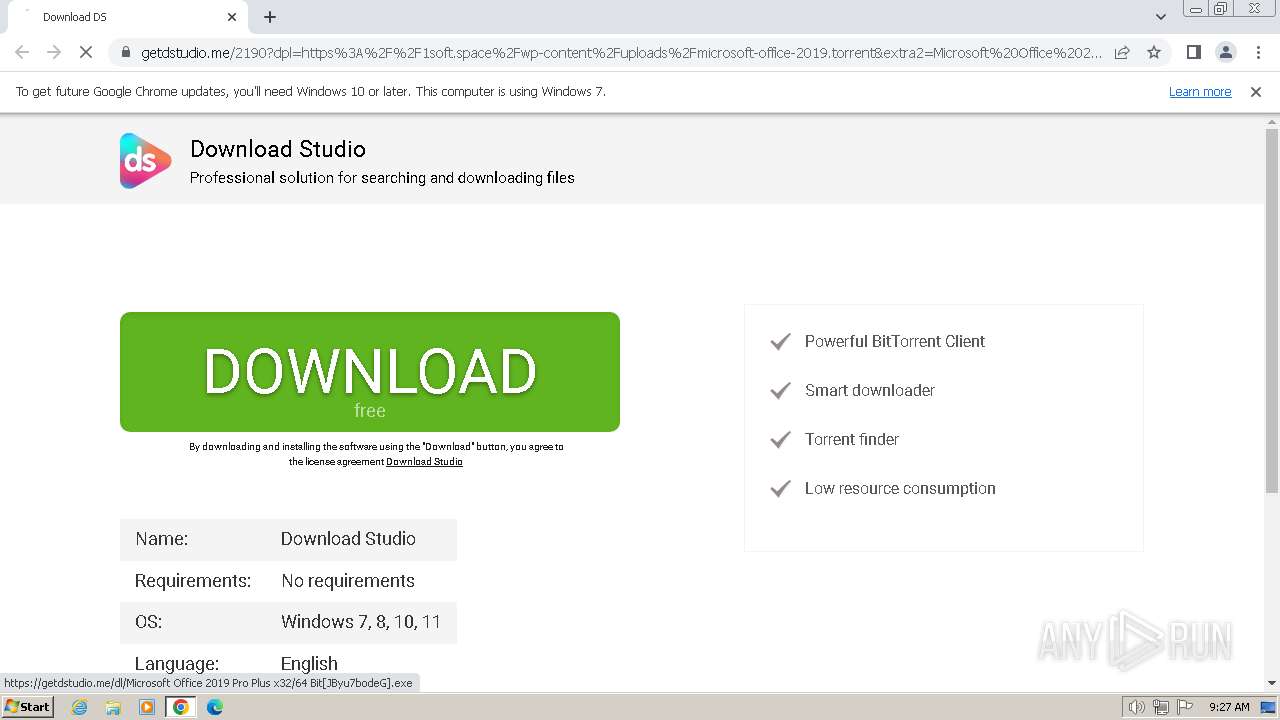
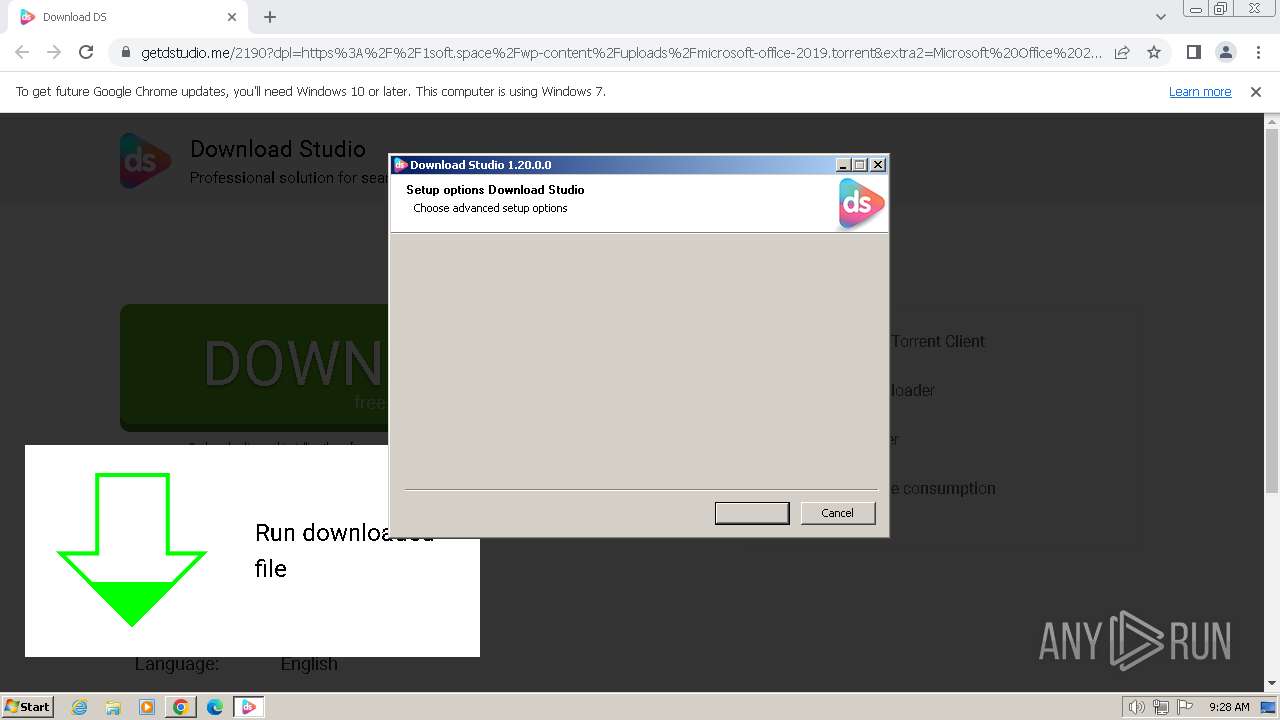
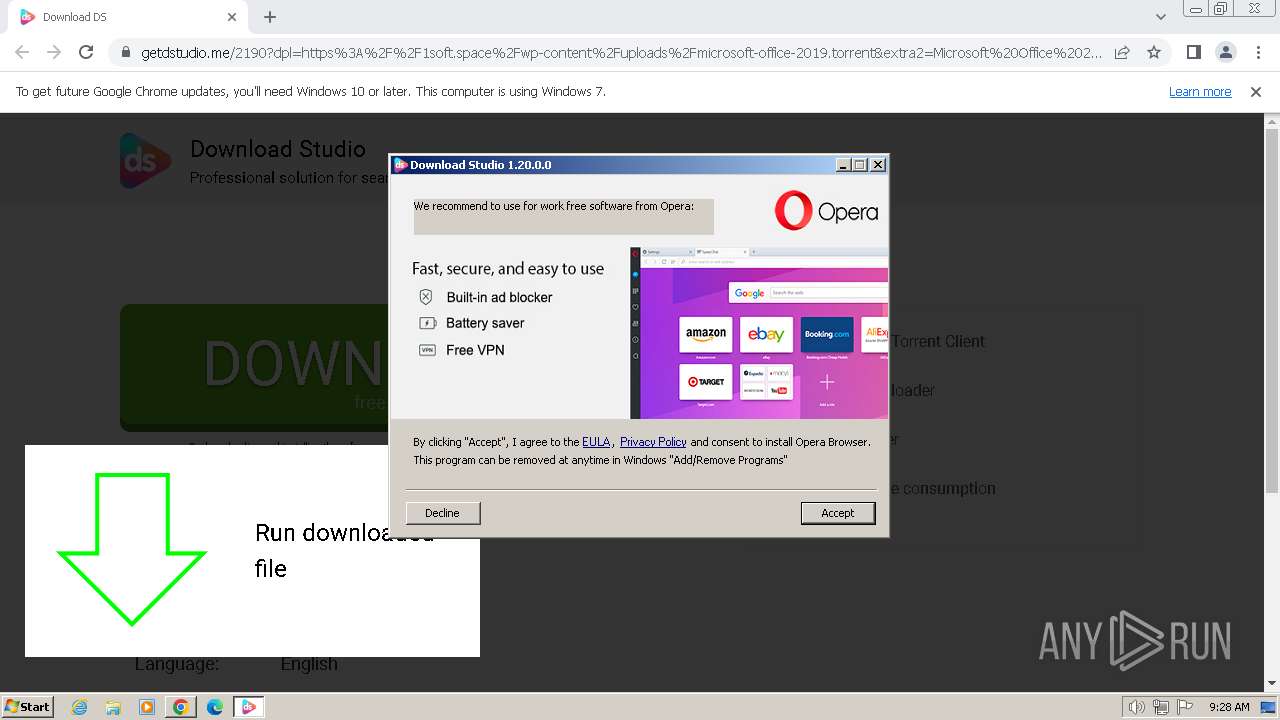
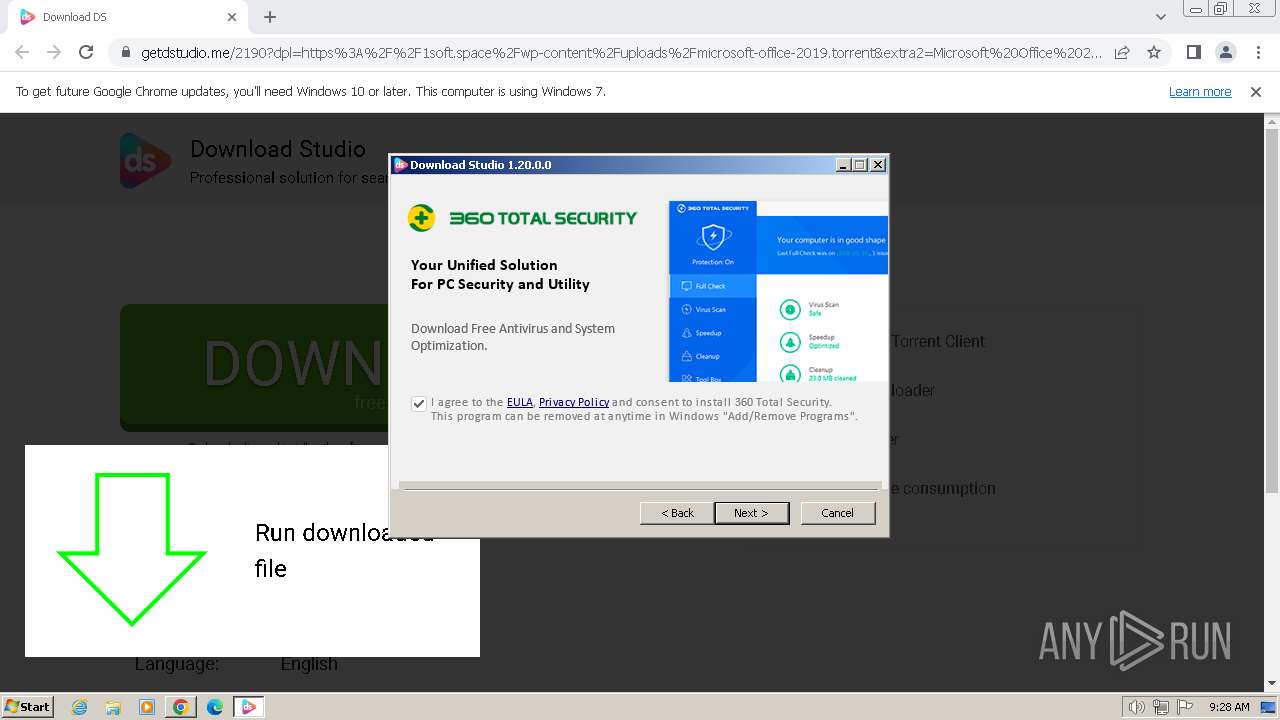
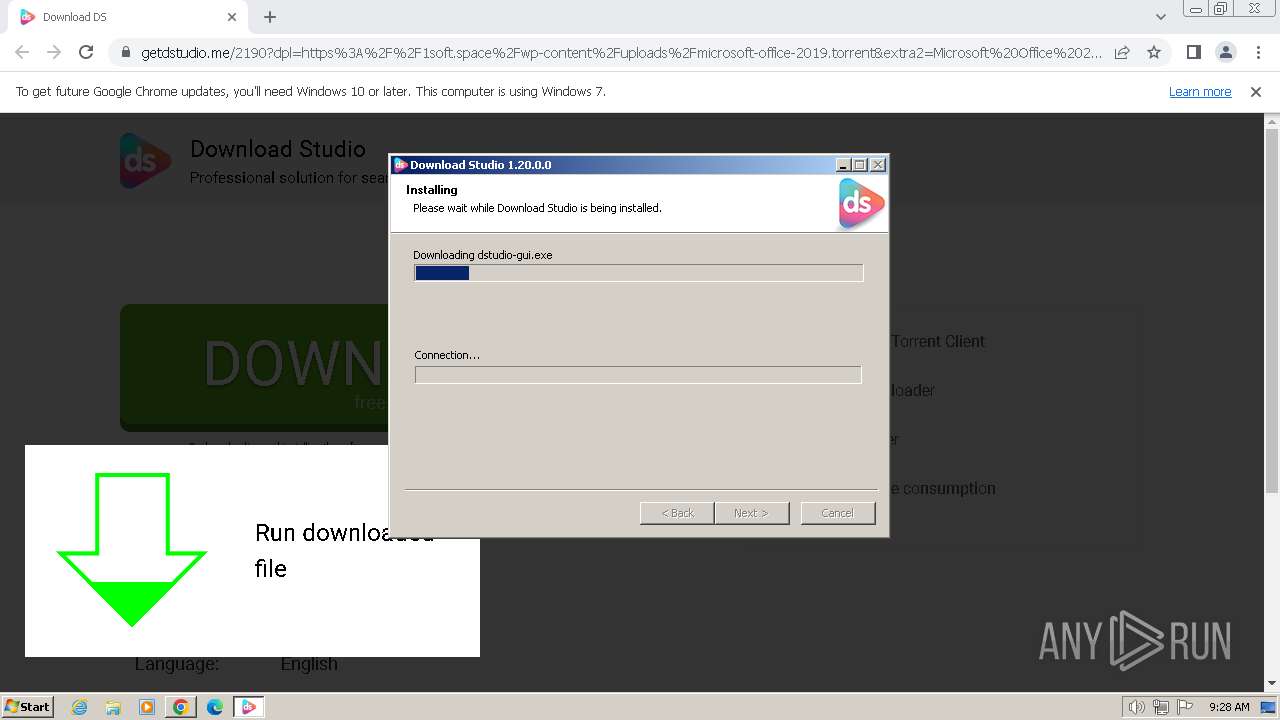
| 480 | "C:\Users\admin\Downloads\64 Bit[JByu7bodeG].exe" | C:\Users\admin\Downloads\64 Bit[JByu7bodeG].exe | chrome.exe | ||||||||||||
User: admin Company: Download Studio Project Integrity Level: MEDIUM Description: DS Setup Exit code: 0 Version: 1.20.0.0 Modules
| |||||||||||||||
| 552 | "C:\Users\admin\Downloads\64 Bit[JByu7bodeG].exe" /UAC:B0216 /NCRC | C:\Users\admin\Downloads\64 Bit[JByu7bodeG].exe | 64 Bit[JByu7bodeG].exe | ||||||||||||
User: admin Company: Download Studio Project Integrity Level: HIGH Description: DS Setup Exit code: 0 Version: 1.20.0.0 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3224 --field-trial-handle=1180,i,15477613091004762491,2289805804974421957,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1028 --field-trial-handle=1180,i,15477613091004762491,2289805804974421957,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1412 --field-trial-handle=1180,i,15477613091004762491,2289805804974421957,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3520 --field-trial-handle=1180,i,15477613091004762491,2289805804974421957,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bcd8b38,0x6bcd8b48,0x6bcd8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3812 --field-trial-handle=1180,i,15477613091004762491,2289805804974421957,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2008 --field-trial-handle=1180,i,15477613091004762491,2289805804974421957,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3532 --field-trial-handle=1180,i,15477613091004762491,2289805804974421957,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
23 692
Read events
23 510
Write events
153
Delete events
29
Modification events
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
18
Suspicious files
13
Text files
38
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f1f1.TMP | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17f23f.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17f8e6.TMP | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF17f3b6.TMP | text | |
MD5:C5B082BC8EA6A9BD1DC6782C00A79605 | SHA256:6168A9E585264DE05DEE1B67427B1BC277F1B83B9297184EFACC5D3BB061ABDE | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF1804fc.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
24
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3864 | chrome.exe | GET | 200 | 52.216.76.163:80 | http://cert.ssl.com/SSLcom-SubCA-EV-CodeSigning-RSA-4096-R3.cer | unknown | binary | 1.72 Kb | unknown |
552 | 64 Bit[JByu7bodeG].exe | GET | 304 | 23.32.238.219:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?88e545c40b6b79a8 | unknown | — | — | unknown |
552 | 64 Bit[JByu7bodeG].exe | GET | 200 | 23.32.238.219:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?446994104483eda8 | unknown | compressed | 65.2 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kvgfu5dyj2vfgt6ov4ftdakcza_8546/hfnkpimlhhgieaddgfemjhofmfblmnib_8546_all_acowzzmbi54lvdd5a5xssidlfgeq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kvgfu5dyj2vfgt6ov4ftdakcza_8546/hfnkpimlhhgieaddgfemjhofmfblmnib_8546_all_acowzzmbi54lvdd5a5xssidlfgeq.crx3 | unknown | binary | 9.95 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kvgfu5dyj2vfgt6ov4ftdakcza_8546/hfnkpimlhhgieaddgfemjhofmfblmnib_8546_all_acowzzmbi54lvdd5a5xssidlfgeq.crx3 | unknown | binary | 6.29 Kb | unknown |
552 | 64 Bit[JByu7bodeG].exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kvgfu5dyj2vfgt6ov4ftdakcza_8546/hfnkpimlhhgieaddgfemjhofmfblmnib_8546_all_acowzzmbi54lvdd5a5xssidlfgeq.crx3 | unknown | binary | 173 b | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kvgfu5dyj2vfgt6ov4ftdakcza_8546/hfnkpimlhhgieaddgfemjhofmfblmnib_8546_all_acowzzmbi54lvdd5a5xssidlfgeq.crx3 | unknown | binary | 9.99 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3864 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3948 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | unknown |
3948 | chrome.exe | 162.55.45.66:443 | getdstudio.me | Hetzner Online GmbH | DE | unknown |
3948 | chrome.exe | 142.250.186.42:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3948 | chrome.exe | 172.217.23.99:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
3864 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3948 | chrome.exe | 142.250.185.164:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
getdstudio.me |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
cert.ssl.com |
| unknown |
apis.downloadstud.io |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |