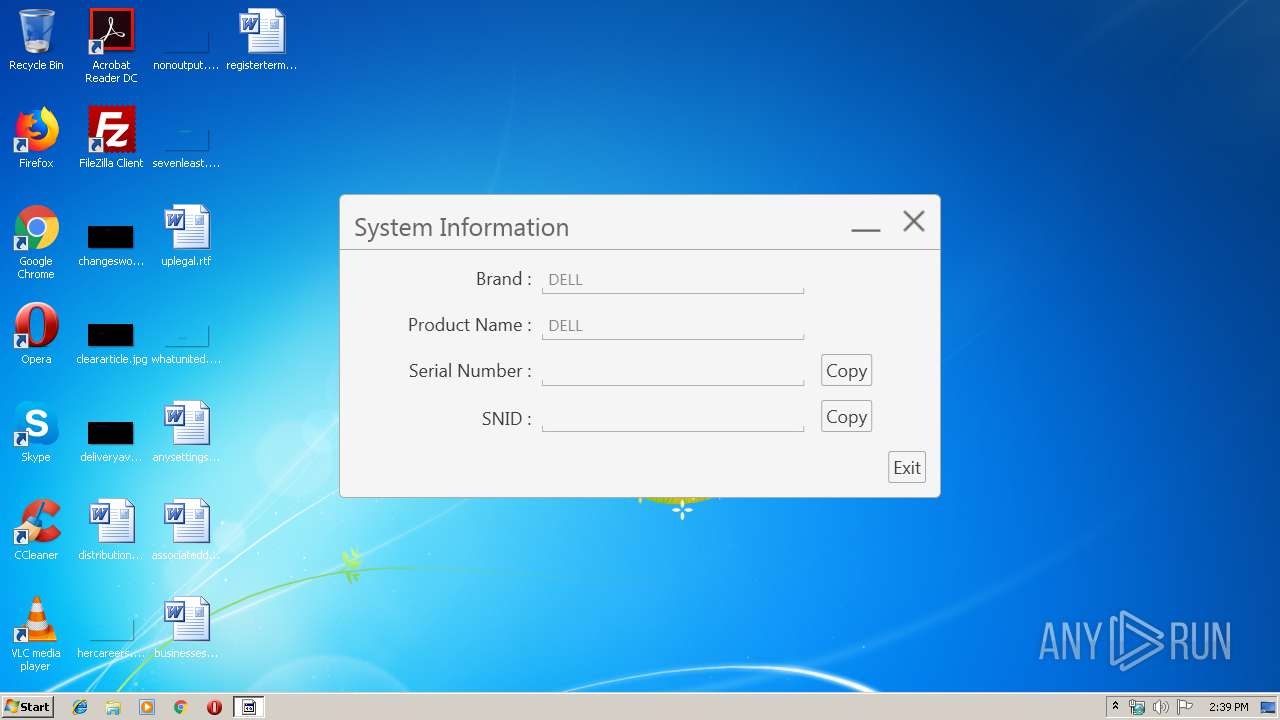
| File name: | SerialNumberDetectionTool.exe |
| Full analysis: | https://app.any.run/tasks/13e52f59-8828-4b76-9b46-08db0ba86e73 |
| Verdict: | No threats detected |
| Analysis date: | April 18, 2019, 13:38:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 098F46A9EE823B240A775C1139457B2C |
| SHA1: | 7245770B360E67A7076228DC67D6B4F6B68346F5 |
| SHA256: | 12795968DB92CA31033C0F3A0F360E502C43DEA3C04A66A944351CBC6BDE6C28 |
| SSDEEP: | 1536:JxqjQ+P04wsmJCLtvOsFToV3rIEwOfKi+tkkVMMX77i+r6xujGNg7SH4NAcymzl+:sr85CDWxmvC7X9 |
MALICIOUS
Application was dropped or rewritten from another process
- SerialNumberDetectionTool.exe (PID: 2276)
SUSPICIOUS
Executable content was dropped or overwritten
- SerialNumberDetectionTool.exe (PID: 2940)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 6 (93.8) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (2.3) |
| .exe | | | Win32 Executable (generic) (1.6) |
| .exe | | | Win16/32 Executable Delphi generic (0.7) |
| .exe | | | Generic Win/DOS Executable (0.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 29696 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x80e4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000722C | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51167 |
DATA | 0x00009000 | 0x00000218 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.1517 |
BSS | 0x0000A000 | 0x0000A899 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00015000 | 0x00000864 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.17386 |
.tls | 0x00016000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00017000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x00018000 | 0x000005CC | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.44309 |
.rsrc | 0x00019000 | 0x00001400 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 1.29674 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 0 | 4264 | UNKNOWN | Russian - Russia | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 6.90278 | 172 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 1.7815 | 20 | UNKNOWN | Russian - Russia | RT_GROUP_ICON |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
34
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2276 | "C:\Users\admin\AppData\Local\Temp\3582-490\SerialNumberDetectionTool.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\SerialNumberDetectionTool.exe | SerialNumberDetectionTool.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AutoDetectSerialNumber Exit code: 0 Version: 1.0.0.3004 Modules
| |||||||||||||||
| 2940 | "C:\Users\admin\AppData\Local\Temp\SerialNumberDetectionTool.exe" | C:\Users\admin\AppData\Local\Temp\SerialNumberDetectionTool.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3496 | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: PresentationFontCache.exe Exit code: 0 Version: 3.0.6920.4902 built by: NetFXw7 Modules
| |||||||||||||||
Total events
394
Read events
377
Write events
17
Delete events
0
Modification events
| (PID) Process: | (2940) SerialNumberDetectionTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2940) SerialNumberDetectionTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2276) SerialNumberDetectionTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2276) SerialNumberDetectionTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: SerialNumberDetectionTool.exe | |||
| (PID) Process: | (2276) SerialNumberDetectionTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\CTF\CUAS\DefaultCompositionWindow |
| Operation: | write | Name: | Left |
Value: 0 | |||
| (PID) Process: | (2276) SerialNumberDetectionTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\CTF\CUAS\DefaultCompositionWindow |
| Operation: | write | Name: | Top |
Value: 0 | |||
Executable files
1
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2276 | SerialNumberDetectionTool.exe | C:\Users\admin\AppData\Local\Temp\CabFD44.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | SerialNumberDetectionTool.exe | C:\Users\admin\AppData\Local\Temp\TarFD45.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | SerialNumberDetectionTool.exe | C:\Users\admin\AppData\Local\Temp\CabFD65.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | SerialNumberDetectionTool.exe | C:\Users\admin\AppData\Local\Temp\TarFD66.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | SerialNumberDetectionTool.exe | C:\Users\admin\AppData\Local\Temp\Cab1FB.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | SerialNumberDetectionTool.exe | C:\Users\admin\AppData\Local\Temp\Tar1FC.tmp | — | |
MD5:— | SHA256:— | |||
| 2276 | SerialNumberDetectionTool.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94308059B57B3142E455B38A6EB92015 | compressed | |
MD5:— | SHA256:— | |||
| 2276 | SerialNumberDetectionTool.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
| 2940 | SerialNumberDetectionTool.exe | C:\Users\admin\AppData\Local\Temp\tmp5023.tmp | binary | |
MD5:— | SHA256:— | |||
| 2940 | SerialNumberDetectionTool.exe | C:\Users\admin\AppData\Local\Temp\3582-490\SerialNumberDetectionTool.exe | executable | |
MD5:72A03D0CD0BB0745704BBB02BB161187 | SHA256:E272684DBBD922D828968BBC7DB79FE495FBC5CDAD25F91BDDB6A603558278FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2276 | SerialNumberDetectionTool.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2276 | SerialNumberDetectionTool.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |