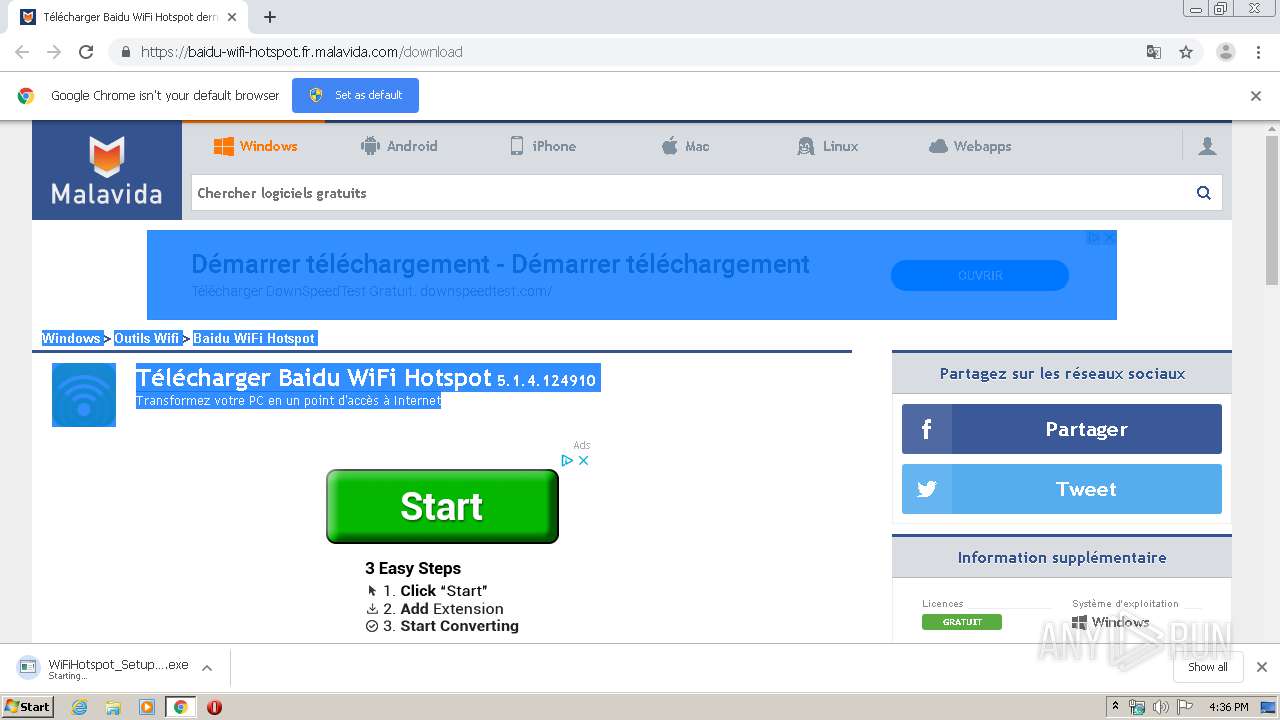
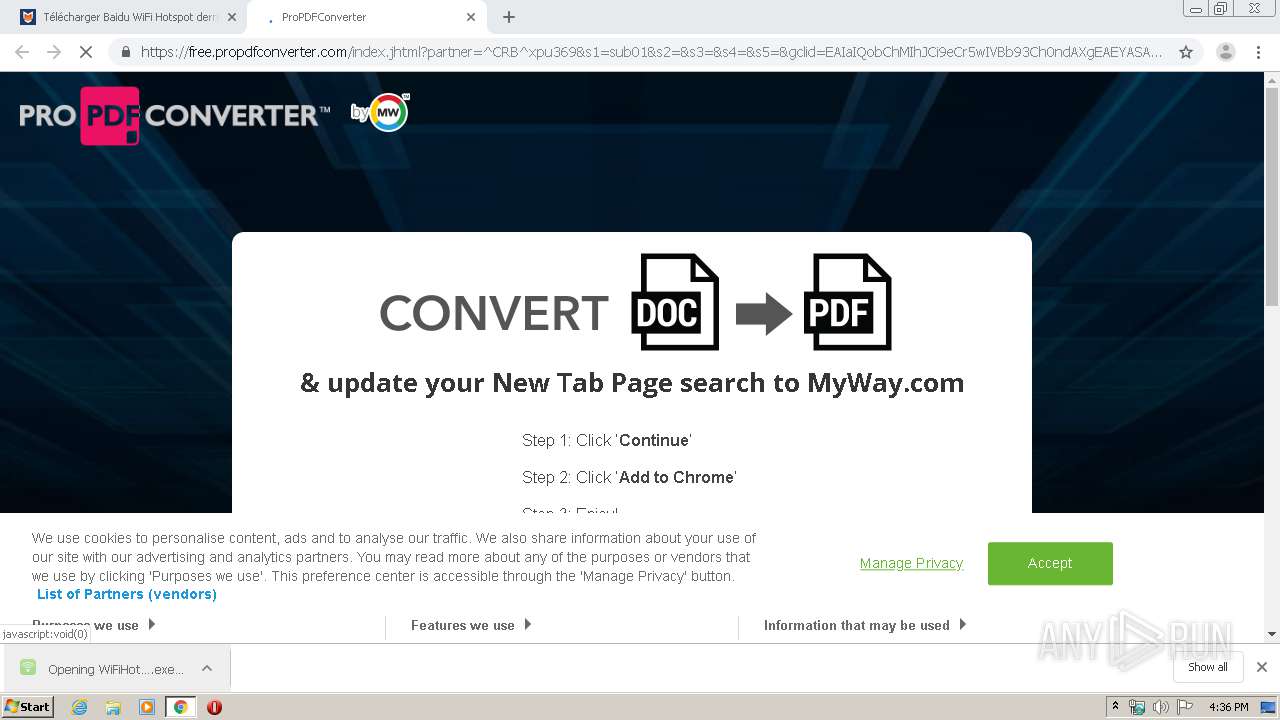
| URL: | https://baidu-wifi-hotspot.fr.malavida.com/download |
| Full analysis: | https://app.any.run/tasks/b0576883-54ad-4349-aaf8-a5cb4560e8c0 |
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2020, 16:35:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AC4AD7844ECBE7AA7682591E90042DB6 |
| SHA1: | 786A0F1064C8EDC69F6EBD0CA8B203A732A97D0A |
| SHA256: | 12080B993B47C99F67F109938FB042CC396E8282C55BB4B9756F6C98F13610BE |
| SSDEEP: | 3:N8PSMDJNKRvl7M:2PSHLM |
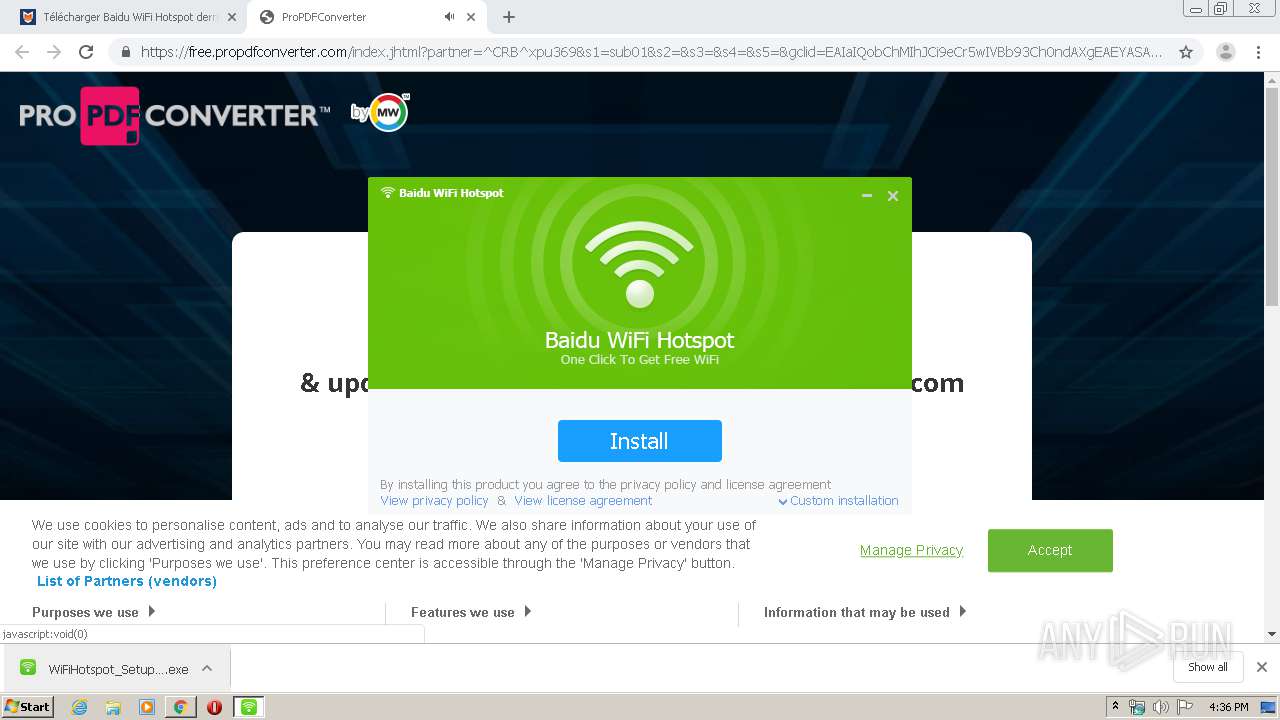
MALICIOUS
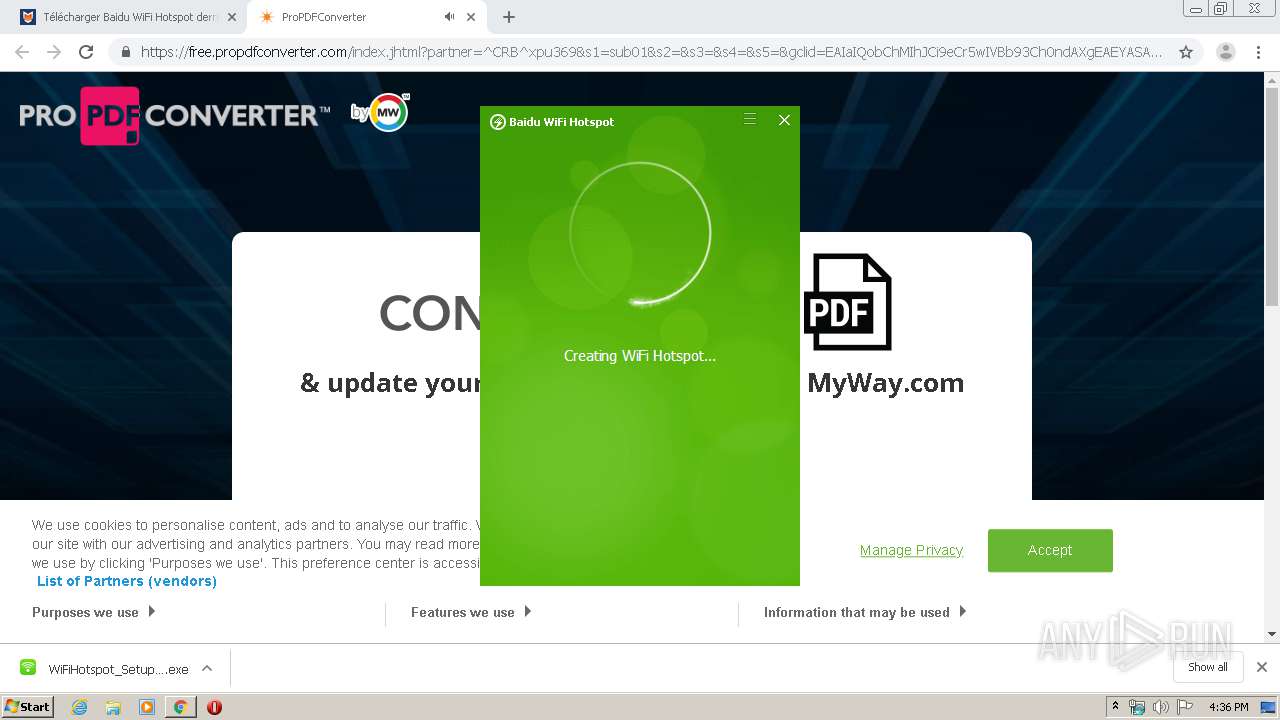
Application was dropped or rewritten from another process
- WiFiHotspot_Setup_GL.exe (PID: 748)
- WiFiHotspot_Setup_GL.exe (PID: 3076)
- MSF43D.exe (PID: 3376)
- WifiHotspot.exe (PID: 2796)
Loads dropped or rewritten executable
- MSF43D.exe (PID: 3376)
- regsvr32.exe (PID: 3976)
- regsvr32.exe (PID: 3048)
- WifiHotspot.exe (PID: 2796)
- regsvr32.exe (PID: 1784)
Registers / Runs the DLL via REGSVR32.EXE
- MSF43D.exe (PID: 3376)
- WifiHotspot.exe (PID: 2796)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3264)
- chrome.exe (PID: 1740)
- WiFiHotspot_Setup_GL.exe (PID: 3076)
- MSF43D.exe (PID: 3376)
Creates files in the program directory
- WiFiHotspot_Setup_GL.exe (PID: 3076)
- WifiHotspot.exe (PID: 2796)
- MSF43D.exe (PID: 3376)
Low-level read access rights to disk partition
- MSF43D.exe (PID: 3376)
- WifiHotspot.exe (PID: 2796)
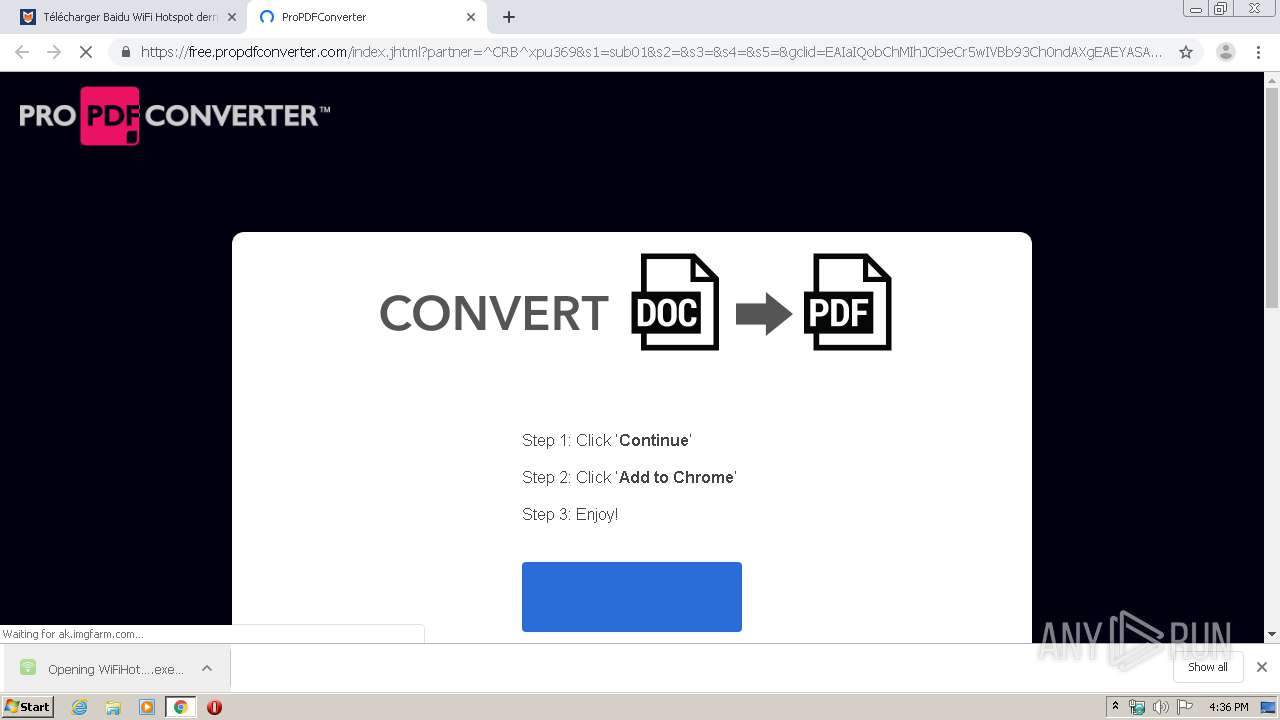
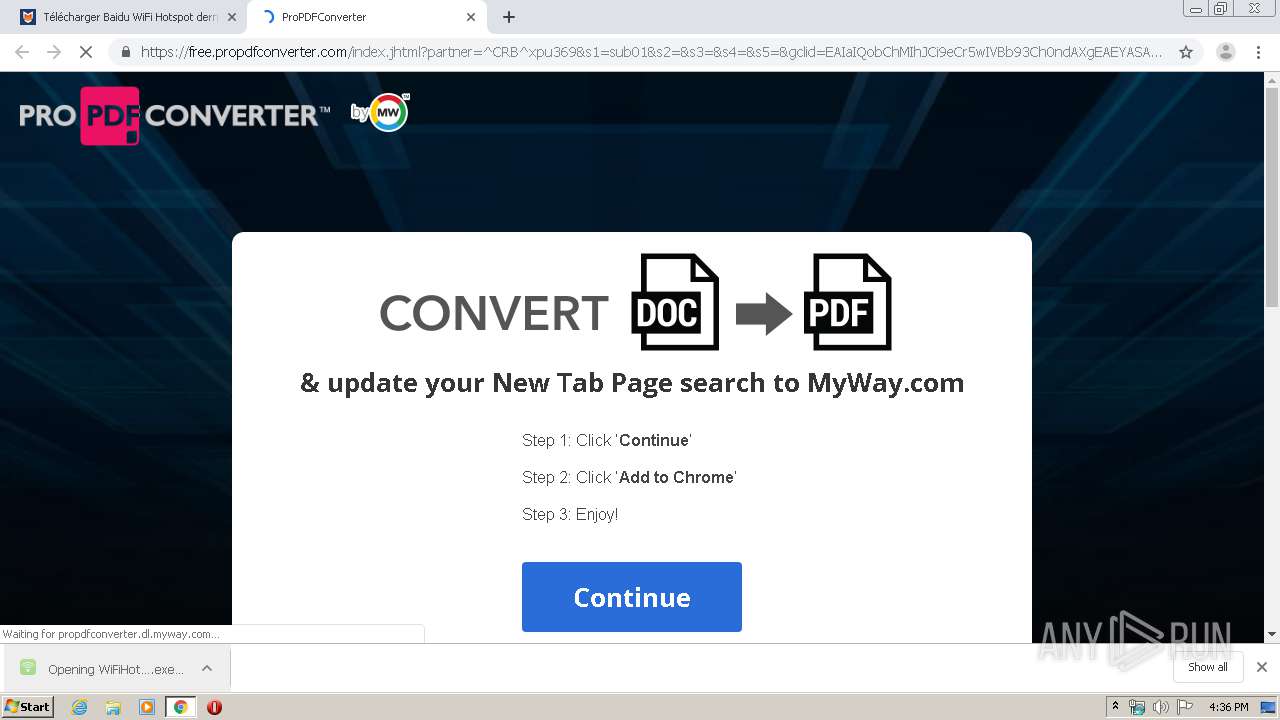
Modifies files in Chrome extension folder
- chrome.exe (PID: 1740)
Creates a software uninstall entry
- MSF43D.exe (PID: 3376)
Creates COM task schedule object
- regsvr32.exe (PID: 3048)
- regsvr32.exe (PID: 1784)
Creates files in the user directory
- WifiHotspot.exe (PID: 2796)
Executed as Windows Service
- alg.exe (PID: 2976)
INFO
Reads the hosts file
- chrome.exe (PID: 3264)
- chrome.exe (PID: 1740)
Reads settings of System Certificates
- chrome.exe (PID: 1740)
- chrome.exe (PID: 3264)
Reads Internet Cache Settings
- chrome.exe (PID: 1740)
Application launched itself
- chrome.exe (PID: 1740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
40
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,4315081550631162817,16954717567339995984,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3051797880886401899 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Users\admin\Downloads\WiFiHotspot_Setup_GL.exe" | C:\Users\admin\Downloads\WiFiHotspot_Setup_GL.exe | — | chrome.exe | |||||||||||
User: admin Company: Baidu, Inc. Integrity Level: MEDIUM Description: Baidu WiFi Hotspot Setup Exit code: 3221226540 Version: 5,1,4,124910 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa6a9d0,0x6fa6a9e0,0x6fa6a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,4315081550631162817,16954717567339995984,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15507429381204569662 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2564 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,4315081550631162817,16954717567339995984,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13813865517962185726 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,4315081550631162817,16954717567339995984,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18362541511461412323 --mojo-platform-channel-handle=3392 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,4315081550631162817,16954717567339995984,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8369883971379918236 --mojo-platform-channel-handle=5944 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,4315081550631162817,16954717567339995984,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8830905949229779065 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,4315081550631162817,16954717567339995984,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14200842924476403344 --mojo-platform-channel-handle=3836 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 425
Read events
1 299
Write events
117
Delete events
9
Modification events
| (PID) Process: | (944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1740-13224875758581875 |
Value: 259 | |||
| (PID) Process: | (1740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1740) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
31
Suspicious files
138
Text files
412
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E3305EE-6CC.pma | — | |
MD5:— | SHA256:— | |||
| 1740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8fb398a7-8da1-46f4-a18d-3f6676b38c7a.tmp | — | |
MD5:— | SHA256:— | |||
| 1740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 1740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66ba3.TMP | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 1740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66b93.TMP | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 1740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66ceb.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
82
DNS requests
53
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3264 | chrome.exe | GET | 200 | 74.125.8.167:80 | http://r1---sn-5hne6nlk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=212.32.229.66&mm=28&mn=sn-5hne6nlk&ms=nvh&mt=1580401921&mv=u&mvi=0&pl=22&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3264 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
3264 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
3264 | chrome.exe | GET | 200 | 209.85.226.73:80 | http://r4---sn-5hnekn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.32.229.66&mm=28&mn=sn-5hnekn7k&ms=nvh&mt=1580401921&mv=u&mvi=3&pl=22&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3264 | chrome.exe | 104.90.148.154:443 | imag.malavida.com | Akamai Technologies, Inc. | NL | unknown |
3264 | chrome.exe | 172.217.16.177:443 | survey.g.doubleclick.net | Google Inc. | US | whitelisted |
3264 | chrome.exe | 172.217.22.104:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 172.217.16.129:443 | tpc.googlesyndication.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 173.194.76.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3264 | chrome.exe | 216.58.207.66:443 | adservice.google.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 91.192.108.161:443 | actions.malavida.com | Comvive Servidores S.L. | ES | suspicious |
3264 | chrome.exe | 172.217.22.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 172.217.16.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
3264 | chrome.exe | 172.217.21.226:443 | adservice.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
baidu-wifi-hotspot.fr.malavida.com |
| unknown |
accounts.google.com |
| shared |
securepubads.g.doubleclick.net |
| whitelisted |
static.malavida.com |
| whitelisted |
survey.g.doubleclick.net |
| whitelisted |
imag.malavida.com |
| whitelisted |
consent-policy.malavida.com |
| unknown |
tpc.googlesyndication.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |