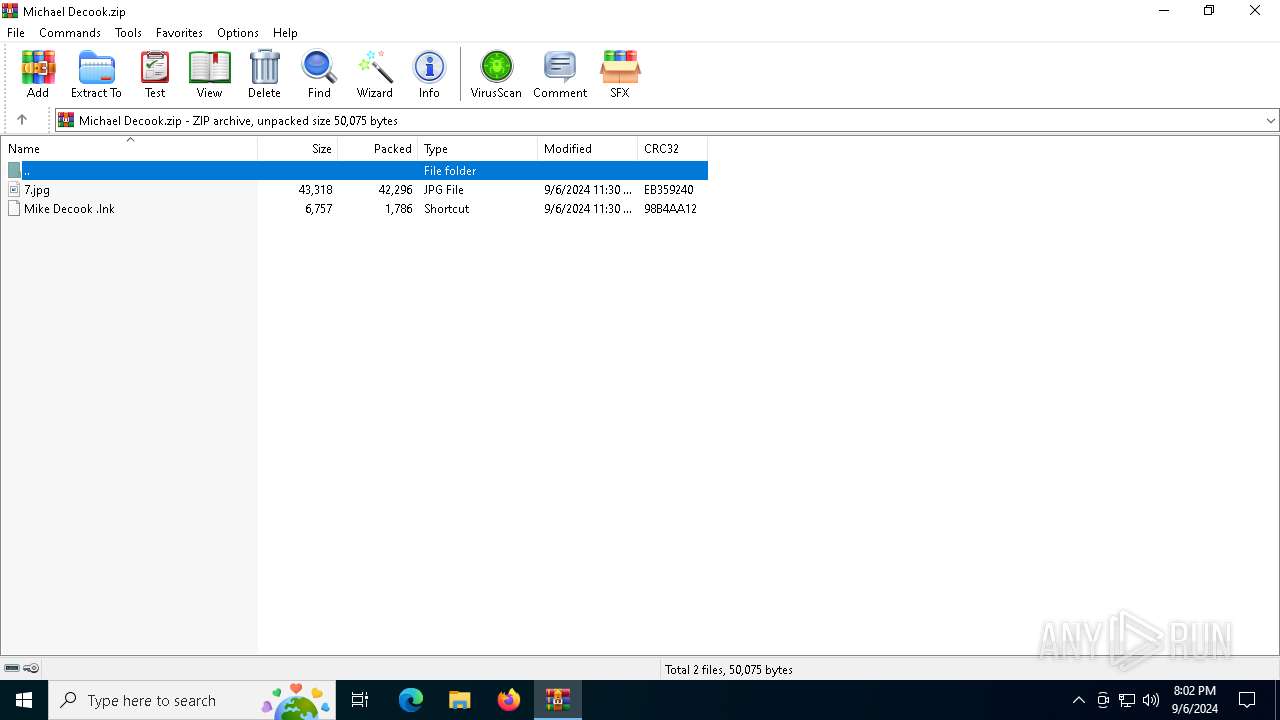
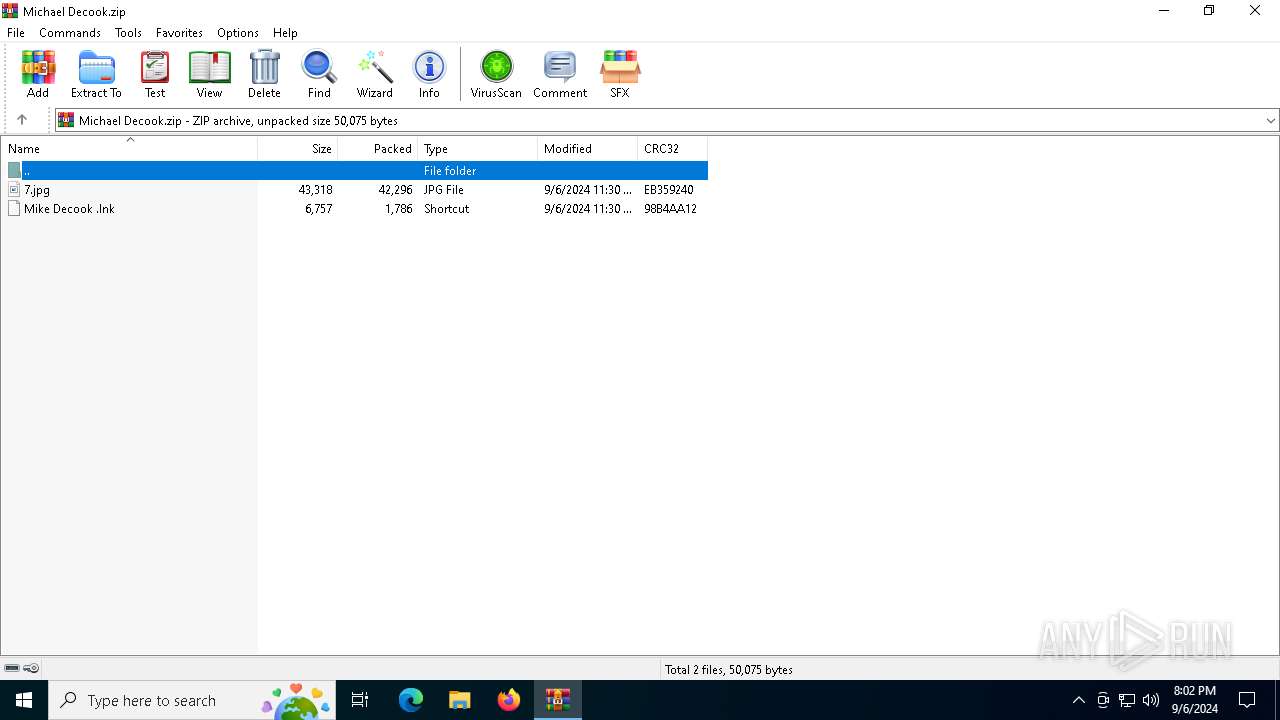
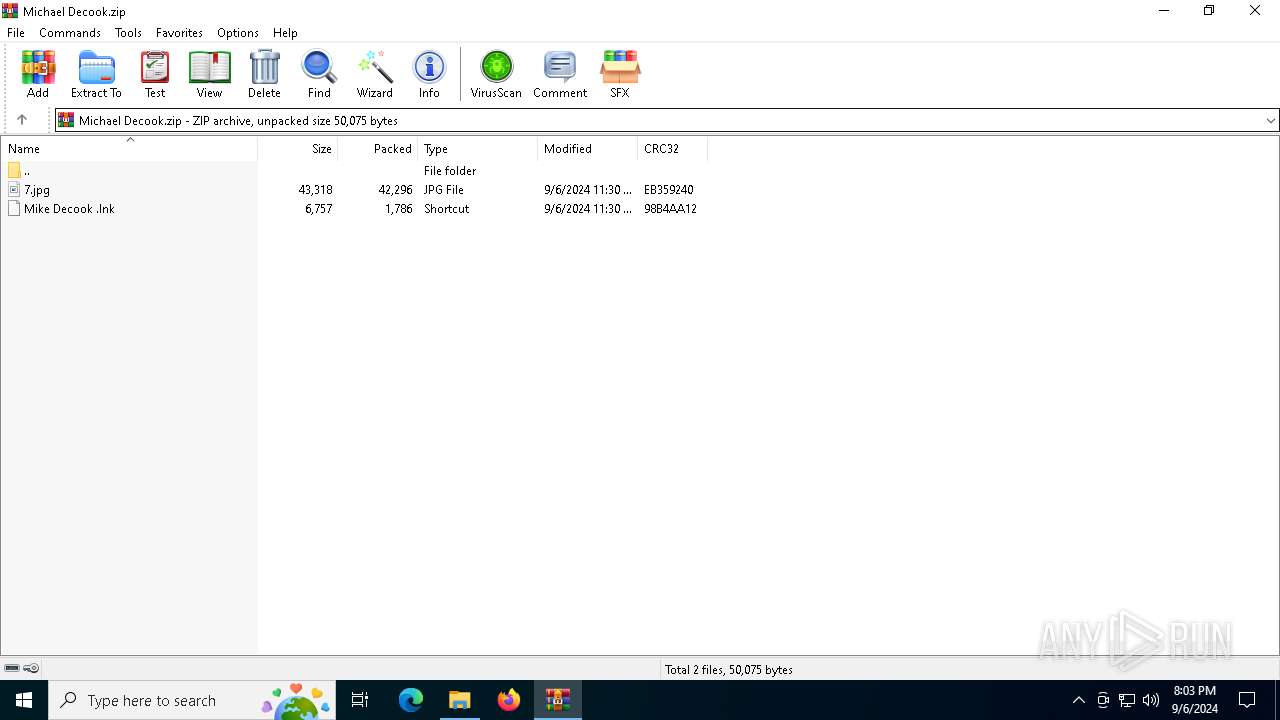
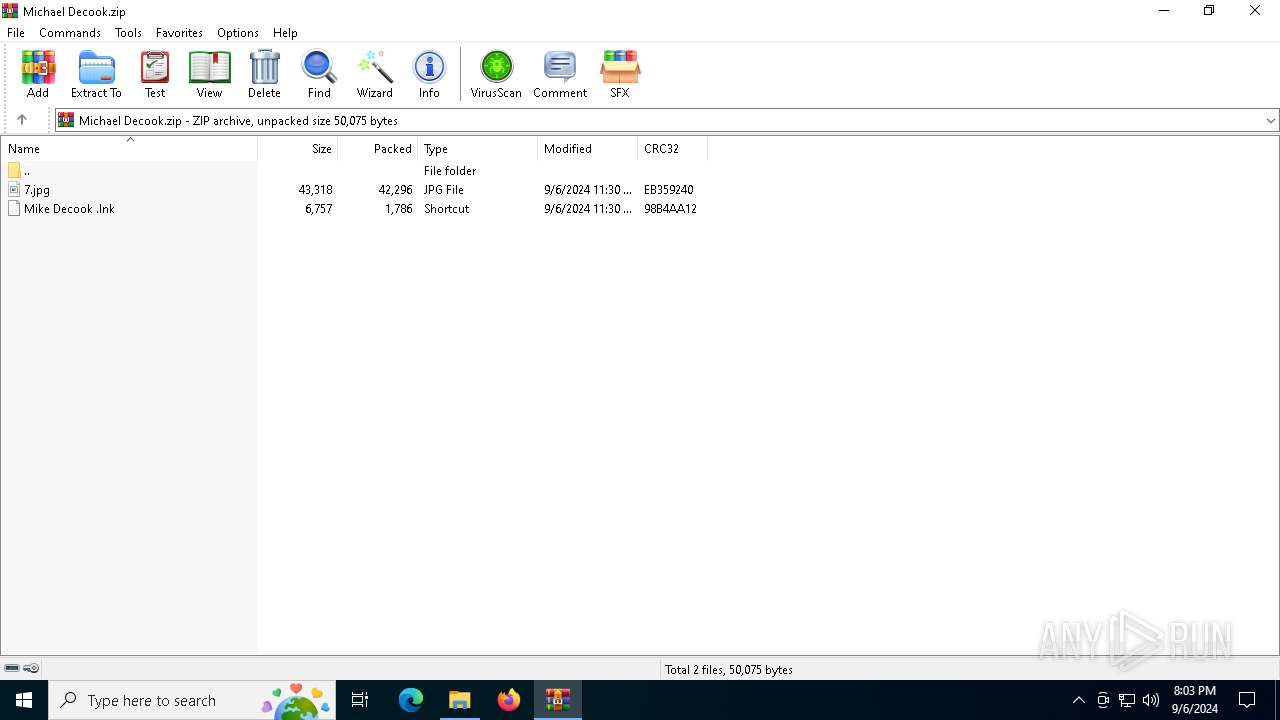
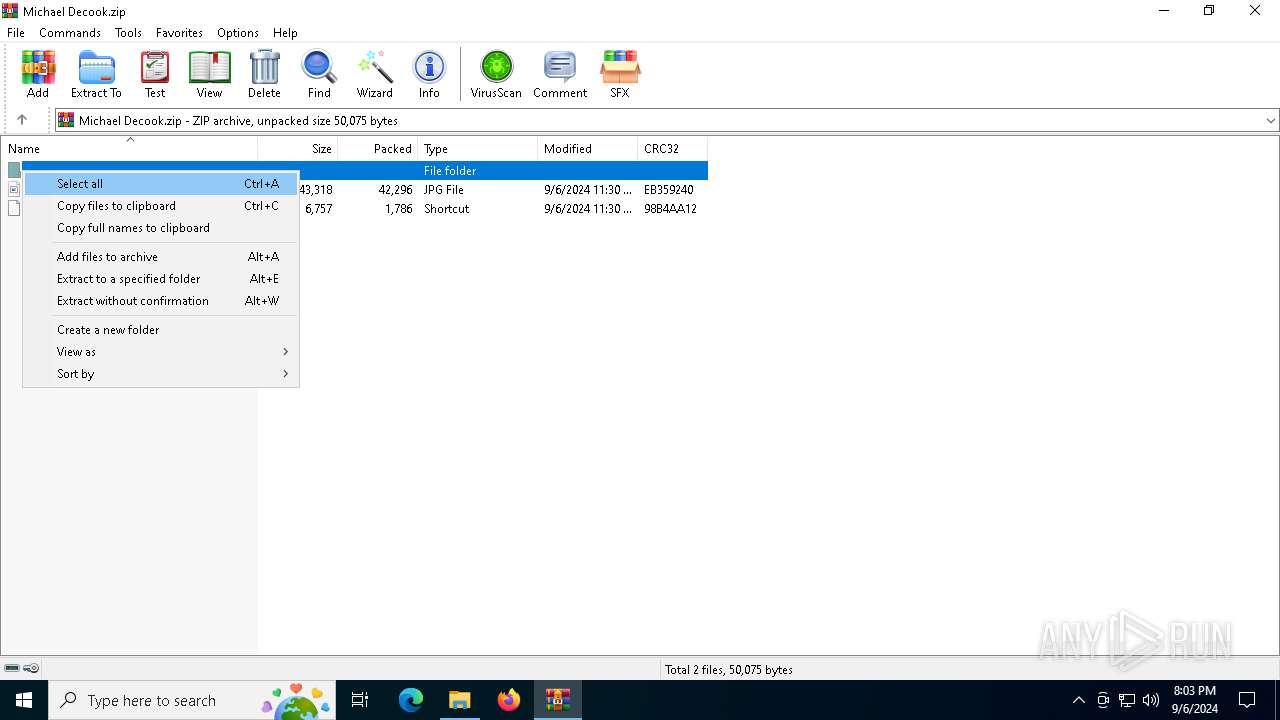
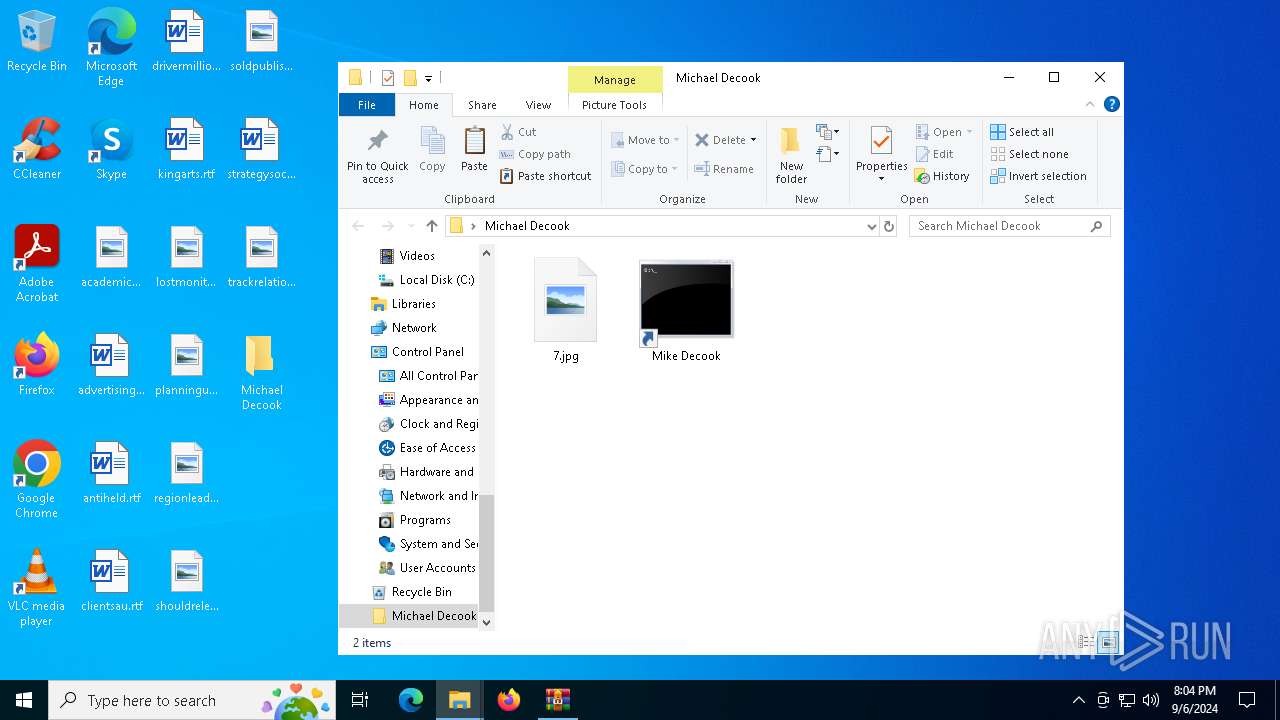
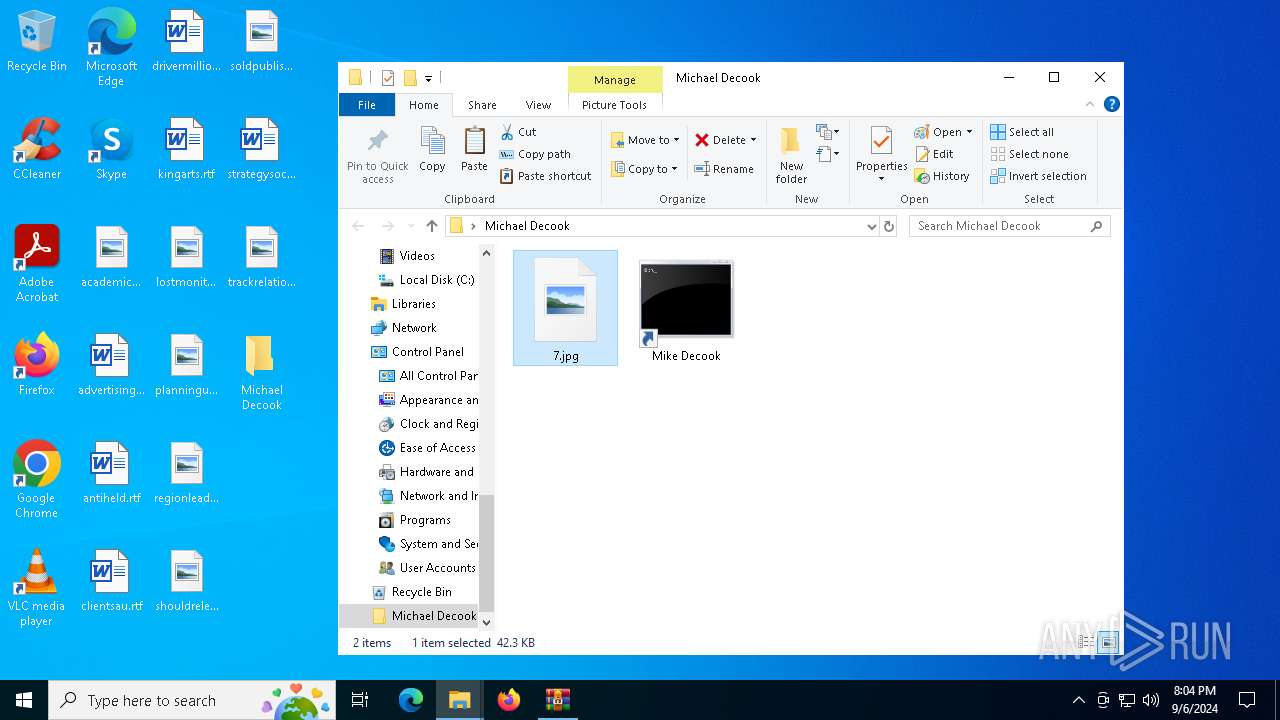
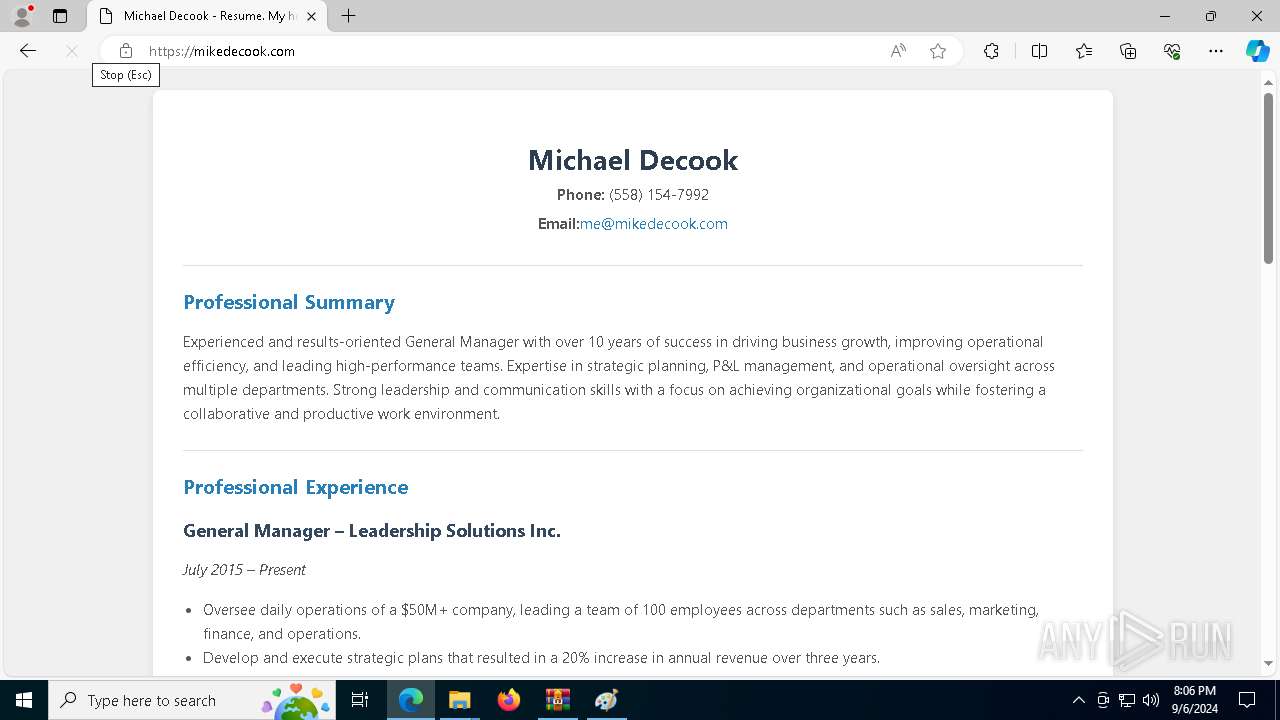
| File name: | Michael Decook.zip |
| Full analysis: | https://app.any.run/tasks/3b044dde-a4cd-45de-bb5f-c0fde0fcf37f |
| Verdict: | Malicious activity |
| Analysis date: | September 06, 2024, 20:02:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 2061310A310DF5EED3EB29AA9AC82E15 |
| SHA1: | 341AFBC7A7C01847648AFF67C835A96ACF6F9CAD |
| SHA256: | 11BED6353B56C2A562B586ABE85121DDA4AC7A581BCCFA07425F23148D293F28 |
| SSDEEP: | 768:kQEuTN4w00aafUnlvPNAhjmzyzEuoSna/0yLBMFPJ2/cp7MMz/3tRwyC0iTh0ng:zB+gJS3qjmezi06MFPnMMz/9R1CjKg |
MALICIOUS
No malicious indicators.SUSPICIOUS
Uses WMIC.EXE to create a new process
- cmd.exe (PID: 6320)
- cmd.exe (PID: 448)
Application launched itself
- cmd.exe (PID: 6160)
- ie4uinit.exe (PID: 6516)
- ie4uinit.exe (PID: 4576)
- cmd.exe (PID: 3424)
Executable content was dropped or overwritten
- xcopy.exe (PID: 6296)
Process copies executable file
- cmd.exe (PID: 2016)
- cmd.exe (PID: 6208)
Process drops legitimate windows executable
- xcopy.exe (PID: 6296)
Executed via WMI
- ie4uinit.exe (PID: 6516)
- ie4uinit.exe (PID: 4576)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6160)
- cmd.exe (PID: 3424)
Reads security settings of Internet Explorer
- ie4uinit.exe (PID: 1452)
- ie4uinit.exe (PID: 6516)
- ie4uinit.exe (PID: 4576)
- ie4uinit.exe (PID: 3112)
Uses RUNDLL32.EXE to load library
- ie4uinit.exe (PID: 1452)
- ie4uinit.exe (PID: 3112)
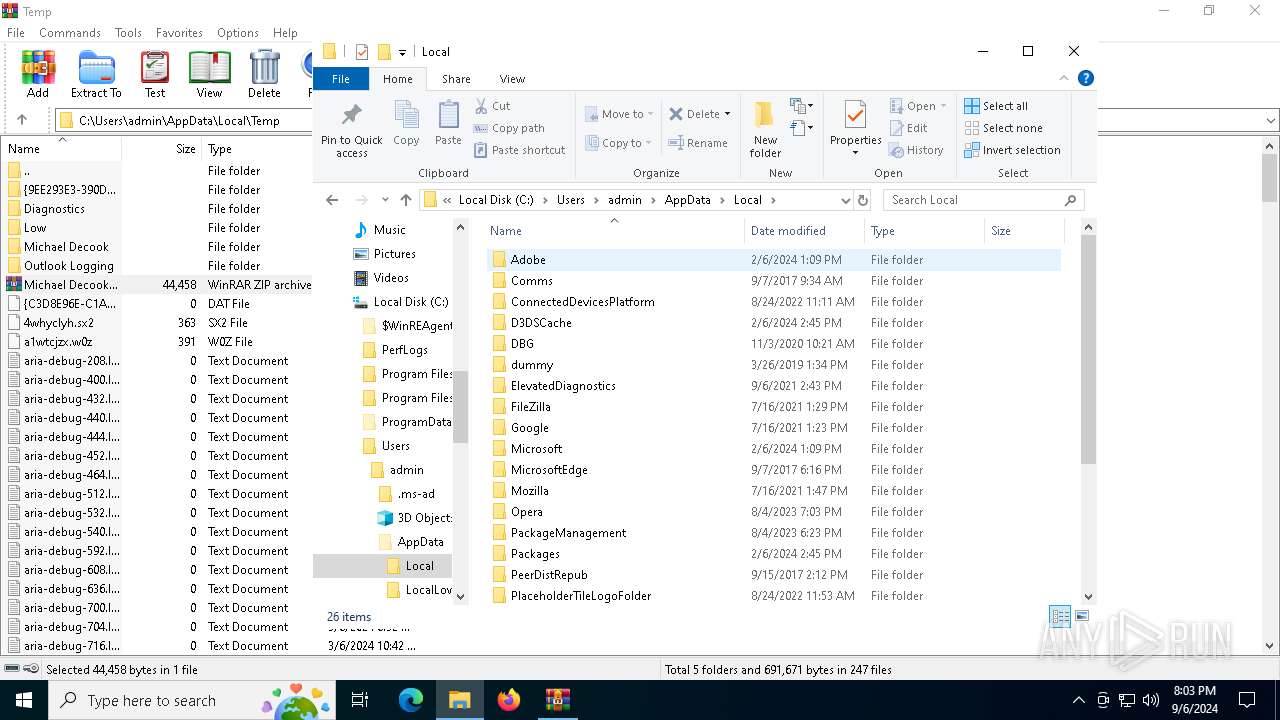
Starts a Microsoft application from unusual location
- ie4uinit.exe (PID: 6516)
- ie4uinit.exe (PID: 1452)
- ie4uinit.exe (PID: 4576)
- ie4uinit.exe (PID: 3112)
INFO
Manual execution by a user
- cmd.exe (PID: 6160)
- mspaint.exe (PID: 6488)
- cmd.exe (PID: 3424)
- msedge.exe (PID: 5284)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6724)
- WMIC.exe (PID: 2180)
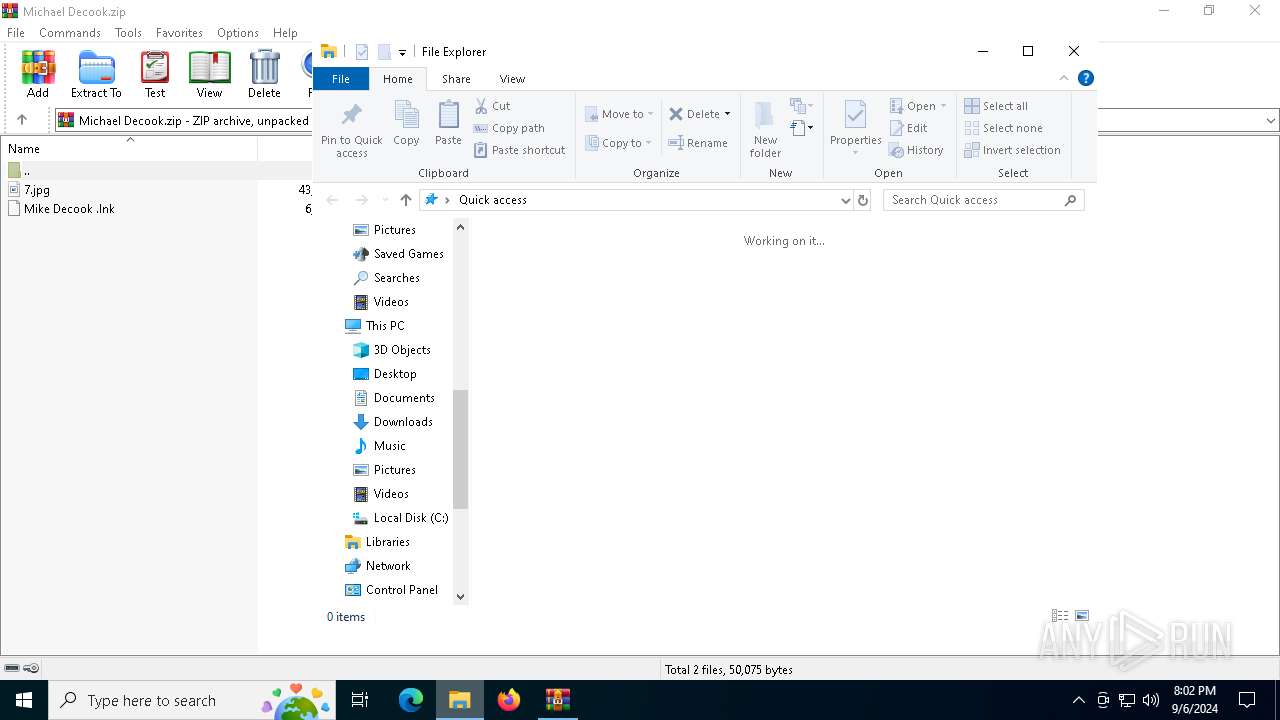
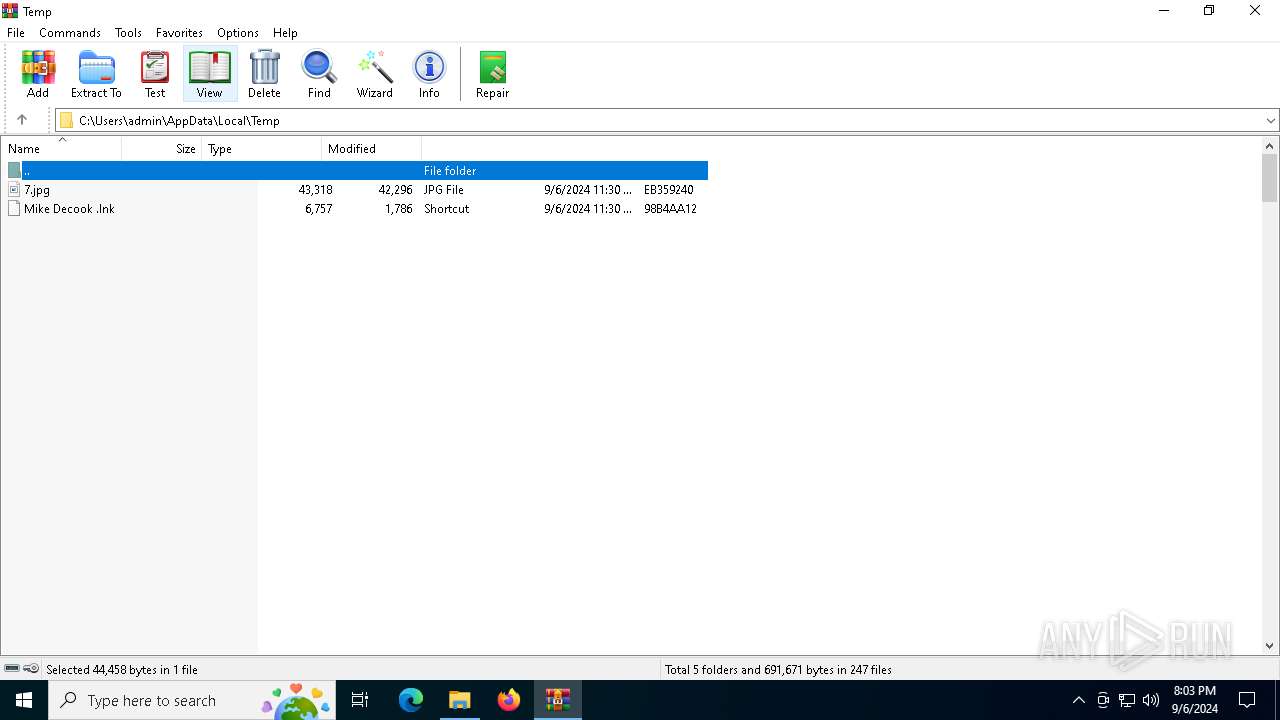
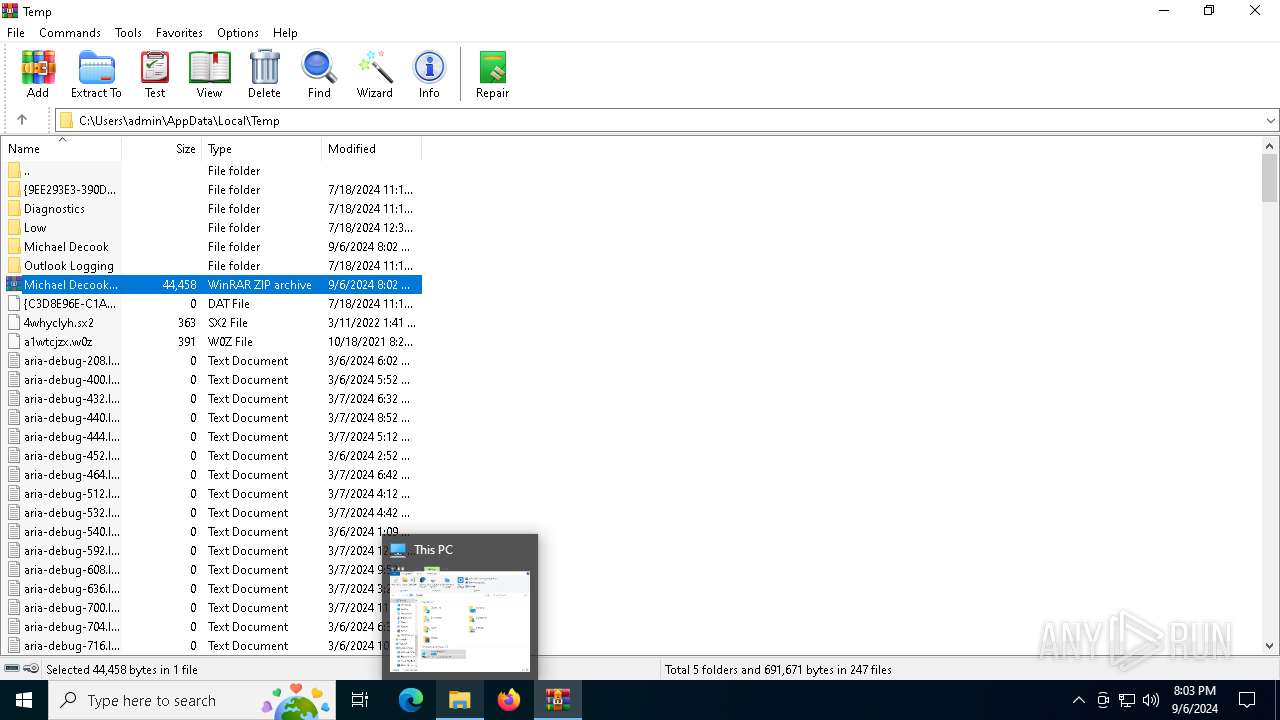
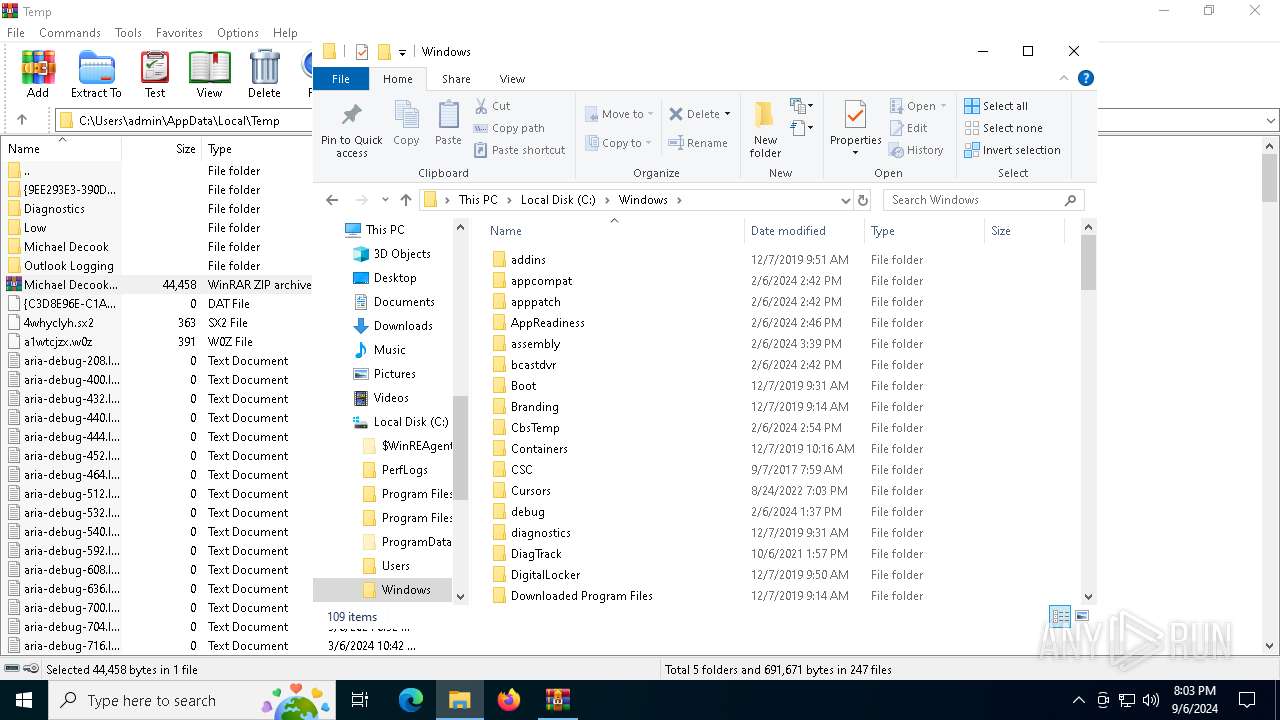
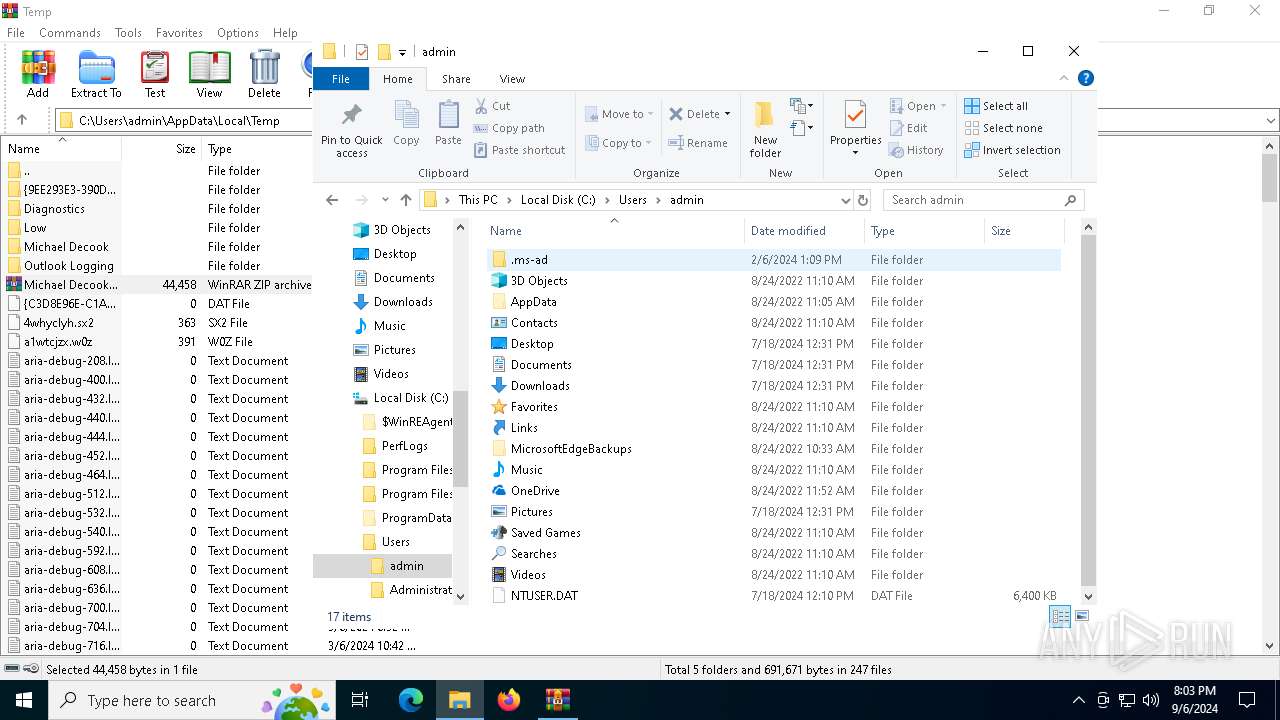
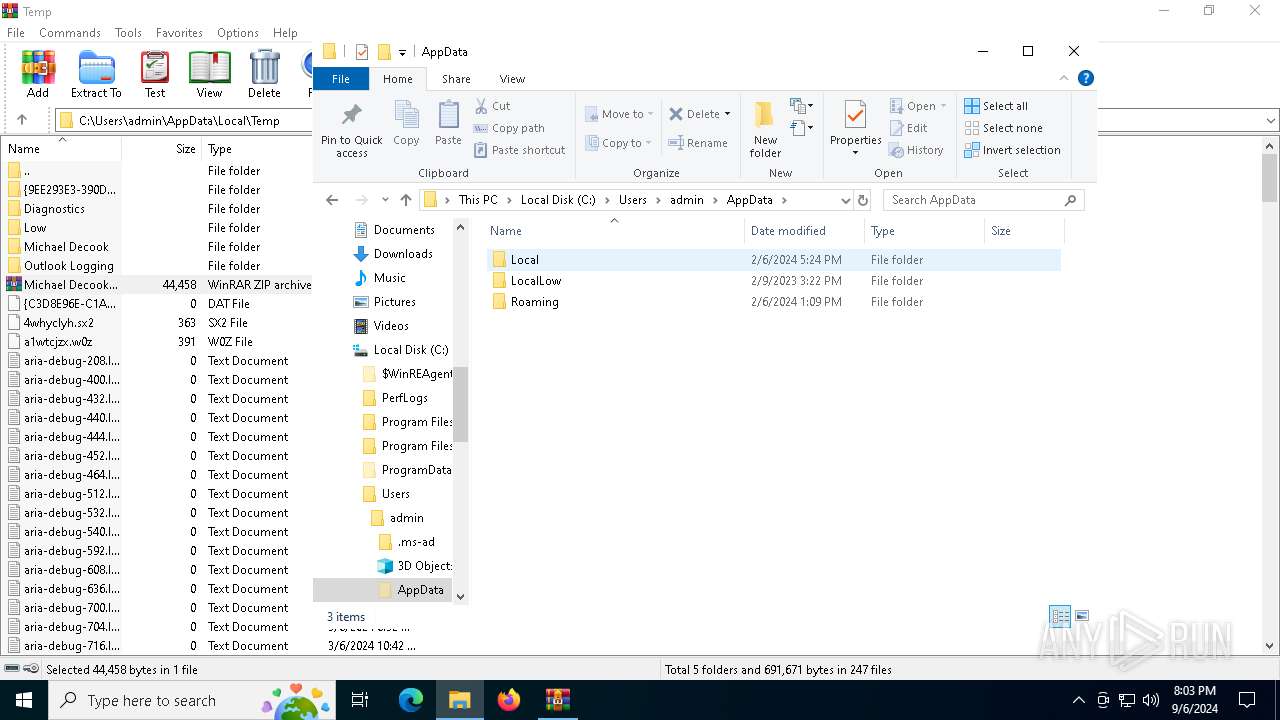
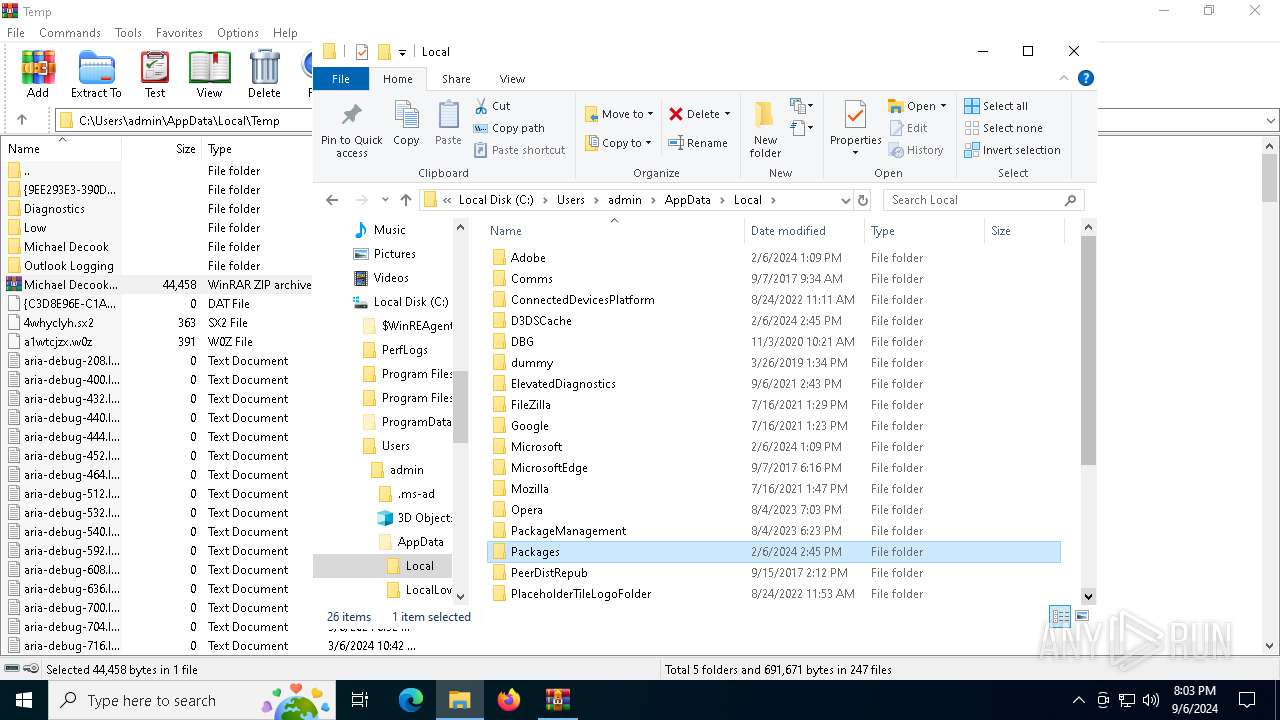
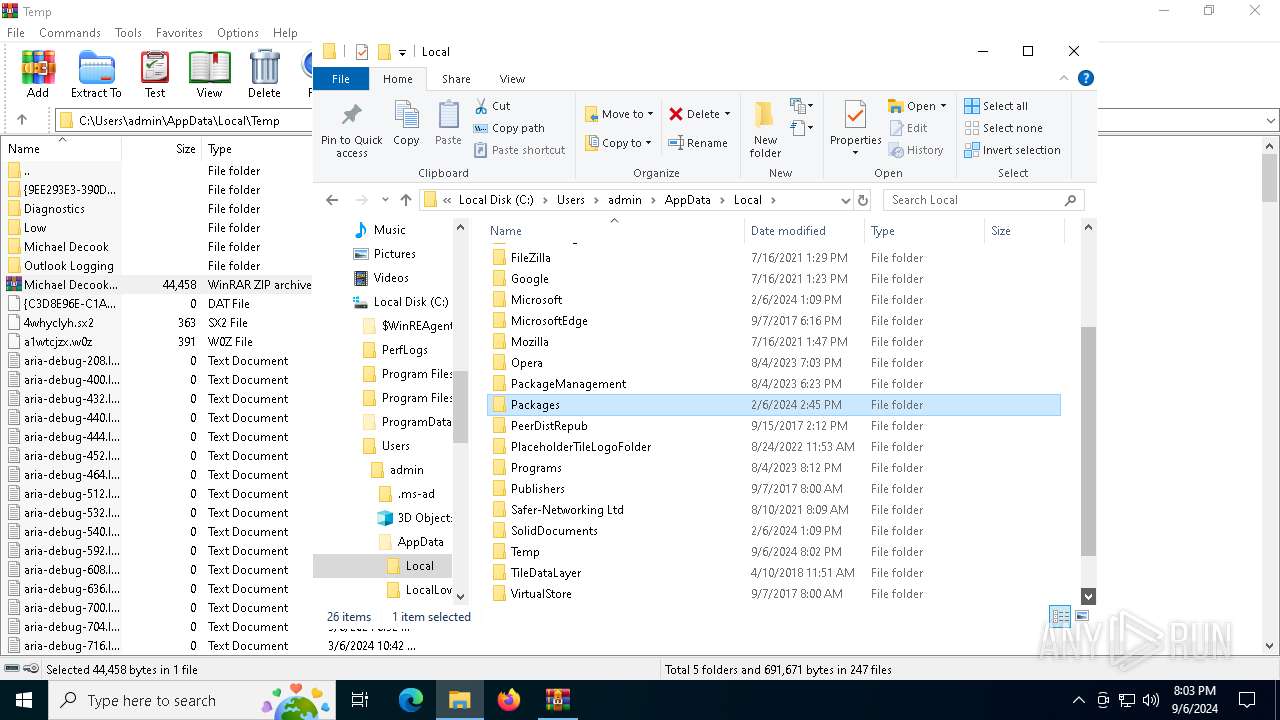
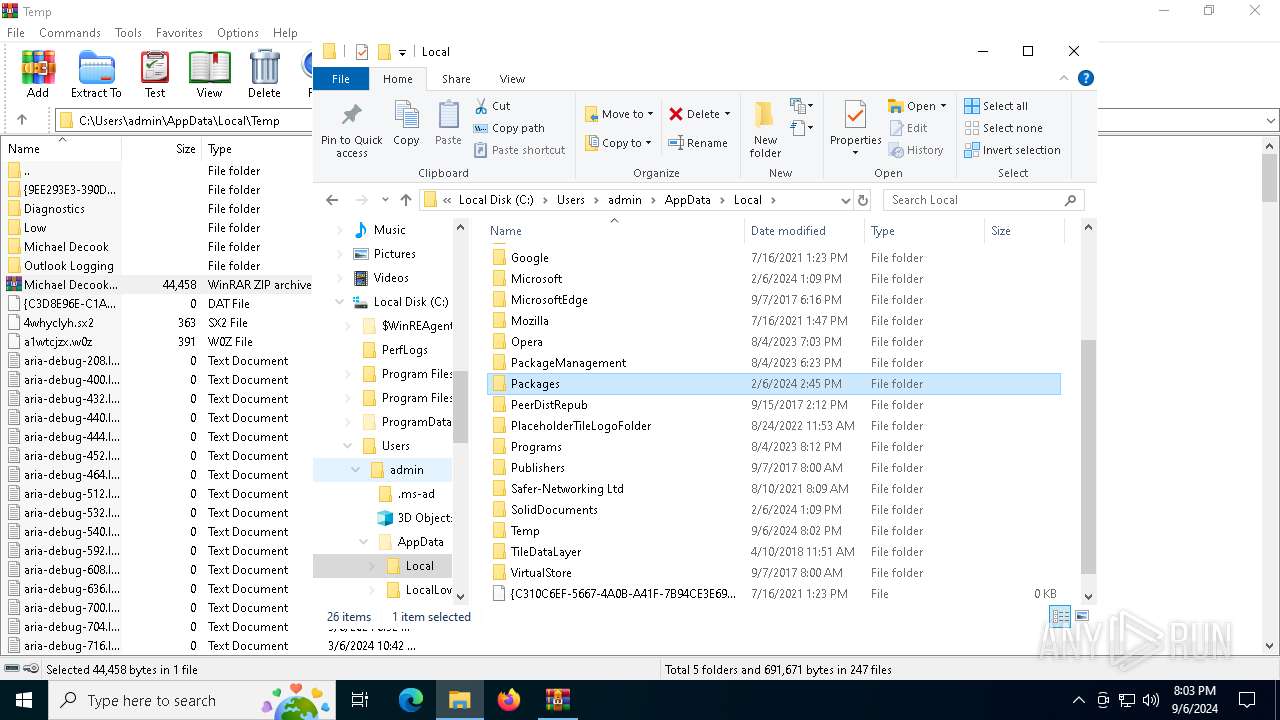
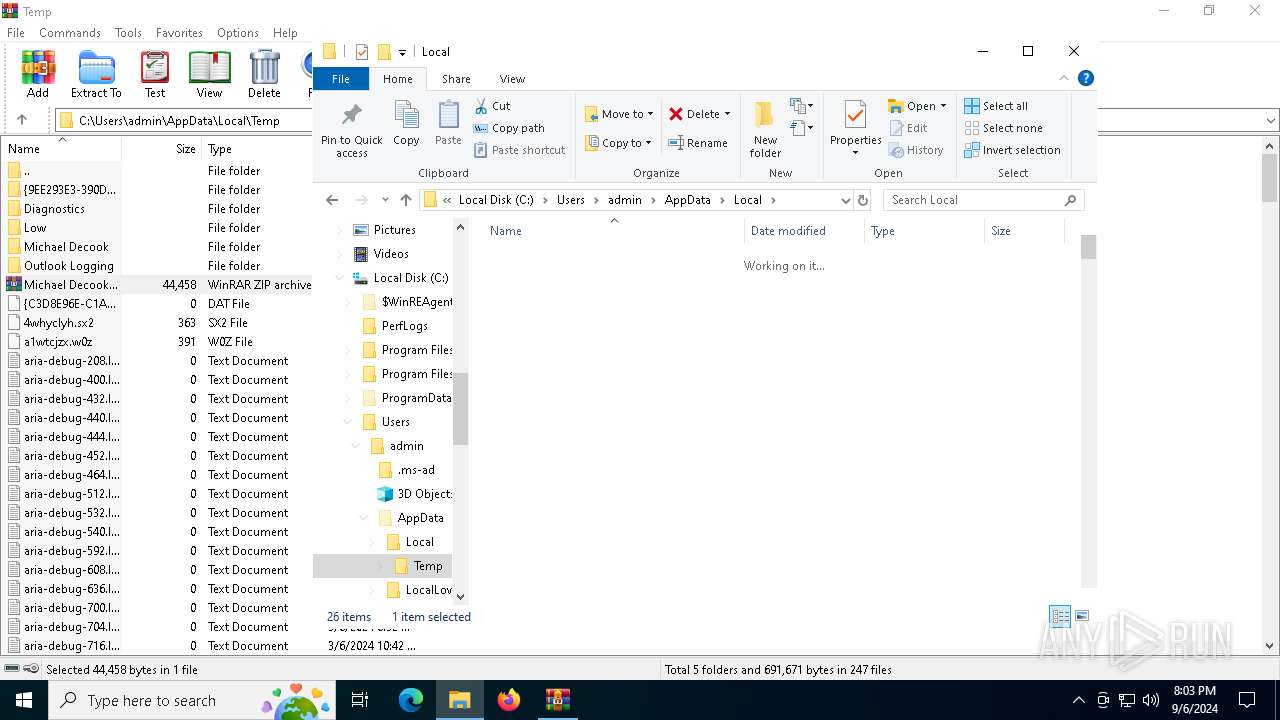
Create files in a temporary directory
- xcopy.exe (PID: 6296)
- xcopy.exe (PID: 4996)
Checks supported languages
- ie4uinit.exe (PID: 1452)
- ie4uinit.exe (PID: 6516)
- ie4uinit.exe (PID: 4576)
- ie4uinit.exe (PID: 3112)
- identity_helper.exe (PID: 7156)
Reads the computer name
- ie4uinit.exe (PID: 1452)
- ie4uinit.exe (PID: 6516)
- ie4uinit.exe (PID: 4576)
- identity_helper.exe (PID: 7156)
- ie4uinit.exe (PID: 3112)
Checks proxy server information
- ie4uinit.exe (PID: 6516)
- slui.exe (PID: 1168)
- ie4uinit.exe (PID: 4576)
Reads the software policy settings
- slui.exe (PID: 6736)
- slui.exe (PID: 1168)
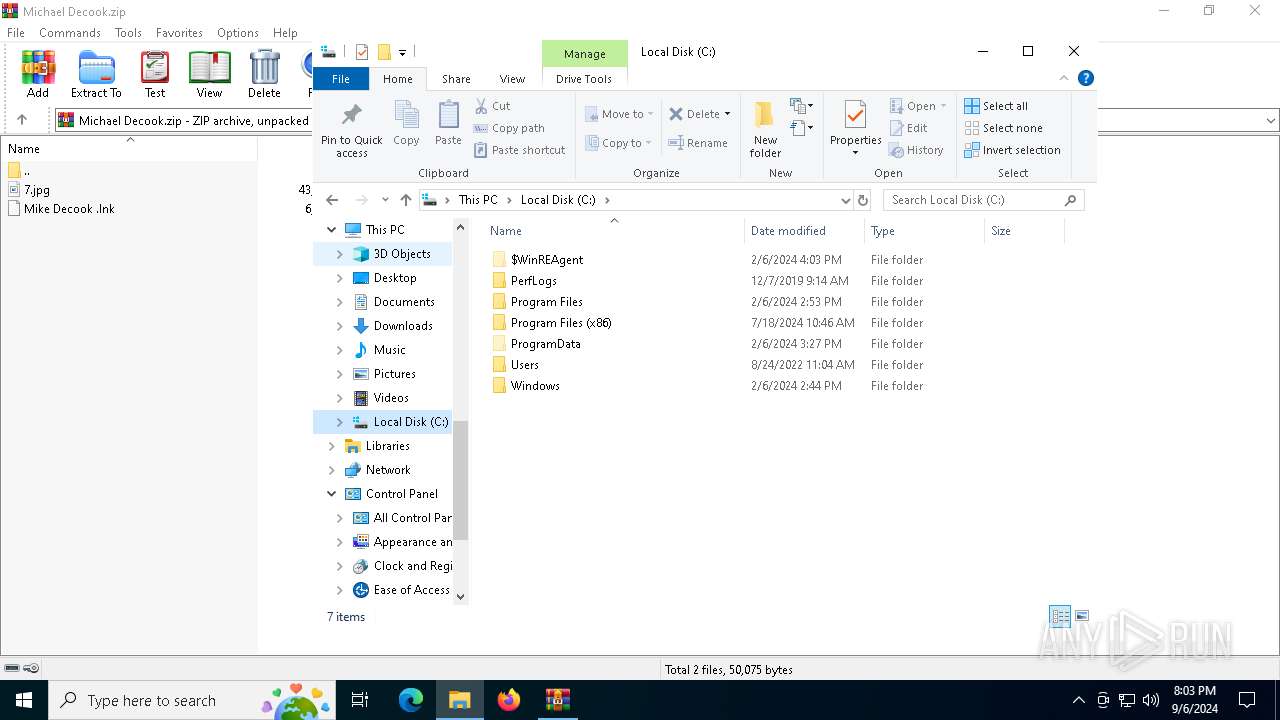
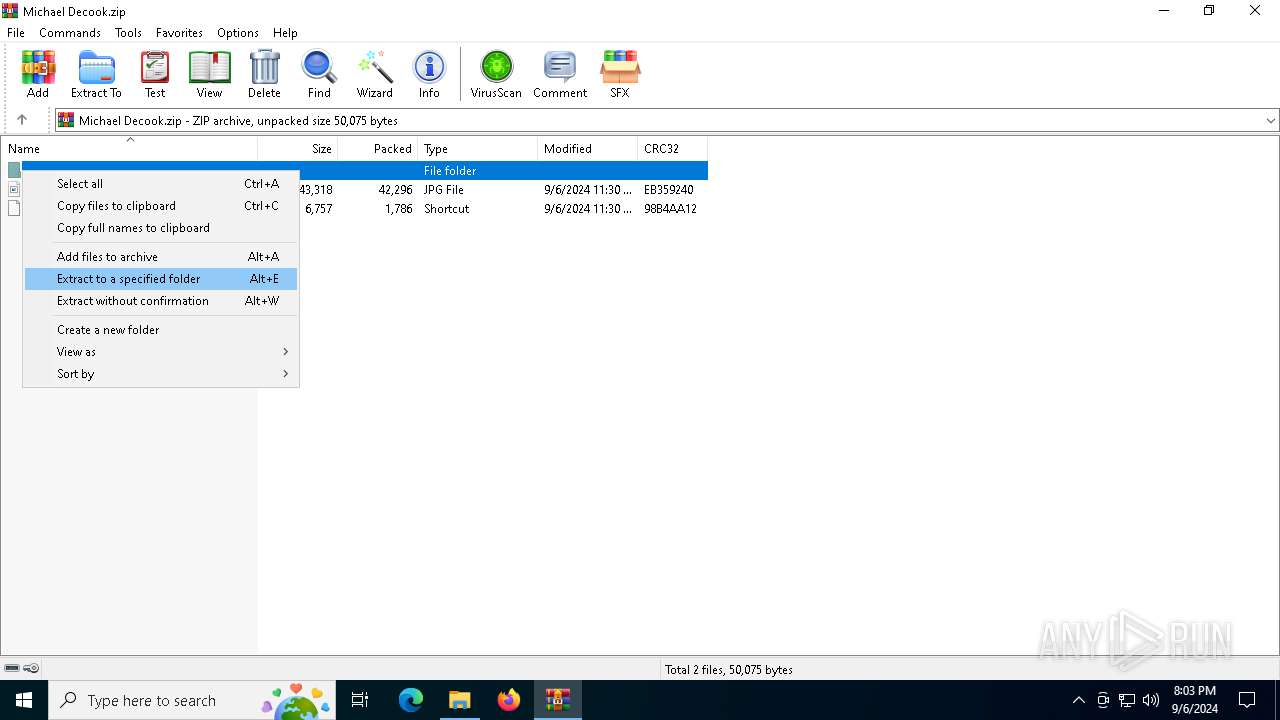
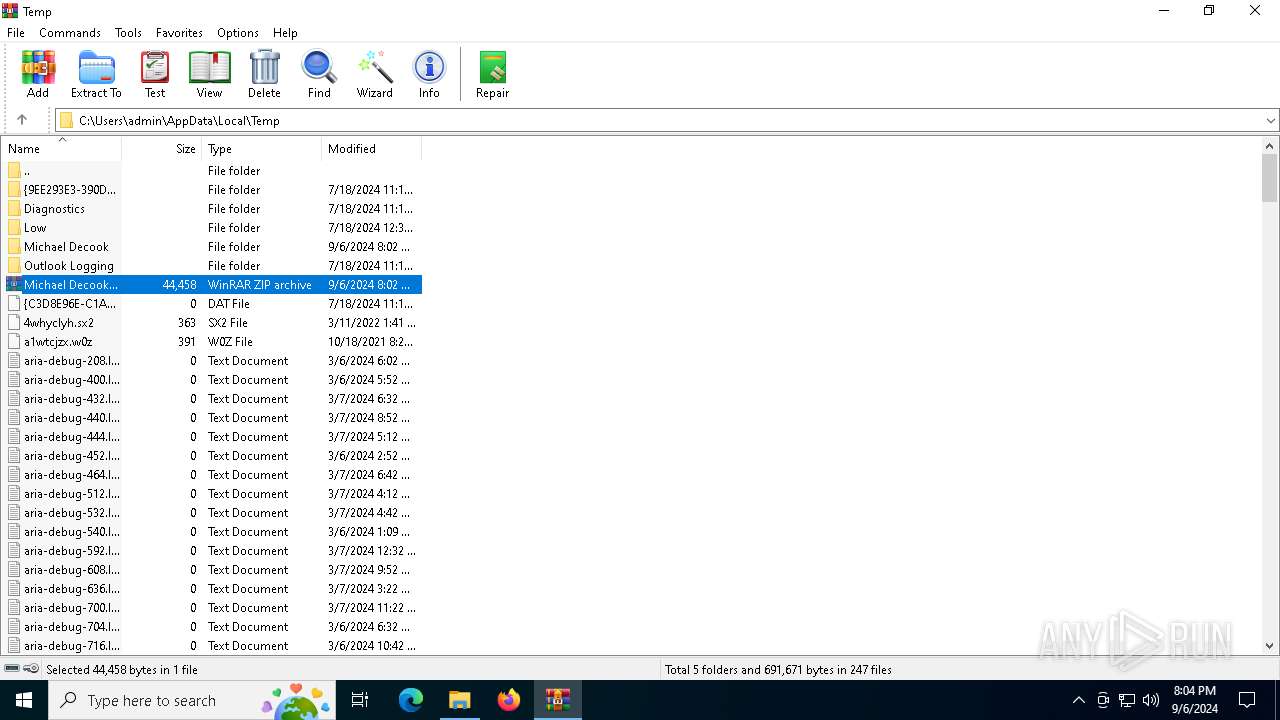
The process uses the downloaded file
- WinRAR.exe (PID: 4976)
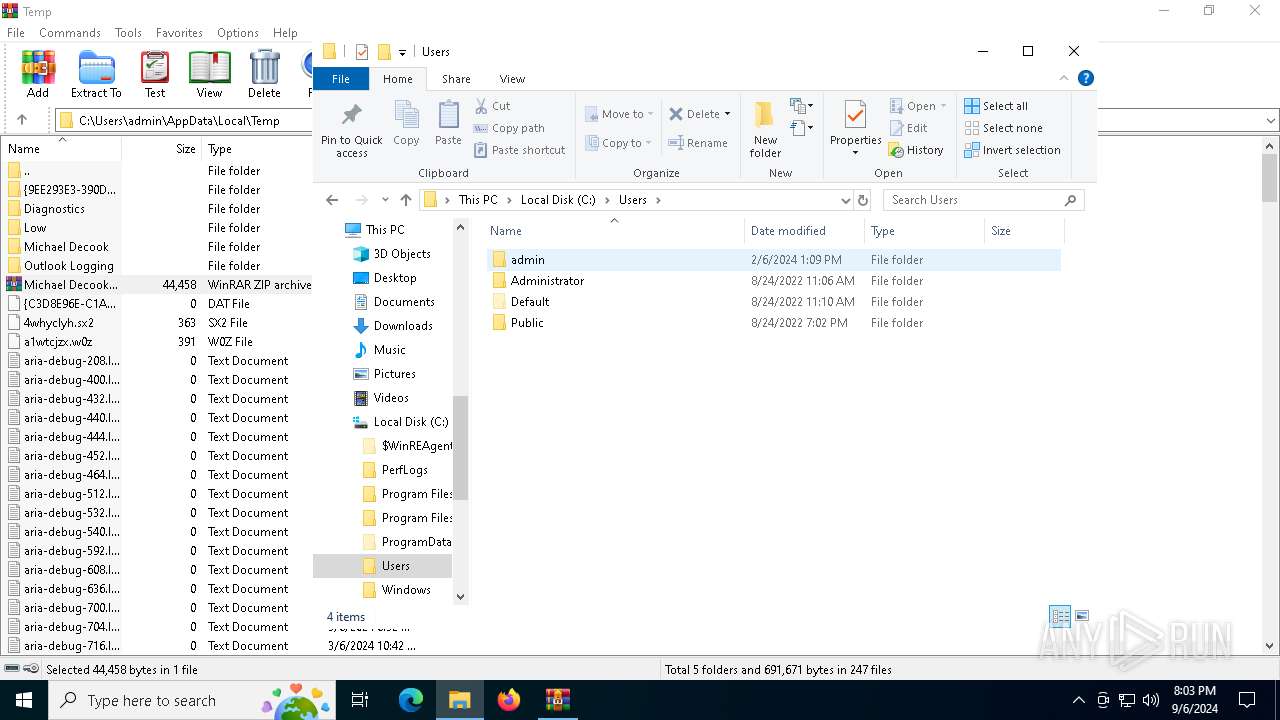
Creates files or folders in the user directory
- ie4uinit.exe (PID: 6516)
- ie4uinit.exe (PID: 4576)
Reads Environment values
- identity_helper.exe (PID: 7156)
Application launched itself
- msedge.exe (PID: 5284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:06 04:30:34 |
| ZipCRC: | 0x98b4aa12 |
| ZipCompressedSize: | 1786 |
| ZipUncompressedSize: | 6757 |
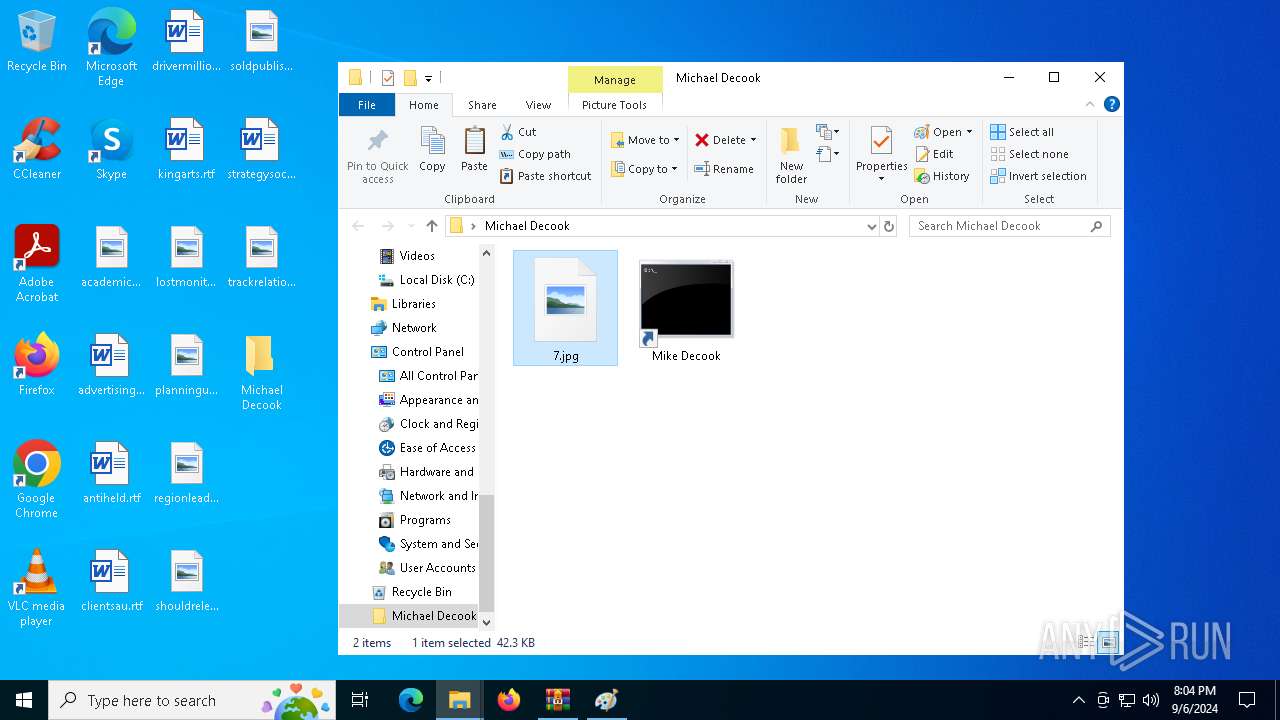
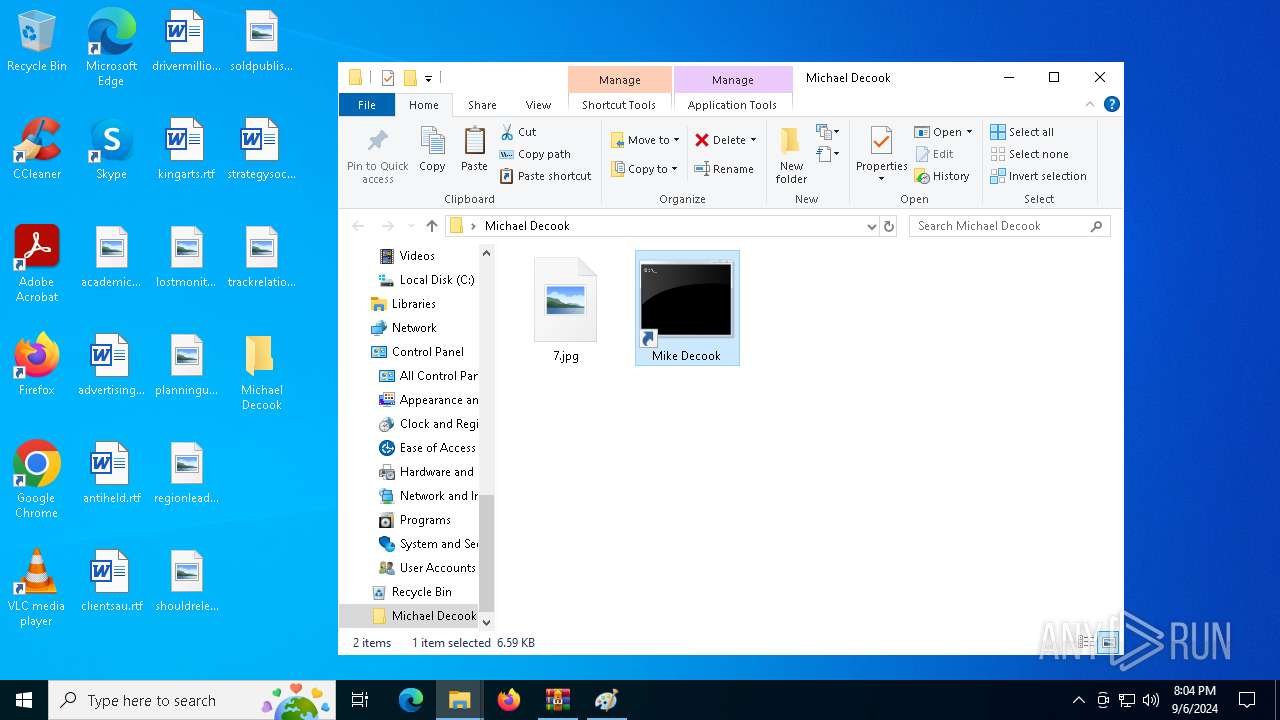
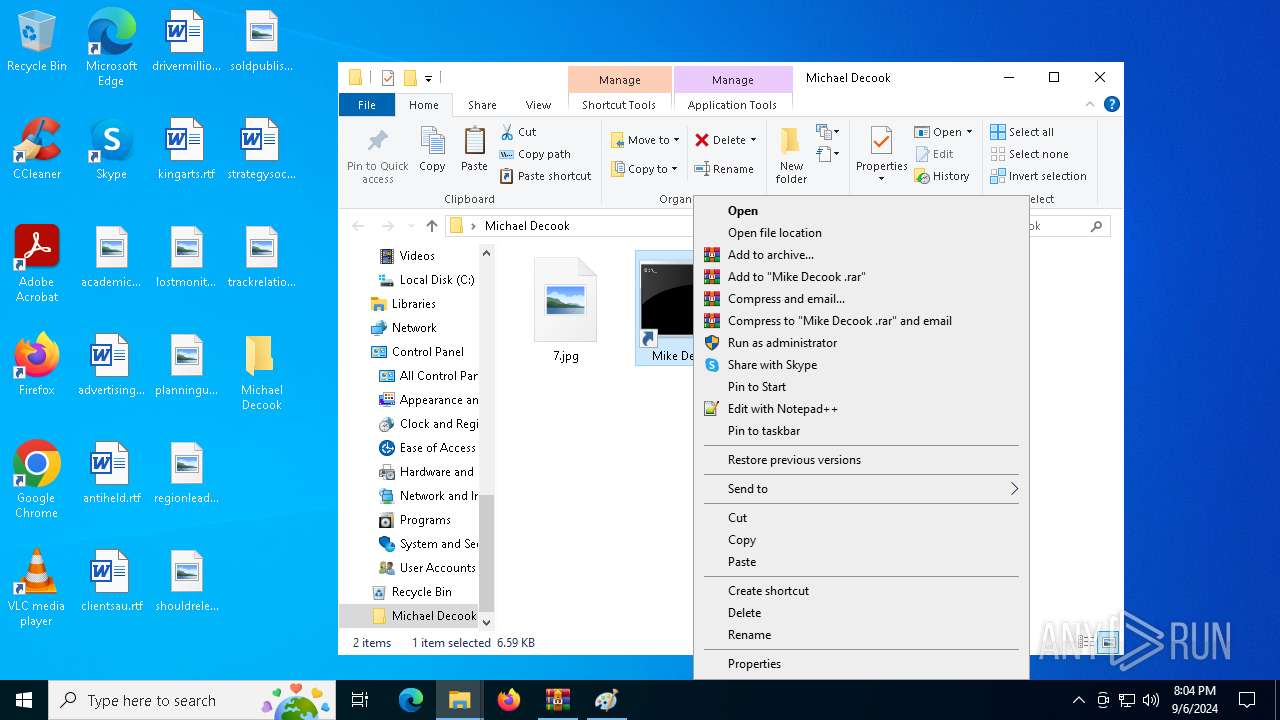
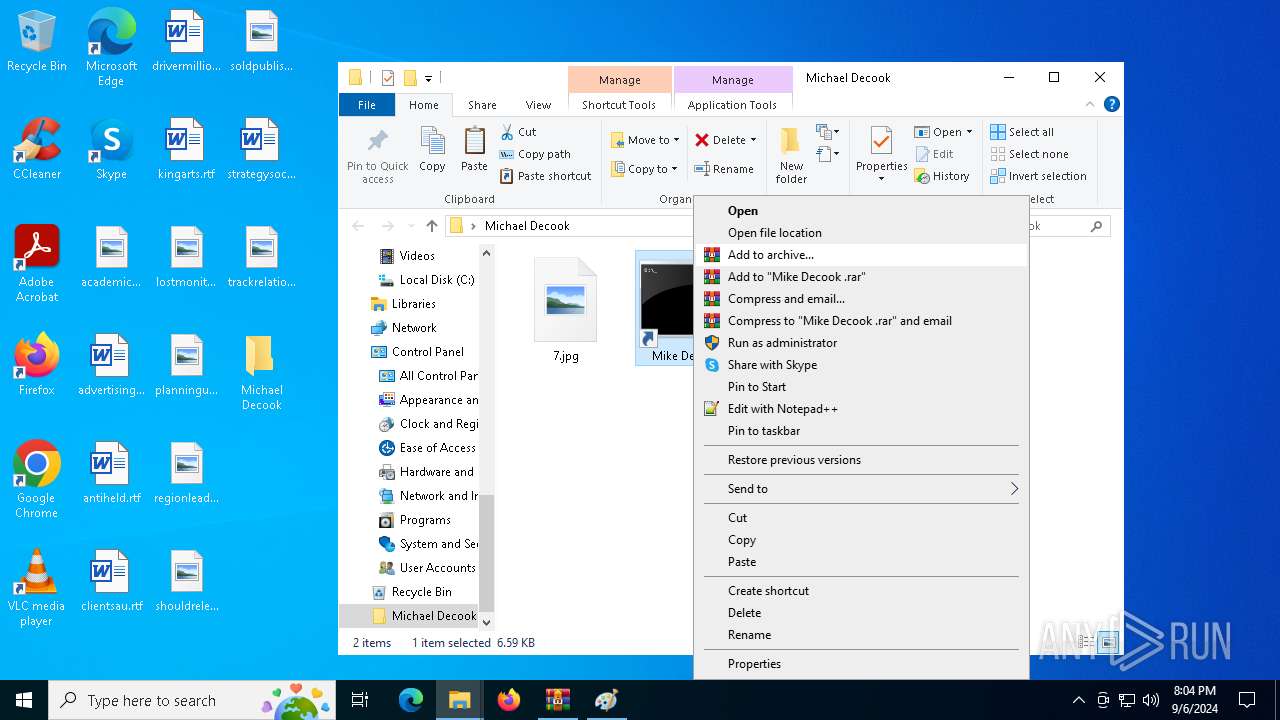
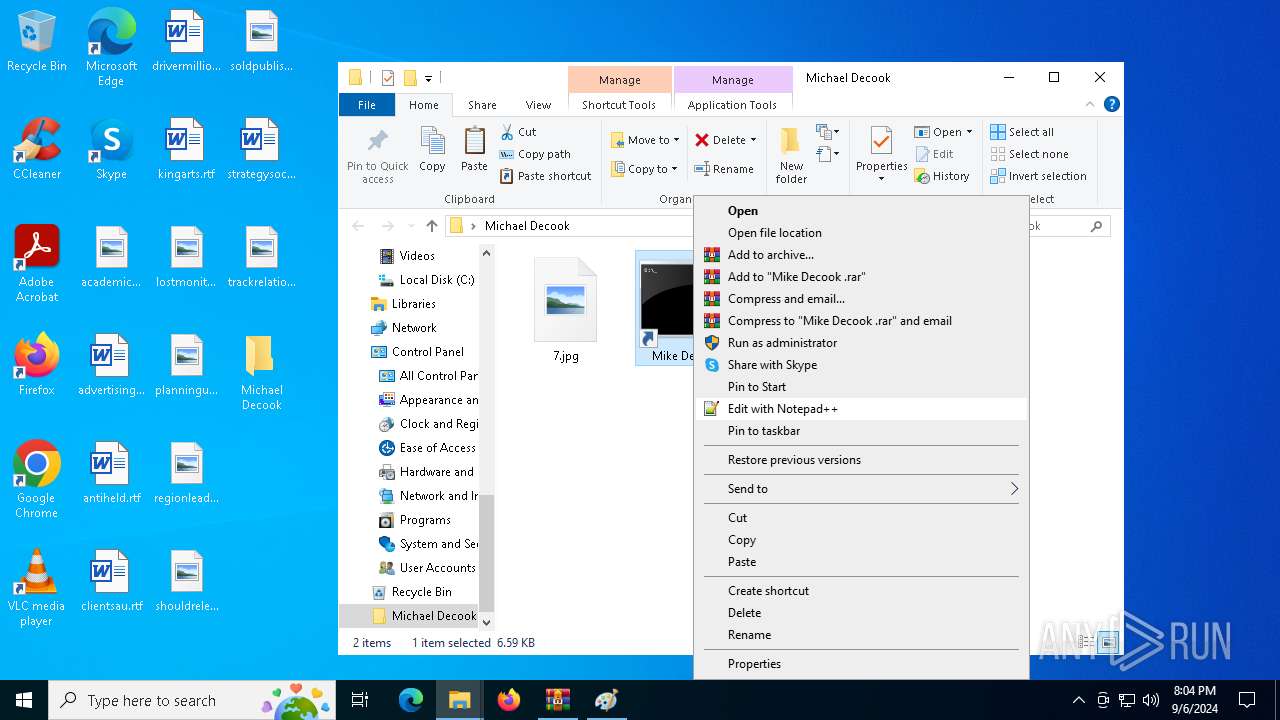
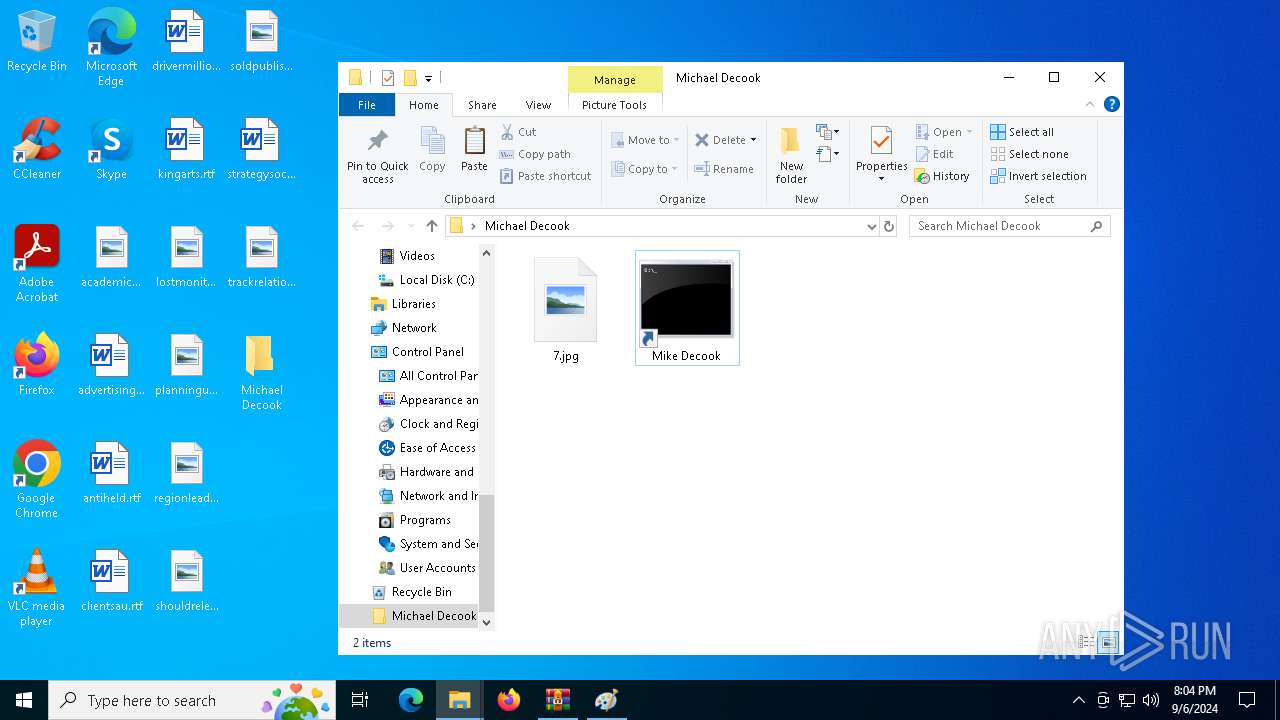
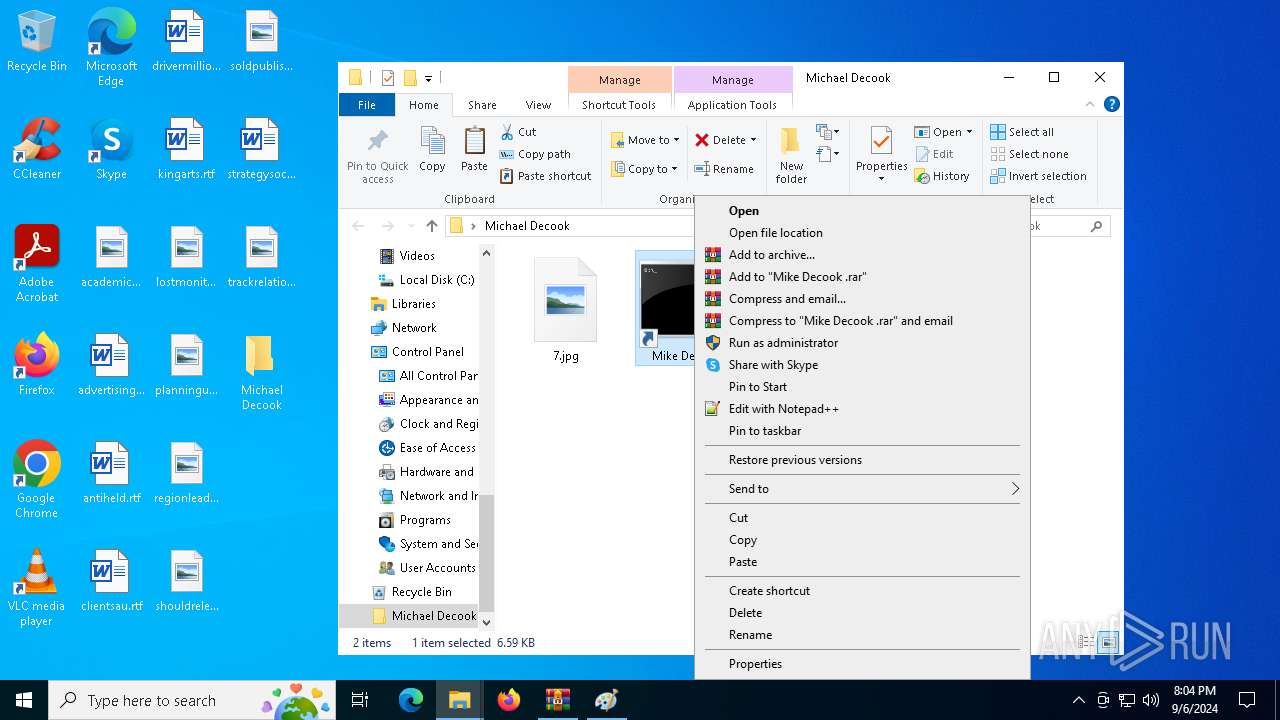
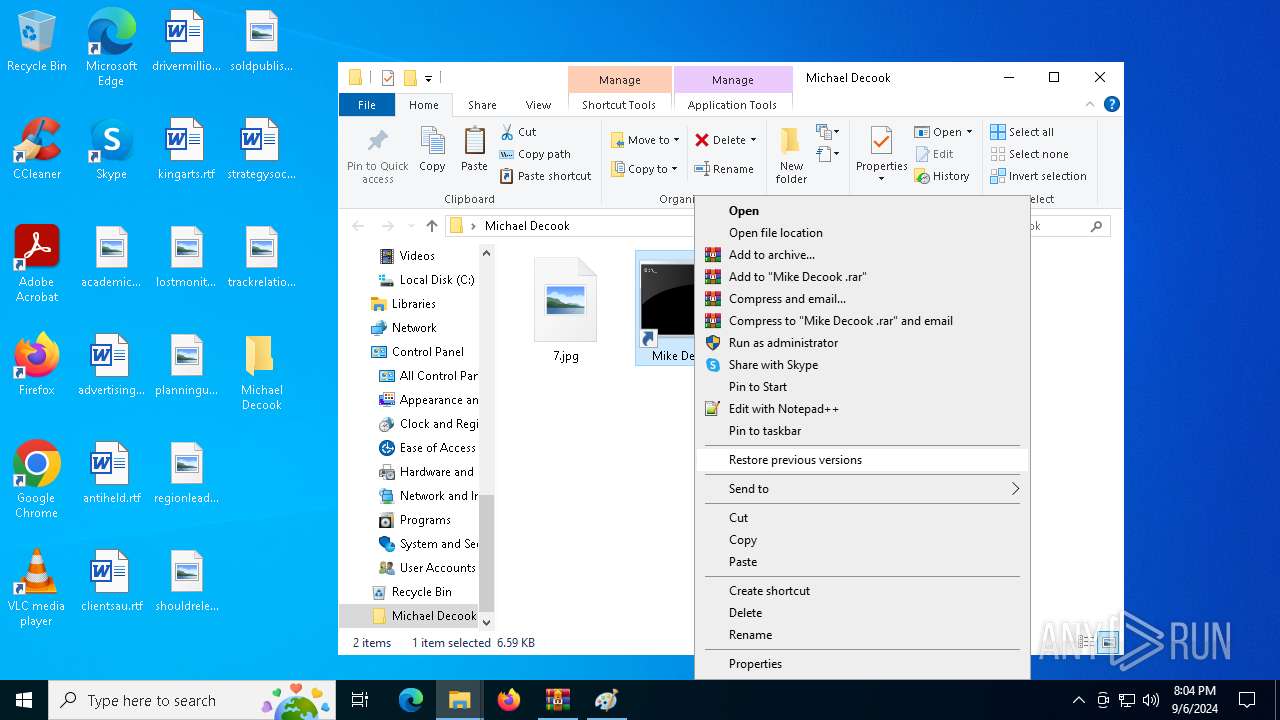
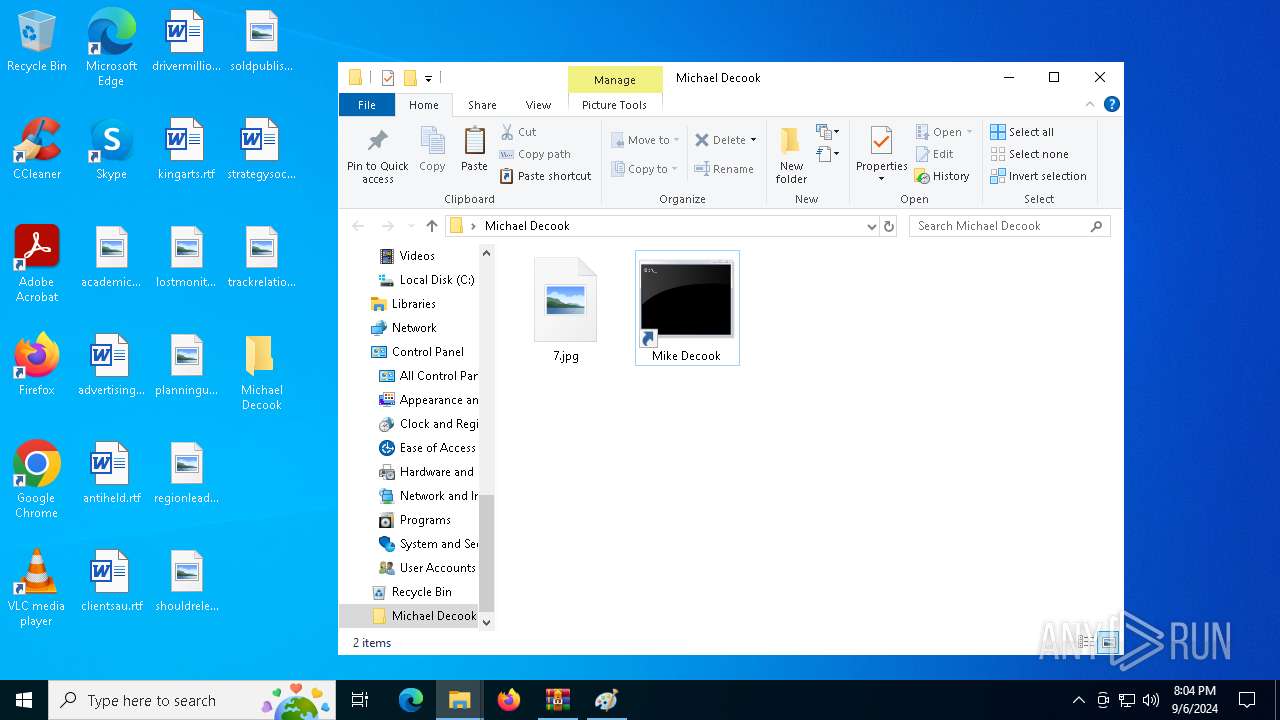
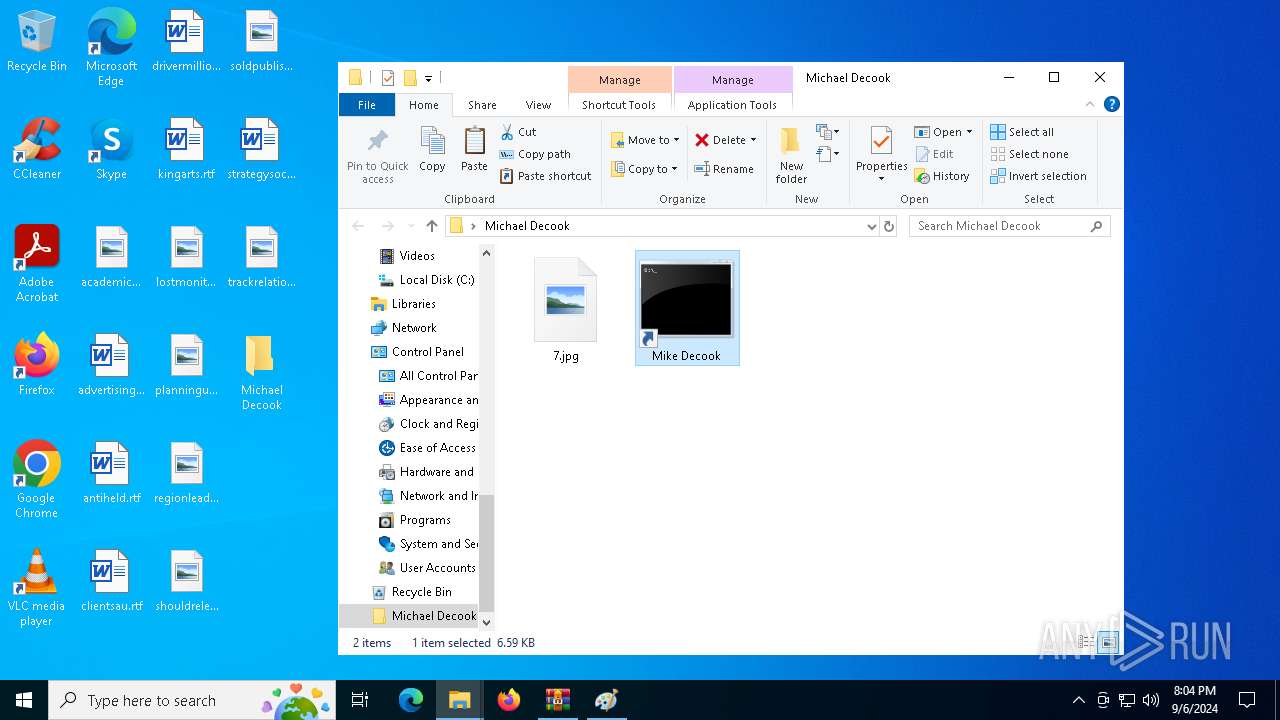
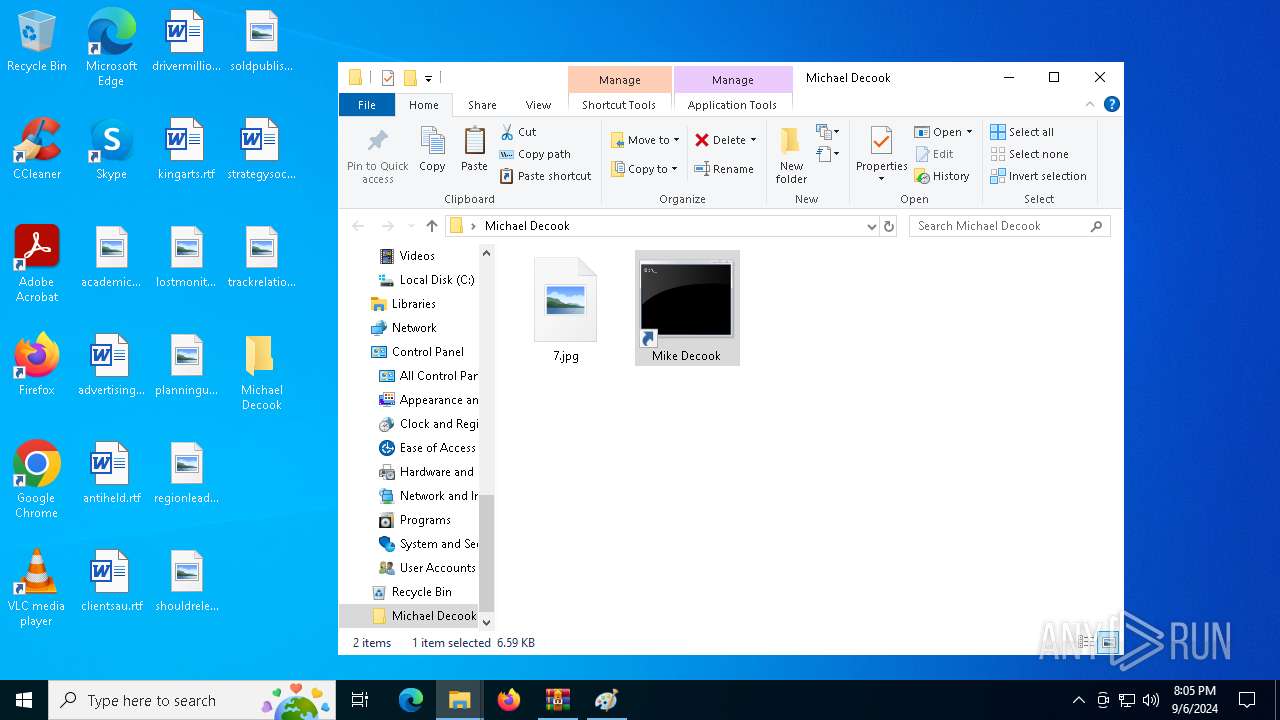
| ZipFileName: | Mike Decook .lnk |
Total processes
212
Monitored processes
73
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5144 --field-trial-handle=2280,i,9335203436359407542,15062318454663675661,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 360 | C:\WINDOWS\system32\cmd.exe /S /D /c" set "Genetics89=Coordinates Protocols Cotton Cheese Teachers Comparisons Disagree Cigar Obscure Forests Slogan Statutes Legends Utility Class Requirements Bless Symbols Purposes Honors Released Rentals Appear Invitations Blast Shoes Adjust Descriptions Manufacturers Walnut Unfold Grain Includes Florists Evaluations Wives Marble Shorts Bestsellers"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | C:\WINDOWS\system32\cmd.exe /S /D /c" start "" wmic process call create "C:\Users\admin\AppData\Local\temp\ie4uinit.exe -basesettings" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3972 --field-trial-handle=2280,i,9335203436359407542,15062318454663675661,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 936 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 940 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6936 --field-trial-handle=2280,i,9335203436359407542,15062318454663675661,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 964 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1064 | C:\WINDOWS\system32\cmd.exe /S /D /c" set "Genetics89=Coordinates Protocols Cotton Cheese Teachers Comparisons Disagree Cigar Obscure Forests Slogan Statutes Legends Utility Class Requirements Bless Symbols Purposes Honors Released Rentals Appear Invitations Blast Shoes Adjust Descriptions Manufacturers Walnut Unfold Grain Includes Florists Evaluations Wives Marble Shorts Bestsellers"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3960 --field-trial-handle=2280,i,9335203436359407542,15062318454663675661,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
17 605
Read events
17 467
Write events
138
Delete events
0
Modification events
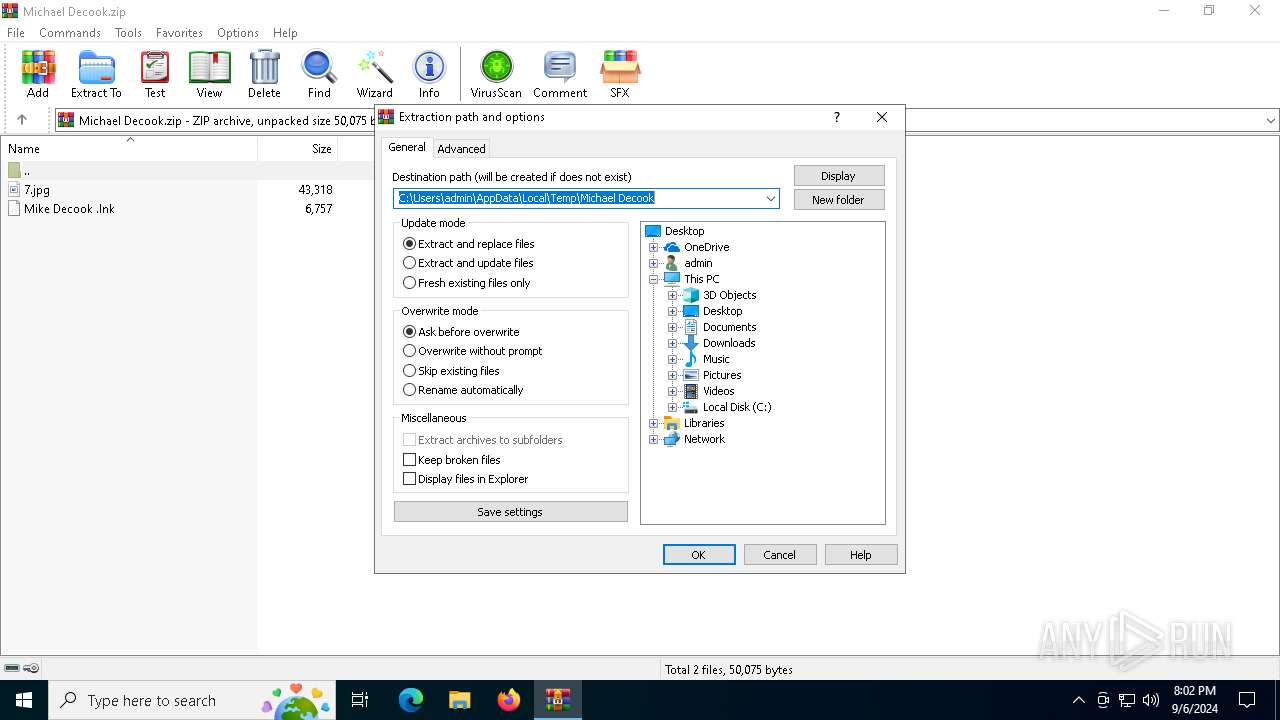
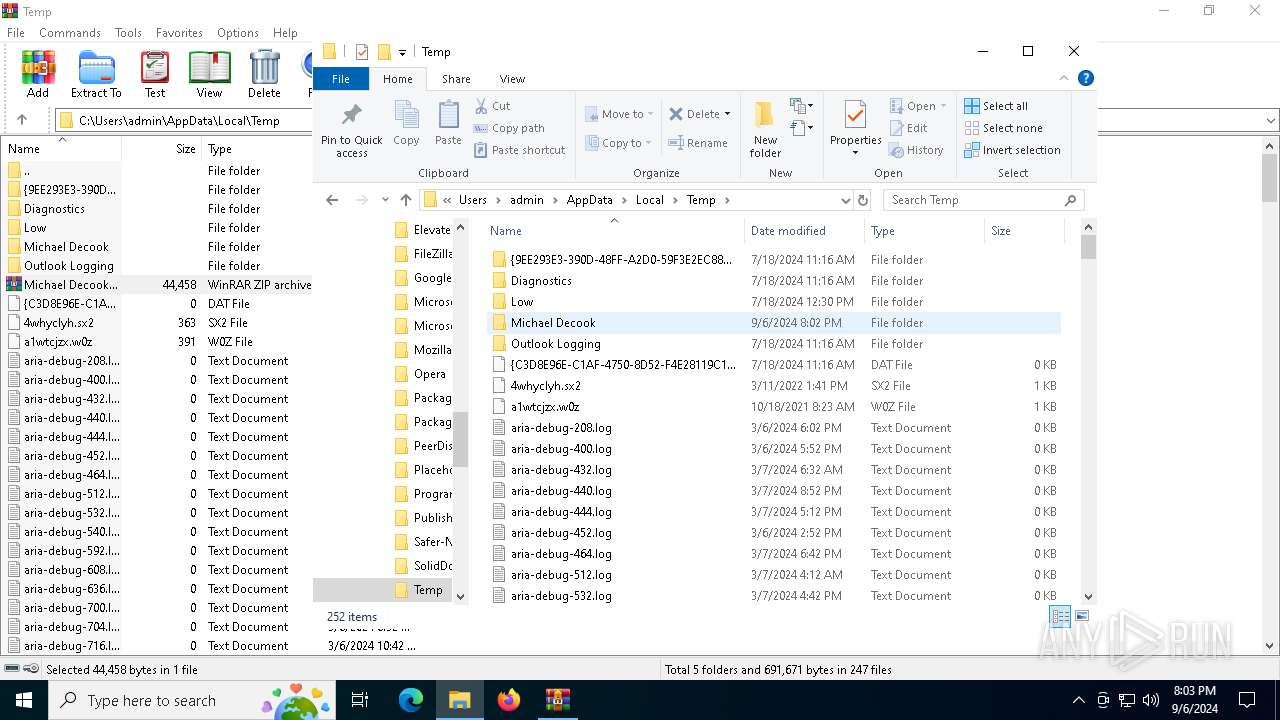
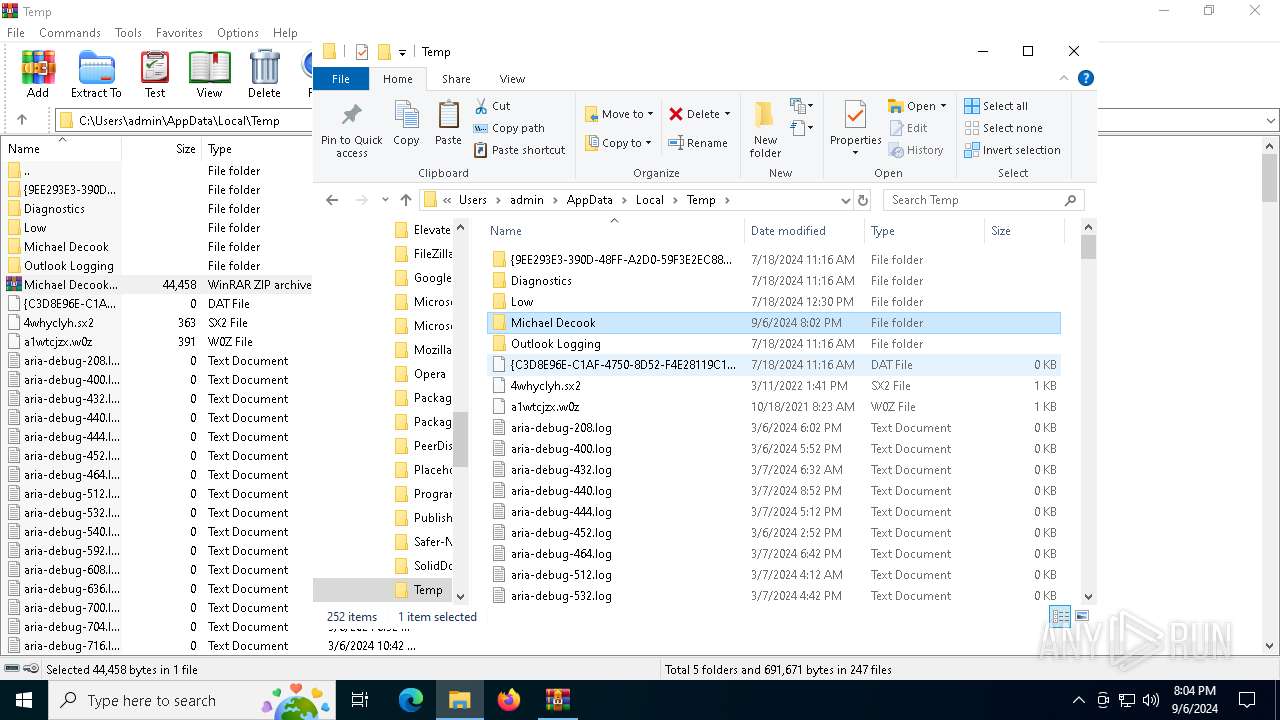
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Michael Decook.zip | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Michael Decook | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
Executable files
25
Suspicious files
650
Text files
142
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6160 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ieuinit.inf | ini | |
MD5:8C9EFF53FF8D2182D37C51F1E7C2EAD1 | SHA256:FC3E021BFE49AD9F1E087C4BD9AB77E6064C60A7F78965EC94AFEC0E7FF99361 | |||
| 5284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF158ae4.TMP | — | |
MD5:— | SHA256:— | |||
| 4976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Michael Decook\Mike Decook .lnk | lnk | |
MD5:E3B5BEE5E5A7F1B6A99D62E7792DC27F | SHA256:599B23987DC0E50E8EDFCC2920260740DB2E4B61750CFFFD1D6427641A65F91C | |||
| 5284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF158ae4.TMP | — | |
MD5:— | SHA256:— | |||
| 5284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF158ae4.TMP | — | |
MD5:— | SHA256:— | |||
| 5284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF158ae4.TMP | — | |
MD5:— | SHA256:— | |||
| 5284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
113
DNS requests
129
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3140 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6052 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6908 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
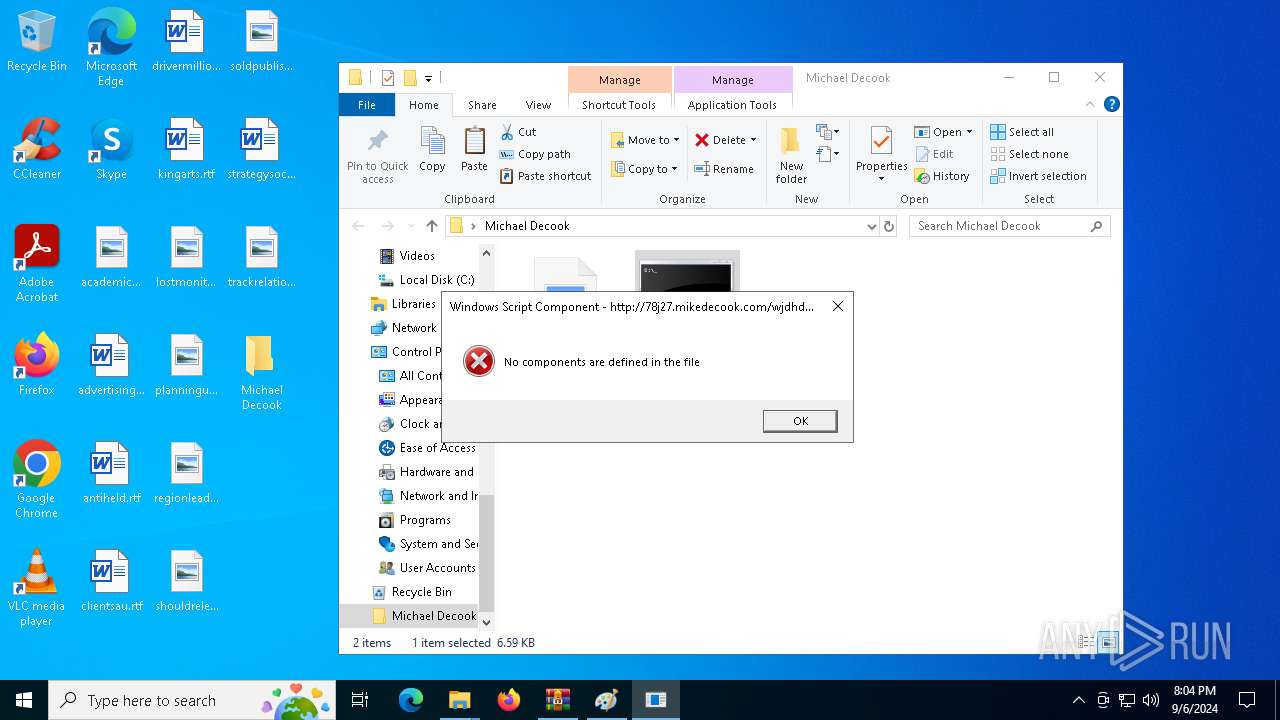
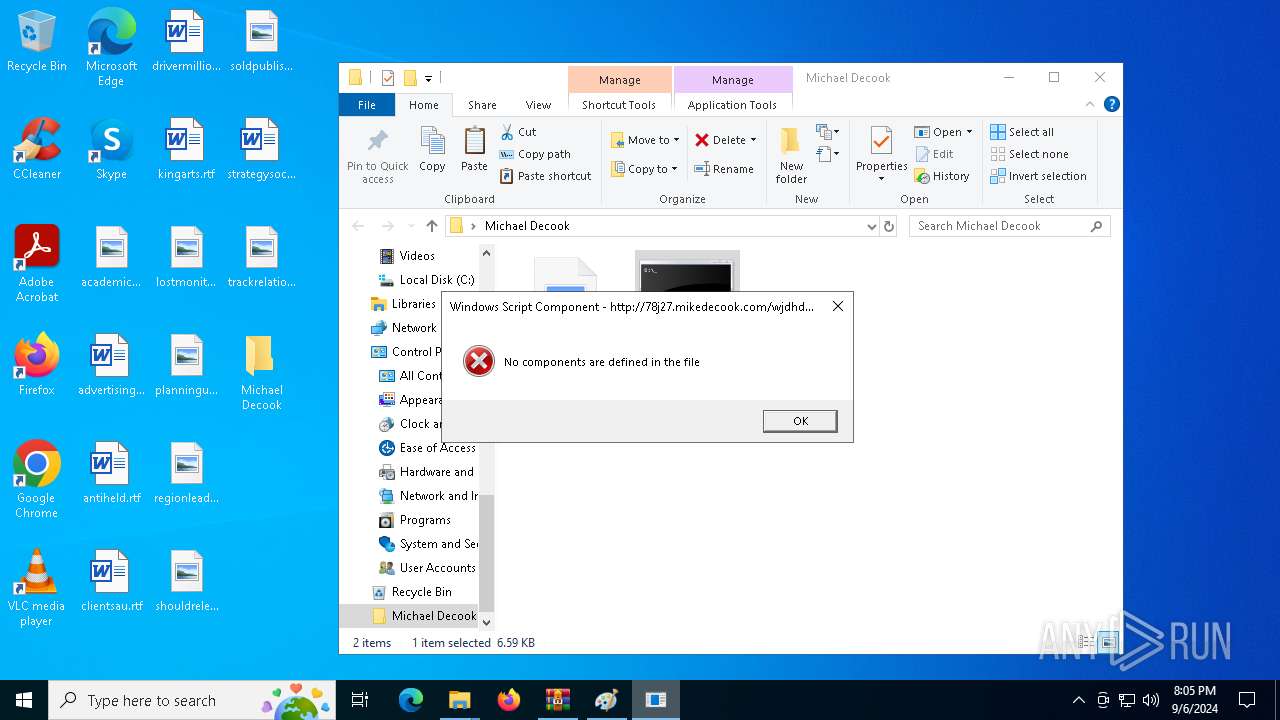
6516 | ie4uinit.exe | GET | 200 | 51.20.35.243:80 | http://78j27.mikedecook.com/wjdhdbia | unknown | — | — | unknown |
3140 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4576 | ie4uinit.exe | GET | 200 | 51.20.35.243:80 | http://78j27.mikedecook.com/wjdhdbia | unknown | — | — | unknown |
6988 | msedge.exe | GET | 304 | 184.24.77.69:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | unknown | — | — | whitelisted |
6988 | msedge.exe | GET | 304 | 69.192.161.44:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
6988 | msedge.exe | GET | 304 | 69.192.161.44:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
6988 | msedge.exe | GET | 200 | 51.20.35.243:80 | http://78j27.mikedecook.com/wjdhdbia | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6428 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6052 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6052 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6052 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6908 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
78j27.mikedecook.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6988 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
6988 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
6988 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6988 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |