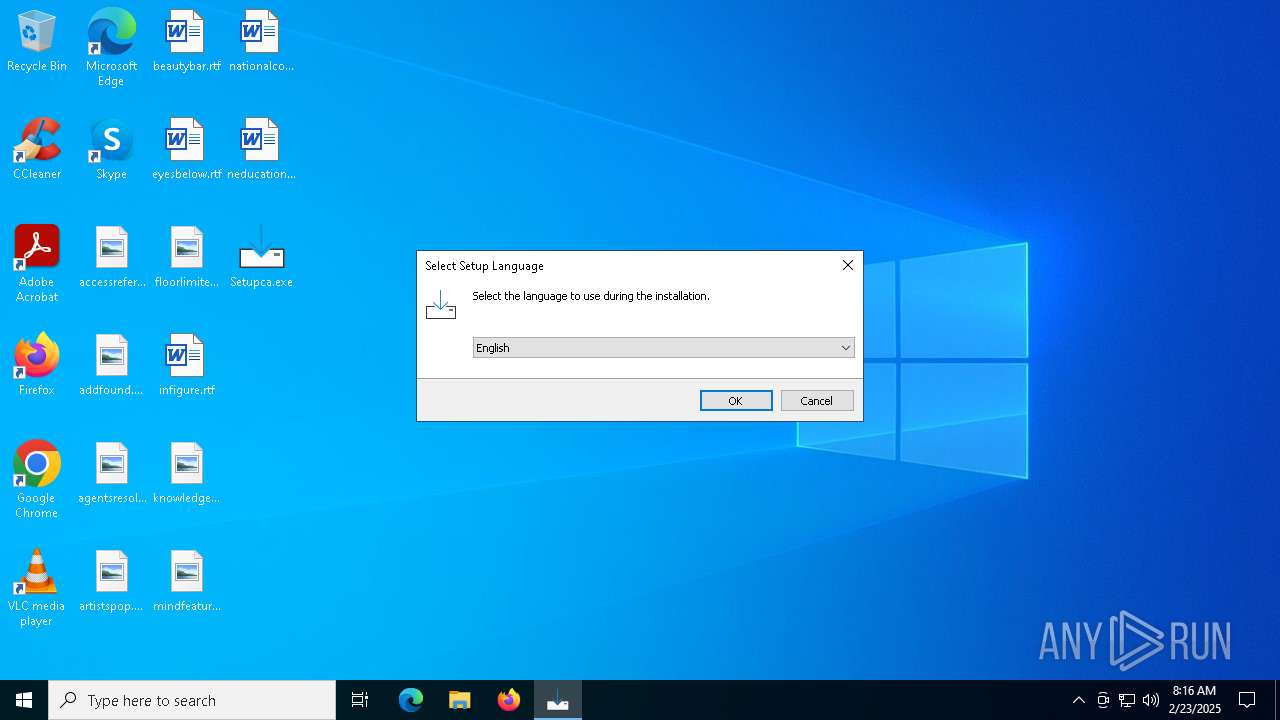
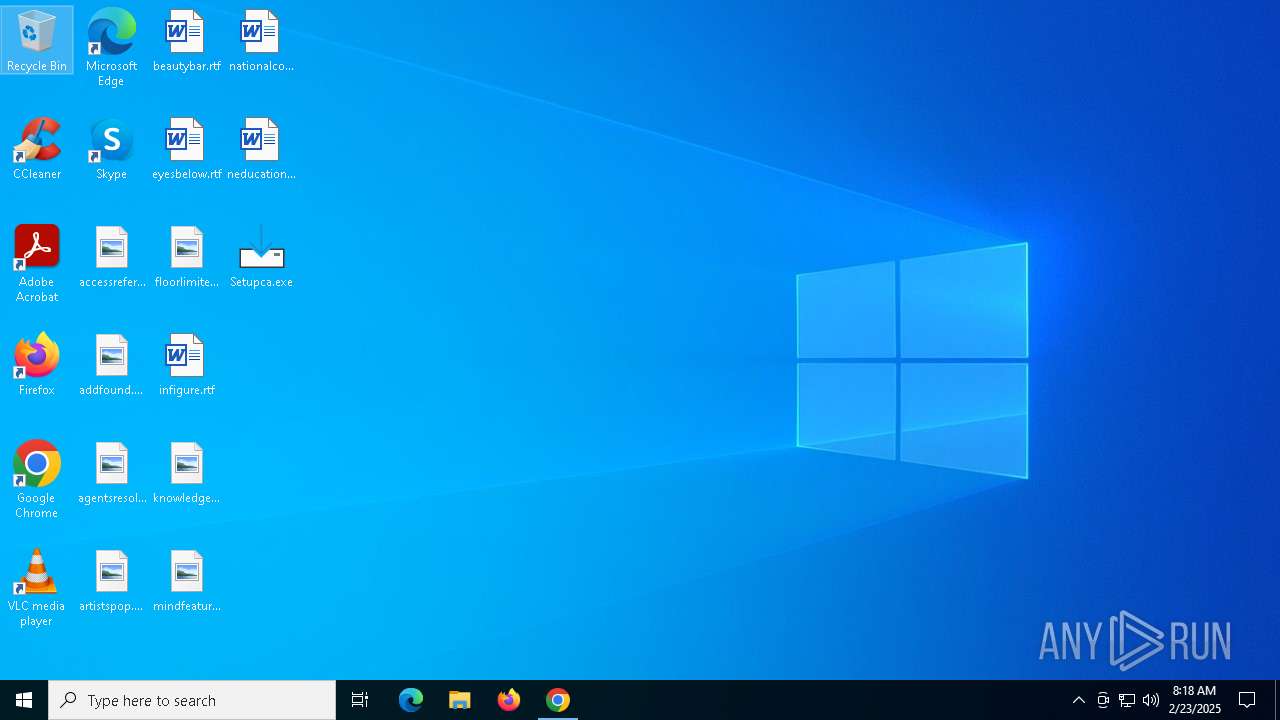
| File name: | Setupca.exe |
| Full analysis: | https://app.any.run/tasks/b729715a-06f3-4c69-b1dc-a3e42223877e |
| Verdict: | Malicious activity |
| Analysis date: | February 23, 2025, 08:16:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 10 sections |
| MD5: | A64517503ADB2A1BB8A2F58CA8A661DE |
| SHA1: | F8A5A7F0F6A974559E63EC744402A497A45150E2 |
| SHA256: | 11F4F22EABB173D8C37E80A3DE3BA1D321805FB6D5ADAE498C6628145811EF2E |
| SSDEEP: | 49152:67HecD4dnbibBlb+D7rP4jsbmLApne0Fop4R2uXB3iyLT/ex4XrL7P42DpJXWZnJ:q+cD4dni2P4IkWnXFopLQ3iUrex4vkYc |
MALICIOUS
Executing a file with an untrusted certificate
- Setupca.exe (PID: 1616)
- Setupca.exe (PID: 6220)
- Certmgr.exe (PID: 6752)
- Certmgr.exe (PID: 6780)
- Certmgr.exe (PID: 6808)
- Certmgr.exe (PID: 6848)
- Certmgr.exe (PID: 6912)
- Certmgr.exe (PID: 6944)
- Certmgr.exe (PID: 6972)
- Certmgr.exe (PID: 7000)
- Certmgr.exe (PID: 6880)
- Certmgr.exe (PID: 7064)
- Certmgr.exe (PID: 7096)
- Certmgr.exe (PID: 7128)
- Certmgr.exe (PID: 7156)
- Certmgr.exe (PID: 7032)
- Certmgr.exe (PID: 2380)
- Certmgr.exe (PID: 2324)
- Certmgr.exe (PID: 4556)
- Certmgr.exe (PID: 4444)
- Certmgr.exe (PID: 6180)
- Certmgr.exe (PID: 4980)
- Certmgr.exe (PID: 4512)
- Certmgr.exe (PID: 5252)
- Certmgr.exe (PID: 4120)
- Certmgr.exe (PID: 4320)
- Certmgr.exe (PID: 244)
- Certmgr.exe (PID: 5728)
- Certmgr.exe (PID: 3928)
- Certmgr.exe (PID: 2408)
- Certmgr.exe (PID: 2160)
- Certmgr.exe (PID: 6724)
- Certmgr.exe (PID: 6728)
- Certmgr.exe (PID: 6752)
- Certmgr.exe (PID: 6824)
- Certmgr.exe (PID: 6864)
- Certmgr.exe (PID: 6664)
- Certmgr.exe (PID: 6928)
- Certmgr.exe (PID: 6912)
- Certmgr.exe (PID: 6944)
- Certmgr.exe (PID: 6896)
- Certmgr.exe (PID: 7072)
- Certmgr.exe (PID: 7108)
- Certmgr.exe (PID: 7140)
- Certmgr.exe (PID: 7016)
- Certmgr.exe (PID: 7056)
- Certmgr.exe (PID: 1596)
- Certmgr.exe (PID: 6200)
- Certmgr.exe (PID: 4544)
- Certmgr.exe (PID: 6192)
- Certmgr.exe (PID: 2600)
- Certmgr.exe (PID: 4244)
- Certmgr.exe (PID: 5740)
- Certmgr.exe (PID: 5560)
- Certmgr.exe (PID: 5460)
- Certmgr.exe (PID: 6132)
SUSPICIOUS
Reads security settings of Internet Explorer
- Setupca.tmp (PID: 1488)
Executable content was dropped or overwritten
- Setupca.exe (PID: 1616)
- Setupca.exe (PID: 6220)
- Setupca.tmp (PID: 6248)
Process drops legitimate windows executable
- Setupca.tmp (PID: 6248)
- WinRAR.exe (PID: 4968)
Starts CMD.EXE for commands execution
- Setupca.tmp (PID: 6248)
Executing commands from a ".bat" file
- Setupca.tmp (PID: 6248)
Reads the Windows owner or organization settings
- Setupca.tmp (PID: 6248)
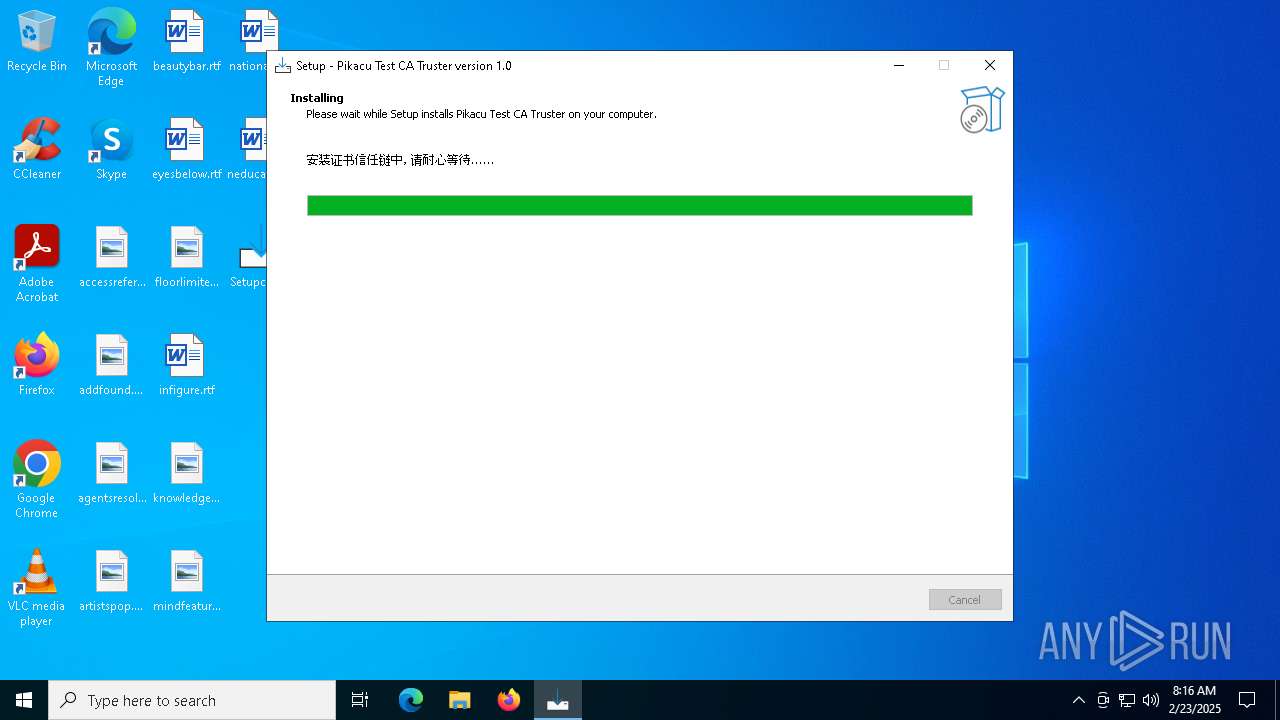
Adds/modifies Windows certificates
- Certmgr.exe (PID: 6752)
- Certmgr.exe (PID: 6780)
- Certmgr.exe (PID: 6808)
- regedit.exe (PID: 6728)
- Certmgr.exe (PID: 6880)
- Certmgr.exe (PID: 6944)
- Certmgr.exe (PID: 7000)
- Certmgr.exe (PID: 7064)
- Certmgr.exe (PID: 7128)
- Certmgr.exe (PID: 6180)
- Certmgr.exe (PID: 2324)
- Certmgr.exe (PID: 4444)
- Certmgr.exe (PID: 4512)
- Certmgr.exe (PID: 4120)
- Certmgr.exe (PID: 244)
- Certmgr.exe (PID: 3928)
- Certmgr.exe (PID: 6724)
- Certmgr.exe (PID: 6752)
- Certmgr.exe (PID: 2160)
- Certmgr.exe (PID: 6864)
- Certmgr.exe (PID: 6928)
- Certmgr.exe (PID: 7056)
- Certmgr.exe (PID: 7108)
- Certmgr.exe (PID: 6944)
- Certmgr.exe (PID: 6192)
- Certmgr.exe (PID: 1596)
- Certmgr.exe (PID: 6132)
- Certmgr.exe (PID: 5740)
- Certmgr.exe (PID: 2600)
Changes settings of the software policy
- regedit.exe (PID: 6728)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6644)
INFO
Checks supported languages
- Setupca.exe (PID: 6220)
- Setupca.exe (PID: 1616)
- Setupca.tmp (PID: 1488)
- Setupca.tmp (PID: 6248)
- Certmgr.exe (PID: 6752)
- Certmgr.exe (PID: 6808)
- mode.com (PID: 6704)
- Certmgr.exe (PID: 6880)
- Certmgr.exe (PID: 6912)
- Certmgr.exe (PID: 6944)
- Certmgr.exe (PID: 6972)
- Certmgr.exe (PID: 7000)
- Certmgr.exe (PID: 6848)
- Certmgr.exe (PID: 7032)
- Certmgr.exe (PID: 7064)
- Certmgr.exe (PID: 7096)
- Certmgr.exe (PID: 7128)
- Certmgr.exe (PID: 6180)
- Certmgr.exe (PID: 4556)
- Certmgr.exe (PID: 2380)
- Certmgr.exe (PID: 2324)
- Certmgr.exe (PID: 4444)
- Certmgr.exe (PID: 7156)
- Certmgr.exe (PID: 4980)
- Certmgr.exe (PID: 4512)
- Certmgr.exe (PID: 5252)
- Certmgr.exe (PID: 4120)
- Certmgr.exe (PID: 4320)
- Certmgr.exe (PID: 244)
- Certmgr.exe (PID: 6780)
- Certmgr.exe (PID: 5728)
- Certmgr.exe (PID: 3928)
- Certmgr.exe (PID: 2408)
- Certmgr.exe (PID: 2160)
- Certmgr.exe (PID: 6724)
- Certmgr.exe (PID: 6824)
- Certmgr.exe (PID: 6728)
- Certmgr.exe (PID: 6752)
- Certmgr.exe (PID: 6664)
- Certmgr.exe (PID: 6896)
- Certmgr.exe (PID: 6928)
- Certmgr.exe (PID: 6912)
- Certmgr.exe (PID: 6944)
- Certmgr.exe (PID: 6864)
- Certmgr.exe (PID: 7072)
- Certmgr.exe (PID: 7056)
- Certmgr.exe (PID: 7108)
- Certmgr.exe (PID: 7140)
- Certmgr.exe (PID: 7016)
- Certmgr.exe (PID: 6192)
- Certmgr.exe (PID: 6200)
- Certmgr.exe (PID: 1596)
- Certmgr.exe (PID: 4544)
- Certmgr.exe (PID: 2600)
- Certmgr.exe (PID: 6132)
- Certmgr.exe (PID: 4244)
- Certmgr.exe (PID: 5740)
- Certmgr.exe (PID: 5560)
- Certmgr.exe (PID: 5460)
Create files in a temporary directory
- Setupca.exe (PID: 1616)
- Setupca.exe (PID: 6220)
- Setupca.tmp (PID: 6248)
Process checks computer location settings
- Setupca.tmp (PID: 1488)
Reads the computer name
- Setupca.tmp (PID: 1488)
- Setupca.tmp (PID: 6248)
Compiled with Borland Delphi (YARA)
- Setupca.tmp (PID: 1488)
- Setupca.exe (PID: 1616)
- Setupca.tmp (PID: 6248)
- Setupca.exe (PID: 6220)
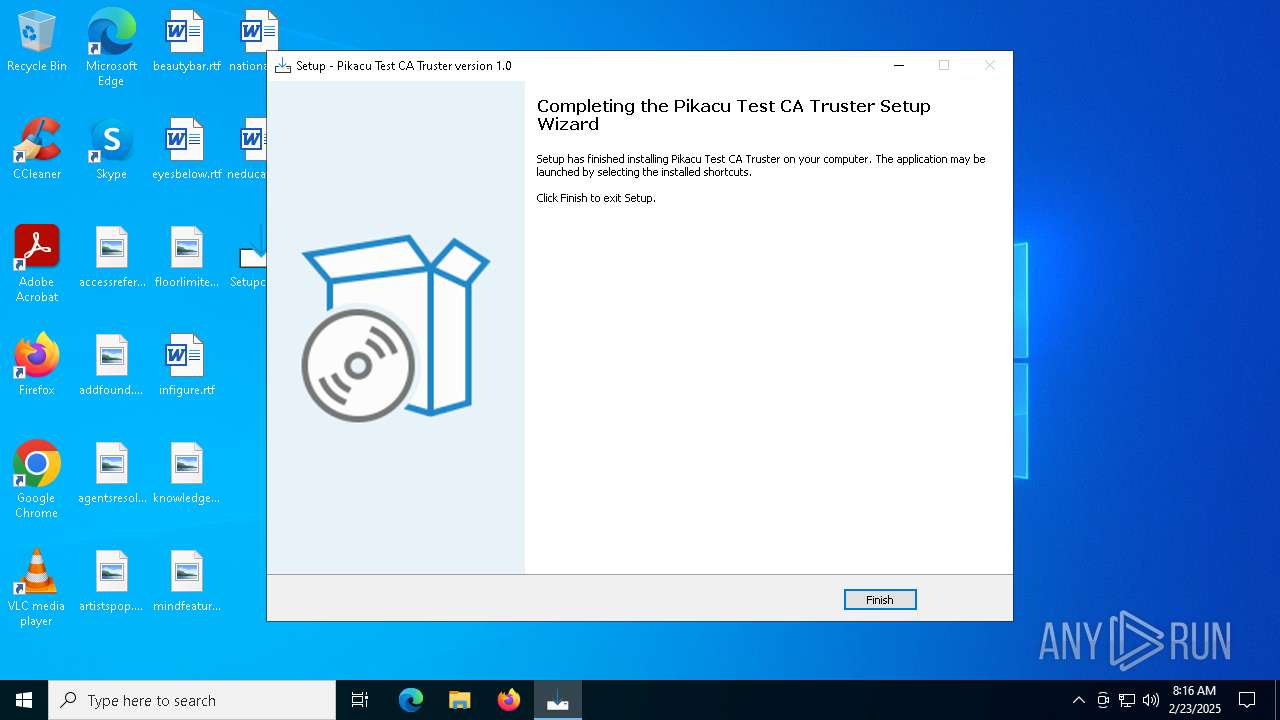
Creates a software uninstall entry
- Setupca.tmp (PID: 6248)
The sample compiled with english language support
- Setupca.tmp (PID: 6248)
- WinRAR.exe (PID: 4968)
Creates files in the program directory
- Setupca.tmp (PID: 6248)
Starts MODE.COM to configure console settings
- mode.com (PID: 6704)
Detects InnoSetup installer (YARA)
- Setupca.exe (PID: 1616)
- Setupca.tmp (PID: 1488)
- Setupca.tmp (PID: 6248)
- Setupca.exe (PID: 6220)
Reads the machine GUID from the registry
- Certmgr.exe (PID: 6752)
- Certmgr.exe (PID: 6780)
- Certmgr.exe (PID: 6808)
- Certmgr.exe (PID: 6912)
- Certmgr.exe (PID: 6944)
- Certmgr.exe (PID: 6972)
- Certmgr.exe (PID: 7000)
- Certmgr.exe (PID: 6848)
- Certmgr.exe (PID: 6880)
- Certmgr.exe (PID: 7032)
- Certmgr.exe (PID: 7064)
- Certmgr.exe (PID: 7096)
- Certmgr.exe (PID: 7128)
- Certmgr.exe (PID: 7156)
- Certmgr.exe (PID: 6180)
- Certmgr.exe (PID: 2380)
- Certmgr.exe (PID: 2324)
- Certmgr.exe (PID: 4556)
- Certmgr.exe (PID: 4444)
- Certmgr.exe (PID: 4980)
- Certmgr.exe (PID: 4512)
- Certmgr.exe (PID: 5252)
- Certmgr.exe (PID: 4120)
- Certmgr.exe (PID: 4320)
- Certmgr.exe (PID: 5728)
- Certmgr.exe (PID: 3928)
- Certmgr.exe (PID: 2408)
- Certmgr.exe (PID: 2160)
- Certmgr.exe (PID: 244)
- Certmgr.exe (PID: 6724)
- Certmgr.exe (PID: 6728)
- Certmgr.exe (PID: 6752)
- Certmgr.exe (PID: 6824)
- Certmgr.exe (PID: 6664)
- Certmgr.exe (PID: 6896)
- Certmgr.exe (PID: 6928)
- Certmgr.exe (PID: 6912)
- Certmgr.exe (PID: 6944)
- Certmgr.exe (PID: 6864)
- Certmgr.exe (PID: 7056)
- Certmgr.exe (PID: 7072)
- Certmgr.exe (PID: 7108)
- Certmgr.exe (PID: 7016)
- Certmgr.exe (PID: 6200)
- Certmgr.exe (PID: 1596)
- Certmgr.exe (PID: 4544)
- Certmgr.exe (PID: 7140)
- Certmgr.exe (PID: 6192)
- Certmgr.exe (PID: 2600)
- Certmgr.exe (PID: 4244)
- Certmgr.exe (PID: 5740)
- Certmgr.exe (PID: 5460)
- Certmgr.exe (PID: 6132)
- Certmgr.exe (PID: 5560)
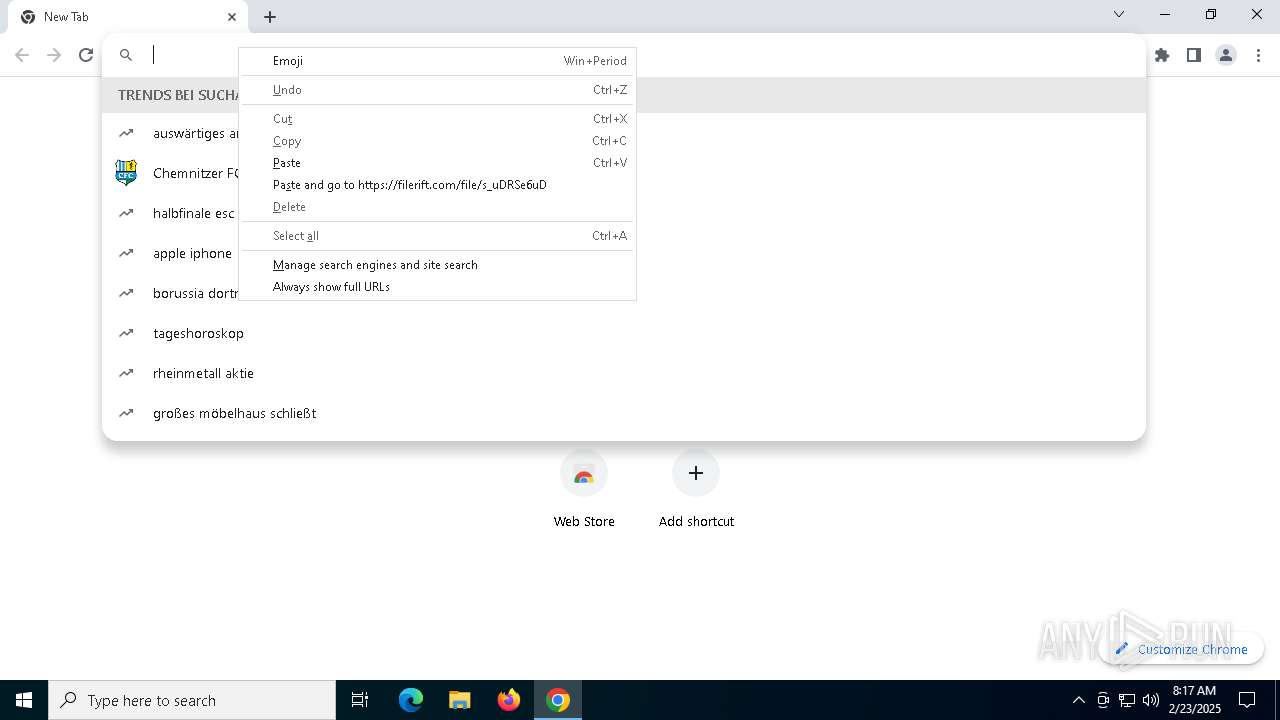
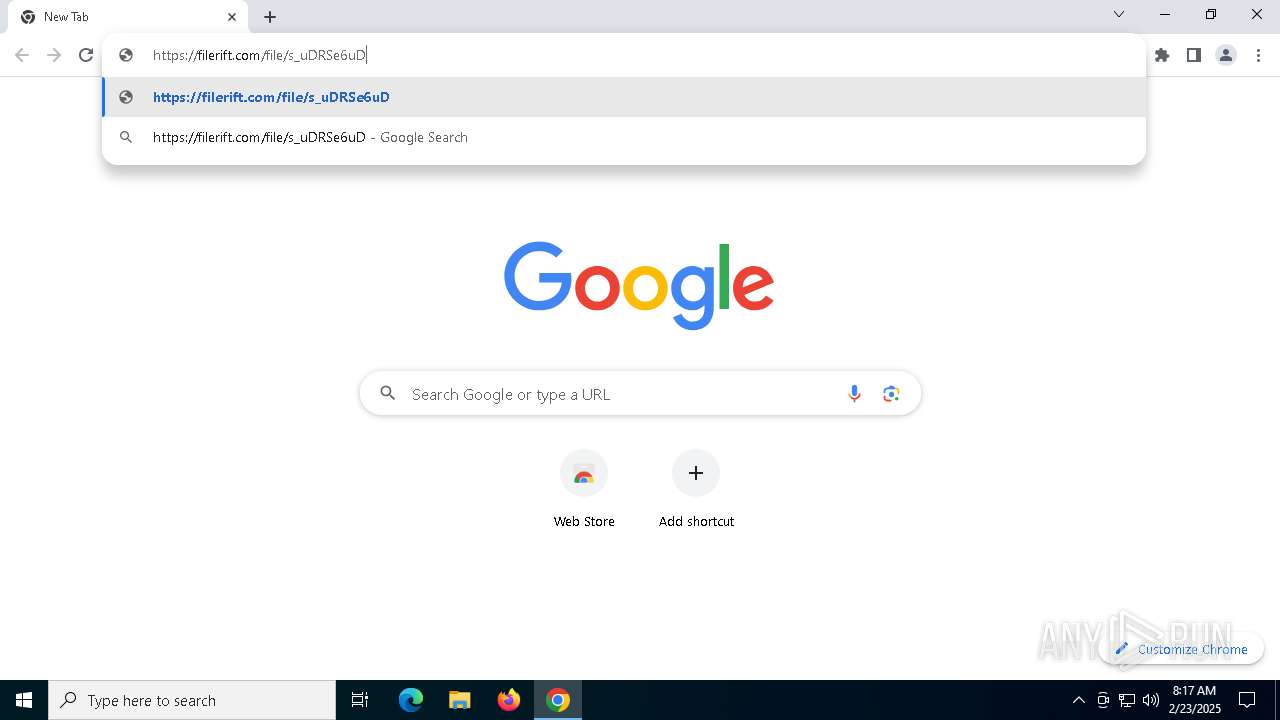
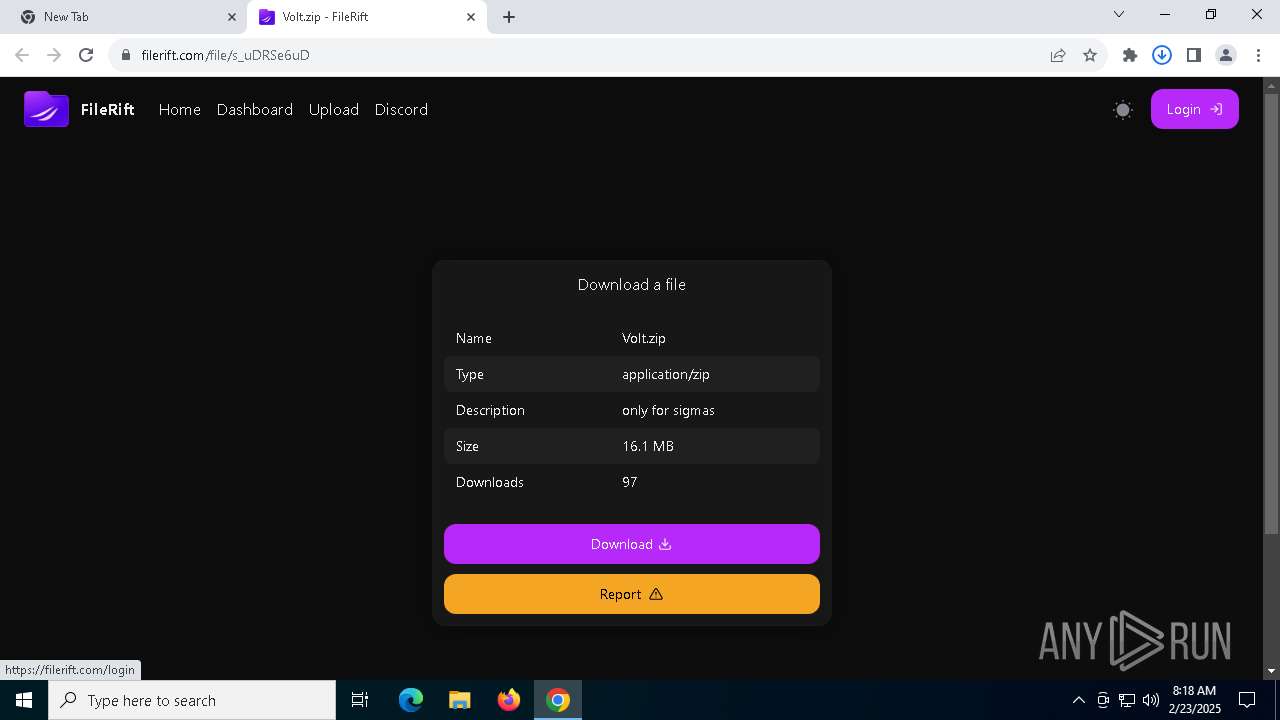
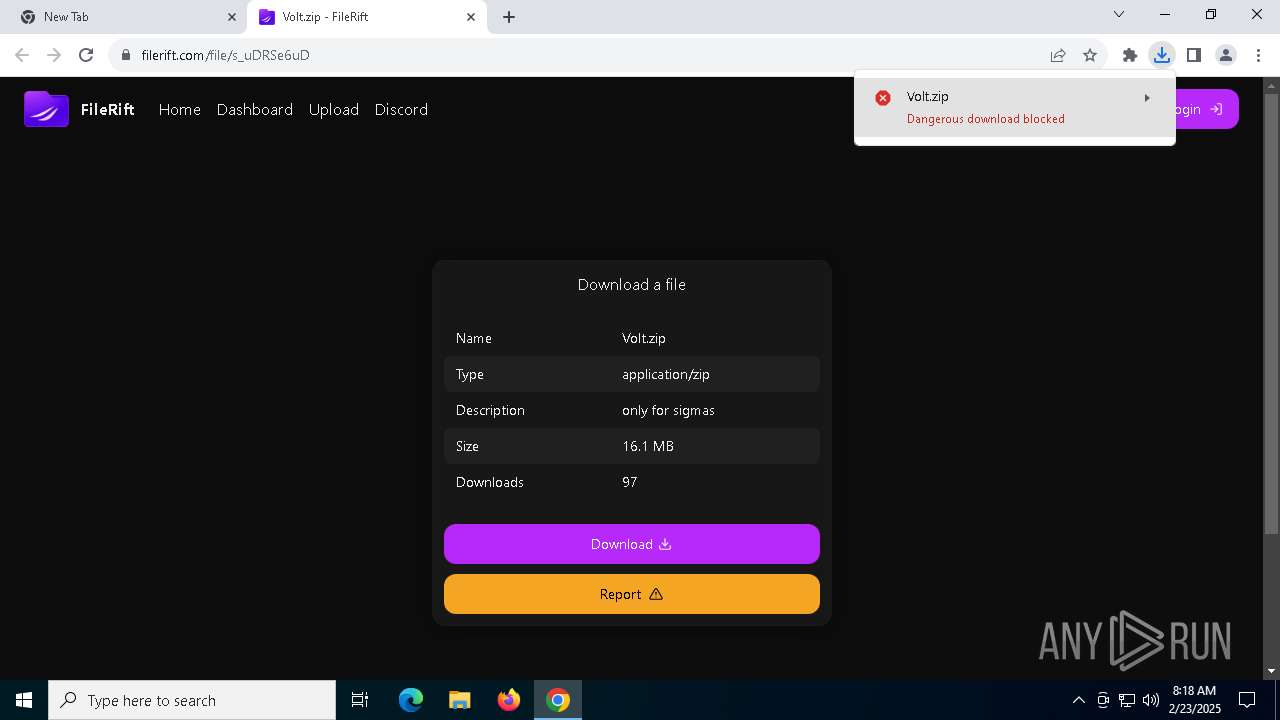
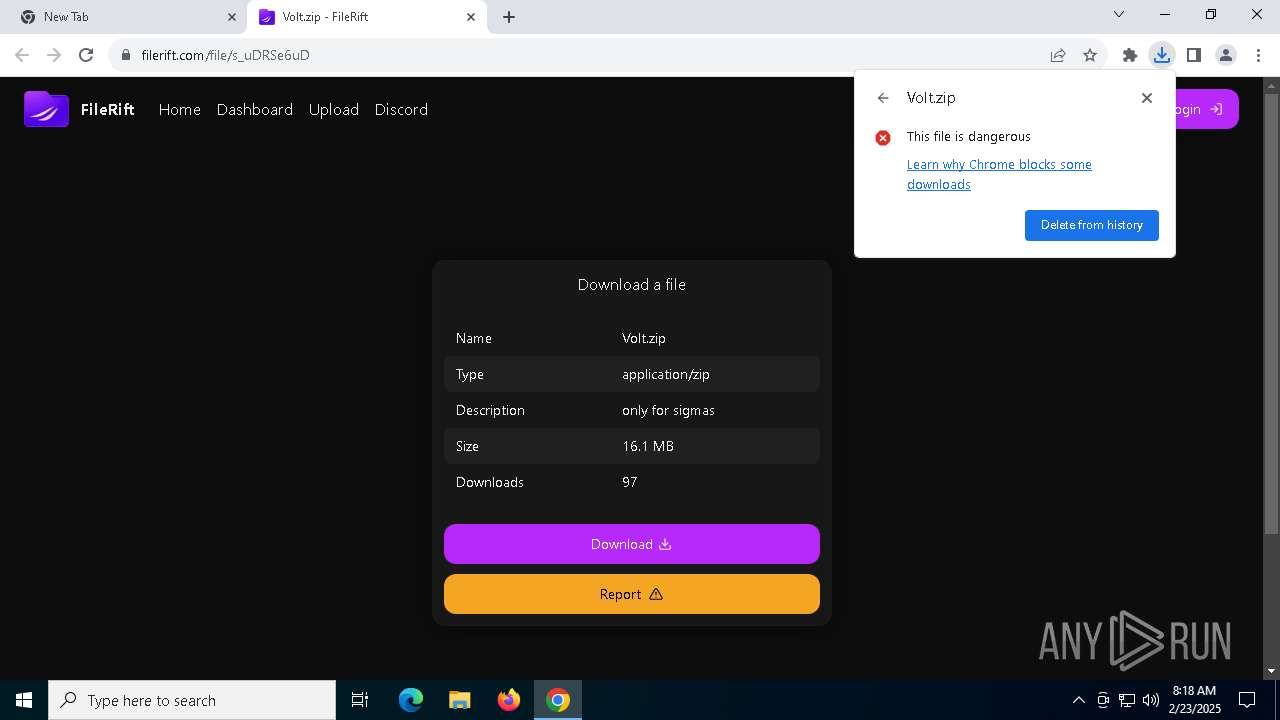
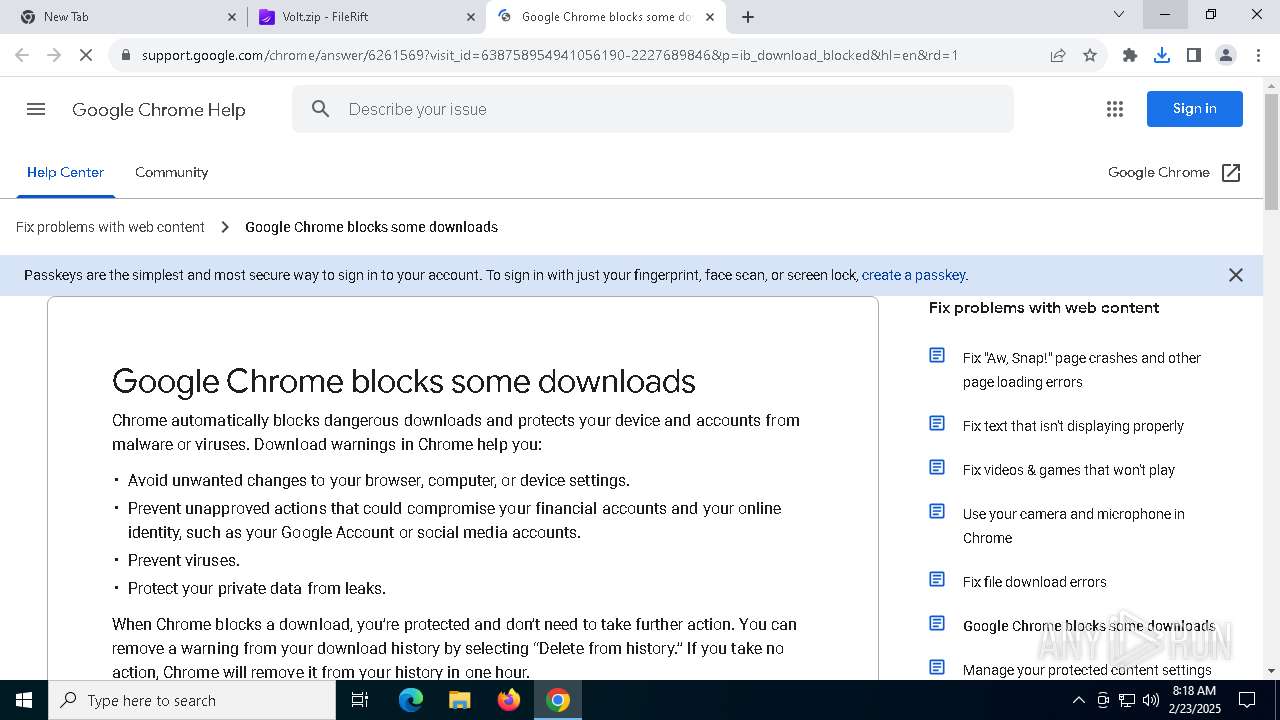
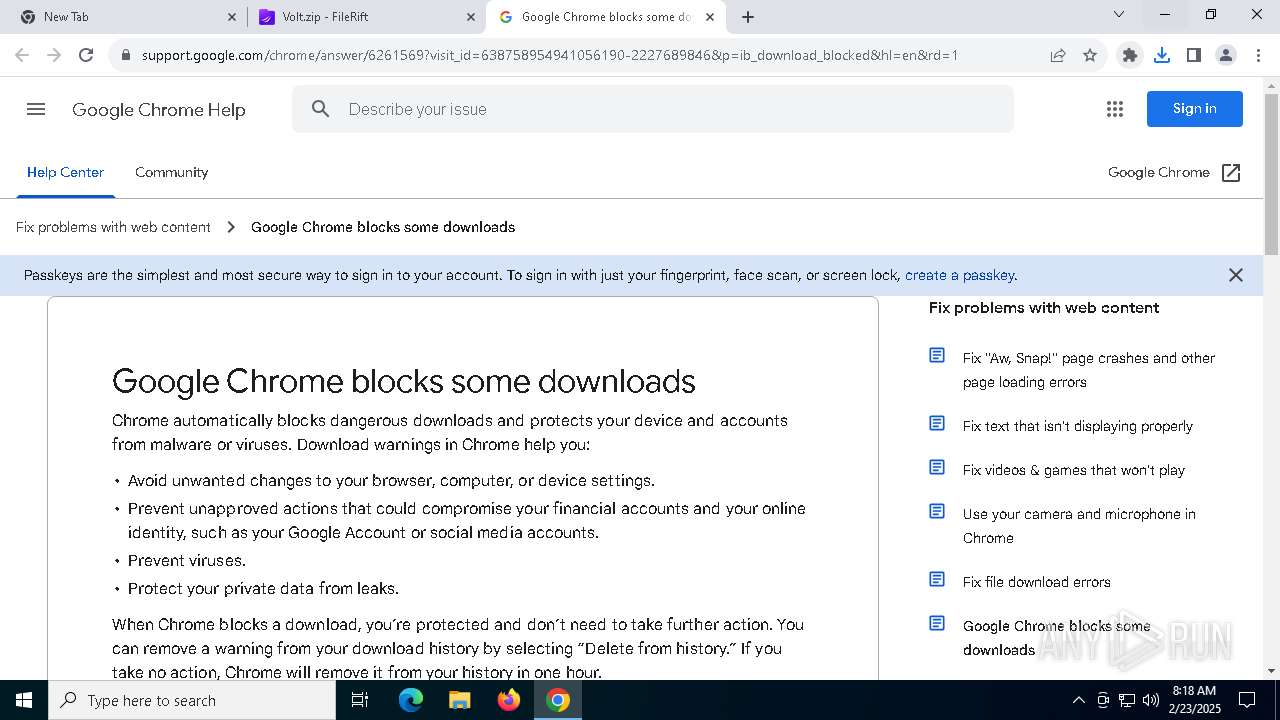
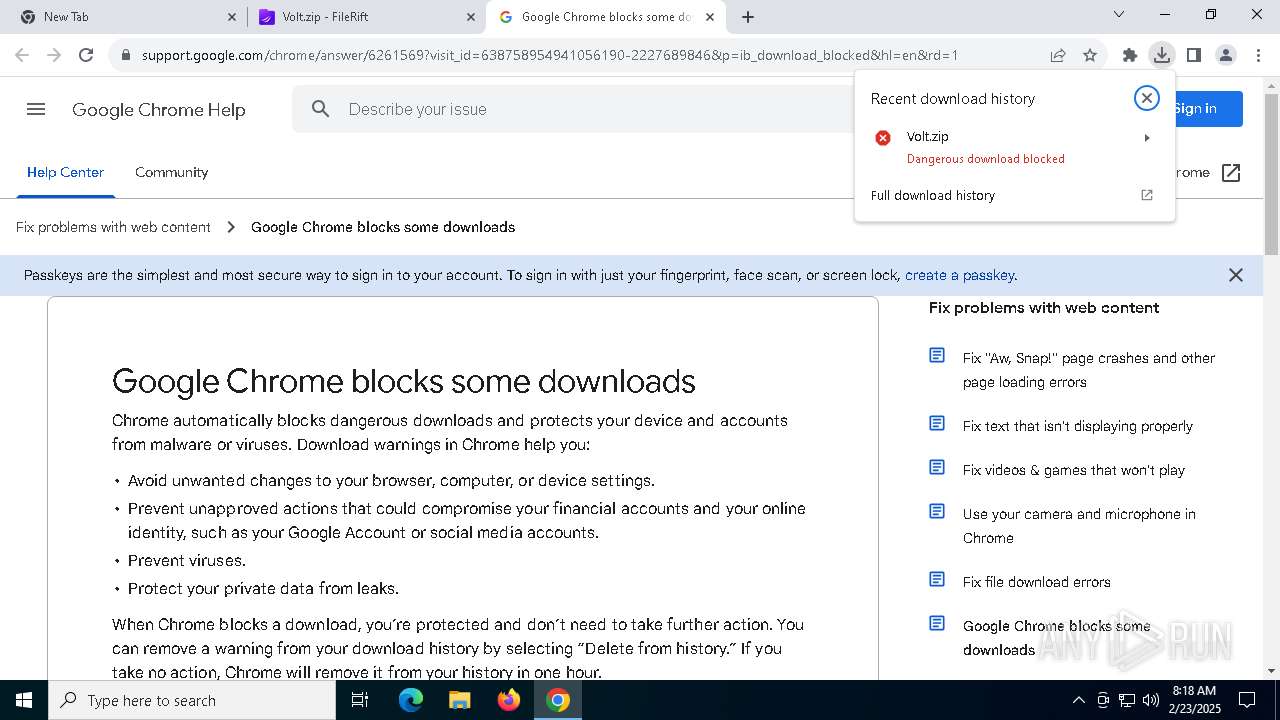
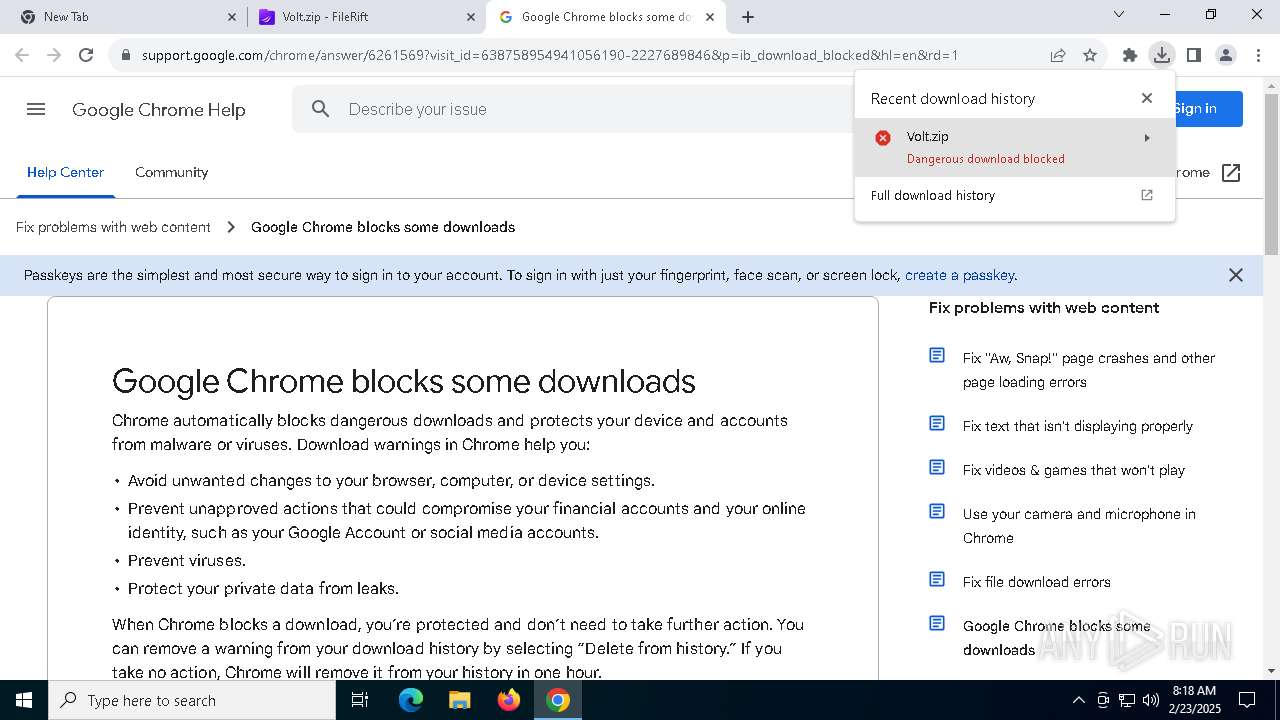
Application launched itself
- chrome.exe (PID: 5268)
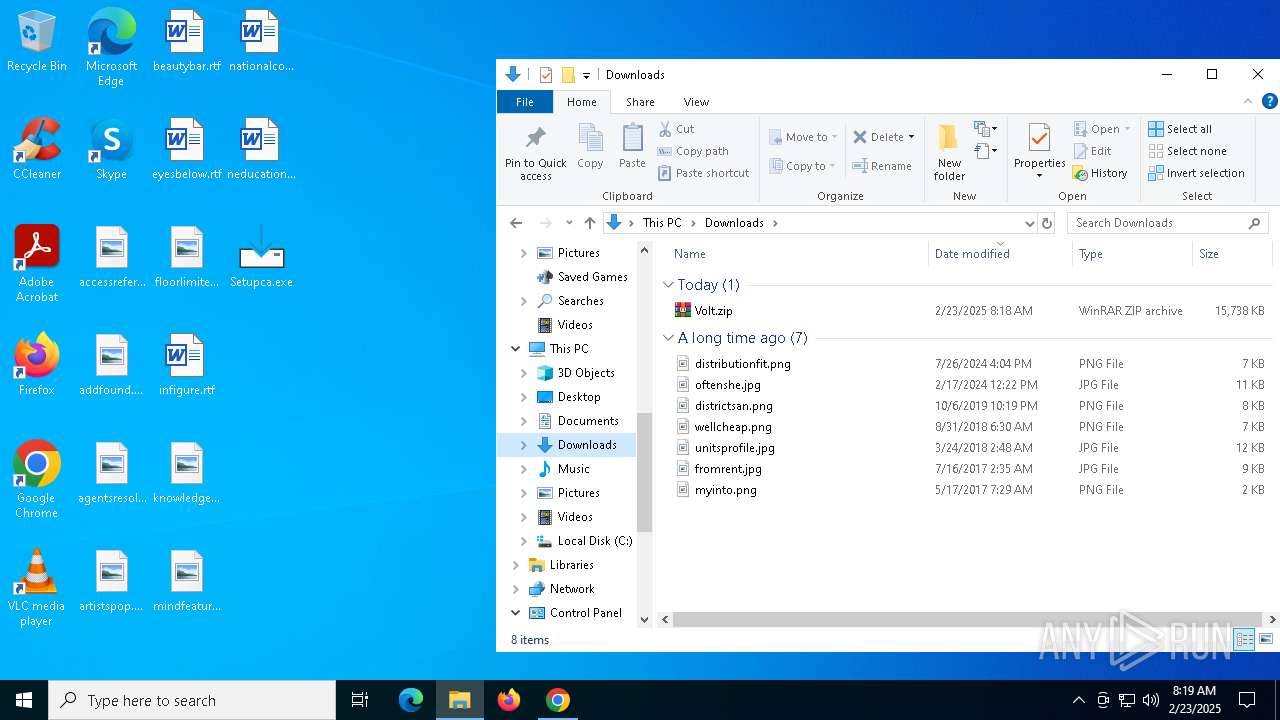
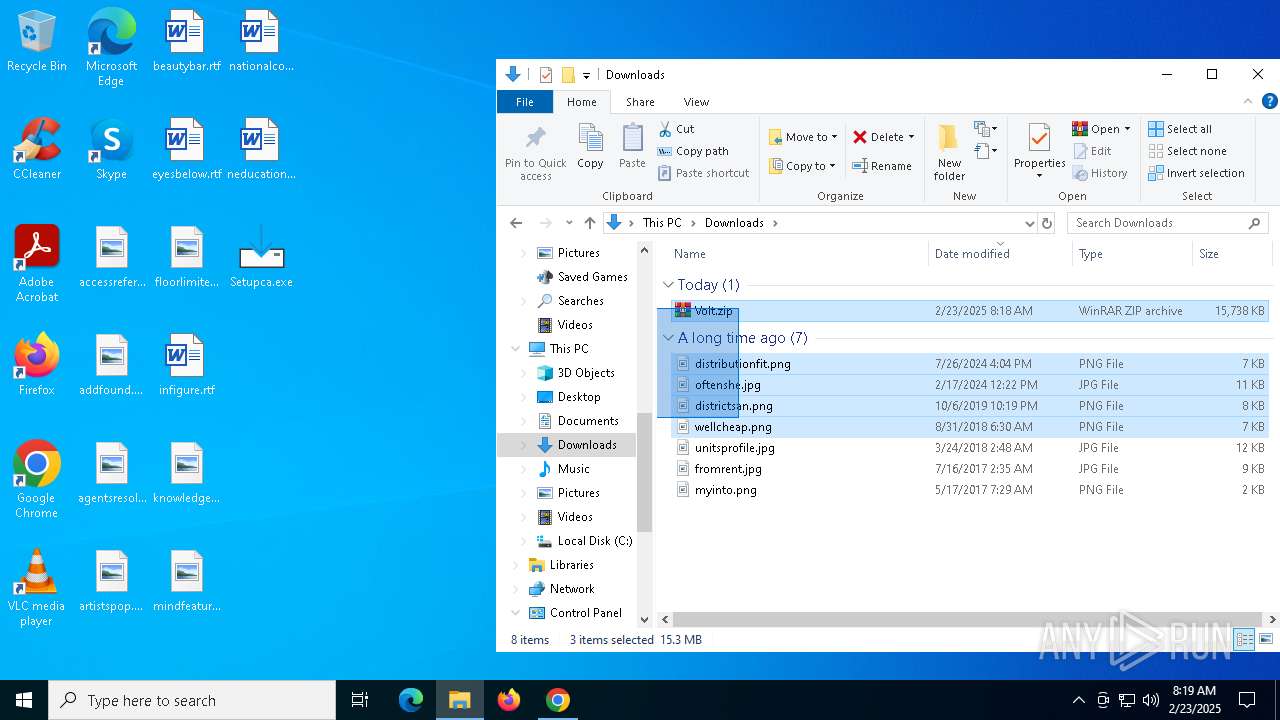
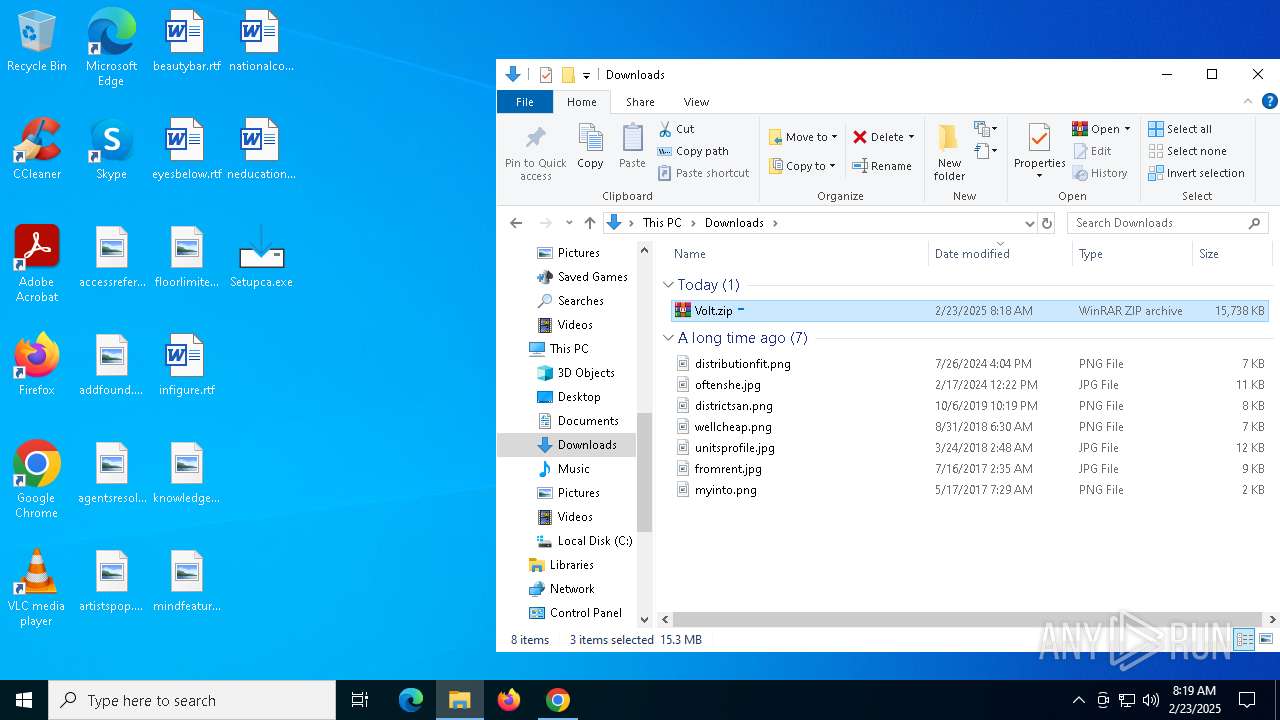
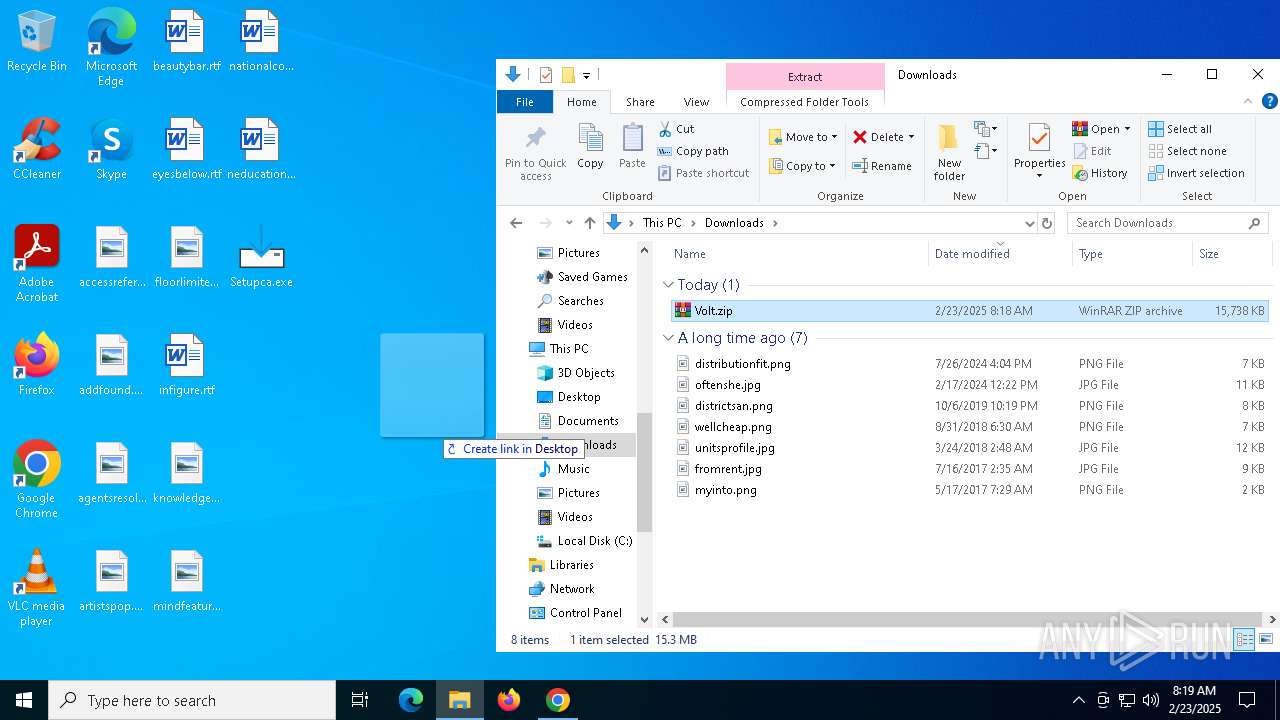
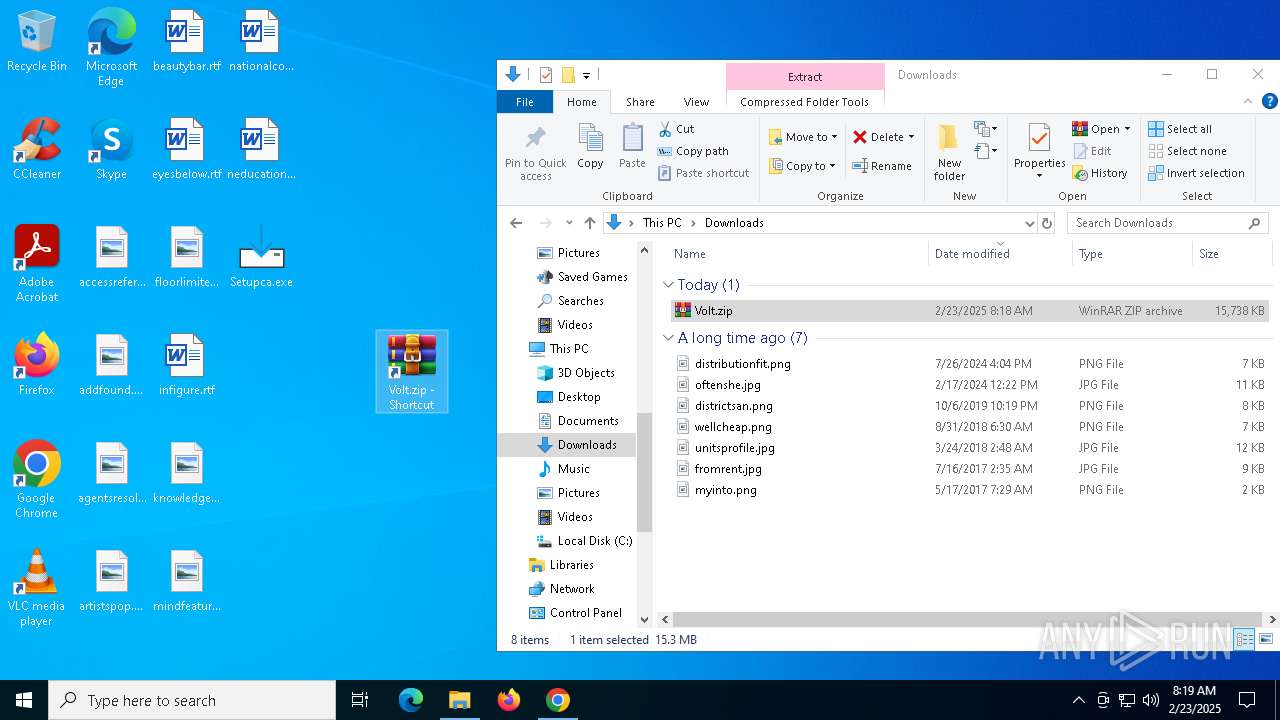
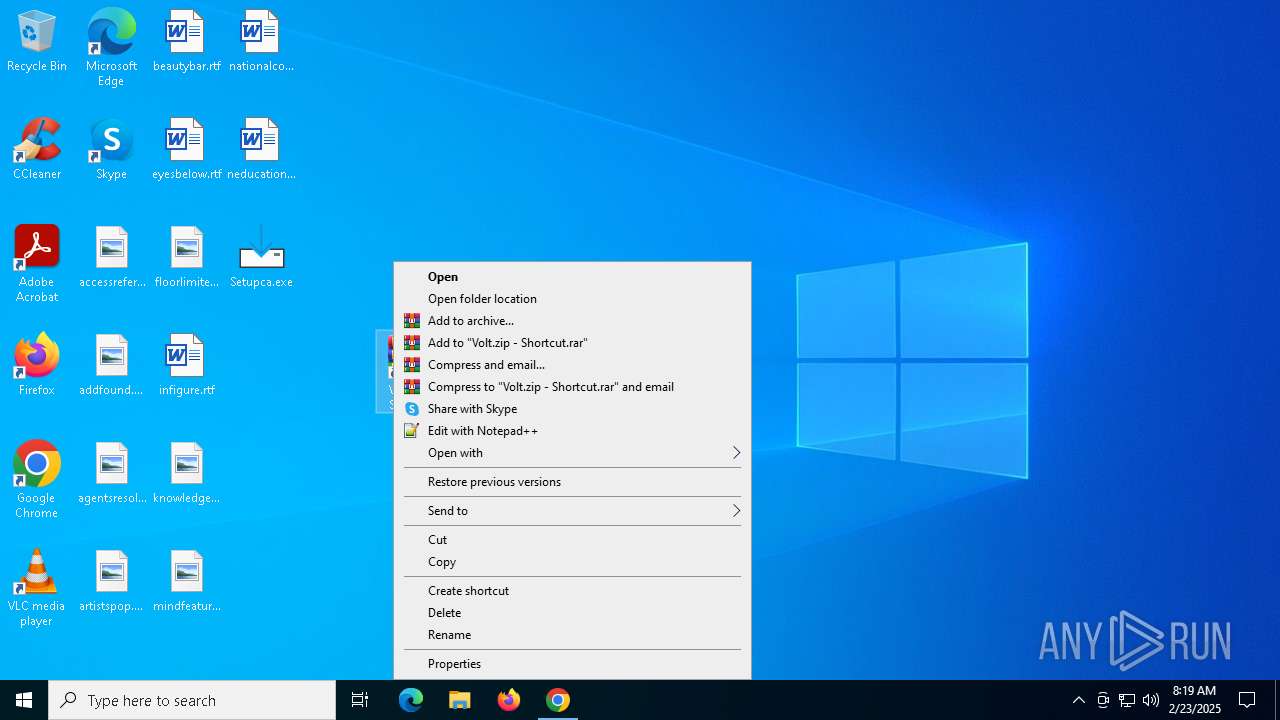
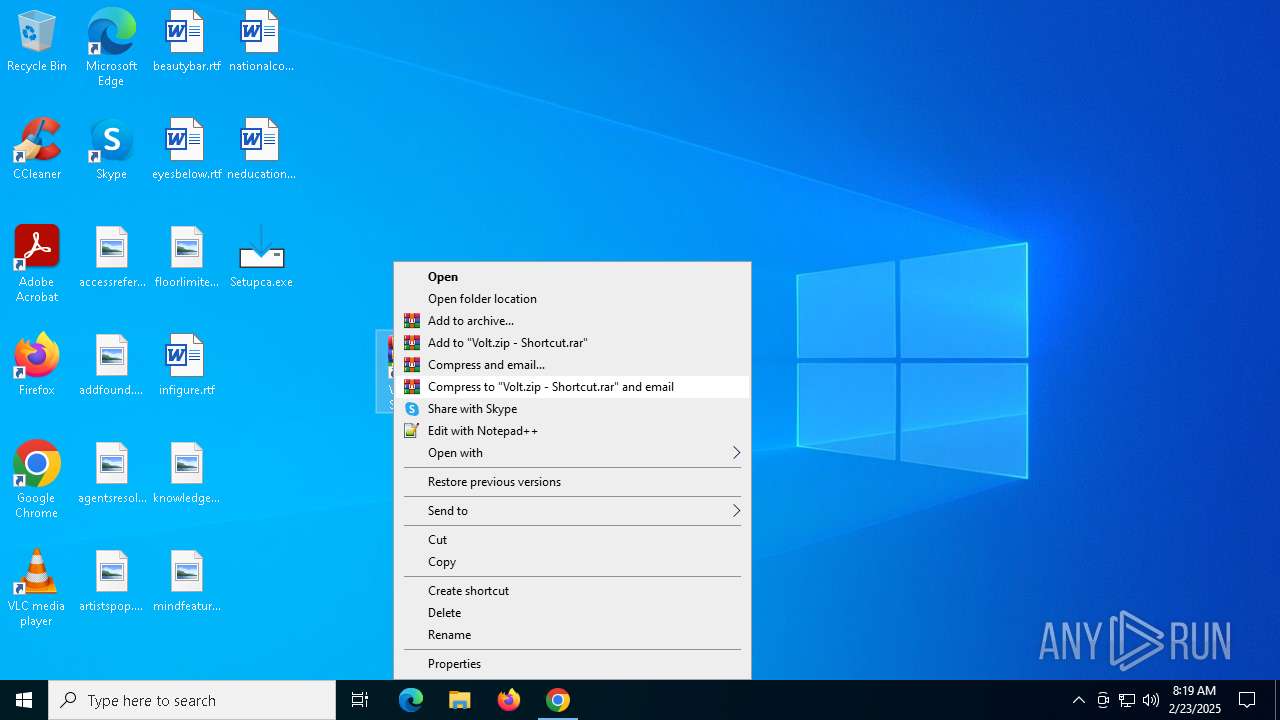
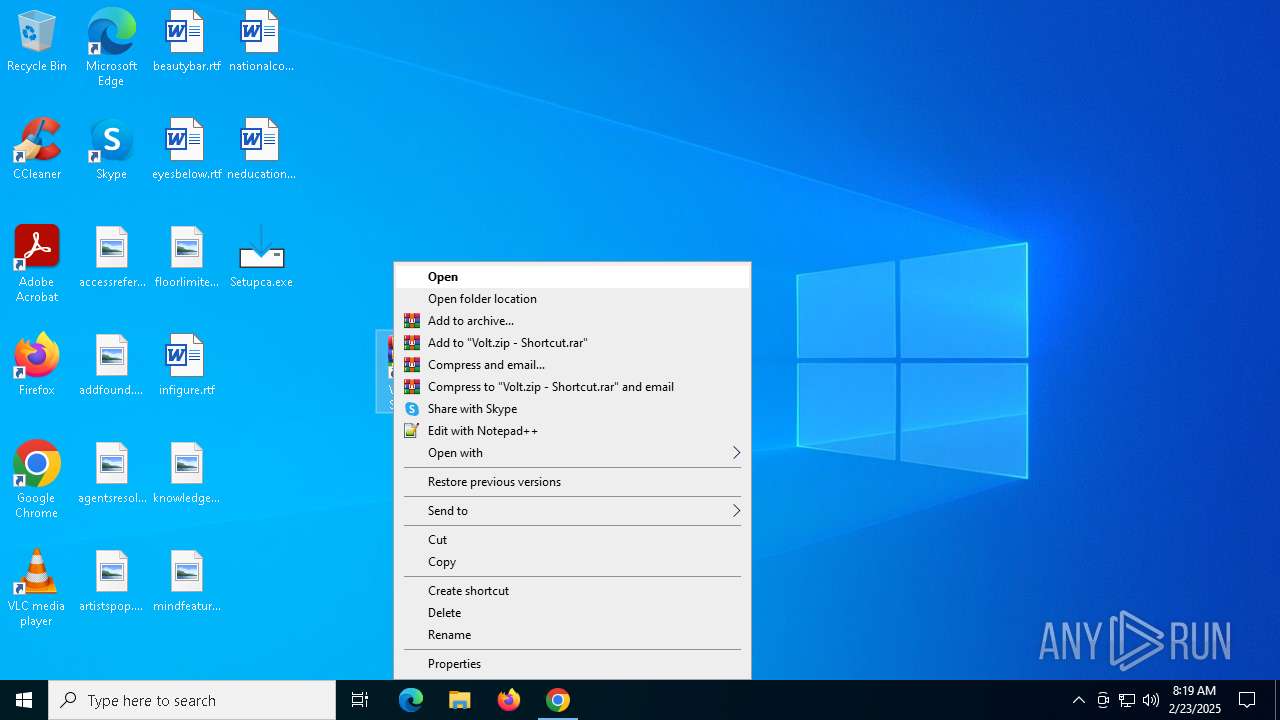
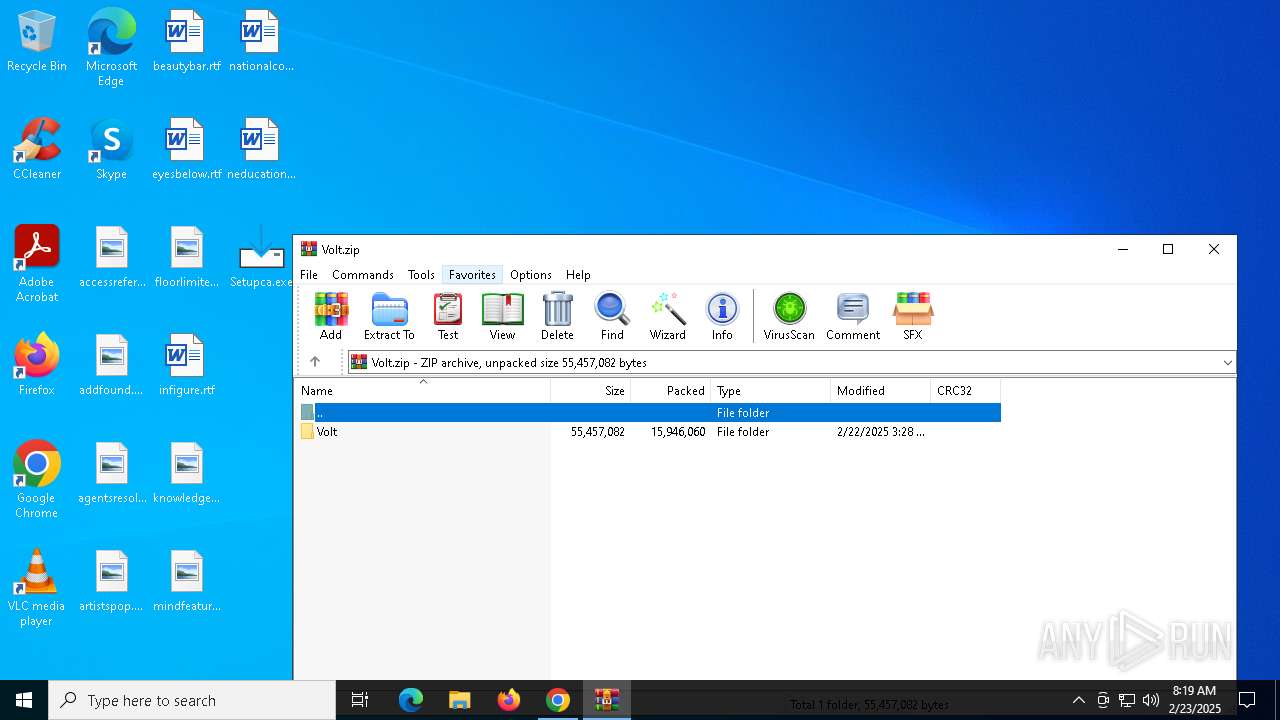
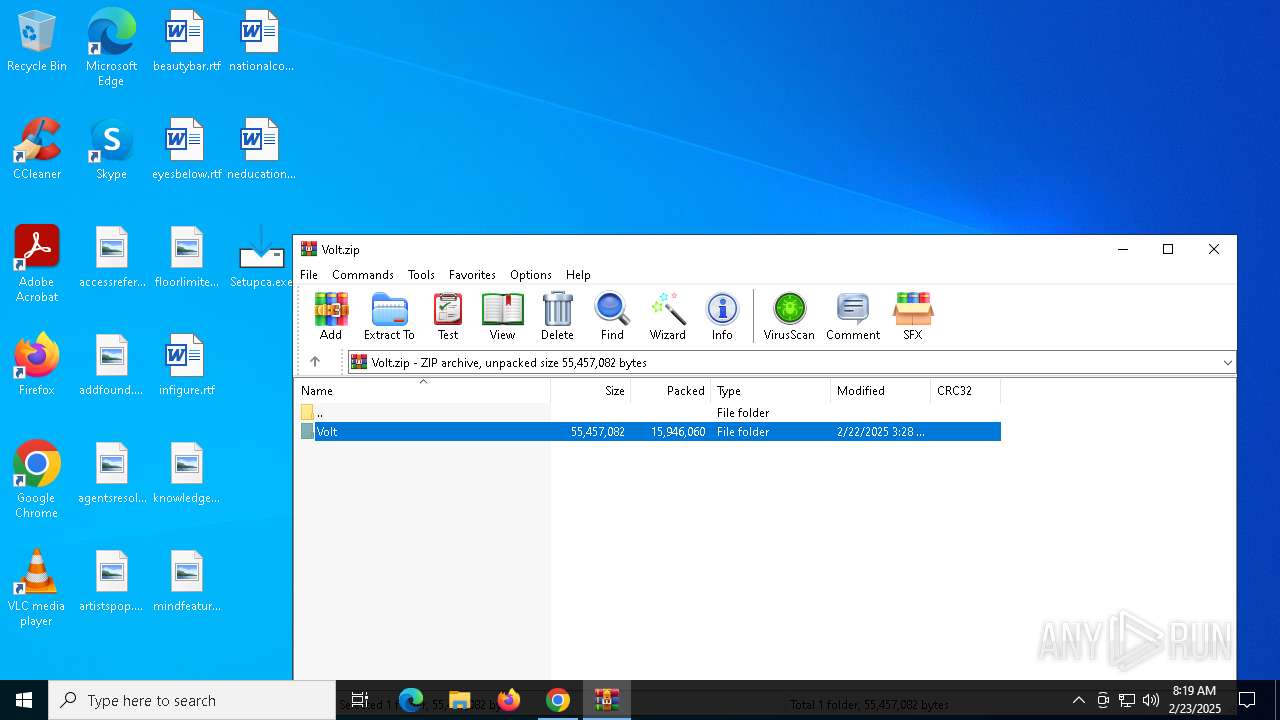
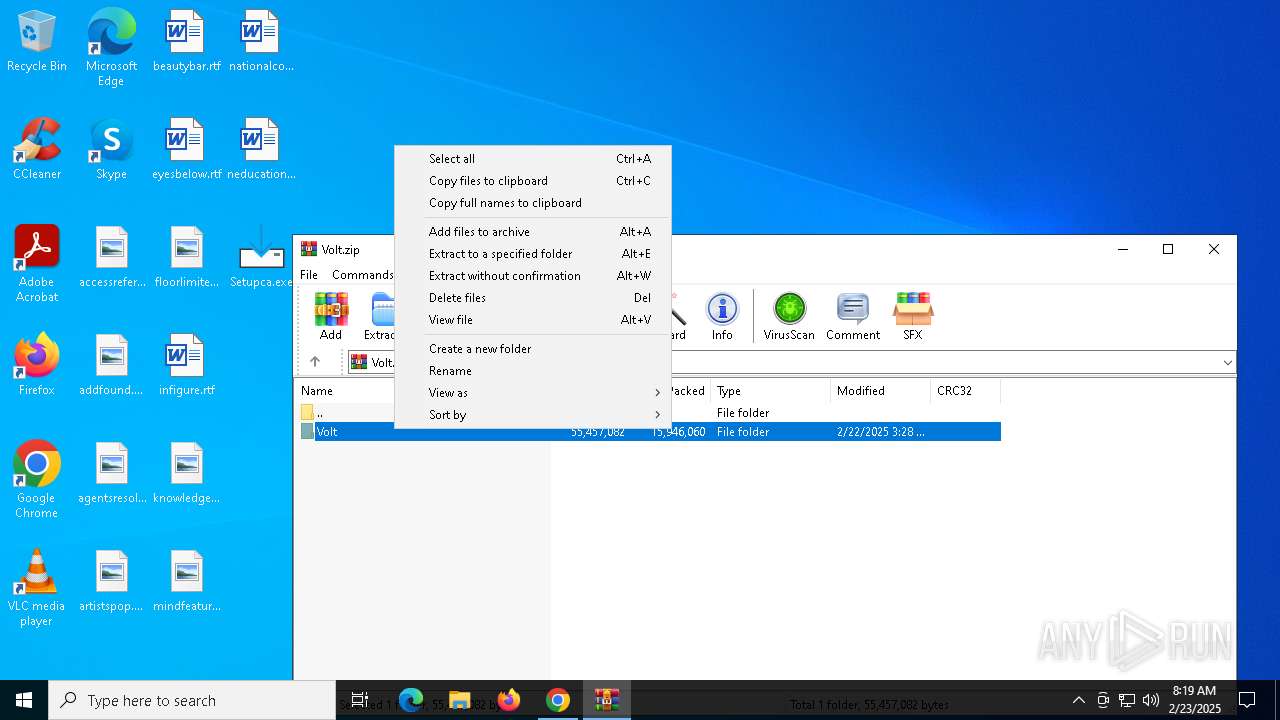
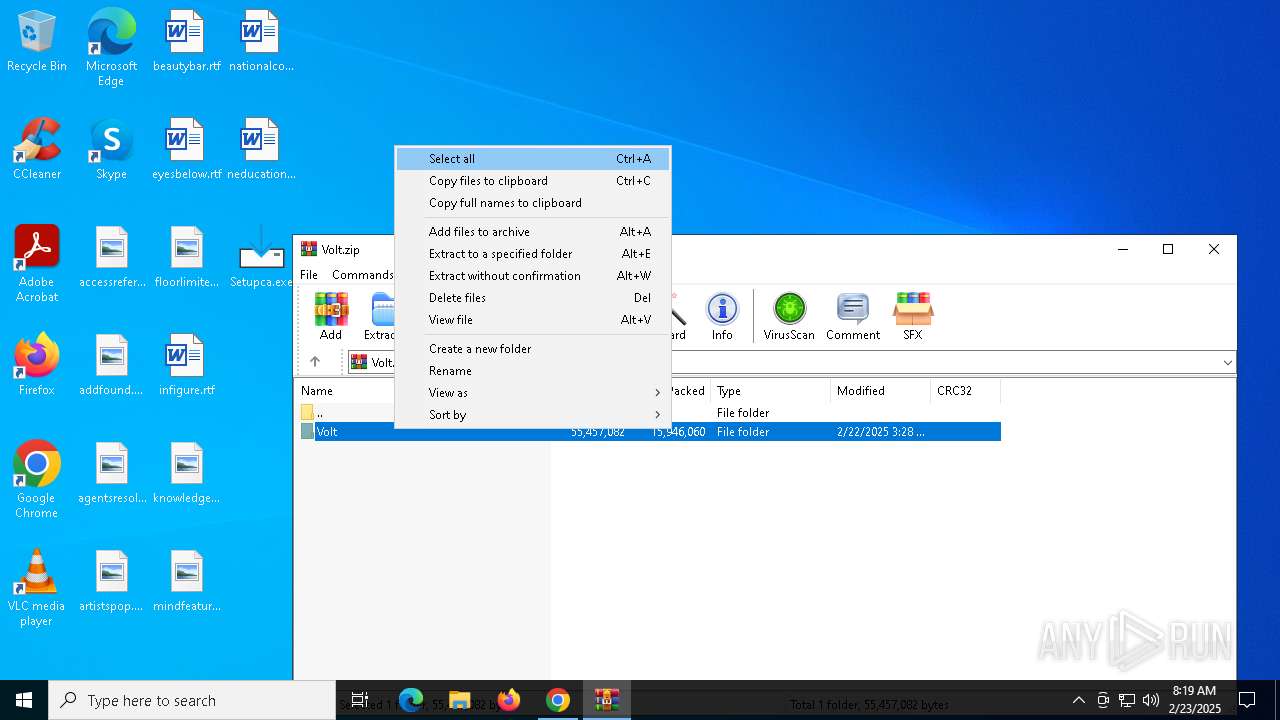
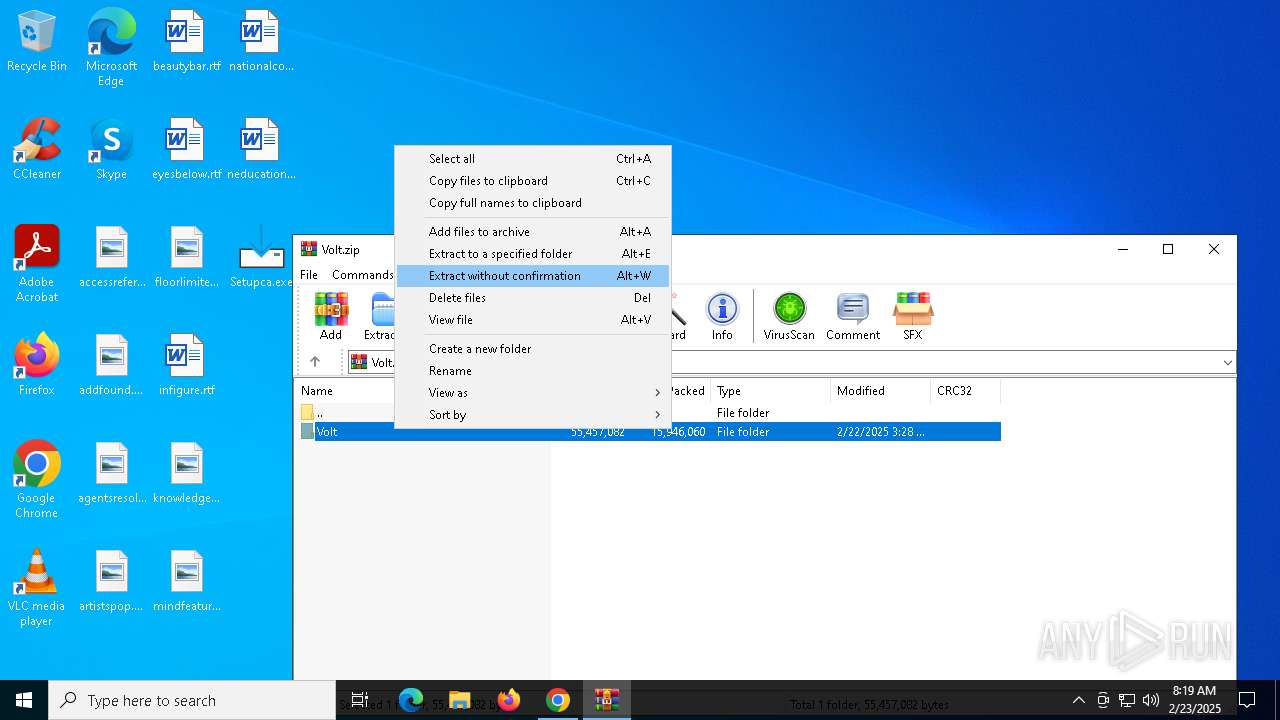
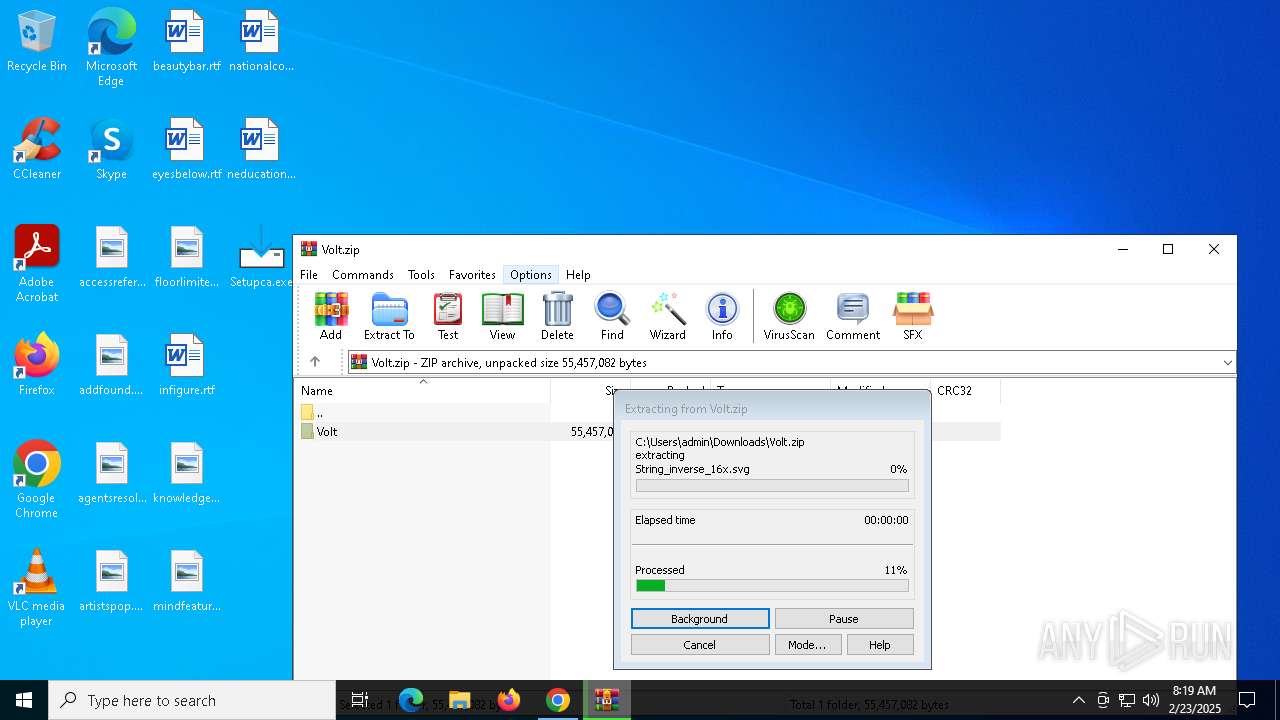
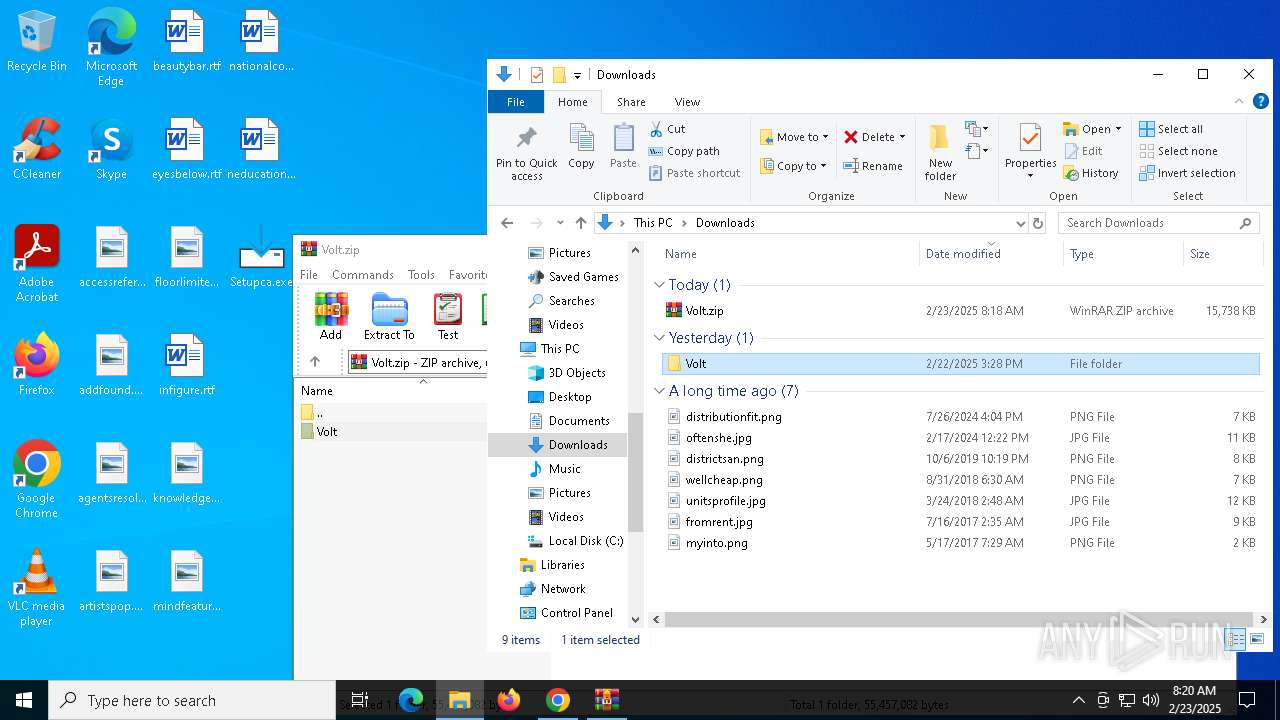
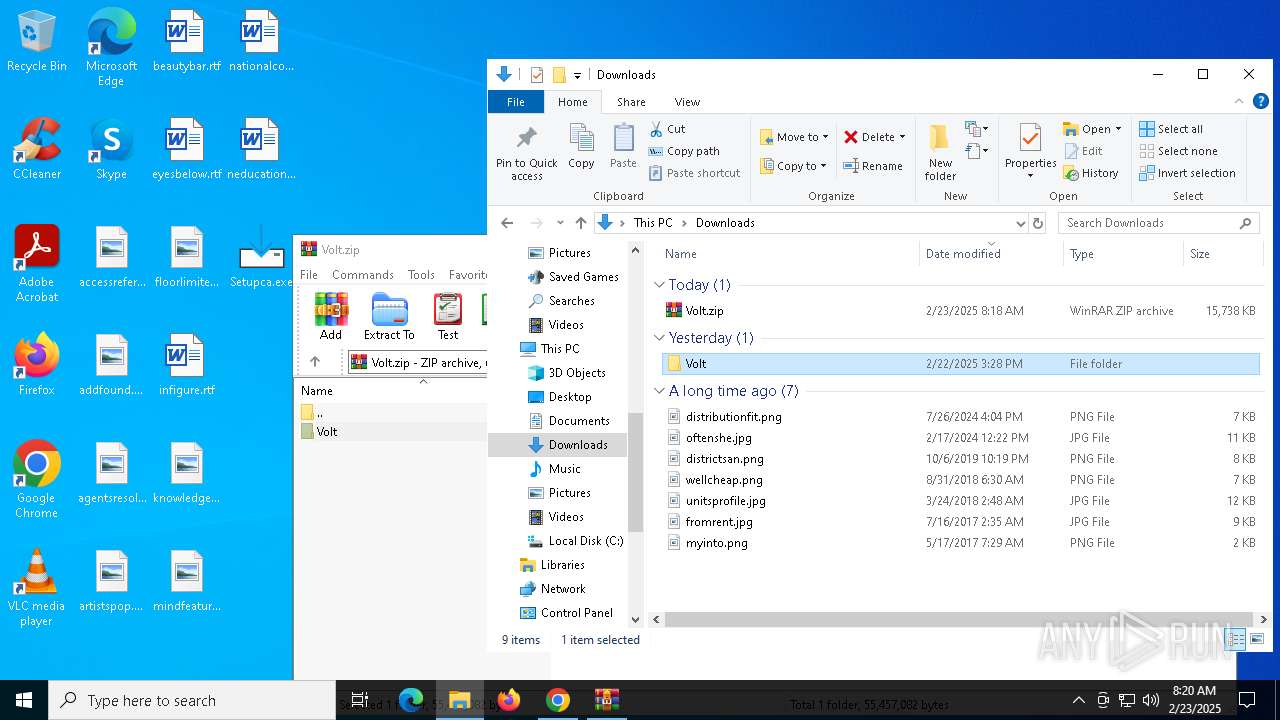
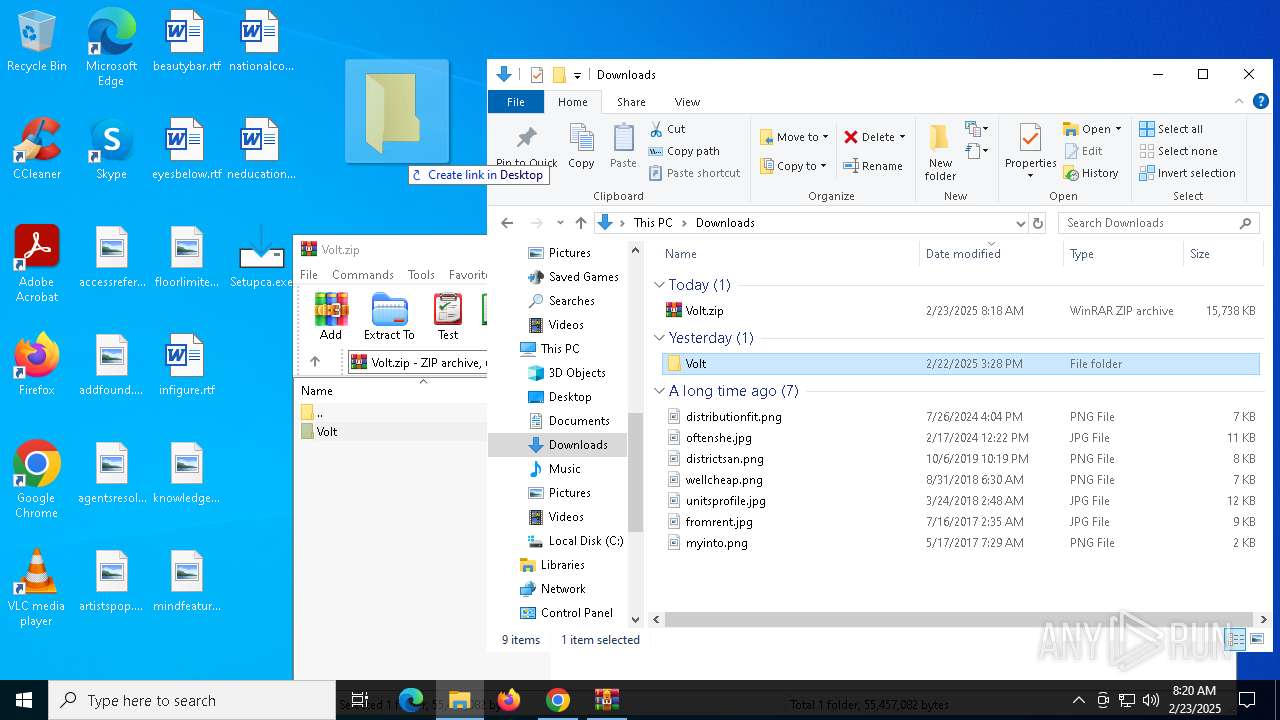
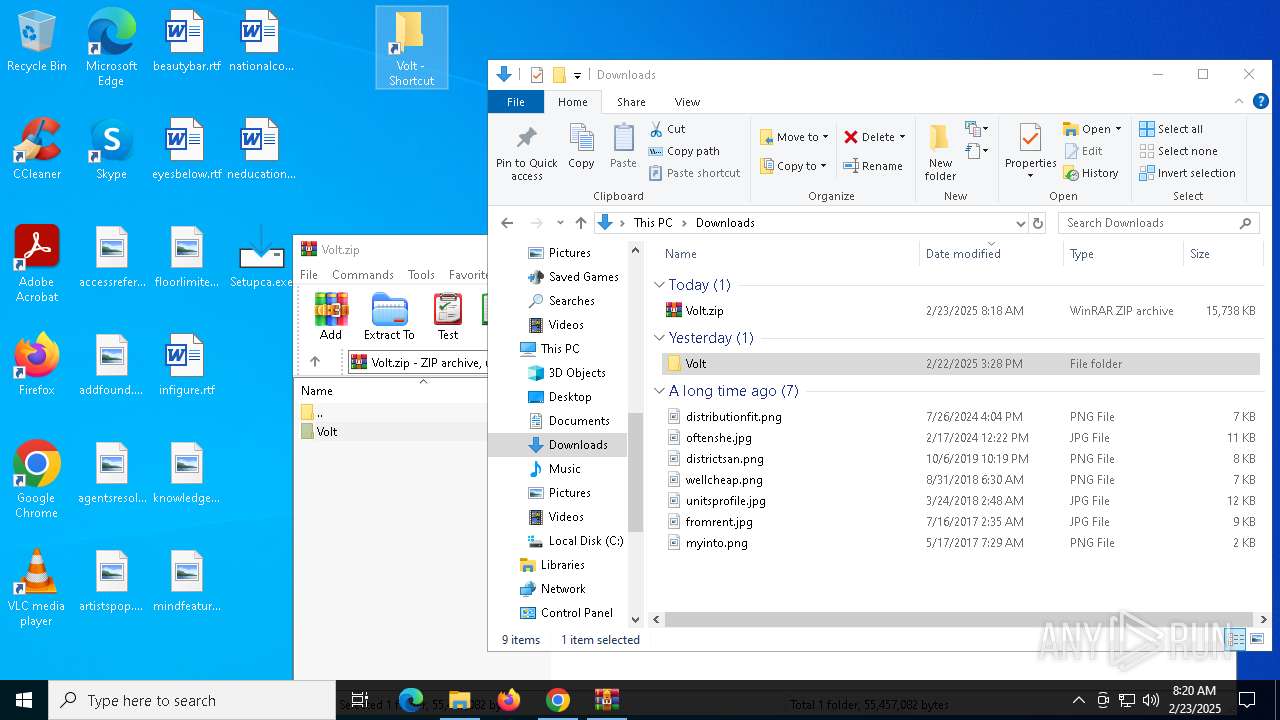
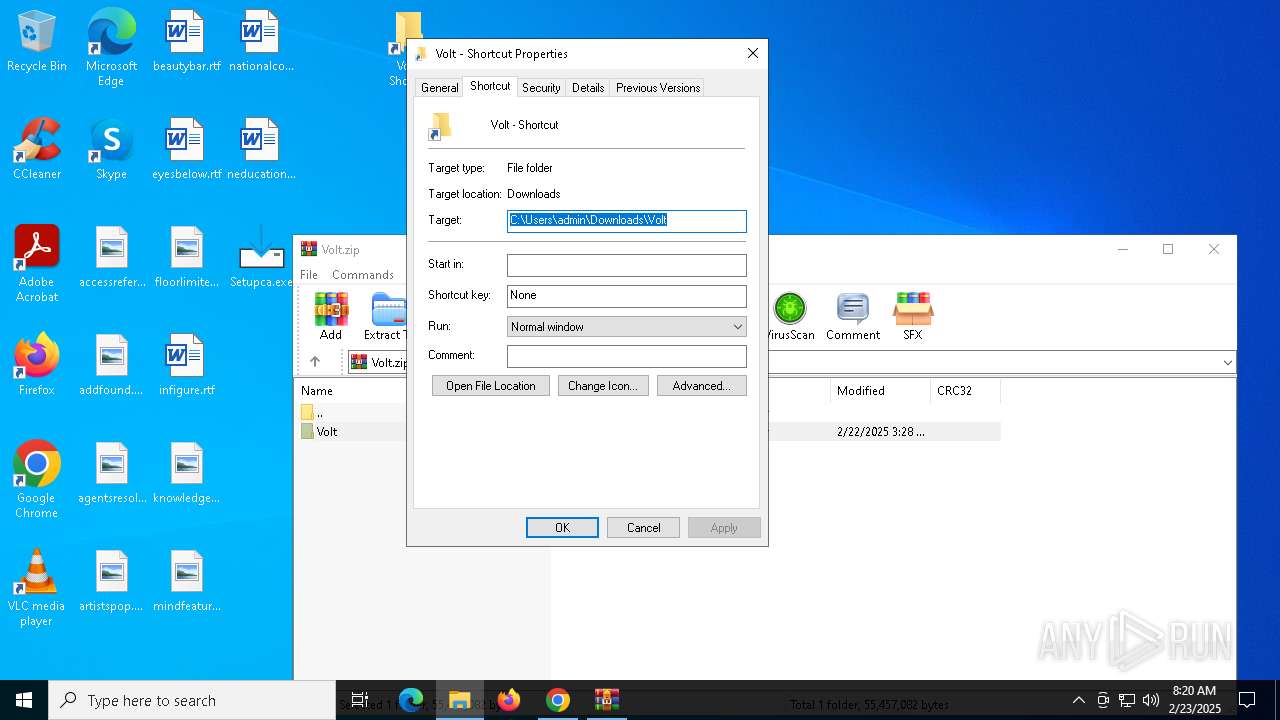
Manual execution by a user
- chrome.exe (PID: 5268)
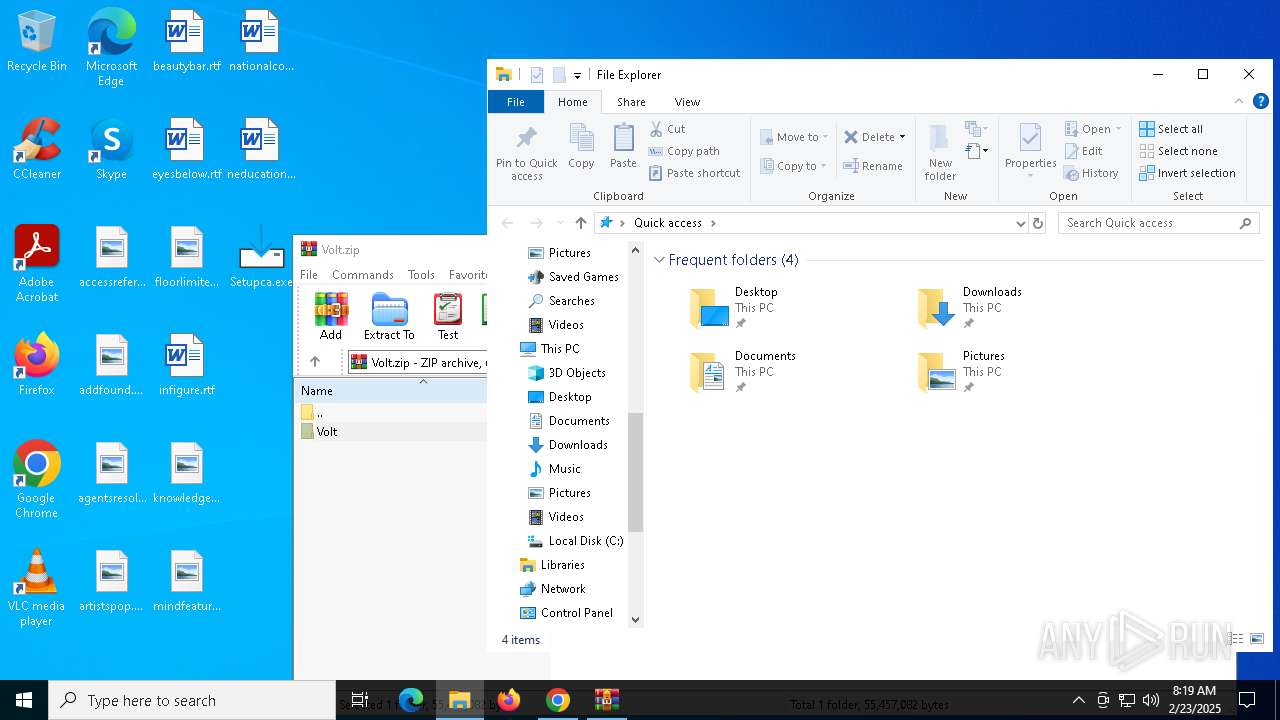
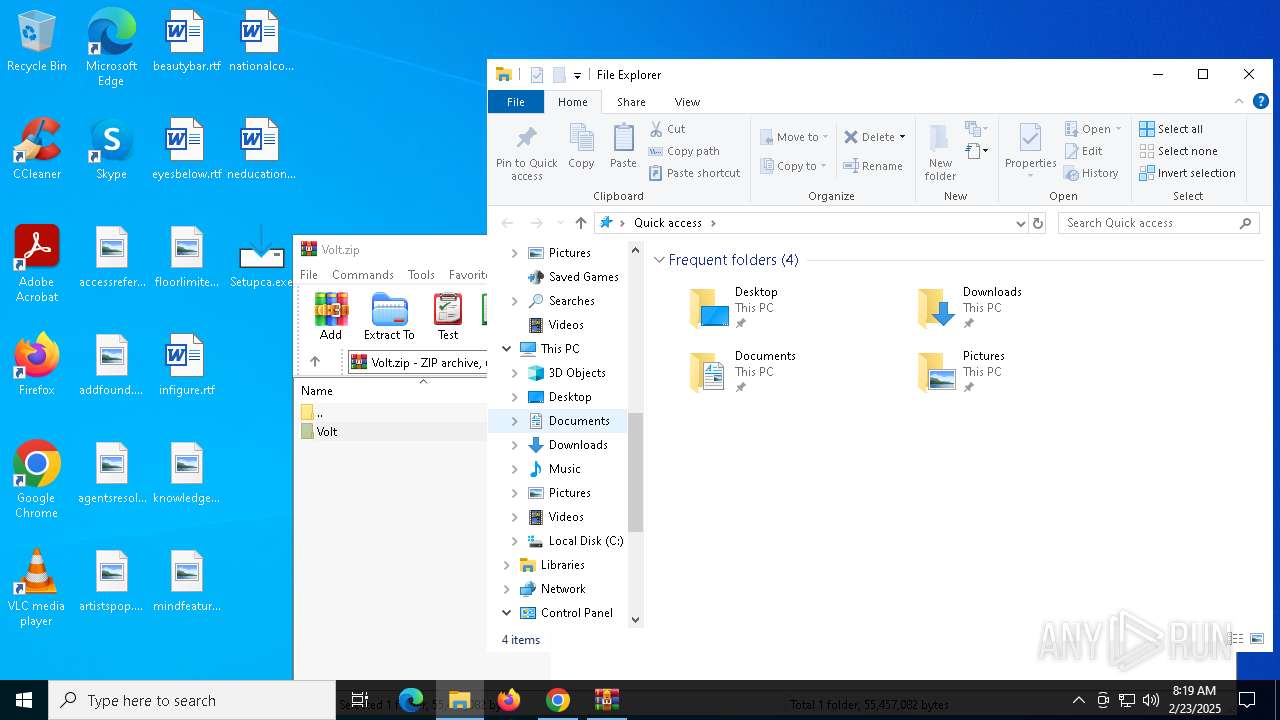
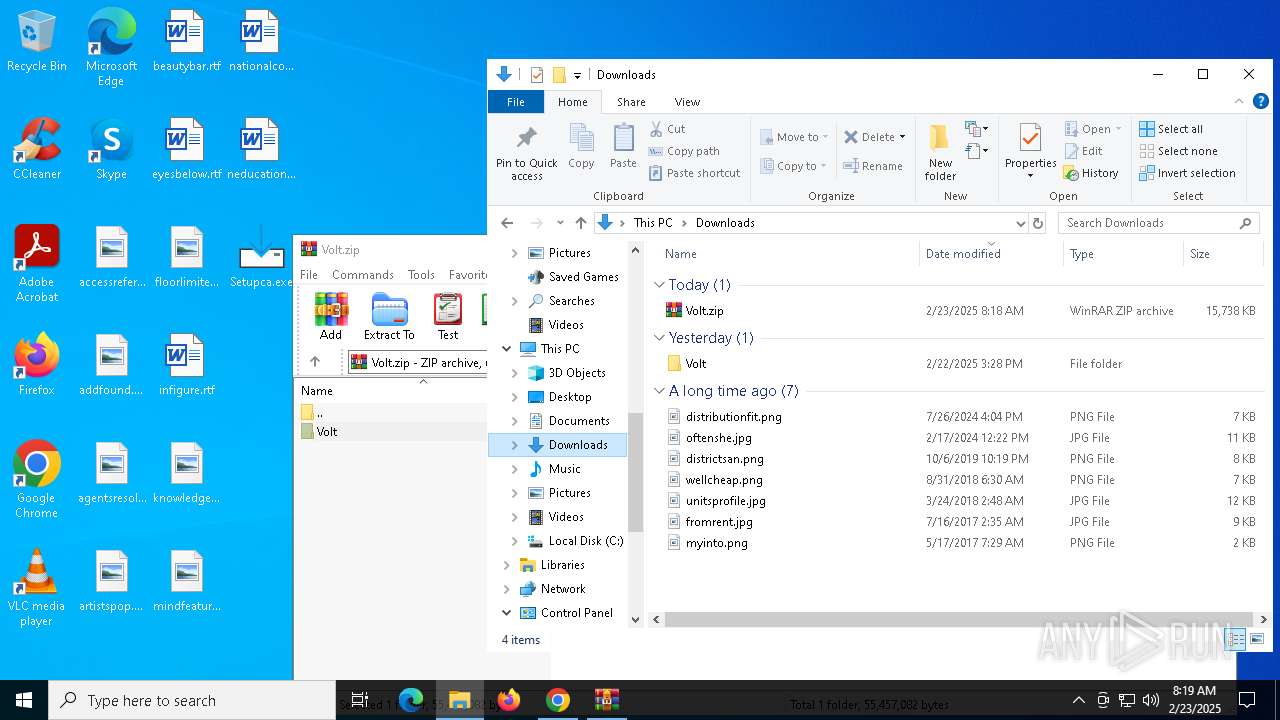
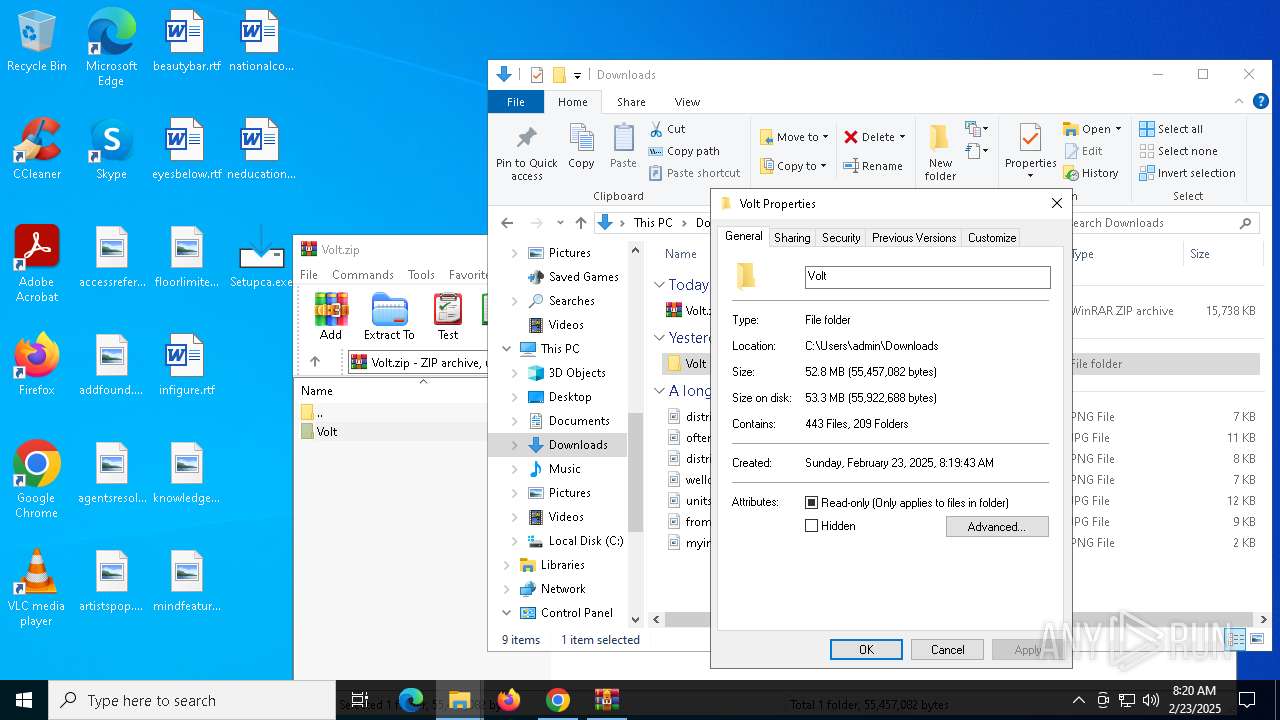
- WinRAR.exe (PID: 4968)
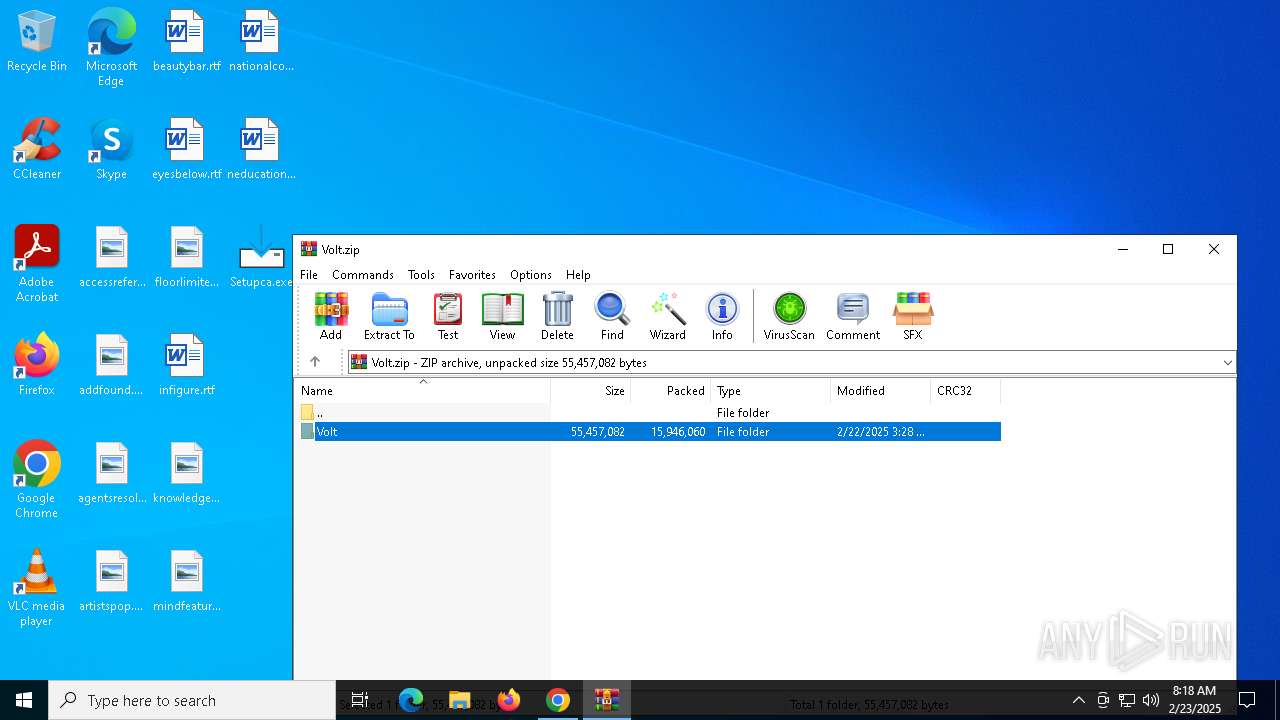
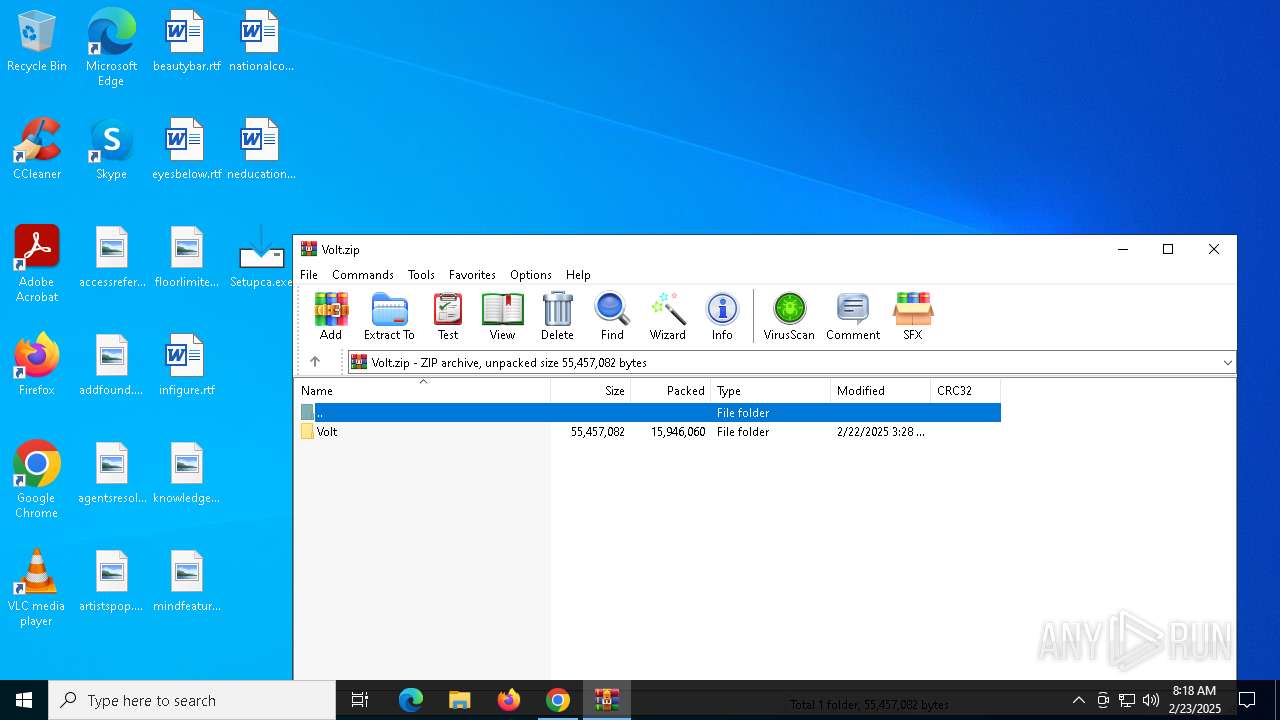
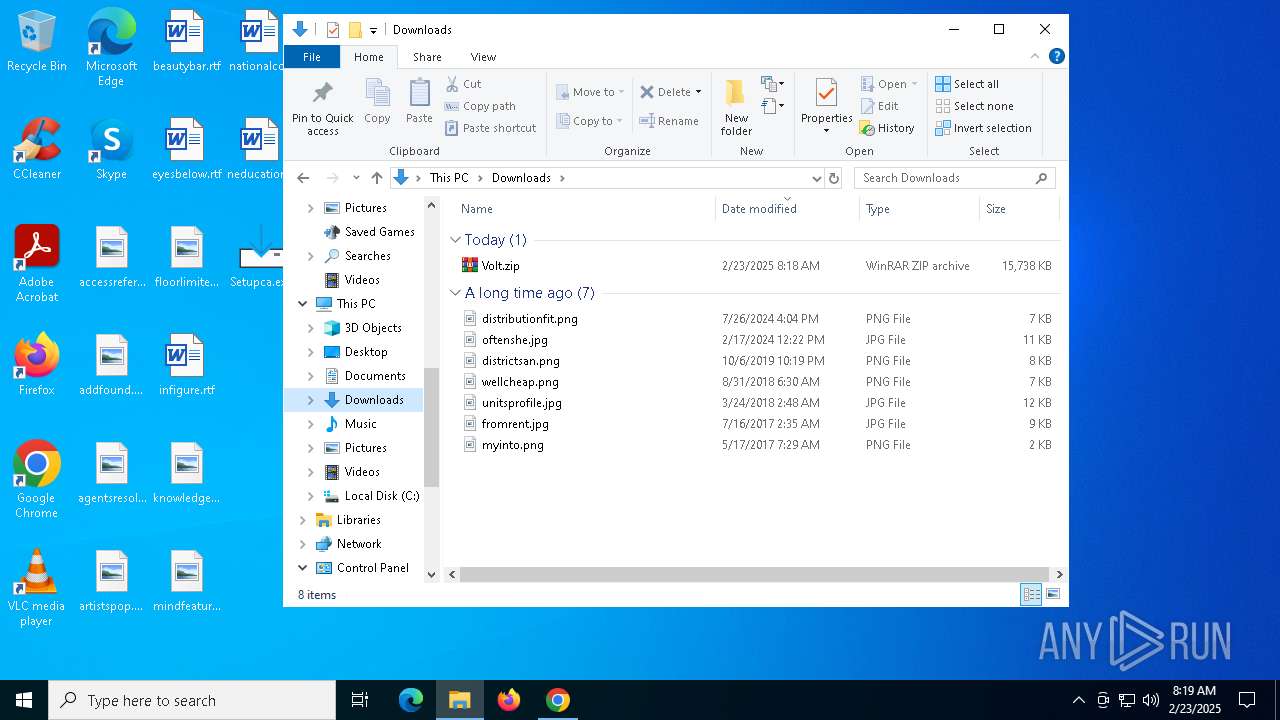
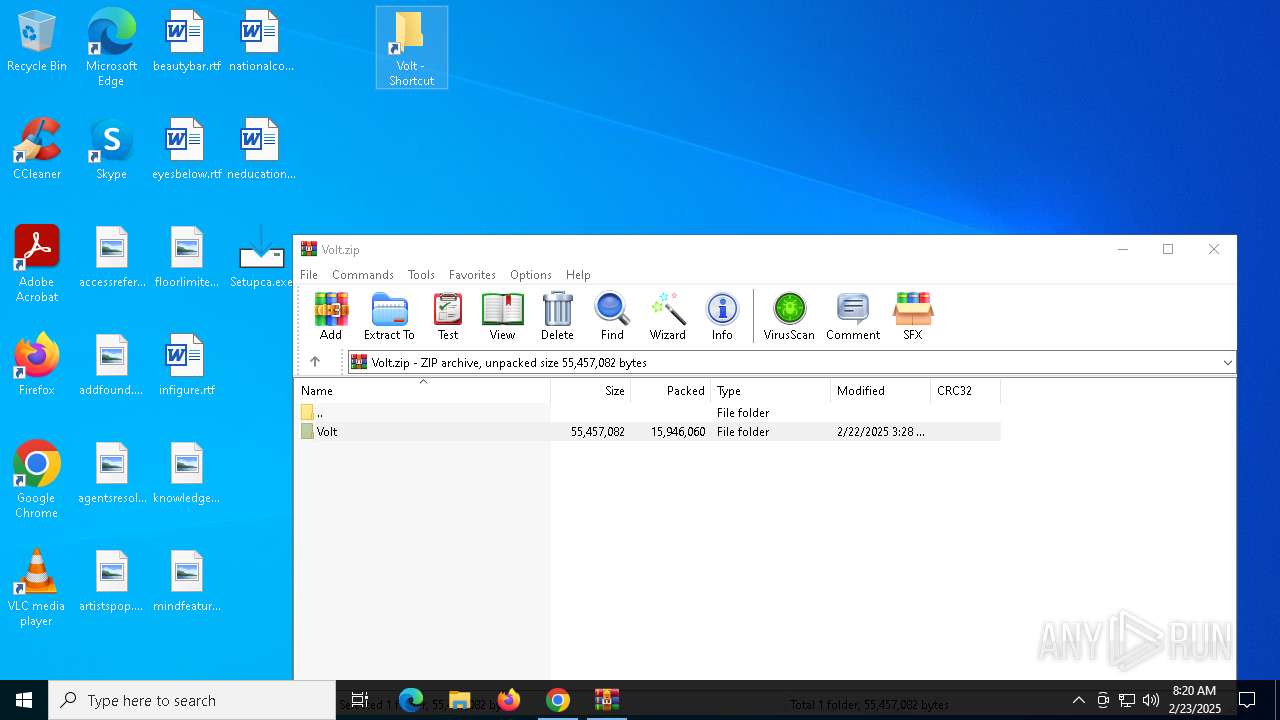
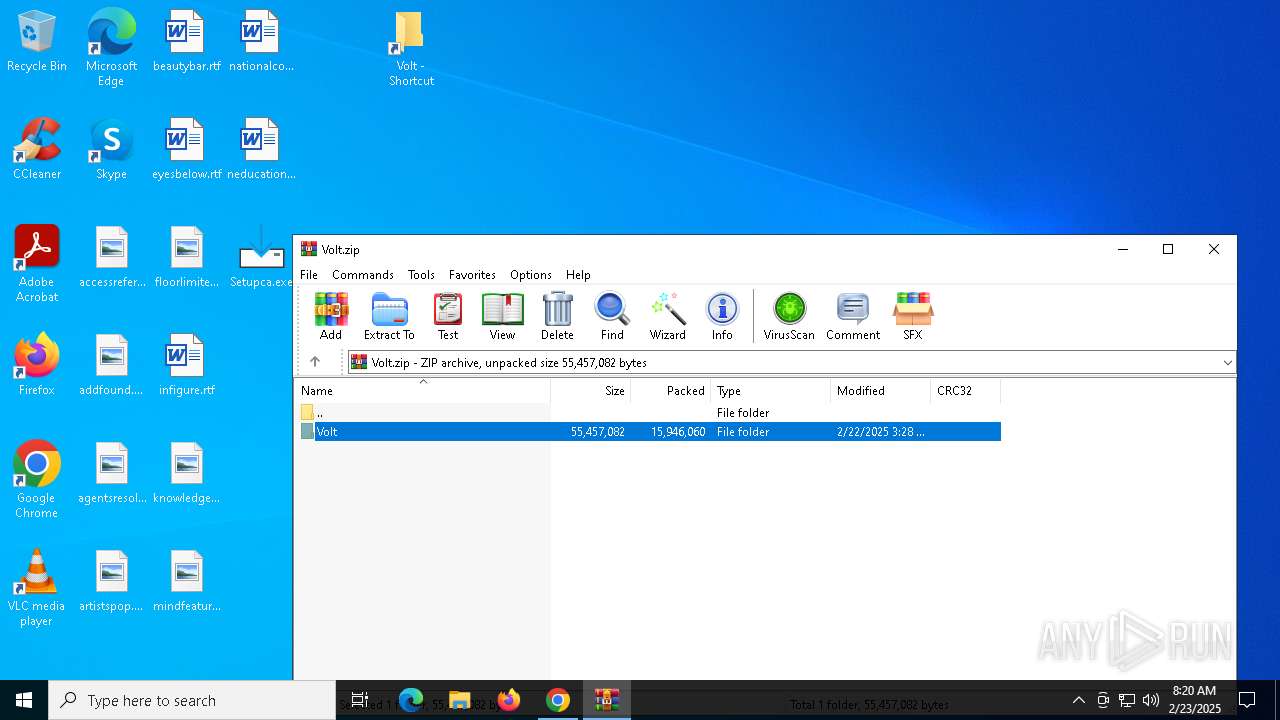
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4968)
Reads Microsoft Office registry keys
- chrome.exe (PID: 5268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:15 14:54:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 89600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
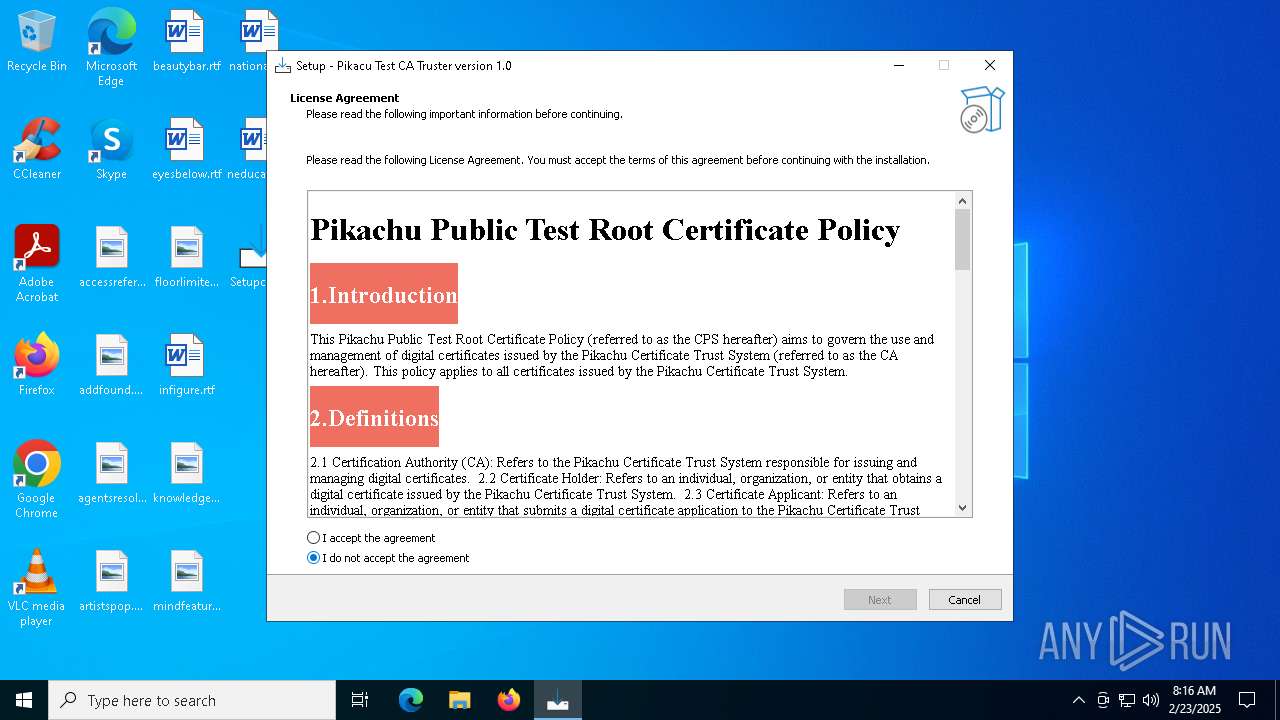
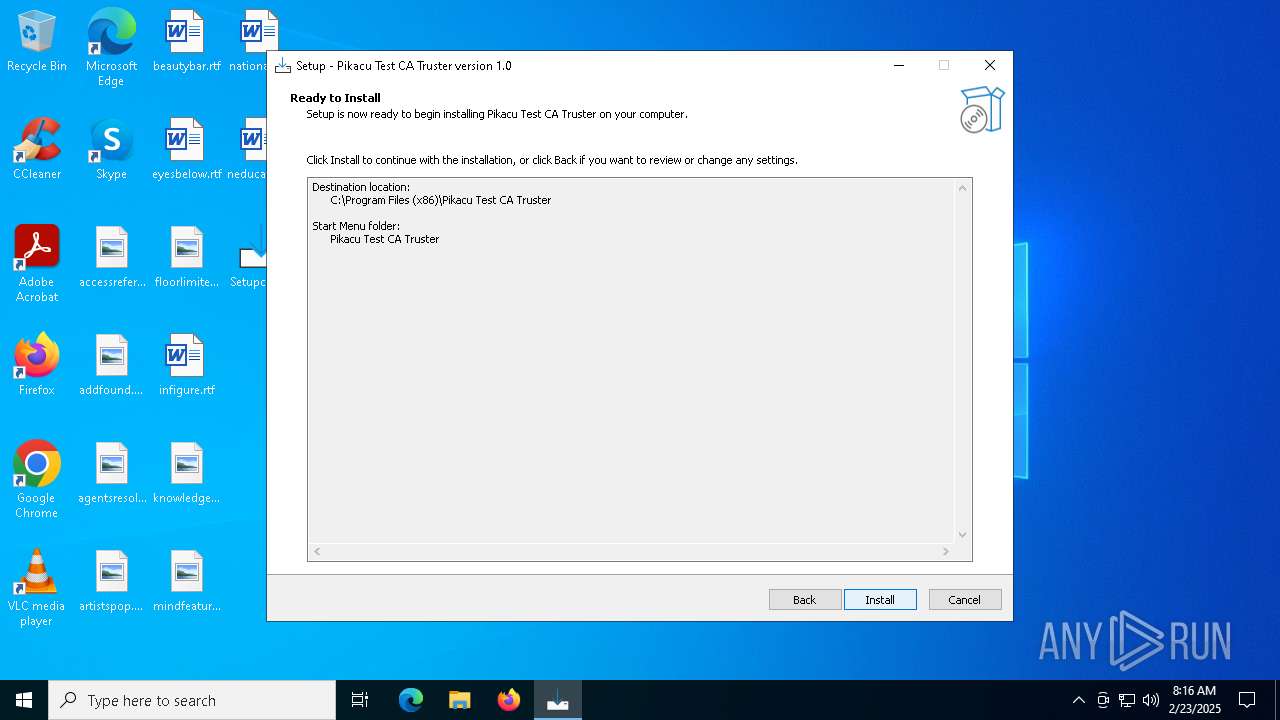
| CompanyName: | Pikachu Software |
| FileDescription: | Pikacu Test CA Truster Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Pikacu Test CA Truster |
| ProductVersion: | 1.0 |
Total processes
224
Monitored processes
89
Malicious processes
5
Suspicious processes
54
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 244 | certmgr.exe -add /all .\5-Pikachu_mTLS_Sub_CA.crt -s -r localMachine AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 1488 | "C:\Users\admin\AppData\Local\Temp\is-VSC8H.tmp\Setupca.tmp" /SL5="$702C6,908493,832512,C:\Users\admin\Desktop\Setupca.exe" | C:\Users\admin\AppData\Local\Temp\is-VSC8H.tmp\Setupca.tmp | — | Setupca.exe | |||||||||||
User: admin Company: Pikachu Software Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1596 | certmgr.exe -crl -add /all .\8-Pikachu_Sign_Sub_CA-G2.crl -s -r localMachine AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 1616 | "C:\Users\admin\Desktop\Setupca.exe" | C:\Users\admin\Desktop\Setupca.exe | explorer.exe | ||||||||||||
User: admin Company: Pikachu Software Integrity Level: MEDIUM Description: Pikacu Test CA Truster Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6472 --field-trial-handle=1948,i,3927212103664814690,1115324724496676184,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3368 --field-trial-handle=1948,i,3927212103664814690,1115324724496676184,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2160 | certmgr.exe -crl -add /all .\5-Pikachu_mTLS_Sub_CA-G2.crl -s -r localMachine AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 2324 | certmgr.exe -crl -add /all .\3-Pikachu_UEFI_Sub_CA-G2.crl -s -r localMachine AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 2380 | certmgr.exe -crl -add /all .\3-Pikachu_UEFI_Sub_CA-G1.crl -s -r currentUser AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 4294967295 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 2408 | certmgr.exe -crl -add /all .\5-Pikachu_mTLS_Sub_CA-G1.crl -s -r currentUser AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 4294967295 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
Total events
79 712
Read events
79 554
Write events
113
Delete events
45
Modification events
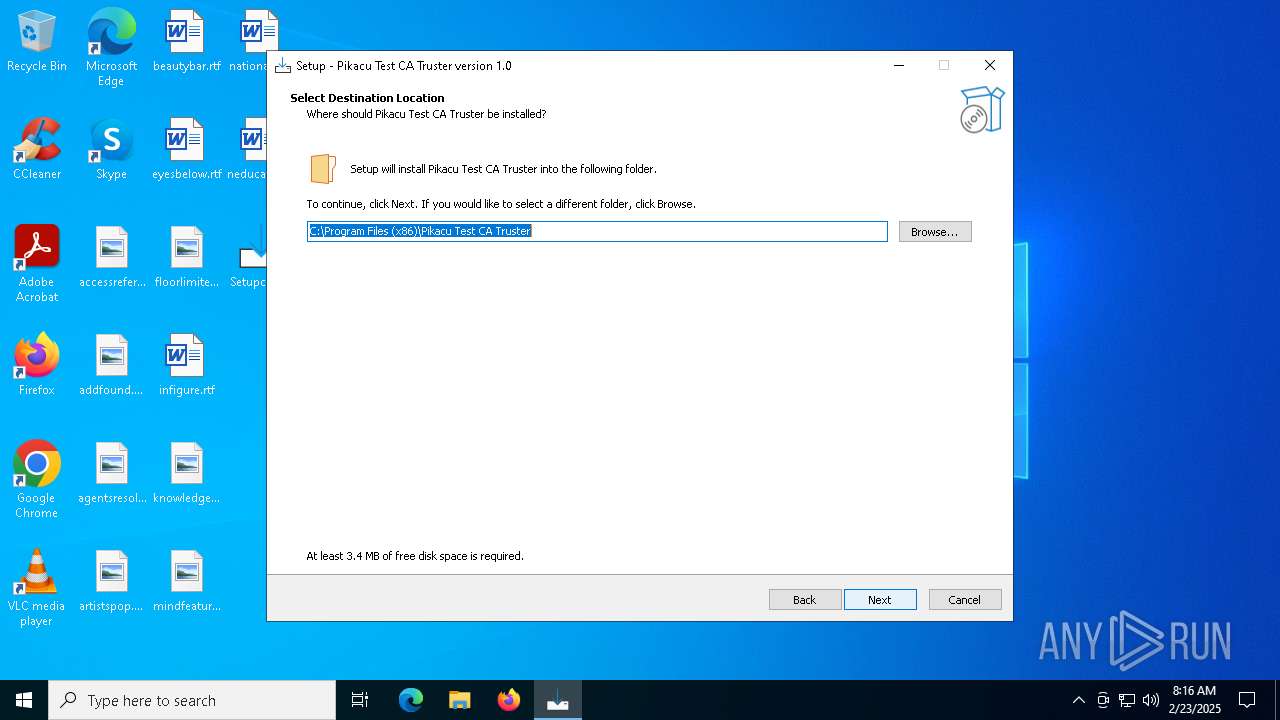
| (PID) Process: | (6248) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (6248) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\Pikacu Test CA Truster | |||
| (PID) Process: | (6248) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\Pikacu Test CA Truster\ | |||
| (PID) Process: | (6248) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Pikacu Test CA Truster | |||
| (PID) Process: | (6248) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (6248) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
| (PID) Process: | (6248) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | DisplayName |
Value: Pikacu Test CA Truster version 1.0 | |||
| (PID) Process: | (6248) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\Pikacu Test CA Truster\unins000.exe" | |||
| (PID) Process: | (6248) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files (x86)\Pikacu Test CA Truster\unins000.exe" /SILENT | |||
| (PID) Process: | (6248) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0 | |||
Executable files
26
Suspicious files
734
Text files
174
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1616 | Setupca.exe | C:\Users\admin\AppData\Local\Temp\is-VSC8H.tmp\Setupca.tmp | executable | |
MD5:2F129949F1A82013642BE1E44EC00CFC | SHA256:9CBF6C1DDC60CF30D4A3E096373B605989A0F7D66A77CE5EA9FD5CDECF847878 | |||
| 6248 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\is-LCD4S.tmp | executable | |
MD5:80D9E21D632513BD35001AFD753DD9C8 | SHA256:9226E6EE21D8AB76F82E8B83D7ED3008A52B696AF2715DAD70D70D61FB8DFCC7 | |||
| 6220 | Setupca.exe | C:\Users\admin\AppData\Local\Temp\is-GNEDI.tmp\Setupca.tmp | executable | |
MD5:2F129949F1A82013642BE1E44EC00CFC | SHA256:9CBF6C1DDC60CF30D4A3E096373B605989A0F7D66A77CE5EA9FD5CDECF847878 | |||
| 6248 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\unins000.exe | executable | |
MD5:80D9E21D632513BD35001AFD753DD9C8 | SHA256:9226E6EE21D8AB76F82E8B83D7ED3008A52B696AF2715DAD70D70D61FB8DFCC7 | |||
| 6248 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\is-ADSO8.tmp | text | |
MD5:9E19758E4FBBE5C3D4CAAD46E3647F6C | SHA256:1BBEFD27048316D71F413EF1BFA225E647B198F73D5B5AE54753484665C3CEBD | |||
| 6248 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\is-DKR1C.tmp | executable | |
MD5:322BF8029866CF3EB7F1DE33F18FB07A | SHA256:312DA44E936C59872EECF0C057F2D21F92EDFB2E712F646569513EE33BE269B0 | |||
| 6248 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | executable | |
MD5:322BF8029866CF3EB7F1DE33F18FB07A | SHA256:312DA44E936C59872EECF0C057F2D21F92EDFB2E712F646569513EE33BE269B0 | |||
| 6248 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\is-JE5OT.tmp | text | |
MD5:D4A7EAE5025AB073E5E535B4A8BCAA2E | SHA256:36B8078C525B816A47A9F711AF22505C958DCD81786D93E67B5DB2CFD2F7C4A2 | |||
| 6248 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\is-9VG3E.tmp | text | |
MD5:C6B82192E9F8FCF65608A1A5640F706B | SHA256:D49701E4F6B57229FE7623A7355EA1B2AC14AD3D5A387D30387A3A82E403553E | |||
| 6248 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\0-Pikachu_Test_CA_RSA-G1.crl | text | |
MD5:51F968C58DCD358393EA98DE5B0D340E | SHA256:1C83C4B49A985BA87BA0CD1BD0D65DB972F1F3FF5C4772744C16A093F7824EC5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
92
DNS requests
106
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.73:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6328 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2600 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/leuwnvr57ab24djzk3hwtstz24_20250213.727981901.14/obedbbhbpmojnkanicioggnmelmoomoc_20250213.727981901.14_all_ENUS500000_acblqmqwzglbt2lc6wsat3ssr6ra.crx3 | unknown | — | — | whitelisted |
6988 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6988 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2600 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/leuwnvr57ab24djzk3hwtstz24_20250213.727981901.14/obedbbhbpmojnkanicioggnmelmoomoc_20250213.727981901.14_all_ENUS500000_acblqmqwzglbt2lc6wsat3ssr6ra.crx3 | unknown | — | — | whitelisted |
2600 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/leuwnvr57ab24djzk3hwtstz24_20250213.727981901.14/obedbbhbpmojnkanicioggnmelmoomoc_20250213.727981901.14_all_ENUS500000_acblqmqwzglbt2lc6wsat3ssr6ra.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5004 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4328 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 104.126.37.154:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1076 | svchost.exe | 2.19.106.8:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
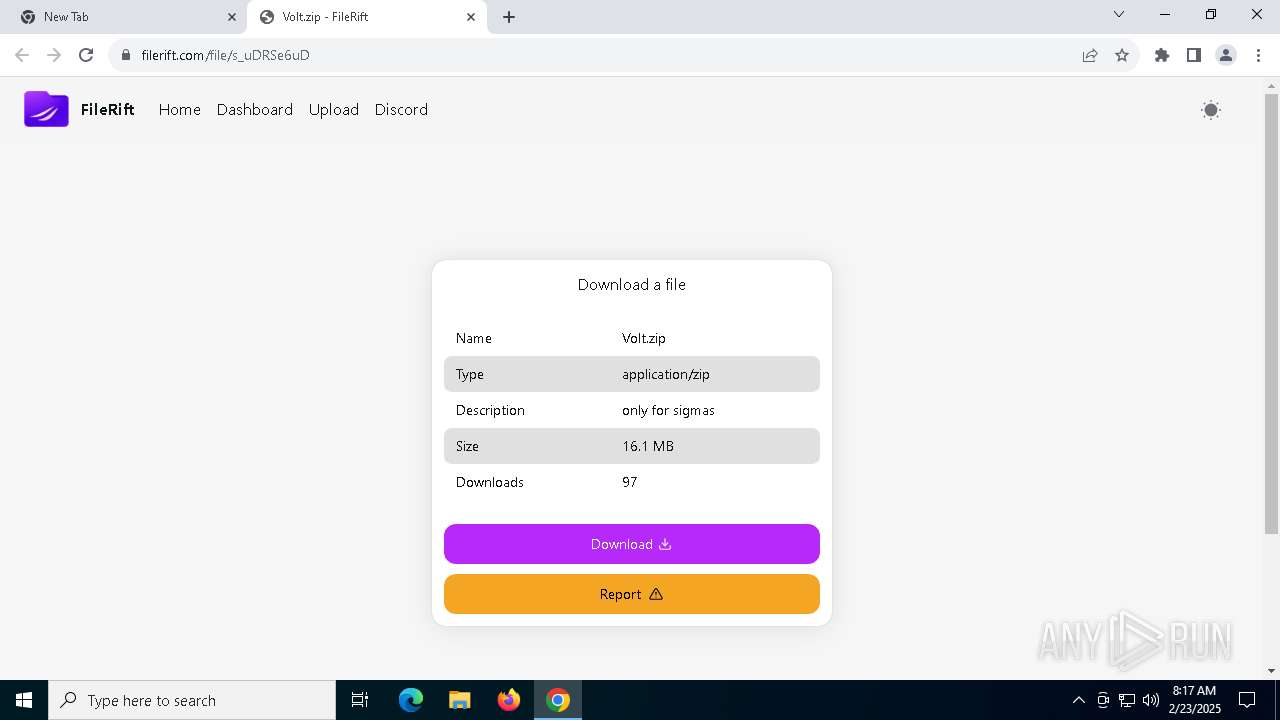
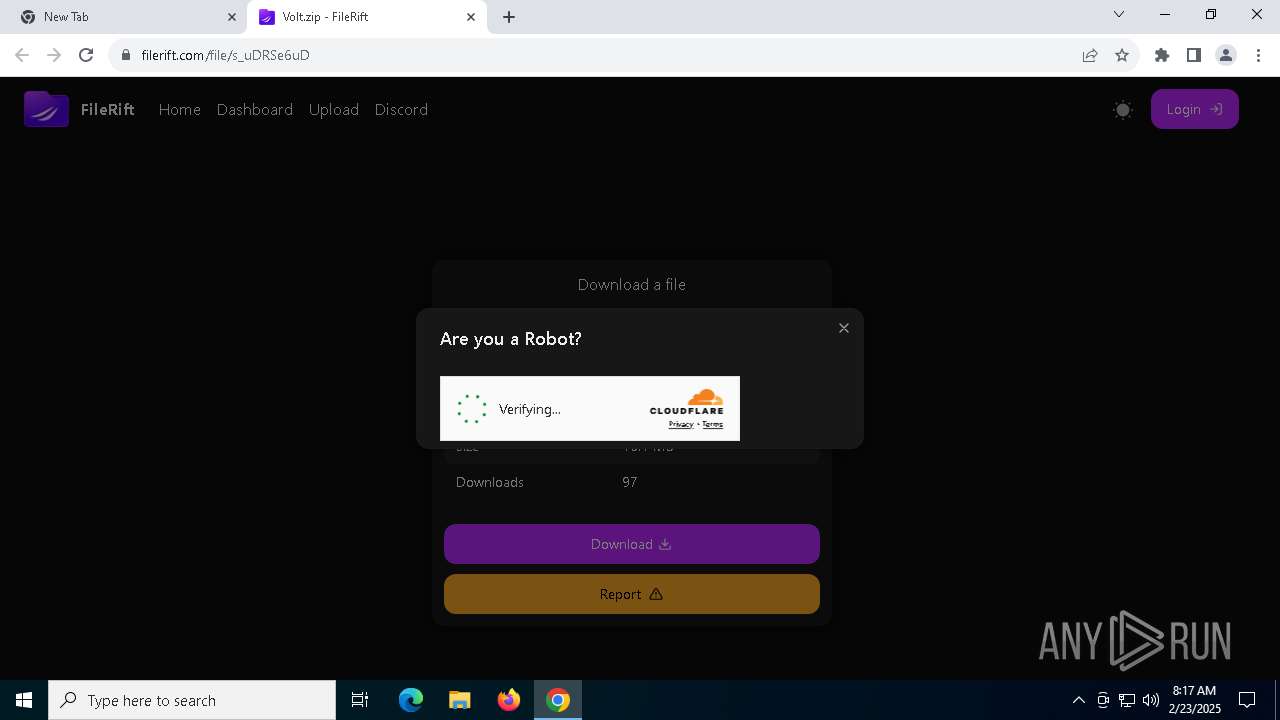
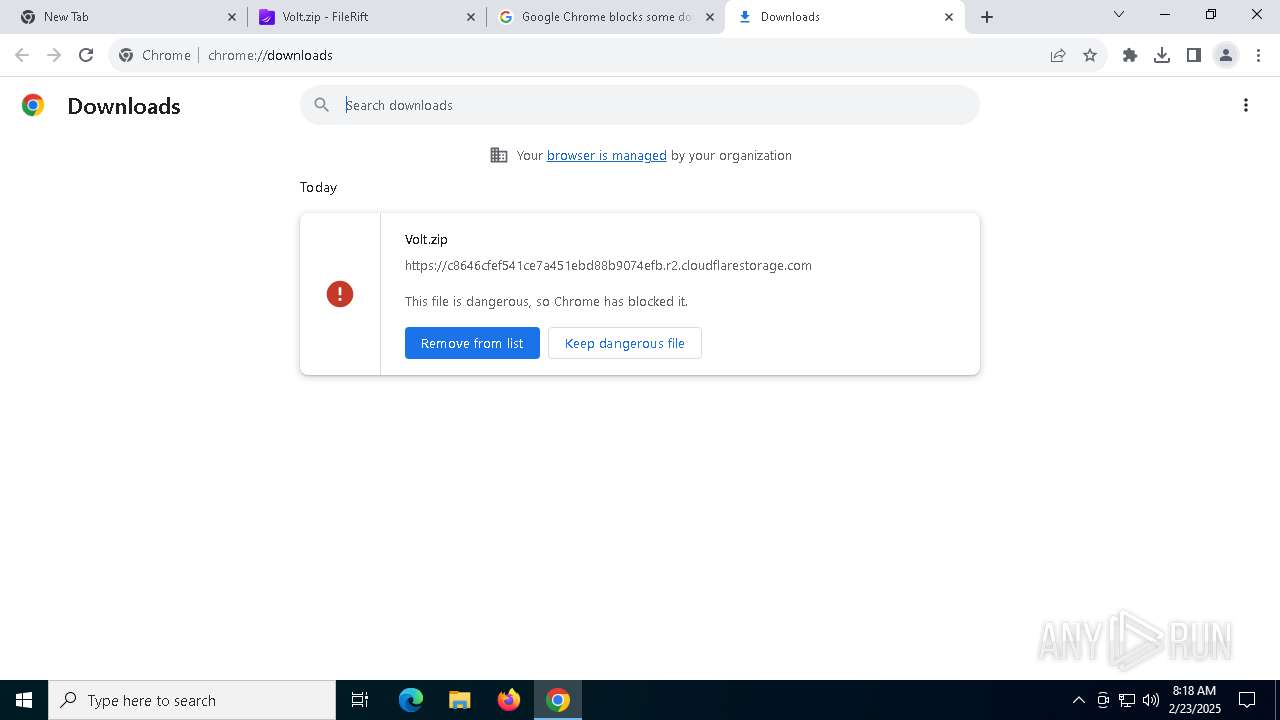
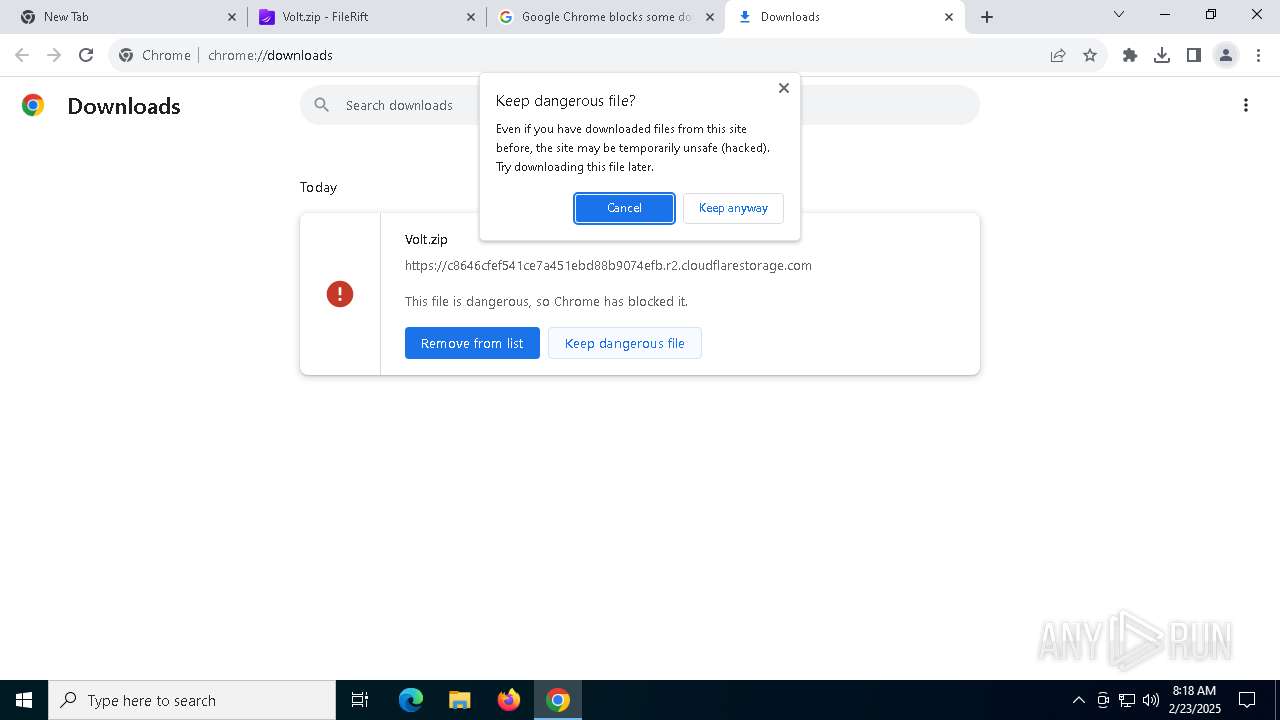
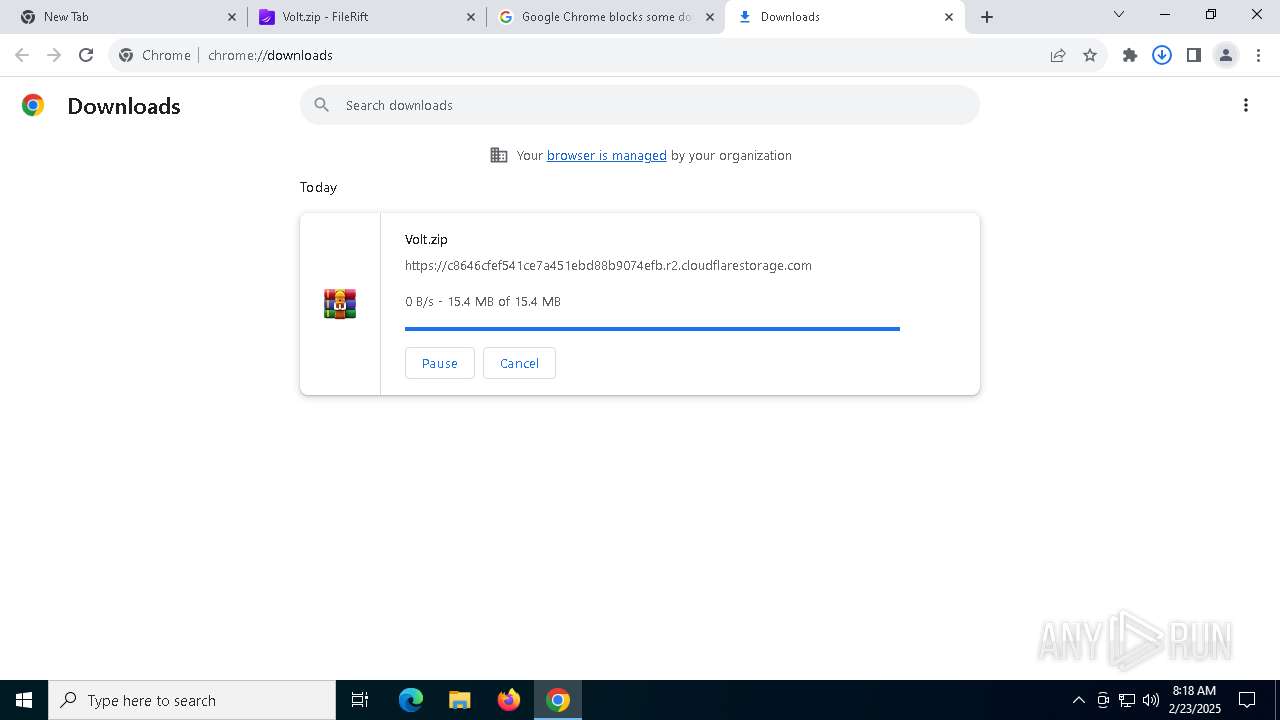
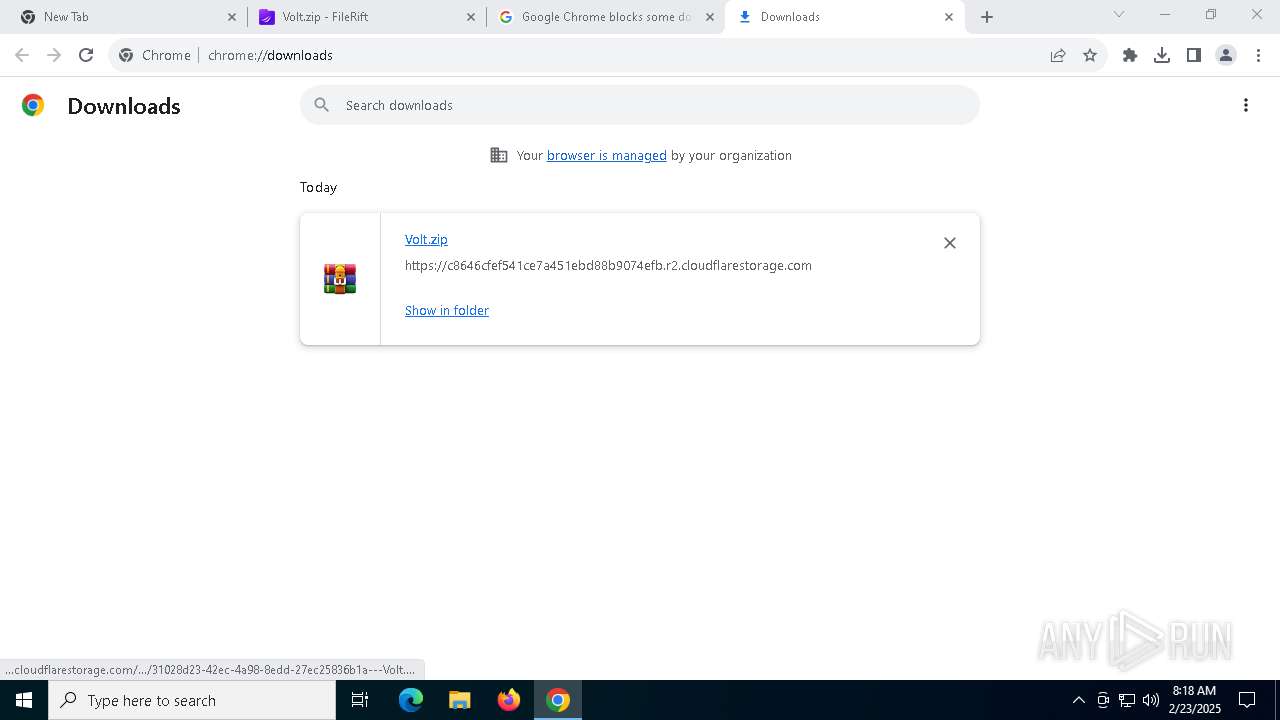
5320 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
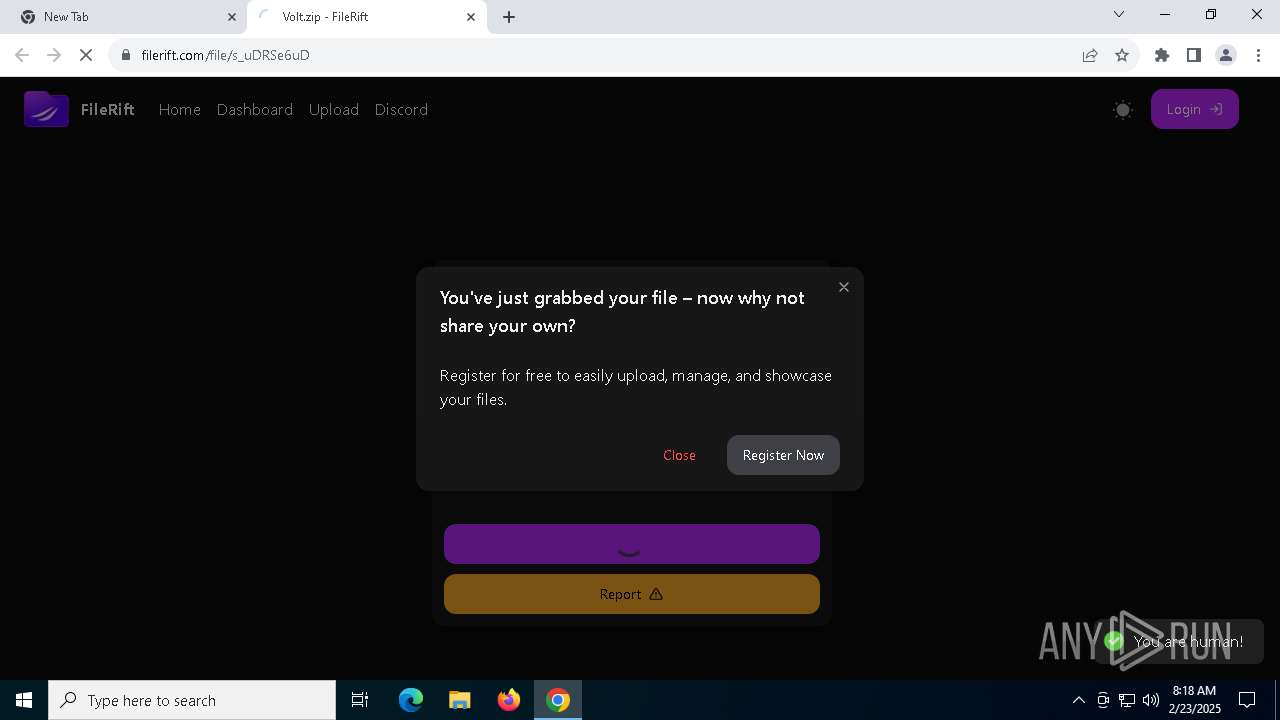
5320 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5320 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5320 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
5320 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
5320 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
5320 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
5320 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |