| URL: | http://www.celebzz.com |
| Full analysis: | https://app.any.run/tasks/d19aff92-d212-4303-93ab-b0f44bbb88aa |
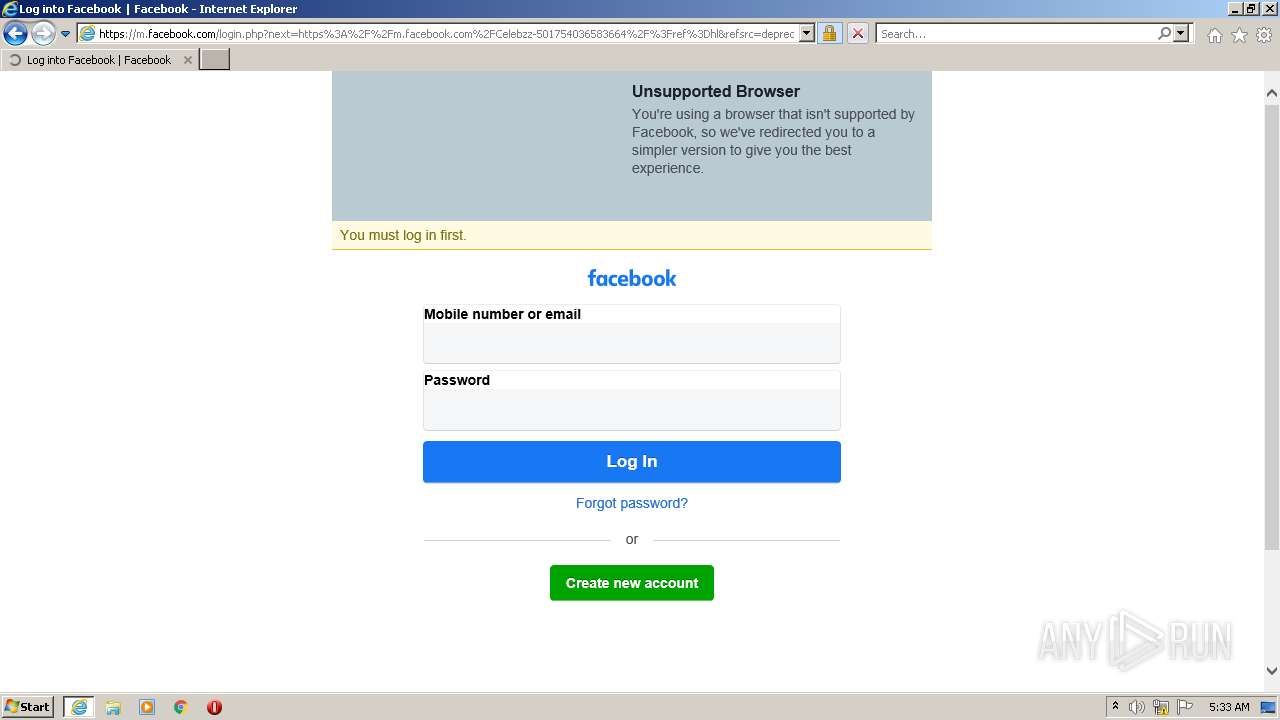
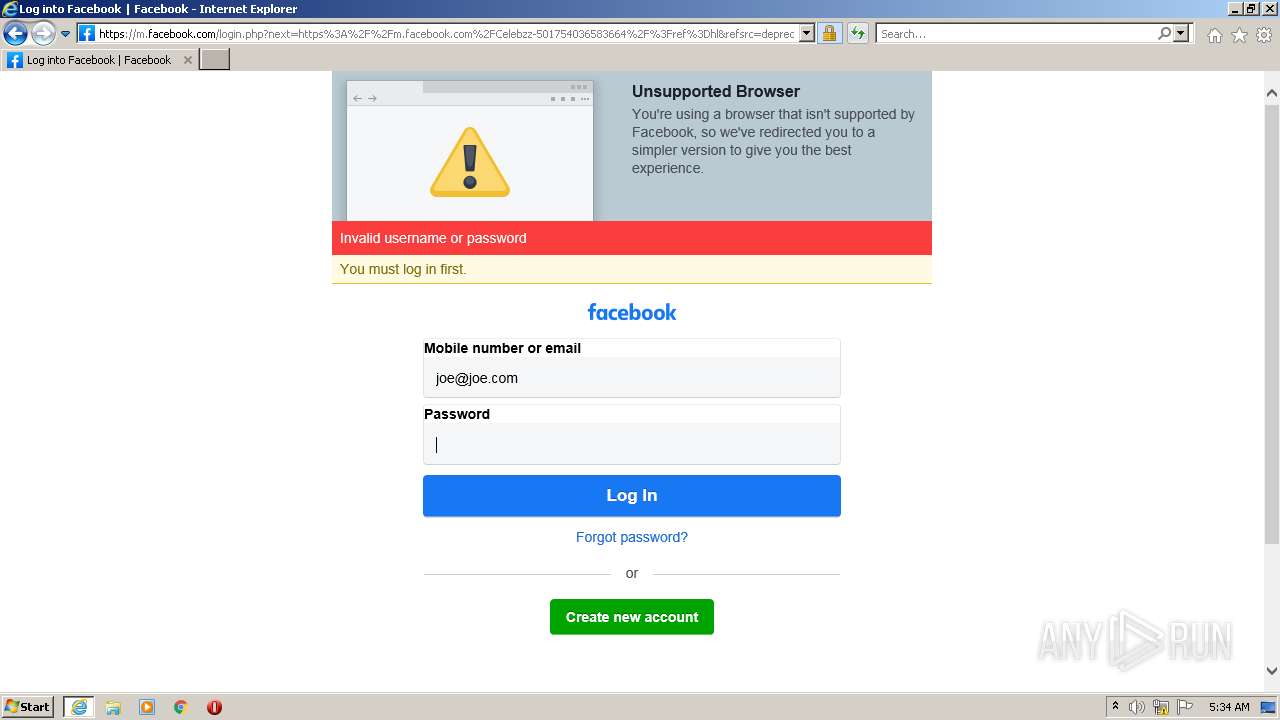
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2022, 05:32:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E8E50AF5F633CF24F51E96F3B7B68CE9 |
| SHA1: | 83C86058BA0C1297931E0E386DE91A5628EF1580 |
| SHA256: | 11C3138D361EC431DE8D43A7A15CAF8C2FE8CDA1AE3981A86650DB02D0723B44 |
| SSDEEP: | 3:N1KJS4ZAHG:Cc4+m |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3832)
INFO
Reads the computer name
- iexplore.exe (PID: 2752)
- iexplore.exe (PID: 3832)
Changes internet zones settings
- iexplore.exe (PID: 2752)
Application launched itself
- iexplore.exe (PID: 2752)
Checks supported languages
- iexplore.exe (PID: 3832)
- iexplore.exe (PID: 2752)
Creates files in the user directory
- iexplore.exe (PID: 3832)
- iexplore.exe (PID: 2752)
Reads internet explorer settings
- iexplore.exe (PID: 3832)
Reads settings of System Certificates
- iexplore.exe (PID: 2752)
- iexplore.exe (PID: 3832)
Checks Windows Trust Settings
- iexplore.exe (PID: 3832)
- iexplore.exe (PID: 2752)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2752)
Changes settings of System certificates
- iexplore.exe (PID: 2752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2752 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.celebzz.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3832 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2752 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
35 338
Read events
35 057
Write events
279
Delete events
2
Modification events
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30934499 | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30934499 | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
22
Text files
248
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\dd-multi-col-cats[1].css | text | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\main[1].js | text | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\jordyn-woods-puts-on-a-sexy-display-of-her-curvy-figure-as-she-arrives-for-a-late-night-dinner-at-craig-s-restaurant-in-west-hollywood-6_thumbnail-160x222[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\72SSBRVM.htm | html | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\alex-jones-looks-sensational-wearing-a-rose-red-dress-after-appearing-on-bbc-the-one-show-in-london-8_thumbnail-160x222[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\layout[1].css | text | |
MD5:F6FAED6EAED92B2021500E5A3CA32992 | SHA256:F0B92945F599CD606ACB1D5BF60B30D1F6A6B4CEE0FF6CB8EA0A29E6903A8CAE | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\st_insights[1].htm | html | |
MD5:E4E384D6672787C1BB2A9B500114F1F5 | SHA256:80785F5520097DDE3B28C617171415CD690CBF1E0353A5F3E348C83A4656EA0F | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\email-decode.min[1].js | html | |
MD5:9E8F56E8E1806253BA01A95CFC3D392C | SHA256:2595496FE48DF6FCF9B1BC57C29A744C121EB4DD11566466BC13D2E52E6BBCC8 | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\jquery-migrate.min[1].js | text | |
MD5:7121994EEC5320FBE6586463BF9651C2 | SHA256:48EB8B500AE6A38617B5738D2B3FAEC481922A7782246E31D2755C034A45CD5D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
151
TCP/UDP connections
198
DNS requests
47
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3832 | iexplore.exe | GET | — | 172.67.200.178:80 | http://www.celebzz.com/wp-content/uploads/2022/01/camila-morrone-in-a-skimpy-black-bikini-enjoying-the-beach-in-st-barts-22_thumbnail.jpg | US | — | — | malicious |
3832 | iexplore.exe | GET | — | 172.67.200.178:80 | http://www.celebzz.com/wp-content/uploads/2022/01/cybill-shepherd-was-seen-out-for-an-afternoon-walk-in-los-angeles-11_thumbnail-160x222.jpg | US | — | — | malicious |
3832 | iexplore.exe | GET | — | 172.67.200.178:80 | http://www.celebzz.com/ | US | — | — | malicious |
3832 | iexplore.exe | GET | — | 172.67.200.178:80 | http://www.celebzz.com/wp-includes/css/dist/block-library/style.min.css?ver=5.4.2 | US | — | — | malicious |
3832 | iexplore.exe | GET | — | 172.67.200.178:80 | http://www.celebzz.com/wp-content/plugins/special-recent-posts/cache/srpthumb-p4048821-160x240-no.jpg | US | — | — | malicious |
3832 | iexplore.exe | GET | — | 172.67.200.178:80 | http://www.celebzz.com/wp-content/themes/hawtmen/dd-multi-col-cats.css | US | — | — | malicious |
3832 | iexplore.exe | GET | 200 | 172.67.200.178:80 | http://www.celebzz.com/wp-content/plugins/special-recent-posts/cache/srpthumb-p4048755-160x240-no.jpg | US | compressed | 6.41 Kb | malicious |
3832 | iexplore.exe | GET | 200 | 172.67.200.178:80 | http://www.celebzz.com/wp-content/themes/hawtmen/js/main.js | US | text | 258 b | malicious |
3832 | iexplore.exe | GET | 200 | 172.67.200.178:80 | http://www.celebzz.com/wp-content/themes/hawtmen/style.css | US | text | 5.80 Kb | malicious |
3832 | iexplore.exe | GET | 301 | 18.66.139.74:80 | http://w.sharethis.com/button/st_insights.js?publisher=4d48b7c5-0ae3-43d4-bfbe-3ff8c17a8ae6&product=simpleshare | US | html | 183 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3832 | iexplore.exe | 172.67.200.178:80 | www.celebzz.com | — | US | suspicious |
3832 | iexplore.exe | 104.18.10.207:80 | maxcdn.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
3832 | iexplore.exe | 104.26.5.7:80 | waust.at | Cloudflare Inc | US | suspicious |
3832 | iexplore.exe | 216.58.207.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3832 | iexplore.exe | 37.48.65.143:80 | celebs.gallery | LeaseWeb Netherlands B.V. | NL | malicious |
3832 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3832 | iexplore.exe | 104.18.14.19:443 | ad.impactify.io | Cloudflare Inc | US | unknown |
3832 | iexplore.exe | 18.66.139.118:80 | cdn2.lockerdomecdn.com | Massachusetts Institute of Technology | US | unknown |
3832 | iexplore.exe | 142.250.184.227:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3832 | iexplore.exe | 172.255.6.144:80 | yepsawomen.com | — | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.celebzz.com |
| malicious |
celebs.gallery |
| malicious |
maxcdn.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
w.sharethis.com |
| shared |
services.vlitag.com |
| shared |
waust.at |
| malicious |
www.google-analytics.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
api.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3832 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |