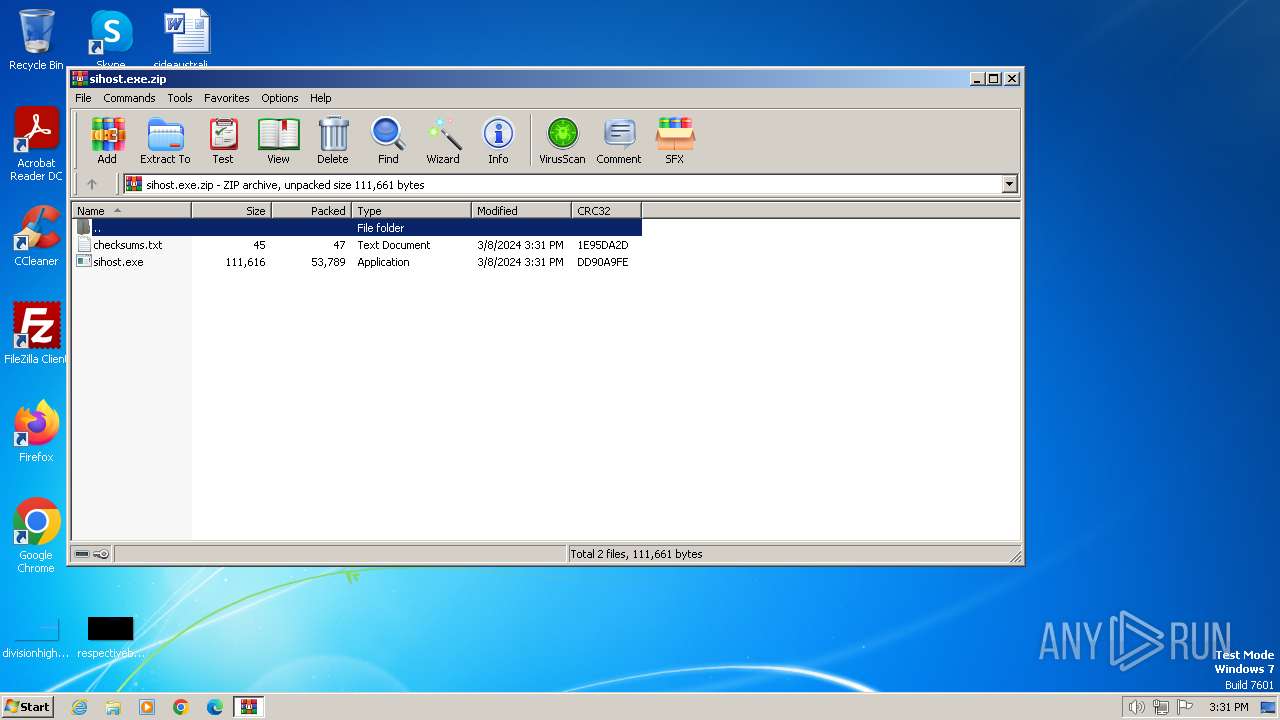
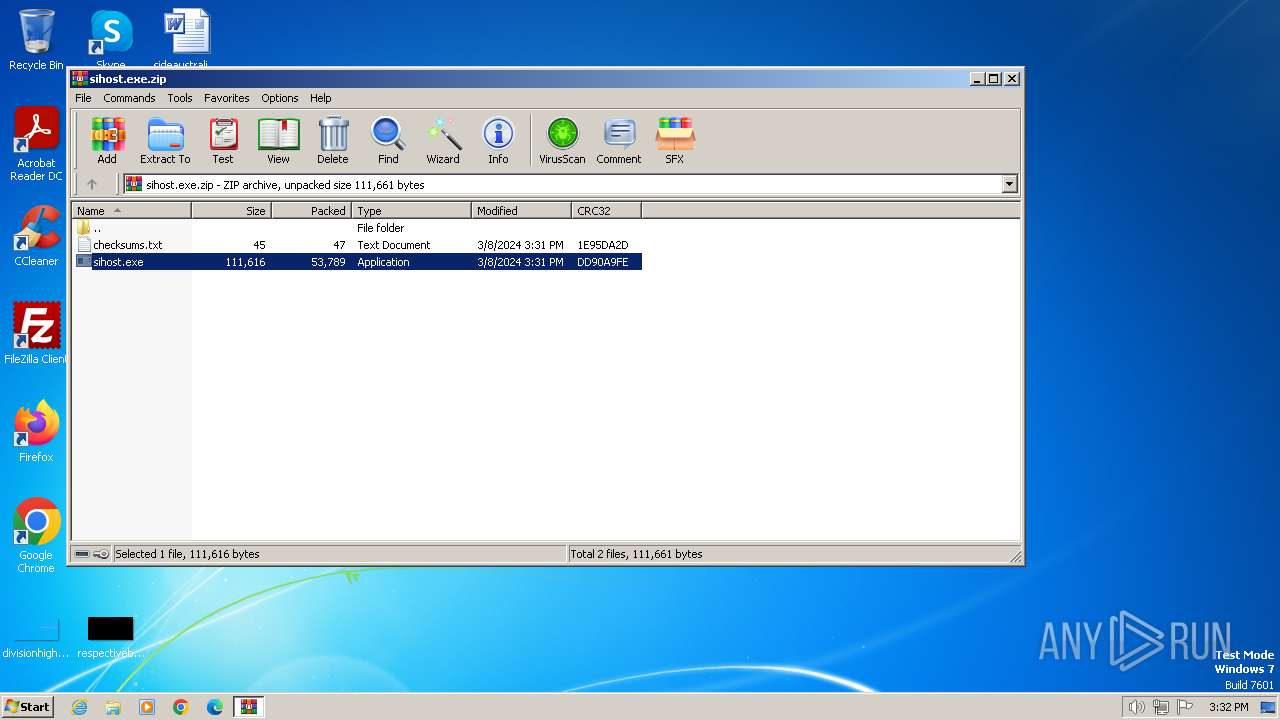
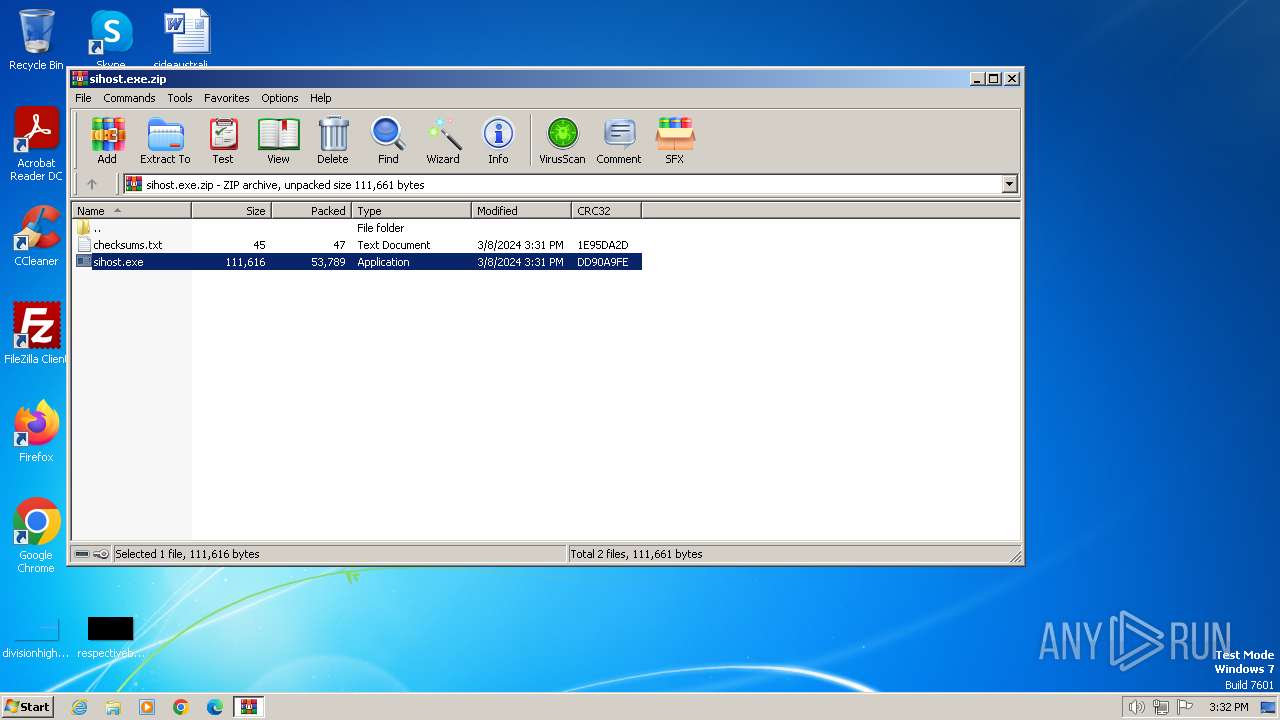
| File name: | sihost.exe.zip |
| Full analysis: | https://app.any.run/tasks/97591efd-678c-4b4a-abfc-5f8e0f957e87 |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2024, 15:31:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 32BEFCB1AEA80DE21D9838EFF871A3B8 |
| SHA1: | 40A75B24ABD81B23B1BEADA4B60A1D1FBB7BED24 |
| SHA256: | 1216C888F7FB9C3AB57B6A053C9F66ABE14AEF94FB4DE41A6BFD89B16249709C |
| SSDEEP: | 1536:vVIDKyixrsxY2BoOw4Cp/y/REcKP8/mbnYimqnxs0:vyiJIY2Be4CU/j/intmAs0 |
MALICIOUS
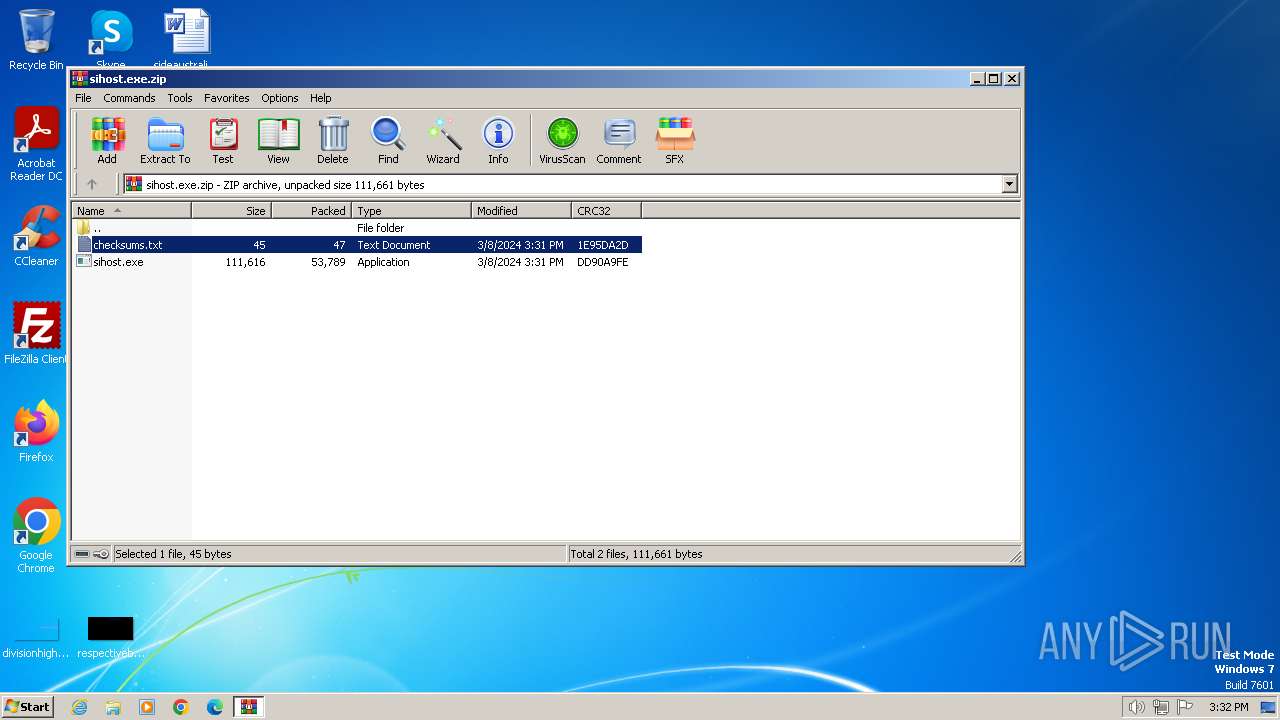
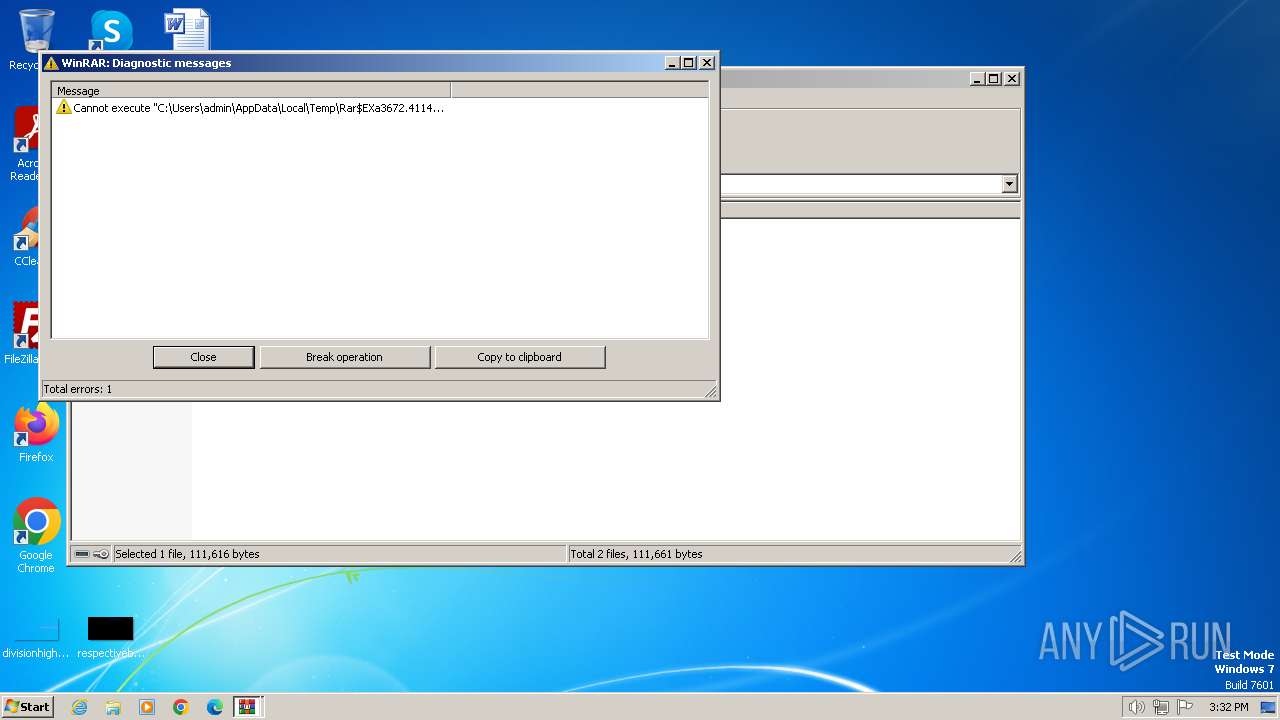
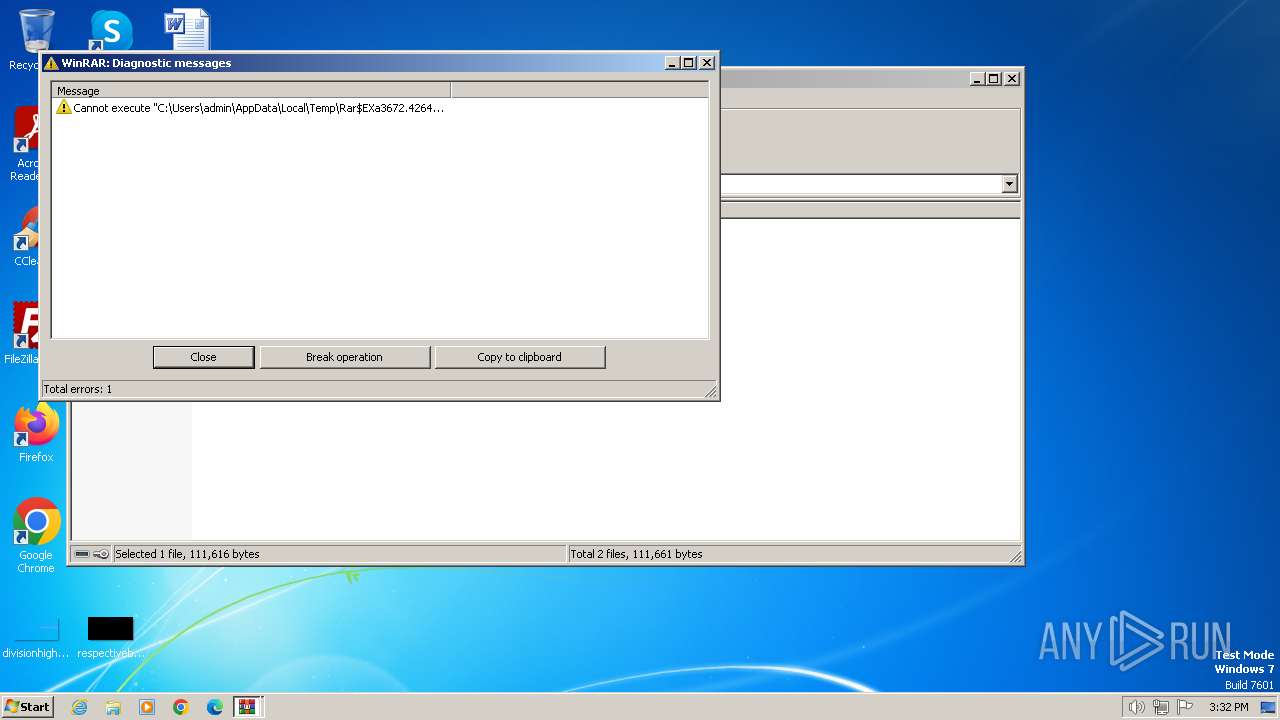
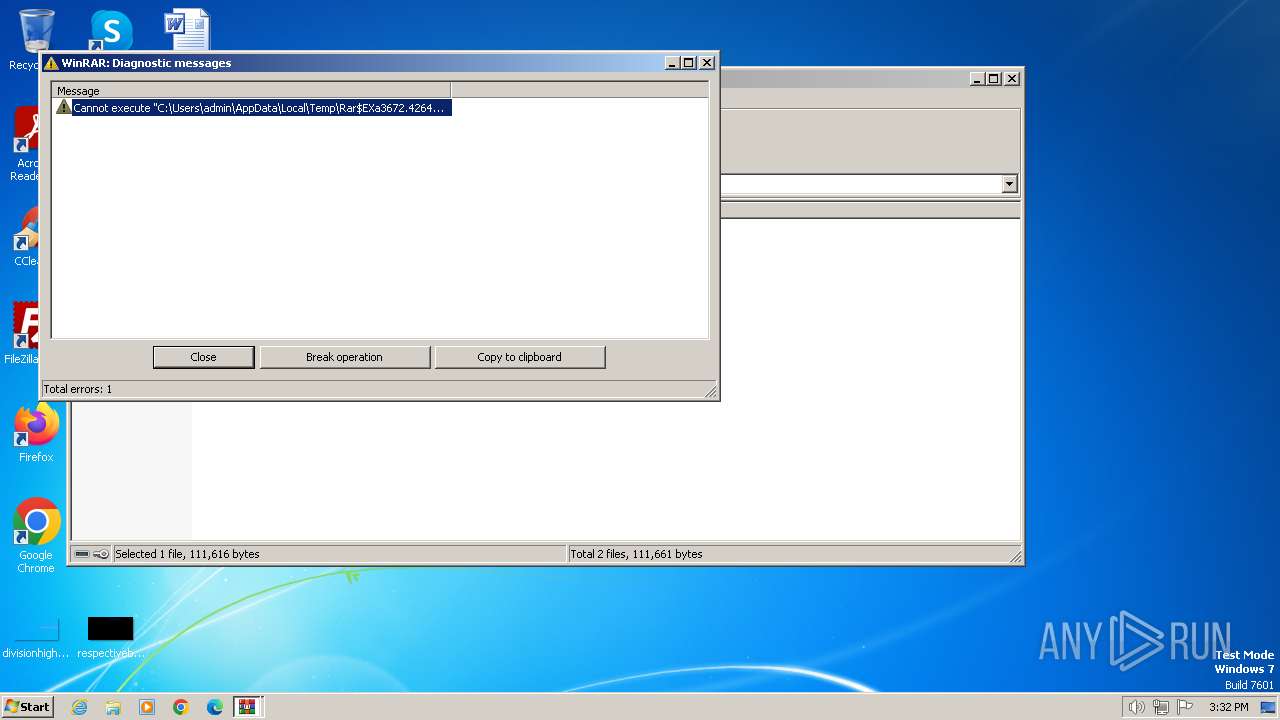
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3672)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 3672)
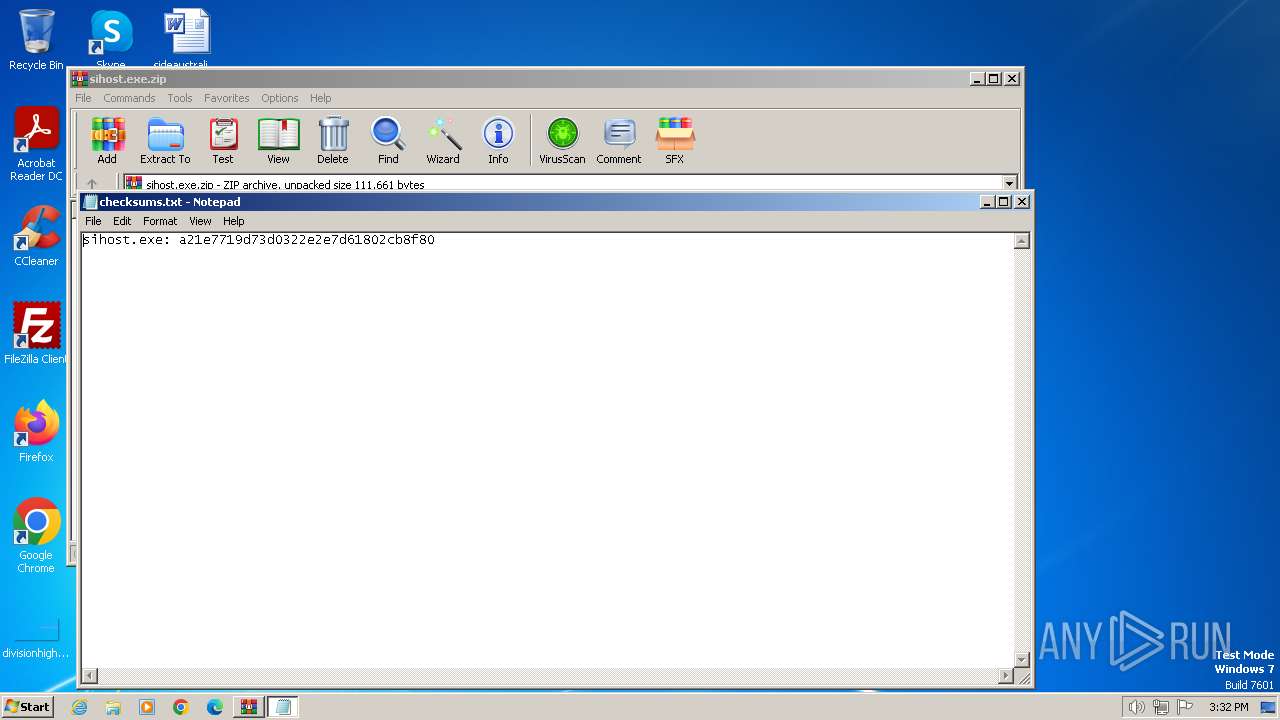
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 3672)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3672)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 3672)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:03:08 15:31:24 |
| ZipCRC: | 0xdd90a9fe |
| ZipCompressedSize: | 53789 |
| ZipUncompressedSize: | 111616 |
| ZipFileName: | sihost.exe |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3672 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sihost.exe.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3972 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa3672.40704\checksums.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 714
Read events
3 694
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3672) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sihost.exe.zip | |||
| (PID) Process: | (3672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
2
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3672.41140\sihost.exe | executable | |
MD5:A21E7719D73D0322E2E7D61802CB8F80 | SHA256:8EE21A0BA8849D31C265B4090A9E2EBE8BA66F58A8F71D4E96509E8A78F7DB00 | |||
| 3672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3672.41140\checksums.txt | text | |
MD5:37E247AC70F88394F8680807A053CB19 | SHA256:F47B6AFE8D3DC42365F78583652BC8B967468F832CE793CDB021D5076E81E1F1 | |||
| 3672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3672.42649\sihost.exe | executable | |
MD5:A21E7719D73D0322E2E7D61802CB8F80 | SHA256:8EE21A0BA8849D31C265B4090A9E2EBE8BA66F58A8F71D4E96509E8A78F7DB00 | |||
| 3672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3672.42649\checksums.txt | text | |
MD5:37E247AC70F88394F8680807A053CB19 | SHA256:F47B6AFE8D3DC42365F78583652BC8B967468F832CE793CDB021D5076E81E1F1 | |||
| 3672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3672.40704\checksums.txt | text | |
MD5:37E247AC70F88394F8680807A053CB19 | SHA256:F47B6AFE8D3DC42365F78583652BC8B967468F832CE793CDB021D5076E81E1F1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |