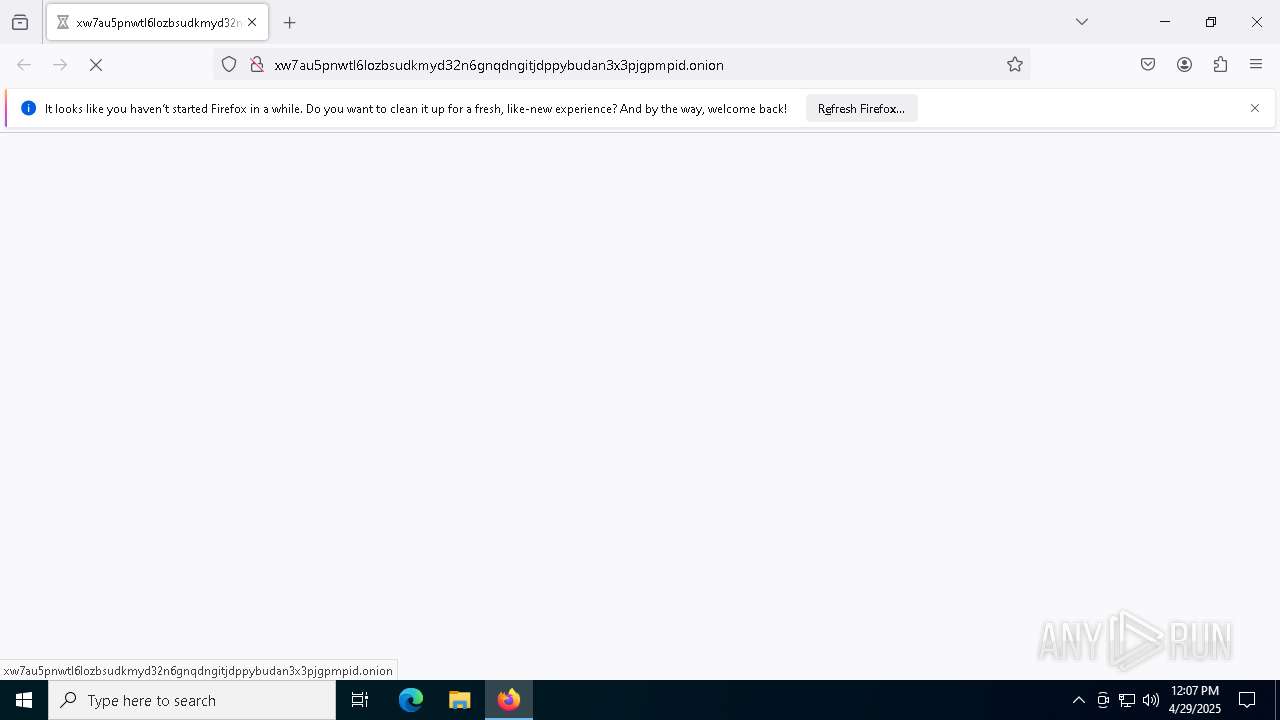
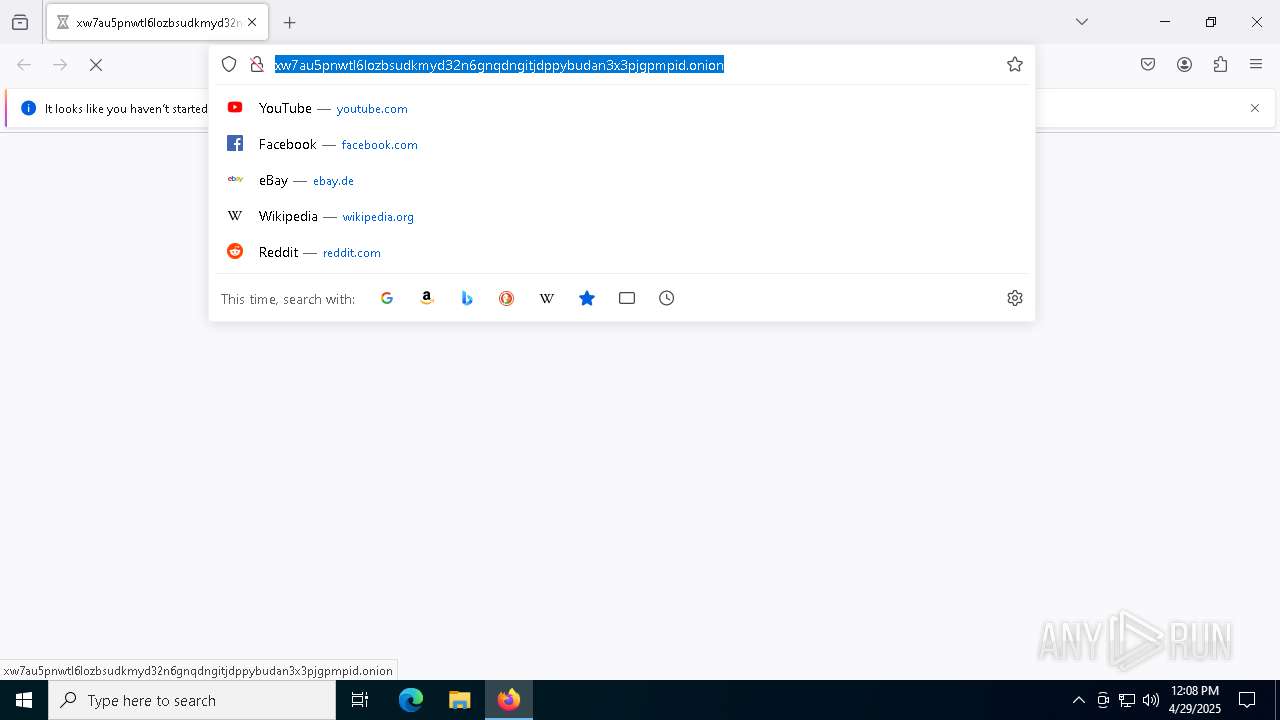
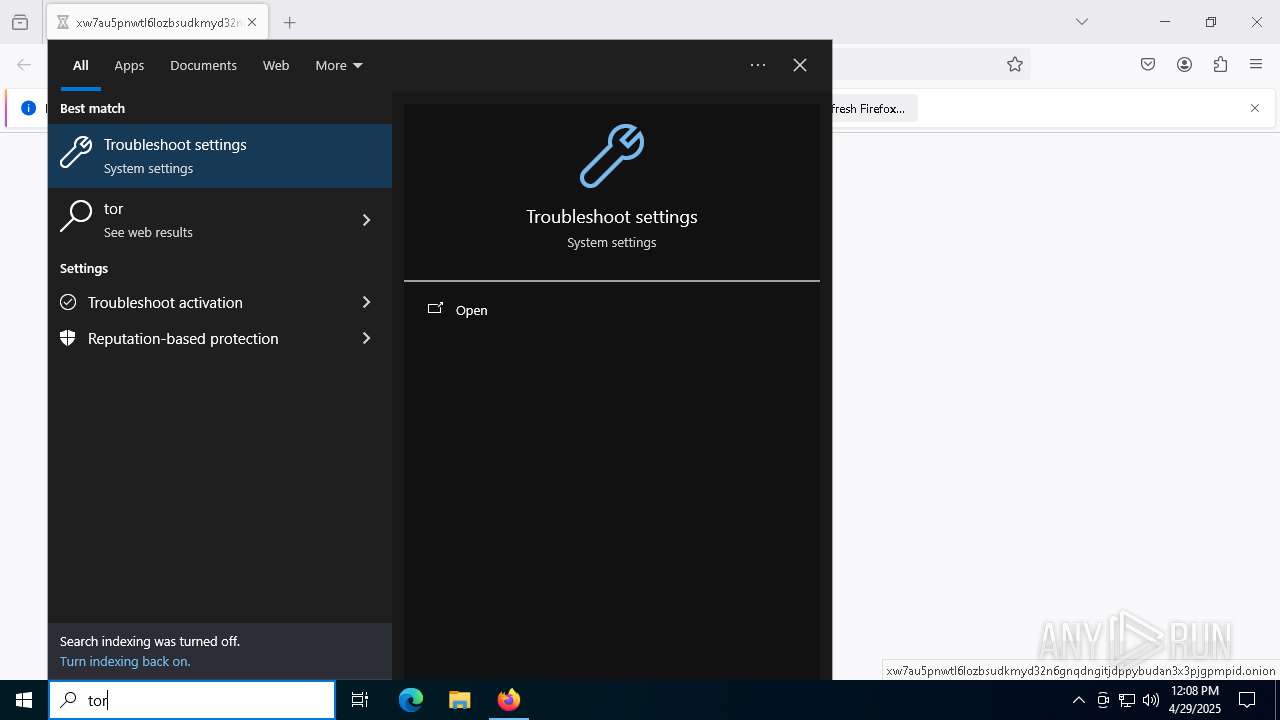
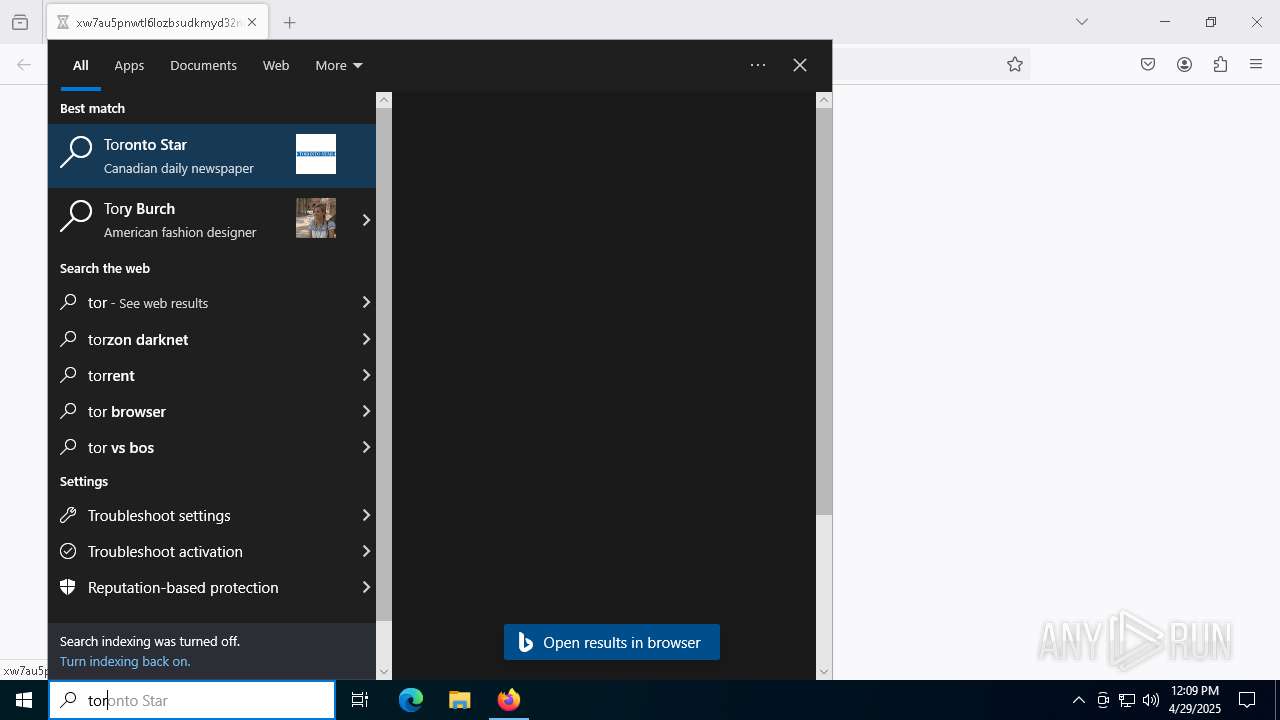
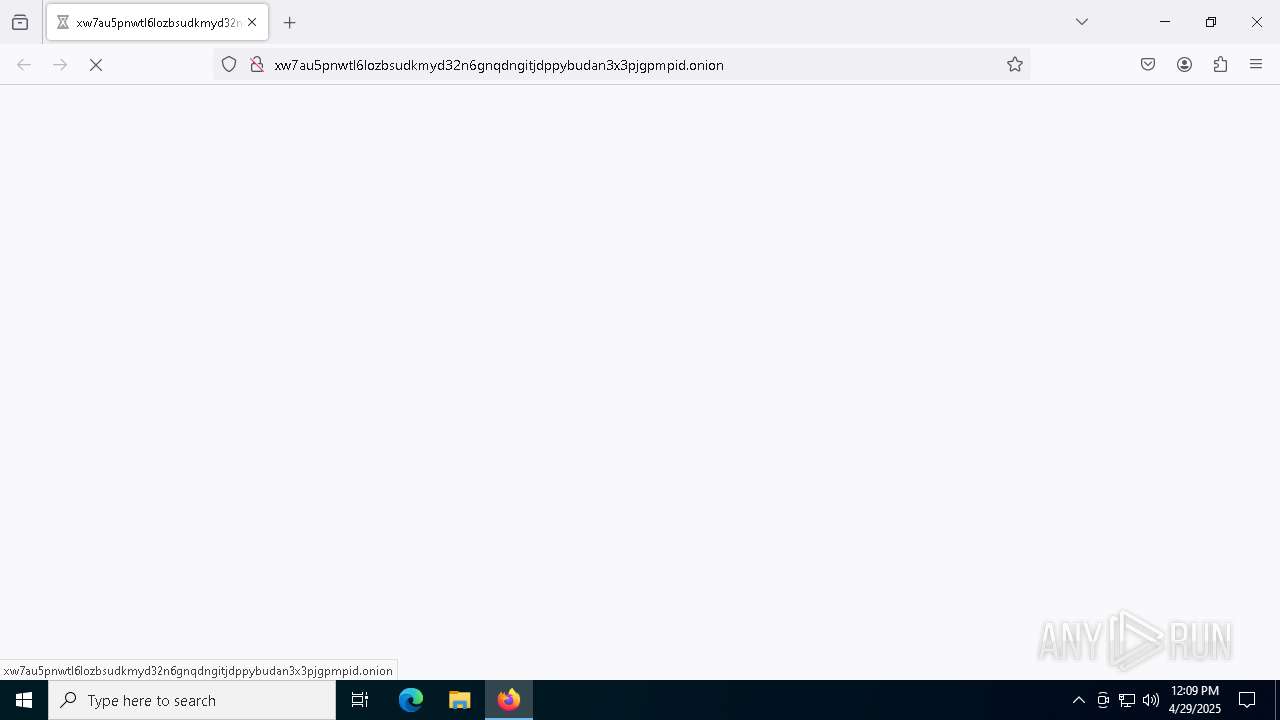
| URL: | http://xw7au5pnwtl6lozbsudkmyd32n6gnqdngitjdppybudan3x3pjgpmpid.onion |
| Full analysis: | https://app.any.run/tasks/9a5f16de-aeb3-4be9-b7fd-60b6a0b08d70 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 12:07:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | D08BC66D4E372807949630627A999D38 |
| SHA1: | 25D499484966D19C478C8599F842BE975922E126 |
| SHA256: | 1222A4E02103DDA0E4A9335AB7A5C79306B22E3D0B816FB912A47B788076A560 |
| SSDEEP: | 3:N1KGS3FVoutkGv/3yLa8CifLL:CGSFV1H/3yLaT6LL |
MALICIOUS
No malicious indicators.SUSPICIOUS
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
INFO
Application launched itself
- firefox.exe (PID: 7208)
- firefox.exe (PID: 7228)
Reads the software policy settings
- slui.exe (PID: 2108)
- slui.exe (PID: 6940)
Checks proxy server information
- slui.exe (PID: 6940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
149
Monitored processes
15
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2108 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3156 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4672 -childID 3 -isForBrowser -prefsHandle 4660 -prefMapHandle 4656 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1312 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {9e994d4f-dc48-4c6e-a93f-e84d5f7ae5db} 7228 "\\.\pipe\gecko-crash-server-pipe.7228" 1c9c1efca10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5344 -childID 6 -isForBrowser -prefsHandle 5476 -prefMapHandle 5480 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1312 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c8b85a8e-9c03-4a5a-b9b0-35c53ca16a5c} 7228 "\\.\pipe\gecko-crash-server-pipe.7228" 1c9bfeed150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4652 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5416 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5320 -childID 4 -isForBrowser -prefsHandle 5316 -prefMapHandle 5212 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1312 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {bae3ac66-0a6a-4e48-8f26-01516c37c6f3} 7228 "\\.\pipe\gecko-crash-server-pipe.7228" 1c9bba1bd90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5892 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5368 -childID 5 -isForBrowser -prefsHandle 5372 -prefMapHandle 5376 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1312 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {5d28e2f6-f691-4254-aa06-c4cd02573165} 7228 "\\.\pipe\gecko-crash-server-pipe.7228" 1c9bdfdd850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6940 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
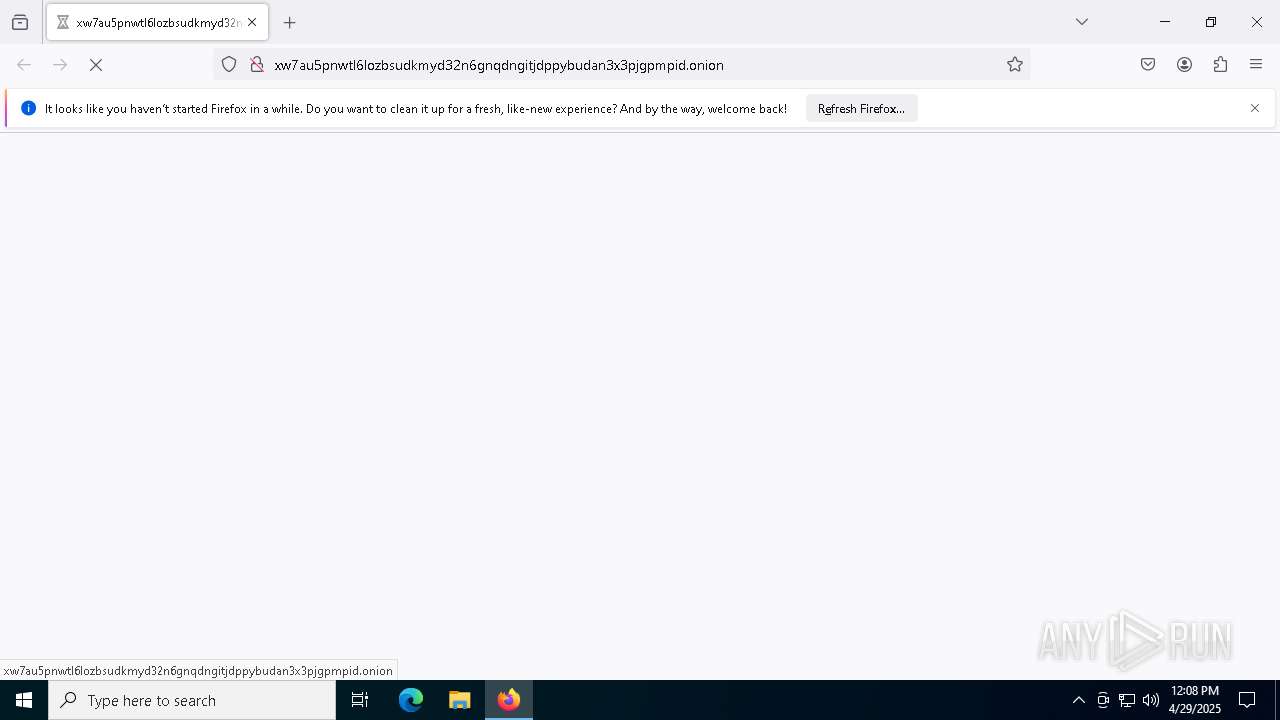
| 7208 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://xw7au5pnwtl6lozbsudkmyd32n6gnqdngitjdppybudan3x3pjgpmpid.onion" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 7228 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://xw7au5pnwtl6lozbsudkmyd32n6gnqdngitjdppybudan3x3pjgpmpid.onion | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
13 931
Read events
13 930
Write events
1
Delete events
0
Modification events
| (PID) Process: | (7228) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
Executable files
0
Suspicious files
157
Text files
28
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7228 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7228 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | dbf | |
MD5:3B156E12141F8CBCE9D60CDCE2077617 | SHA256:E6287E44B44ABEA20E1B2E3F415D22B9E5E5FBBC155AD9DADBABA63951B2AF6F | |||
| 7228 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7228 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7228 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7228 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7228 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C39086FDEB6180B99839FB157FC1FDB | SHA256:63DDB3B0C046A419F85549FF5C372FD685CFCABAFD2C8100AFCEEE99C8538861 | |||
| 7228 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7228 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7228 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
86
DNS requests
145
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4784 | RUXIMICS.exe | GET | 200 | 88.221.25.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 88.221.25.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7228 | firefox.exe | GET | — | 10.201.172.182:80 | http://xw7au5pnwtl6lozbsudkmyd32n6gnqdngitjdppybudan3x3pjgpmpid.onion/ | unknown | — | — | malicious |
4784 | RUXIMICS.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7228 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7228 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7228 | firefox.exe | POST | 200 | 88.221.25.162:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7228 | firefox.exe | POST | 200 | 88.221.25.162:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7228 | firefox.exe | POST | 200 | 84.53.175.9:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 88.221.25.177:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4784 | RUXIMICS.exe | 88.221.25.177:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | whitelisted |
4784 | RUXIMICS.exe | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7228 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7228 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
xw7au5pnwtl6lozbsudkmyd32n6gnqdngitjdppybudan3x3pjgpmpid.onion |
| malicious |
detectportal.firefox.com |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |