| File name: | HPNT.exe |
| Full analysis: | https://app.any.run/tasks/13ddce17-3535-4651-a97b-b16eabecefca |
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2019, 15:33:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | FBDE05F62FA120C5F12C474E14E55353 |
| SHA1: | BF9594AC80D1A2123A8D0843A746056EFD9F005B |
| SHA256: | 11D1EDCC9DA58E5AA76B4D5B8697E330A1A993C9751A10020A5881E2126C85F7 |
| SSDEEP: | 98304:64AinCz+Bq0J6zGmWrrAxFBFs457zAp31EkJMiWb0c:IqCT0Uf8EzBxHO1E/7gc |
MALICIOUS
Application was dropped or rewritten from another process
- HPSetup.exe (PID: 2700)
- setup.exe (PID: 3672)
- HPWMISVC.exe (PID: 1428)
SUSPICIOUS
Executable content was dropped or overwritten
- HPNT.exe (PID: 2376)
- setup.exe (PID: 3672)
- msiexec.exe (PID: 2272)
Creates files in the Windows directory
- HPNT.exe (PID: 2376)
- msiexec.exe (PID: 2272)
Changes the autorun value in the registry
- msiexec.exe (PID: 2272)
Starts CMD.EXE for commands execution
- HPSetup.exe (PID: 2700)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3412)
INFO
Application launched itself
- msiexec.exe (PID: 2272)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3528)
Creates a software uninstall entry
- msiexec.exe (PID: 2272)
Changes settings of System certificates
- DrvInst.exe (PID: 3760)
Creates files in the program directory
- msiexec.exe (PID: 2272)
Searches for installed software
- msiexec.exe (PID: 2272)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:26:10+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 262144 |
| UninitializedDataSize: | 8192 |
| EntryPoint: | 0x3328 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:26:10 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:26:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006077 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41601 |
.rdata | 0x00008000 | 0x00001250 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04481 |
.data | 0x0000A000 | 0x0003D838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22159 |
.ndata | 0x00048000 | 0x00044000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0008C000 | 0x00034B48 | 0x00034C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.2863 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28794 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.76386 | 38056 | UNKNOWN | English - United States | RT_ICON |
3 | 2.9356 | 19496 | UNKNOWN | English - United States | RT_ICON |
4 | 2.99654 | 16936 | UNKNOWN | English - United States | RT_ICON |
5 | 7.94023 | 15006 | UNKNOWN | English - United States | RT_ICON |
6 | 7.94836 | 11662 | UNKNOWN | English - United States | RT_ICON |
7 | 3.23783 | 11432 | UNKNOWN | English - United States | RT_ICON |
8 | 3.23473 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 3.5842 | 5672 | UNKNOWN | English - United States | RT_ICON |
10 | 3.83963 | 4264 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
47
Monitored processes
13
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1428 | "C:\Program Files\HP\HP System Event\HPWMISVC.exe" /Install | C:\Program Files\HP\HP System Event\HPWMISVC.exe | — | msiexec.exe | |||||||||||
User: admin Company: HP Inc. Integrity Level: HIGH Description: HP WMI Service Exit code: 0 Version: 1.4.8.0 Modules
| |||||||||||||||
| 2240 | REG DELETE "HKCU\Software\HP\HP System Event" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | "C:\Users\admin\AppData\Local\Temp\HPNT.exe" | C:\Users\admin\AppData\Local\Temp\HPNT.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2536 | C:\Windows\system32\MsiExec.exe -Embedding 0ED72E05DFD95E2446DB0EA55349C115 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2648 | REG DELETE "HKCU\Software\Hewlett-Packard\HP System Event" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2700 | "C:\SWSetup\SP76260\HPSetup.exe" | C:\SWSetup\SP76260\HPSetup.exe | — | setup.exe | |||||||||||
User: admin Company: Hewlett-Packard Development Company, L.P. Integrity Level: HIGH Description: HP Setup Program Exit code: 0 Version: 1.0.3.0 Modules
| |||||||||||||||
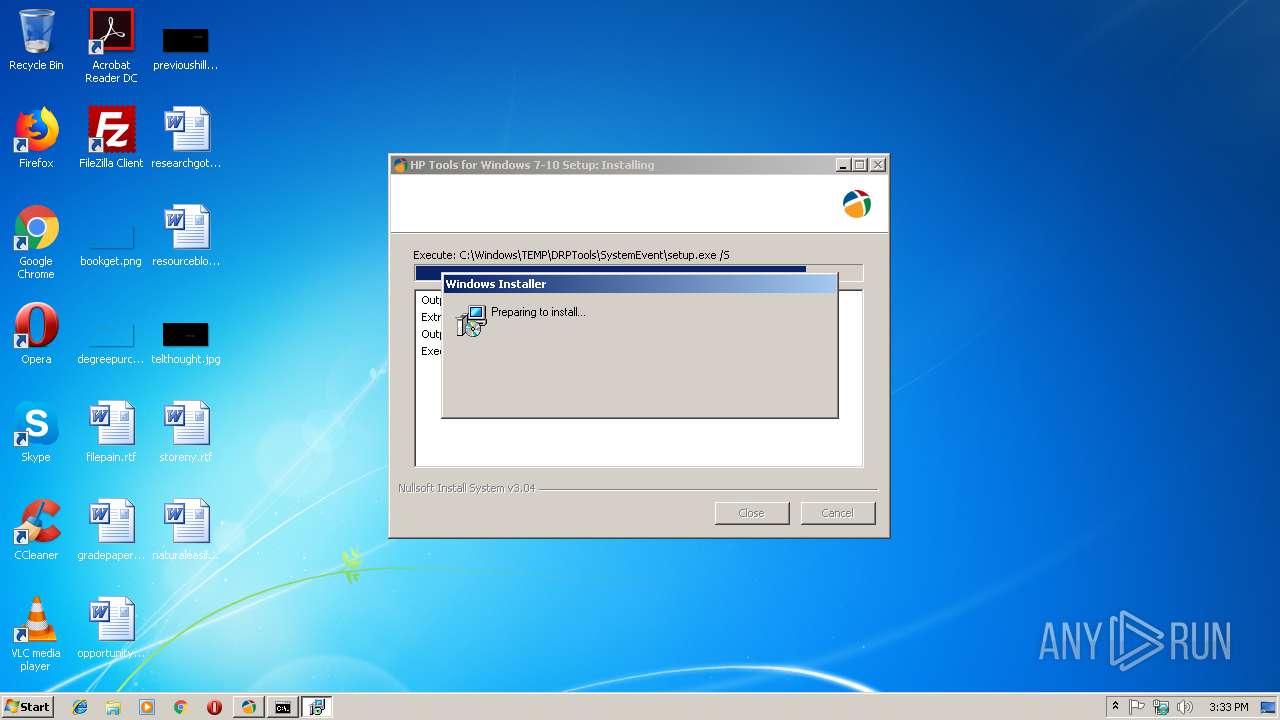
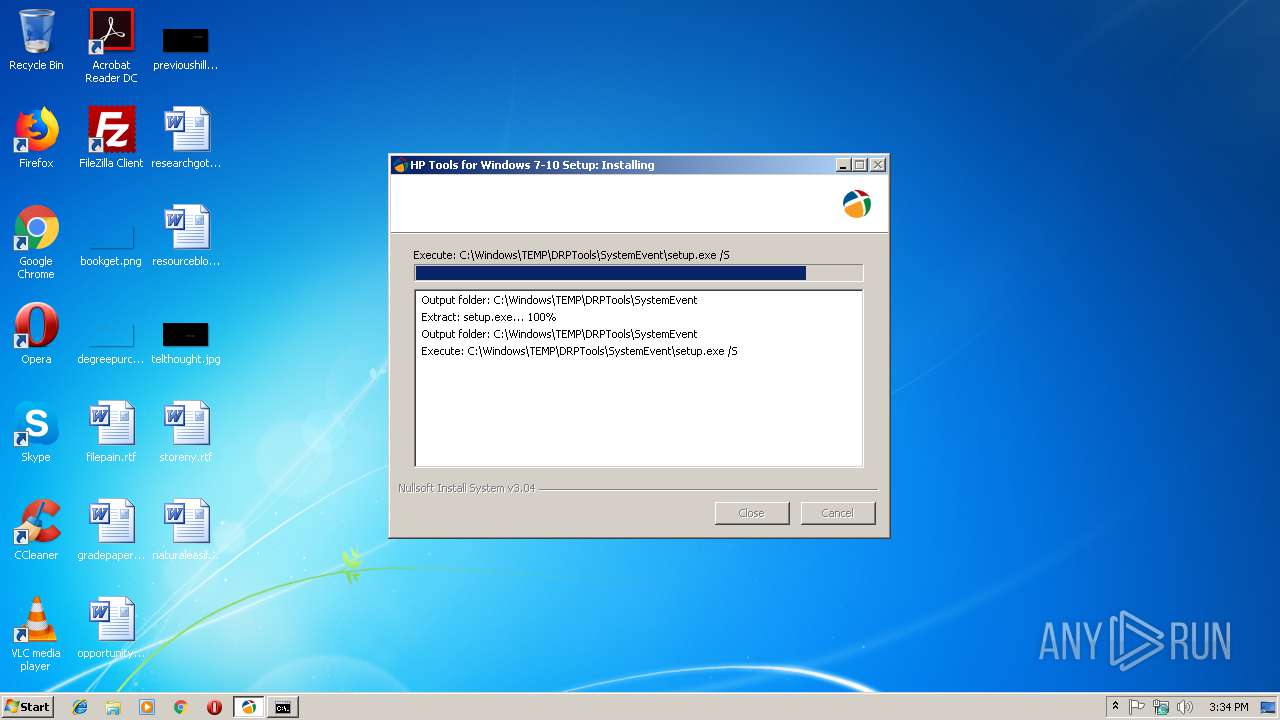
| 3064 | msiexec.exe /i HPSystemEventUtility.msi /passive | C:\Windows\system32\msiexec.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3152 | "C:\Users\admin\AppData\Local\Temp\HPNT.exe" | C:\Users\admin\AppData\Local\Temp\HPNT.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 3412 | cmd /c Install.bat | C:\Windows\system32\cmd.exe | — | HPSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
985
Read events
598
Write events
369
Delete events
18
Modification events
| (PID) Process: | (2272) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000D405A6BAE7ACD401E0080000DC0C0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2272) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000D405A6BAE7ACD401E0080000DC0C0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3528) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E46305BBE7ACD401C80D00001C080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3528) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E46305BBE7ACD401C80D000018080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3528) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E46305BBE7ACD401C80D0000700C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3528) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E46305BBE7ACD401C80D0000580C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3528) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000F28A0CBBE7ACD401C80D0000580C0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3528) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000004CED0EBBE7ACD401C80D00001C080000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3528) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000004CED0EBBE7ACD401C80D000018080000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2272) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
Executable files
20
Suspicious files
10
Text files
115
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | setup.exe | C:\Users\admin\AppData\Local\Temp\extF40A.tmp | — | |
MD5:— | SHA256:— | |||
| 3672 | setup.exe | C:\Users\admin\AppData\Local\Temp\welF409.tmp | — | |
MD5:— | SHA256:— | |||
| 3672 | setup.exe | C:\Users\admin\AppData\Local\Temp\extF41B.tmp | — | |
MD5:— | SHA256:— | |||
| 3672 | setup.exe | C:\Users\admin\AppData\Local\Temp\pftF41C.tmp\pftw1.pkg | — | |
MD5:— | SHA256:— | |||
| 3672 | setup.exe | C:\SWSetup\SP76260\HPSystemEventUtility.msi | — | |
MD5:— | SHA256:— | |||
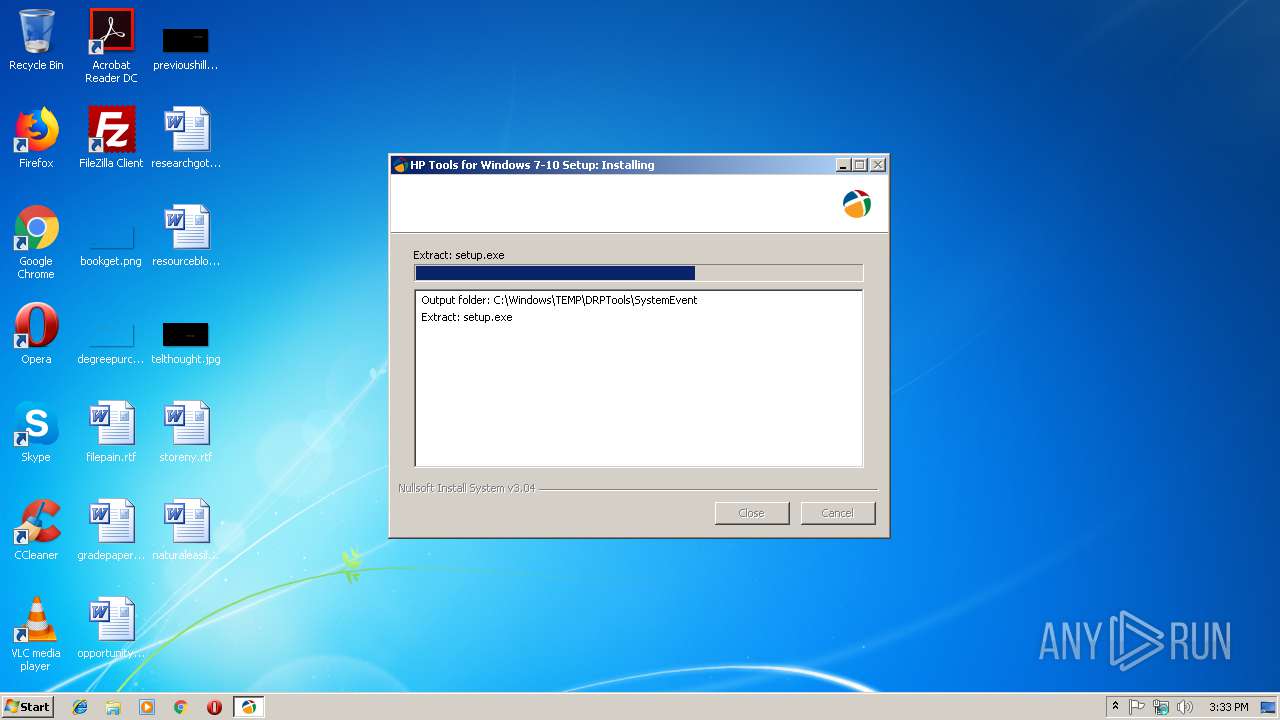
| 2376 | HPNT.exe | C:\Windows\TEMP\DRPTools\SystemEvent\setup.exe | executable | |
MD5:— | SHA256:— | |||
| 3672 | setup.exe | C:\SWSetup\SP76260\Install.bat | text | |
MD5:— | SHA256:— | |||
| 3672 | setup.exe | C:\SWSetup\SP76260\HPSetup.log | ini | |
MD5:— | SHA256:— | |||
| 2700 | HPSetup.exe | C:\SWSetup\SP76260\HPSetup.log | ini | |
MD5:— | SHA256:— | |||
| 3412 | cmd.exe | C:\HP\DATA\HPSE\Button.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report