| File name: | HP_104xFWUpg1525_131025101126V3.exe |
| Full analysis: | https://app.any.run/tasks/f1a31138-7c08-45ed-bff2-99e64a8324e7 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2023, 15:57:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2A1586BB60B0447938FBFABCB52F35E9 |
| SHA1: | 824E8DED8519457A9DFEC9E73C0DD5EBB27E78C5 |
| SHA256: | 11D740EB16AB672E534CA3FE91C9B3F63749410E7421B41DA8209CAA3A8AFC28 |
| SSDEEP: | 12288:1M/dfJ7rN1/fSxPnSo6zXYfdyilFCY7HA6:1MvVFKxPnSoRfZT7HA |
MALICIOUS
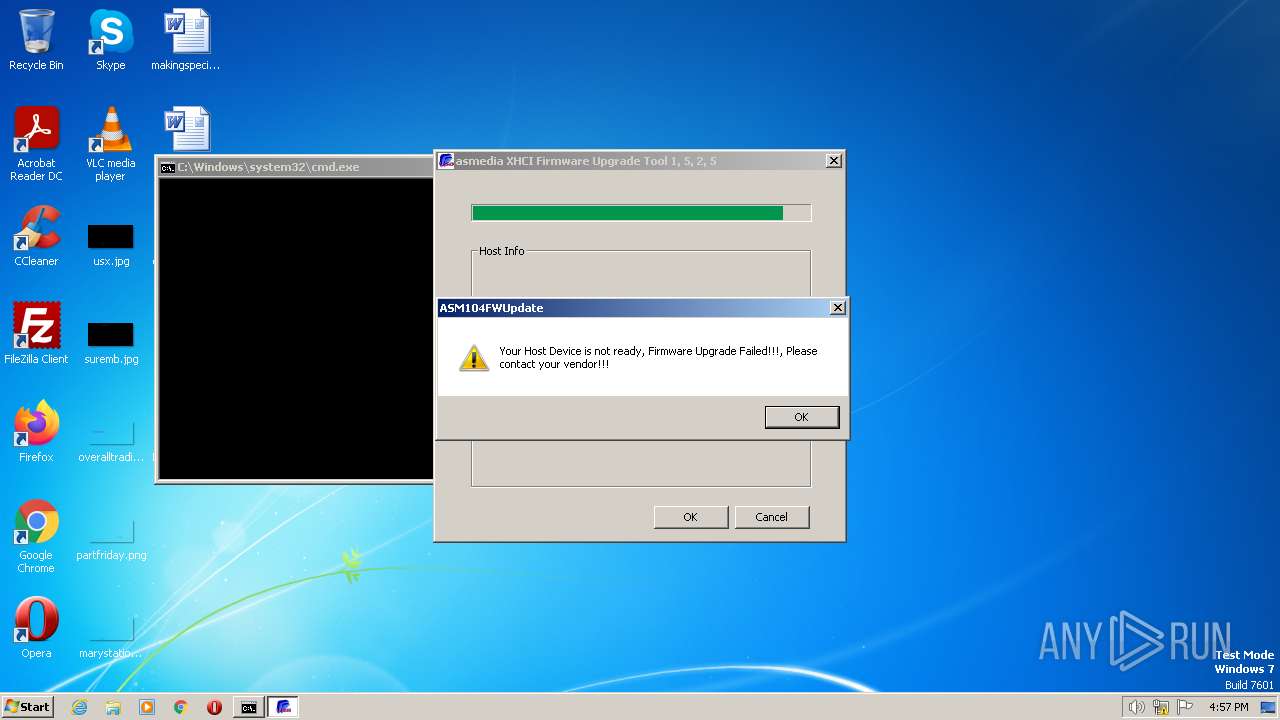
Application was dropped or rewritten from another process
- ASM104FWUpdate.exe (PID: 1276)
- ASM104FWUpdate.exe (PID: 2296)
- ASM104FWUpdate.exe (PID: 2752)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- HP_104xFWUpg1525_131025101126V3.exe (PID: 3960)
Reads the Internet Settings
- HP_104xFWUpg1525_131025101126V3.exe (PID: 3960)
- cmd.exe (PID: 2360)
Executable content was dropped or overwritten
- HP_104xFWUpg1525_131025101126V3.exe (PID: 3960)
Starts CMD.EXE for commands execution
- HP_104xFWUpg1525_131025101126V3.exe (PID: 3960)
Executing commands from a ".bat" file
- HP_104xFWUpg1525_131025101126V3.exe (PID: 3960)
INFO
Checks supported languages
- HP_104xFWUpg1525_131025101126V3.exe (PID: 3960)
- ASM104FWUpdate.exe (PID: 2752)
The process checks LSA protection
- HP_104xFWUpg1525_131025101126V3.exe (PID: 3960)
Reads the computer name
- HP_104xFWUpg1525_131025101126V3.exe (PID: 3960)
- ASM104FWUpdate.exe (PID: 2752)
Create files in a temporary directory
- HP_104xFWUpg1525_131025101126V3.exe (PID: 3960)
The executable file from the user directory is run by the CMD process
- ASM104FWUpdate.exe (PID: 1276)
- ASM104FWUpdate.exe (PID: 2296)
- ASM104FWUpdate.exe (PID: 2752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (45.7) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (31) |
| .exe | | | Win32 Executable Borland Delphi 6 (18) |
| .exe | | | InstallShield setup (2.9) |
| .exe | | | Win32 Executable Delphi generic (0.9) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xb064 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 13824 |
| CodeSize: | 44032 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000AB78 | 0x0000AC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47393 |
DATA | 0x0000C000 | 0x0000055C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.84654 |
BSS | 0x0000D000 | 0x00100AC9 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0010E000 | 0x00000A6E | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.41371 |
.tls | 0x0010F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00110000 | 0x00000036 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.714657 |
.reloc | 0x00111000 | 0x00000FB0 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58234 |
.rsrc | 0x00112000 | 0x00001200 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.73508 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40518 | 744 | UNKNOWN | Czech - Czech Republic | RT_ICON |
4091 | 2.48495 | 112 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 2.8942 | 240 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.9852 | 216 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20513 | 608 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.25436 | 892 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.18442 | 672 | UNKNOWN | UNKNOWN | RT_STRING |
DESCRIPTION | 2.7612 | 60 | UNKNOWN | UNKNOWN | RT_RCDATA |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 4.68504 | 132 | UNKNOWN | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
43
Monitored processes
5
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1276 | ASM104FWUpdate.exe /I 8190-103C | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\ASM104FWUpdate.exe | — | cmd.exe | |||||||||||
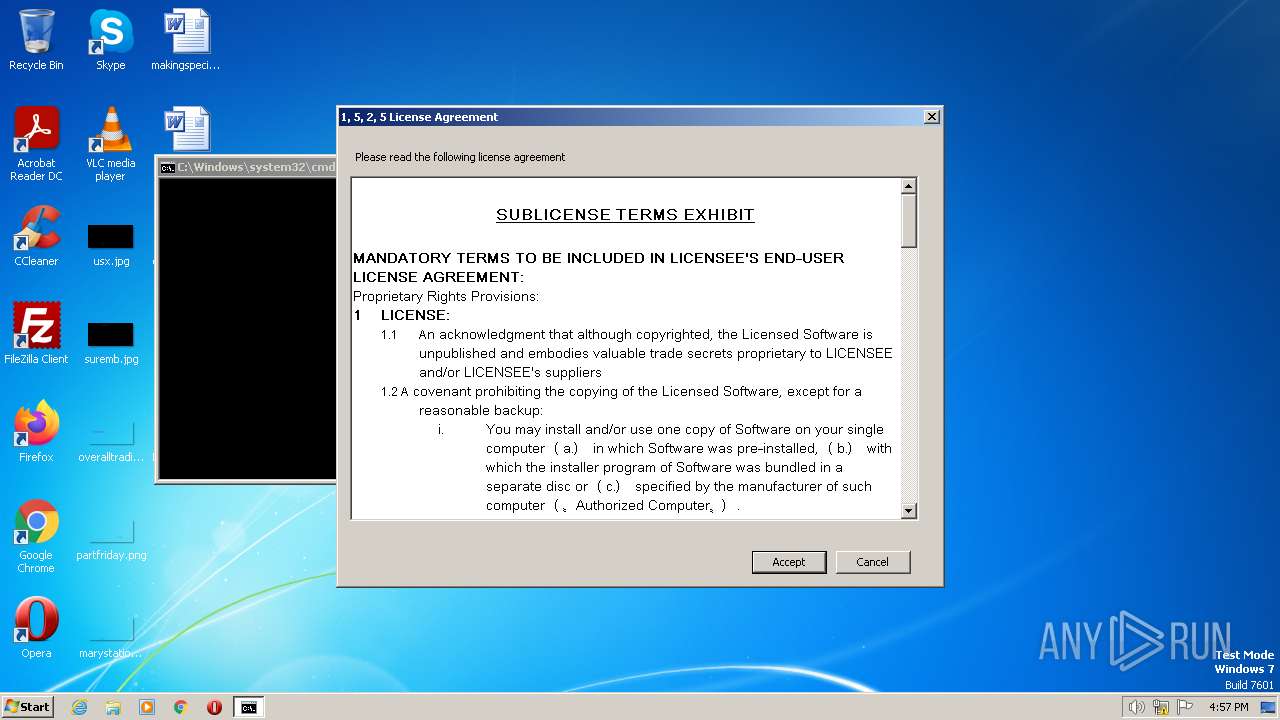
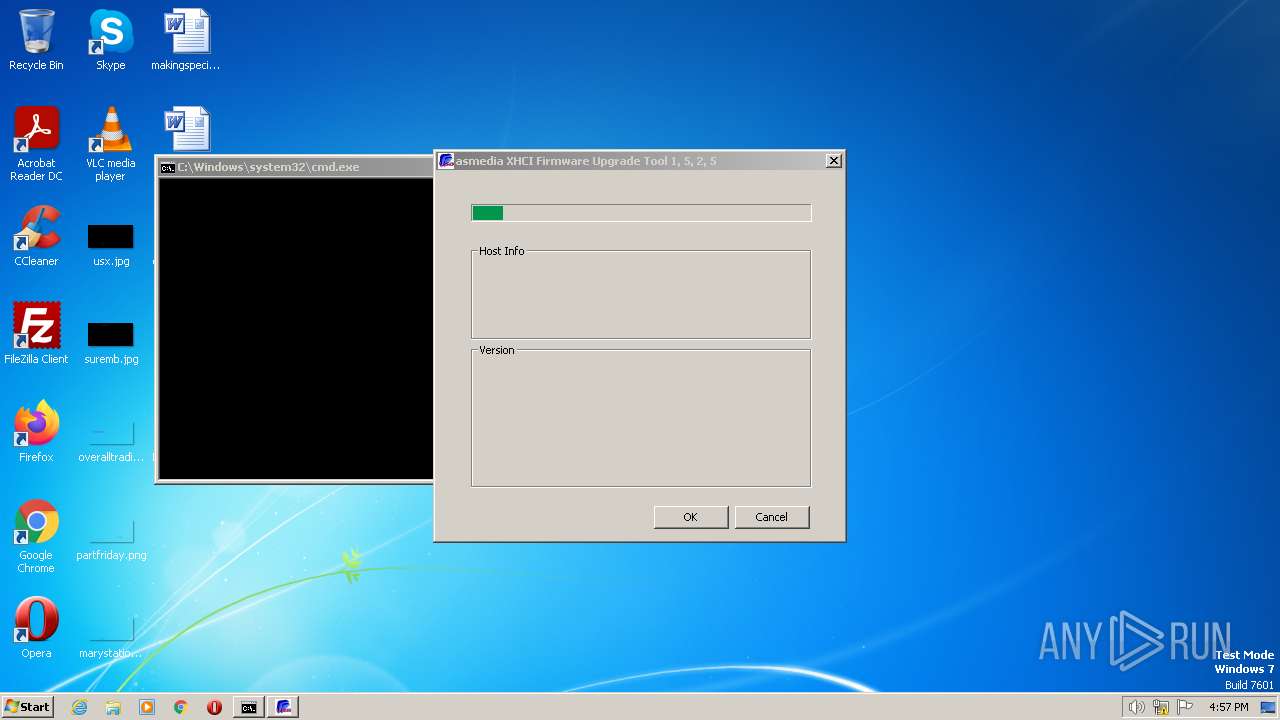
User: admin Company: asmedia Integrity Level: MEDIUM Description: ASM104x Firmware Update Exit code: 3221226540 Version: 1, 5, 2, 5 Modules
| |||||||||||||||
| 2296 | "C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\ASM104FWUpdate.exe" /I 8190-103C | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\ASM104FWUpdate.exe | — | cmd.exe | |||||||||||
User: admin Company: asmedia Integrity Level: MEDIUM Description: ASM104x Firmware Update Exit code: 3221226540 Version: 1, 5, 2, 5 Modules
| |||||||||||||||
| 2360 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\RunASM104xFWUpgradeTool.bat" " | C:\Windows\System32\cmd.exe | — | HP_104xFWUpg1525_131025101126V3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294967295 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2752 | "C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\ASM104FWUpdate.exe" /I 8190-103C | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\ASM104FWUpdate.exe | cmd.exe | ||||||||||||
User: admin Company: asmedia Integrity Level: HIGH Description: ASM104x Firmware Update Exit code: 4294967295 Version: 1, 5, 2, 5 Modules
| |||||||||||||||
| 3960 | "C:\Users\admin\AppData\Local\Temp\HP_104xFWUpg1525_131025101126V3.exe" | C:\Users\admin\AppData\Local\Temp\HP_104xFWUpg1525_131025101126V3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
Total events
1 533
Read events
1 517
Write events
16
Delete events
0
Modification events
| (PID) Process: | (3960) HP_104xFWUpg1525_131025101126V3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3960) HP_104xFWUpg1525_131025101126V3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3960) HP_104xFWUpg1525_131025101126V3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3960) HP_104xFWUpg1525_131025101126V3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2360) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2360) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2360) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2360) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
6
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3960 | HP_104xFWUpg1525_131025101126V3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\devconAMD64.exe | executable | |
MD5:3904D0698962E09DA946046020CBCB17 | SHA256:A51E25ACC489948B31B1384E1DC29518D19B421D6BC0CED90587128899275289 | |||
| 3960 | HP_104xFWUpg1525_131025101126V3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\License_Agreement.rtf | text | |
MD5:0871362EB511645BD0FD1574FFE740C0 | SHA256:7A74C306BA1EDA2071EB404098D9DD45662884E338EFDAA43692E22FBA4DD474 | |||
| 3960 | HP_104xFWUpg1525_131025101126V3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\asmiodll.dll | executable | |
MD5:986FF9F59BFBFA5E4C224CAEB186ECDA | SHA256:F520DB0767F7E6C3CCAE76780FFBC104D915870EE7FC6C3CBA5E98ACD86BFE6D | |||
| 3960 | HP_104xFWUpg1525_131025101126V3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\devcon.exe | executable | |
MD5:C4B470269324517EE838789C7CF5E606 | SHA256:5F9B898315AD8192E87E21A499FD87D31B886513BB39D368476174AAA89A2BF9 | |||
| 3960 | HP_104xFWUpg1525_131025101126V3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\AsmIo.sys | executable | |
MD5:D6B83263AF7C6AF7AB1DE08FAC17DB70 | SHA256:D76D2C6D220BB750CA891D94E400E0BE09FB3EDDAFDE9651739EB61436068089 | |||
| 3960 | HP_104xFWUpg1525_131025101126V3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\Config_131025_10_11_26.bin | image | |
MD5:2FC832CF501CEF3516F6D64ADE8EEE73 | SHA256:81834F7E91A241C18F60E71AD3C329E06EA2928BA4A63165CB1BB64A82A23E4B | |||
| 3960 | HP_104xFWUpg1525_131025101126V3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\ASM104FWUpdate.exe | executable | |
MD5:E33D524F0AF6888AFB876B1F973D2FBA | SHA256:35852EF094BC3192DE737653BAEDFF8A78A02EECD742F698A918FB7626E70069 | |||
| 3960 | HP_104xFWUpg1525_131025101126V3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\RunASM104xFWUpgradeTool.bat | text | |
MD5:29D177E6850EF35B8A9B20ED89B44D23 | SHA256:02723512EBE2D956FC0CC1E65F0407864AAE6D1E3561D3FBE973F187884D90A3 | |||
| 3960 | HP_104xFWUpg1525_131025101126V3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00653ECF59\AsmIo64.sys | executable | |
MD5:5F6C374847144974259CE589CC06F4CA | SHA256:04533B9EBB42FBBABA3F59A1CB57896B081B997E356BF224876D8AE805EB2B76 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3376 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |