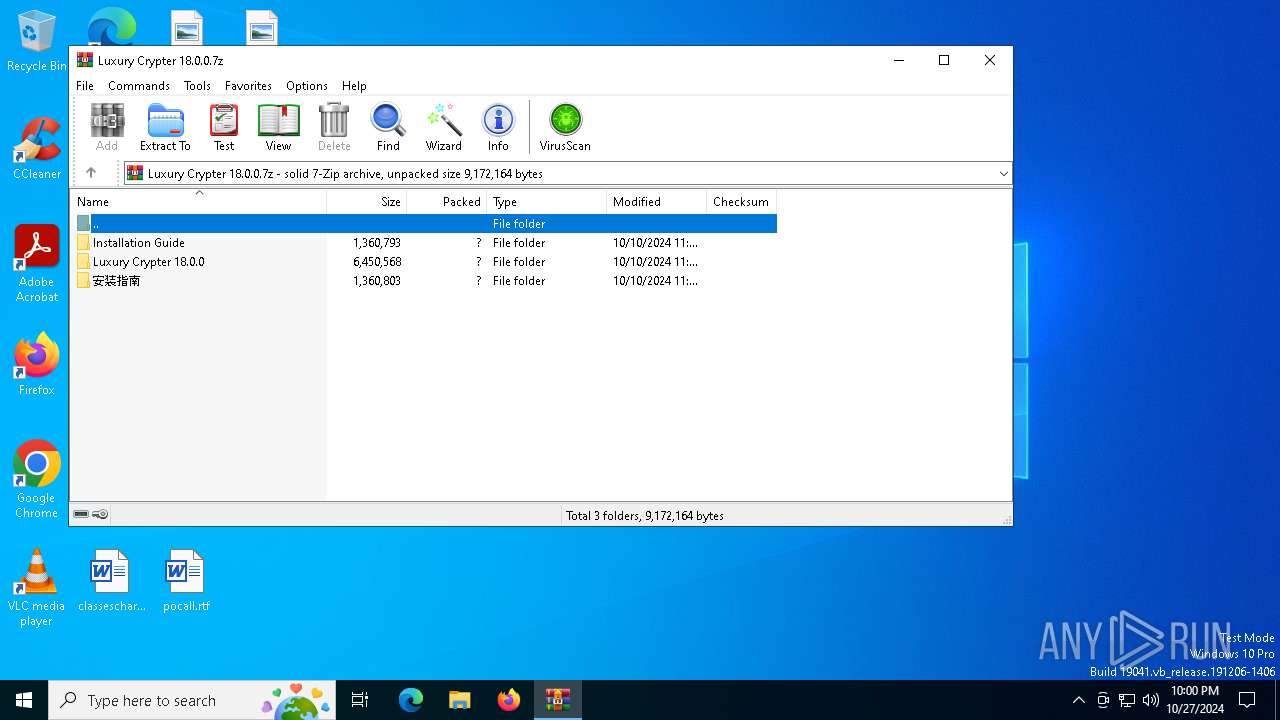
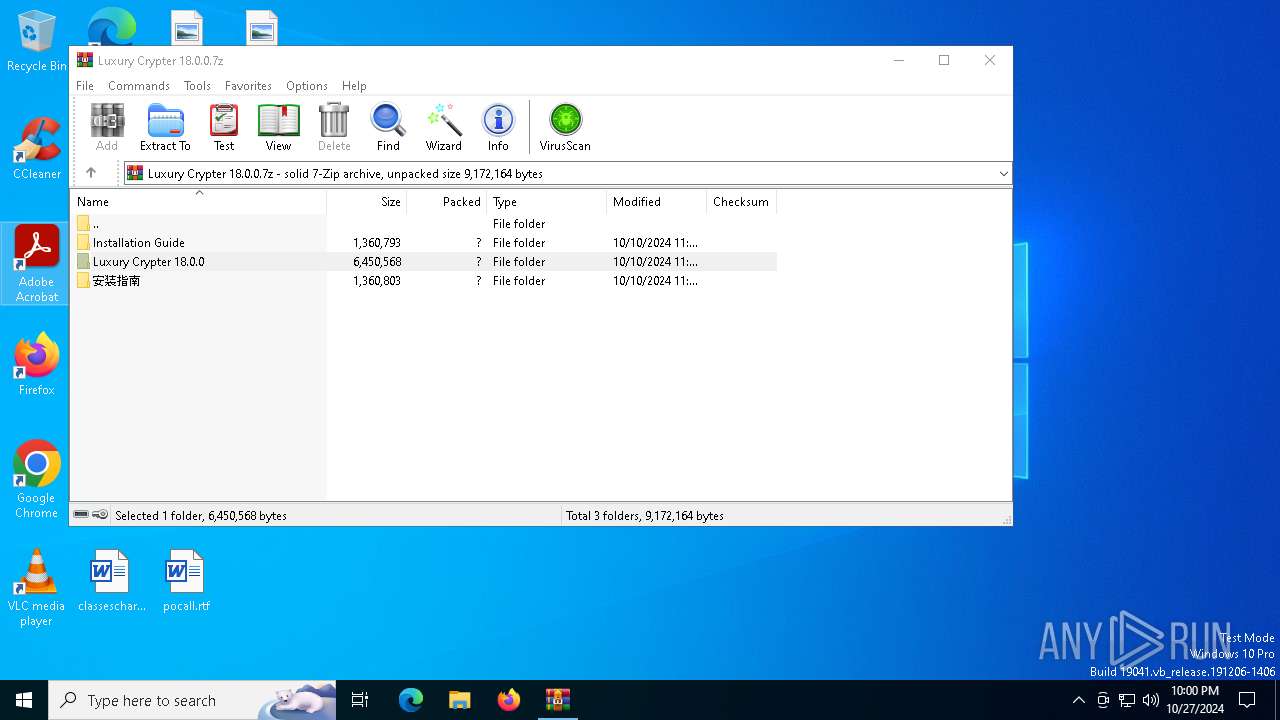
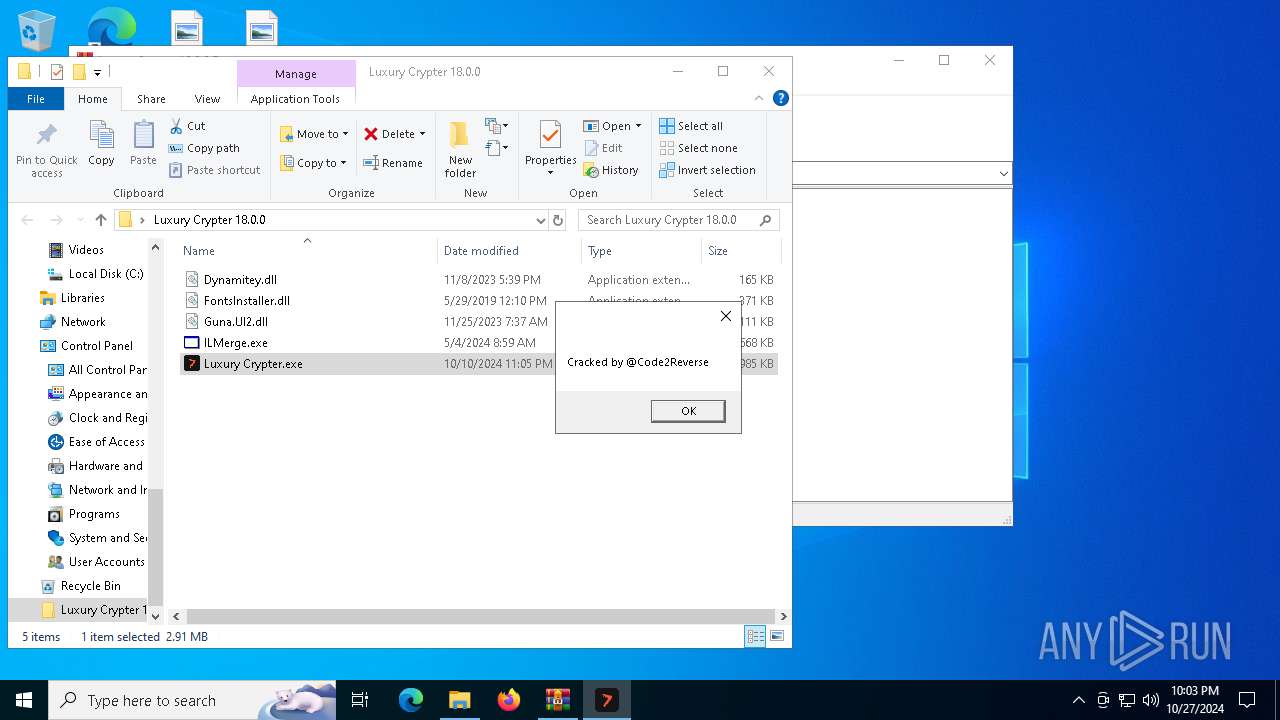
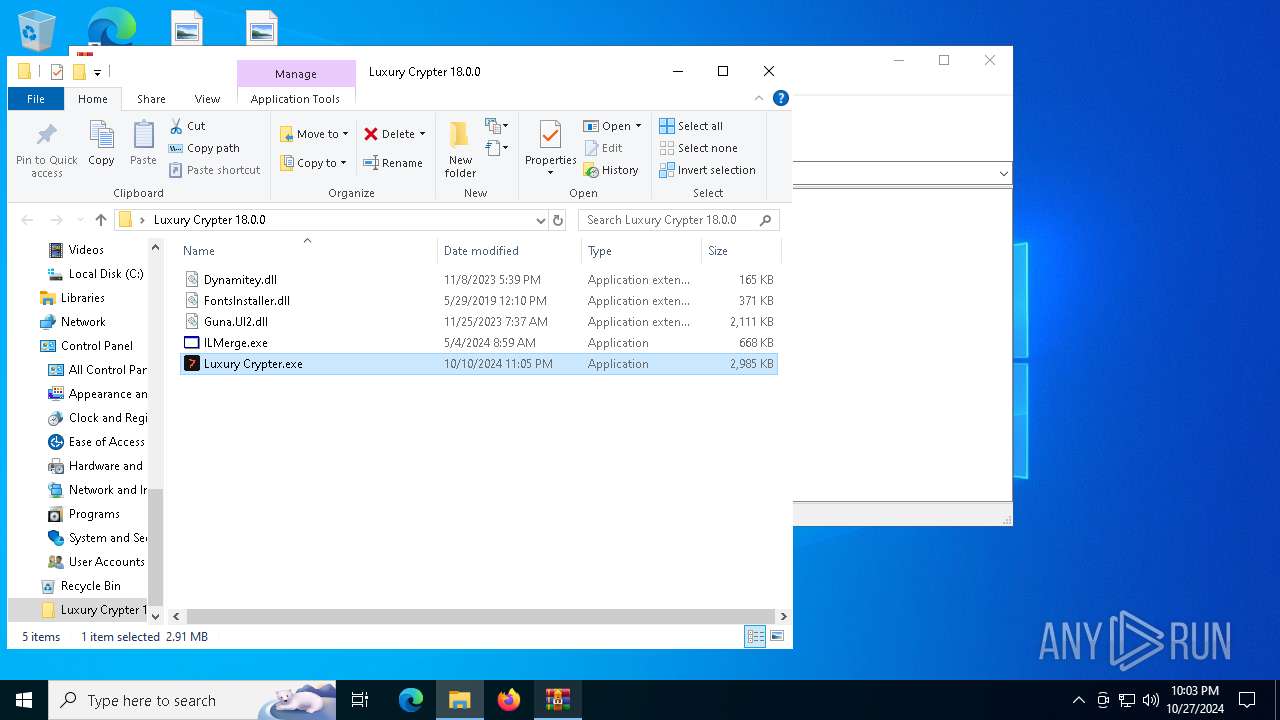
| File name: | Luxury Crypter 18.0.0.7z |
| Full analysis: | https://app.any.run/tasks/58964835-bc9b-4306-b3df-519a924d504a |
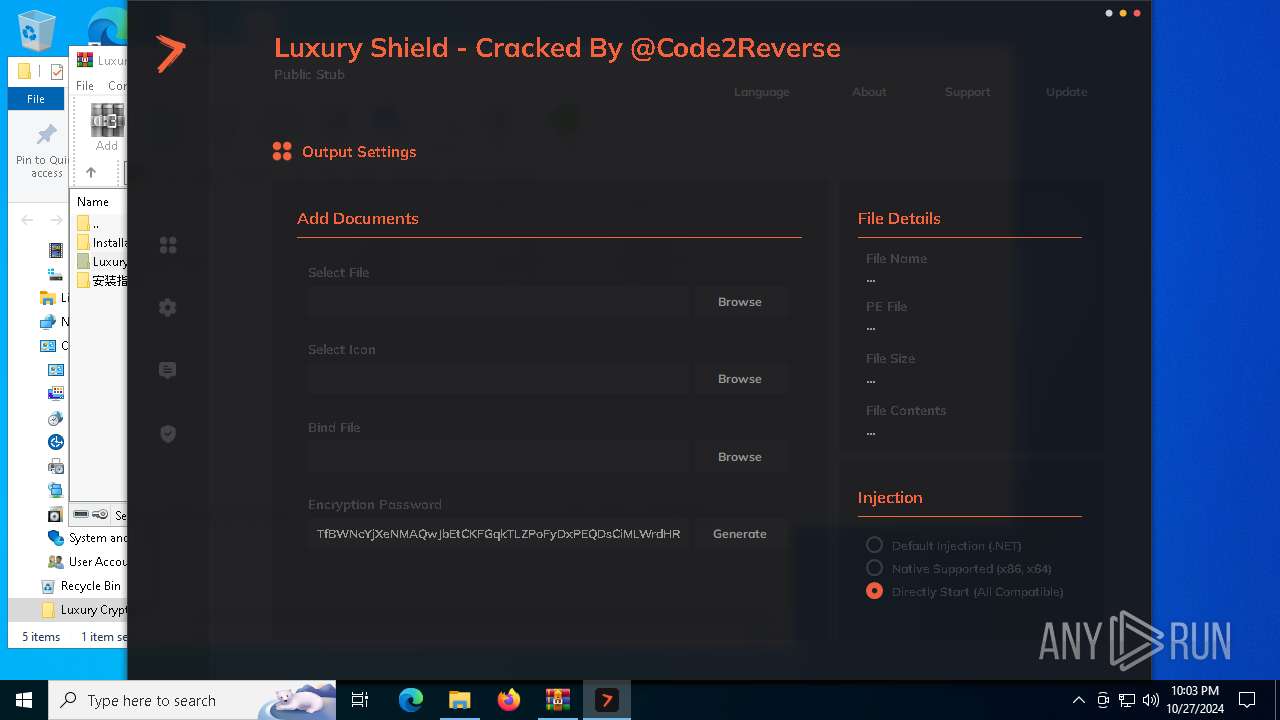
| Verdict: | Malicious activity |
| Analysis date: | October 27, 2024, 21:59:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.3 |
| MD5: | F9EF786783F16792EB9965B19705E930 |
| SHA1: | 997A903E880601DDE86945F89A1BE19045655C45 |
| SHA256: | 1252C59F28ED87F9236AF0B045978C17351FAF34649E639B1DC8FDFDD5CCC0AE |
| SSDEEP: | 98304:b6GnYO2ayzIXIWk6cjWOUsj9LzSHGhrCofaOLwrg79+e7zkRp+U5DRTWO8qHJm7x:aJtN2OS0F |
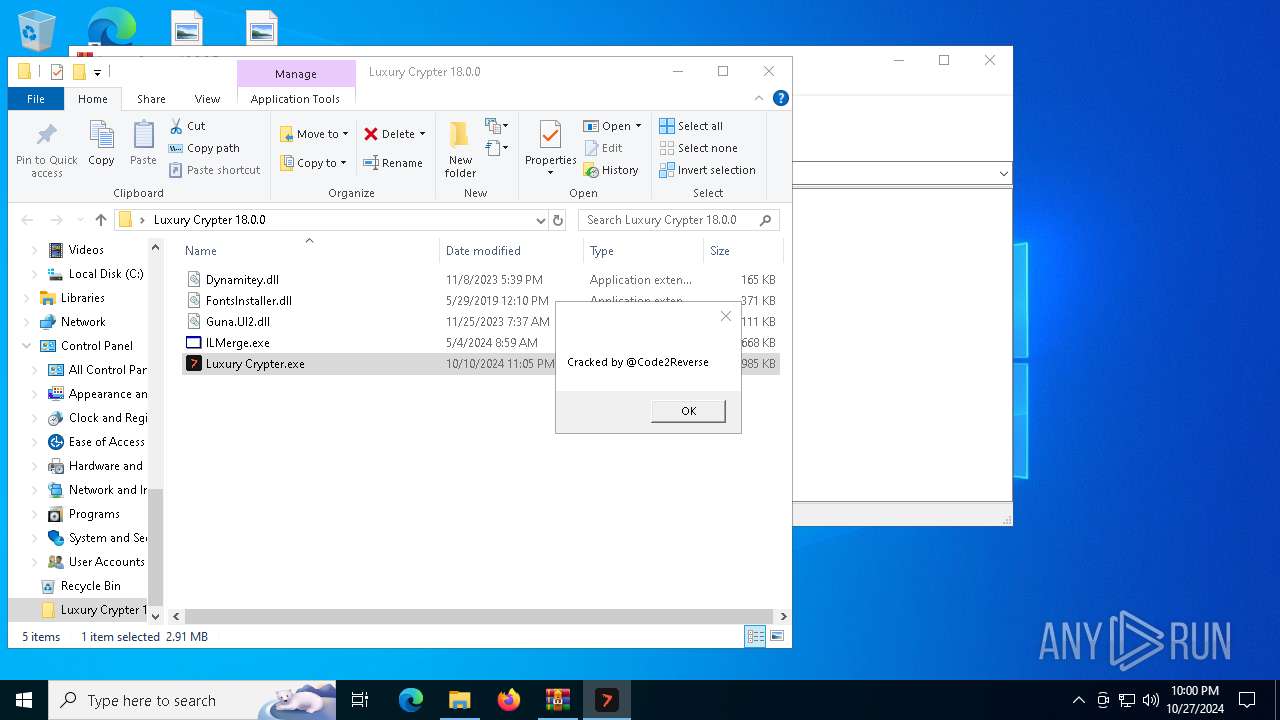
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6424)
Create files in the Startup directory
- svchost.exe (PID: 5584)
- msedgewebview2.exe (PID: 2360)
Adds path to the Windows Defender exclusion list
- msedgewebview2.exe (PID: 2360)
Uses Task Scheduler to run other applications
- msedgewebview2.exe (PID: 2360)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 6424)
- Luxury Crypter.exe (PID: 6800)
Executable content was dropped or overwritten
- Luxury Crypter.exe (PID: 6800)
- Luxury Crypter.exe (PID: 6268)
The process creates files with name similar to system file names
- Luxury Crypter.exe (PID: 6800)
Reads the date of Windows installation
- Luxury Crypter.exe (PID: 6800)
- Luxury Crypter.exe (PID: 3772)
- msedgewebview2.exe (PID: 2360)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- svchost.exe (PID: 5584)
Script adds exclusion path to Windows Defender
- msedgewebview2.exe (PID: 2360)
Starts POWERSHELL.EXE for commands execution
- msedgewebview2.exe (PID: 2360)
Connects to unusual port
- svchost.exe (PID: 5584)
Reads security settings of Internet Explorer
- Luxury Crypter.exe (PID: 6268)
- msedgewebview2.exe (PID: 2360)
- Luxury Crypter.exe (PID: 3772)
- Luxury Crypter.exe (PID: 7120)
- Luxury Crypter.exe (PID: 6800)
Starts a Microsoft application from unusual location
- ILMerge.exe (PID: 6476)
- ILMerge.exe (PID: 1068)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 1048)
The process executes VB scripts
- Luxury Crypter.exe (PID: 6268)
Creates a Folder object (SCRIPT)
- cscript.exe (PID: 1048)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 1048)
Executing commands from ".cmd" file
- msedgewebview2.exe (PID: 2360)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6908)
Starts CMD.EXE for commands execution
- msedgewebview2.exe (PID: 2360)
Starts itself from another location
- msedgewebview2.exe (PID: 2360)
INFO
Checks supported languages
- Luxury Crypter.exe (PID: 6800)
- Luxury Crypter.exe (PID: 6268)
- svchost.exe (PID: 5584)
- msedgewebview2.exe (PID: 2360)
- ILMerge.exe (PID: 6476)
- msedgewebview2.exe (PID: 1172)
- Luxury Crypter.exe (PID: 3772)
- Luxury Crypter.exe (PID: 7120)
- msedgewebview2.exe (PID: 6820)
- ILMerge.exe (PID: 1068)
- svchost.exe (PID: 5444)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6424)
The process uses the downloaded file
- WinRAR.exe (PID: 6424)
- Luxury Crypter.exe (PID: 6800)
- Luxury Crypter.exe (PID: 6268)
- Luxury Crypter.exe (PID: 3772)
- Luxury Crypter.exe (PID: 7120)
- msedgewebview2.exe (PID: 2360)
Reads the machine GUID from the registry
- Luxury Crypter.exe (PID: 6800)
- svchost.exe (PID: 5584)
- Luxury Crypter.exe (PID: 6268)
- ILMerge.exe (PID: 6476)
- msedgewebview2.exe (PID: 1172)
- Luxury Crypter.exe (PID: 3772)
- svchost.exe (PID: 5444)
- Luxury Crypter.exe (PID: 7120)
- ILMerge.exe (PID: 1068)
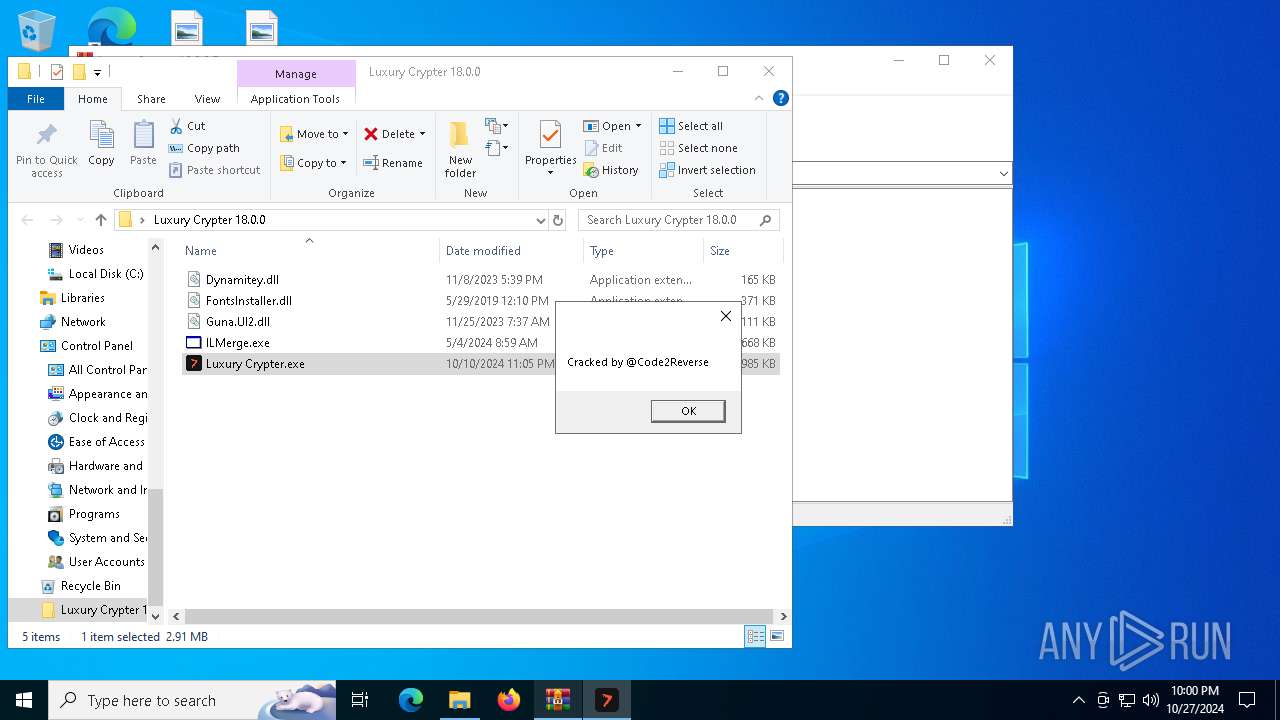
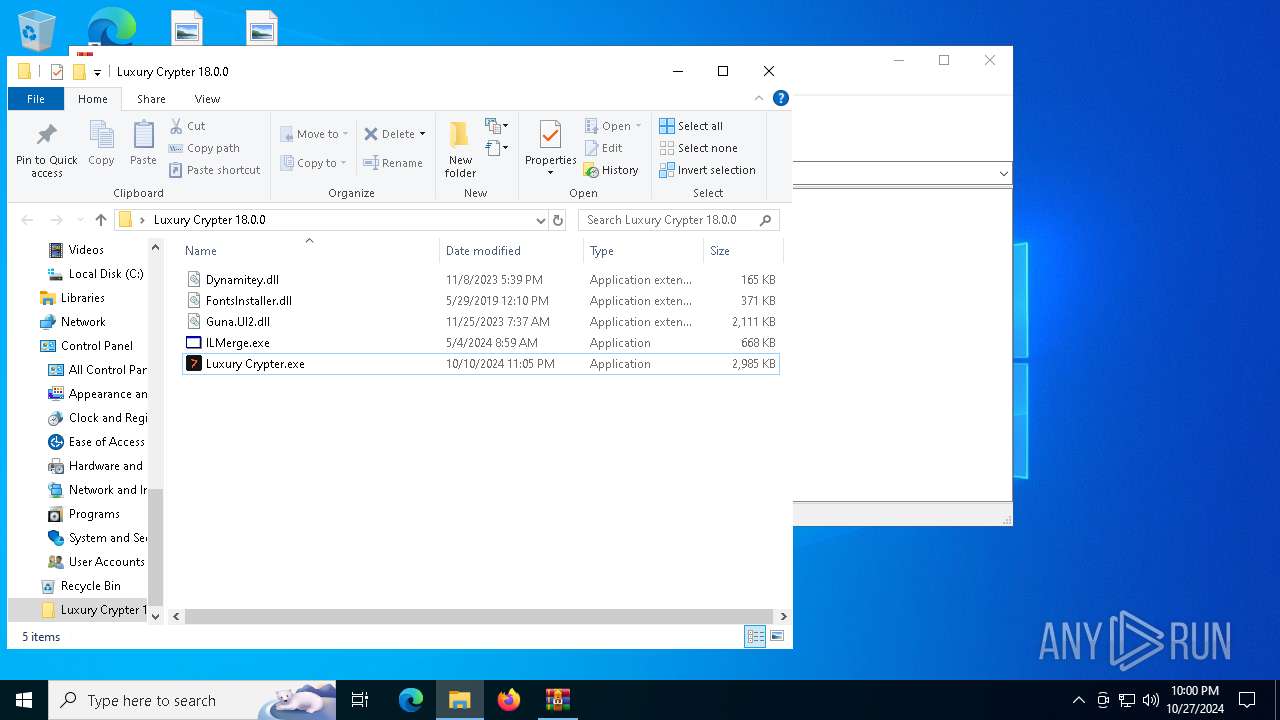
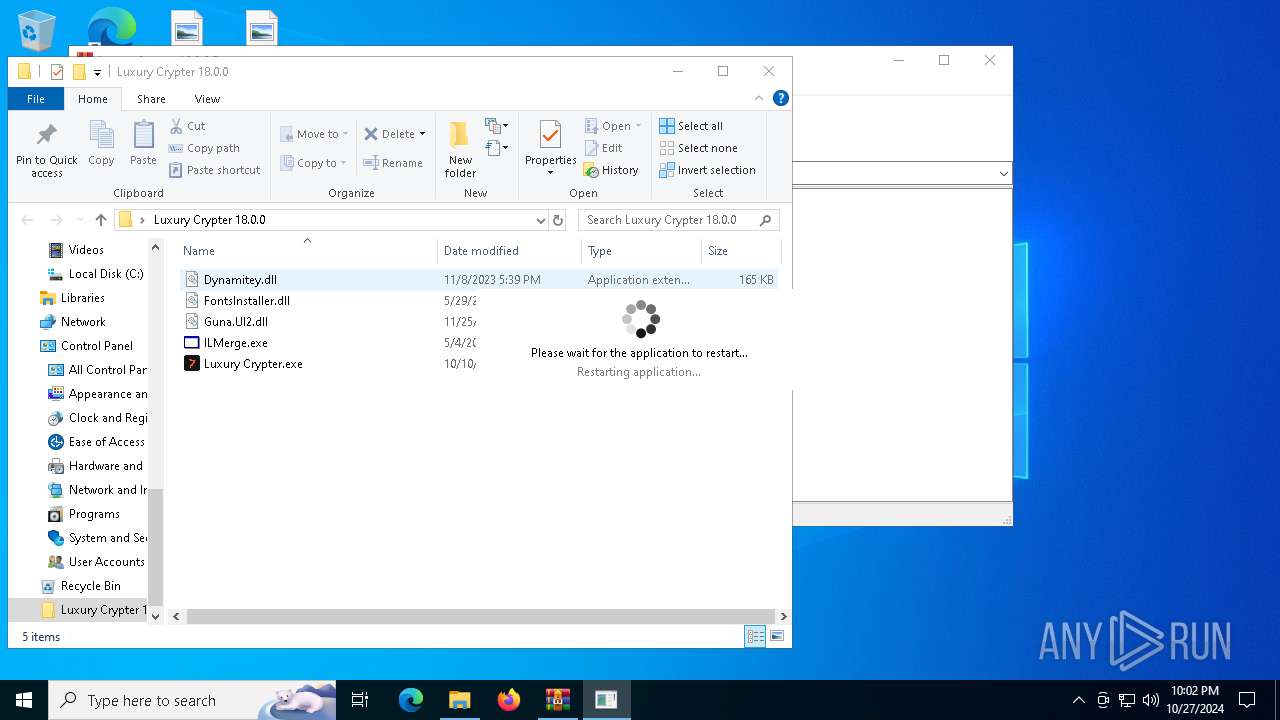
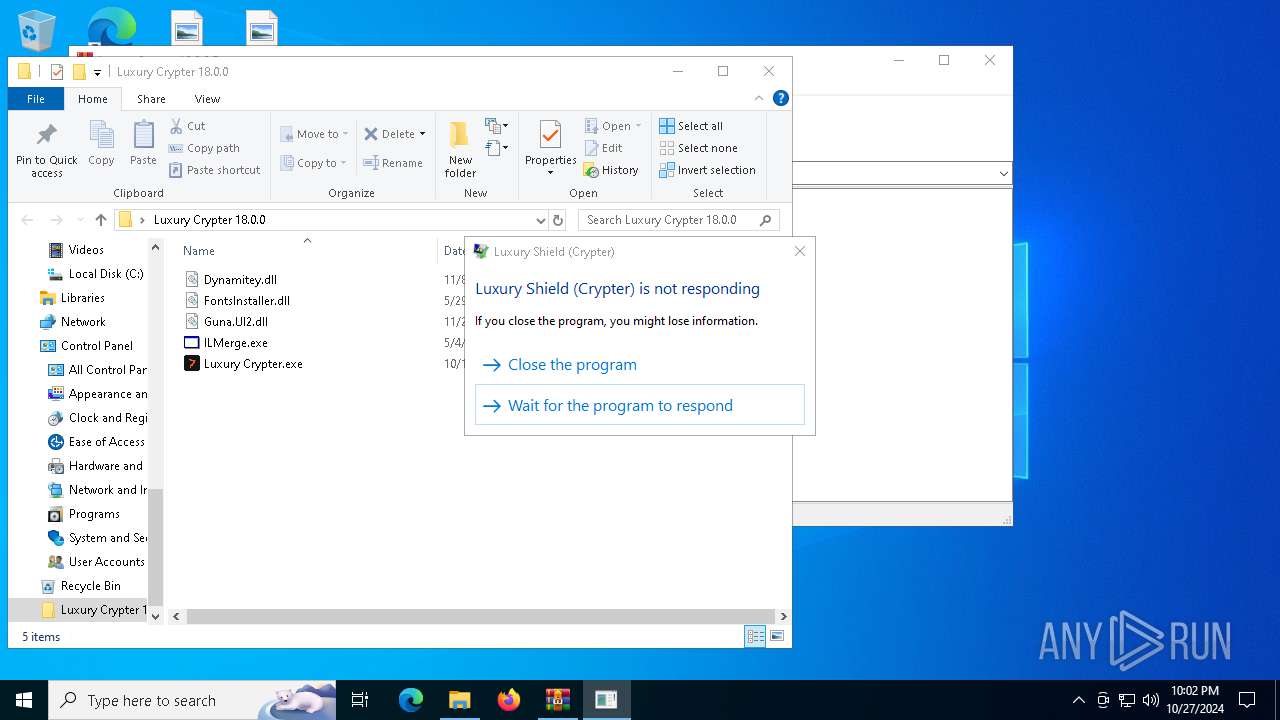
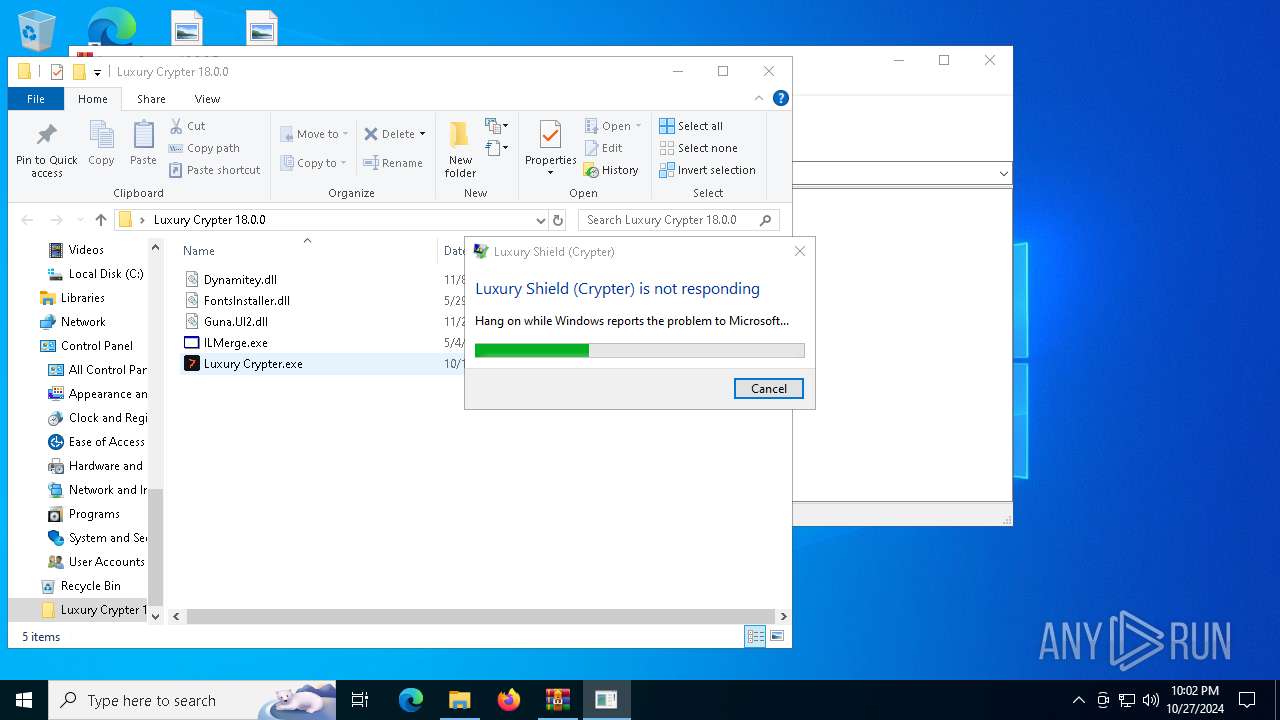
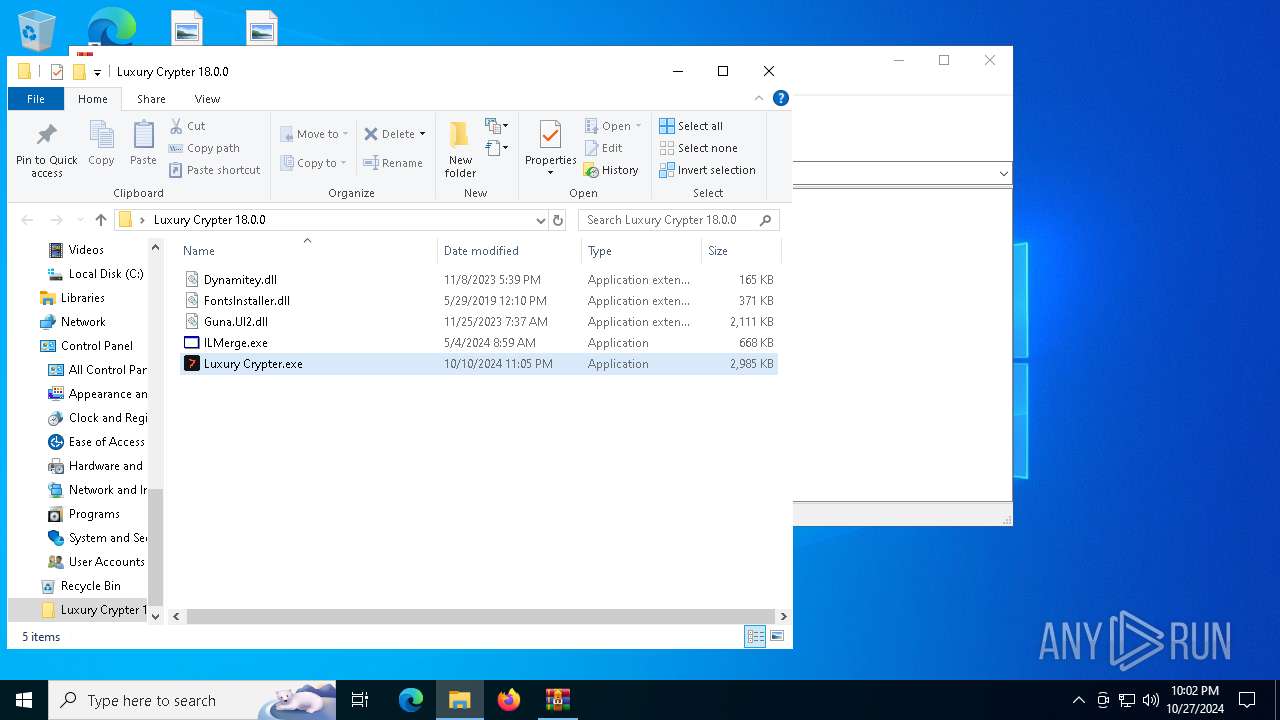
Manual execution by a user
- Luxury Crypter.exe (PID: 6800)
- Luxury Crypter.exe (PID: 3772)
Reads the computer name
- Luxury Crypter.exe (PID: 6800)
- svchost.exe (PID: 5584)
- Luxury Crypter.exe (PID: 6268)
- msedgewebview2.exe (PID: 2360)
- msedgewebview2.exe (PID: 1172)
- ILMerge.exe (PID: 6476)
- Luxury Crypter.exe (PID: 3772)
- Luxury Crypter.exe (PID: 7120)
- msedgewebview2.exe (PID: 6820)
- svchost.exe (PID: 5444)
- ILMerge.exe (PID: 1068)
Process checks computer location settings
- Luxury Crypter.exe (PID: 6800)
- Luxury Crypter.exe (PID: 6268)
- msedgewebview2.exe (PID: 2360)
- Luxury Crypter.exe (PID: 3772)
- Luxury Crypter.exe (PID: 7120)
Creates files or folders in the user directory
- Luxury Crypter.exe (PID: 6800)
- svchost.exe (PID: 5584)
- msedgewebview2.exe (PID: 2360)
- Luxury Crypter.exe (PID: 6268)
- cscript.exe (PID: 1048)
- Luxury Crypter.exe (PID: 7120)
Sends debugging messages
- Luxury Crypter.exe (PID: 6268)
- Luxury Crypter.exe (PID: 7120)
Reads Environment values
- svchost.exe (PID: 5584)
Creates files in the program directory
- Luxury Crypter.exe (PID: 6800)
Checks proxy server information
- svchost.exe (PID: 5584)
- cscript.exe (PID: 1048)
- slui.exe (PID: 1244)
Reads the software policy settings
- svchost.exe (PID: 5584)
- cscript.exe (PID: 1048)
- slui.exe (PID: 6448)
Disables trace logs
- svchost.exe (PID: 5584)
Create files in a temporary directory
- svchost.exe (PID: 5584)
- Luxury Crypter.exe (PID: 6268)
- msedgewebview2.exe (PID: 2360)
- Luxury Crypter.exe (PID: 7120)
Attempting to use instant messaging service
- svchost.exe (PID: 5584)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7004)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7004)
Reads security settings of Internet Explorer
- cscript.exe (PID: 1048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (gen) (100) |
|---|
EXIF
ZIP
| FileVersion: | 7z v0.03 |
|---|---|
| ModifyDate: | 2023:11:08 17:39:22+00:00 |
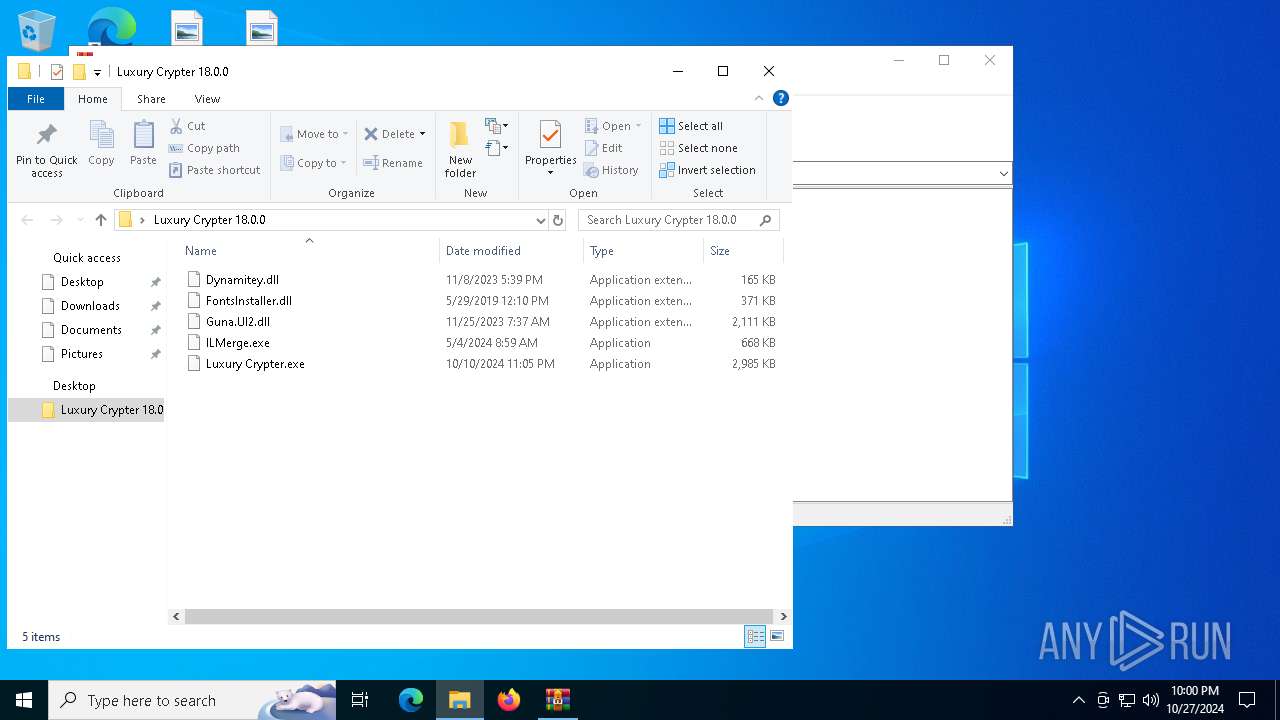
| ArchivedFileName: | Luxury Crypter 18.0.0/Dynamitey.dll |
Total processes
166
Monitored processes
27
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
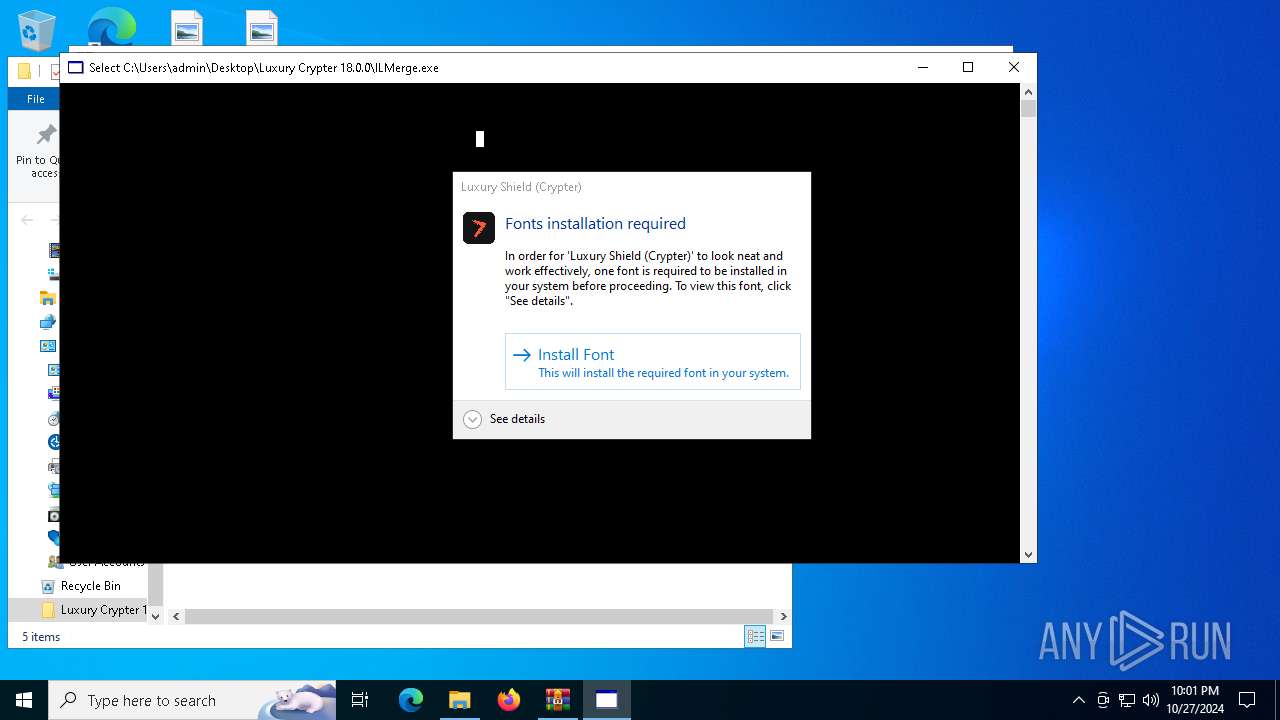
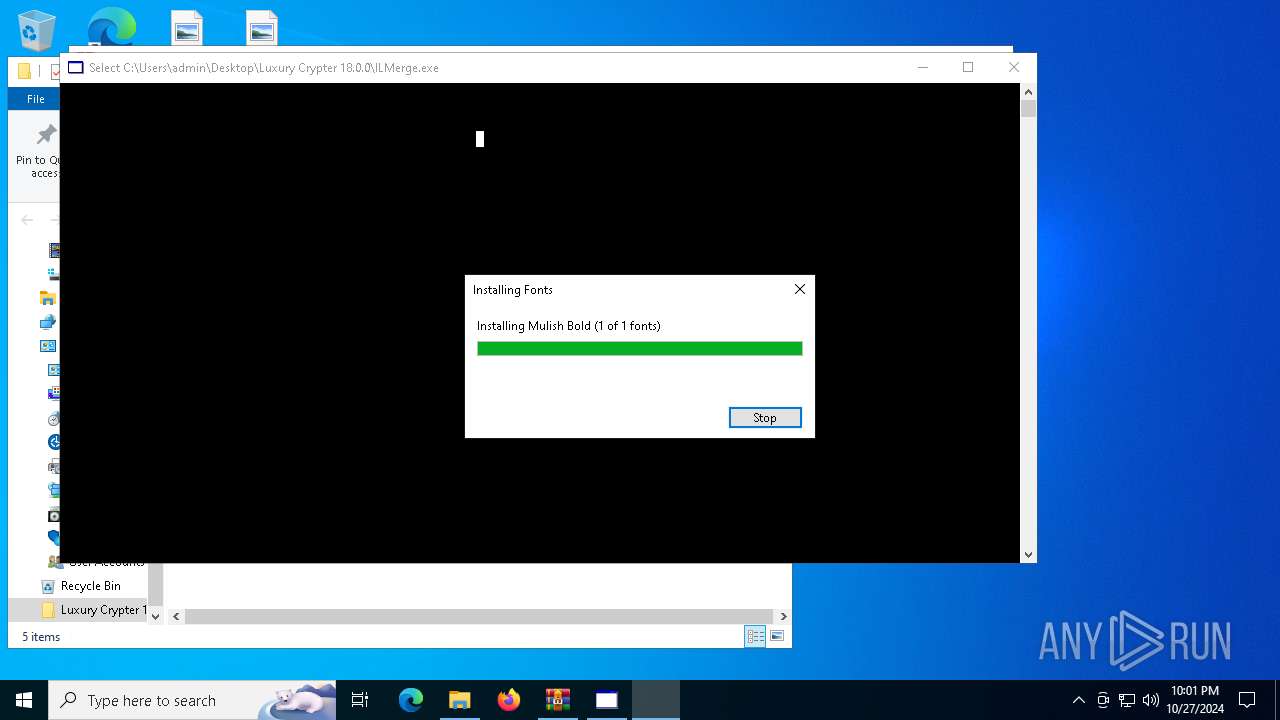
| 1048 | "C:\Windows\System32\cscript.exe" "C:\Users\admin\AppData\Roaming\WK.Libraries.FontsInstaller\\Unavailable\Installer.vbs" | C:\Windows\SysWOW64\cscript.exe | Luxury Crypter.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1068 | "C:\Users\admin\Desktop\Luxury Crypter 18.0.0\ILMerge.exe" | C:\Users\admin\Desktop\Luxury Crypter 18.0.0\ILMerge.exe | — | Luxury Crypter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ILMerge Exit code: 0 Version: 2.11.1103.0 Modules
| |||||||||||||||
| 1172 | "C:\Users\admin\AppData\Local\msedgewebview2\msedgewebview2.exe" | C:\Users\admin\AppData\Local\msedgewebview2\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 128.0.2739.79 Modules
| |||||||||||||||
| 1244 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2076 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2132 | "schtasks.exe" /create /tn msedgewebview2 /tr "C:\Users\admin\AppData\Local\msedgewebview2\msedgewebview2.exe" /st 22:05 /du 23:59 /sc daily /ri 1 /f | C:\Windows\System32\schtasks.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2360 | "C:\ProgramData\msedgewebview2.exe" | C:\ProgramData\msedgewebview2.exe | Luxury Crypter.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Exit code: 0 Version: 128.0.2739.79 Modules
| |||||||||||||||
| 2816 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3772 | "C:\Users\admin\Desktop\Luxury Crypter 18.0.0\Luxury Crypter.exe" | C:\Users\admin\Desktop\Luxury Crypter 18.0.0\Luxury Crypter.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Luxury Shield (Crypter) Exit code: 0 Version: 18.0.0.0 Modules
| |||||||||||||||
Total events
16 896
Read events
16 886
Write events
10
Delete events
0
Modification events
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Luxury Crypter 18.0.0.7z | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6800) Luxury Crypter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (1048) cscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {BD84B380-8CA2-1069-AB1D-08000948F534} {000214E6-0000-0000-C000-000000000046} 0xFFFF |
Value: 010000000000000073623AB9BB28DB01 | |||
| (PID) Process: | (1048) cscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | write | Name: | Mulish Bold (TrueType) |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows\Fonts\Mulish.ttf | |||
| (PID) Process: | (3772) Luxury Crypter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
Executable files
8
Suspicious files
11
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6800 | Luxury Crypter.exe | C:\ProgramData\msedgewebview2.exe | — | |
MD5:— | SHA256:— | |||
| 6424 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6424.24353\Luxury Crypter 18.0.0\Dynamitey.dll | executable | |
MD5:BE2E56A09631590B126E7391C7452C48 | SHA256:DA043BD3A340F9155A54547E3BC379279D488E9BA56CE76076C5A5D6C26337A4 | |||
| 6424 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6424.24353\Luxury Crypter 18.0.0\Luxury Crypter.exe | executable | |
MD5:FFAF52E43618A09017BA3B764C5E205F | SHA256:4EFB2B692FD63845DC443F589F83D410905C7CF4A1013444D083120506A26076 | |||
| 7004 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_14gijyvx.hx1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2360 | msedgewebview2.exe | C:\Users\admin\AppData\Local\msedgewebview2\msedgewebview2.exe | — | |
MD5:— | SHA256:— | |||
| 5584 | svchost.exe | C:\Users\admin\AppData\Local\Temp\Log.tmp | text | |
MD5:AAD3FF66C9C718A37CF6686A04547F73 | SHA256:F242A9C5E845F14F001583D97A4F5792B0AFB10790B2C59E95DCA77C57F5D9ED | |||
| 6268 | Luxury Crypter.exe | C:\Users\admin\AppData\Roaming\WK.Libraries.FontsInstaller\Mulish.ttf | binary | |
MD5:987E18DFFD501E760AFDBEA36A4DBEED | SHA256:0D12A5128D541738D925CC8DDA9630BE3FD808AB8C04F19A8B83BCDEBF64498A | |||
| 2360 | msedgewebview2.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\msedgewebview2.exe.lnk | binary | |
MD5:9F8ED7BAD99C87EE24DD910F419835A8 | SHA256:45990FCB3000525CD898696B21F1DC9518EC6A9E56857D3C15334C43DD785DF9 | |||
| 7004 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:99F80371E7C8BC4393DFF869079DBF3E | SHA256:2DFC3CF86334399180BA700C11F3DC58330BA5079EBE2F8F53D29C70C241EFC1 | |||
| 6268 | Luxury Crypter.exe | C:\Users\admin\AppData\Roaming\WK.Libraries.FontsInstaller\Unavailable\Installer.vbs | text | |
MD5:F3040D44A71F07E4117DBF0755391D90 | SHA256:590538E3897A340F3E9549155F93152AFAF378D2CBEE8027D3FB23BF5265A475 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
53
DNS requests
31
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1552 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3944 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4380 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6852 | WerFault.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1048 | cscript.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSPwl%2BrBFlJbvzLXU1bGW08VysJ2wQUj%2Bh%2B8G0yagAFI8dwl2o6kP9r6tQCEArpX67NvgTIijrRFeb33aI%3D | unknown | — | — | whitelisted |
4380 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6852 | WerFault.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
864 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 104.126.37.155:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1552 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
5584 | svchost.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
5584 | svchost.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
5584 | svchost.exe | Misc activity | ET SCAN Behavioral Unusually fast Terminal Server Traffic Potential Scan or Infection (Outbound) |