| File name: | 123.bat |
| Full analysis: | https://app.any.run/tasks/0417aa2c-f3a3-4916-b802-62b3fa99220b |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 13:11:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines |
| MD5: | F30C877EAAB4EF0DCD295F4AFBB20667 |
| SHA1: | CF1C9BE75B53A44EB782ED31884F681A173BA5EE |
| SHA256: | 124806F14ACA720592AD081B129CED5B0D6232FDB5F8DA4A50EF4CB883AF9CB1 |
| SSDEEP: | 24:IJtUwe/wegbweIwe0wweahYzwejweiAweJ4bwZGzwe/wepwLFwe69rweFkweF6Oo:IIwe/weqweIwe0wwesYzwejweJweObwS |
MALICIOUS
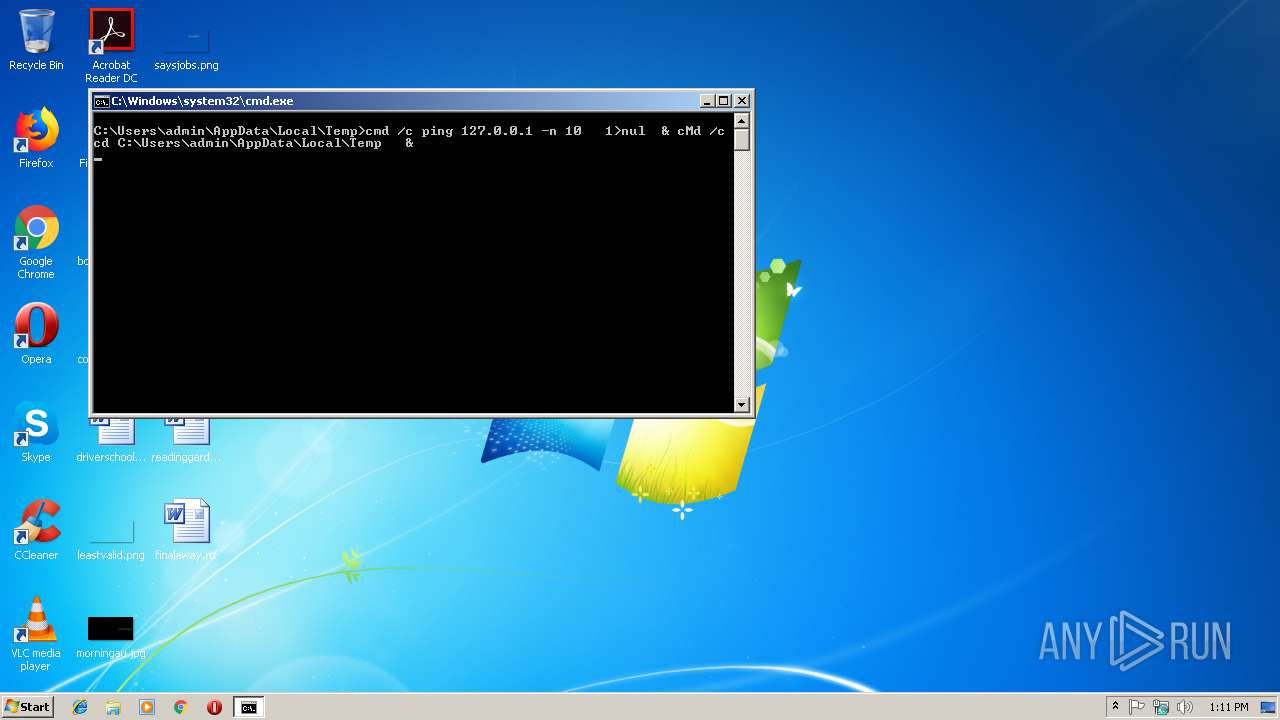
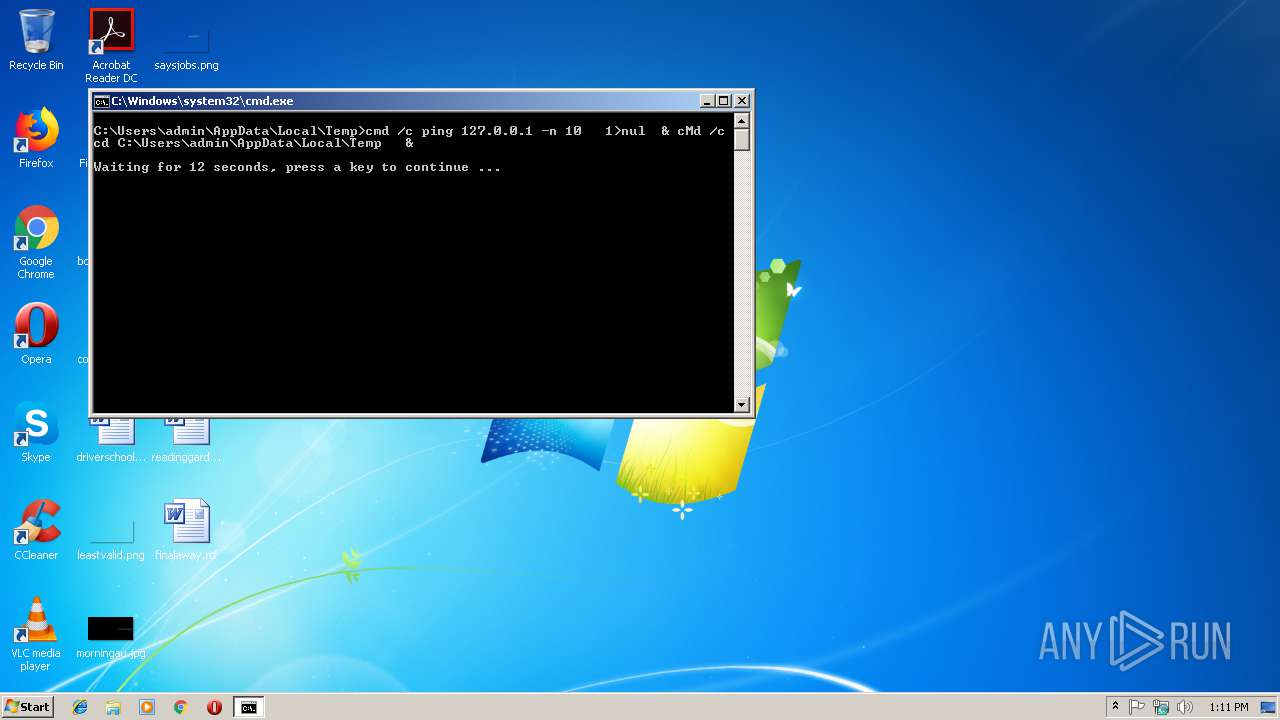
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3928)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 3132)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3132)
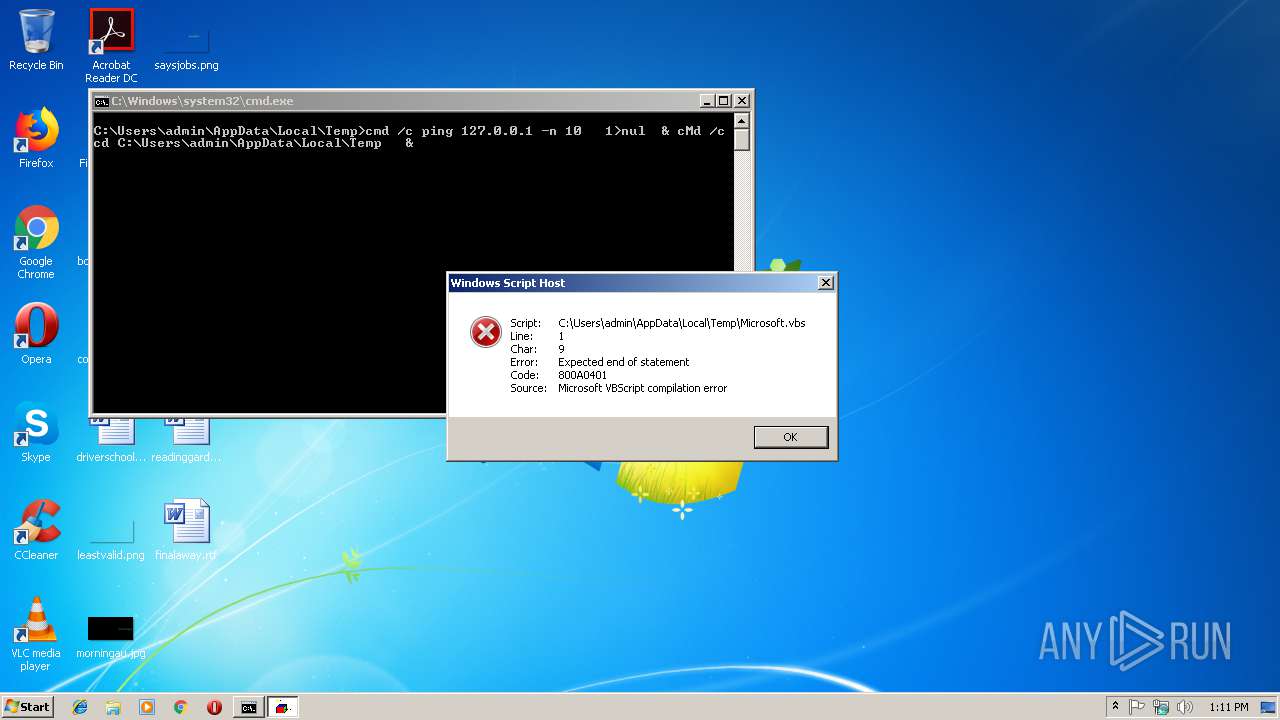
Executes scripts
- cmd.exe (PID: 3132)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1920 | ping 127.0.0.1 -n 10 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2080 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Microsoft.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3132 | cmd /c ""C:\Users\admin\AppData\Local\Temp\123.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3228 | timeout 12 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3284 | cMd /c cd C:\Users\admin\AppData\Local\Temp | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3928 | cmd /c ping 127.0.0.1 -n 10 | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
382
Read events
378
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3132) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3132) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3132 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Microsoft.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report