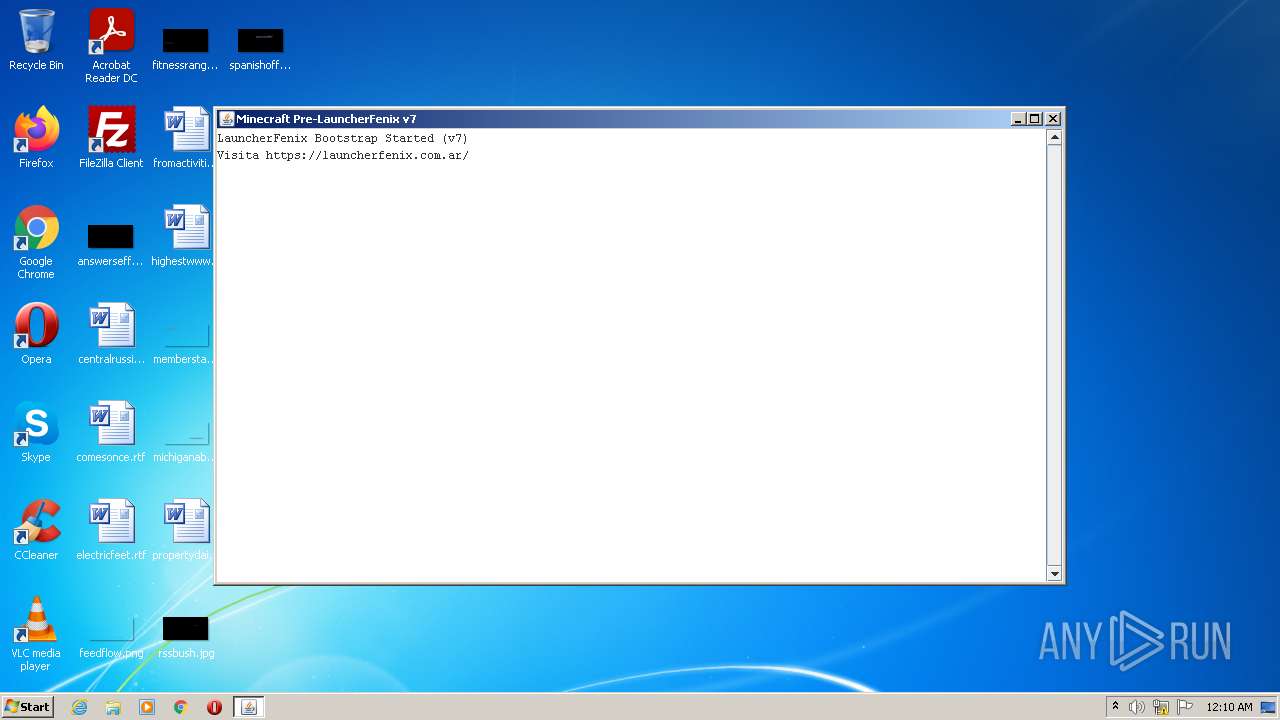
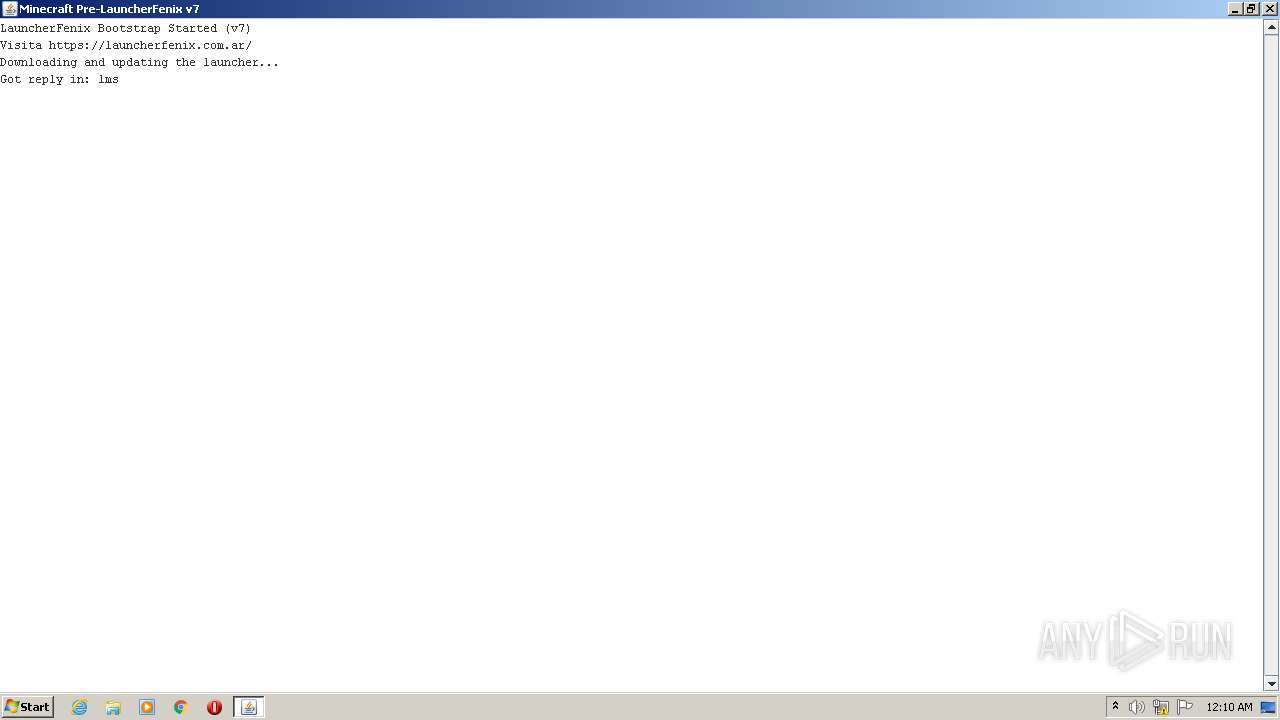
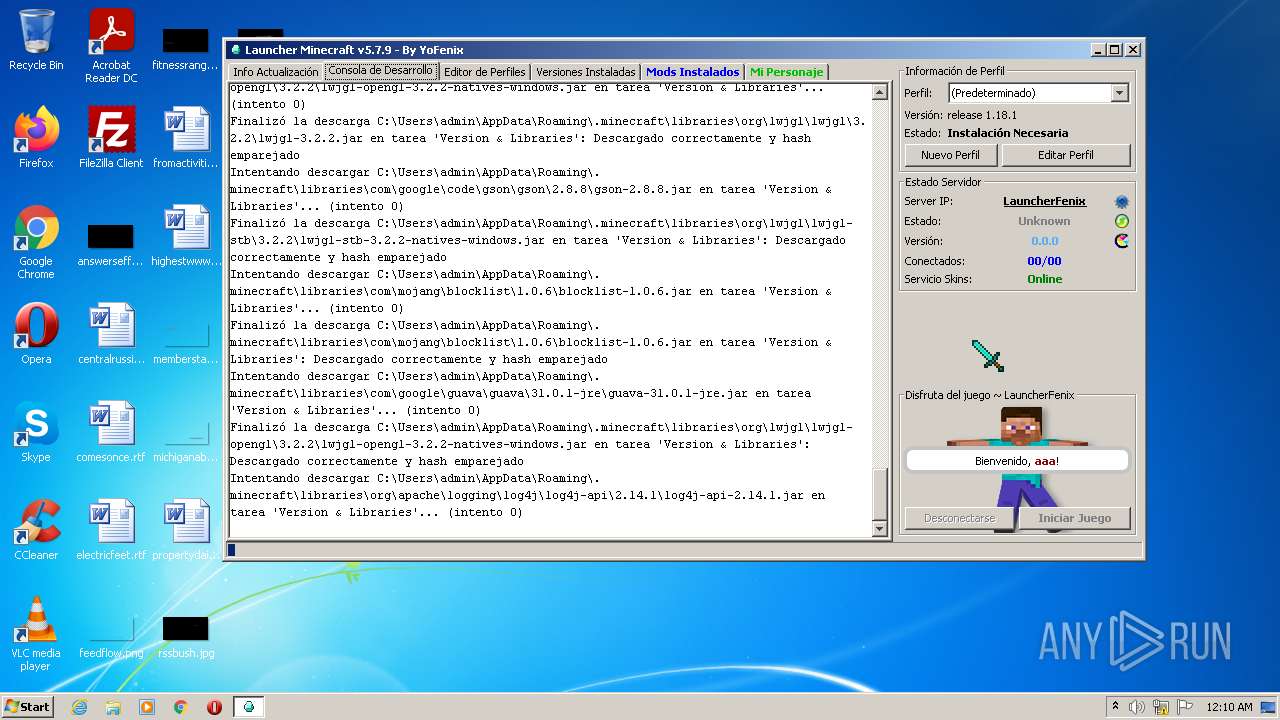
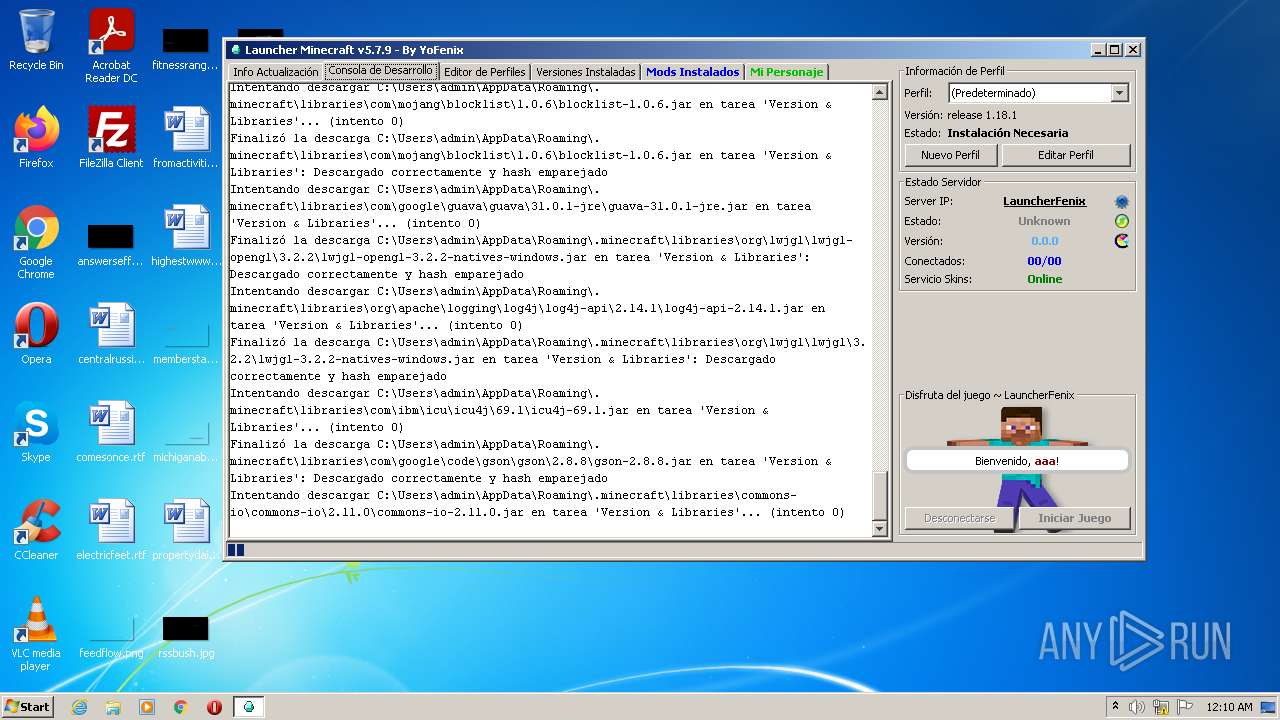
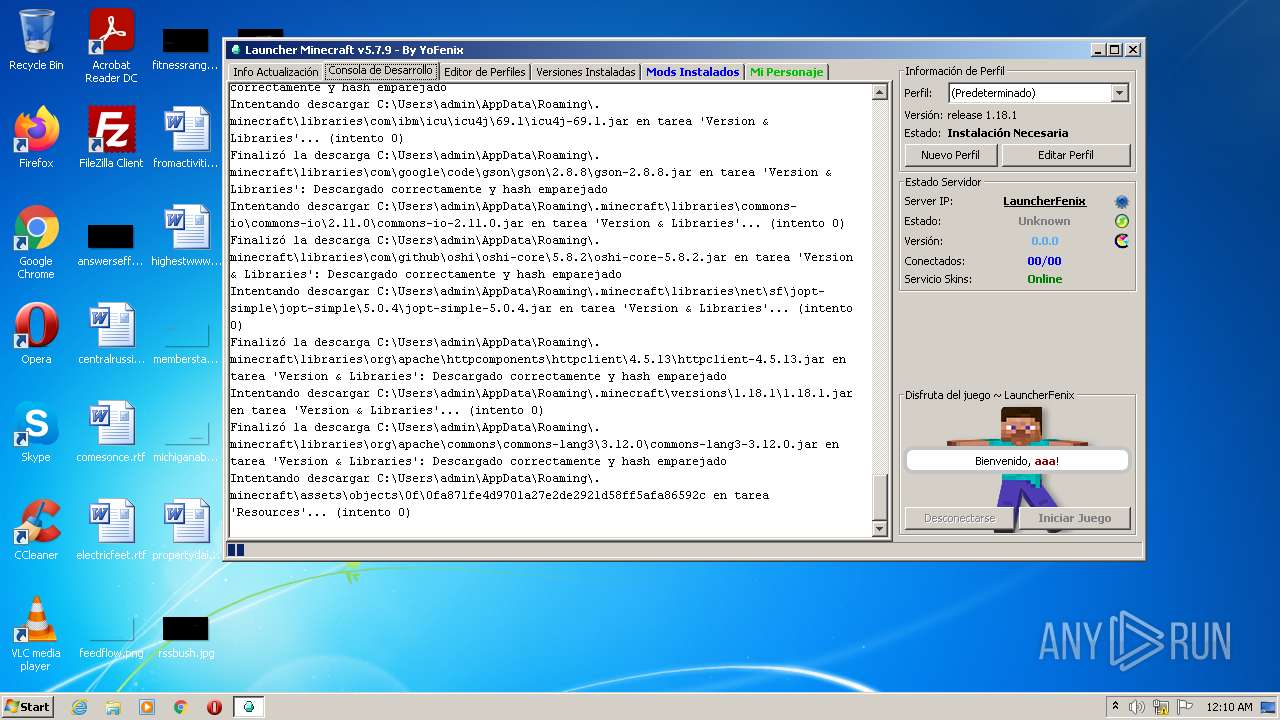
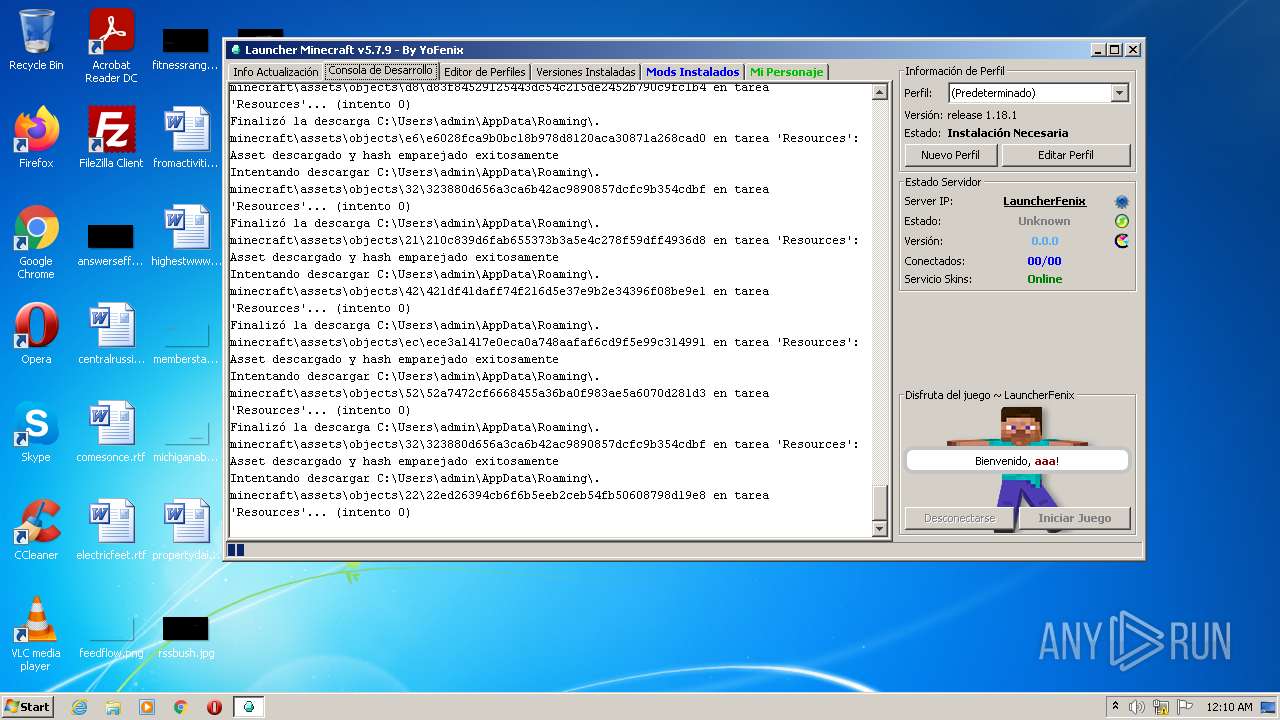
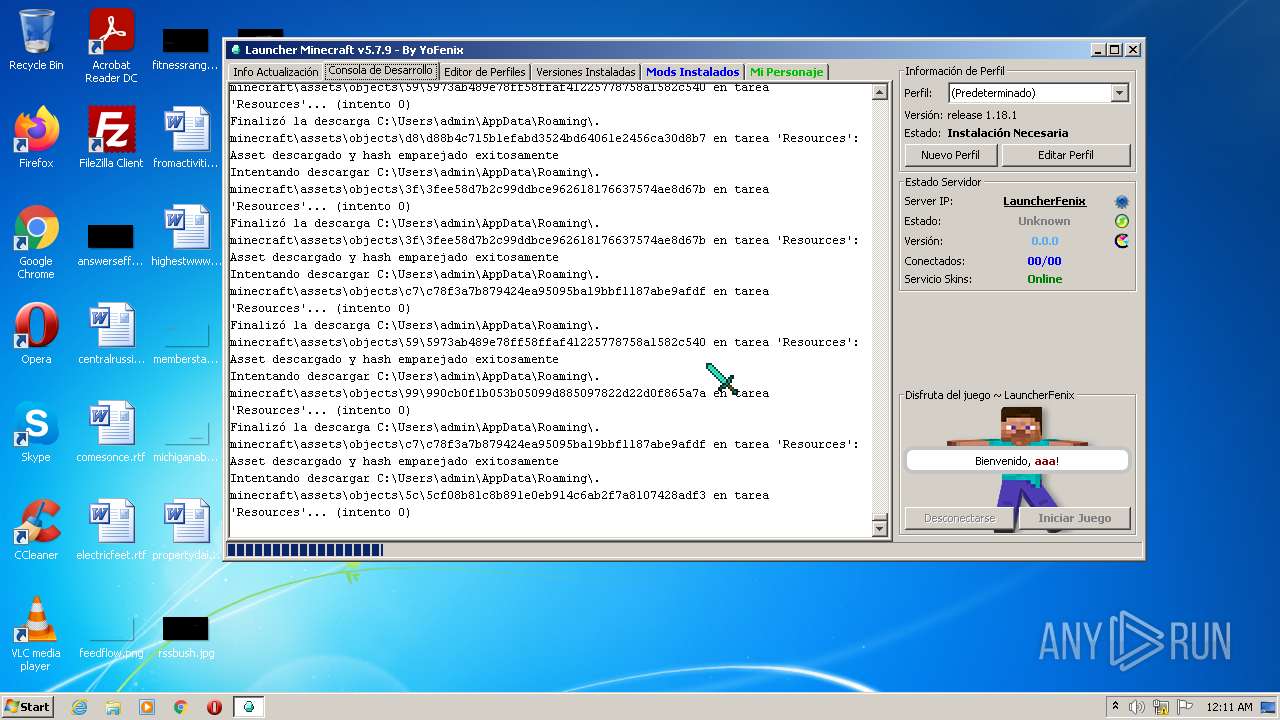
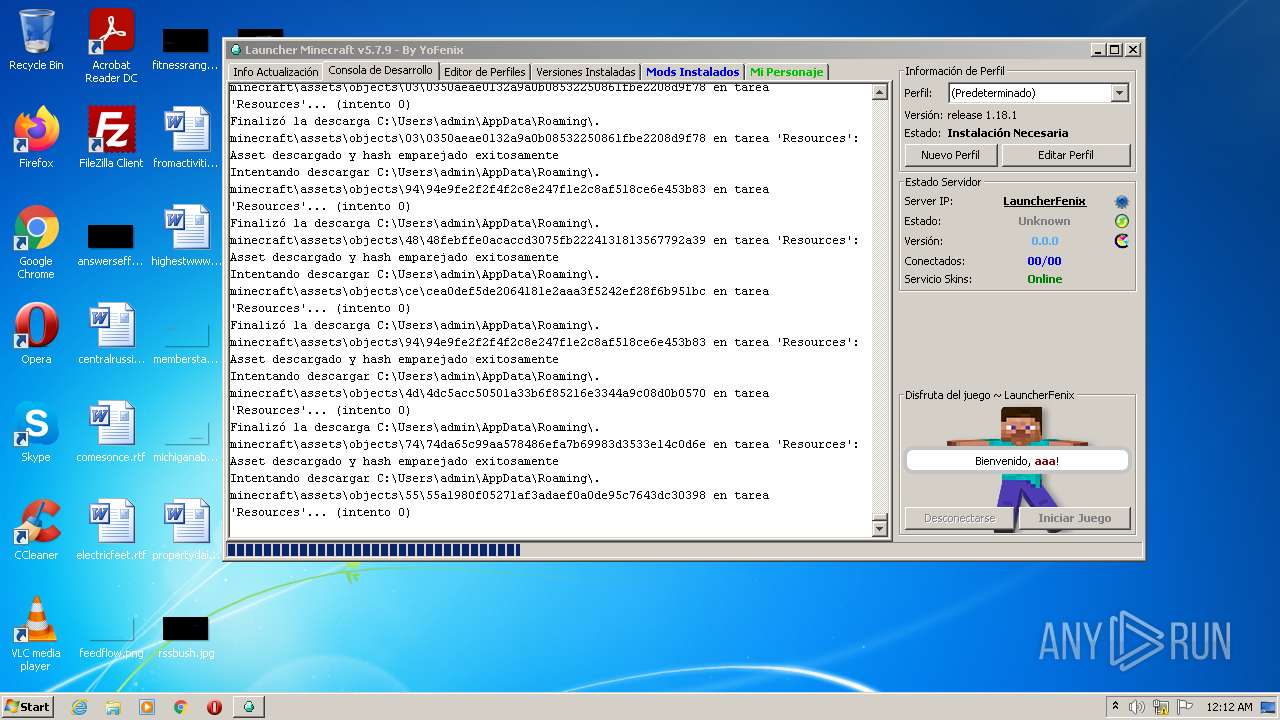
| download: | LauncherFenix-Minecraft-v7.exe |
| Full analysis: | https://app.any.run/tasks/b30b8e8e-3c9c-411d-8f47-ec6f928930f2 |
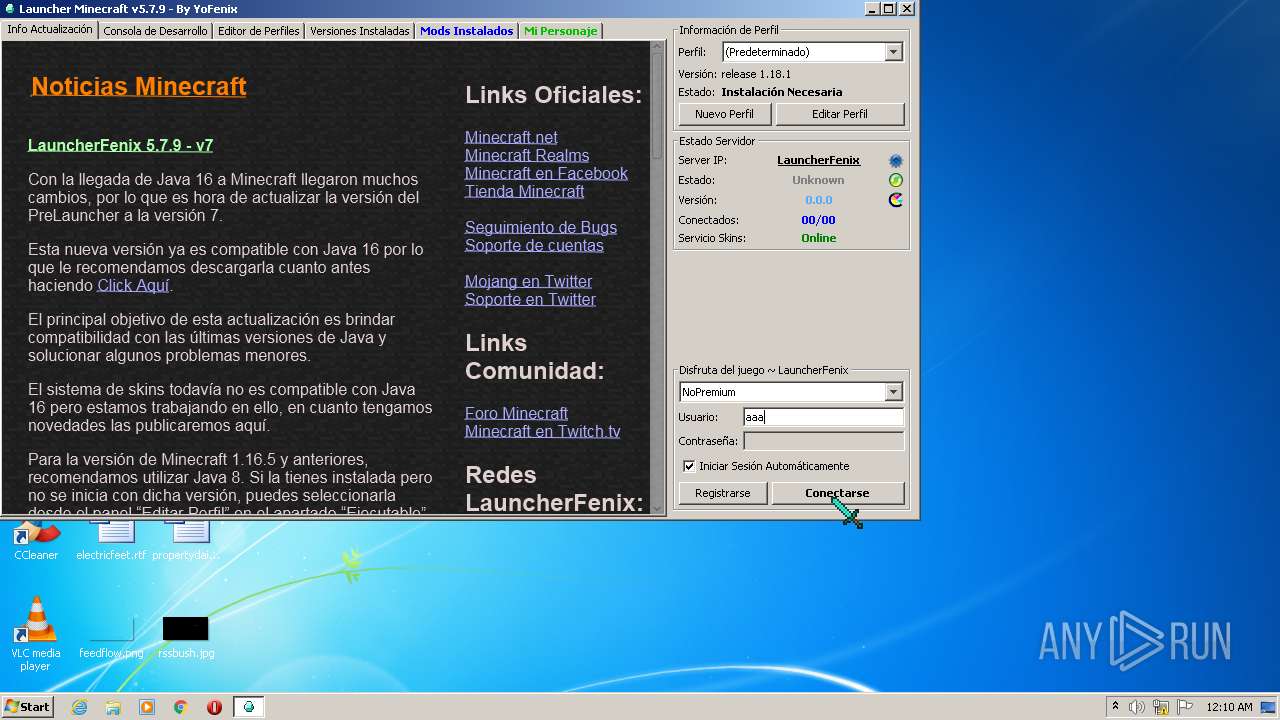
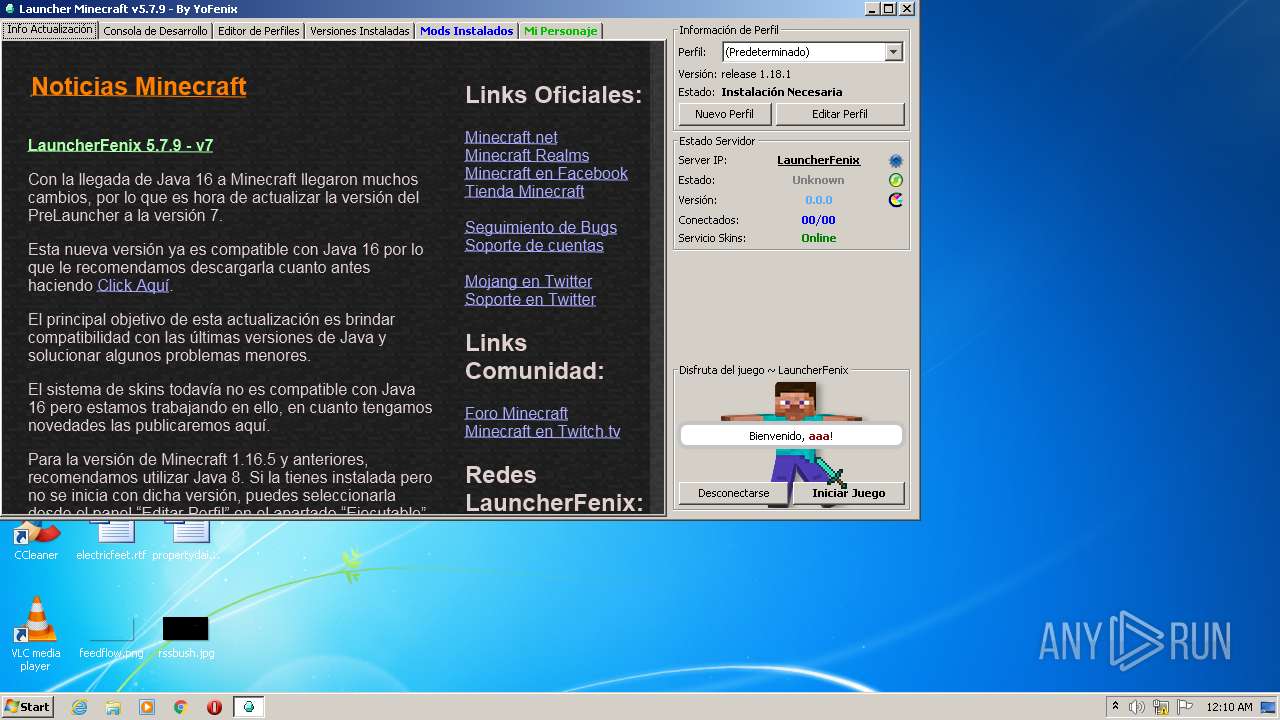
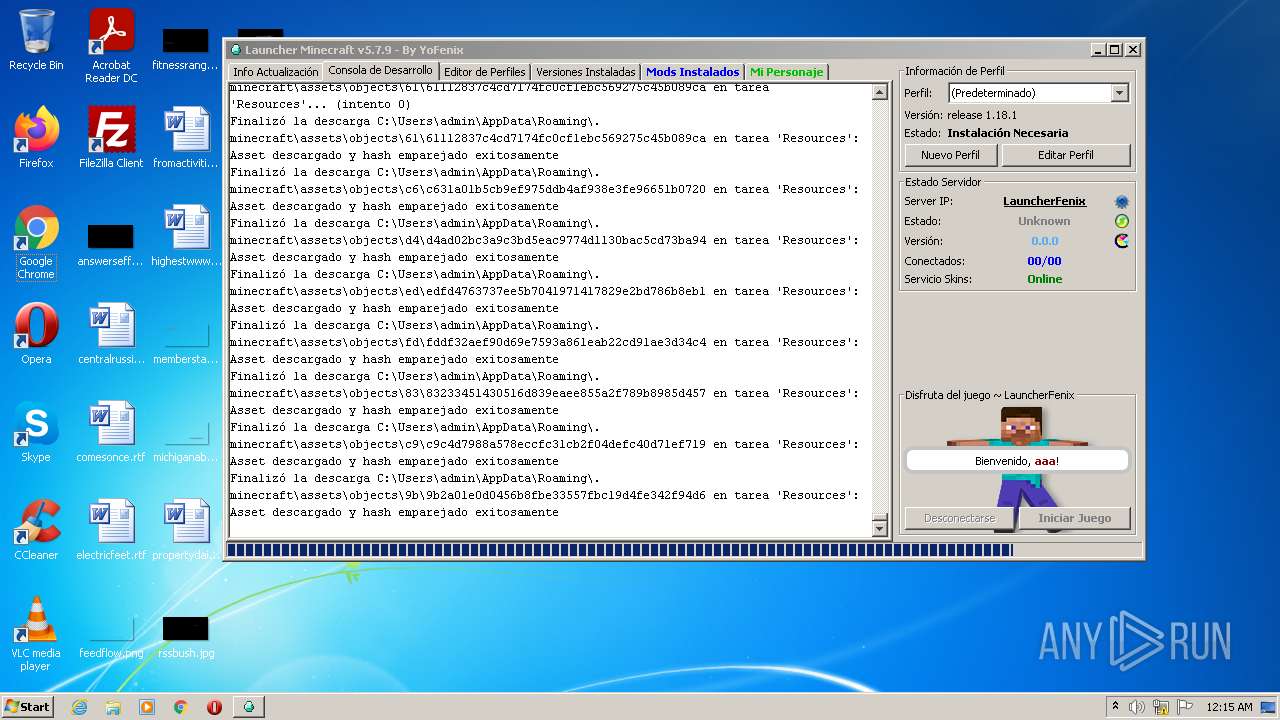
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2022, 00:10:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | D99BB55B57712065BC88BE297C1DA38C |
| SHA1: | FB6662DD31E8E5BE380FBD7A33A50A45953FE1E7 |
| SHA256: | 122BFBB9F67E355340991DEEACB167BE9C12AD726B5A7C5779448DD0CC4AF0CB |
| SSDEEP: | 3072:puzvch1rugYc4wqYSRR756K7ItBjgXHUYCnlK:Wch1aIqYSRVM+unlK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- LauncherFenix-Minecraft-v7.exe (PID: 3652)
- javaw.exe (PID: 4084)
Check for Java to be installed
- LauncherFenix-Minecraft-v7.exe (PID: 3652)
Reads the computer name
- javaw.exe (PID: 4084)
Executes JAVA applets
- LauncherFenix-Minecraft-v7.exe (PID: 3652)
Creates files in the program directory
- javaw.exe (PID: 4084)
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 4084)
Creates files in the user directory
- javaw.exe (PID: 4084)
INFO
Checks supported languages
- icacls.exe (PID: 1800)
Reads the computer name
- icacls.exe (PID: 1800)
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 4084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 7.0.0.1 |
|---|---|
| ProductName: | LauncherFenix |
| OriginalFileName: | LauncherFenix Minecraft.exe |
| LegalTrademarks: | - |
| LegalCopyright: | © Fenix Projects |
| InternalName: | PreLauncherv7 |
| FileVersion: | 7.0.0.1 |
| FileDescription: | Minecraft Launcher |
| CompanyName: | FenixProjects |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 7.0.0.1 |
| FileVersionNumber: | 6.0.0.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x1590 |
| UninitializedDataSize: | 36352 |
| InitializedDataSize: | 315904 |
| CodeSize: | 23040 |
| LinkerVersion: | 2.22 |
| PEType: | PE32 |
| TimeStamp: | 2021:05:31 00:29:07+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-May-2021 22:29:07 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
| CompanyName: | FenixProjects |
| FileDescription: | Minecraft Launcher |
| FileVersion: | 7.0.0.1 |
| InternalName: | PreLauncherv7 |
| LegalCopyright: | © Fenix Projects |
| LegalTrademarks: | - |
| OriginalFilename: | LauncherFenix Minecraft.exe |
| ProductName: | LauncherFenix |
| ProductVersion: | 7.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 30-May-2021 22:29:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005970 | 0x00005A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.17063 |
.data | 0x00007000 | 0x00000010 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.11837 |
.rdata | 0x00008000 | 0x00000918 | 0x00000A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.27517 |
.eh_fram\x14\x11 | 0x00009000 | 0x00001114 | 0x00001200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.82235 |
.bss | 0x0000B000 | 0x00008DCC | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00014000 | 0x00000CC0 | 0x00000E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.91037 |
.CRT | 0x00015000 | 0x00000018 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0980042 |
.tls | 0x00016000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.231158 |
.rsrc | 0x00017000 | 0x0004A1EC | 0x0004A200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.81989 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.29834 | 792 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
4 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
5 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
6 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
7 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
8 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
10 | 3.48301 | 29 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
advapi32.dll |
kernel32.dll |
msvcrt.dll |
shell32.dll |
user32.dll |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
1
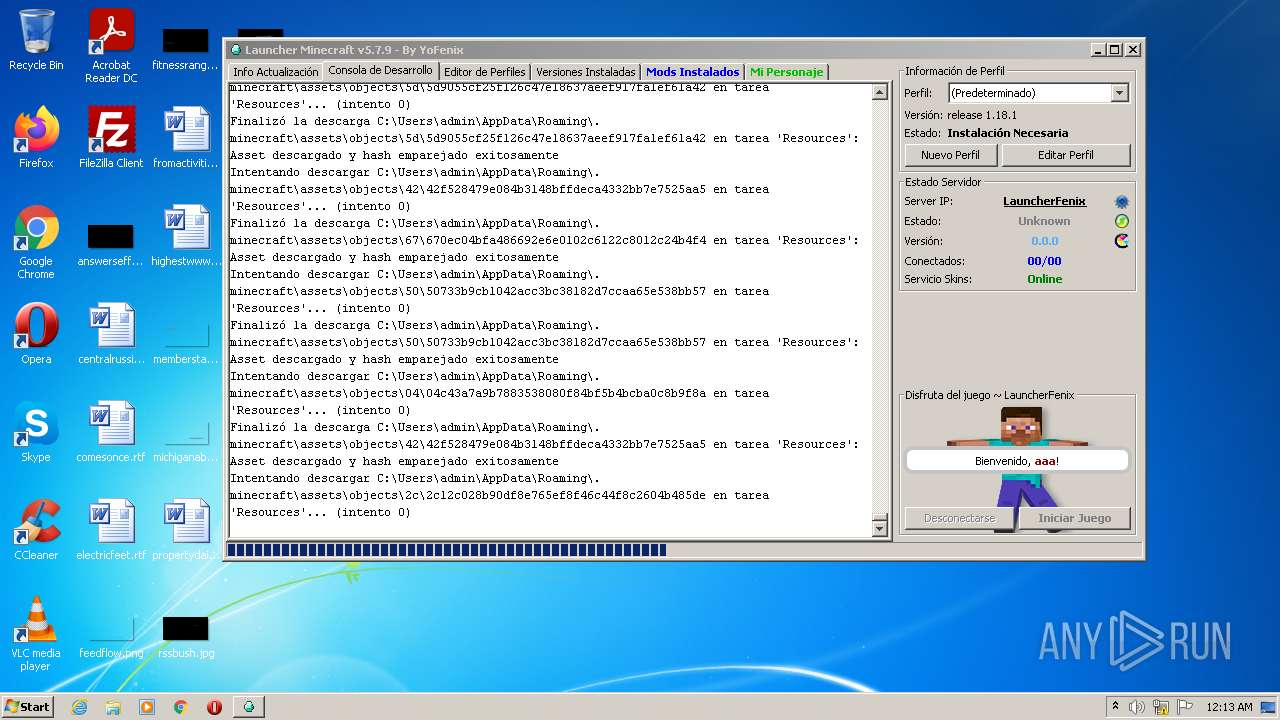
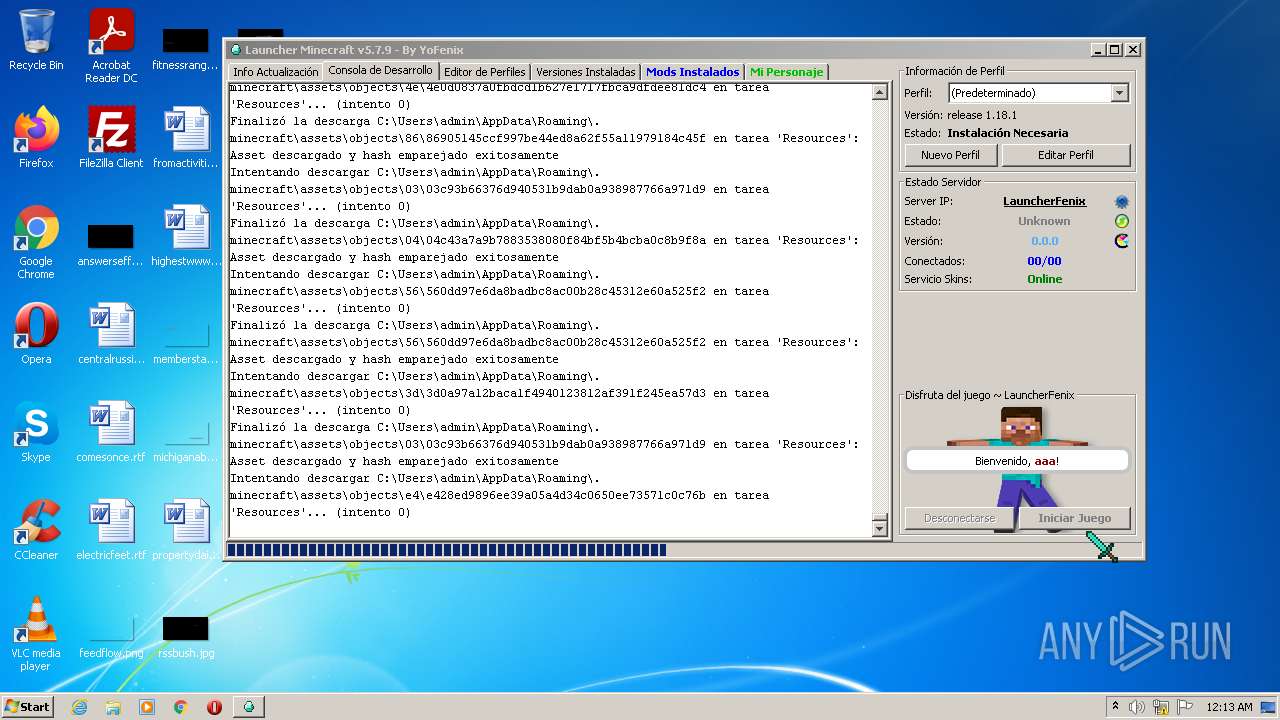
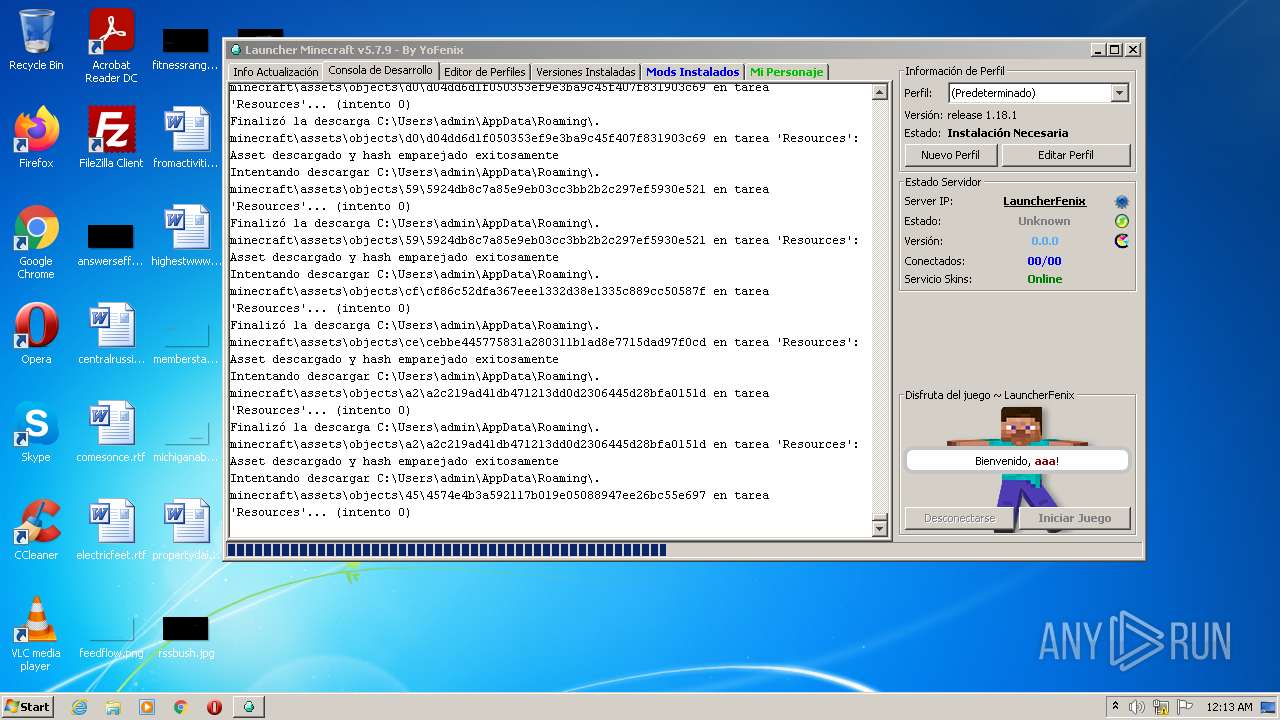
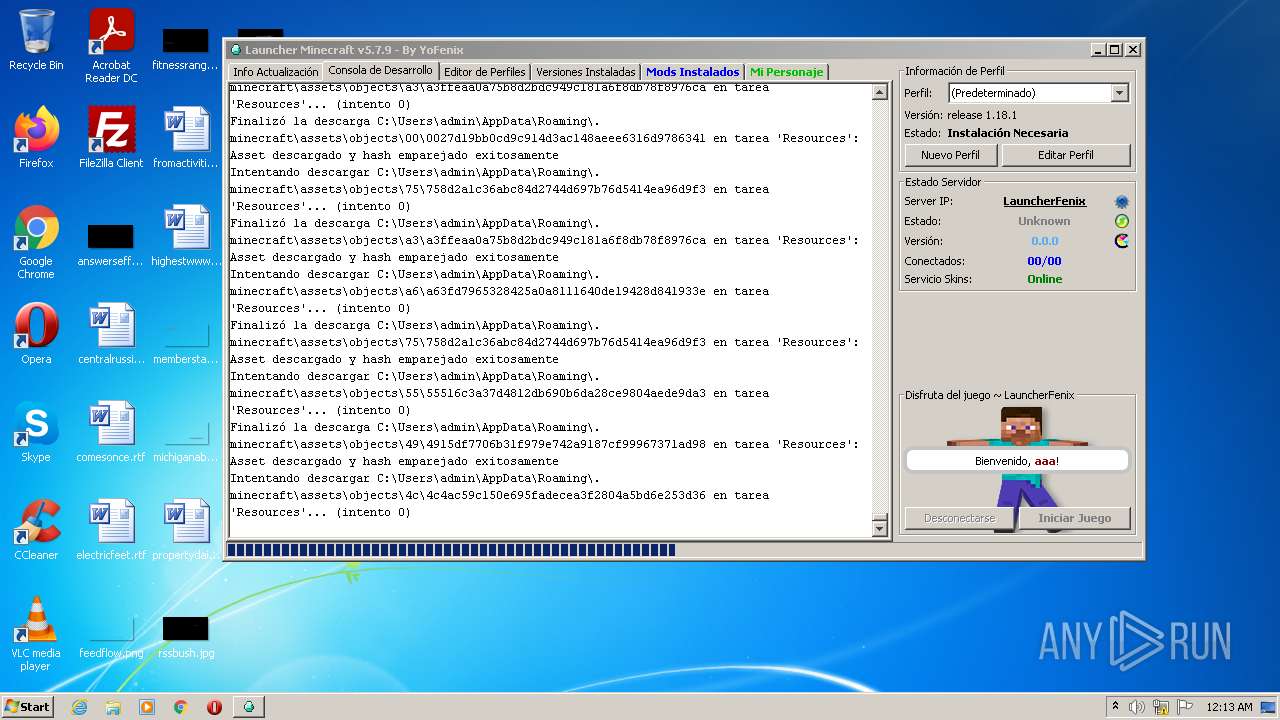
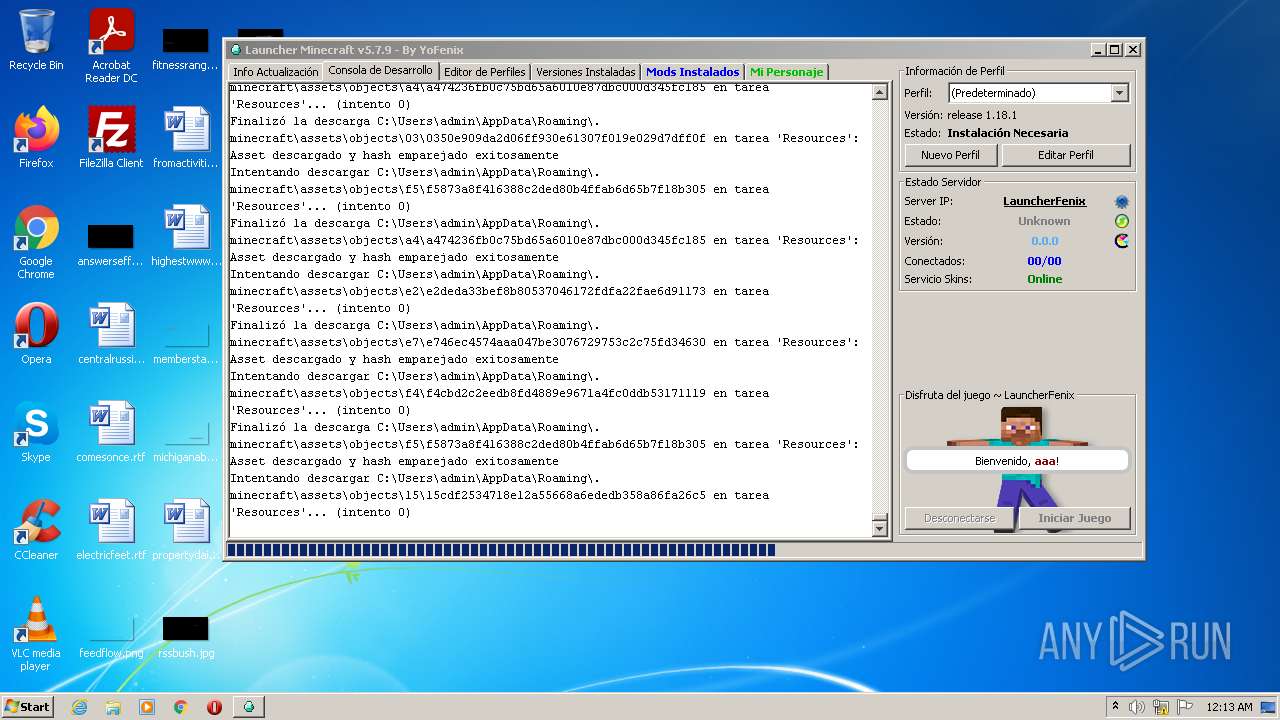
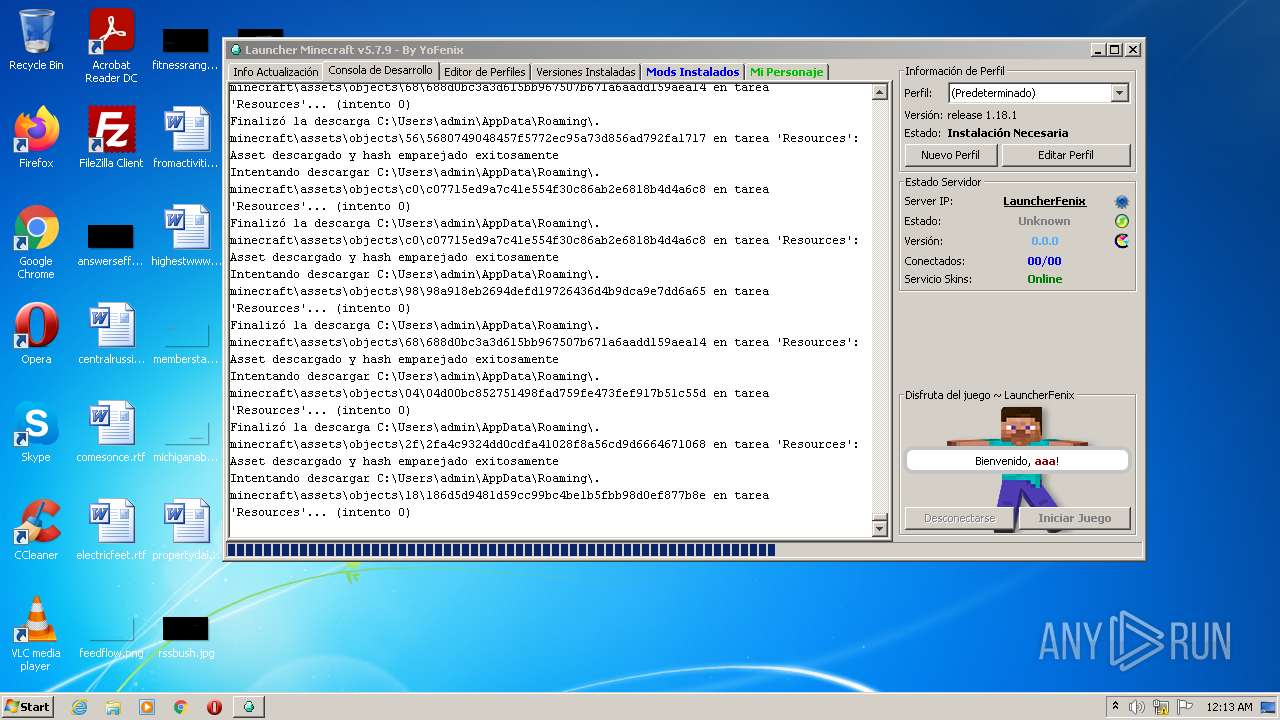
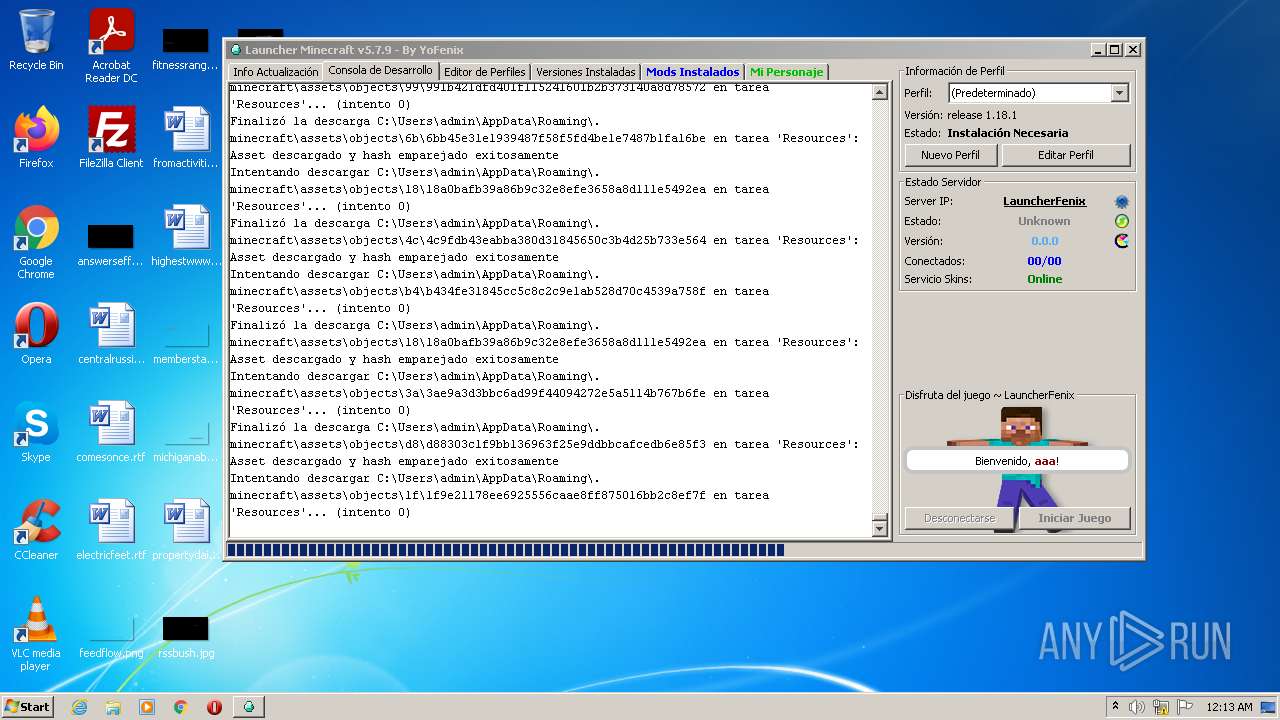
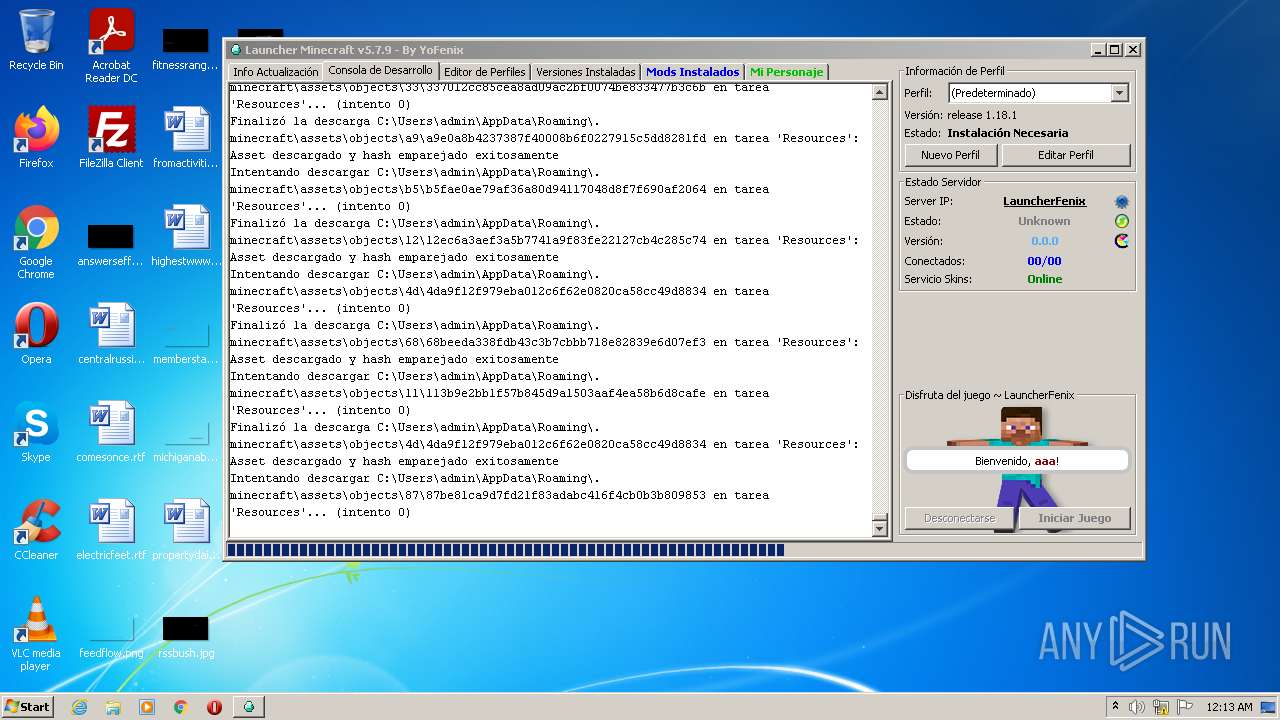
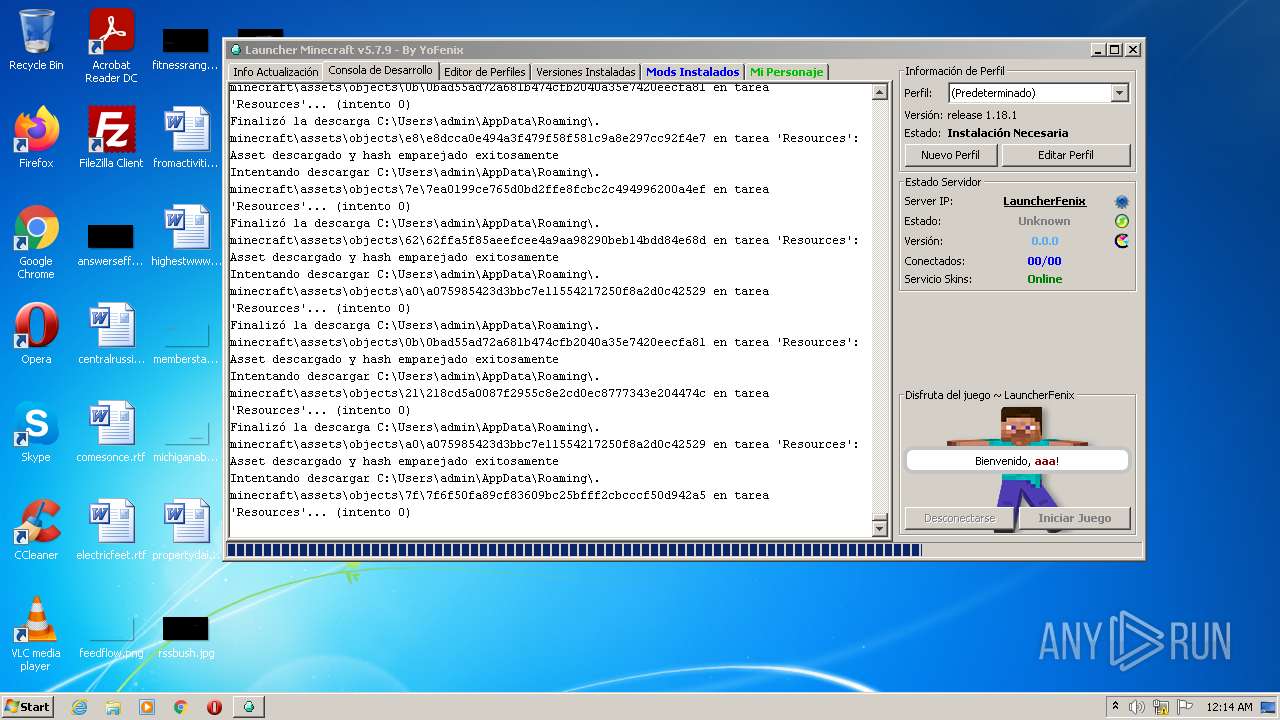
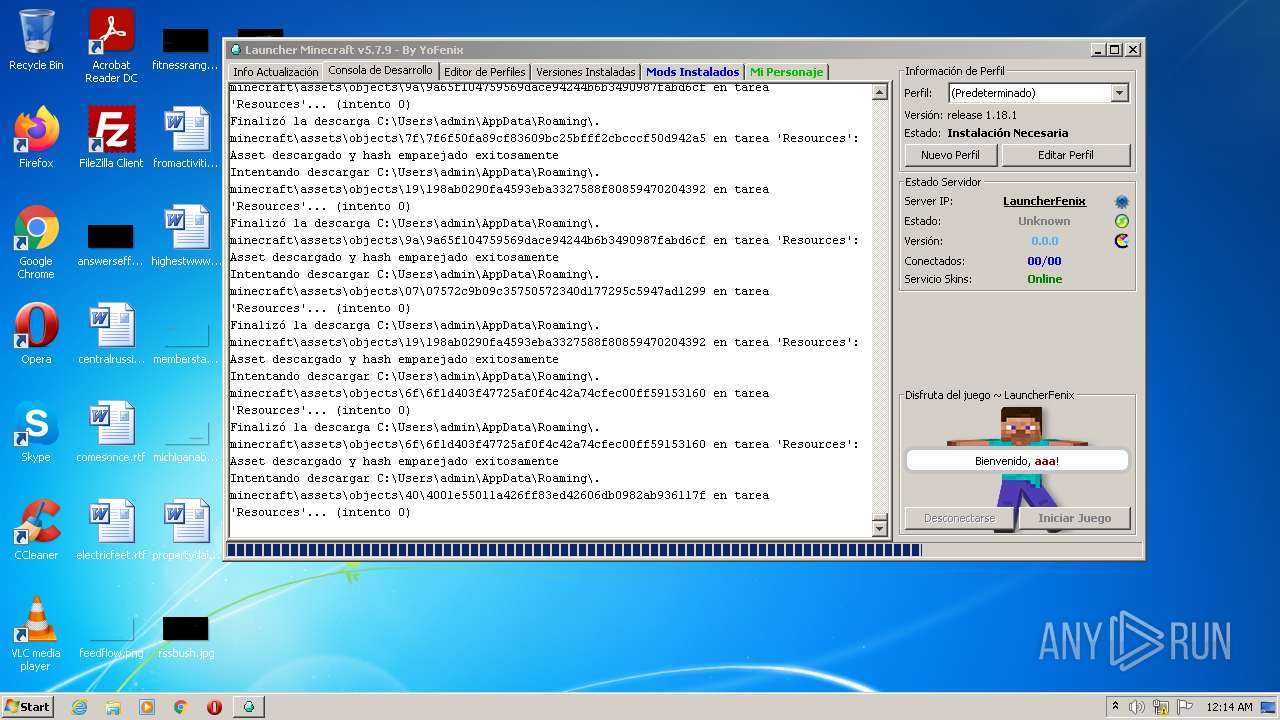
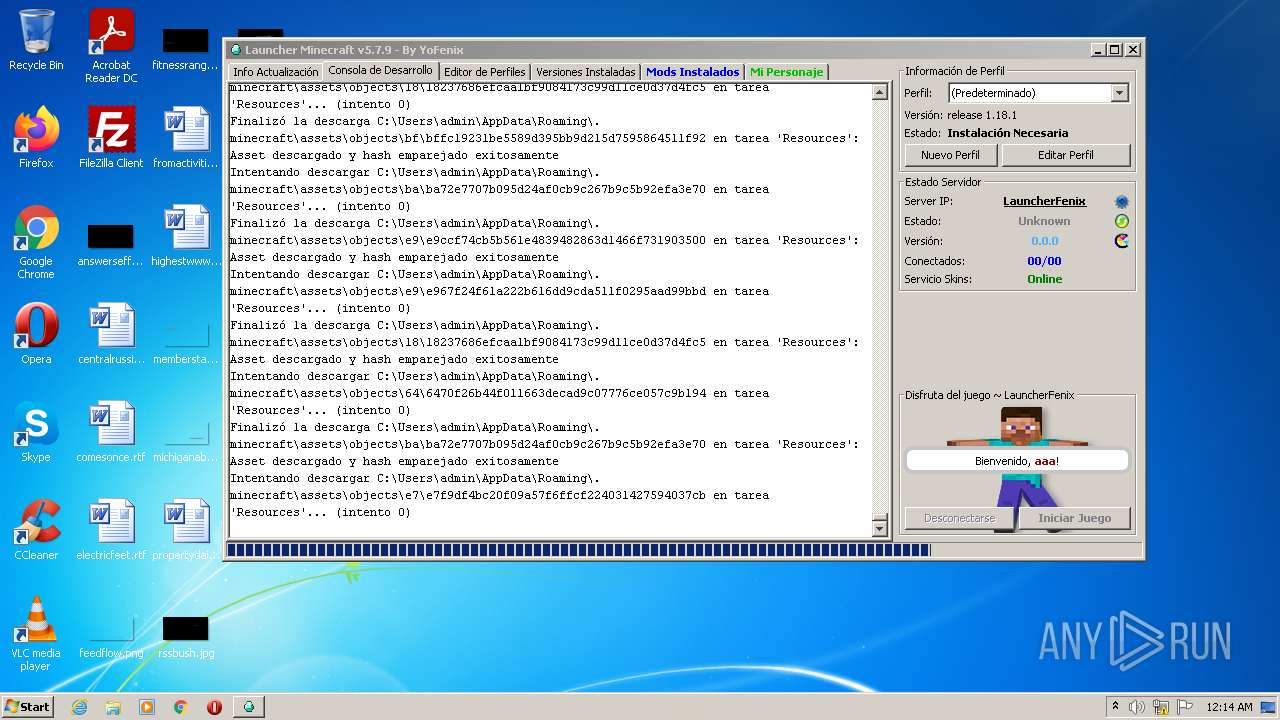
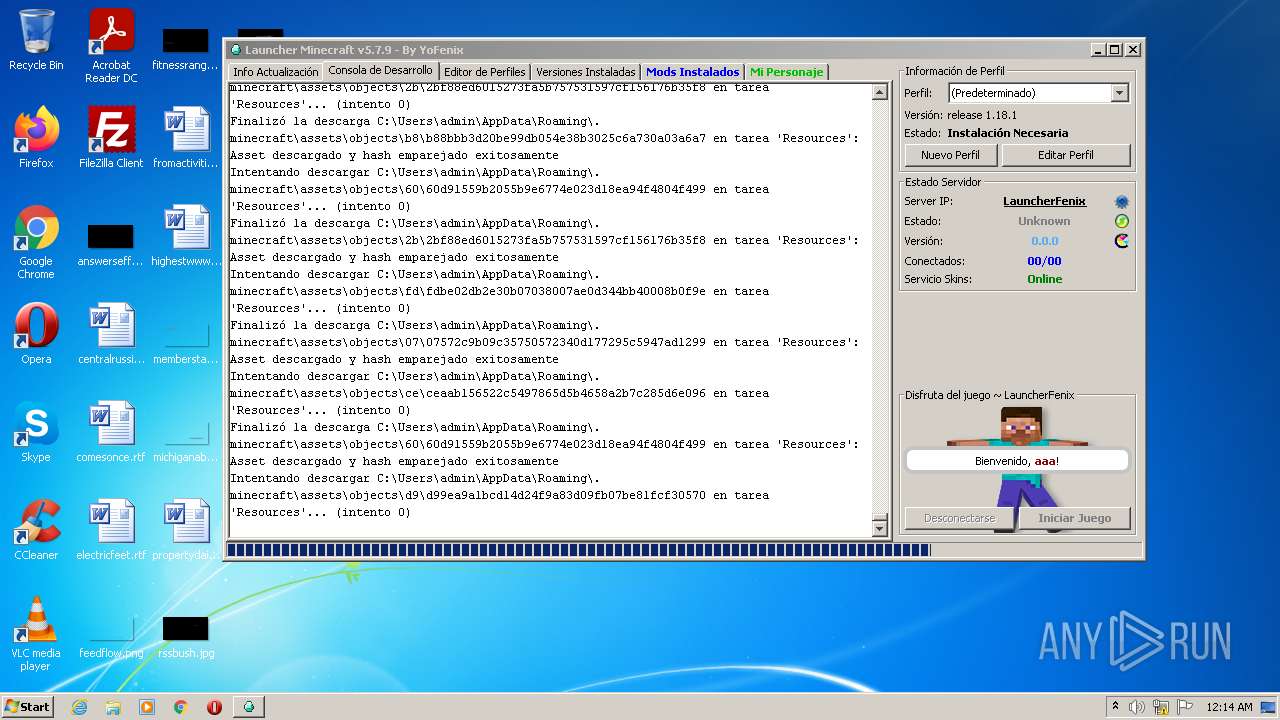
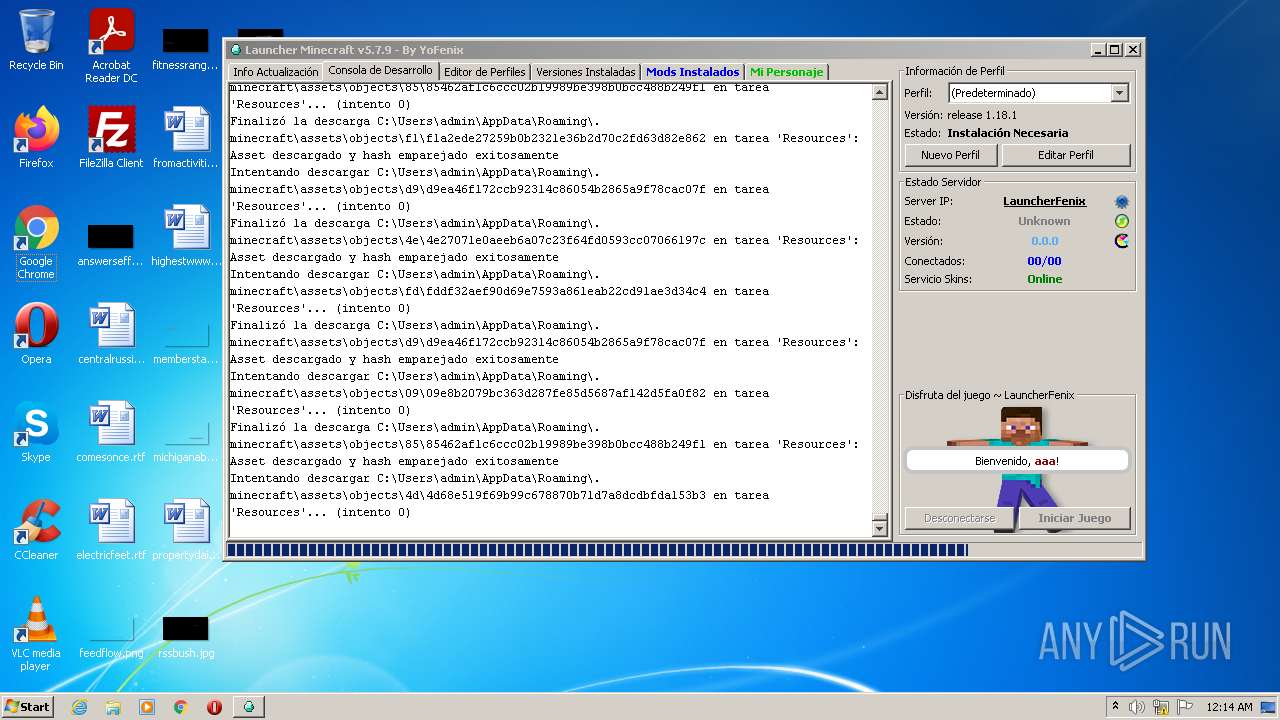
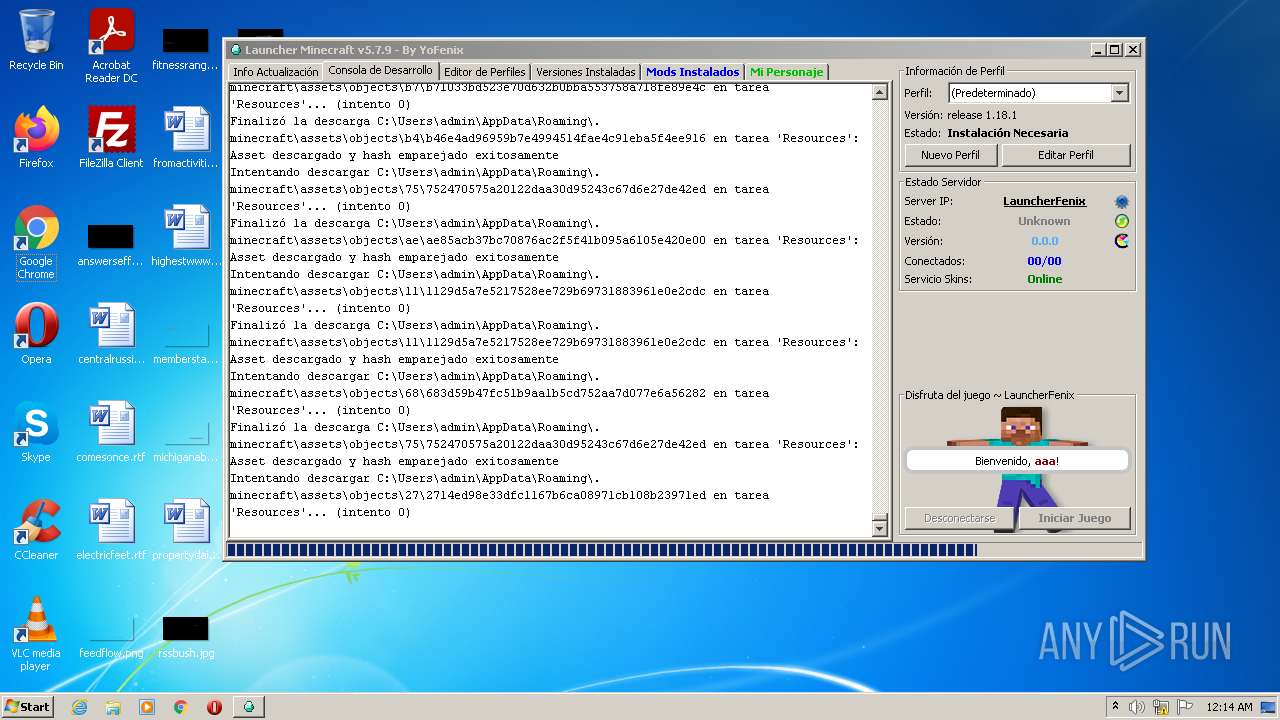
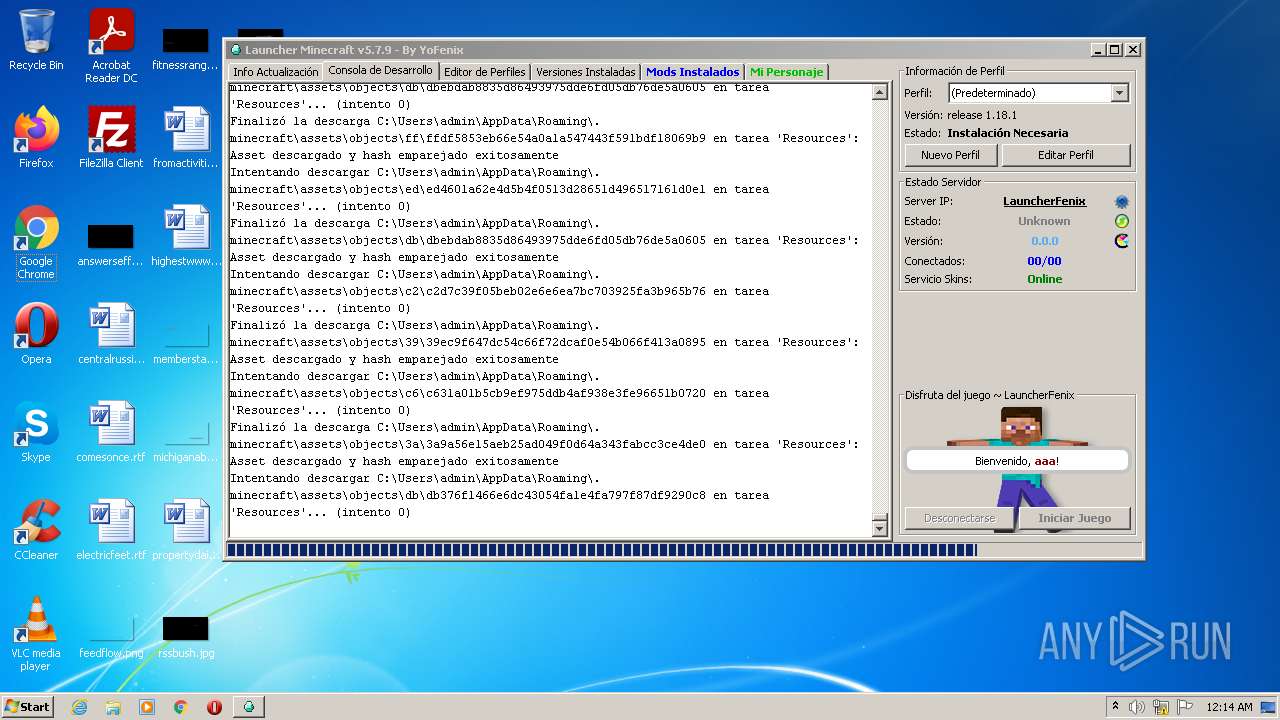
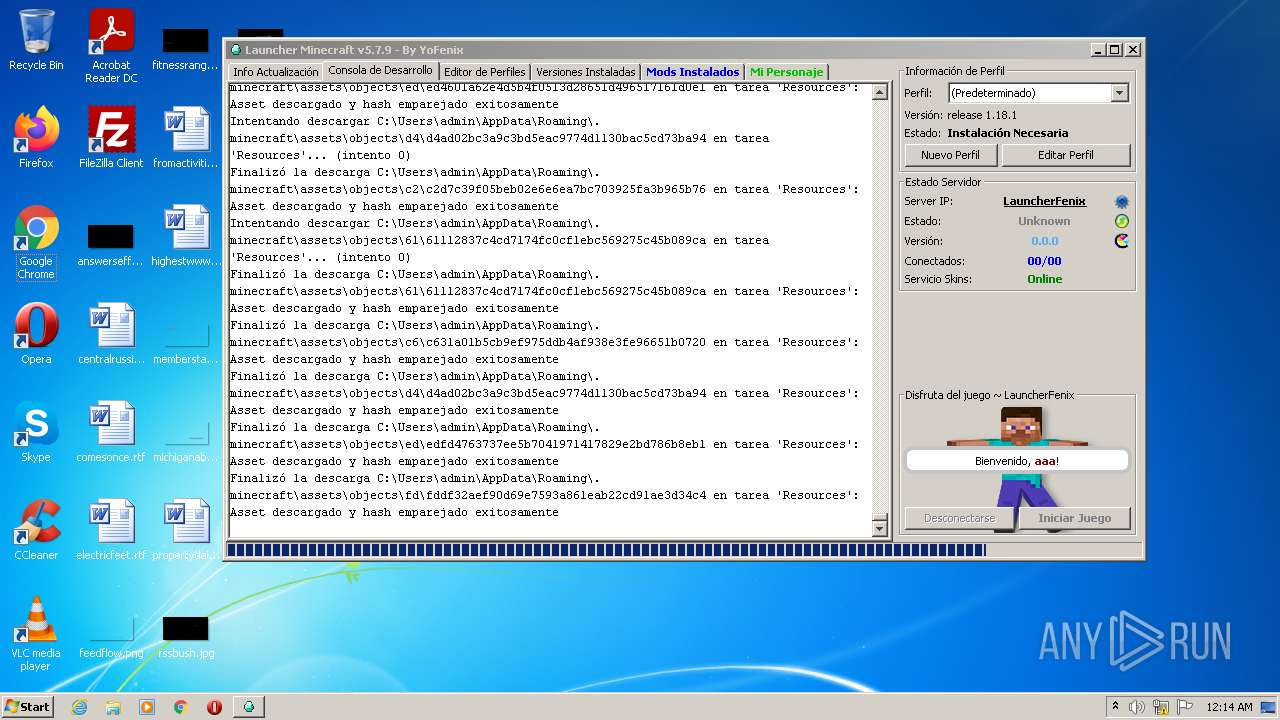
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 1800 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
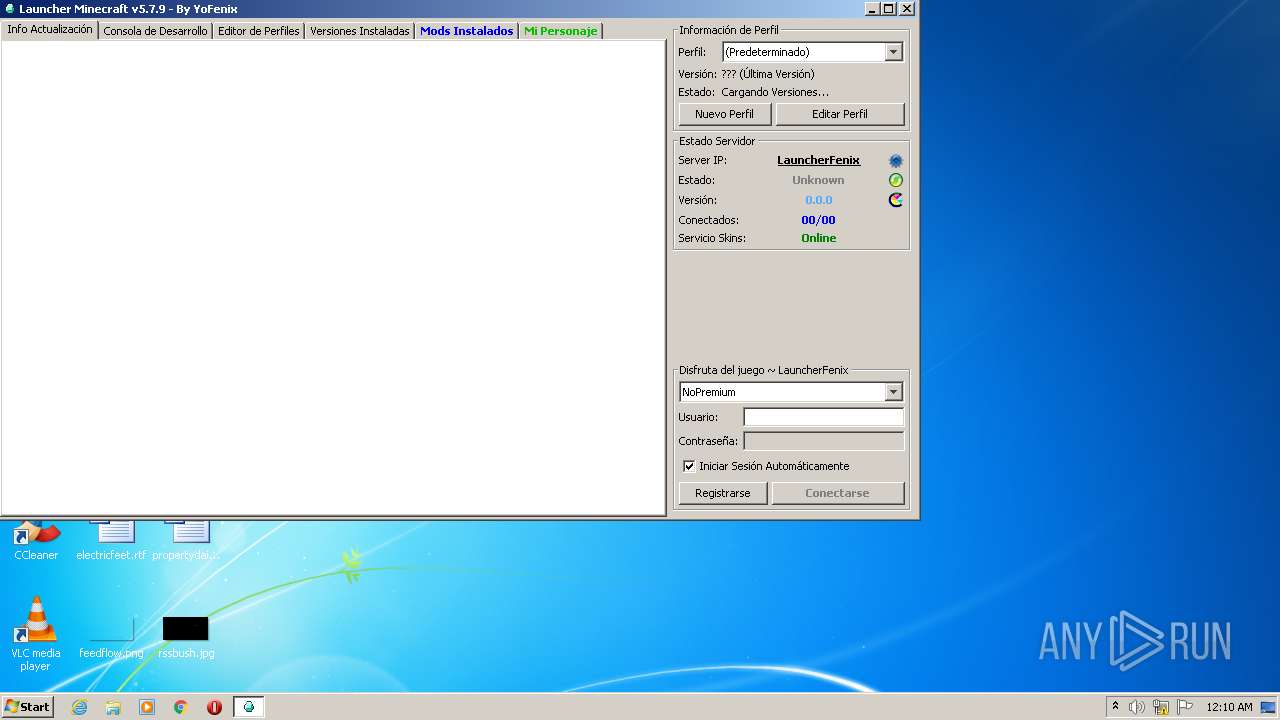
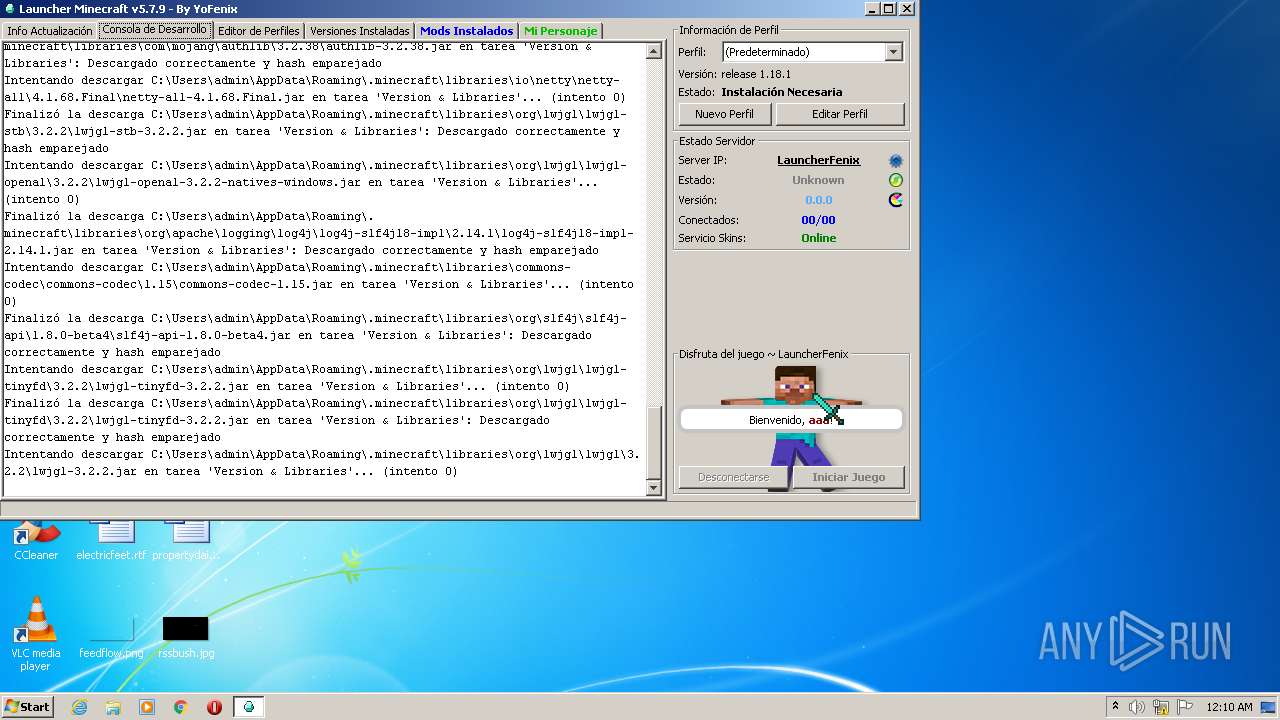
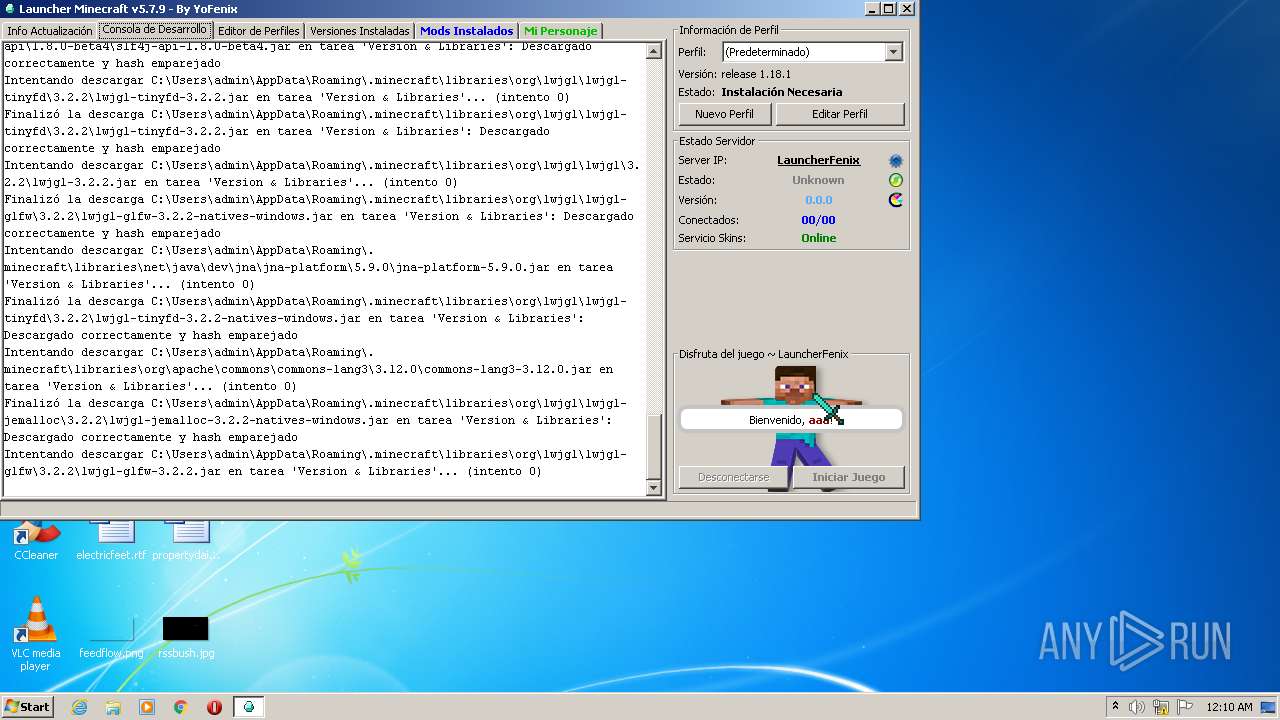
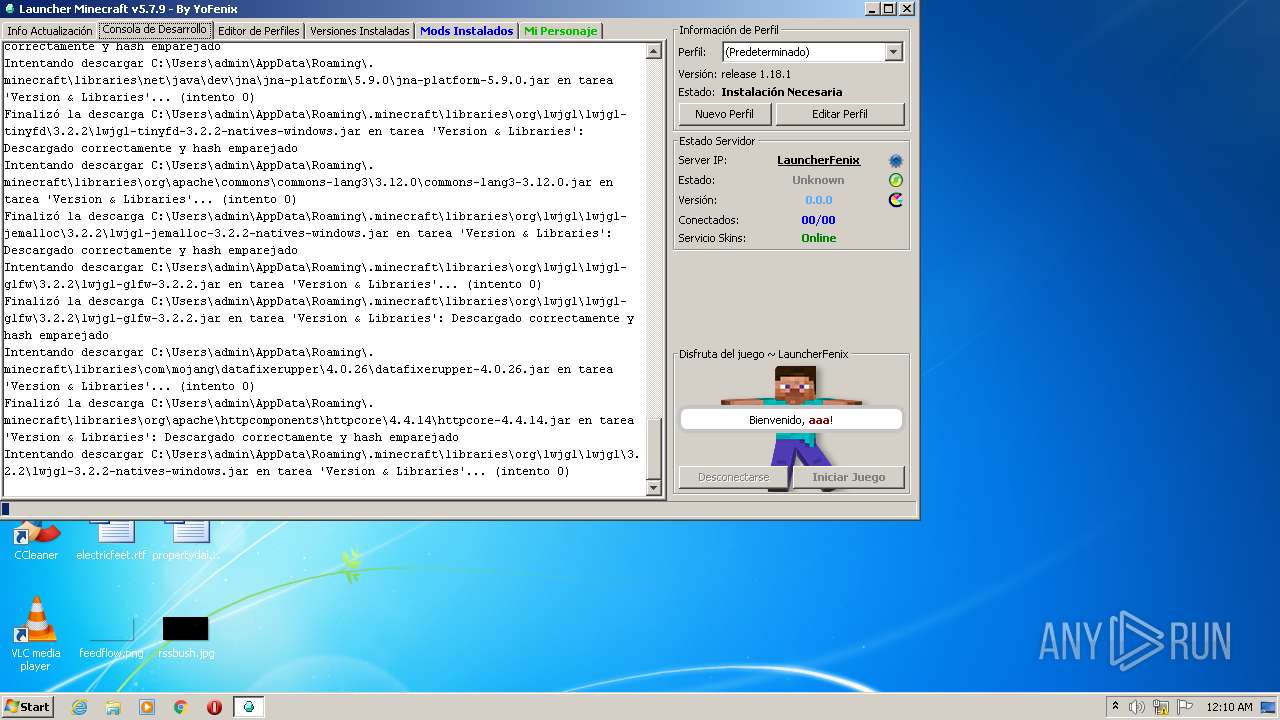
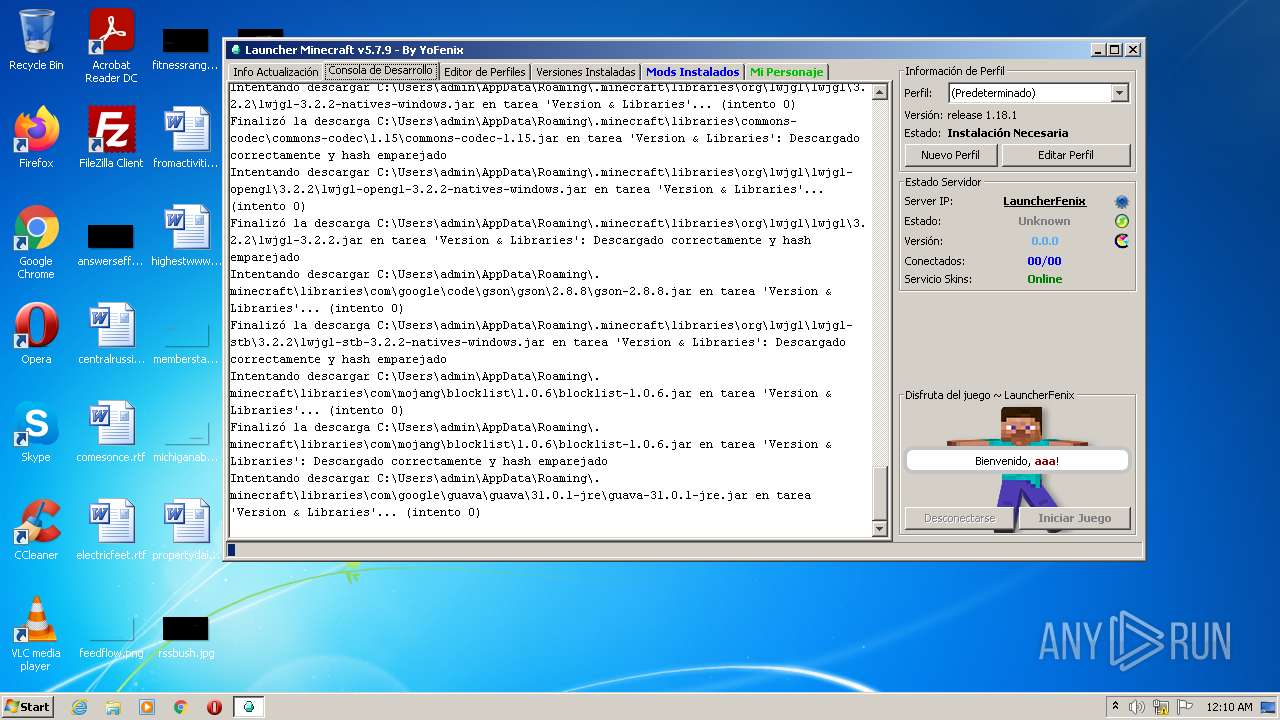
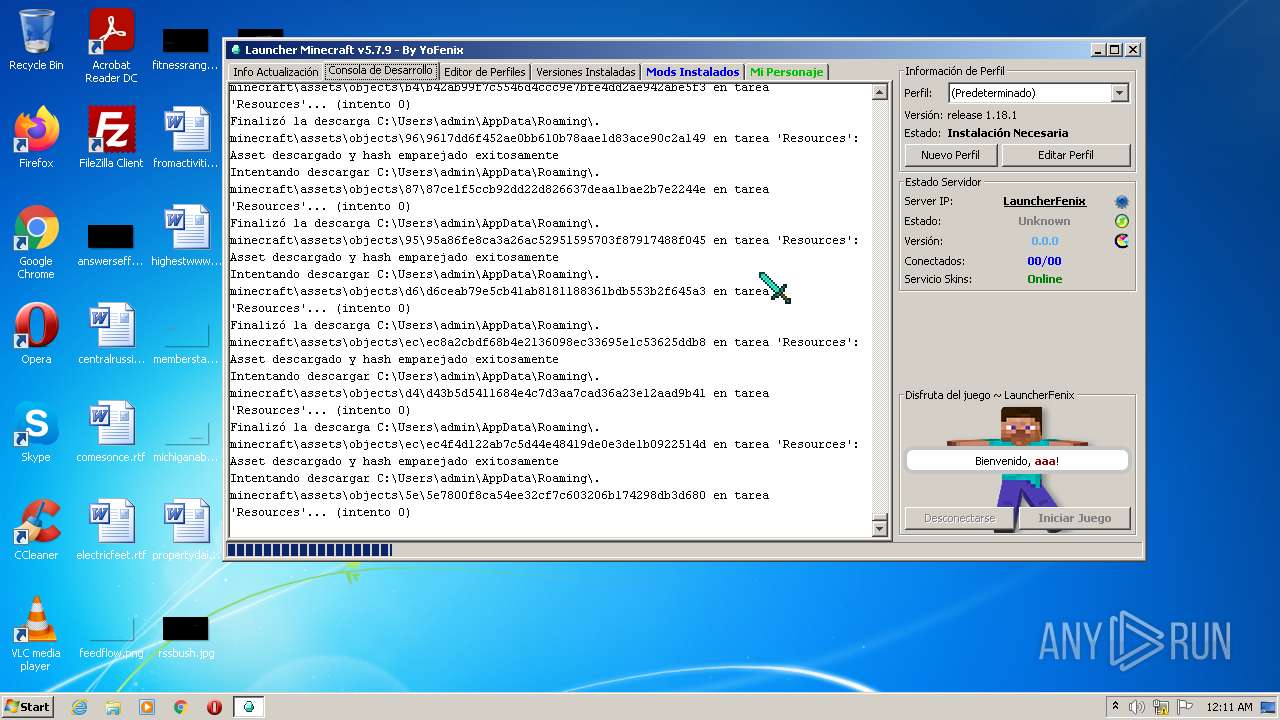
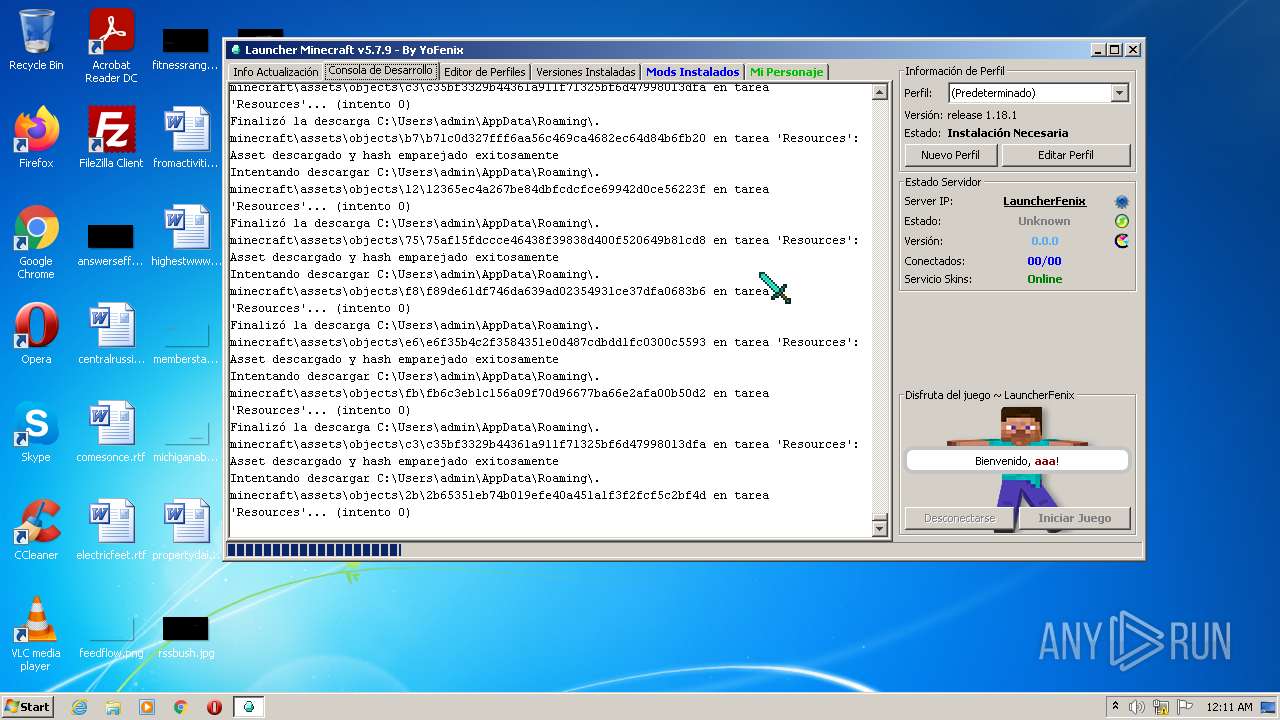
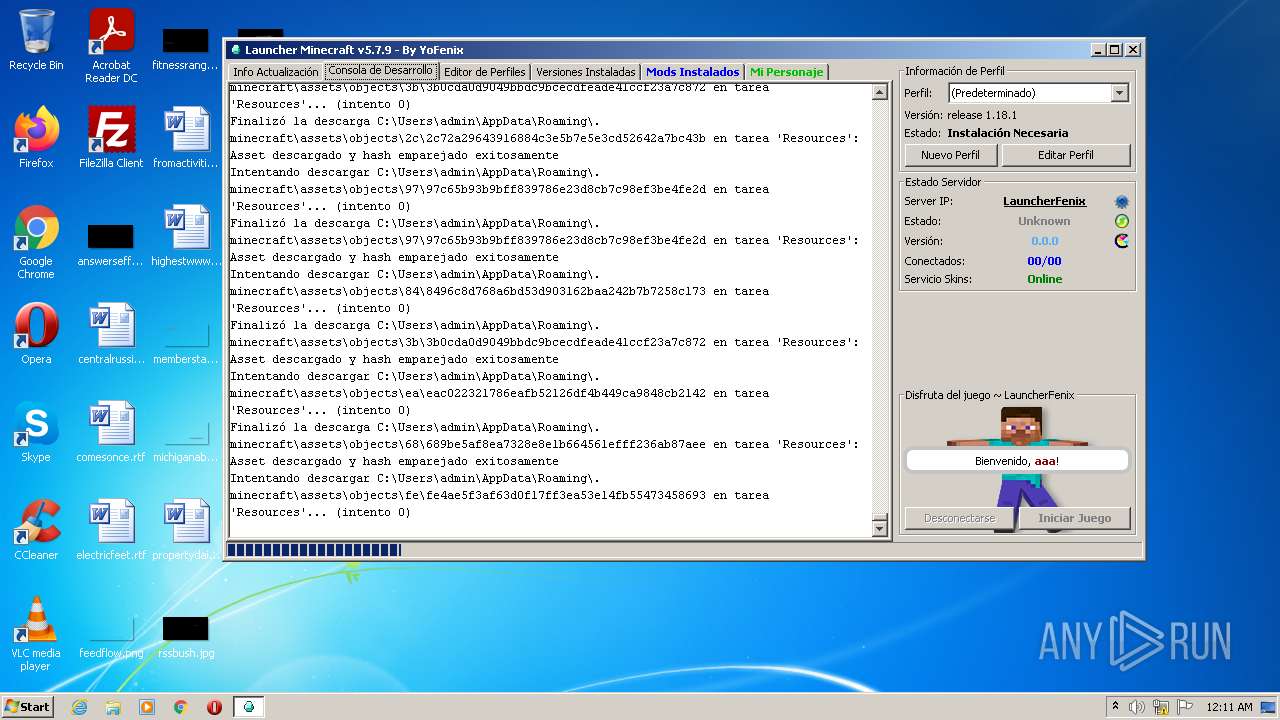
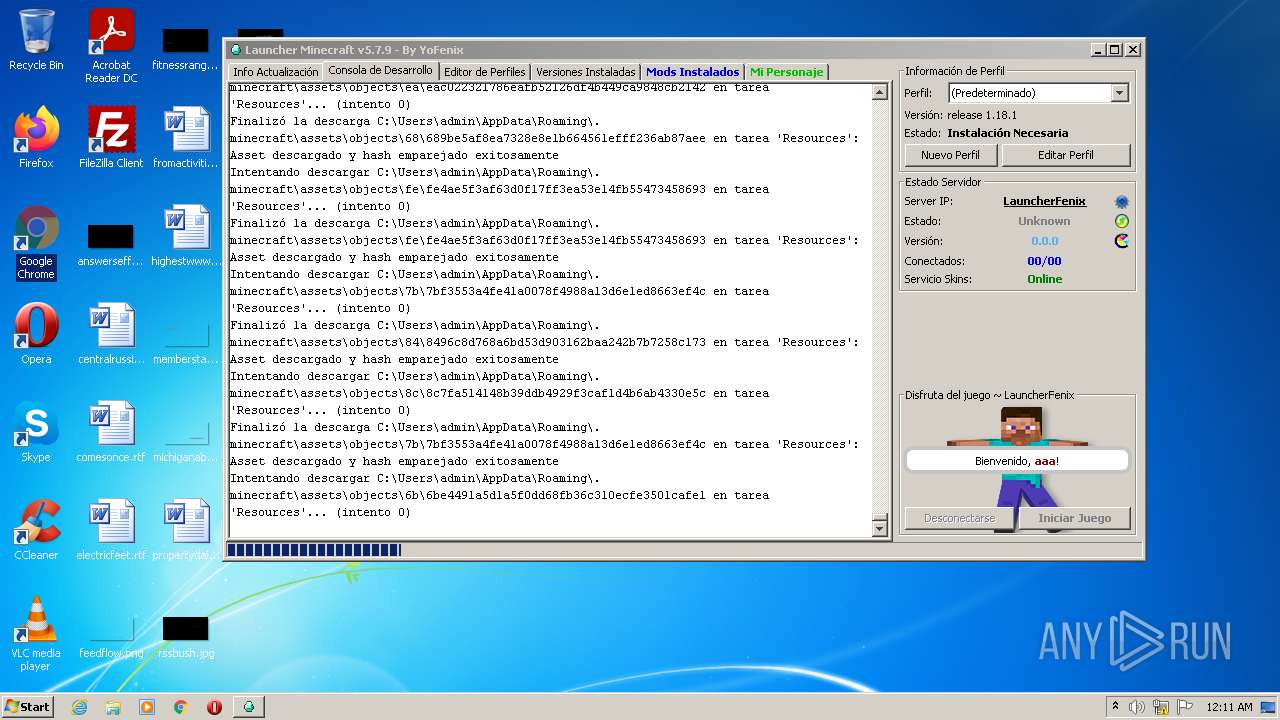
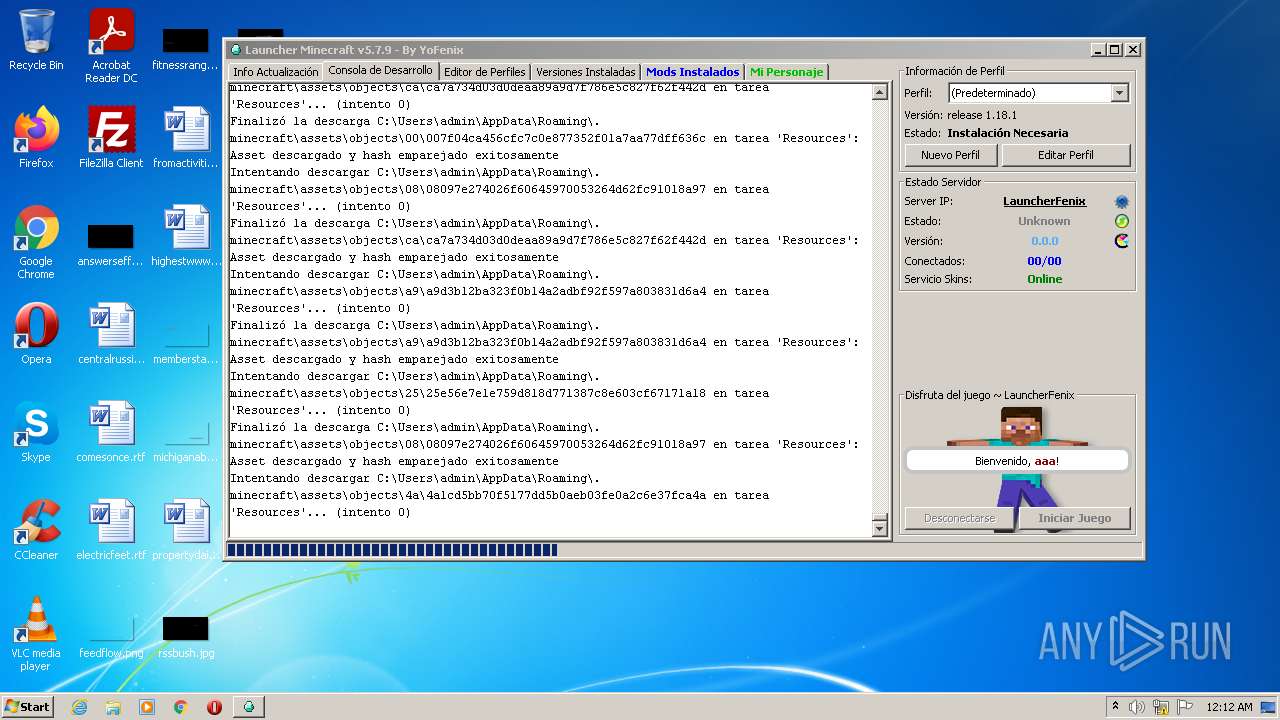
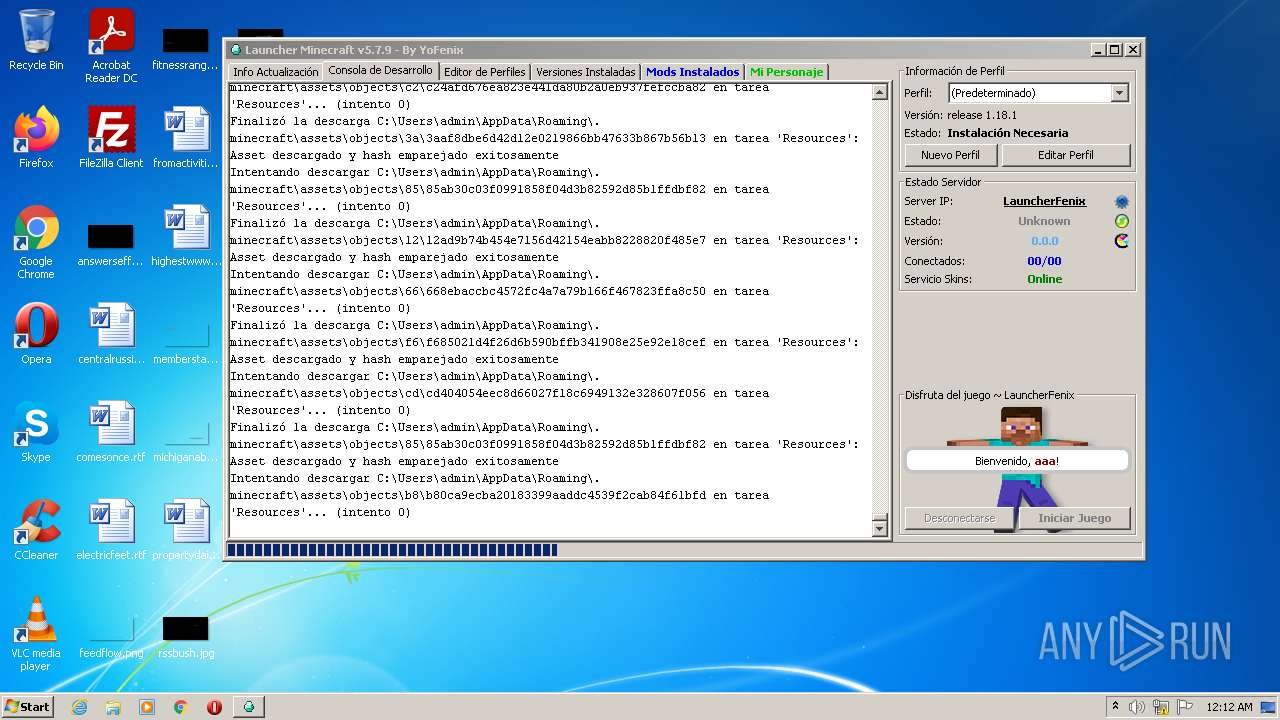
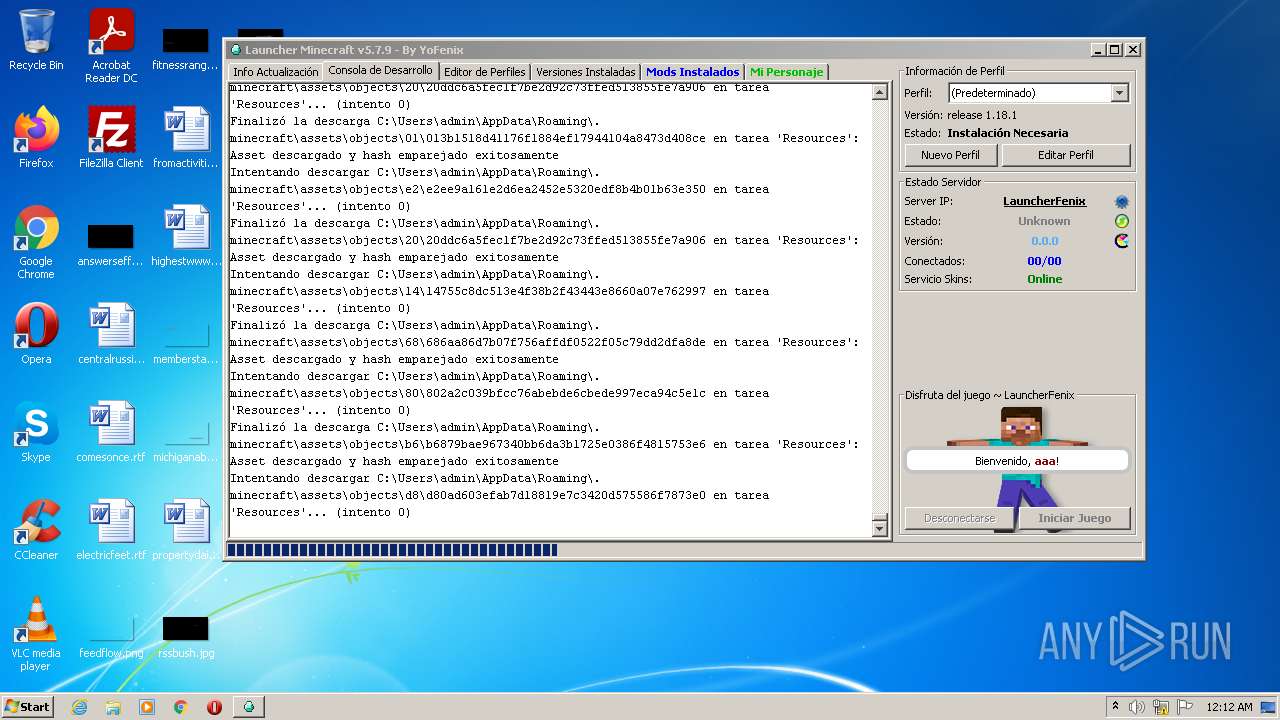
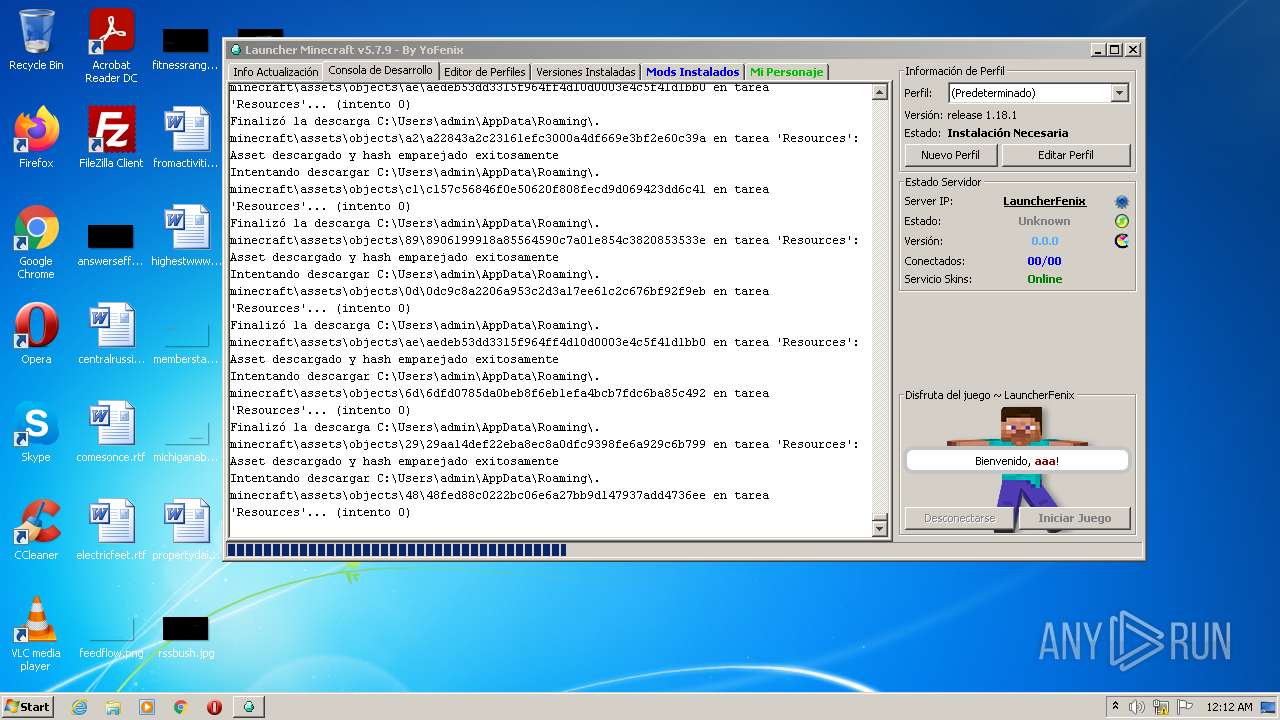
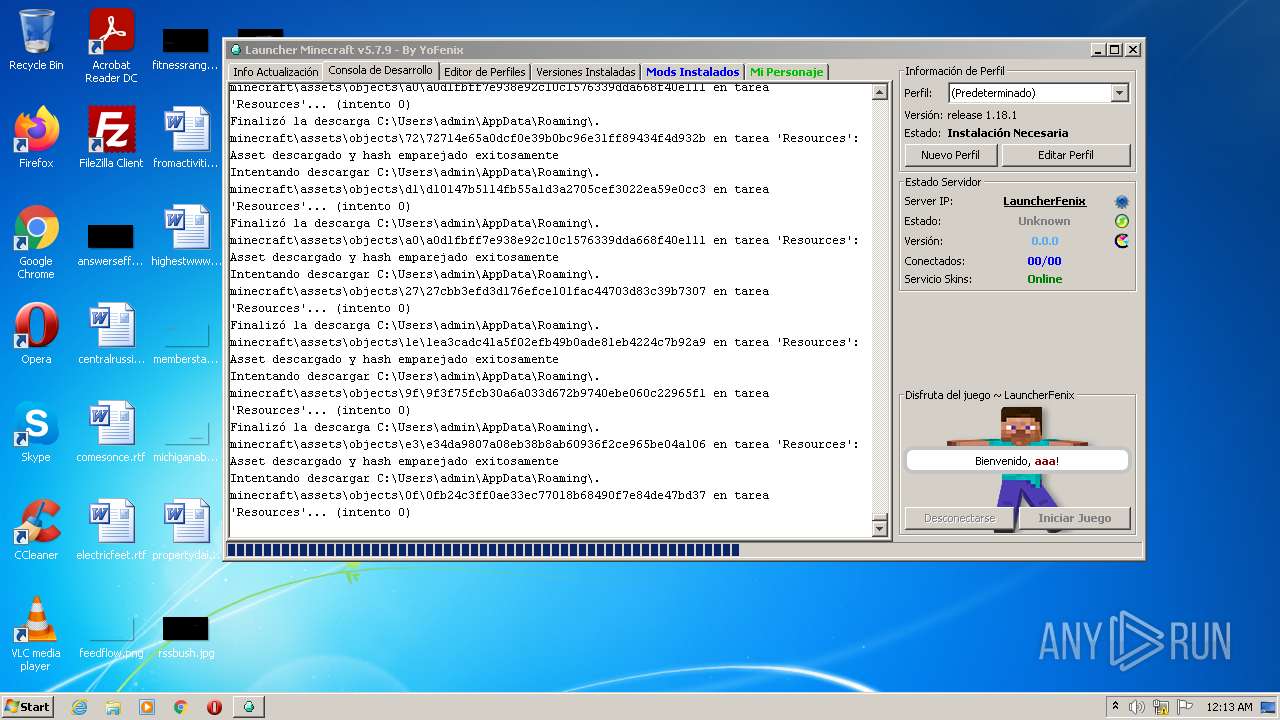
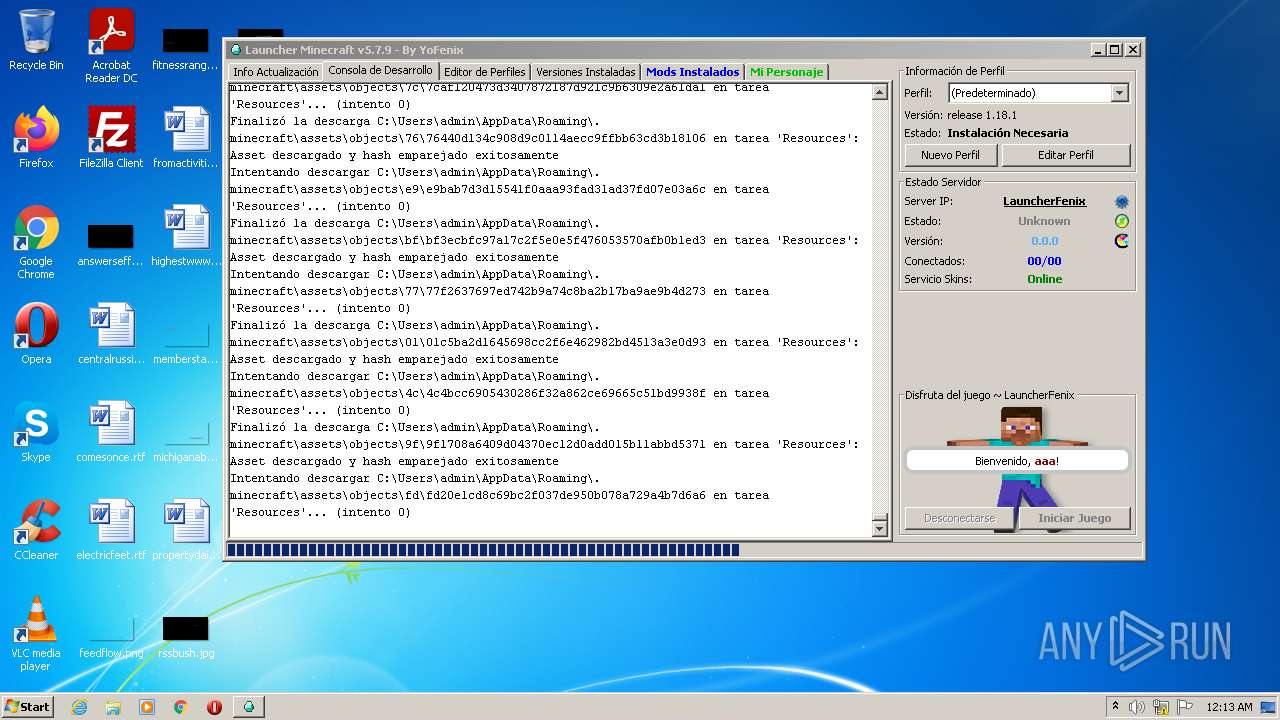
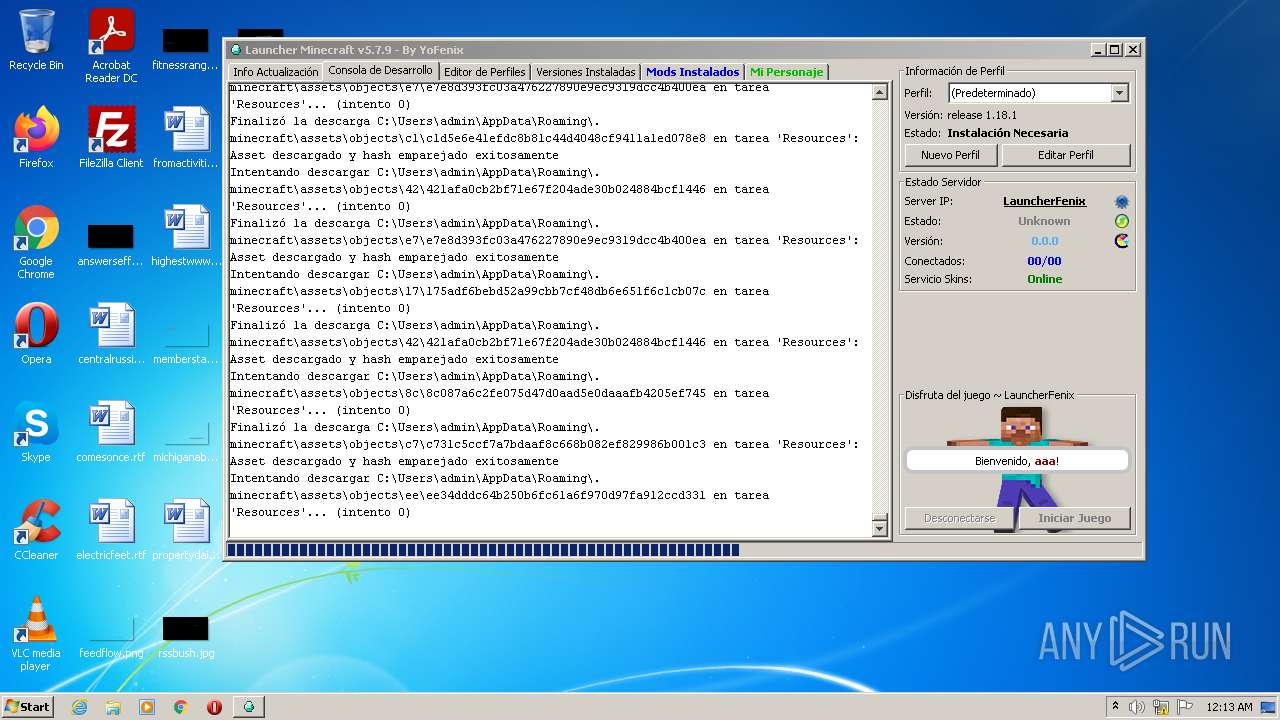
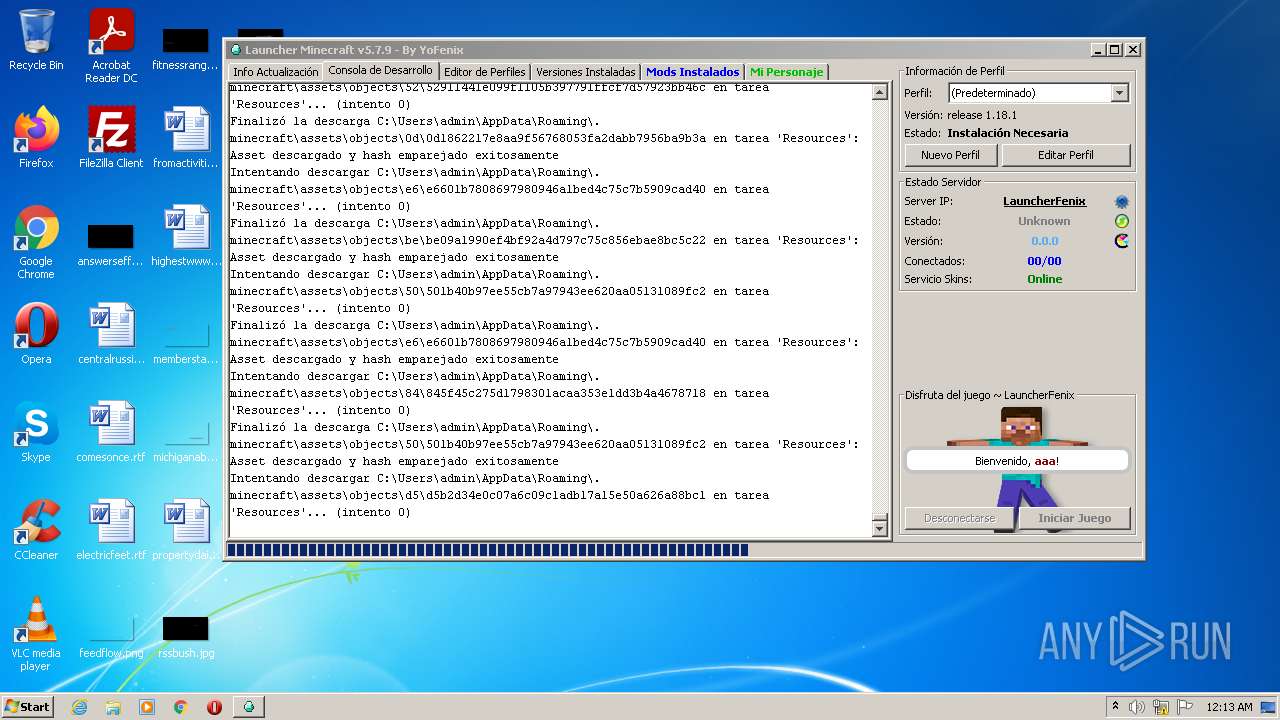
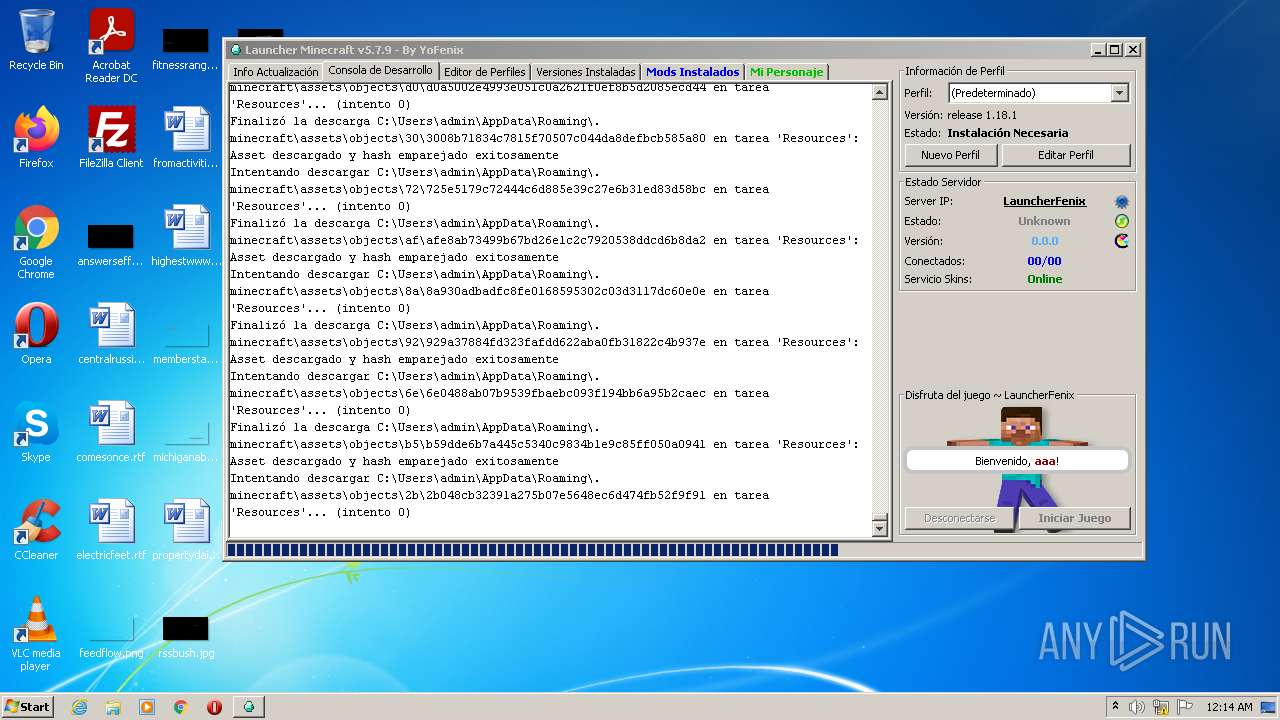
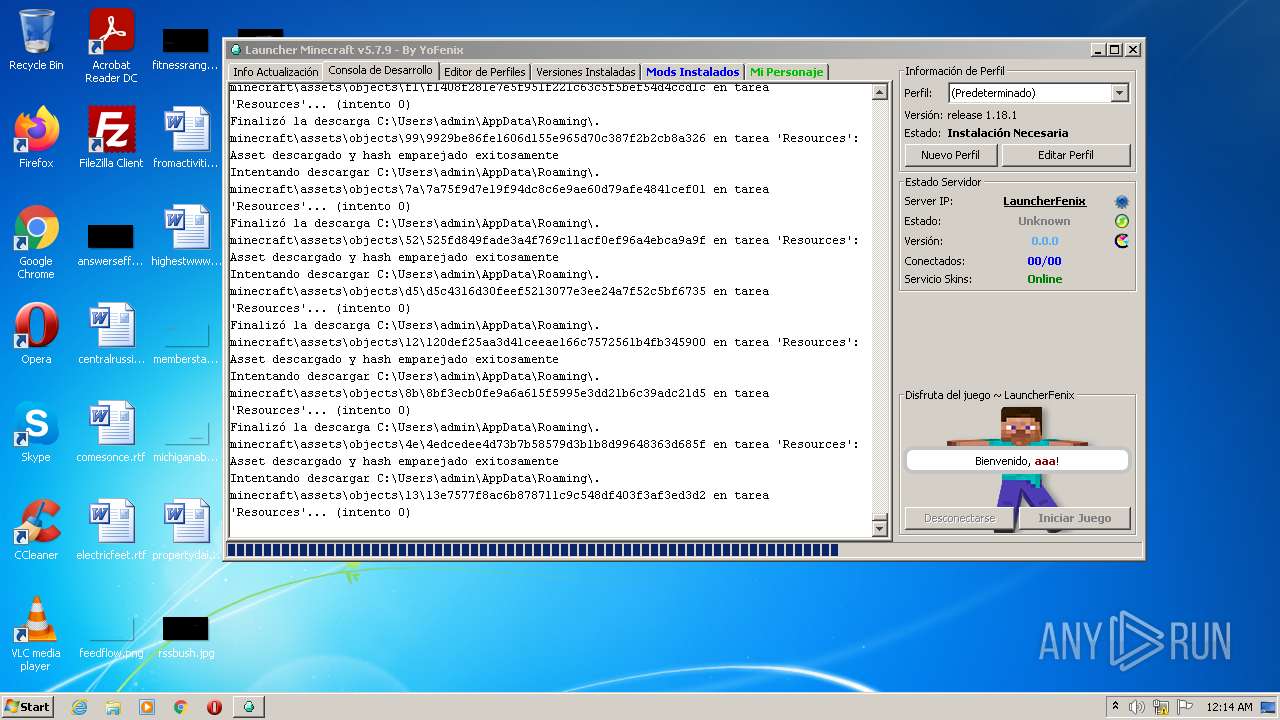
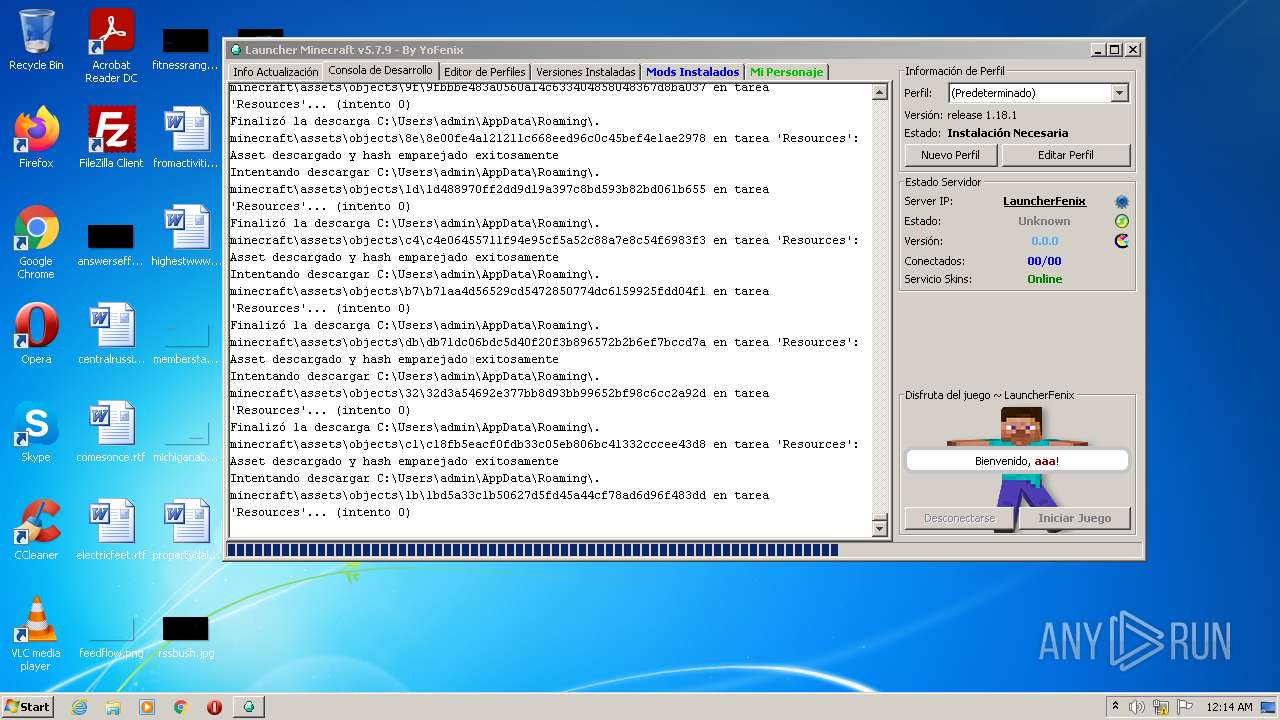
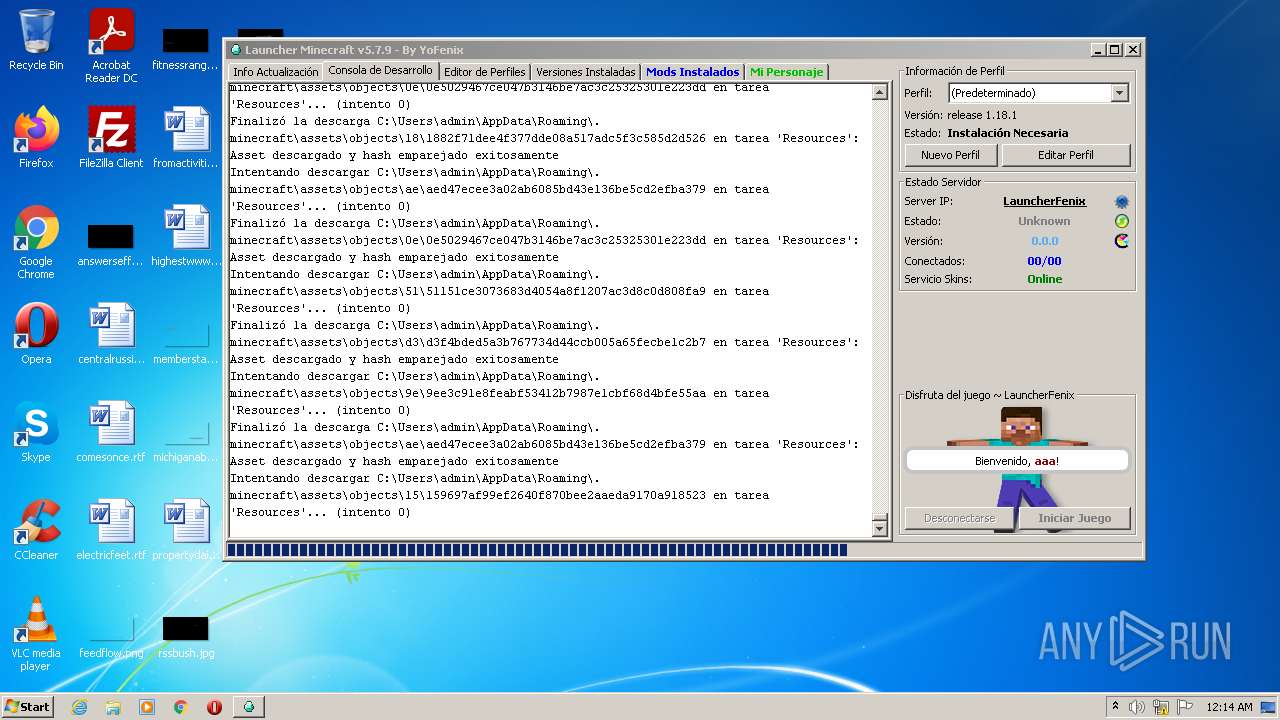
| 3652 | "C:\Users\admin\AppData\Local\Temp\LauncherFenix-Minecraft-v7.exe" | C:\Users\admin\AppData\Local\Temp\LauncherFenix-Minecraft-v7.exe | — | Explorer.EXE |
User: admin Company: FenixProjects Integrity Level: MEDIUM Description: Minecraft Launcher Exit code: 259 Version: 7.0.0.1 | ||||
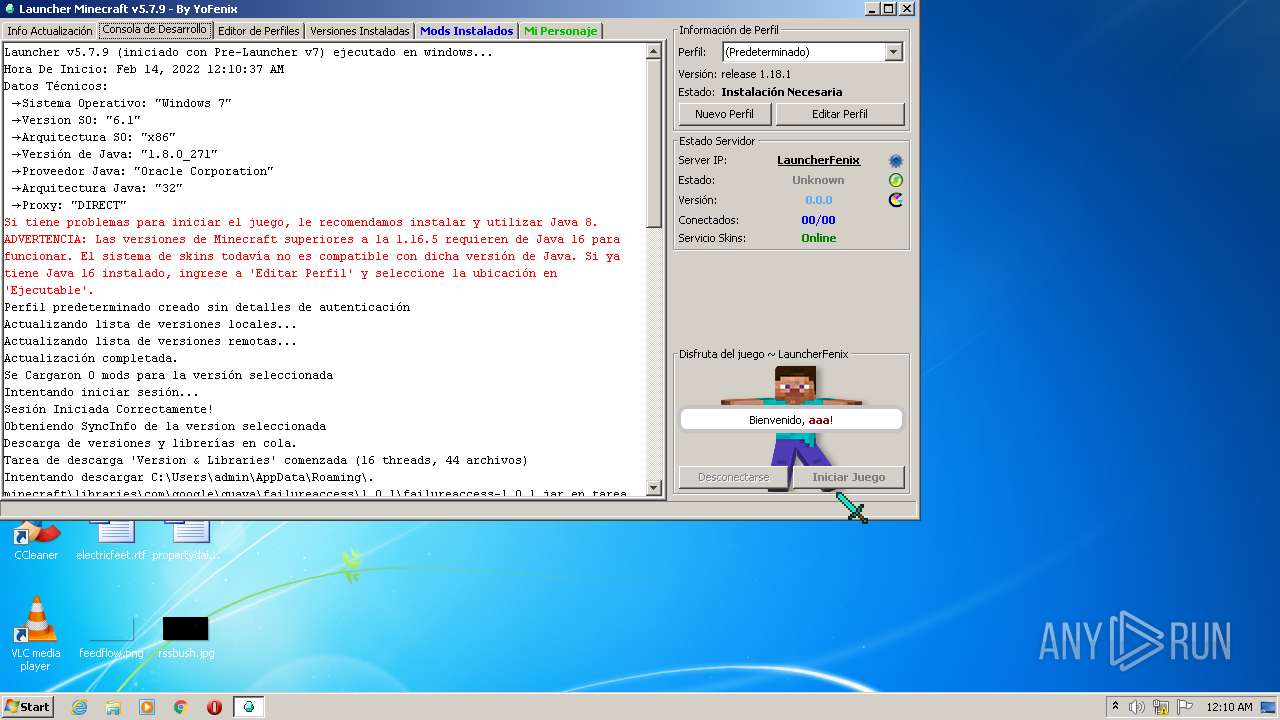
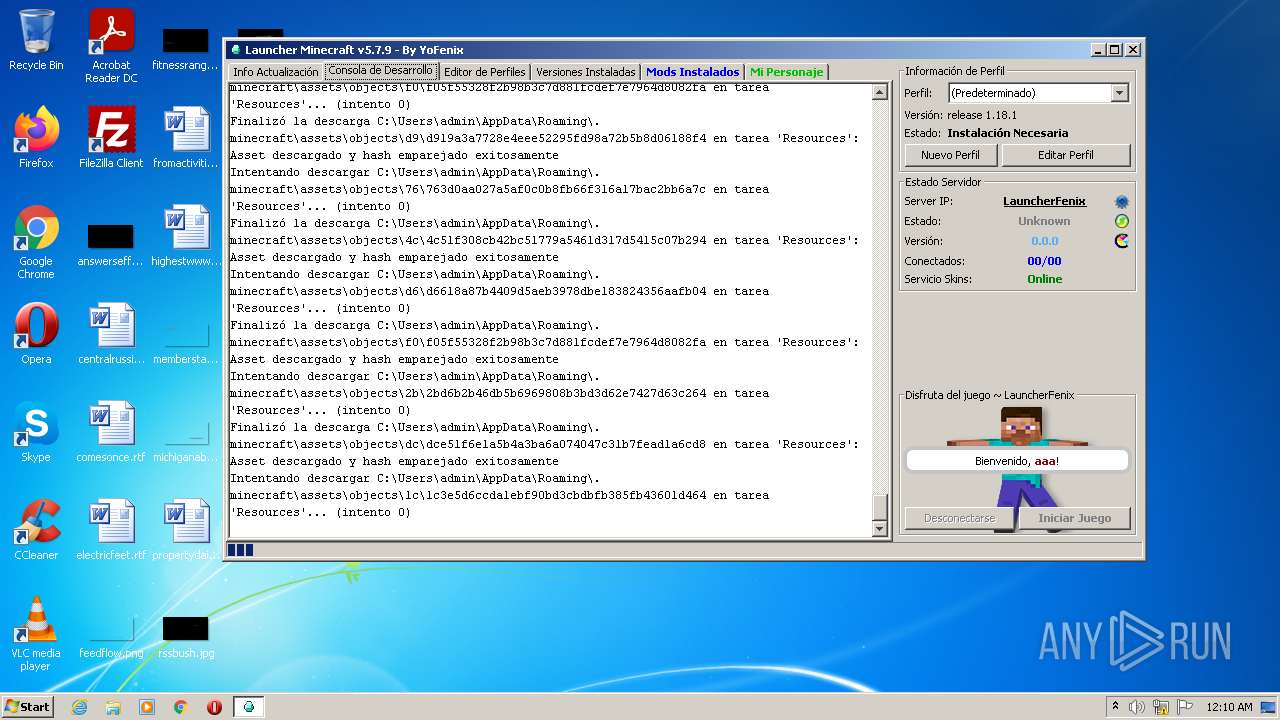
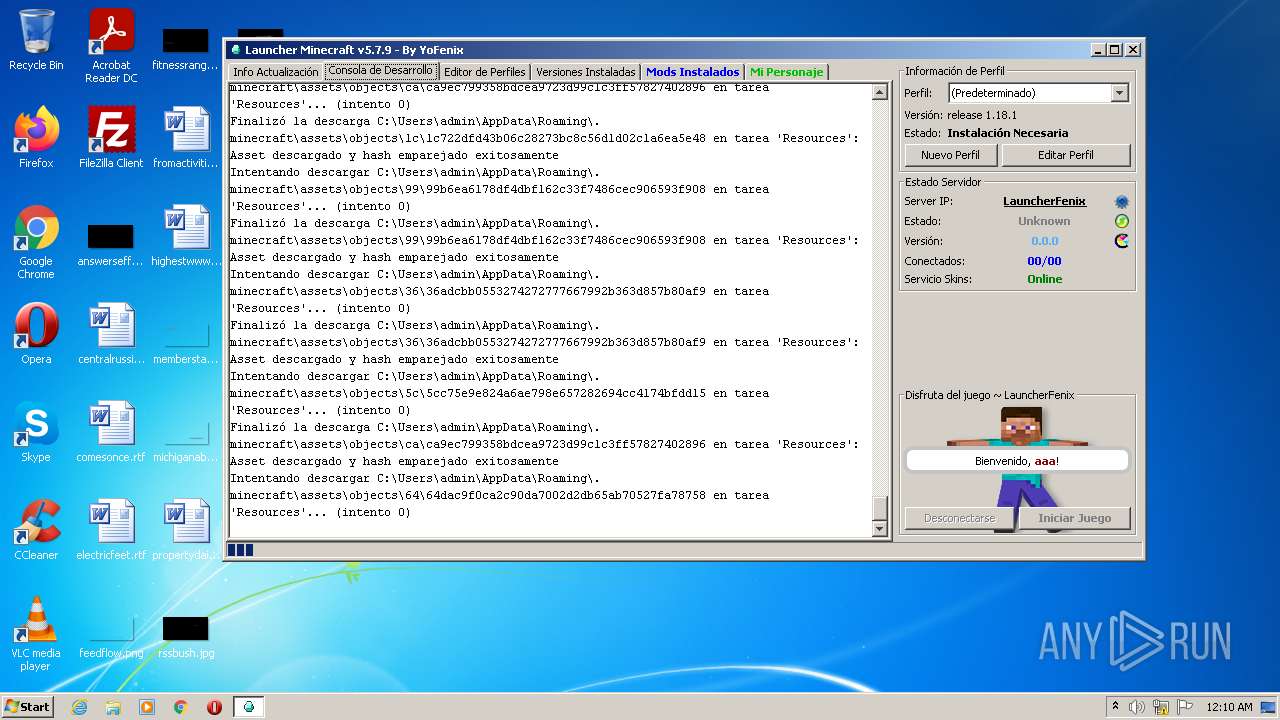
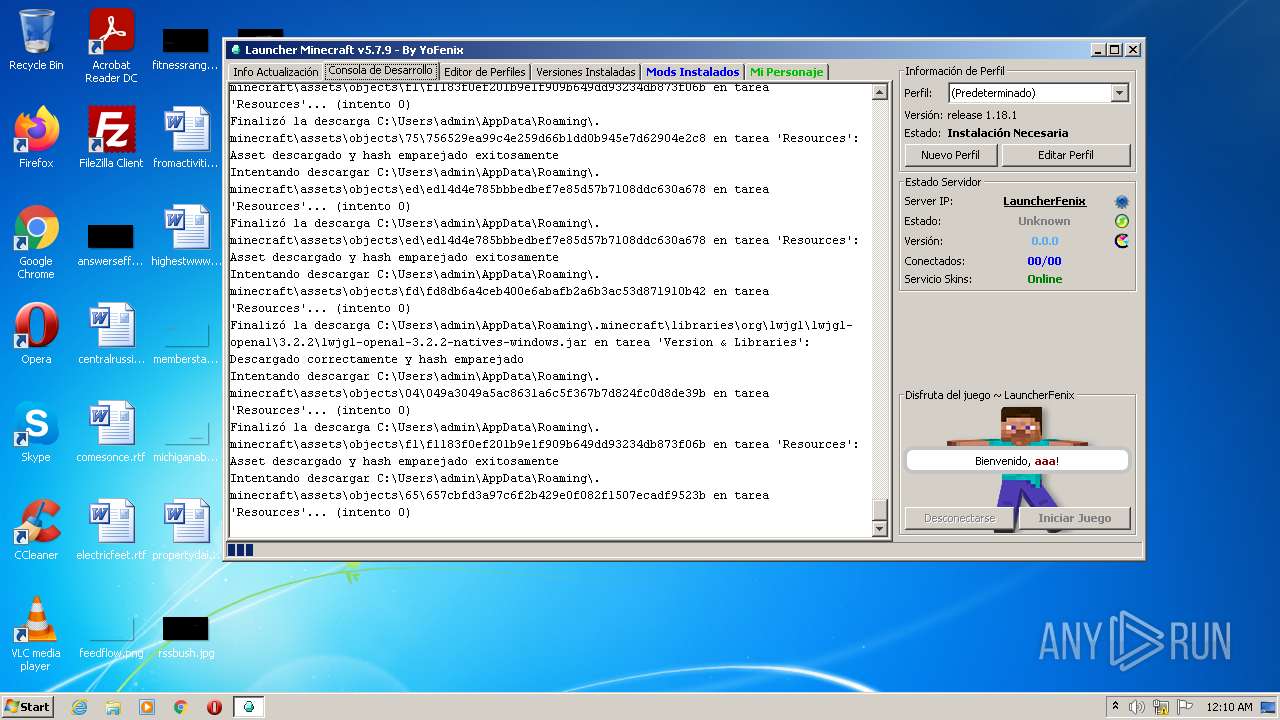
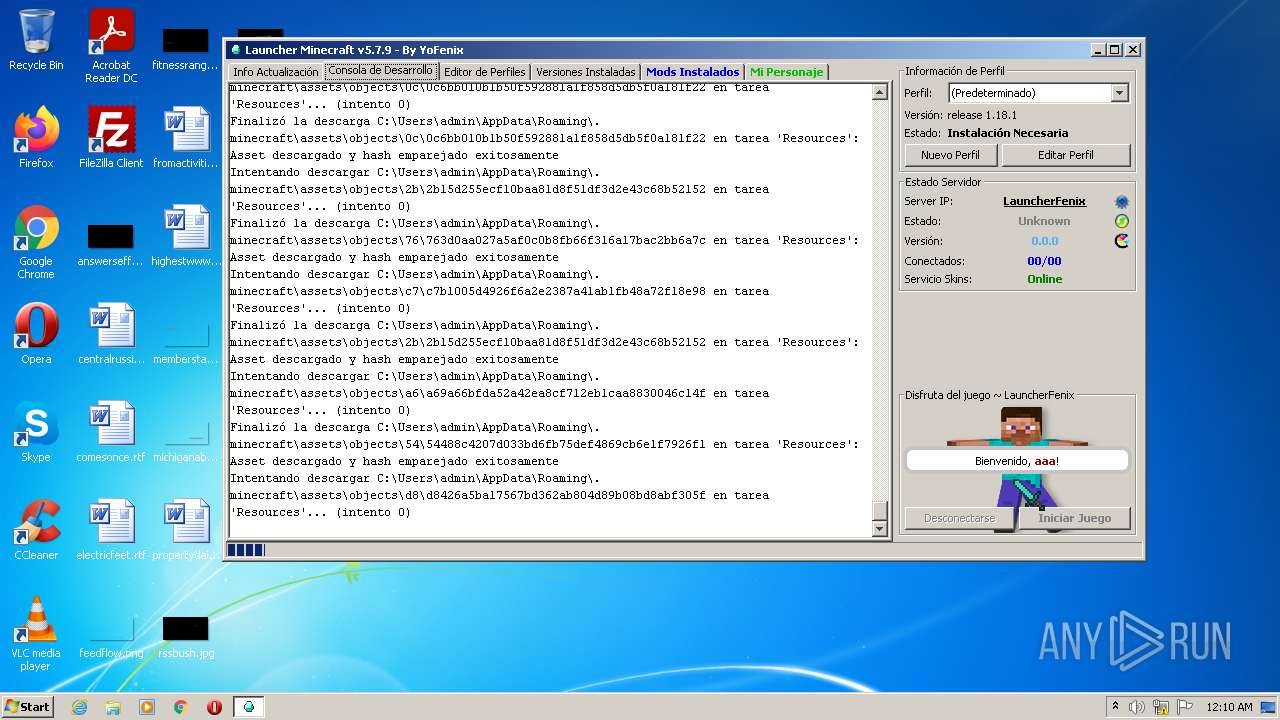
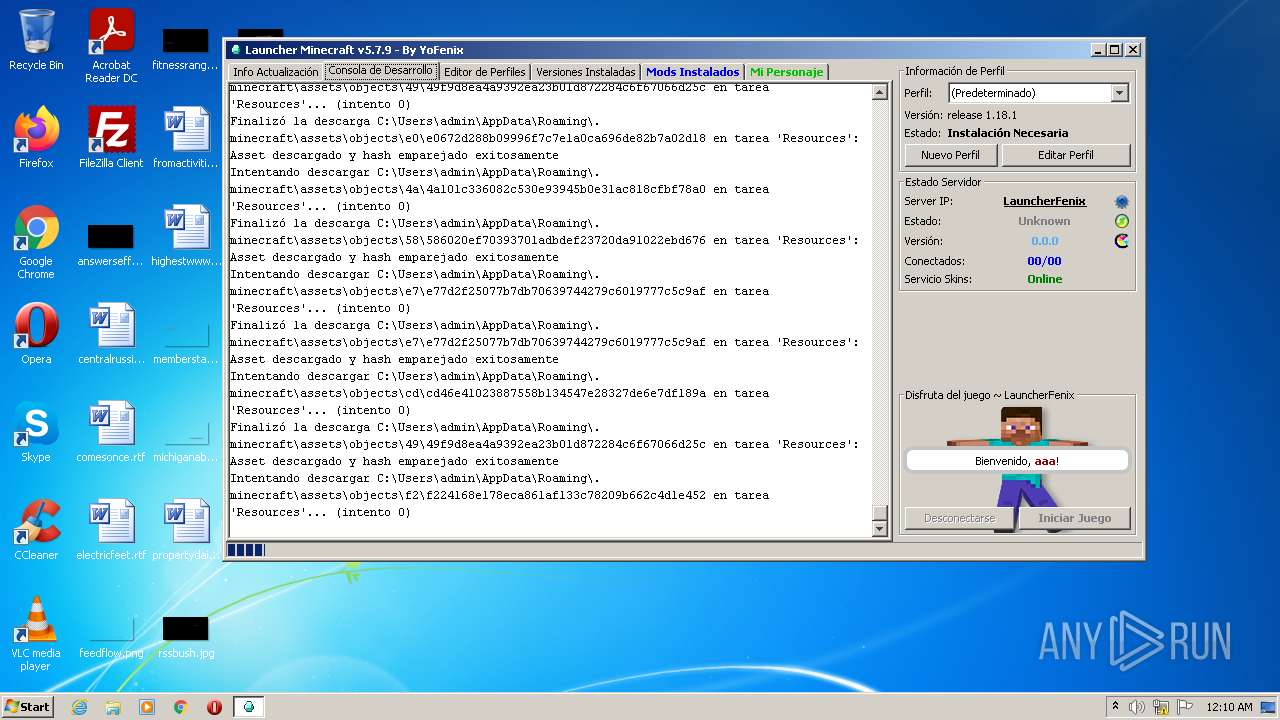
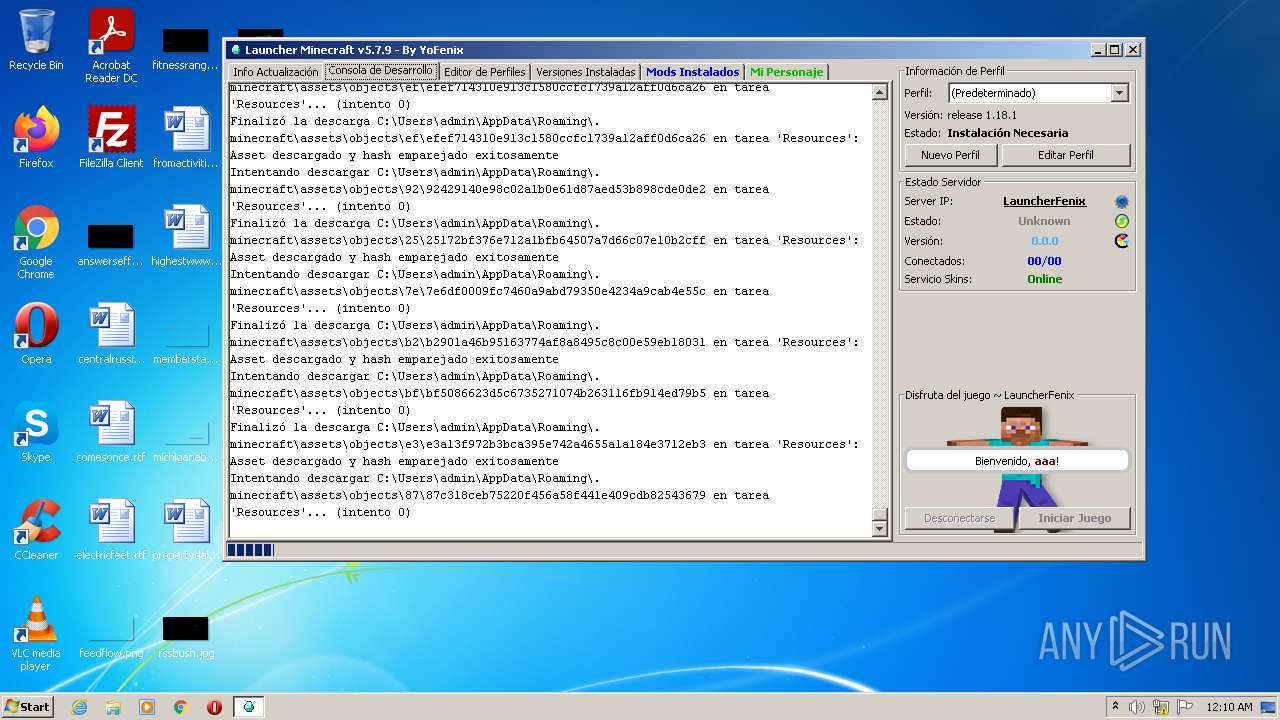
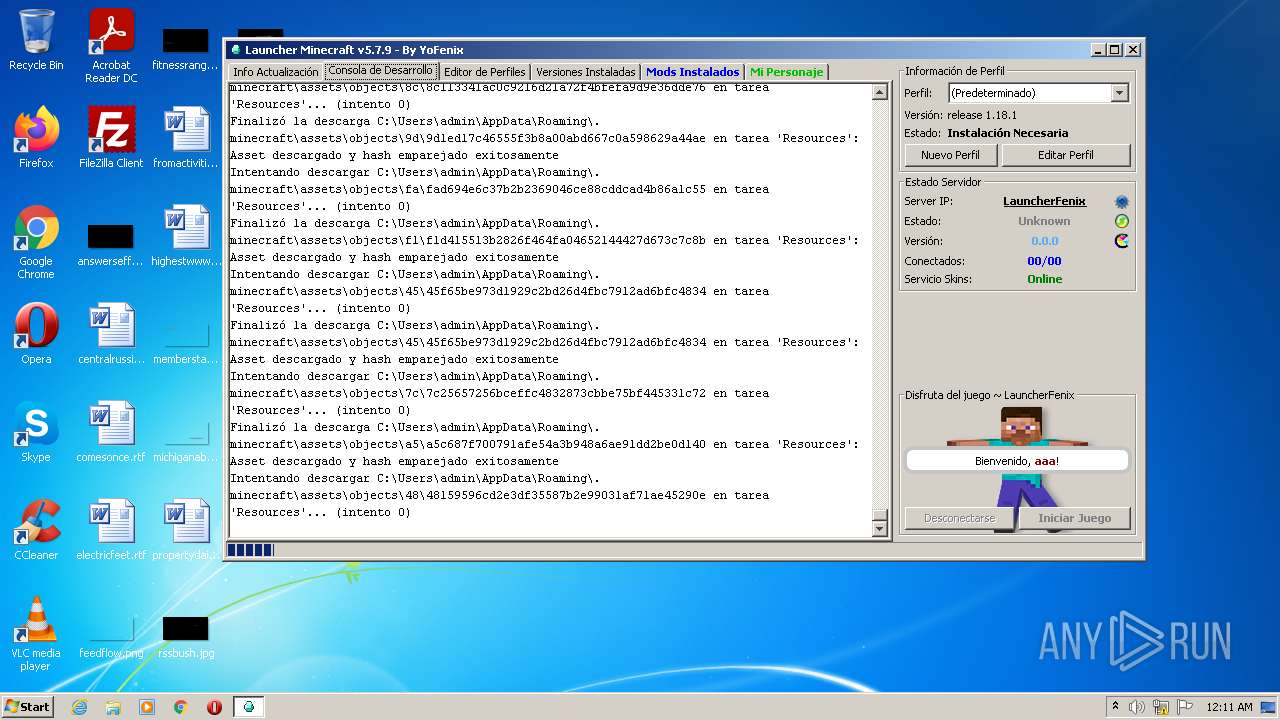
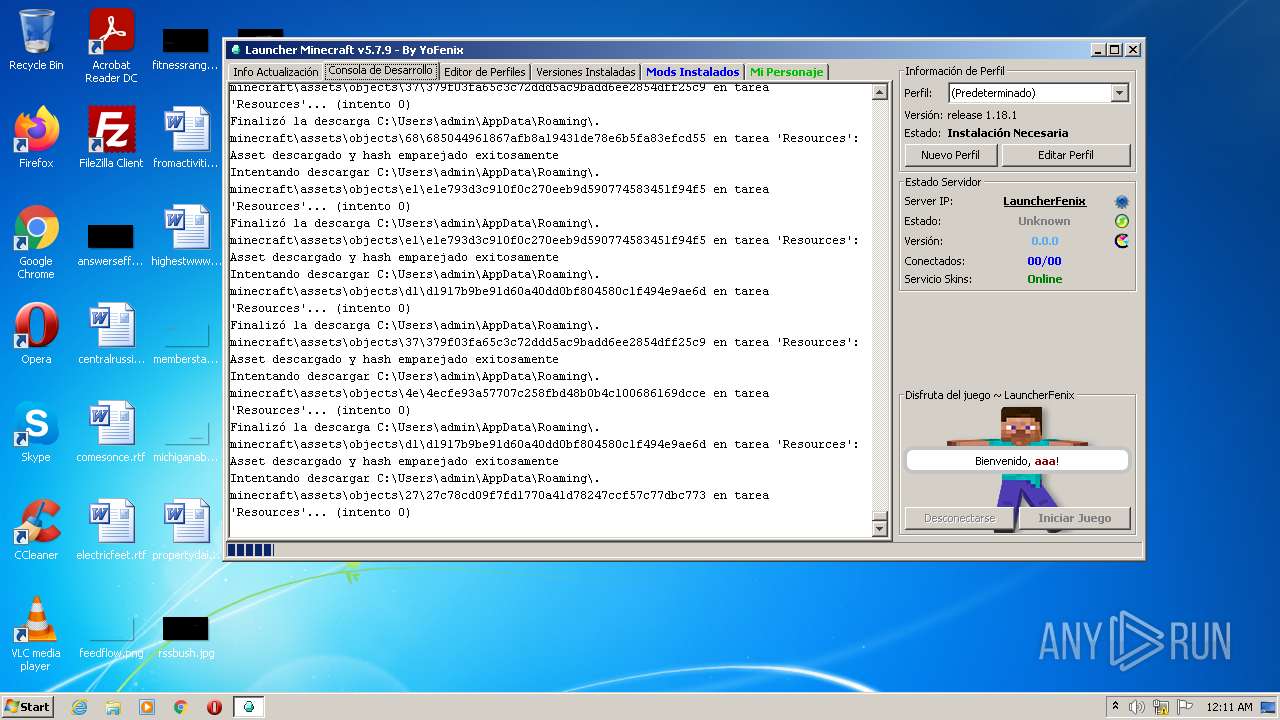
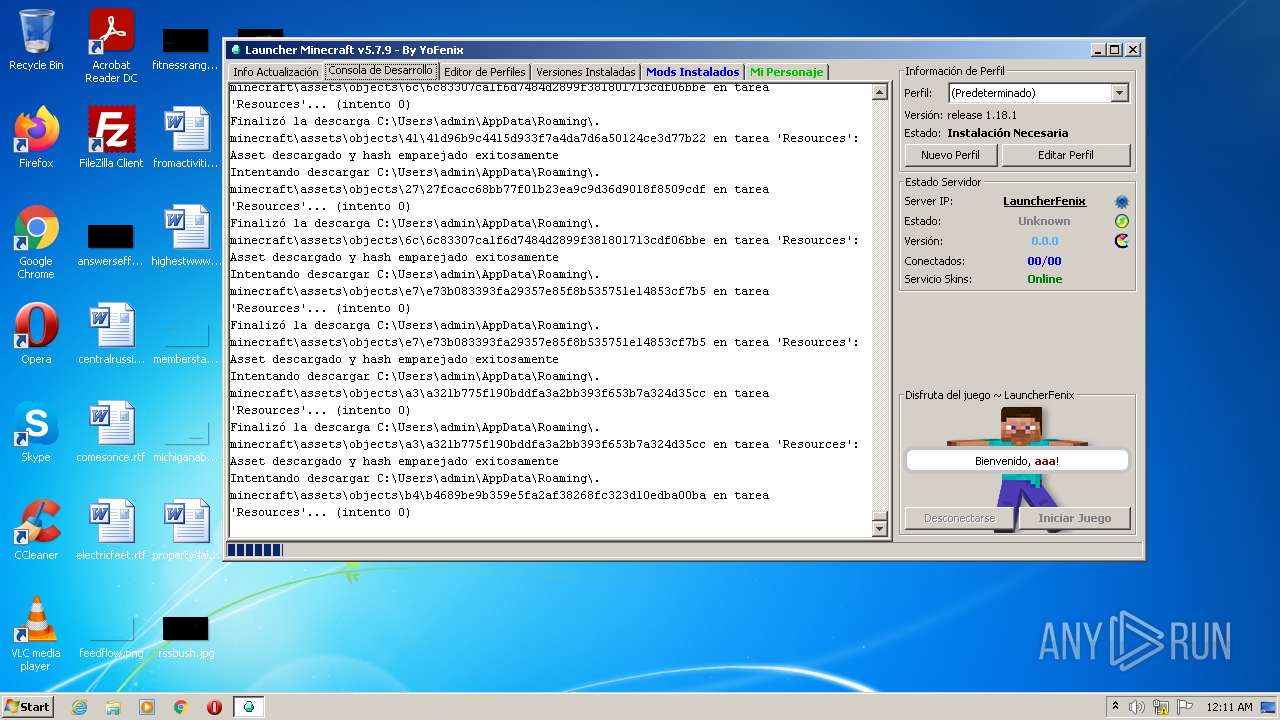
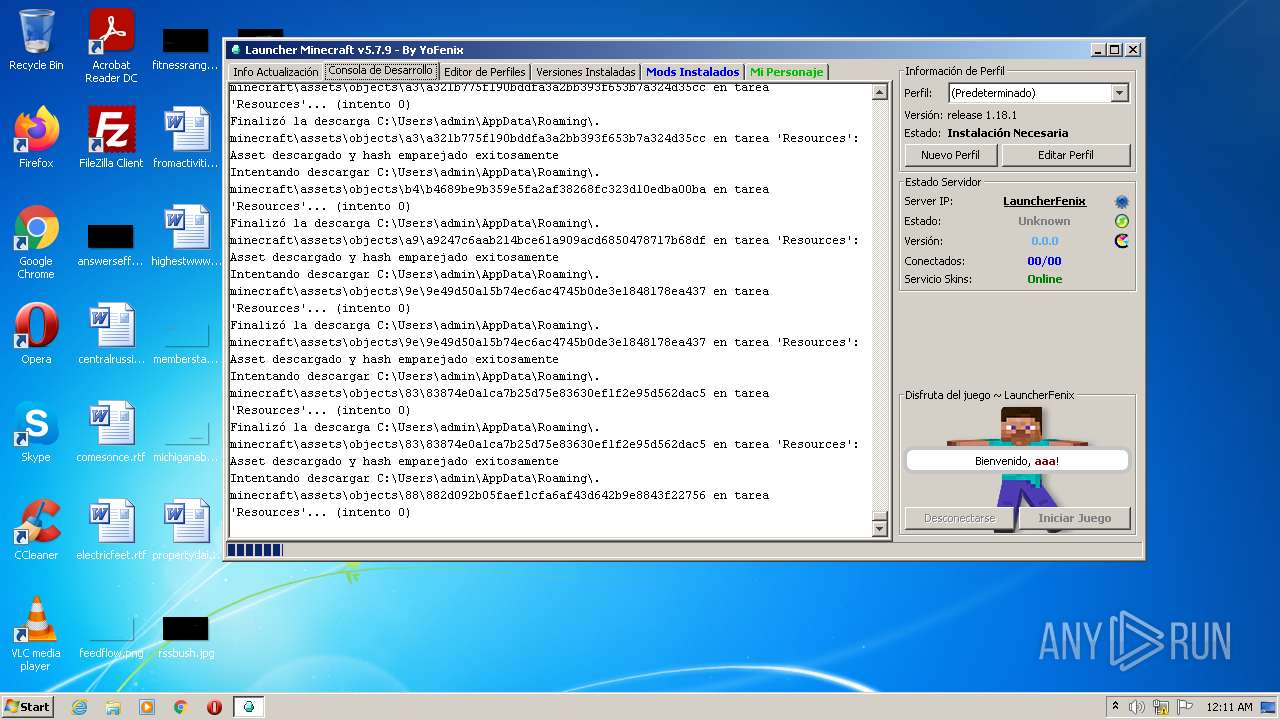
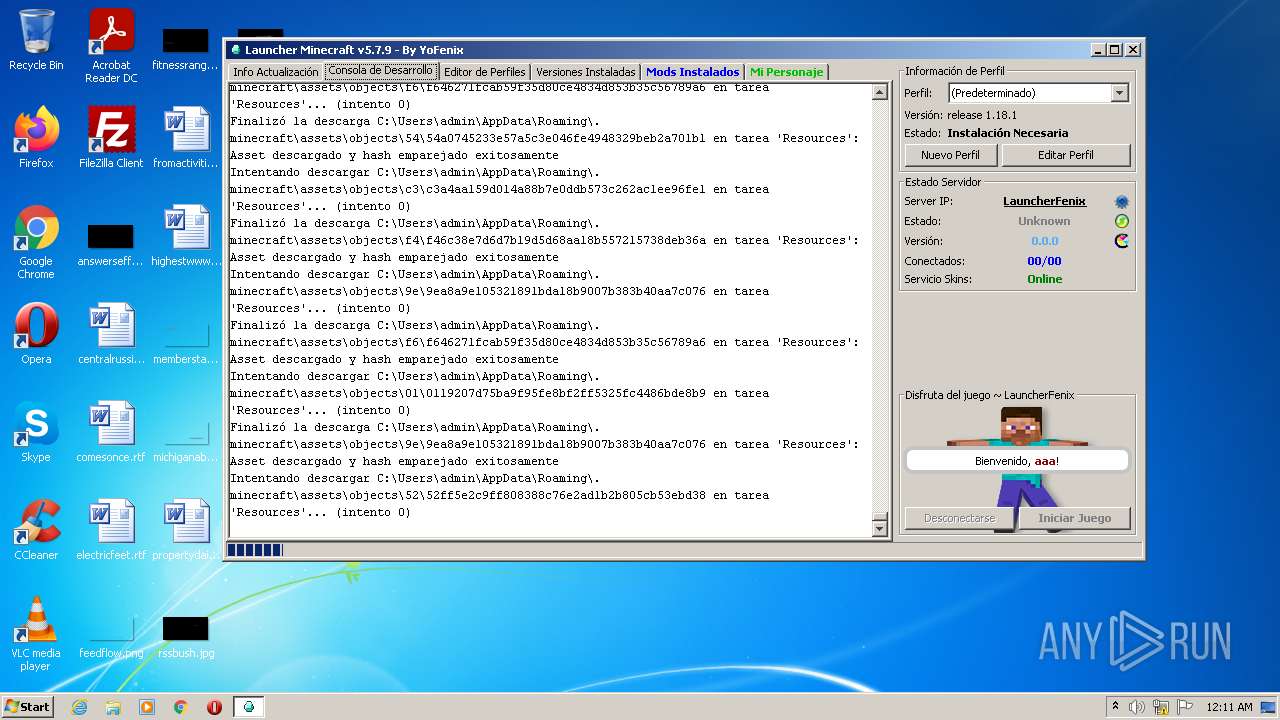
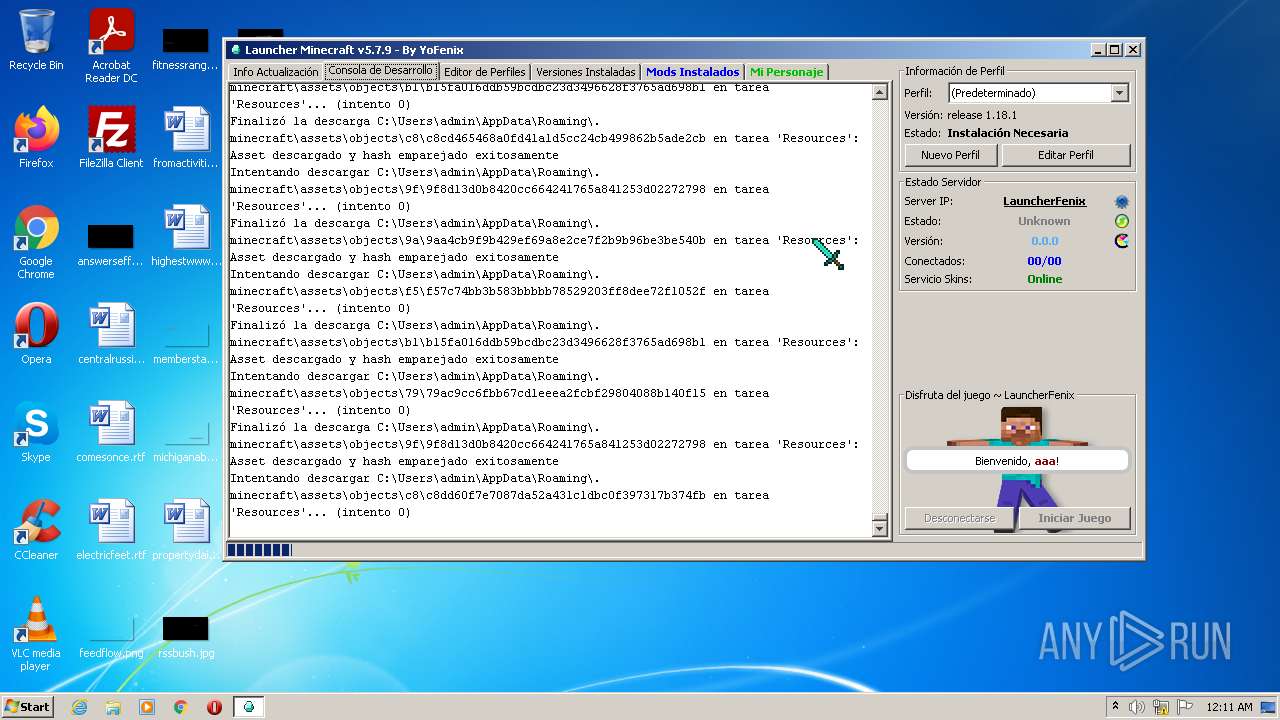
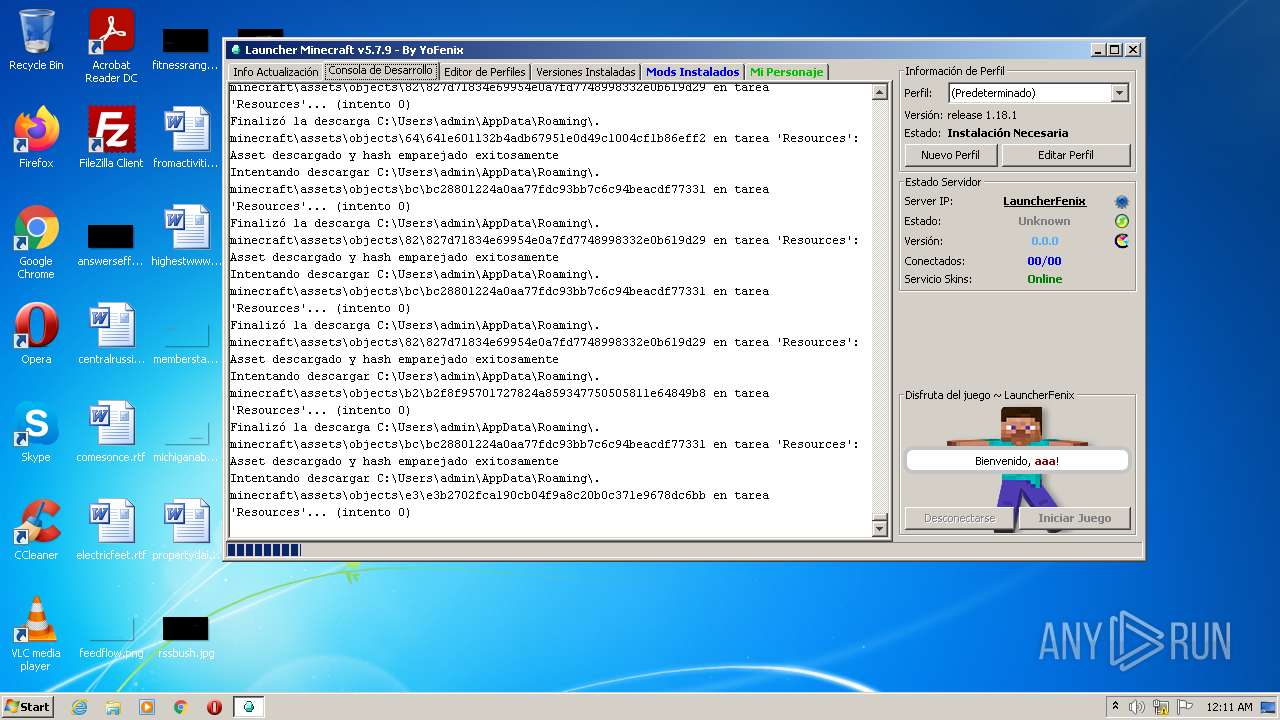
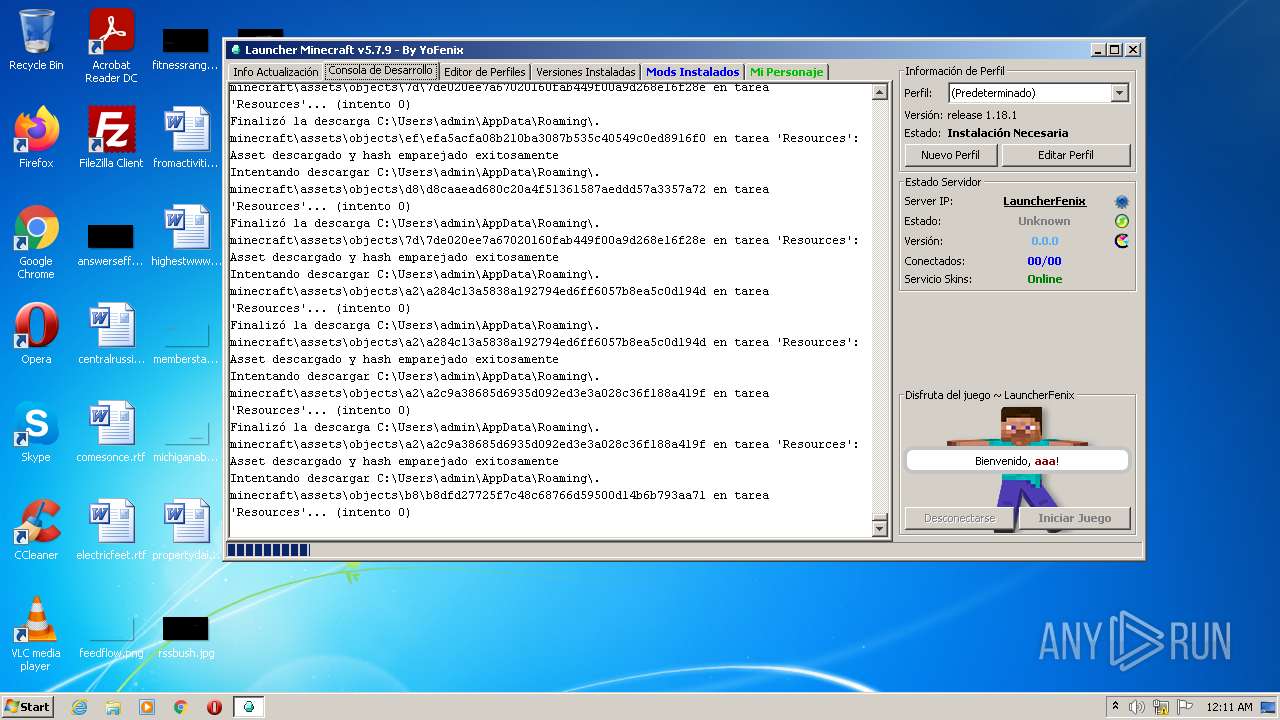
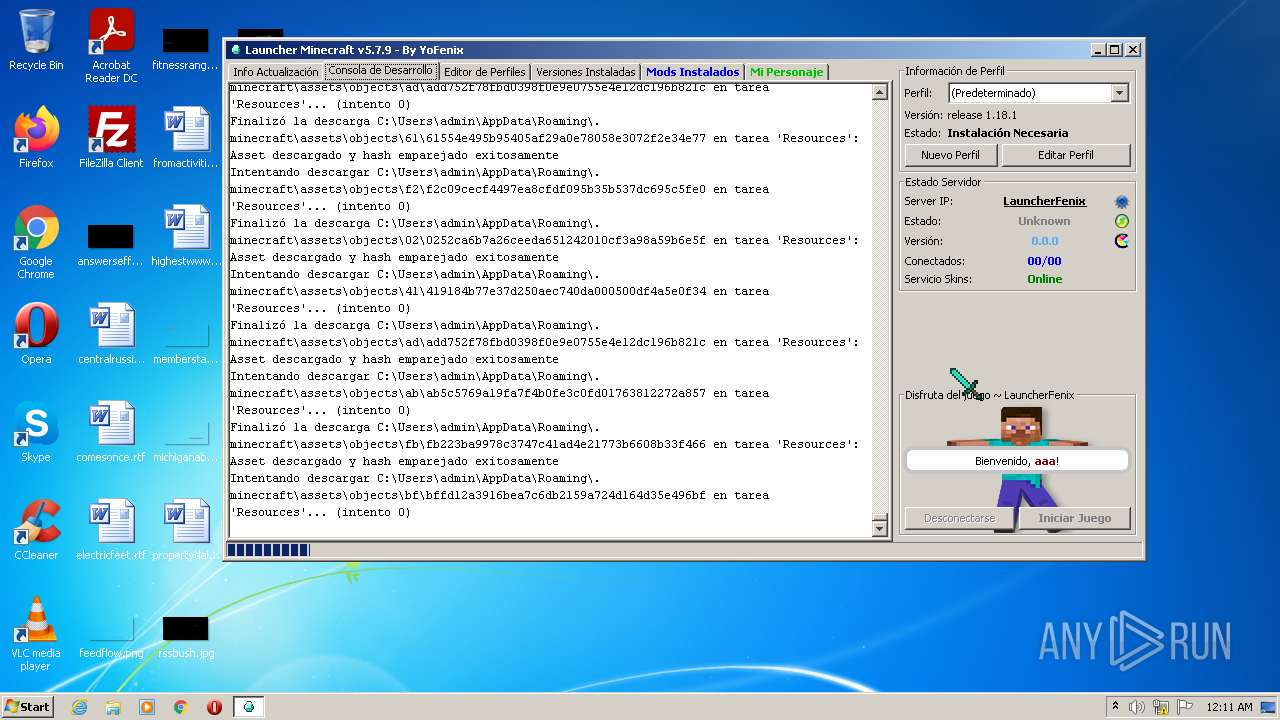
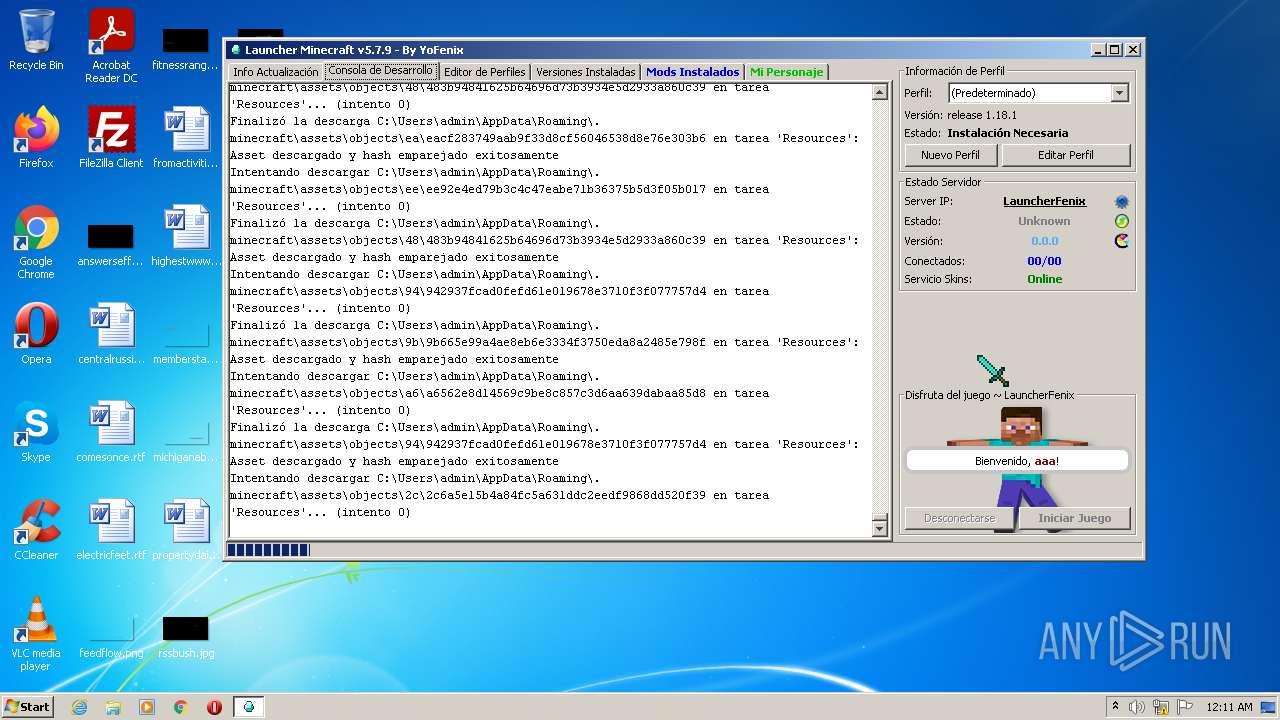
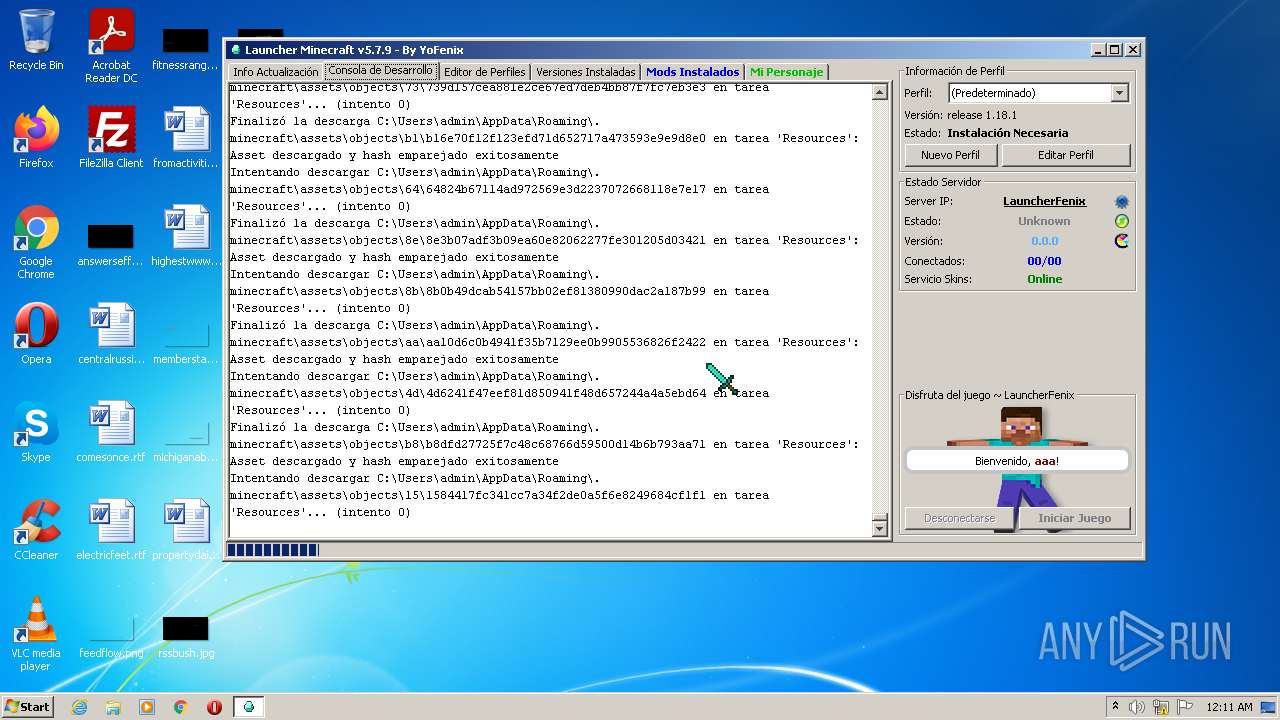
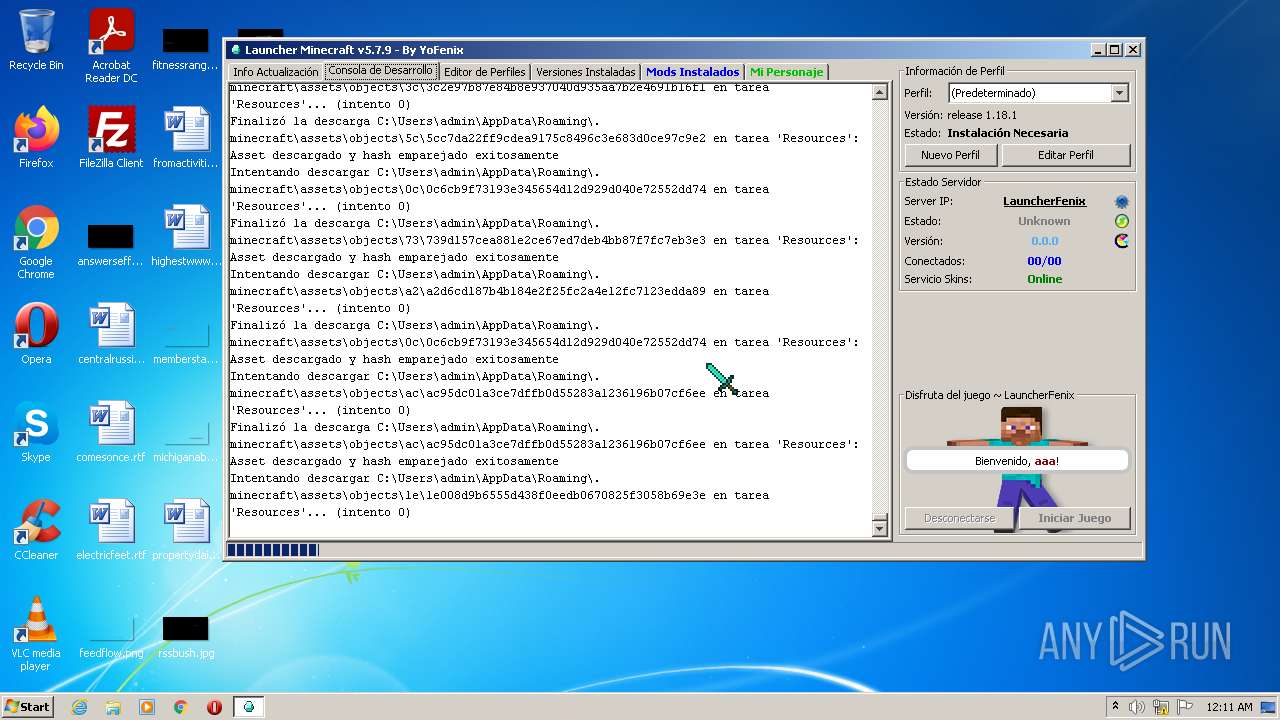
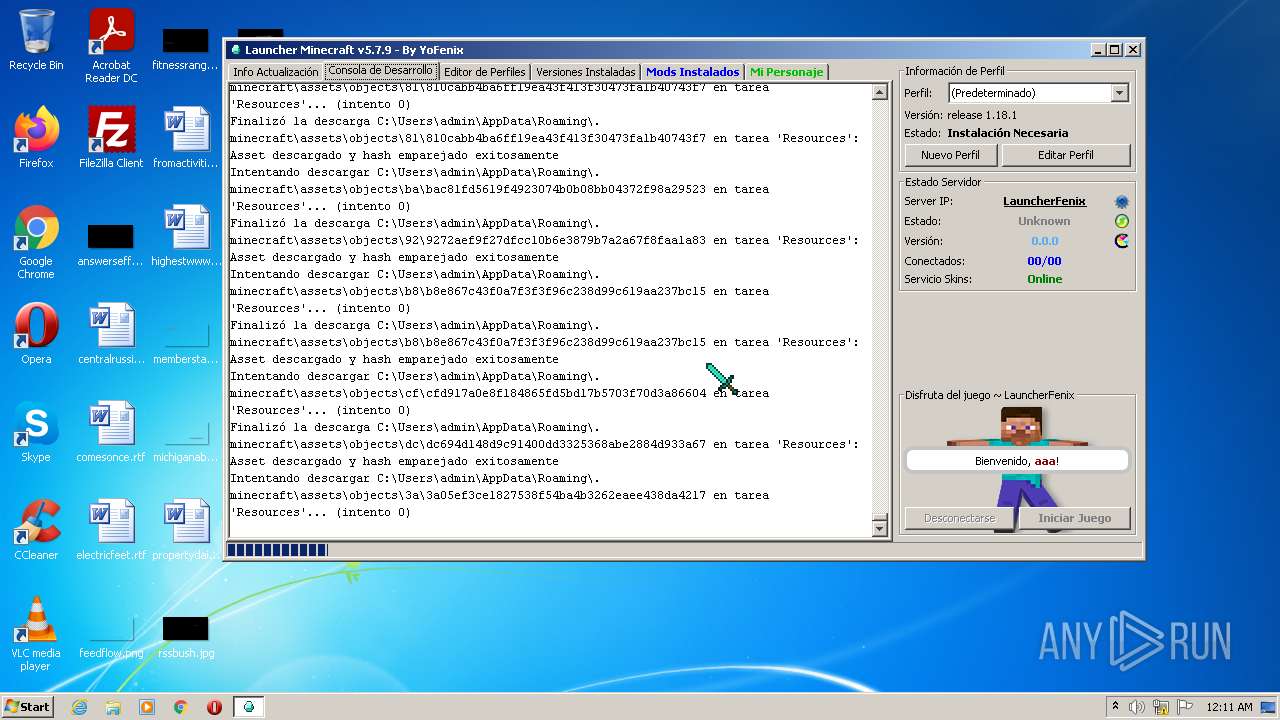
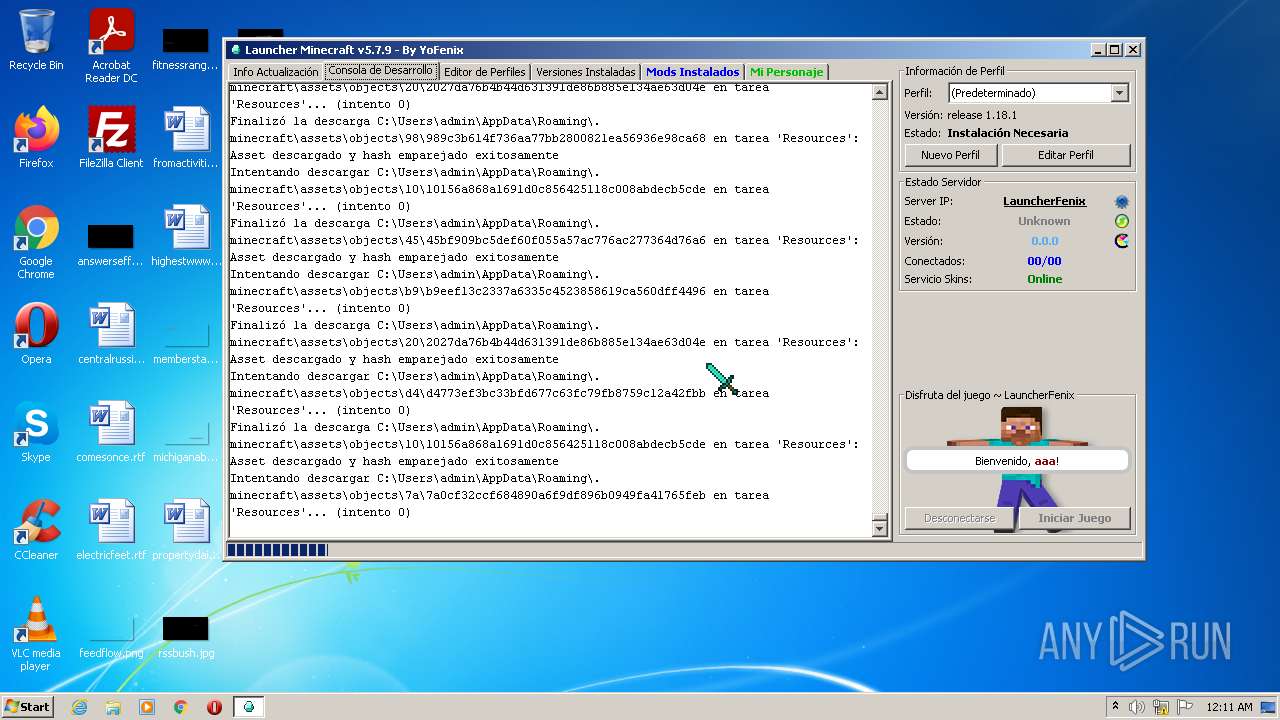
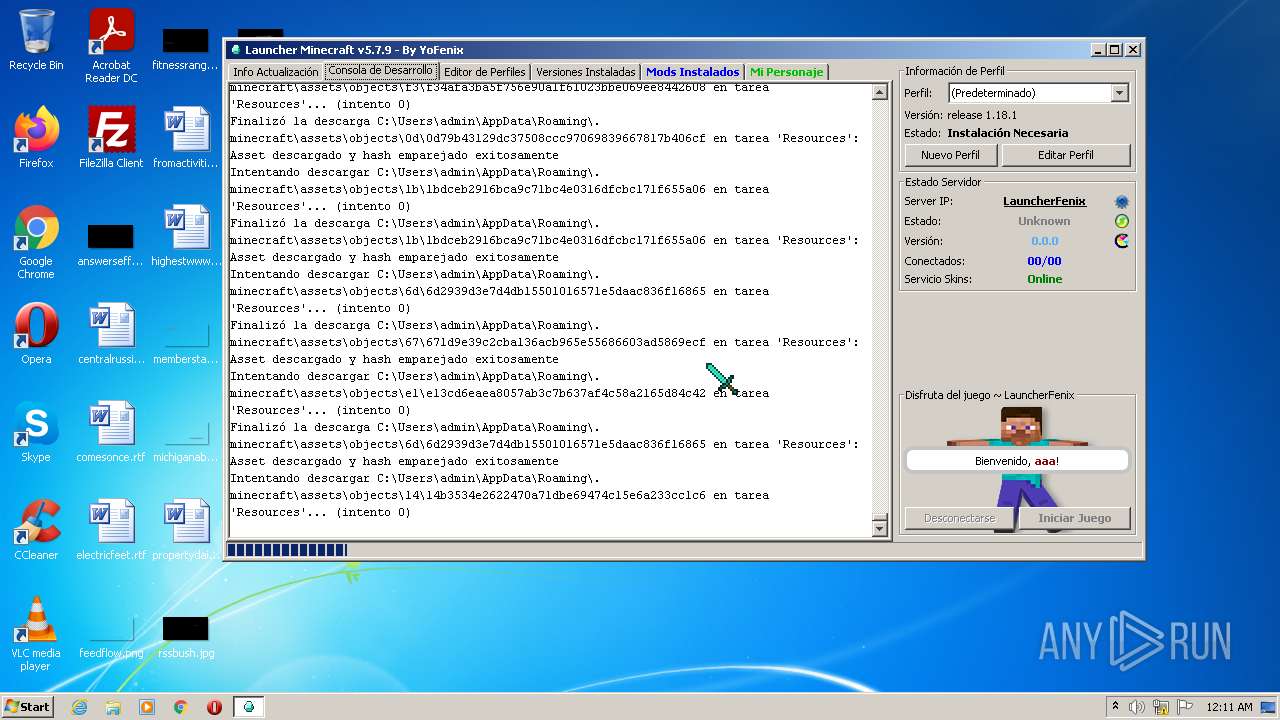
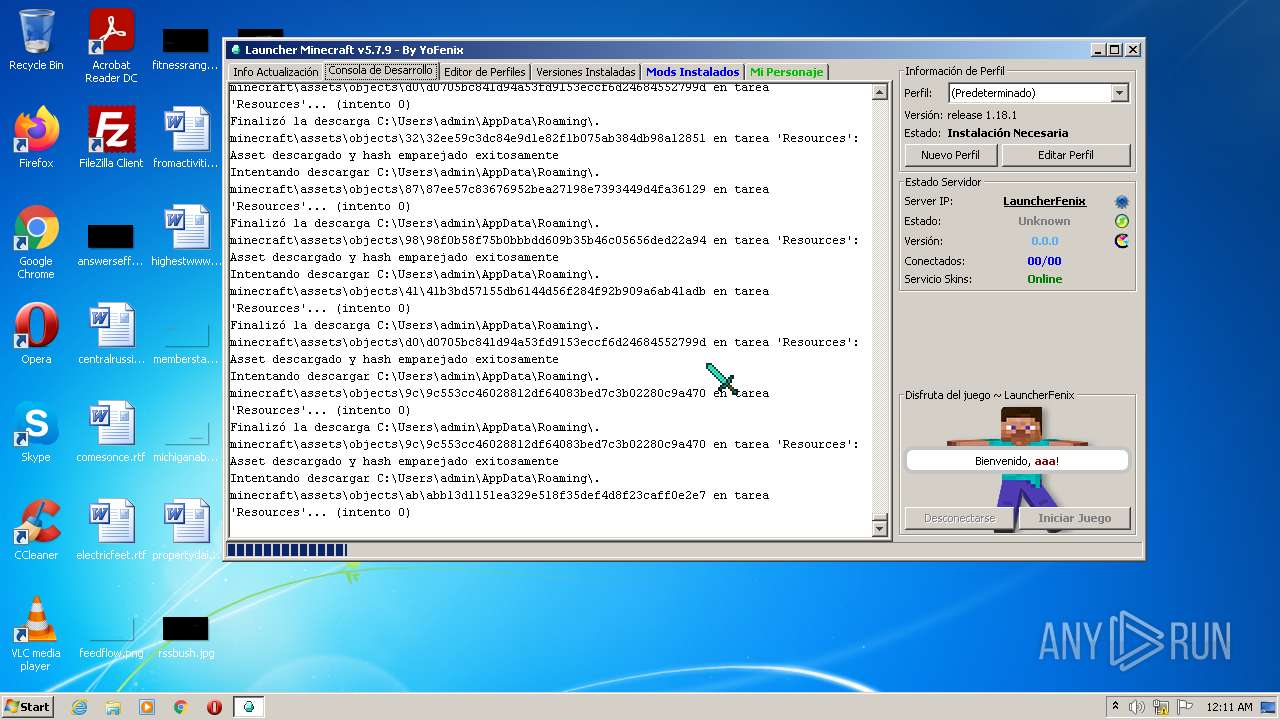
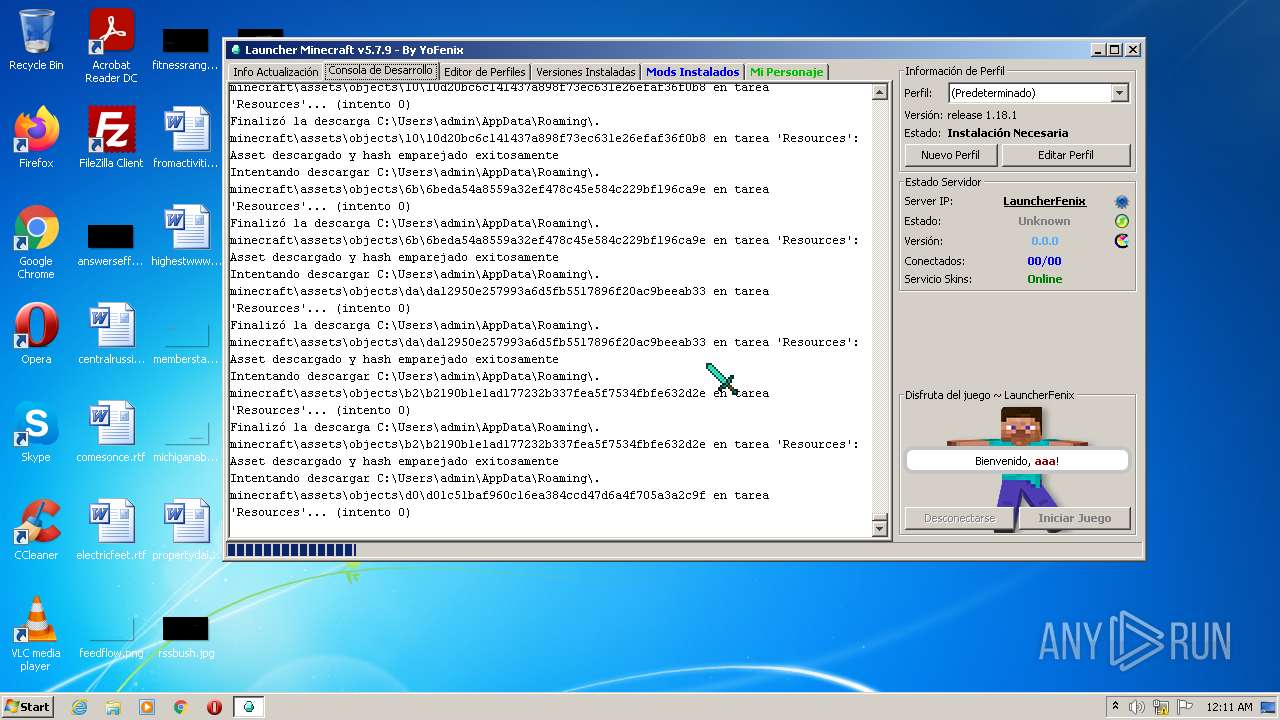
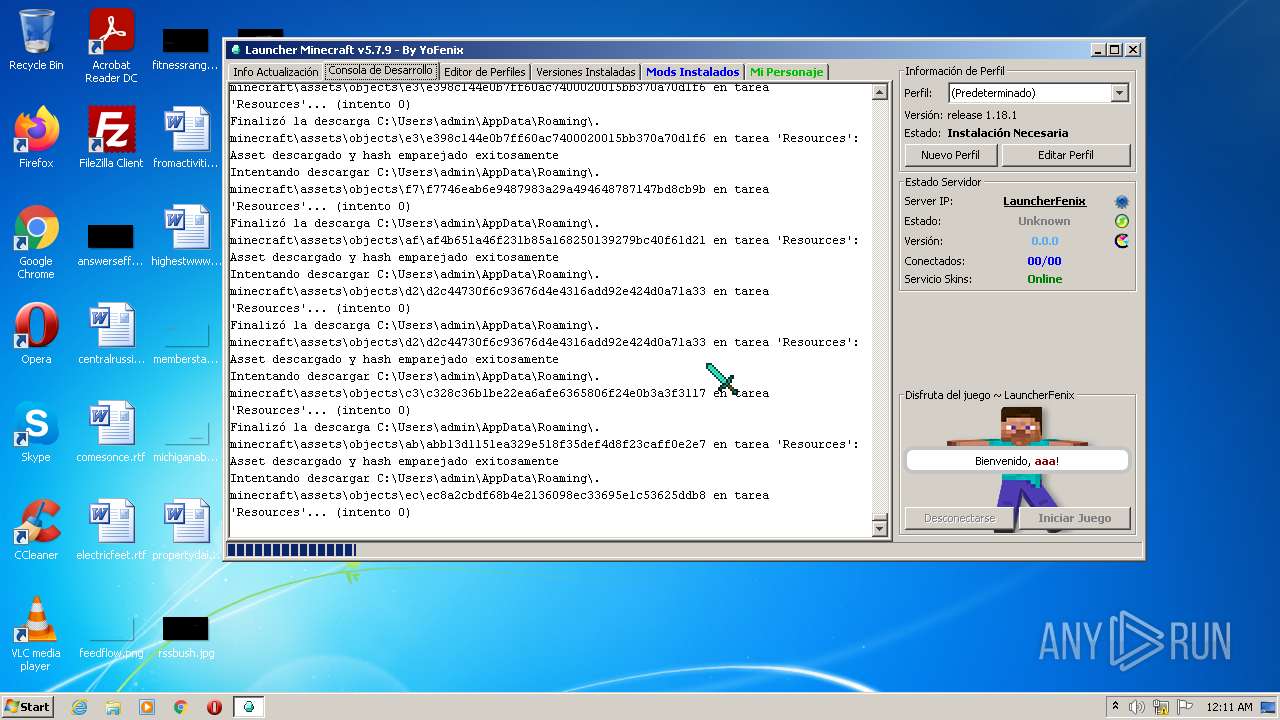
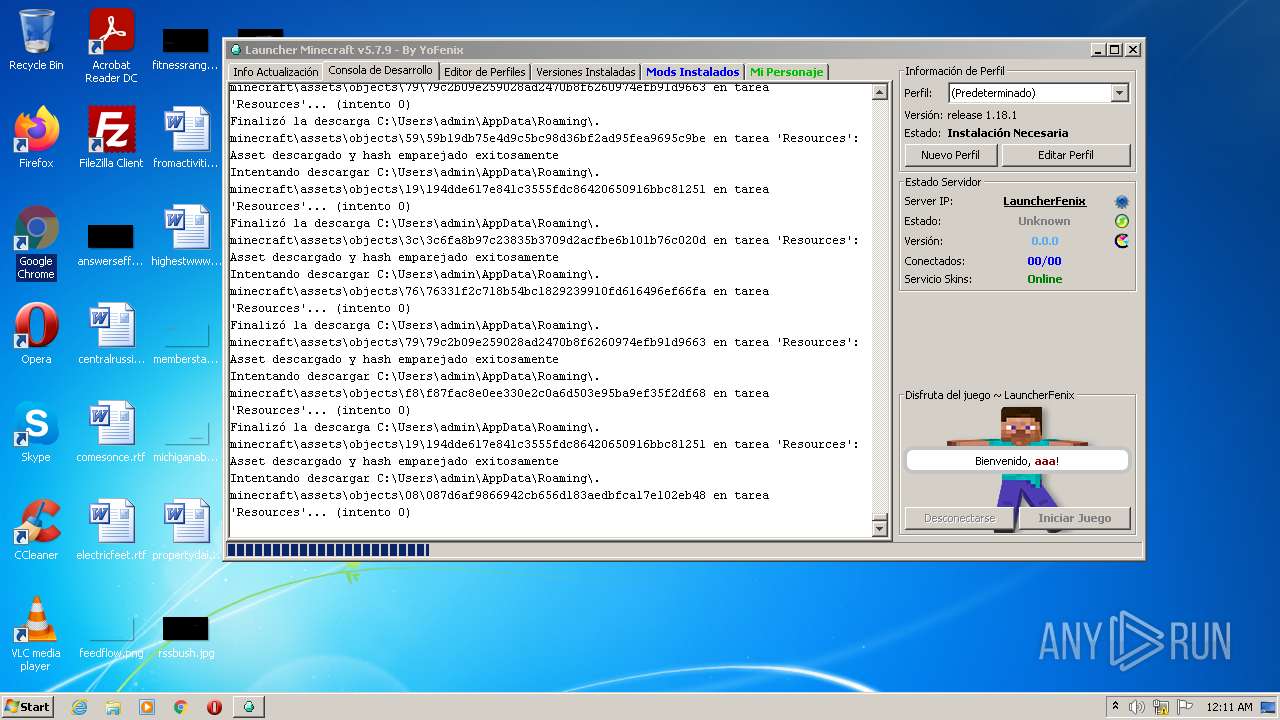
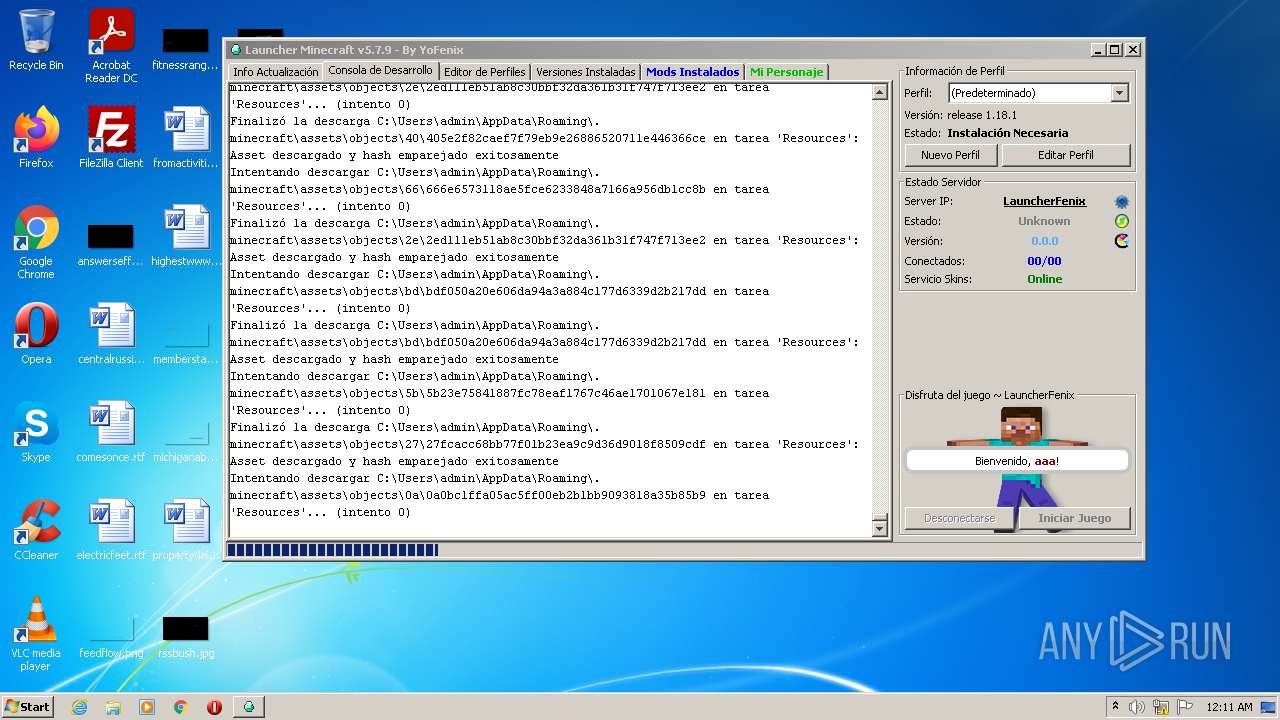
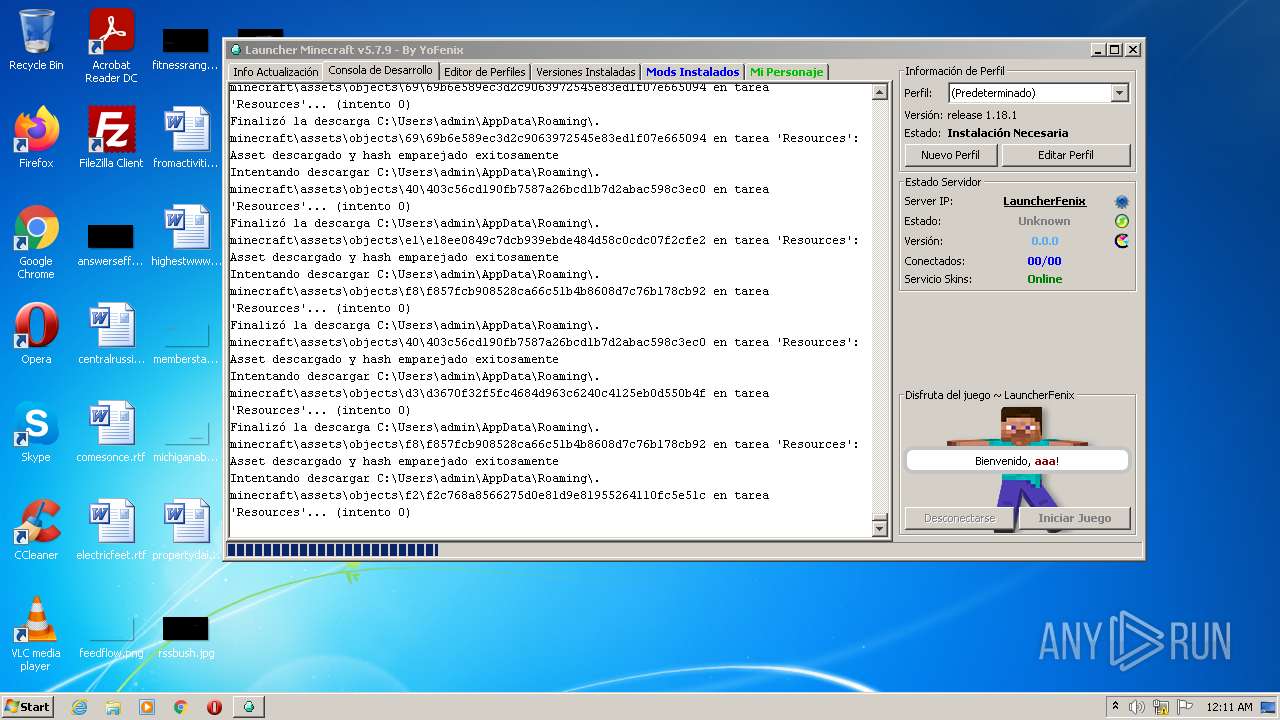
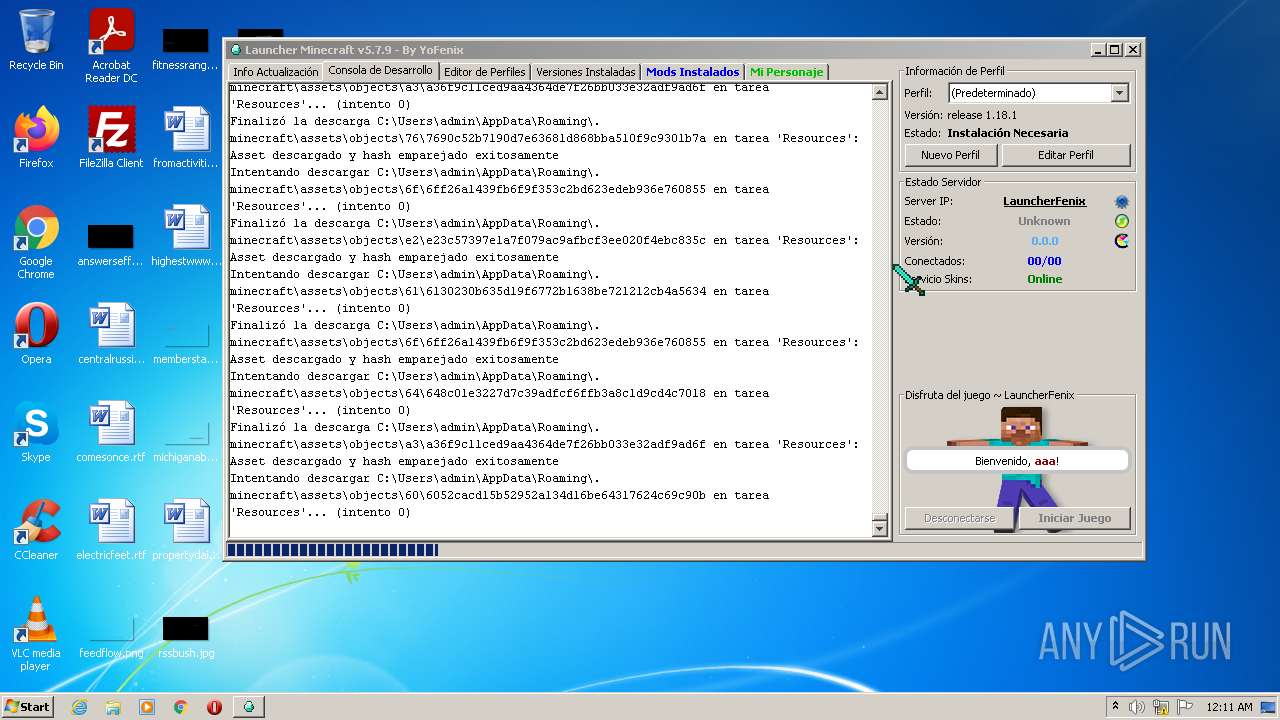
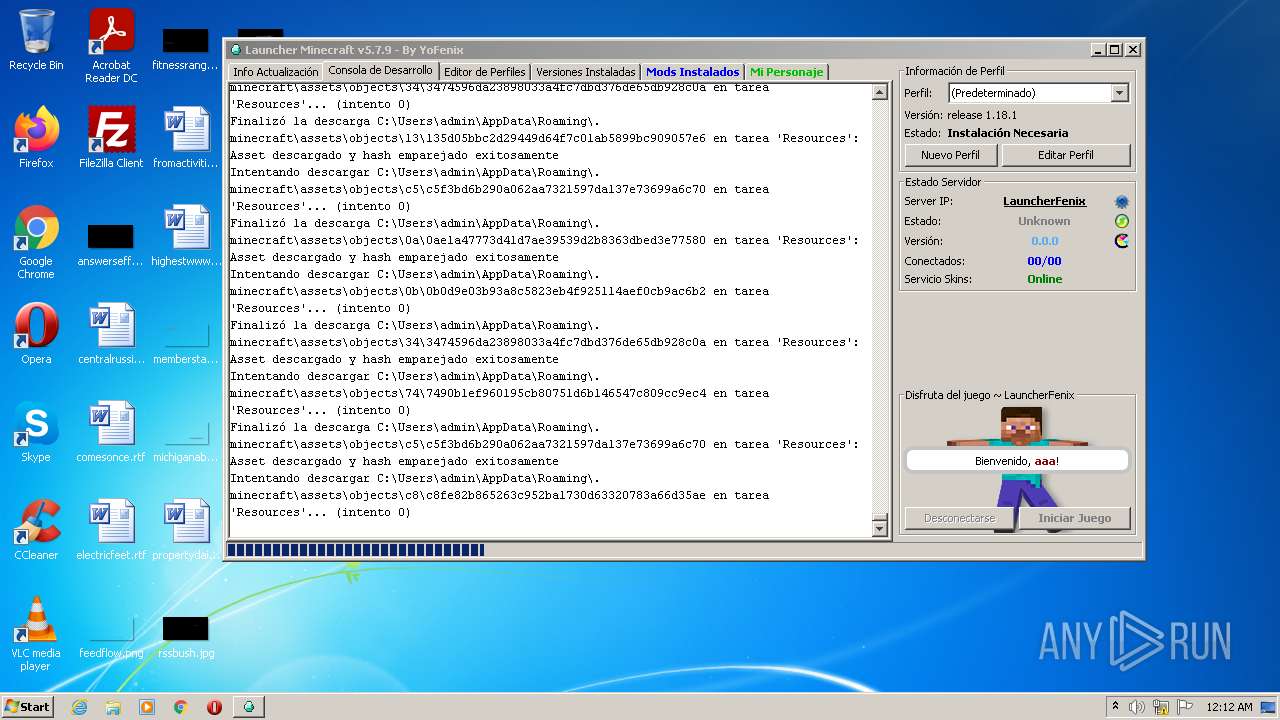
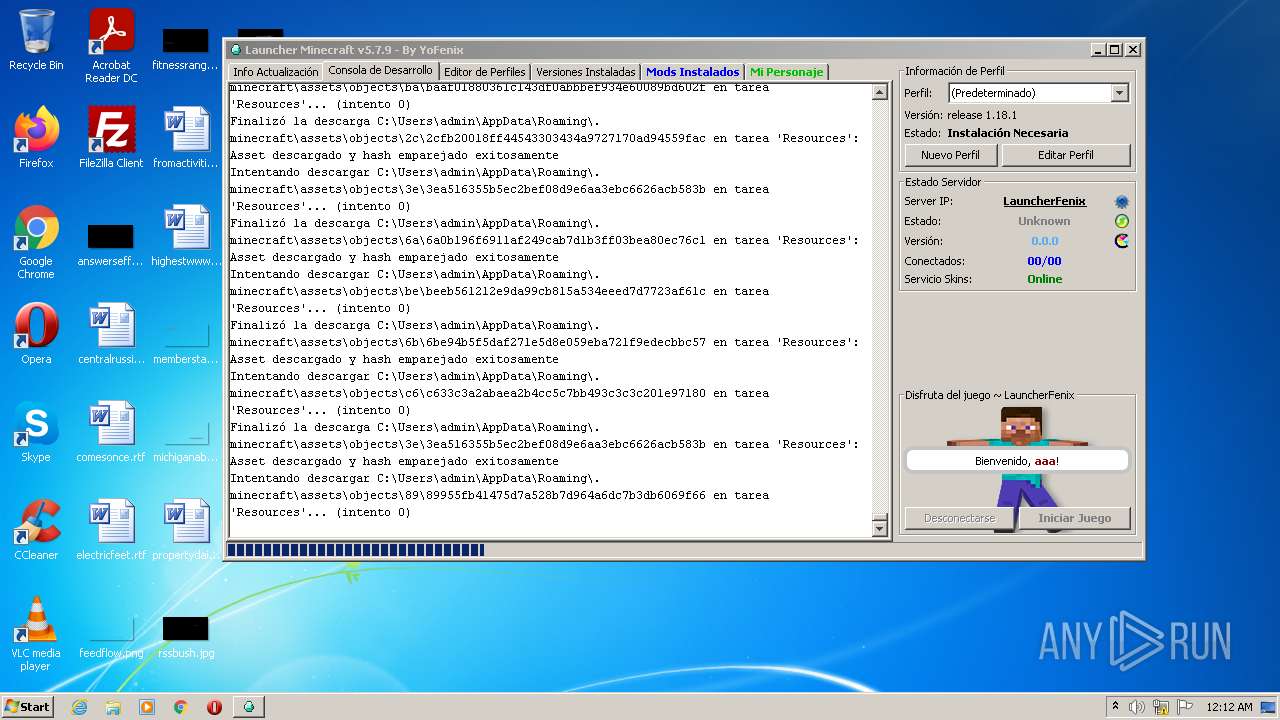
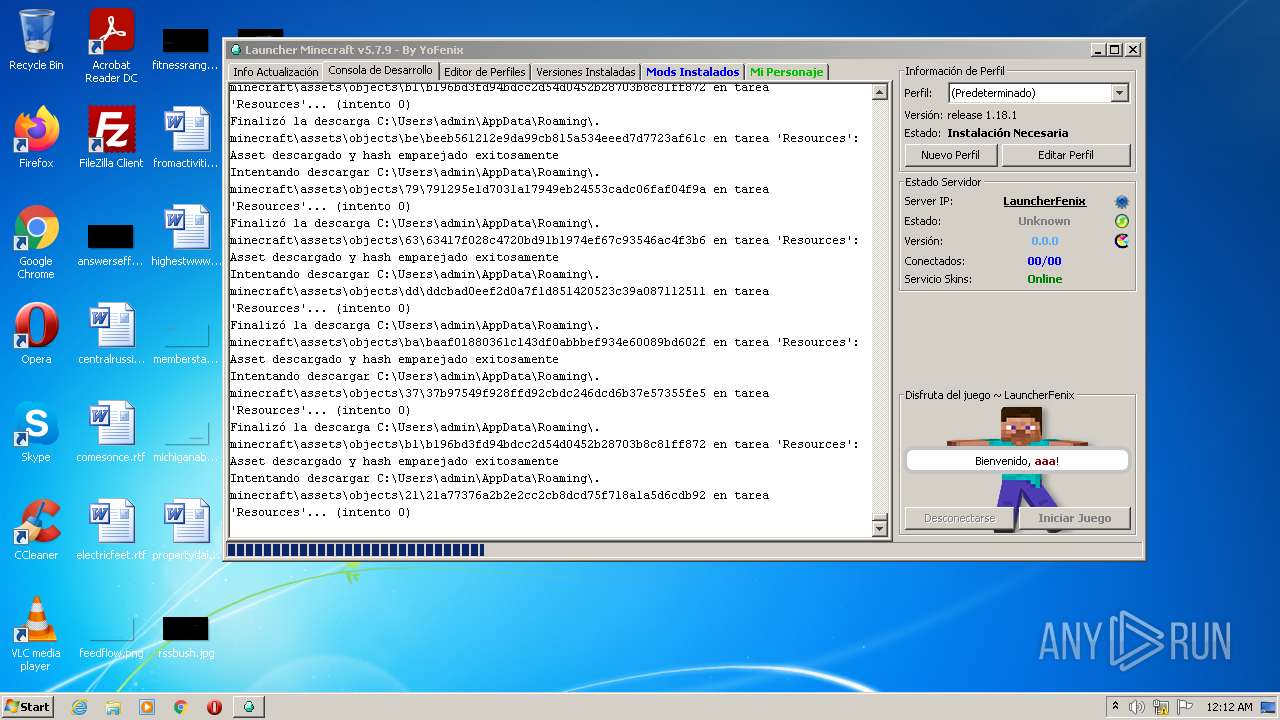
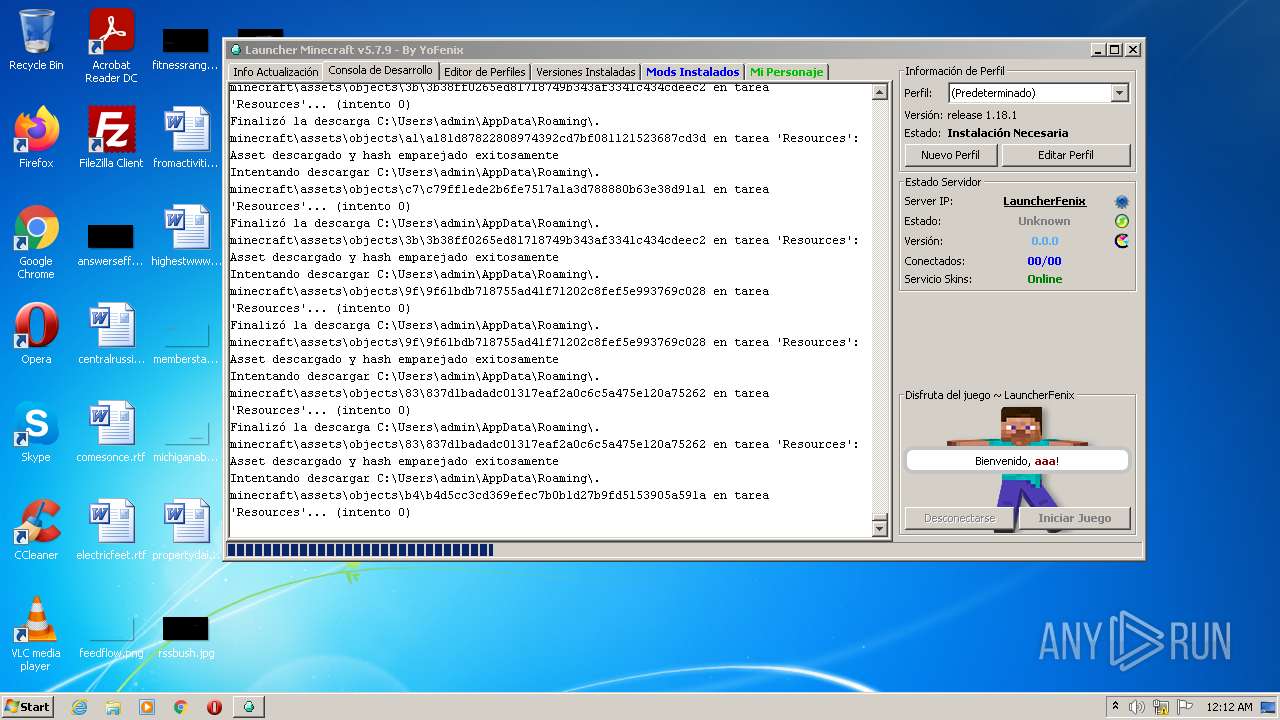
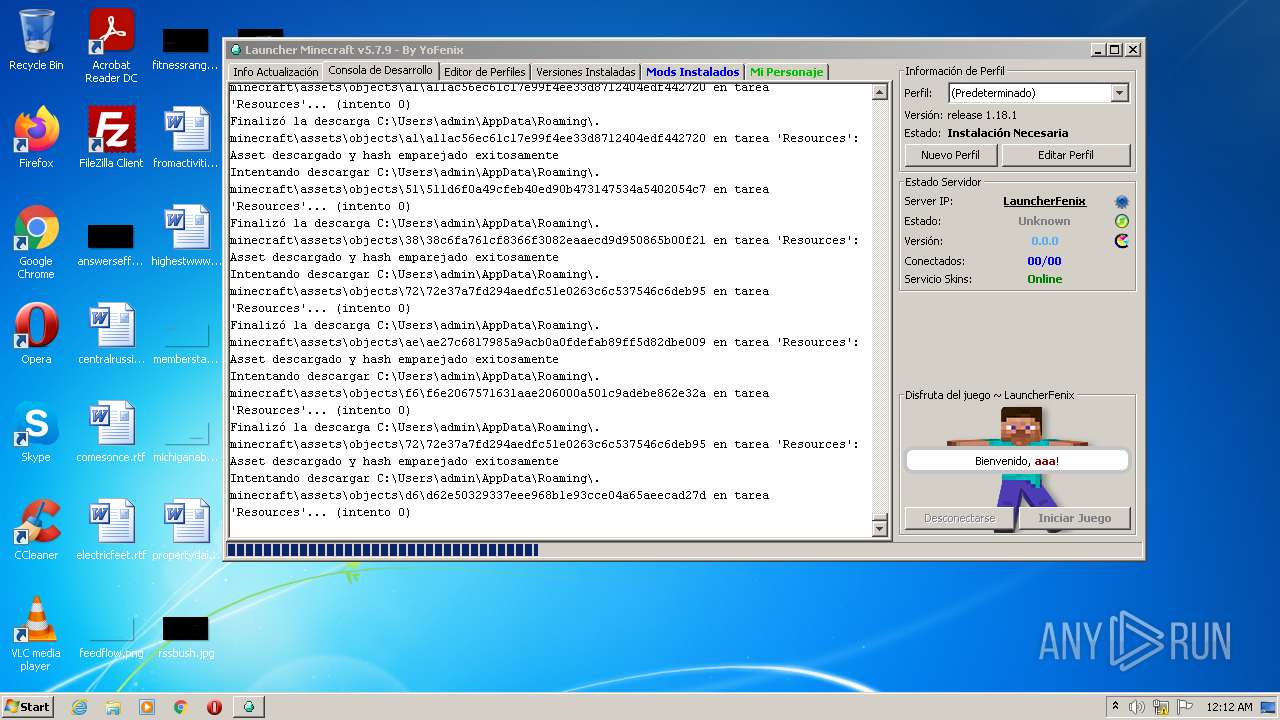
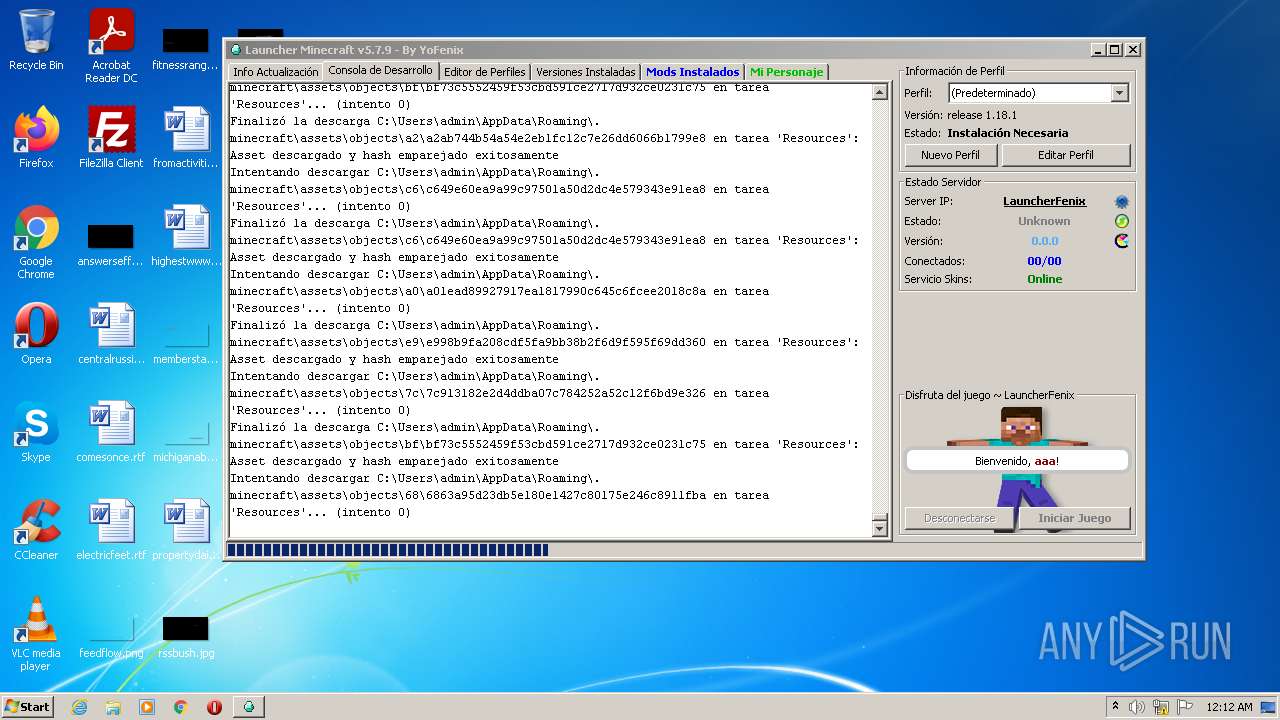
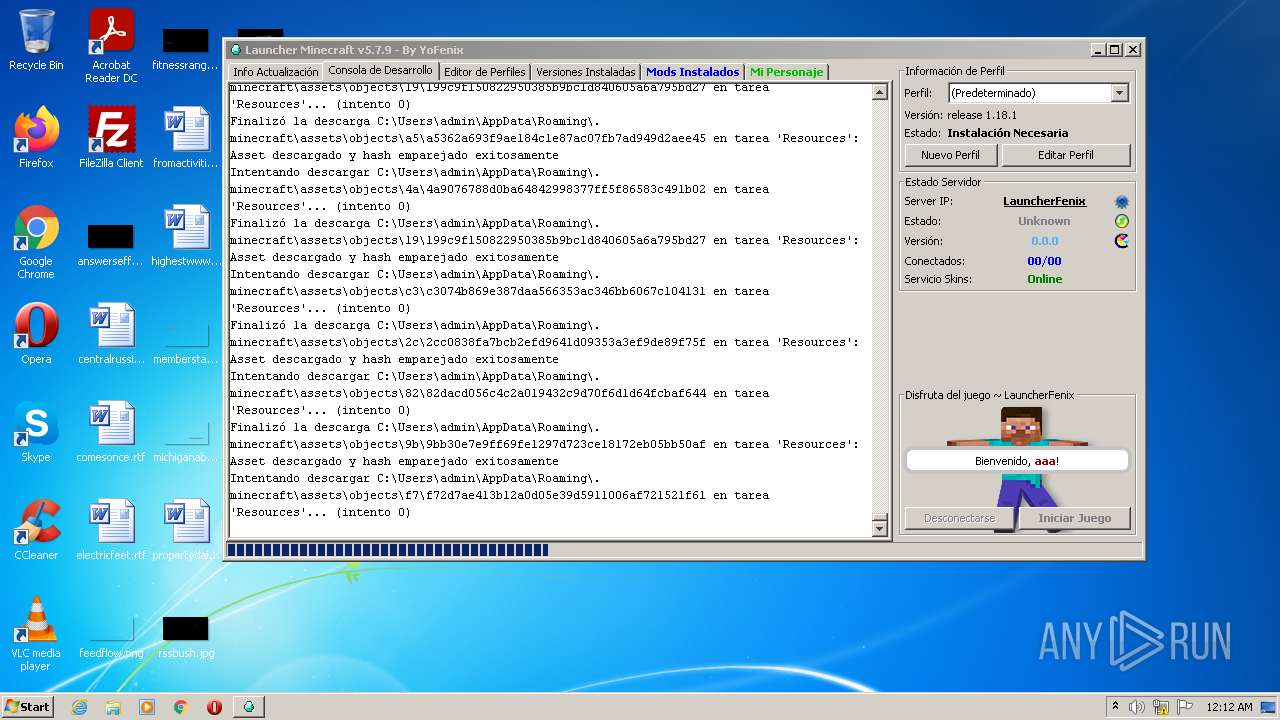
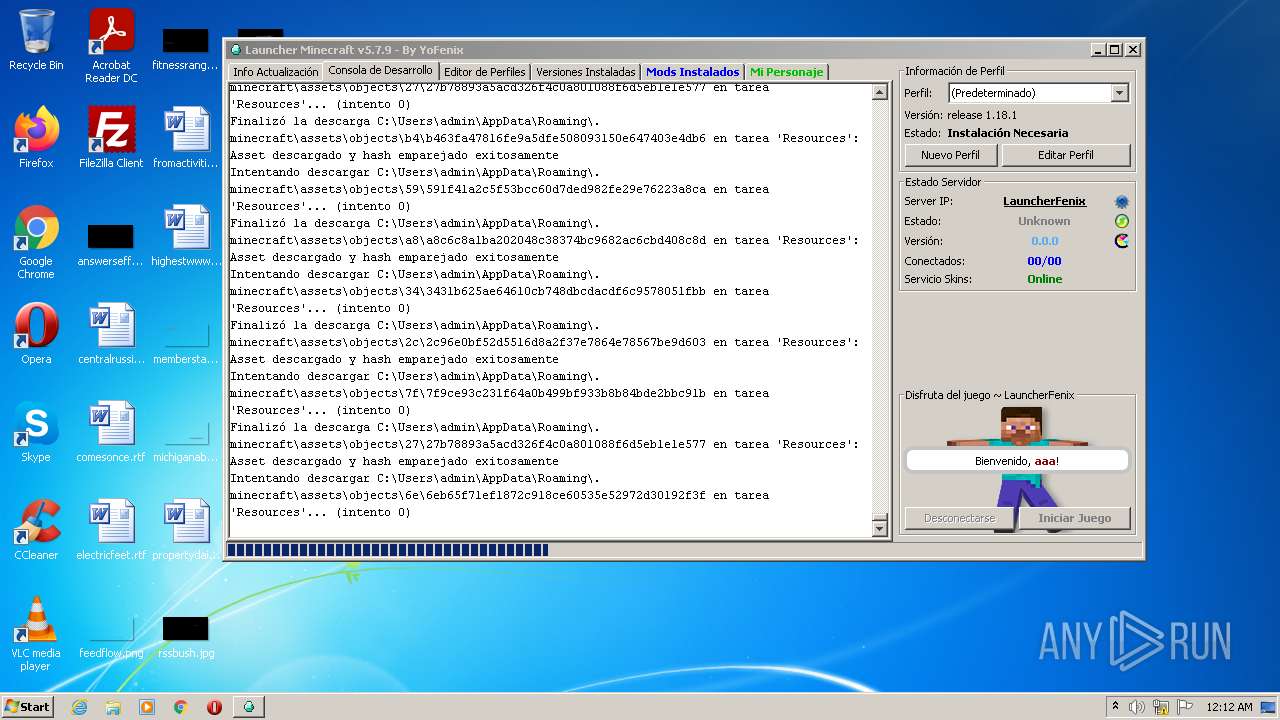
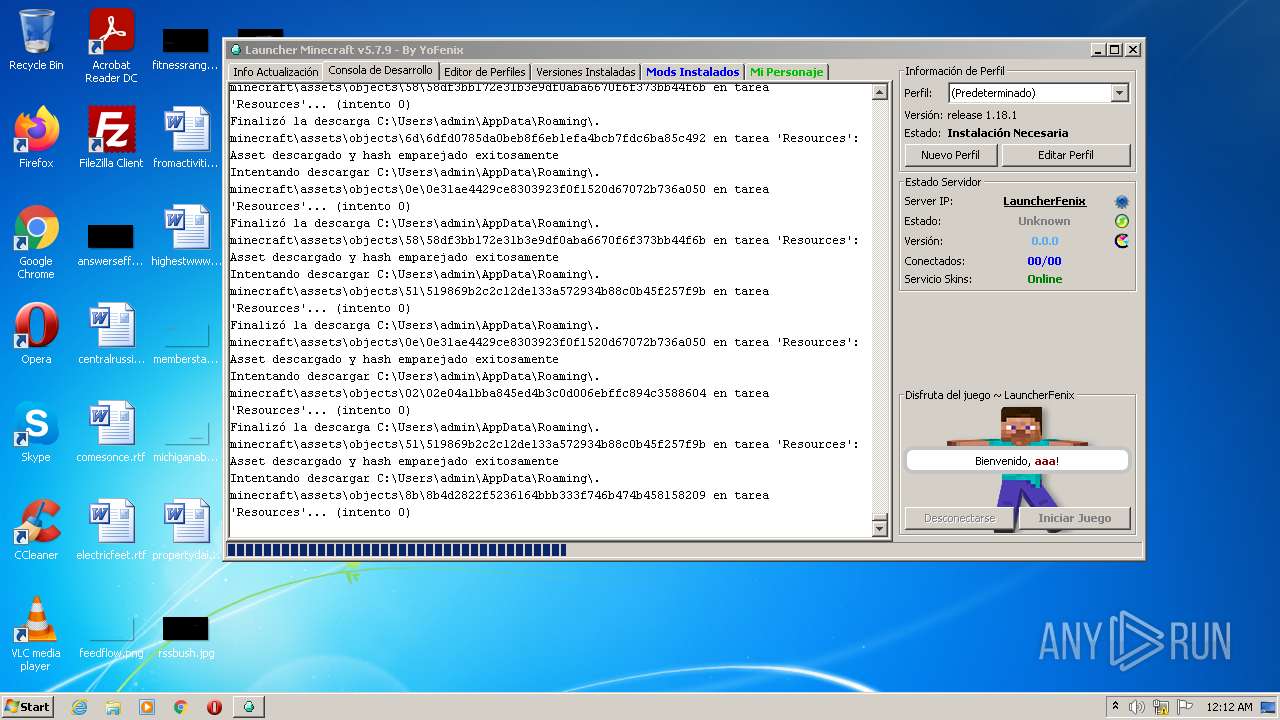
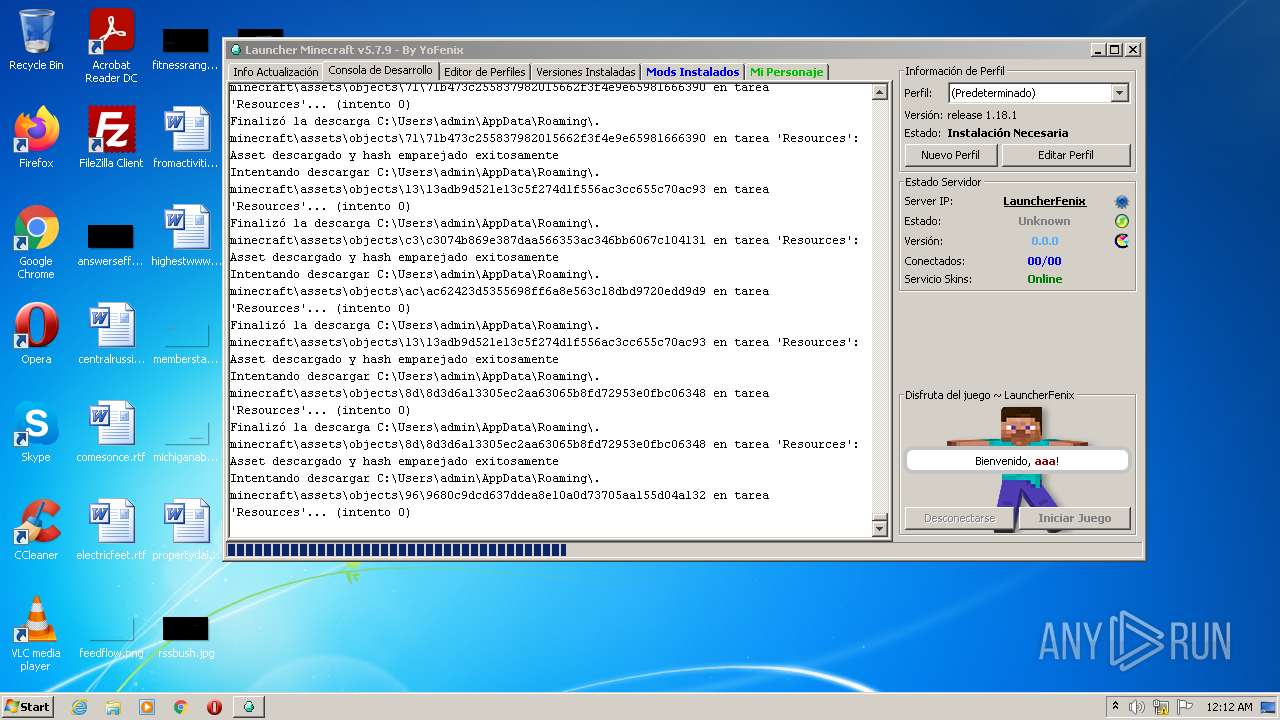
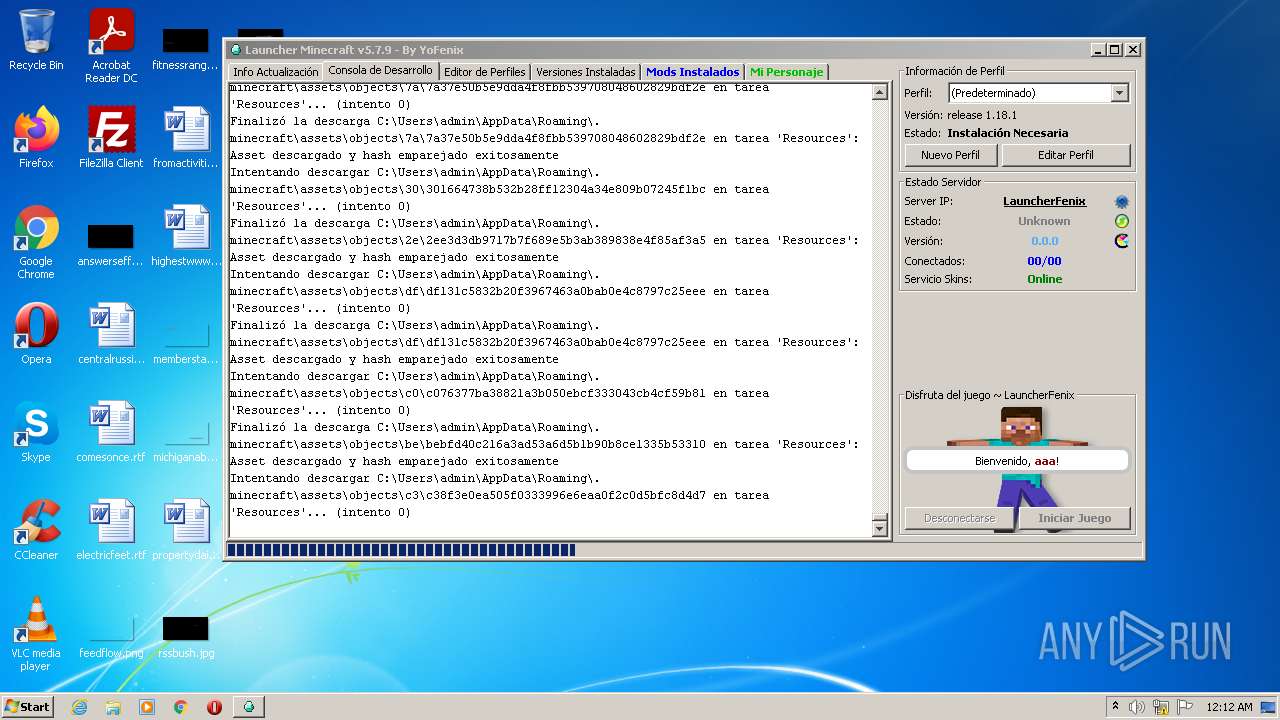
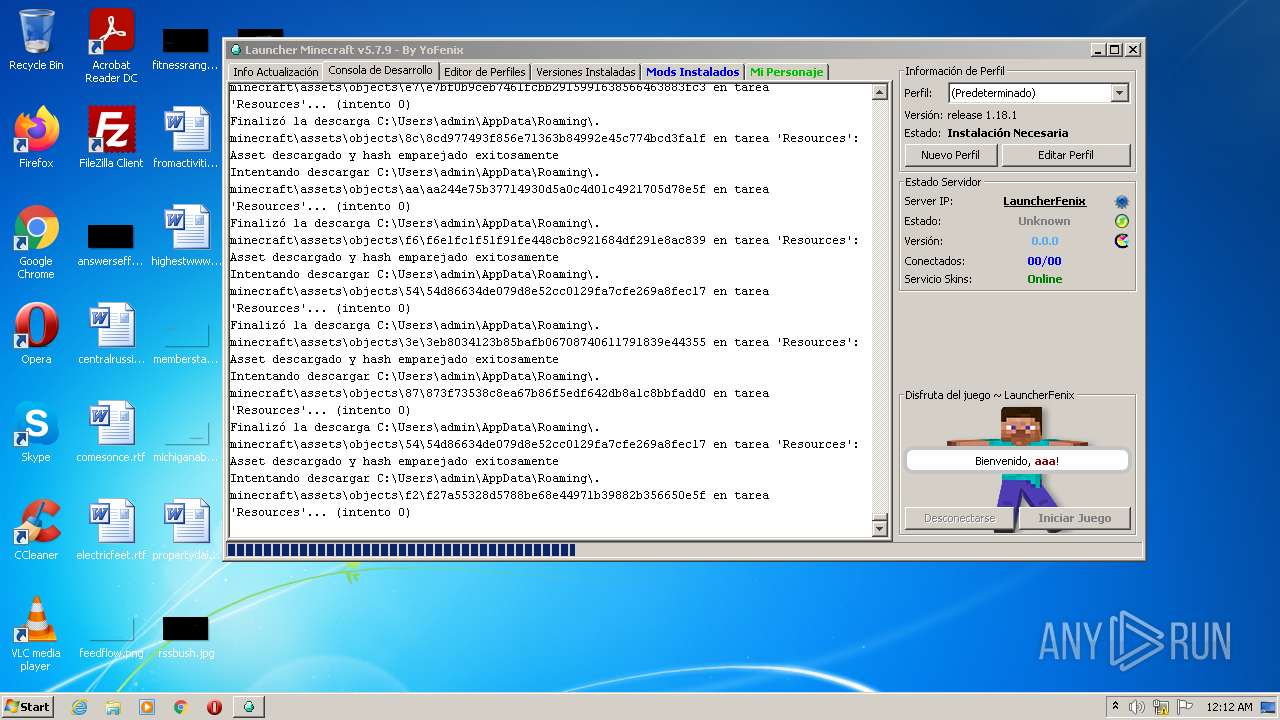
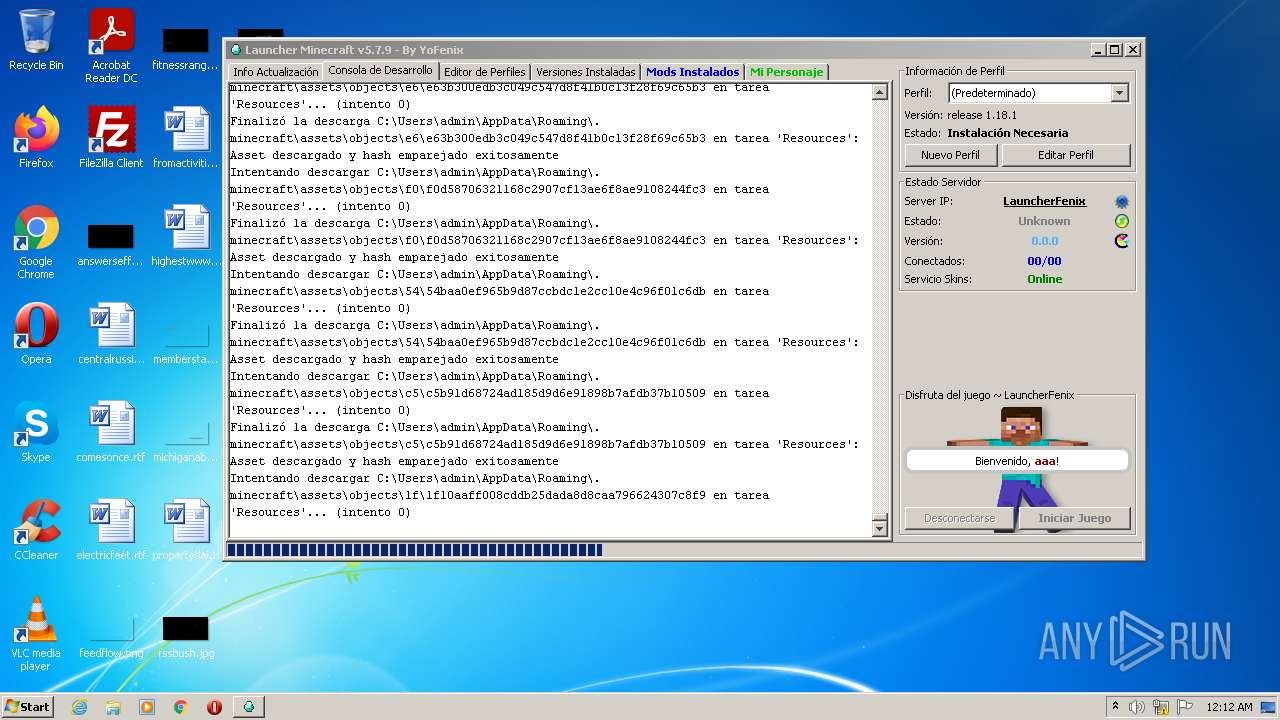
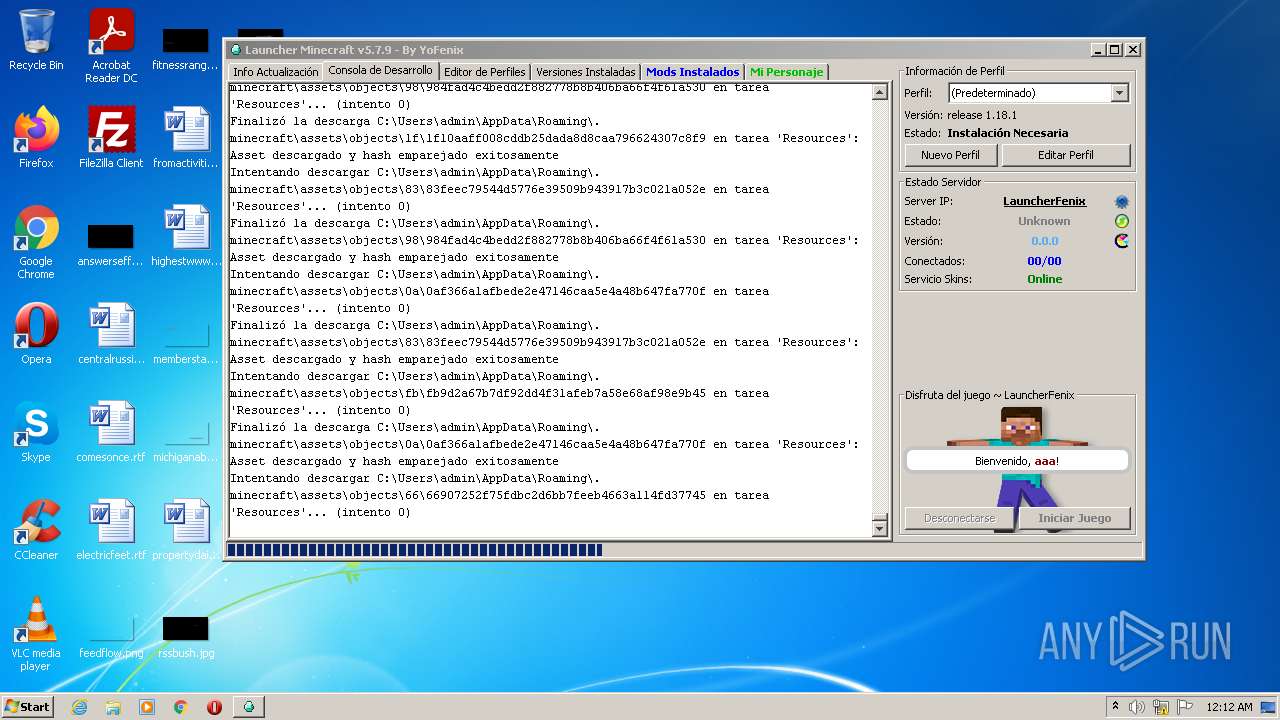
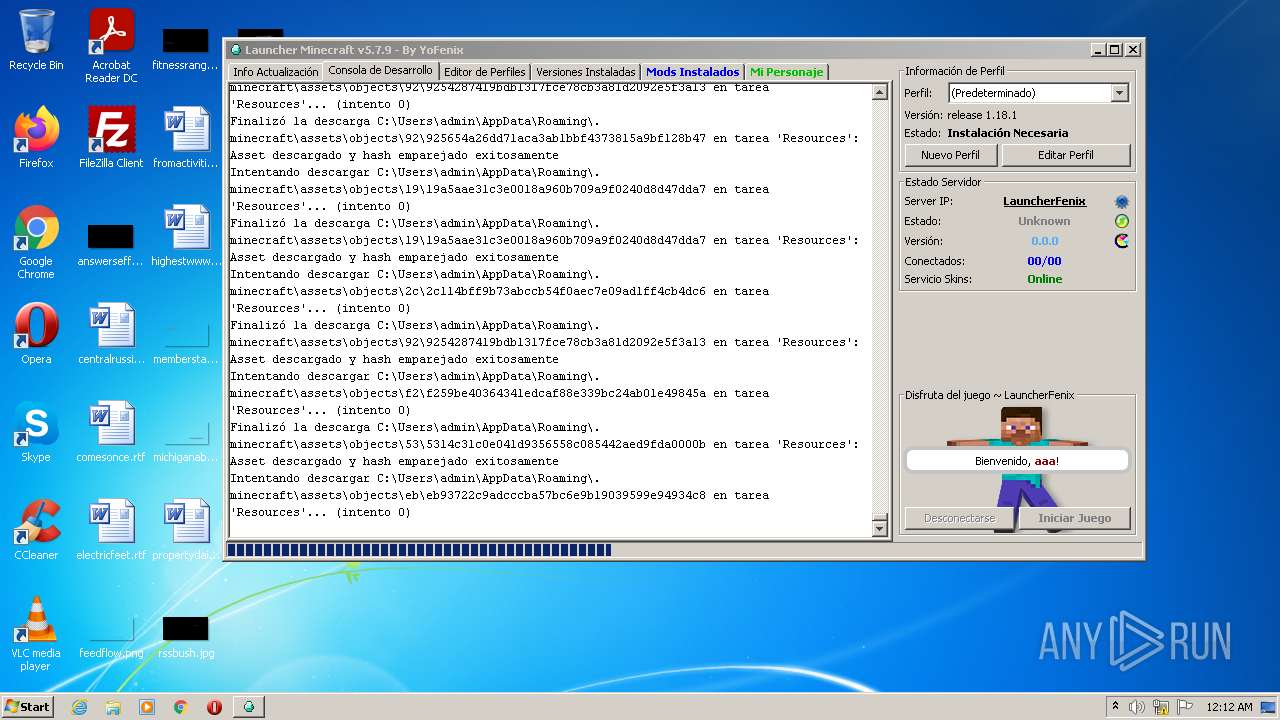
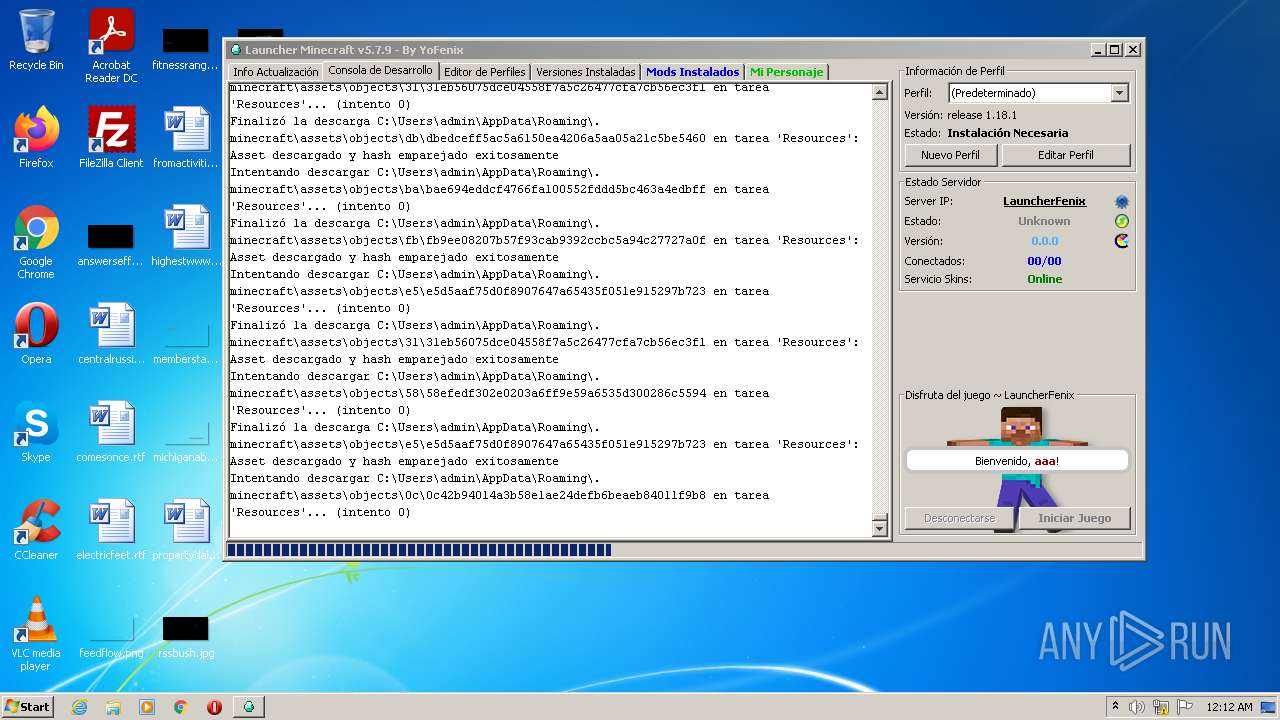
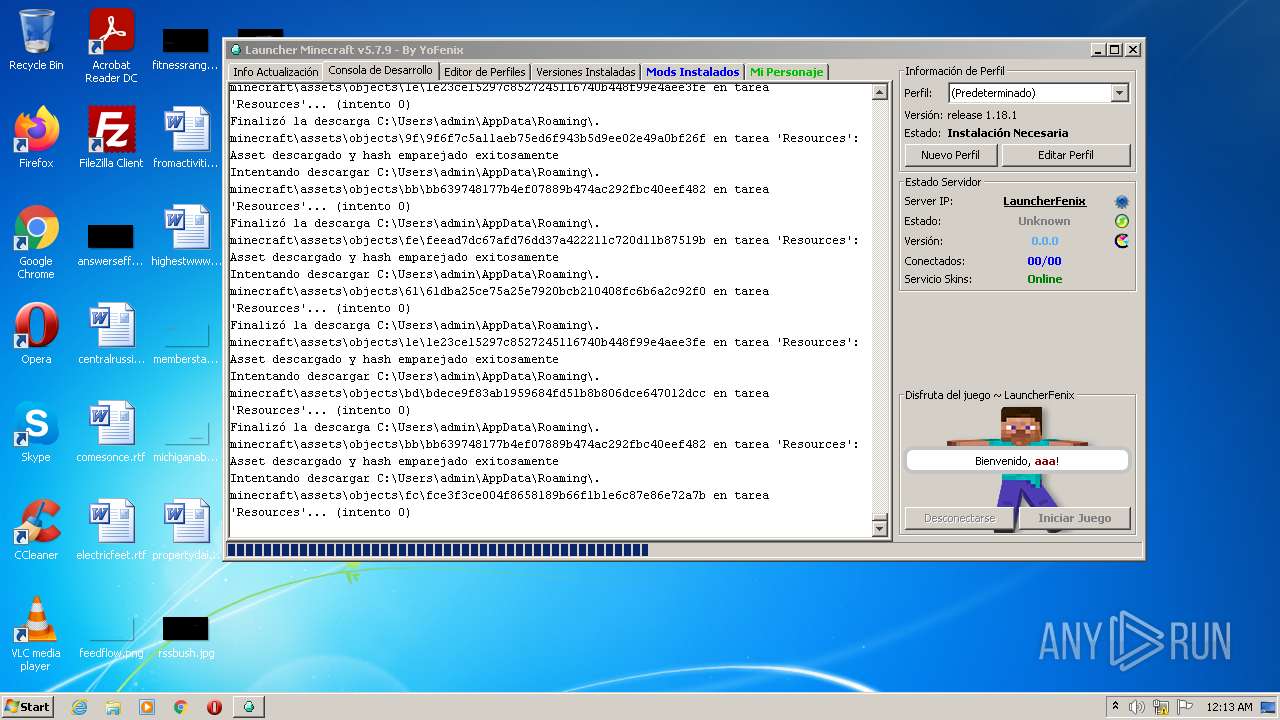
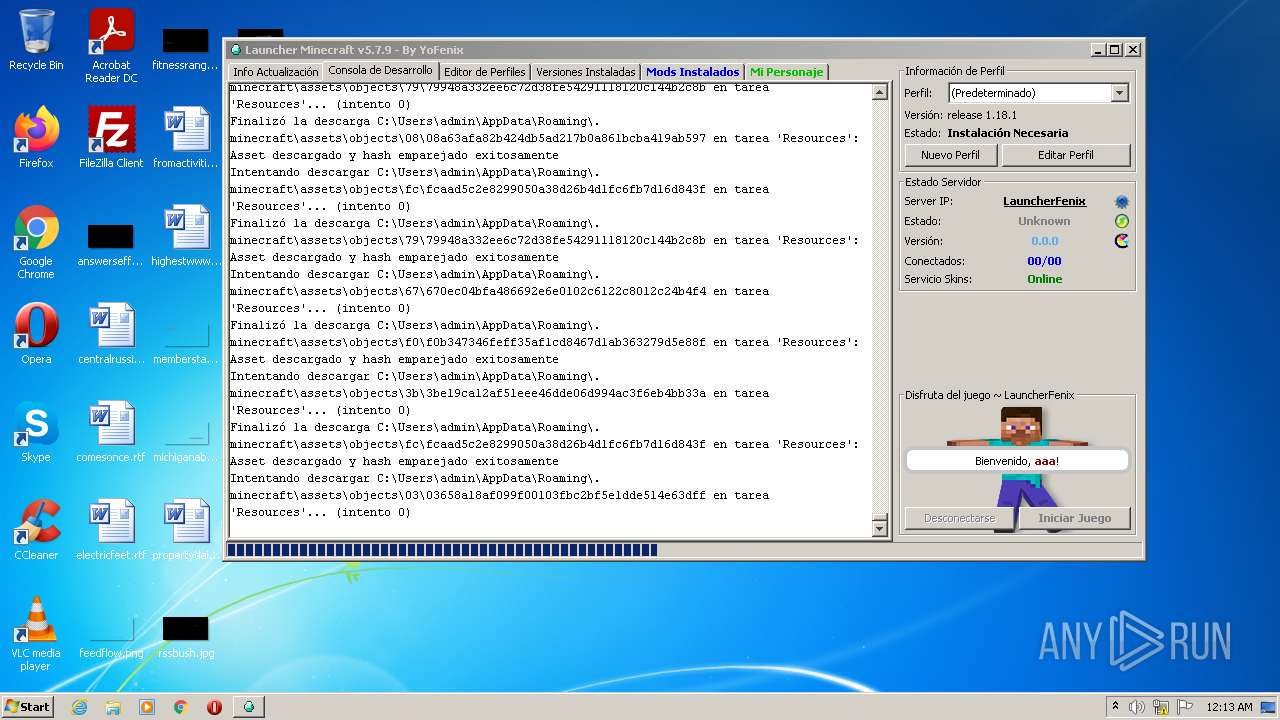
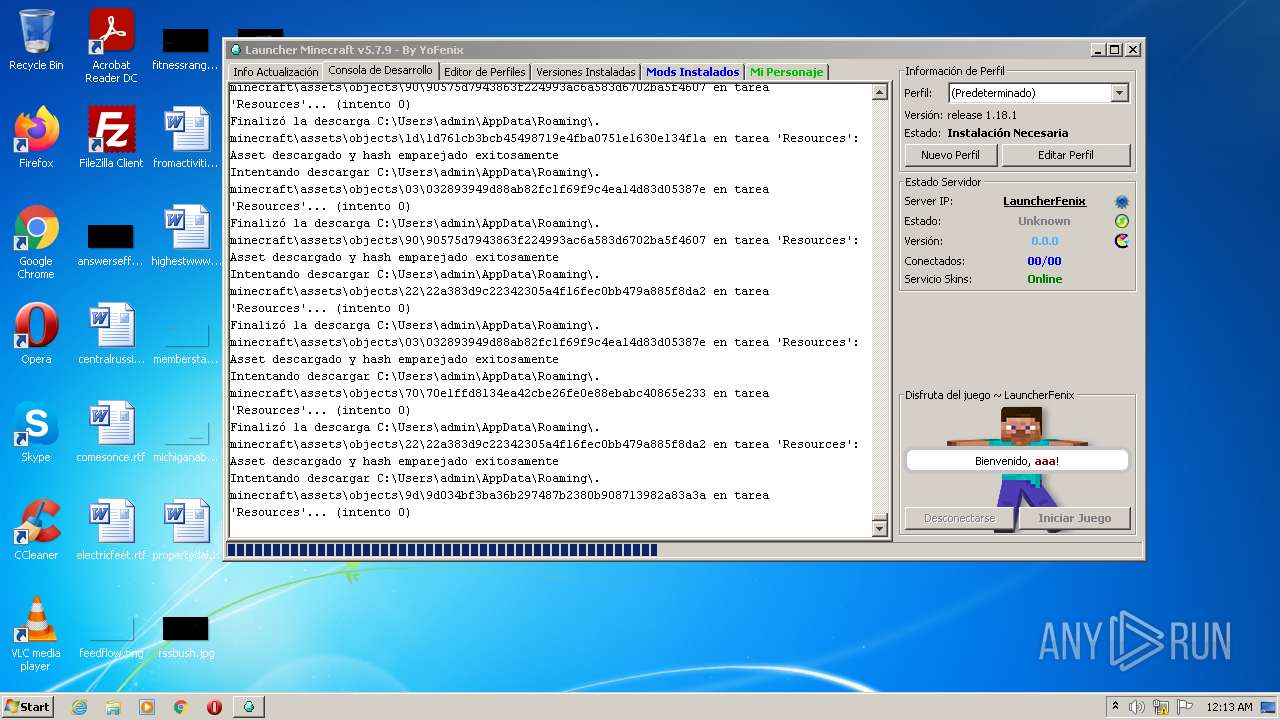
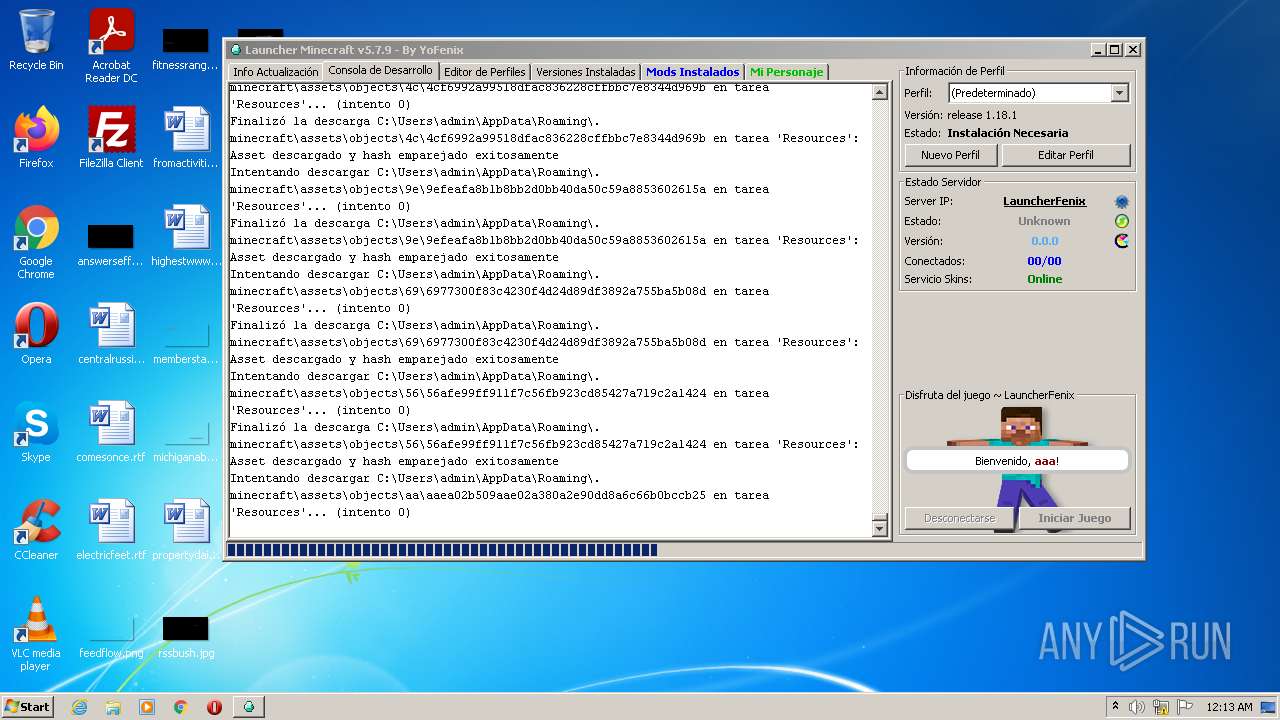
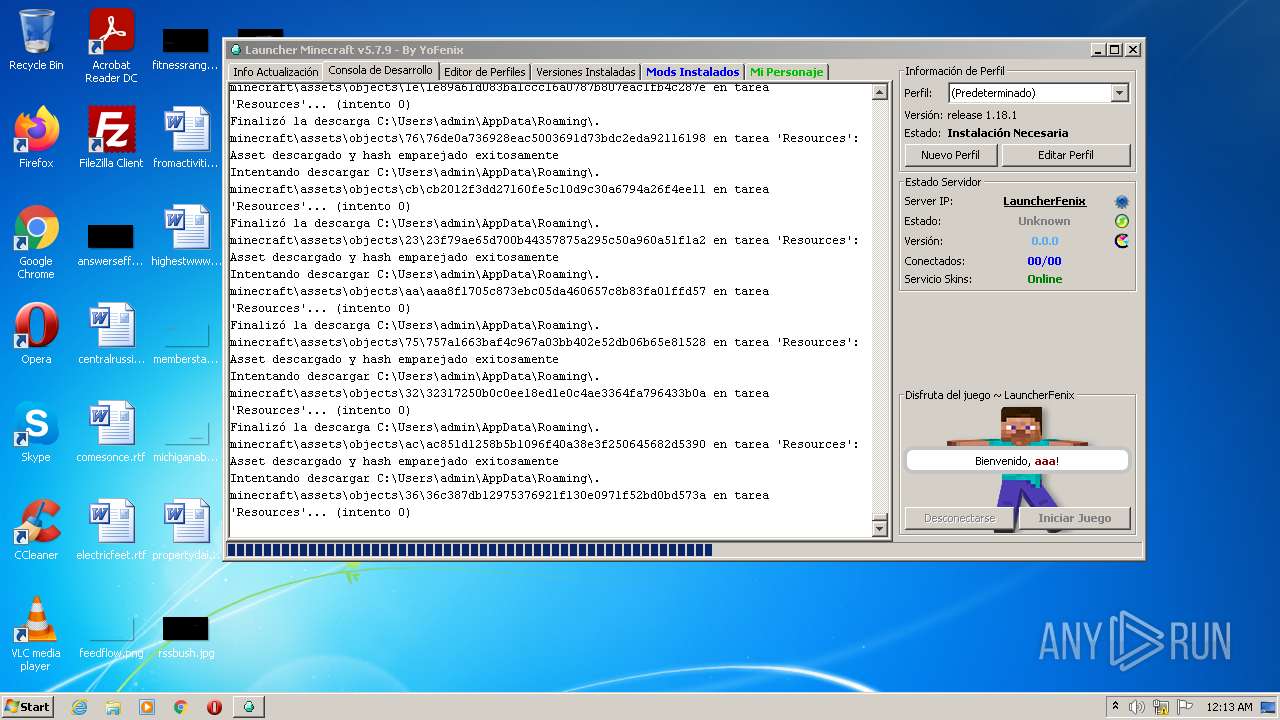
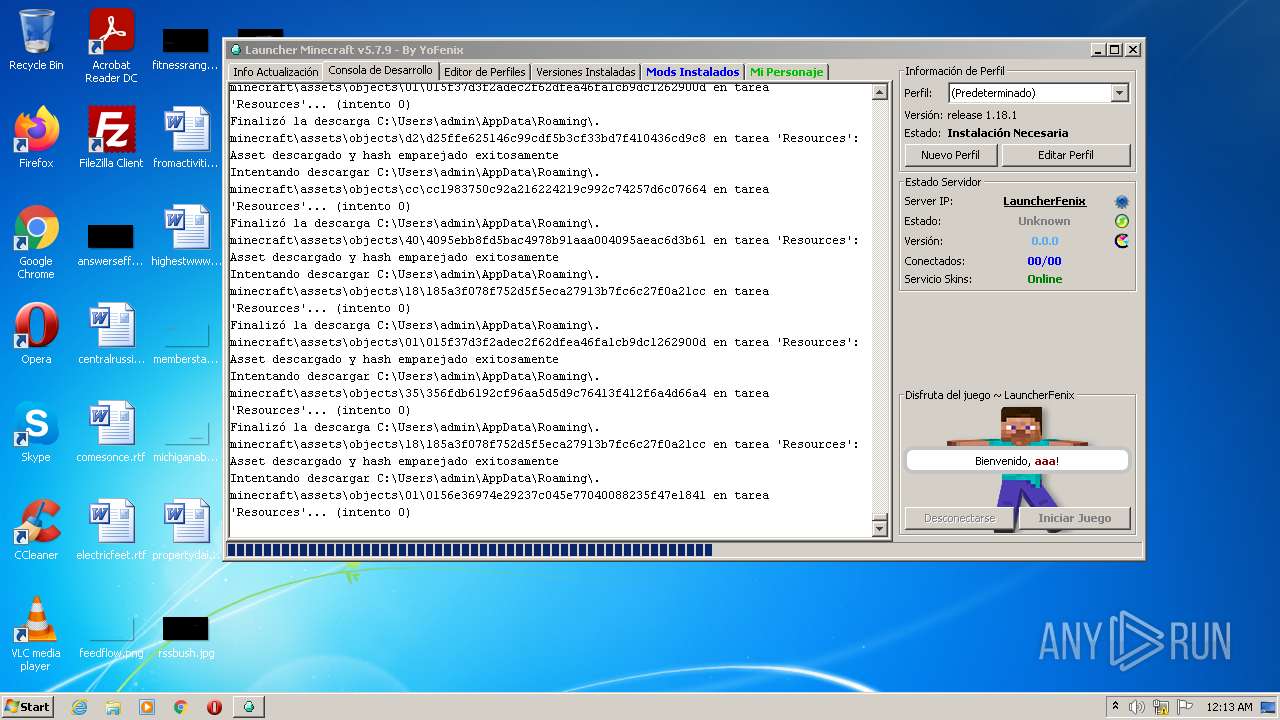
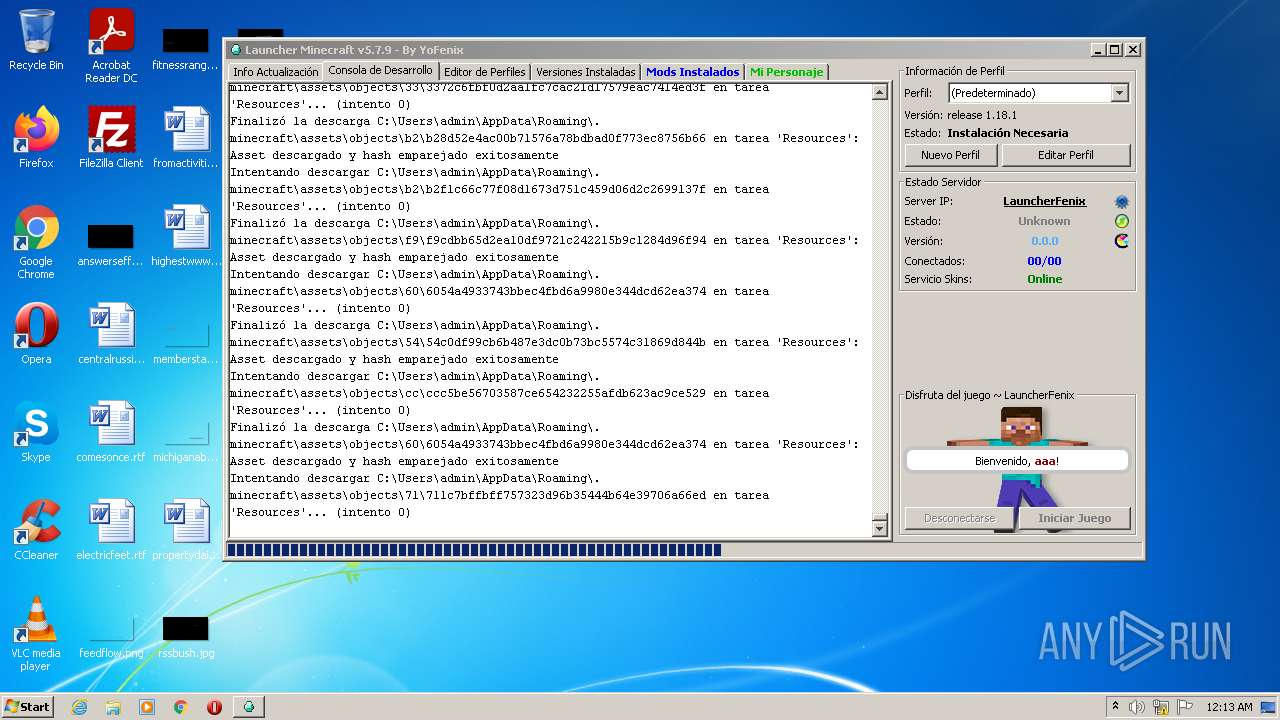
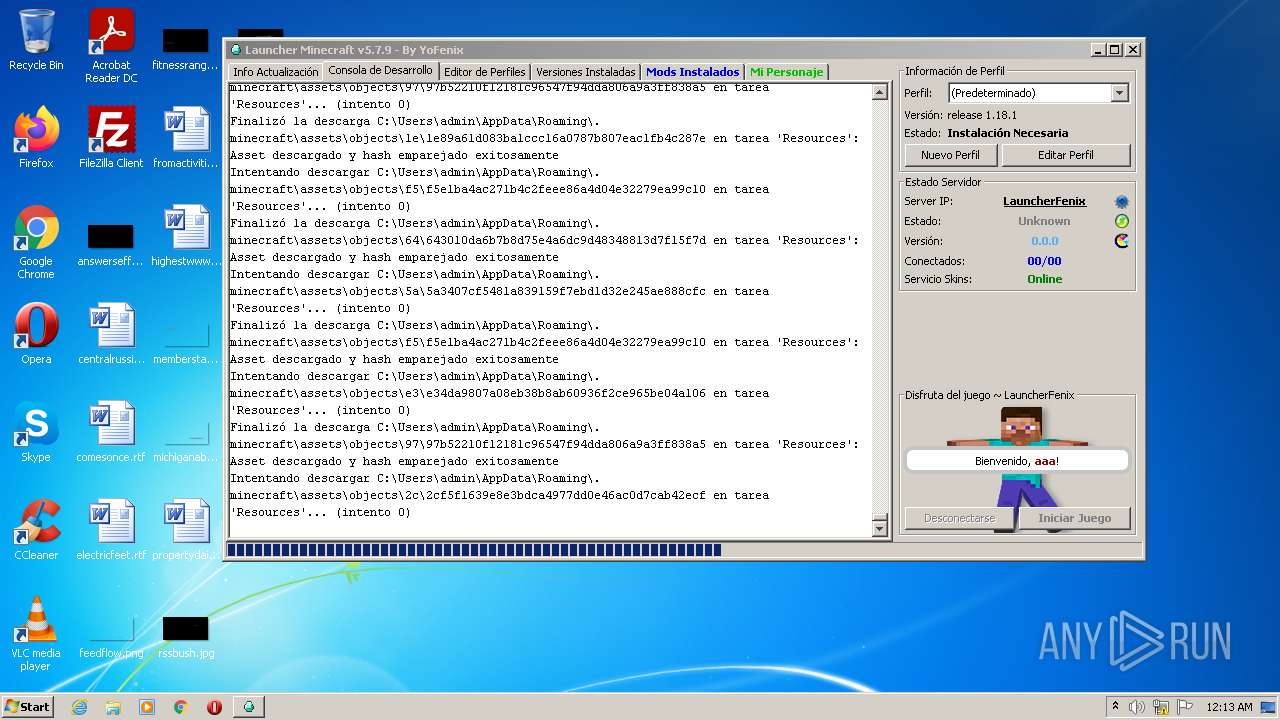
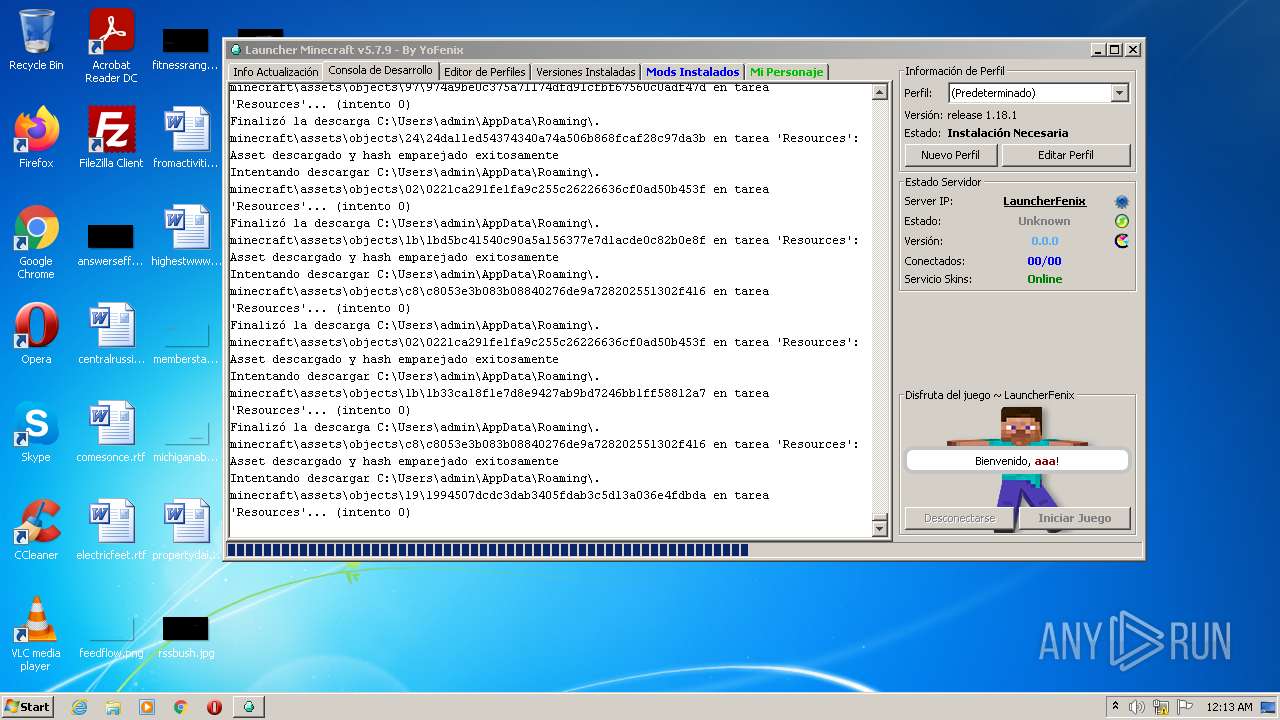
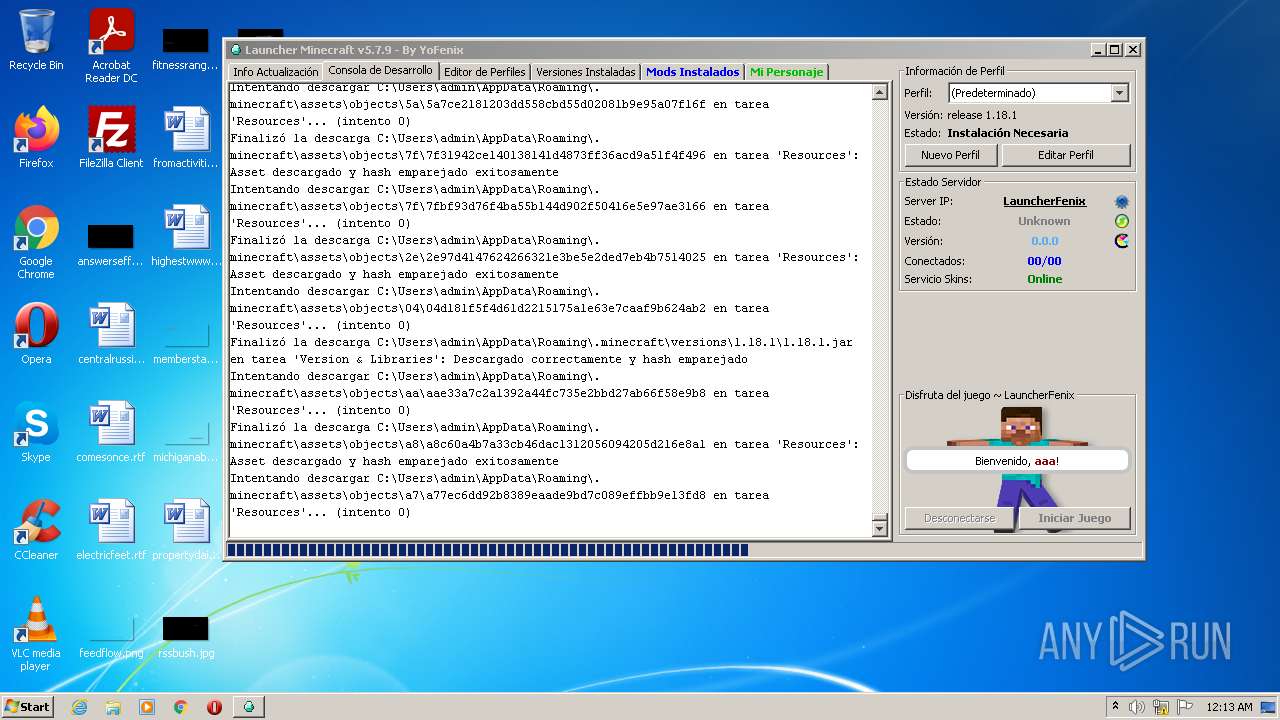
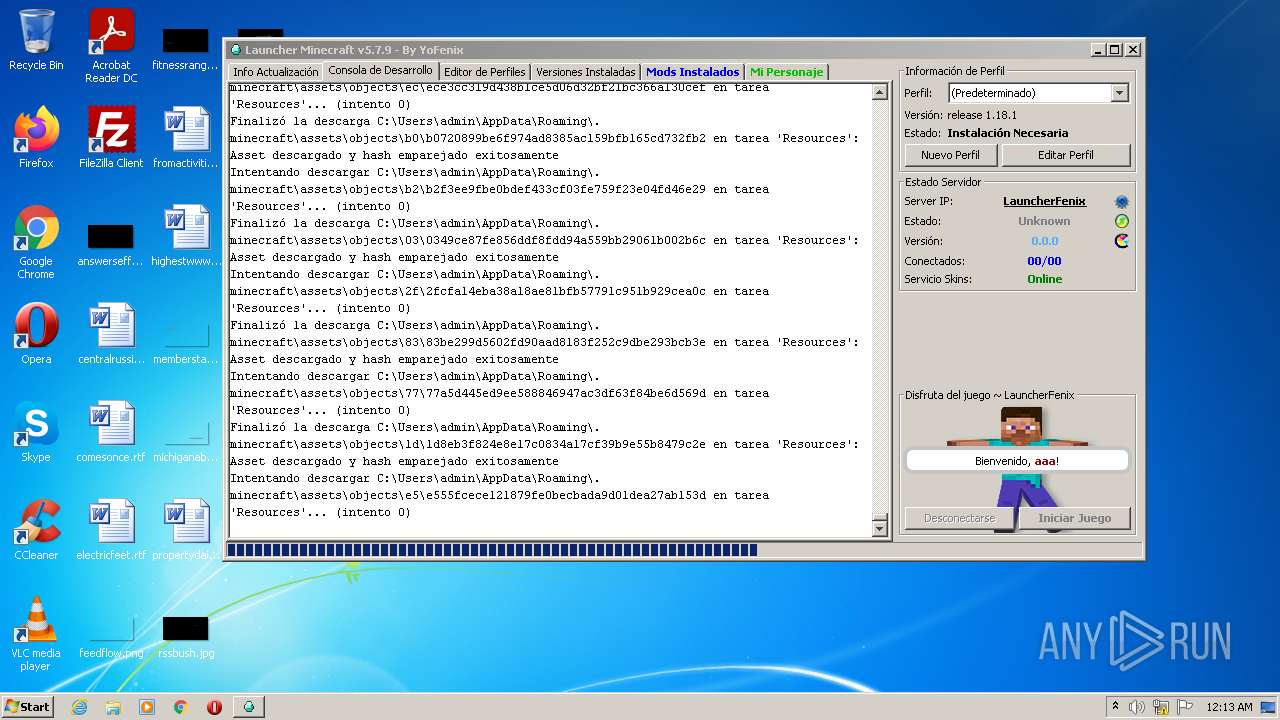
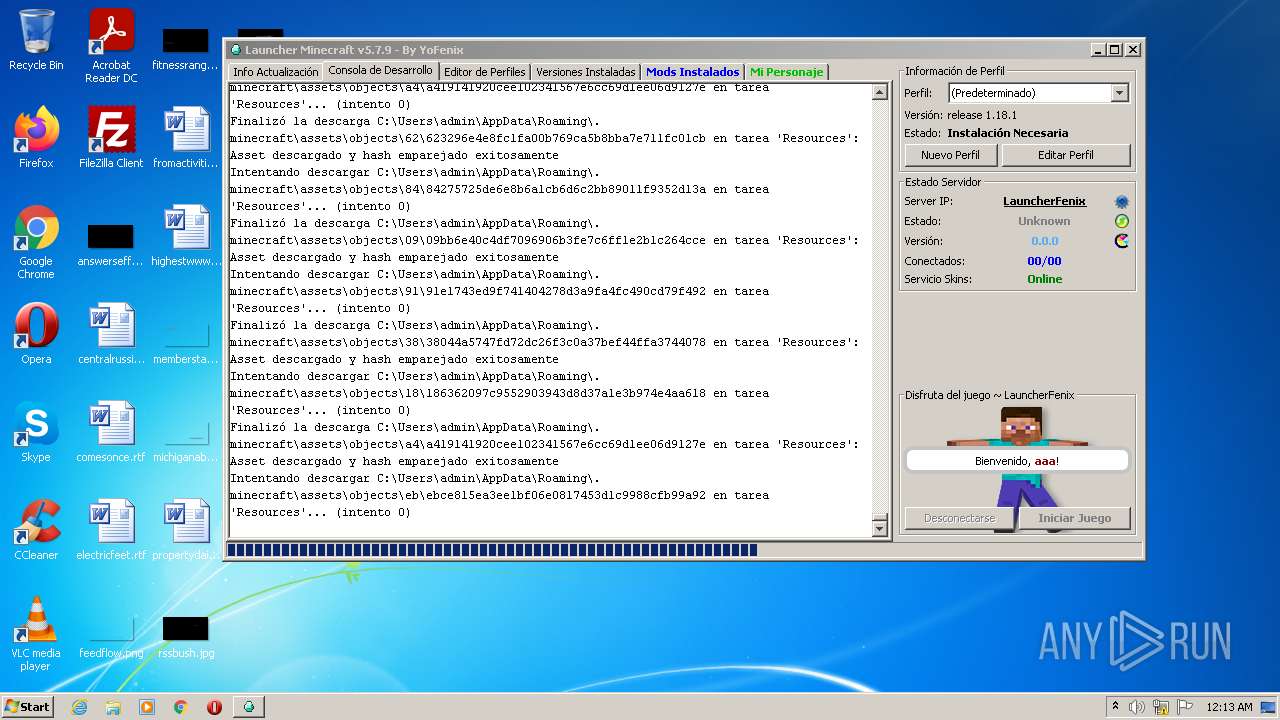
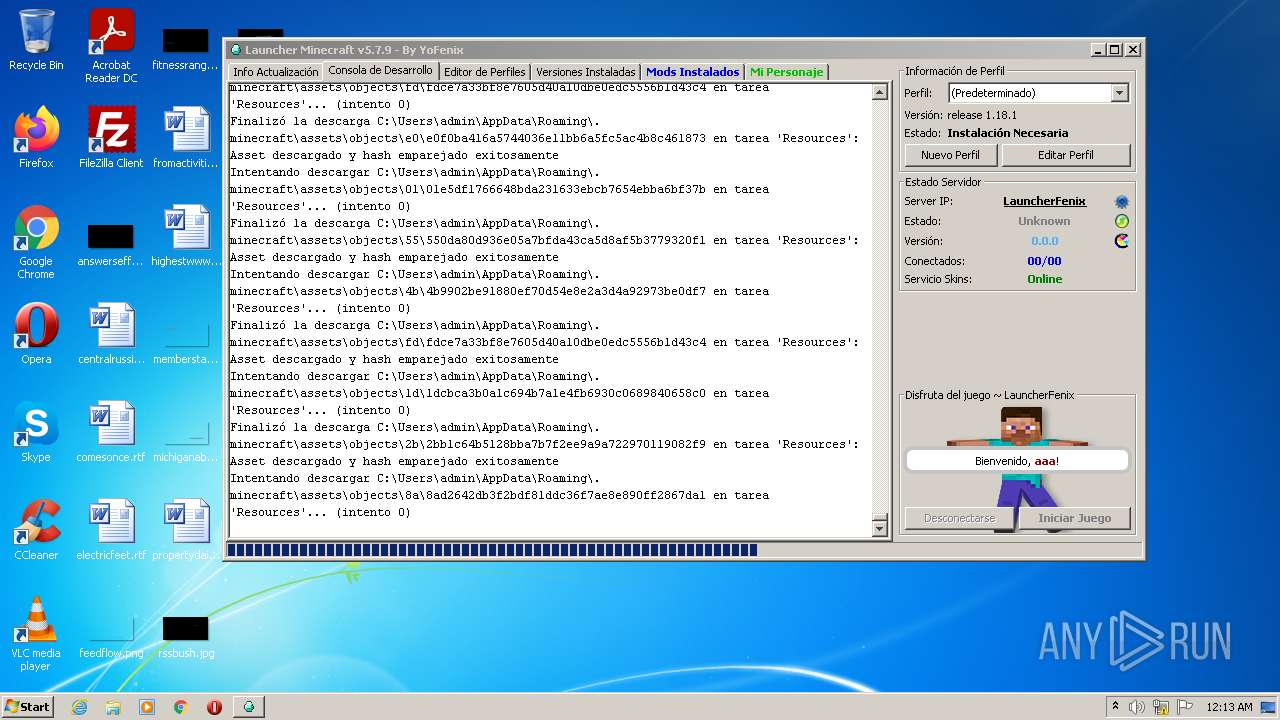
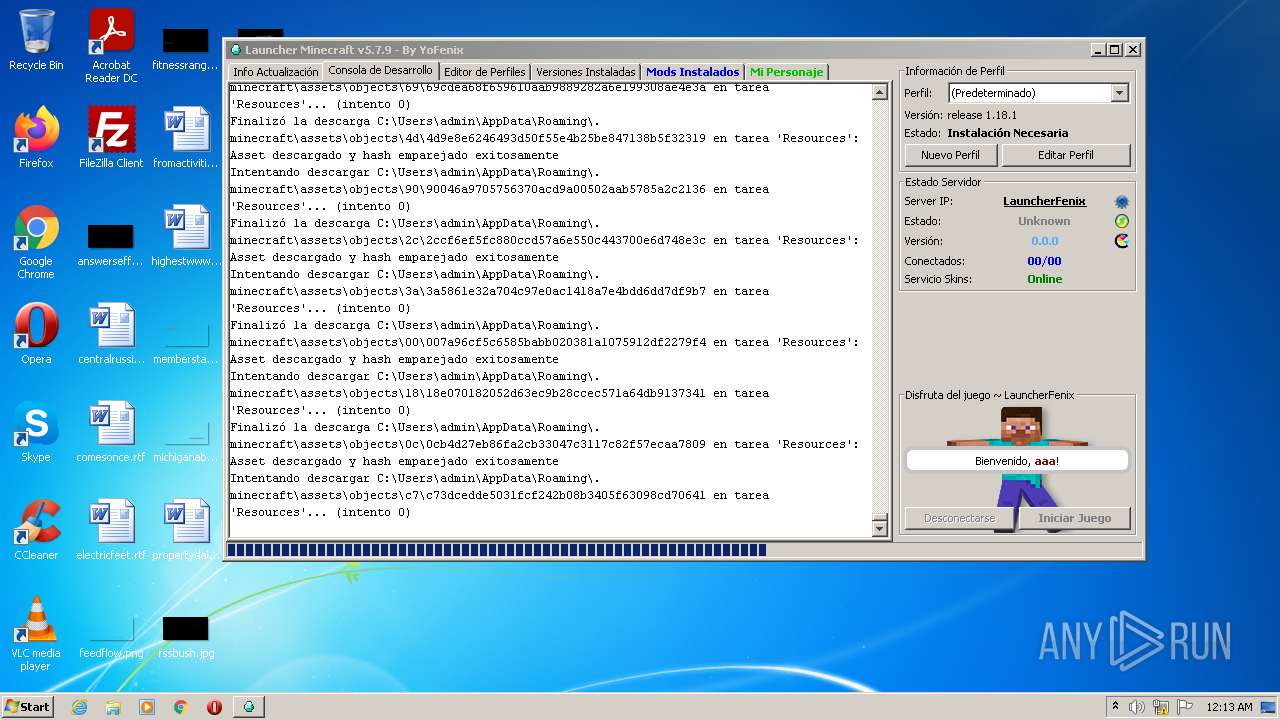
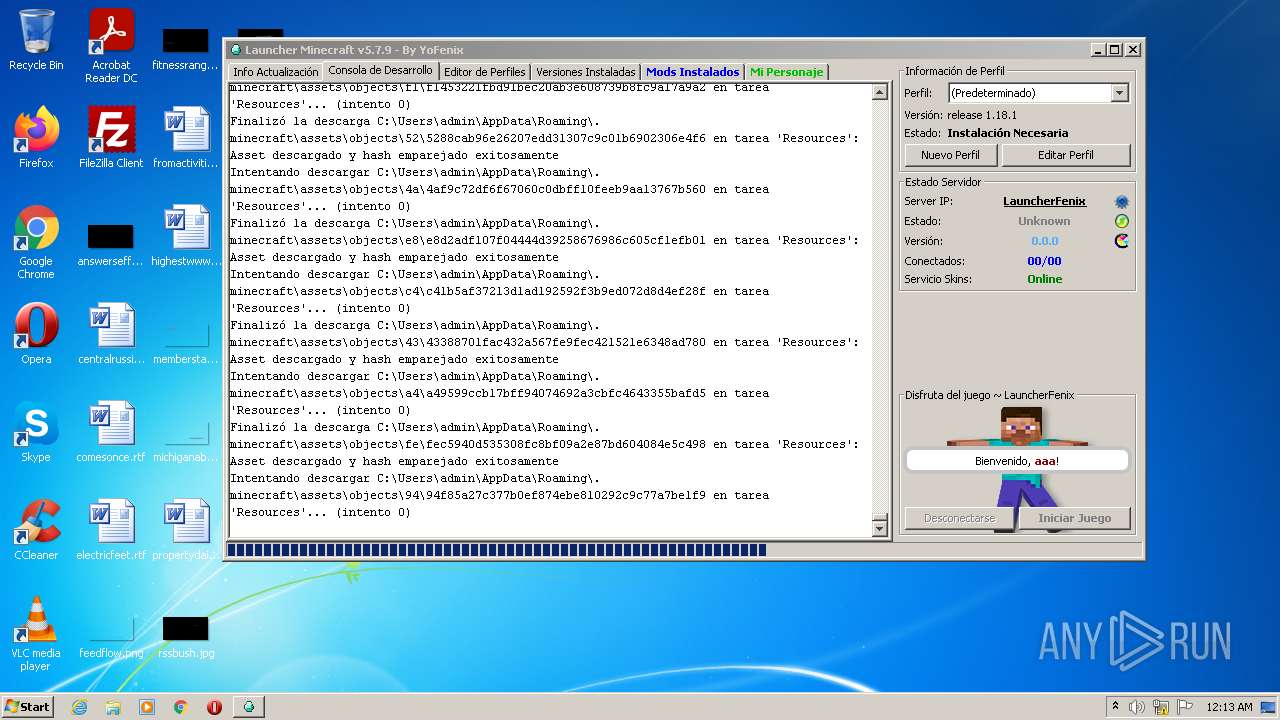
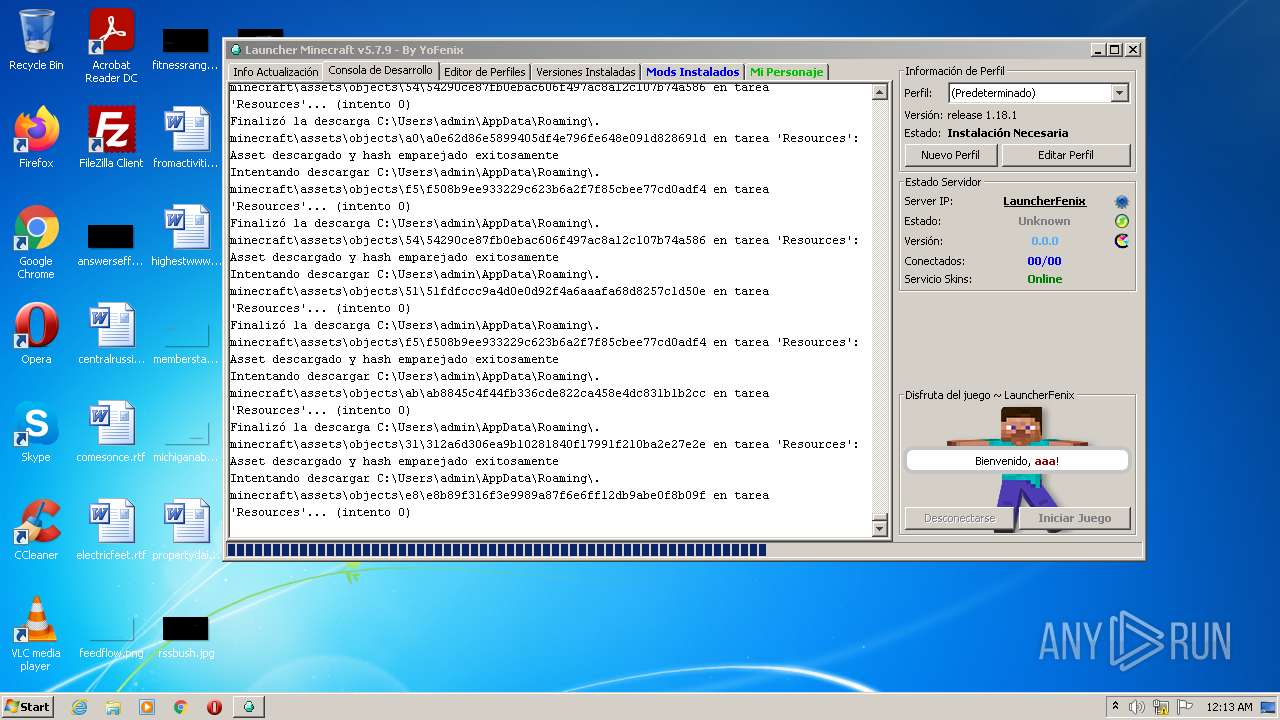
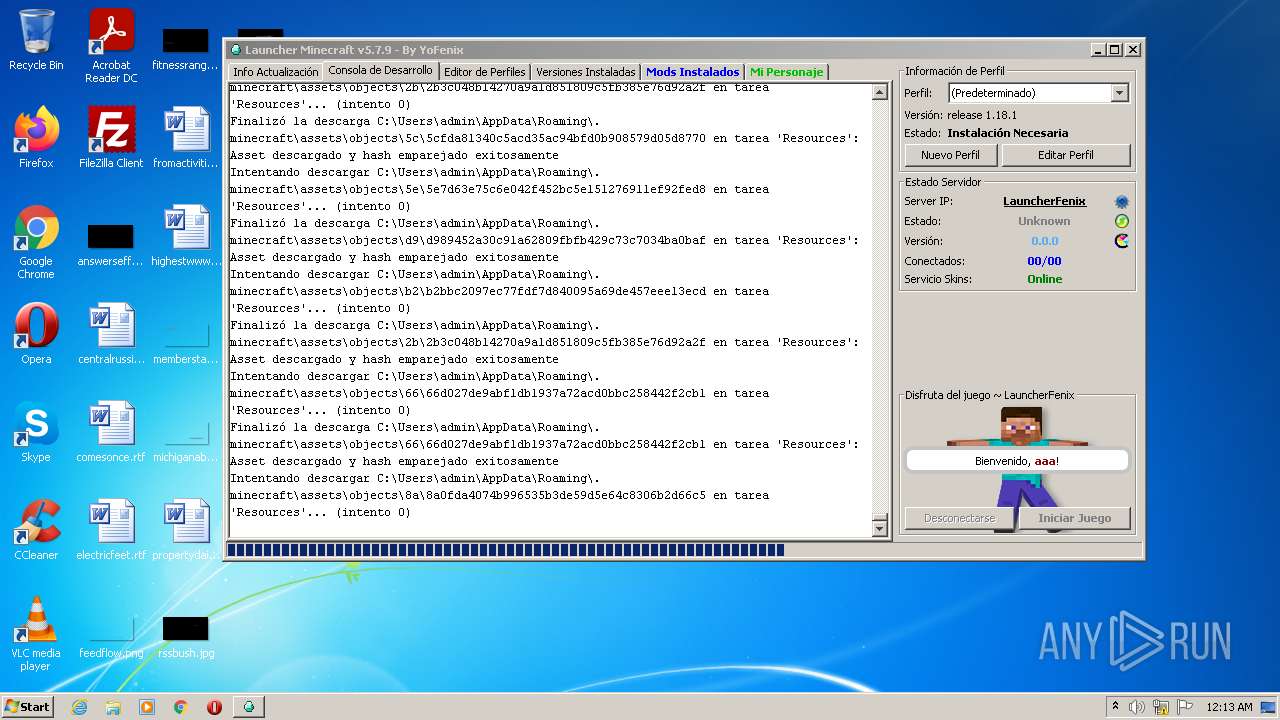
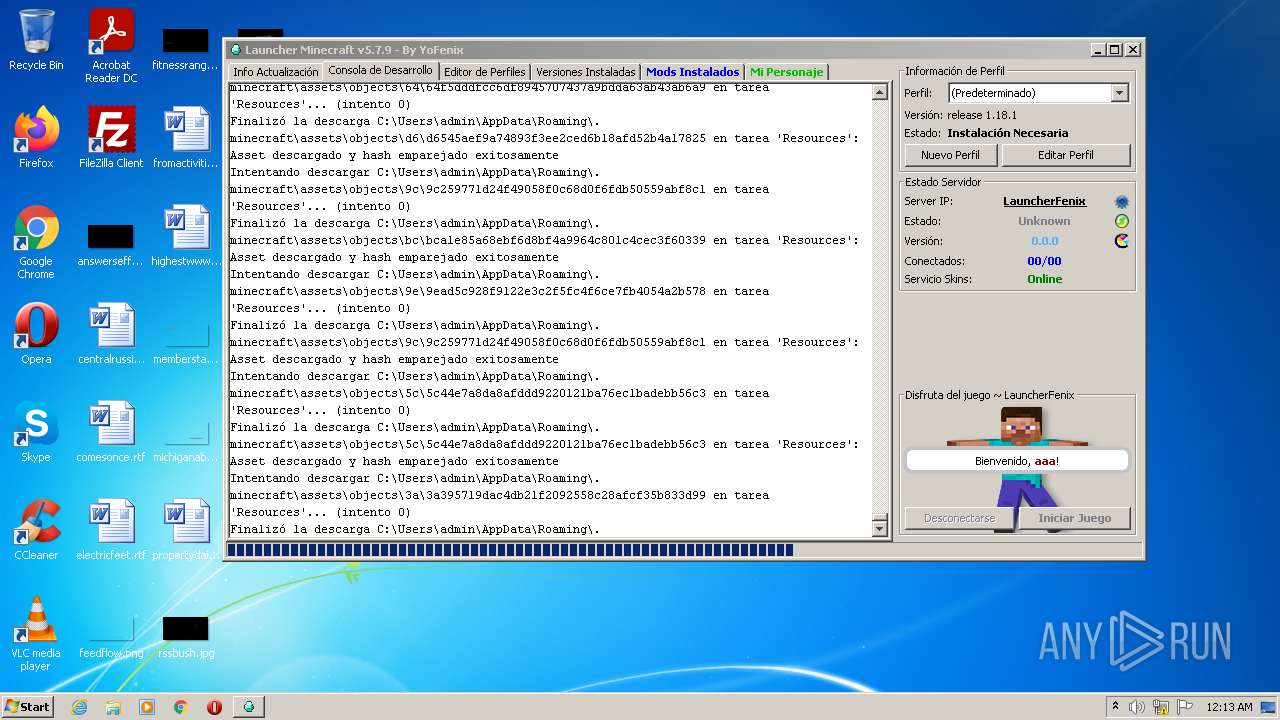
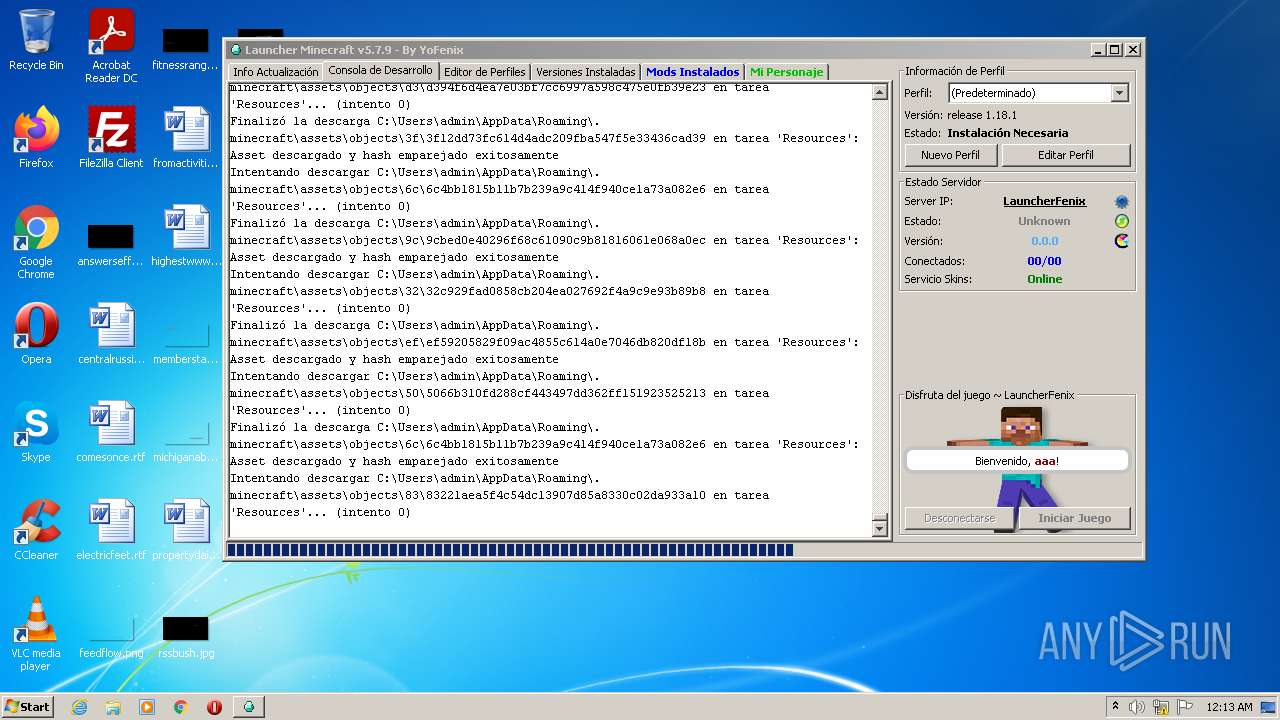
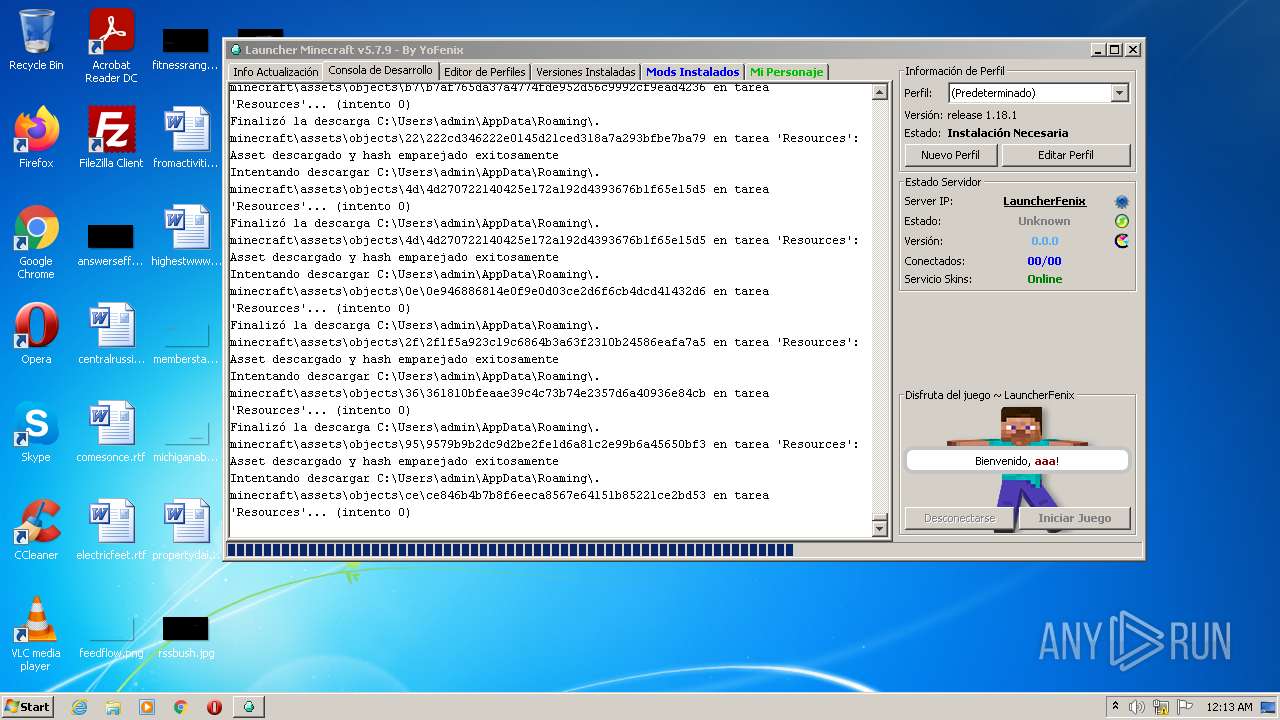
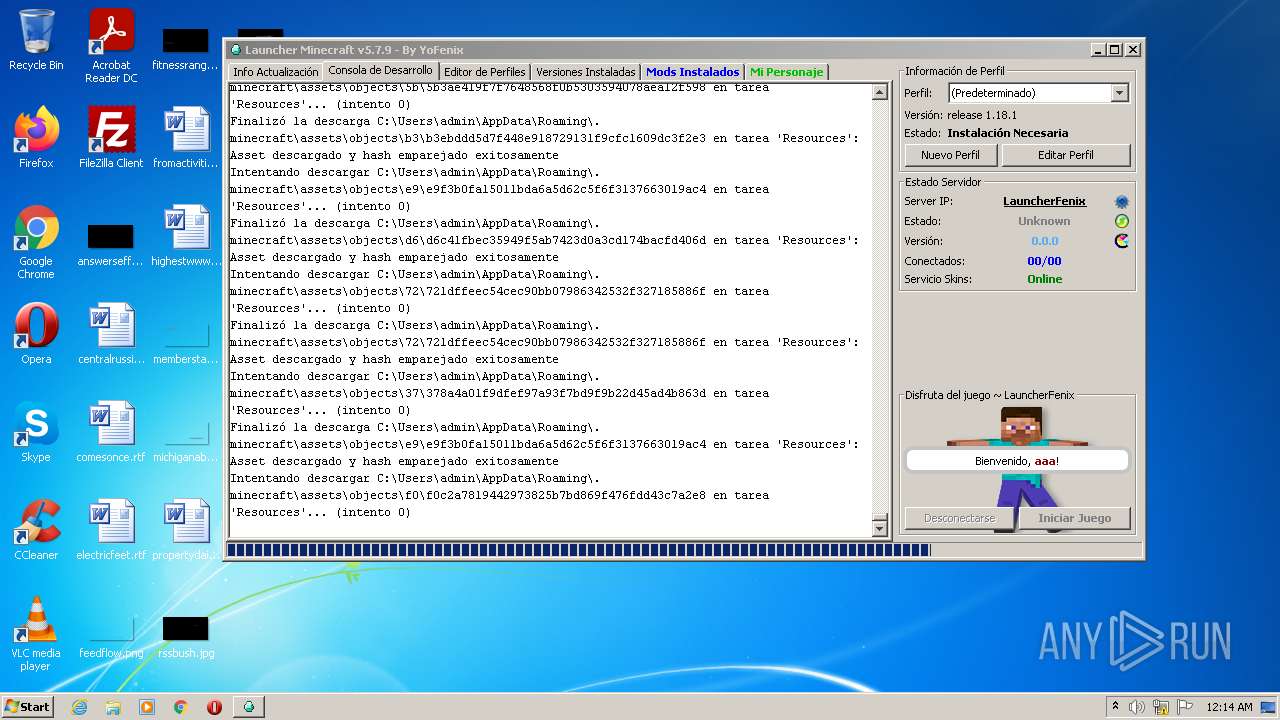
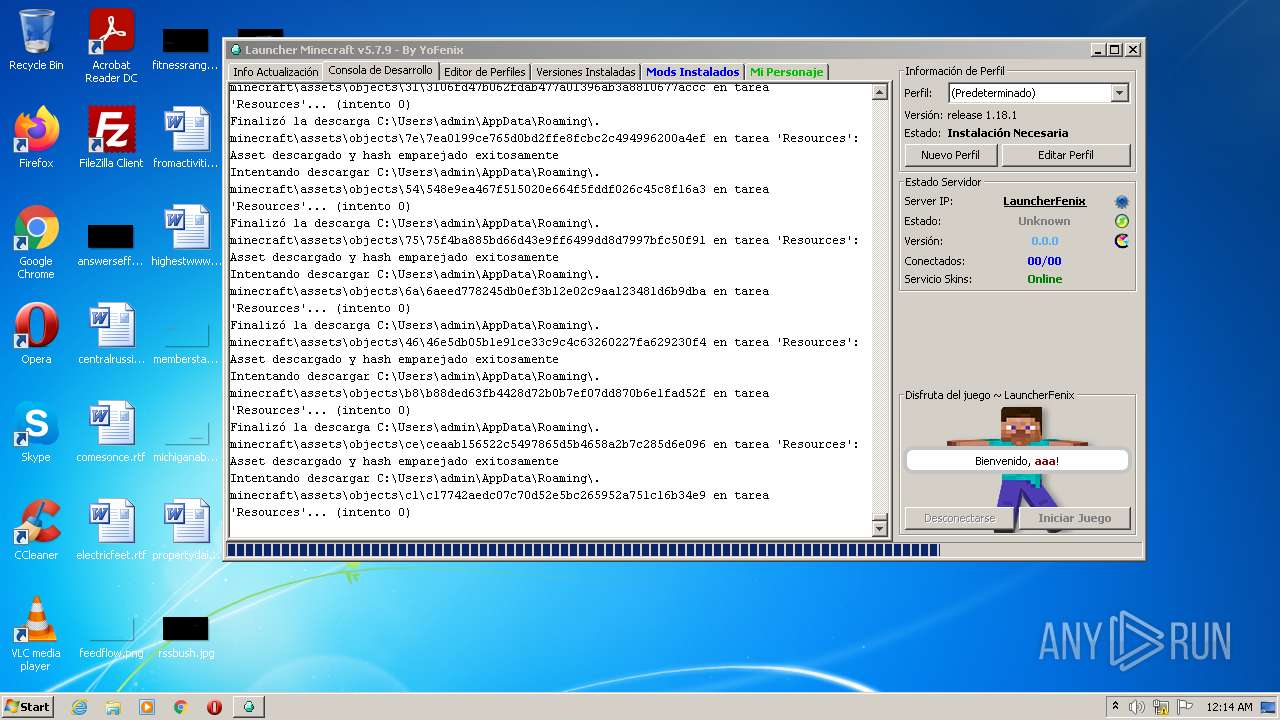
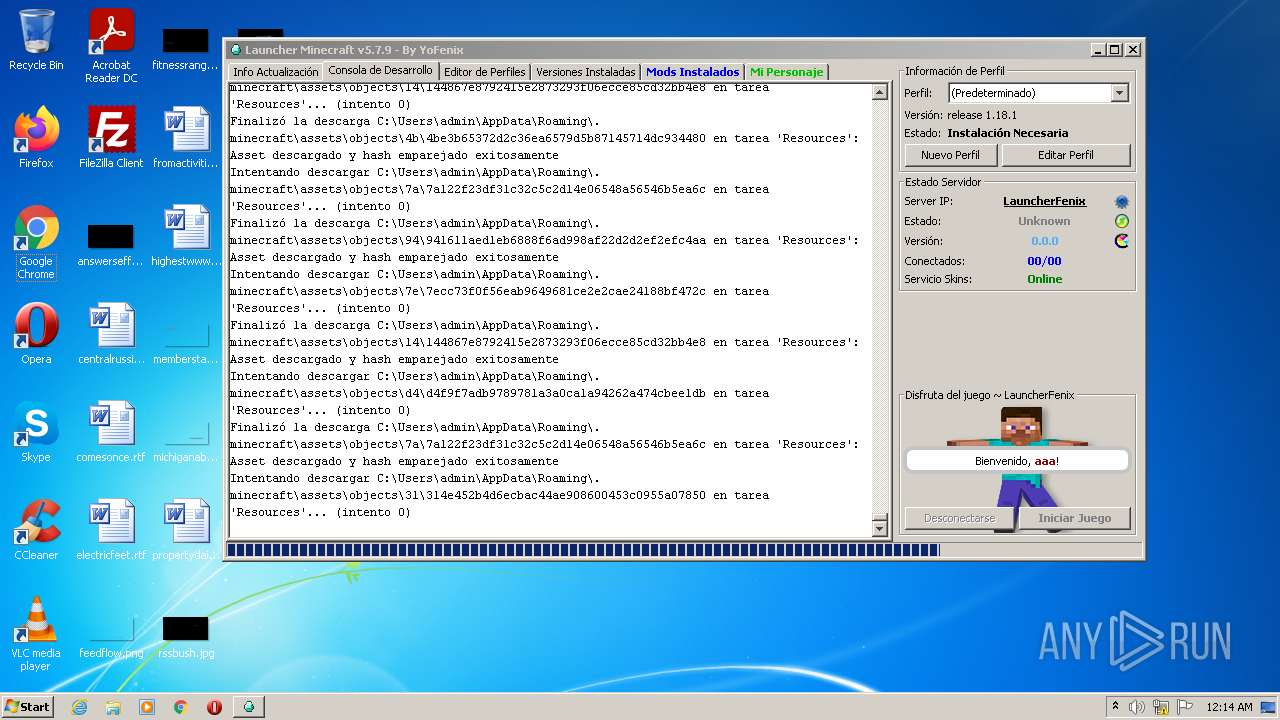
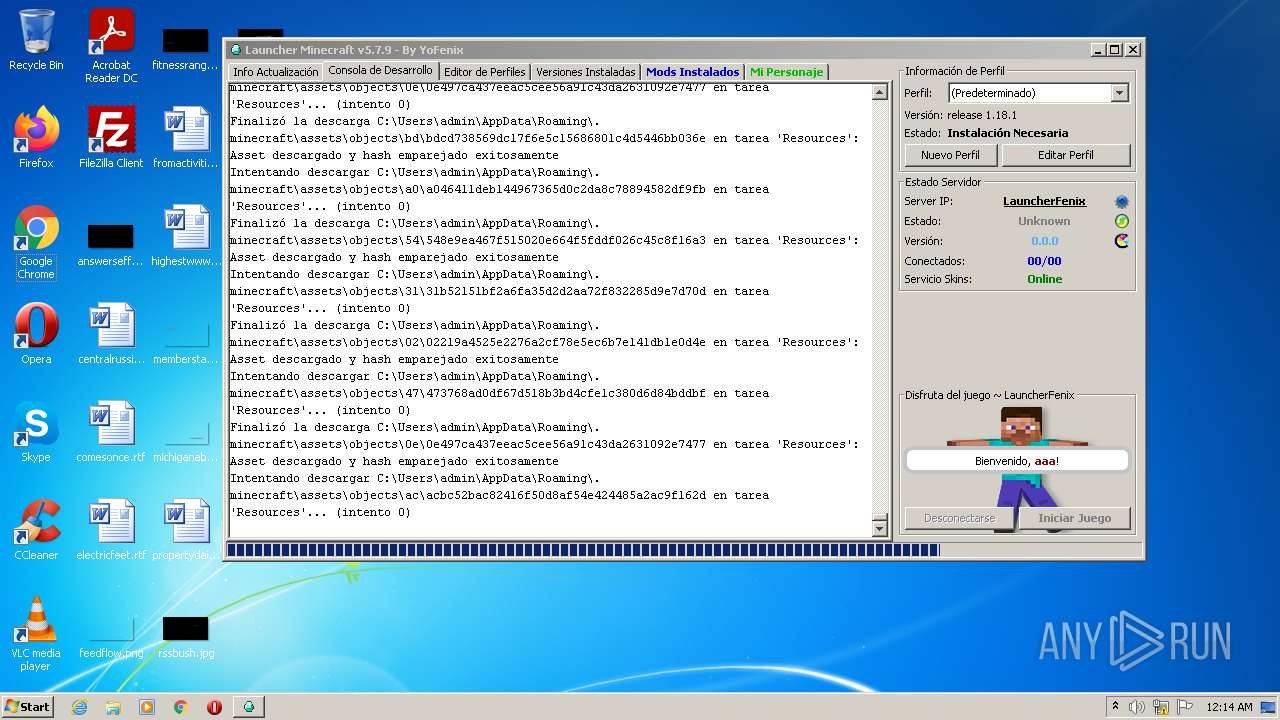
| 4084 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\LauncherFenix-Minecraft-v7.exe" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | LauncherFenix-Minecraft-v7.exe | |
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
21
Suspicious files
153
Text files
28
Unknown types
2 878
Dropped files
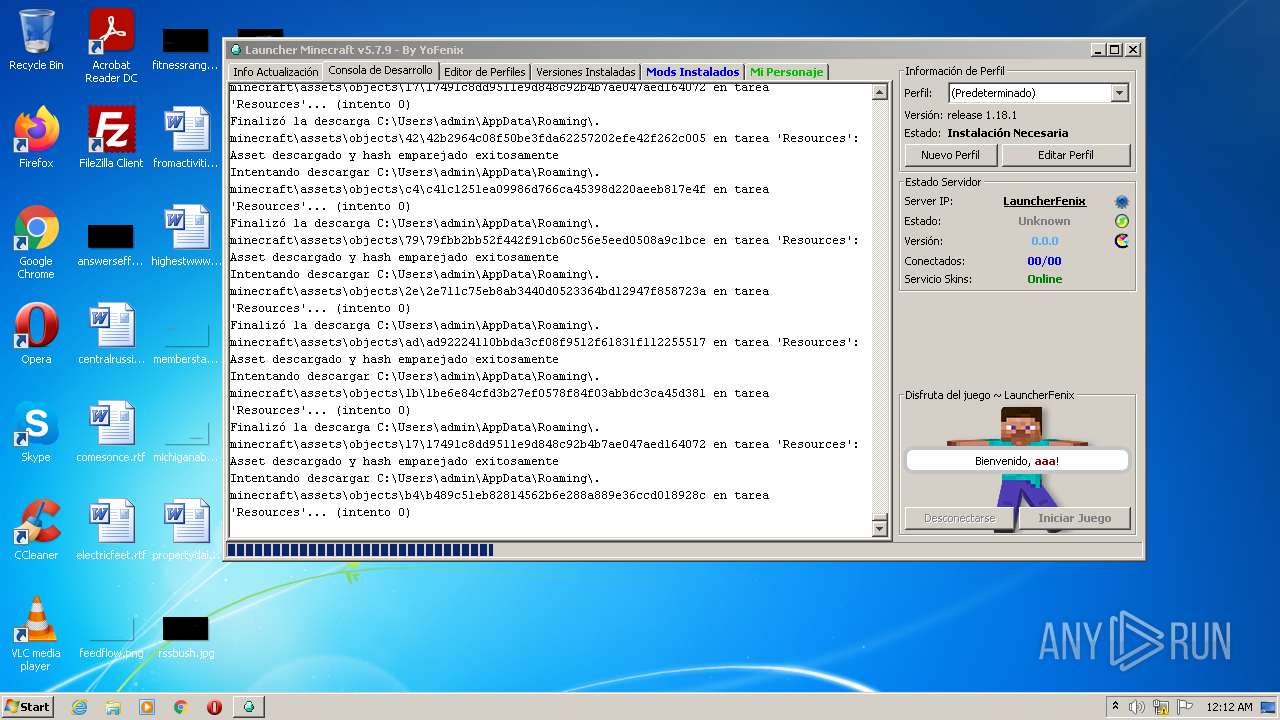
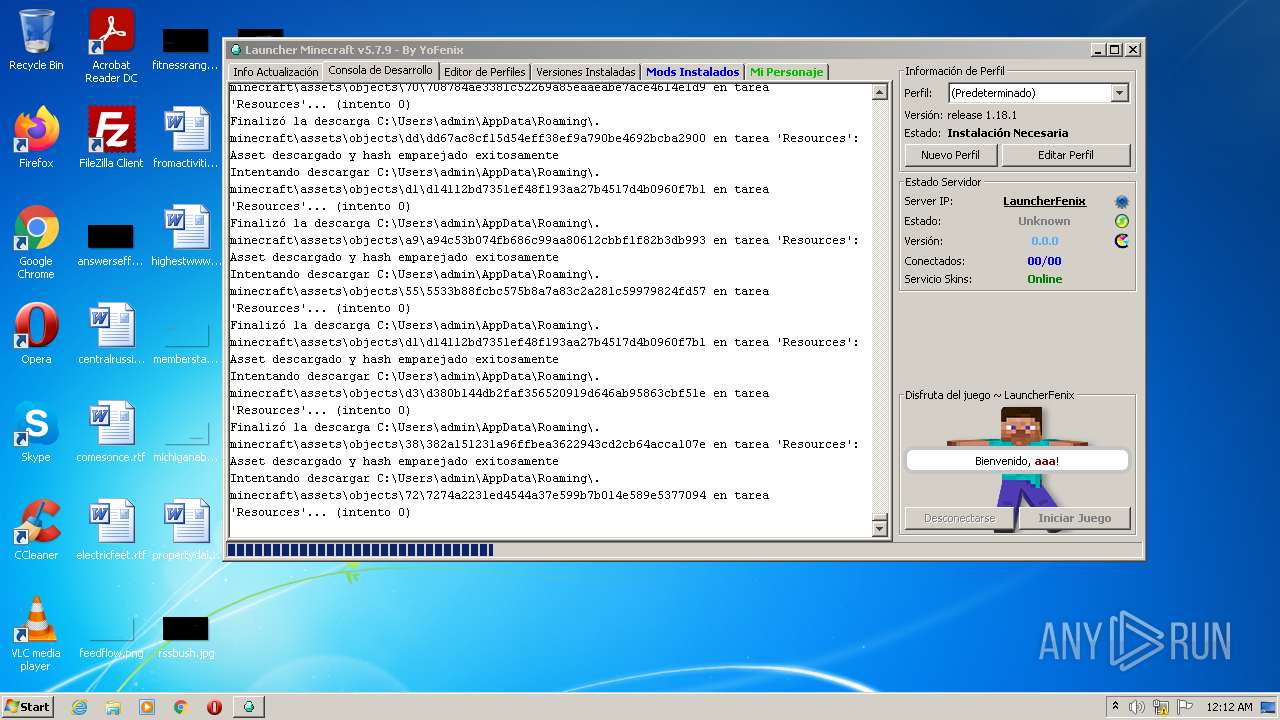
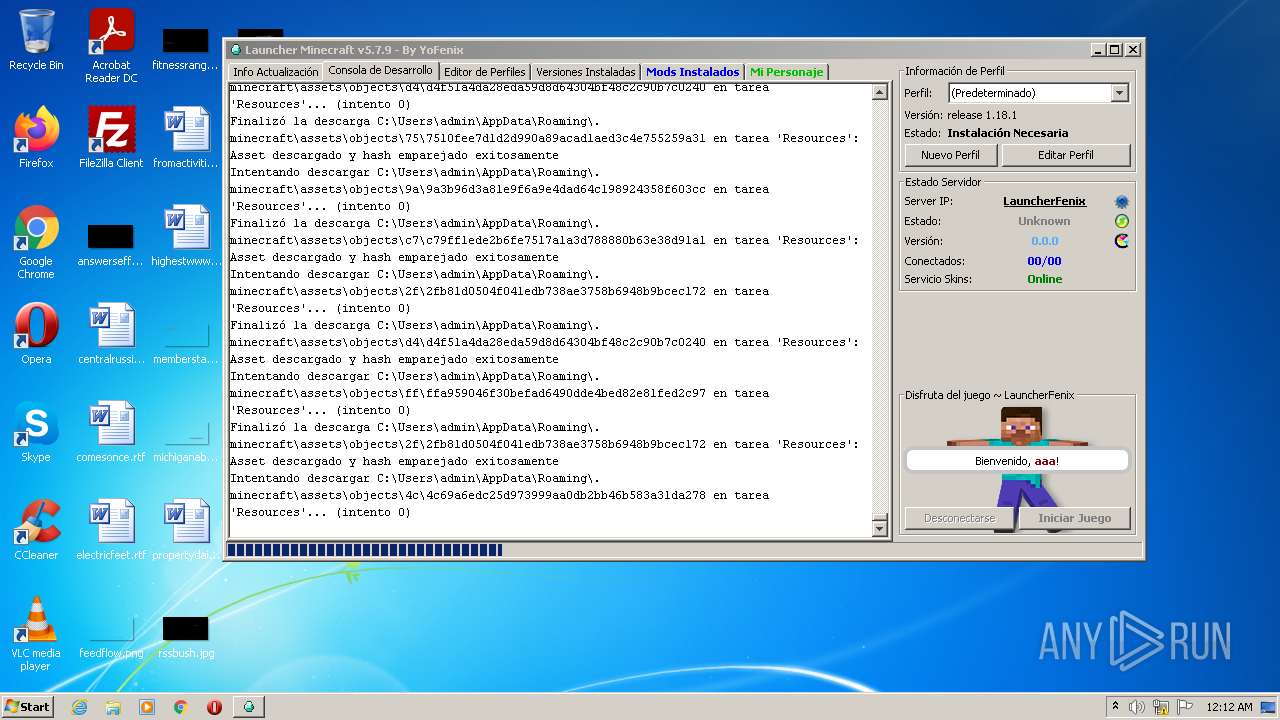
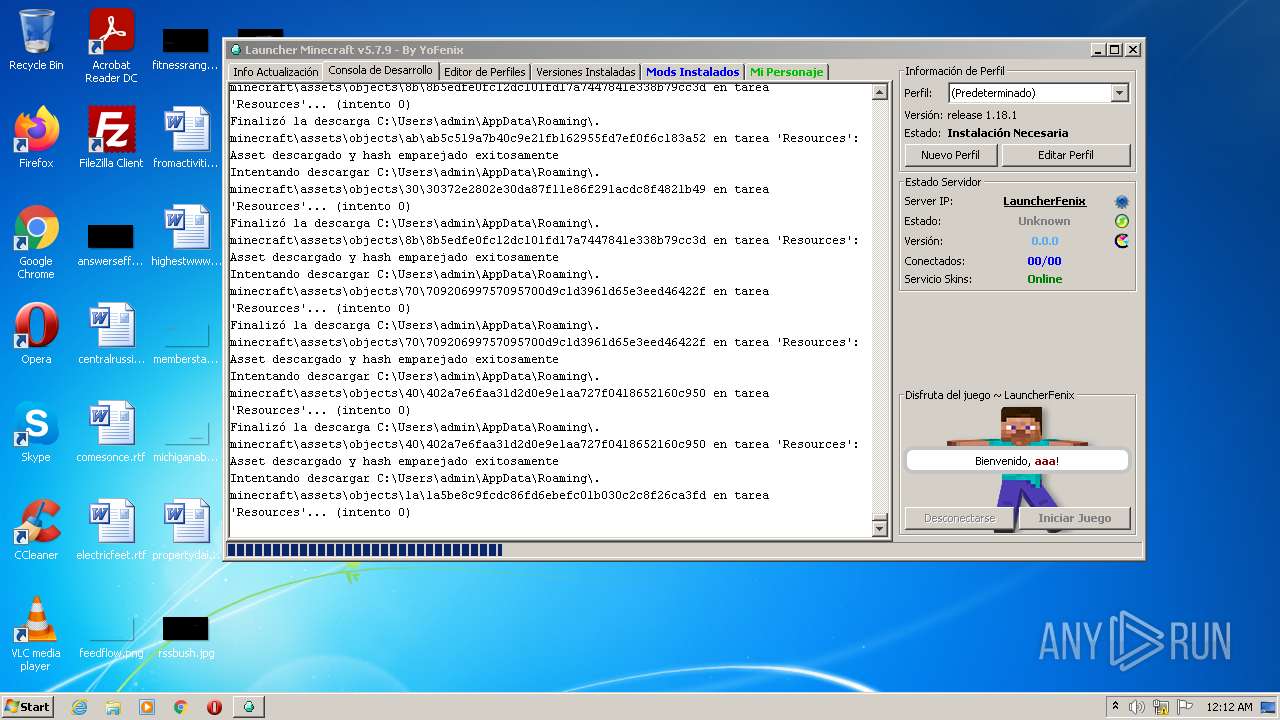
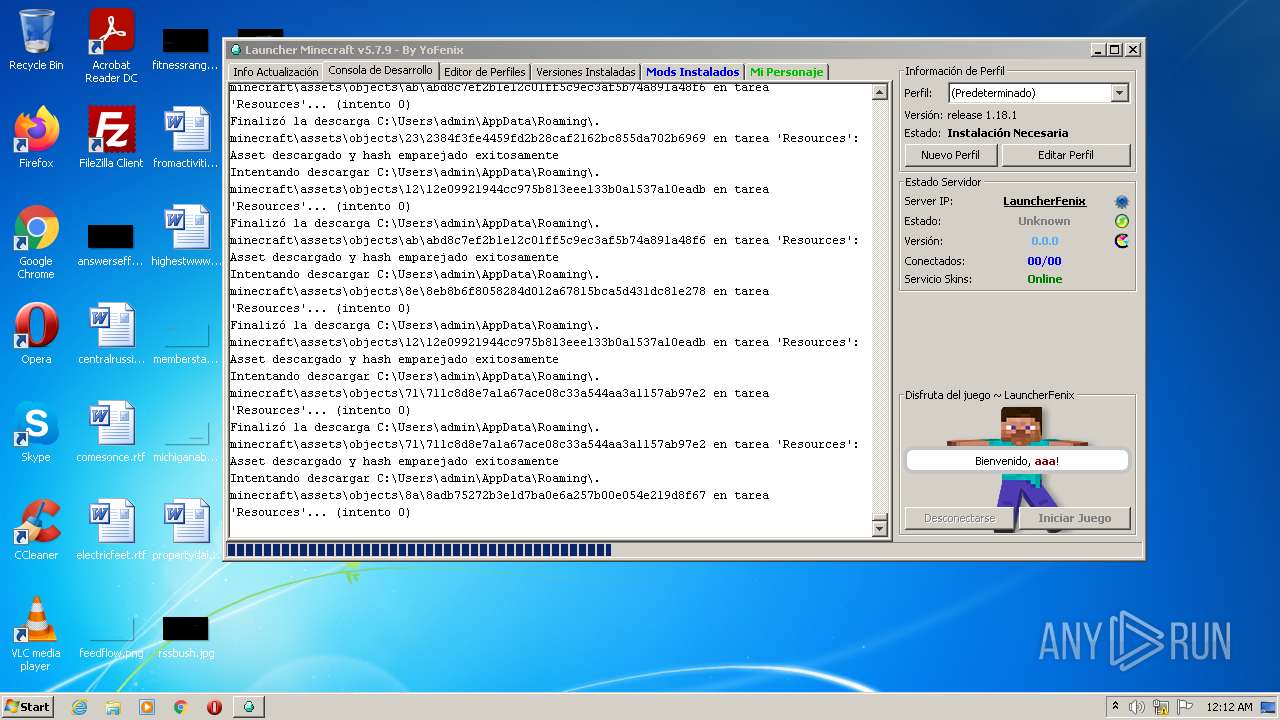
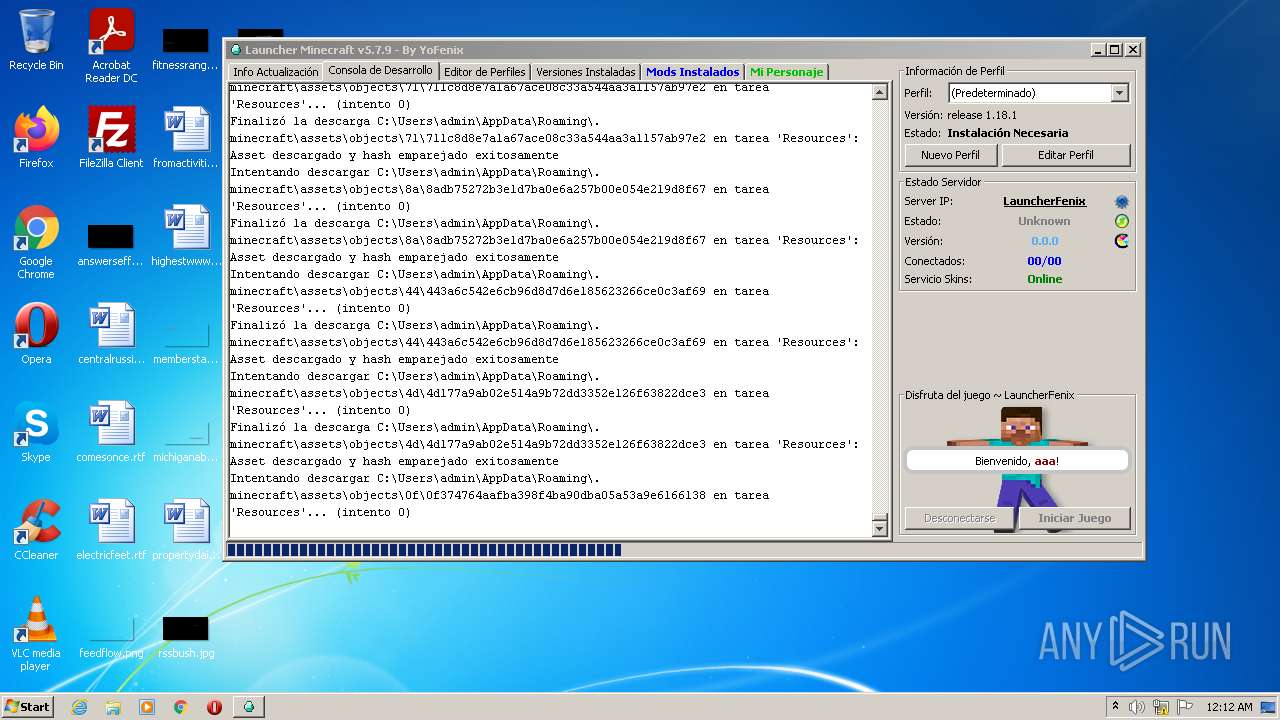
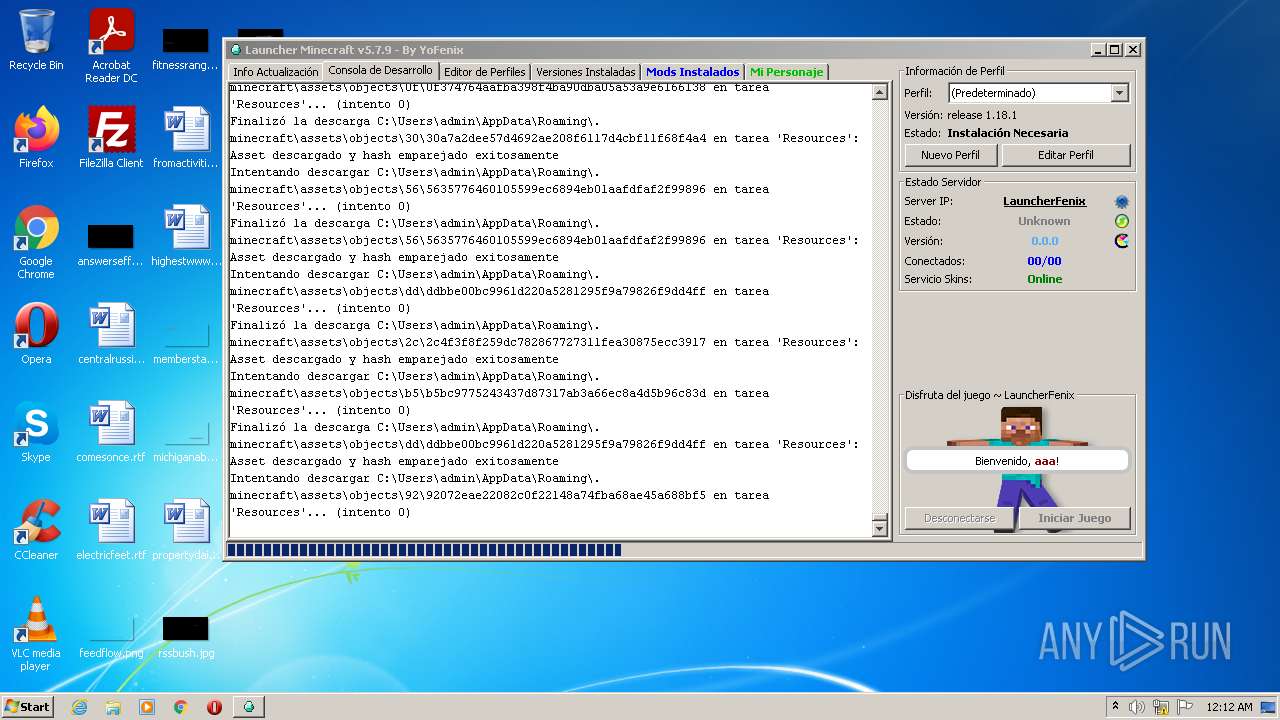
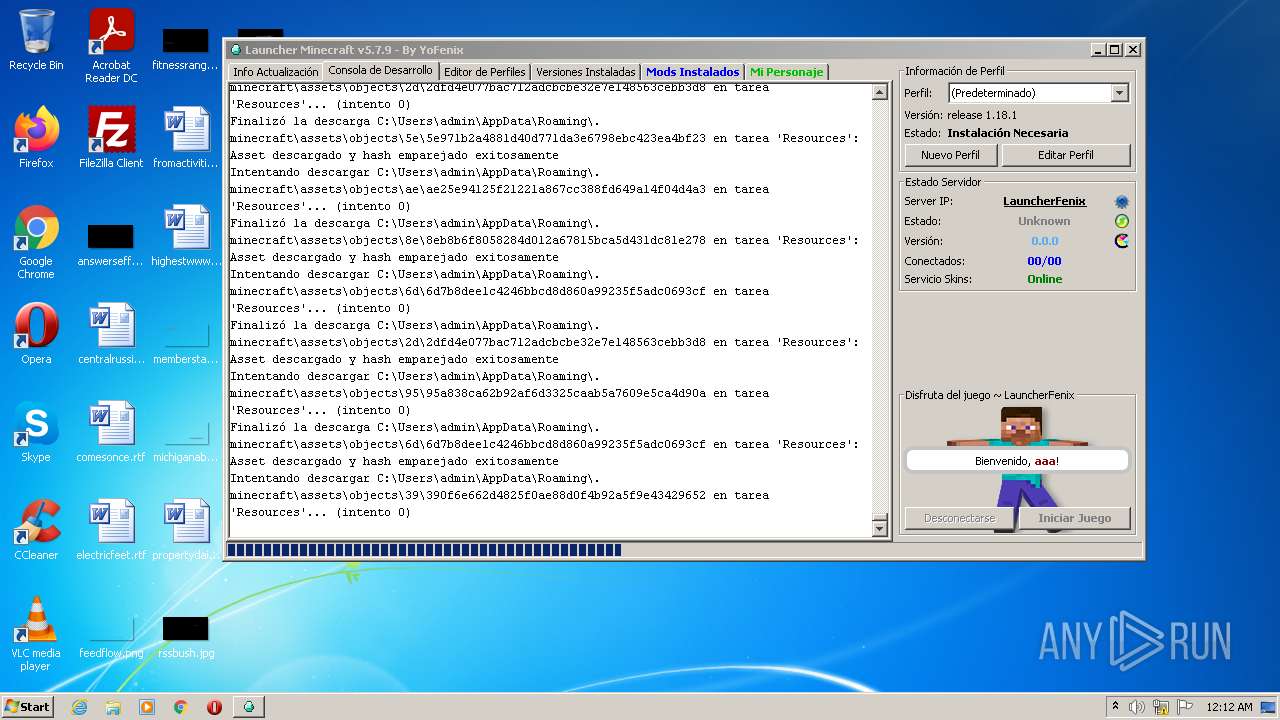
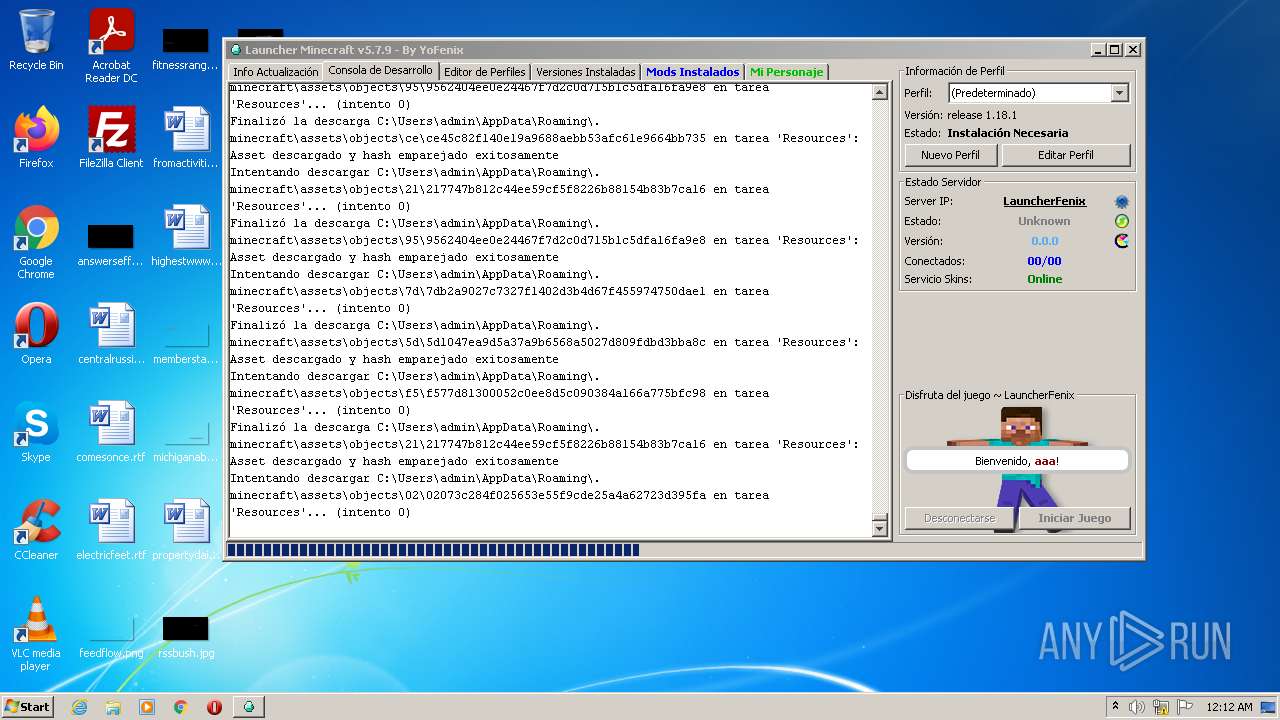
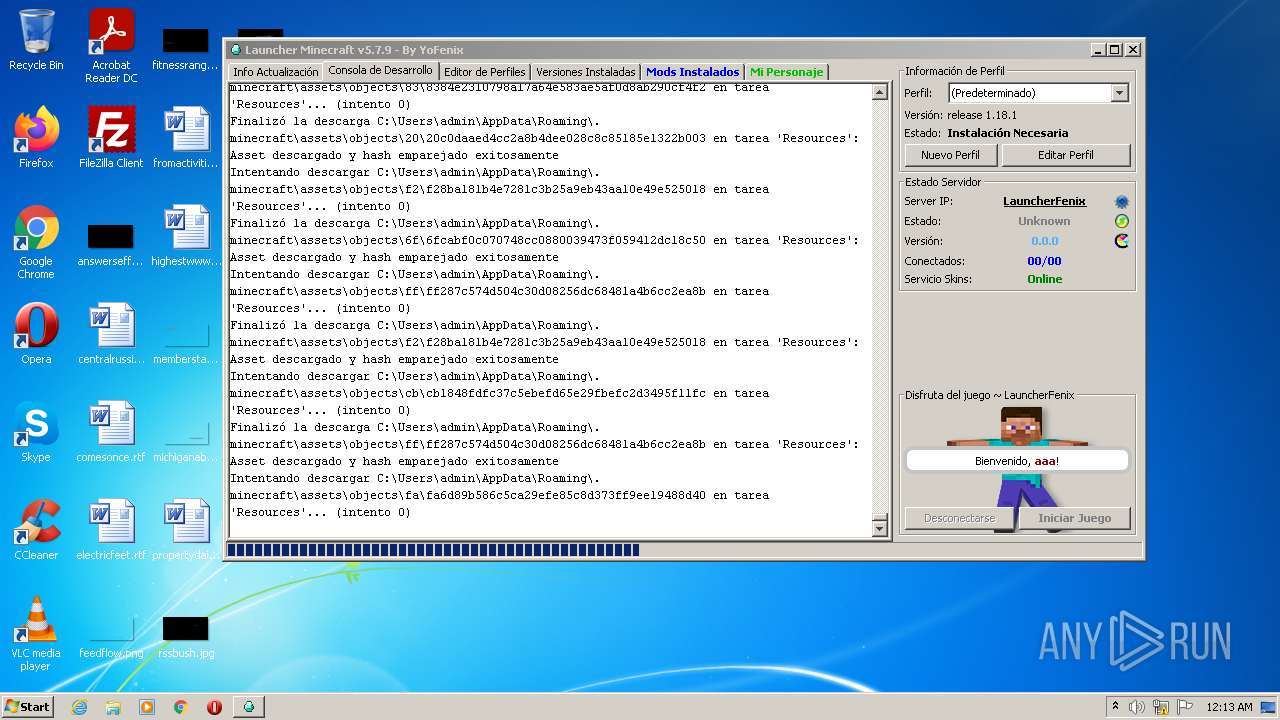
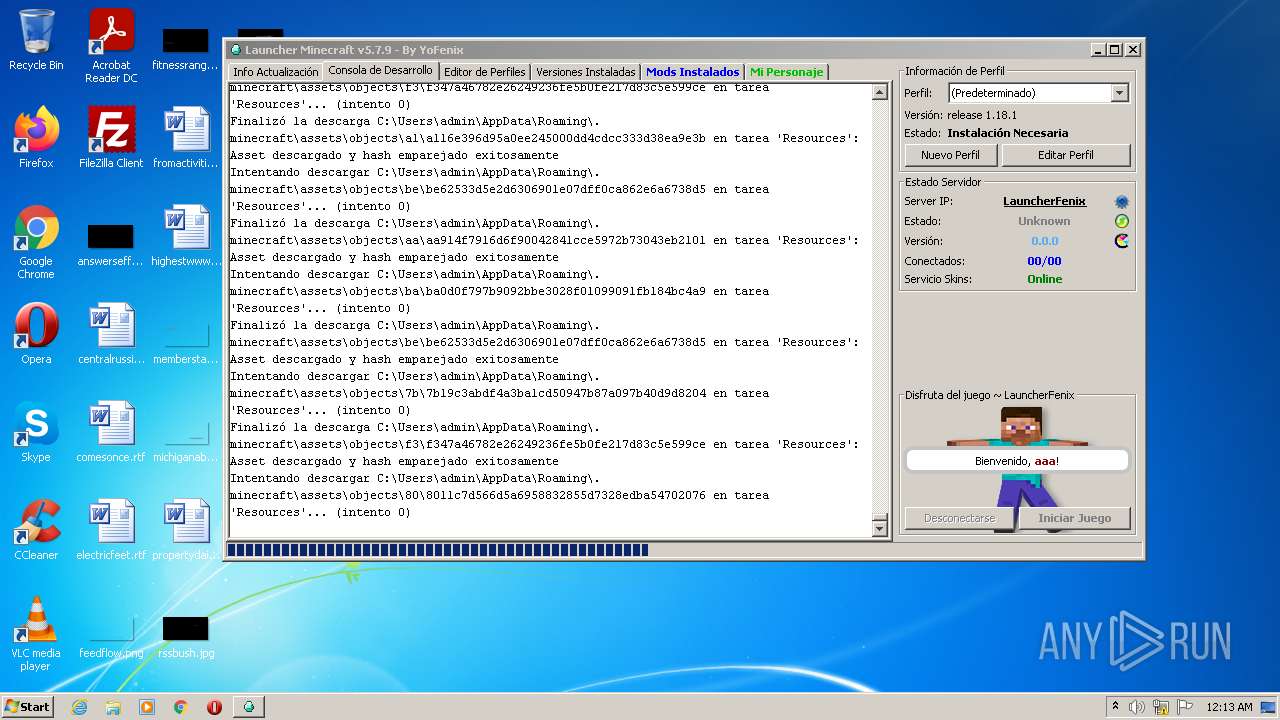
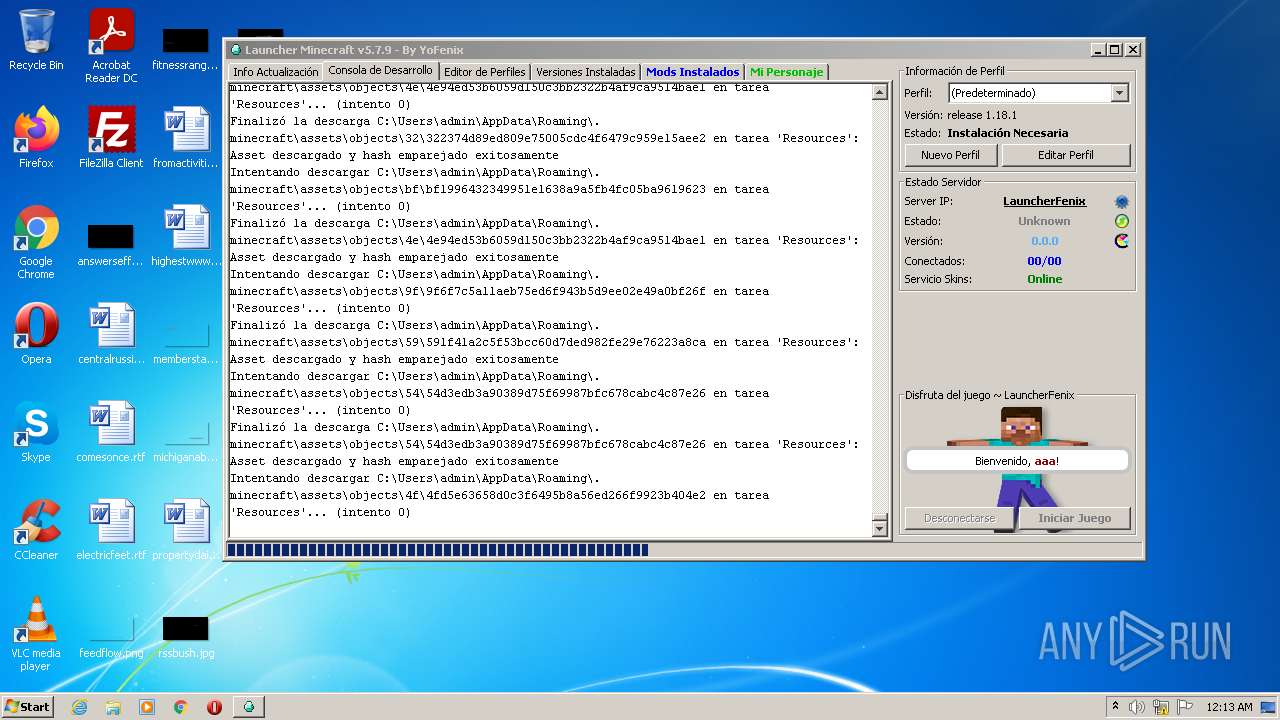
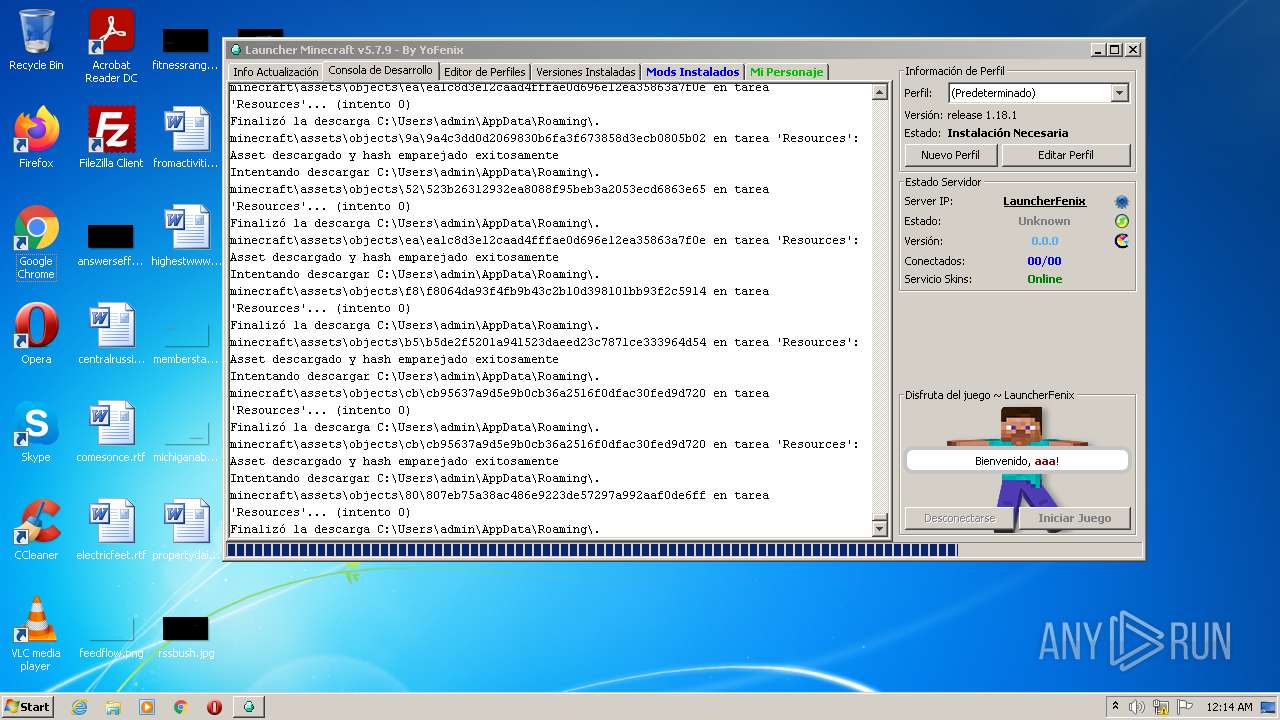
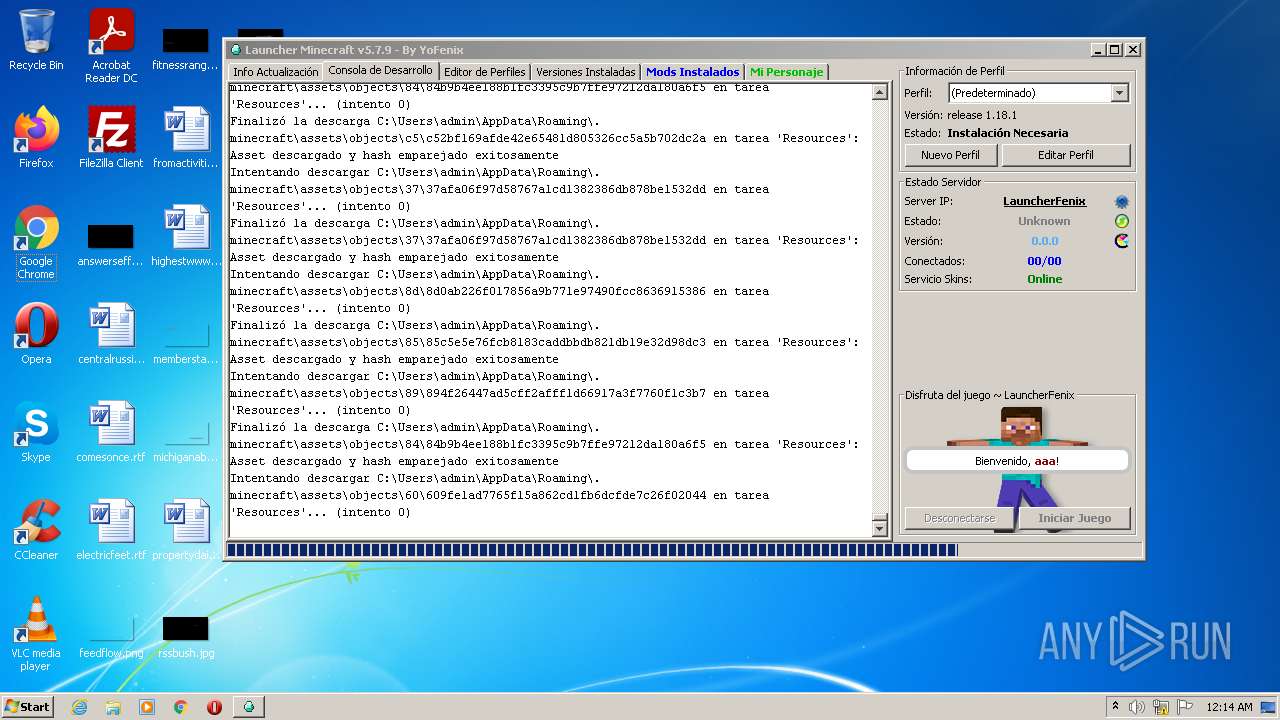
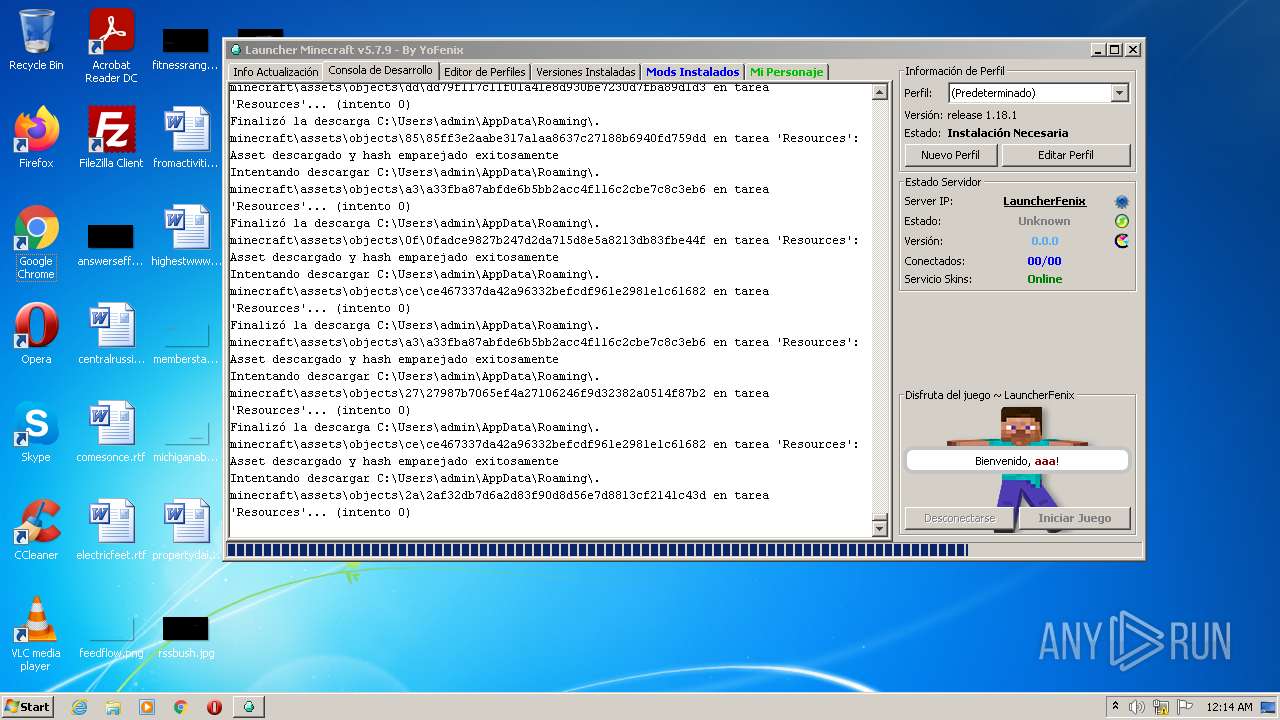
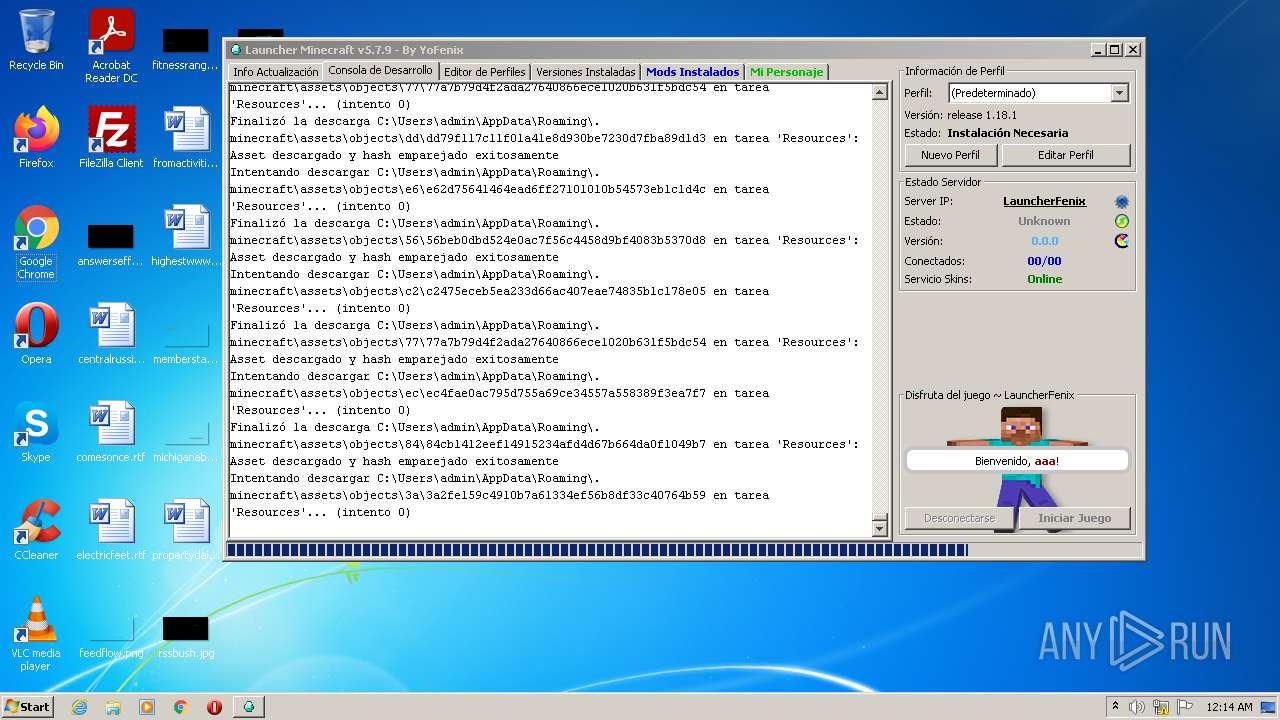
PID | Process | Filename | Type | |
|---|---|---|---|---|
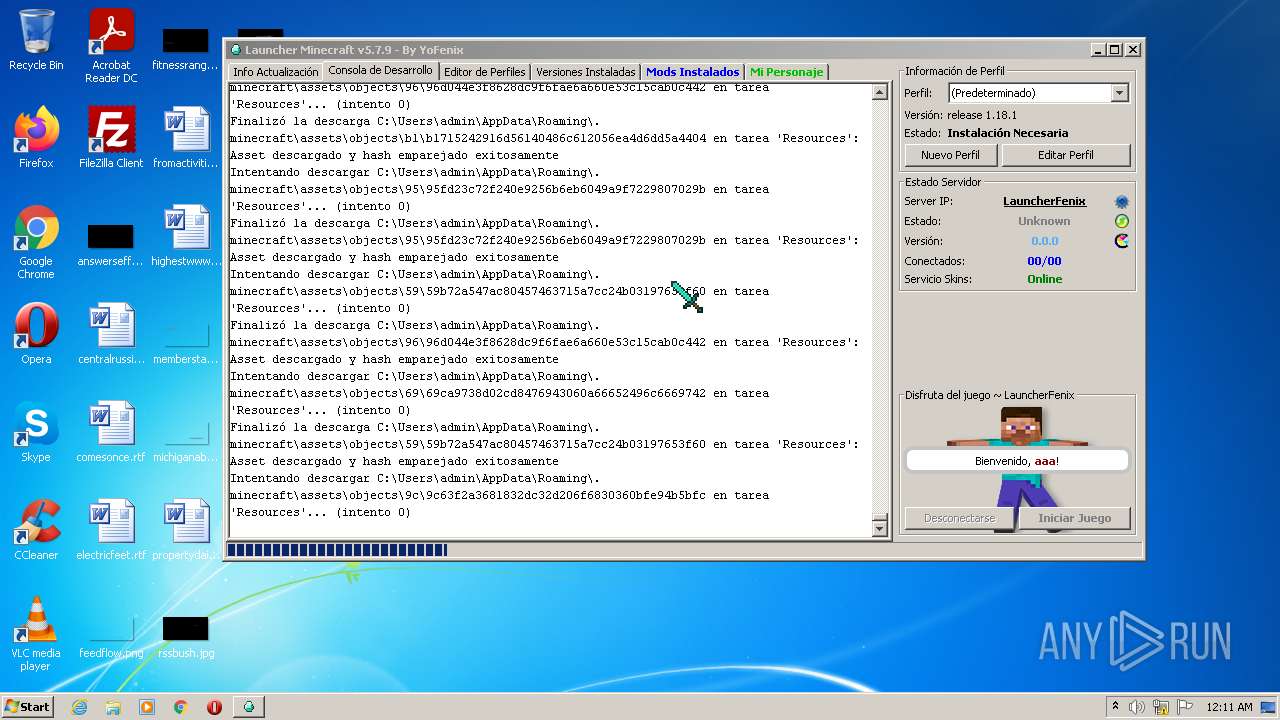
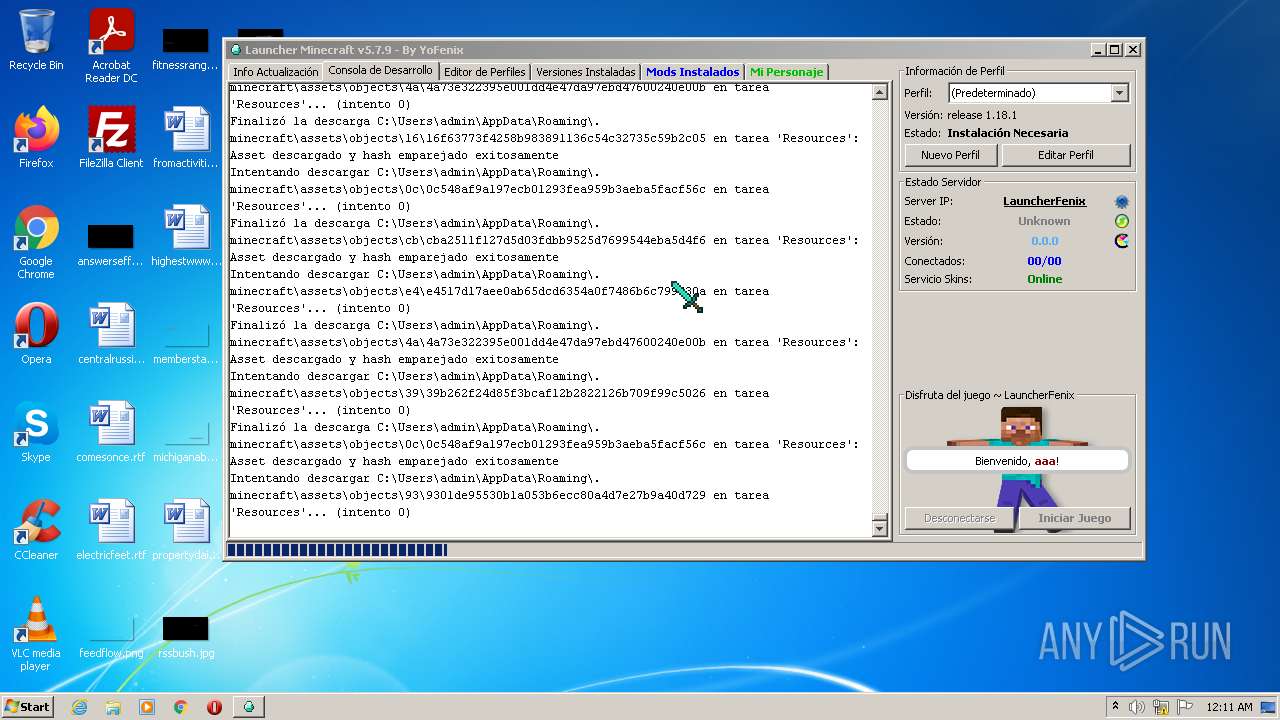
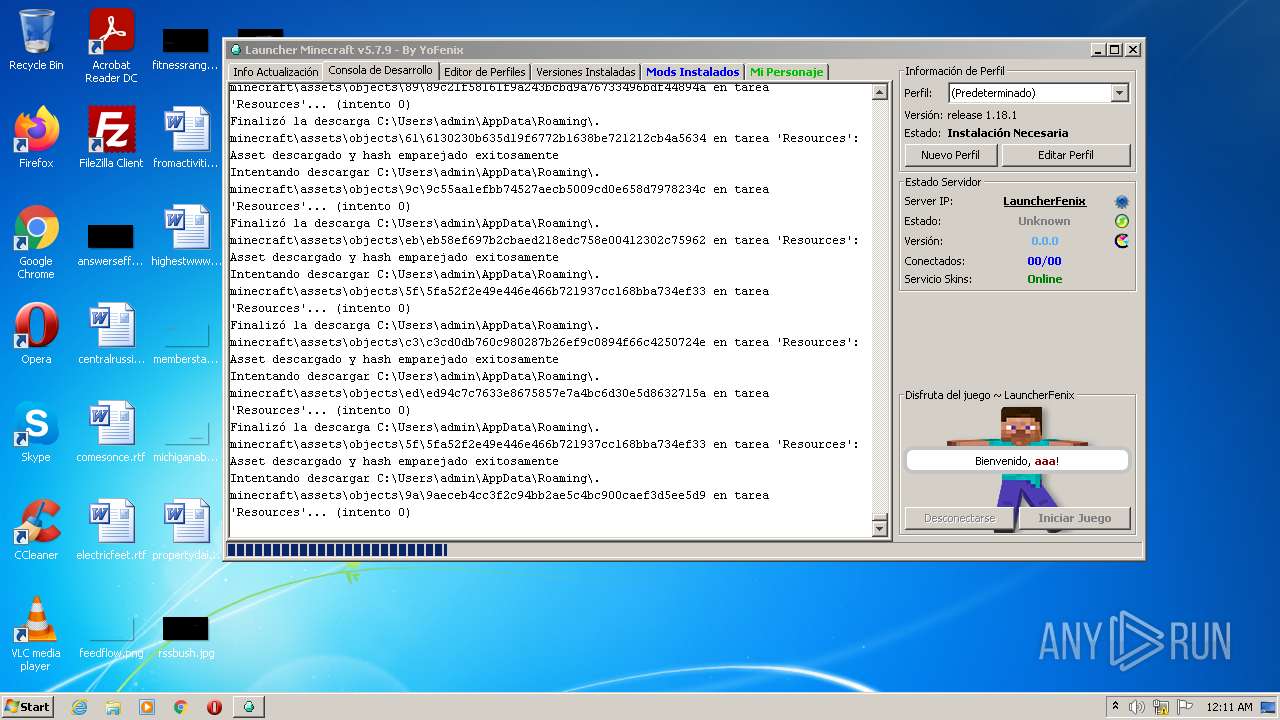
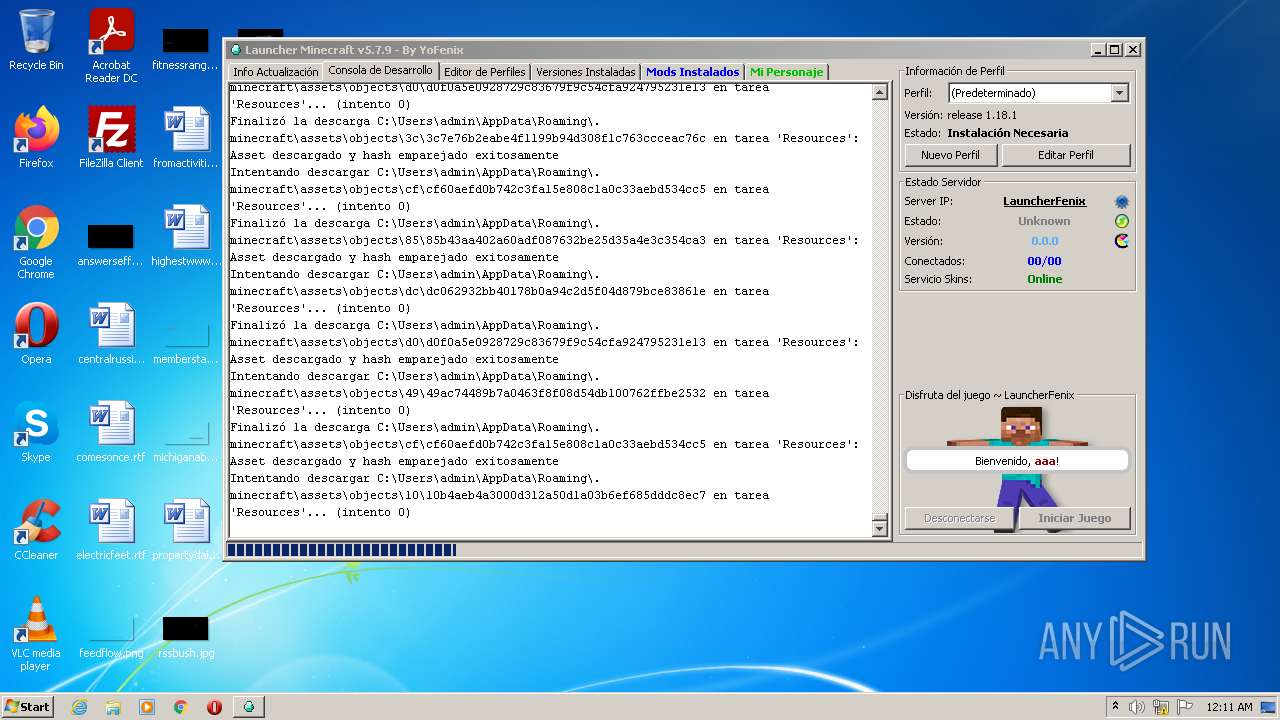
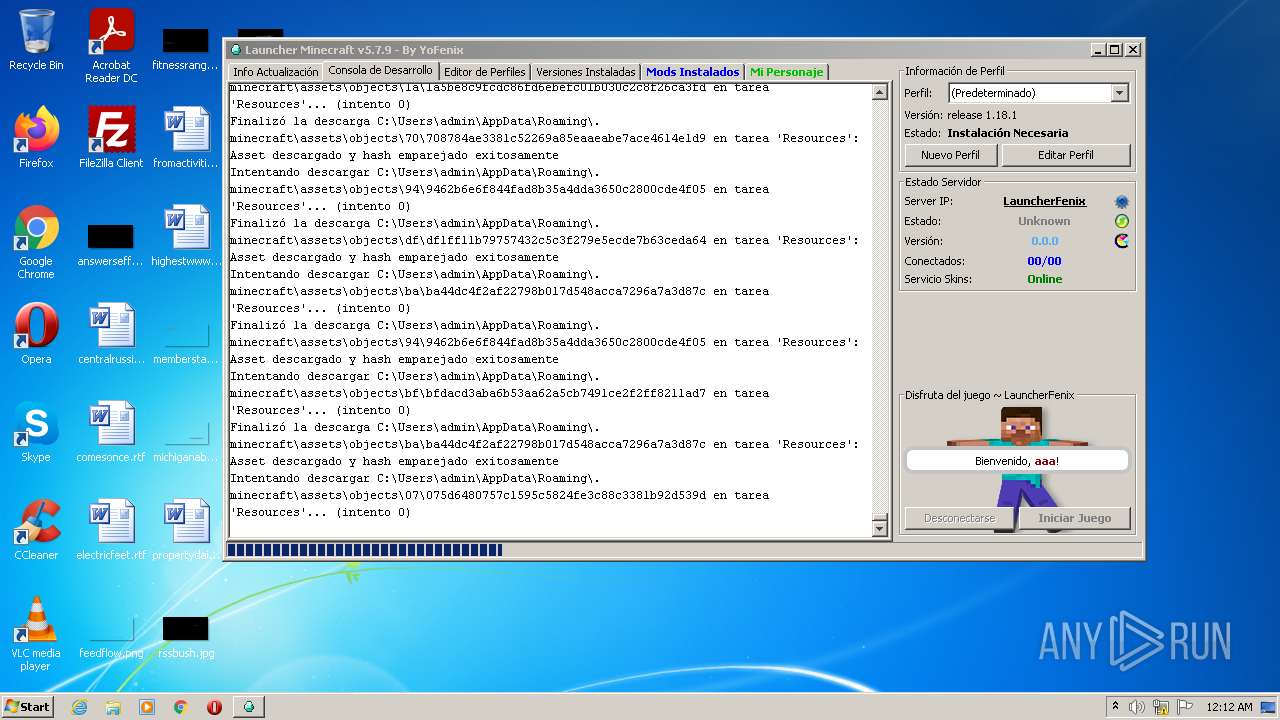
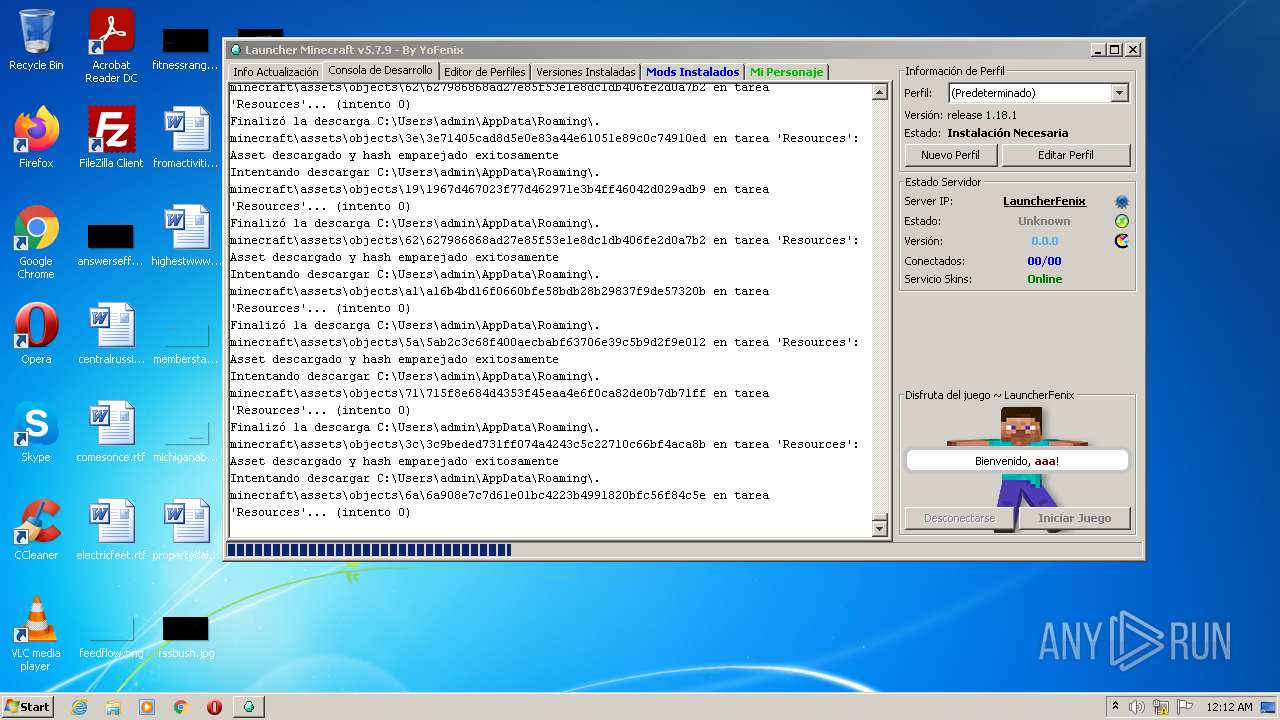
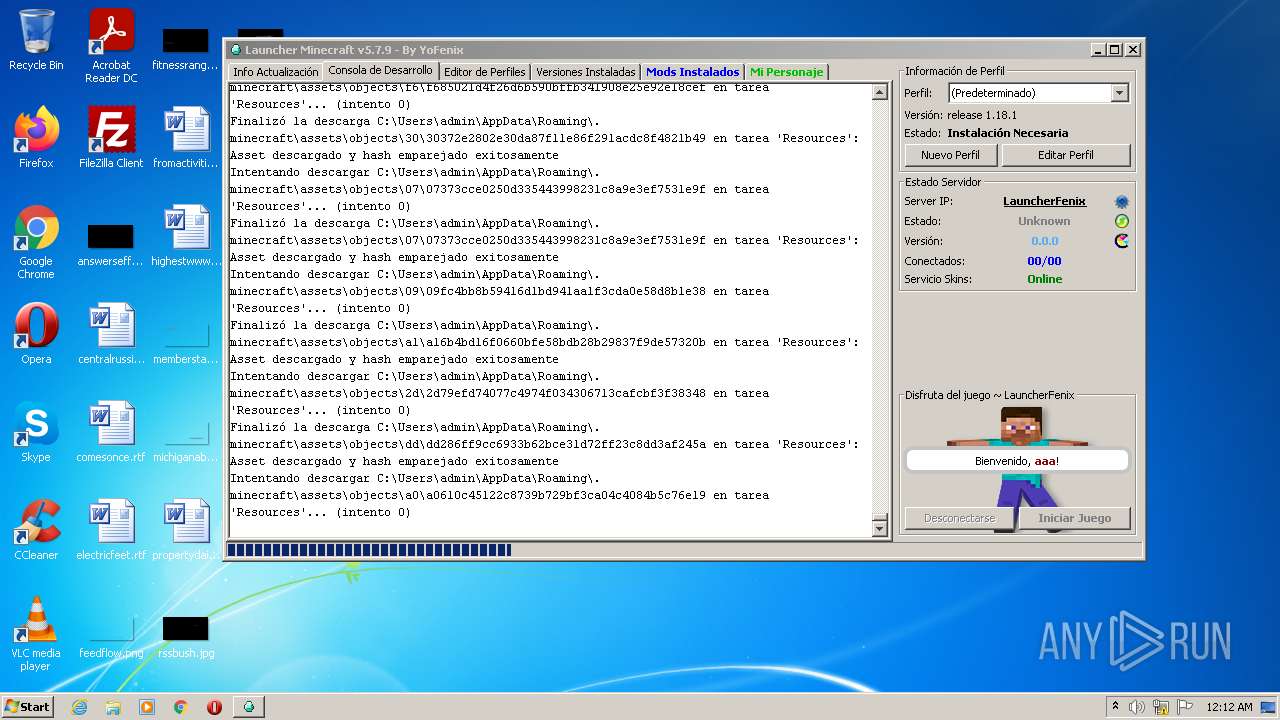
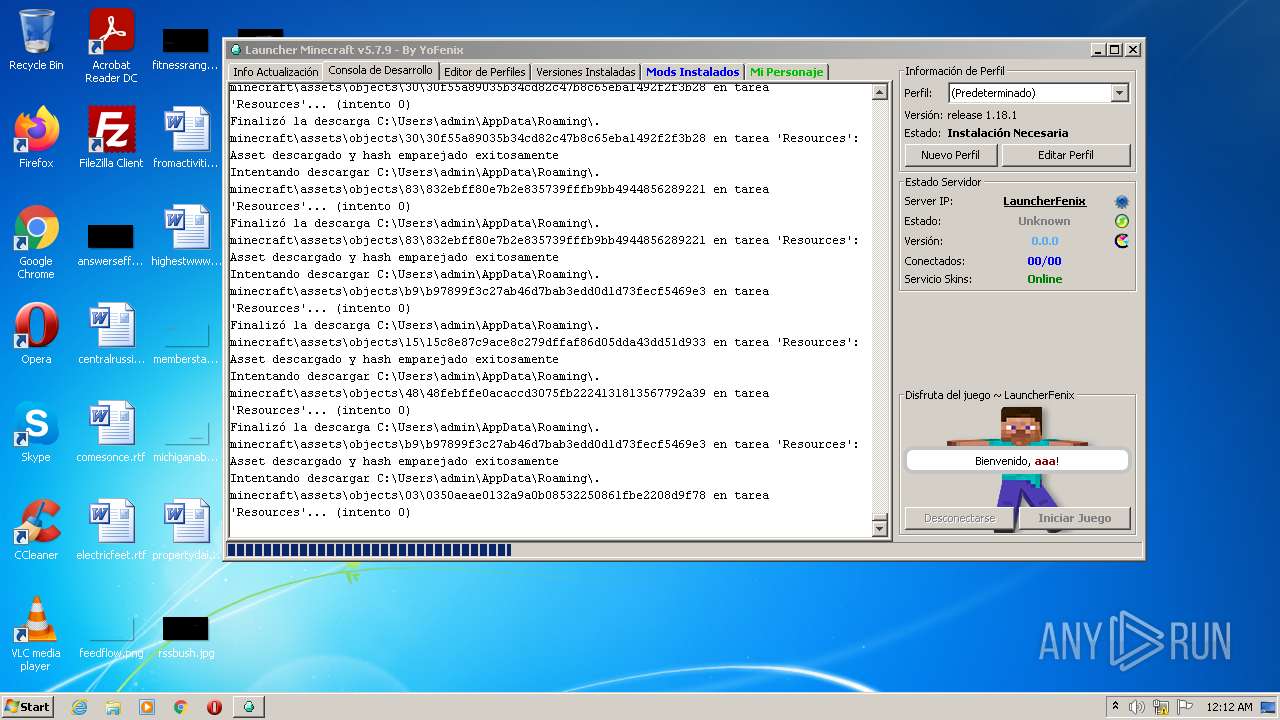
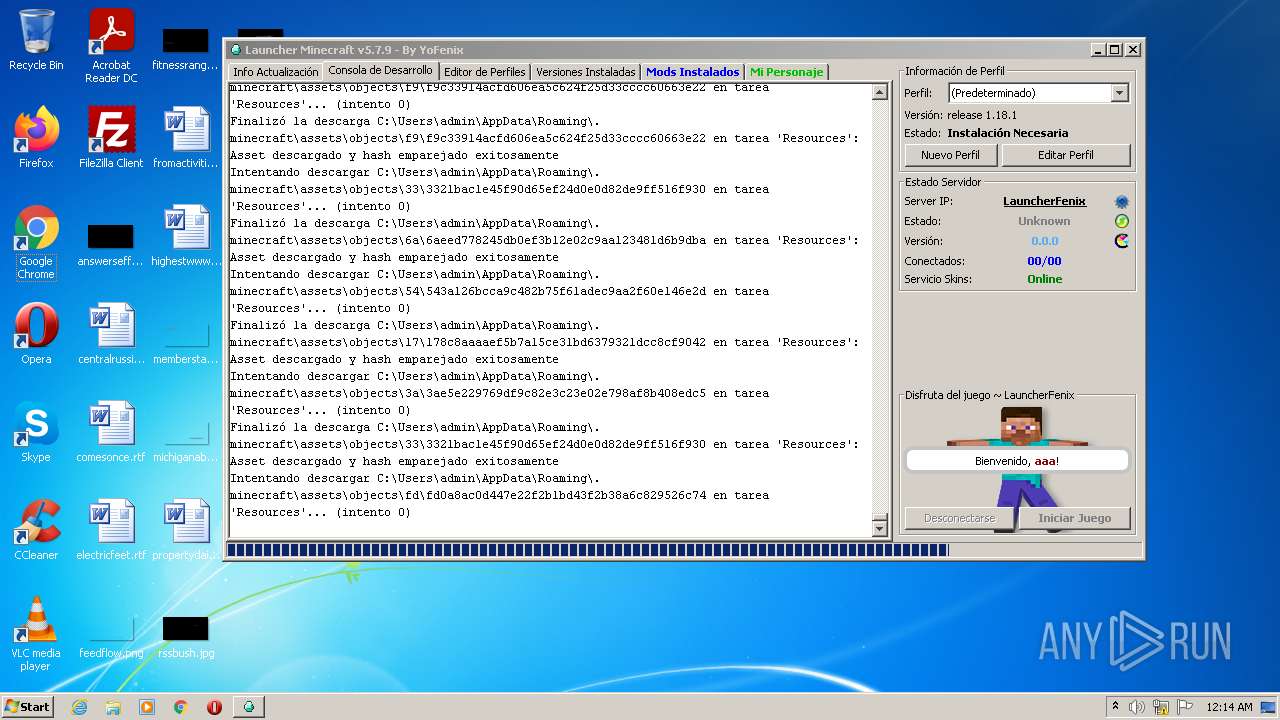
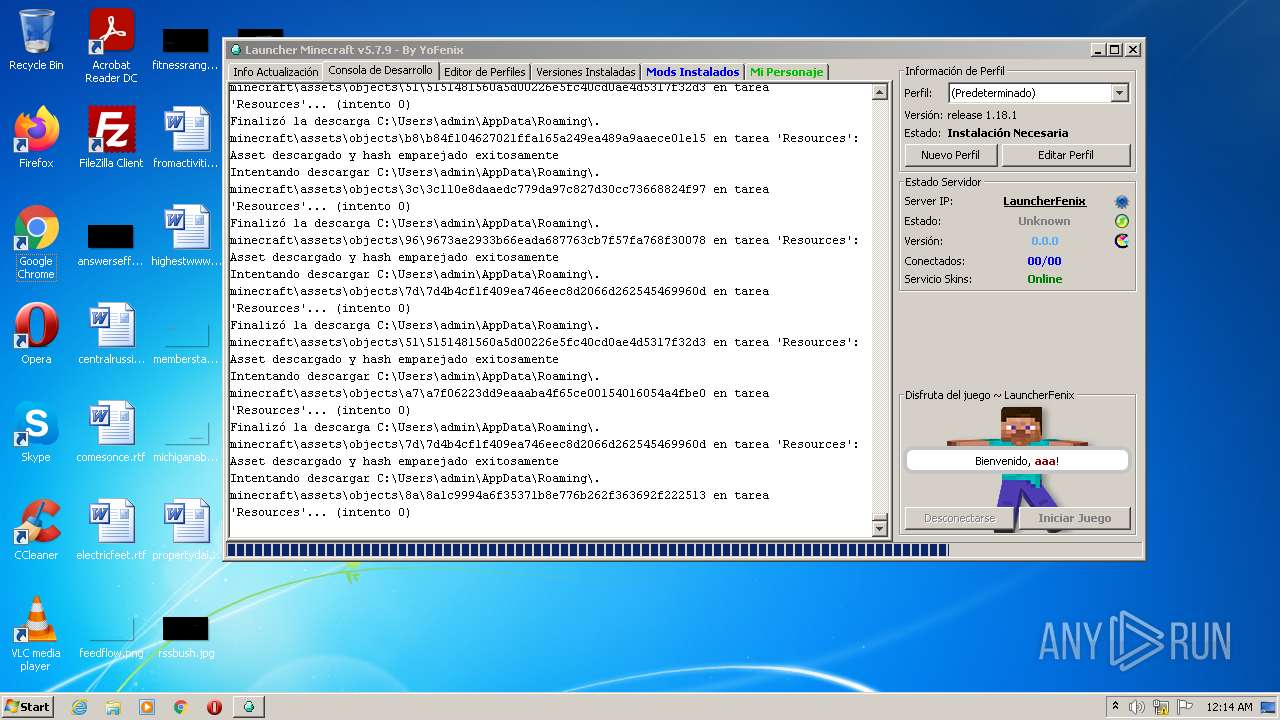
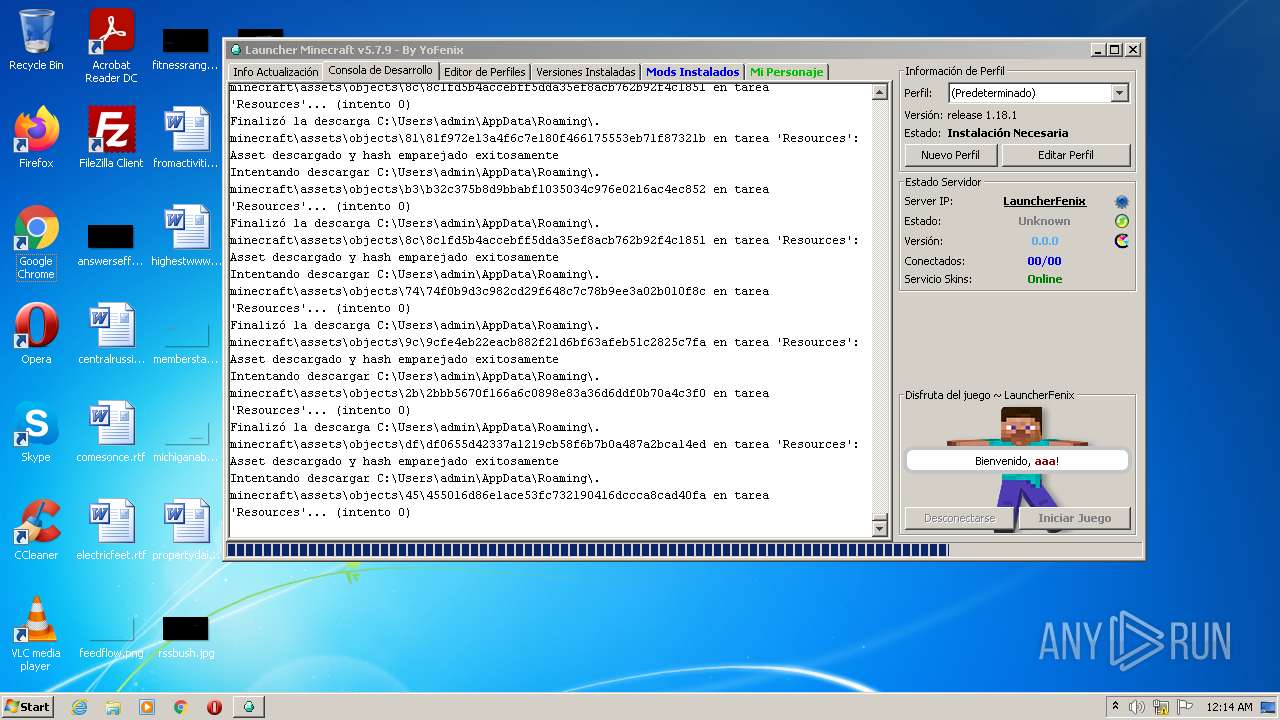
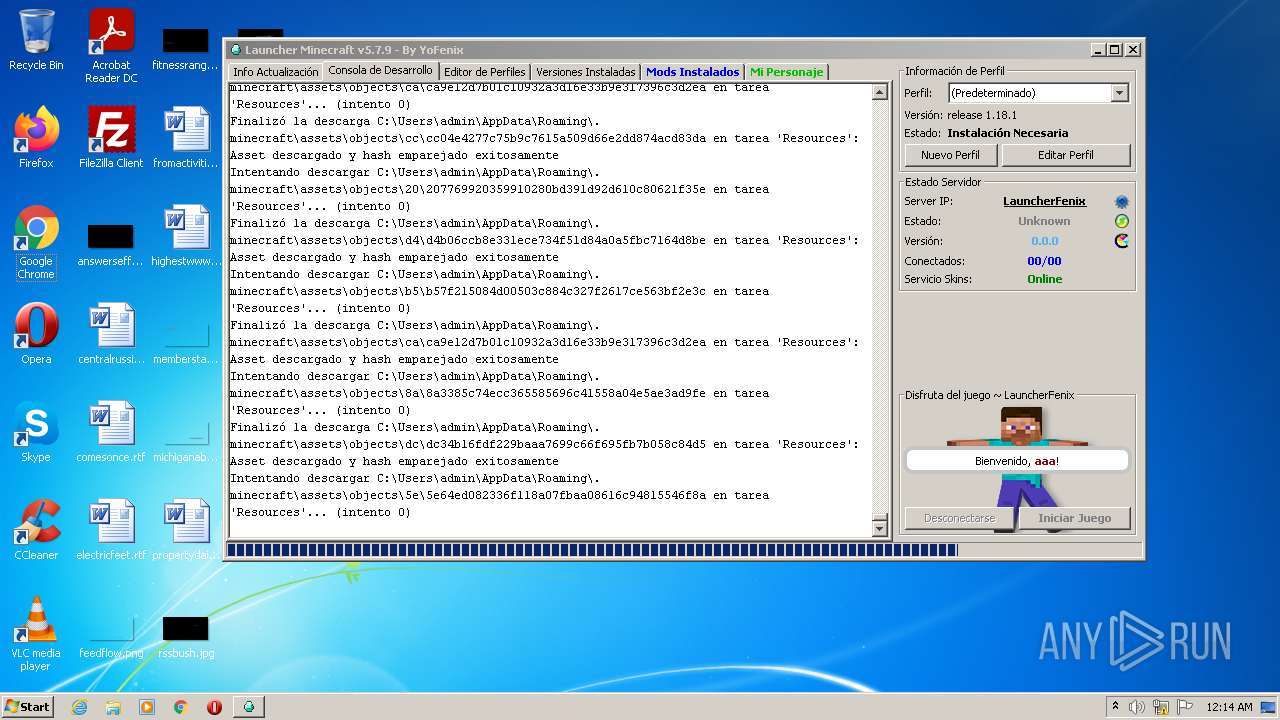
| 4084 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher_profiles.json | binary | |
MD5:— | SHA256:— | |||
| 4084 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\versions\1.18.1\1.18.1.json | binary | |
MD5:— | SHA256:— | |||
| 4084 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 4084 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\assets\indexes\1.18.json | binary | |
MD5:— | SHA256:— | |||
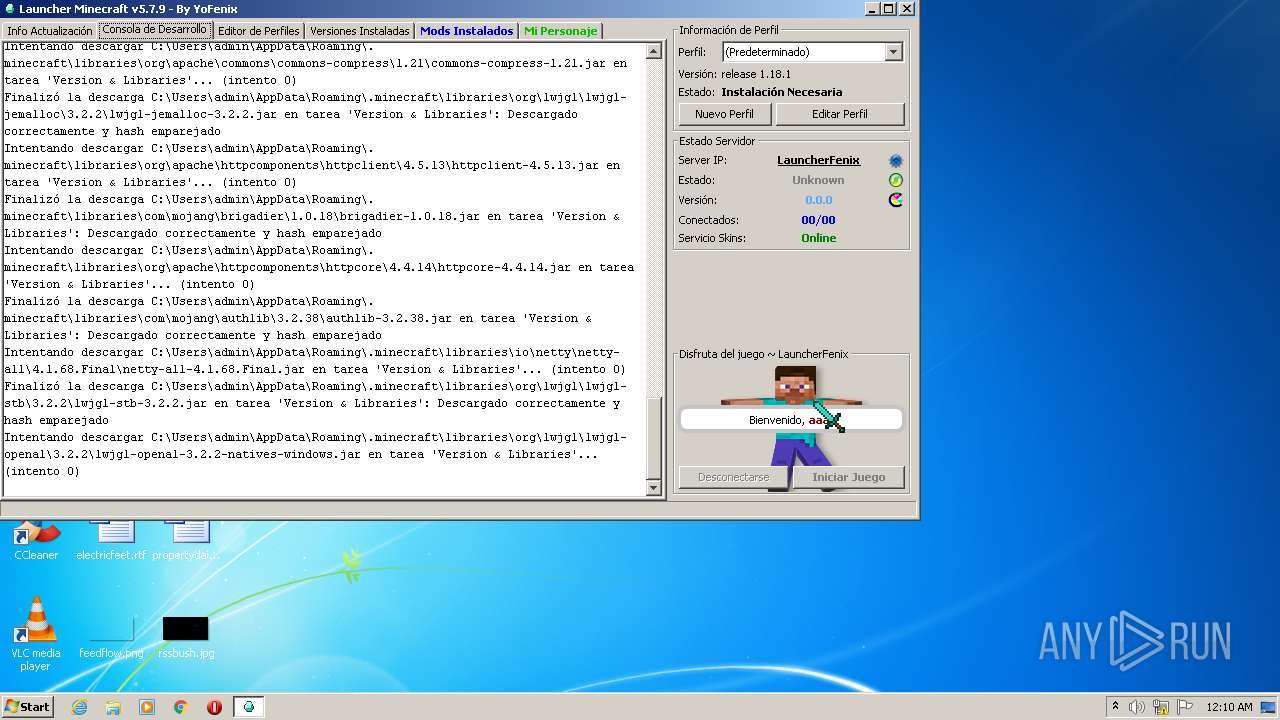
| 4084 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\text2speech\1.11.3\text2speech-1.11.3.jar | compressed | |
MD5:538B4224FA0C42012B4631FD1D25FD01 | SHA256:7DB3CFA0CA877DD08EA3336138F91F47EB93528BF04703EB8FA478E2DA97EF66 | |||
| 4084 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\patchy\2.1.6\patchy-2.1.6.jar | compressed | |
MD5:9BB5FAB2EE5E0364AADA05342DAEC9C4 | SHA256:302C68C244F0F8C13E186F9201030B21FC99C302F30E41D4ED8E8D31276FAF1F | |||
| 4084 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcherfenix.lzma | lzma | |
MD5:8797CC848D15E715E1C2383DD2980B44 | SHA256:E55755FE4BEAF8BC726E7F10D525817A76051B6A29A9E828B9D2E8035B953D7B | |||
| 4084 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio443760337667900585.tmp | image | |
MD5:2CA5B74339059672FBB666B5404E7B42 | SHA256:D2BC07BB8C7687D1353A103208657A81566E402A0463EDE94E12BE157FE3ADEA | |||
| 4084 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\google\guava\failureaccess\1.0.1\failureaccess-1.0.1.jar | java | |
MD5:091883993EF5BFA91DA01DCC8FC52236 | SHA256:A171EE4C734DD2DA837E4B16BE9DF4661AFAB72A41ADAF31EB84DFDAF936CA26 | |||
| 4084 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\javabridge\1.2.24\javabridge-1.2.24.jar | compressed | |
MD5:636482F086E794F2CB227672828392FA | SHA256:B5F8871A1799B36E27A5F2AD8A4B47DB39210031C967B794707B92E9E3F8598E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3 050
TCP/UDP connections
55
DNS requests
16
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
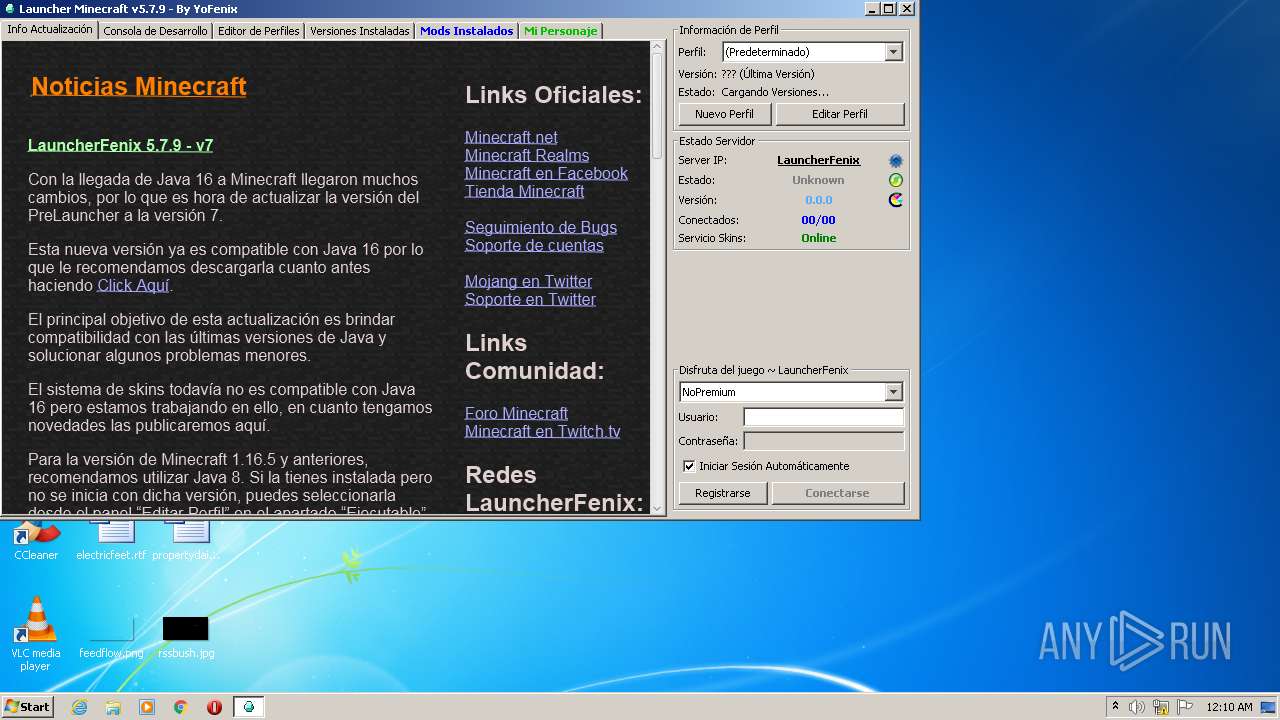
4084 | javaw.exe | GET | 302 | 74.114.154.18:80 | http://iniciolauncherfx.tumblr.com/ | CA | — | — | malicious |
4084 | javaw.exe | GET | 200 | 104.21.72.175:80 | http://mc.launcherfenix.com.ar/modsloader/mcforge/version_manifest.json | US | binary | 3.33 Kb | suspicious |
4084 | javaw.exe | GET | 200 | 13.225.80.114:80 | http://resources.download.minecraft.net/d8/d83f84529125443dc54c215de2452b790c9fc1b4 | US | ogg | 46.3 Kb | shared |
4084 | javaw.exe | GET | 200 | 13.225.80.114:80 | http://resources.download.minecraft.net/0f/0fa871fe4d9701a27e2de2921d58ff5afa86592c | US | ogg | 19.2 Kb | shared |
4084 | javaw.exe | GET | 200 | 13.225.80.114:80 | http://resources.download.minecraft.net/21/210c839d6fab655373b3a5e4c278f59dff4936d8 | US | ogg | 89.3 Kb | shared |
4084 | javaw.exe | GET | 200 | 13.225.80.114:80 | http://resources.download.minecraft.net/66/66cca21cf1176d784ac278f7568e605c9a60fbb1 | US | tss | 403 Kb | shared |
4084 | javaw.exe | GET | 200 | 13.225.80.114:80 | http://resources.download.minecraft.net/06/0671f582b7c77b8cd33e82f8fdd6d1e95a7f6fb8 | US | ogg | 18.2 Kb | shared |
4084 | javaw.exe | GET | 200 | 13.225.80.114:80 | http://resources.download.minecraft.net/f1/f1d415513b2826f464fa04652144427d673c7c8b | US | tss | 795 Kb | shared |
4084 | javaw.exe | GET | 200 | 13.225.80.114:80 | http://resources.download.minecraft.net/c3/c31af622a2ee7beffb9daf72363a77a607be64a3 | US | ogg | 9.08 Kb | shared |
4084 | javaw.exe | GET | 200 | 13.225.80.114:80 | http://resources.download.minecraft.net/26/26c66e23e467bd088fc3341d49620a9ea992af7e | US | ogg | 5.63 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4084 | javaw.exe | 162.125.66.18:443 | www.dropbox.com | Dropbox, Inc. | DE | suspicious |
4084 | javaw.exe | 162.125.66.15:443 | uc178d0da7ba58cae1f4afd2df86.dl.dropboxusercontent.com | Dropbox, Inc. | DE | malicious |
4084 | javaw.exe | 13.225.30.128:443 | launchermeta.mojang.com | — | US | unknown |
4084 | javaw.exe | 74.114.154.18:80 | iniciolauncherfx.tumblr.com | Automattic, Inc | CA | malicious |
4084 | javaw.exe | 74.114.154.18:443 | iniciolauncherfx.tumblr.com | Automattic, Inc | CA | malicious |
4084 | javaw.exe | 172.67.153.84:80 | profile.launcherfenix.com.ar | — | US | suspicious |
4084 | javaw.exe | 18.66.248.14:80 | resources.download.minecraft.net | Massachusetts Institute of Technology | US | suspicious |
4084 | javaw.exe | 18.66.248.120:80 | resources.download.minecraft.net | Massachusetts Institute of Technology | US | suspicious |
4084 | javaw.exe | 13.225.80.114:80 | resources.download.minecraft.net | — | US | suspicious |
4084 | javaw.exe | 13.224.193.128:443 | launcher.mojang.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dropbox.com |
| shared |
uc178d0da7ba58cae1f4afd2df86.dl.dropboxusercontent.com |
| malicious |
uc6bad22fd5b93d4798cfe7927b2.dl.dropboxusercontent.com |
| malicious |
launchermeta.mojang.com |
| whitelisted |
profile.launcherfenix.com.ar |
| suspicious |
iniciolauncherfx.tumblr.com |
| malicious |
assets.tumblr.com |
| whitelisted |
px.srvcs.tumblr.com |
| whitelisted |
static.tumblr.com |
| whitelisted |
mc.launcherfenix.com.ar |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4084 | javaw.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
4084 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
4084 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |