| File name: | 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897 |
| Full analysis: | https://app.any.run/tasks/abf50c2c-44c9-405e-a015-920b8cb33055 |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2024, 19:51:54 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 9 sections |
| MD5: | 4731AFCED628BE06B59B1DB8C919129E |
| SHA1: | DD4E6A90C25C5DF5BEF864A0C00AE7DC609E91F8 |
| SHA256: | 11BD90FBDA02E466CD3615D5930FA5EAFF12EB7306155F5A60FFEAB6F6B5B897 |
| SSDEEP: | 6144:oQunJsKxb4/NFTI9ACa7k/GGjoRsBLp4WP7GOAtBW8:oQEjxb4nI9fa7k/Xjf3P7ELW8 |
MALICIOUS
Executing a file with an untrusted certificate
- 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe (PID: 1492)
Changes the login/logoff helper path in the registry
- 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe (PID: 1492)
SUSPICIOUS
Reads the date of Windows installation
- 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe (PID: 1492)
The process checks if it is being run in the virtual environment
- 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe (PID: 1492)
Reads the Internet Settings
- 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe (PID: 1492)
Reads security settings of Internet Explorer
- 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe (PID: 1492)
There is functionality for taking screenshot (YARA)
- 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe (PID: 1492)
INFO
Reads the computer name
- 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe (PID: 1492)
Checks supported languages
- 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe (PID: 1492)
Checks proxy server information
- 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe (PID: 1492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1998:02:03 07:29:08+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5.11 |
| CodeSize: | 10240 |
| InitializedDataSize: | 223232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x154c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.0.2 |
| ProductVersionNumber: | 5.0.7.9 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileVersion: | 3.0.0.2 |
| ProductVersion: | 5.0.7.9 |
| FileDescription: | Unbasedness |
| CompanyName: | FRISK Software International |
| LegalCopyright: | textilist |
| ProductName: | dropflower |
Total processes
113
Monitored processes
1
Malicious processes
1
Suspicious processes
0
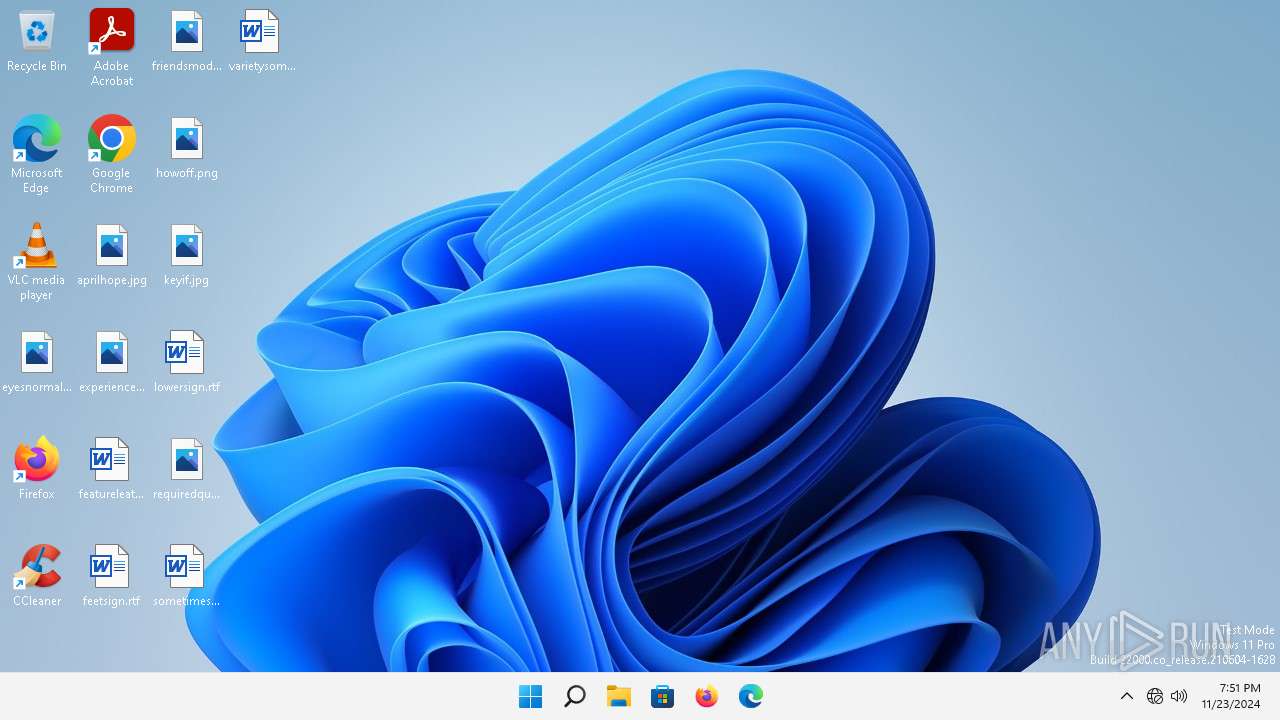
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1492 | "C:\Users\admin\Desktop\11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe" | C:\Users\admin\Desktop\11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | explorer.exe | ||||||||||||
User: admin Company: FRISK Software International Integrity Level: MEDIUM Description: Unbasedness Version: 3.0.0.2 Modules
| |||||||||||||||
Total events
3 805
Read events
3 791
Write events
14
Delete events
0
Modification events
| (PID) Process: | (1492) 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | dc123c8a |
Value: C:\Users\admin\Desktop\11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | |||
| (PID) Process: | (1492) 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | userinit |
Value: C:\Windows\system32\userinit.exe,, | |||
| (PID) Process: | (1492) 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1492) 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1492) 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1492) 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1492) 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1492) 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1492) 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1492) 11bd90fbda02e466cd3615d5930fa5eaff12eb7306155f5a60ffeab6f6b5b897.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft |
| Operation: | write | Name: | dc123c1ca |
Value: 2225875 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
31
DNS requests
35
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4928 | MoUsoCoreWorker.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?74b7d417c4f58613 | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.110.147:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
6368 | firefox.exe | POST | 200 | 2.16.241.15:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6368 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
6368 | firefox.exe | POST | 200 | 2.16.241.8:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2860 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2356e5d8e5bd8b39 | unknown | — | — | whitelisted |
2860 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?8a3f5205275d40c7 | unknown | — | — | whitelisted |
2860 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?c8be12605aaef0f9 | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.107.6.156:443 | https://mrodevicemgr.officeapps.live.com/mrodevicemgrsvc/api/v1/C2RTargetAudienceData?omid=97560490bafb0d49bca6f8f0df91025d&susid=c408ee57-2103-4c34-9e6f-30bdf6c87e50&audienceFFN=492350f6-3a01-4f97-b9c0-c7c6ddf67d60&tid=&osver=Client%7C10.0.22000&offver=16.0.16626.20134&ring=Production&aud=Production&ch=CC&osarch=x64&manstate=6 | unknown | binary | 192 b | whitelisted |
— | — | GET | 200 | 52.113.194.132:443 | https://ecs.office.com/config/v2/Office/officeclicktorun/16.0.16626.20134/Production/CC?&Clientid=%7b80C2A92B-EDEE-479E-8470-DBC6C547F2FB%7d&Application=officeclicktorun&Platform=win32&Version=16.0.16626.20134&MsoVersion=16.0.16626.20134&ProcessName=officec2rclient.exe&Audience=Production&Build=ship&Architecture=x64&OsVersion=10.0&OsBuild=22000&Channel=CC&InstallType=C2R&SessionId=%7b04957DD9-1F5B-4D39-A13E-370CAD776C83%7d&LabMachine=false | unknown | tss | 79.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6368 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
6368 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
3420 | rundll32.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1996 | OfficeC2RClient.exe | 52.109.28.46:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
5052 | OfficeC2RClient.exe | 52.109.28.46:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 88.221.110.147:80 | — | Akamai International B.V. | DE | unknown |
4928 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4928 | MoUsoCoreWorker.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
firefox.settings.services.mozilla.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
www.bing.com |
| whitelisted |
nonasthmatic.com |
| unknown |
ecs.office.com |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |