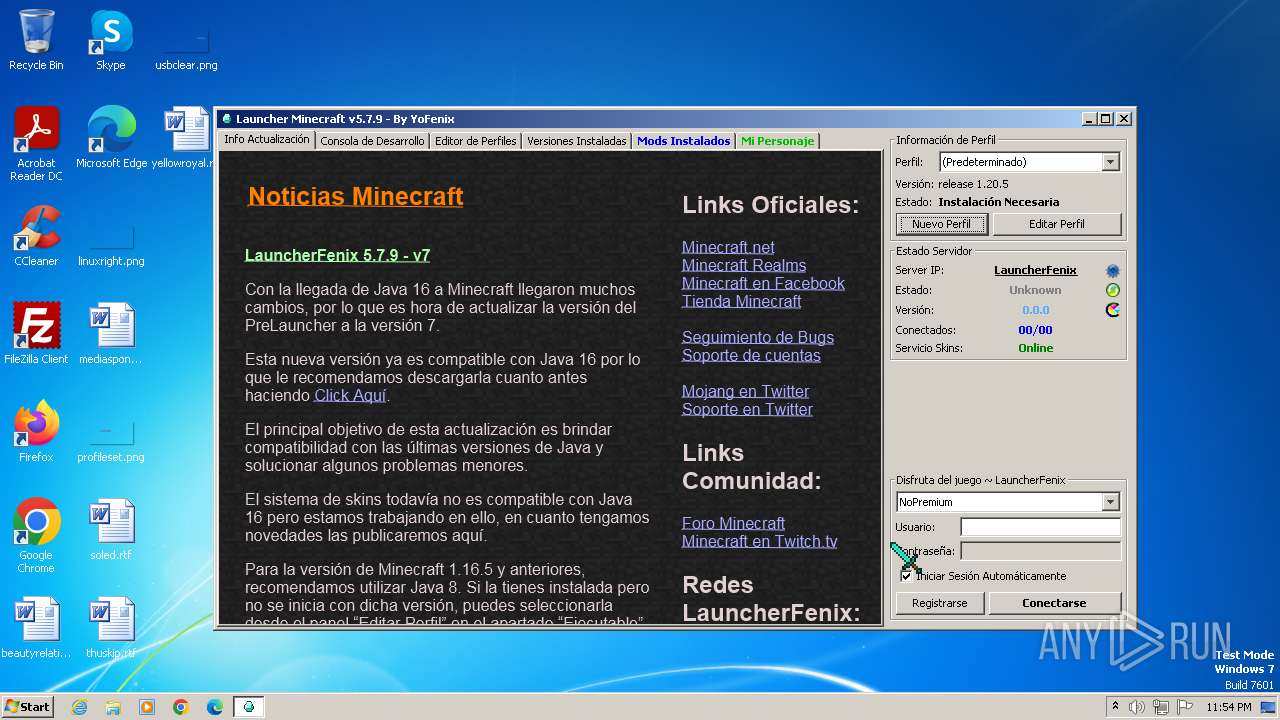
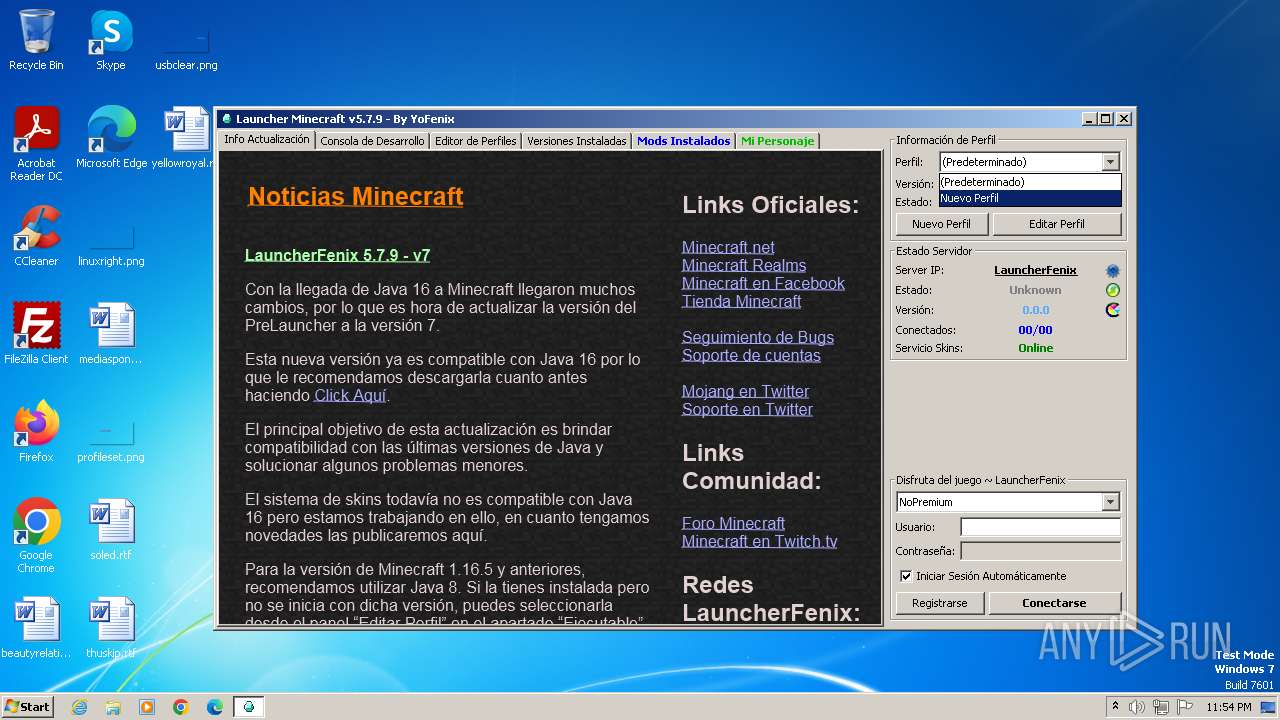
| File name: | LauncherFenix-Minecraft-v7.exe |
| Full analysis: | https://app.any.run/tasks/2c26ed7f-4124-4261-b0c0-a1212d5831f9 |
| Verdict: | Malicious activity |
| Analysis date: | April 27, 2024, 22:54:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | D99BB55B57712065BC88BE297C1DA38C |
| SHA1: | FB6662DD31E8E5BE380FBD7A33A50A45953FE1E7 |
| SHA256: | 122BFBB9F67E355340991DEEACB167BE9C12AD726B5A7C5779448DD0CC4AF0CB |
| SSDEEP: | 3072:puzvch1rugYc4wqYSRR756K7ItBjgXHUYCnlK:Wch1aIqYSRVM+unlK |
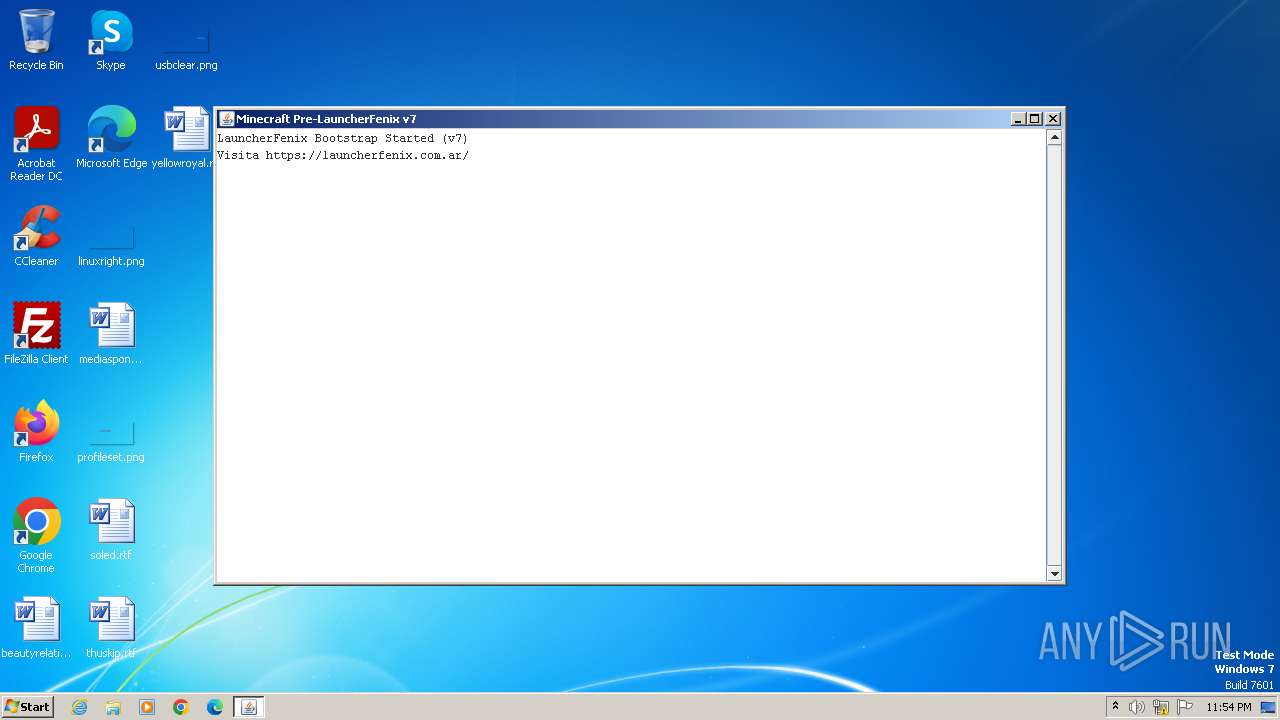
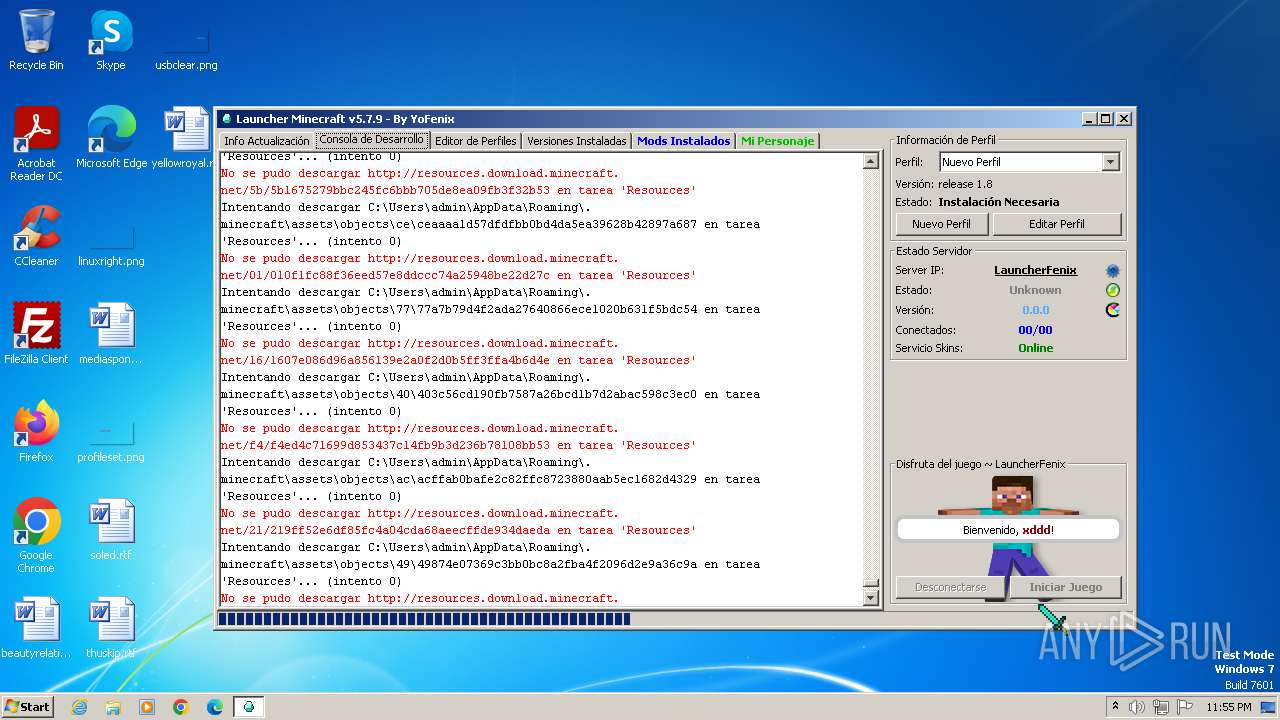
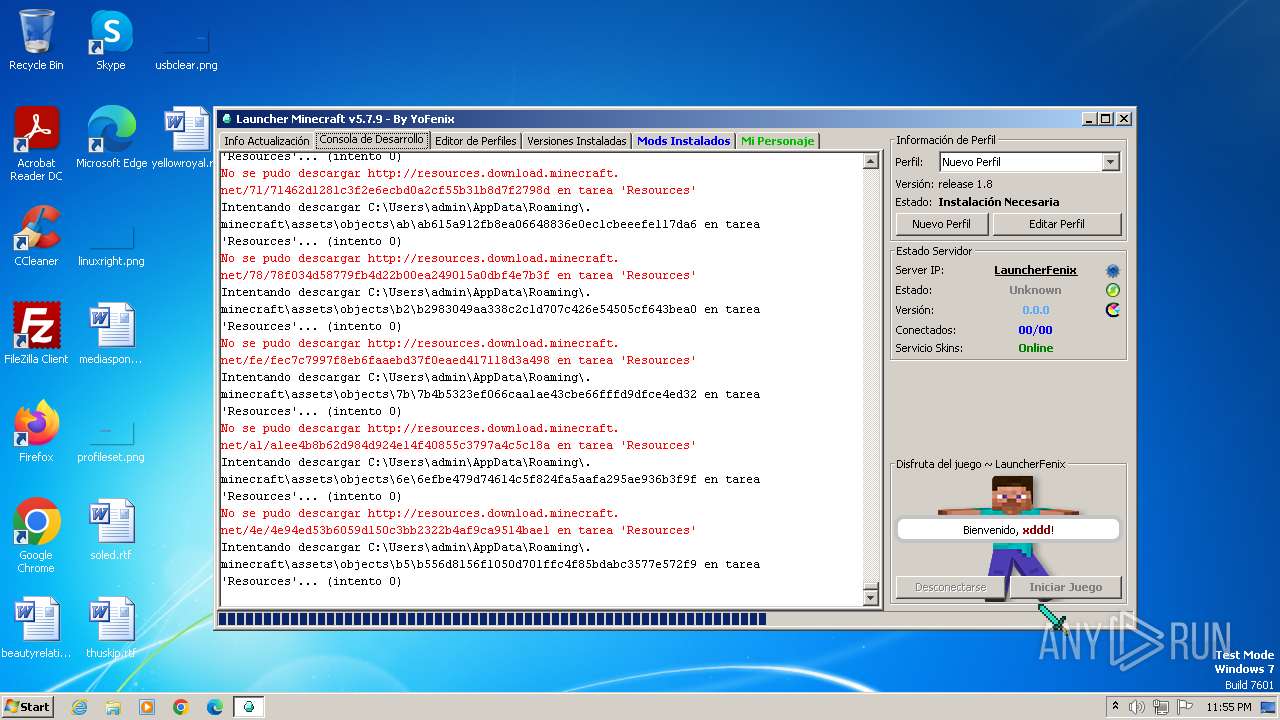
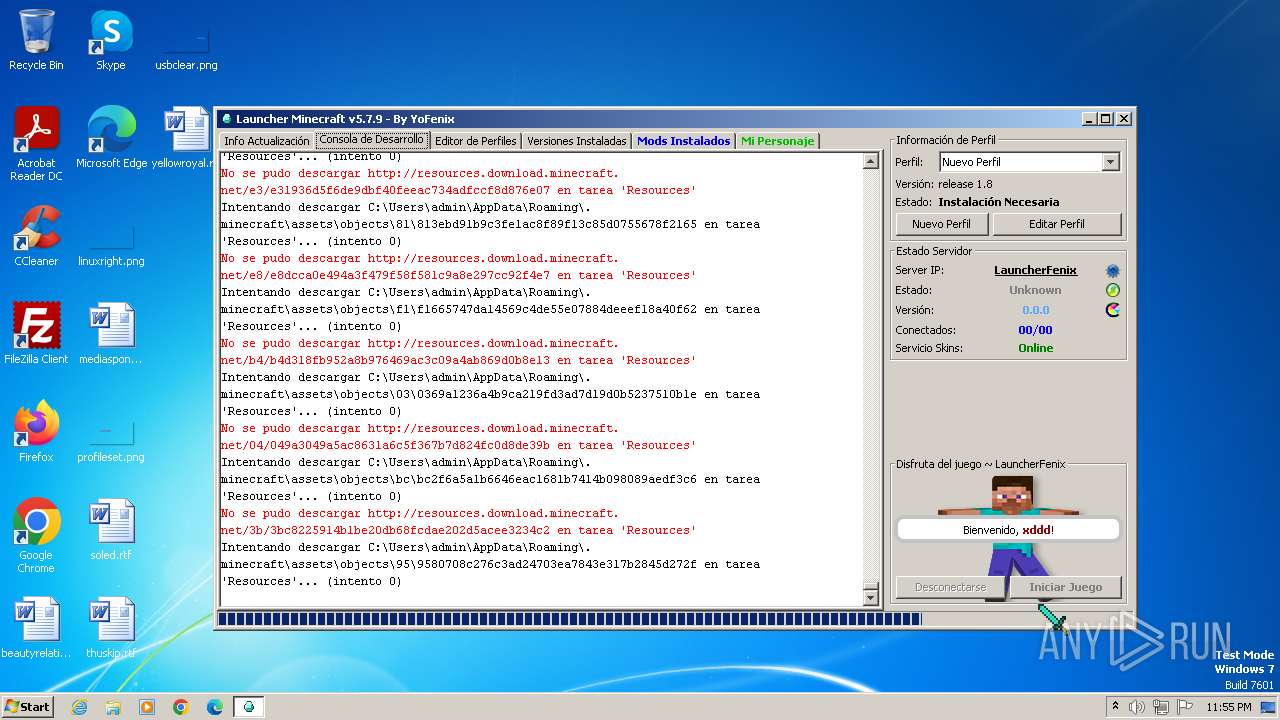
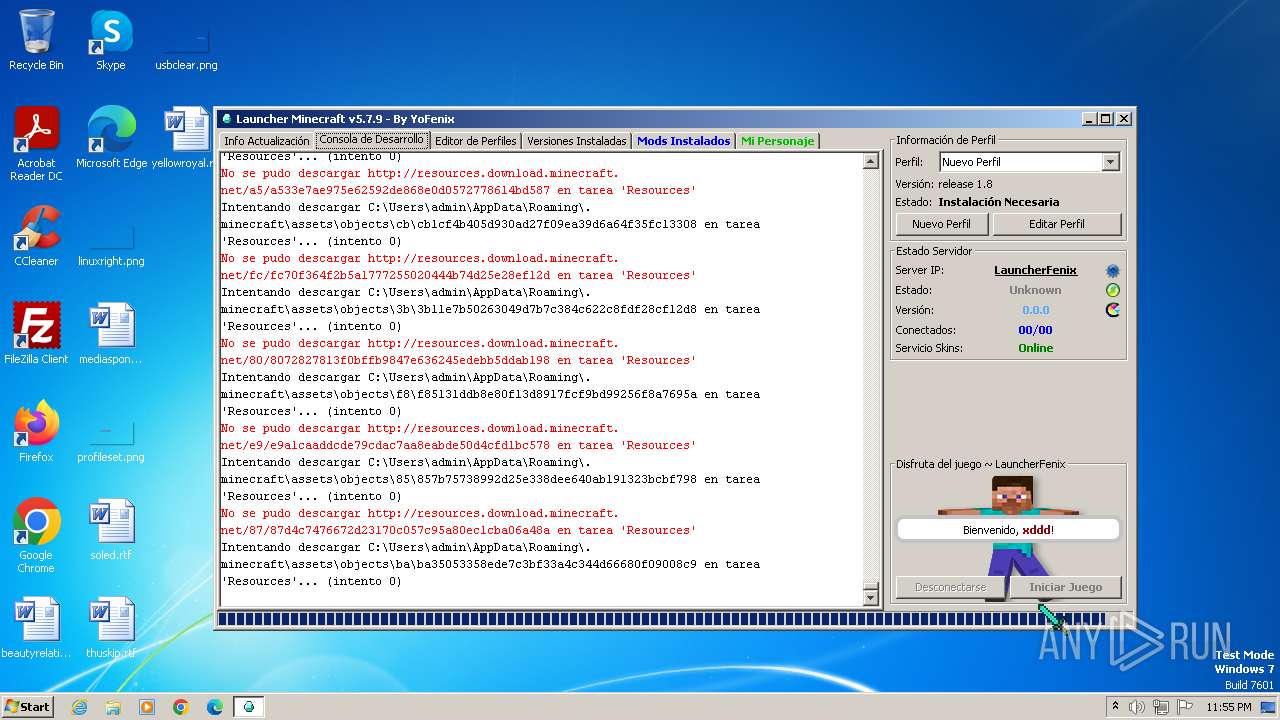
MALICIOUS
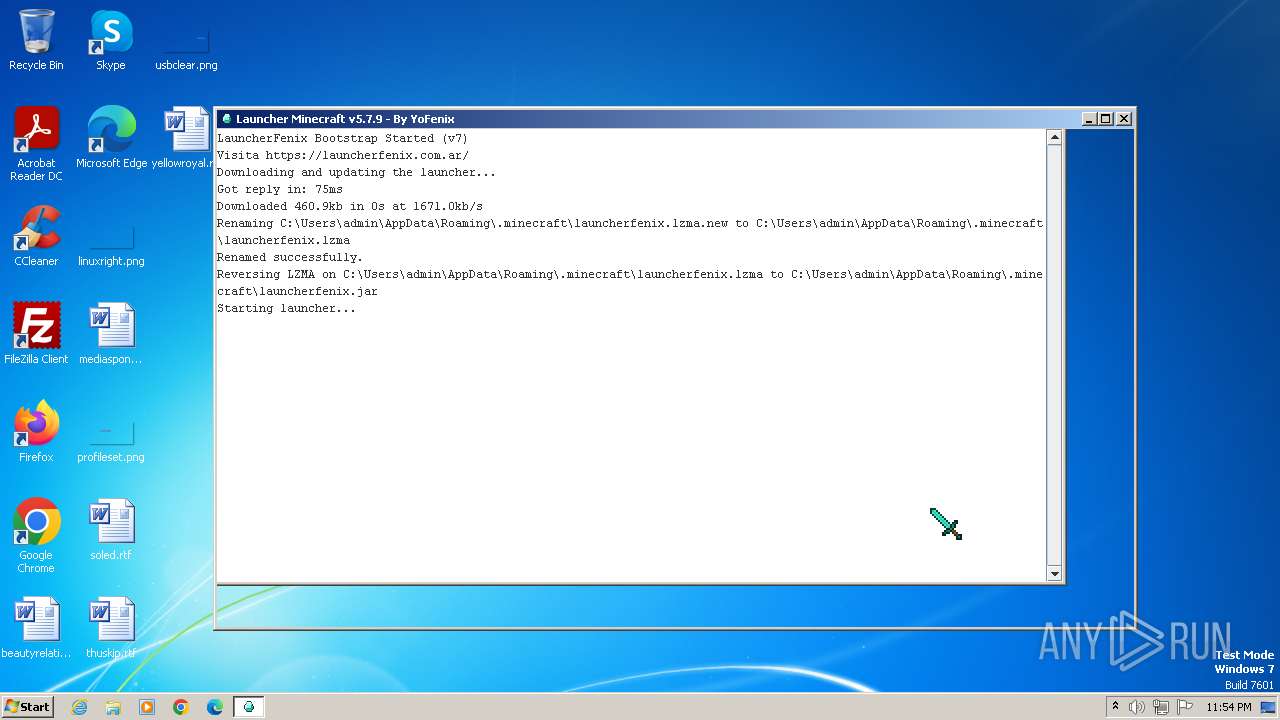
Drops the executable file immediately after the start
- LauncherFenix-Minecraft-v7.exe (PID: 3968)
- javaw.exe (PID: 3984)
SUSPICIOUS
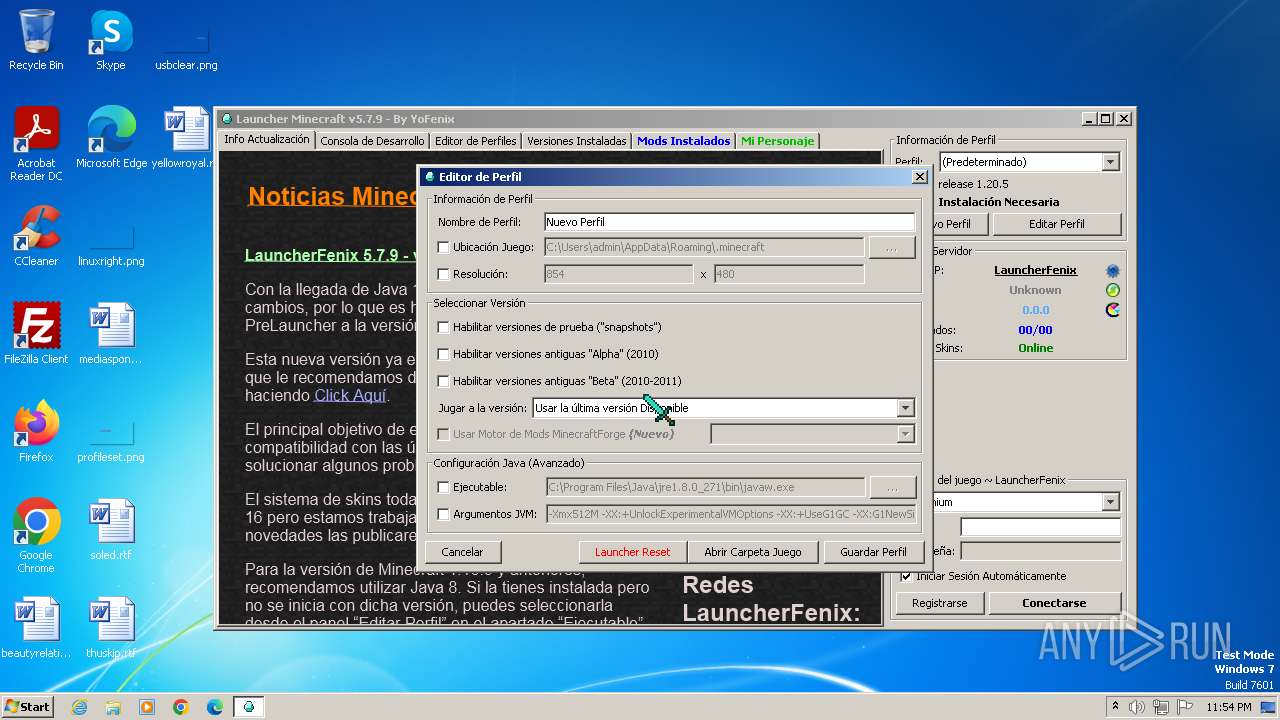
Checks for Java to be installed
- LauncherFenix-Minecraft-v7.exe (PID: 3968)
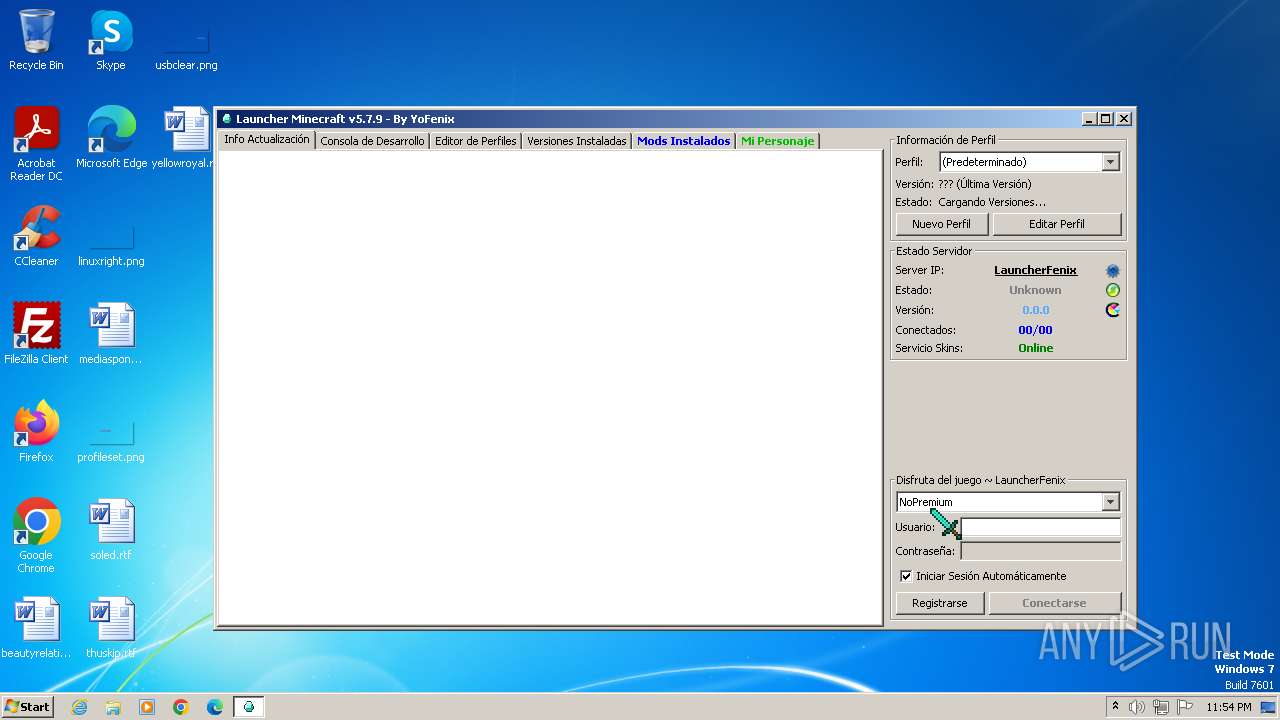
Potential Corporate Privacy Violation
- javaw.exe (PID: 3984)
Process requests binary or script from the Internet
- javaw.exe (PID: 3984)
INFO
Checks supported languages
- javaw.exe (PID: 3984)
- LauncherFenix-Minecraft-v7.exe (PID: 3968)
- wmpnscfg.exe (PID: 752)
Create files in a temporary directory
- javaw.exe (PID: 3984)
Reads the computer name
- javaw.exe (PID: 3984)
- wmpnscfg.exe (PID: 752)
Reads the machine GUID from the registry
- javaw.exe (PID: 3984)
Creates files in the program directory
- javaw.exe (PID: 3984)
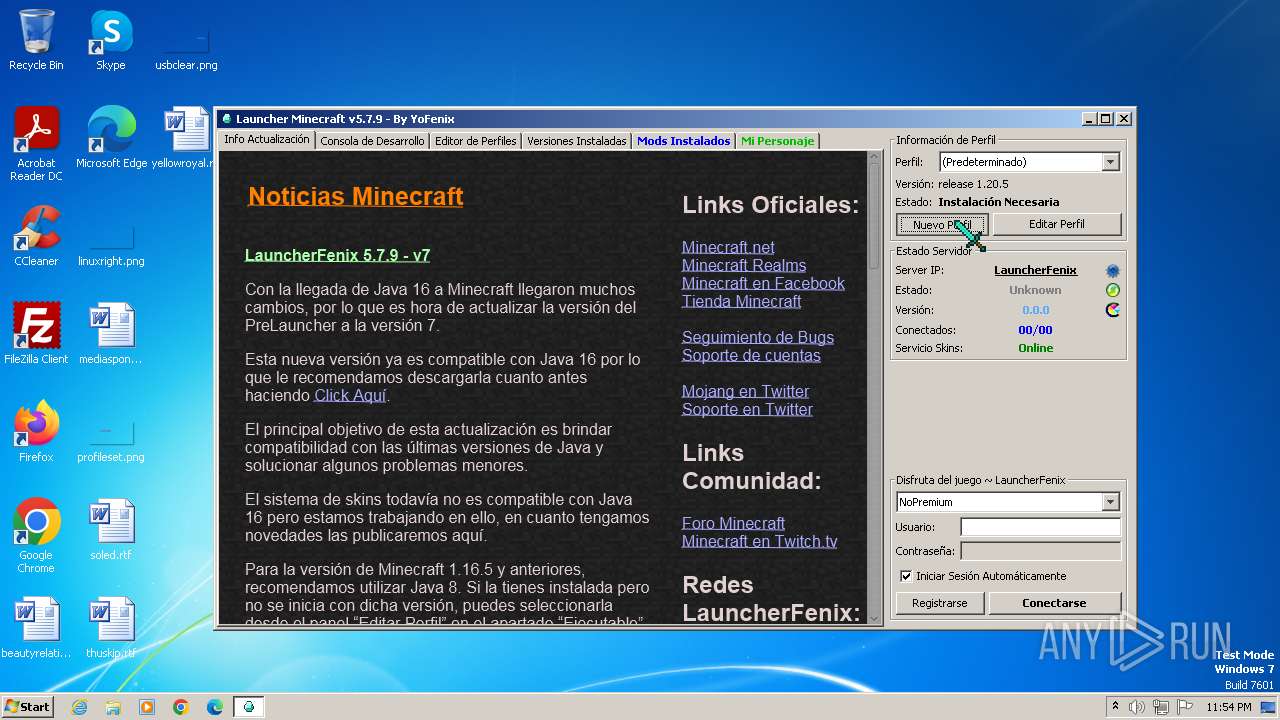
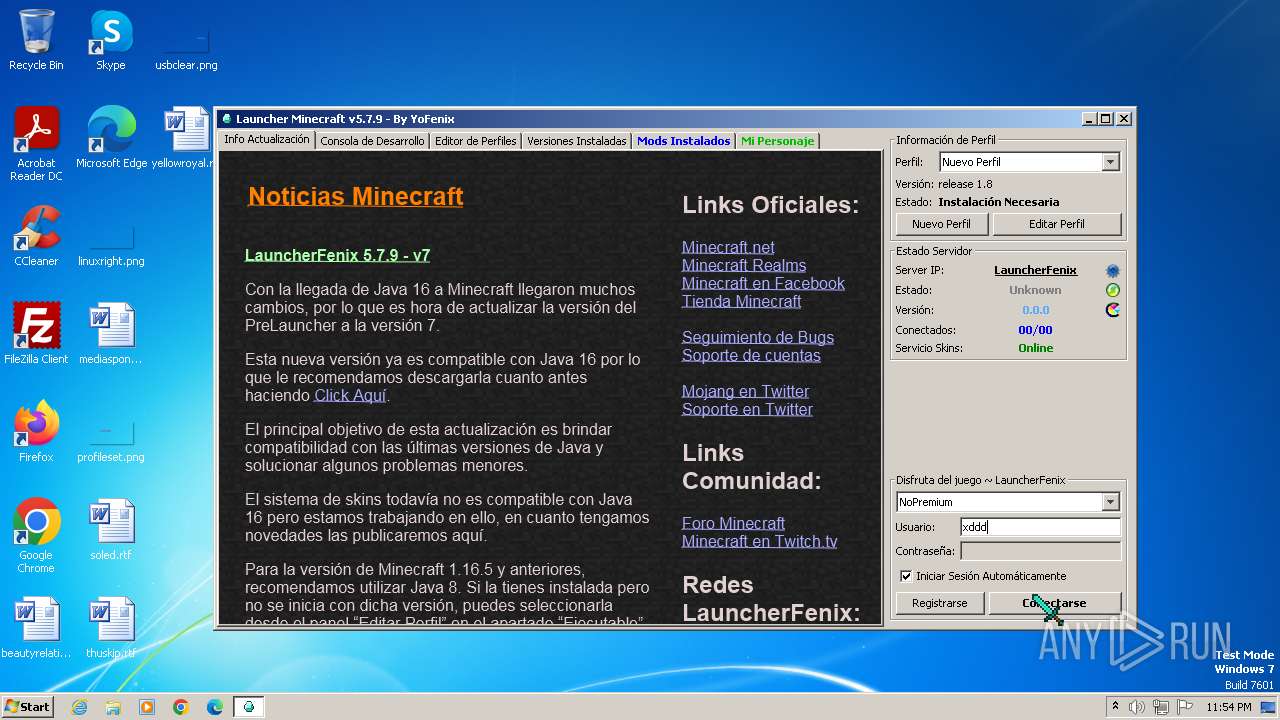
Manual execution by a user
- wmpnscfg.exe (PID: 752)
Creates files or folders in the user directory
- javaw.exe (PID: 3984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:05:30 22:29:07+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 23040 |
| InitializedDataSize: | 315904 |
| UninitializedDataSize: | 36352 |
| EntryPoint: | 0x1590 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.0.1 |
| ProductVersionNumber: | 7.0.0.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
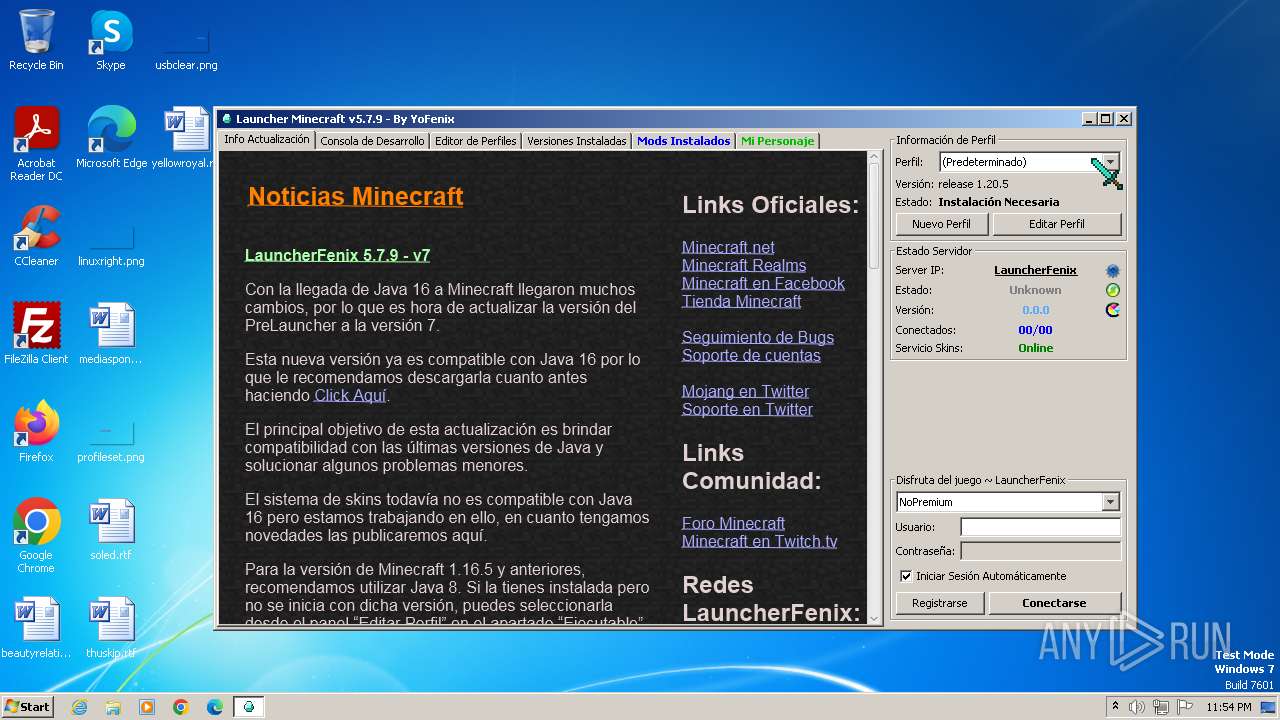
| CompanyName: | FenixProjects |
| FileDescription: | Minecraft Launcher |
| FileVersion: | 7.0.0.1 |
| InternalName: | PreLauncherv7 |
| LegalCopyright: | © Fenix Projects |
| LegalTrademarks: | - |
| OriginalFileName: | LauncherFenix Minecraft.exe |
| ProductName: | LauncherFenix |
| ProductVersion: | 7.0.0.1 |
Total processes
36
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
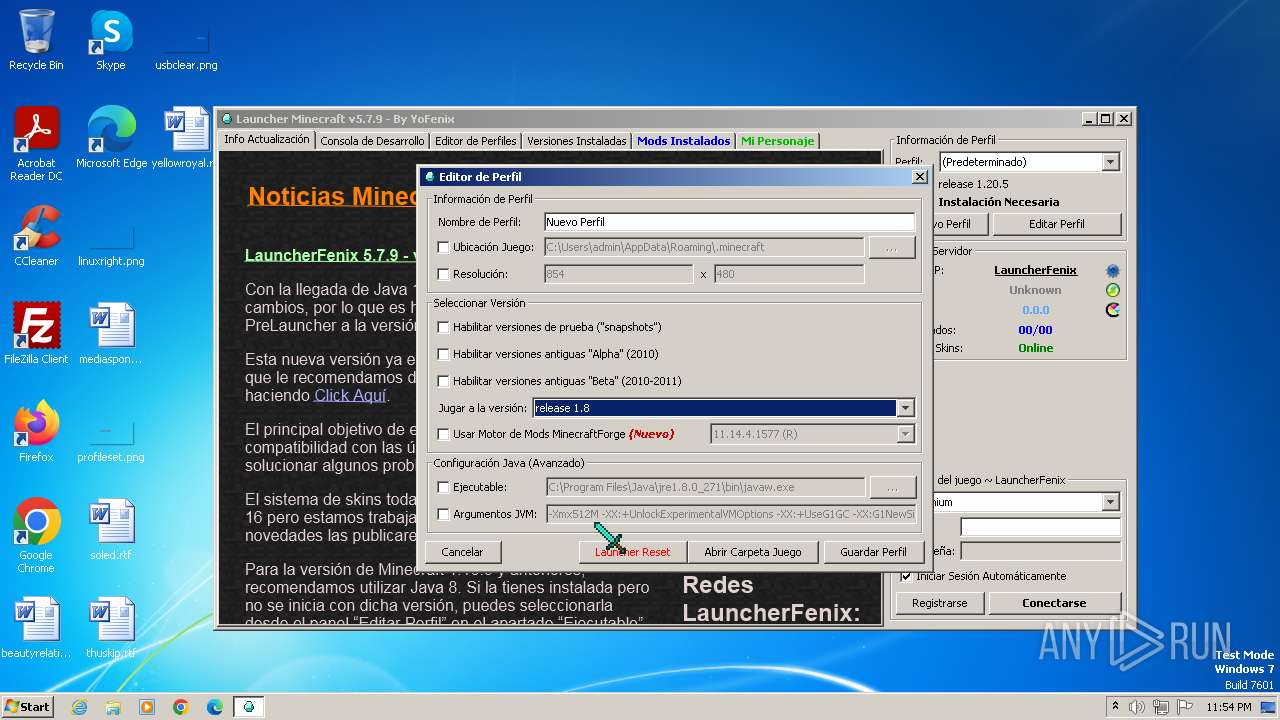
| 752 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\AppData\Local\Temp\LauncherFenix-Minecraft-v7.exe" | C:\Users\admin\AppData\Local\Temp\LauncherFenix-Minecraft-v7.exe | — | explorer.exe | |||||||||||
User: admin Company: FenixProjects Integrity Level: MEDIUM Description: Minecraft Launcher Exit code: 259 Version: 7.0.0.1 Modules
| |||||||||||||||
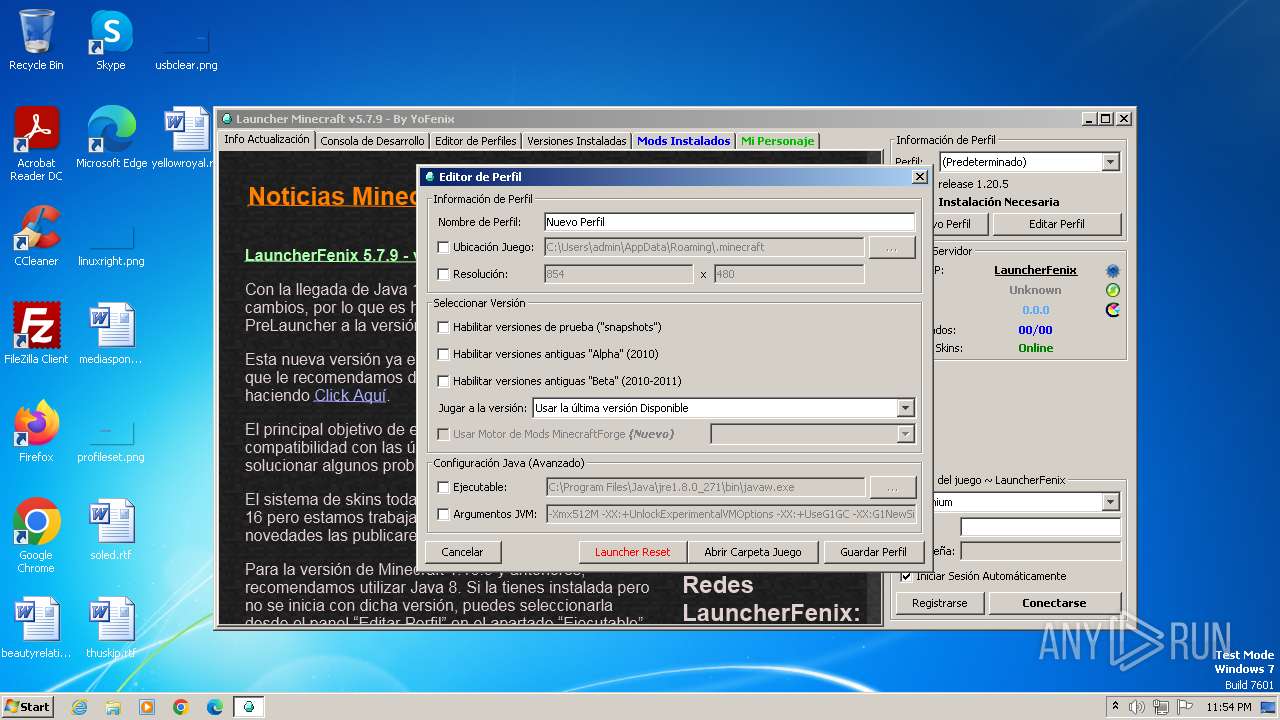
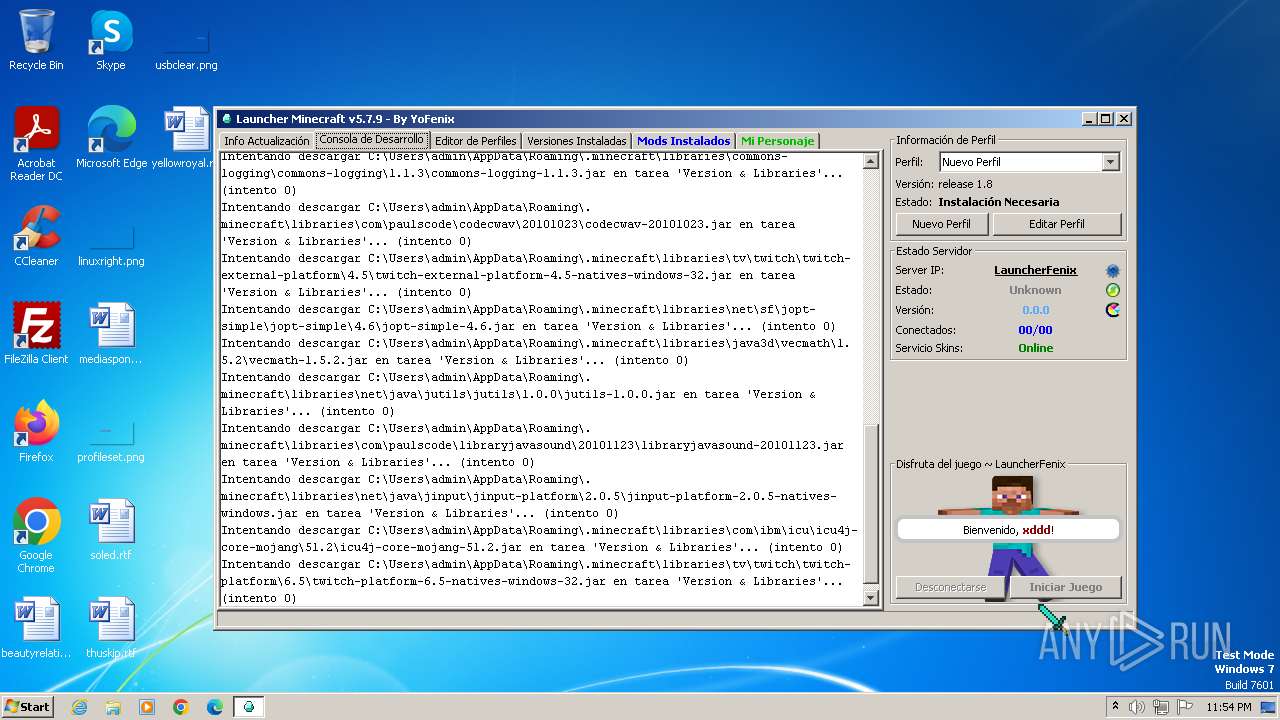
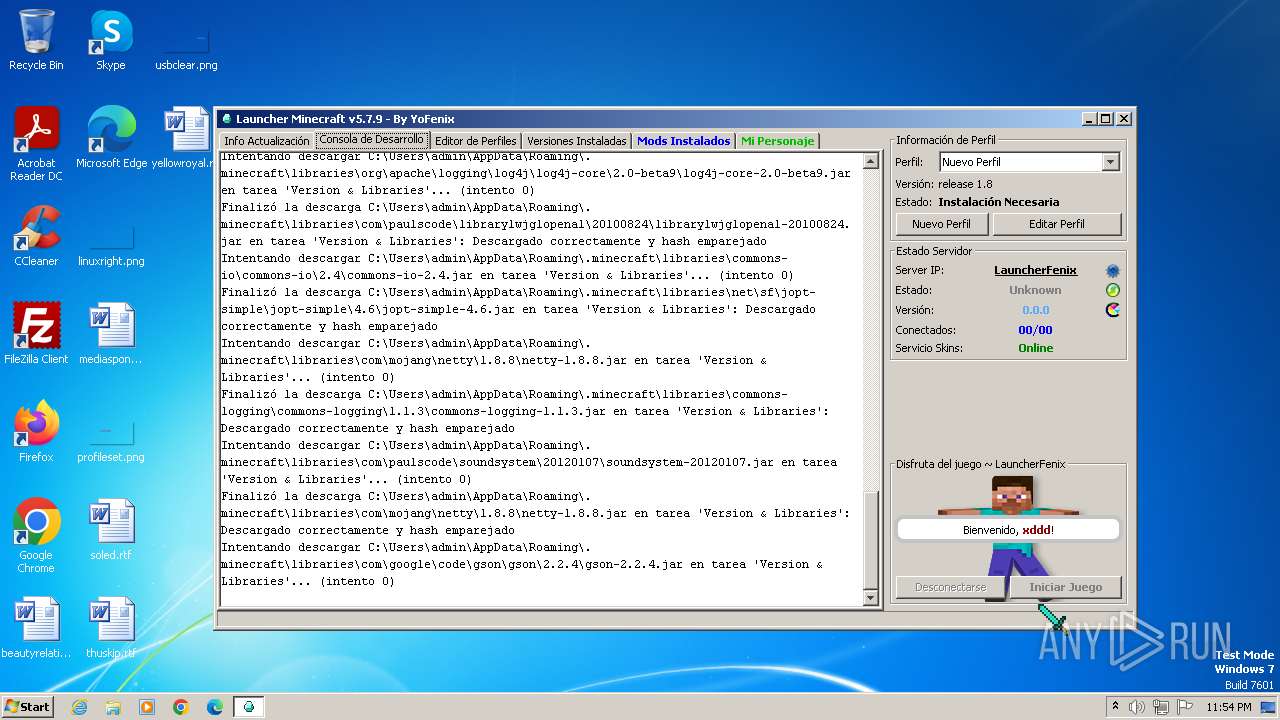
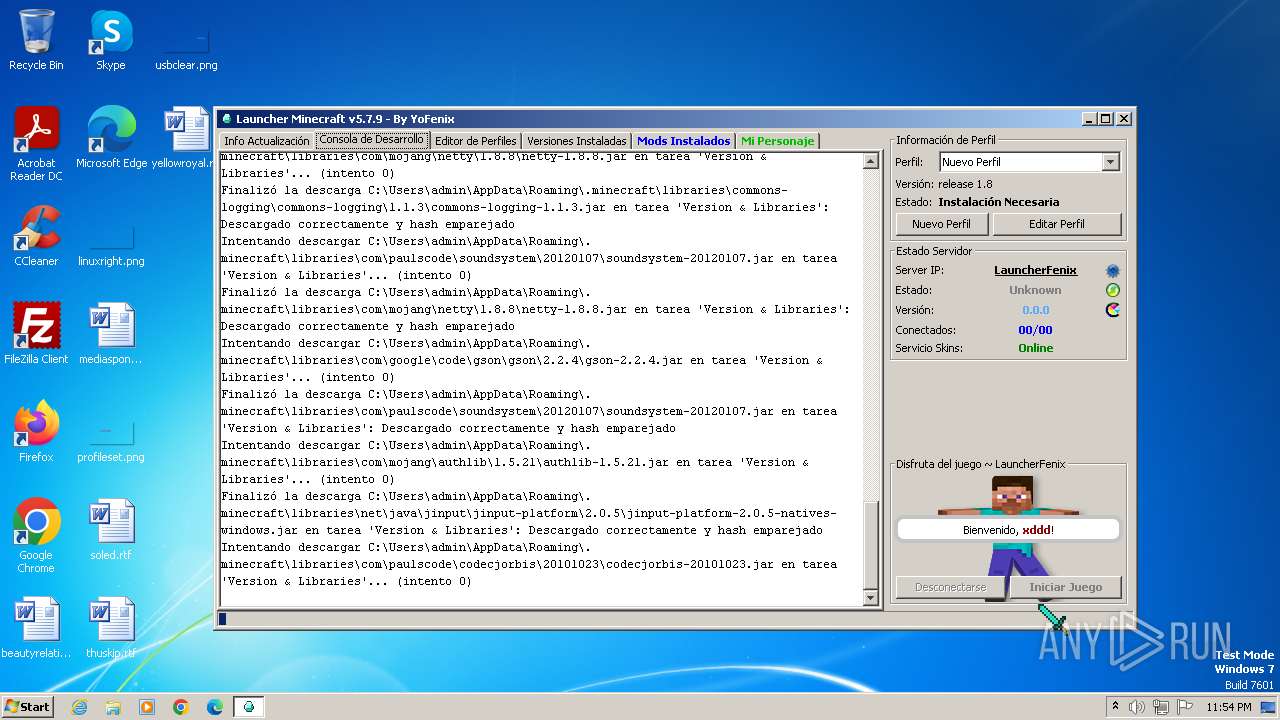
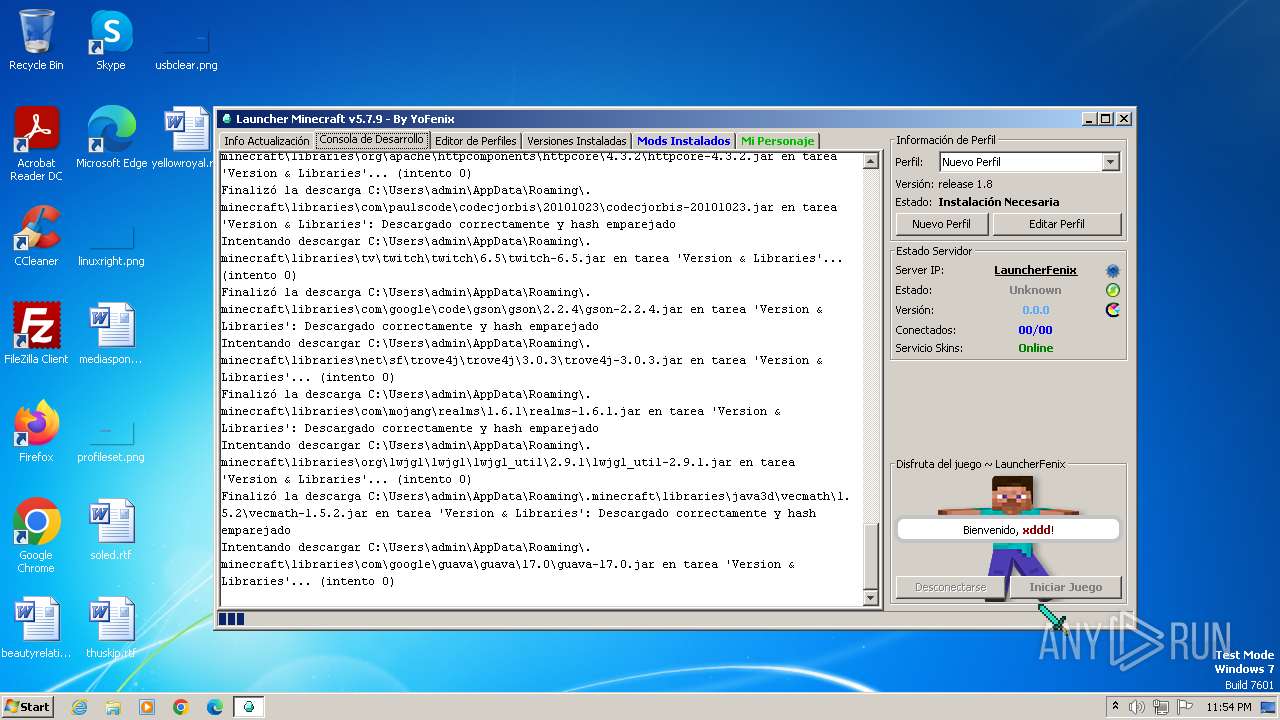
| 3984 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\LauncherFenix-Minecraft-v7.exe" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | LauncherFenix-Minecraft-v7.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Version: 8.0.2710.9 Modules
| |||||||||||||||
| 4024 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 310
Read events
1 308
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3984) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
7
Suspicious files
32
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcherfenix.lzma | binary | |
MD5:8797CC848D15E715E1C2383DD2980B44 | SHA256:E55755FE4BEAF8BC726E7F10D525817A76051B6A29A9E828B9D2E8035B953D7B | |||
| 3984 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcherfenix.lzma.new | binary | |
MD5:8797CC848D15E715E1C2383DD2980B44 | SHA256:E55755FE4BEAF8BC726E7F10D525817A76051B6A29A9E828B9D2E8035B953D7B | |||
| 3984 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio2510378066016491433.tmp | image | |
MD5:2CA5B74339059672FBB666B5404E7B42 | SHA256:D2BC07BB8C7687D1353A103208657A81566E402A0463EDE94E12BE157FE3ADEA | |||
| 3984 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher_profiles.json | binary | |
MD5:D003E058680A309B05DCDE878E30B01A | SHA256:5E591F4C8DB56B55D71FB9216801E6C51CB51E728F93CF5145E0CDFB9499D196 | |||
| 3984 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:6324974991BBCD2259F42753644AB52B | SHA256:8DA025C4308ACA8318D14F19D6E1E9E0E629C6C1B2C9BA9B27A89B7E9CD64EC9 | |||
| 3984 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+~JF8830166198247548141.tmp | ttf | |
MD5:1963698109C9563DA49B072DED6C1BD9 | SHA256:314F1C8BE13A733603C72C1F852A2E1E597473E30413246137A13E76EA46267D | |||
| 3984 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcherfenix.jar | compressed | |
MD5:84591CF8BBE4B94D5A83B2CDD605D4B5 | SHA256:B8C2BF47CB70A77582C302284554ECD4A29F9EE55C09FC2193B3BA942D5884AE | |||
| 3984 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\sf\jopt-simple\jopt-simple\4.6\jopt-simple-4.6.jar | compressed | |
MD5:13560A58A79B46B82057686543E8D727 | SHA256:3FCFBE3203C2EA521BF7640484FD35D6303186EA2E08E72F032D640CA067FFDA | |||
| 3984 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\java\jutils\jutils\1.0.0\jutils-1.0.0.jar | compressed | |
MD5:F60976B19661C849C5C87433045A9885 | SHA256:C3334FF39CF0AB3B54925619101054C90098B7C733B1E7834C7B75E4C41E84A5 | |||
| 3984 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\commons-logging\commons-logging\1.1.3\commons-logging-1.1.3.jar | compressed | |
MD5:92EB5AABC1B47287DE53D45C086A435C | SHA256:70903F6FC82E9908C8DA9F20443F61D90F0870A312642991FE8462A0B9391784 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2 059
TCP/UDP connections
2 080
DNS requests
14
Threats
3
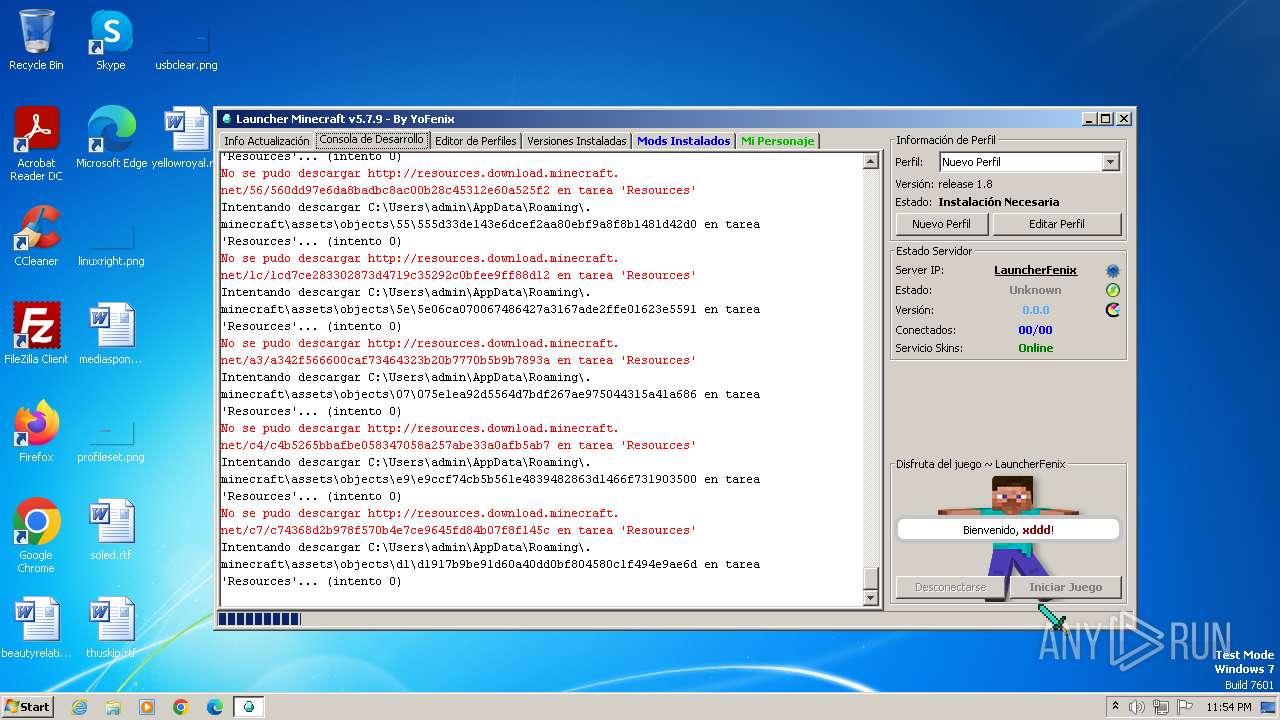
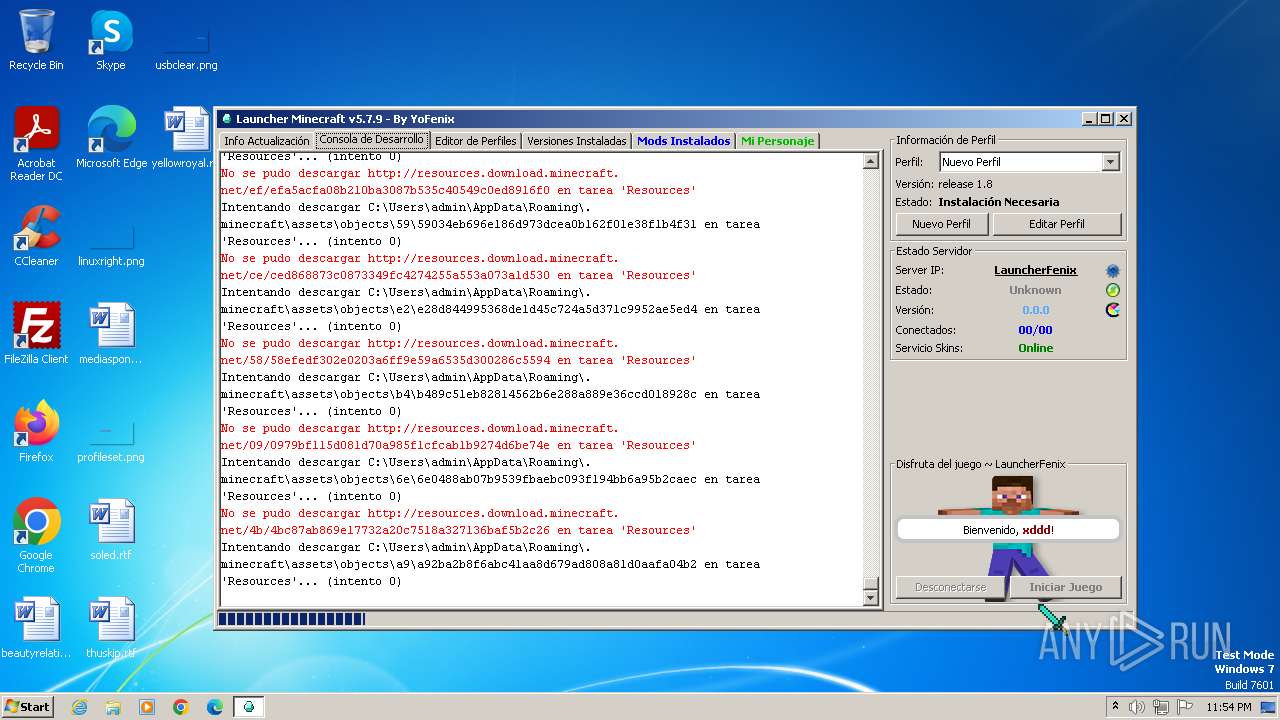
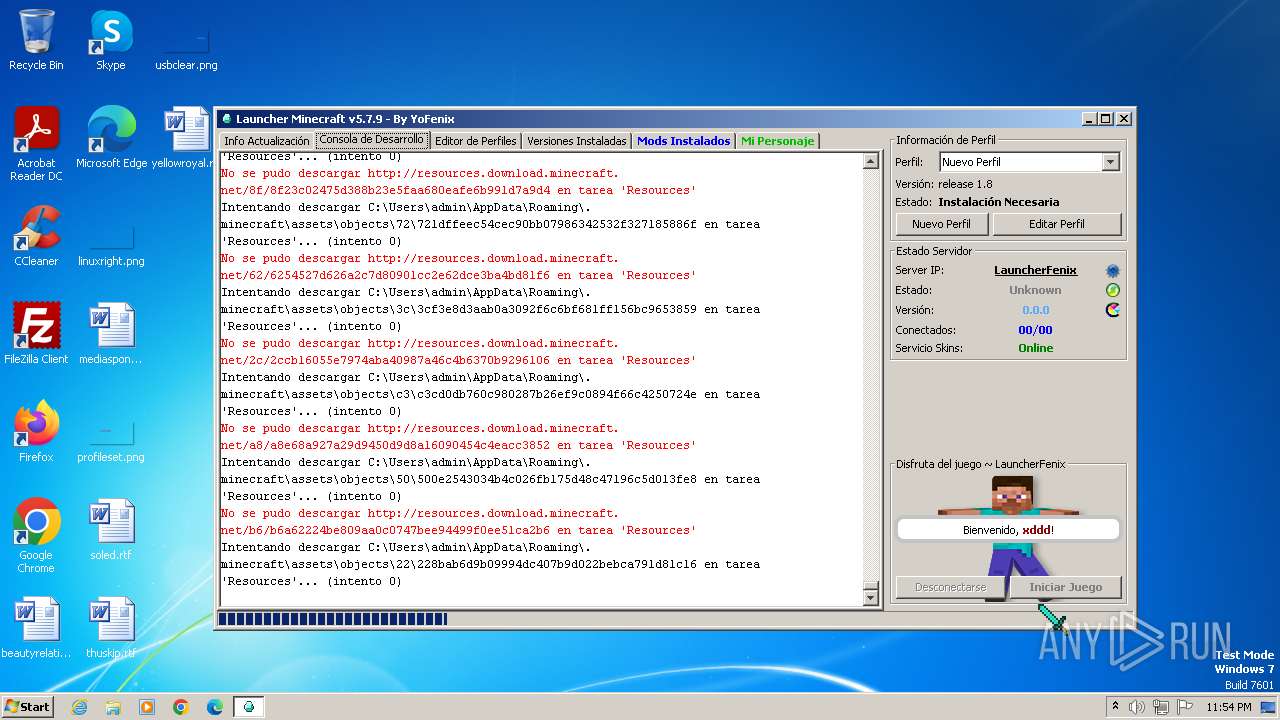
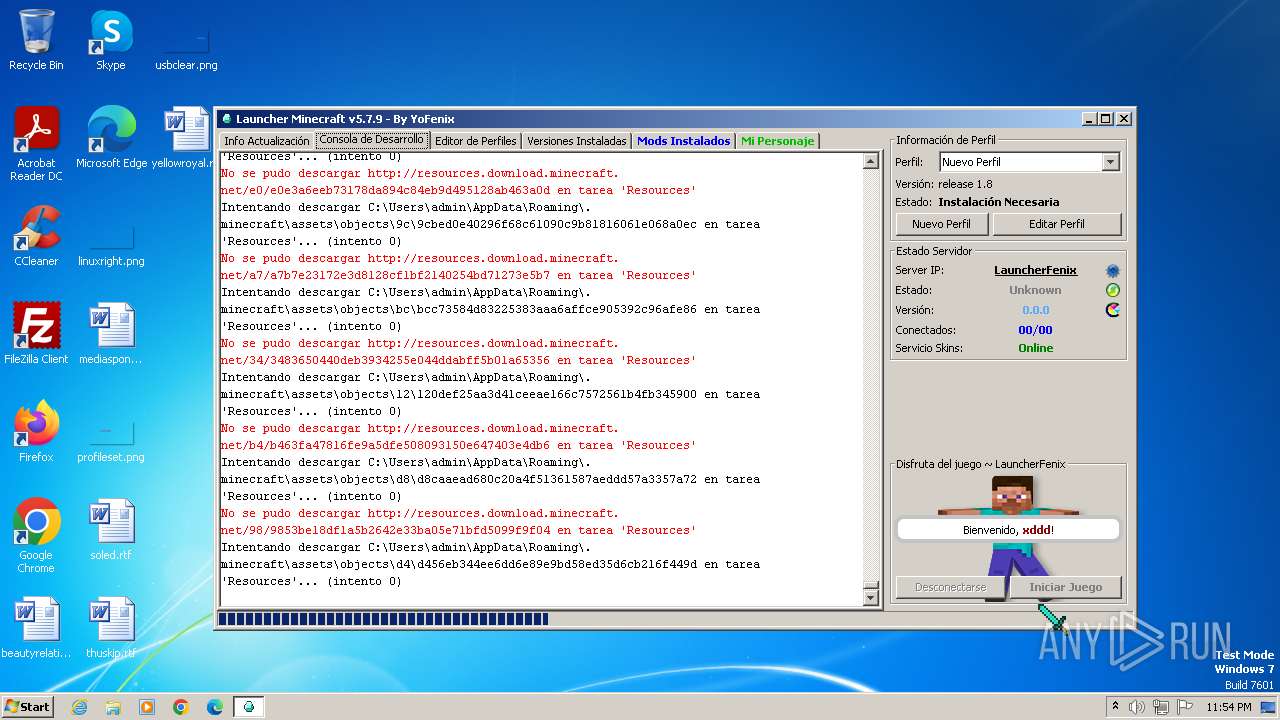
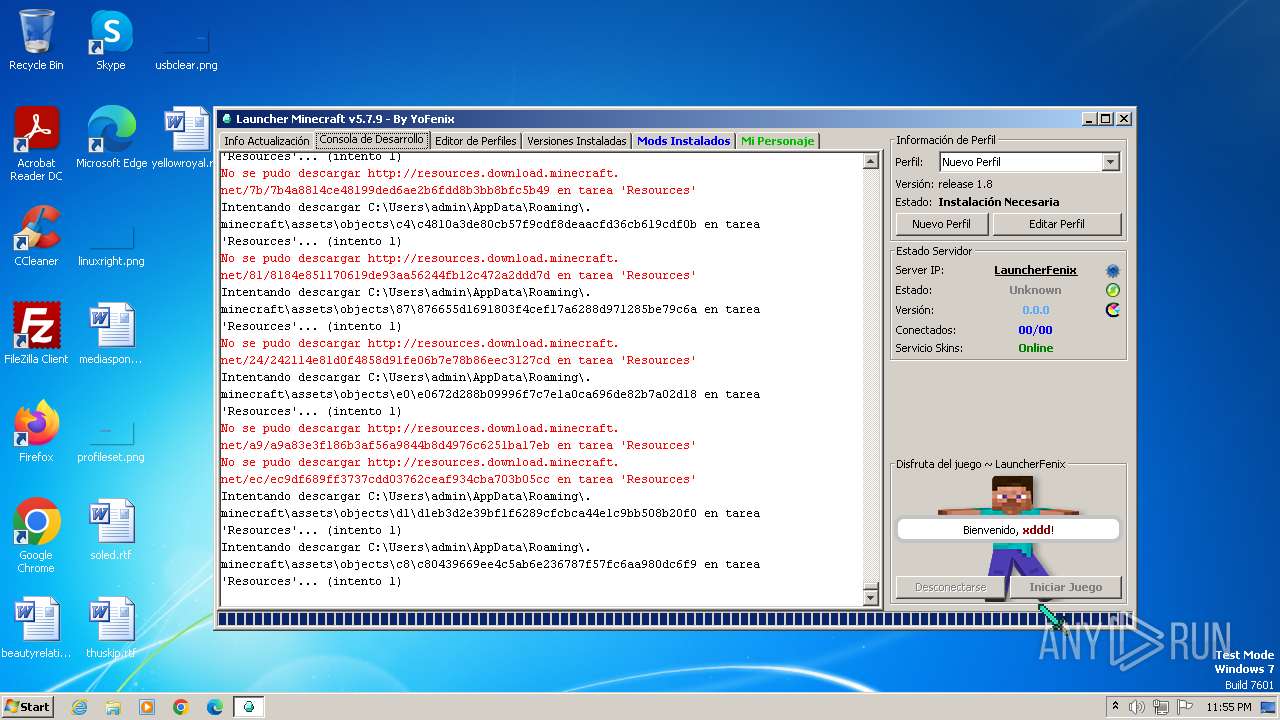
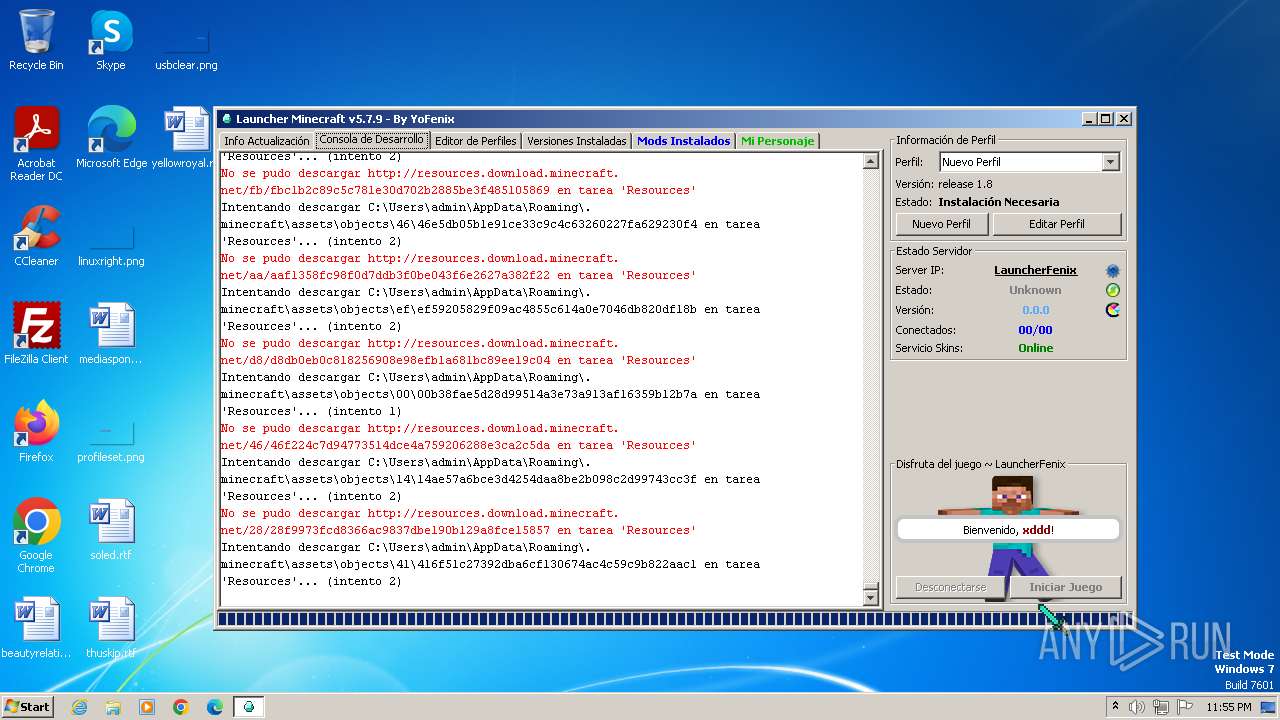
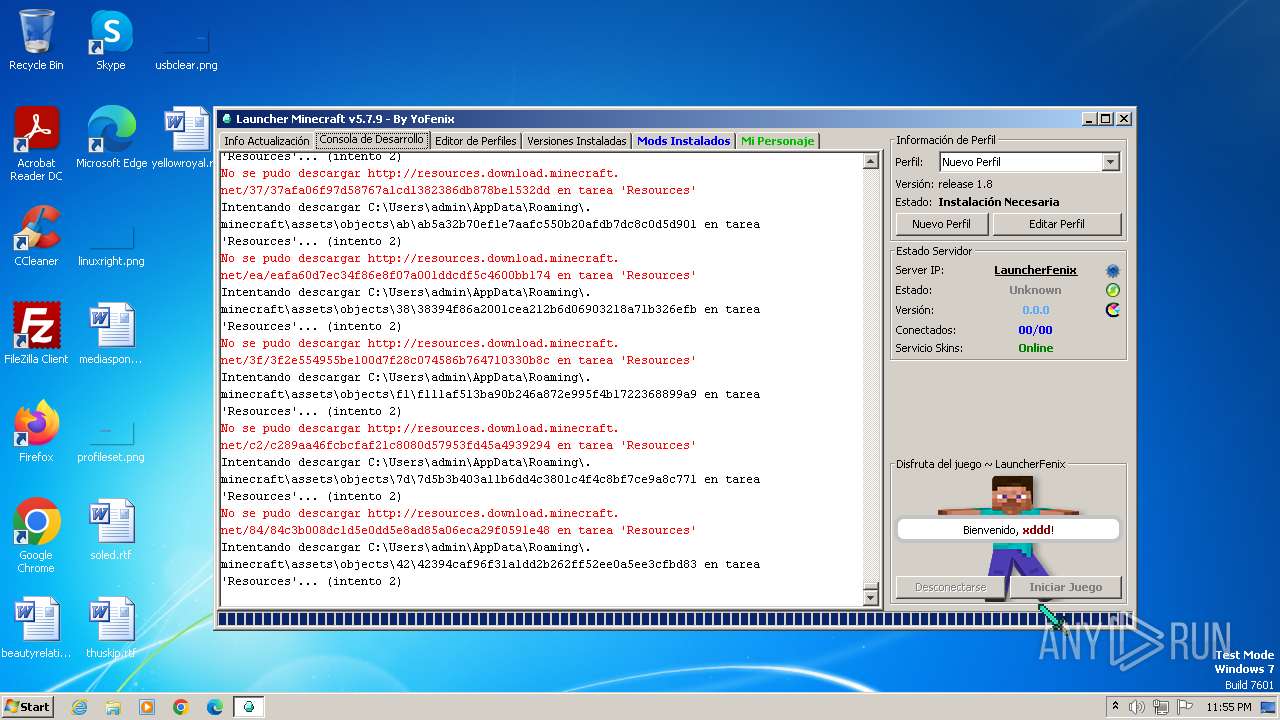
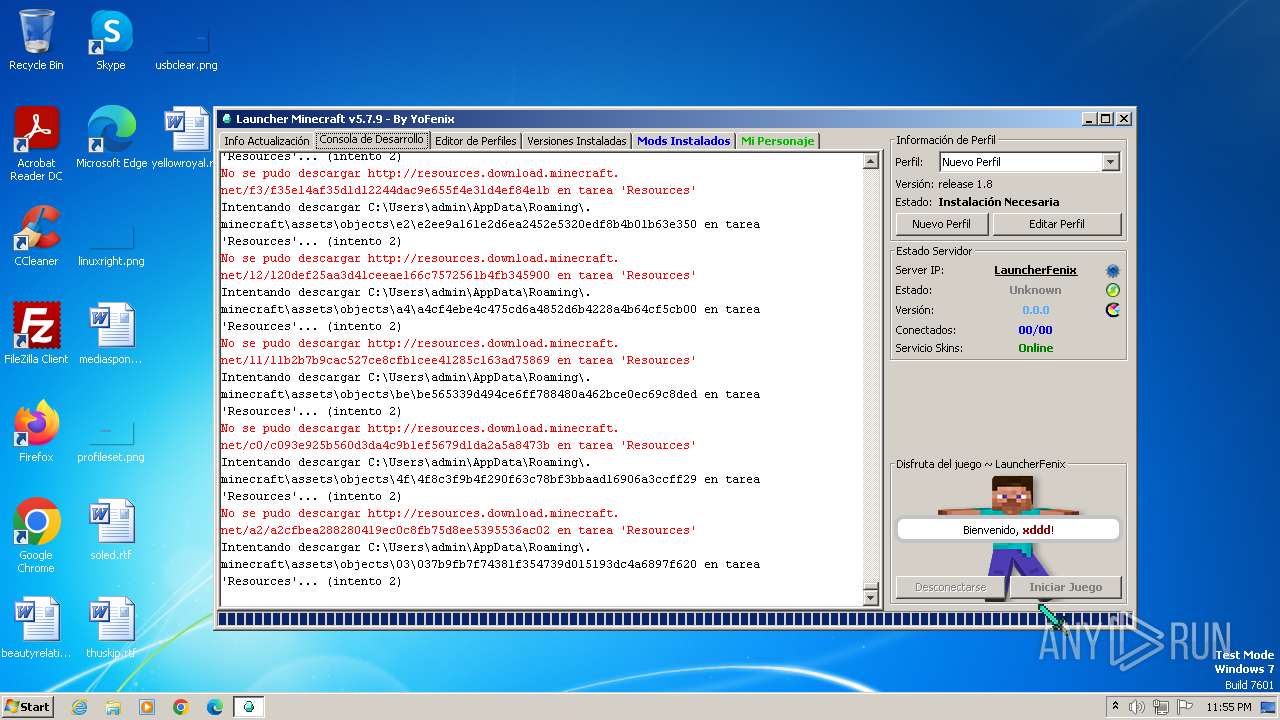
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
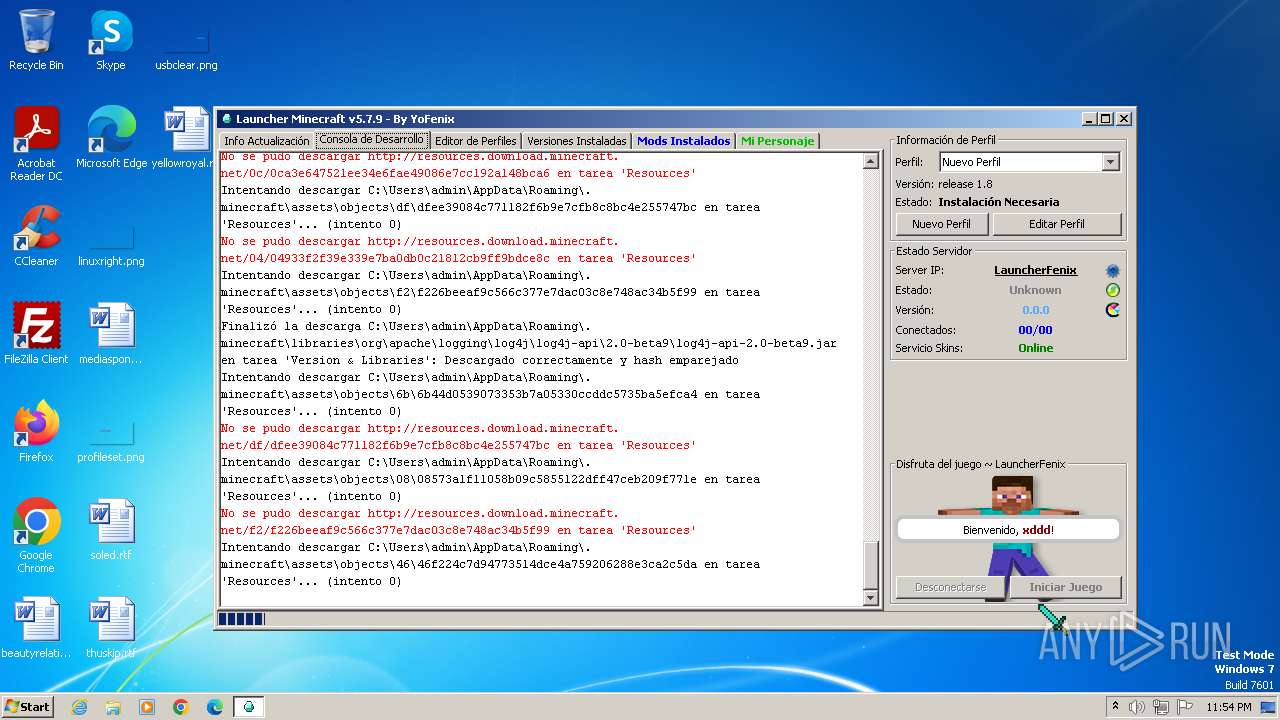
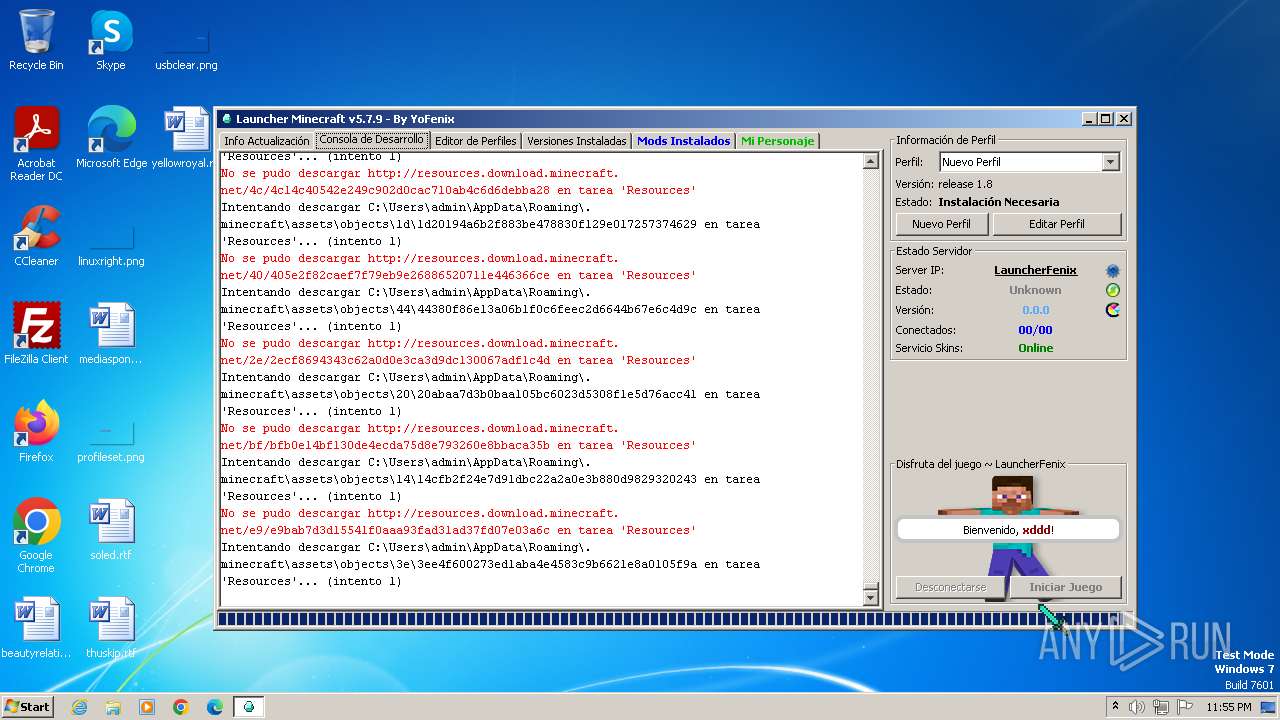
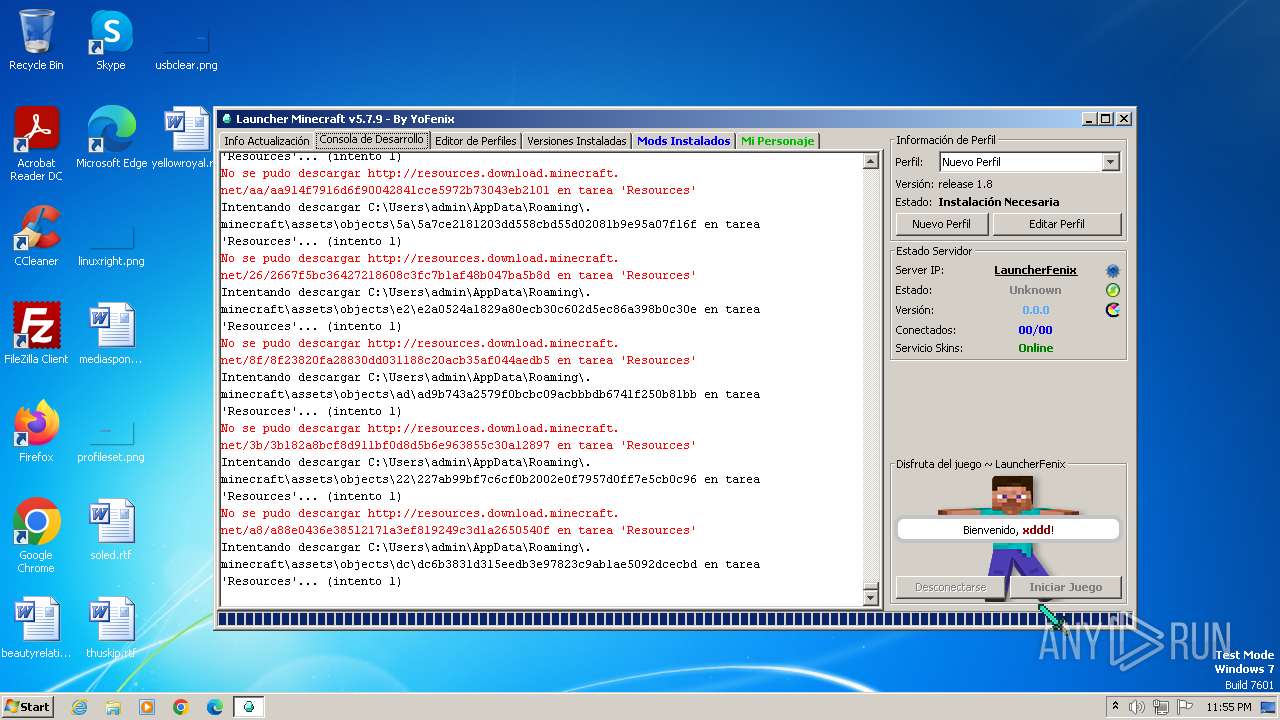
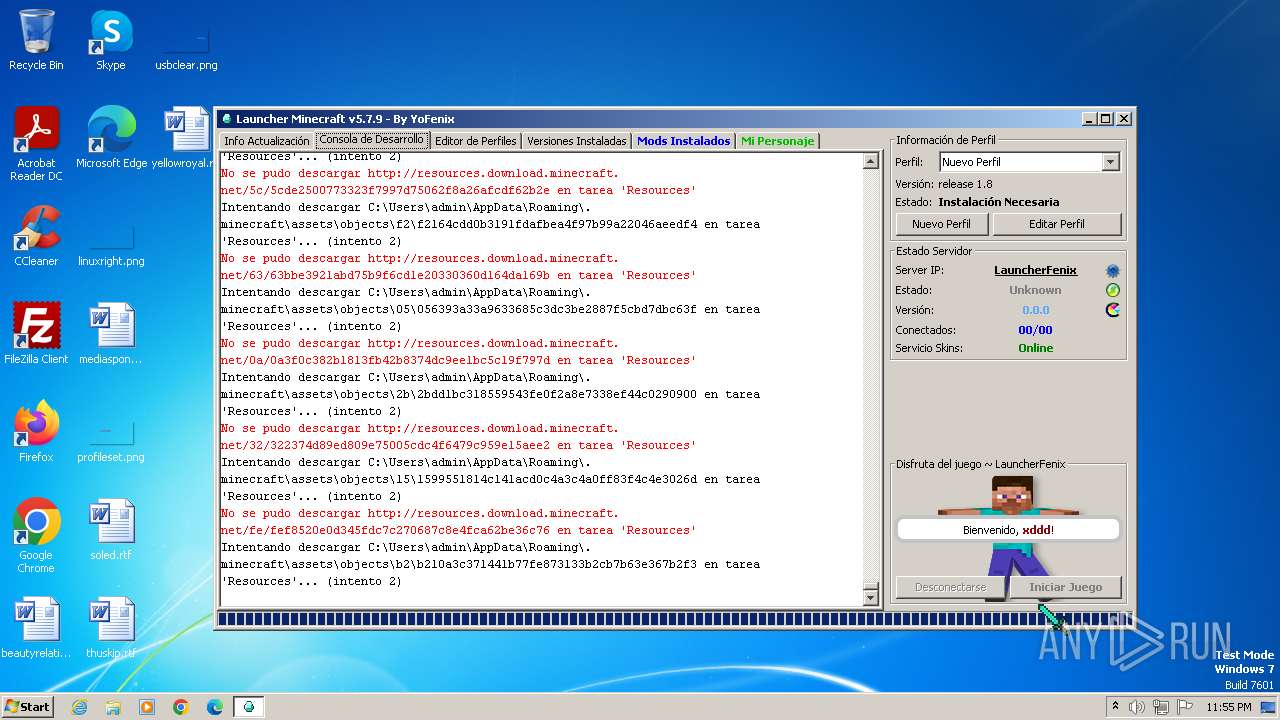
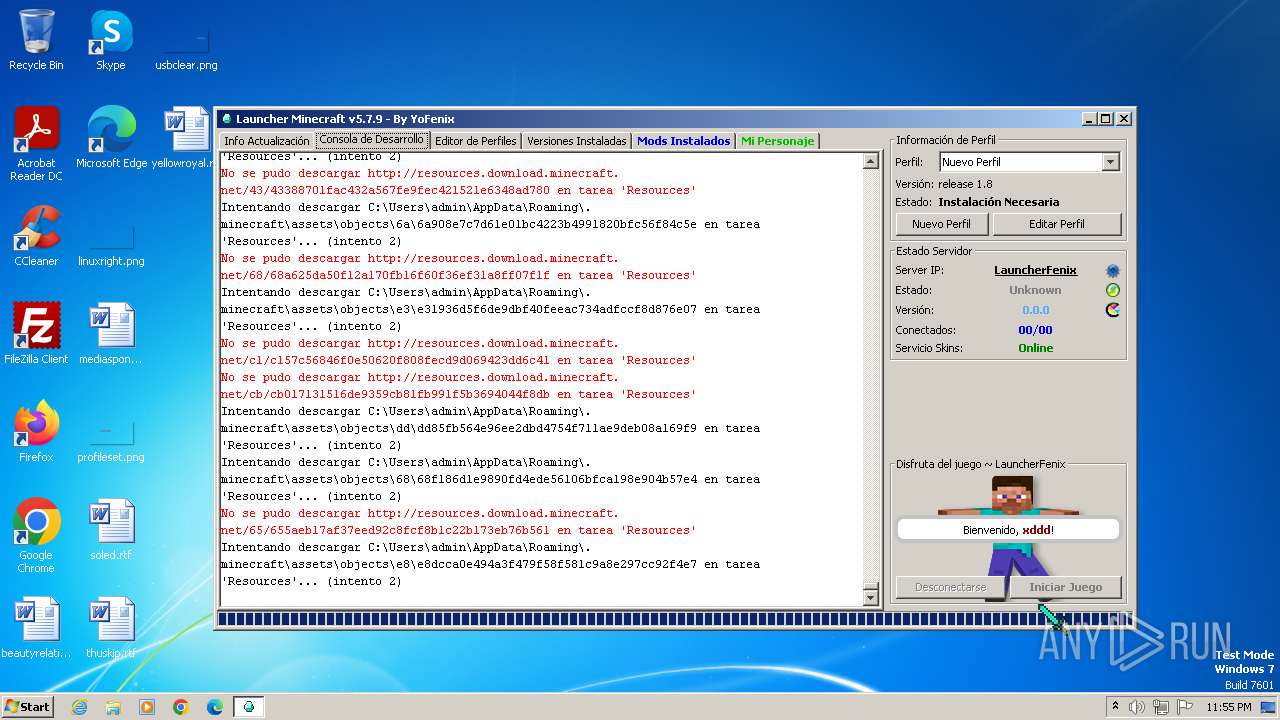
3984 | javaw.exe | GET | 302 | 74.114.154.18:80 | http://iniciolauncherfx.tumblr.com/ | US | — | — | unknown |
3984 | javaw.exe | GET | 400 | 13.107.246.45:80 | http://resources.download.minecraft.net/b9/b9c60e807ba770e8c4a2b1bae81d51813dc64b6c | US | xml | 289 b | unknown |
3984 | javaw.exe | GET | 200 | 104.21.72.175:80 | http://mc.launcherfenix.com.ar/modsloader/mcforge/version_manifest.json | unknown | binary | 3.33 Kb | unknown |
3984 | javaw.exe | GET | 400 | 13.107.246.45:80 | http://resources.download.minecraft.net/a1/a116e396d95a0ee245000dd4cdcc333d38ea9e3b | US | xml | 289 b | unknown |
3984 | javaw.exe | GET | 200 | 104.21.72.175:80 | http://mc.launcherfenix.com.ar/modsloader/mcforge/1.8/1.8.json | unknown | binary | 2.25 Kb | unknown |
3984 | javaw.exe | GET | 400 | 13.107.246.45:80 | http://resources.download.minecraft.net/28/281b87984ddf8e94324bc86911a36c971cb3d831 | US | xml | 289 b | unknown |
3984 | javaw.exe | GET | 400 | 13.107.246.45:80 | http://resources.download.minecraft.net/0c/0ca3e647521ee34e6fae49086e7cc192a148bca6 | US | xml | 289 b | unknown |
3984 | javaw.exe | GET | 400 | 13.107.246.45:80 | http://resources.download.minecraft.net/04/04933f2f39e339e7ba0db0c21812cb9ff9bdce8c | US | xml | 289 b | unknown |
3984 | javaw.exe | GET | 400 | 13.107.246.45:80 | http://resources.download.minecraft.net/df/dfee39084c771182f6b9e7cfb8c8bc4e255747bc | US | xml | 289 b | unknown |
3984 | javaw.exe | GET | 400 | 13.107.246.45:80 | http://resources.download.minecraft.net/f2/f226beeaf9c566c377e7dac03c8e748ac34b5f99 | US | xml | 289 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3984 | javaw.exe | 162.125.66.18:443 | www.dropbox.com | DROPBOX | DE | unknown |
3984 | javaw.exe | 162.125.66.15:443 | ucbe74f331dc0f0f49b05dfe4ccd.dl.dropboxusercontent.com | DROPBOX | DE | malicious |
3984 | javaw.exe | 13.107.246.45:443 | launchermeta.mojang.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3984 | javaw.exe | 104.21.72.175:80 | profile.launcherfenix.com.ar | CLOUDFLARENET | — | unknown |
3984 | javaw.exe | 74.114.154.18:80 | iniciolauncherfx.tumblr.com | AUTOMATTIC | US | unknown |
3984 | javaw.exe | 74.114.154.18:443 | iniciolauncherfx.tumblr.com | AUTOMATTIC | US | unknown |
3984 | javaw.exe | 192.0.77.40:443 | assets.tumblr.com | AUTOMATTIC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dropbox.com |
| shared |
ucbe74f331dc0f0f49b05dfe4ccd.dl.dropboxusercontent.com |
| unknown |
uca4d08d3bf005597950edc6bf84.dl.dropboxusercontent.com |
| unknown |
launchermeta.mojang.com |
| whitelisted |
profile.launcherfenix.com.ar |
| unknown |
iniciolauncherfx.tumblr.com |
| unknown |
mc.launcherfenix.com.ar |
| unknown |
assets.tumblr.com |
| whitelisted |
px.srvcs.tumblr.com |
| whitelisted |
static.tumblr.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3984 | javaw.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
— | — | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
— | — | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |