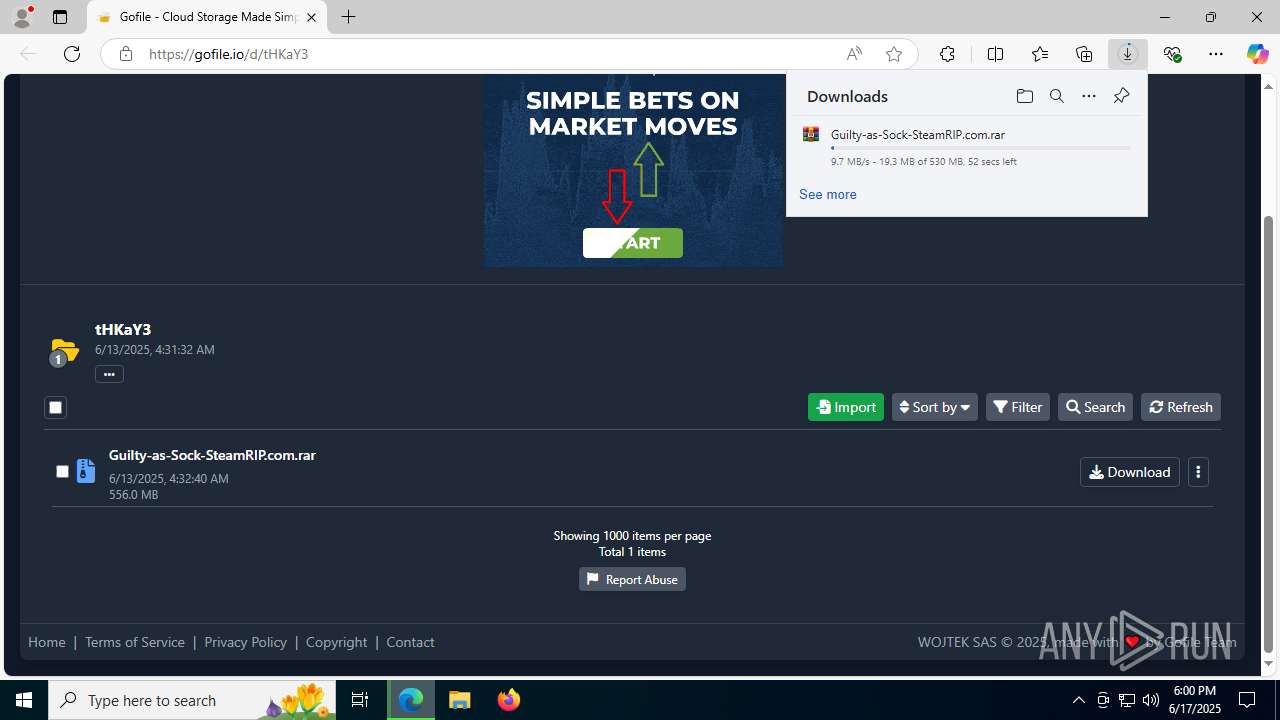
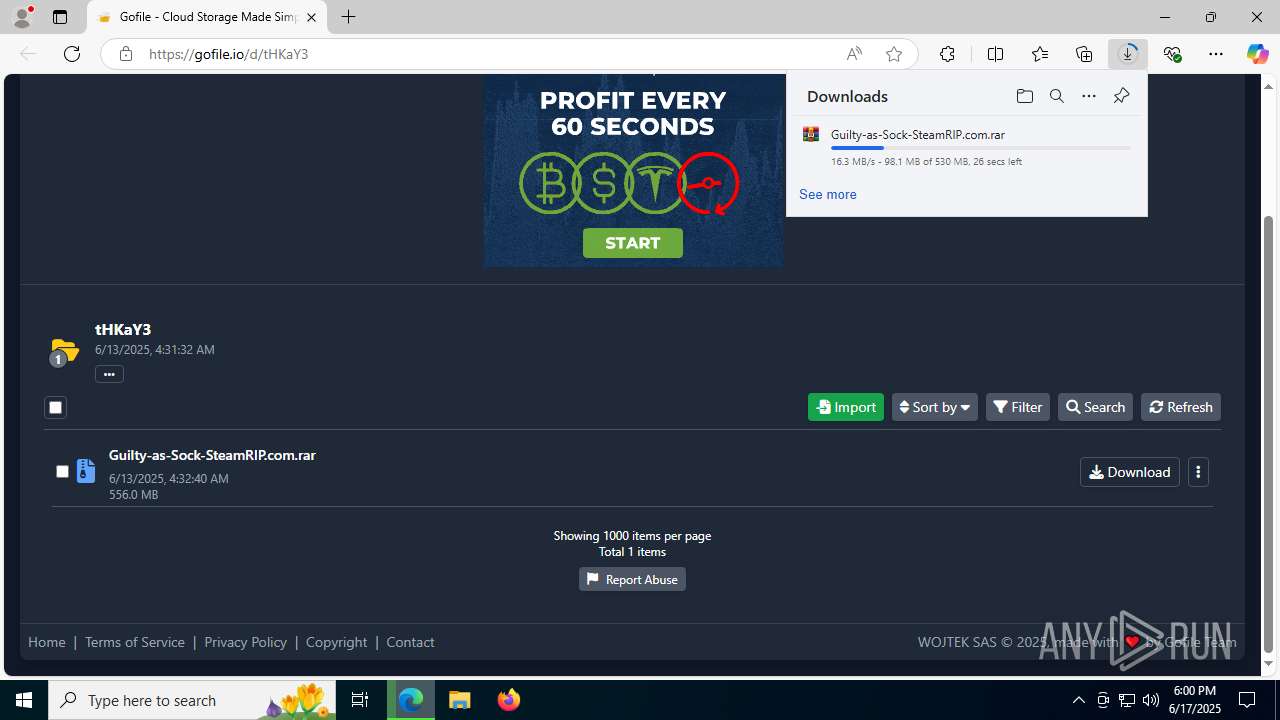
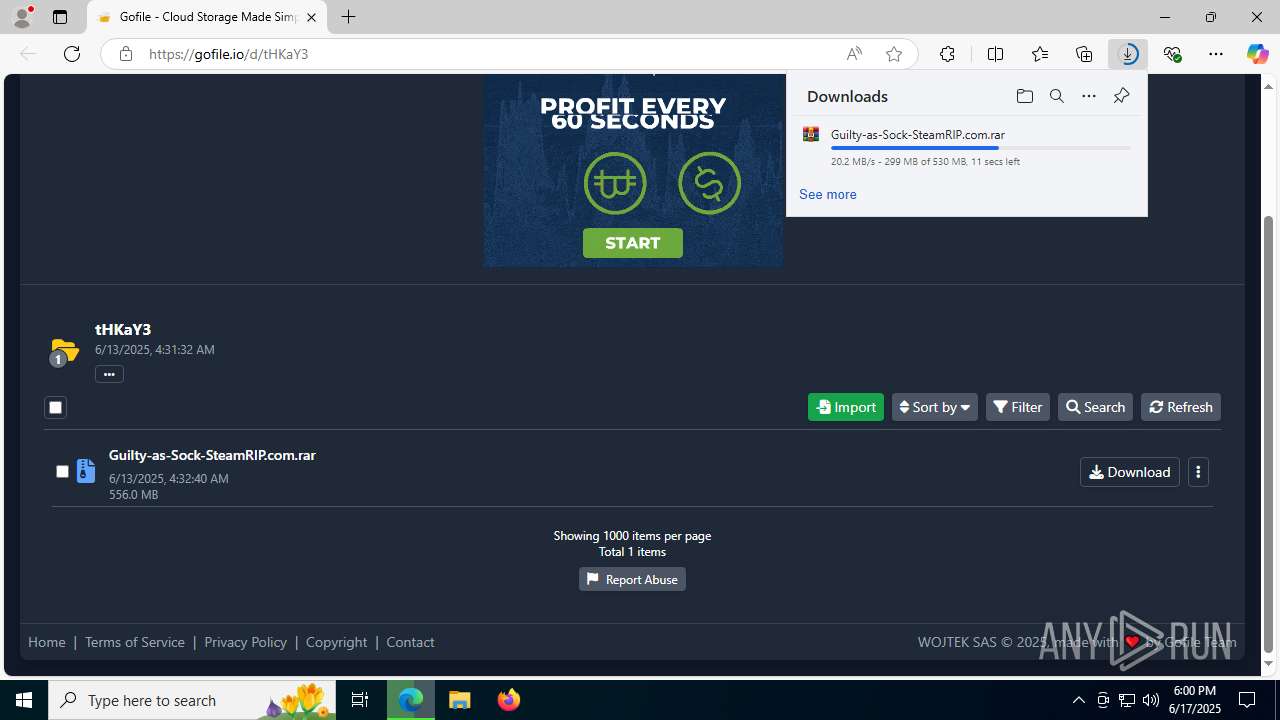
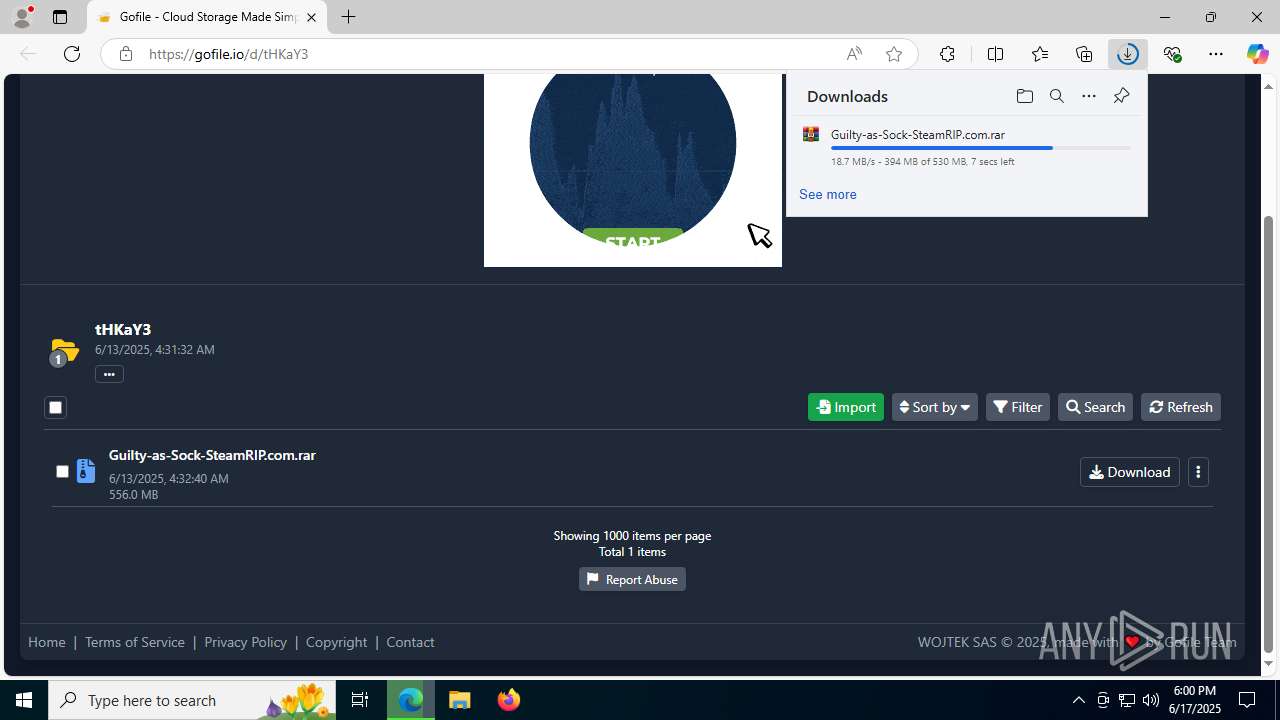
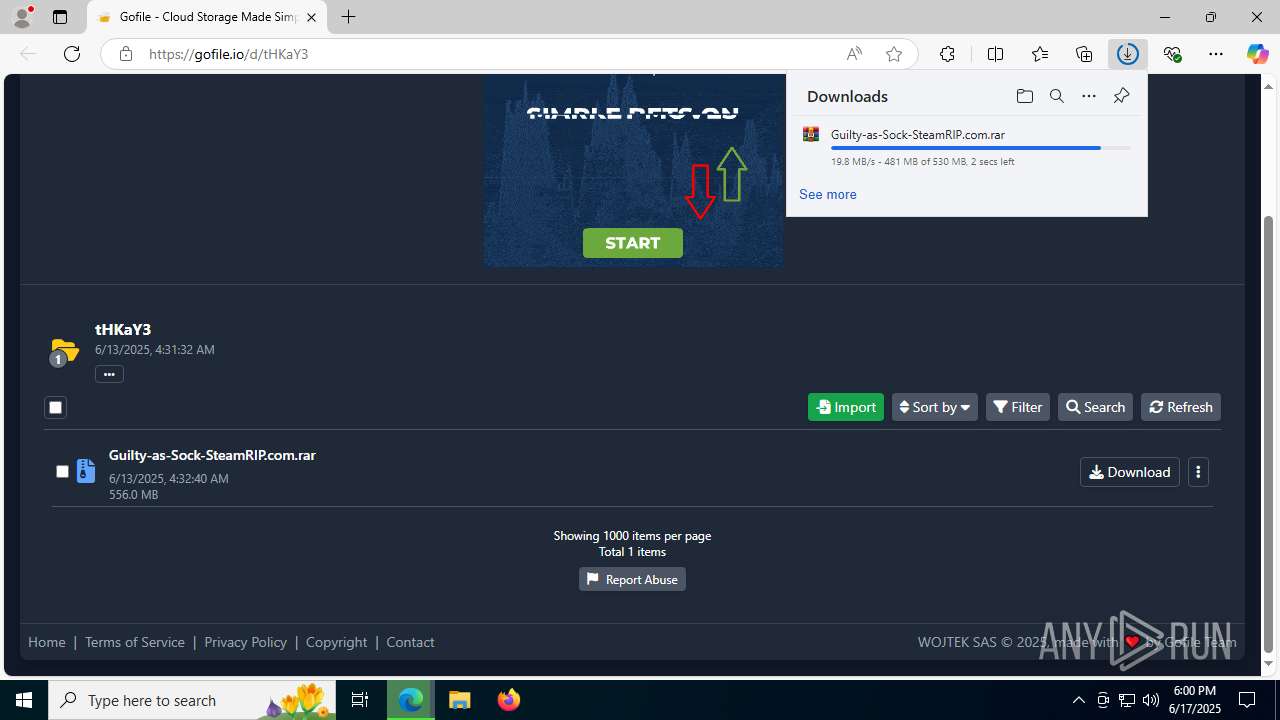
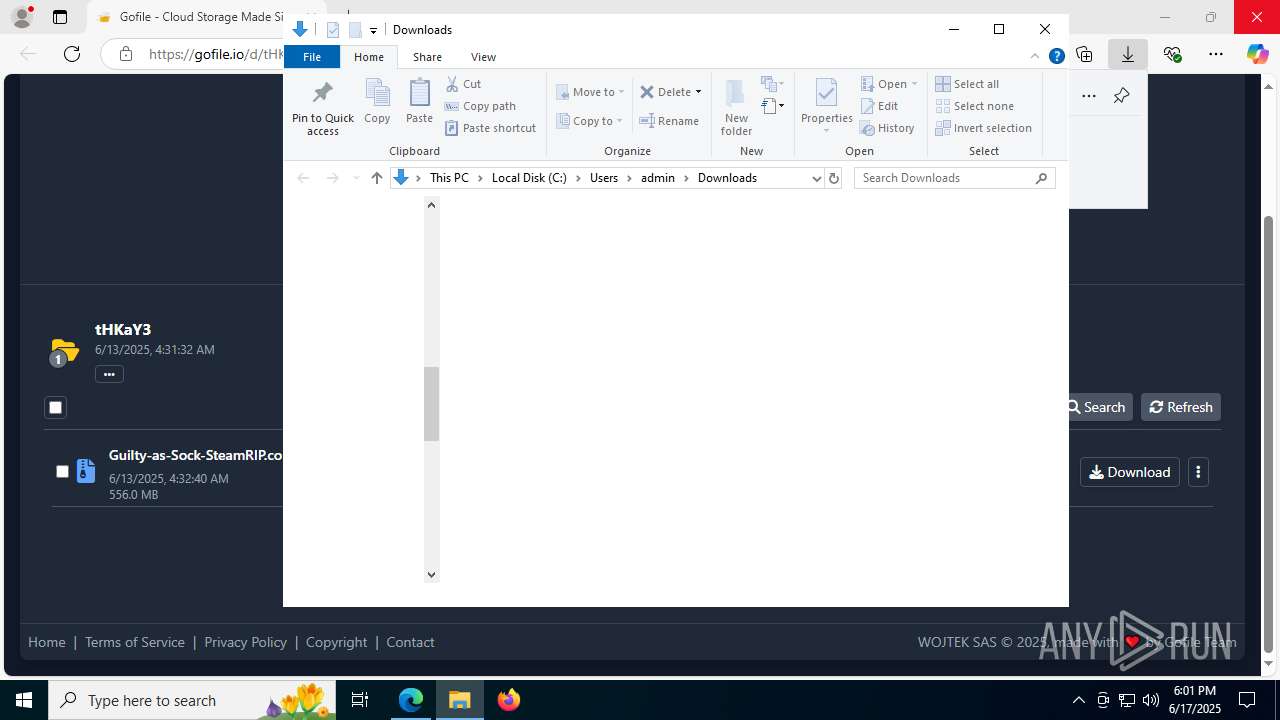
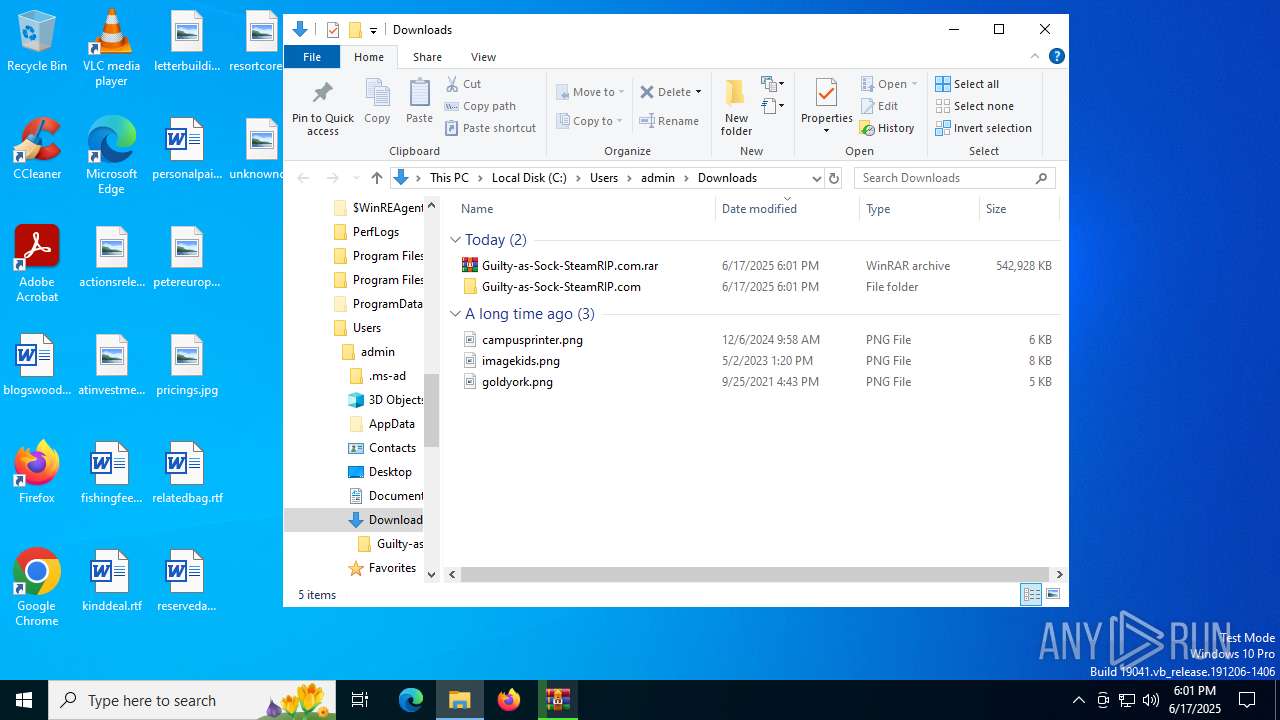
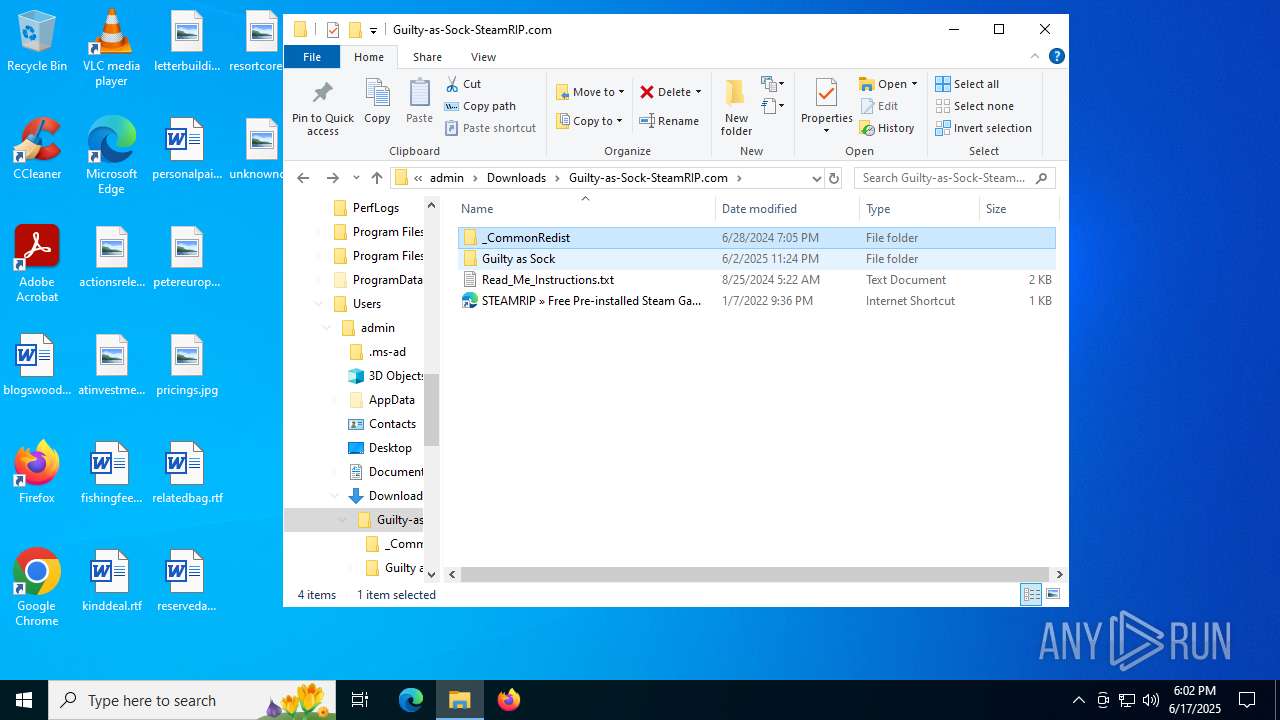
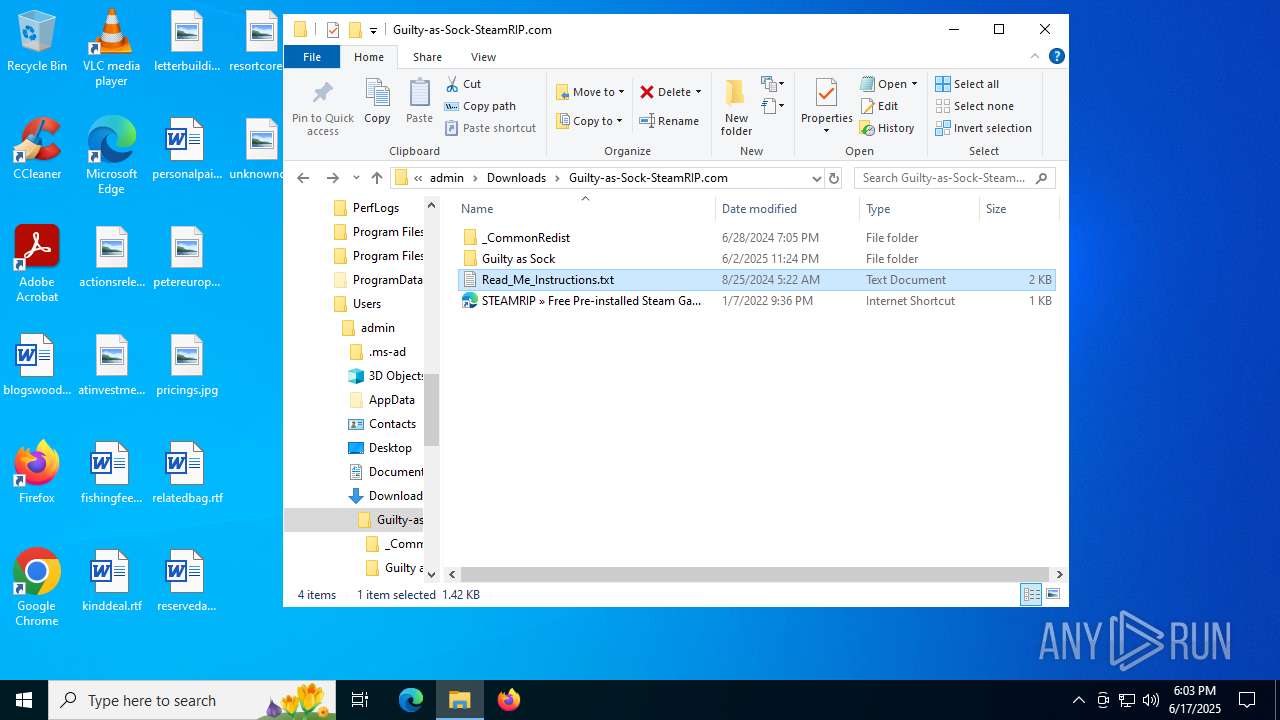
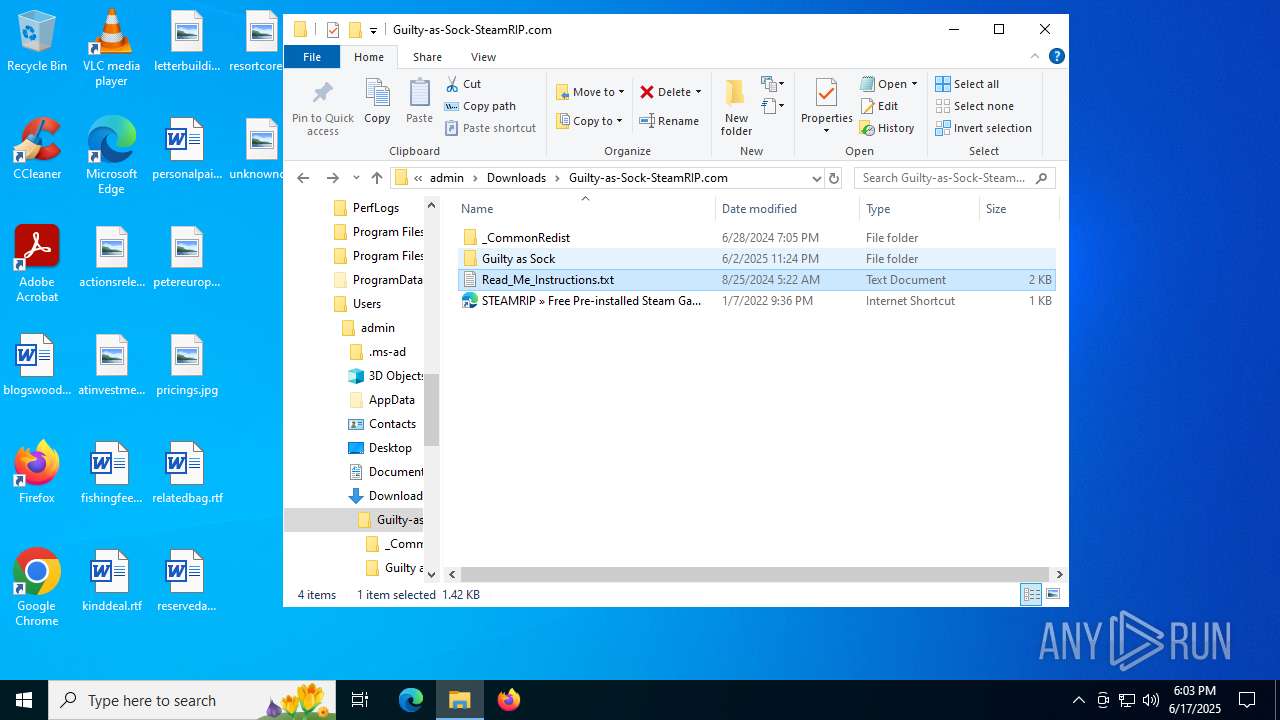
| URL: | https://gofile.io/d/tHKaY3 |
| Full analysis: | https://app.any.run/tasks/6f36ceb0-14f1-460a-8a53-e72f42176c08 |
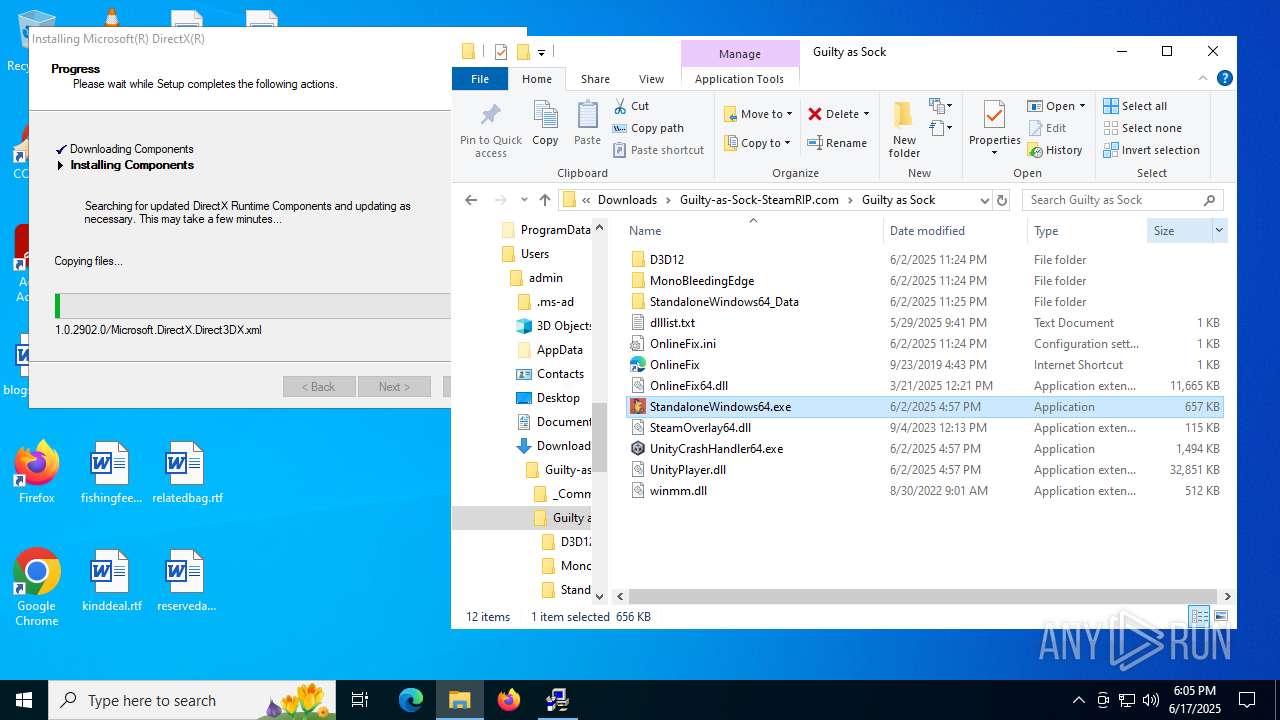
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2025, 18:00:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 07D7B414969E2FCEFA690AA18B959B2F |
| SHA1: | 5CF3E54F3161855290FB7A27D6E7E5DEDC03A9C4 |
| SHA256: | 126B1A769483C62EC923694F60E635A8F5BF368A0A8E114145A605AD21AD18CB |
| SSDEEP: | 3:N8rxL1Lu8n:2ZJu8n |
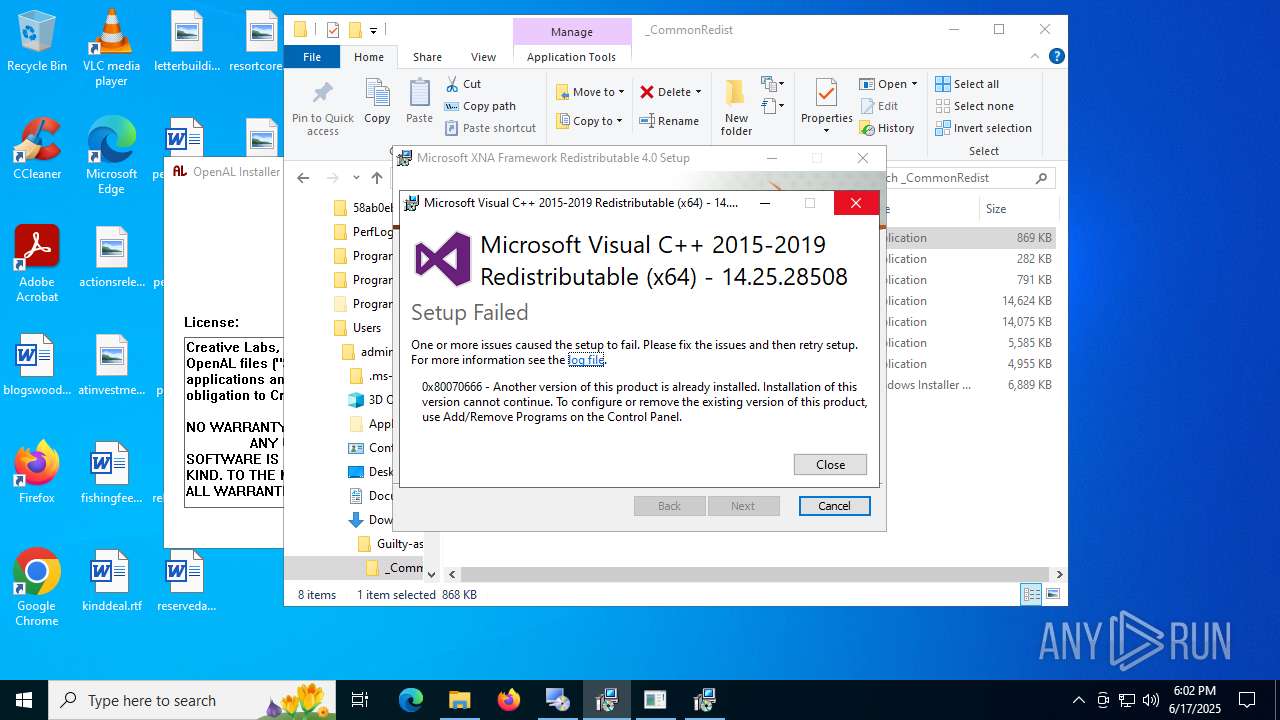
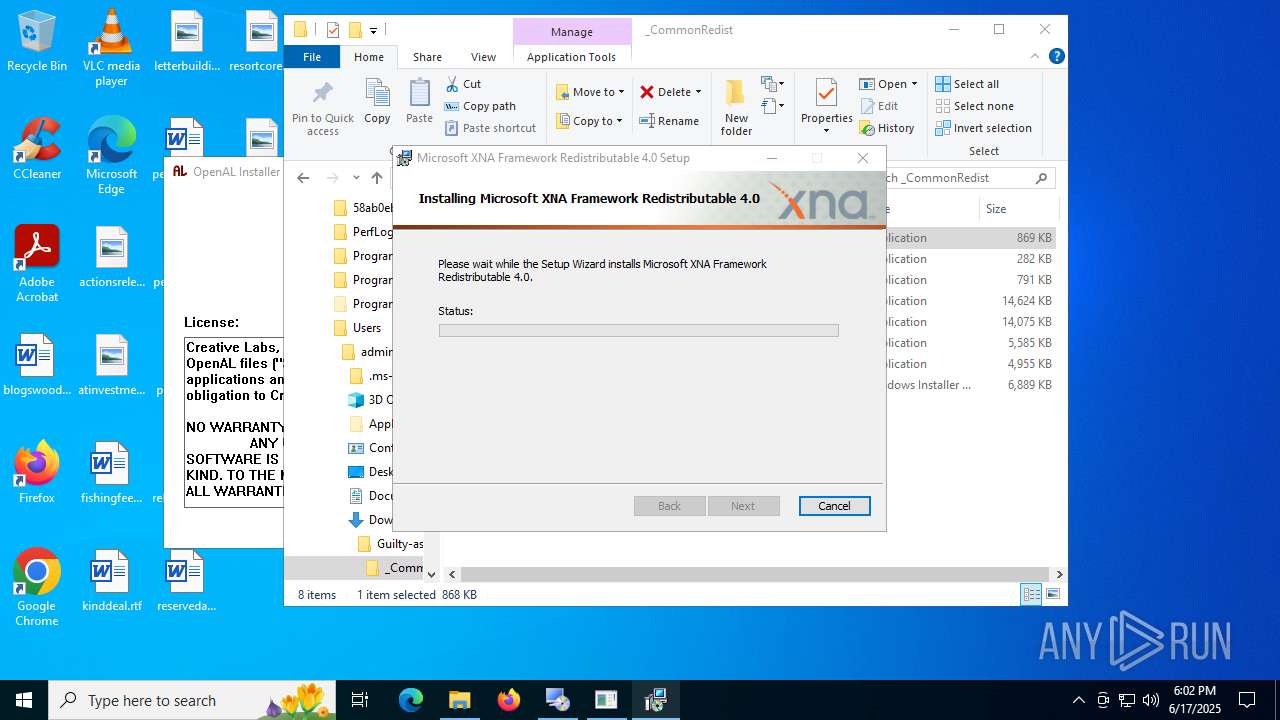
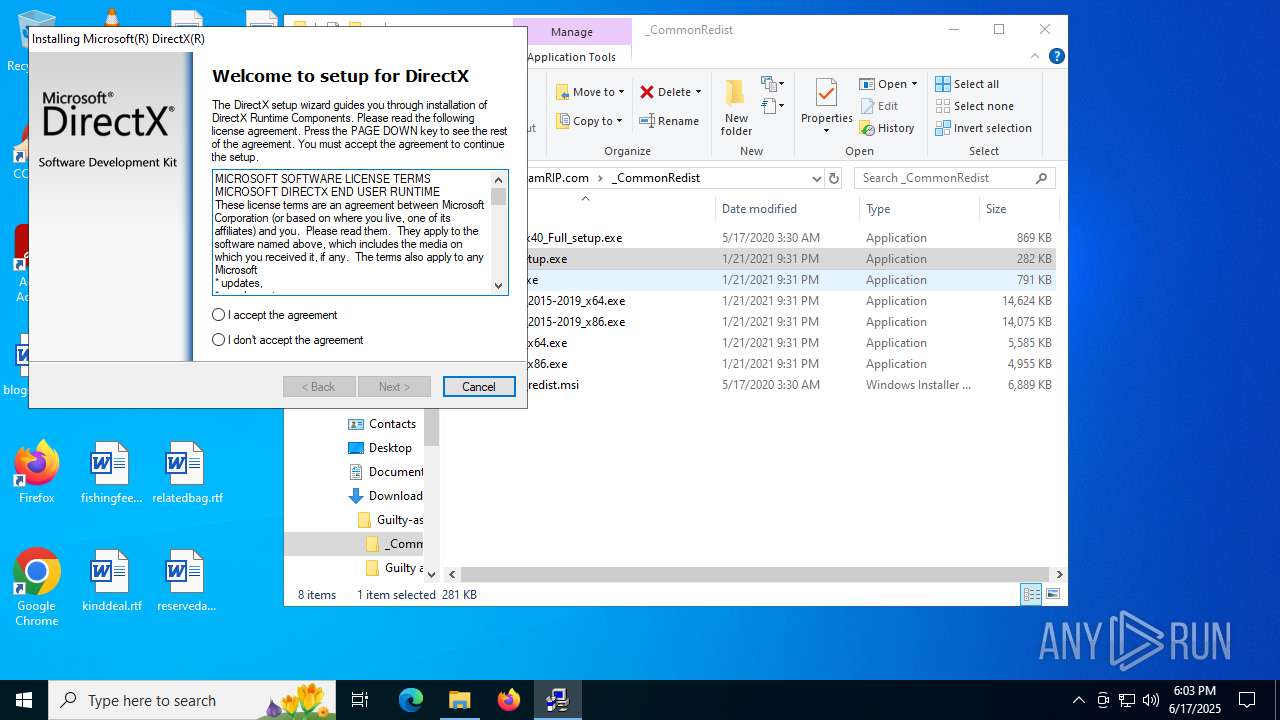
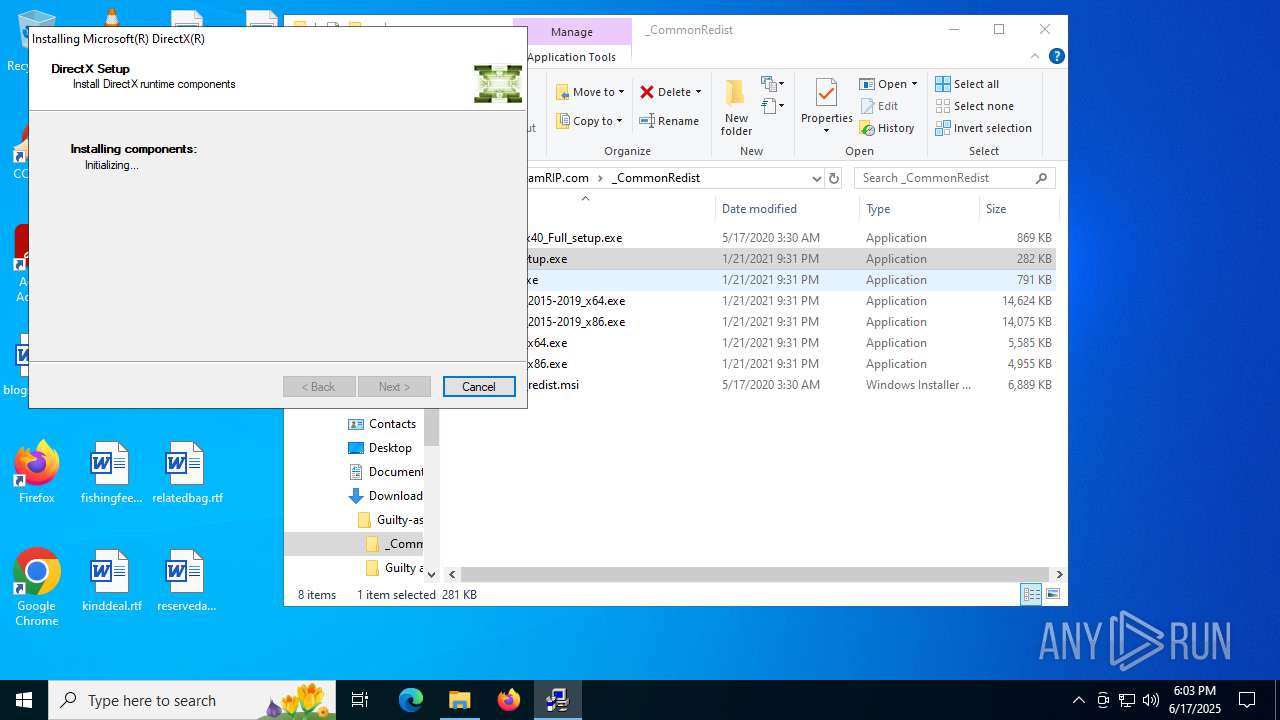
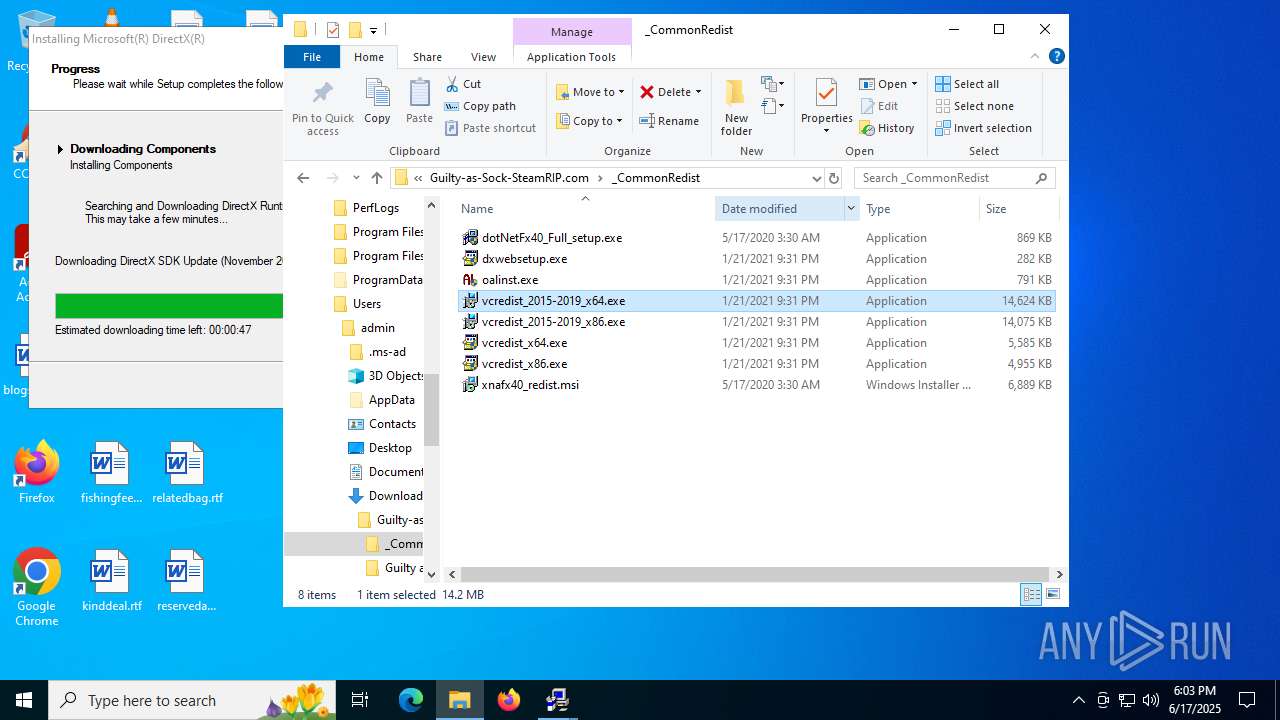
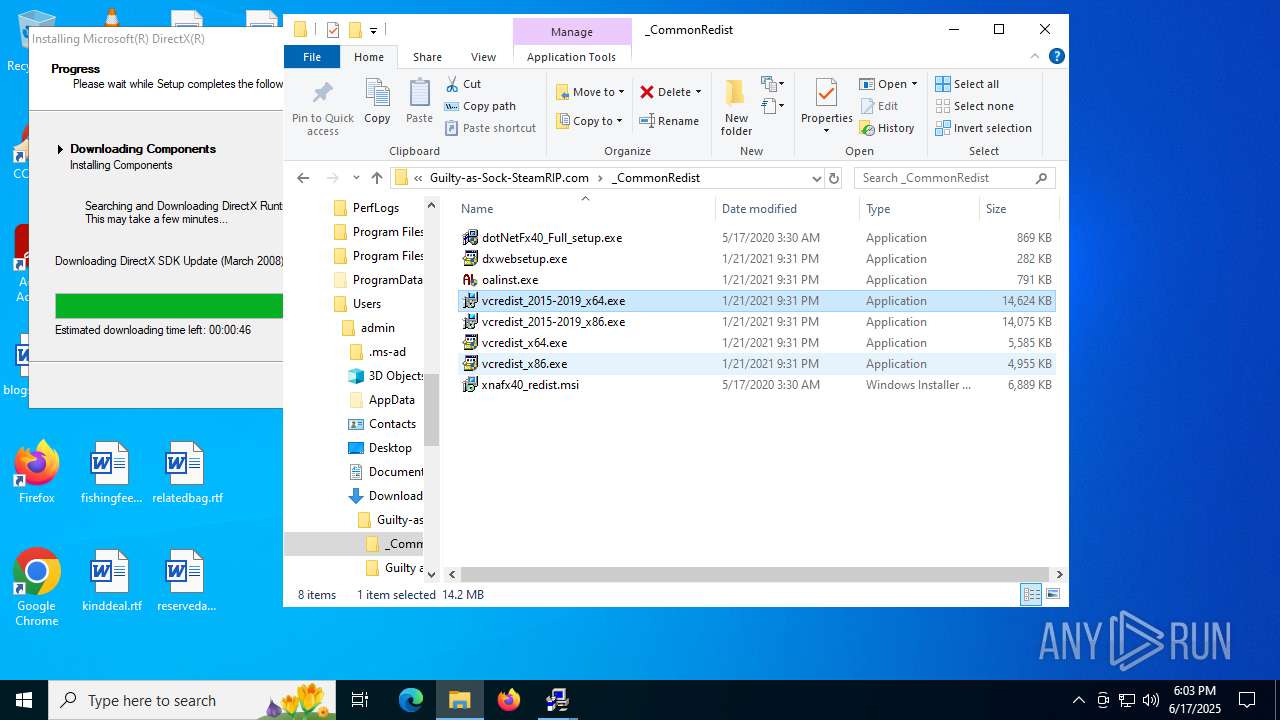
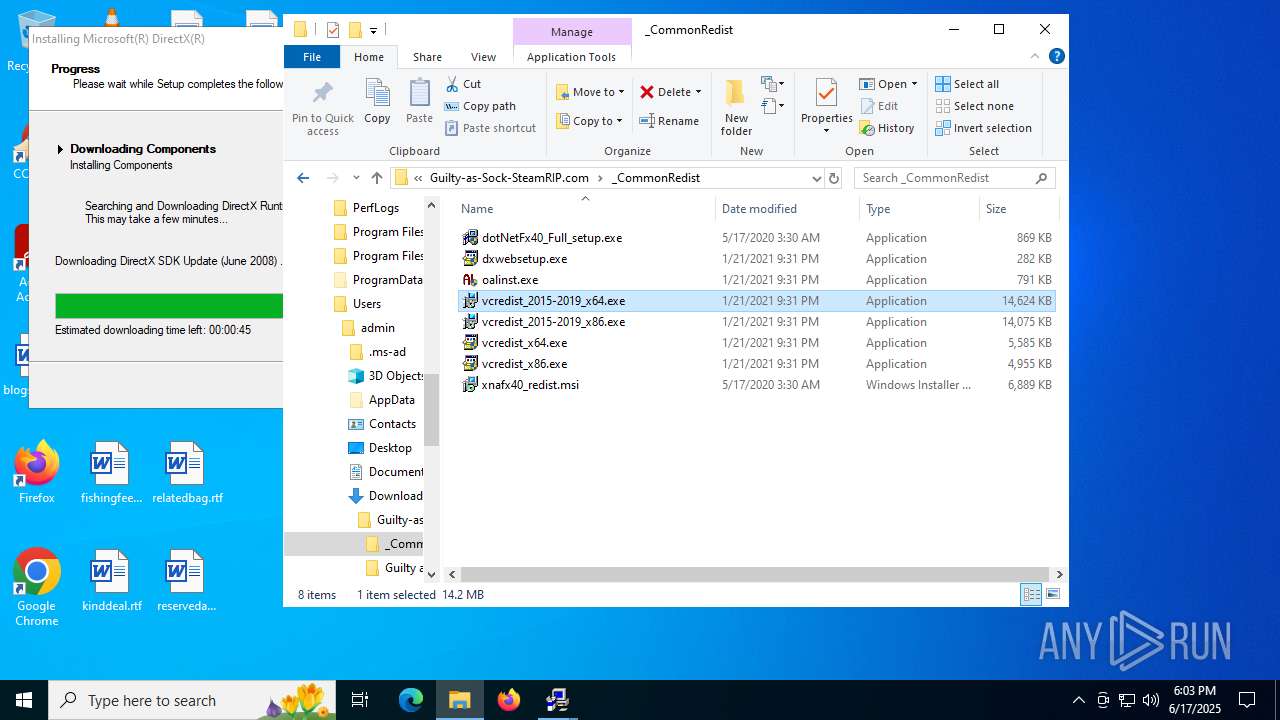
MALICIOUS
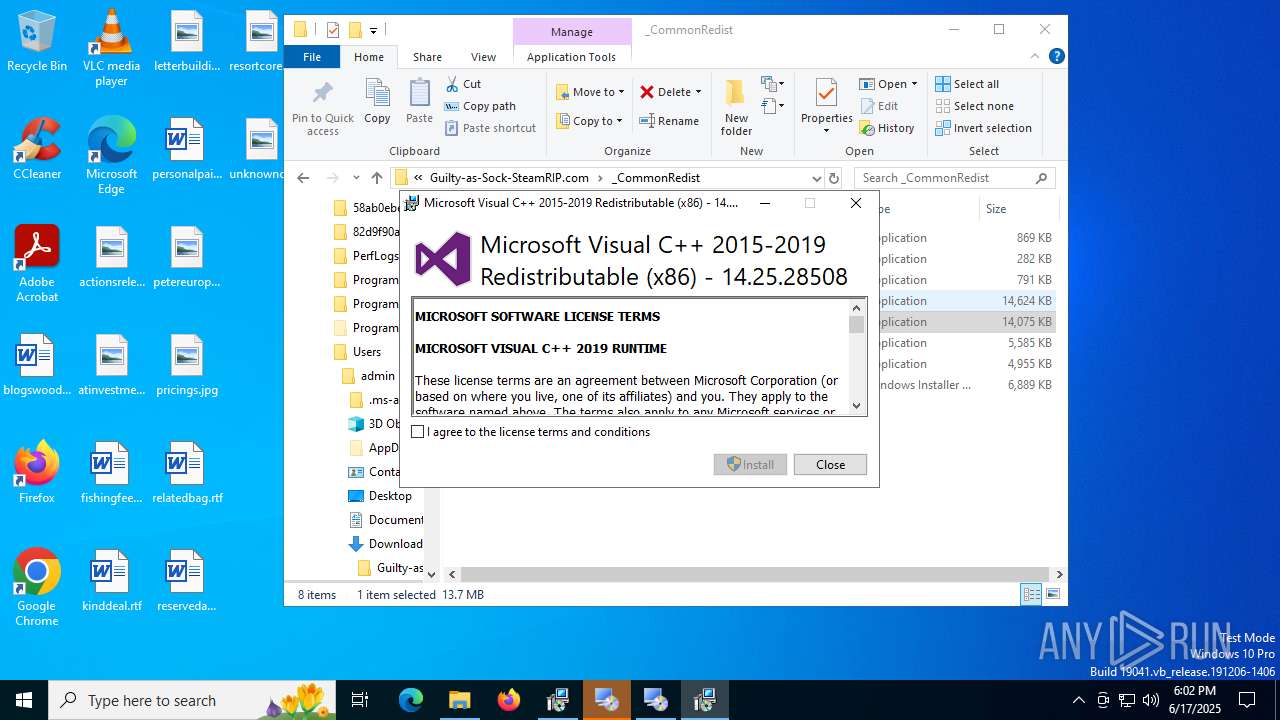
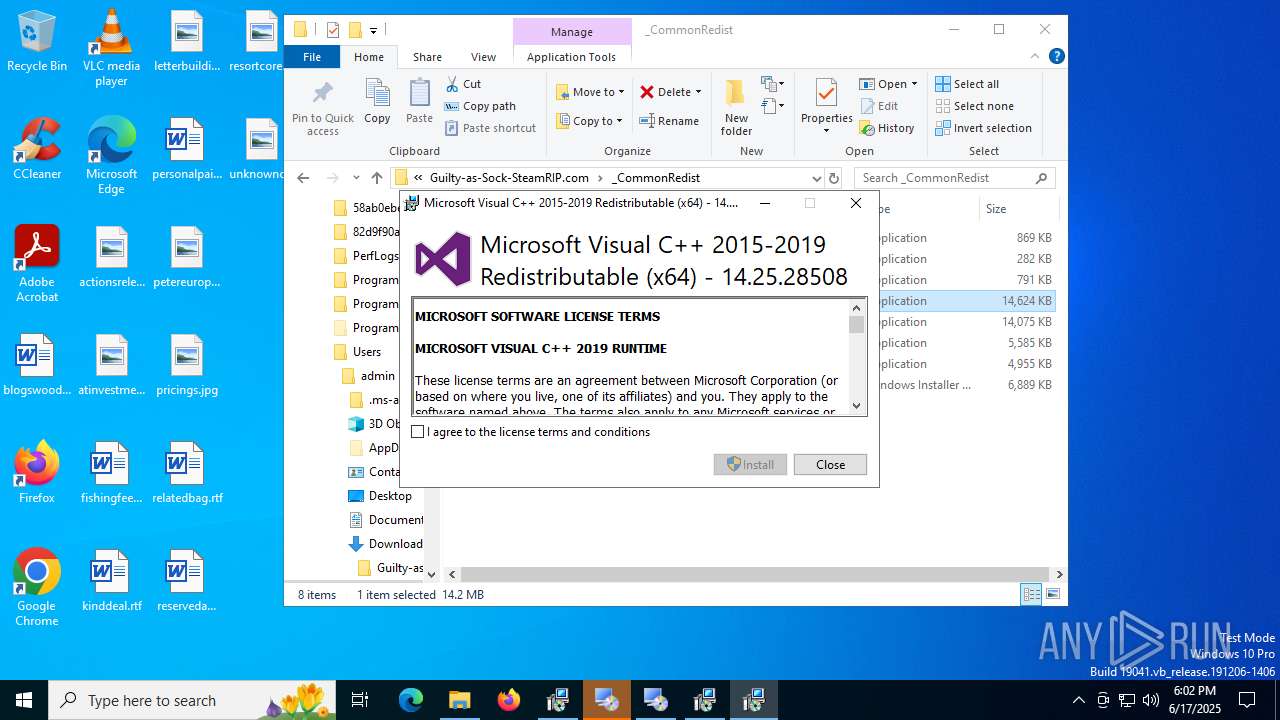
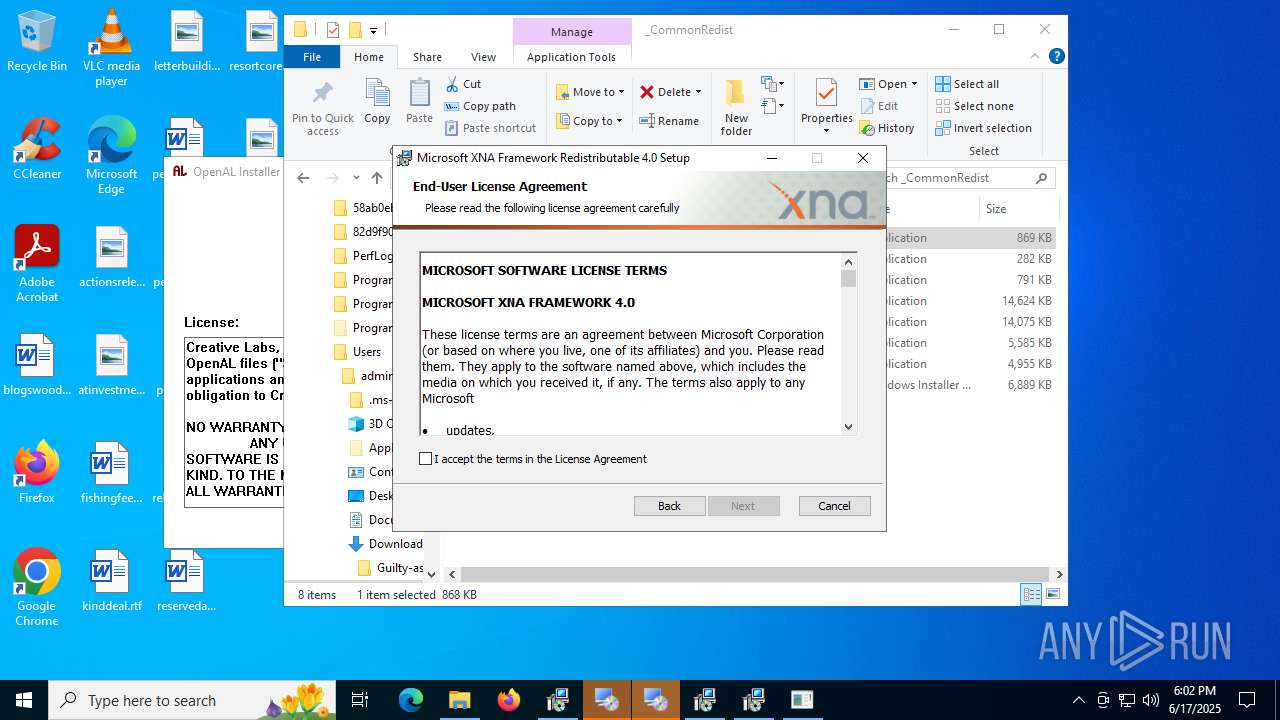
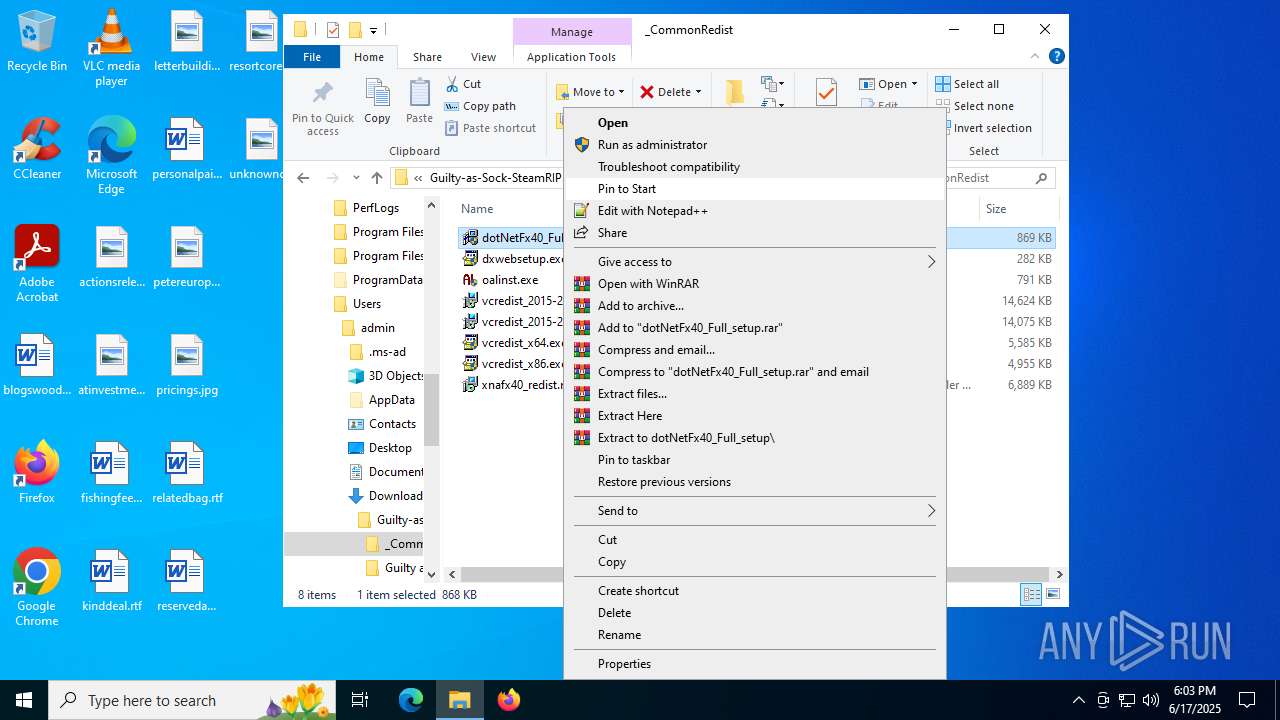
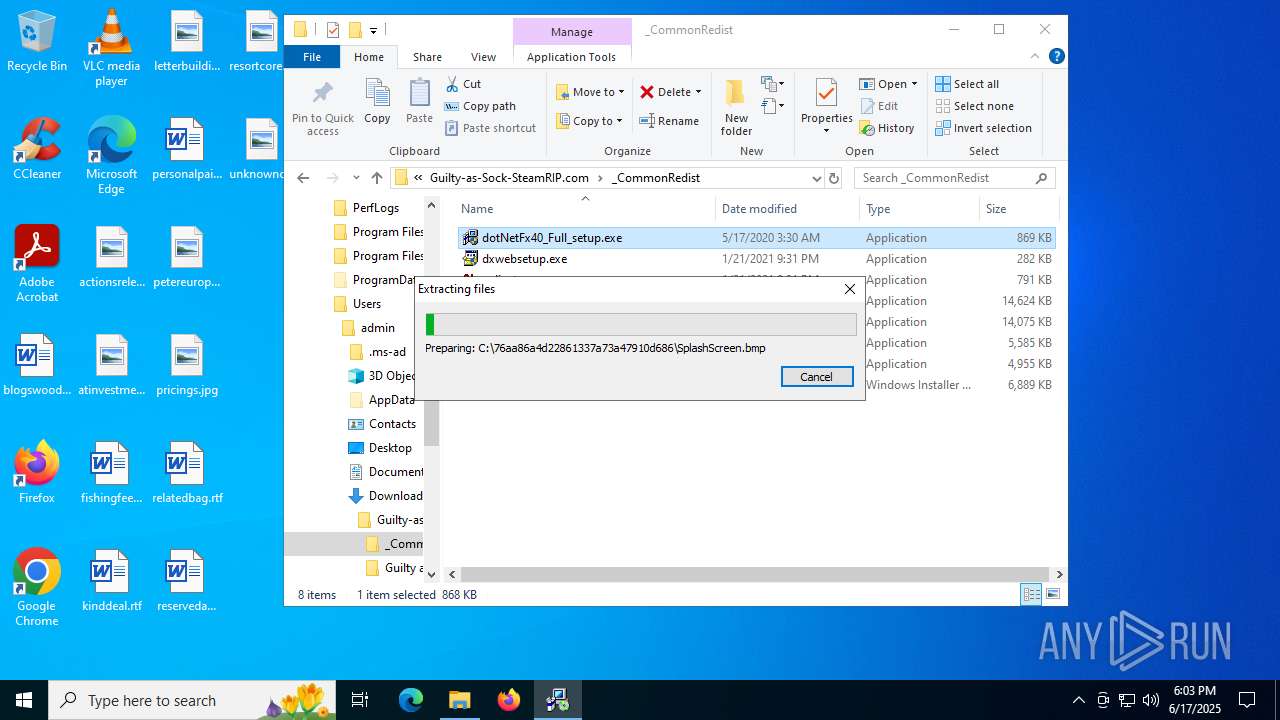
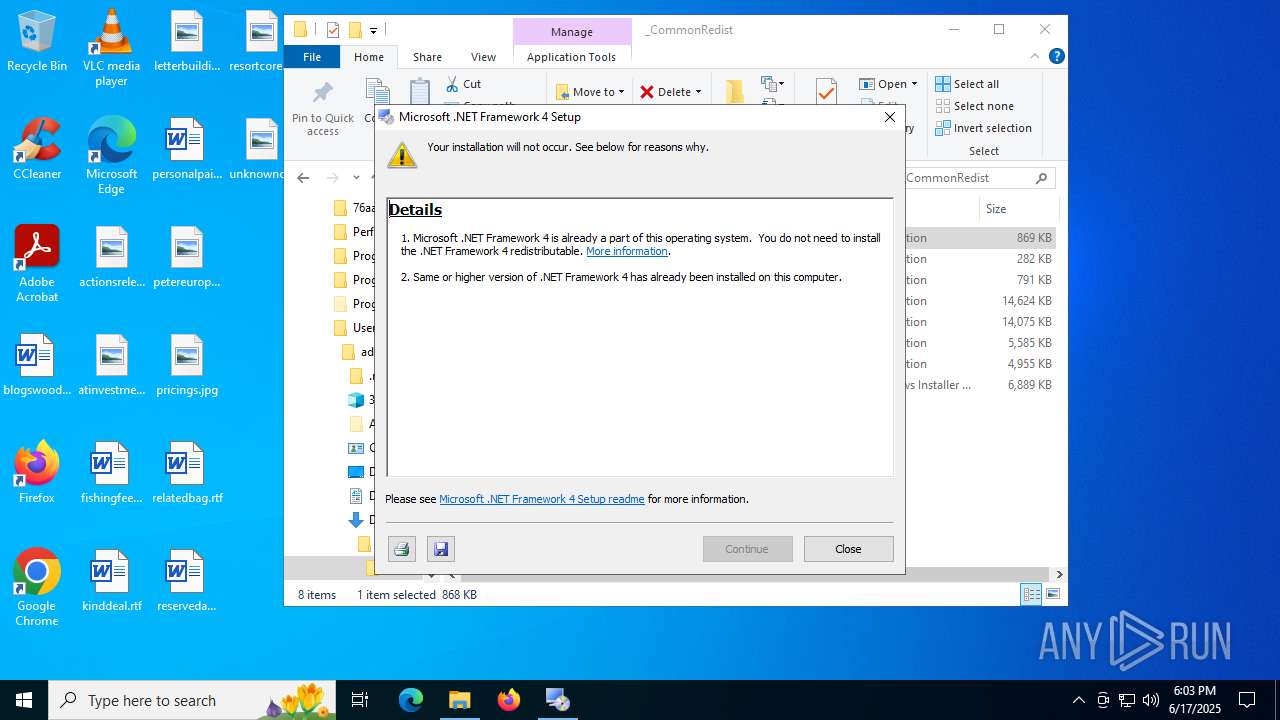
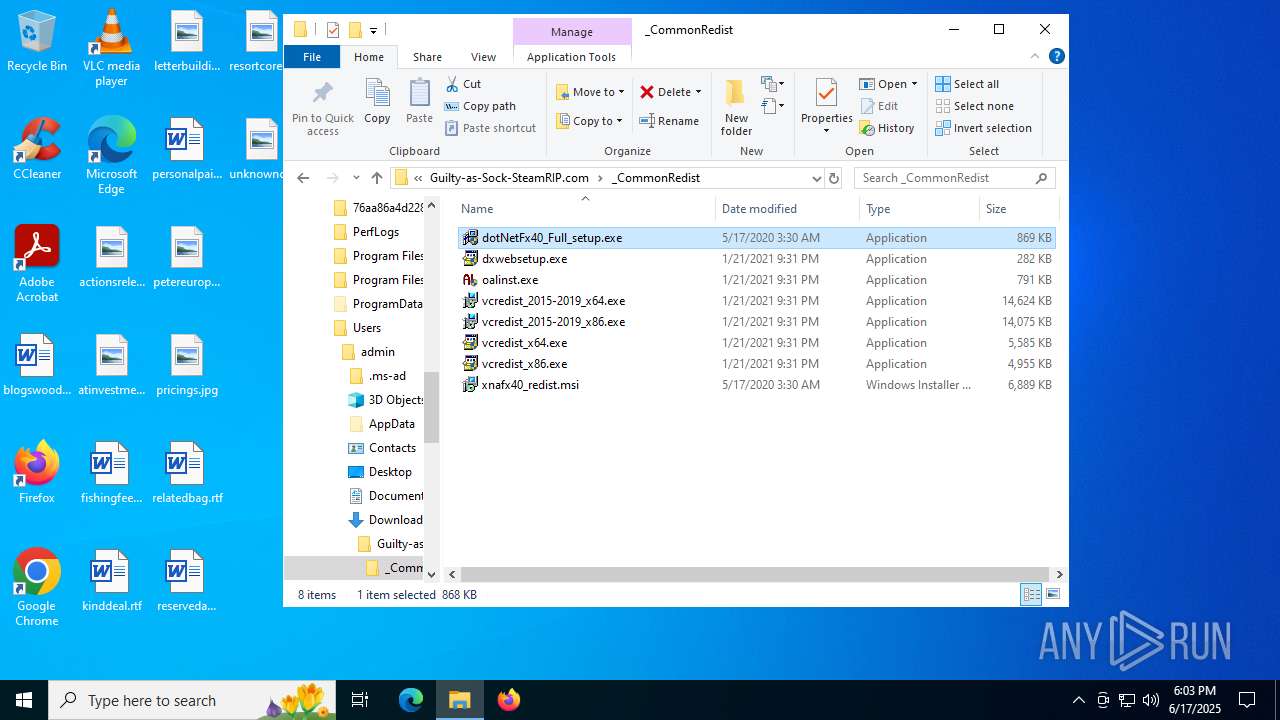
Executing a file with an untrusted certificate
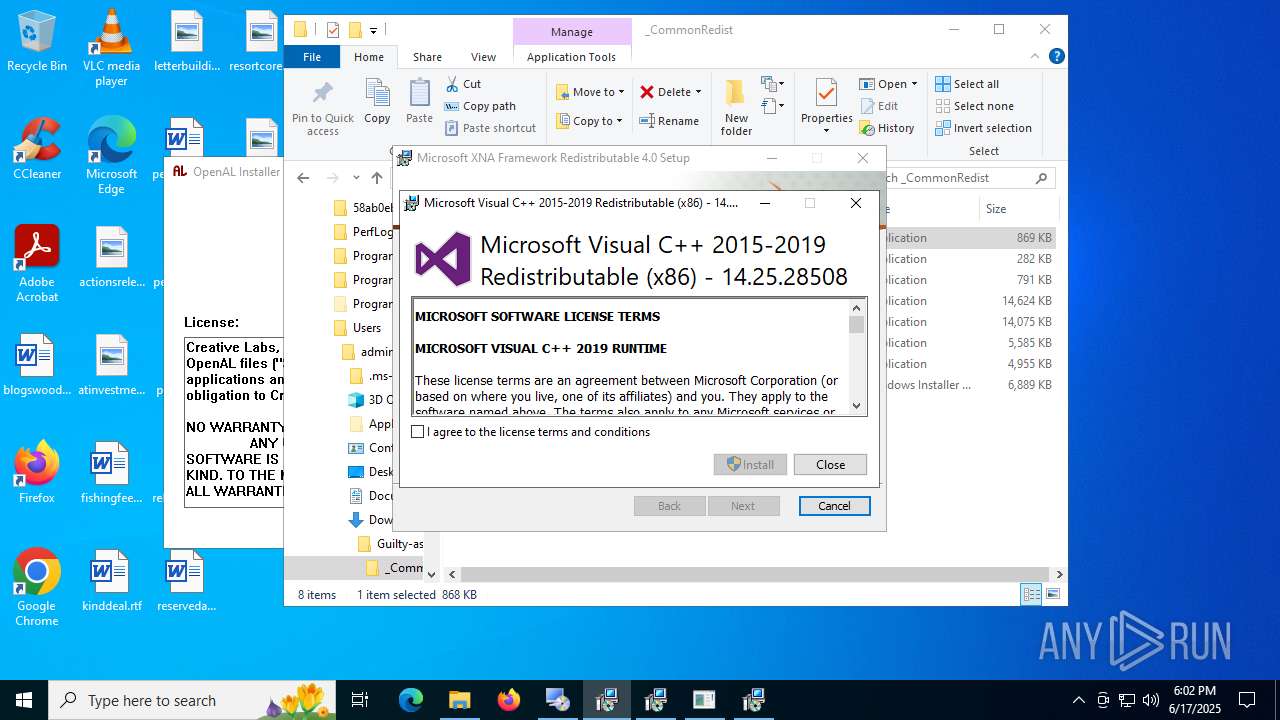
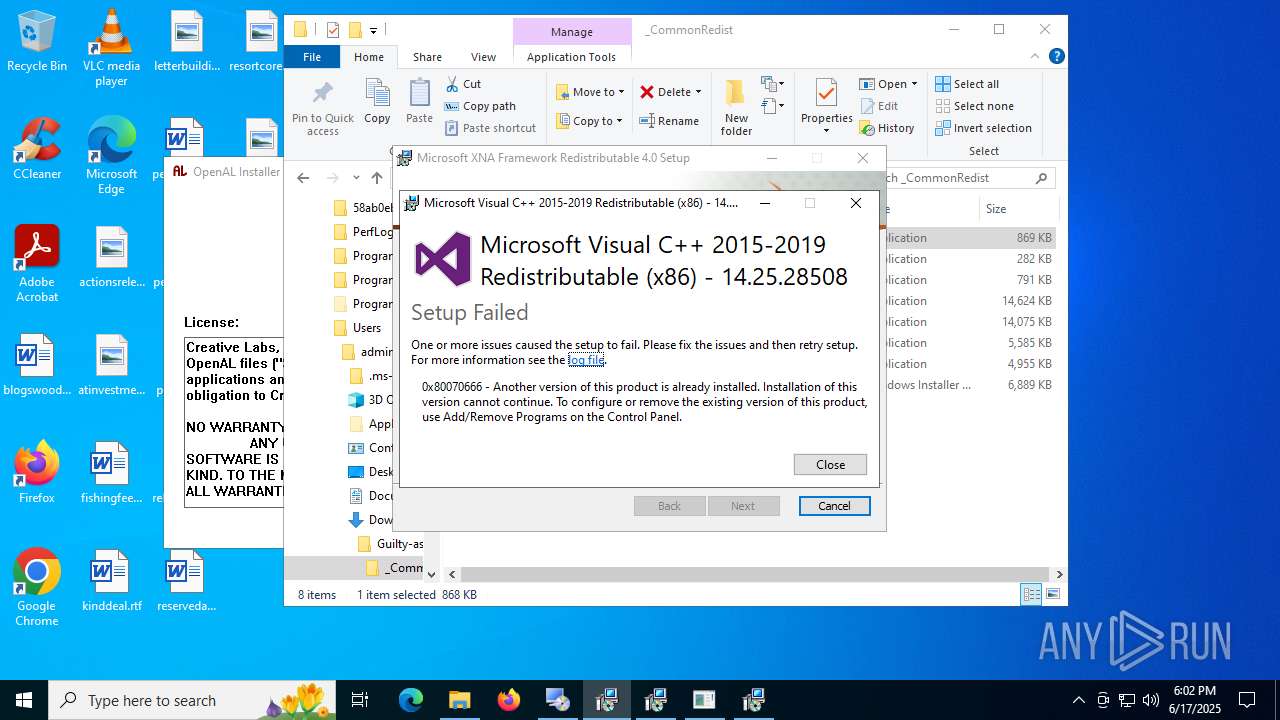
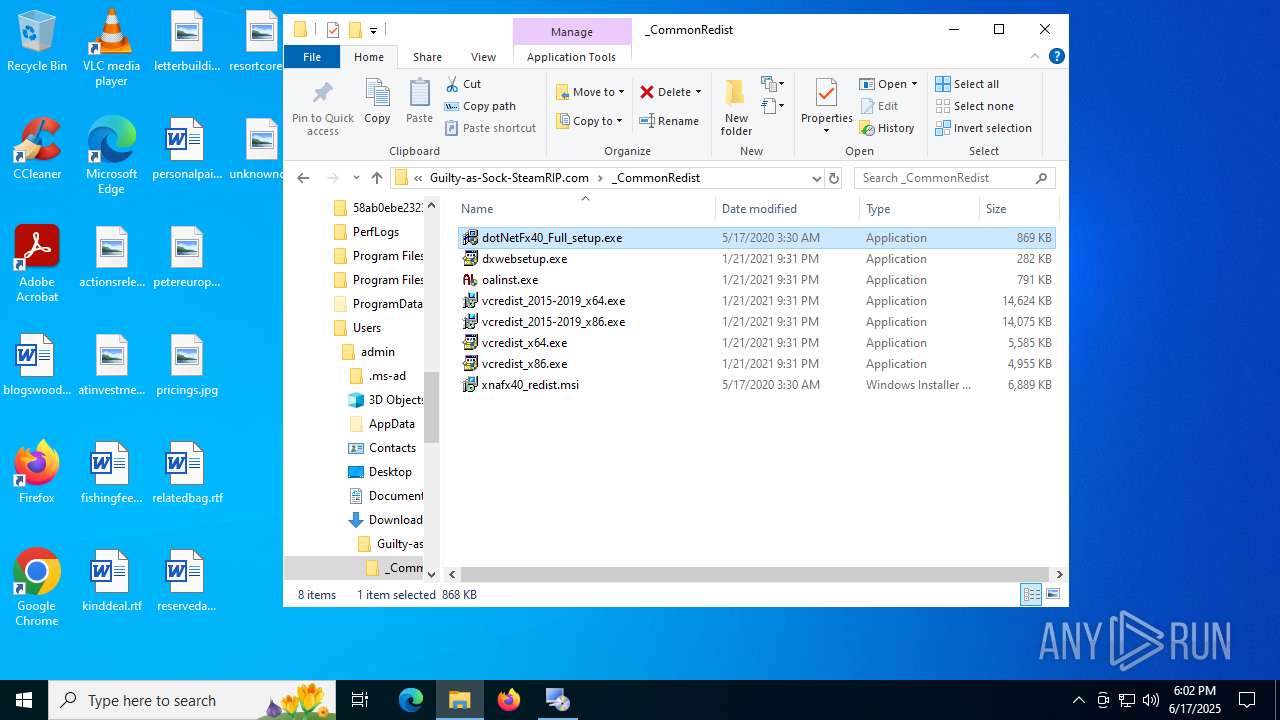
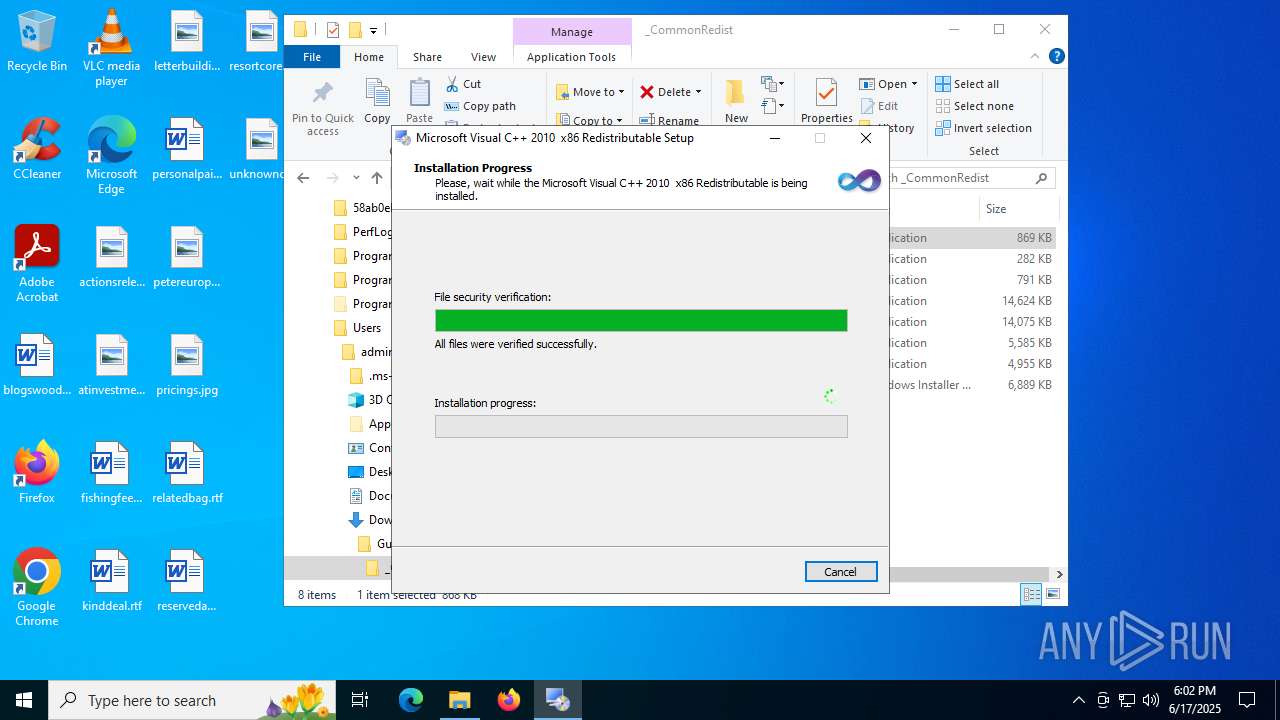
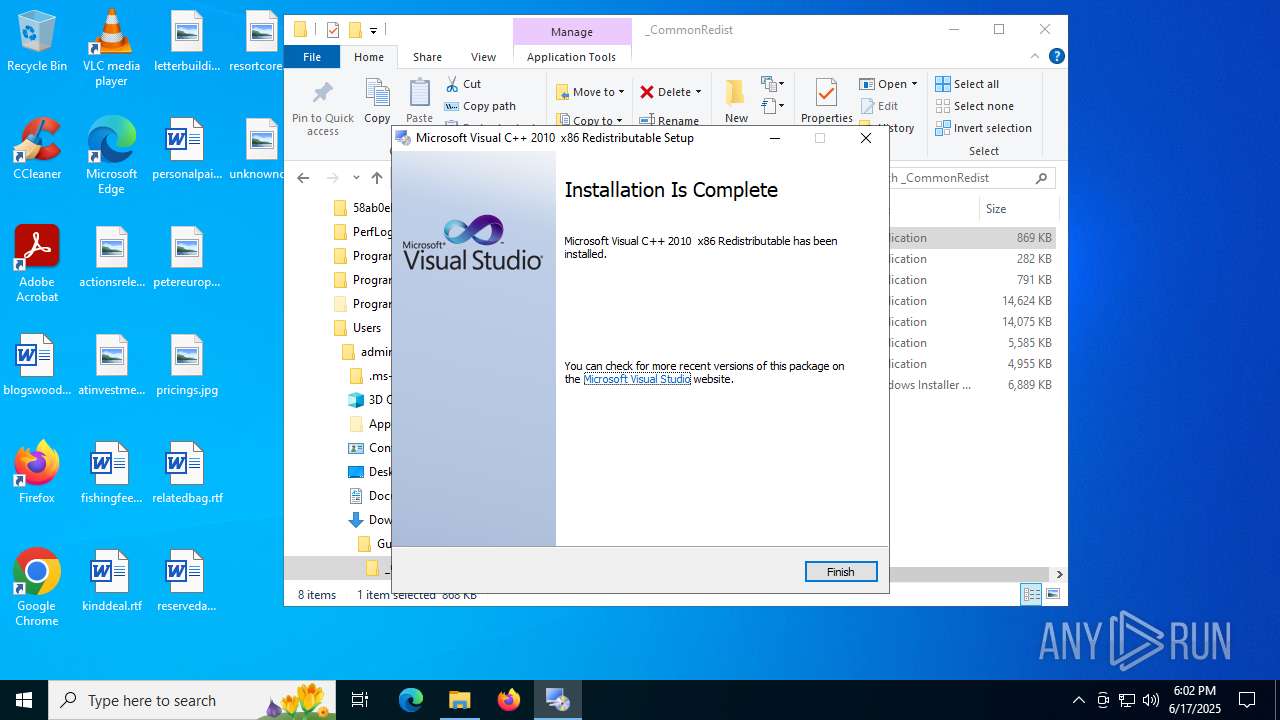
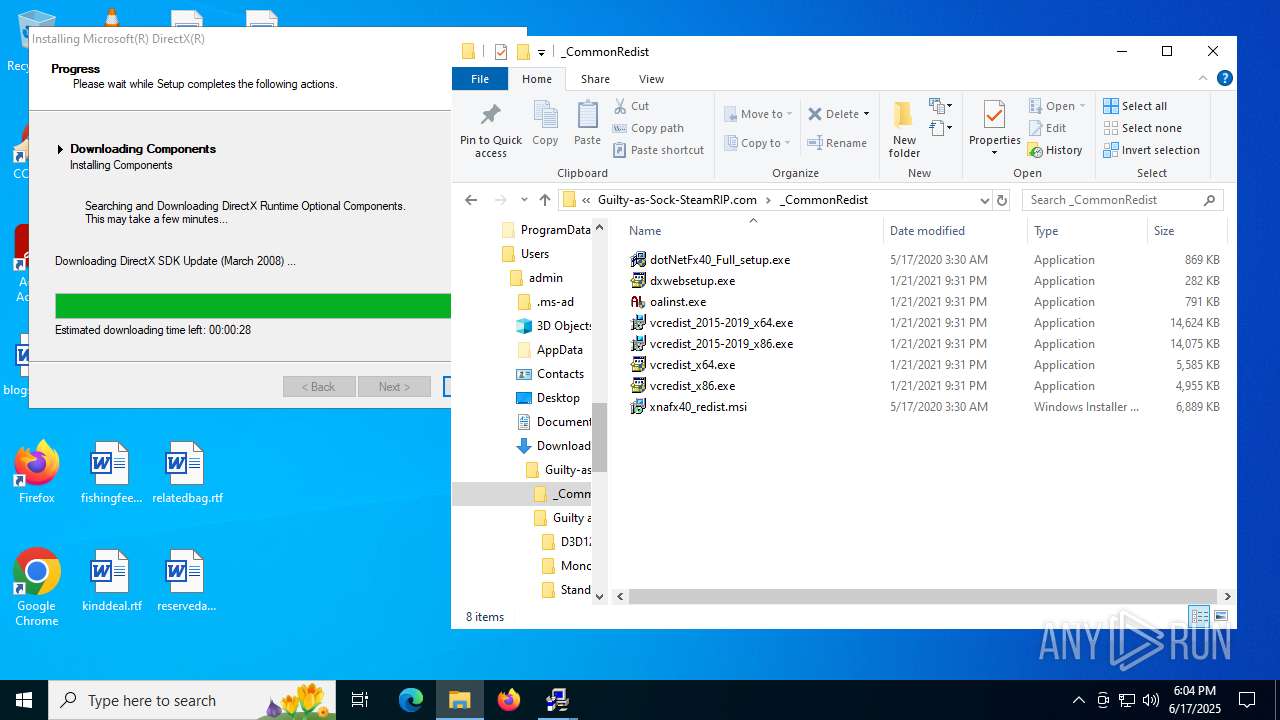
- vcredist_x86.exe (PID: 6320)
- vcredist_x86.exe (PID: 5372)
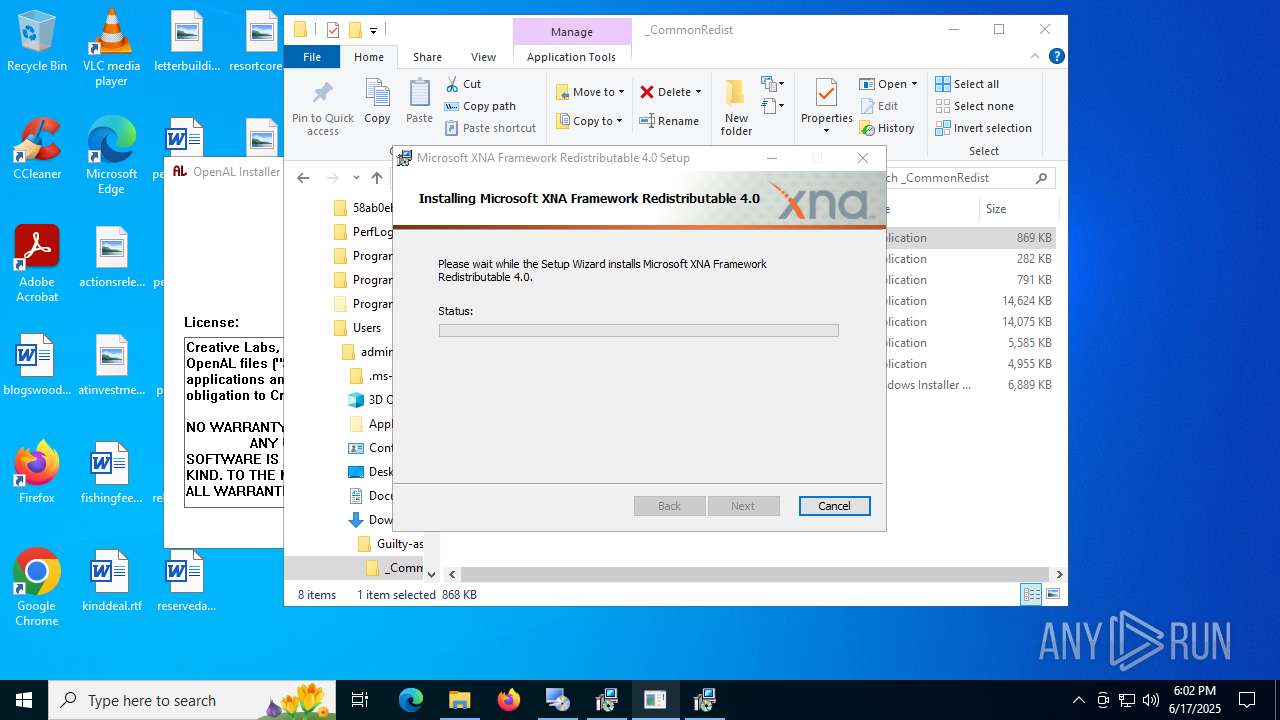
- Setup.exe (PID: 3504)
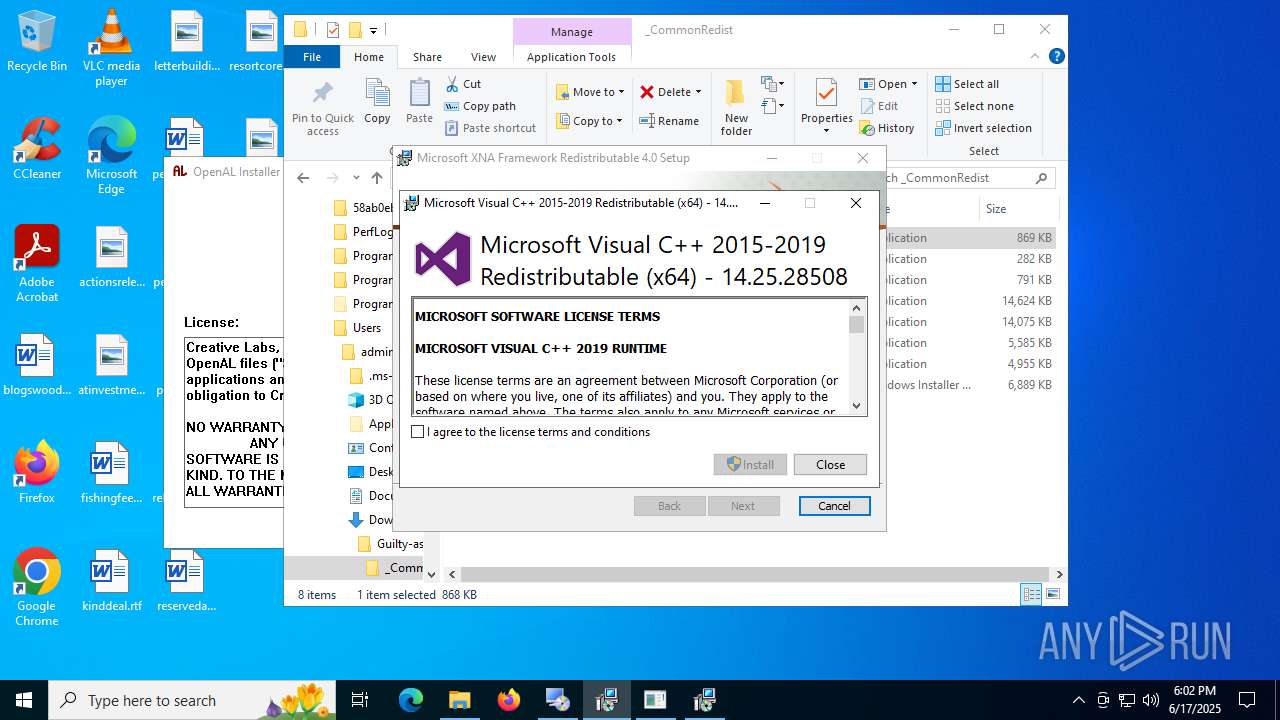
- vcredist_x64.exe (PID: 3480)
- vcredist_x64.exe (PID: 2552)
- Setup.exe (PID: 1100)
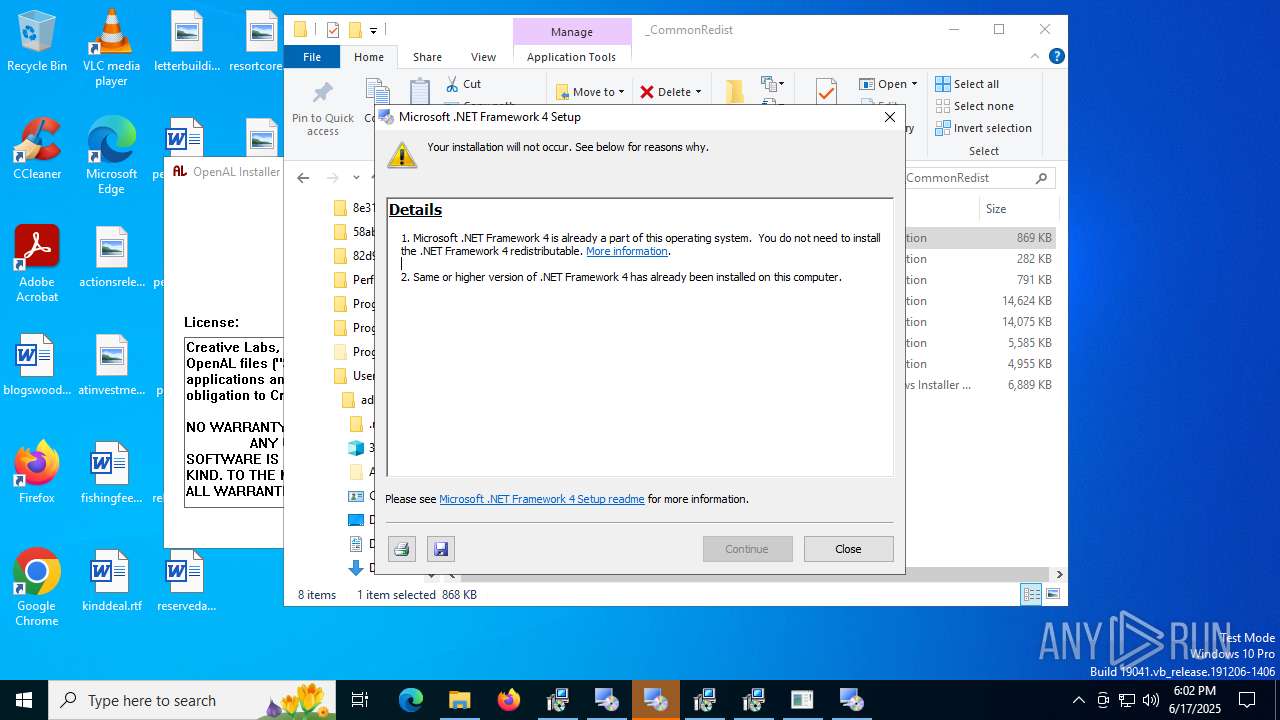
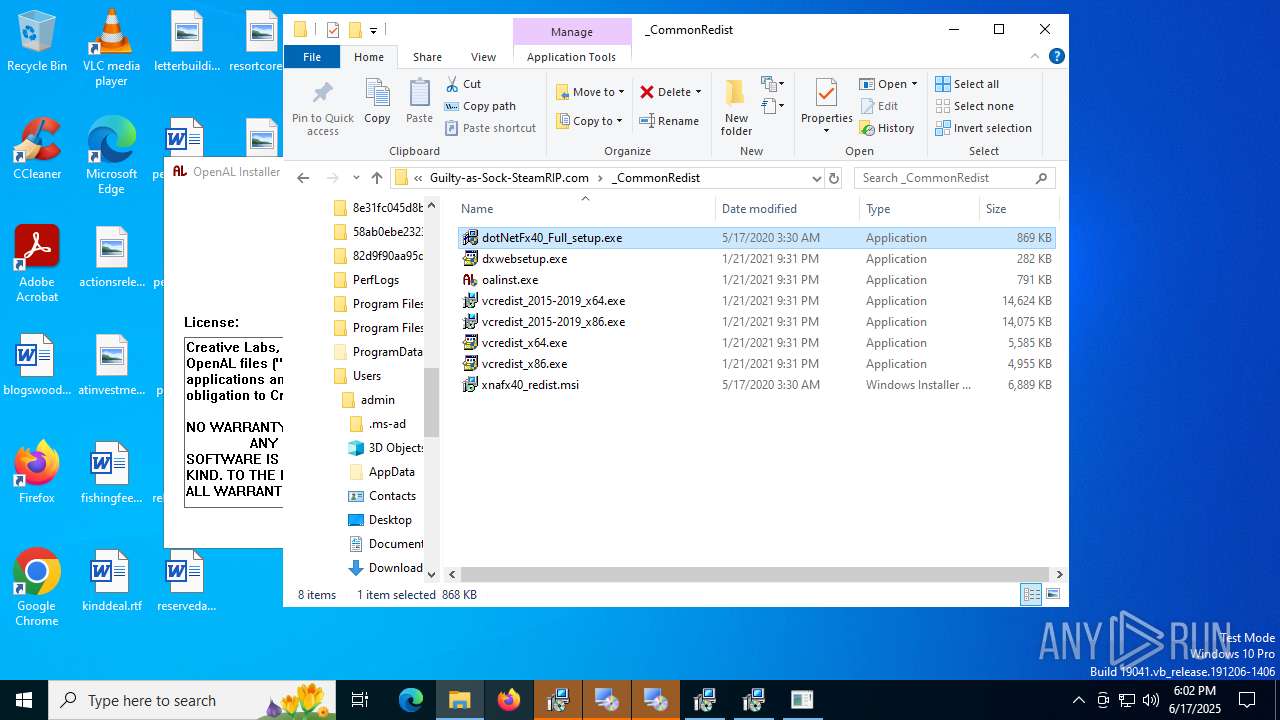
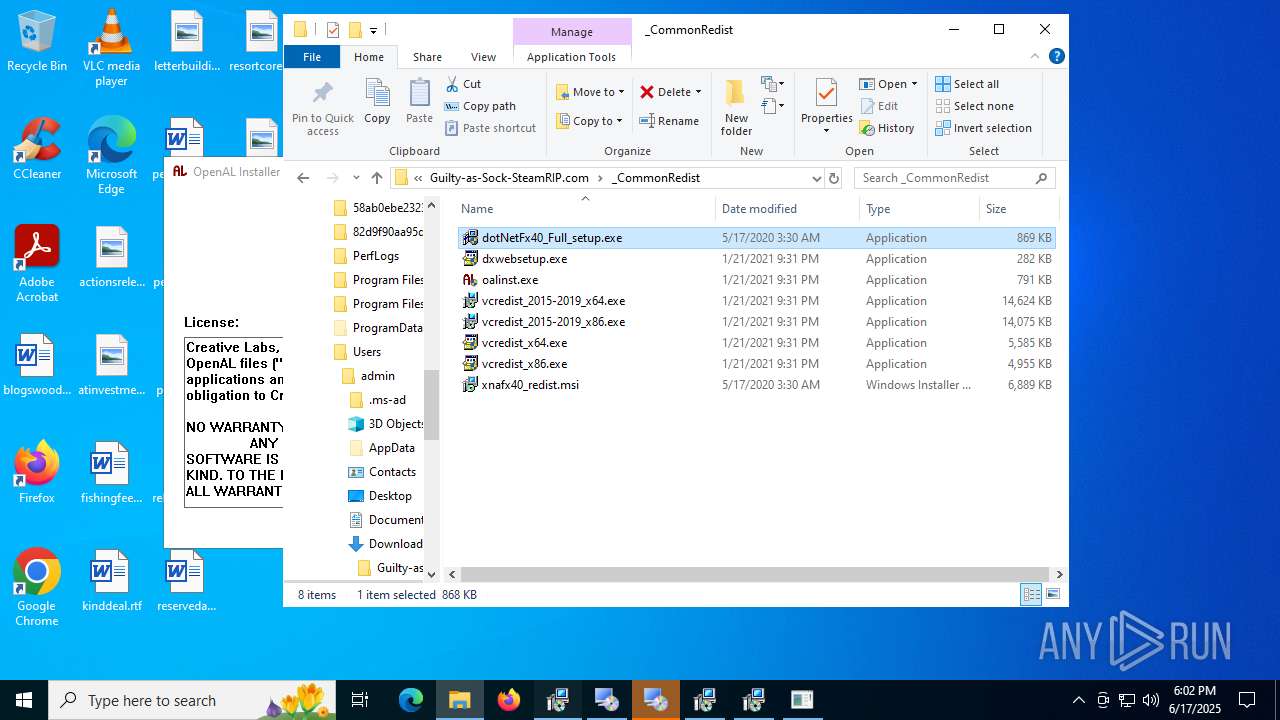
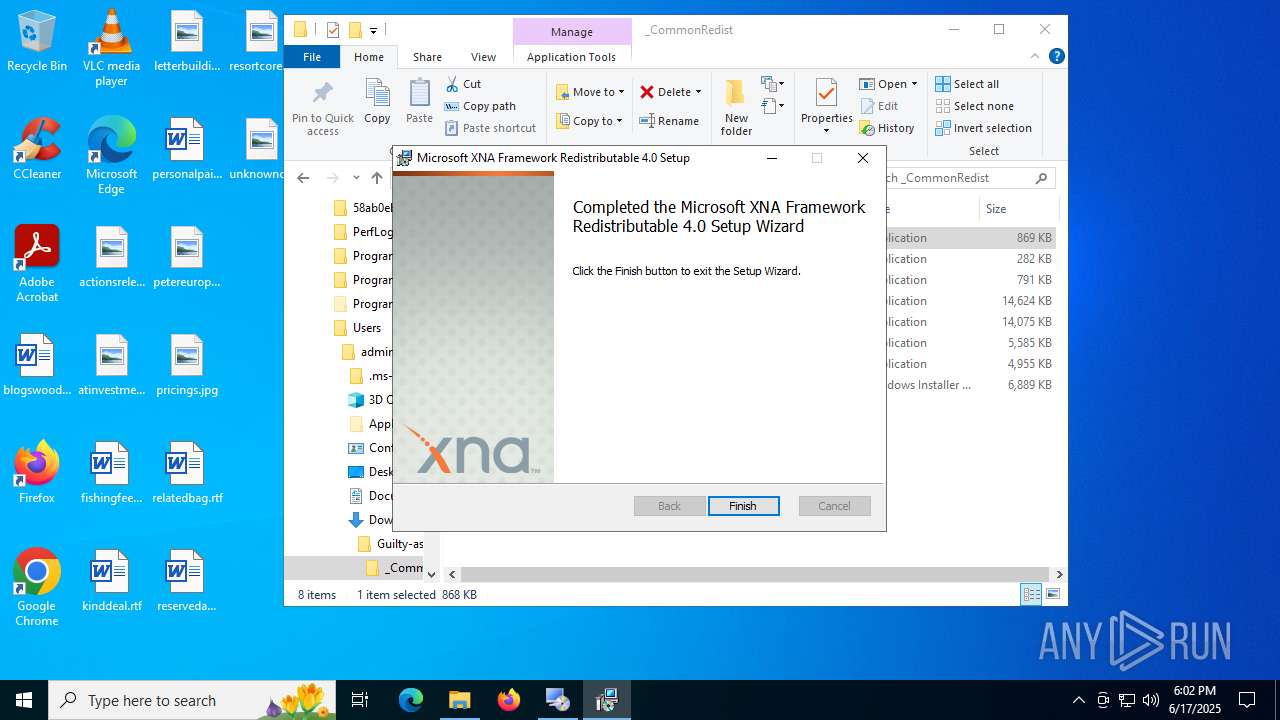
- dotNetFx40_Full_setup.exe (PID: 4552)
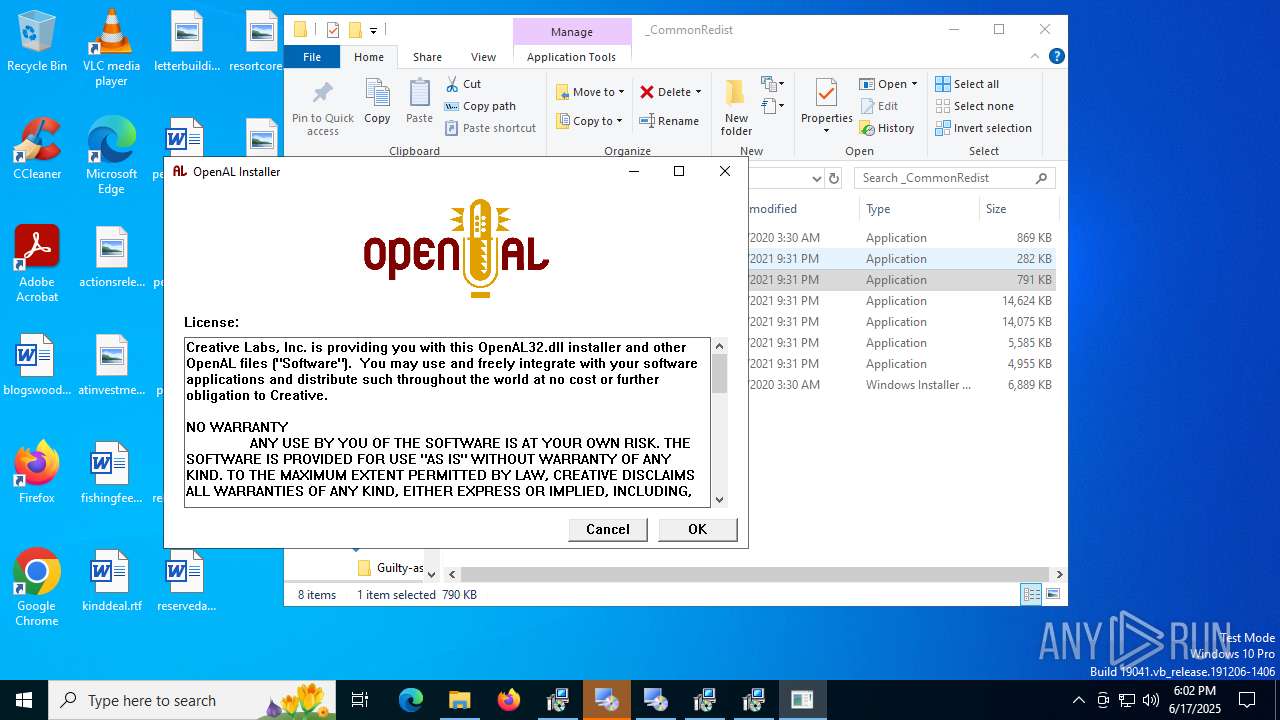
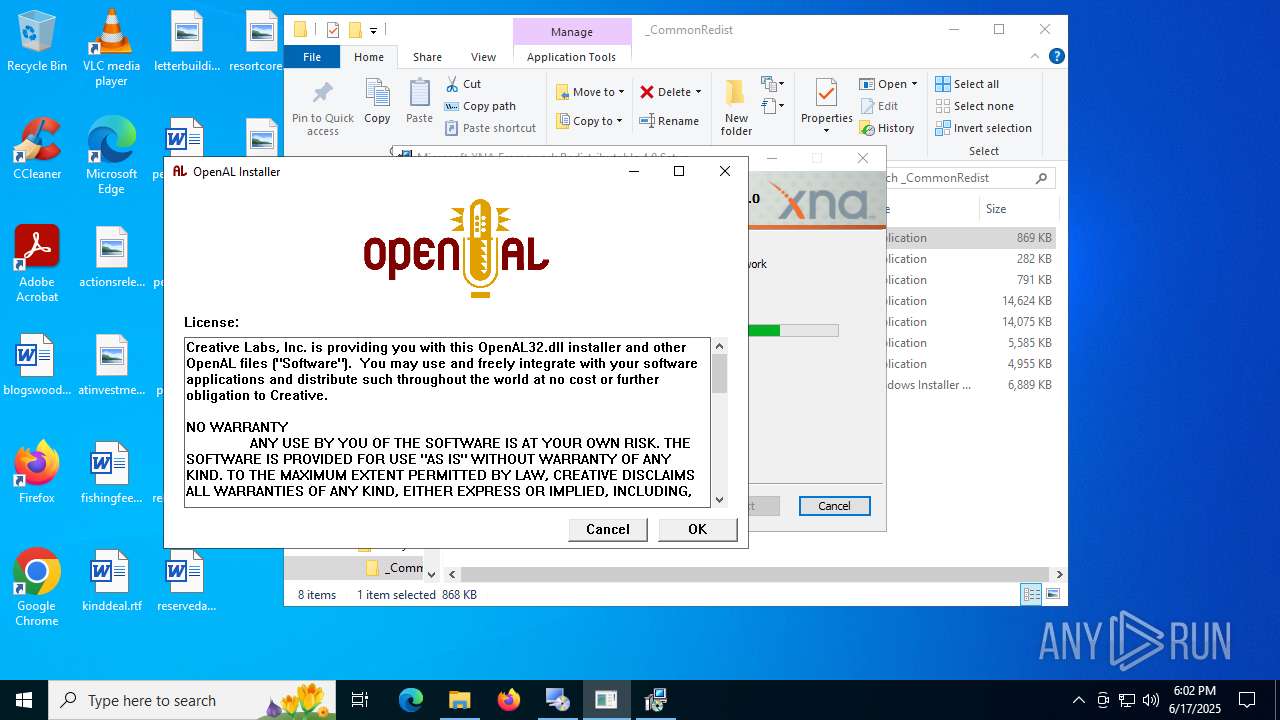
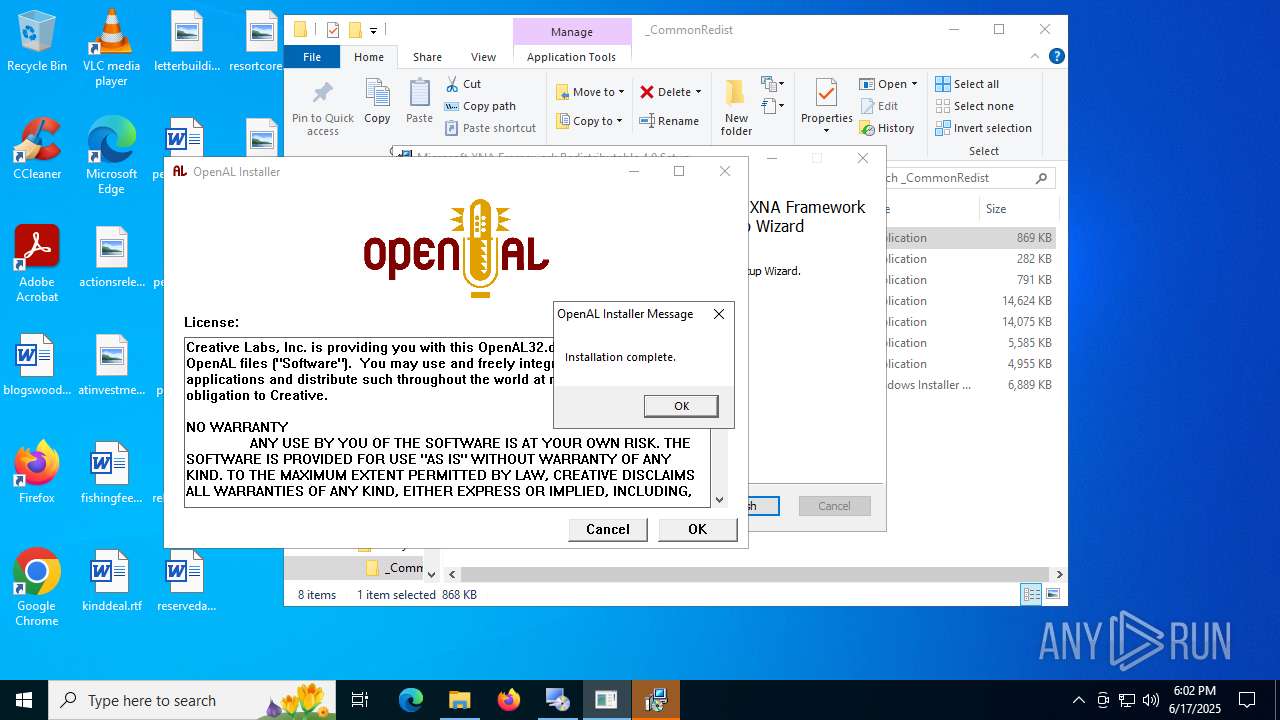
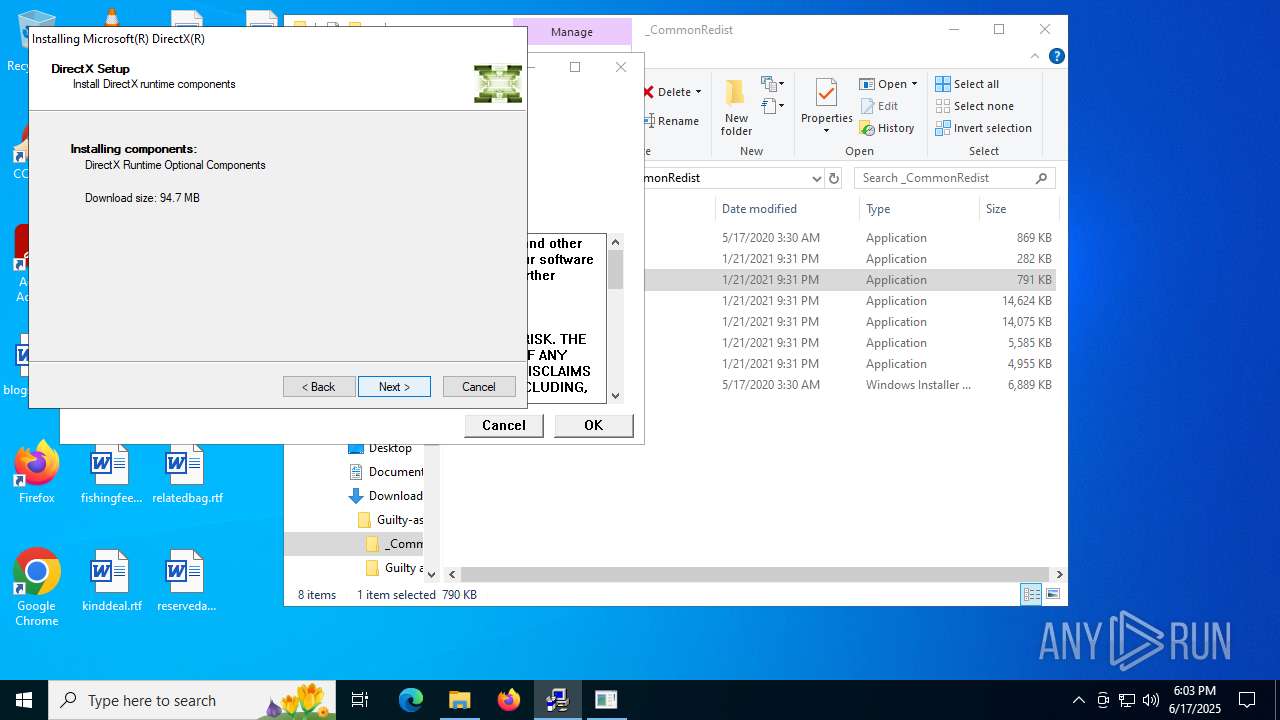
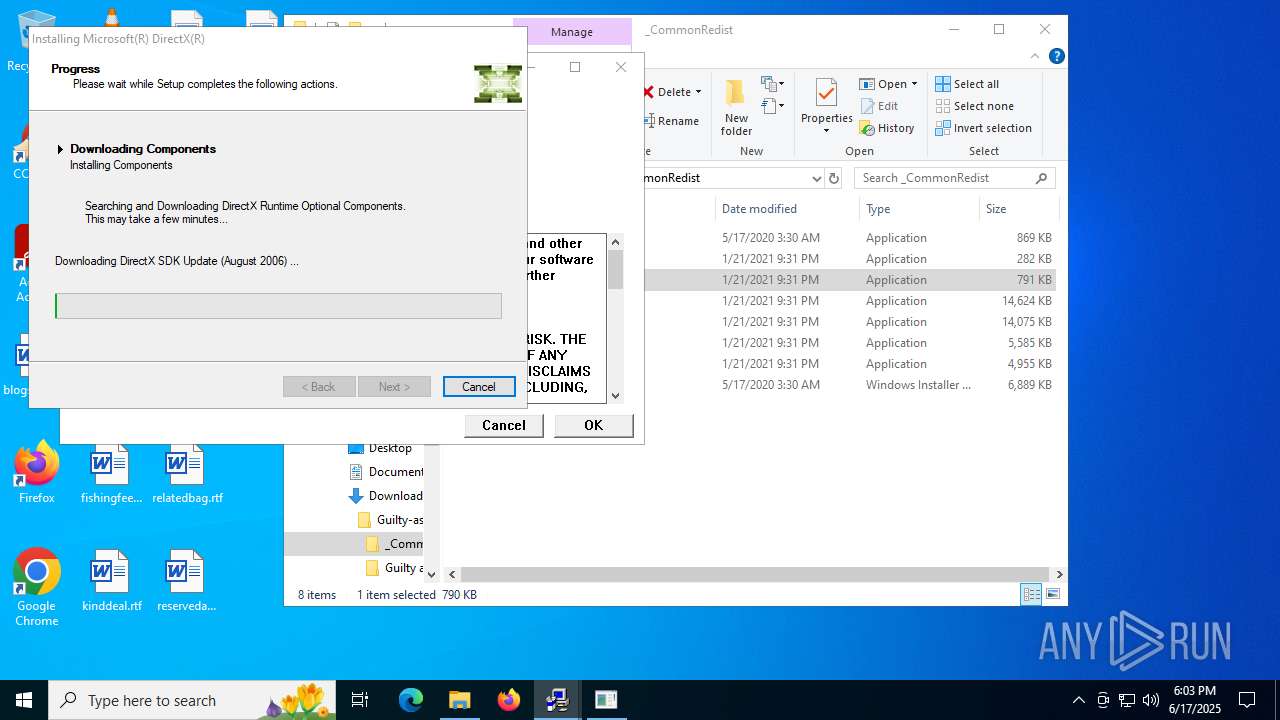
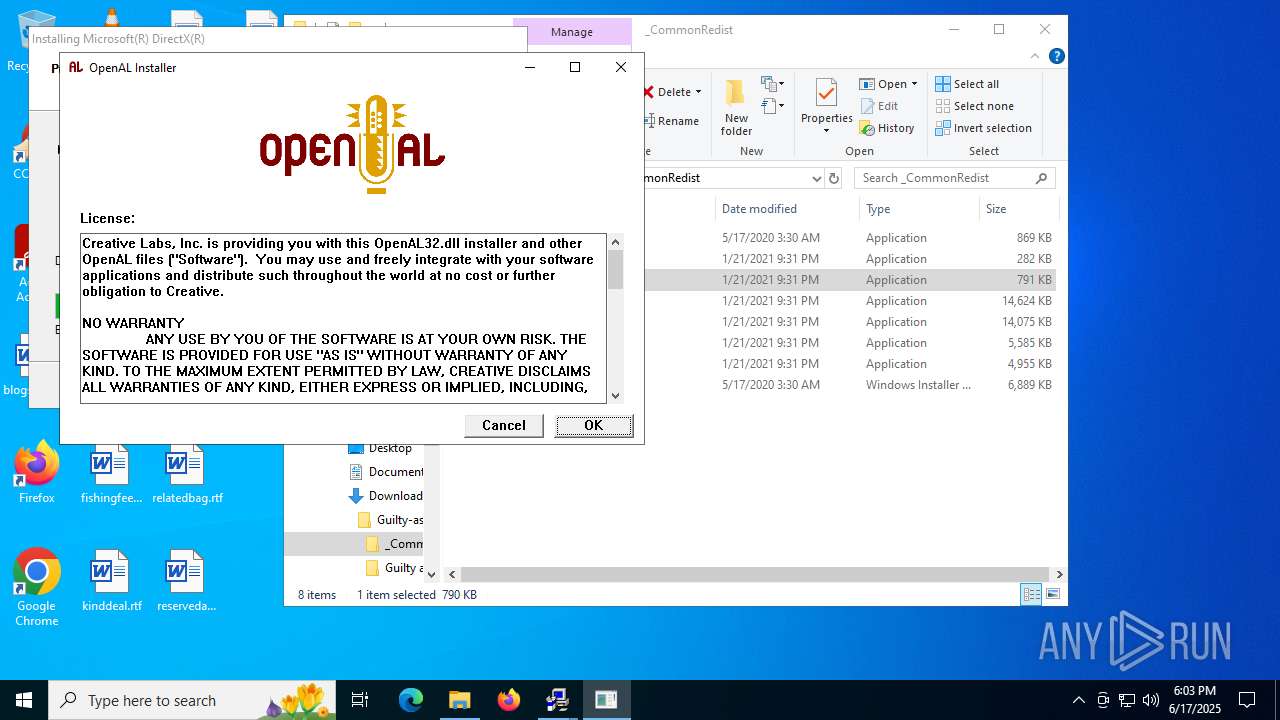
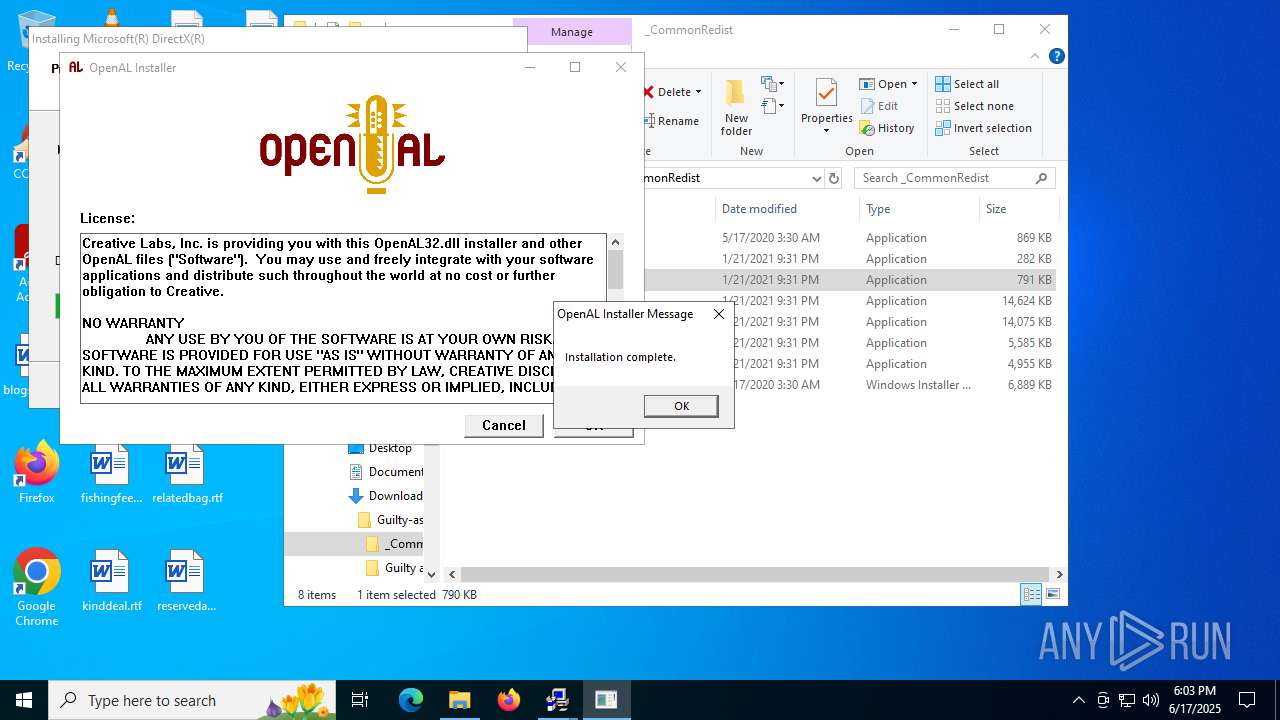
- oalinst.exe (PID: 6656)
- dotNetFx40_Full_setup.exe (PID: 5720)
- Setup.exe (PID: 6620)
- oalinst.exe (PID: 188)
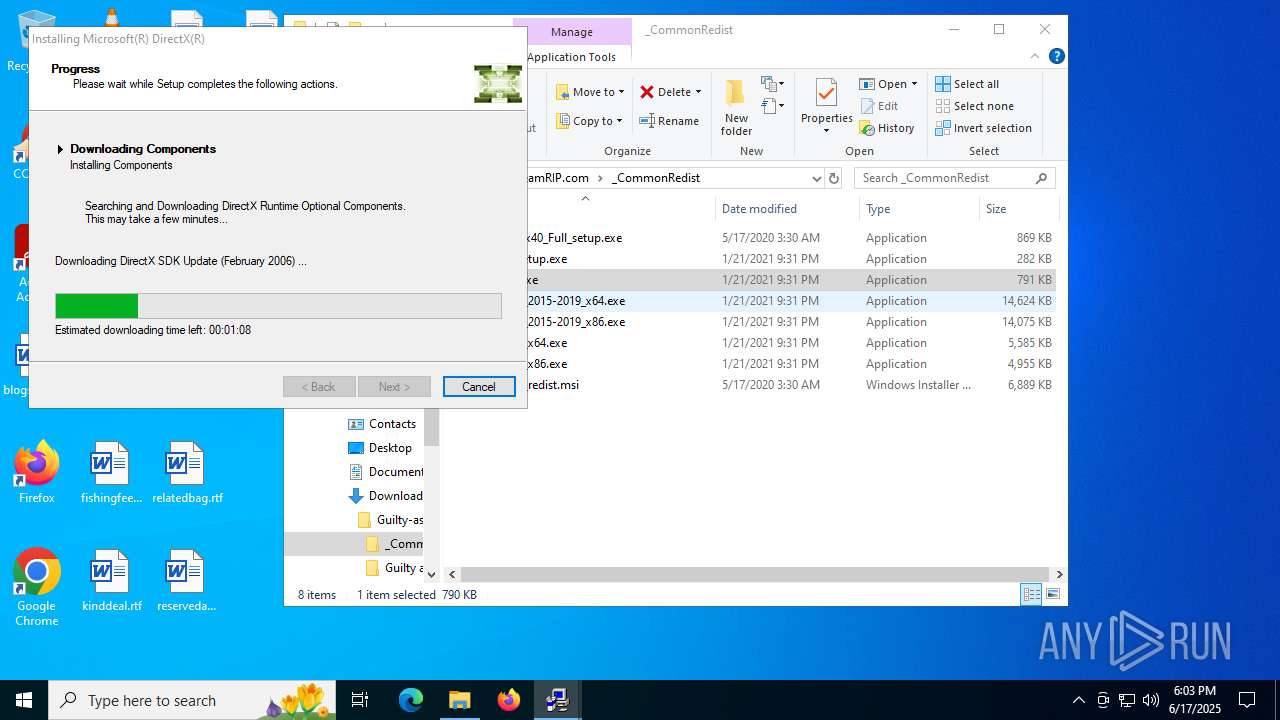
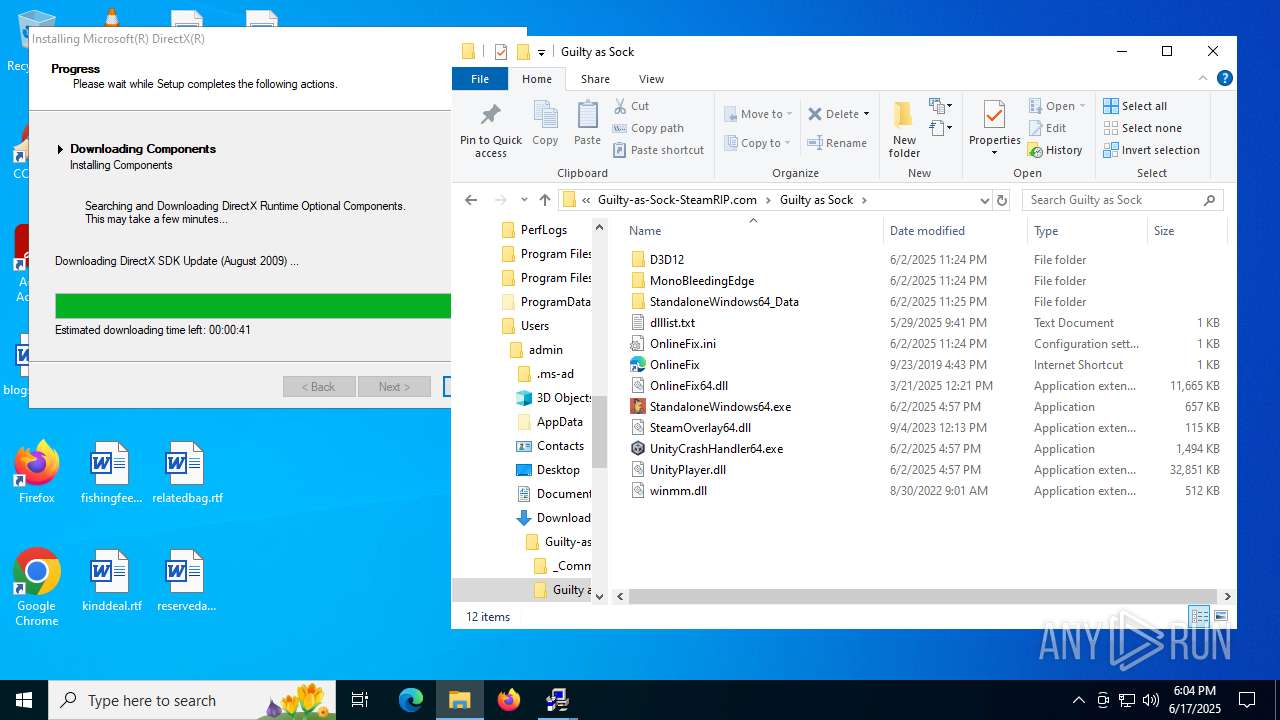
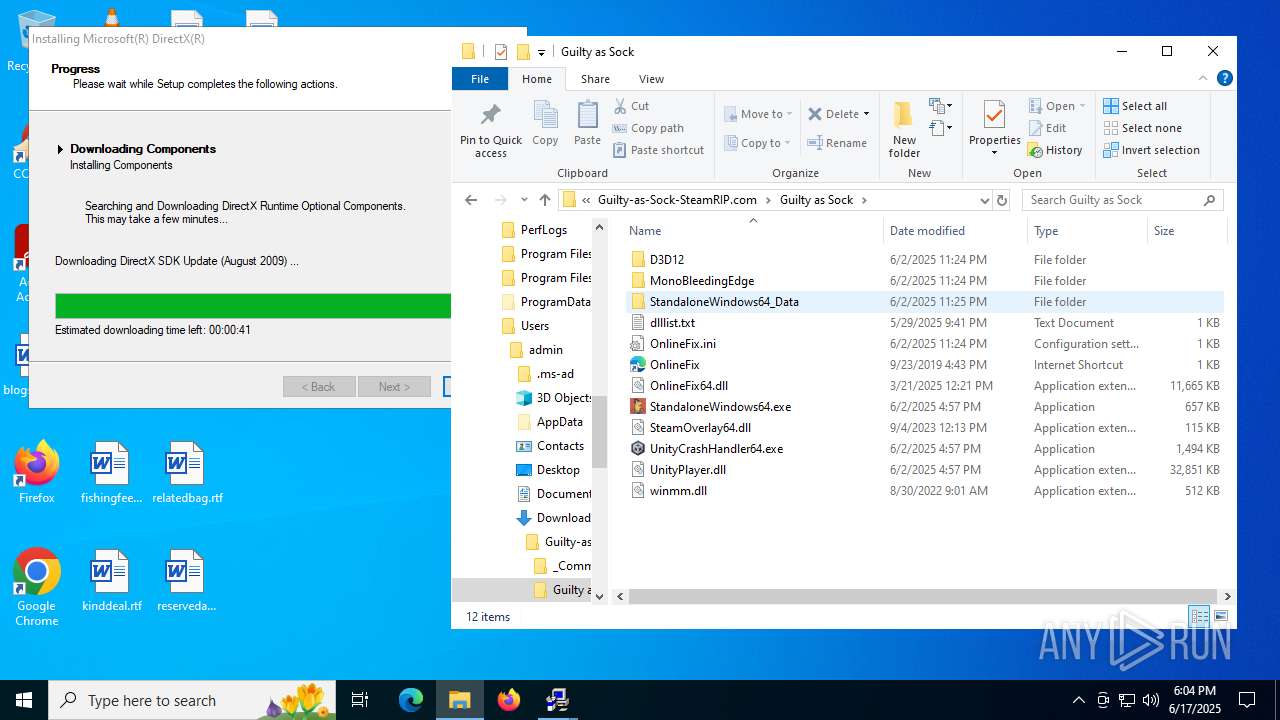
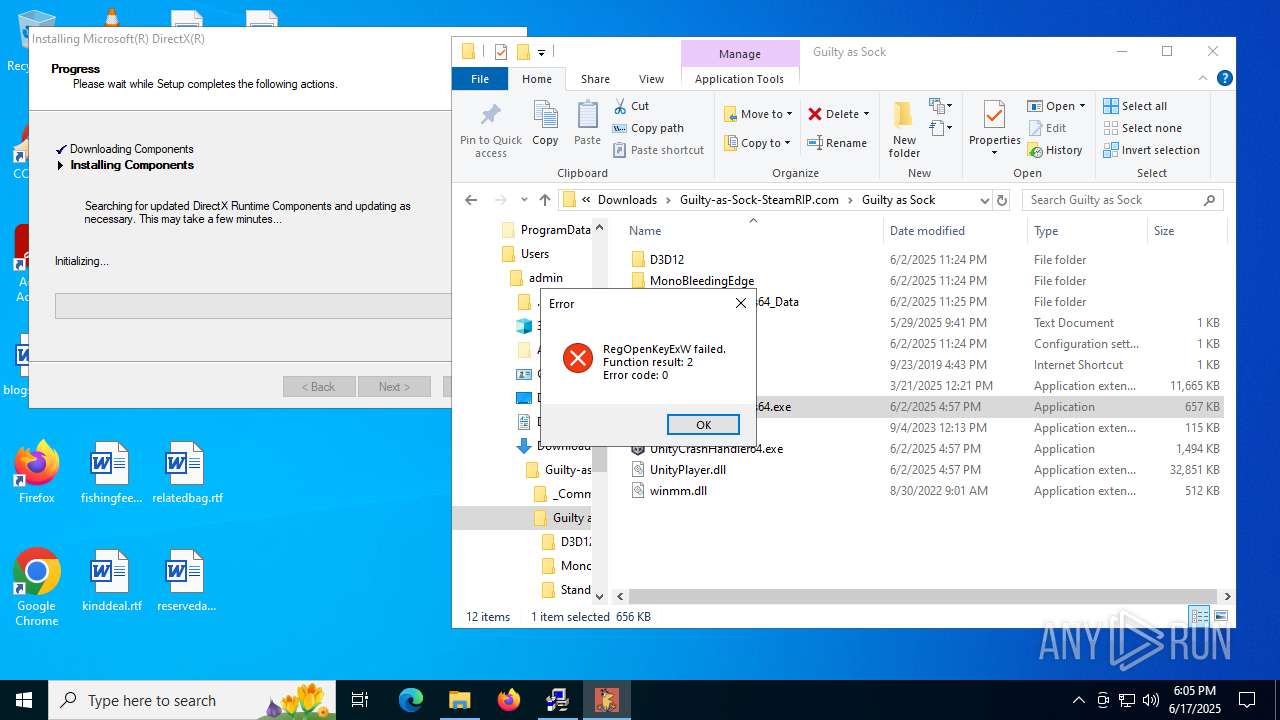
- DXSETUP.exe (PID: 4808)
- dotNetFx40_Full_setup.exe (PID: 8092)
- Setup.exe (PID: 3100)
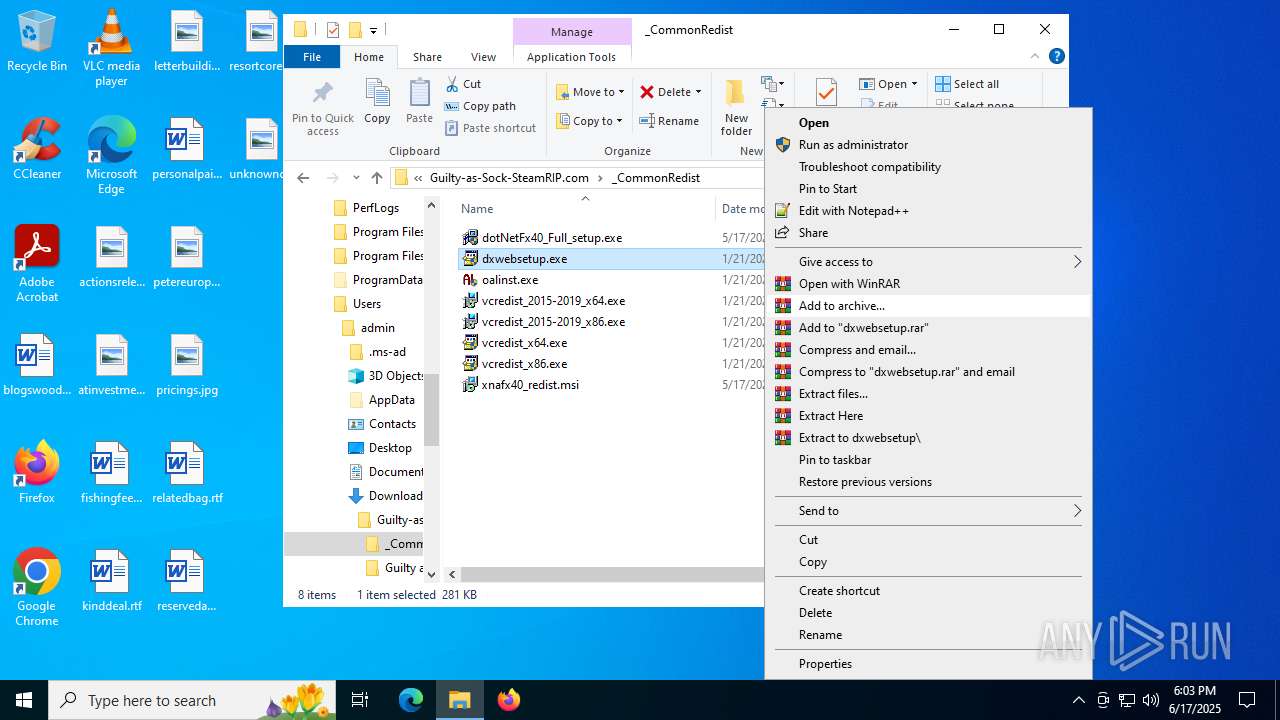
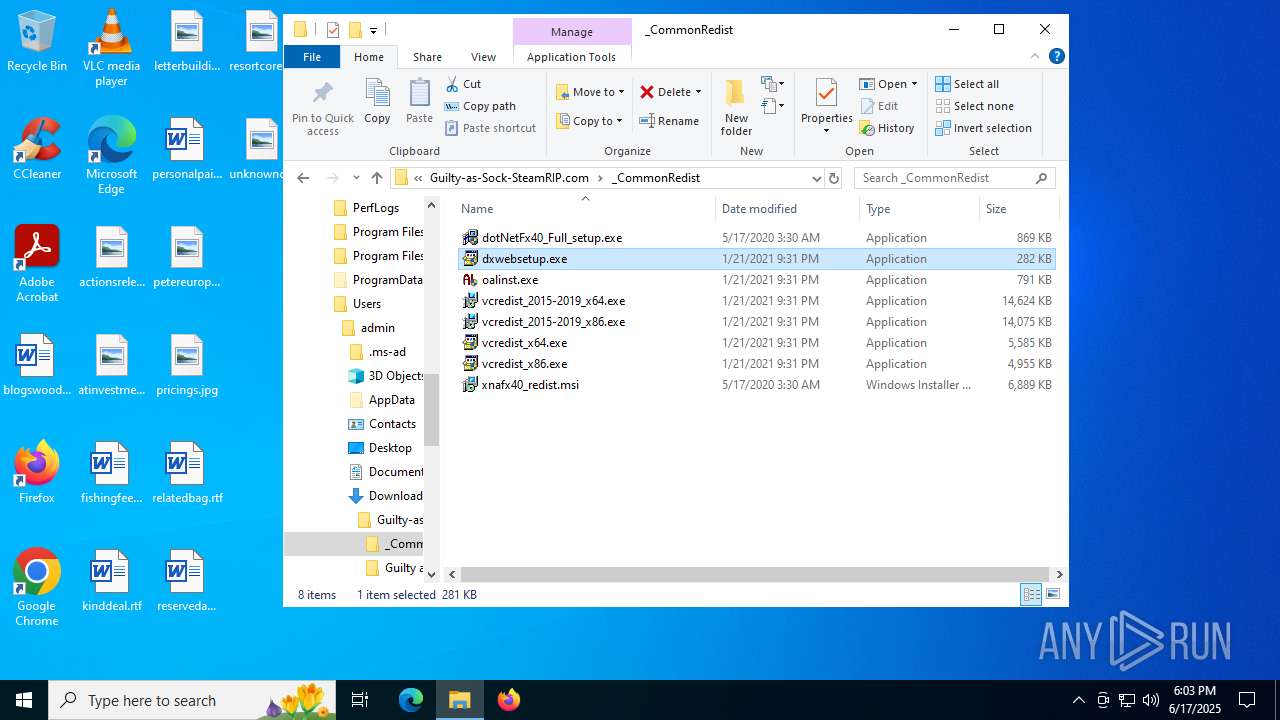
- dxwebsetup.exe (PID: 5436)
- oalinst.exe (PID: 1036)
SUSPICIOUS
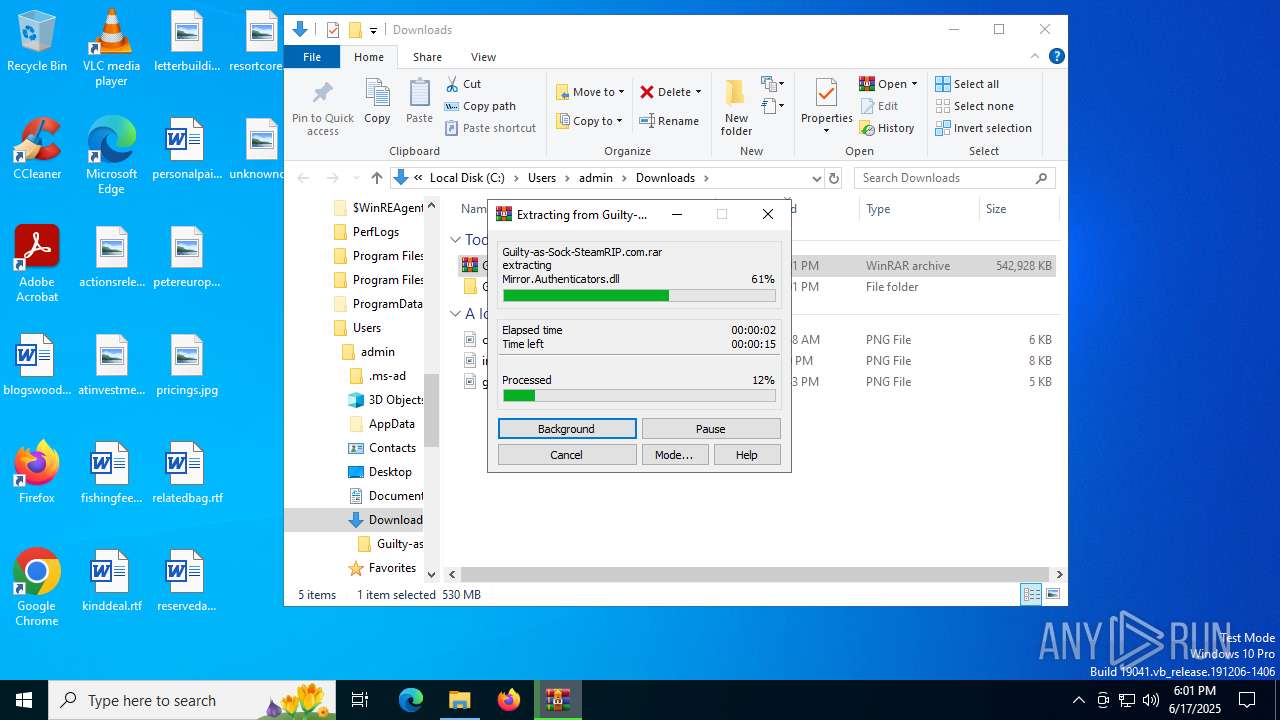
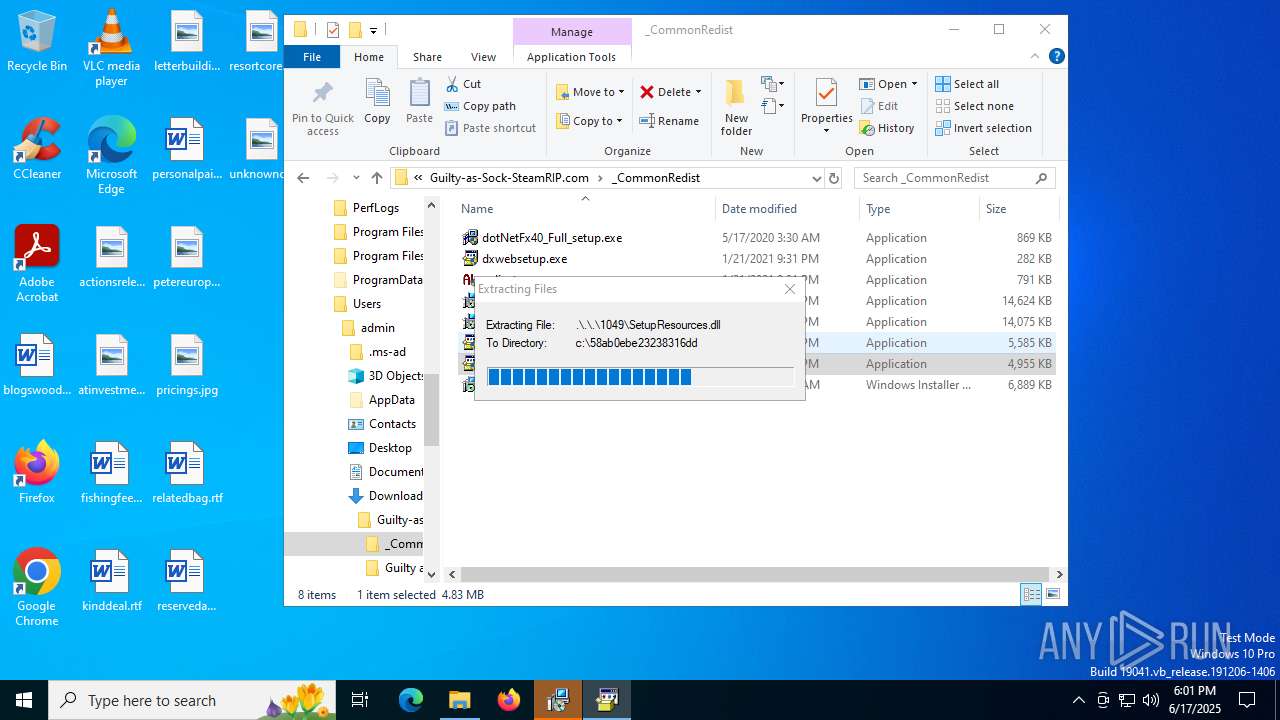
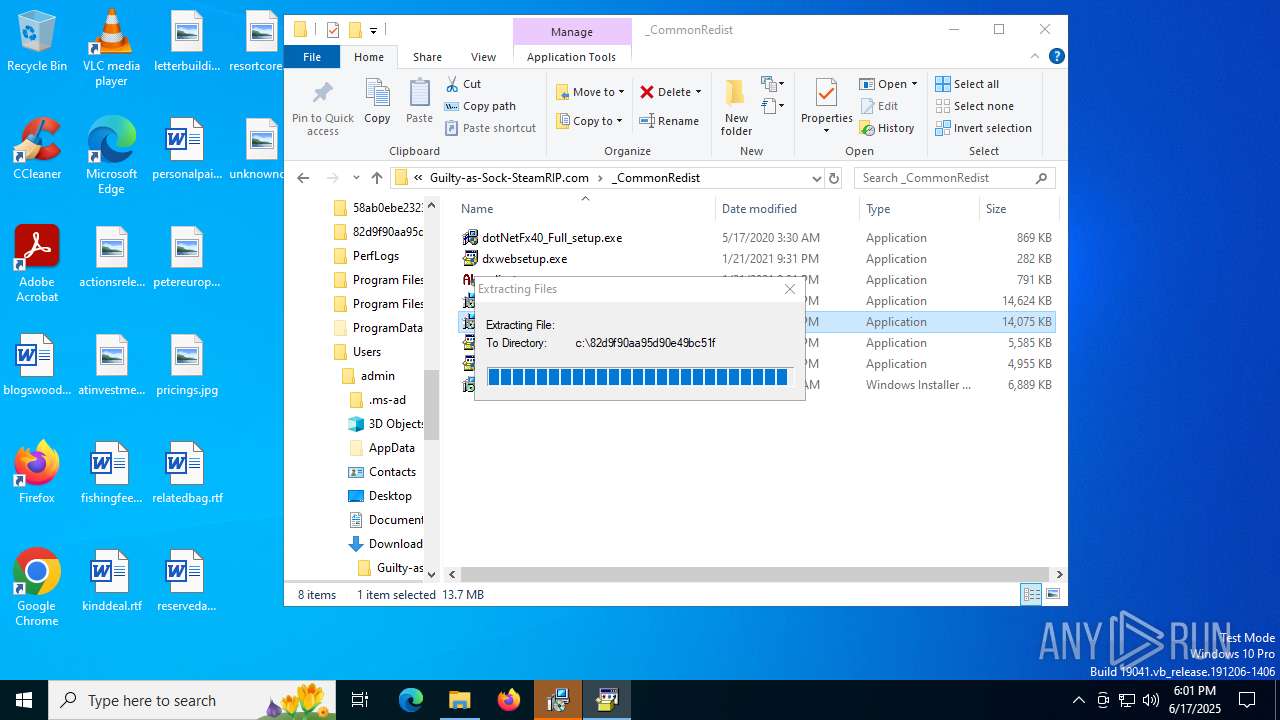
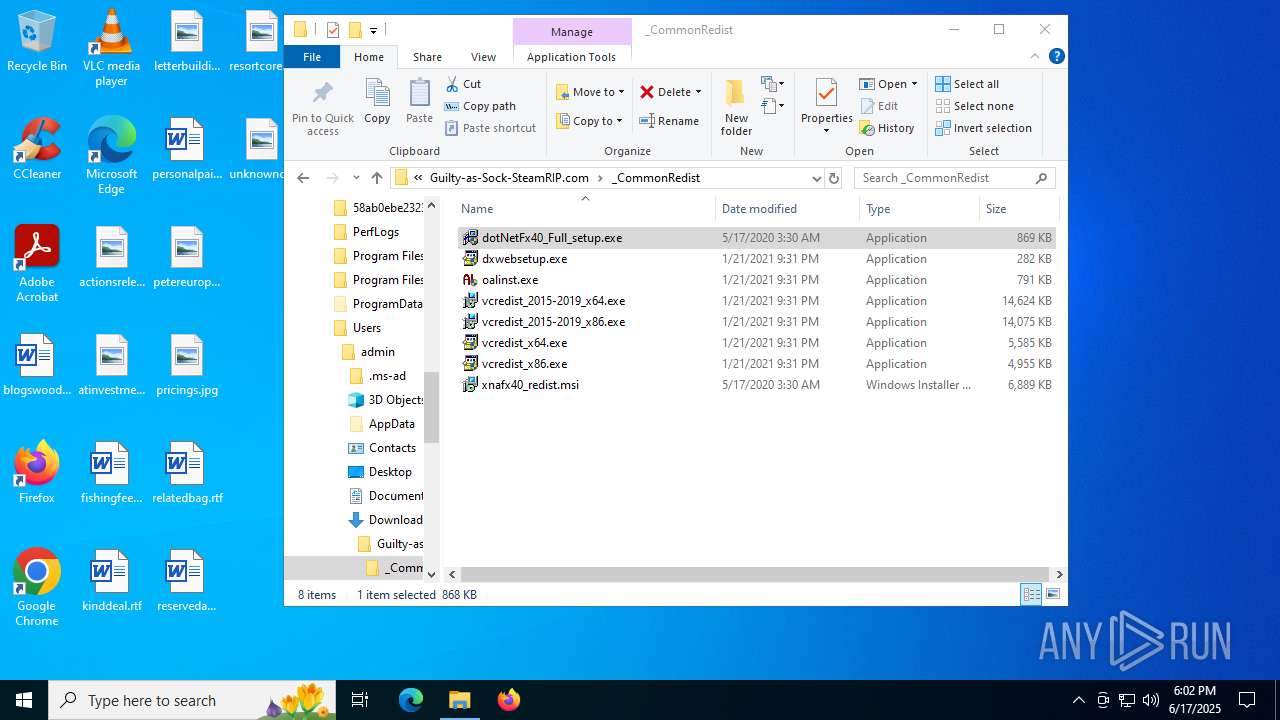
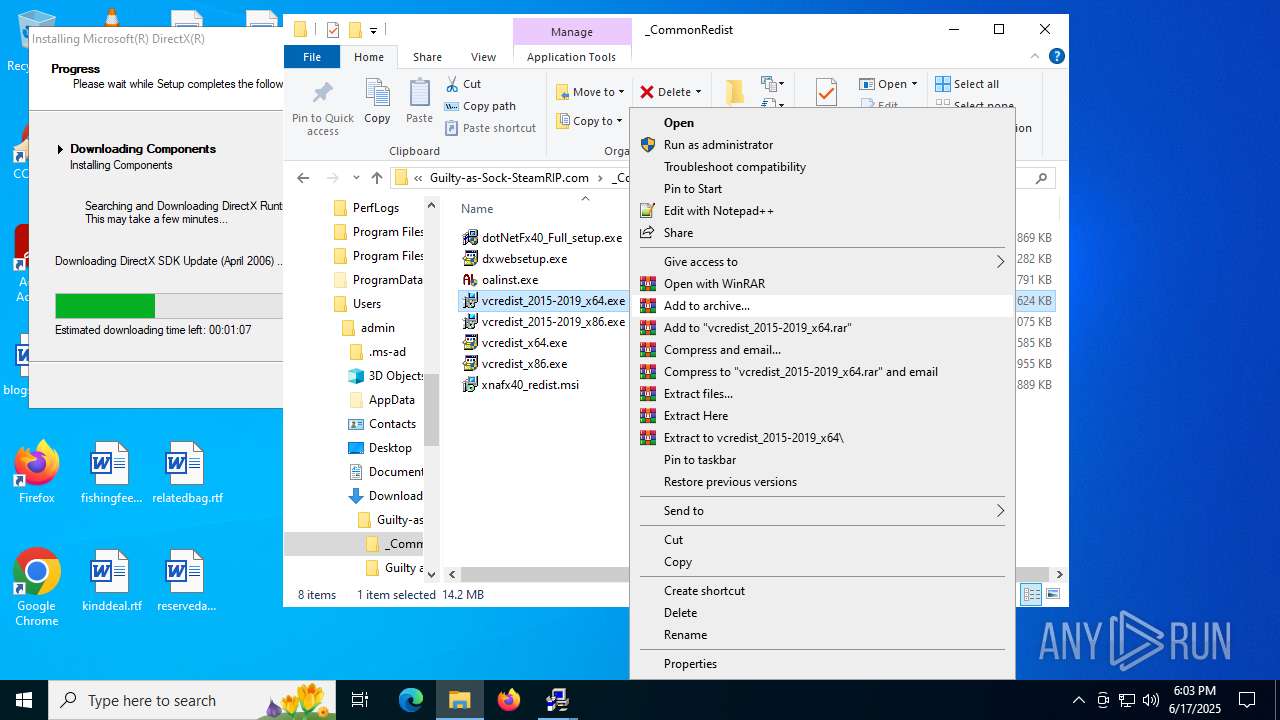
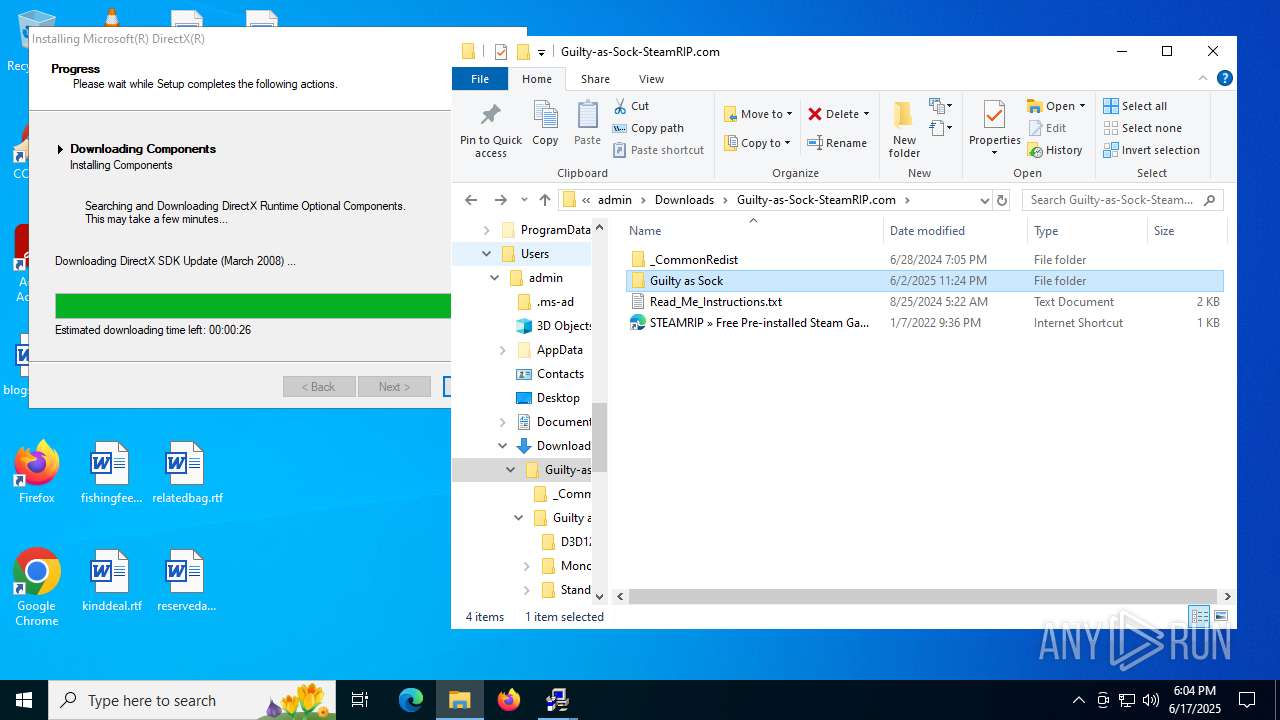
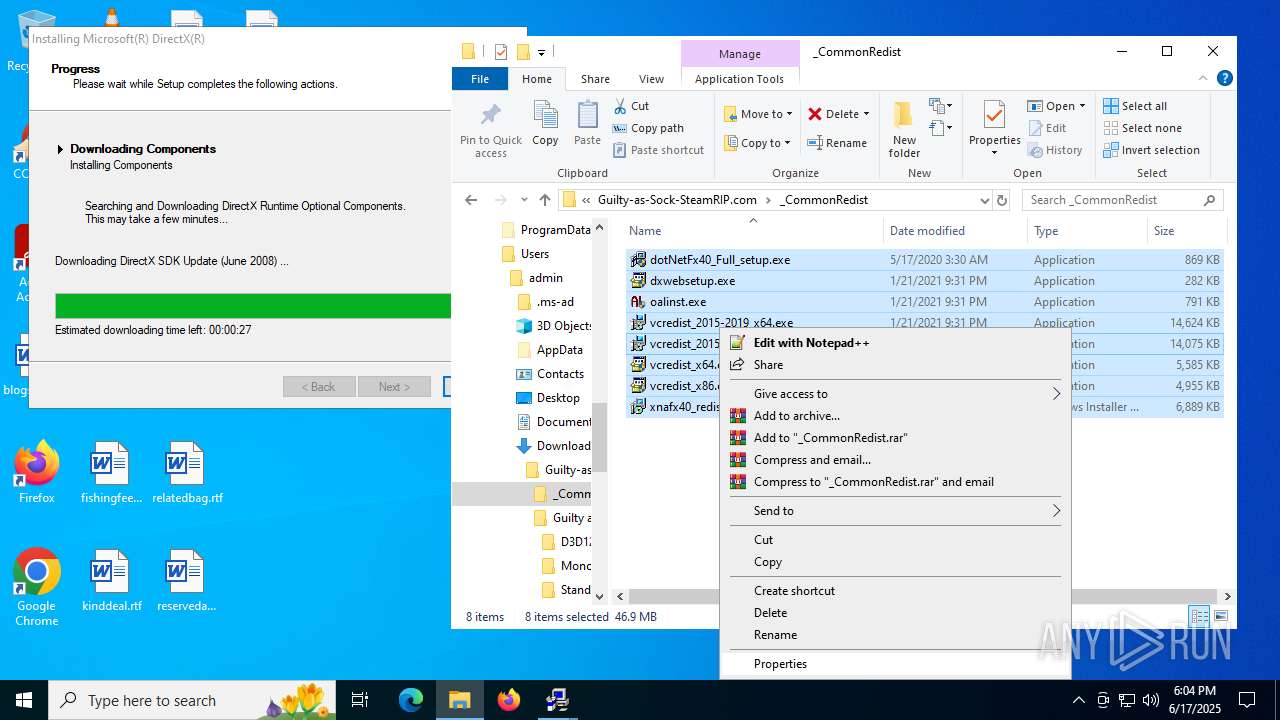
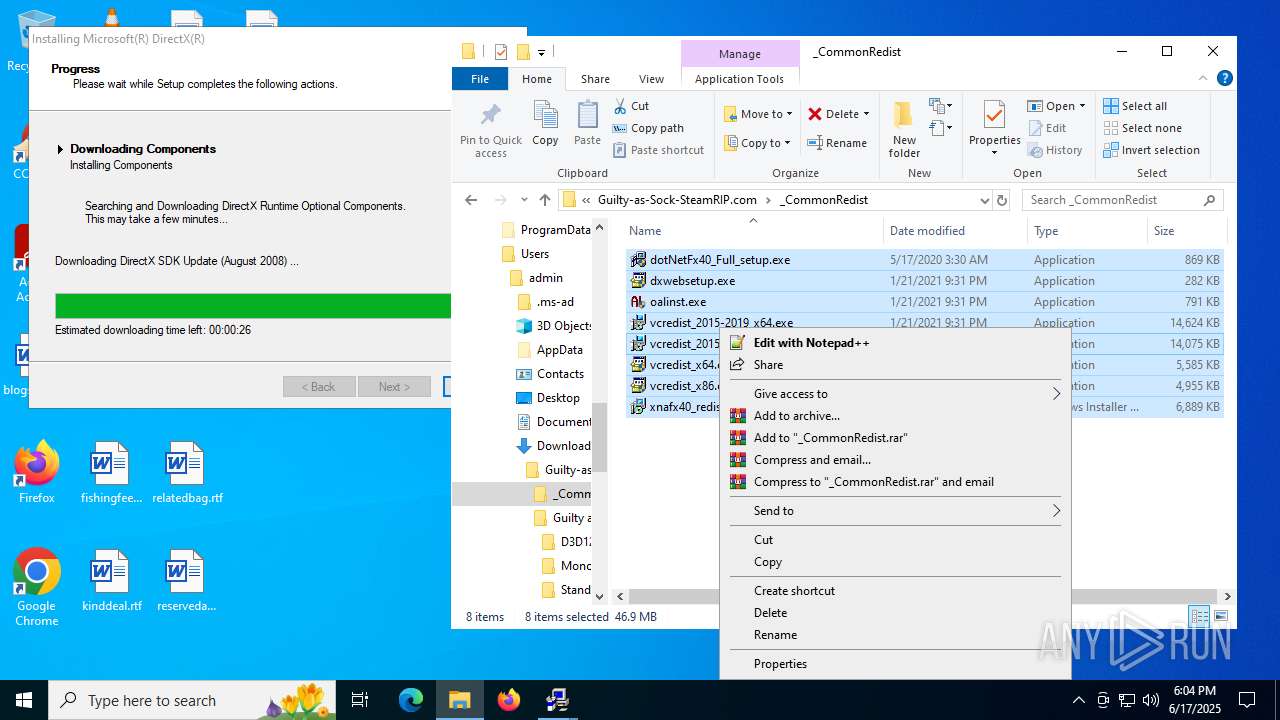
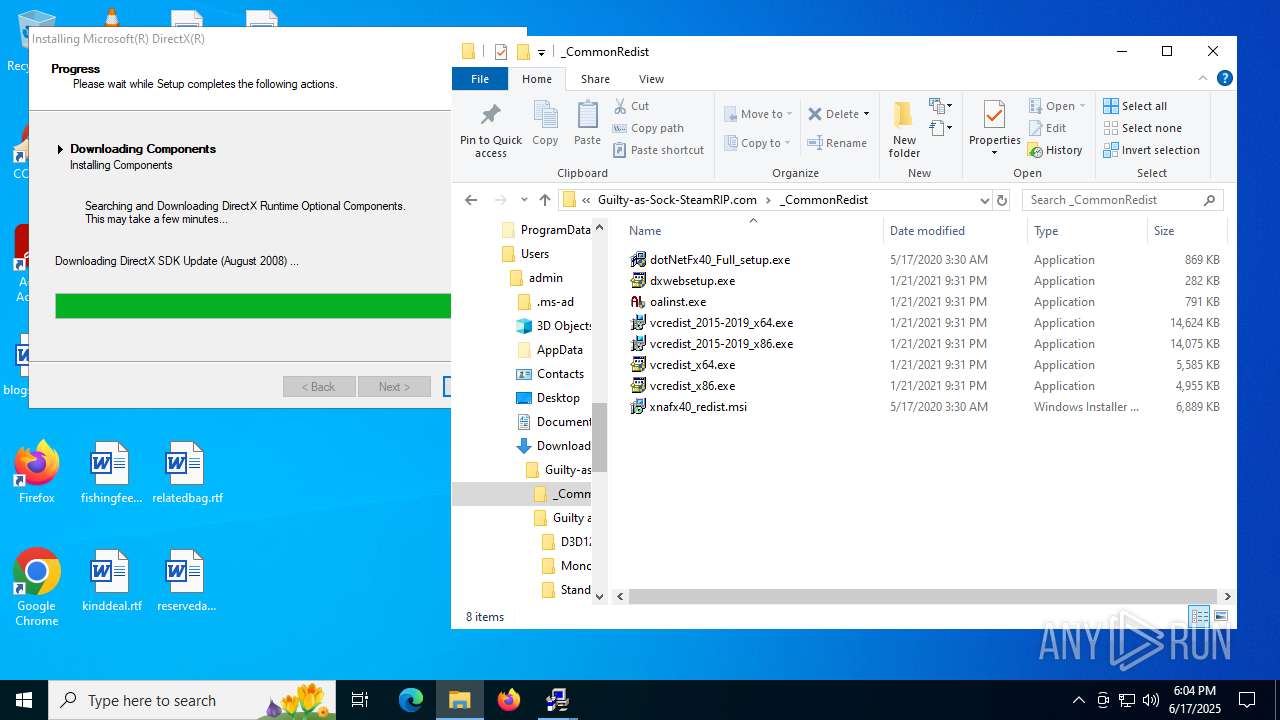
Process drops legitimate windows executable
- WinRAR.exe (PID: 1728)
- vcredist_x86.exe (PID: 5372)
- vcredist_x64.exe (PID: 2552)
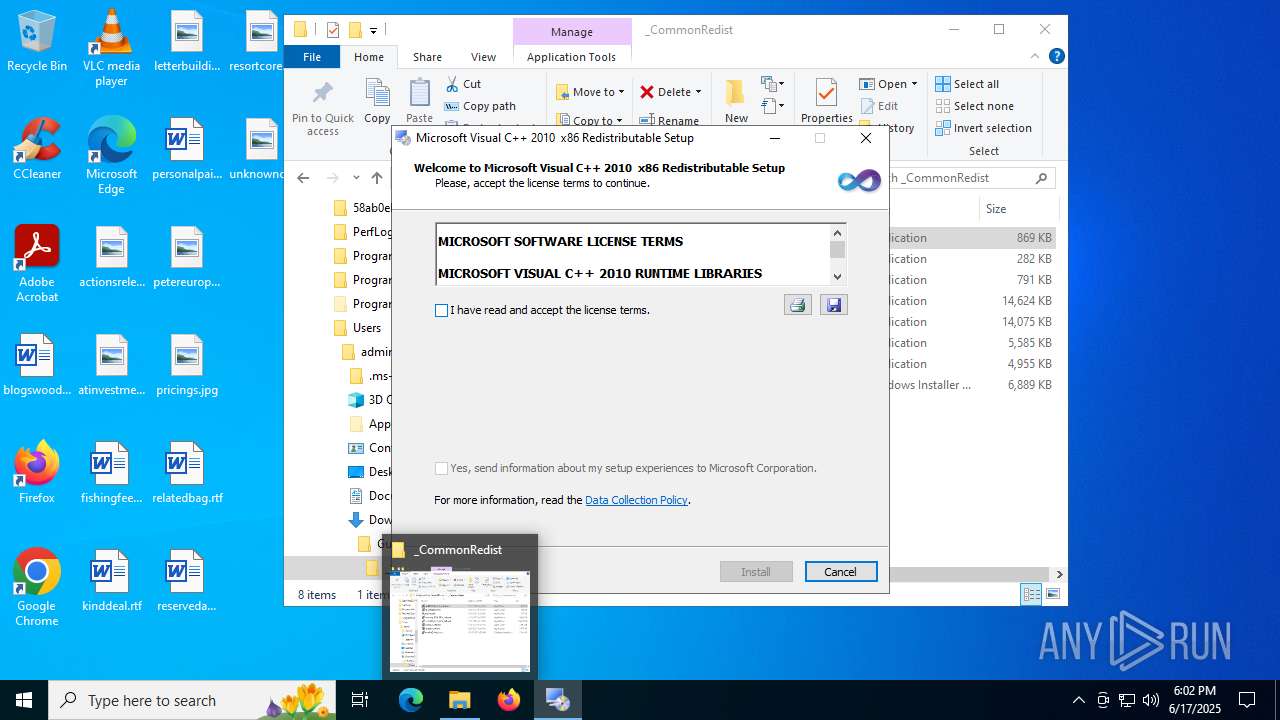
- vcredist_2015-2019_x86.exe (PID: 5644)
- vcredist_2015-2019_x64.exe (PID: 1128)
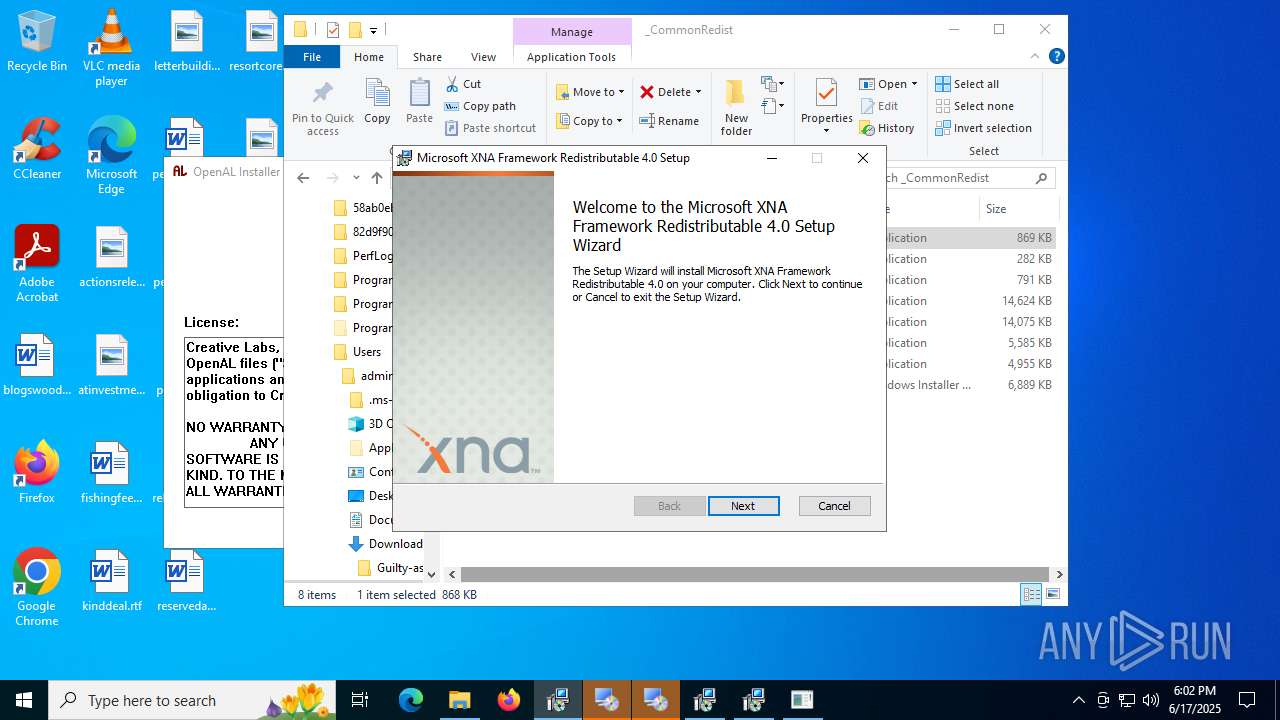
- dotNetFx40_Full_setup.exe (PID: 5720)
- msiexec.exe (PID: 7540)
- DXSETUP.exe (PID: 4808)
- dotNetFx40_Full_setup.exe (PID: 8092)
- dxwebsetup.exe (PID: 5436)
- dxwsetup.exe (PID: 7624)
- vcredist_2015-2019_x64.exe (PID: 304)
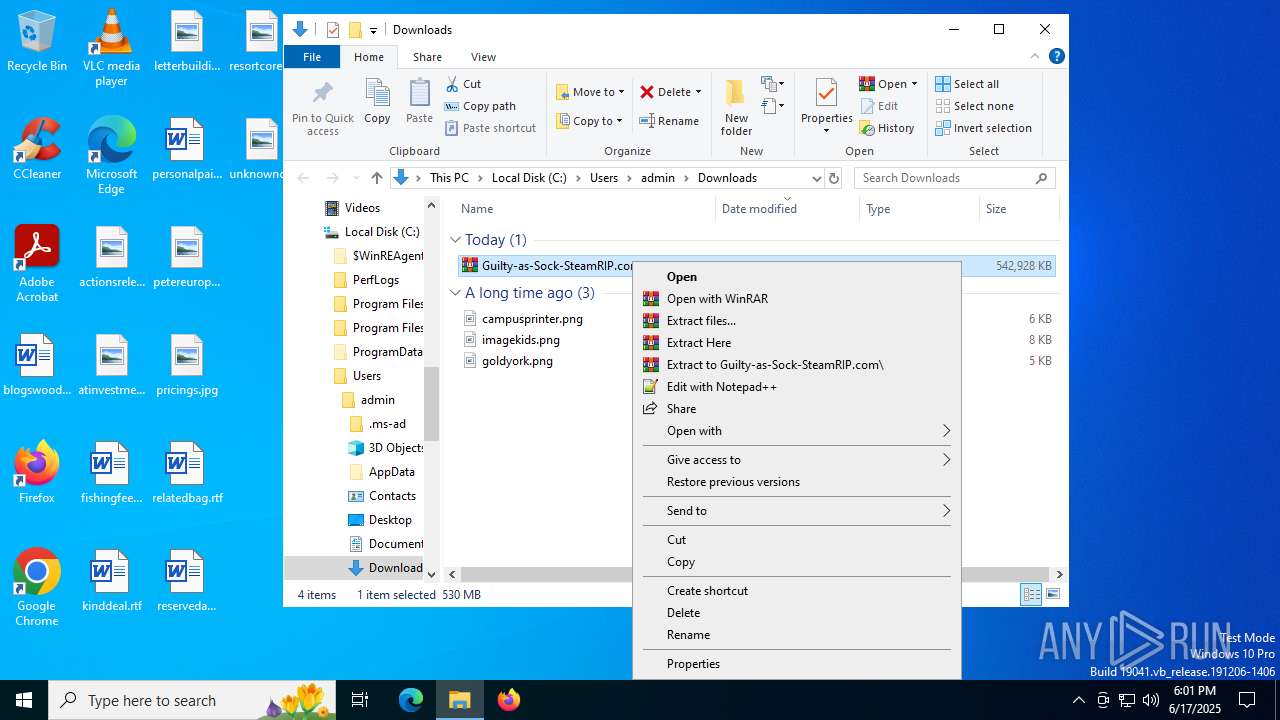
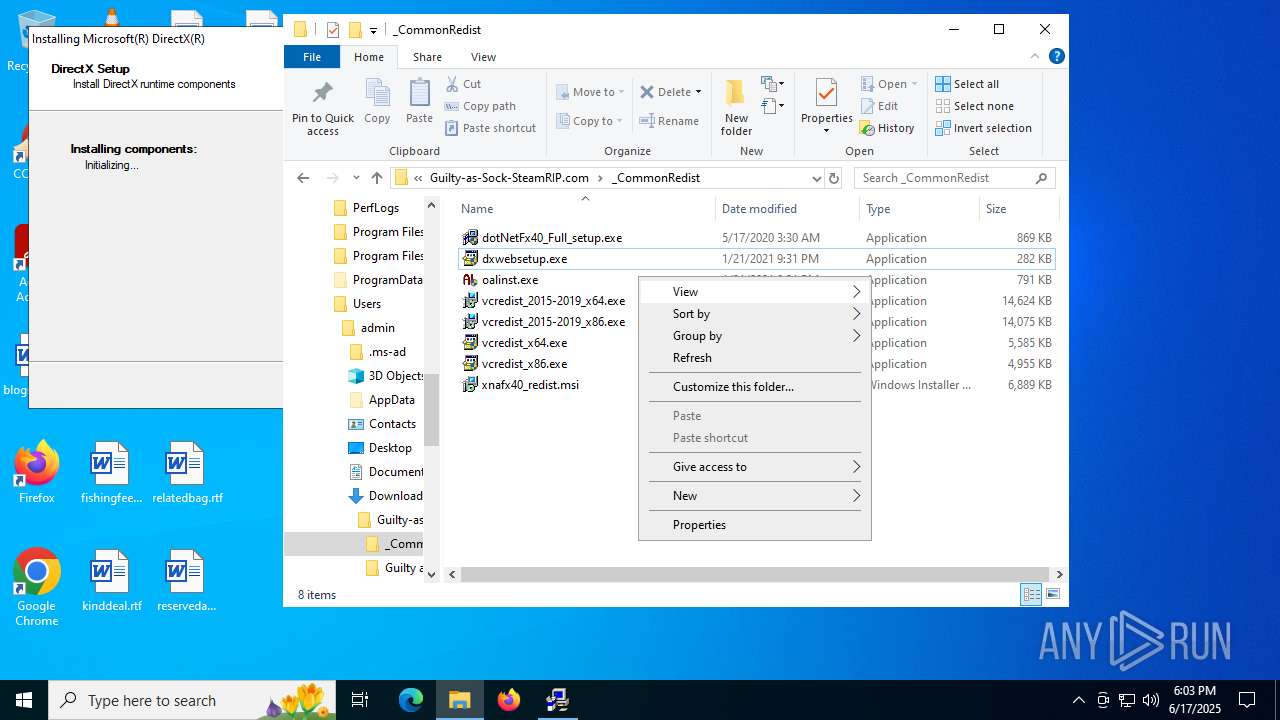
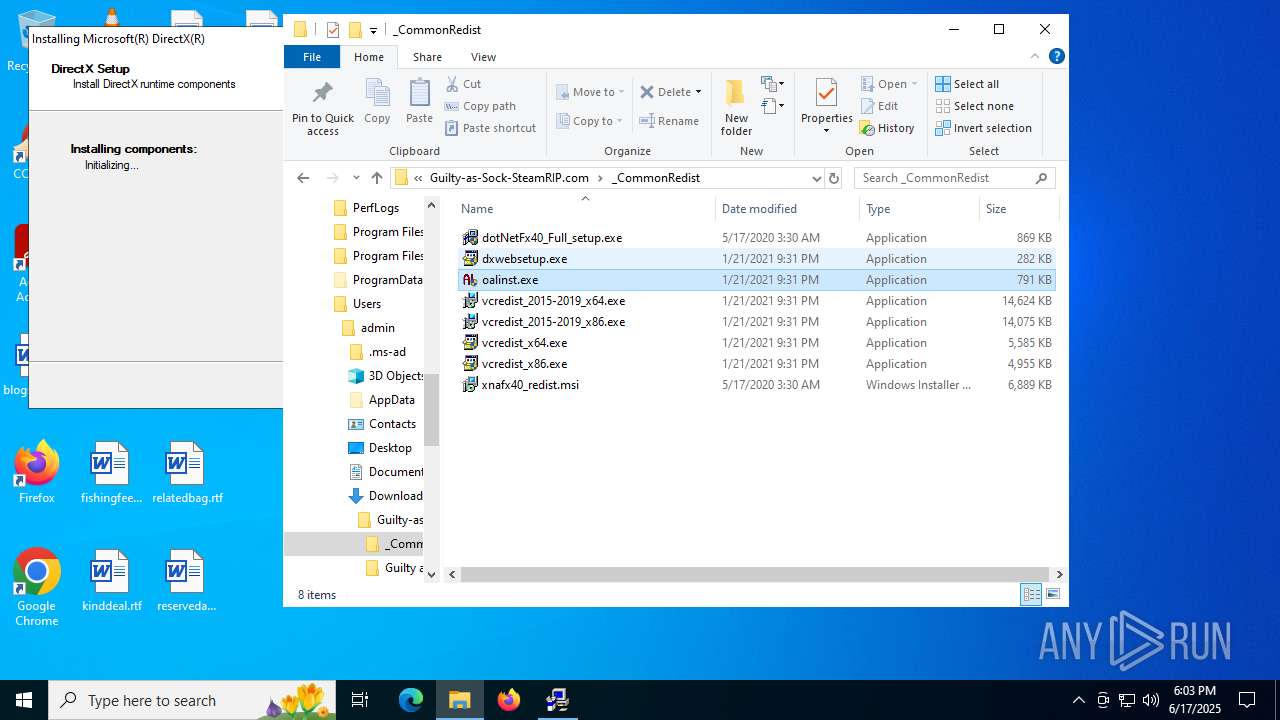
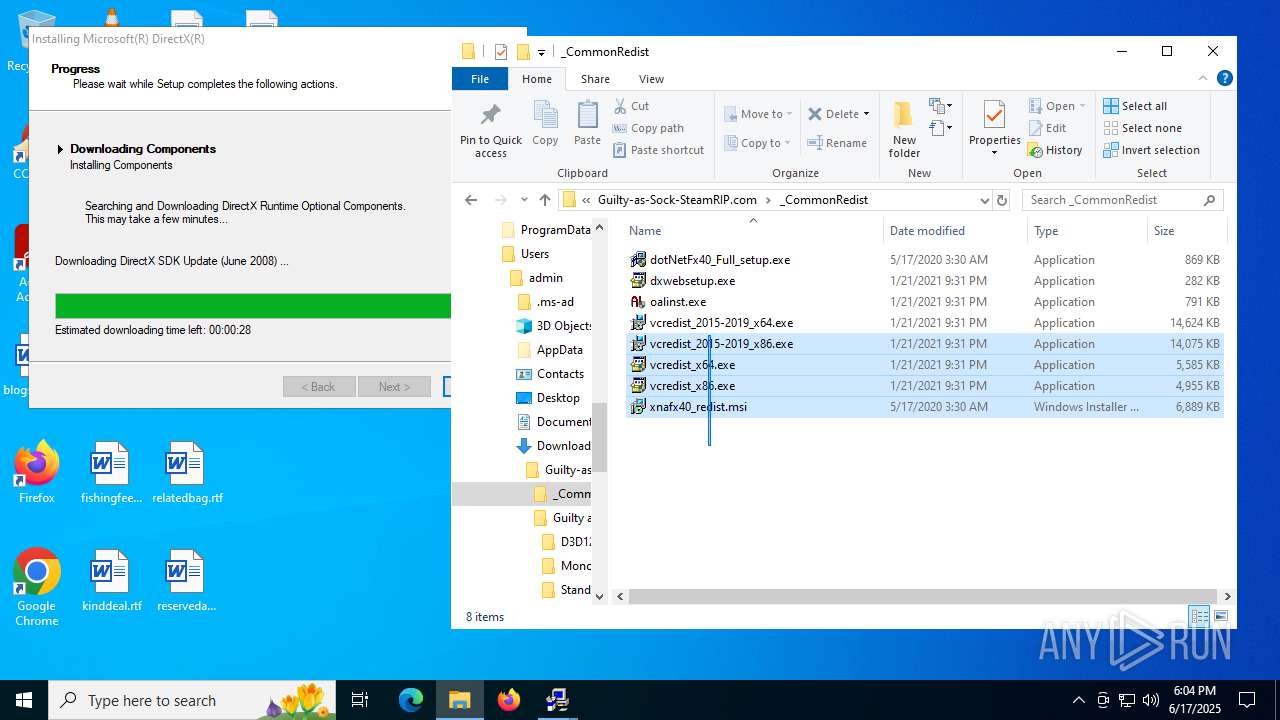
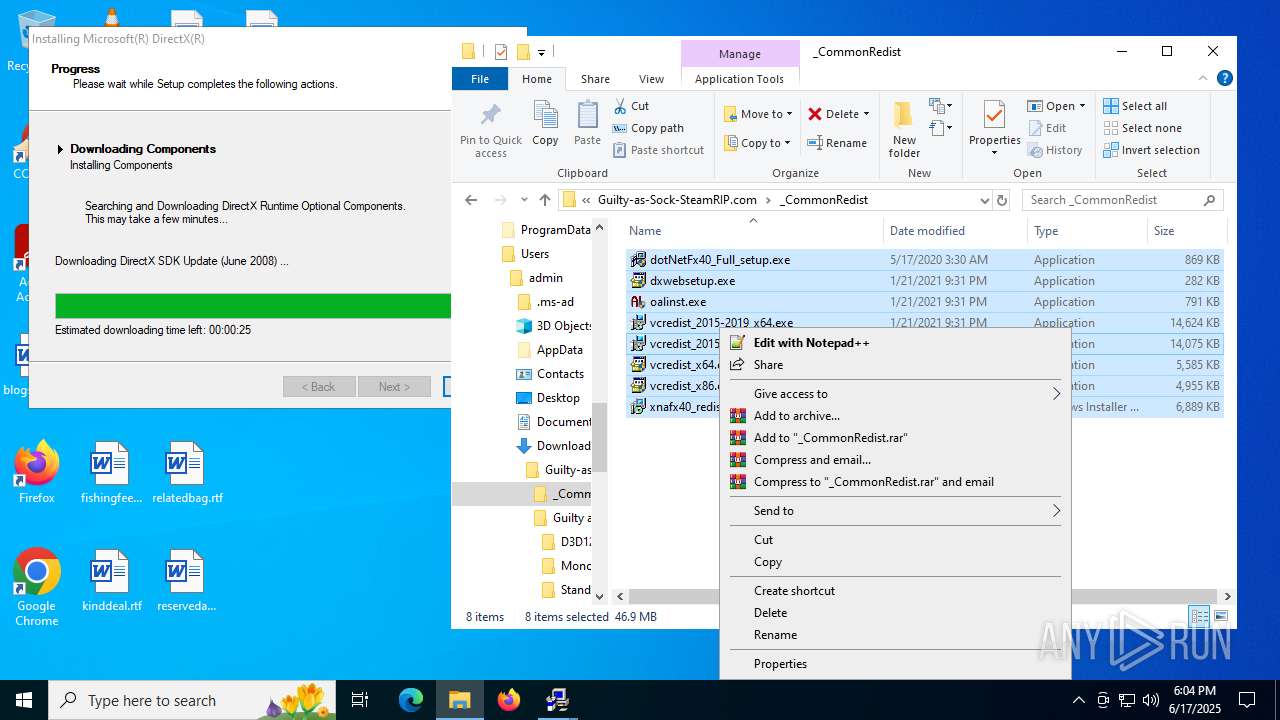
The process creates files with name similar to system file names
- WinRAR.exe (PID: 1728)
Executable content was dropped or overwritten
- vcredist_x64.exe (PID: 2552)
- vcredist_2015-2019_x86.exe (PID: 5644)
- vcredist_x86.exe (PID: 5372)
- vcredist_2015-2019_x86.exe (PID: 6892)
- vcredist_2015-2019_x64.exe (PID: 1128)
- vcredist_2015-2019_x64.exe (PID: 4984)
- dotNetFx40_Full_setup.exe (PID: 5720)
- DXSETUP.exe (PID: 4808)
- dotNetFx40_Full_setup.exe (PID: 8092)
- dxwebsetup.exe (PID: 5436)
- dxwsetup.exe (PID: 7624)
- oalinst.exe (PID: 1036)
- vcredist_2015-2019_x64.exe (PID: 304)
- vcredist_2015-2019_x64.exe (PID: 7248)
- oalinst.exe (PID: 6656)
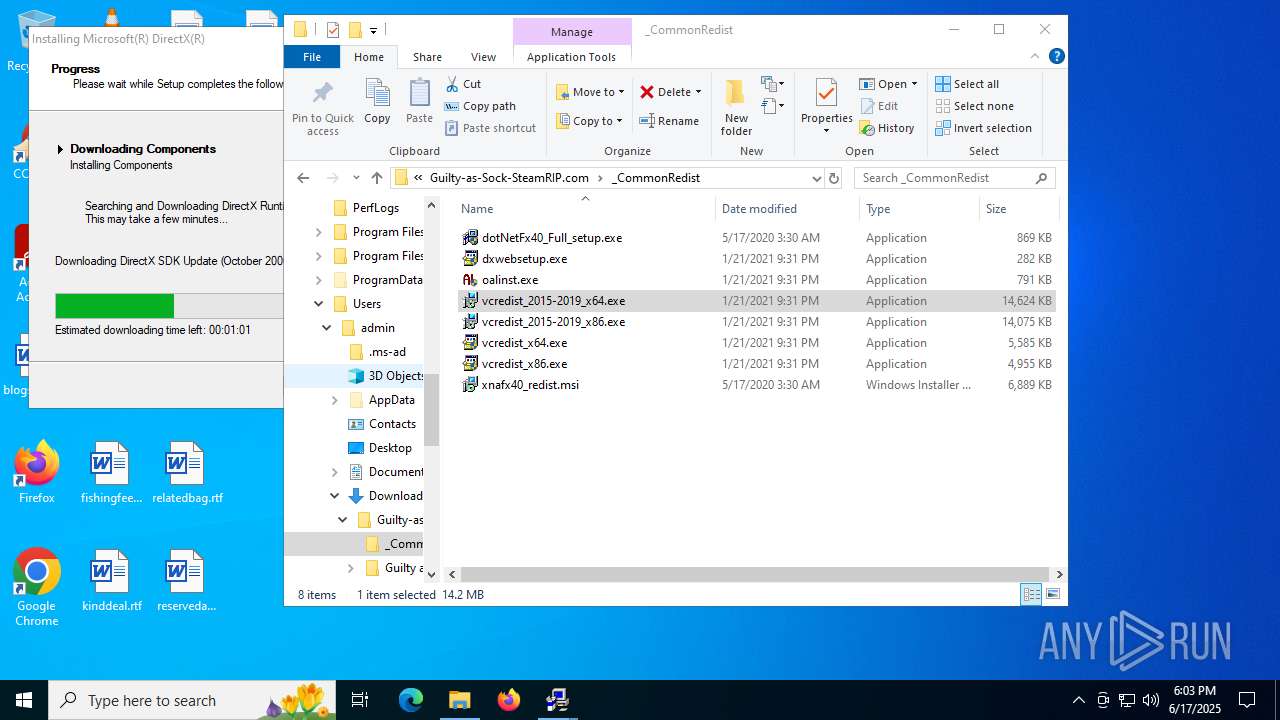
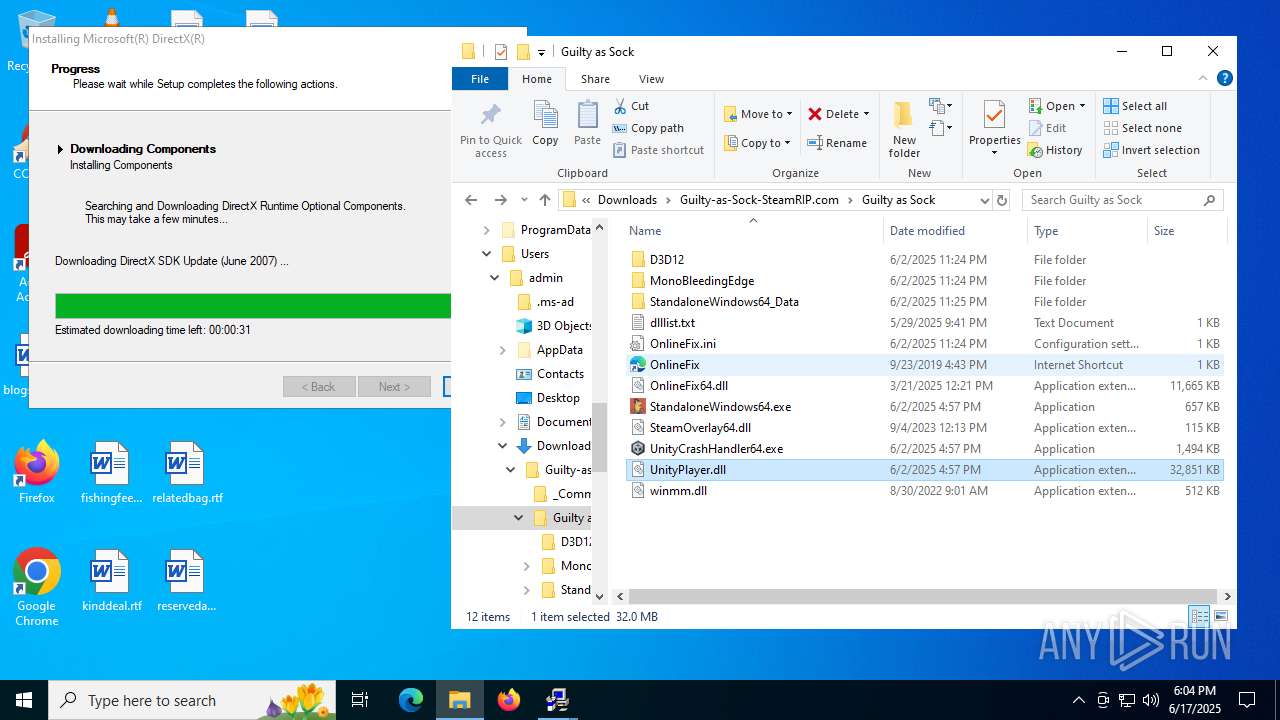
Starts a Microsoft application from unusual location
- vcredist_2015-2019_x86.exe (PID: 6892)
- vcredist_2015-2019_x64.exe (PID: 4984)
- dxwsetup.exe (PID: 7624)
- vcredist_2015-2019_x64.exe (PID: 7248)
Executes as Windows Service
- VSSVC.exe (PID: 8116)
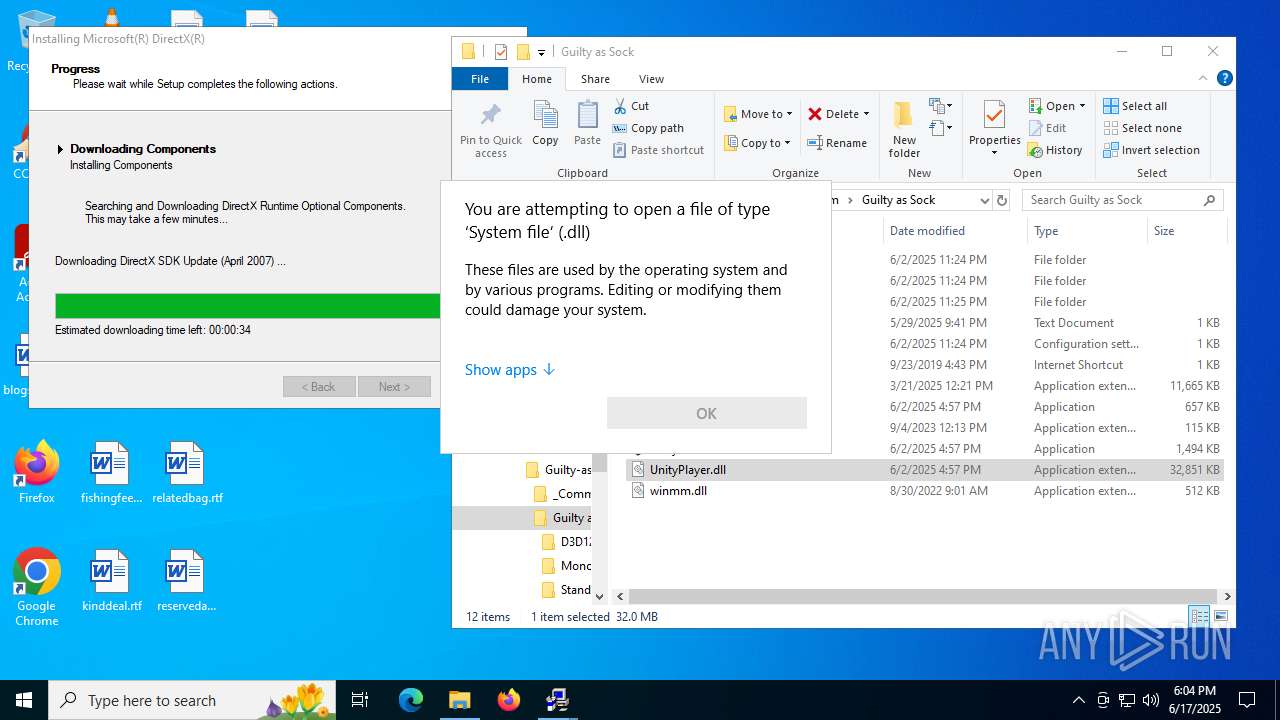
The process drops C-runtime libraries
- msiexec.exe (PID: 7540)
There is functionality for taking screenshot (YARA)
- oalinst.exe (PID: 6656)
INFO
Application launched itself
- msedge.exe (PID: 2648)
- msedge.exe (PID: 5244)
Checks supported languages
- identity_helper.exe (PID: 7240)
- identity_helper.exe (PID: 7960)
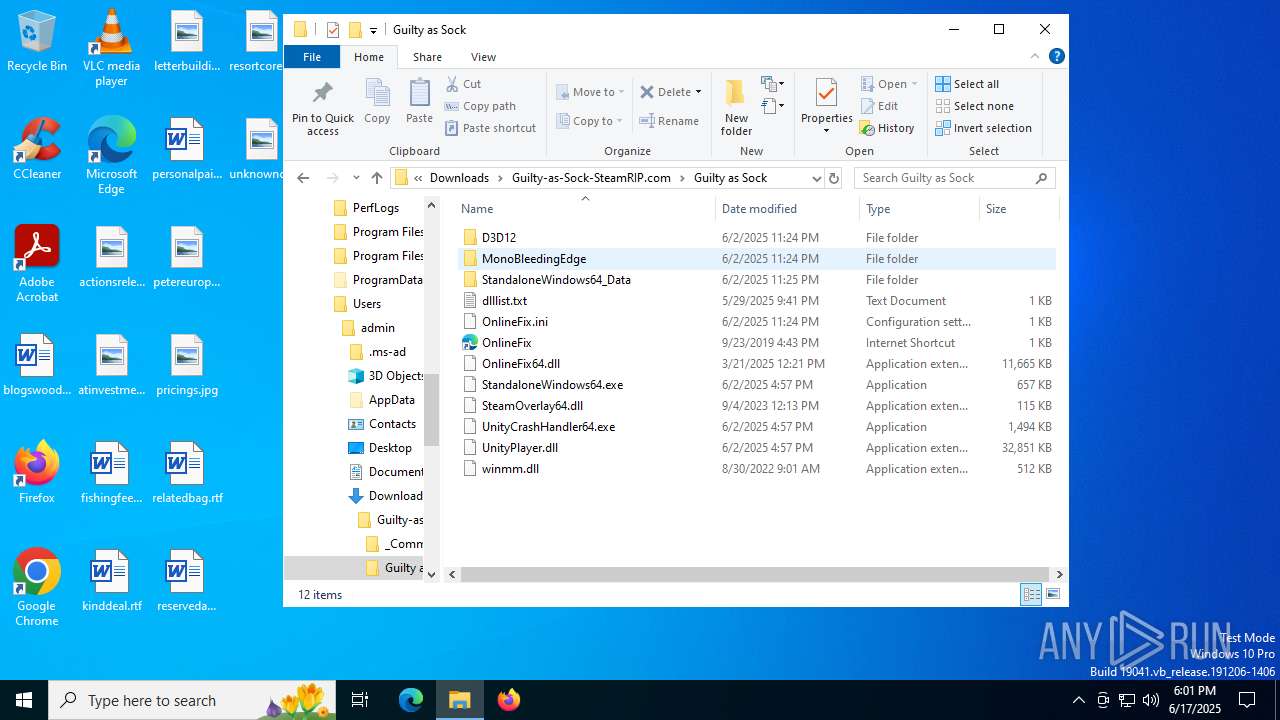
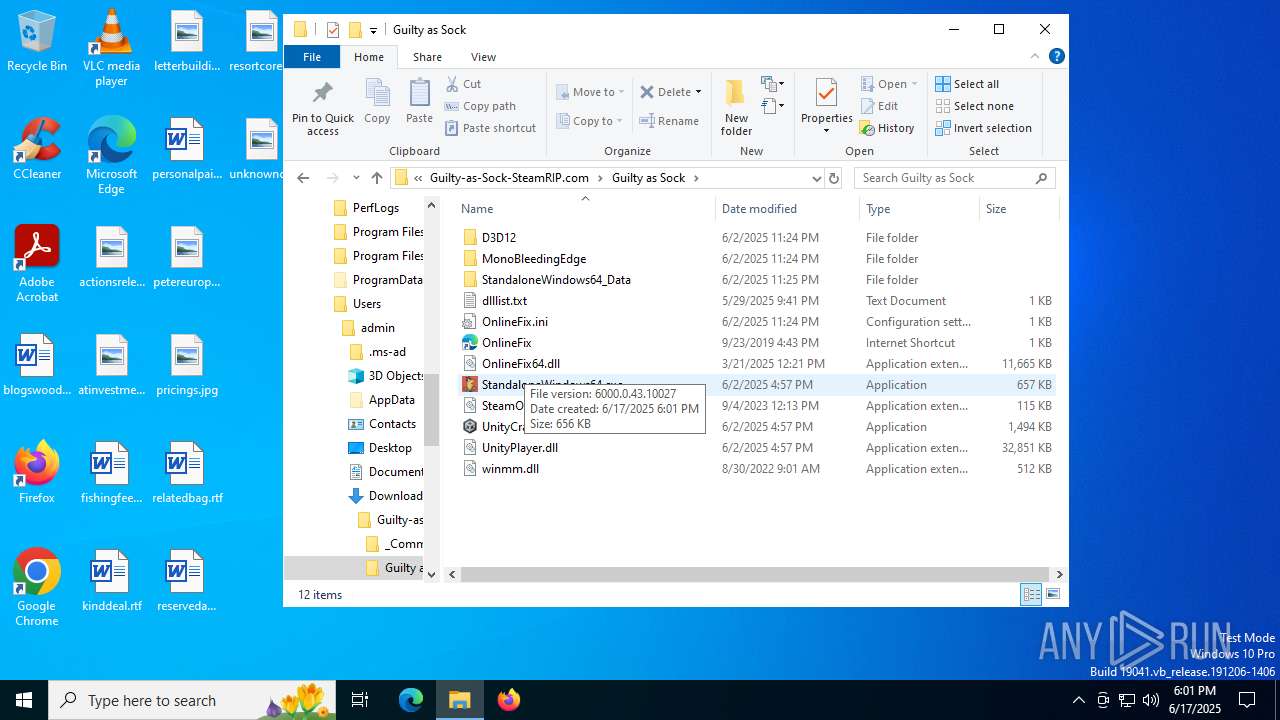
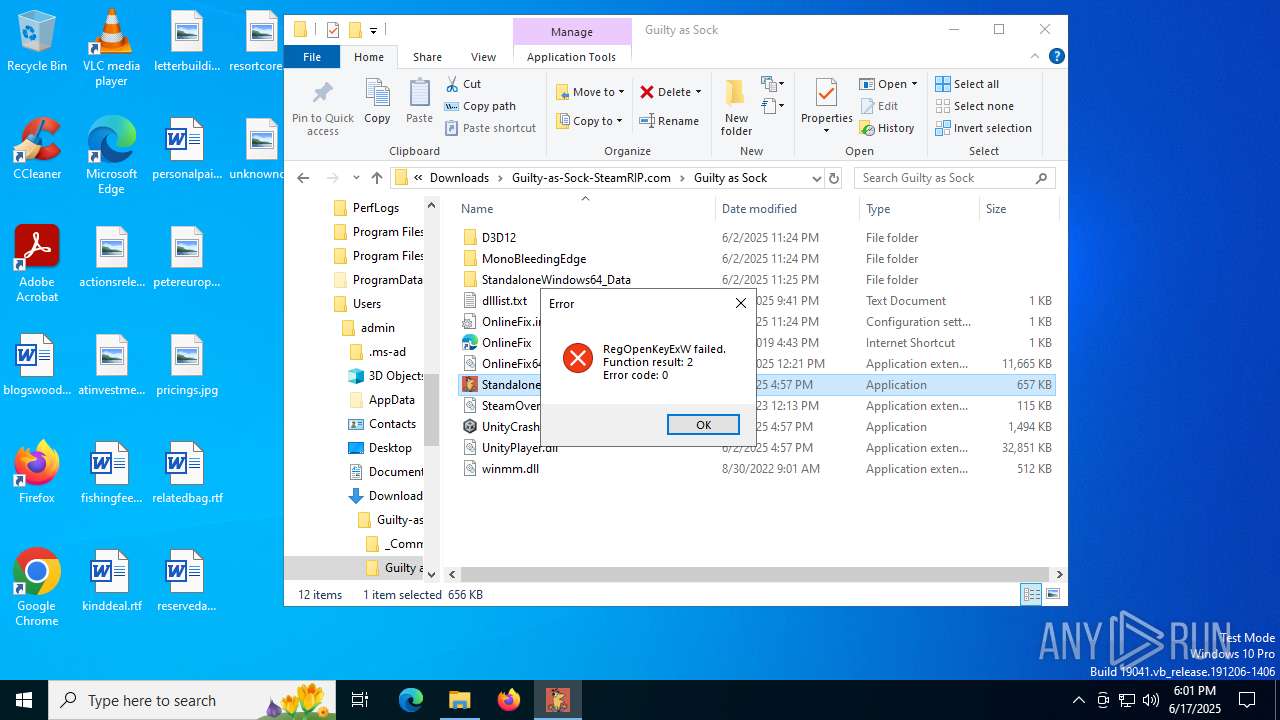
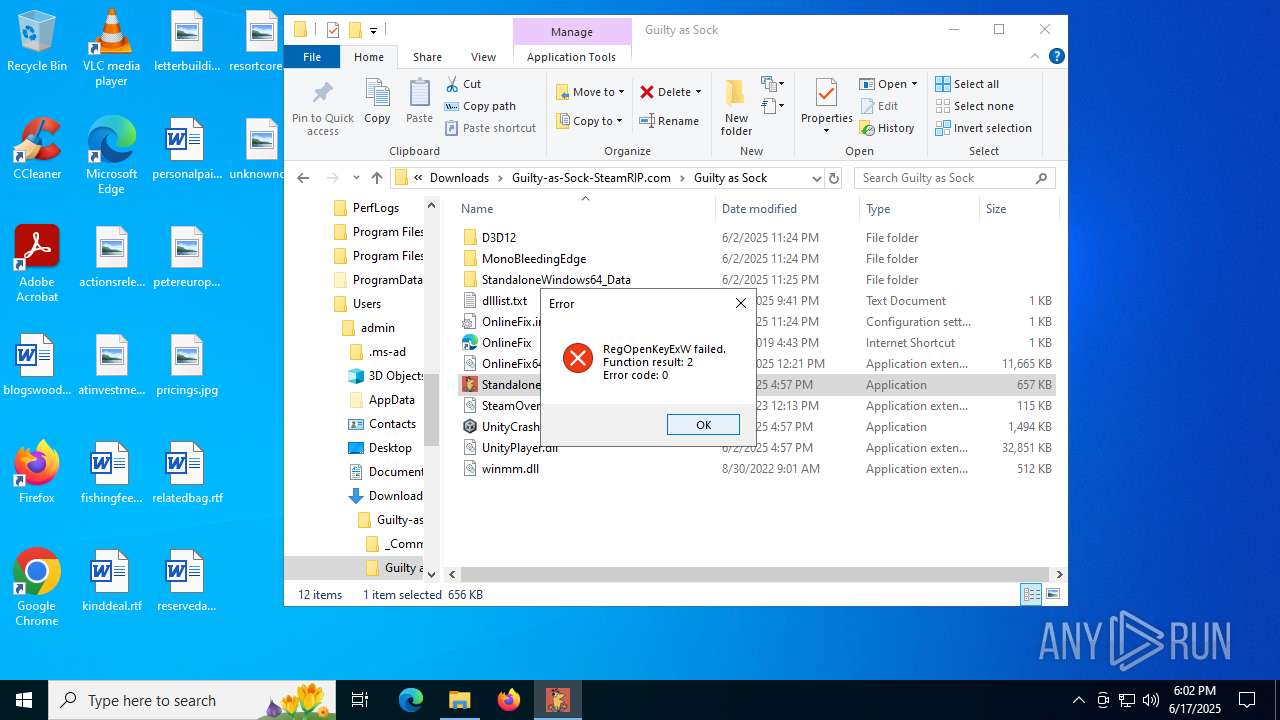
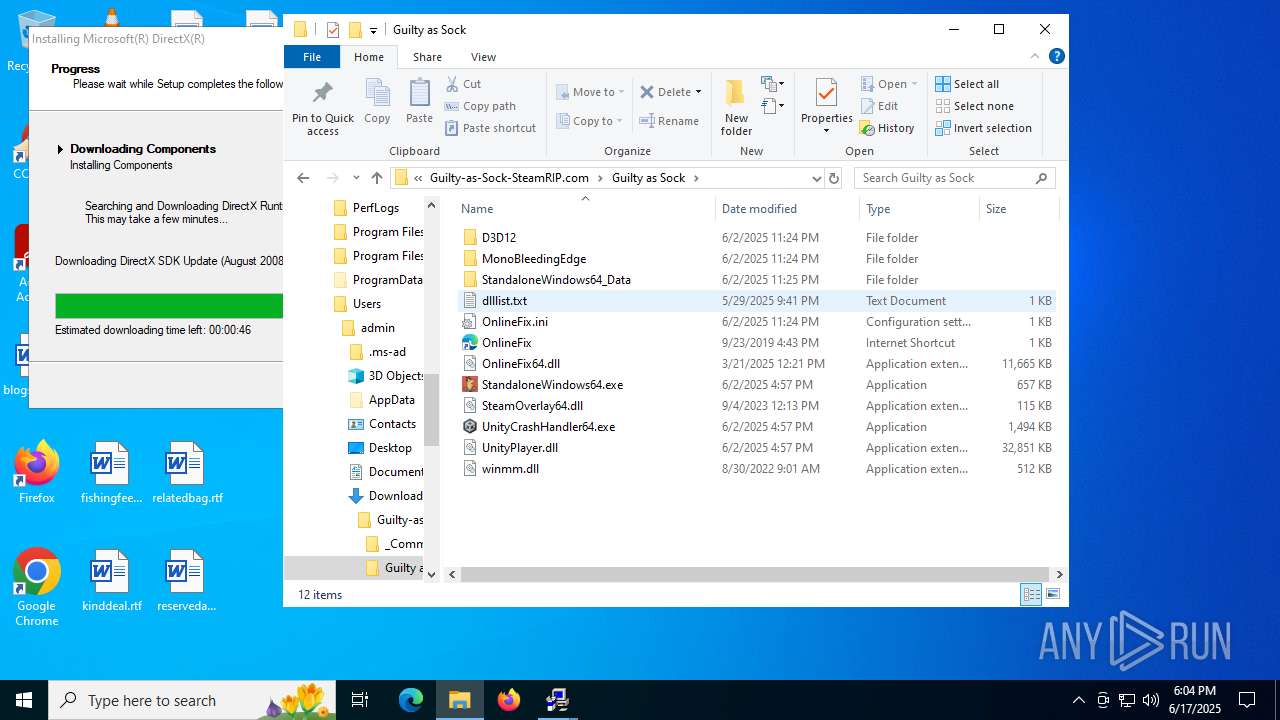
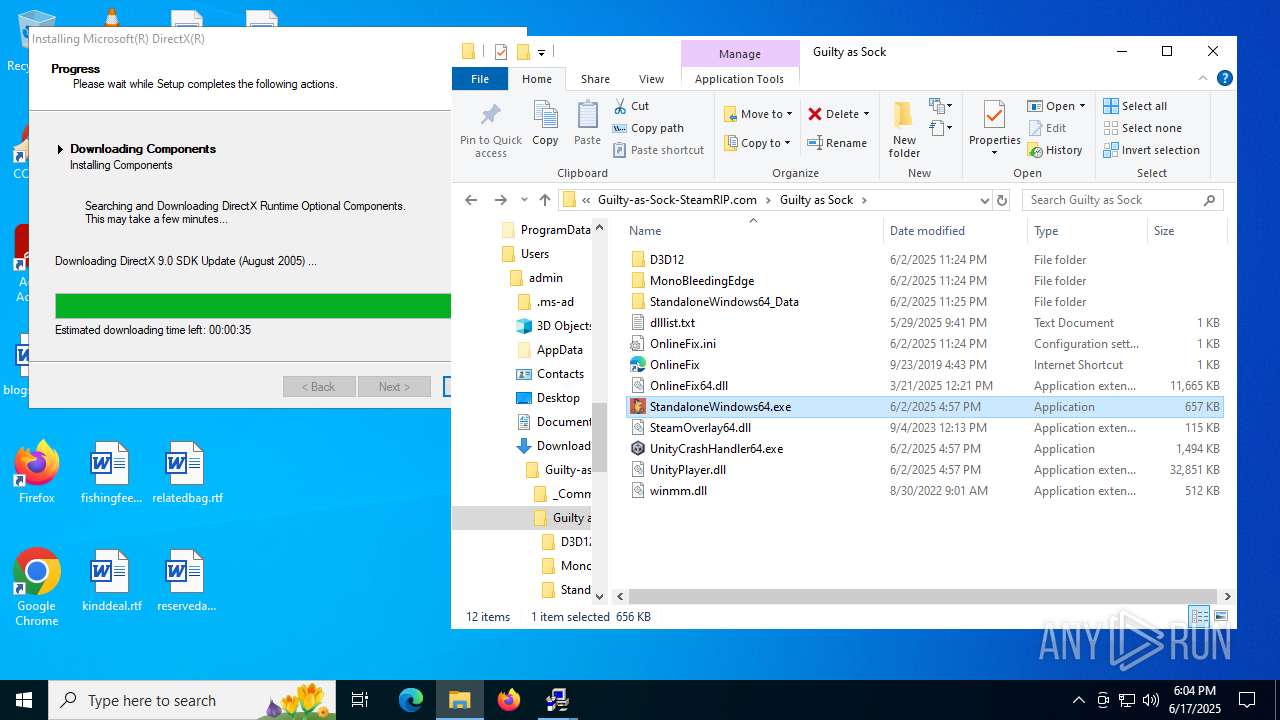
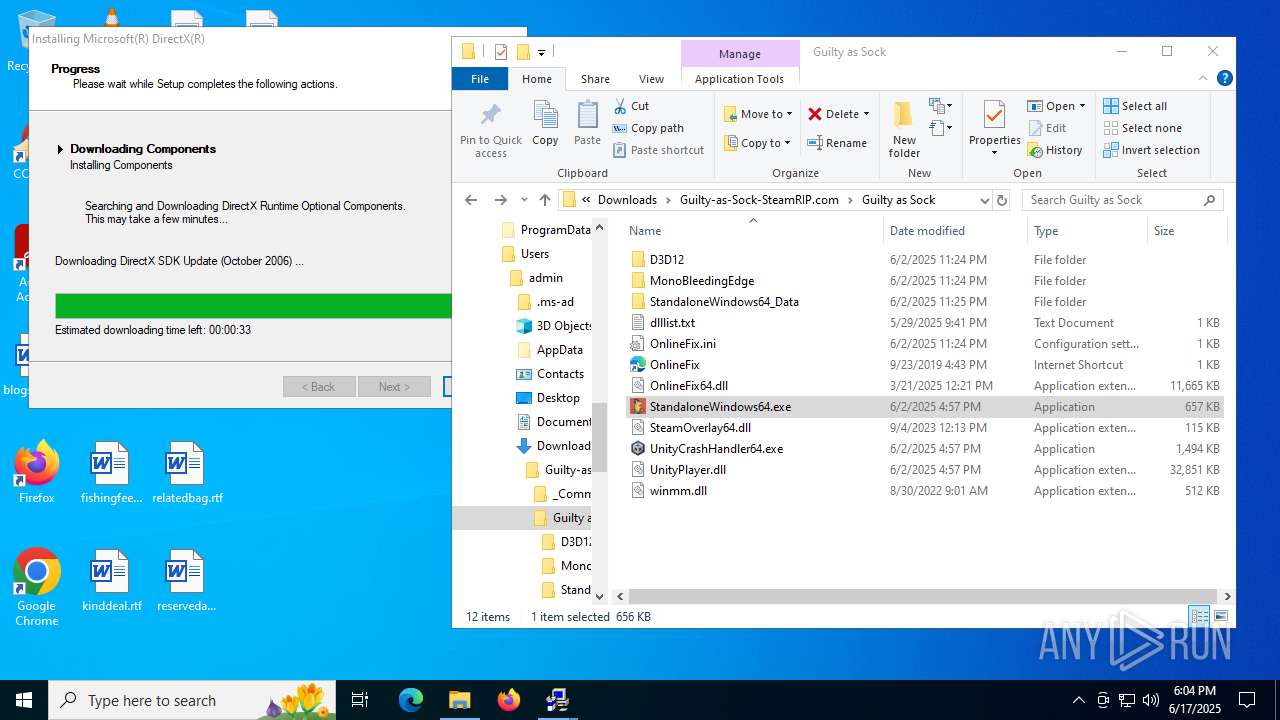
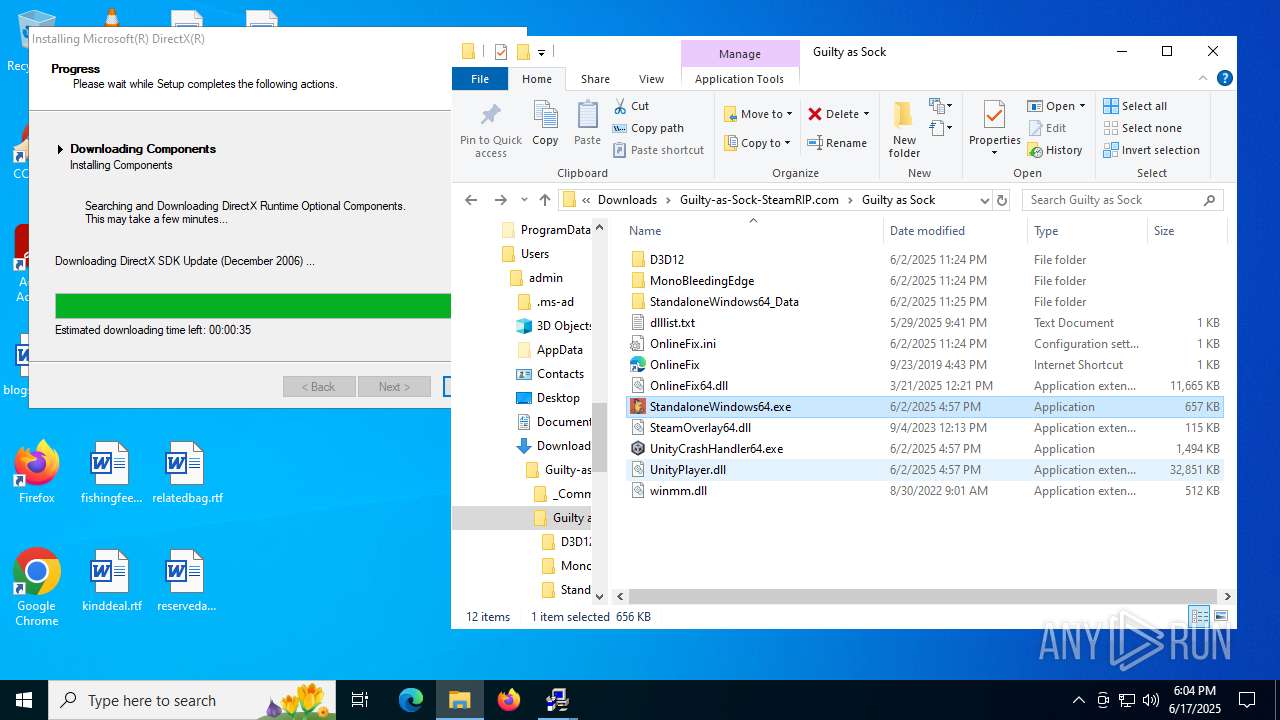
- StandaloneWindows64.exe (PID: 7412)
- msiexec.exe (PID: 7540)
Reads Environment values
- identity_helper.exe (PID: 7960)
- identity_helper.exe (PID: 7240)
Executable content was dropped or overwritten
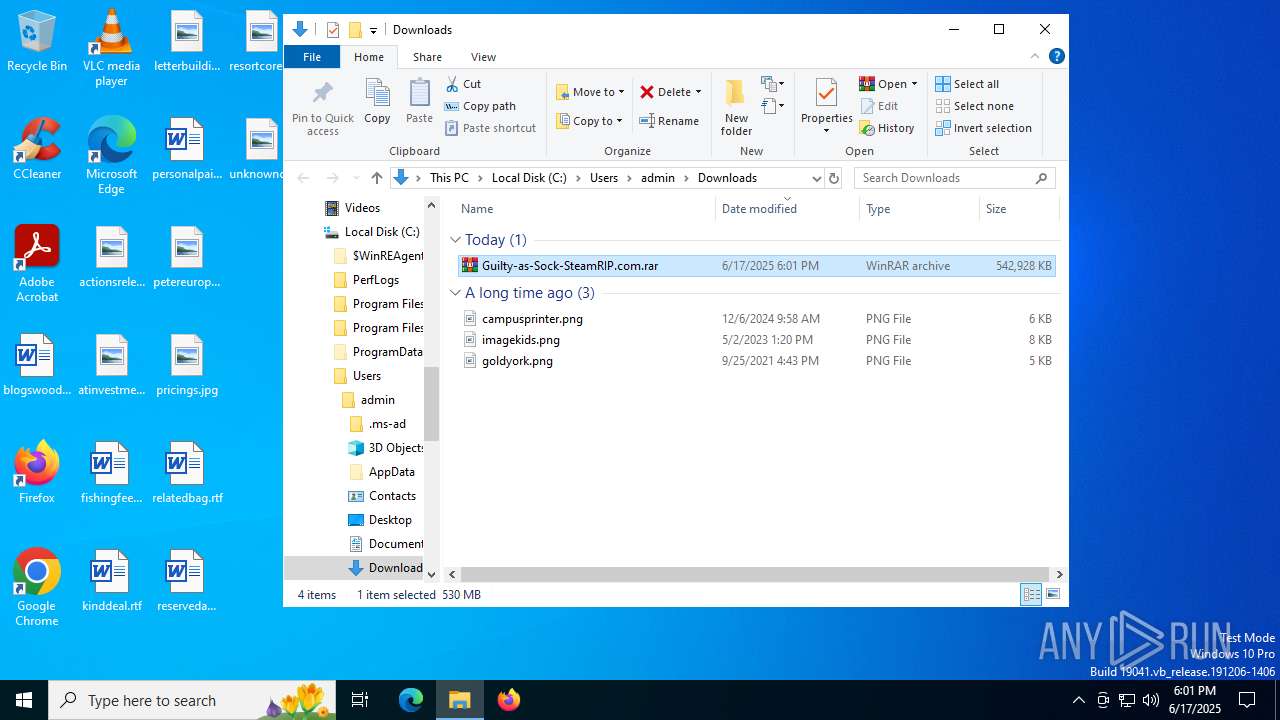
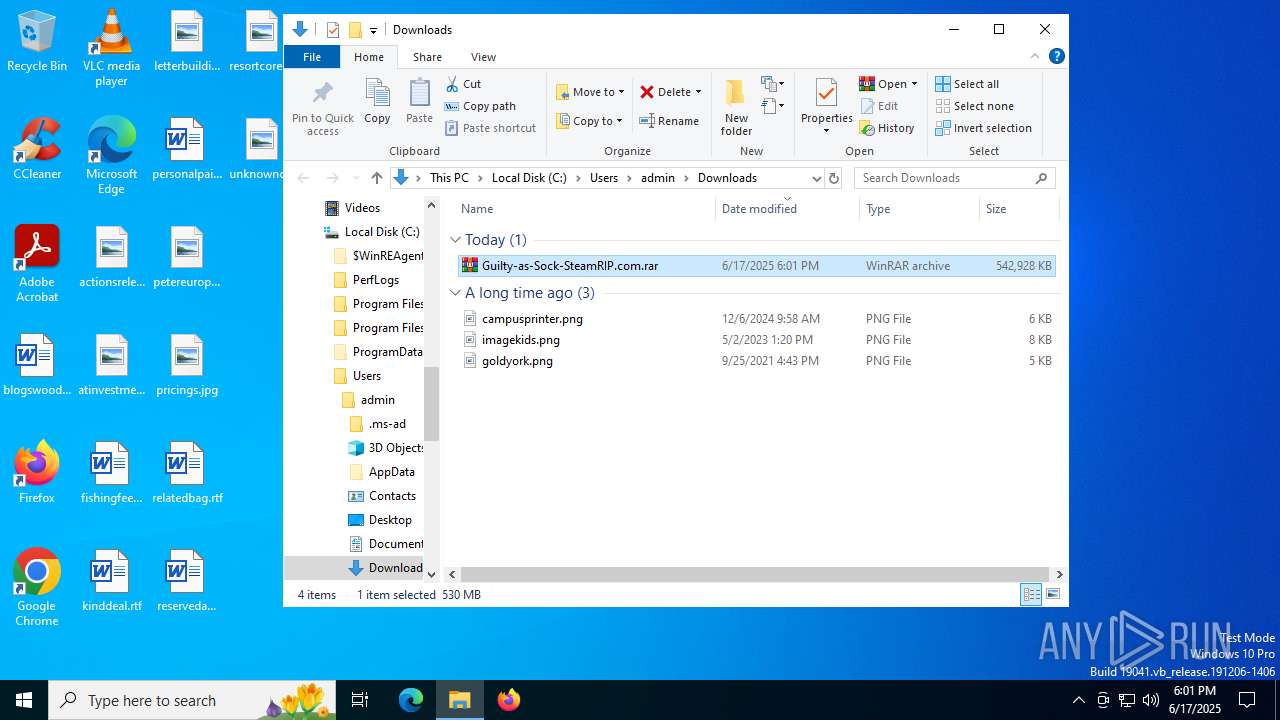
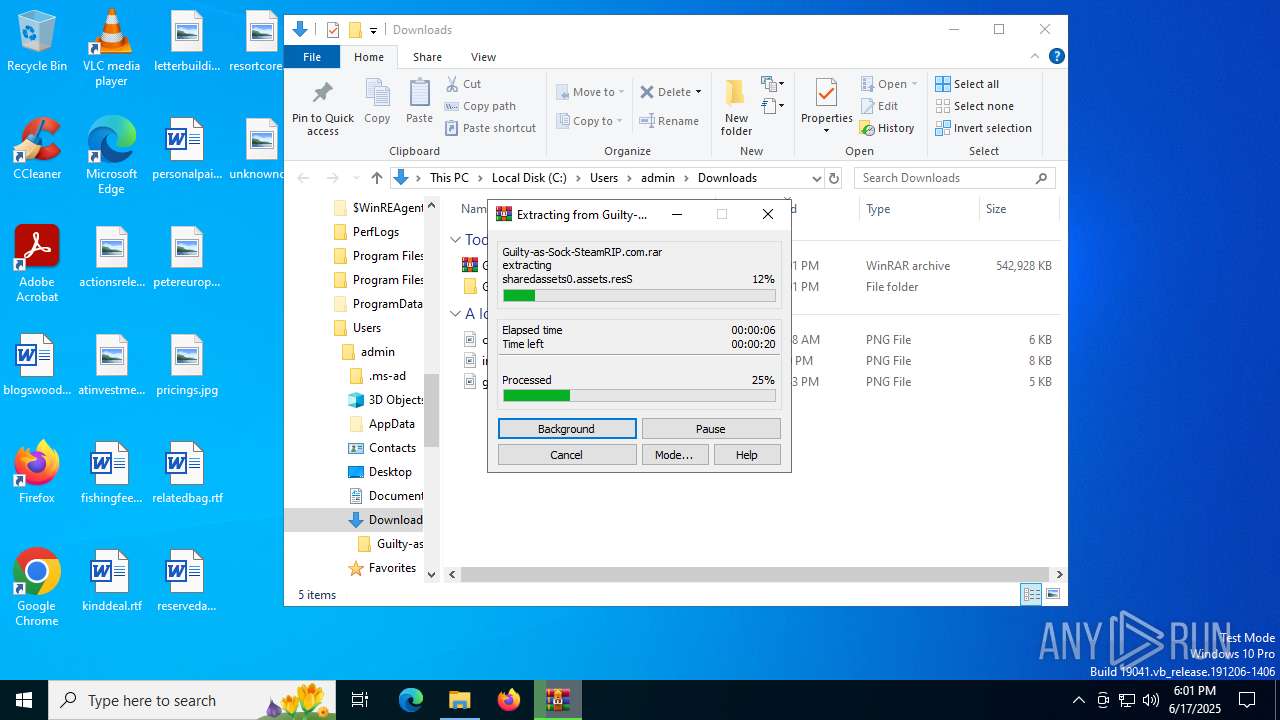
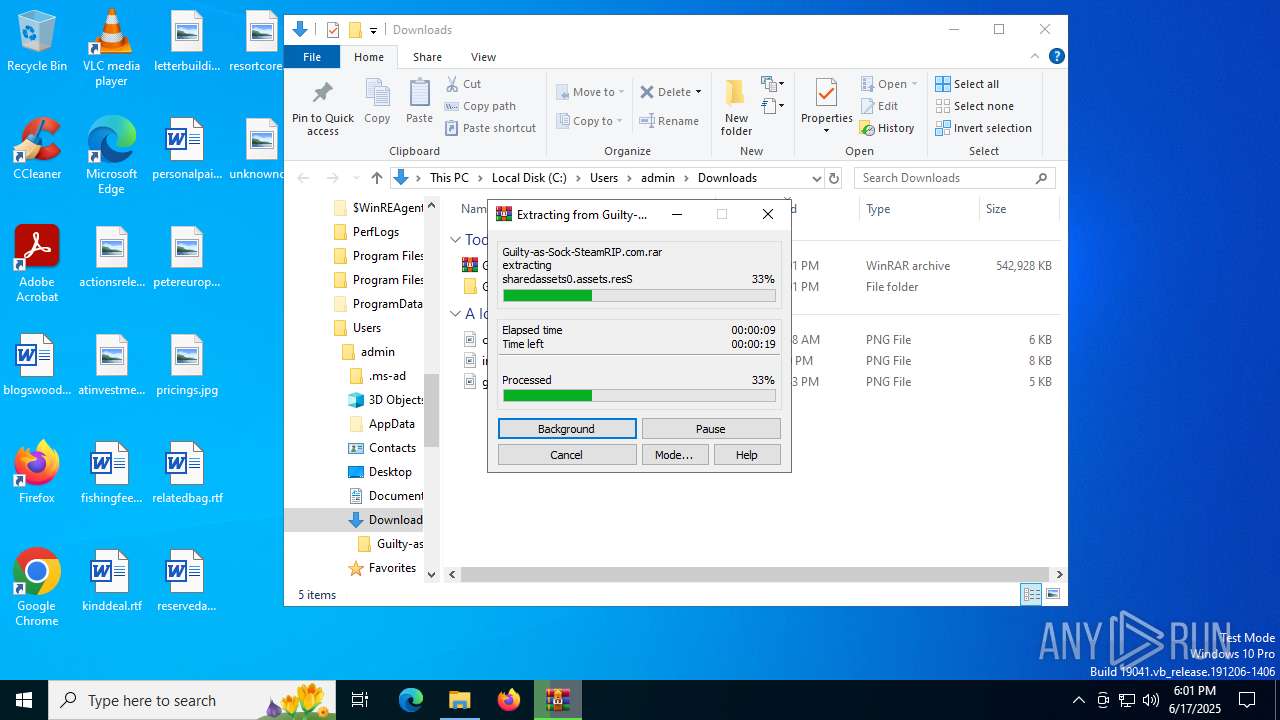
- WinRAR.exe (PID: 1728)
- msiexec.exe (PID: 7540)
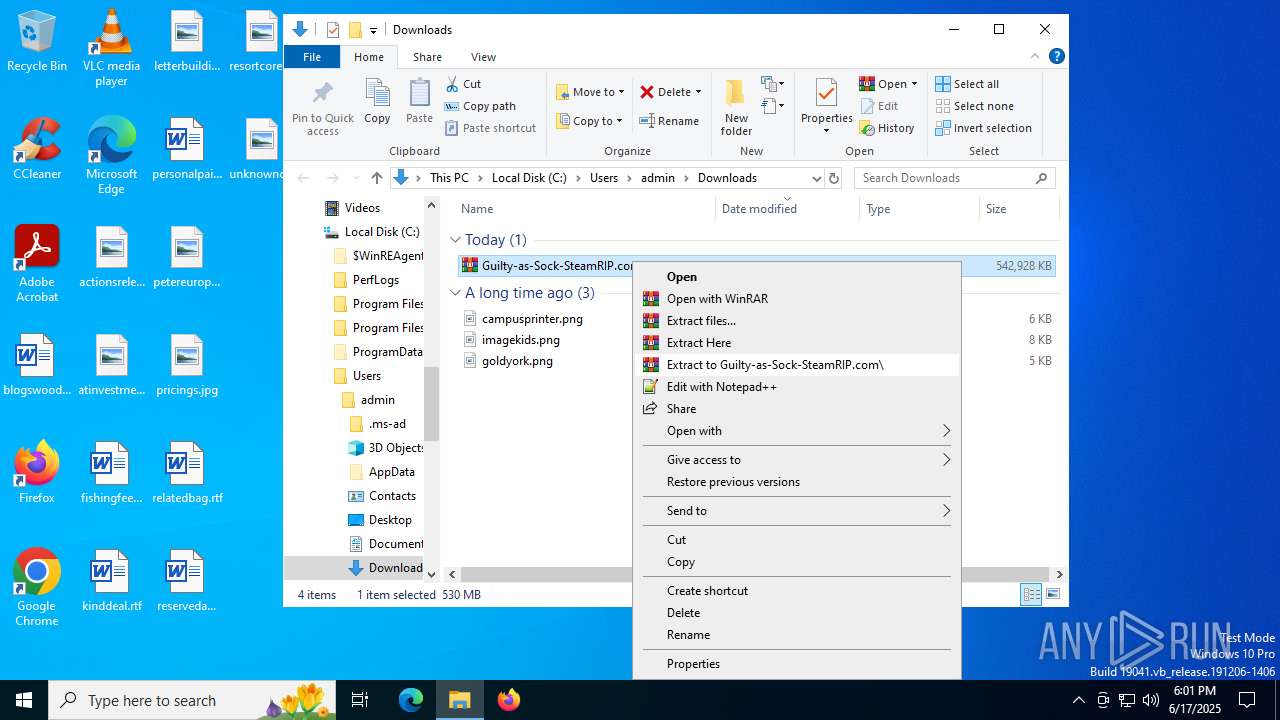
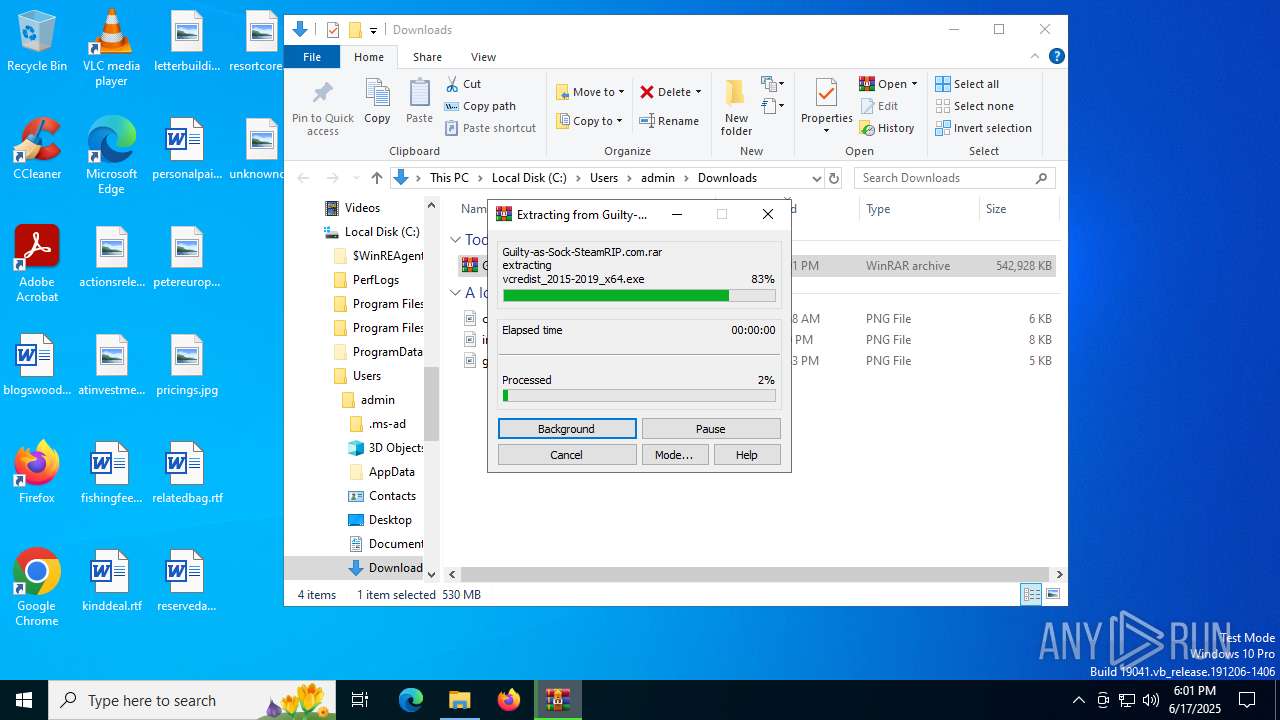
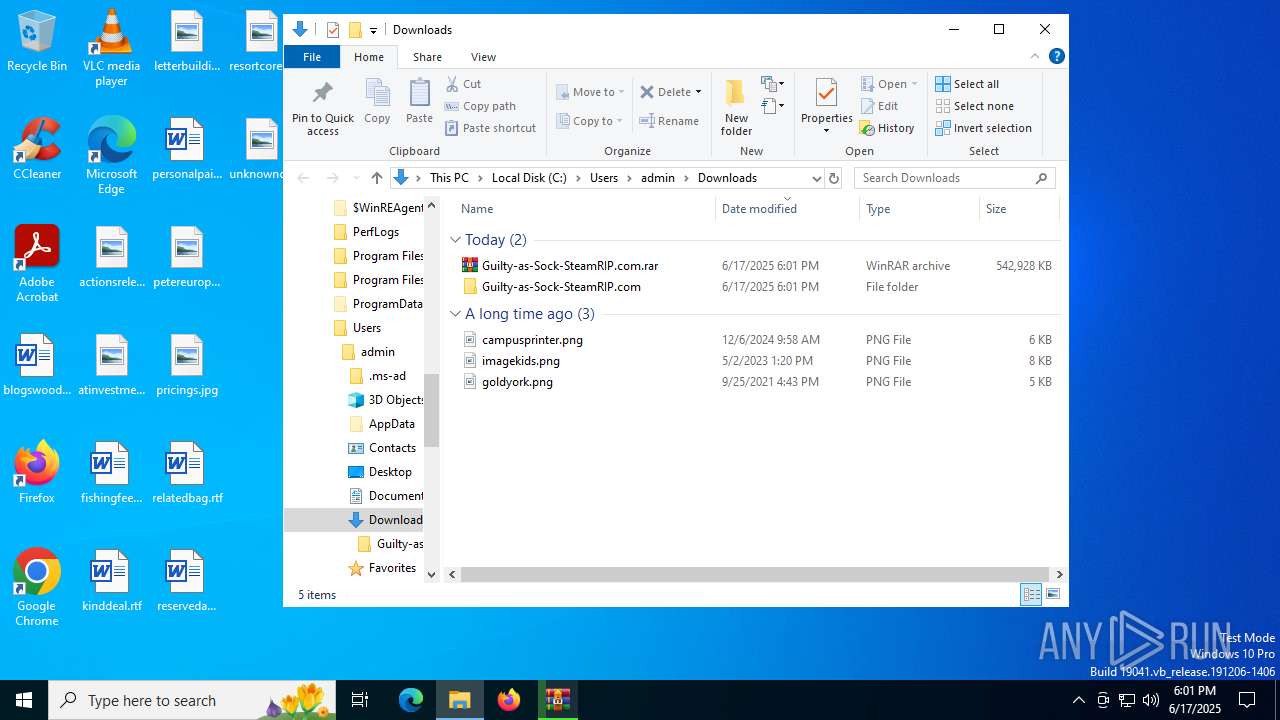
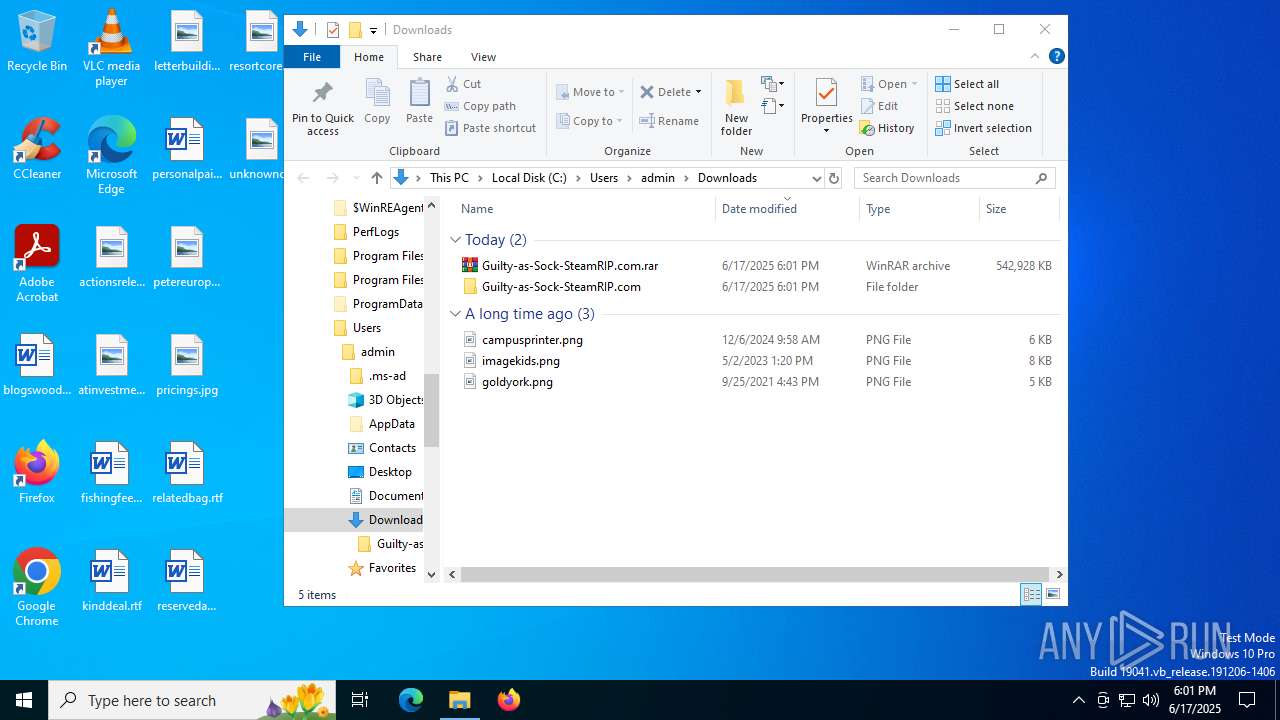
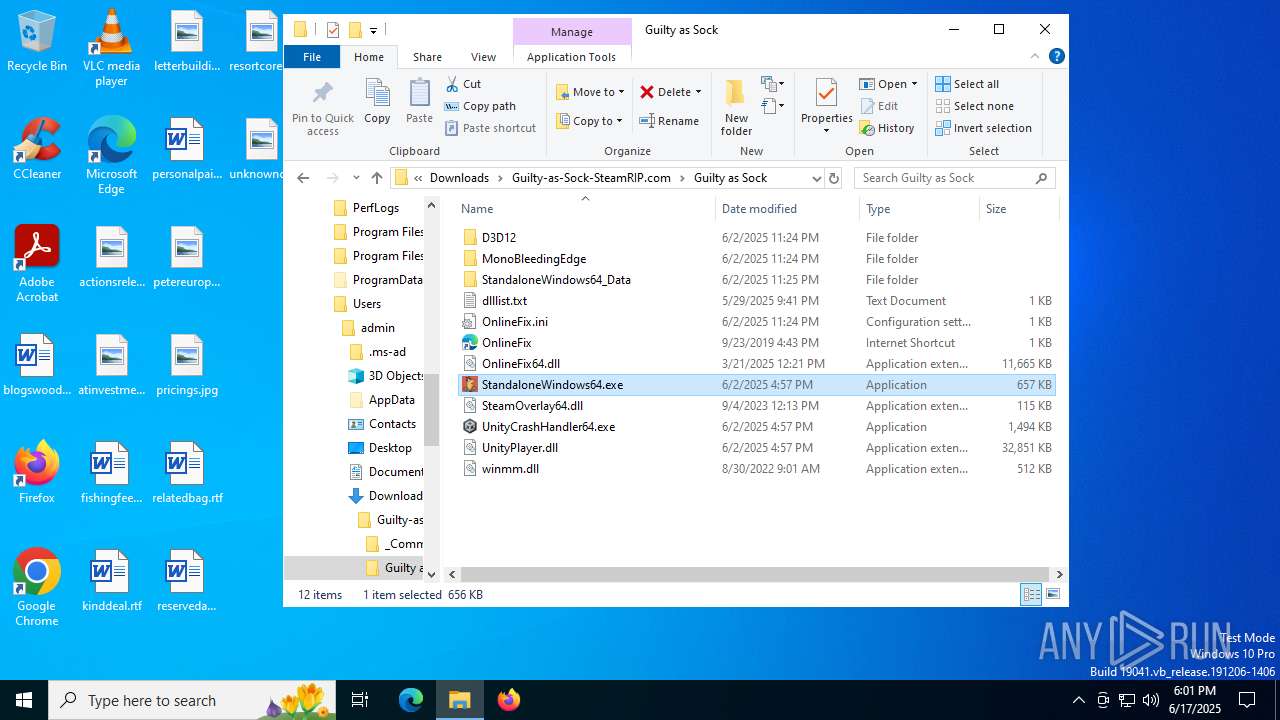
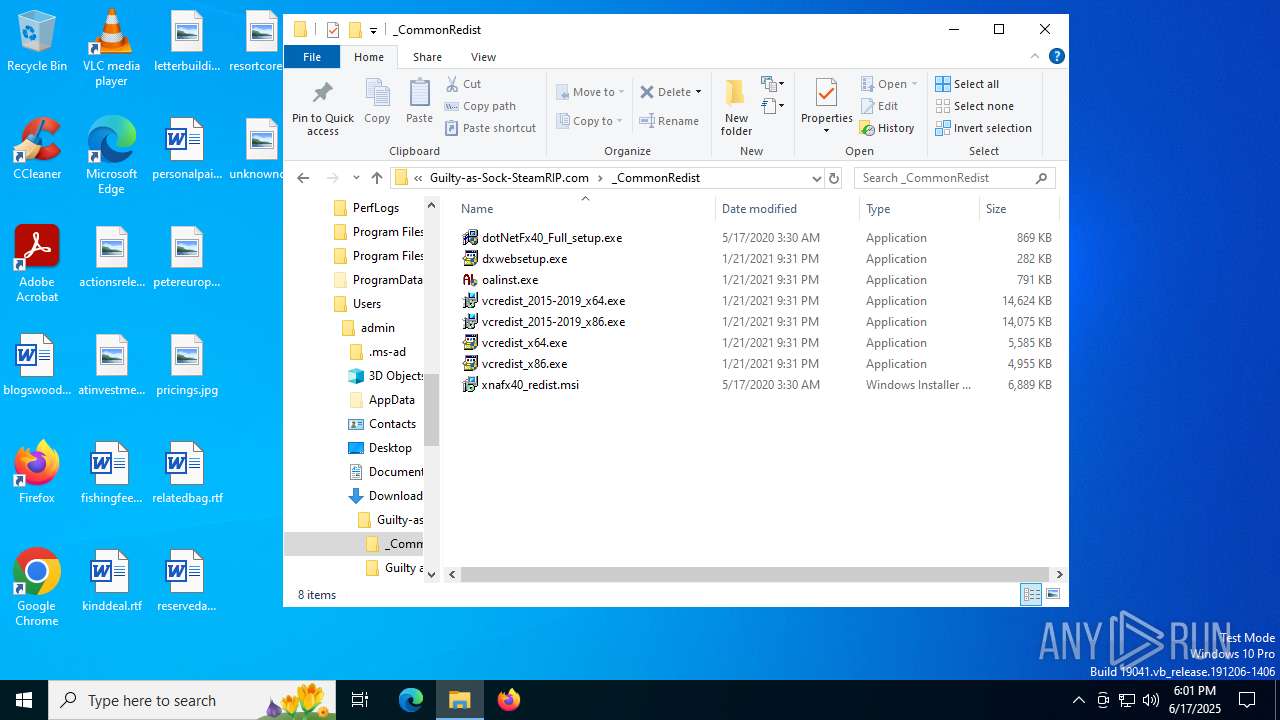
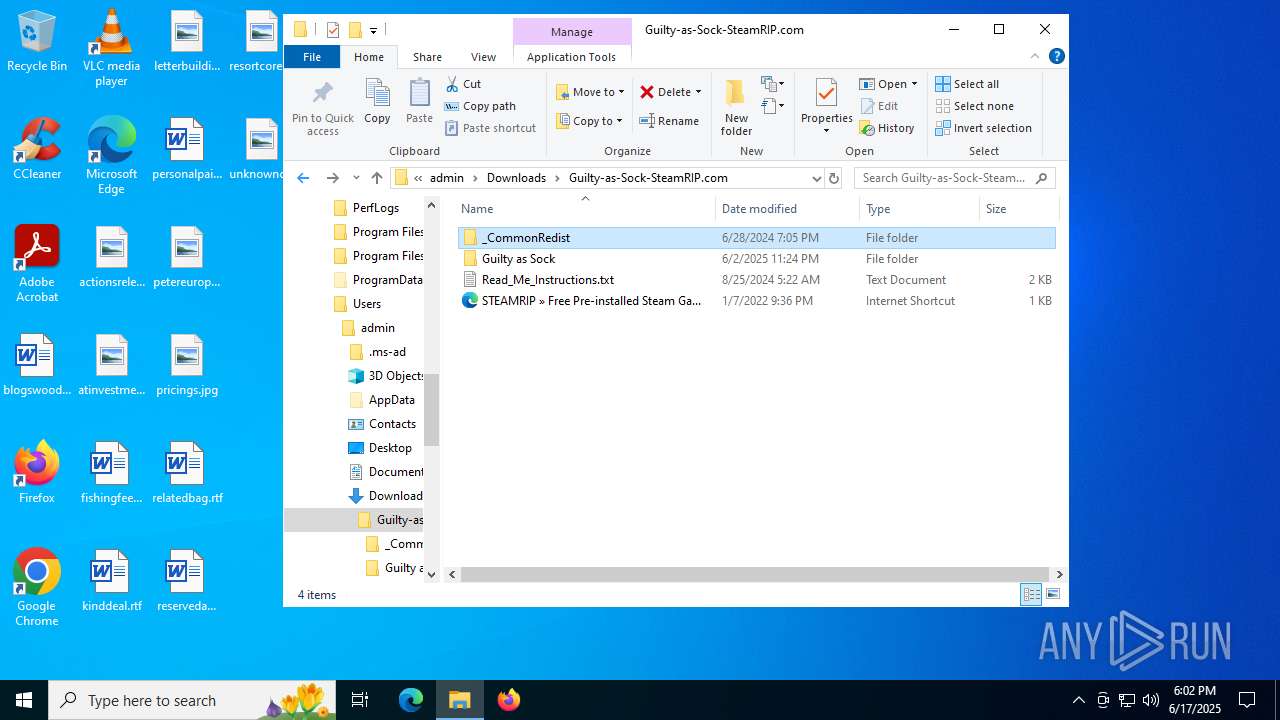
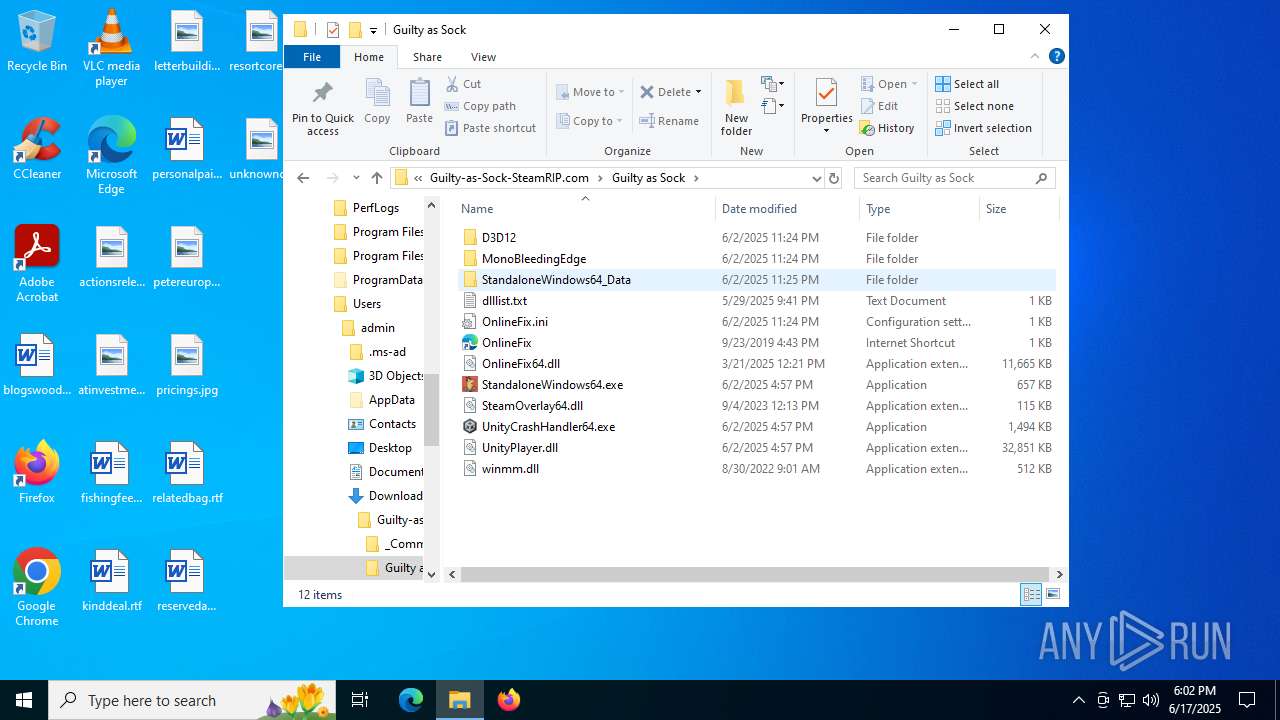
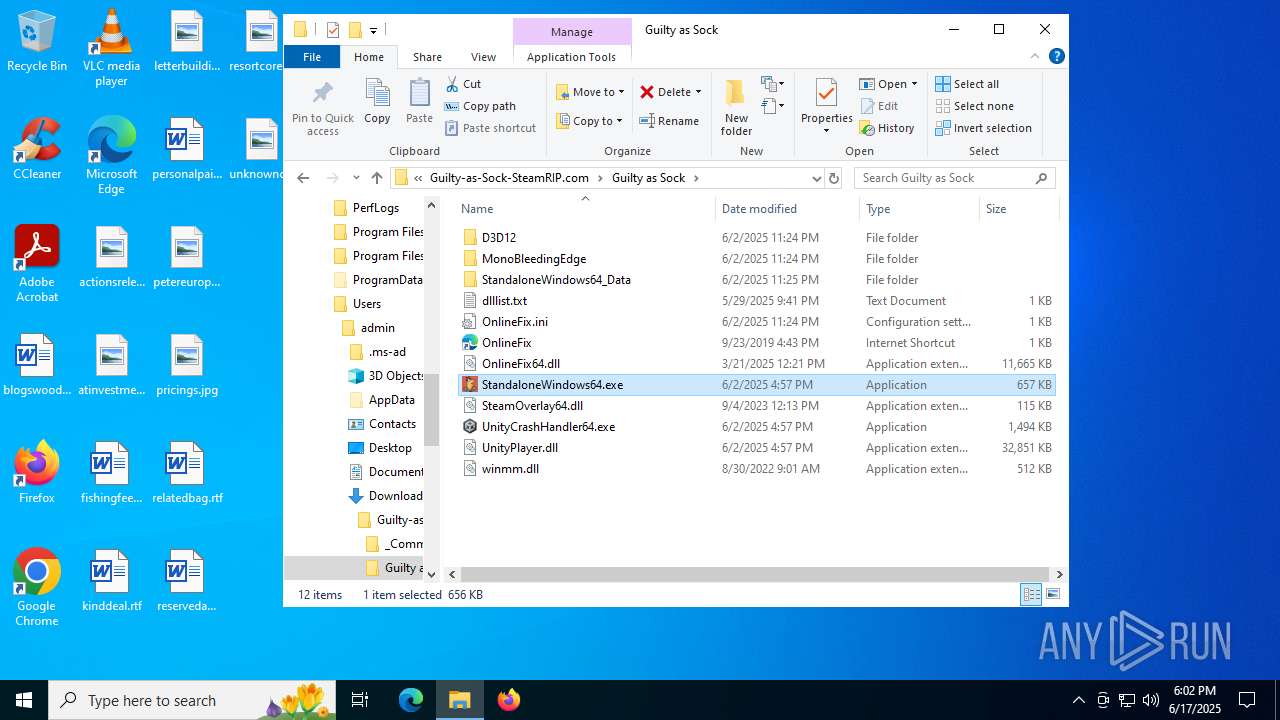
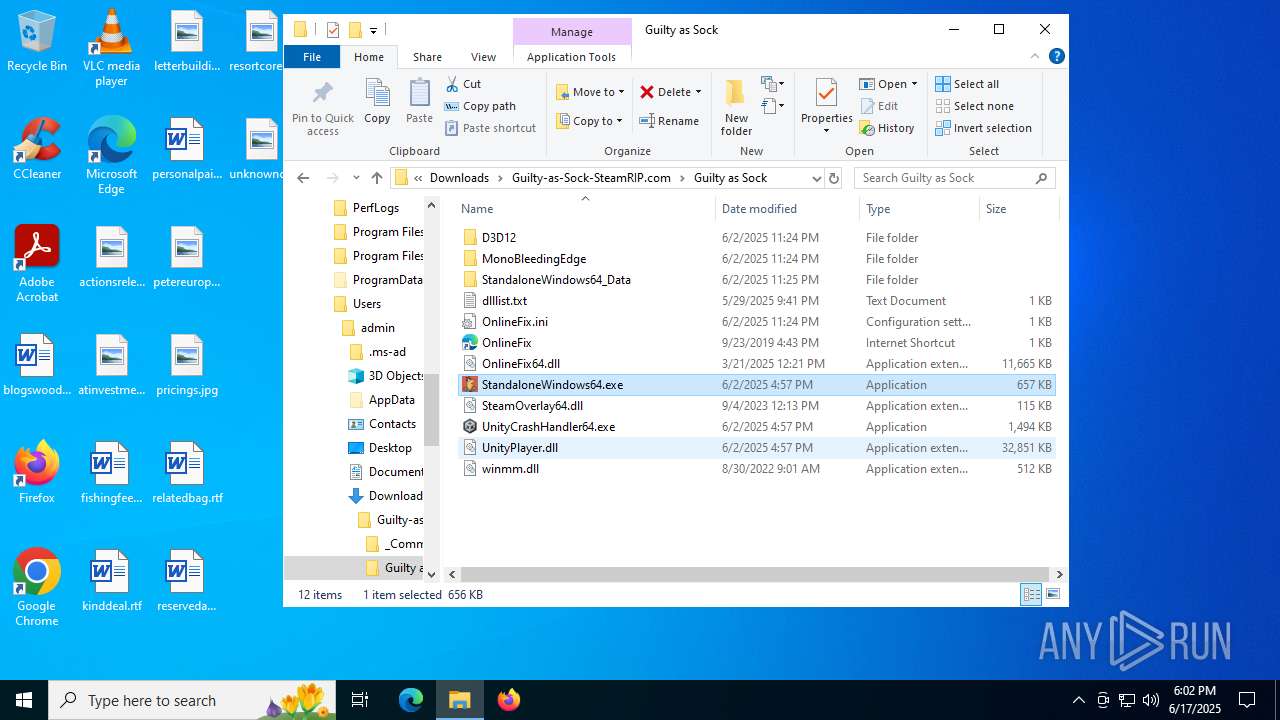
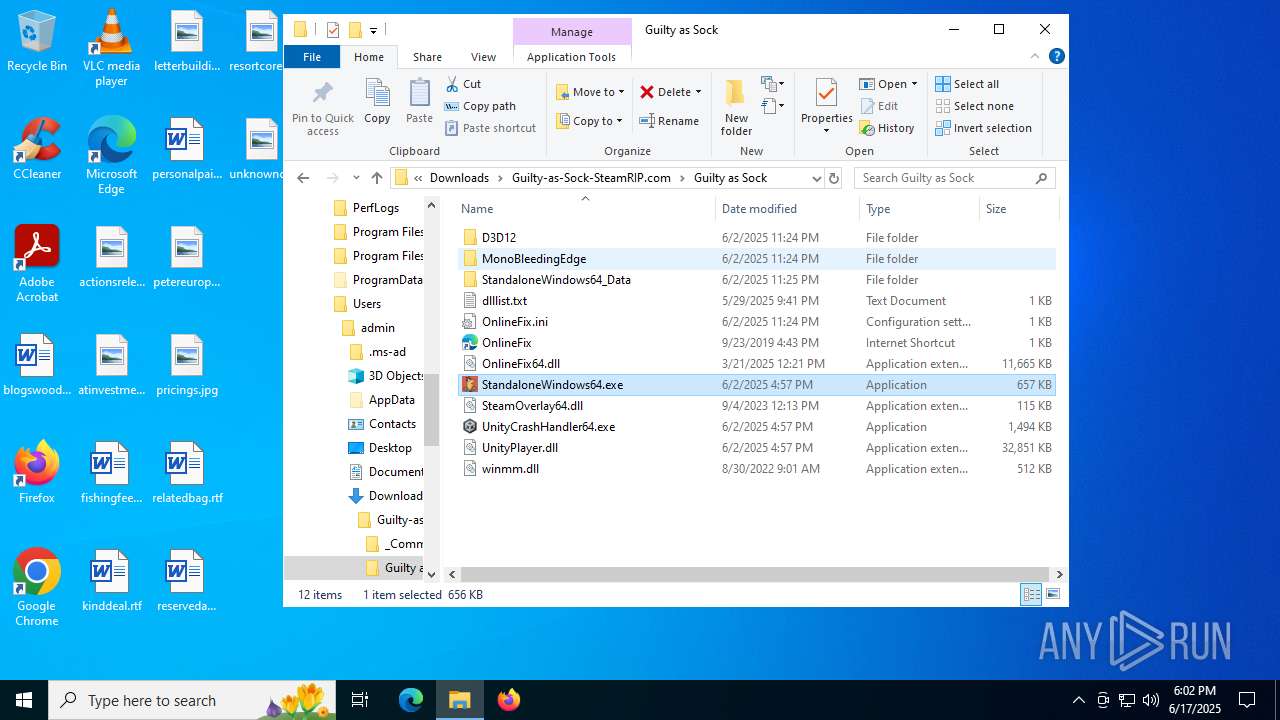
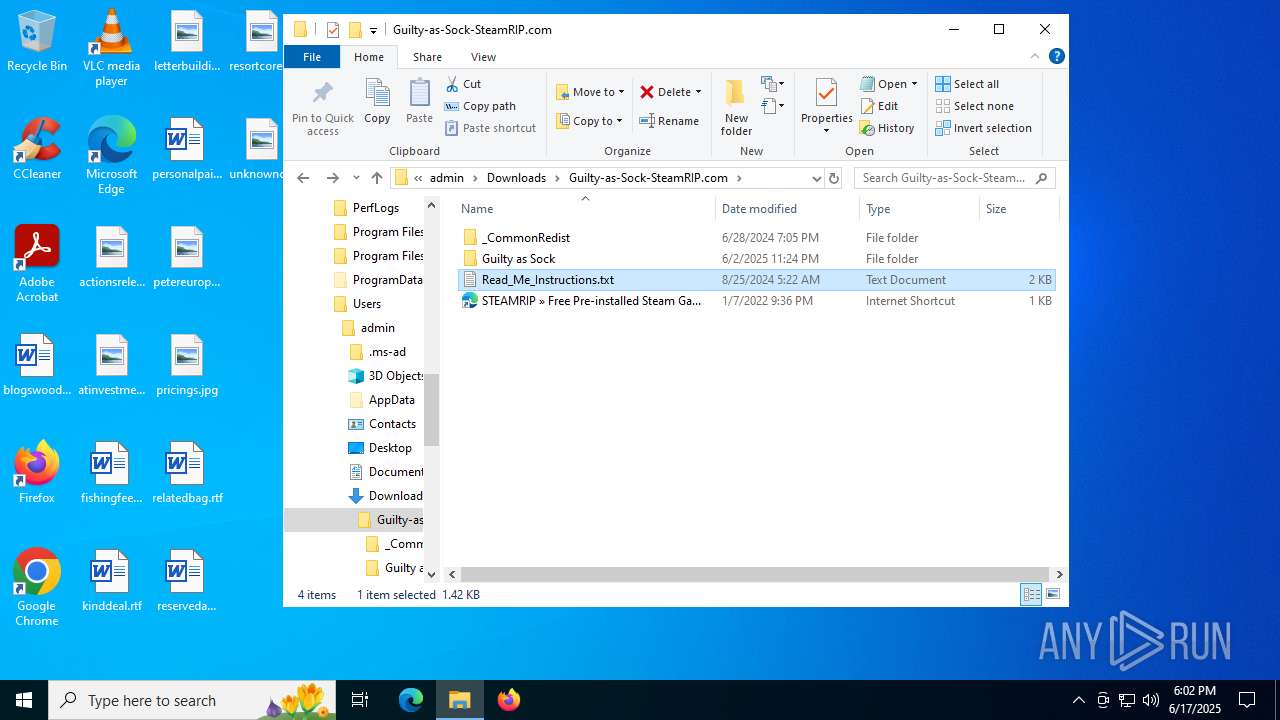
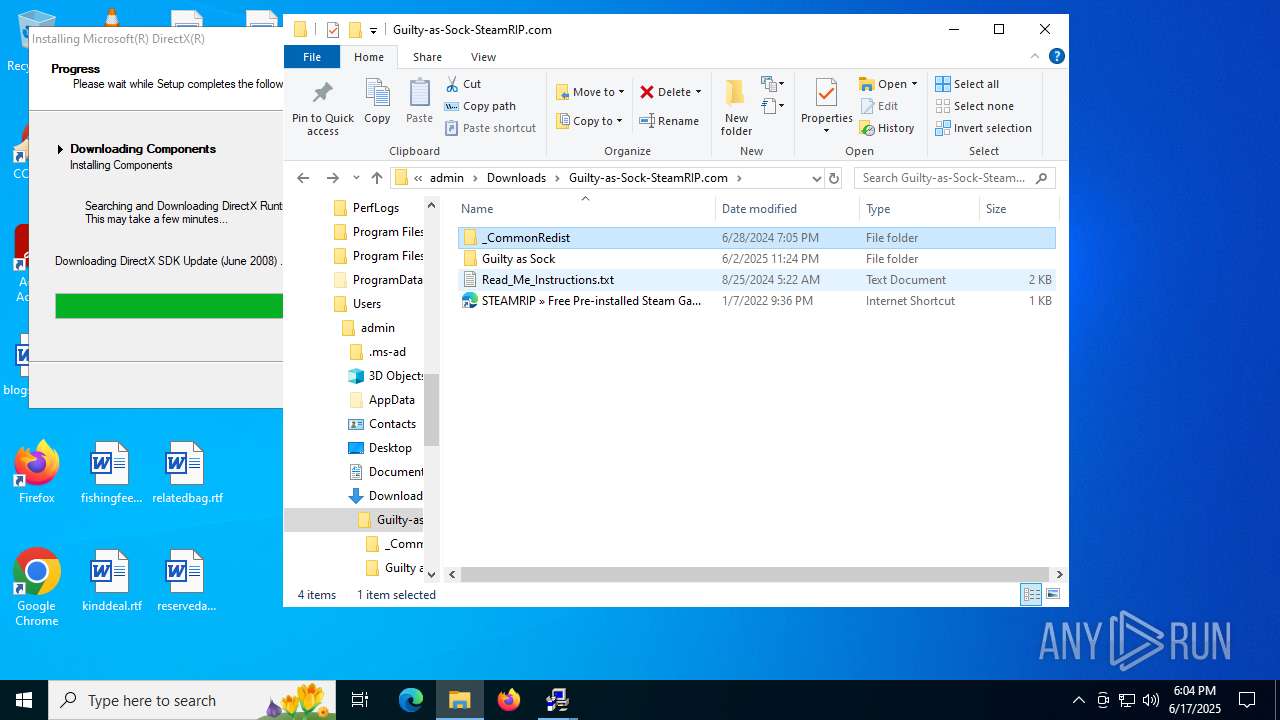
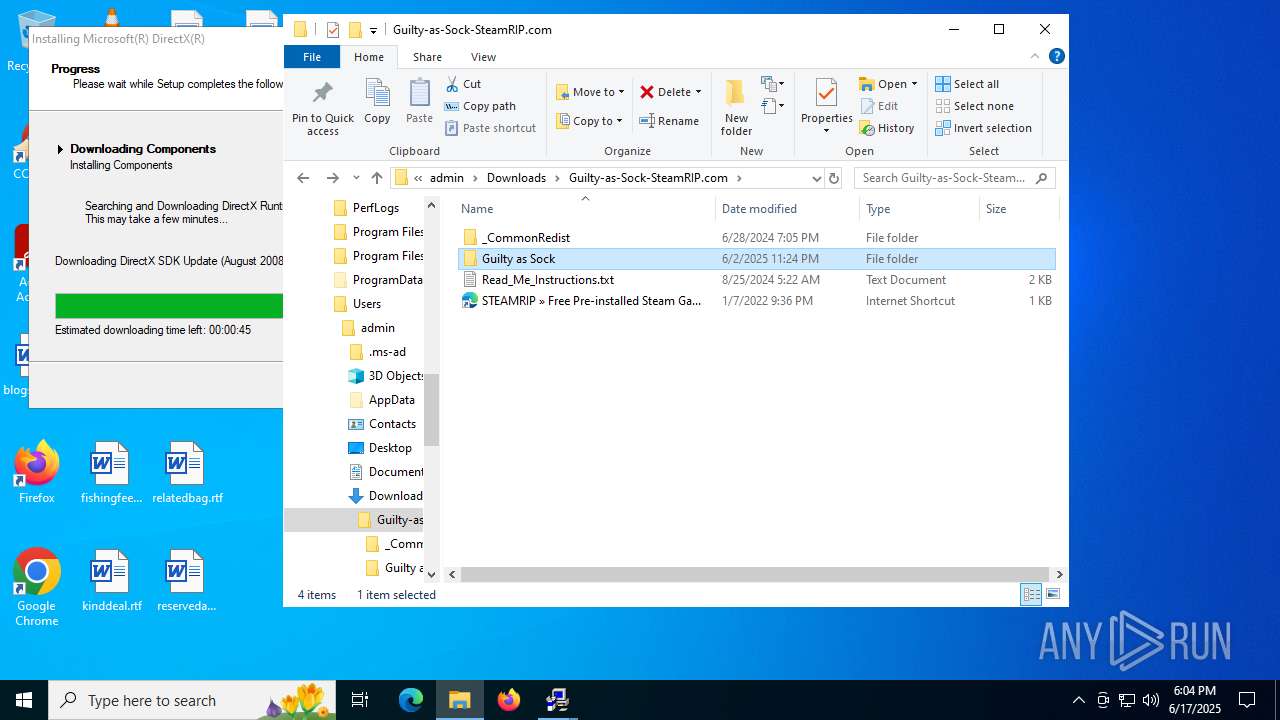
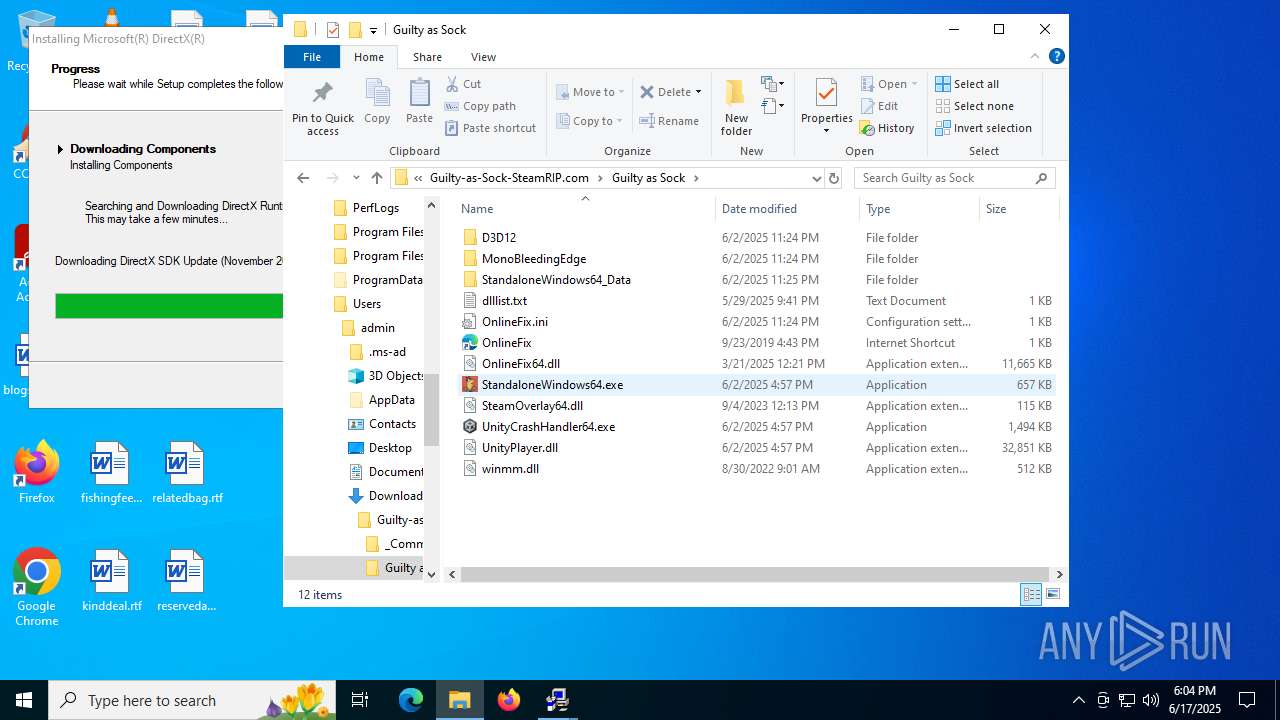
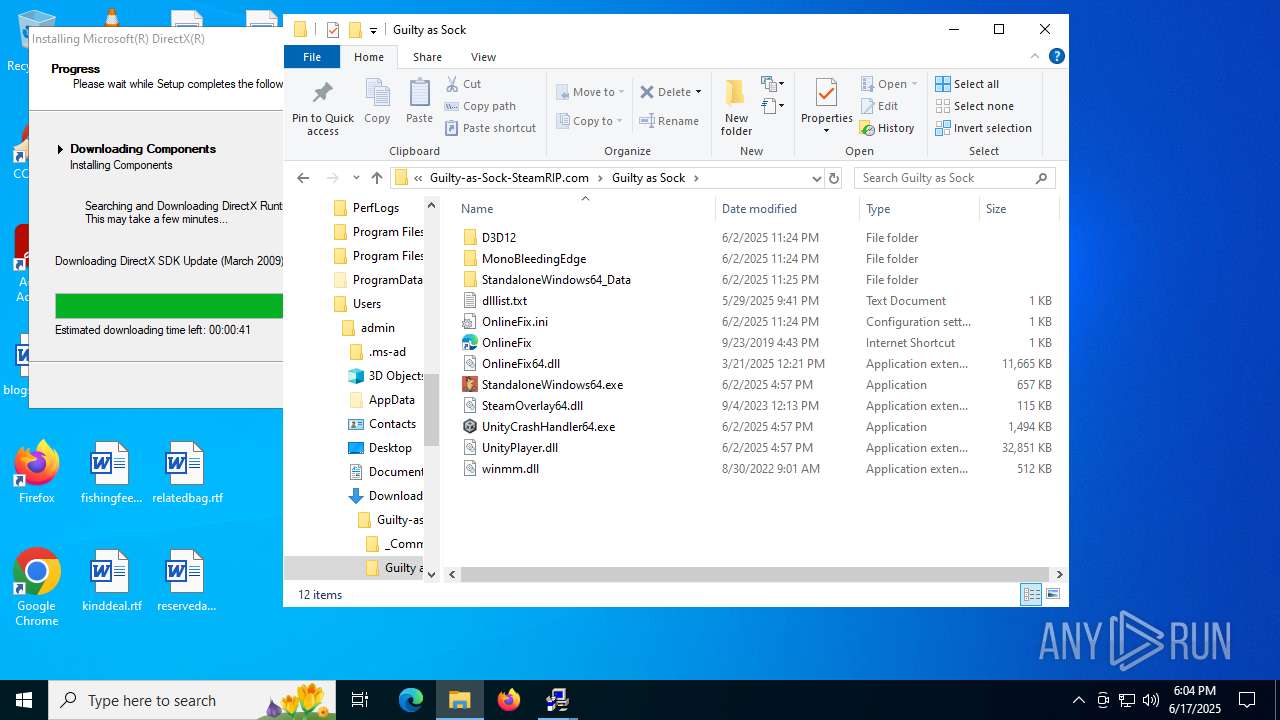
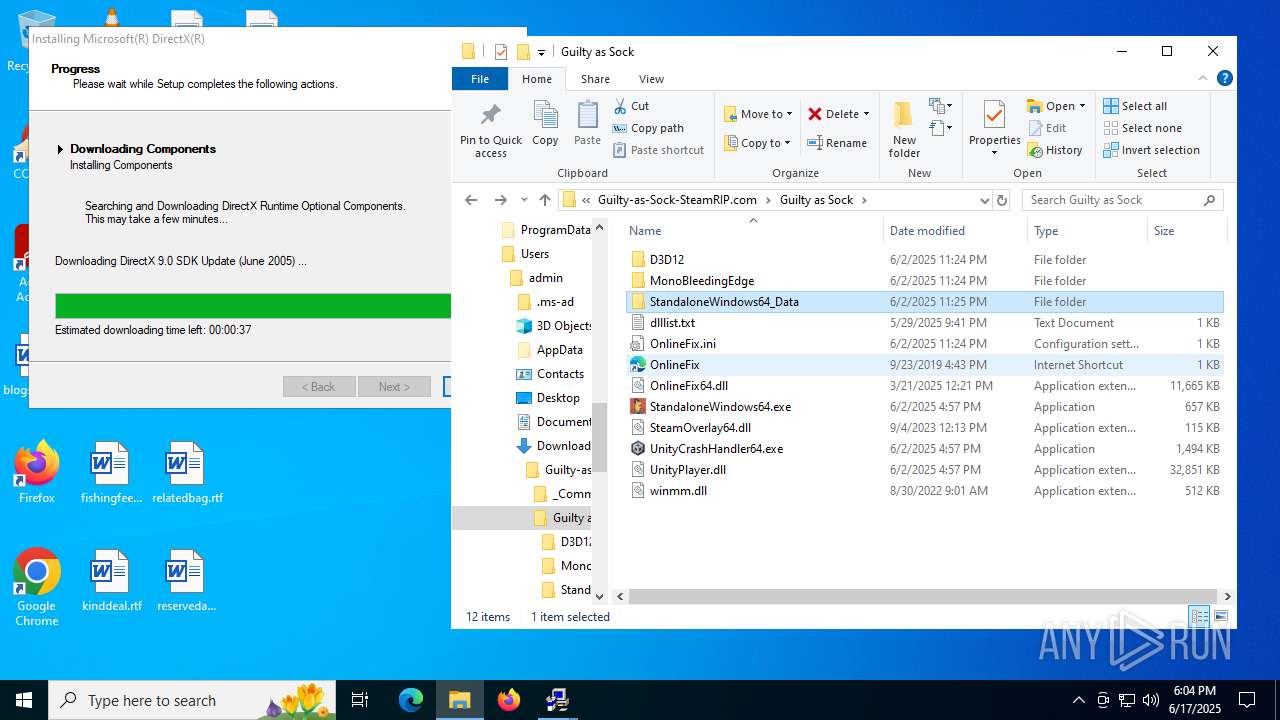
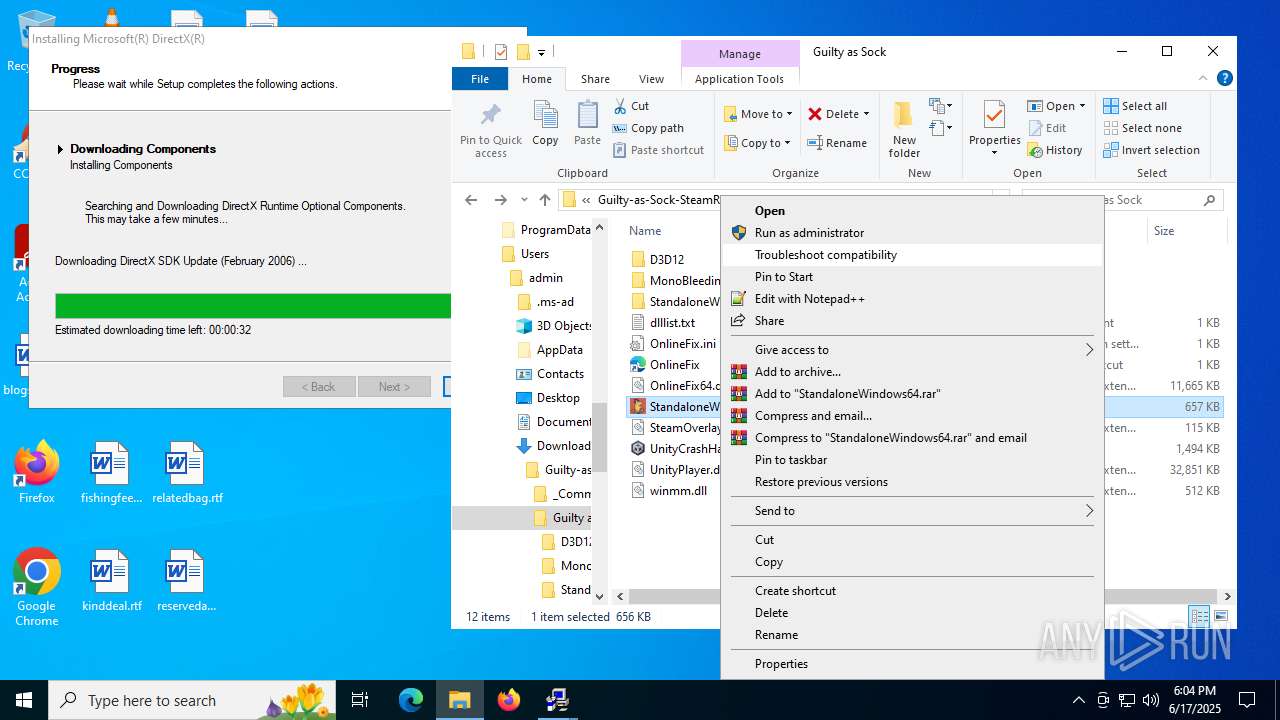
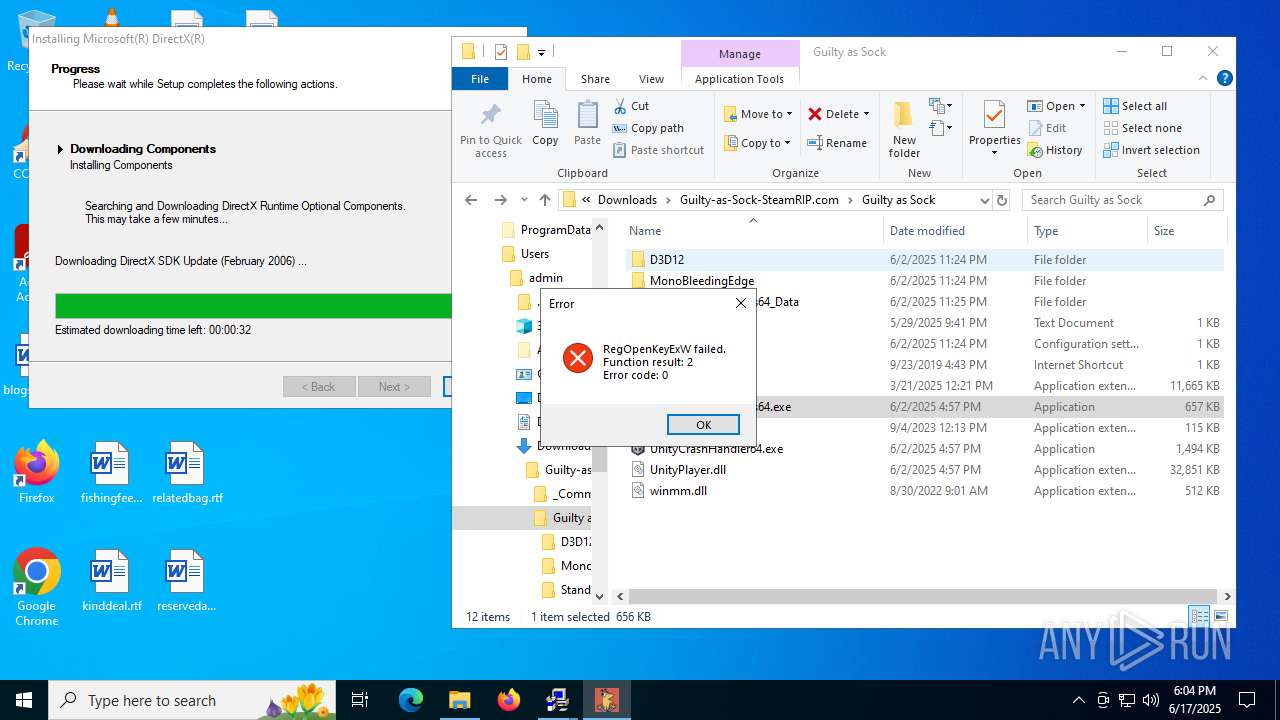
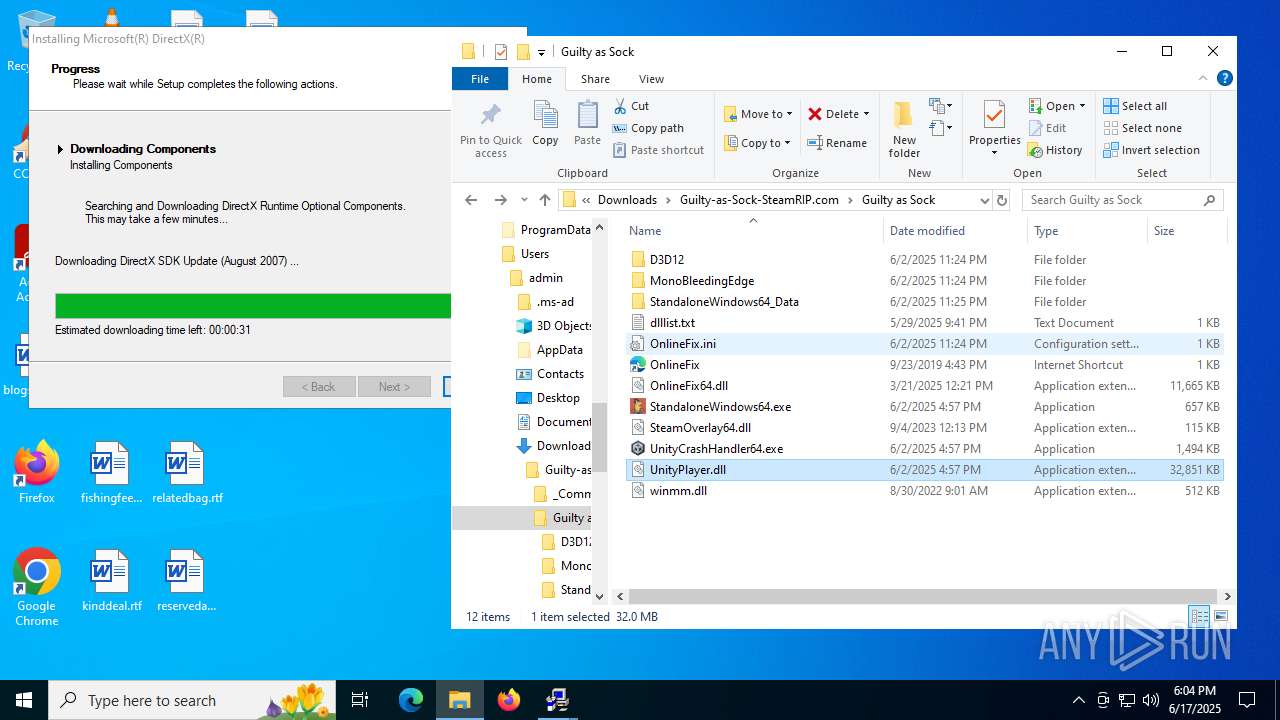
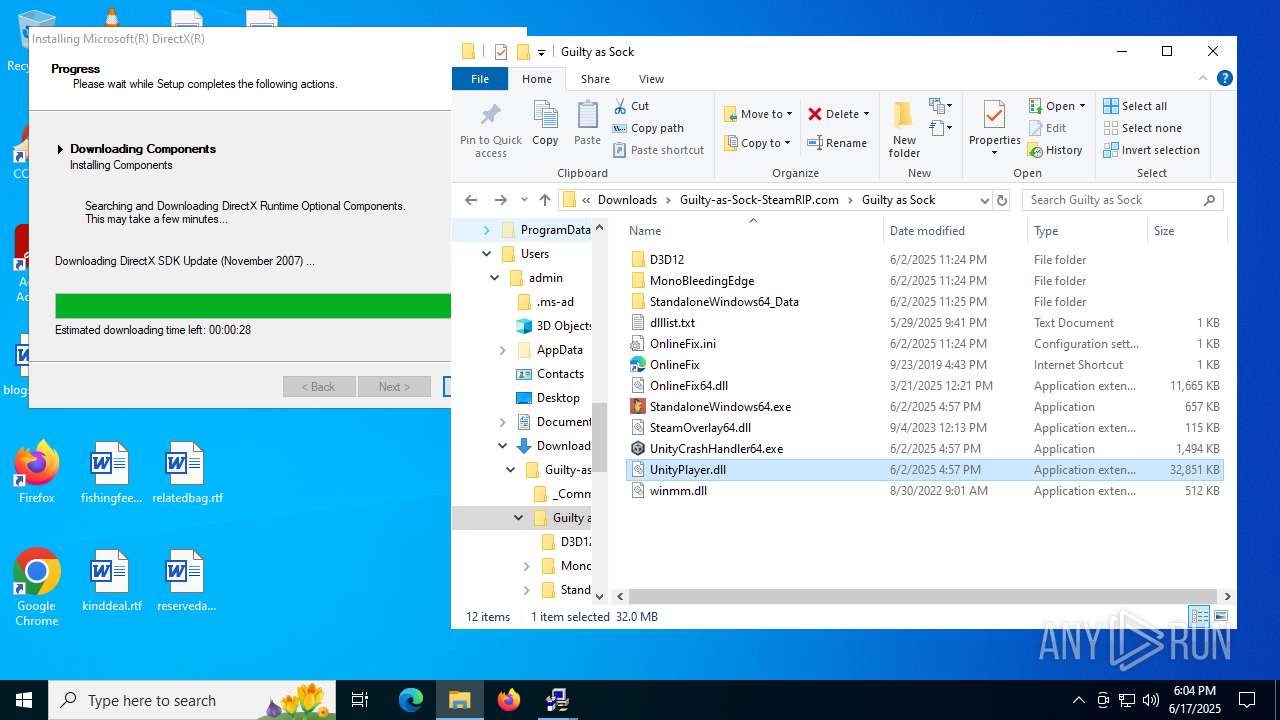
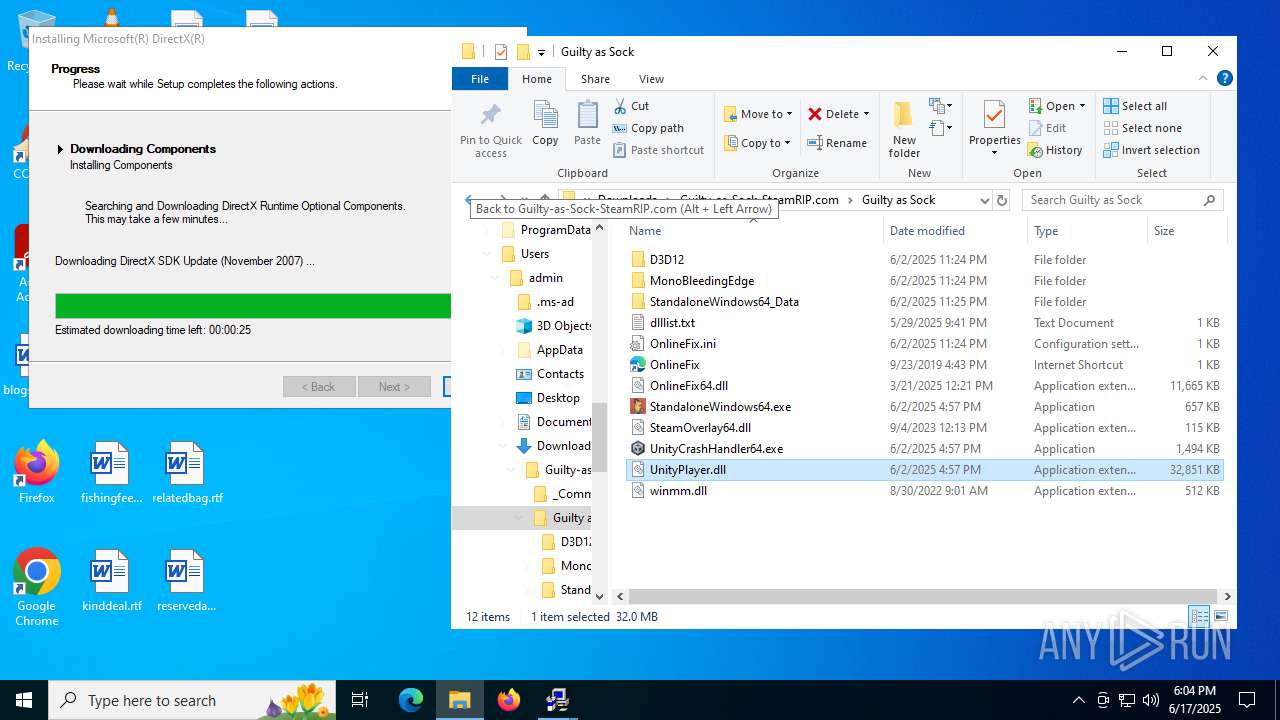
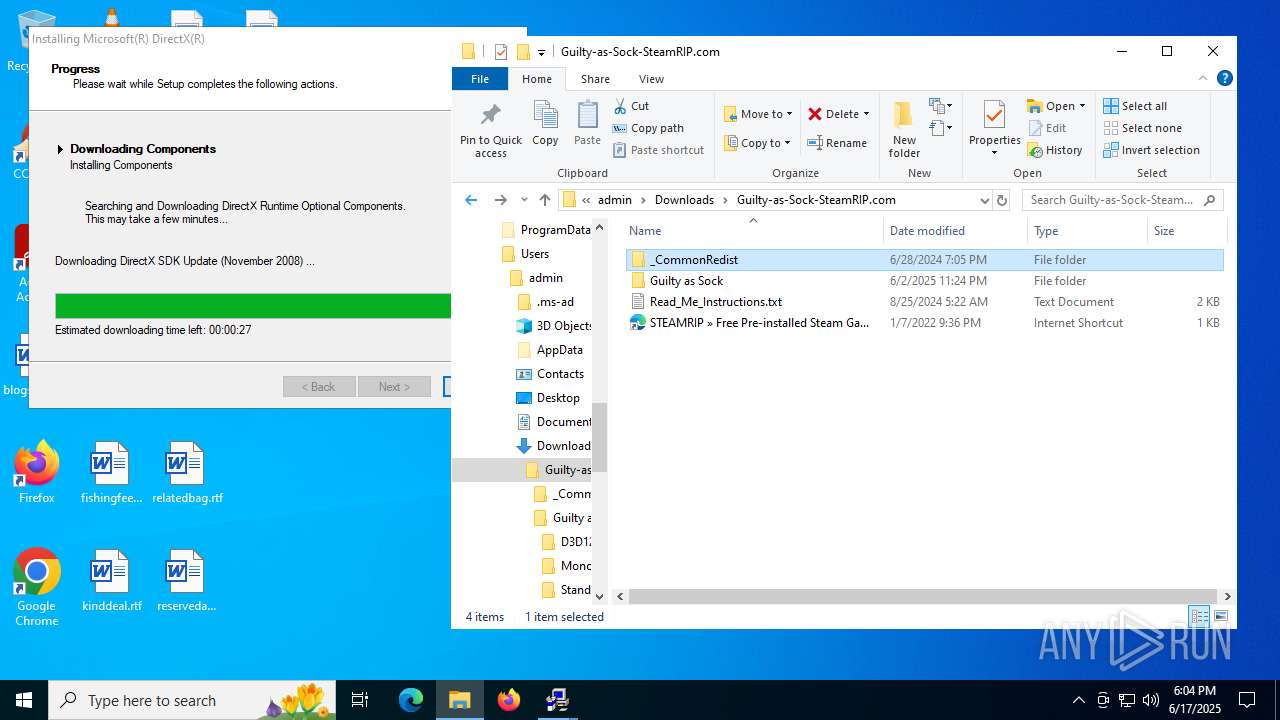
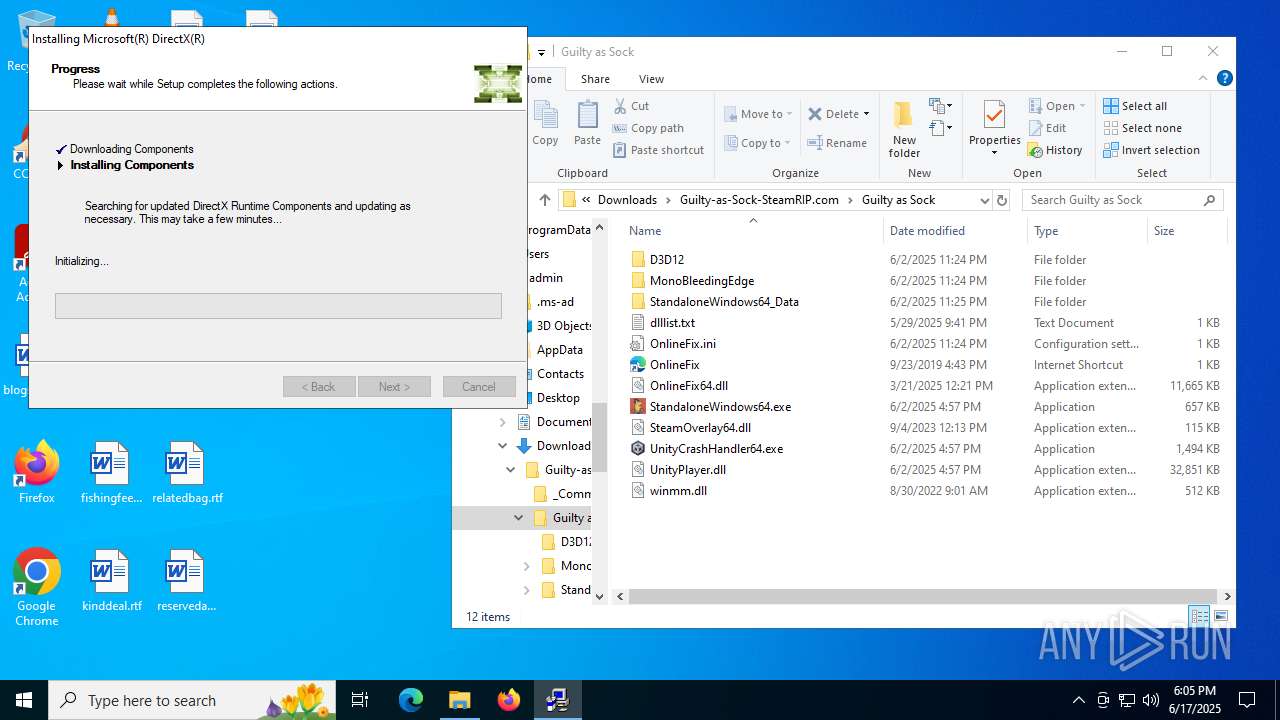
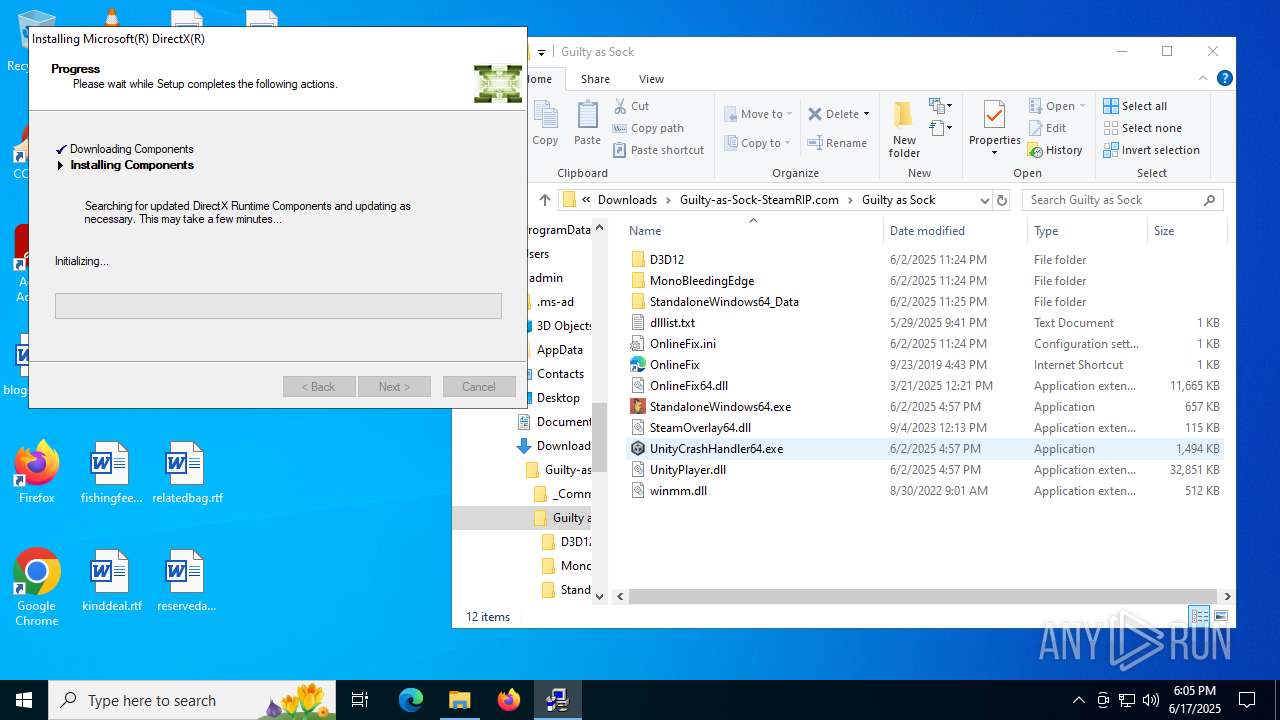
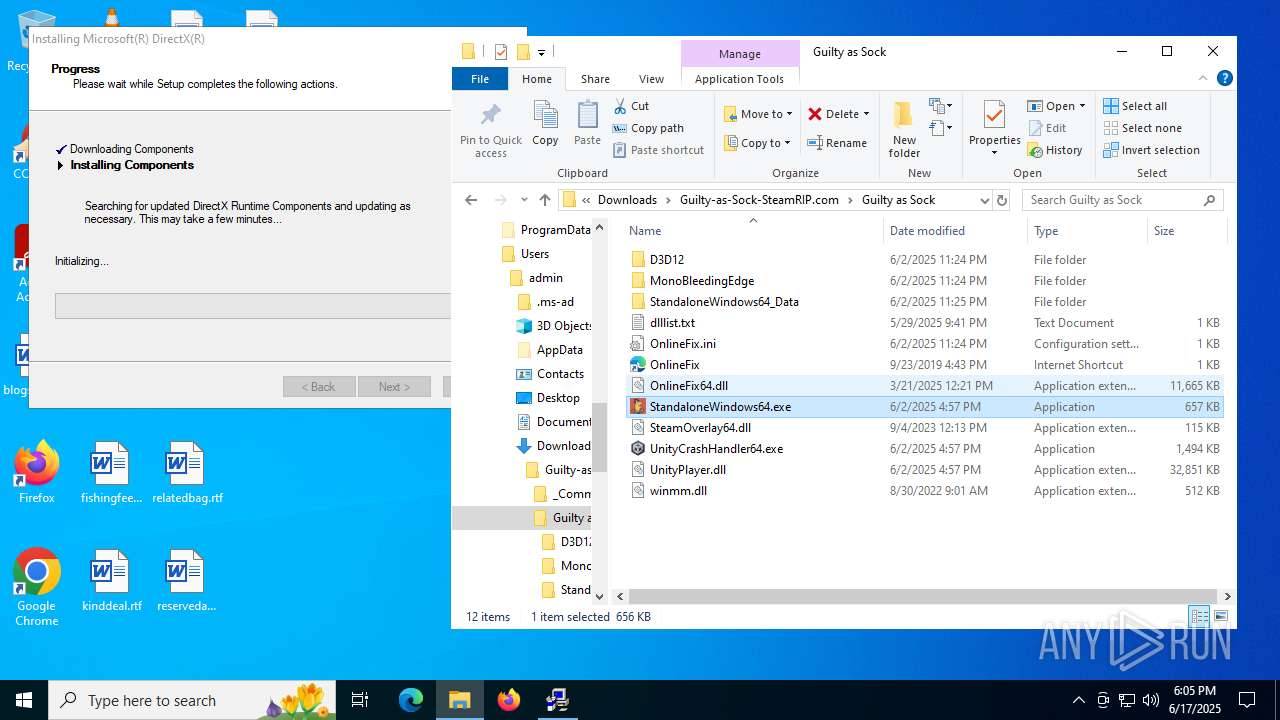
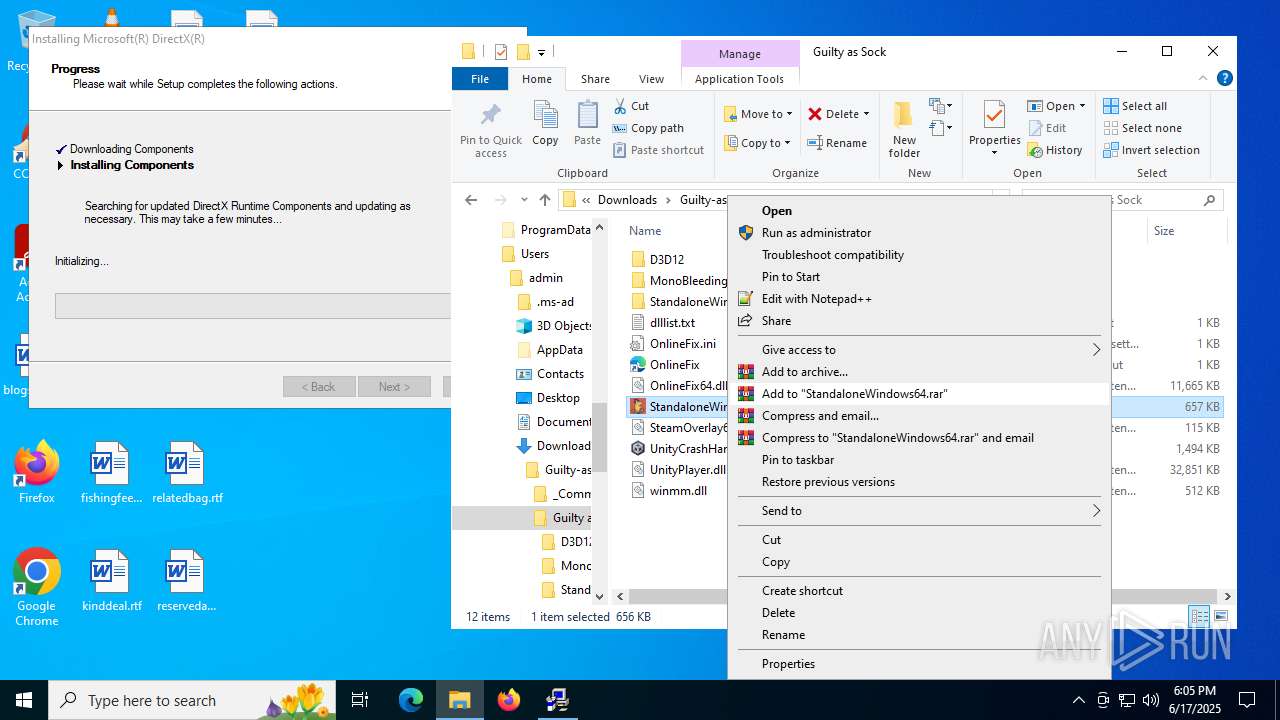
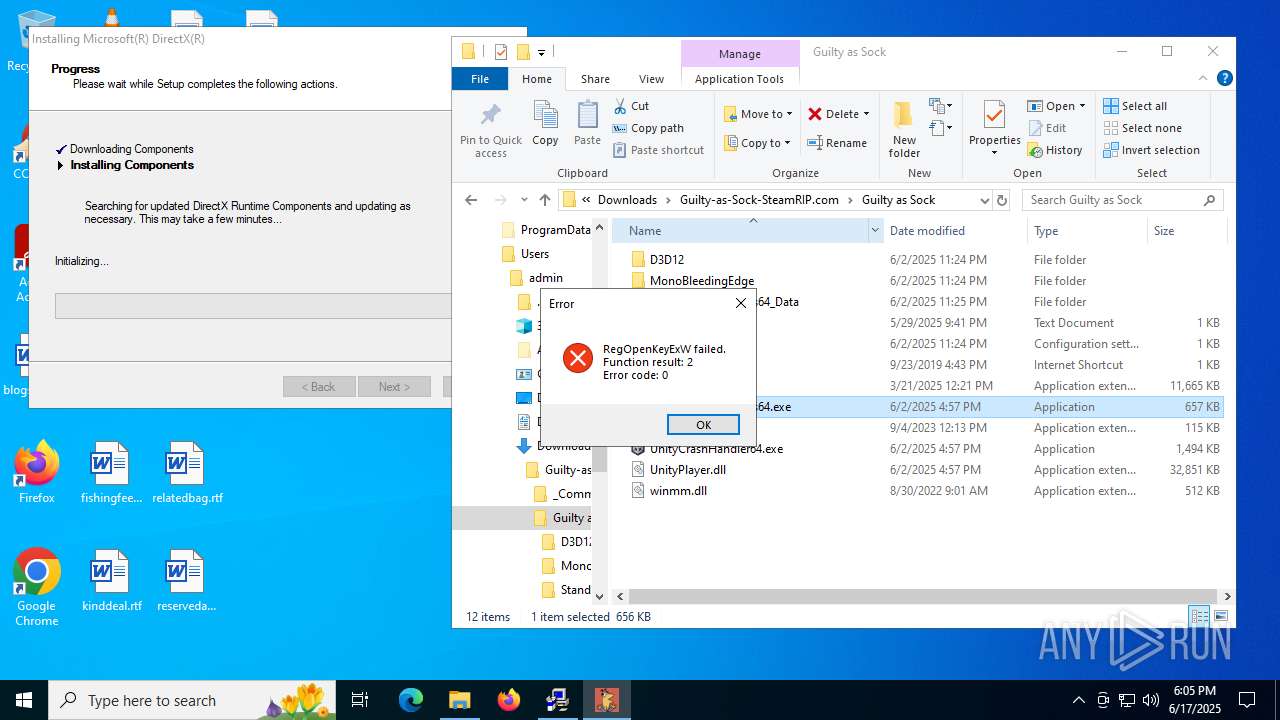
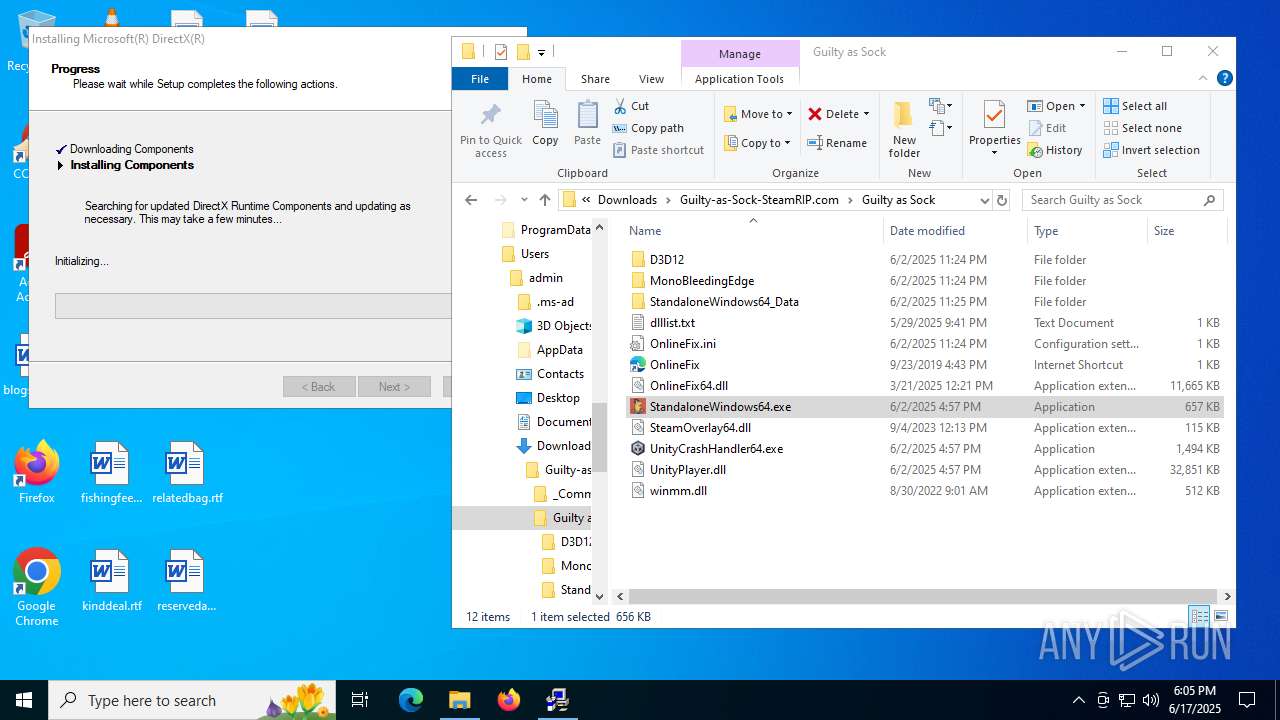
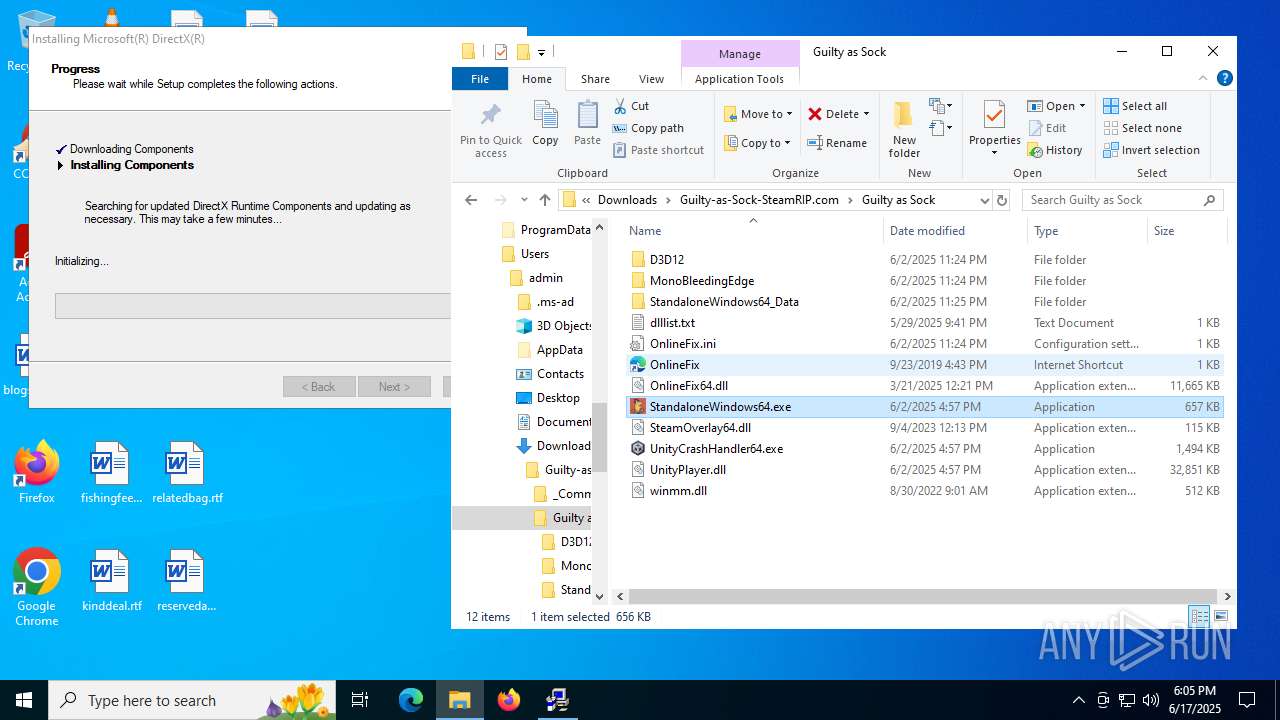
Manual execution by a user
- StandaloneWindows64.exe (PID: 7412)
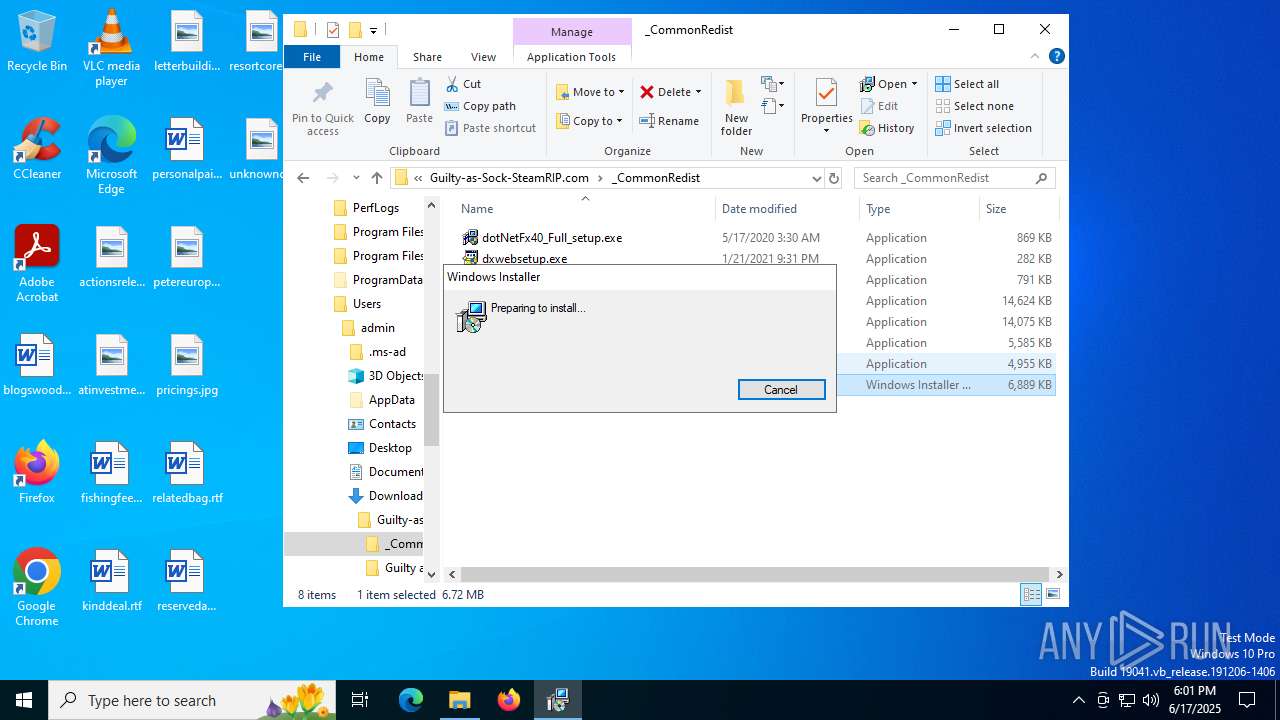
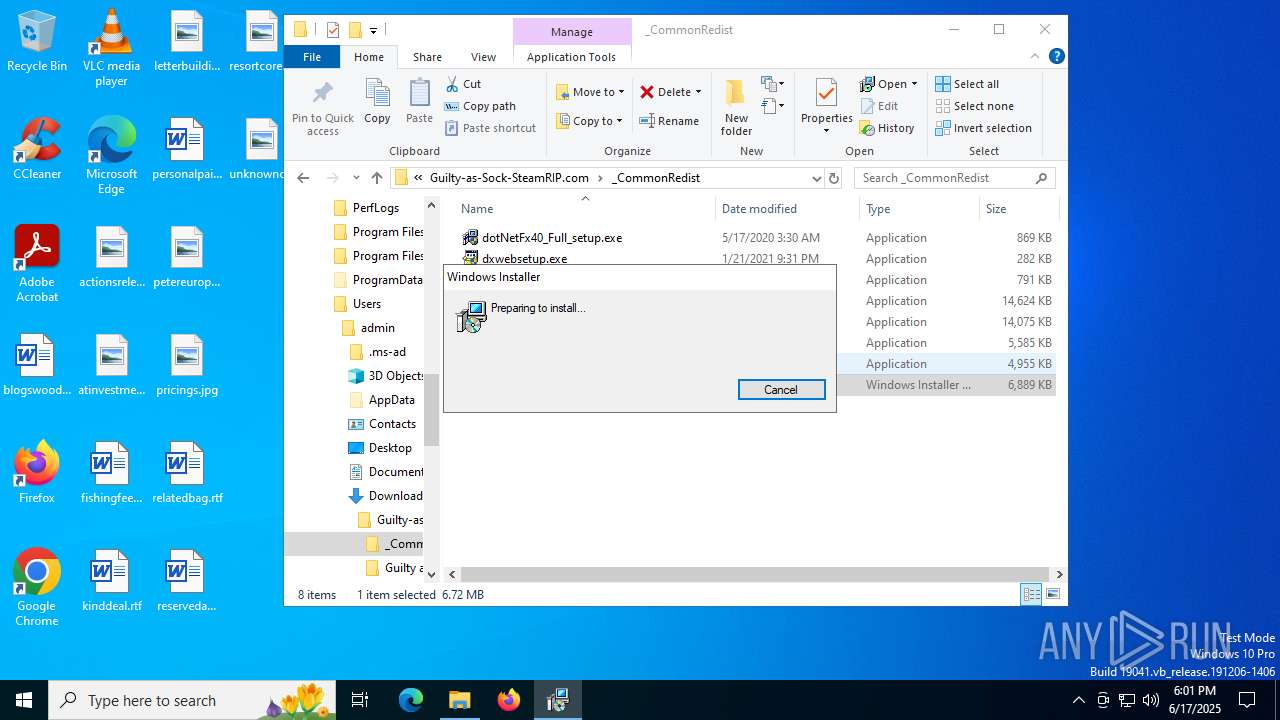
- msiexec.exe (PID: 7228)
- WinRAR.exe (PID: 1728)
- vcredist_x86.exe (PID: 5372)
- vcredist_x86.exe (PID: 6320)
- vcredist_x64.exe (PID: 3480)
- vcredist_x64.exe (PID: 2552)
- vcredist_2015-2019_x86.exe (PID: 5644)
- vcredist_2015-2019_x64.exe (PID: 1128)
- oalinst.exe (PID: 6656)
- oalinst.exe (PID: 188)
- dotNetFx40_Full_setup.exe (PID: 5720)
- dotNetFx40_Full_setup.exe (PID: 4552)
- StandaloneWindows64.exe (PID: 4892)
- dotNetFx40_Full_setup.exe (PID: 8092)
- notepad.exe (PID: 7004)
- dxwebsetup.exe (PID: 5436)
- oalinst.exe (PID: 1036)
- vcredist_2015-2019_x64.exe (PID: 304)
- StandaloneWindows64.exe (PID: 1080)
- StandaloneWindows64.exe (PID: 7104)
- StandaloneWindows64.exe (PID: 5980)
The sample compiled with german language support
- WinRAR.exe (PID: 1728)
- vcredist_x86.exe (PID: 5372)
- vcredist_x64.exe (PID: 2552)
- dotNetFx40_Full_setup.exe (PID: 5720)
- msiexec.exe (PID: 7540)
- dotNetFx40_Full_setup.exe (PID: 8092)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7228)
Creates files or folders in the user directory
- msiexec.exe (PID: 7228)
Reads the software policy settings
- msiexec.exe (PID: 7228)
Reads the computer name
- identity_helper.exe (PID: 7240)
- msiexec.exe (PID: 7540)
- identity_helper.exe (PID: 7960)
Checks proxy server information
- msiexec.exe (PID: 7228)
The sample compiled with japanese language support
- vcredist_x86.exe (PID: 5372)
- vcredist_x64.exe (PID: 2552)
- dotNetFx40_Full_setup.exe (PID: 5720)
- msiexec.exe (PID: 7540)
- dotNetFx40_Full_setup.exe (PID: 8092)
The sample compiled with english language support
- WinRAR.exe (PID: 1728)
- vcredist_x86.exe (PID: 5372)
- vcredist_x64.exe (PID: 2552)
- vcredist_2015-2019_x86.exe (PID: 5644)
- vcredist_2015-2019_x86.exe (PID: 6892)
- vcredist_2015-2019_x64.exe (PID: 4984)
- vcredist_2015-2019_x64.exe (PID: 1128)
- dotNetFx40_Full_setup.exe (PID: 5720)
- msiexec.exe (PID: 7540)
- DXSETUP.exe (PID: 4808)
- oalinst.exe (PID: 6656)
- dotNetFx40_Full_setup.exe (PID: 8092)
- dxwebsetup.exe (PID: 5436)
- dxwsetup.exe (PID: 7624)
- oalinst.exe (PID: 1036)
- vcredist_2015-2019_x64.exe (PID: 304)
- vcredist_2015-2019_x64.exe (PID: 7248)
The sample compiled with chinese language support
- vcredist_x86.exe (PID: 5372)
- vcredist_x64.exe (PID: 2552)
- dotNetFx40_Full_setup.exe (PID: 5720)
- msiexec.exe (PID: 7540)
- dotNetFx40_Full_setup.exe (PID: 8092)
The sample compiled with french language support
- vcredist_x86.exe (PID: 5372)
- vcredist_x64.exe (PID: 2552)
- dotNetFx40_Full_setup.exe (PID: 5720)
- msiexec.exe (PID: 7540)
- dotNetFx40_Full_setup.exe (PID: 8092)
The sample compiled with spanish language support
- vcredist_x86.exe (PID: 5372)
- vcredist_x64.exe (PID: 2552)
- dotNetFx40_Full_setup.exe (PID: 5720)
- msiexec.exe (PID: 7540)
- dotNetFx40_Full_setup.exe (PID: 8092)
The sample compiled with russian language support
- vcredist_x86.exe (PID: 5372)
- vcredist_x64.exe (PID: 2552)
- dotNetFx40_Full_setup.exe (PID: 5720)
- msiexec.exe (PID: 7540)
- dotNetFx40_Full_setup.exe (PID: 8092)
The sample compiled with Italian language support
- vcredist_x86.exe (PID: 5372)
- vcredist_x64.exe (PID: 2552)
- dotNetFx40_Full_setup.exe (PID: 5720)
- msiexec.exe (PID: 7540)
- dotNetFx40_Full_setup.exe (PID: 8092)
The sample compiled with korean language support
- vcredist_x86.exe (PID: 5372)
- vcredist_x64.exe (PID: 2552)
- dotNetFx40_Full_setup.exe (PID: 5720)
- msiexec.exe (PID: 7540)
- dotNetFx40_Full_setup.exe (PID: 8092)
The sample compiled with czech language support
- dotNetFx40_Full_setup.exe (PID: 5720)
- dotNetFx40_Full_setup.exe (PID: 8092)
The sample compiled with arabic language support
- dotNetFx40_Full_setup.exe (PID: 5720)
- dotNetFx40_Full_setup.exe (PID: 8092)
The sample compiled with swedish language support
- dotNetFx40_Full_setup.exe (PID: 5720)
- dotNetFx40_Full_setup.exe (PID: 8092)
The sample compiled with portuguese language support
- dotNetFx40_Full_setup.exe (PID: 5720)
- dotNetFx40_Full_setup.exe (PID: 8092)
The sample compiled with turkish language support
- dotNetFx40_Full_setup.exe (PID: 5720)
- dotNetFx40_Full_setup.exe (PID: 8092)
Manages system restore points
- SrTasks.exe (PID: 7192)
The sample compiled with polish language support
- dotNetFx40_Full_setup.exe (PID: 5720)
- dotNetFx40_Full_setup.exe (PID: 8092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
248
Monitored processes
87
Malicious processes
11
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
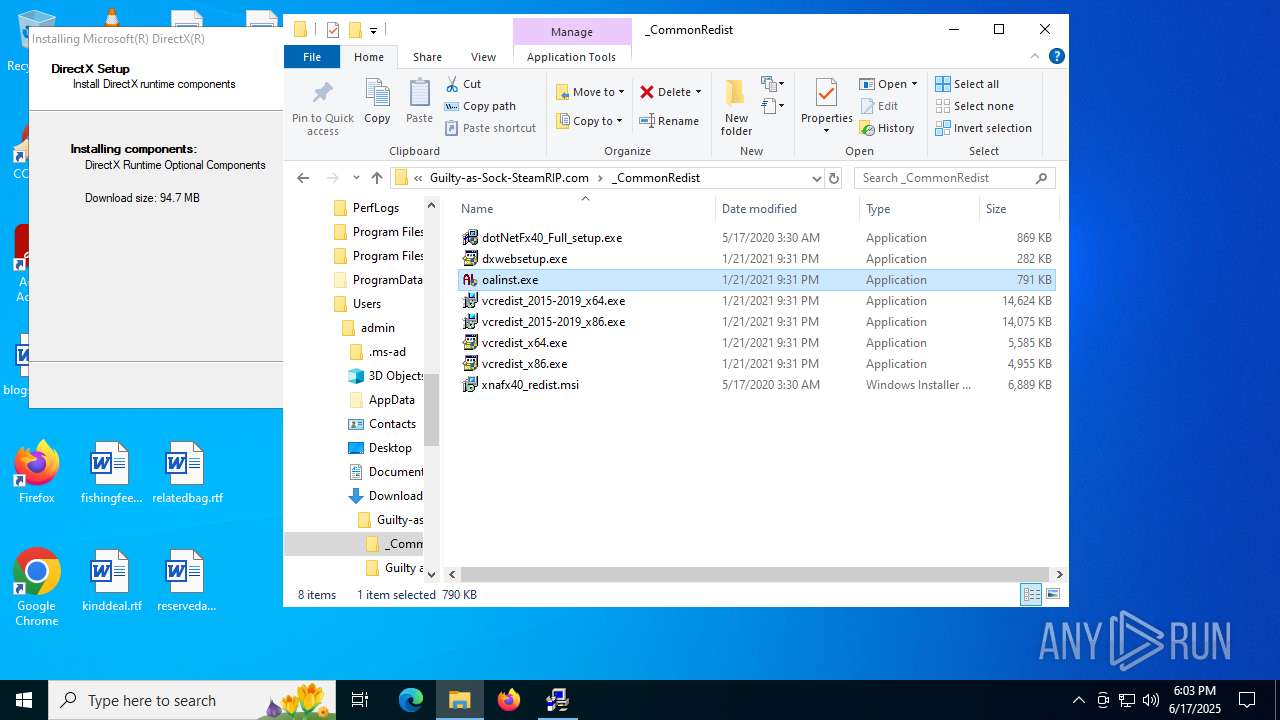
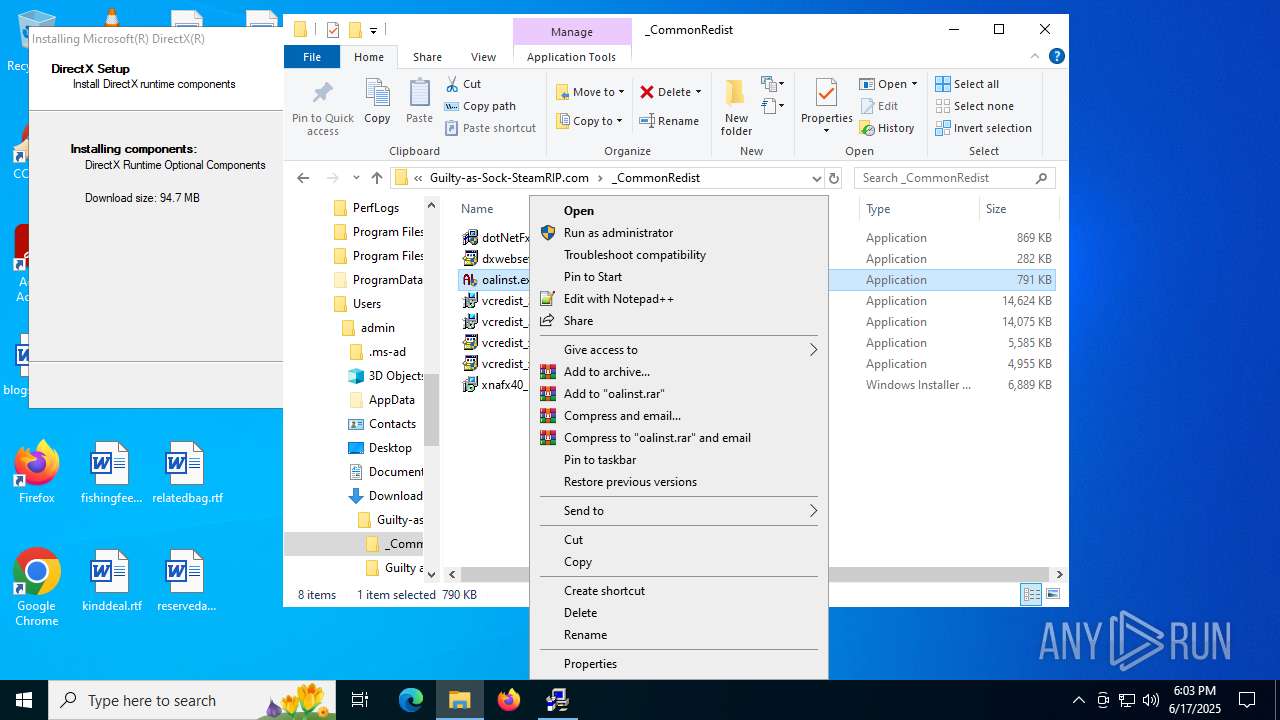
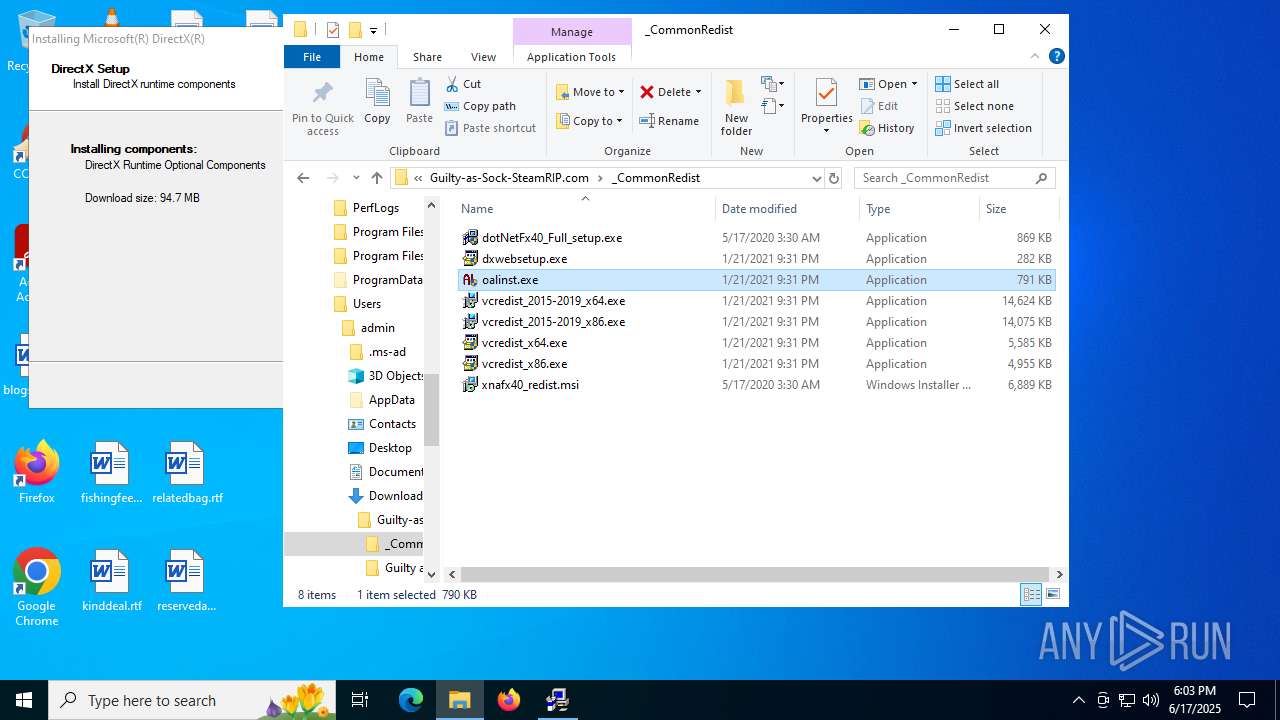
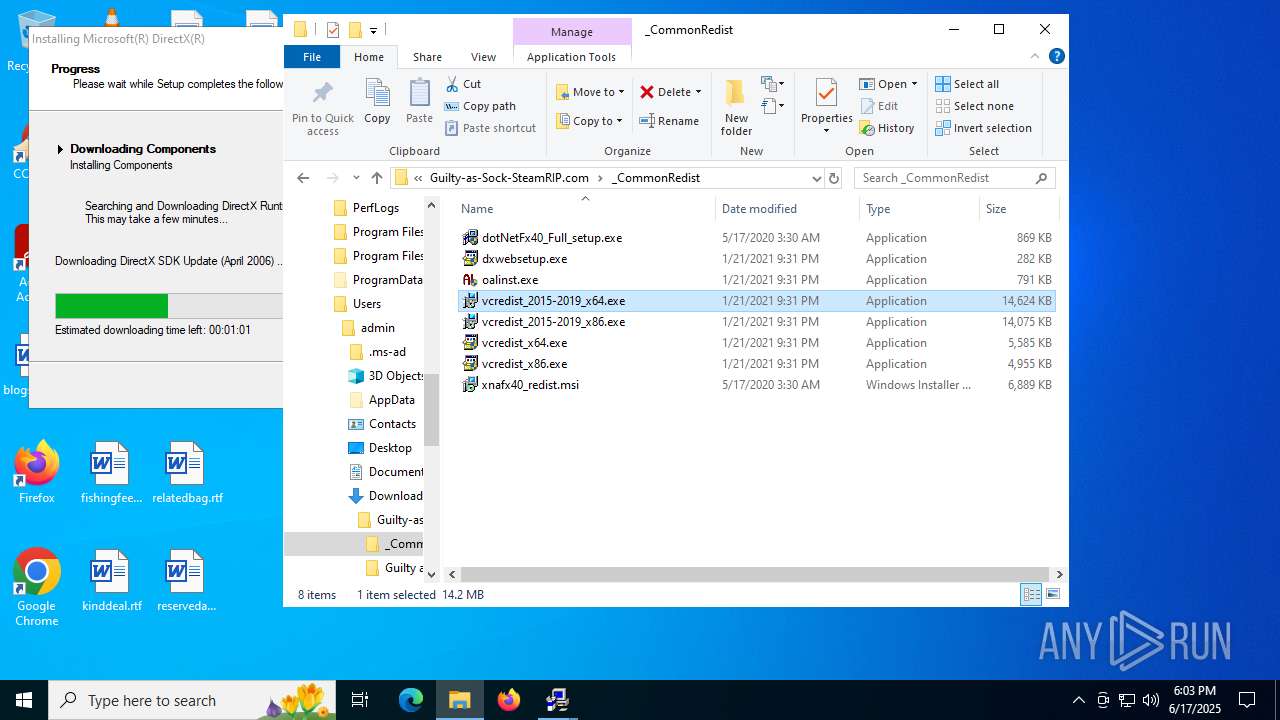
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
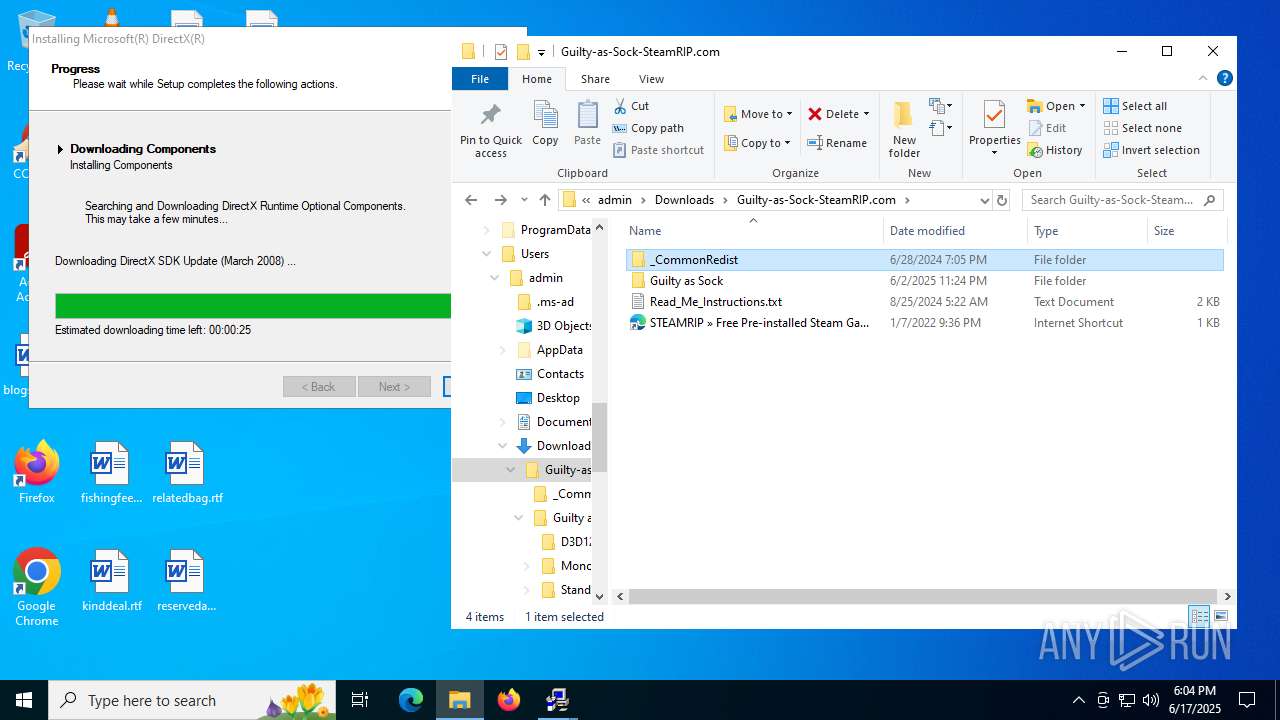
| 188 | "C:\Users\admin\Downloads\Guilty-as-Sock-SteamRIP.com\_CommonRedist\oalinst.exe" | C:\Users\admin\Downloads\Guilty-as-Sock-SteamRIP.com\_CommonRedist\oalinst.exe | — | explorer.exe | |||||||||||
User: admin Company: Creative Labs Inc. Integrity Level: MEDIUM Description: OpenAL Installer Exit code: 3221226540 Version: 2, 0, 7, 0 Modules
| |||||||||||||||
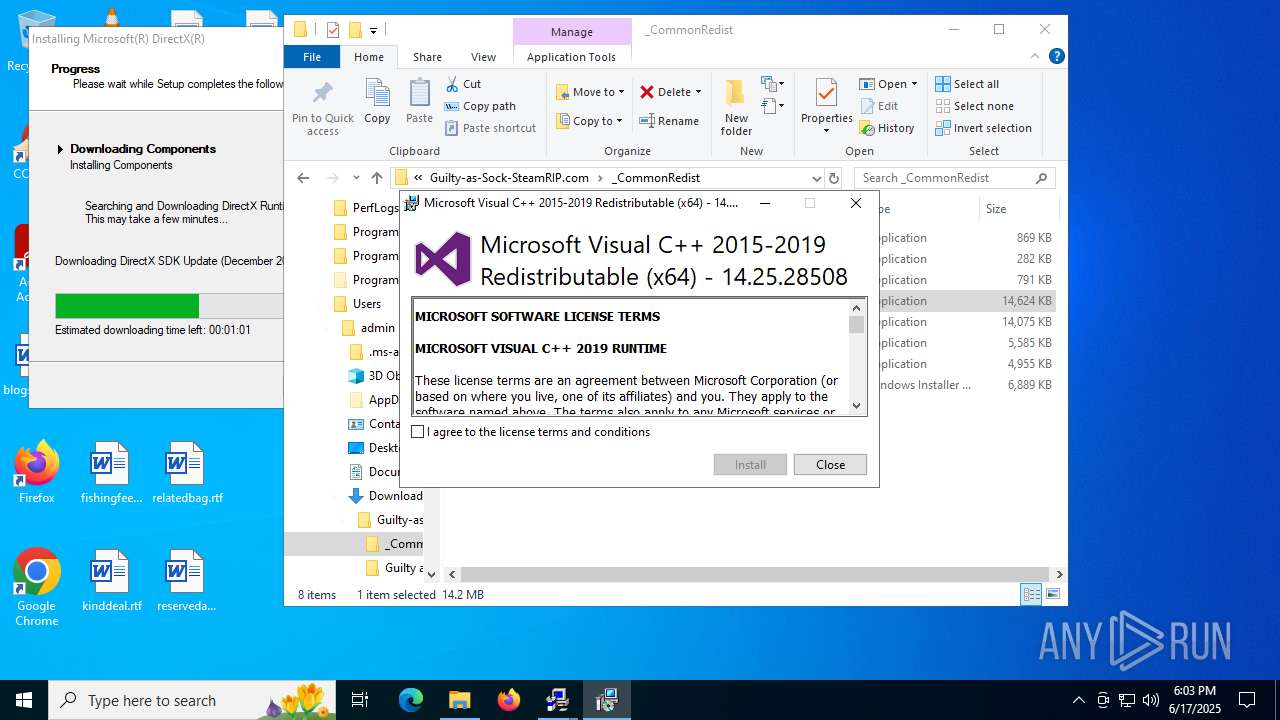
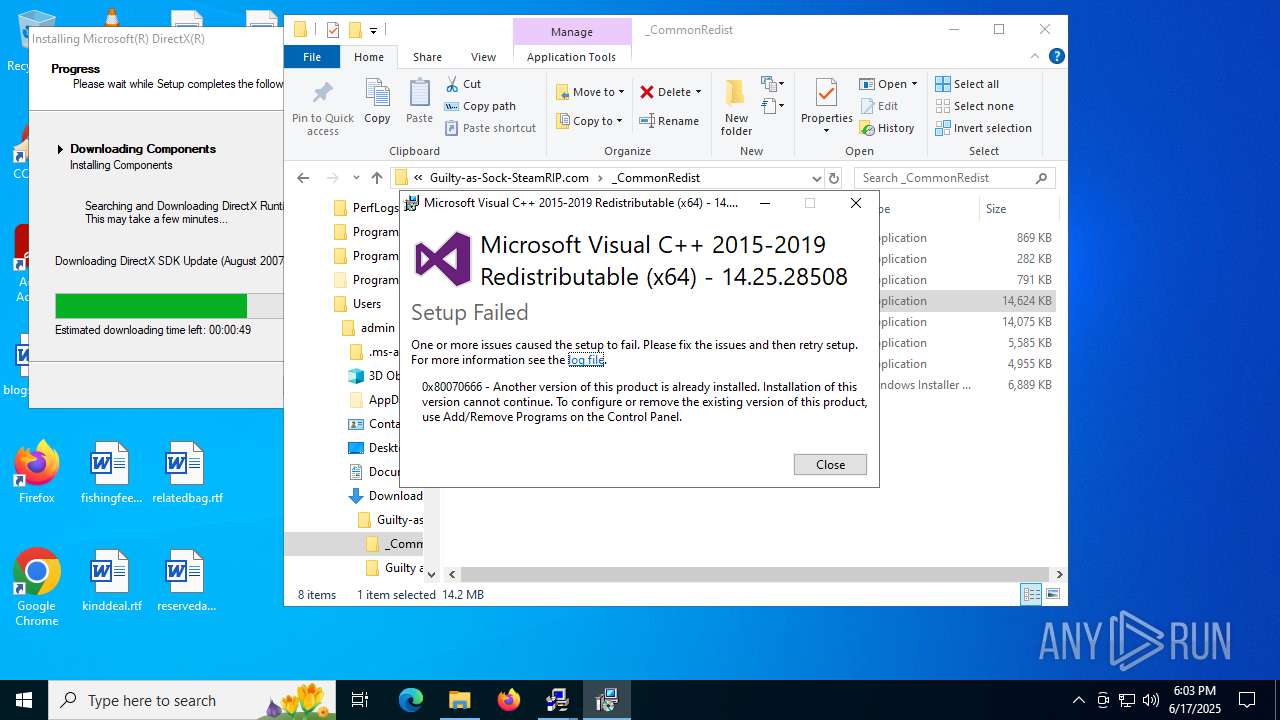
| 304 | "C:\Users\admin\Downloads\Guilty-as-Sock-SteamRIP.com\_CommonRedist\vcredist_2015-2019_x64.exe" | C:\Users\admin\Downloads\Guilty-as-Sock-SteamRIP.com\_CommonRedist\vcredist_2015-2019_x64.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.25.28508 Exit code: 1638 Version: 14.25.28508.3 Modules
| |||||||||||||||
| 592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=4928,i,8443196274220349935,4516530064649956757,262144 --variations-seed-version --mojo-platform-channel-handle=4508 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 592 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\Downloads\Guilty-as-Sock-SteamRIP.com\_CommonRedist\oalinst.exe" | C:\Users\admin\Downloads\Guilty-as-Sock-SteamRIP.com\_CommonRedist\oalinst.exe | explorer.exe | ||||||||||||
User: admin Company: Creative Labs Inc. Integrity Level: HIGH Description: OpenAL Installer Exit code: 0 Version: 2, 0, 7, 0 Modules
| |||||||||||||||
| 1080 | "C:\Users\admin\Downloads\Guilty-as-Sock-SteamRIP.com\Guilty as Sock\StandaloneWindows64.exe" | C:\Users\admin\Downloads\Guilty-as-Sock-SteamRIP.com\Guilty as Sock\StandaloneWindows64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 6000.0.43.9905963 Modules
| |||||||||||||||
| 1100 | c:\82d9f90aa95d90e49bc51f\Setup.exe | C:\82d9f90aa95d90e49bc51f\Setup.exe | vcredist_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 5100 Version: 10.0.30319.1 built by: RTMRel Modules
| |||||||||||||||
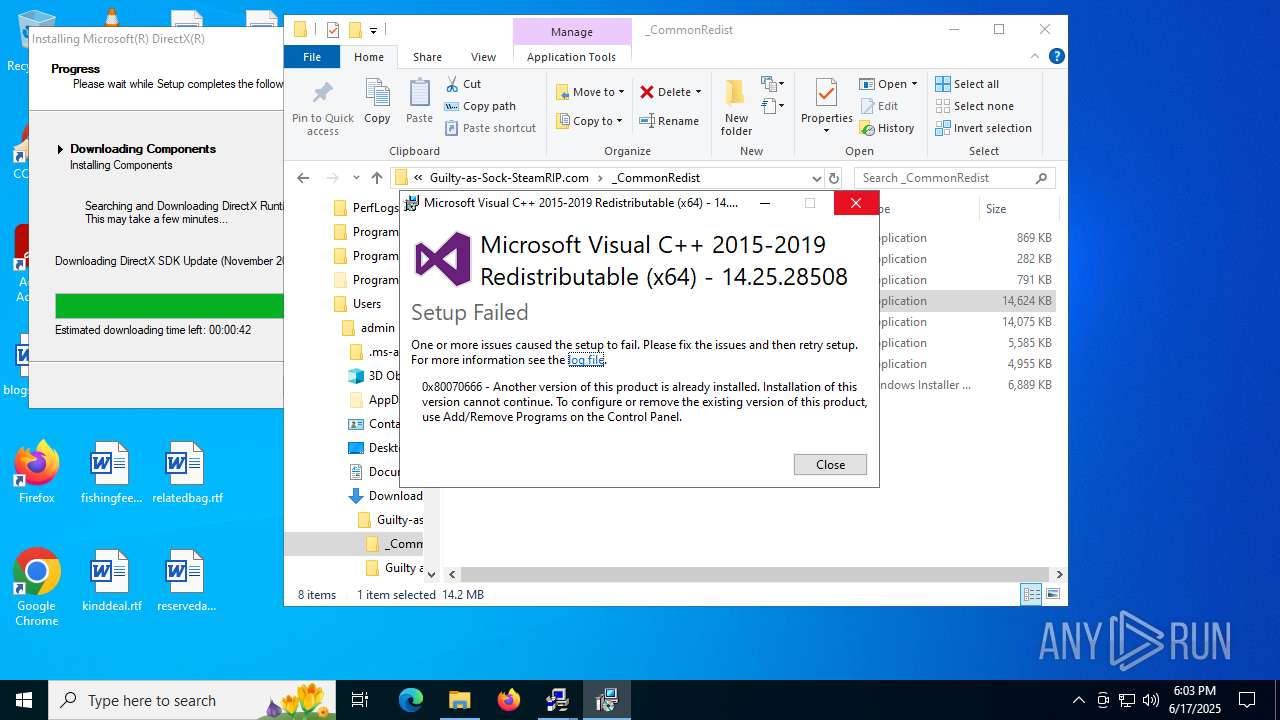
| 1128 | "C:\Users\admin\Downloads\Guilty-as-Sock-SteamRIP.com\_CommonRedist\vcredist_2015-2019_x64.exe" | C:\Users\admin\Downloads\Guilty-as-Sock-SteamRIP.com\_CommonRedist\vcredist_2015-2019_x64.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.25.28508 Exit code: 1638 Version: 14.25.28508.3 Modules
| |||||||||||||||
| 1160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2488,i,8484918394822726649,7912104167837448357,262144 --variations-seed-version --mojo-platform-channel-handle=2480 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc43b1f208,0x7ffc43b1f214,0x7ffc43b1f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
40 215
Read events
39 614
Write events
569
Delete events
32
Modification events
| (PID) Process: | (2648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2648) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 70B331925E962F00 | |||
| (PID) Process: | (2648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459518 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FD791F88-7912-4AAB-B58A-98E63DEF74F0} | |||
| (PID) Process: | (2648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459518 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E6756A45-1125-46BB-985E-727FEBA82A66} | |||
| (PID) Process: | (2648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459518 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F94148CC-47FE-42C4-96E2-0C897041DC3A} | |||
| (PID) Process: | (2648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459518 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6B3DB709-139F-4509-A4F1-C34B5D04FA15} | |||
| (PID) Process: | (2648) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
415
Suspicious files
849
Text files
500
Unknown types
104
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1771f4.TMP | — | |
MD5:— | SHA256:— | |||
| 2648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1771f4.TMP | — | |
MD5:— | SHA256:— | |||
| 2648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1771f4.TMP | — | |
MD5:— | SHA256:— | |||
| 2648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF177203.TMP | — | |
MD5:— | SHA256:— | |||
| 2648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1771f4.TMP | — | |
MD5:— | SHA256:— | |||
| 2648 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
187
TCP/UDP connections
92
DNS requests
93
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4984 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:pxayiHQsvISsYfXcmJXygCHM3AT1EhcmHd-Q1SfEUjI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2596 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7748 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.16.252.233:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7748 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7228 | msiexec.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
1068 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750787926&P2=404&P3=2&P4=cCbpNXIT8FX%2bBKaT8T0yFHaN3elOl3EvXwp7rzGdSDrovIDdqWkCIza57U7G3YT5FlkQJRMhg9ladfr94D2qLQ%3d%3d | unknown | — | — | whitelisted |
4808 | DXSETUP.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/CSPCA.crl | unknown | — | — | whitelisted |
1068 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1750787927&P2=404&P3=2&P4=LtAx%2fEoe6r0uKnyx4EB%2brAxyS%2faYQsDX31vKlJoPgW6NYs33weGrLB3RCWPwf4xm0v09%2f4HVi5RRlO43KoMHdg%3d%3d | unknown | — | — | whitelisted |
7228 | msiexec.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/CodeSigPCA.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4984 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4984 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4984 | msedge.exe | 45.112.123.126:443 | gofile.io | AMAZON-02 | SG | whitelisted |
4984 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4984 | msedge.exe | 2.16.204.153:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
4984 | msedge.exe | 2.16.204.158:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
gofile.io |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
s.gofile.io |
| whitelisted |
api.gofile.io |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4984 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4984 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
4984 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4984 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
4984 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
4984 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4984 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4984 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
4984 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4984 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
Process | Message |
|---|---|
Setup.exe | The operation completed successfully.
|
Setup.exe | A StopBlock was hit or a System Requirement was not met. |
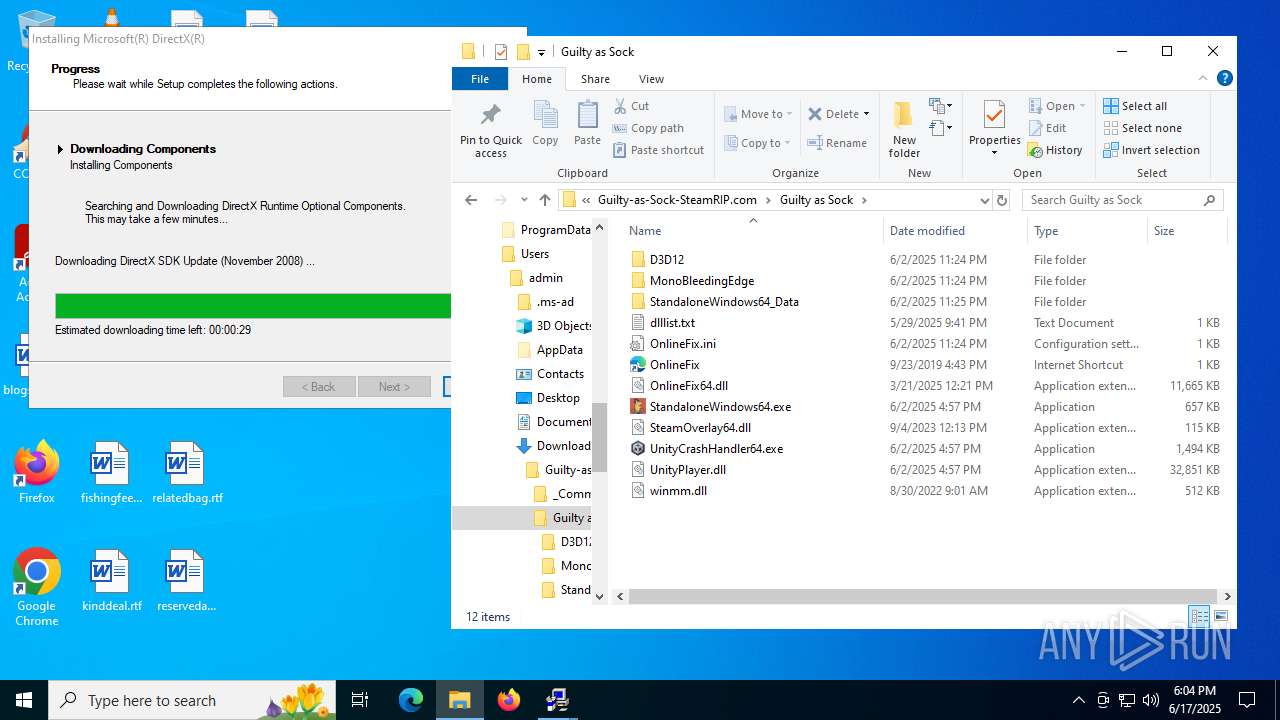
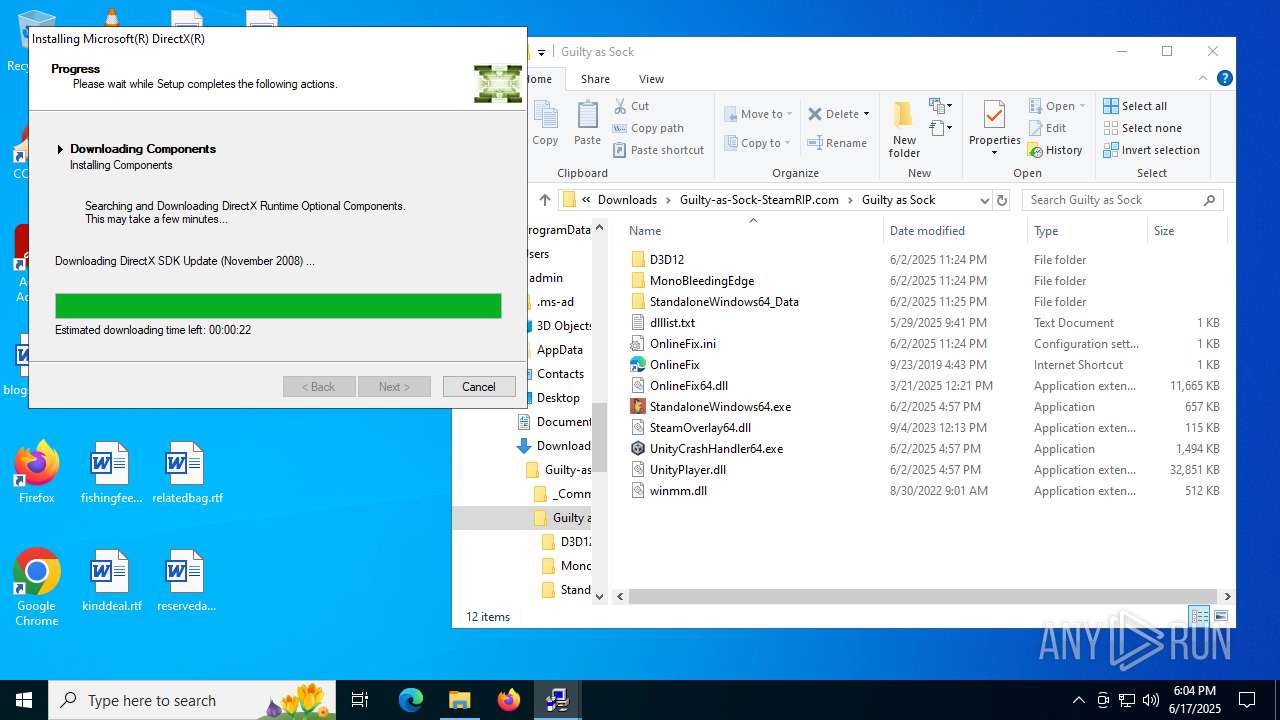
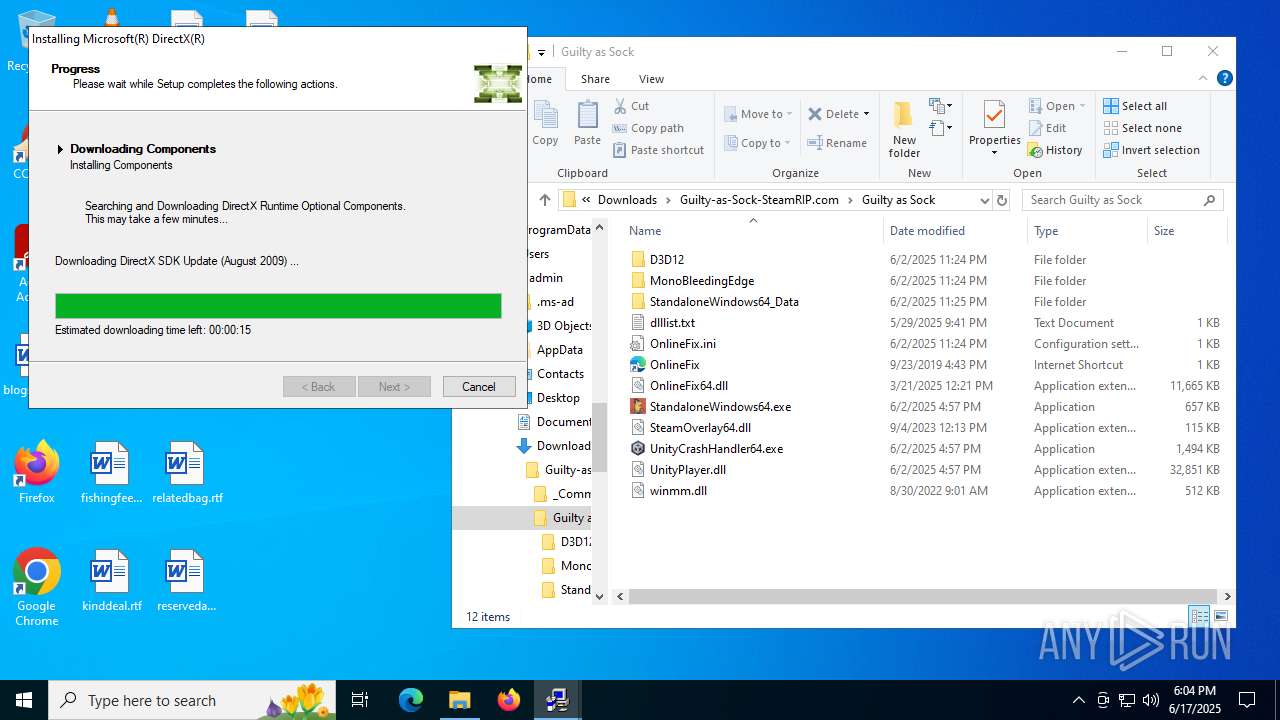
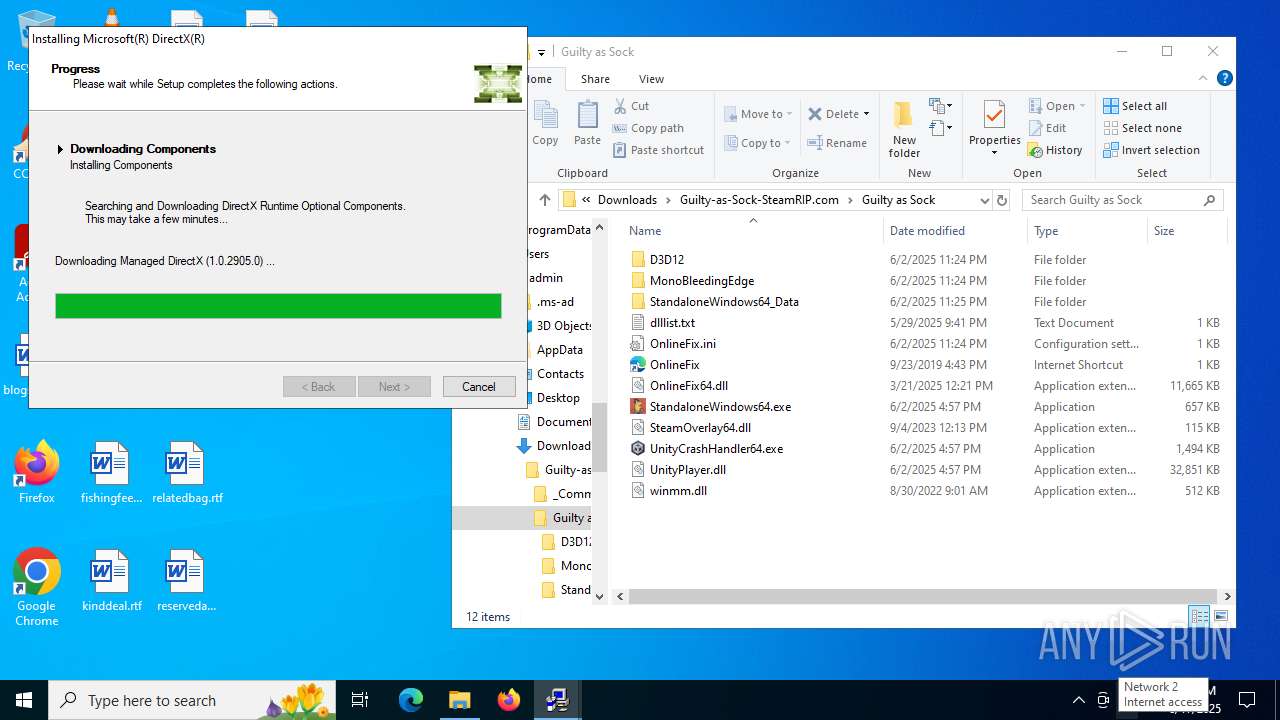
DXSETUP.exe | DLL_PROCESS_ATTACH |
DXSETUP.exe | DLL_PROCESS_ATTACH |
DXSETUP.exe | DLL_PROCESS_DETACH |
DXSETUP.exe | DLL_PROCESS_DETACH |
Setup.exe | The operation completed successfully.
|
Setup.exe | The operation completed successfully.
|
Setup.exe | The operation completed successfully.
|
dxwsetup.exe | DLL_PROCESS_ATTACH |