| File name: | Project1.exe |
| Full analysis: | https://app.any.run/tasks/2e67a0cc-507a-445b-8479-8a7c52a82029 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2019, 06:37:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C5D2480C37DFA380E71B206C857E510A |
| SHA1: | 83433C8AD7BDB58DB8D348D169E42067F6F112B9 |
| SHA256: | 11C8865917C8DF4882262FDB4FD7DE46062B35302EC3737B8D01EC79A19FDE8C |
| SSDEEP: | 12288:eEUMj5k/dRgupUgcQ2nIw7M8YyqnuFgUs2:eVFTg0CQ2Iccy+uPs2 |
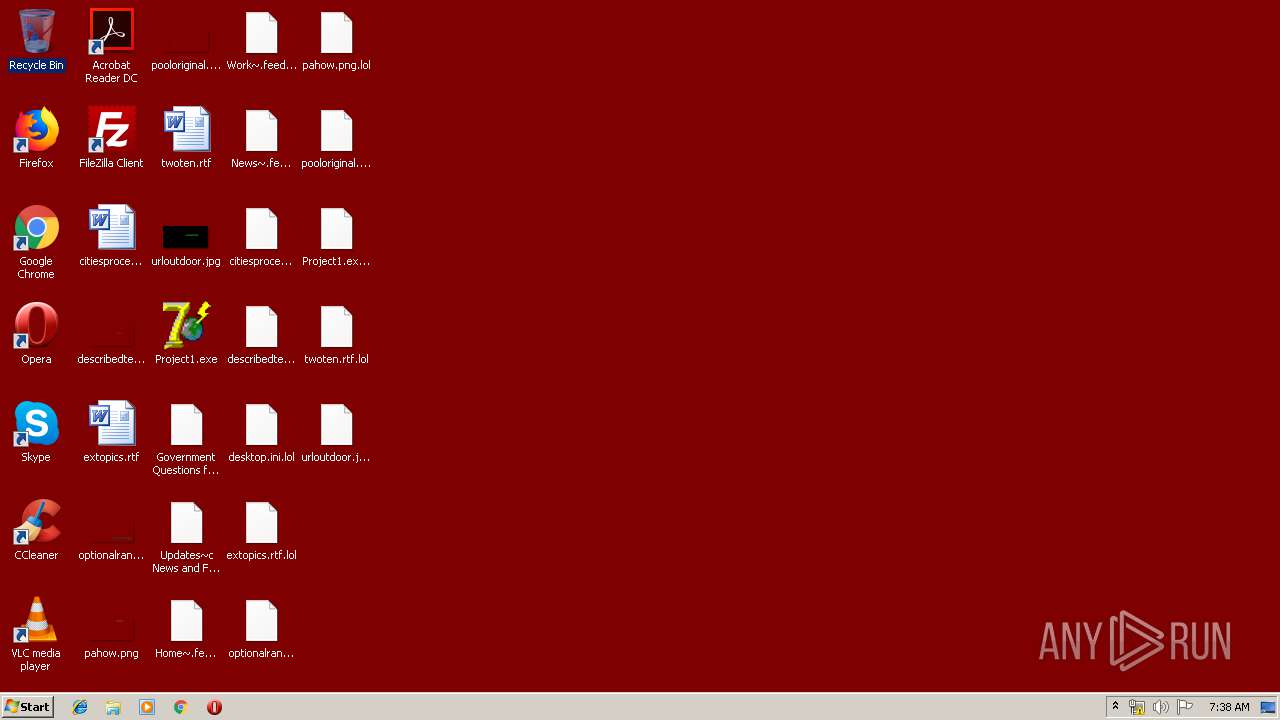
MALICIOUS
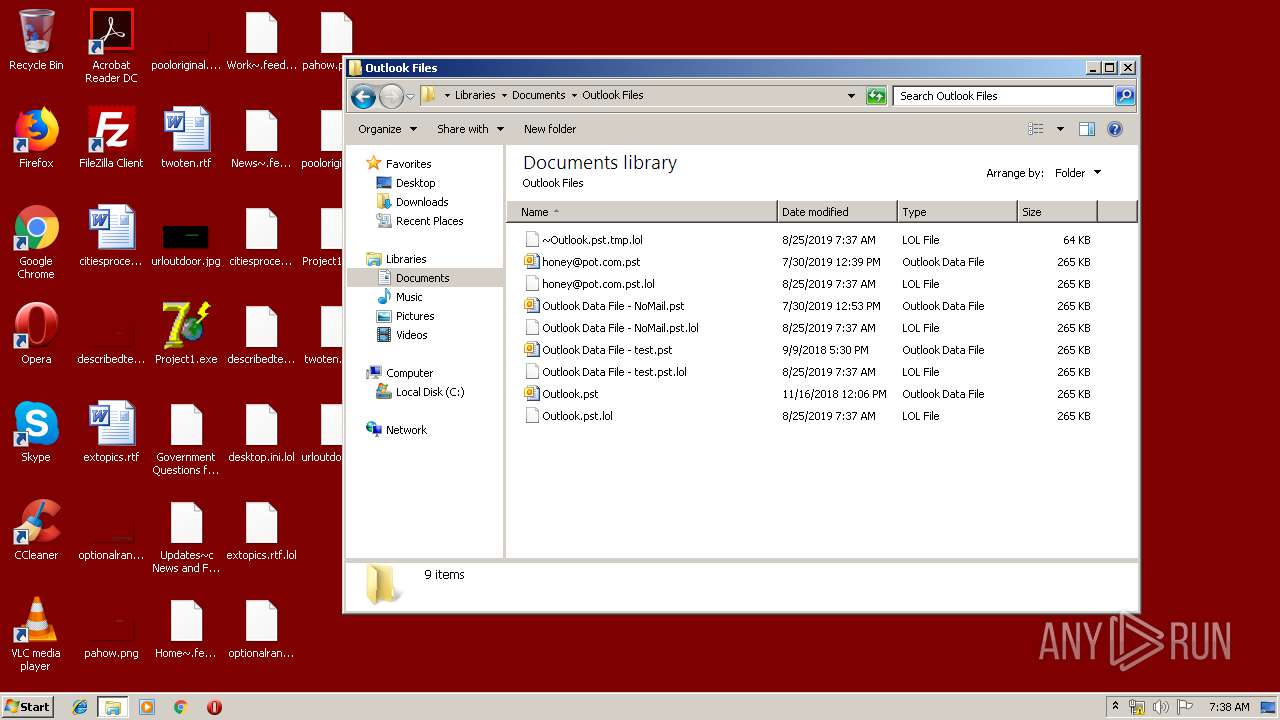
Actions looks like stealing of personal data
- Project1.exe (PID: 3352)
SUSPICIOUS
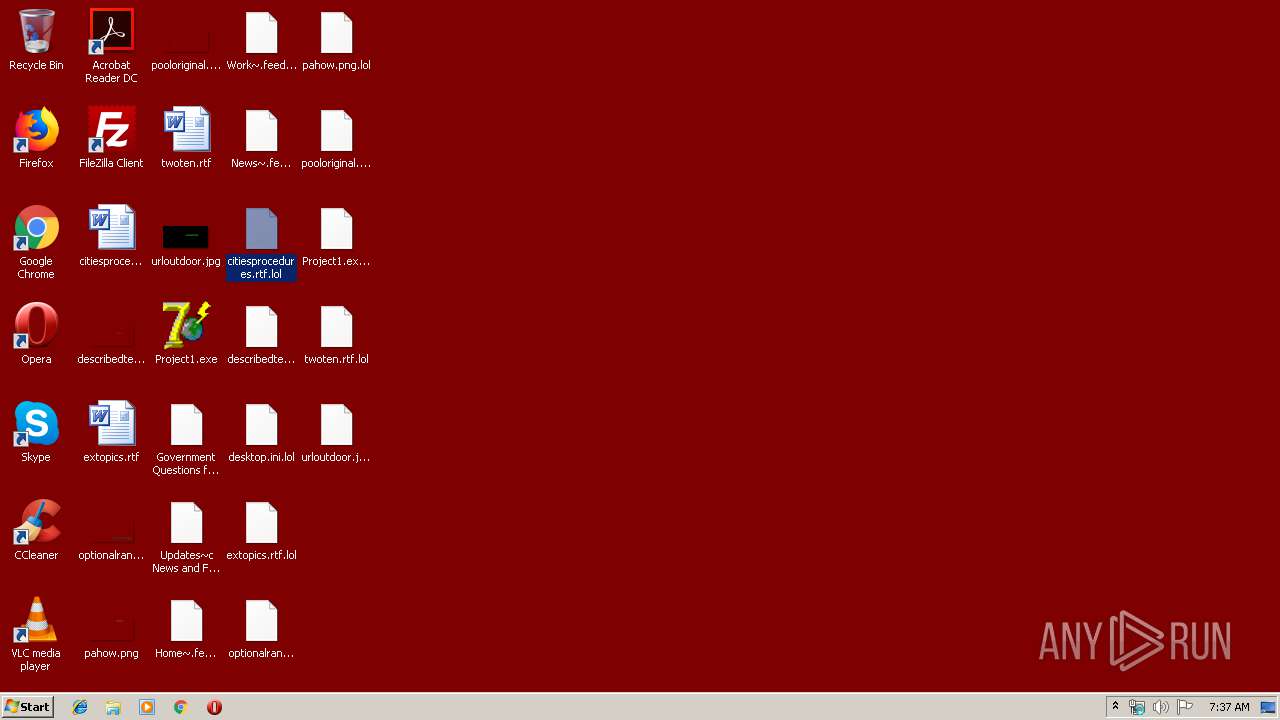
Executable content was dropped or overwritten
- Project1.exe (PID: 3352)
Reads the cookies of Mozilla Firefox
- Project1.exe (PID: 3352)
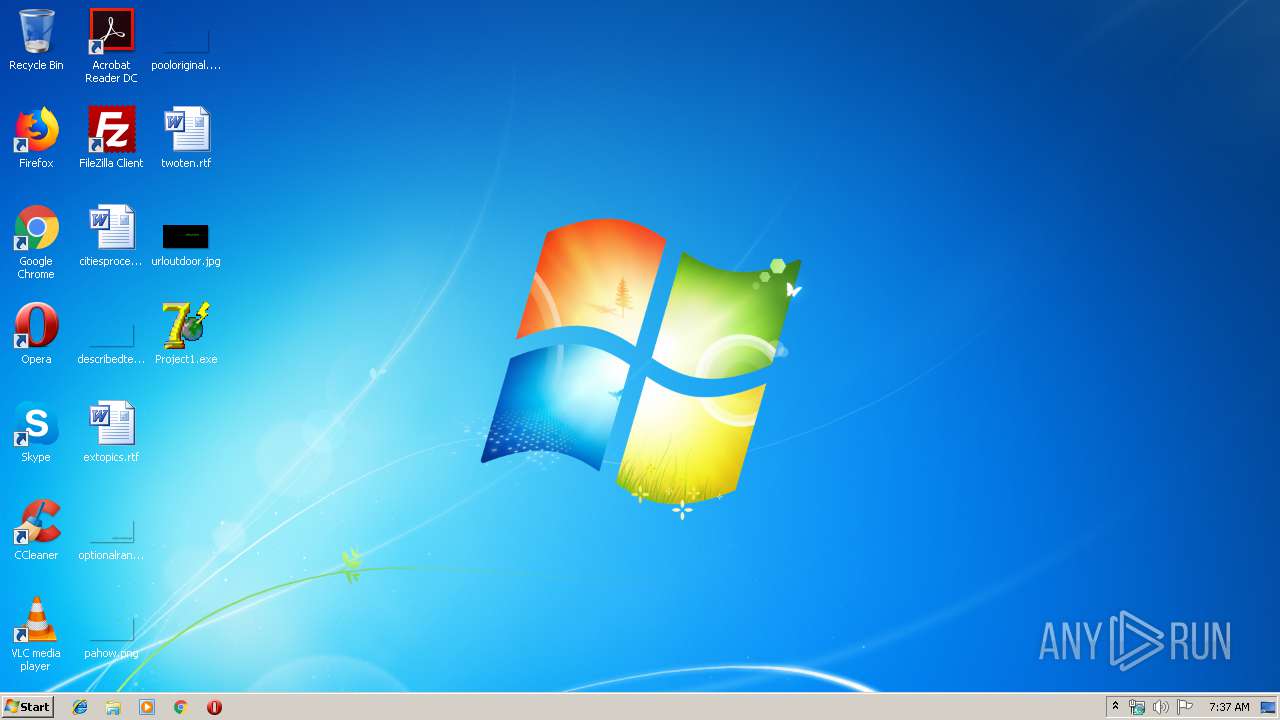
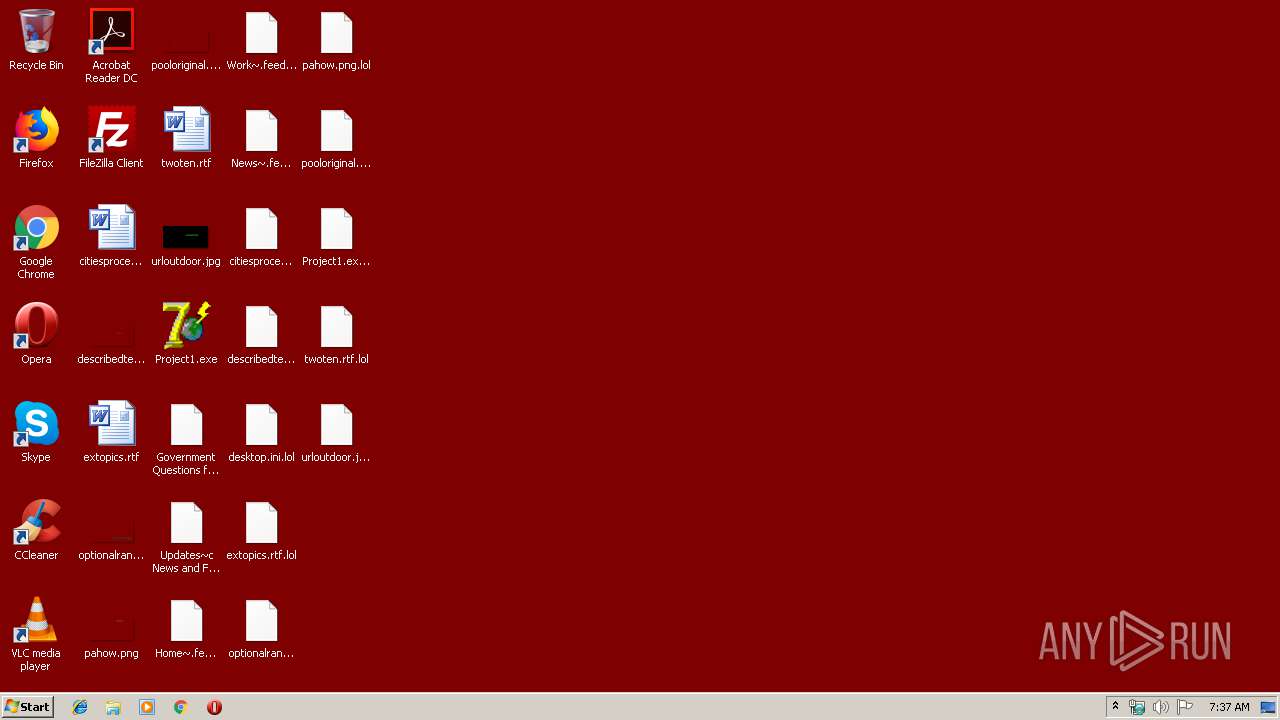
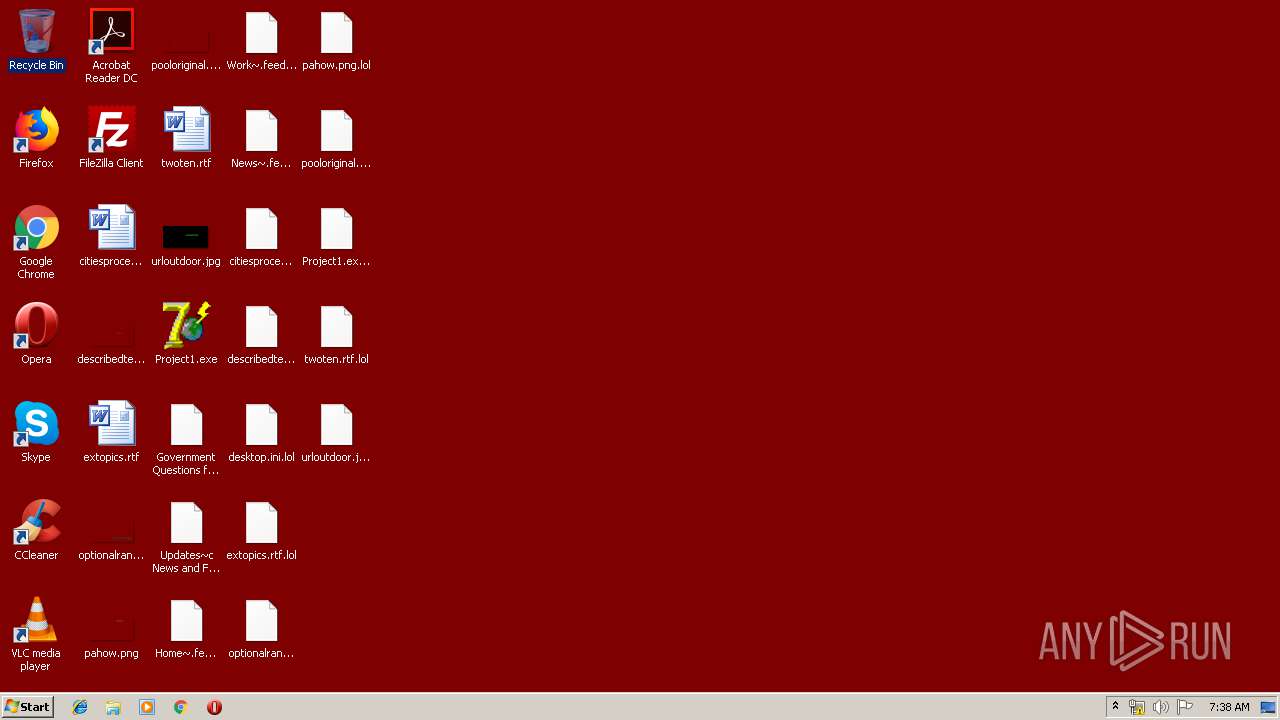
Changes the desktop background image
- Project1.exe (PID: 3352)
Creates files in the user directory
- Project1.exe (PID: 3352)
- notepad++.exe (PID: 2204)
Creates files in the program directory
- Project1.exe (PID: 3352)
INFO
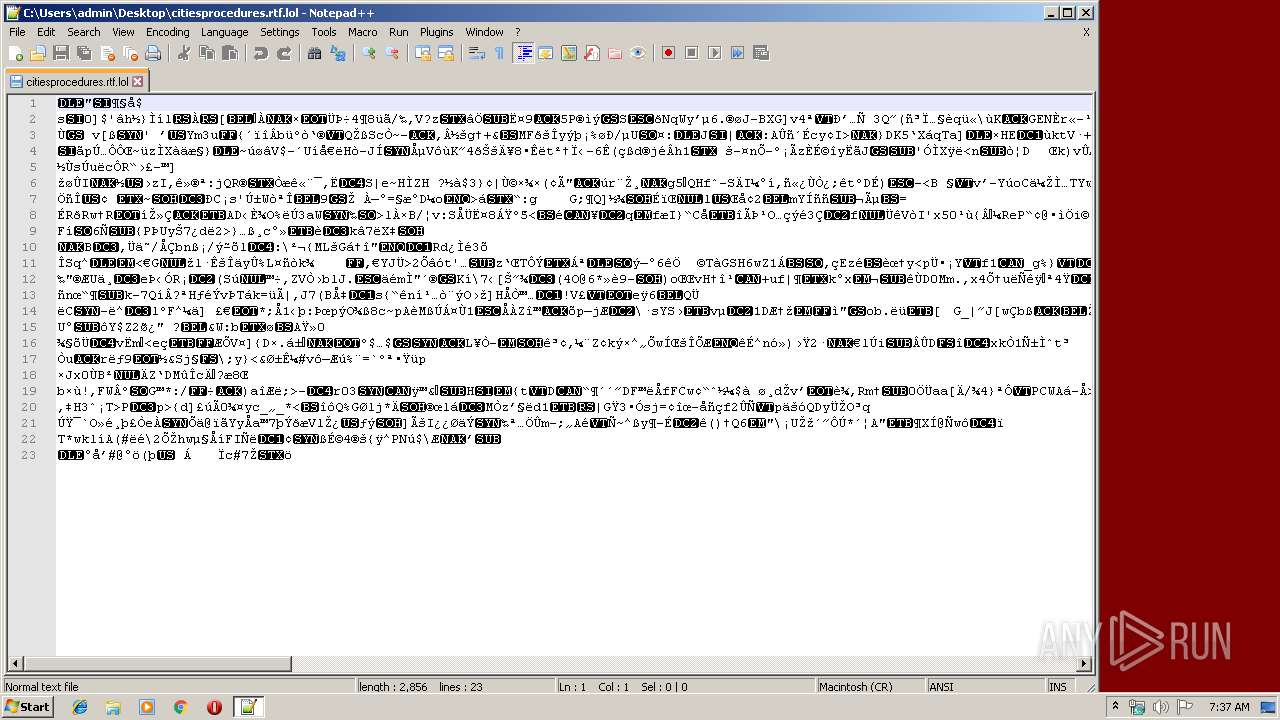
Dropped object may contain Bitcoin addresses
- Project1.exe (PID: 3352)
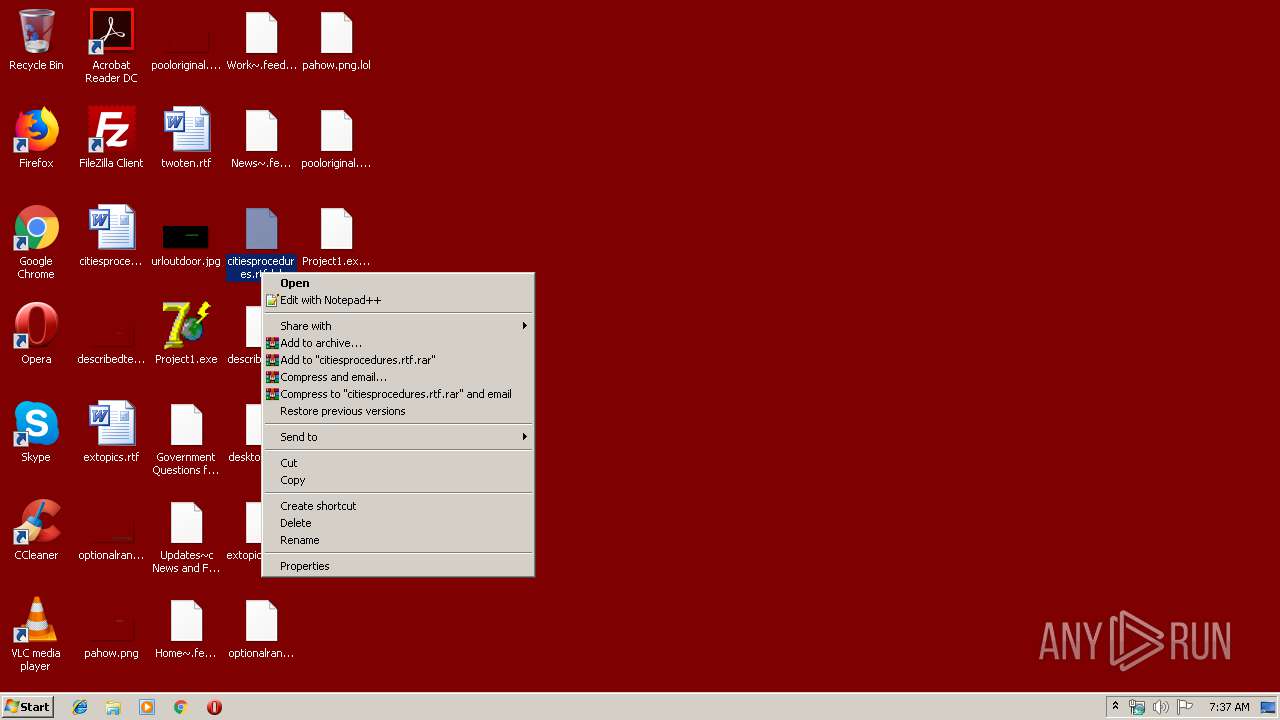
Manual execution by user
- notepad++.exe (PID: 2204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (68.4) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 6 (27) |
| .exe | | | Win32 Executable Delphi generic (1.4) |
| .scr | | | Windows screen saver (1.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 363520 |
| InitializedDataSize: | 86528 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x59b74 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00058BBC | 0x00058C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55354 |
DATA | 0x0005A000 | 0x00004530 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.37528 |
BSS | 0x0005F000 | 0x00000BA9 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00060000 | 0x00002136 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96702 |
.tls | 0x00063000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00064000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x00065000 | 0x000063D8 | 0x00006400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.6862 |
.rsrc | 0x0006C000 | 0x00008400 | 0x00008400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.80868 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.85232 | 744 | UNKNOWN | Russian - Russia | RT_ICON |
2 | 2.80231 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4081 | 2.88322 | 336 | UNKNOWN | UNKNOWN | RT_STRING |
4082 | 3.35401 | 496 | UNKNOWN | UNKNOWN | RT_STRING |
4083 | 3.27601 | 456 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
user32.dll |
version.dll |
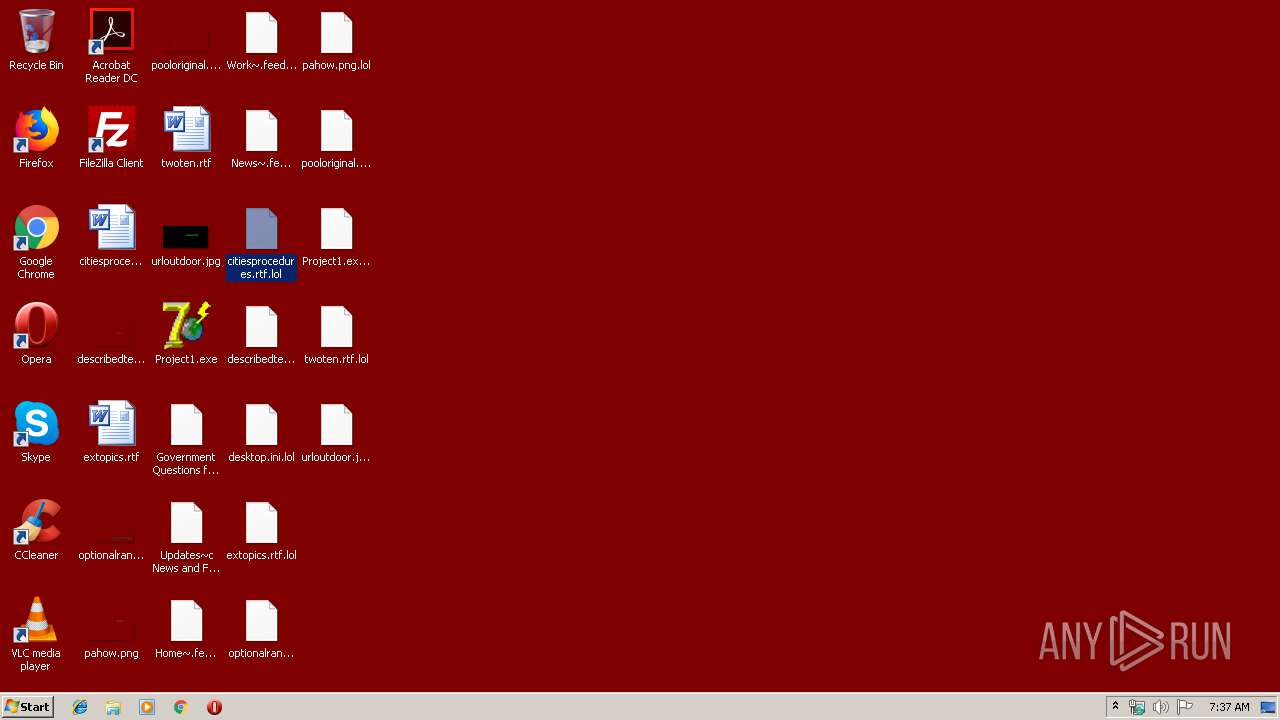
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2204 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\citiesprocedures.rtf.lol" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 3352 | "C:\Users\admin\Desktop\Project1.exe" | C:\Users\admin\Desktop\Project1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3468 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
Total events
91
Read events
74
Write events
17
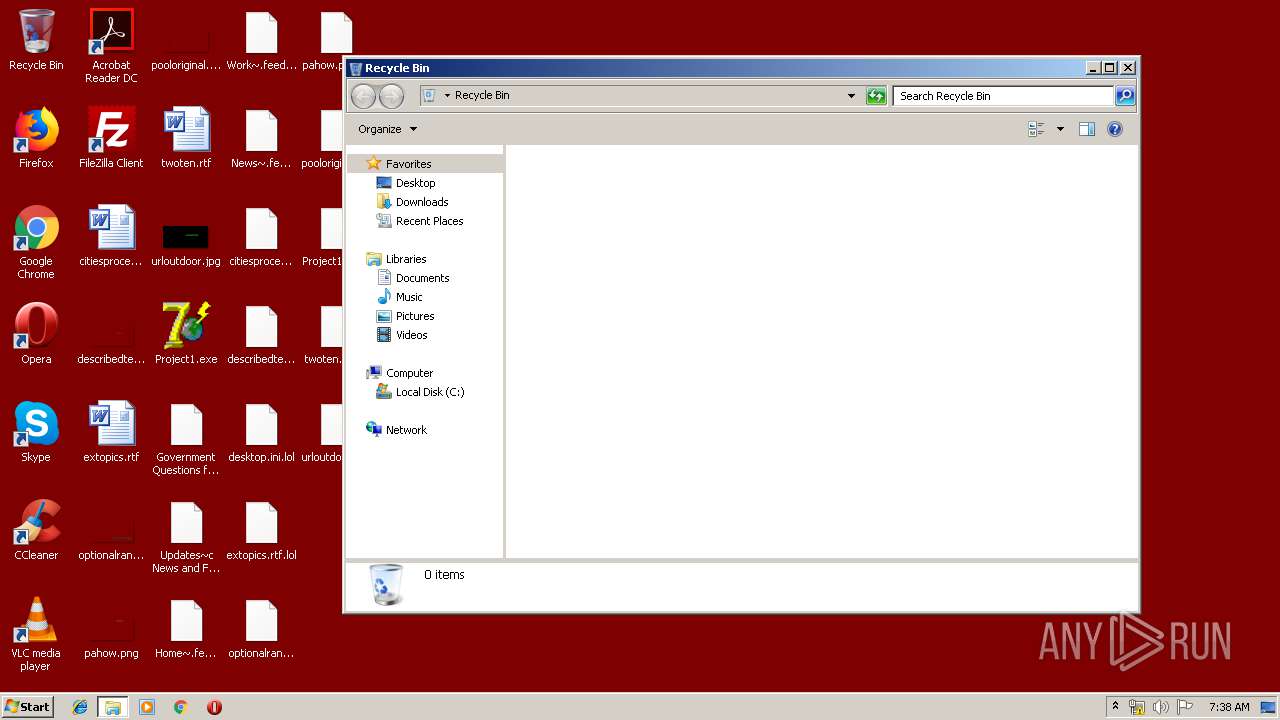
Delete events
0
Modification events
| (PID) Process: | (3352) Project1.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | TileWallpaper |
Value: 0 | |||
| (PID) Process: | (3352) Project1.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | WallpaperStyle |
Value: 10 | |||
| (PID) Process: | (3352) Project1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Desktop\General |
| Operation: | write | Name: | WallpaperSource |
Value: C:\vsworkdir\shantazh.jpg | |||
| (PID) Process: | (2204) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2204) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2204) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
54
Suspicious files
680
Text files
27
Unknown types
10
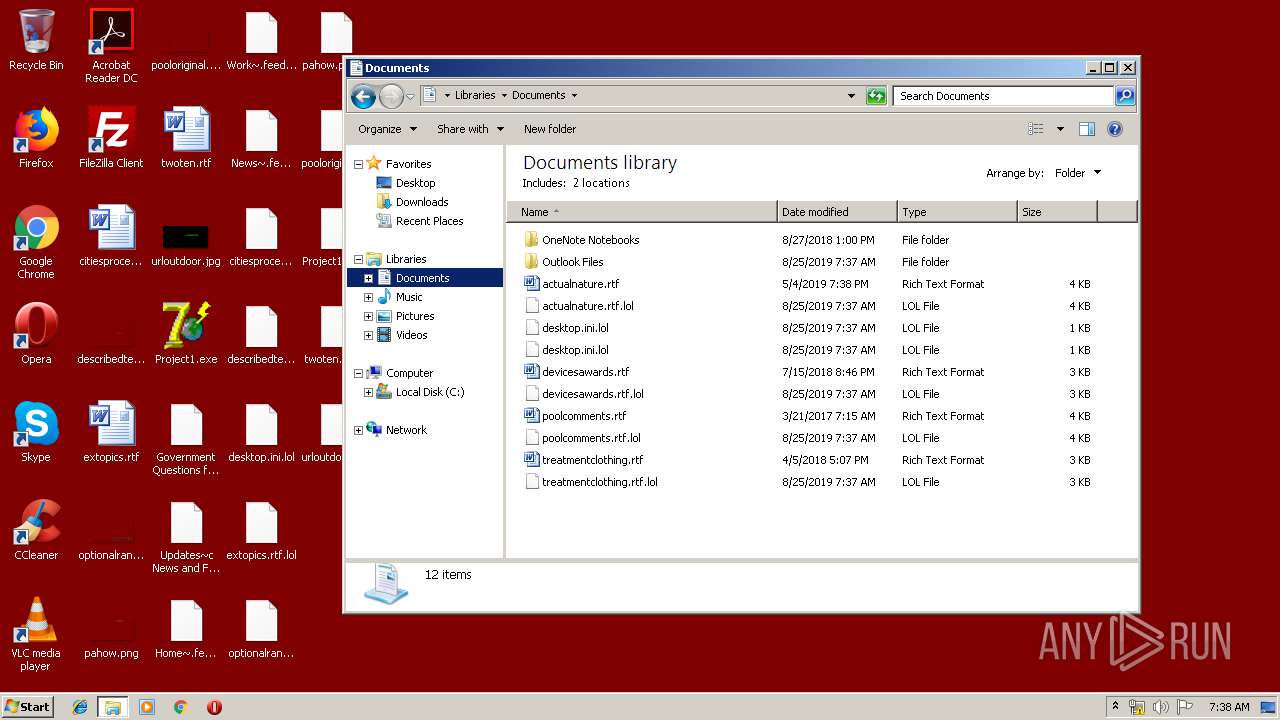
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3352 | Project1.exe | C:\vsworkdir\CSCA1.DLL | executable | |
MD5:— | SHA256:— | |||
| 3352 | Project1.exe | C:\Users\admin\AppData\Local\CEF\User Data\CrashpadMetrics-active.pma.lol | binary | |
MD5:— | SHA256:— | |||
| 3352 | Project1.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\IconCacheRdr.dat.lol | binary | |
MD5:— | SHA256:— | |||
| 3352 | Project1.exe | C:\Users\admin\AppData\Local\CEF\User Data\CrashpadMetrics.pma.lol | binary | |
MD5:— | SHA256:— | |||
| 3352 | Project1.exe | C:\Users\admin\AppData\Local\FileZilla\default_close12x12.png.lol | binary | |
MD5:— | SHA256:— | |||
| 3352 | Project1.exe | C:\Users\admin\AppData\Local\FileZilla\default_auto16x16.png.lol | binary | |
MD5:— | SHA256:— | |||
| 3352 | Project1.exe | C:\Users\admin\AppData\Local\FileZilla\default_cancel20x20.png.lol | binary | |
MD5:— | SHA256:— | |||
| 3352 | Project1.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\UserCache.bin.lol | binary | |
MD5:— | SHA256:— | |||
| 3352 | Project1.exe | C:\Users\admin\AppData\Local\Adobe\Color\Profiles\wscRGB.icc.lol | binary | |
MD5:— | SHA256:— | |||
| 3352 | Project1.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\IconCacheRdr65536.dat.lol | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 92.122.244.34:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | FR | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 92.122.244.34:80 | isrg.trustid.ocsp.identrust.com | GTT Communications Inc. | FR | unknown |
3468 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|