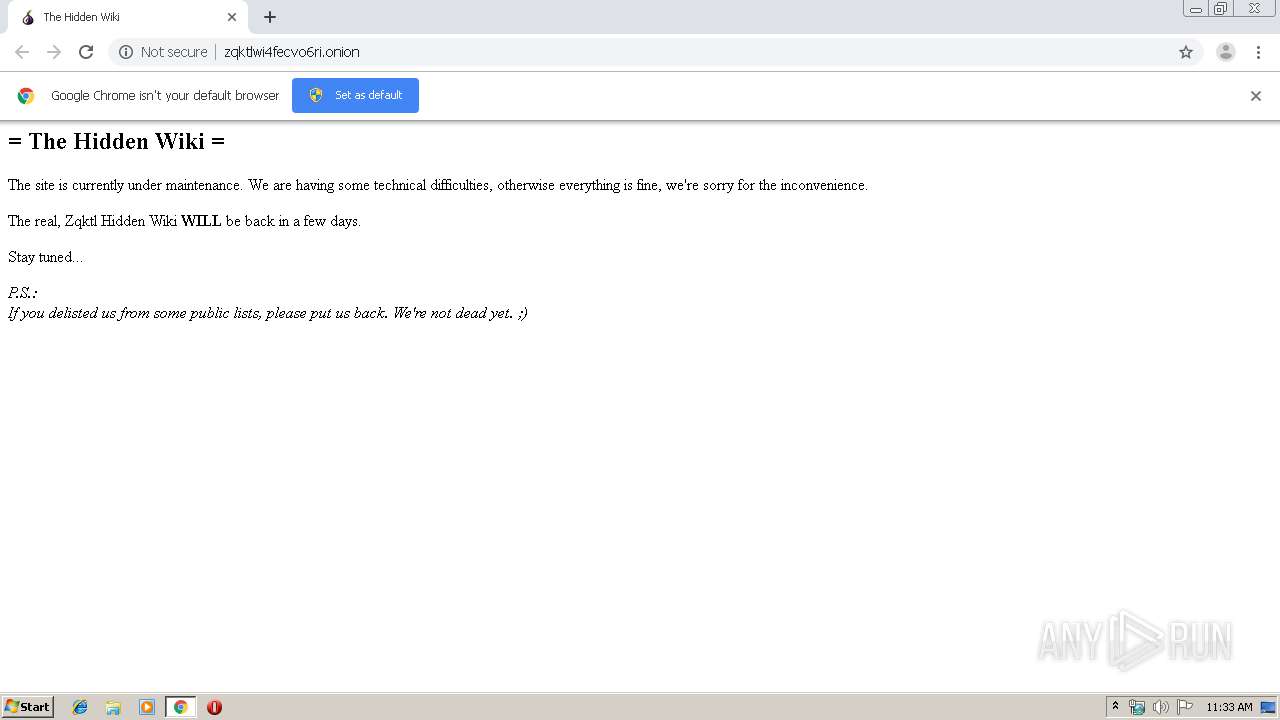
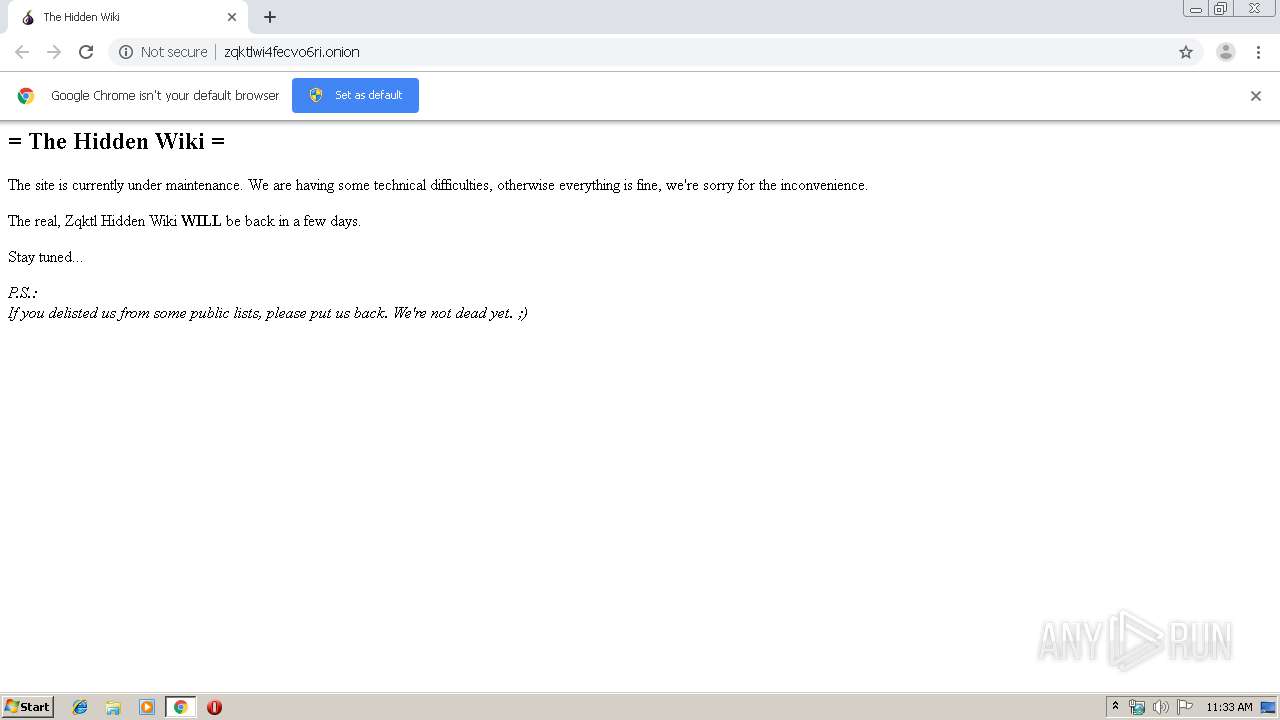
| URL: | http://zqktlwi4fecvo6ri.onion |
| Full analysis: | https://app.any.run/tasks/56f35c59-a86b-4cdc-a166-1ae2234aae72 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 10:32:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9D58E72084D32291BDB22A30920E8FA4 |
| SHA1: | B714E0FE783046806E92A3237722B57BC6A5DB71 |
| SHA256: | 1271F80513F91D0C5FD37812202C894FE372F26748EA8ABD9BD54B058228238A |
| SSDEEP: | 3:N1KEXR9lSbB:CEXXlSB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2428)
INFO
Reads the hosts file
- chrome.exe (PID: 2428)
- chrome.exe (PID: 1856)
Application launched itself
- chrome.exe (PID: 2428)
Reads settings of System Certificates
- chrome.exe (PID: 1856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
36
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,354074665677595639,13888712457643397029,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8855961990393259810 --mojo-platform-channel-handle=4616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,354074665677595639,13888712457643397029,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6262604570994492637 --mojo-platform-channel-handle=4080 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,354074665677595639,13888712457643397029,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6002628797828208739 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,354074665677595639,13888712457643397029,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3140328732781946177 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,354074665677595639,13888712457643397029,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11046240594675075362 --mojo-platform-channel-handle=4564 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,354074665677595639,13888712457643397029,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1720681964894795109 --mojo-platform-channel-handle=4368 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2580 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,354074665677595639,13888712457643397029,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13963348343229473385 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,354074665677595639,13888712457643397029,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10947363229468480377 --mojo-platform-channel-handle=3948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,354074665677595639,13888712457643397029,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13509317673699931120 --mojo-platform-channel-handle=1528 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
632
Read events
526
Write events
101
Delete events
5
Modification events
| (PID) Process: | (1316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2428-13215522770427875 |
Value: 259 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
65
Text files
270
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a6186117-6680-4cc0-bc62-762ef4af7af2.tmp | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a821.TMP | text | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a86f.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
50
DNS requests
33
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
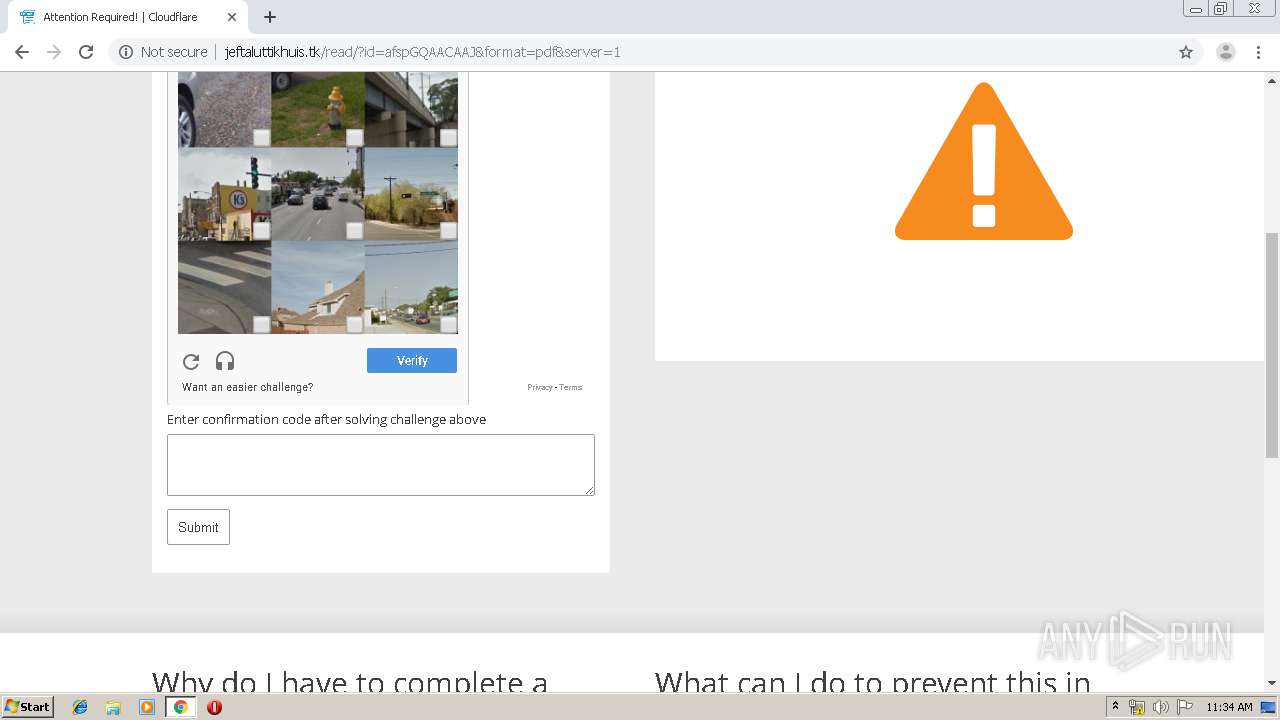
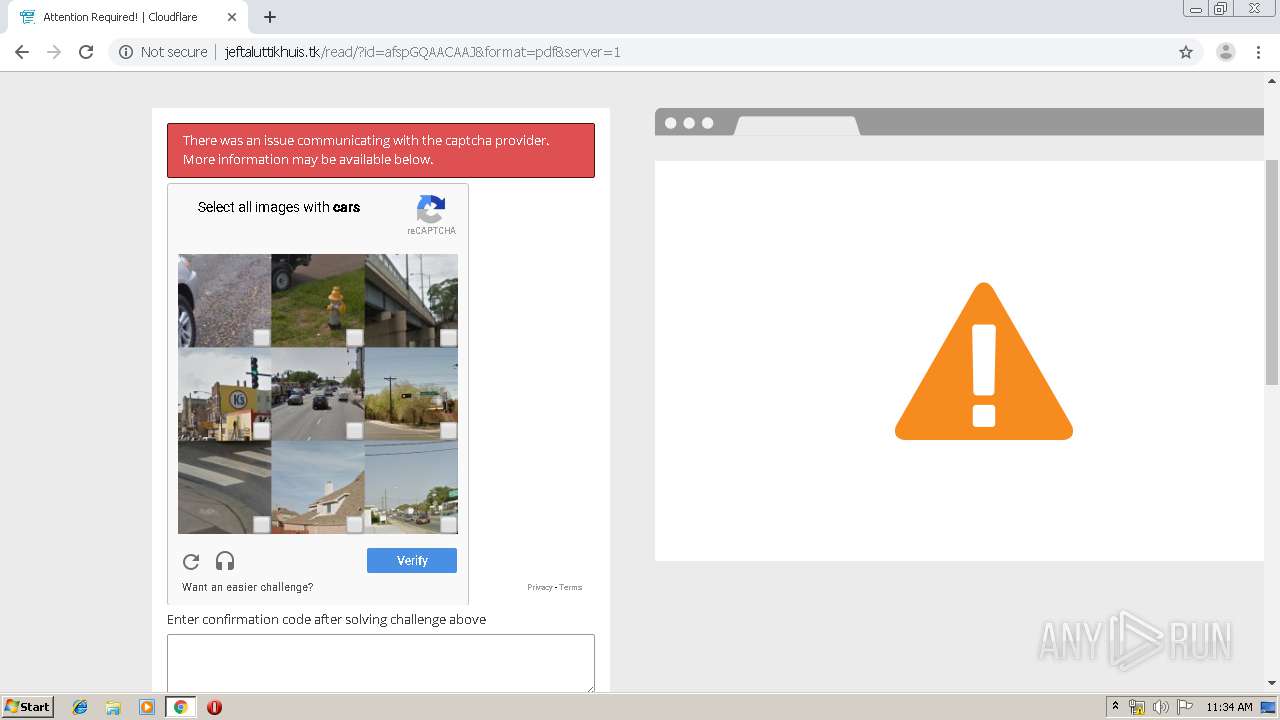
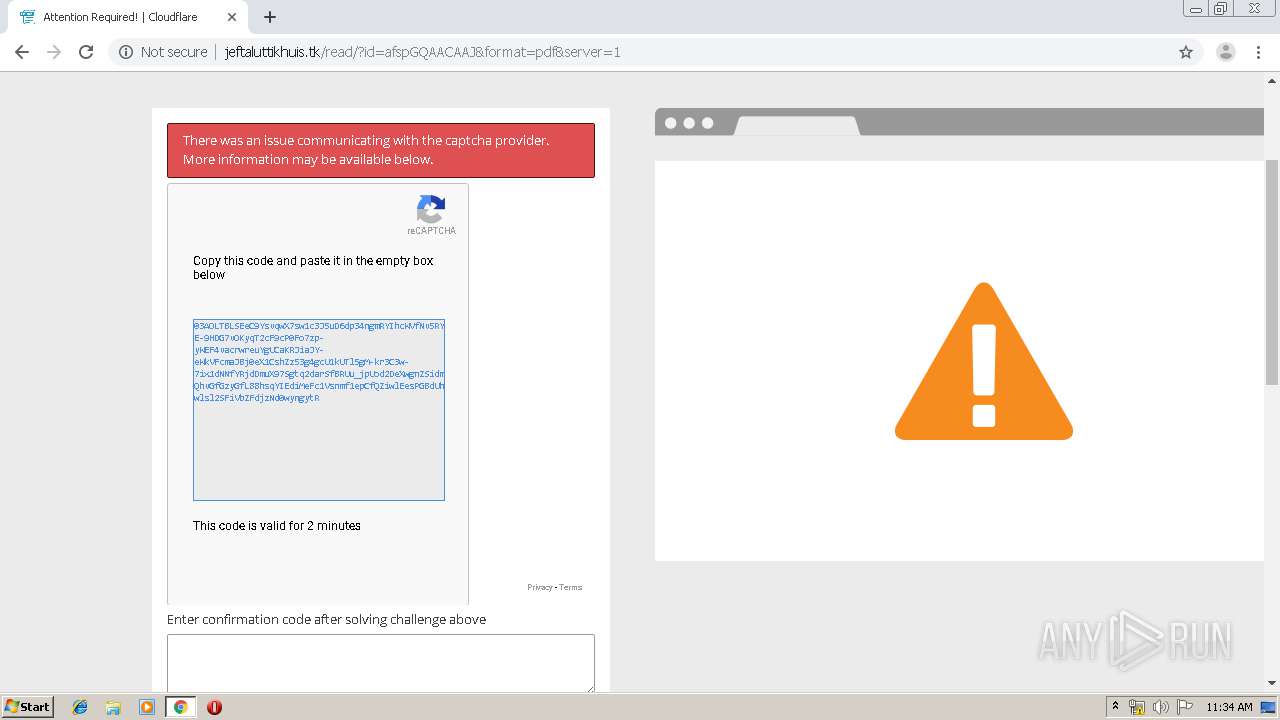
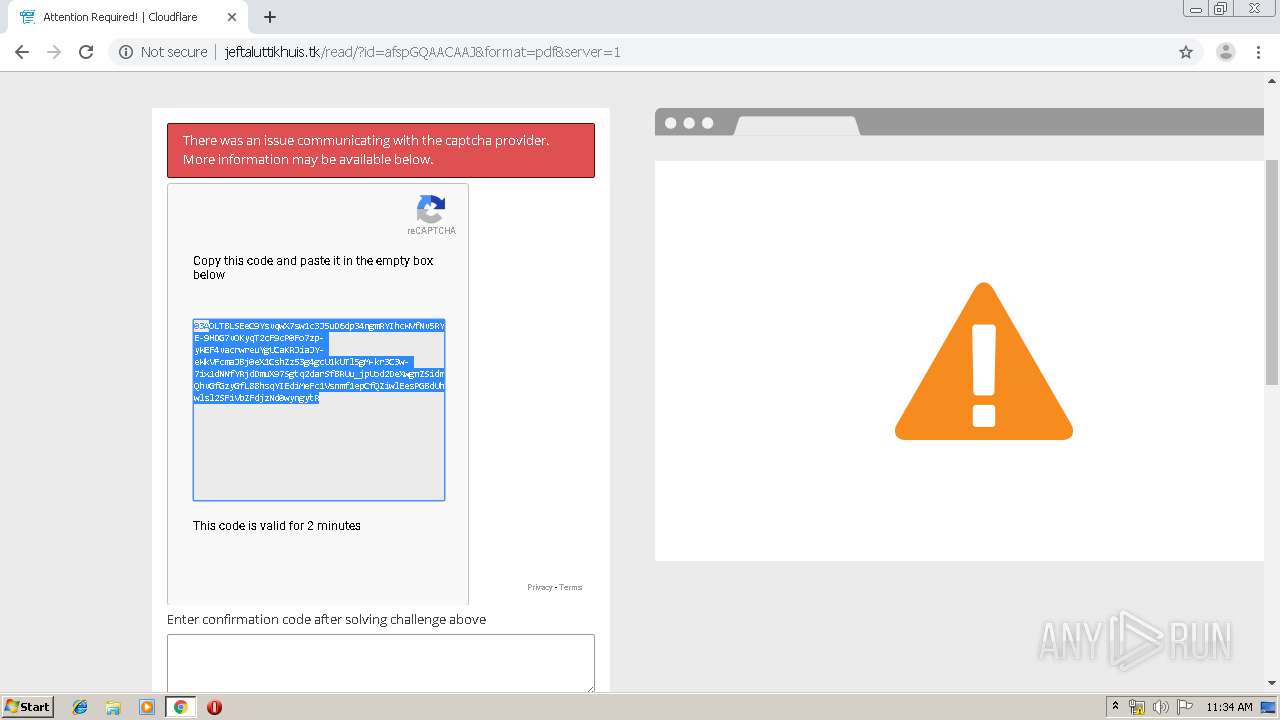
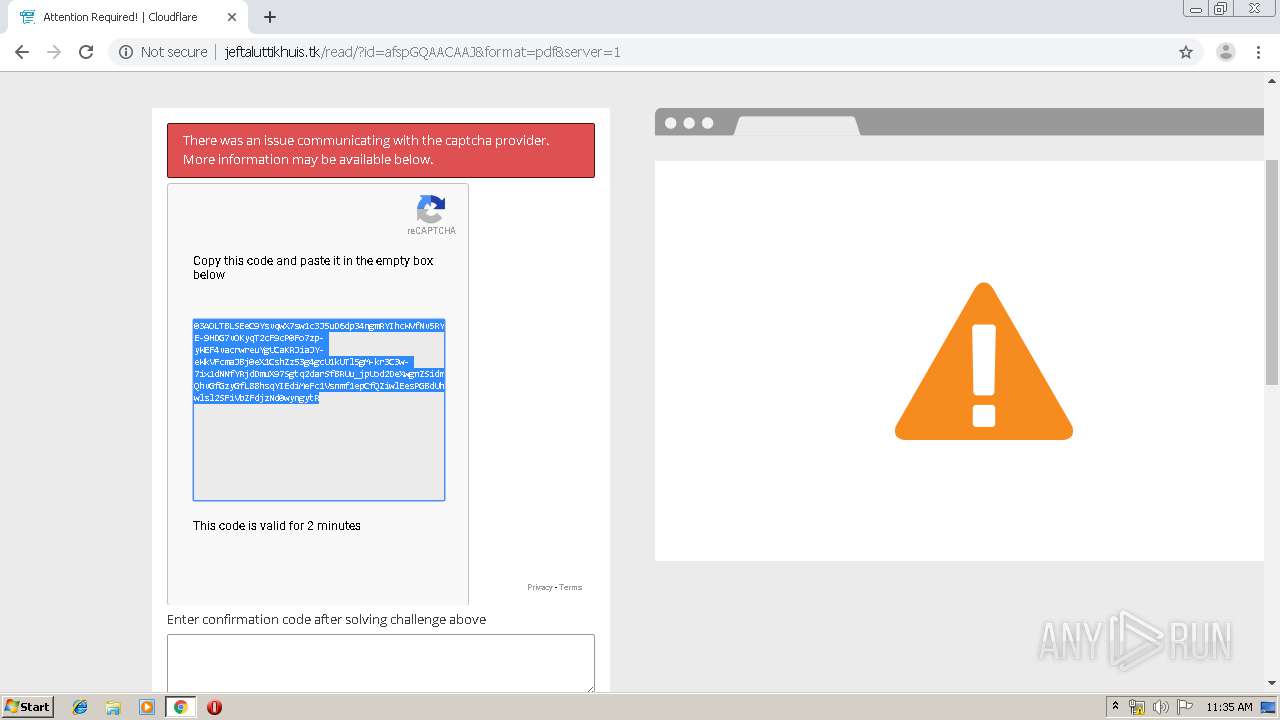
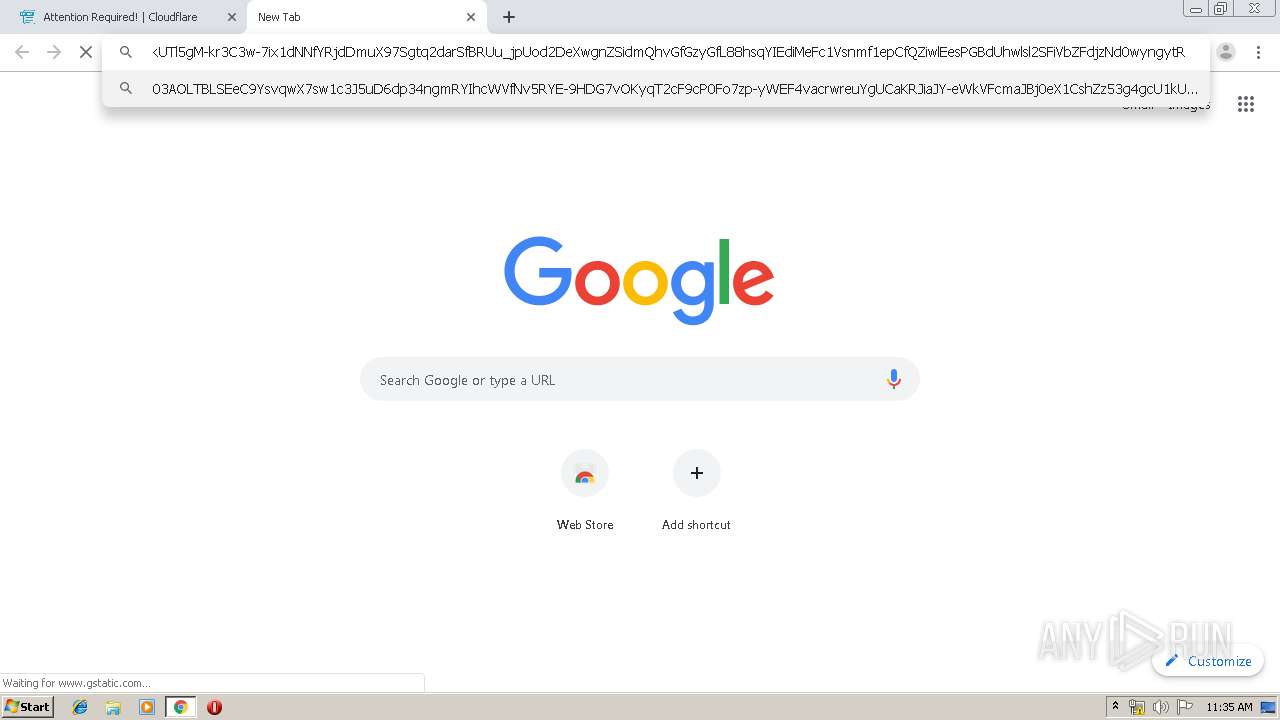
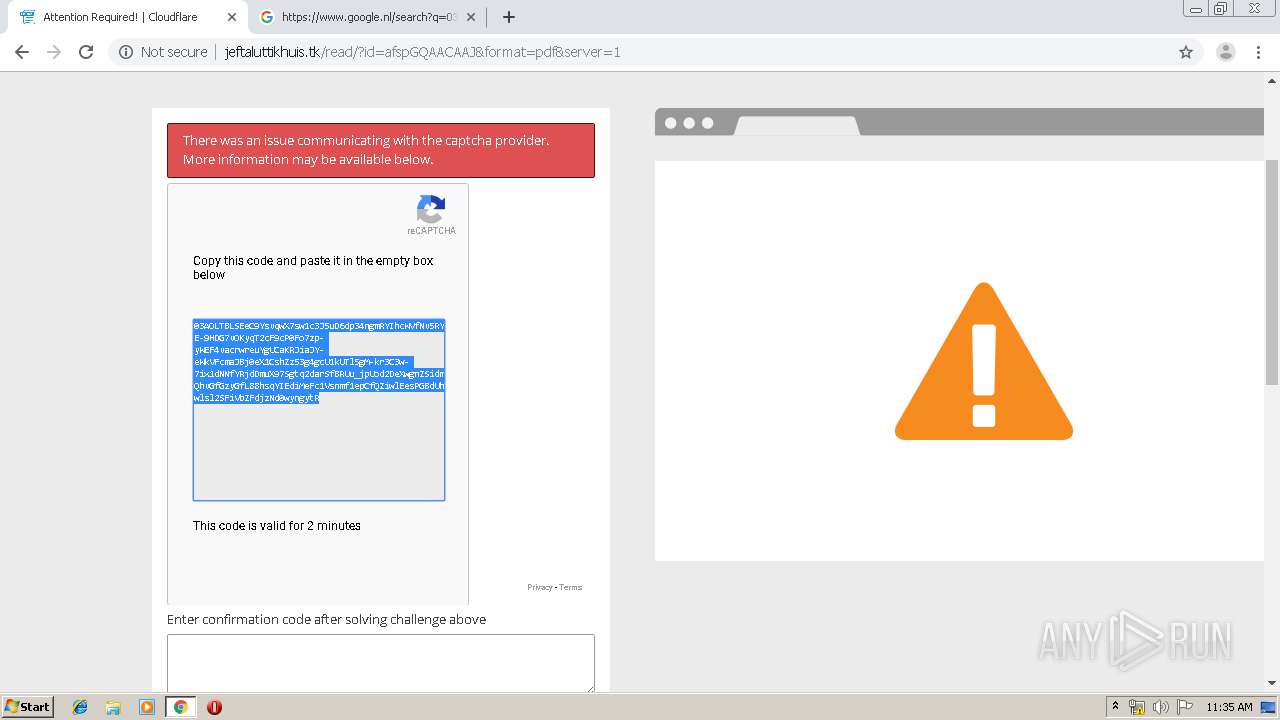
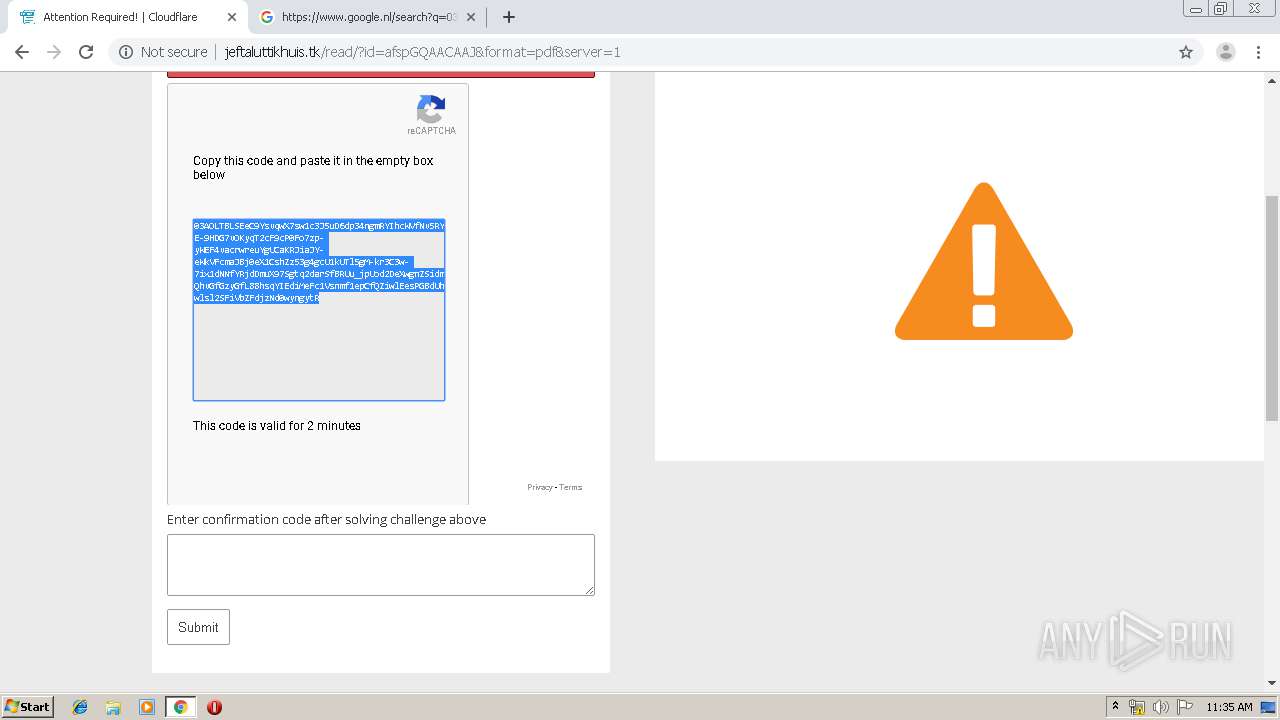
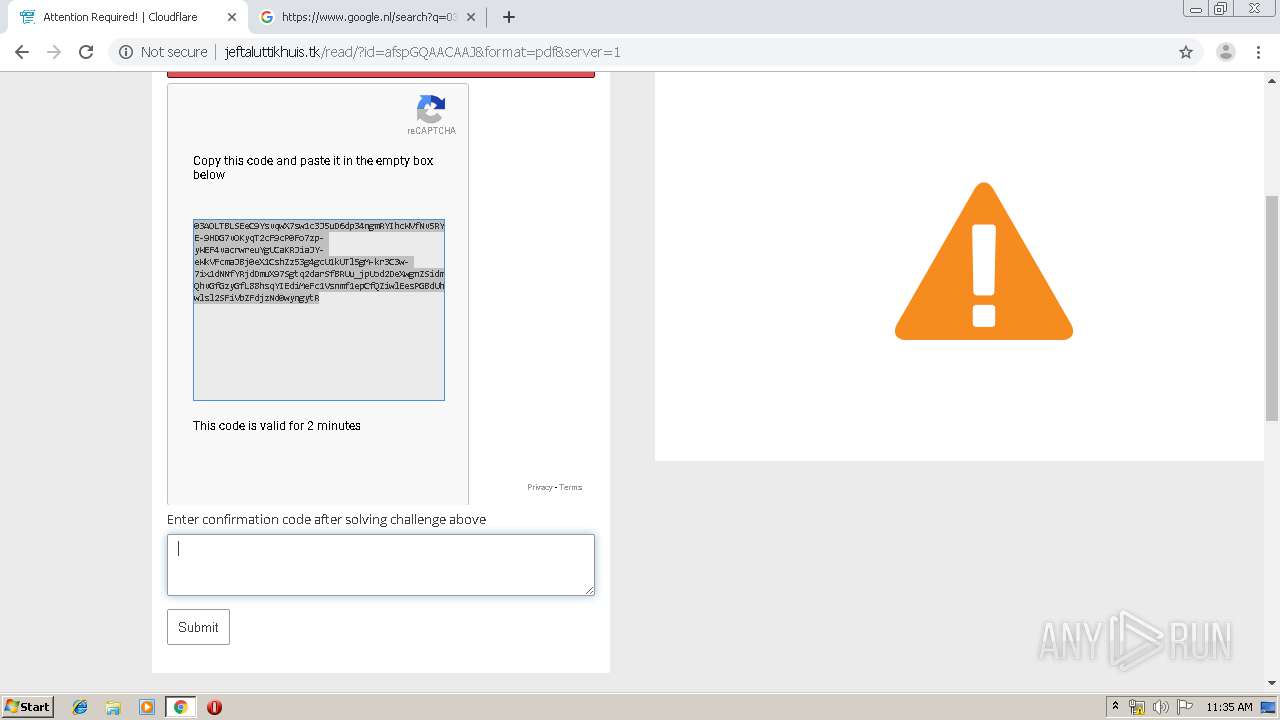
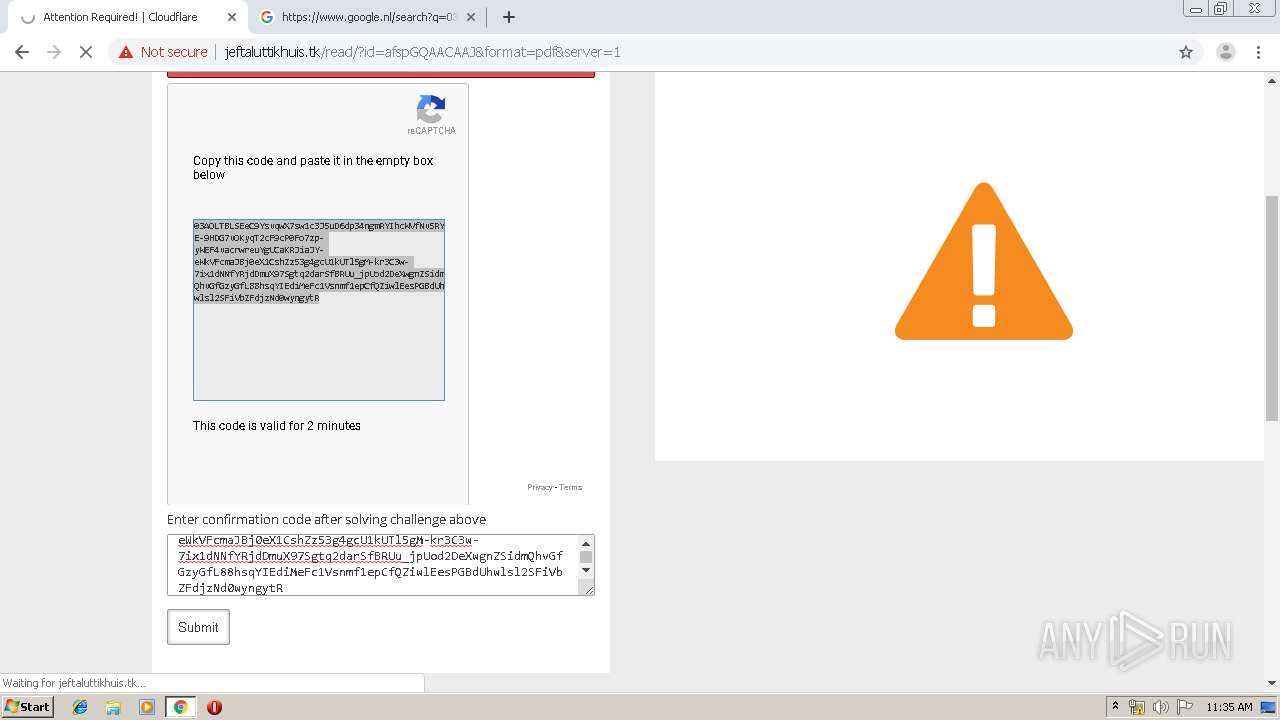
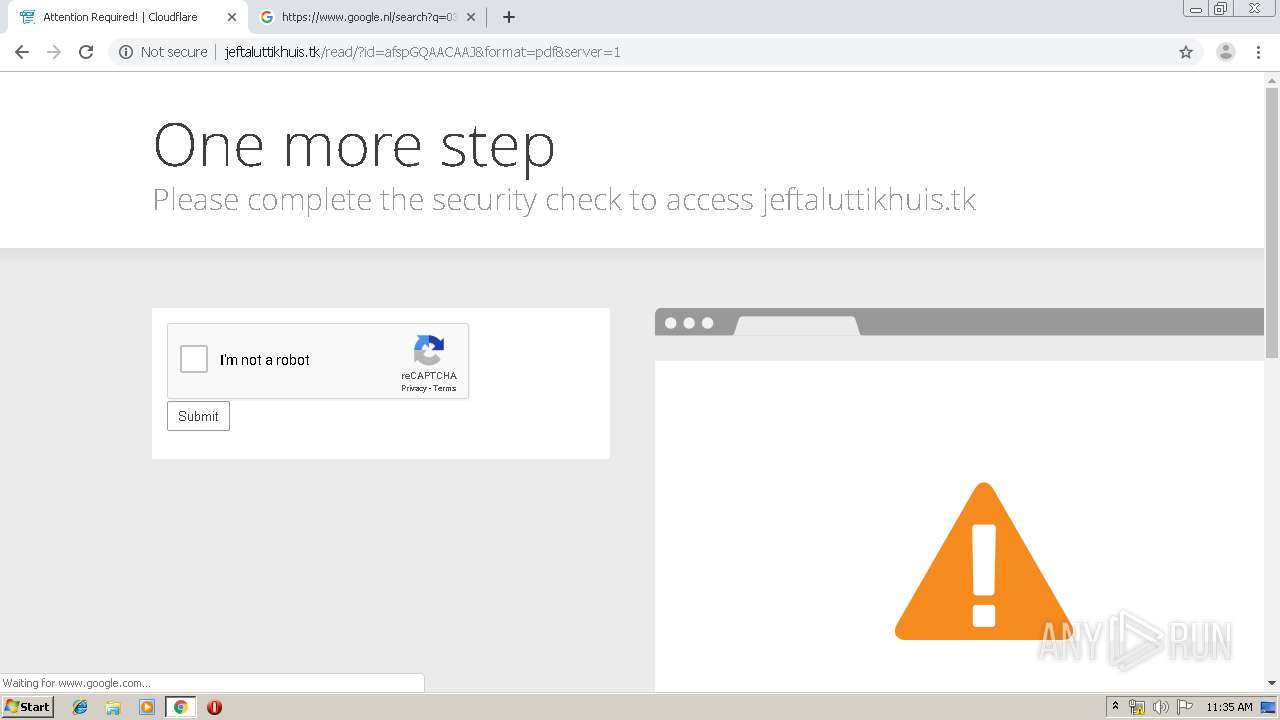
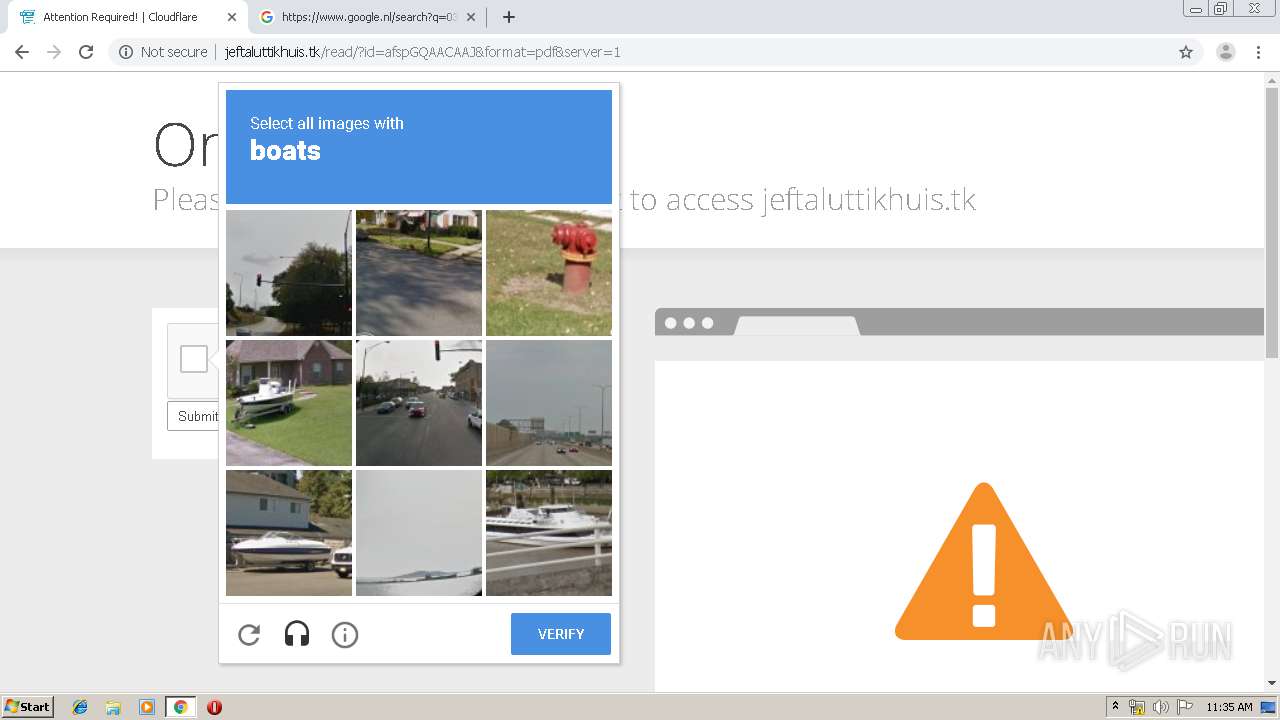
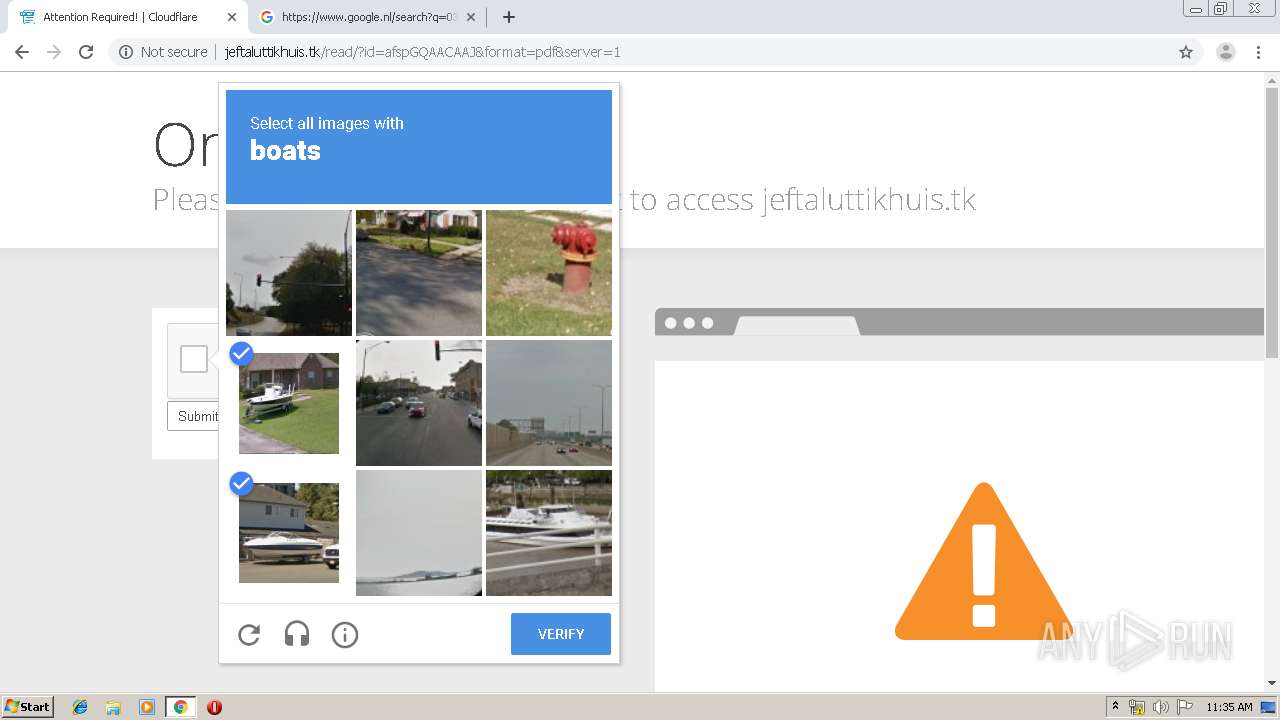
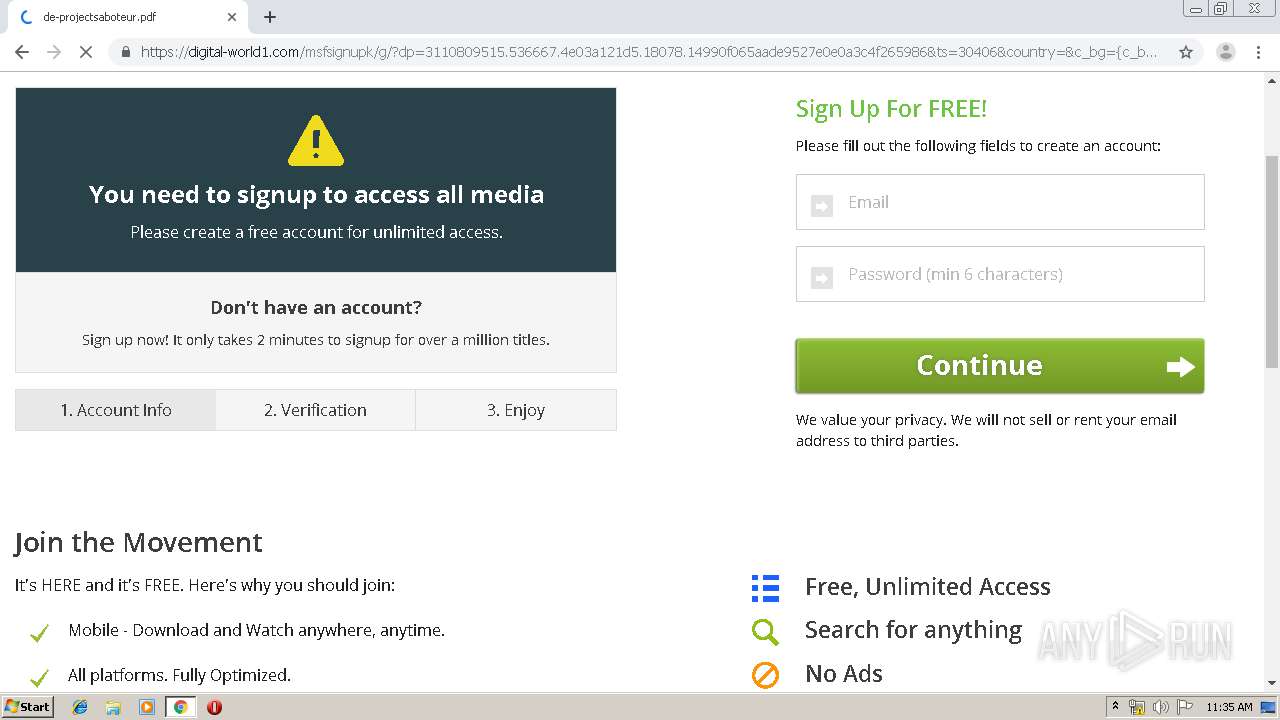
1856 | chrome.exe | GET | 302 | 104.27.142.217:80 | http://jeftaluttikhuis.tk/cdn-cgi/l/chk_captcha?s=e870d929b3dcf307a5df45fd6622590e2aef27b4-1571049319-0-ASMhzqkuQlEFFAcxlt6ykCwRFnAy5ZMl9Ql8oI7CKRfpkJfRzQbMHsokDfzvUdauFsA6b0QGOwuMWxMaQCGCR300gCWZKHEBzRdlMBjqH9AEqQh4p4PMjkWBta44FXQAlx0A9DHzPrp4M4eX5iouYU7ADNa4JVy2HFMjN35F6nSx6HKg5ejxXxlHRdlsg3MdGIvM5Zym7GzTIqTk87Z%2FassQyfhDvuFVLIYvIho%2FIBIdxYBCm8ESsKxhBKqacP2EDQ%3D%3D&id=5258e7e478b6bf32&g-recaptcha-response=03AOLTBLQFGgcSQcp7x86VLV-c2OtHpf-vd-UcGy4VovNemqxKWZZnX4K87ySqHH7UikbMygfKESJNFQ_cZwAe4BwTkersVFdhUQq00Dhf3nR3UeLIVJqmfAH6Dl-vqe4nBxWivcYf6AV0-VKBsMWKmtF1ahQN6YnDgnvhTzWQtdfEloBonlaIIOn6FAg9KBrrA6paD2zIjQodGhgg1P65pBk6EgD6hSBcAZp4UB9BJmst2KHuctQJnyKxK1eNMwBt4fr4KF98mFLoYI9plSqskb8gRH4Y9dIFErrraxFTGToUWsbDLxiNapsekdgr42Kw9HsUOUbagfjjsomrLPT4l7sYDXKEzuQwXVKb8cUndhiL4dEFRl1G9XTdYYqb6ngSp2GOnPzyGiHVnyz6764sNttAgerhJkOYVFweOH1UEbr9LBmUpuoRA0dlTmRtAI3vEVZ-LWfVptrBjpL_Sx7QKJtFBKcVZ08__04-WImrke8rXmi1edMAK1GI7P07OpbIJUtLJD41kTZ4&cv_chal_result=%5B%22be2cece62c8e9f0cf25cfc58029bc674%22%2C%2260cf537b24fa6f2e41ca2c6f1a2f67cd%22%5D&cv_chal_fp=%7B%22r%22%3A%5B1280%2C720%5D%2C%22ar%22%3A%5B692%2C1280%5D%2C%22pr%22%3A1%2C%22cd%22%3A24%7D&bf_challenge_id=689&bf_execution_time=2&bf_result_hash=3469217798 | US | — | 159 b | suspicious |
1856 | chrome.exe | GET | 200 | 104.27.142.217:80 | http://jeftaluttikhuis.tk/favicon.ico | US | image | 309 b | suspicious |
1856 | chrome.exe | GET | 302 | 172.217.20.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
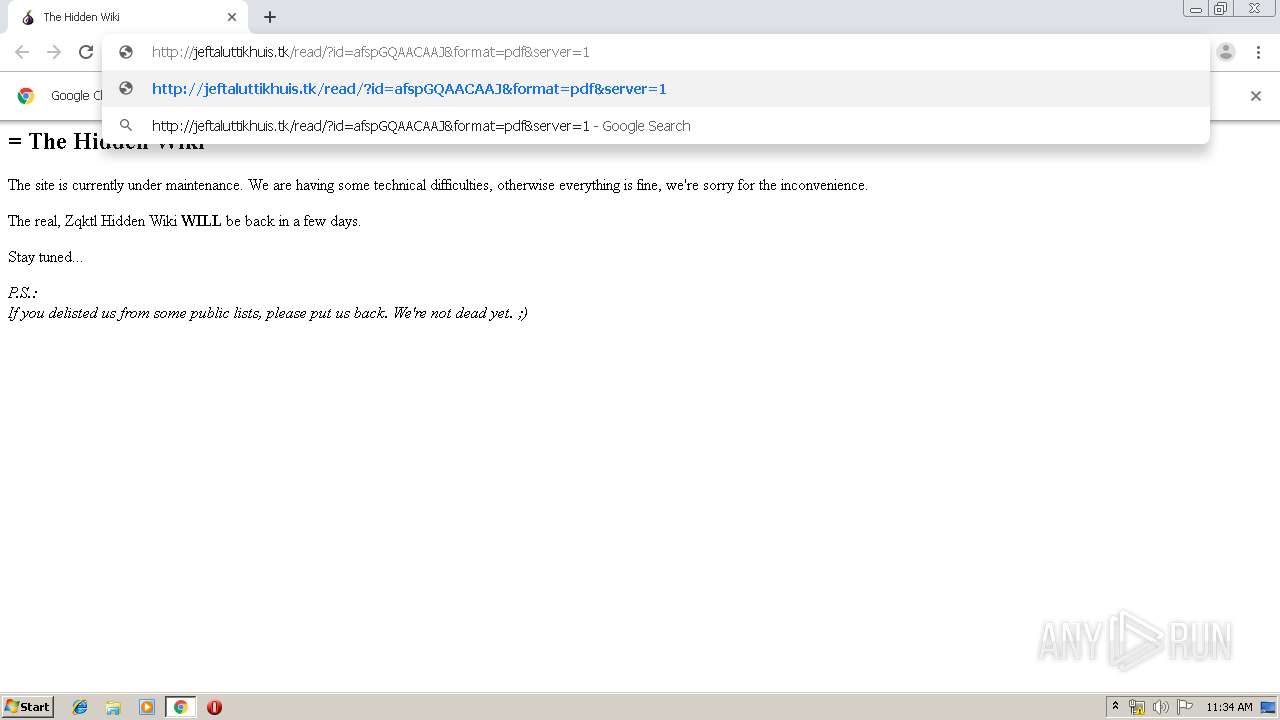
1856 | chrome.exe | GET | 403 | 104.27.142.217:80 | http://jeftaluttikhuis.tk/read/?id=afspGQAACAAJ&format=pdf&server=1 | US | html | 15.3 Kb | suspicious |
1856 | chrome.exe | GET | 302 | 172.217.20.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
1856 | chrome.exe | GET | 200 | 10.206.160.207:80 | http://zqktlwi4fecvo6ri.onion/ | unknown | html | 285 b | unknown |
1856 | chrome.exe | GET | 200 | 104.27.142.217:80 | http://jeftaluttikhuis.tk/cdn-cgi/scripts/cf.common.js | US | text | 1.94 Kb | suspicious |
1856 | chrome.exe | GET | 200 | 104.27.142.217:80 | http://jeftaluttikhuis.tk/cdn-cgi/scripts/cf.challenge.js | US | text | 3.20 Kb | suspicious |
1856 | chrome.exe | GET | 200 | 104.27.142.217:80 | http://jeftaluttikhuis.tk/cdn-cgi/styles/cf.errors.css | US | text | 4.77 Kb | suspicious |
1856 | chrome.exe | GET | 200 | 104.27.142.217:80 | http://jeftaluttikhuis.tk/cdn-cgi/scripts/zepto.min.js | US | text | 9.12 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1856 | chrome.exe | 10.206.160.207:80 | zqktlwi4fecvo6ri.onion | — | — | unknown |
1856 | chrome.exe | 172.217.17.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1856 | chrome.exe | 172.217.20.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
1856 | chrome.exe | 172.217.20.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1856 | chrome.exe | 216.58.208.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1856 | chrome.exe | 74.125.100.7:80 | r2---sn-5hnekn7l.gvt1.com | Google Inc. | US | whitelisted |
1856 | chrome.exe | 74.125.8.140:80 | r6---sn-5hnednlk.gvt1.com | Google Inc. | US | whitelisted |
1856 | chrome.exe | 104.27.142.217:80 | jeftaluttikhuis.tk | Cloudflare Inc | US | shared |
1856 | chrome.exe | 104.19.196.151:443 | ajax.cloudflare.com | Cloudflare Inc | US | shared |
1856 | chrome.exe | 172.217.168.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zqktlwi4fecvo6ri.onion |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
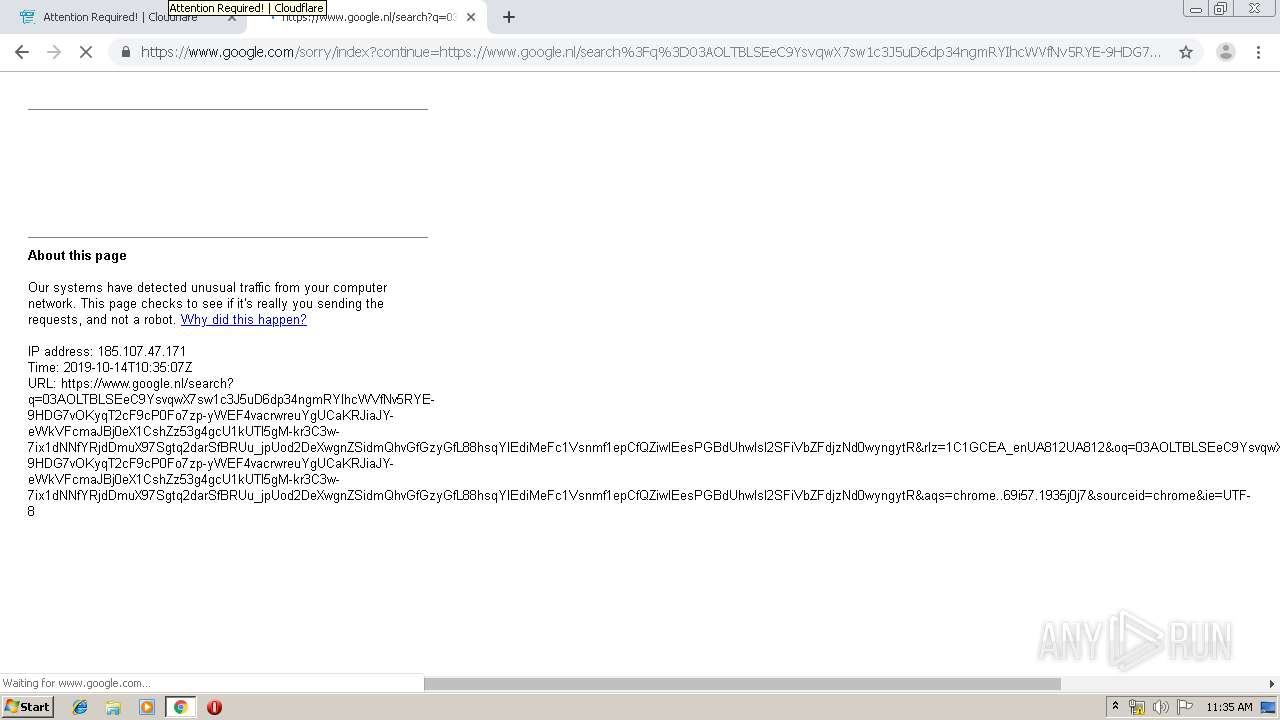
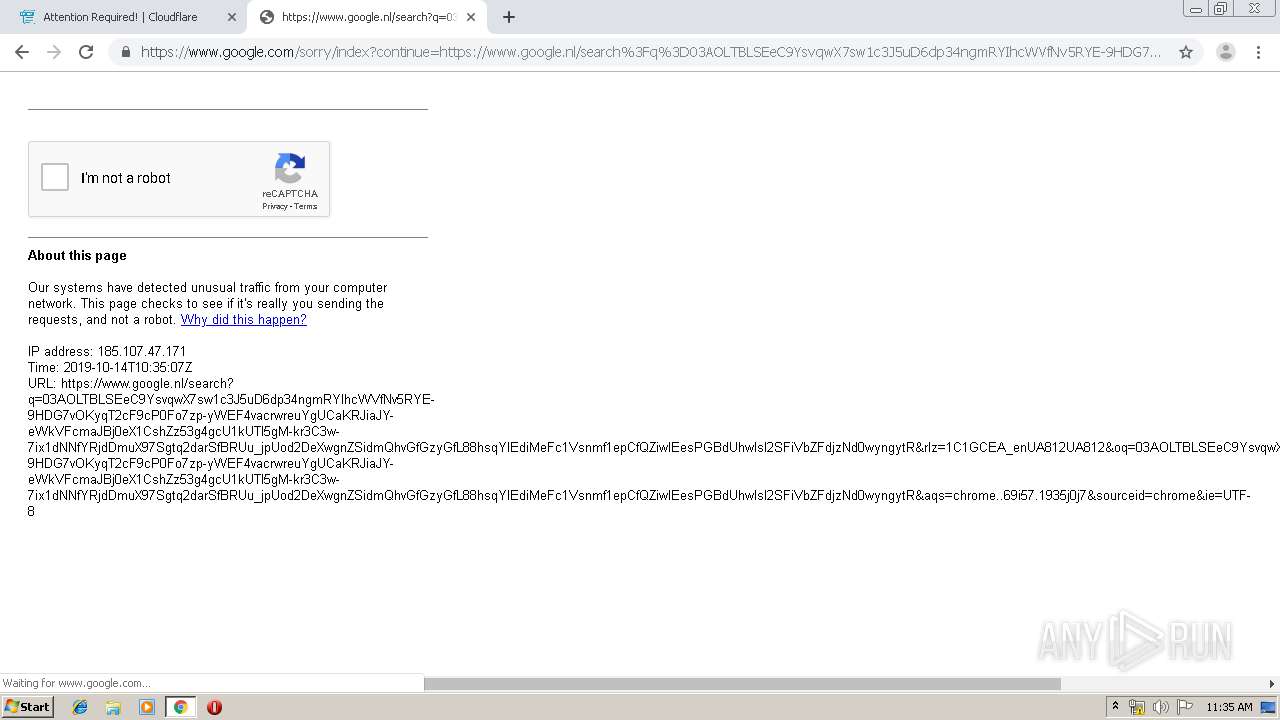
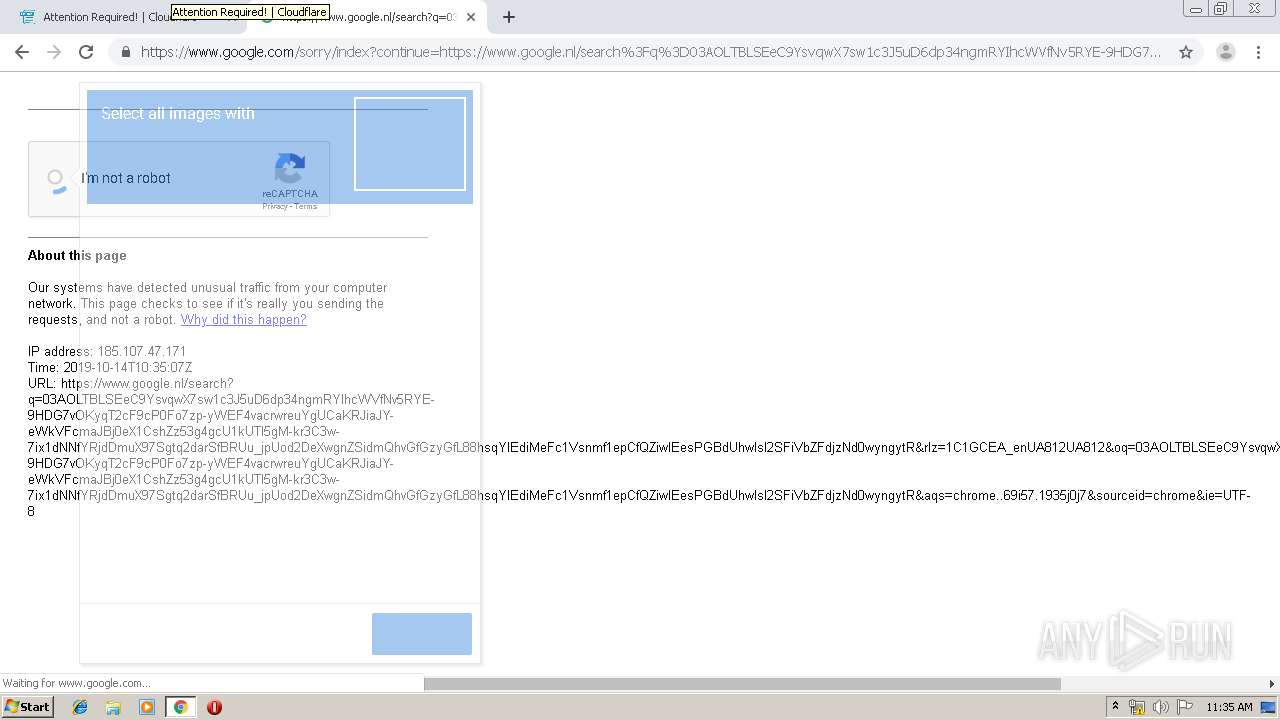
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-5hnekn7l.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
r6---sn-5hnednlk.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1856 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
1856 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
1856 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
1856 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
1856 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
1856 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
1856 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
1856 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |