| File name: | Setupca.exe |
| Full analysis: | https://app.any.run/tasks/4e9bd086-df3b-46b6-a0d1-78d8187fdb55 |
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2025, 05:58:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 10 sections |
| MD5: | A64517503ADB2A1BB8A2F58CA8A661DE |
| SHA1: | F8A5A7F0F6A974559E63EC744402A497A45150E2 |
| SHA256: | 11F4F22EABB173D8C37E80A3DE3BA1D321805FB6D5ADAE498C6628145811EF2E |
| SSDEEP: | 49152:67HecD4dnbibBlb+D7rP4jsbmLApne0Fop4R2uXB3iyLT/ex4XrL7P42DpJXWZnJ:q+cD4dni2P4IkWnXFopLQ3iUrex4vkYc |
MALICIOUS
Executing a file with an untrusted certificate
- Setupca.exe (PID: 6484)
- Setupca.exe (PID: 6644)
- Certmgr.exe (PID: 6316)
- Certmgr.exe (PID: 1580)
- Certmgr.exe (PID: 4864)
- Certmgr.exe (PID: 6312)
- Certmgr.exe (PID: 628)
- Certmgr.exe (PID: 3840)
- Certmgr.exe (PID: 6408)
- Certmgr.exe (PID: 6396)
- Certmgr.exe (PID: 6252)
- Certmgr.exe (PID: 6204)
- Certmgr.exe (PID: 3688)
- Certmgr.exe (PID: 6608)
- Certmgr.exe (PID: 6568)
- Certmgr.exe (PID: 5880)
- Certmgr.exe (PID: 4704)
- Certmgr.exe (PID: 6288)
- Certmgr.exe (PID: 5096)
- Certmgr.exe (PID: 3420)
- Certmgr.exe (PID: 5252)
- Certmgr.exe (PID: 5540)
- Certmgr.exe (PID: 5452)
- Certmgr.exe (PID: 4540)
- Certmgr.exe (PID: 1576)
- Certmgr.exe (PID: 4188)
- Certmgr.exe (PID: 2216)
- Certmgr.exe (PID: 4576)
- Certmgr.exe (PID: 4976)
- Certmgr.exe (PID: 3172)
- Certmgr.exe (PID: 1512)
- Certmgr.exe (PID: 396)
- Certmgr.exe (PID: 6192)
- Certmgr.exe (PID: 4136)
- Certmgr.exe (PID: 6224)
- Certmgr.exe (PID: 5720)
- Certmgr.exe (PID: 6324)
- Certmgr.exe (PID: 904)
- Certmgr.exe (PID: 2928)
- Certmgr.exe (PID: 6232)
- Certmgr.exe (PID: 1480)
- Certmgr.exe (PID: 6420)
- Certmgr.exe (PID: 6252)
- Certmgr.exe (PID: 6292)
- Certmgr.exe (PID: 6372)
- Certmgr.exe (PID: 6280)
- Certmgr.exe (PID: 3744)
- Certmgr.exe (PID: 6640)
- Certmgr.exe (PID: 6568)
- Certmgr.exe (PID: 5880)
- Certmgr.exe (PID: 5576)
- Certmgr.exe (PID: 4648)
- Certmgr.exe (PID: 6004)
- Certmgr.exe (PID: 5872)
- Certmgr.exe (PID: 3420)
- Certmgr.exe (PID: 4624)
SUSPICIOUS
Executable content was dropped or overwritten
- Setupca.exe (PID: 6484)
- Setupca.exe (PID: 6644)
- Setupca.tmp (PID: 6672)
Reads security settings of Internet Explorer
- Setupca.tmp (PID: 6524)
Reads the Windows owner or organization settings
- Setupca.tmp (PID: 6672)
Process drops legitimate windows executable
- Setupca.tmp (PID: 6672)
Adds/modifies Windows certificates
- regedit.exe (PID: 6264)
- Certmgr.exe (PID: 1580)
- Certmgr.exe (PID: 4864)
- Certmgr.exe (PID: 628)
- Certmgr.exe (PID: 6316)
- Certmgr.exe (PID: 3840)
- Certmgr.exe (PID: 6396)
- Certmgr.exe (PID: 5880)
- Certmgr.exe (PID: 6608)
- Certmgr.exe (PID: 6288)
- Certmgr.exe (PID: 5096)
- Certmgr.exe (PID: 5252)
- Certmgr.exe (PID: 1576)
- Certmgr.exe (PID: 2216)
- Certmgr.exe (PID: 5452)
- Certmgr.exe (PID: 4576)
- Certmgr.exe (PID: 1512)
- Certmgr.exe (PID: 6224)
- Certmgr.exe (PID: 4136)
- Certmgr.exe (PID: 6324)
- Certmgr.exe (PID: 904)
- Certmgr.exe (PID: 6372)
- Certmgr.exe (PID: 6420)
- Certmgr.exe (PID: 6252)
- Certmgr.exe (PID: 3744)
- Certmgr.exe (PID: 6568)
- Certmgr.exe (PID: 5872)
- Certmgr.exe (PID: 6004)
- Certmgr.exe (PID: 3420)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7156)
Executing commands from a ".bat" file
- Setupca.tmp (PID: 6672)
Changes settings of the software policy
- regedit.exe (PID: 6264)
Starts CMD.EXE for commands execution
- Setupca.tmp (PID: 6672)
INFO
Create files in a temporary directory
- Setupca.exe (PID: 6484)
- Setupca.exe (PID: 6644)
- Setupca.tmp (PID: 6672)
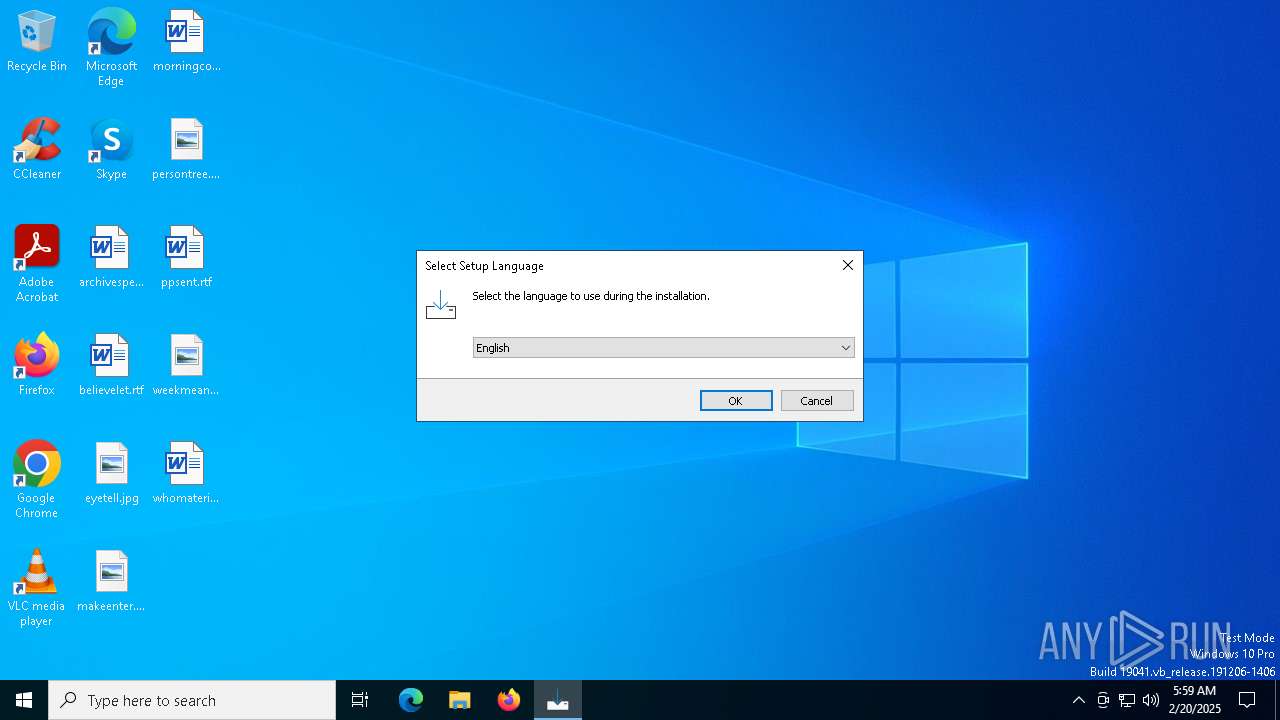
Checks supported languages
- Setupca.exe (PID: 6484)
- Setupca.tmp (PID: 6524)
- Setupca.exe (PID: 6644)
- Setupca.tmp (PID: 6672)
- mode.com (PID: 4308)
- Certmgr.exe (PID: 1580)
- Certmgr.exe (PID: 4864)
- Certmgr.exe (PID: 6312)
- Certmgr.exe (PID: 628)
- Certmgr.exe (PID: 6316)
- Certmgr.exe (PID: 3840)
- Certmgr.exe (PID: 6408)
- Certmgr.exe (PID: 6396)
- Certmgr.exe (PID: 6252)
- Certmgr.exe (PID: 6204)
- Certmgr.exe (PID: 3688)
- Certmgr.exe (PID: 6608)
- Certmgr.exe (PID: 6568)
- Certmgr.exe (PID: 5880)
- Certmgr.exe (PID: 4704)
- Certmgr.exe (PID: 6288)
- Certmgr.exe (PID: 5096)
- Certmgr.exe (PID: 3420)
- Certmgr.exe (PID: 5452)
- Certmgr.exe (PID: 5540)
- Certmgr.exe (PID: 5252)
- Certmgr.exe (PID: 1576)
- Certmgr.exe (PID: 4188)
- Certmgr.exe (PID: 2216)
- Certmgr.exe (PID: 4540)
- Certmgr.exe (PID: 4576)
- Certmgr.exe (PID: 4976)
- Certmgr.exe (PID: 6224)
- Certmgr.exe (PID: 396)
- Certmgr.exe (PID: 4136)
- Certmgr.exe (PID: 3172)
- Certmgr.exe (PID: 1512)
- Certmgr.exe (PID: 6192)
- Certmgr.exe (PID: 5720)
- Certmgr.exe (PID: 6324)
- Certmgr.exe (PID: 2928)
- Certmgr.exe (PID: 904)
- Certmgr.exe (PID: 1480)
- Certmgr.exe (PID: 6420)
- Certmgr.exe (PID: 6252)
- Certmgr.exe (PID: 6292)
- Certmgr.exe (PID: 6232)
- Certmgr.exe (PID: 6372)
- Certmgr.exe (PID: 6280)
- Certmgr.exe (PID: 3744)
- Certmgr.exe (PID: 6640)
- Certmgr.exe (PID: 6568)
- Certmgr.exe (PID: 5880)
- Certmgr.exe (PID: 4648)
- Certmgr.exe (PID: 6004)
- Certmgr.exe (PID: 5872)
- Certmgr.exe (PID: 5576)
- Certmgr.exe (PID: 3420)
- Certmgr.exe (PID: 4624)
Process checks computer location settings
- Setupca.tmp (PID: 6524)
Reads the computer name
- Setupca.tmp (PID: 6524)
- Setupca.tmp (PID: 6672)
Detects InnoSetup installer (YARA)
- Setupca.exe (PID: 6484)
- Setupca.tmp (PID: 6524)
- Setupca.exe (PID: 6644)
- Setupca.tmp (PID: 6672)
Compiled with Borland Delphi (YARA)
- Setupca.exe (PID: 6484)
- Setupca.tmp (PID: 6524)
- Setupca.tmp (PID: 6672)
- Setupca.exe (PID: 6644)
Creates files in the program directory
- Setupca.tmp (PID: 6672)
The sample compiled with english language support
- Setupca.tmp (PID: 6672)
Creates a software uninstall entry
- Setupca.tmp (PID: 6672)
Starts MODE.COM to configure console settings
- mode.com (PID: 4308)
Reads the machine GUID from the registry
- Certmgr.exe (PID: 4864)
- Certmgr.exe (PID: 6312)
- Certmgr.exe (PID: 6316)
- Certmgr.exe (PID: 1580)
- Certmgr.exe (PID: 628)
- Certmgr.exe (PID: 6204)
- Certmgr.exe (PID: 6252)
- Certmgr.exe (PID: 3840)
- Certmgr.exe (PID: 6408)
- Certmgr.exe (PID: 6396)
- Certmgr.exe (PID: 3688)
- Certmgr.exe (PID: 6608)
- Certmgr.exe (PID: 6568)
- Certmgr.exe (PID: 5880)
- Certmgr.exe (PID: 6288)
- Certmgr.exe (PID: 4704)
- Certmgr.exe (PID: 3420)
- Certmgr.exe (PID: 5096)
- Certmgr.exe (PID: 4540)
- Certmgr.exe (PID: 5452)
- Certmgr.exe (PID: 5540)
- Certmgr.exe (PID: 5252)
- Certmgr.exe (PID: 4188)
- Certmgr.exe (PID: 1576)
- Certmgr.exe (PID: 2216)
- Certmgr.exe (PID: 4576)
- Certmgr.exe (PID: 4976)
- Certmgr.exe (PID: 3172)
- Certmgr.exe (PID: 1512)
- Certmgr.exe (PID: 6224)
- Certmgr.exe (PID: 6192)
- Certmgr.exe (PID: 396)
- Certmgr.exe (PID: 4136)
- Certmgr.exe (PID: 5720)
- Certmgr.exe (PID: 6324)
- Certmgr.exe (PID: 2928)
- Certmgr.exe (PID: 904)
- Certmgr.exe (PID: 1480)
- Certmgr.exe (PID: 6420)
- Certmgr.exe (PID: 6292)
- Certmgr.exe (PID: 6252)
- Certmgr.exe (PID: 6232)
- Certmgr.exe (PID: 6372)
- Certmgr.exe (PID: 6280)
- Certmgr.exe (PID: 6568)
- Certmgr.exe (PID: 3744)
- Certmgr.exe (PID: 6640)
- Certmgr.exe (PID: 5880)
- Certmgr.exe (PID: 5576)
- Certmgr.exe (PID: 3420)
- Certmgr.exe (PID: 4648)
- Certmgr.exe (PID: 6004)
- Certmgr.exe (PID: 5872)
- Certmgr.exe (PID: 4624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:15 14:54:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 89600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
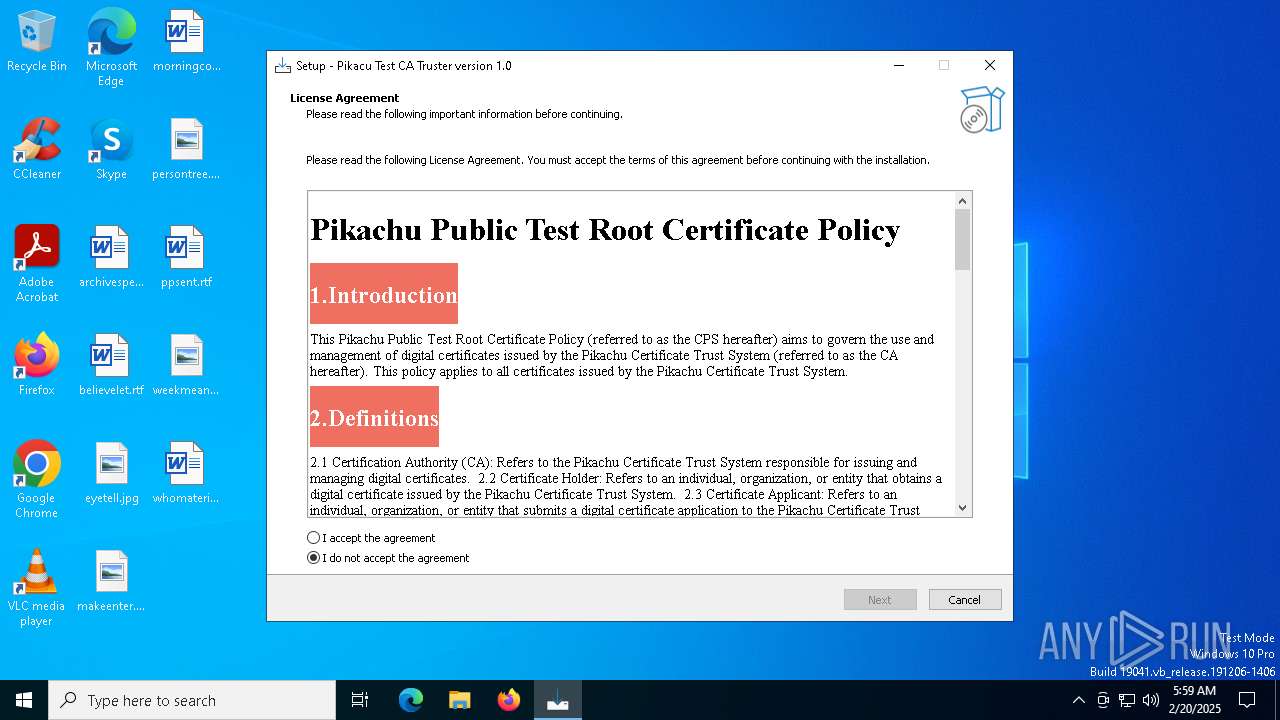
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Pikachu Software |
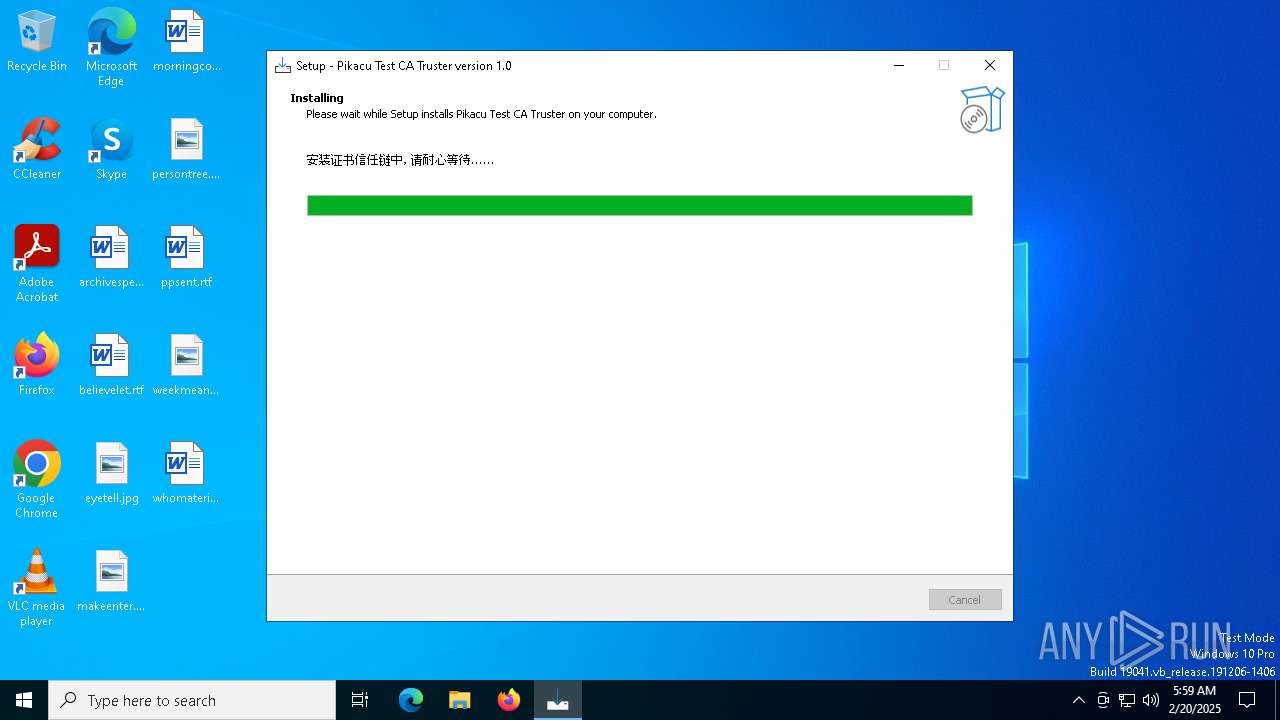
| FileDescription: | Pikacu Test CA Truster Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Pikacu Test CA Truster |
| ProductVersion: | 1.0 |
Total processes
185
Monitored processes
62
Malicious processes
5
Suspicious processes
54
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | certmgr.exe -add /all .\6-Pikachu_File_Sub_CA.crt -s -r currentUser AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 4294967295 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 628 | certmgr.exe -crl -add /all .\0-Pikachu_Test_CA_RSA-G2.crl -s -r localMachine AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 904 | certmgr.exe -add /all .\7-Pikachu_Mail_Sub_CA.crt -s -r localMachine AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 1480 | certmgr.exe -crl -add /all .\7-Pikachu_Mail_Sub_CA-G1.crl -s -r currentUser AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 4294967295 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 1512 | certmgr.exe -crl -add /all .\5-Pikachu_mTLS_Sub_CA-G2.crl -s -r localMachine AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 1576 | certmgr.exe -add /all .\5-Pikachu_mTLS_Sub_CA.crt -s -r localMachine AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 1580 | certmgr.exe -add /all .\0-Pikachu_Test_CA_RSA.crt -s -r currentUser AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 2216 | certmgr.exe -crl -add /all .\5-Pikachu_mTLS_Sub_CA-G1.crl -s -r localMachine AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 2928 | certmgr.exe -crl -add /all .\6-Pikachu_File_Sub_CA-G2.crl -s -r currentUser AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 4294967295 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 3172 | certmgr.exe -crl -add /all .\5-Pikachu_mTLS_Sub_CA-G1.crl -s -r currentUser AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 4294967295 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
Total events
68 787
Read events
68 696
Write events
53
Delete events
38
Modification events
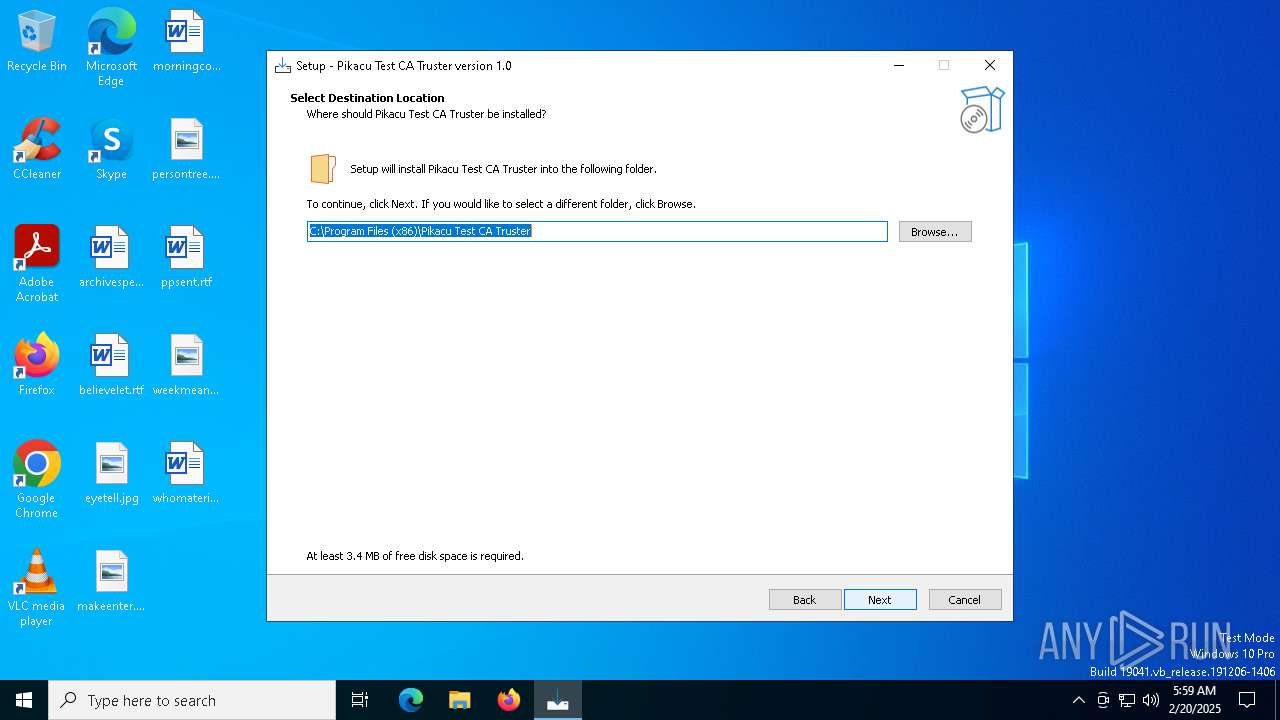
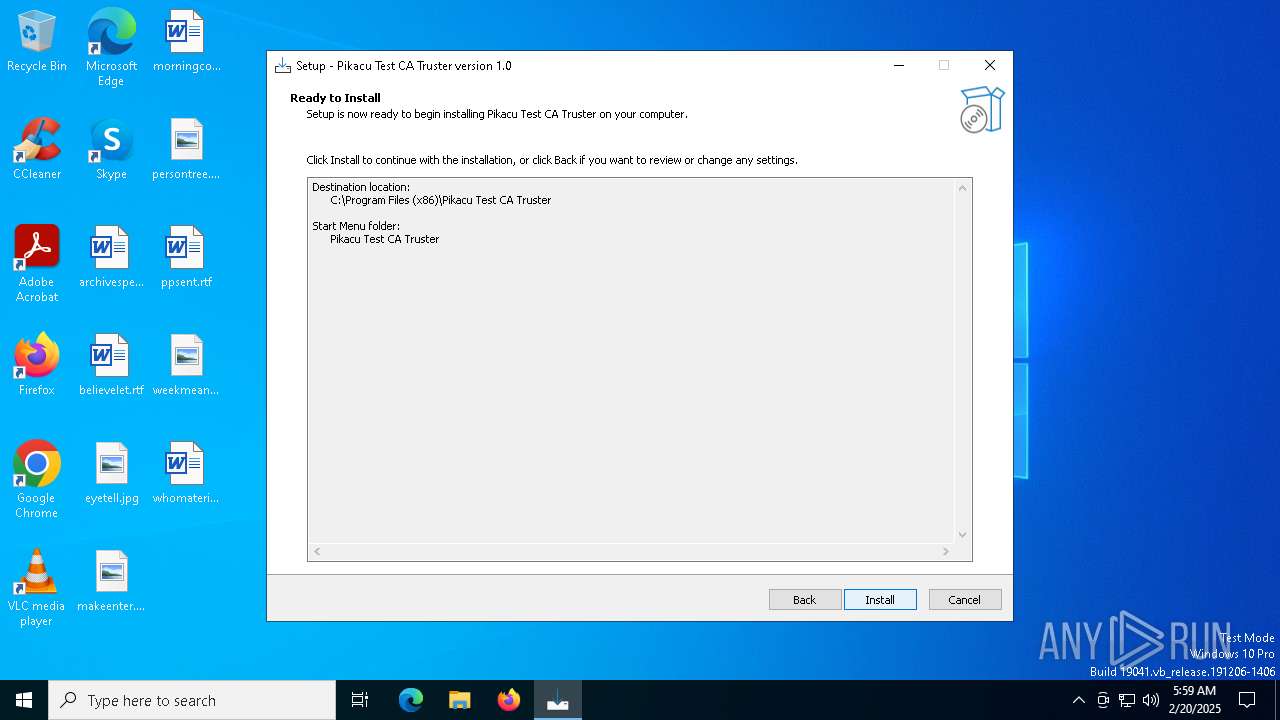
| (PID) Process: | (6672) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (6672) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\Pikacu Test CA Truster | |||
| (PID) Process: | (6672) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\Pikacu Test CA Truster\ | |||
| (PID) Process: | (6672) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Pikacu Test CA Truster | |||
| (PID) Process: | (6672) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (6672) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
| (PID) Process: | (6672) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | DisplayName |
Value: Pikacu Test CA Truster version 1.0 | |||
| (PID) Process: | (6672) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\Pikacu Test CA Truster\unins000.exe" | |||
| (PID) Process: | (6672) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files (x86)\Pikacu Test CA Truster\unins000.exe" /SILENT | |||
| (PID) Process: | (6672) Setupca.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7D4A8BF8-23CE-42A9-A2FB-37C8A1704FAC}_is1 |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0 | |||
Executable files
8
Suspicious files
3
Text files
64
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6672 | Setupca.tmp | C:\Users\admin\AppData\Local\Temp\is-V3K71.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 6644 | Setupca.exe | C:\Users\admin\AppData\Local\Temp\is-M93OB.tmp\Setupca.tmp | executable | |
MD5:2F129949F1A82013642BE1E44EC00CFC | SHA256:9CBF6C1DDC60CF30D4A3E096373B605989A0F7D66A77CE5EA9FD5CDECF847878 | |||
| 6672 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\is-EN1QB.tmp | text | |
MD5:9E19758E4FBBE5C3D4CAAD46E3647F6C | SHA256:1BBEFD27048316D71F413EF1BFA225E647B198F73D5B5AE54753484665C3CEBD | |||
| 6484 | Setupca.exe | C:\Users\admin\AppData\Local\Temp\is-E80JA.tmp\Setupca.tmp | executable | |
MD5:2F129949F1A82013642BE1E44EC00CFC | SHA256:9CBF6C1DDC60CF30D4A3E096373B605989A0F7D66A77CE5EA9FD5CDECF847878 | |||
| 6672 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\License.rtf | text | |
MD5:9E19758E4FBBE5C3D4CAAD46E3647F6C | SHA256:1BBEFD27048316D71F413EF1BFA225E647B198F73D5B5AE54753484665C3CEBD | |||
| 6672 | Setupca.tmp | C:\Users\admin\AppData\Local\Temp\is-V3K71.tmp\_isetup\_isdecmp.dll | executable | |
MD5:077CB4461A2767383B317EB0C50F5F13 | SHA256:8287D0E287A66EE78537C8D1D98E426562B95C50F569B92CEA9CE36A9FA57E64 | |||
| 6672 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\0-Pikachu_Test_CA_RSA.crt | text | |
MD5:C6B82192E9F8FCF65608A1A5640F706B | SHA256:D49701E4F6B57229FE7623A7355EA1B2AC14AD3D5A387D30387A3A82E403553E | |||
| 6672 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\is-N4G10.tmp | text | |
MD5:AEE260B1675E4E2C28EAA9D5BA8DAA53 | SHA256:7373E065047C75F671FA75BAC5A65E78FAD71ECB59FF2CC7E1DE89D4C7207884 | |||
| 6672 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\is-B9464.tmp | text | |
MD5:C6B82192E9F8FCF65608A1A5640F706B | SHA256:D49701E4F6B57229FE7623A7355EA1B2AC14AD3D5A387D30387A3A82E403553E | |||
| 6672 | Setupca.tmp | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\0-Pikachu_Test_CA_RSA-G2.crl | text | |
MD5:D4A7EAE5025AB073E5E535B4A8BCAA2E | SHA256:36B8078C525B816A47A9F711AF22505C958DCD81786D93E67B5DB2CFD2F7C4A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
32
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
188 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 23.51.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 23.51.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
188 | svchost.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3540 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3540 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6752 | backgroundTaskHost.exe | GET | 200 | 23.51.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2632 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
188 | svchost.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
188 | svchost.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
188 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 23.15.178.200:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |