| File name: | 64bit Patch build 5.exe |
| Full analysis: | https://app.any.run/tasks/f6fc057a-1cfe-47fa-b76c-f0d5ee578daf |
| Verdict: | No threats detected |
| Analysis date: | February 10, 2019, 18:50:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E9255982650A1B34F64E31D4F3EBABD0 |
| SHA1: | F863511E13A3344B5BC42F776F4D9BC8DD1C4E25 |
| SHA256: | 12133D29C57C54C55A6EB2FE0F235AC5B8C25A3B74879B0EDAE5C84D03638FED |
| SSDEEP: | 24576:OAT8QE+k6EQFseFljaFTPd0/IROySYK1XC/b7bhVIdmC0ydYYtqaNXupNhu0qnKH:OAI+lseFlILOWK1y/brIoC0yB1eU0A67 |
MALICIOUS
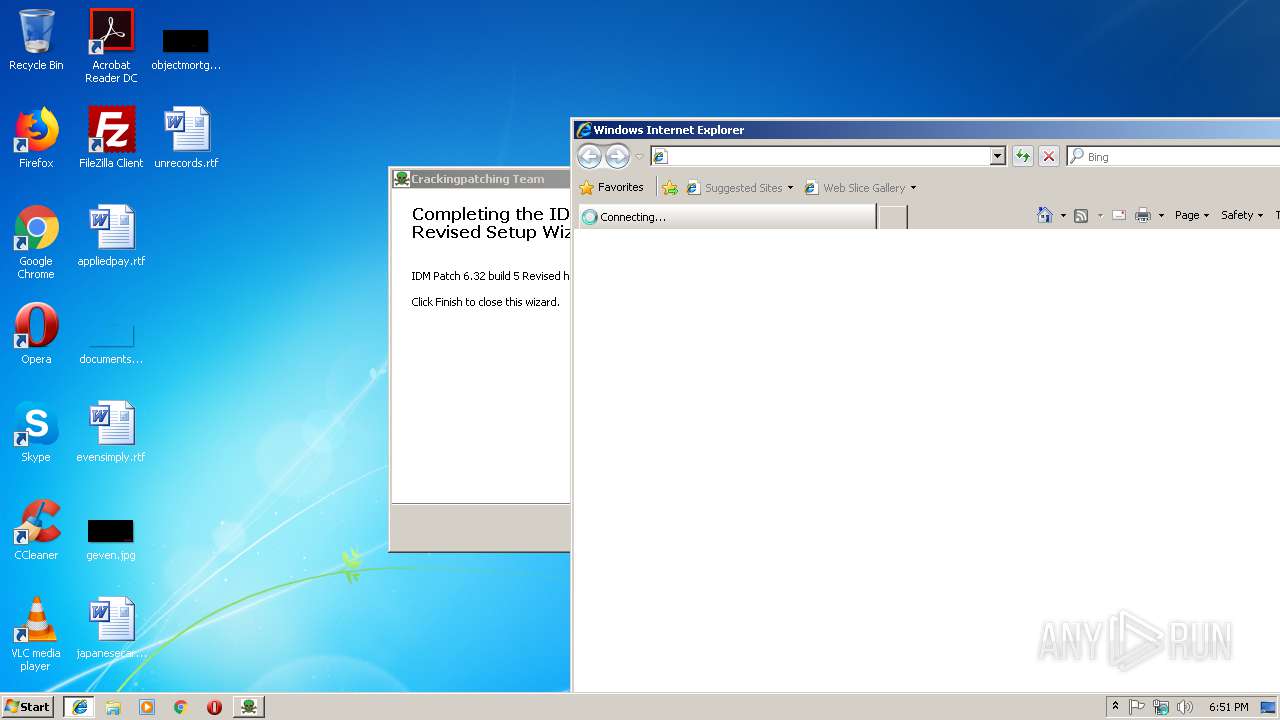
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- 64bit Patch build 5.exe (PID: 4080)
- iexplore.exe (PID: 2152)
Creates a software uninstall entry
- 64bit Patch build 5.exe (PID: 4080)
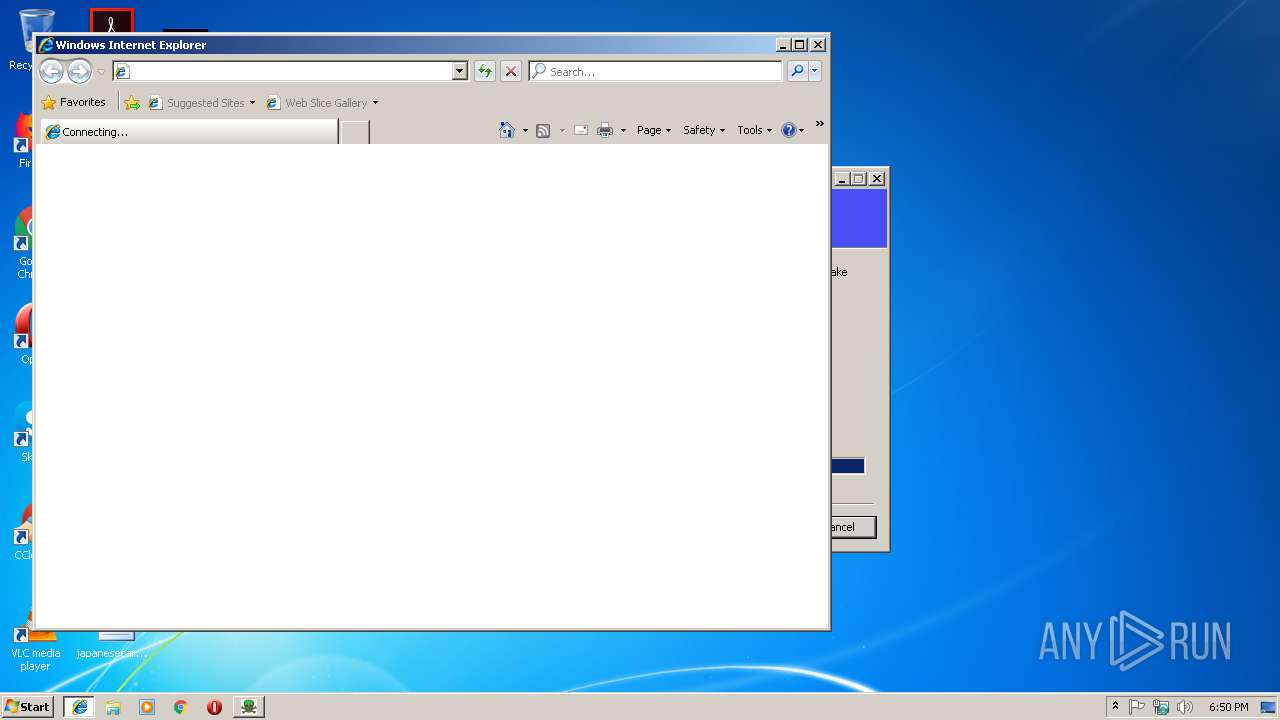
Starts Internet Explorer
- 64bit Patch build 5.exe (PID: 4080)
Executable content was dropped or overwritten
- 64bit Patch build 5.exe (PID: 4080)
INFO
Application launched itself
- iexplore.exe (PID: 3648)
Changes settings of System certificates
- iexplore.exe (PID: 2152)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2152)
Changes internet zones settings
- iexplore.exe (PID: 3648)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2152)
Reads internet explorer settings
- iexplore.exe (PID: 2152)
Creates files in the user directory
- iexplore.exe (PID: 2152)
Reads Internet Cache Settings
- iexplore.exe (PID: 2152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 148992 |
| InitializedDataSize: | 314880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25468 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
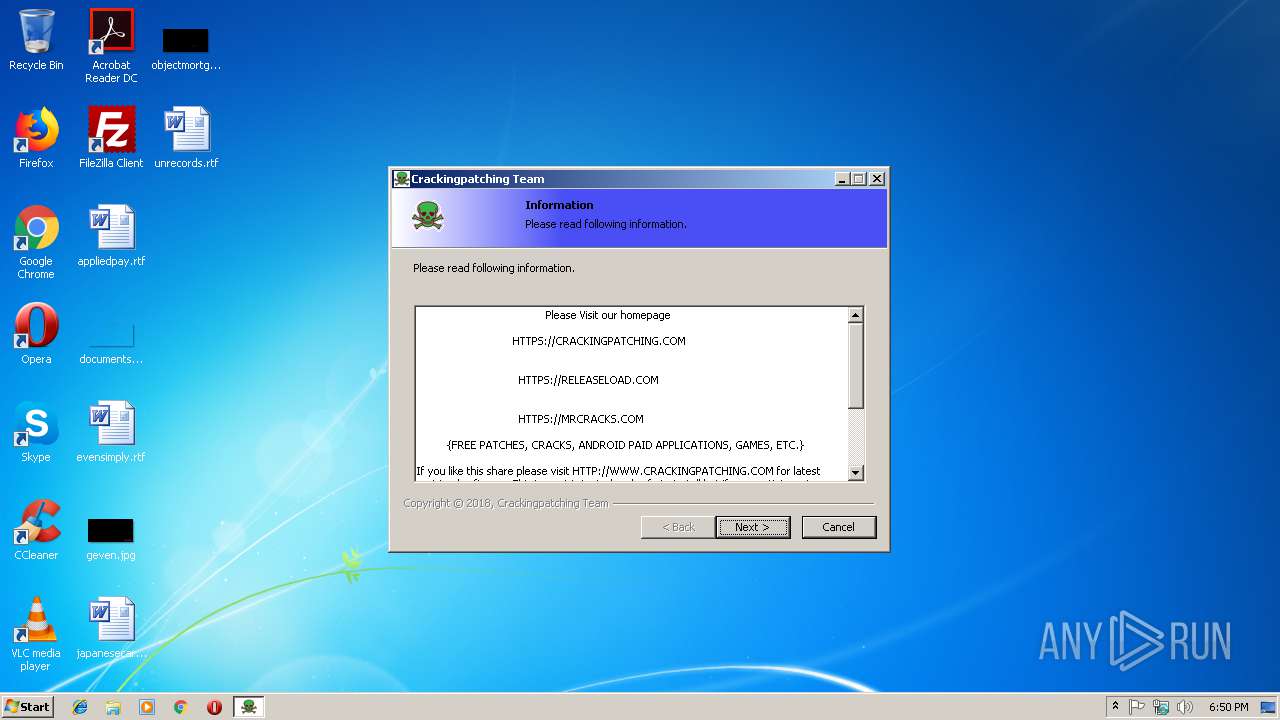
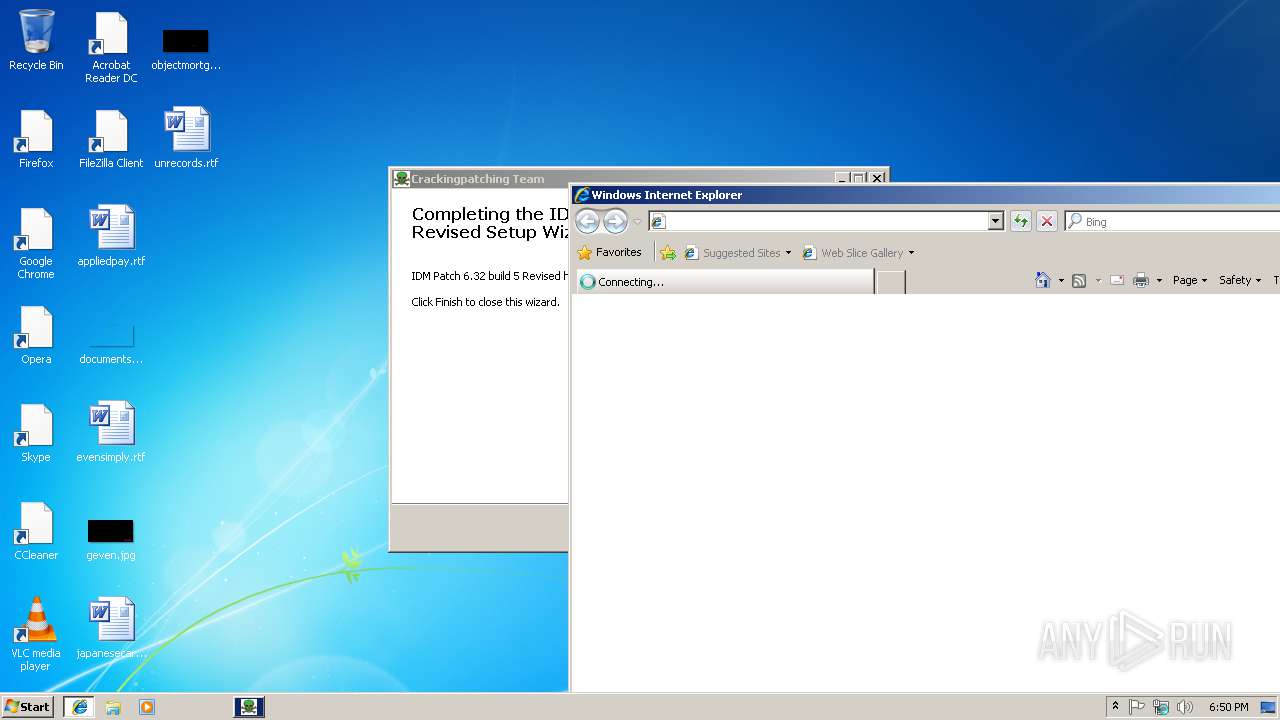
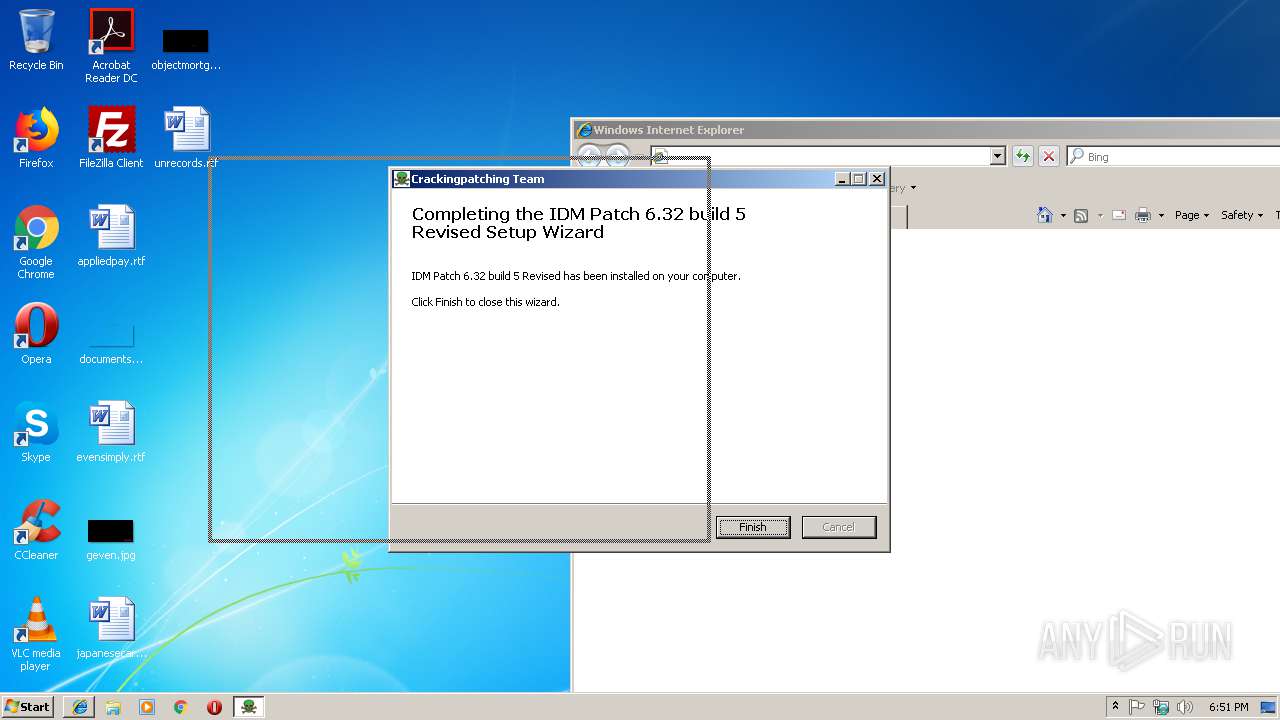
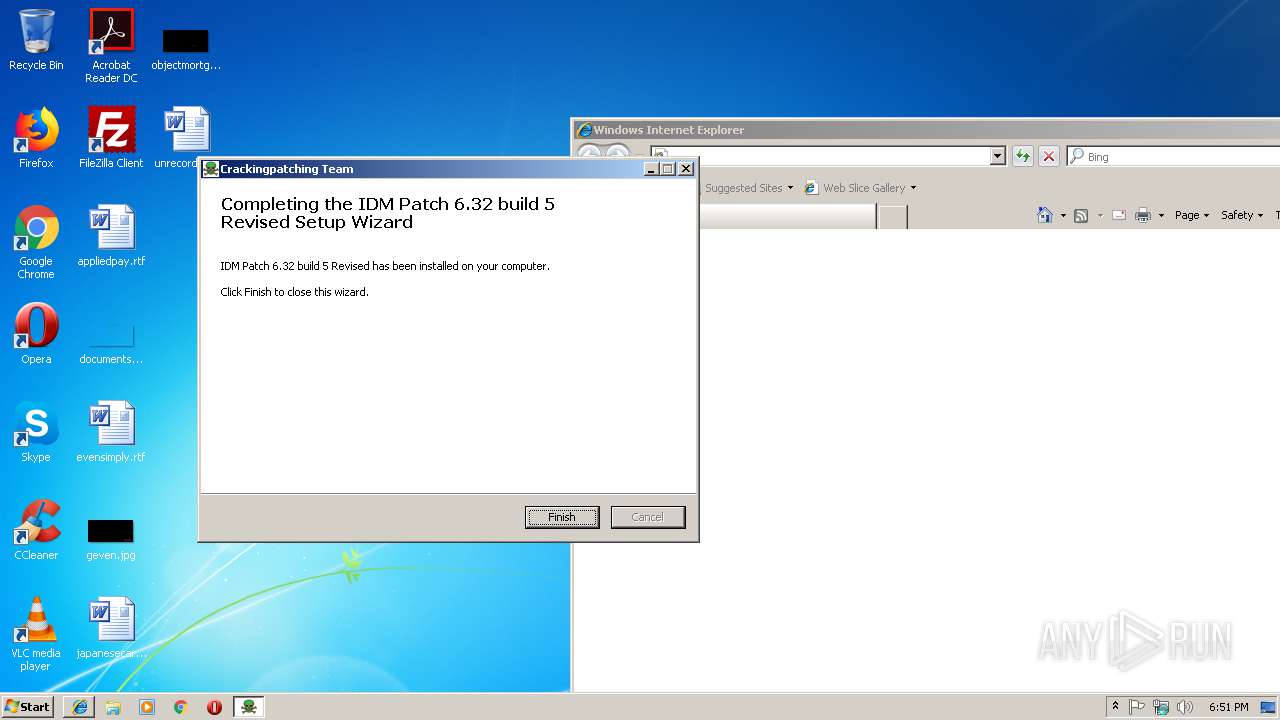
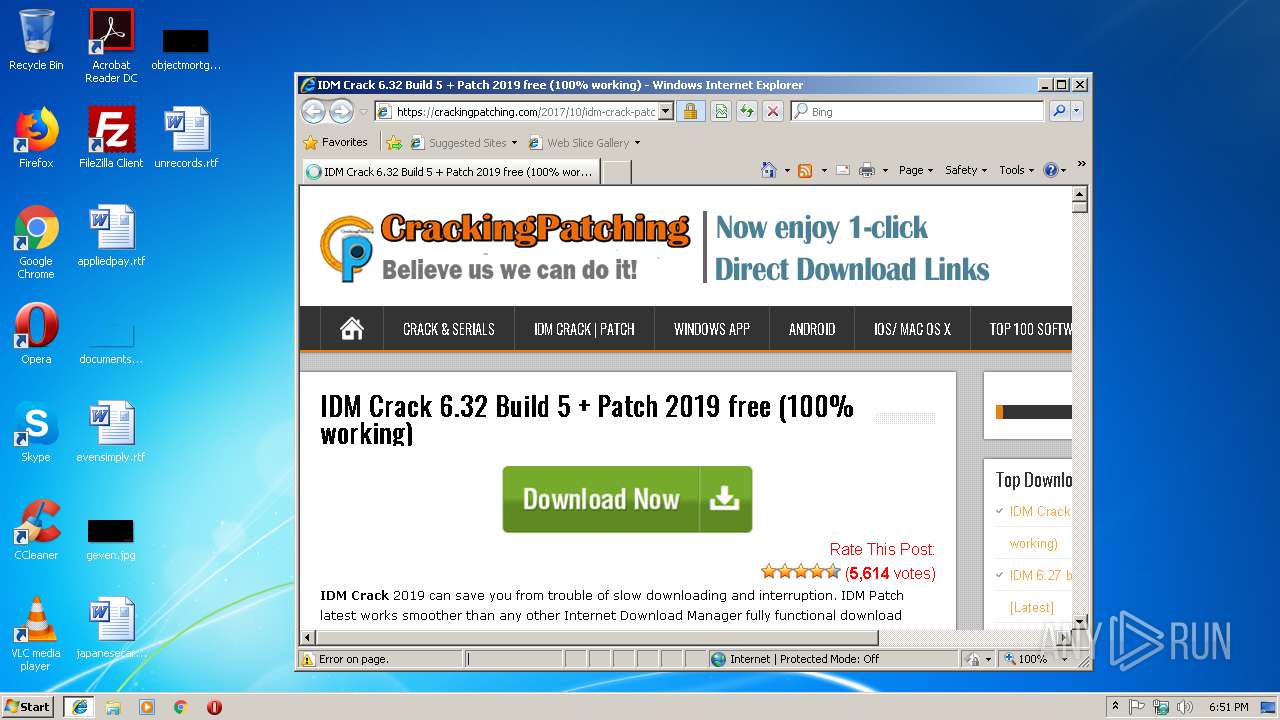
| CompanyName: | Crackingpatching.com Team |
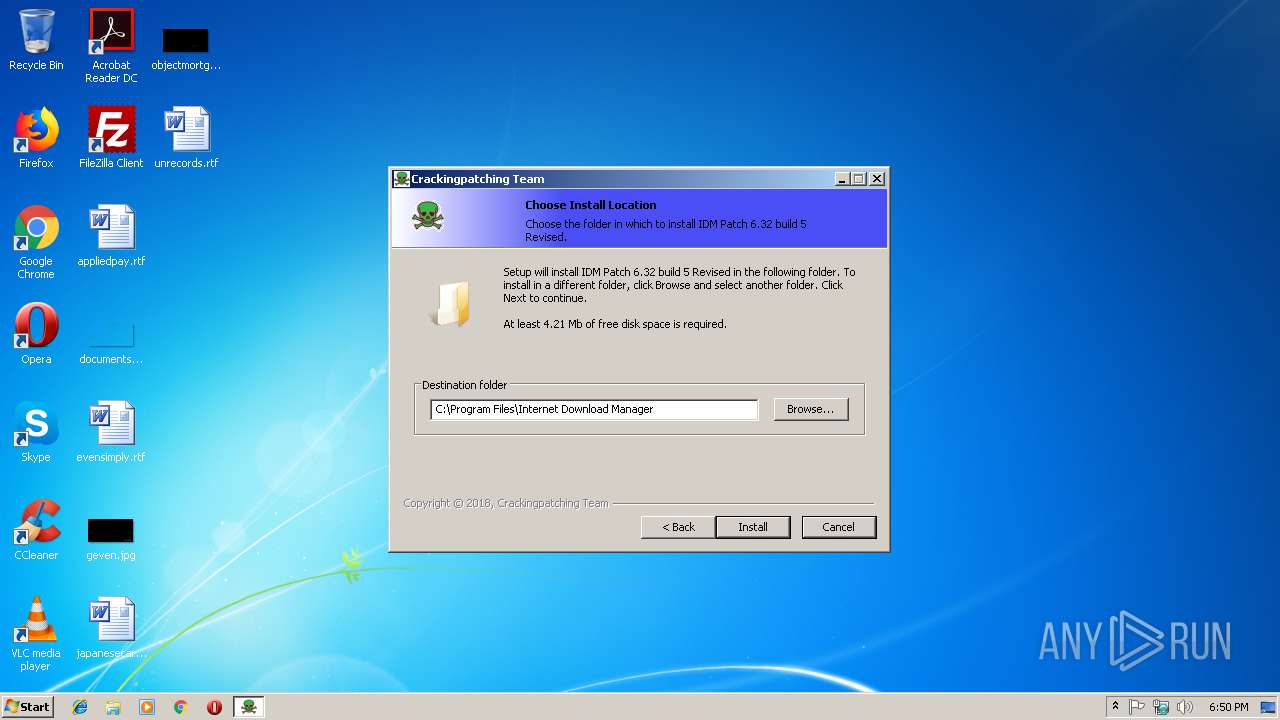
| FileDescription: | IDM Patch 6.32 build 5 Revised 6.32 build 5 Installation |
| FileVersion: | 6.32 build 5 |
| LegalCopyright: | Crackingpatching.com Team |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Crackingpatching.com Team |
| FileDescription: | IDM Patch 6.32 build 5 Revised 6.32 build 5 Installation |
| FileVersion: | 6.32 build 5 |
| LegalCopyright: | Crackingpatching.com Team |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59443 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88555 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x00046F60 | 0x00047000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.14044 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 5.24025 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 4.94231 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 4.73718 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 4.51902 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
54 | 4.05378 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.75922 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
36
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2152 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3648 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3528 | "C:\Users\admin\AppData\Local\Temp\64bit Patch build 5.exe" | C:\Users\admin\AppData\Local\Temp\64bit Patch build 5.exe | — | explorer.exe | |||||||||||
User: admin Company: Crackingpatching.com Team Integrity Level: MEDIUM Description: IDM Patch 6.32 build 5 Revised 6.32 build 5 Installation Exit code: 3221226540 Version: 6.32 build 5 Modules
| |||||||||||||||
| 3648 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | 64bit Patch build 5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\AppData\Local\Temp\64bit Patch build 5.exe" | C:\Users\admin\AppData\Local\Temp\64bit Patch build 5.exe | explorer.exe | ||||||||||||
User: admin Company: Crackingpatching.com Team Integrity Level: HIGH Description: IDM Patch 6.32 build 5 Revised 6.32 build 5 Installation Exit code: 0 Version: 6.32 build 5 Modules
| |||||||||||||||
Total events
487
Read events
369
Write events
118
Delete events
0
Modification events
| (PID) Process: | (4080) 64bit Patch build 5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | FName |
Value: Crackingpatching.com | | |||
| (PID) Process: | (4080) 64bit Patch build 5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | InstallStatus |
Value: 3 | |||
| (PID) Process: | (4080) 64bit Patch build 5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | LName |
Value: MrCracks.com | |||
| (PID) Process: | (4080) 64bit Patch build 5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | |
Value: info@tonec.com | |||
| (PID) Process: | (4080) 64bit Patch build 5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | Serial |
Value: KI6P5-CY0NH-V5XCS-ZRS3I | |||
| (PID) Process: | (4080) 64bit Patch build 5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Internet Download Manager |
| Operation: | write | Name: | FName |
Value: Crackingpatching.com | | |||
| (PID) Process: | (4080) 64bit Patch build 5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Internet Download Manager |
| Operation: | write | Name: | InstallStatus |
Value: 3 | |||
| (PID) Process: | (4080) 64bit Patch build 5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Internet Download Manager |
| Operation: | write | Name: | LName |
Value: MrCracks.com | |||
| (PID) Process: | (4080) 64bit Patch build 5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Internet Download Manager |
| Operation: | write | Name: | |
Value: info@tonec.com | |||
| (PID) Process: | (4080) 64bit Patch build 5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Internet Download Manager |
| Operation: | write | Name: | Serial |
Value: KI6P5-CY0NH-V5XCS-ZRS3I | |||
Executable files
3
Suspicious files
3
Text files
174
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3648 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4080 | 64bit Patch build 5.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:— | SHA256:— | |||
| 4080 | 64bit Patch build 5.exe | C:\Program Files\Internet Download Manager\IDM Patch Uninstaller 6.32 build 5.ini | text | |
MD5:— | SHA256:— | |||
| 4080 | 64bit Patch build 5.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | compressed | |
MD5:— | SHA256:— | |||
| 4080 | 64bit Patch build 5.exe | C:\Program Files\Internet Download Manager\IDMan.exe | executable | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@crackingpatching[1].txt | text | |
MD5:— | SHA256:— | |||
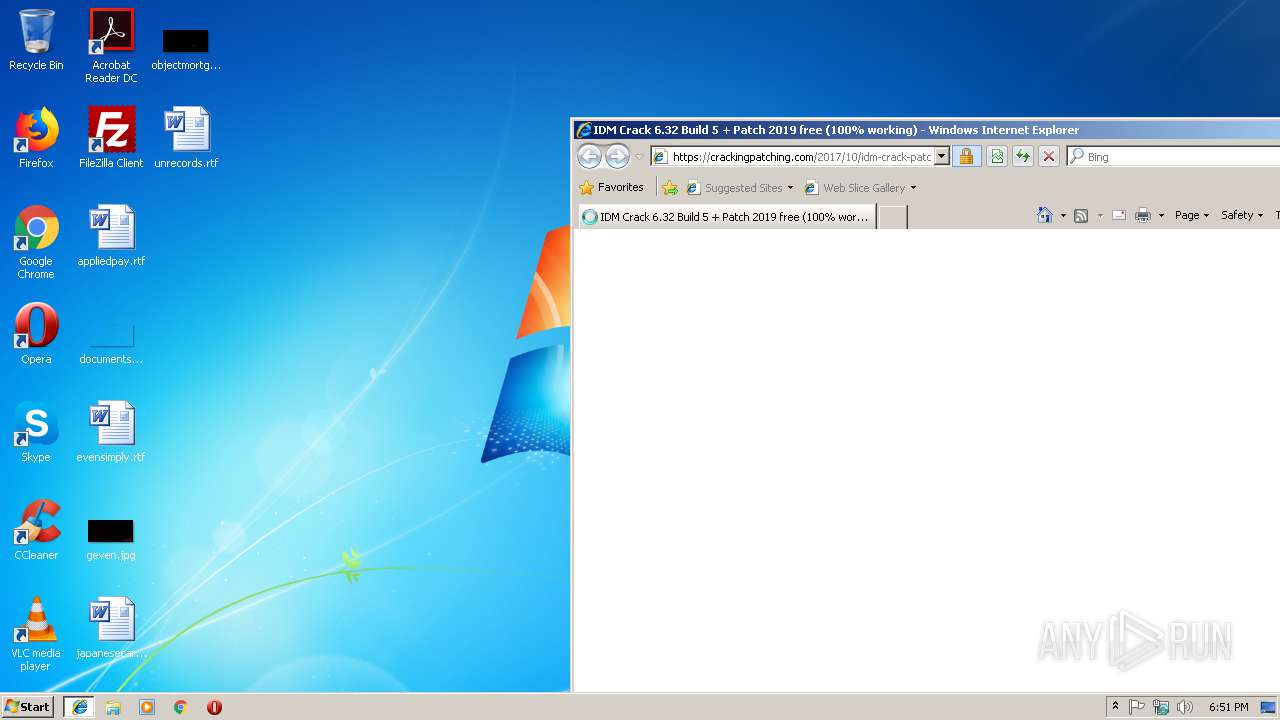
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\idm-crack-patch[1].html | html | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\styles[1].css | text | |
MD5:— | SHA256:— | |||
| 4080 | 64bit Patch build 5.exe | C:\Users\admin\AppData\Local\Temp\$inst\7.tmp | image | |
MD5:696641D2325E8B142B6C16D1183ACA43 | SHA256:4A56FFCE0E414F3495F70E9C2960837DF25423B0DBAFD21A073DBDBAA461BC90 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
52
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3648 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2152 | iexplore.exe | 104.18.56.24:443 | crackingpatching.com | Cloudflare Inc | US | shared |
2152 | iexplore.exe | 192.0.78.9:443 | wordpress.com | Automattic, Inc | US | malicious |
2152 | iexplore.exe | 172.217.22.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2152 | iexplore.exe | 172.217.22.98:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2152 | iexplore.exe | 172.217.22.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2152 | iexplore.exe | 172.217.21.226:443 | adservice.google.dk | Google Inc. | US | whitelisted |
2152 | iexplore.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2152 | iexplore.exe | 216.58.205.226:443 | adservice.google.com | Google Inc. | US | whitelisted |
2152 | iexplore.exe | 192.0.77.2:443 | i1.wp.com | Automattic, Inc | US | suspicious |
2152 | iexplore.exe | 172.217.16.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crackingpatching.com |
| malicious |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
wordpress.com |
| whitelisted |
adservice.google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
adservice.google.dk |
| whitelisted |
i1.wp.com |
| whitelisted |