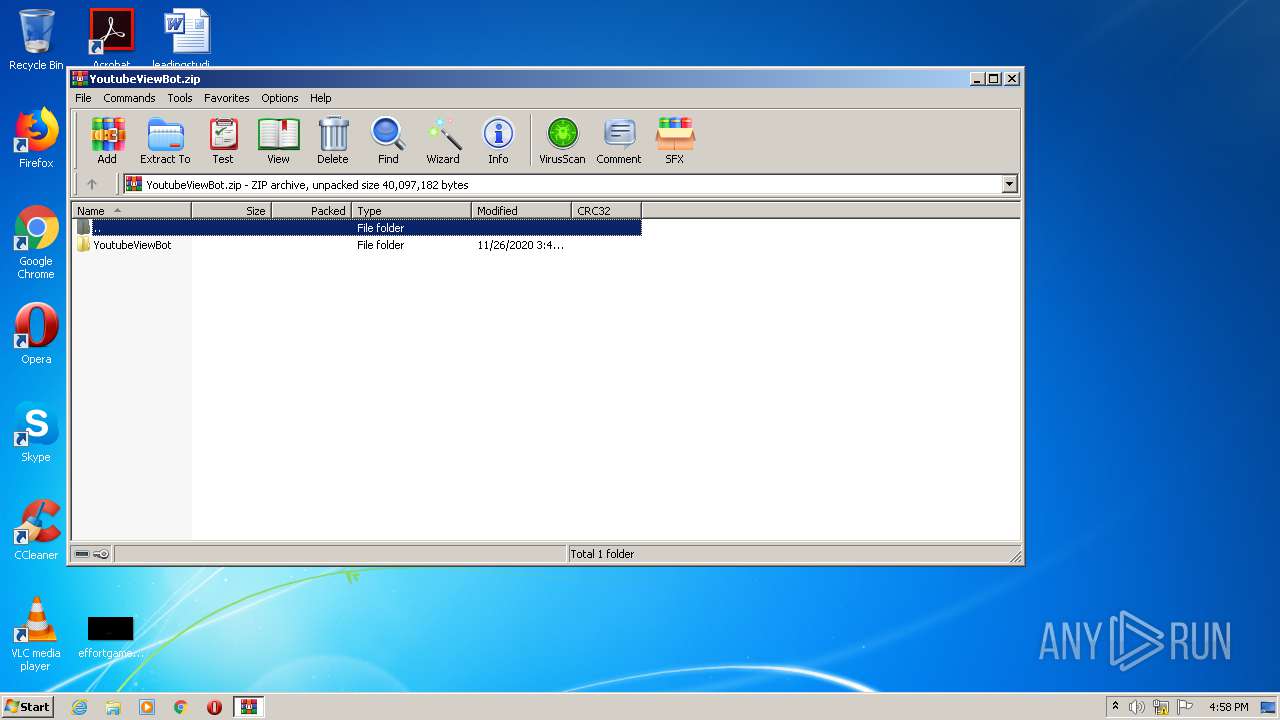
| File name: | YoutubeViewBot.zip |
| Full analysis: | https://app.any.run/tasks/a2b4c44d-1299-4fbd-832e-96a775a32e44 |
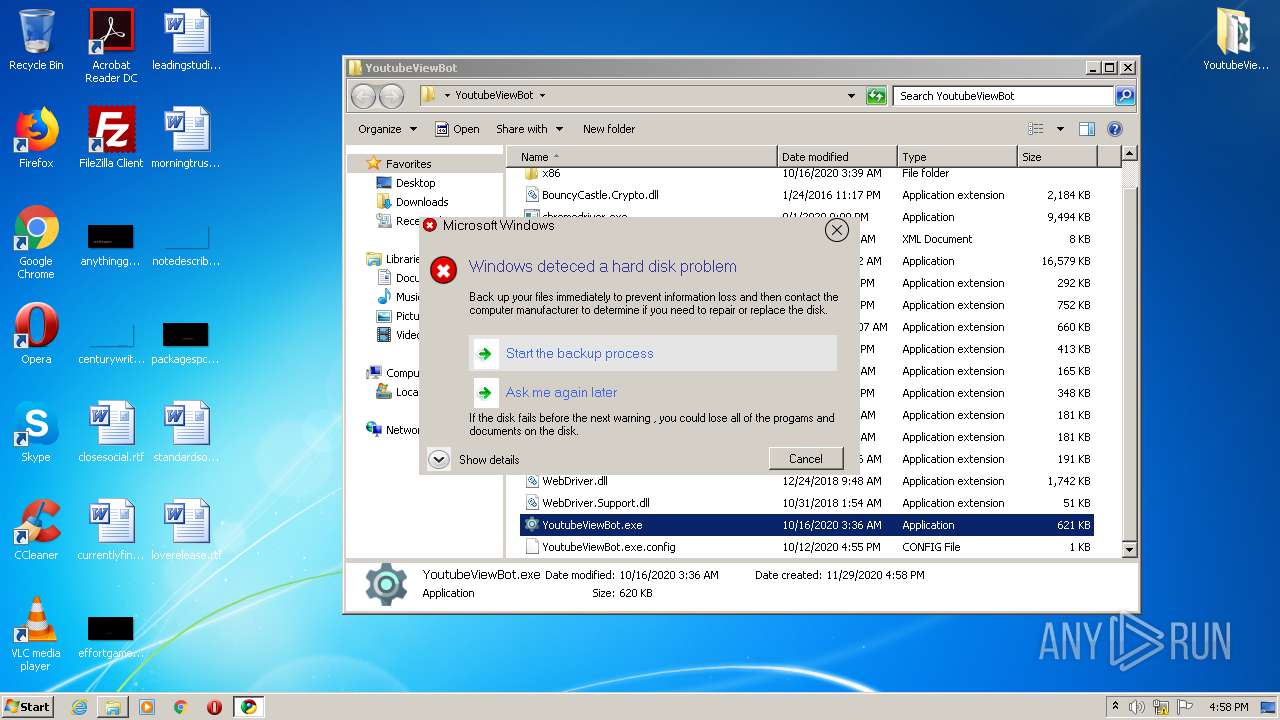
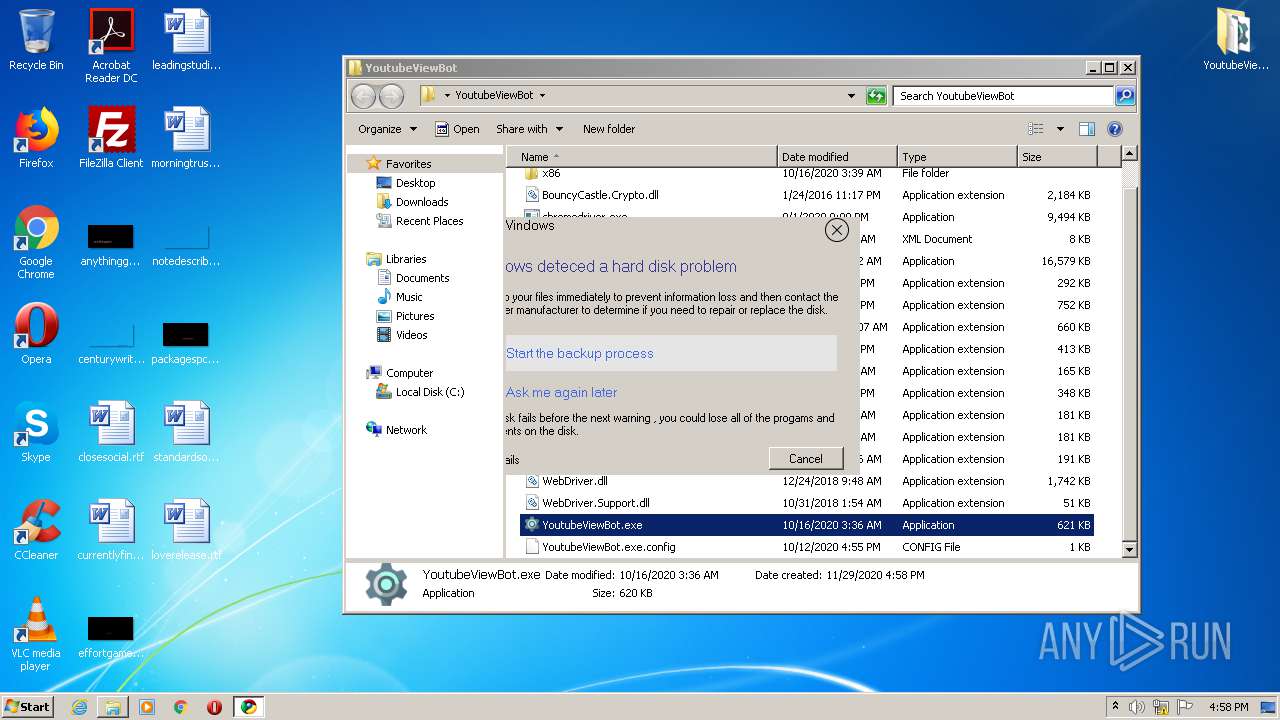
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 16:57:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 6C55D50144B9132402395F8621700219 |
| SHA1: | 567A02648C523FFD871526ACDC8CA162E4EA7F40 |
| SHA256: | 129F8322C852EFDE288AA7C2A7EF7D5E17B393902C009D382378F4E84052007E |
| SSDEEP: | 393216:ybAE1hxNQTJwqDcLzXeHL8/OzXLFsp0XkCy8ZdOb3kDDIpfWvIJAP:ub1pEijXOHeAXLq2XdyEw5svIKP |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3164)
- explorer.exe (PID: 352)
- YoutubeViewBot.exe (PID: 2592)
- YoutubeViewBot.exe (PID: 1032)
Drops executable file immediately after starts
- YoutubeViewBot.exe (PID: 2592)
Actions looks like stealing of personal data
- YoutubeViewBot.exe (PID: 2592)
- YoutubeViewBot.exe (PID: 1032)
SUSPICIOUS
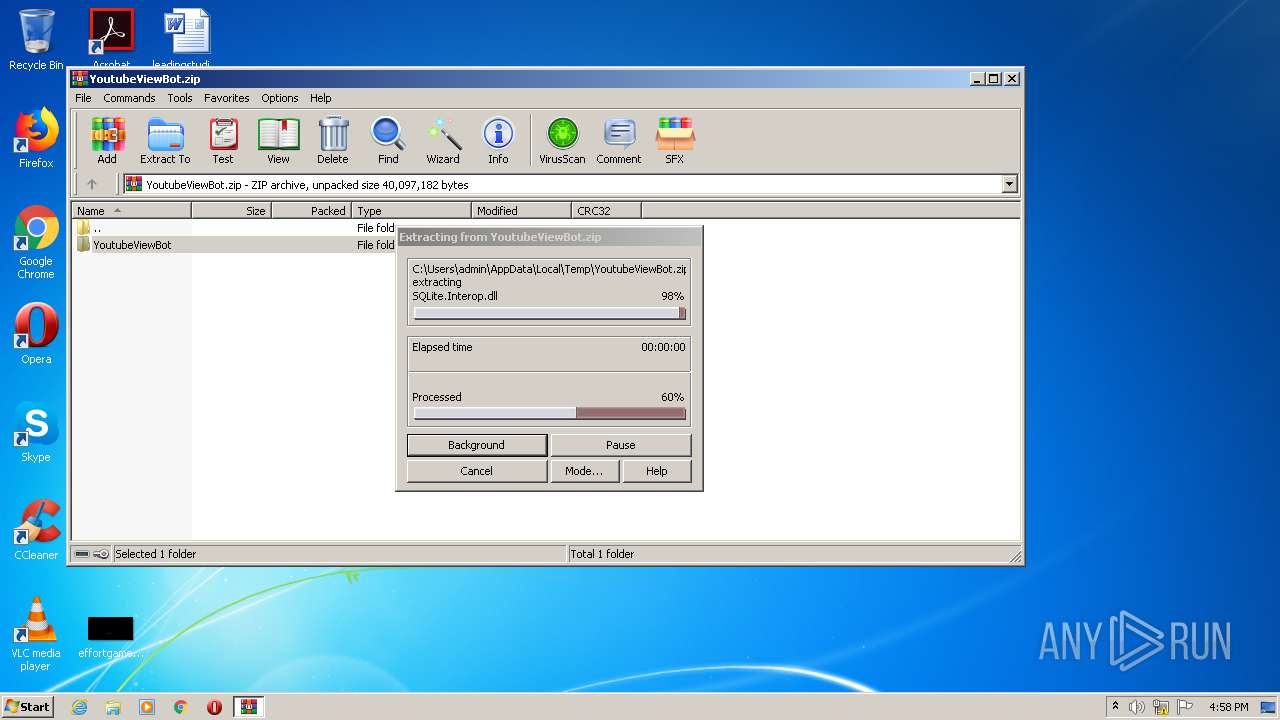
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1388)
- YoutubeViewBot.exe (PID: 2592)
Drops a file with too old compile date
- WinRAR.exe (PID: 1388)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 352)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1388)
Reads the cookies of Google Chrome
- YoutubeViewBot.exe (PID: 2592)
- YoutubeViewBot.exe (PID: 1032)
Starts CMD.EXE for commands execution
- YoutubeViewBot.exe (PID: 2592)
- YoutubeViewBot.exe (PID: 1032)
Checks for external IP
- nslookup.exe (PID: 1256)
- nslookup.exe (PID: 2652)
INFO
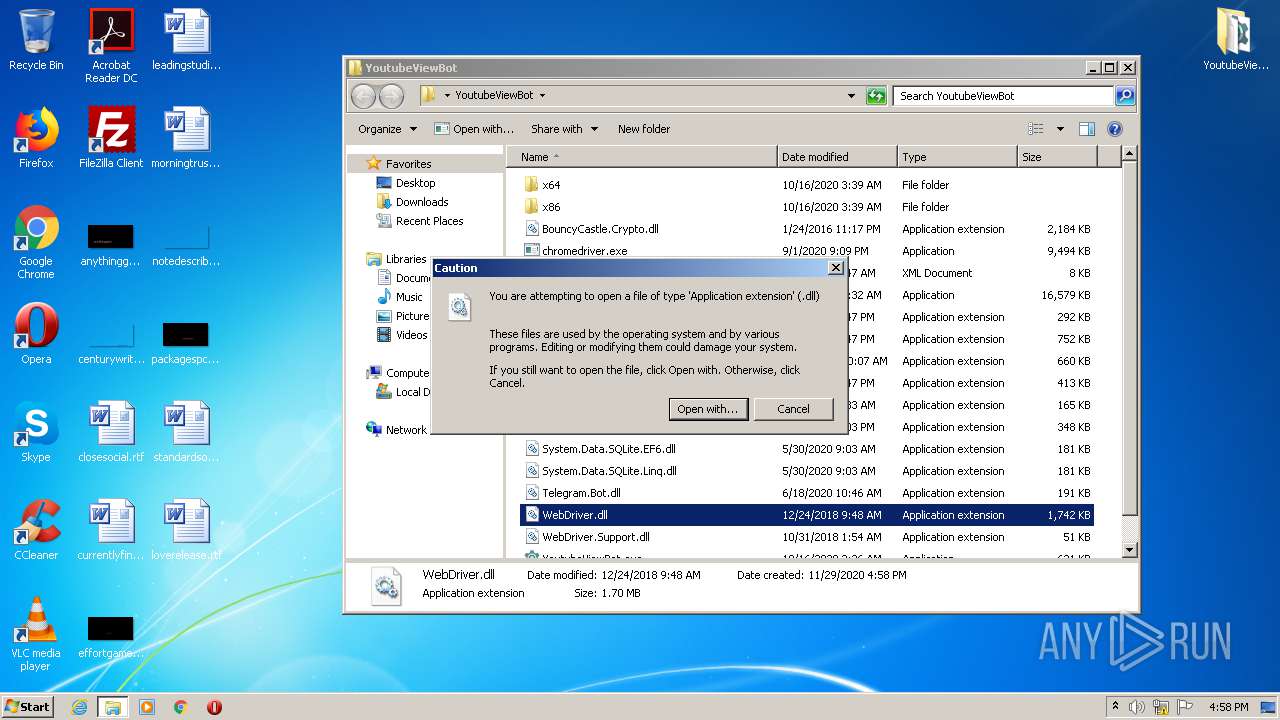
Manual execution by user
- rundll32.exe (PID: 1552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:11:26 23:47:11 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | YoutubeViewBot/ |
Total processes
45
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1032 | "C:\Users\admin\Desktop\YoutubeViewBot\YoutubeViewBot.exe" | C:\Users\admin\Desktop\YoutubeViewBot\YoutubeViewBot.exe | explorer.exe | ||||||||||||
User: admin Company: Garena flasform Integrity Level: MEDIUM Description: Garena flasform Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1152 | "cmd.exe" /c nslookup myip.opendns.com. resolver1.opendns.com | C:\Windows\system32\cmd.exe | — | YoutubeViewBot.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1256 | nslookup myip.opendns.com. resolver1.opendns.com | C:\Windows\system32\nslookup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1388 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\YoutubeViewBot.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1552 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\YoutubeViewBot\WebDriver.dll | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2268 | "cmd.exe" /c nslookup myip.opendns.com. resolver1.opendns.com | C:\Windows\system32\cmd.exe | — | YoutubeViewBot.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2592 | "C:\Users\admin\Desktop\YoutubeViewBot\YoutubeViewBot.exe" | C:\Users\admin\Desktop\YoutubeViewBot\YoutubeViewBot.exe | explorer.exe | ||||||||||||
User: admin Company: Garena flasform Integrity Level: MEDIUM Description: Garena flasform Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2652 | nslookup myip.opendns.com. resolver1.opendns.com | C:\Windows\system32\nslookup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3164 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 110
Read events
2 005
Write events
105
Delete events
0
Modification events
| (PID) Process: | (1388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1388) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\YoutubeViewBot.zip | |||
| (PID) Process: | (1388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
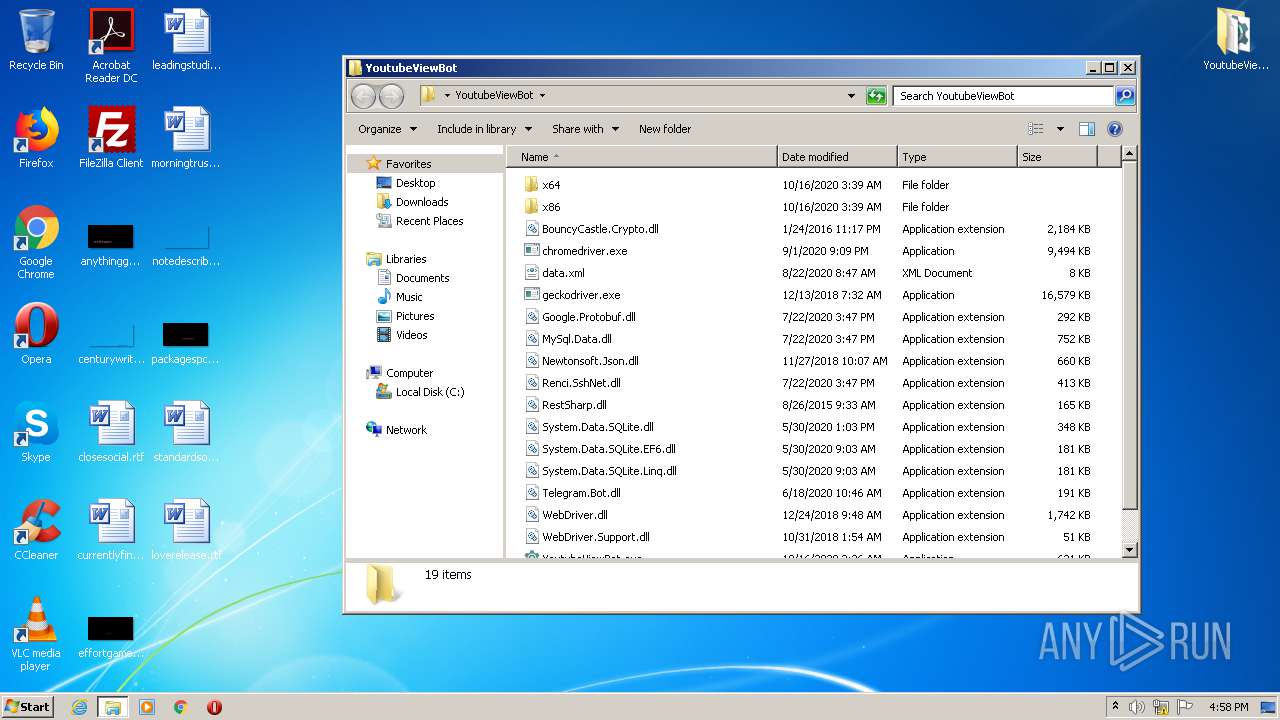
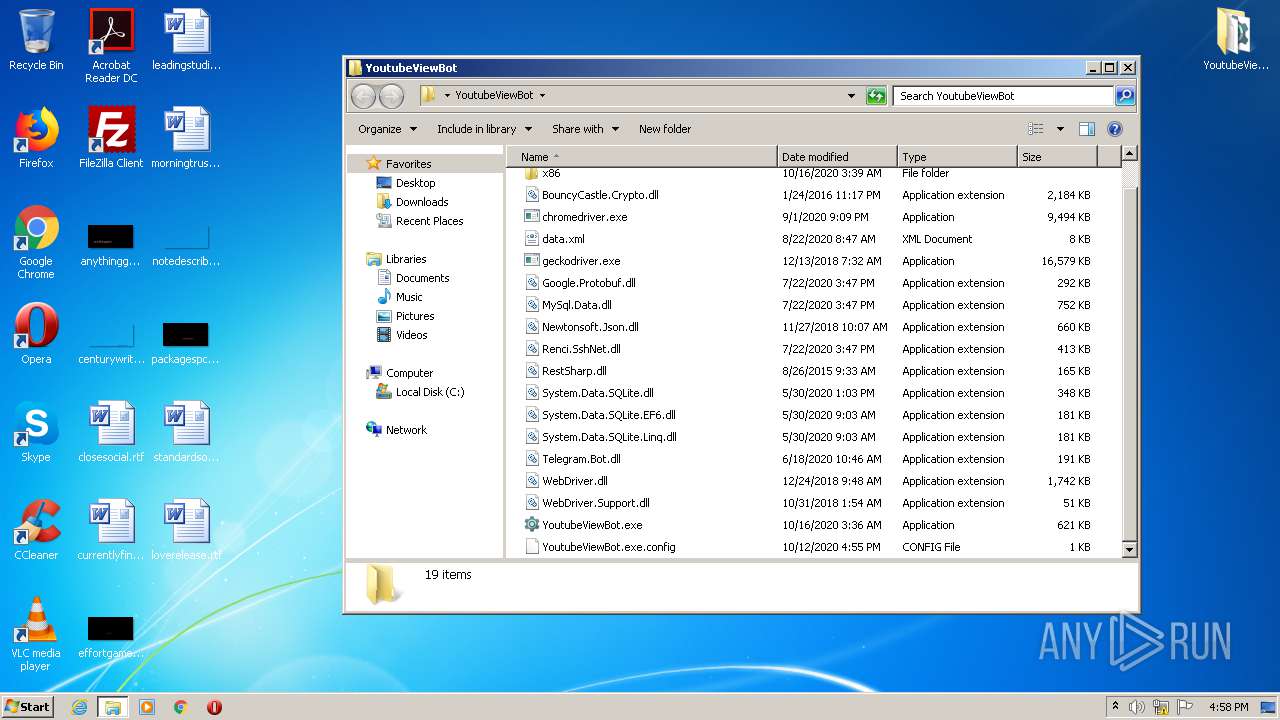
Executable files
18
Suspicious files
0
Text files
1
Unknown types
0
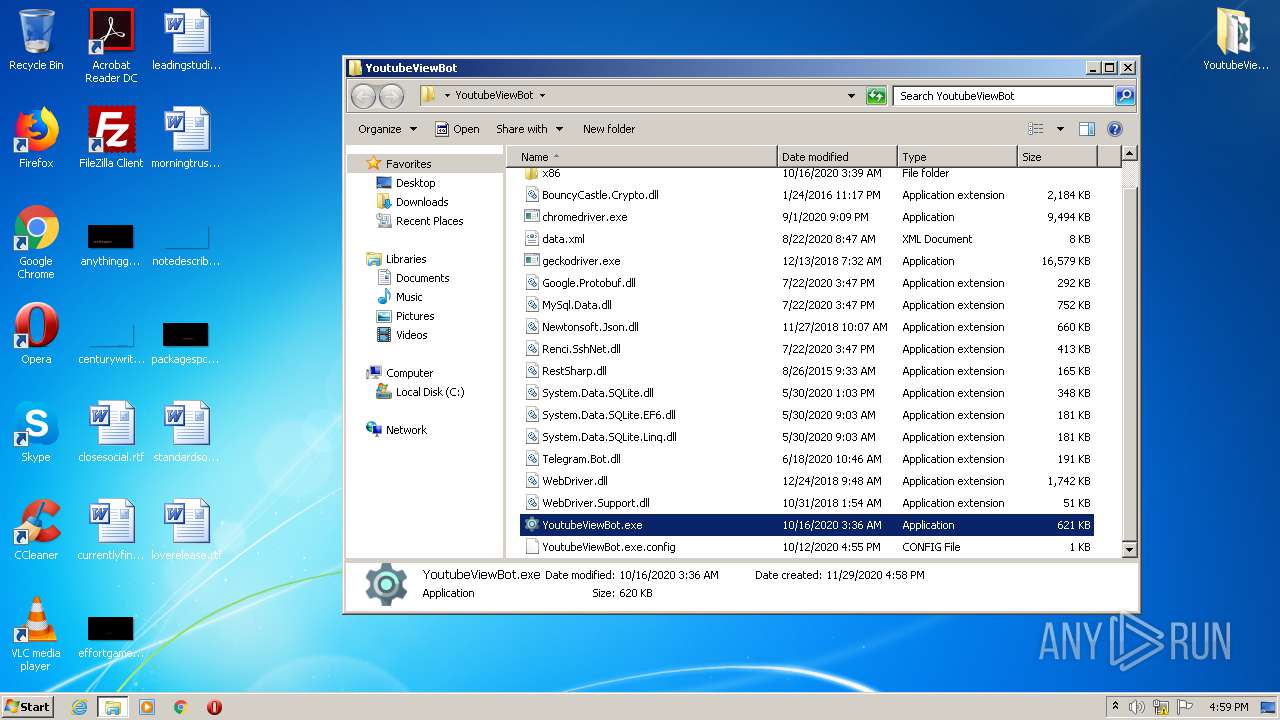
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1388.43594\YoutubeViewBot\x86\sqlite3.dll | — | |
MD5:— | SHA256:— | |||
| 1388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1388.43594\YoutubeViewBot\YoutubeViewBot.exe | — | |
MD5:— | SHA256:— | |||
| 1388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1388.43594\YoutubeViewBot\YoutubeViewBot.exe.config | — | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\YoutubeViewBot | — | |
MD5:— | SHA256:— | |||
| 2592 | YoutubeViewBot.exe | C:\Users\admin\AppData\Local\Temp\tmp6DDF.tmp | — | |
MD5:— | SHA256:— | |||
| 2592 | YoutubeViewBot.exe | C:\Users\admin\AppData\Local\Temp\tmp6E3D.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | YoutubeViewBot.exe | C:\Users\admin\AppData\Local\Temp\tmpF80E.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | YoutubeViewBot.exe | C:\Users\admin\AppData\Local\Temp\tmpF85D.tmp | — | |
MD5:— | SHA256:— | |||
| 1388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1388.43594\YoutubeViewBot\geckodriver.exe | executable | |
MD5:— | SHA256:— | |||
| 1388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1388.43594\YoutubeViewBot\x64\sqlite3.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
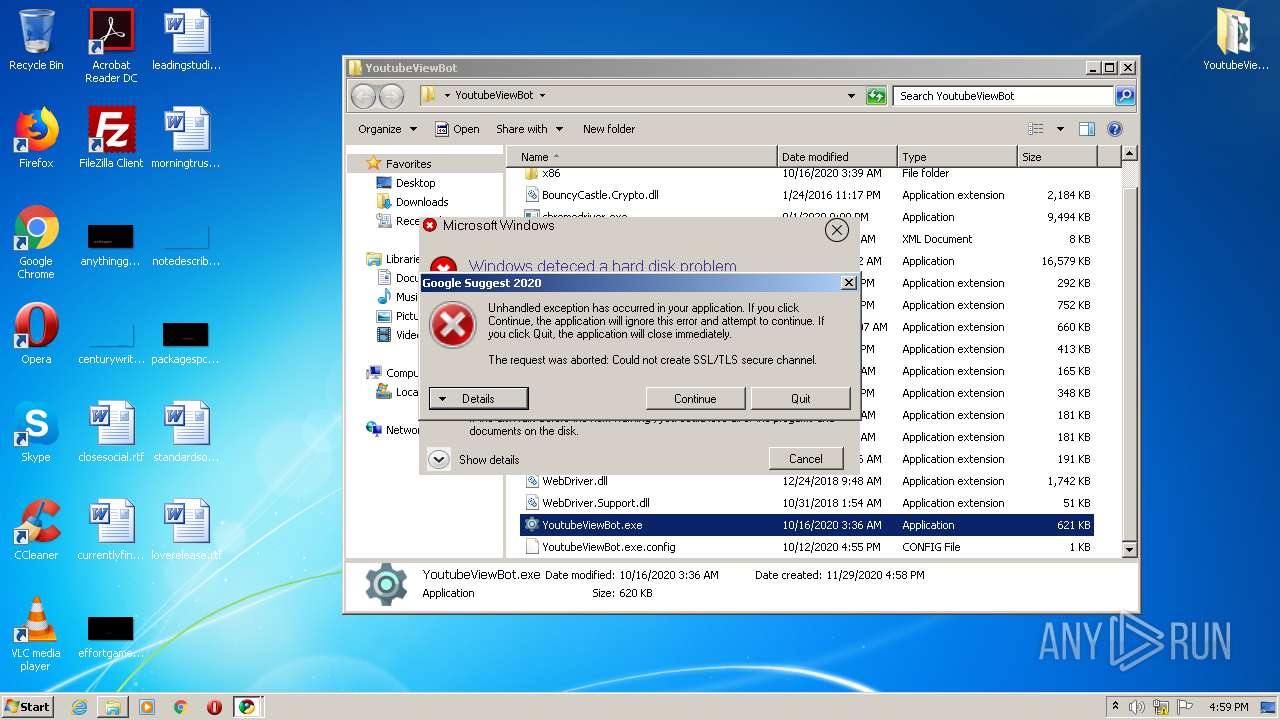
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
9
Threats
8
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2592 | YoutubeViewBot.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
1256 | nslookup.exe | 208.67.222.222:53 | resolver1.opendns.com | OpenDNS, LLC | US | malicious |
1032 | YoutubeViewBot.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
2652 | nslookup.exe | 208.67.222.222:53 | resolver1.opendns.com | OpenDNS, LLC | US | malicious |
— | — | 208.67.222.222:53 | resolver1.opendns.com | OpenDNS, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.telegram.org |
| shared |
resolver1.opendns.com |
| shared |
222.222.67.208.in-addr.arpa |
| unknown |
myip.opendns.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
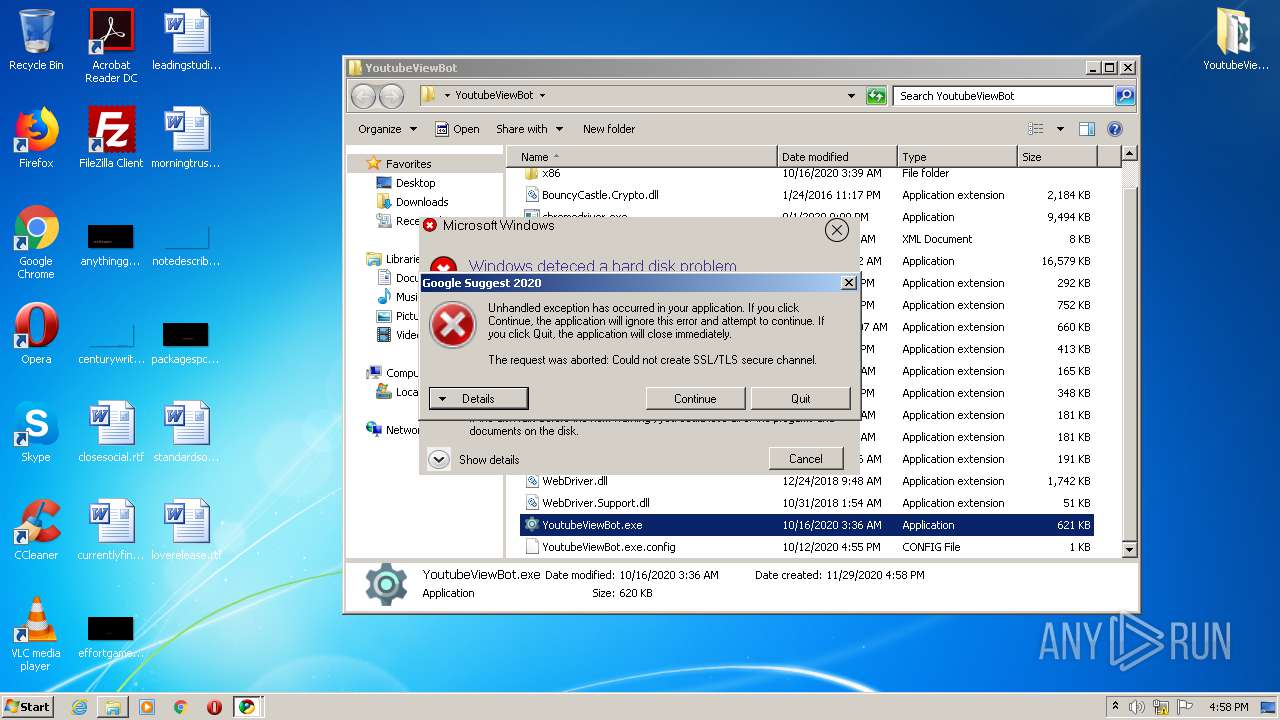
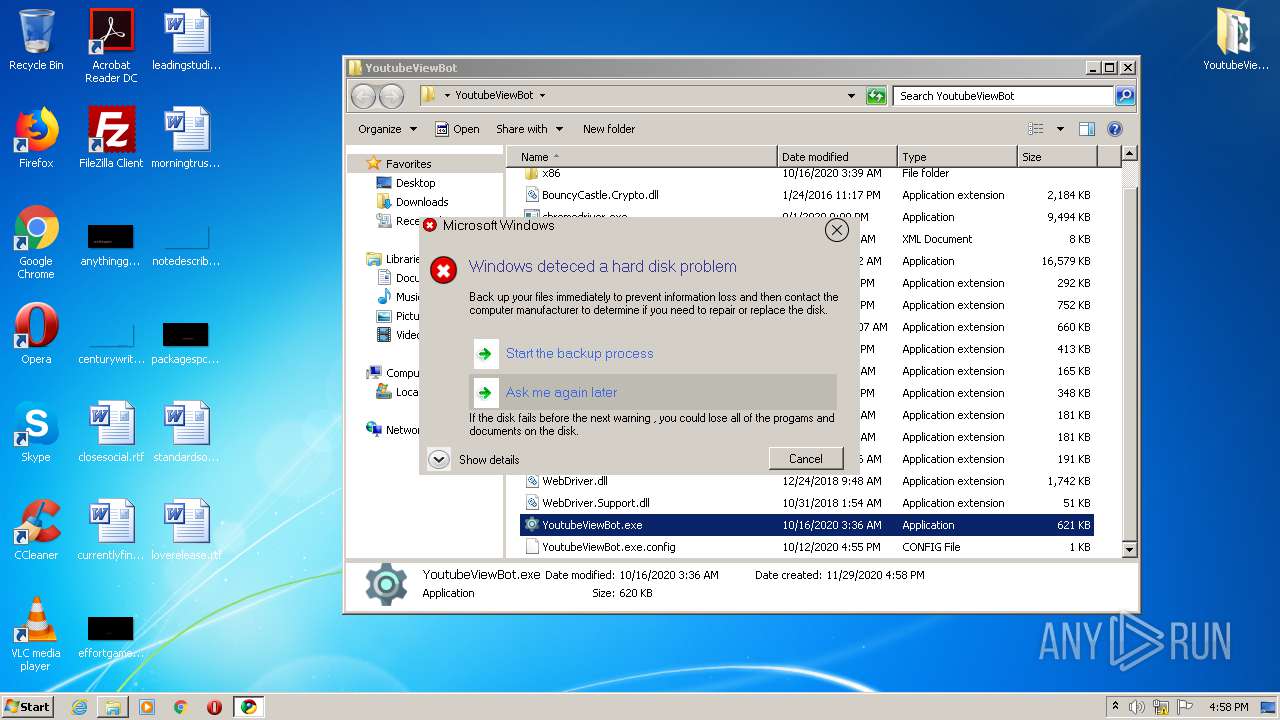
2592 | YoutubeViewBot.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1256 | nslookup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (myip.opendns .com in DNS lookup) |
1256 | nslookup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (myip.opendns .com in DNS lookup) |
2592 | YoutubeViewBot.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1032 | YoutubeViewBot.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1032 | YoutubeViewBot.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2652 | nslookup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (myip.opendns .com in DNS lookup) |
2652 | nslookup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (myip.opendns .com in DNS lookup) |
Process | Message |
|---|---|
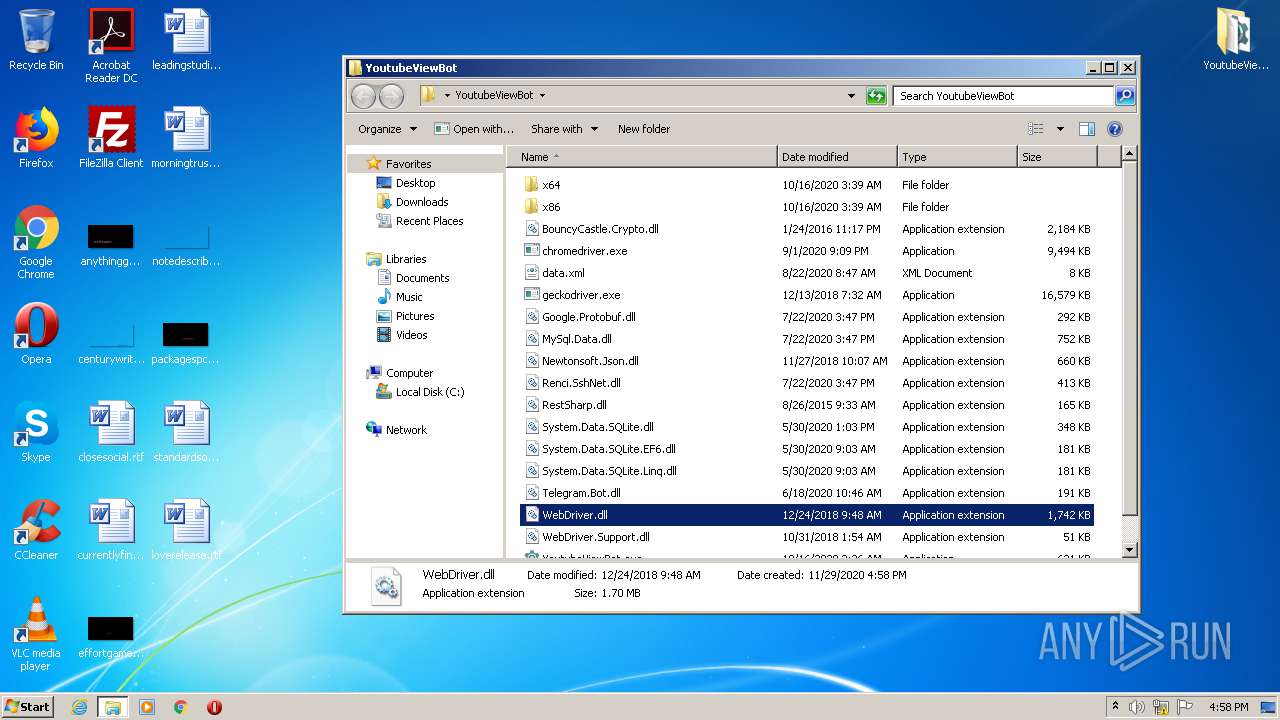
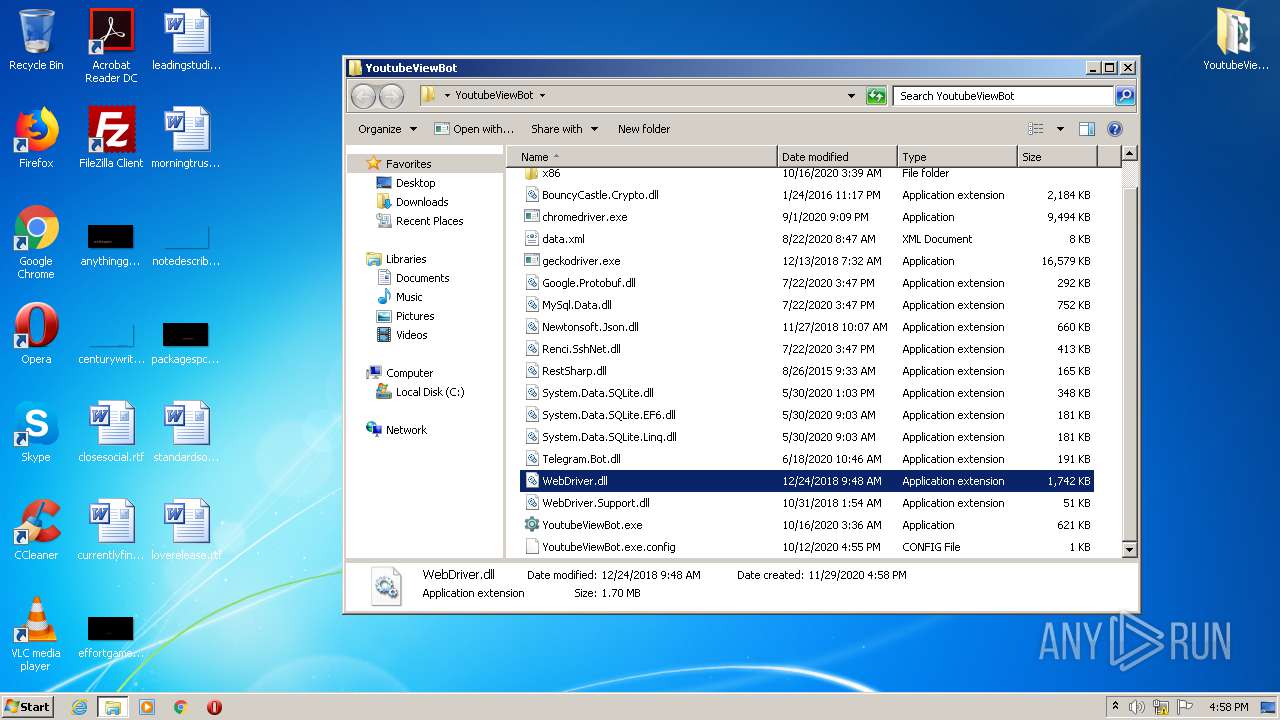
YoutubeViewBot.exe | Native library pre-loader is trying to load native SQLite library "C:\Users\admin\Desktop\YoutubeViewBot\x86\SQLite.Interop.dll"...
|
YoutubeViewBot.exe | Native library pre-loader is trying to load native SQLite library "C:\Users\admin\Desktop\YoutubeViewBot\x86\SQLite.Interop.dll"...
|