| File name: | r00tkitty_dump1.bin |
| Full analysis: | https://app.any.run/tasks/e6018c83-947a-4c65-98d1-f6342b0e5fb7 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 16:09:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 35C8B2E08976769B7240883038B76F35 |
| SHA1: | D0AF68A65E713B96F294E25BED260F306CF0B8DD |
| SHA256: | 11A29B98C9918365AFE35666519E90BA21D4F4B0589E0DD8934A69F3A1957040 |
| SSDEEP: | 768:I18yfZb2262yUP8NQyTfVh9yFUn2+EDk19YZJ:IqylRrP8NQUz9GaX9 |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 372)
- WerFault.exe (PID: 2612)
- svchost.exe (PID: 860)
SUSPICIOUS
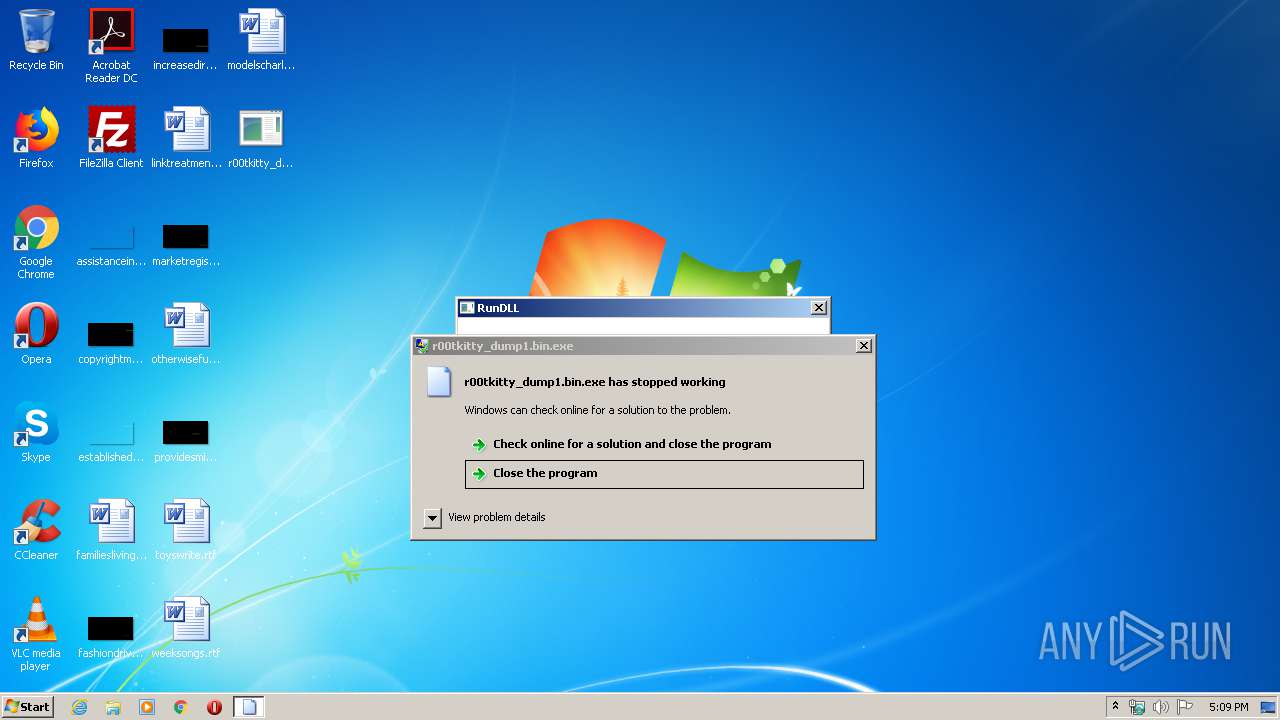
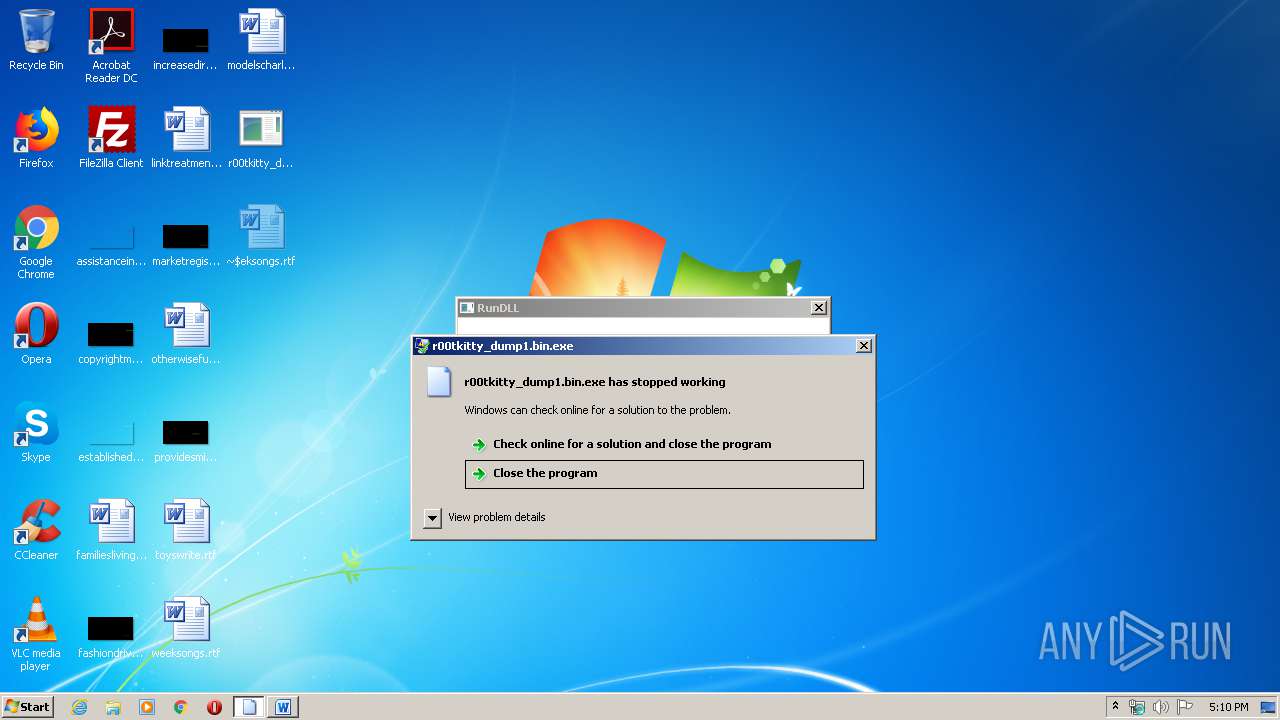
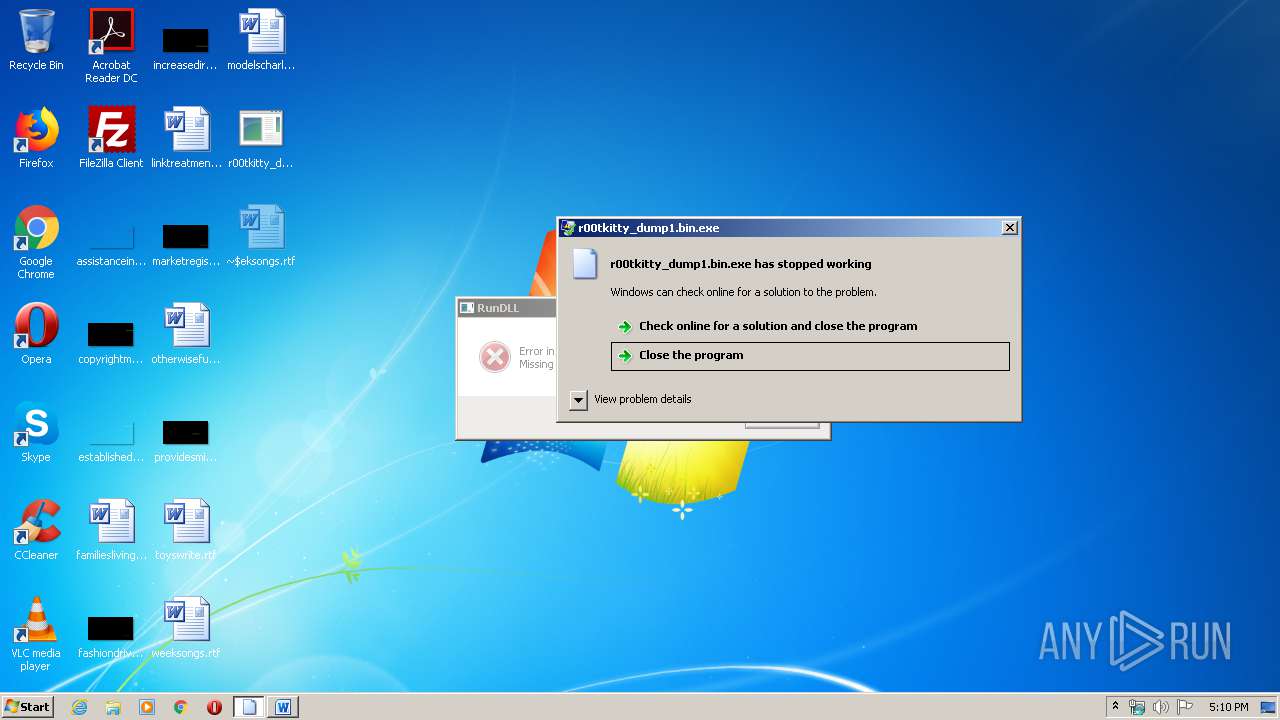
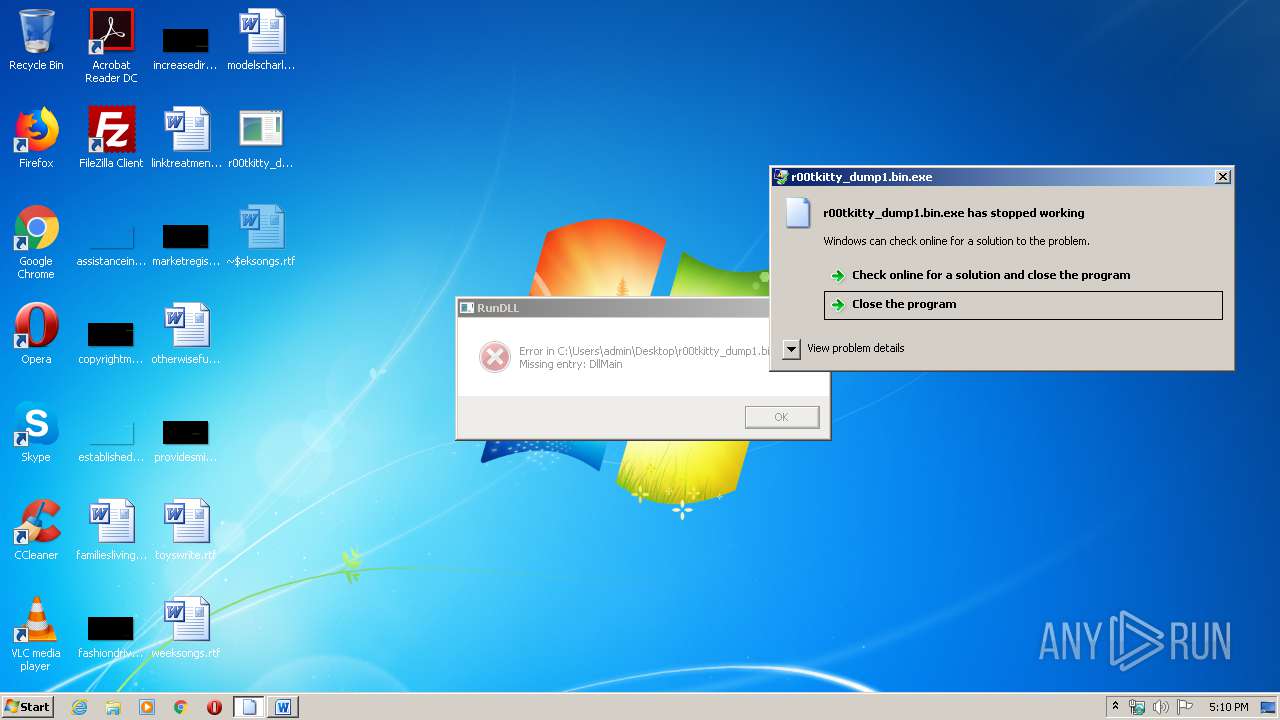
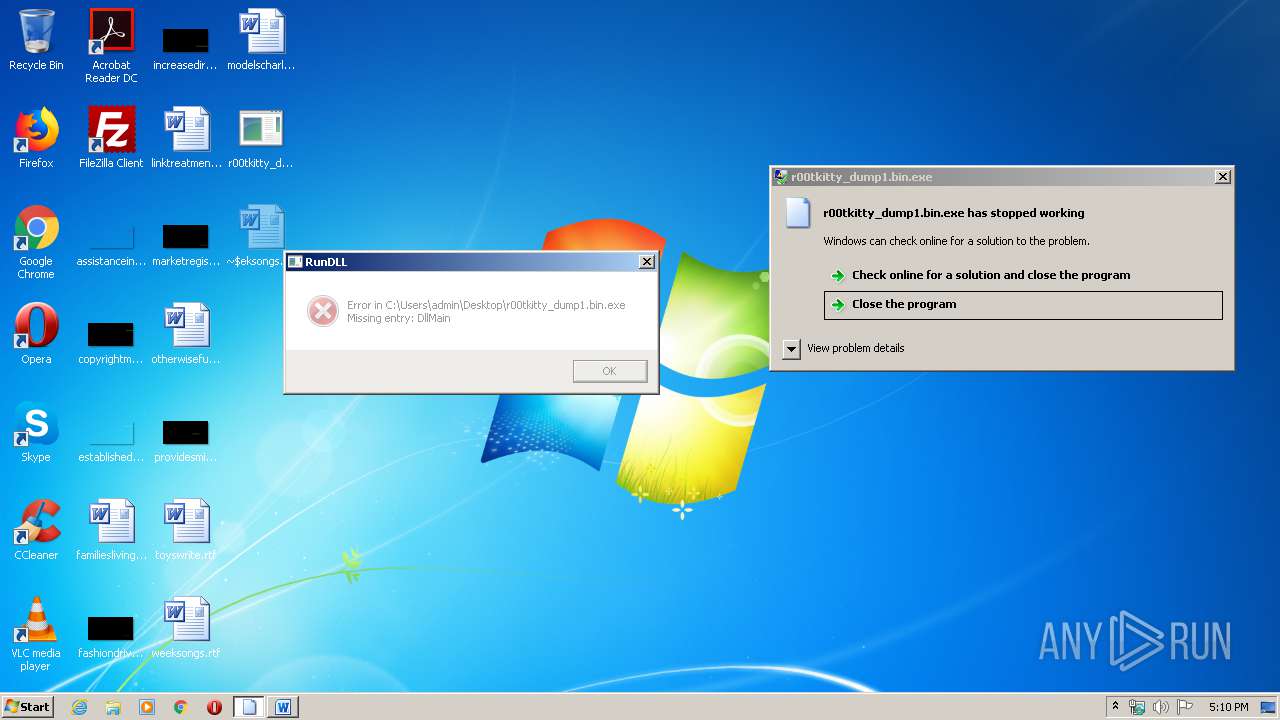
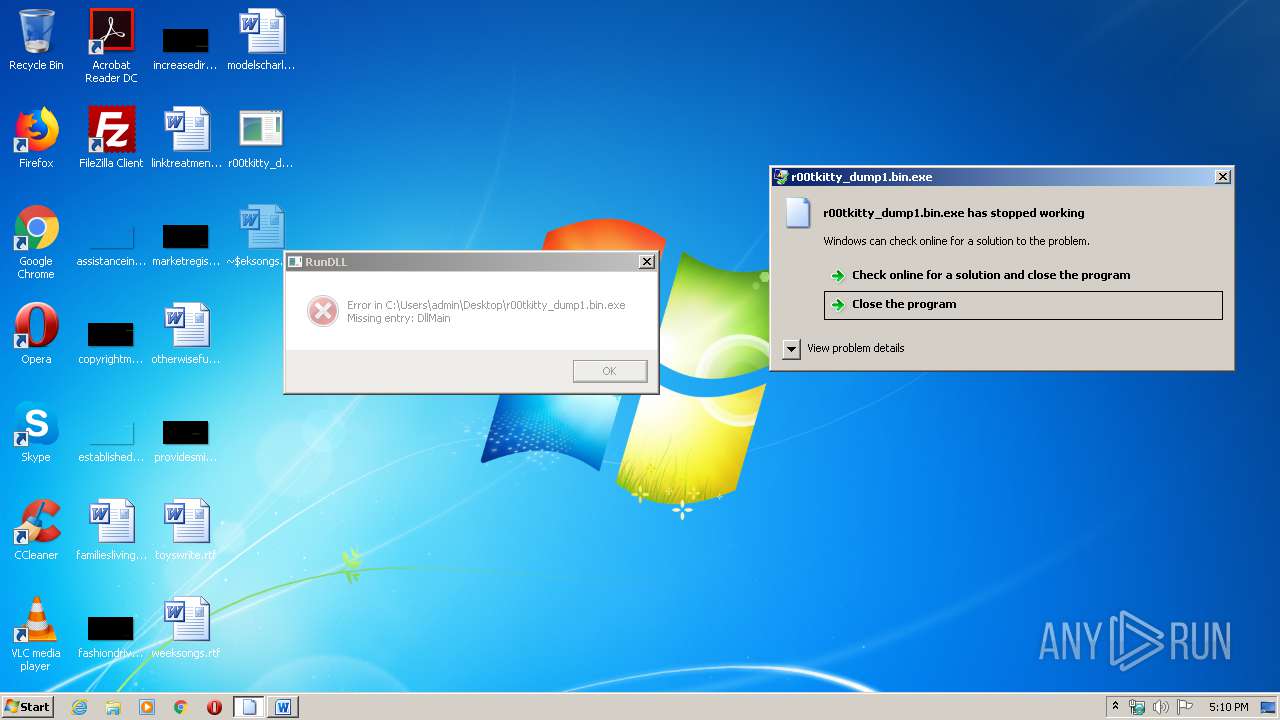
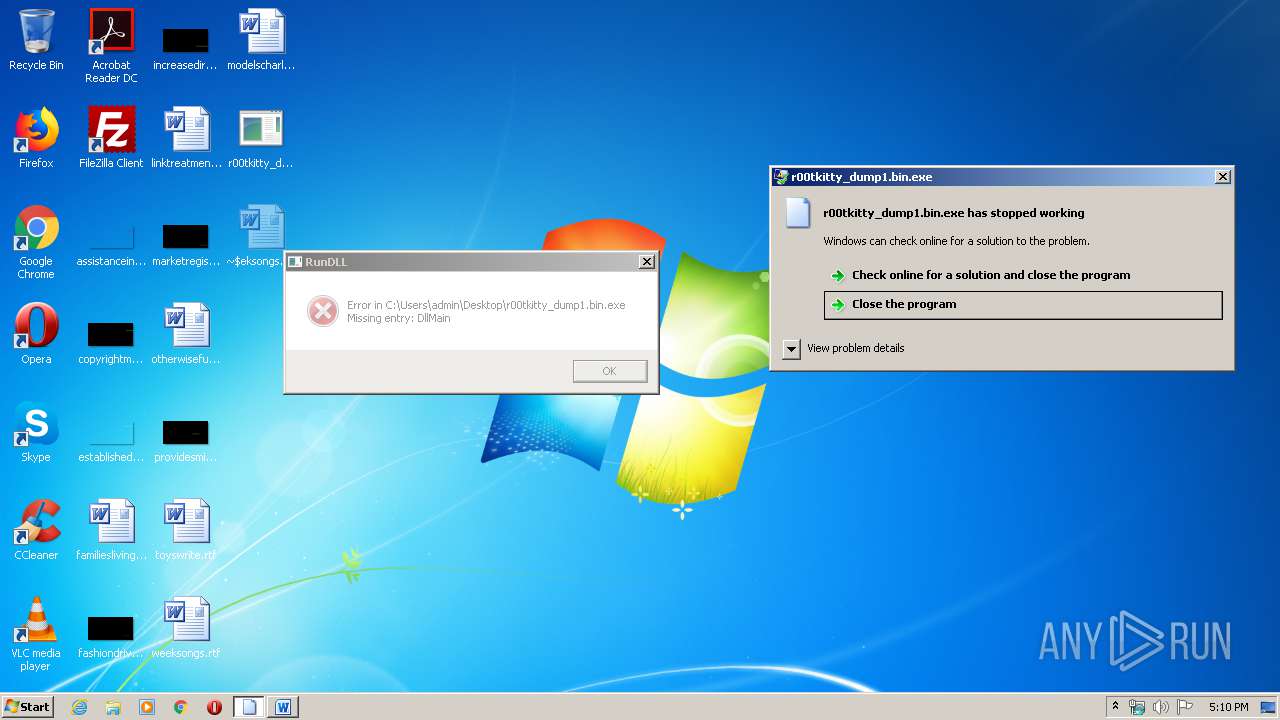
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 372)
Creates files in the user directory
- explorer.exe (PID: 372)
INFO
Loads main object executable
- rundll32.exe (PID: 3236)
Starts Microsoft Office Application
- explorer.exe (PID: 372)
Creates files in the user directory
- WINWORD.EXE (PID: 1872)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:30 20:41:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 20480 |
| InitializedDataSize: | 15360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1aaa |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-May-2018 18:41:50 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-May-2018 18:41:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004E2A | 0x00005000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45838 |
.rdata | 0x00006000 | 0x000020C0 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.69041 |
.data | 0x00009000 | 0x000018FC | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.44541 |
.rsrc | 0x0000B000 | 0x000002B8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16876 |
.reloc | 0x0000C000 | 0x000009F2 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.82019 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
2 | 4.94904 | 607 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
Total processes
39
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\weeksongs.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2612 | C:\Windows\system32\WerFault.exe -u -p 3236 -s 184 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3236 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\Desktop\r00tkitty_dump1.bin.exe", DllMain | C:\Windows\System32\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 205
Read events
2 480
Write events
580
Delete events
145
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1350434878 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {7P5N40RS-N0SO-4OSP-874N-P0S2R0O9SN8R}\Zvpebfbsg Bssvpr\Bssvpr14\JVAJBEQ.RKR |
Value: 00000000060000000500000053190000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF005430AEAD06D60100000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000400000004F0000007EAB25000A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rtf\OpenWithList |
| Operation: | write | Name: | a |
Value: WINWORD.EXE | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rtf\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rtf\OpenWithProgids |
| Operation: | write | Name: | Word.RTF.8 |
Value: | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs |
| Operation: | write | Name: | 9 |
Value: 7700650065006B0073006F006E00670073002E0072007400660000007C003200000000000000000000007765656B736F6E67732E727466202832292E6C6E6B00580008000400EFBE00000000000000002A000000000000000000000000000000000000000000000000007700650065006B0073006F006E00670073002E0072007400660020002800320029002E006C006E006B00000024000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs\.rtf |
| Operation: | write | Name: | 0 |
Value: 7700650065006B0073006F006E00670073002E0072007400660000007C003200000000000000000000007765656B736F6E67732E727466202832292E6C6E6B00580008000400EFBE00000000000000002A000000000000000000000000000000000000000000000000007700650065006B0073006F006E00670073002E0072007400660020002800320029002E006C006E006B00000024000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RecentDocs\.rtf |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
Executable files
0
Suspicious files
1
Text files
2
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1872 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR92D2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 372 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\weeksongs.rtf (2).lnk | lnk | |
MD5:— | SHA256:— | |||
| 372 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\a7bd71699cd38d1c.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 1872 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
| 860 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 372 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 1872 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\weeksongs.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2612 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_rundll32.exe_r00_cfd322f6229a81e2bbf559dd10ebfcd7322850ab_0a92e1ec\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 1872 | WINWORD.EXE | C:\Users\admin\Desktop\~$eksongs.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2612 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\rundll32.exe.3236.dmp | dmp | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report